| File name: | sconnect-host-v2.9.1.0.exe |
| Full analysis: | https://app.any.run/tasks/a7f77495-9dba-43bc-91ad-44875e07e804 |
| Verdict: | Malicious activity |
| Analysis date: | June 20, 2019, 12:53:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 2D5F19B7B17706CA86B75A1D30FC8639 |
| SHA1: | ADC711D8262F1F7C822C77AB3EA48D4318BB75DA |
| SHA256: | 7A441EAD732E6B37614C56F3297653FBB040608C598EA82A44E214E4368E7F36 |
| SSDEEP: | 6144:BzZZOD/vhNKTxbW3Cj4TTxxKIPfoMu1vxit3SE1jtZ:BzZADr6WesD7H+Zs |
MALICIOUS
Application was dropped or rewritten from another process
- nsE71.tmp (PID: 3120)
- nsEEF.tmp (PID: 3448)
Loads dropped or rewritten executable
- sconnect-host-v2.9.1.0.exe (PID: 1892)
SUSPICIOUS
Executable content was dropped or overwritten
- sconnect-host-v2.9.1.0.exe (PID: 1892)
Uses TASKKILL.EXE to kill process
- nsEEF.tmp (PID: 3448)
Starts application with an unusual extension
- sconnect-host-v2.9.1.0.exe (PID: 1892)
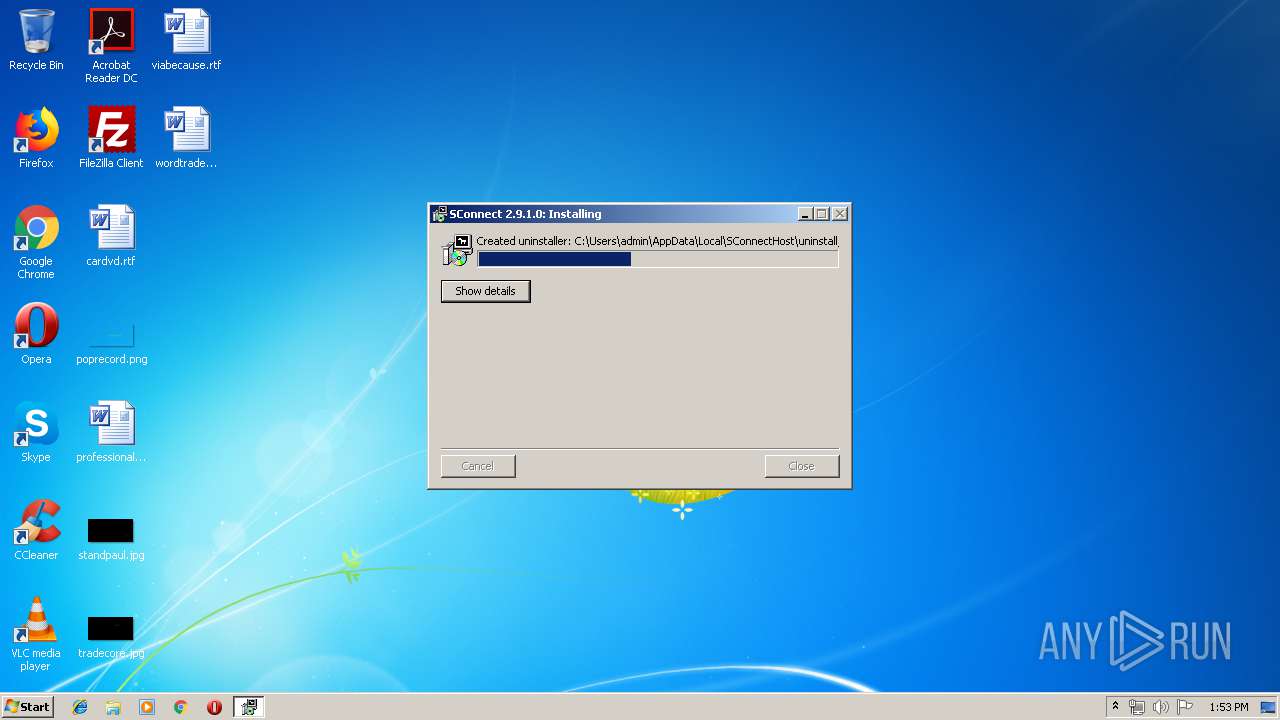
Creates a software uninstall entry
- sconnect-host-v2.9.1.0.exe (PID: 1892)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:07:06 16:31:20+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 26624 |
| InitializedDataSize: | 475136 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3415 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.9.1.0 |
| ProductVersionNumber: | 2.9.1.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | SConnect |
| CompanyName: | Gemalto |
| FileDescription: | SConnect |
| FileVersion: | 2.9.1.0 |
| LegalCopyright: | © Gemalto 2006 |
| LegalTrademarks: | SConnect is a trademark of Gemalto |
| ProductName: | SConnect |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Jul-2011 14:31:20 |
| Detected languages: |
|
| Comments: | SConnect |
| CompanyName: | Gemalto |
| FileDescription: | SConnect |
| FileVersion: | 2.9.1.0 |
| LegalCopyright: | © Gemalto 2006 |
| LegalTrademarks: | SConnect is a trademark of Gemalto |
| ProductName: | SConnect |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Jul-2011 14:31:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000671C | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50461 |
.rdata | 0x00008000 | 0x000019D6 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02684 |
.data | 0x0000A000 | 0x0007139C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.73601 |
.ndata | 0x0007C000 | 0x00089000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00105000 | 0x00000DA8 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.43966 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22631 | 957 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
38
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "taskkill" /IM sconnect.exe | C:\Windows\system32\taskkill.exe | — | nsEEF.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1892 | "C:\Users\admin\AppData\Local\Temp\sconnect-host-v2.9.1.0.exe" | C:\Users\admin\AppData\Local\Temp\sconnect-host-v2.9.1.0.exe | explorer.exe | ||||||||||||
User: admin Company: Gemalto Integrity Level: MEDIUM Description: SConnect Exit code: 0 Version: 2.9.1.0 Modules
| |||||||||||||||
| 3120 | "C:\Users\admin\AppData\Local\Temp\nsfE70.tmp\nsE71.tmp" C:\Users\admin\AppData\Local\SConnectHost\..\SConnectCR\uninstall_sconnect.exe | C:\Users\admin\AppData\Local\Temp\nsfE70.tmp\nsE71.tmp | — | sconnect-host-v2.9.1.0.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225501 Modules
| |||||||||||||||
| 3448 | "C:\Users\admin\AppData\Local\Temp\nsfE70.tmp\nsEEF.tmp" "taskkill" /IM sconnect.exe | C:\Users\admin\AppData\Local\Temp\nsfE70.tmp\nsEEF.tmp | — | sconnect-host-v2.9.1.0.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 128 Modules
| |||||||||||||||
Total events
342
Read events
333
Write events
9
Delete events
0
Modification events
| (PID) Process: | (1892) sconnect-host-v2.9.1.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\SConnectHost |
| Operation: | write | Name: | DisplayName |
Value: SConnect Host | |||
| (PID) Process: | (1892) sconnect-host-v2.9.1.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\SConnectHost |
| Operation: | write | Name: | UninstallString |
Value: C:\Users\admin\AppData\Local\SConnectHost\uninstall_sconnect.exe | |||
| (PID) Process: | (1892) sconnect-host-v2.9.1.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\SConnectHost |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\SConnectHost | |||
| (PID) Process: | (1892) sconnect-host-v2.9.1.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\SConnectHost |
| Operation: | write | Name: | Publisher |
Value: Gemalto | |||
| (PID) Process: | (1892) sconnect-host-v2.9.1.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\SConnectHost |
| Operation: | write | Name: | DisplayVersion |
Value: 2.9.1.0 | |||
| (PID) Process: | (1892) sconnect-host-v2.9.1.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\SConnectHost |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (1892) sconnect-host-v2.9.1.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\SConnectHost |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (1892) sconnect-host-v2.9.1.0.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\NativeMessagingHosts\com.gemalto.sconnect |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\SConnectHost\host.json | |||
| (PID) Process: | (1892) sconnect-host-v2.9.1.0.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\NativeMessagingHosts\com.gemalto.sconnect |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\SConnectHost\host-ff.json | |||
Executable files
5
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1892 | sconnect-host-v2.9.1.0.exe | C:\Users\admin\AppData\Local\Temp\nsfE70.tmp\FindProcDLL.dll | — | |
MD5:— | SHA256:— | |||
| 1892 | sconnect-host-v2.9.1.0.exe | C:\Users\admin\AppData\Local\Temp\nsfE70.tmp\nsEEF.tmp | executable | |
MD5:— | SHA256:— | |||
| 1892 | sconnect-host-v2.9.1.0.exe | C:\Users\admin\AppData\Local\Temp\nsfE70.tmp\nsE71.tmp | executable | |
MD5:— | SHA256:— | |||
| 1892 | sconnect-host-v2.9.1.0.exe | C:\Users\admin\AppData\Local\SConnectHost\uninstall_sconnect.exe | executable | |
MD5:— | SHA256:— | |||
| 1892 | sconnect-host-v2.9.1.0.exe | C:\Users\admin\AppData\Local\SConnectHost\sconnect.exe | executable | |
MD5:— | SHA256:— | |||
| 1892 | sconnect-host-v2.9.1.0.exe | C:\Users\admin\AppData\Local\Temp\nsfE70.tmp\nsExec.dll | executable | |
MD5:55317A22D09C800966CC2F45B82AA5A3 | SHA256:7A920776397D079C2D4525E85BB32D47C2CA938D4BD01EAF4473D2AD89F09322 | |||
| 1892 | sconnect-host-v2.9.1.0.exe | C:\Users\admin\AppData\Local\SConnectHost\host.json | text | |
MD5:06F9A5B830175D07740BE2BFBDCCF0AF | SHA256:E537C8BB6033A278C4E4FC0F2448A76E644E2A2E4FF6C480677D39067E03DE2C | |||
| 1892 | sconnect-host-v2.9.1.0.exe | C:\Users\admin\AppData\Local\SConnectHost\host-ff.json | text | |
MD5:AE9DF05435C139971045D63EC7424A04 | SHA256:9671199EF062E8C89F1443C9037CADEADD3741A2ABA92BB7B3F59F27EDF16D6E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report