| File name: | archangel-v1.5.exe |
| Full analysis: | https://app.any.run/tasks/ca05b0eb-c629-452c-a59e-3db19ac4e36d |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2022, 20:17:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 539D159BAFA6A2E436DFB71980E84BAF |
| SHA1: | D0148F367F8591FD2A835489947C35901B20F4CF |
| SHA256: | 7A412AE3911FF20DD3B08920E029EFA673B42A99A4A1713F4D686541B6C66DA3 |
| SSDEEP: | 196608:XH6d3xtDWN7GtEDcIsIVB/cWWQFVLKxgdlTPybgqSpDiRDm71J8c94amBq9waIrp:X6d3xtDDedHB/vVLWgd1PyTaORDm73Ns |
MALICIOUS
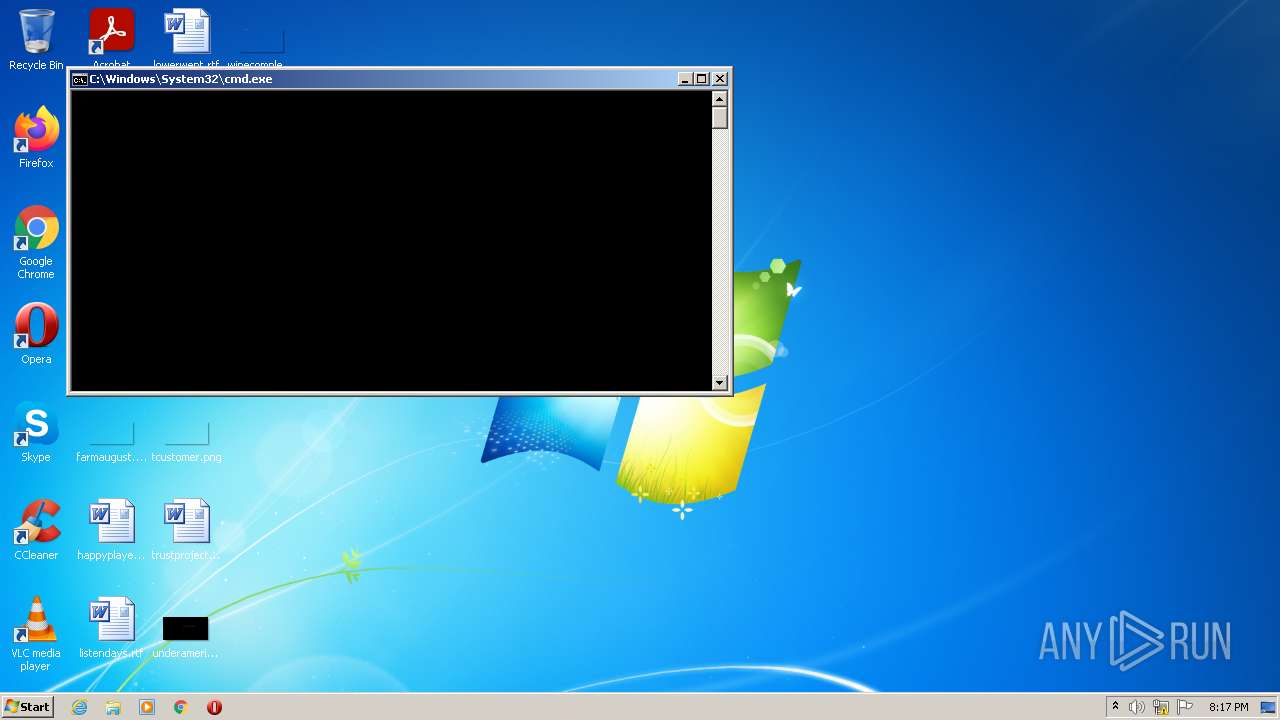
Drops executable file immediately after starts
- cmd.exe (PID: 3892)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 1808)
- cmd.exe (PID: 2848)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2792)
- schtasks.exe (PID: 3276)
Changes the autorun value in the registry
- reg.exe (PID: 548)
- reg.exe (PID: 2880)
- reg.exe (PID: 3212)
- reg.exe (PID: 3276)
Application was dropped or rewritten from another process
- winlive.exe (PID: 928)
Runs app for hidden code execution
- winlive.exe (PID: 928)
SUSPICIOUS
Reads Microsoft Outlook installation path
- archangel-v1.5.exe (PID: 960)
Checks supported languages
- archangel-v1.5.exe (PID: 960)
- WScript.exe (PID: 2988)
- cmd.exe (PID: 328)
- cmd.exe (PID: 3892)
- cmd.exe (PID: 1924)
- cmd.exe (PID: 276)
- cmd.exe (PID: 2420)
- cmd.exe (PID: 2848)
- winlive.exe (PID: 928)
- cmd.exe (PID: 1808)
- cmd.exe (PID: 1492)
- WScript.exe (PID: 3768)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 964)
- cmd.exe (PID: 336)
- cmd.exe (PID: 2056)
- cmd.exe (PID: 1976)
Reads the computer name
- archangel-v1.5.exe (PID: 960)
- WScript.exe (PID: 2988)
- cmd.exe (PID: 1492)
- WScript.exe (PID: 3768)
Drops a file with too old compile date
- archangel-v1.5.exe (PID: 960)
Executes scripts
- archangel-v1.5.exe (PID: 960)
- cmd.exe (PID: 1492)
Executable content was dropped or overwritten
- archangel-v1.5.exe (PID: 960)
- cmd.exe (PID: 3892)
Drops a file that was compiled in debug mode
- archangel-v1.5.exe (PID: 960)
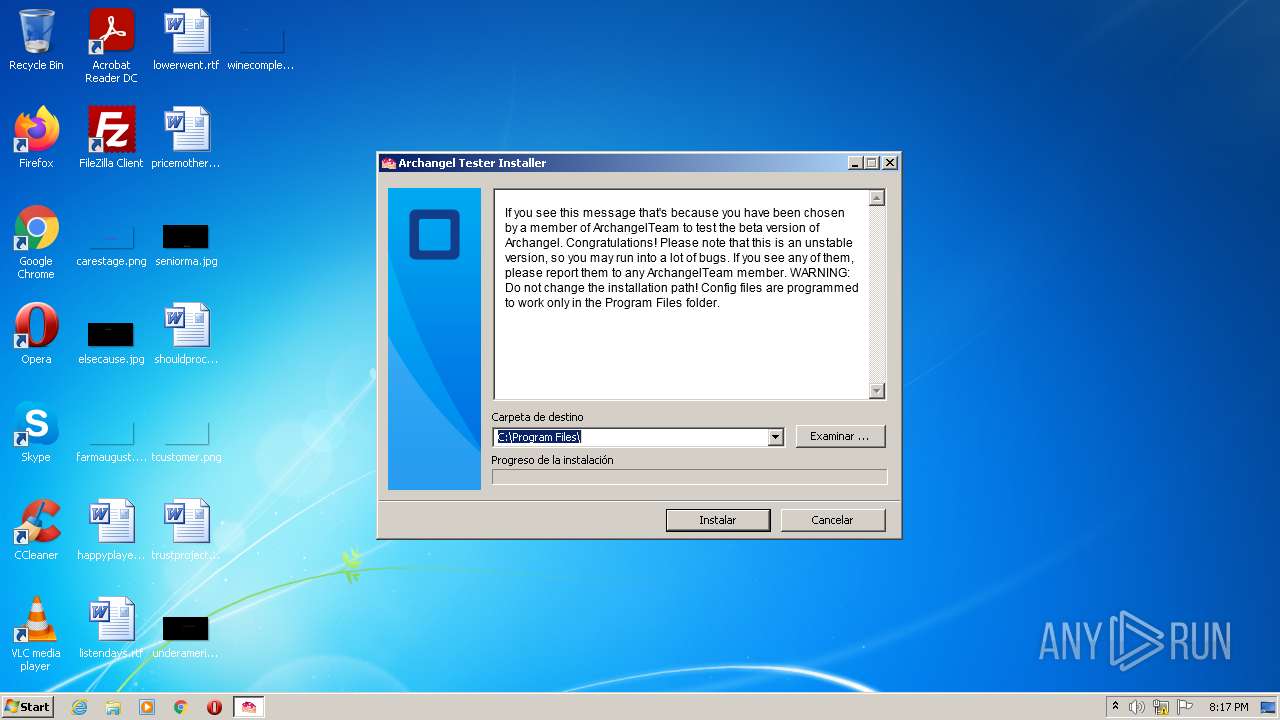
Creates a directory in Program Files
- archangel-v1.5.exe (PID: 960)
Drops a file with a compile date too recent
- archangel-v1.5.exe (PID: 960)
- cmd.exe (PID: 3892)
Reads internet explorer settings
- archangel-v1.5.exe (PID: 960)
Creates files in the program directory
- archangel-v1.5.exe (PID: 960)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2988)
- winlive.exe (PID: 928)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 964)
- cmd.exe (PID: 336)
- cmd.exe (PID: 2056)
- cmd.exe (PID: 3460)
Uses WHOAMI.EXE to obtaining logged on user information
- cmd.exe (PID: 1976)
INFO
Checks Windows Trust Settings
- WScript.exe (PID: 2988)
- WScript.exe (PID: 3768)
Checks supported languages
- schtasks.exe (PID: 2792)
- schtasks.exe (PID: 3276)
- reg.exe (PID: 548)
- reg.exe (PID: 2880)
- reg.exe (PID: 3212)
- reg.exe (PID: 3276)
- whoami.exe (PID: 3480)
Reads the computer name
- schtasks.exe (PID: 2792)
- schtasks.exe (PID: 3276)
- whoami.exe (PID: 3480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1f110 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 144384 |
| CodeSize: | 201216 |
| LinkerVersion: | 14.3 |
| PEType: | PE32 |
| TimeStamp: | 2022:01:24 08:31:18+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Jan-2022 07:31:18 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Jan-2022 07:31:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000311EA | 0x00031200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71153 |
.rdata | 0x00033000 | 0x0000AB02 | 0x0000AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23189 |
.data | 0x0003E000 | 0x000246D8 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.34668 |
.didat | 0x00063000 | 0x0000018C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.36381 |
.rsrc | 0x00064000 | 0x0001518C | 0x00015200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.01068 |
.reloc | 0x0007A000 | 0x0000229C | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56962 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26192 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.11236 | 440 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.21979 | 1132 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.12889 | 358 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.01704 | 338 | Latin 1 / Western European | English - United States | RT_STRING |
14 | 2.94627 | 266 | Latin 1 / Western European | English - United States | RT_STRING |
15 | 2.83619 | 188 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
76
Monitored processes
25
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Windows\System32\cmd.exe" /c move attrib +s +h "C:\Windows\System32\arch" | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 328 | "C:\Windows\System32\cmd.exe" /c mkdir C:\windows\system32\arch | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 336 | "C:\Windows\System32\cmd.exe" /c reg.exe add "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run" /f /v Java /t REG_SZ /d "C:\Windows\System32\arch\start.vbs" | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 548 | reg.exe add "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run" /f /v Java /t REG_SZ /d "C:\Windows\System32\arch\start.vbs" | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 928 | "C:\windows\syswow64\arch\winlive.exe" | C:\windows\syswow64\arch\winlive.exe | WScript.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 960 | "C:\Users\admin\AppData\Local\Temp\archangel-v1.5.exe" | C:\Users\admin\AppData\Local\Temp\archangel-v1.5.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 964 | "C:\Windows\System32\cmd.exe" /c reg.exe add "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run" /f /v HealthChecker /t REG_SZ /d "C:\Windows\Syswow64\arch\start.vbs" | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1492 | "C:\Windows\System32\cmd.exe" /c C:\Windows\System32\arch\start.vbs | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1808 | "C:\Windows\System32\cmd.exe" /c SCHTASKS /CREATE /SC ONLOGON /TN "Microsoft\SecurityChecker" /TR "C:\windows\syswow64\arch\start.vbs" /RU system | C:\Windows\System32\cmd.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1924 | "C:\Windows\System32\cmd.exe" /c move "C:\Program Files\archangel-v1.5\lib\bin\start.vbs" "C:\windows\system32\arch\start.vbs" | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 670
Read events
1 631
Write events
39
Delete events
0
Modification events
| (PID) Process: | (960) archangel-v1.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (960) archangel-v1.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (960) archangel-v1.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (960) archangel-v1.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (960) archangel-v1.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (960) archangel-v1.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (960) archangel-v1.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2988) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2988) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2988) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
52
Suspicious files
0
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 960 | archangel-v1.5.exe | C:\Program Files\archangel-v1.5\AdbWinApi.dll | executable | |
MD5:— | SHA256:— | |||
| 960 | archangel-v1.5.exe | C:\Program Files\archangel-v1.5\AdbWinUsbApi.dll | executable | |
MD5:— | SHA256:— | |||
| 960 | archangel-v1.5.exe | C:\Program Files\archangel-v1.5\adb.exe | executable | |
MD5:— | SHA256:— | |||
| 960 | archangel-v1.5.exe | C:\Program Files\archangel-v1.5\Archangel_v1.5.exe | executable | |
MD5:— | SHA256:— | |||
| 960 | archangel-v1.5.exe | C:\Program Files\archangel-v1.5\icon.ico | image | |
MD5:— | SHA256:— | |||
| 960 | archangel-v1.5.exe | C:\Program Files\archangel-v1.5\lib\AboveLockAppHost.dll | executable | |
MD5:— | SHA256:— | |||
| 960 | archangel-v1.5.exe | C:\Program Files\archangel-v1.5\avcodec-58.dll | executable | |
MD5:— | SHA256:— | |||
| 960 | archangel-v1.5.exe | C:\Program Files\archangel-v1.5\lib\aadauthhelper.dll | executable | |
MD5:— | SHA256:— | |||
| 960 | archangel-v1.5.exe | C:\Program Files\archangel-v1.5\avformat-58.dll | executable | |
MD5:— | SHA256:— | |||
| 960 | archangel-v1.5.exe | C:\Program Files\archangel-v1.5\avutil-56.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
928 | winlive.exe | 20.206.101.236:472 | — | — | US | suspicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
928 | winlive.exe | Successful Administrator Privilege Gain | ET ATTACK_RESPONSE Windows 7 CMD Shell from Local System |
928 | winlive.exe | Successful Administrator Privilege Gain | ET ATTACK_RESPONSE Possible MS CMD Shell opened on local system 2 |
928 | winlive.exe | Successful Administrator Privilege Gain | ET ATTACK_RESPONSE Windows 7 CMD Shell from Local System |
928 | winlive.exe | Successful Administrator Privilege Gain | ET ATTACK_RESPONSE Possible MS CMD Shell opened on local system 2 |