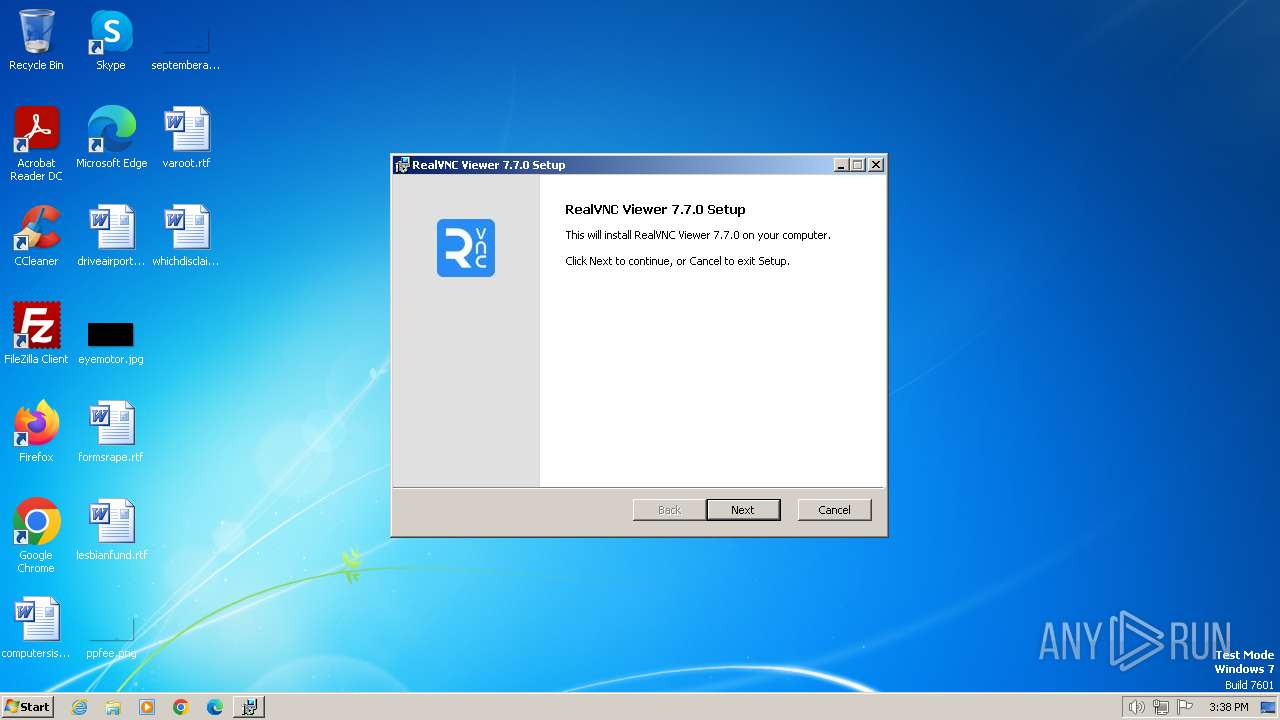
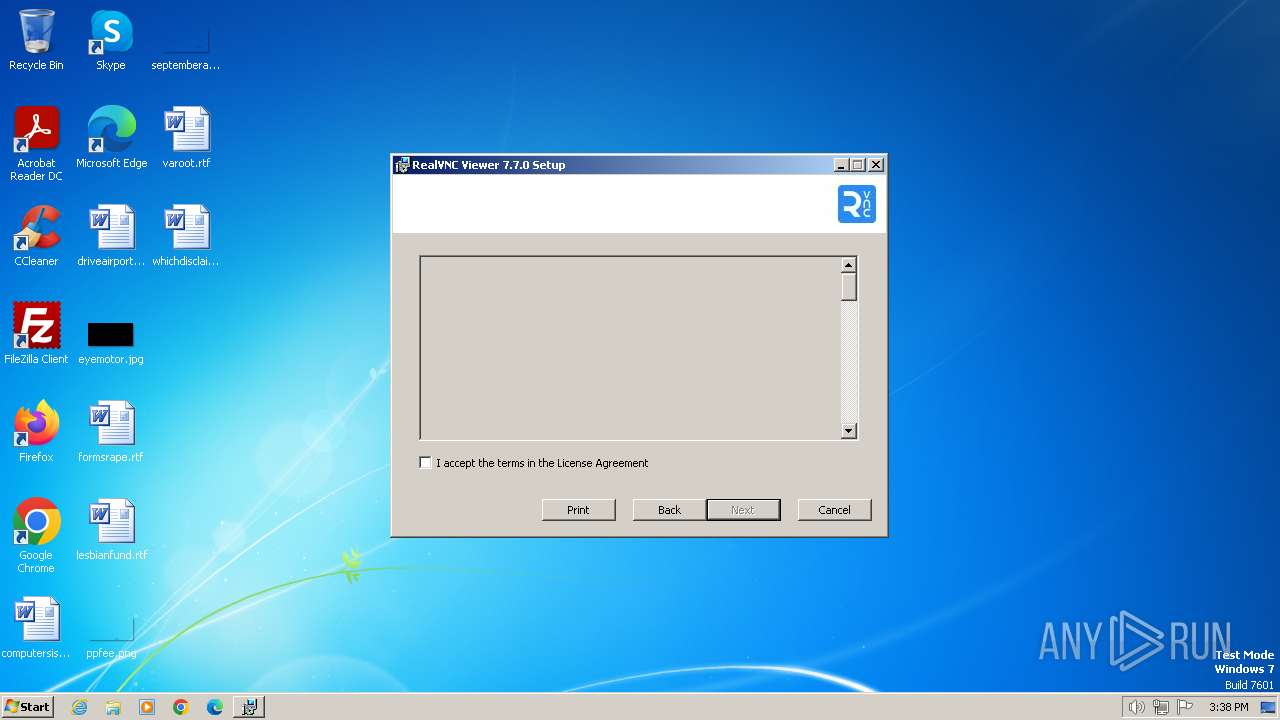
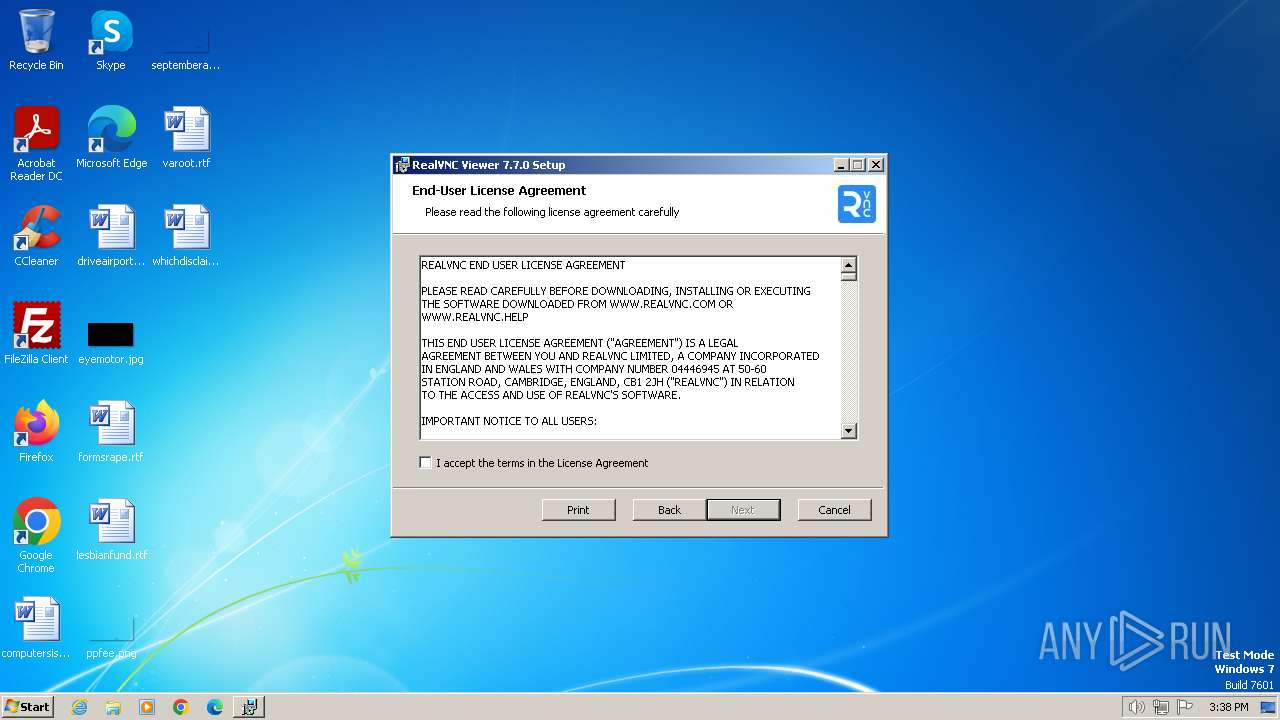
| File name: | VNC-Viewer-7.7.0-Windows.exe |
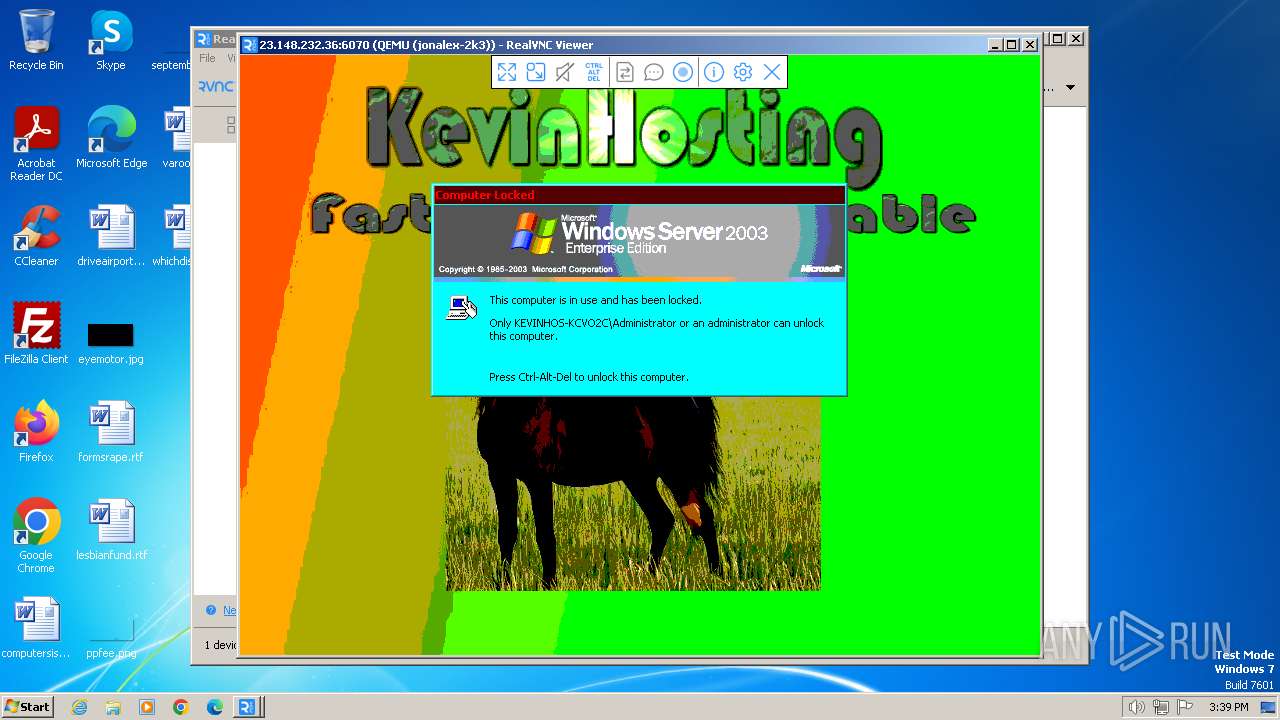
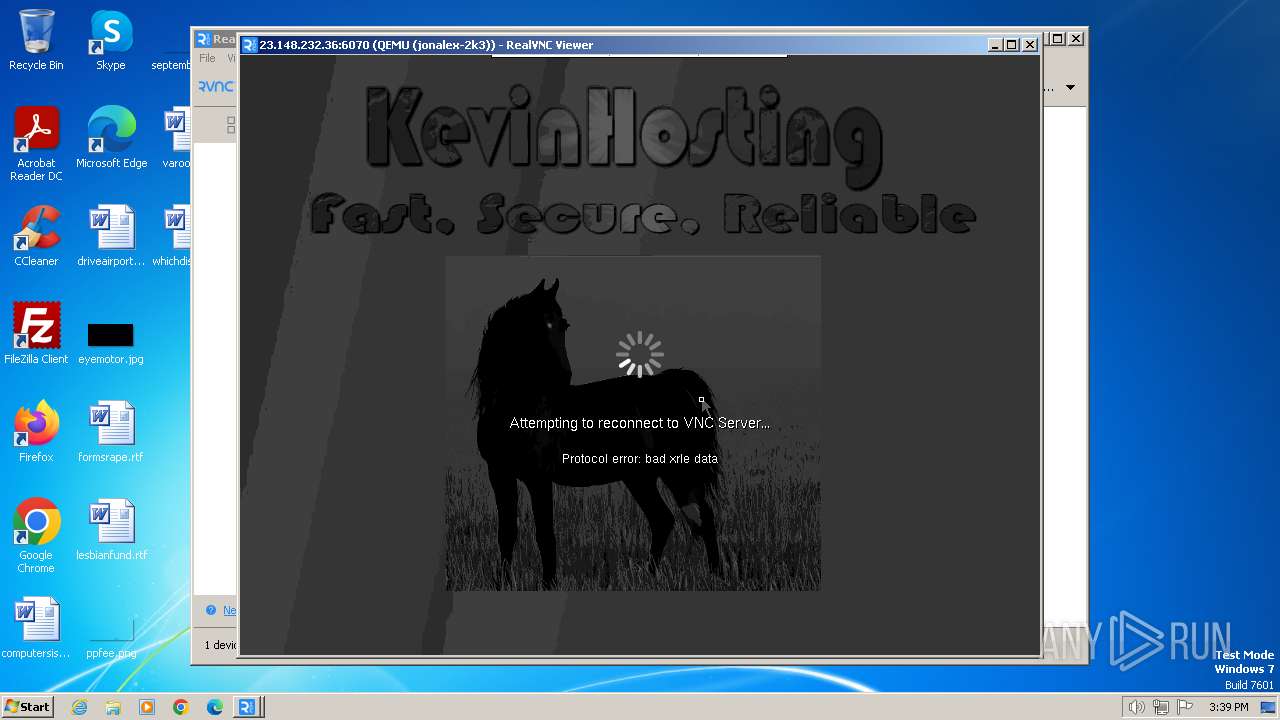
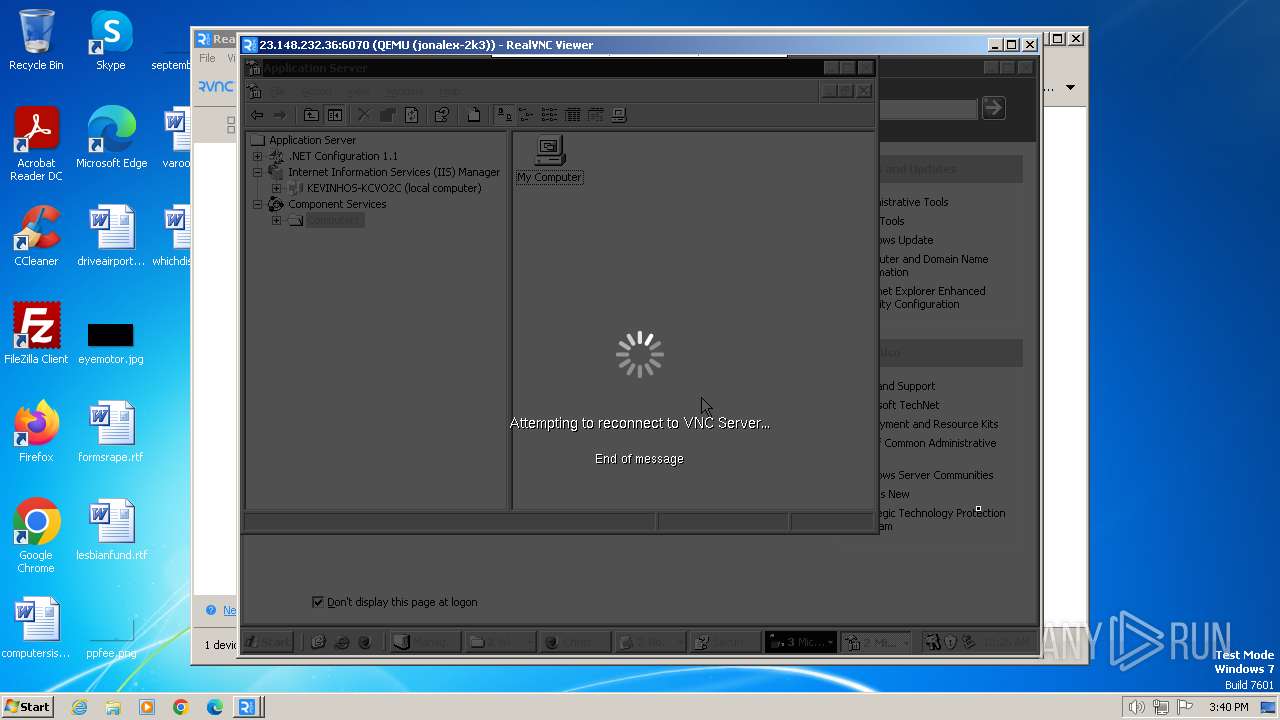
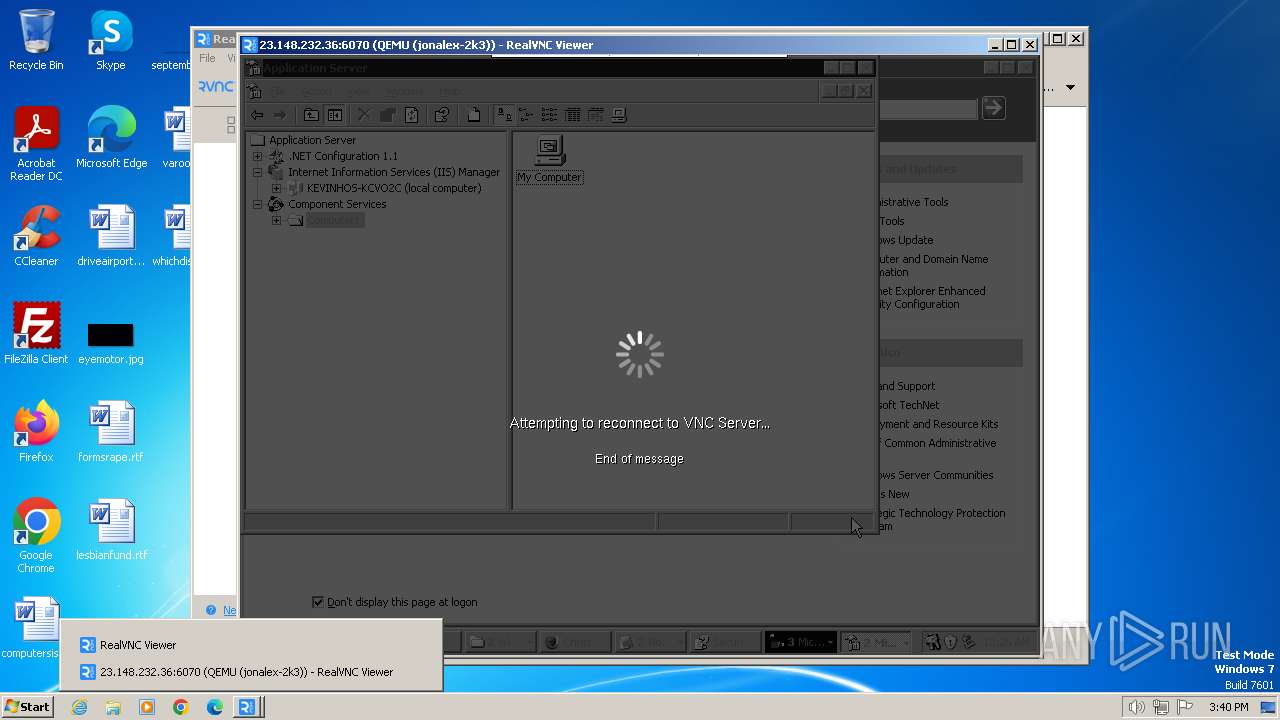
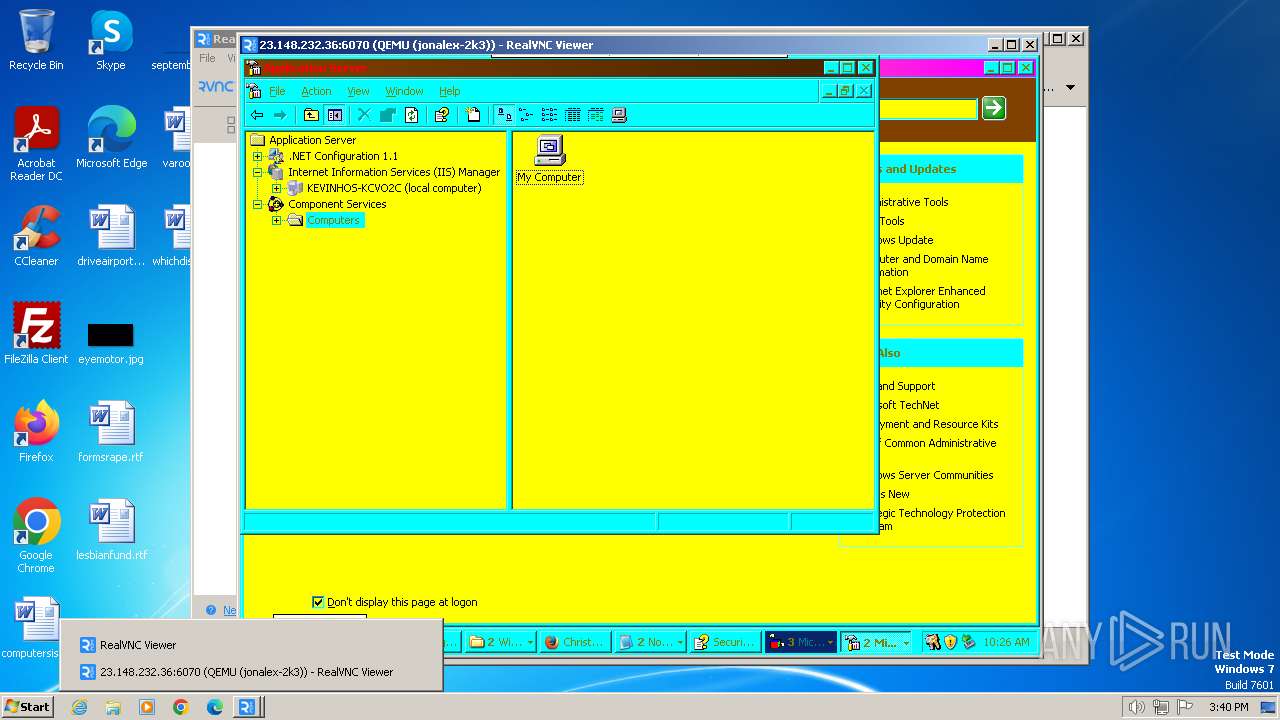
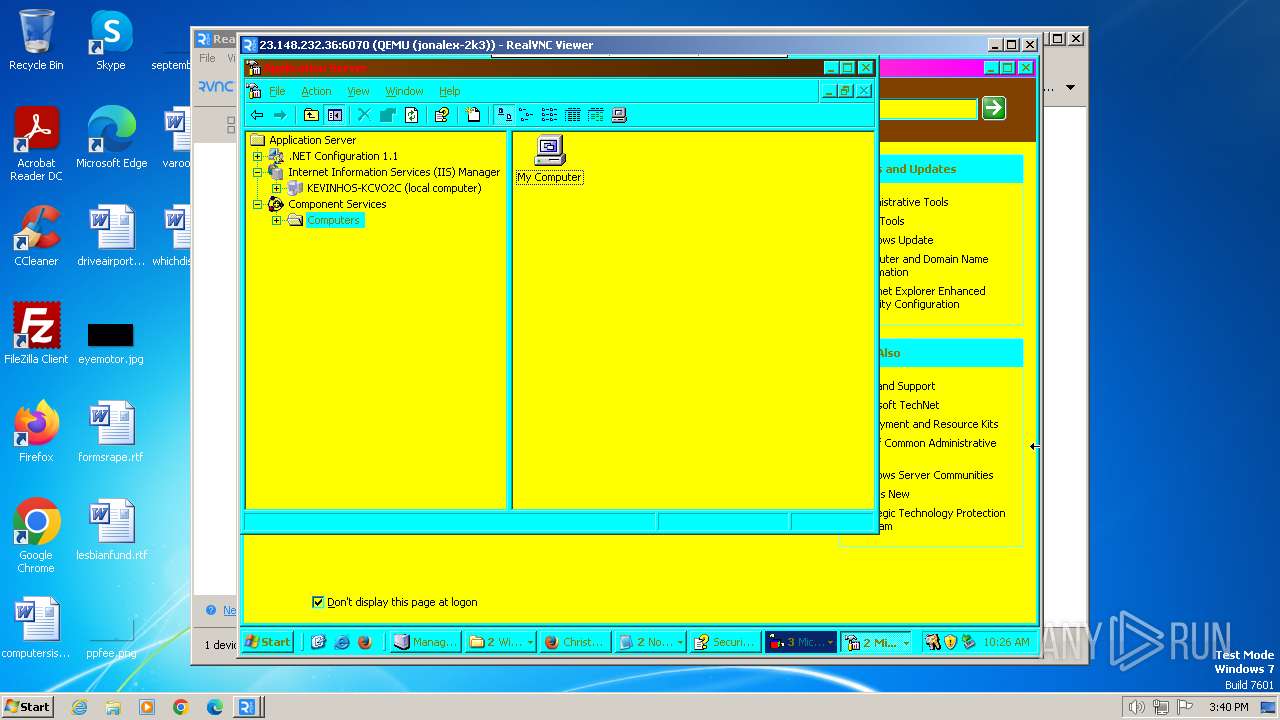
| Full analysis: | https://app.any.run/tasks/f5ce1713-fc45-4612-a0d4-9ae41a20354b |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2024, 15:37:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C0E535279E6DD9719B3E6C61056B6985 |
| SHA1: | E478432998C2033BC279A35E3A241ACDA8D1C765 |
| SHA256: | 7A3434FE3B26CA74B7B743BC195DBBECA3FB7CB56CCAF216C6BA39FAD0A334F8 |
| SSDEEP: | 98304:AvUyLBCdQ8EI/7mP09ANgcQTnzyaOisNAkHty4QJKYE6VFIMbz+oeW/xryZ4dG8s:bZRTXDXwihJGbK4D1 |
MALICIOUS
Drops the executable file immediately after the start
- VNC-Viewer-7.7.0-Windows.exe (PID: 128)
- msiexec.exe (PID: 2088)
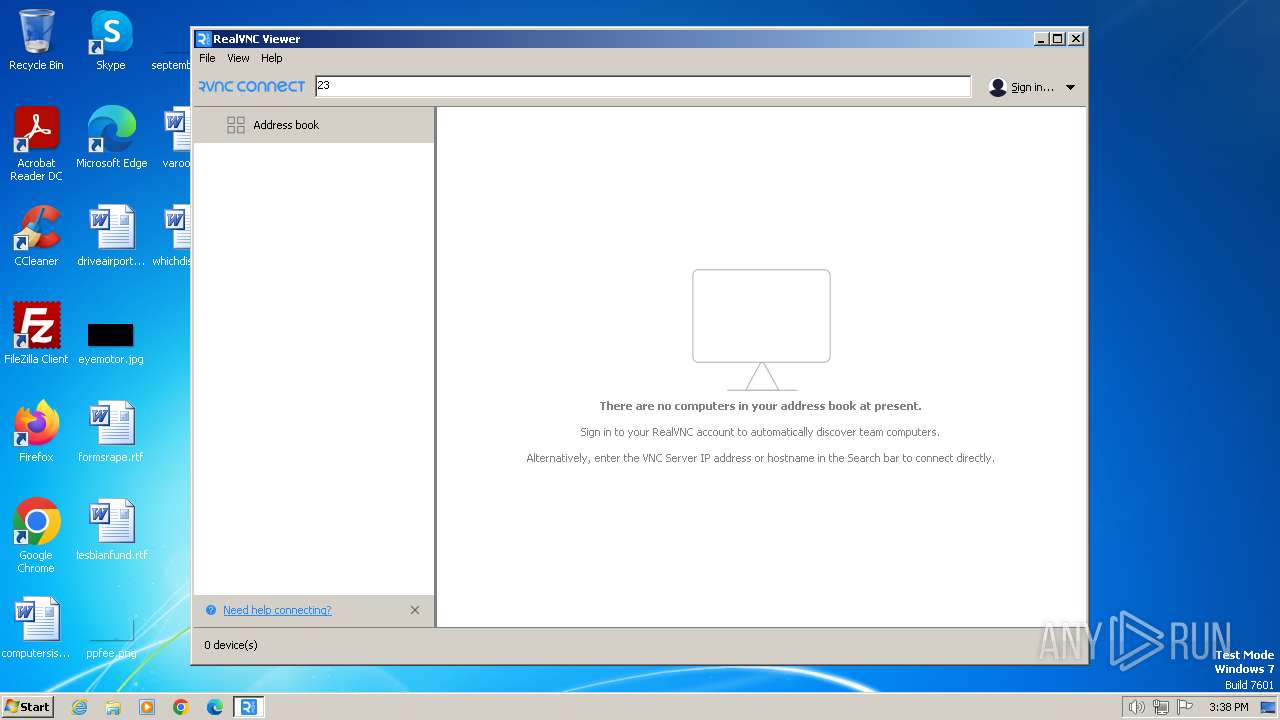
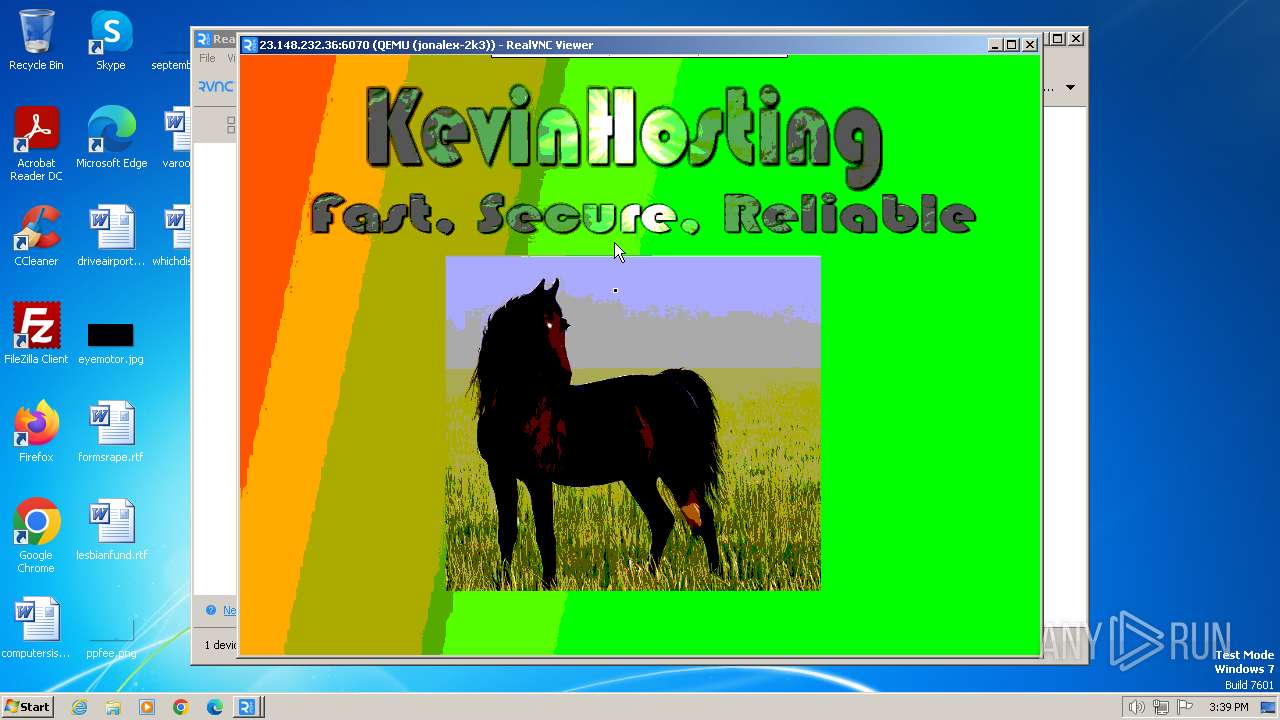
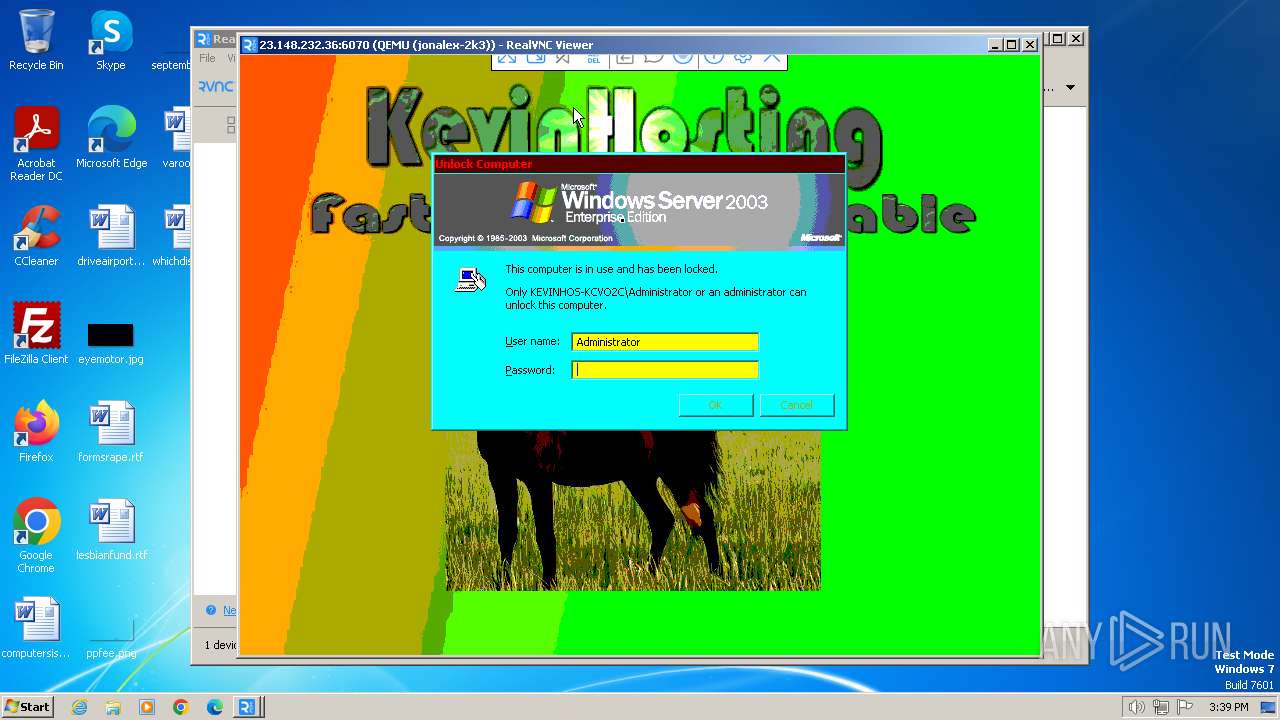
VNCCLIENT has been detected (SURICATA)
- vncviewer.exe (PID: 1984)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 2420)
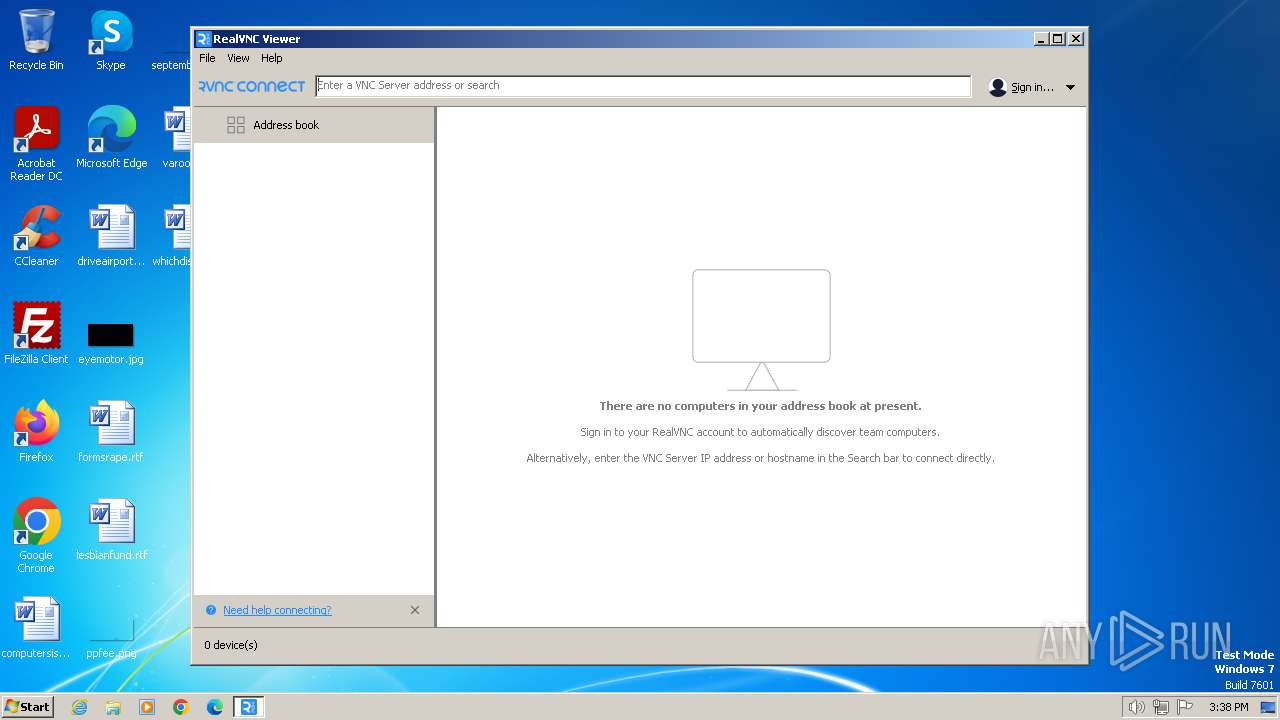
Reads the Internet Settings
- vncviewer.exe (PID: 1384)
- vncviewer.exe (PID: 1984)
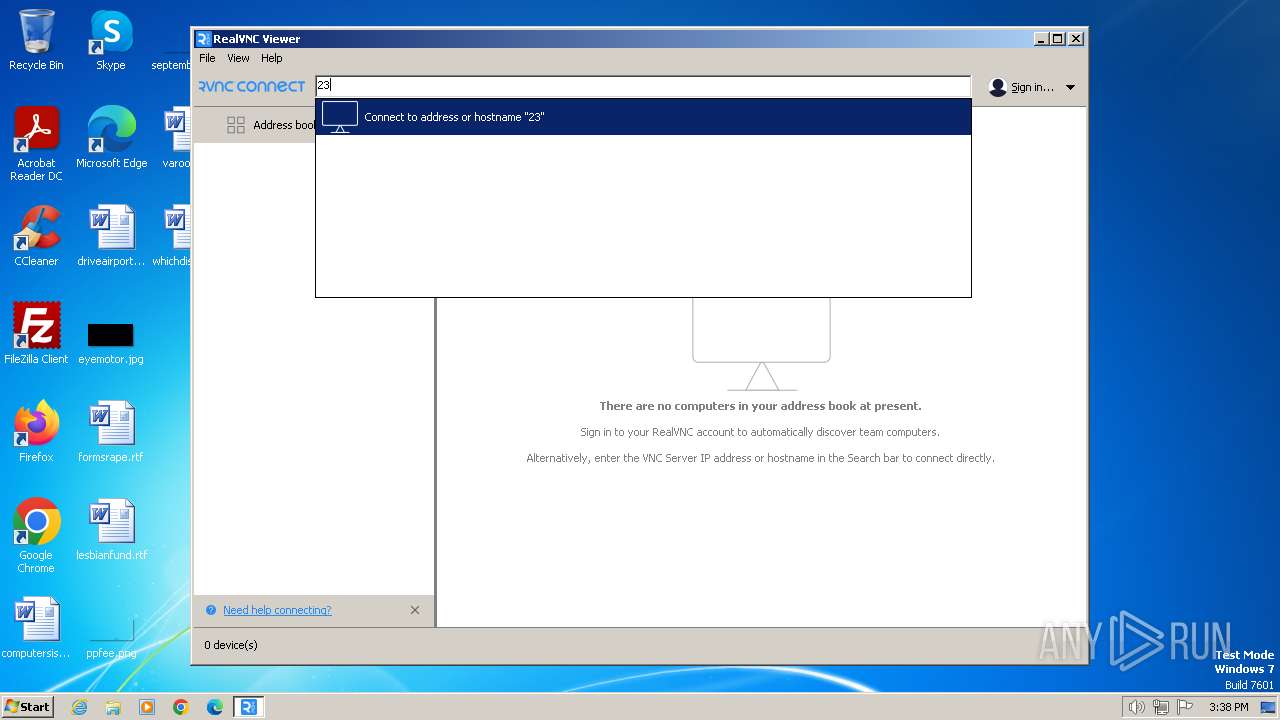
Application launched itself
- vncviewer.exe (PID: 1384)
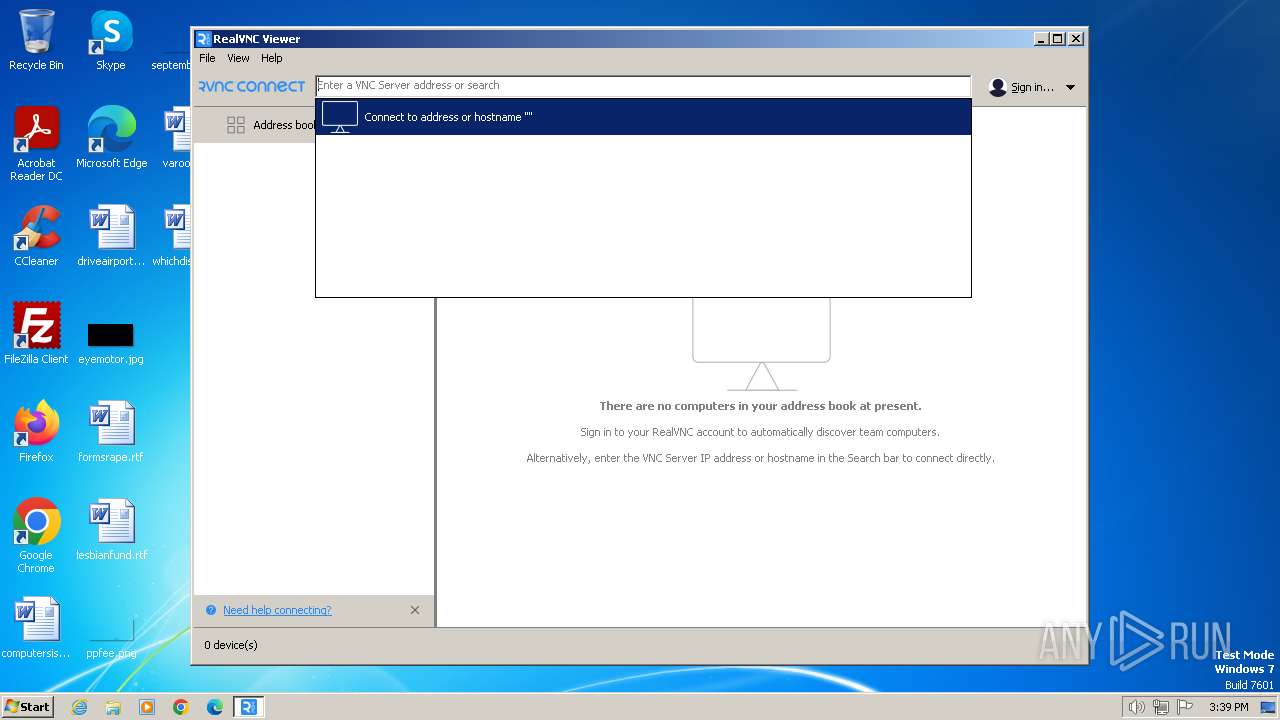
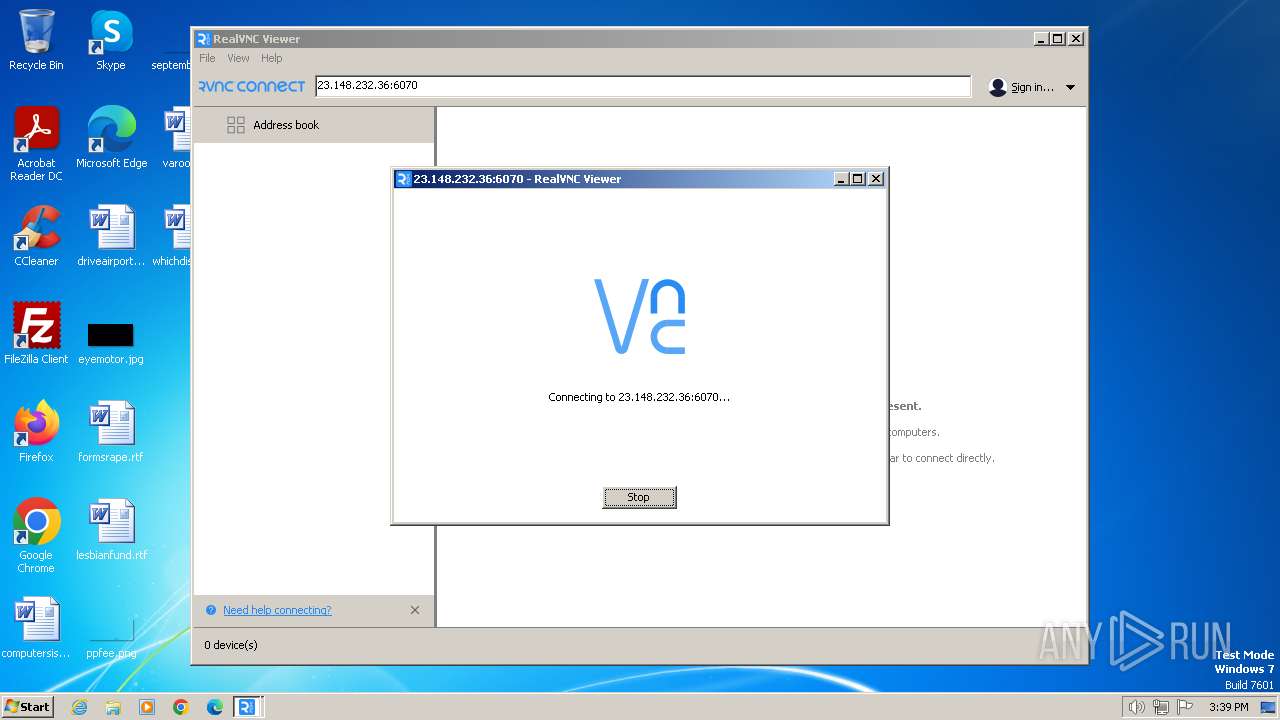
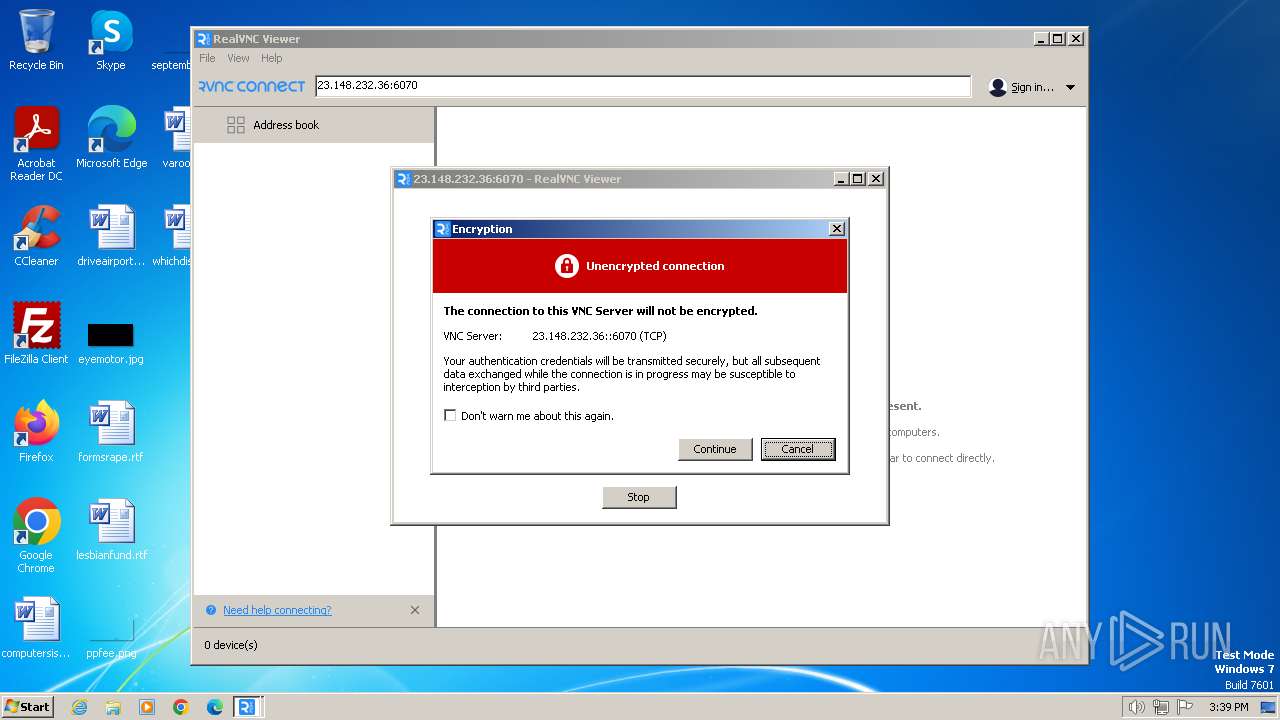
Connects to unusual port
- vncviewer.exe (PID: 1984)
Checks Windows Trust Settings
- msiexec.exe (PID: 2088)
INFO
Checks supported languages
- VNC-Viewer-7.7.0-Windows.exe (PID: 128)
- msiexec.exe (PID: 2088)
- vncviewer.exe (PID: 1384)
- vncviewer.exe (PID: 1984)
- msiexec.exe (PID: 2620)
Create files in a temporary directory
- VNC-Viewer-7.7.0-Windows.exe (PID: 128)
- msiexec.exe (PID: 2088)
Reads the computer name
- VNC-Viewer-7.7.0-Windows.exe (PID: 128)
- msiexec.exe (PID: 2088)
- vncviewer.exe (PID: 1384)
- vncviewer.exe (PID: 1984)
- msiexec.exe (PID: 2620)
Reads the machine GUID from the registry
- msiexec.exe (PID: 2088)
- vncviewer.exe (PID: 1384)
- vncviewer.exe (PID: 1984)
- msiexec.exe (PID: 2620)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1776)
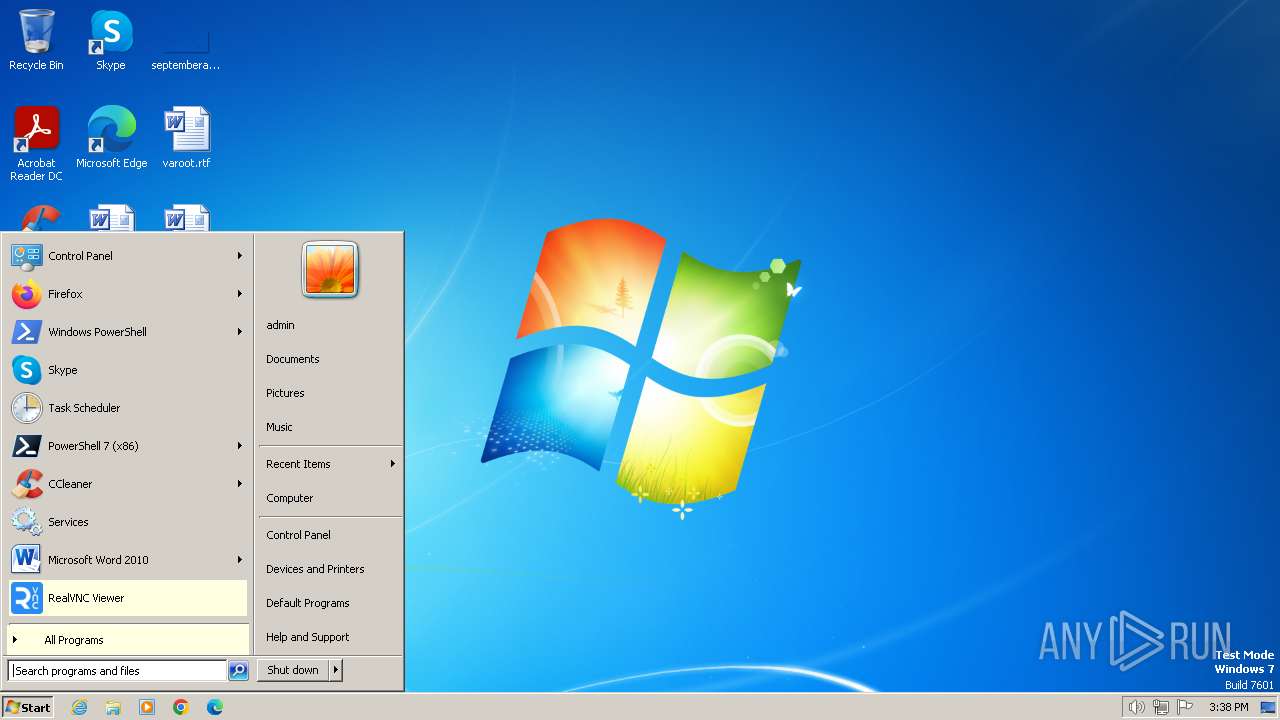
Manual execution by a user
- vncviewer.exe (PID: 1384)
Creates files or folders in the user directory
- vncviewer.exe (PID: 1384)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2088)
Application launched itself
- msiexec.exe (PID: 2088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:11 12:32:35+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 1190912 |
| InitializedDataSize: | 10396160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7b464 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.7.0.51227 |
| ProductVersionNumber: | 7.7.0.51227 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
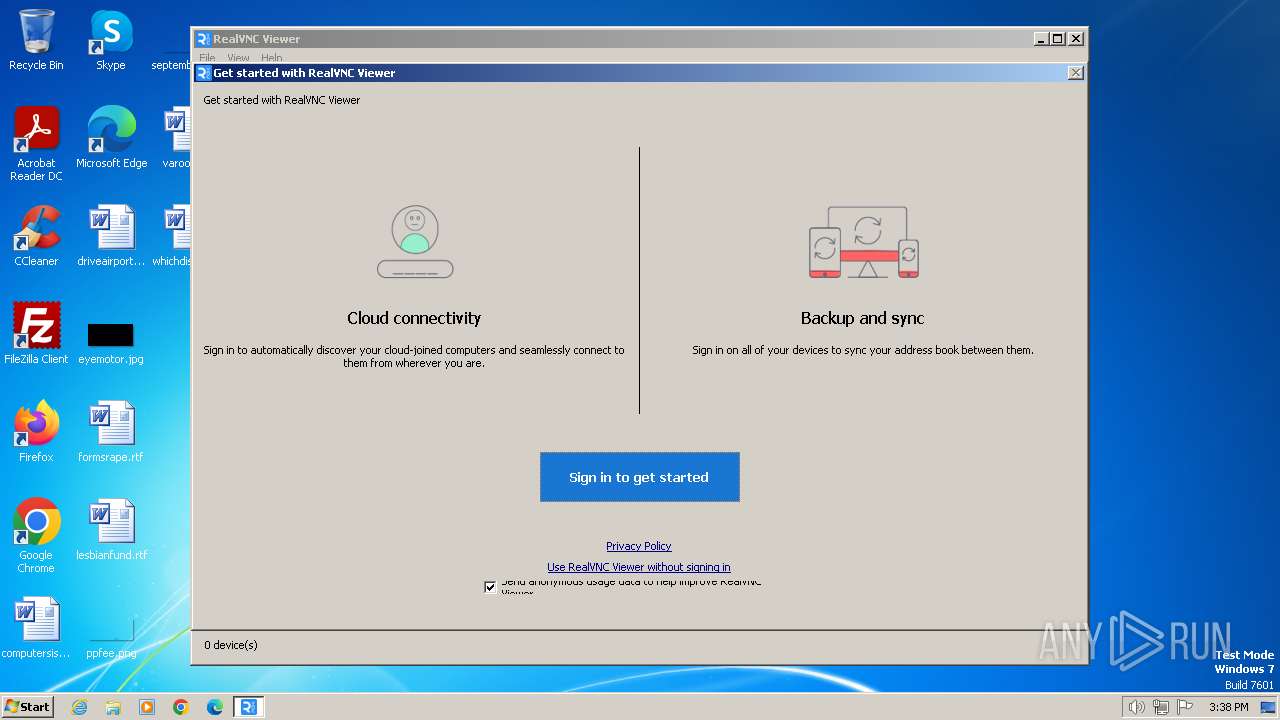
| CompanyName: | RealVNC |
| FileDescription: | VNC® Viewer Installer |
| FileVersion: | 7.7.0 (r51227) |
| InternalName: | vncviewer-installer |
| LegalCopyright: | Copyright © RealVNC Ltd. |
| LegalTrademarks: | RealVNC and VNC are trademarks of RealVNC Ltd and are protected by trademark registrations and/or pending trademark applications in the European Union, United States of America and other jurisdictions. |
| OriginalFileName: | vncviewer-installer.exe |
| ProductName: | VNC® |
| ProductVersion: | 7.7.0 (r51227) |
| ProgramName: | VNC® Viewer Installer |
Total processes
41
Monitored processes
7
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Users\admin\AppData\Local\Temp\VNC-Viewer-7.7.0-Windows.exe" | C:\Users\admin\AppData\Local\Temp\VNC-Viewer-7.7.0-Windows.exe | — | explorer.exe | |||||||||||
User: admin Company: RealVNC Integrity Level: MEDIUM Description: VNC® Viewer Installer Exit code: 0 Version: 7.7.0 (r51227) Modules
| |||||||||||||||
| 1384 | "C:\Program Files\RealVNC\VNC Viewer\vncviewer.exe" | C:\Program Files\RealVNC\VNC Viewer\vncviewer.exe | explorer.exe | ||||||||||||
User: admin Company: RealVNC Integrity Level: MEDIUM Description: VNC® Viewer Exit code: 0 Version: 7.7.0 (r51227) Modules
| |||||||||||||||
| 1776 | C:\Windows\system32\msiexec.exe /i C:\Users\admin\AppData\Local\Temp\vnc32.msi ProductLanguage=1033 | C:\Windows\System32\msiexec.exe | — | VNC-Viewer-7.7.0-Windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1984 | "C:\Program Files\RealVNC\VNC Viewer\vncviewer.exe" -child 23.148.232.36:6070 -hash bb9946d014521d4c0a78380bc5524cd87fd88af24727d6443183697b8f2fbc31 -sid S-1-5-21-1302019708-1500728564-335382590-1000 RealVNC.admin.vncviewer.launchpipe.316303053 | C:\Program Files\RealVNC\VNC Viewer\vncviewer.exe | vncviewer.exe | ||||||||||||
User: admin Company: RealVNC Integrity Level: MEDIUM Description: VNC® Viewer Exit code: 0 Version: 7.7.0 (r51227) Modules
| |||||||||||||||
| 2088 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2620 | C:\Windows\system32\MsiExec.exe -Embedding D9B75EC863B6DFA11731F5E9D0A3B6E9 E Global\MSI0000 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 657
Read events
9 596
Write events
50
Delete events
11
Modification events
| (PID) Process: | (1776) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2088) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000009F5A7BD72FB0D90164030000840D0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2088) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000009F5A7BD72FB0D90164030000840D0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2088) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 73 | |||
| (PID) Process: | (2088) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000008543C5D72FB0D90164030000840D0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2088) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Leave) |
Value: 4000000000000000D1ABF1D82FB0D90164030000840D0000D3070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2088) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Enter) |
Value: 4000000000000000D1ABF1D82FB0D90164030000840D0000D4070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2088) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Leave) |
Value: 4000000000000000475C02D92FB0D90164030000840D0000D4070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2088) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Leave) |
Value: 4000000000000000E57701DA2FB0D90164030000840D0000D0070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2088) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Leave) |
Value: 4000000000000000E57701DA2FB0D90164030000840D0000D5070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
3
Suspicious files
12
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 128 | VNC-Viewer-7.7.0-Windows.exe | C:\Users\admin\AppData\Local\Temp\vnc32.msi | — | |
MD5:— | SHA256:— | |||
| 2088 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2088 | msiexec.exe | C:\Windows\Installer\e4dcd.msi | — | |
MD5:— | SHA256:— | |||
| 2088 | msiexec.exe | C:\Program Files\RealVNC\VNC Viewer\SetupCache\VNC-Viewer-7.7.0-Windows-32bit.msi | — | |
MD5:— | SHA256:— | |||
| 2088 | msiexec.exe | C:\Program Files\RealVNC\VNC Viewer\SetupCache\VNC-Viewer-7.7.0-Windows-32bit.msiKey | — | |
MD5:— | SHA256:— | |||
| 2088 | msiexec.exe | C:\Windows\Installer\e4dd0.msi | — | |
MD5:— | SHA256:— | |||
| 2088 | msiexec.exe | C:\Program Files\RealVNC\VNC Viewer\logmessages.dll | executable | |
MD5:8DD2A1351EBC02B8156C48B1486076F6 | SHA256:30EAAA98D0CE9CF2081C8B84BAA7863900AF47017D6D5BB7B093289A939B5983 | |||
| 2088 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFA59B4FB9342EF736.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 2088 | msiexec.exe | C:\Windows\Installer\{B92BE517-DCDB-4A97-BBCE-164FC5A4BFD9}\IconViewer.exe | image | |
MD5:BF9D3B025D116AB0B9512FF5E3C0BED3 | SHA256:668C44FECA49CE78EC85BEDFABD59C12D585AE4DD145A9B5900B4F75DA382563 | |||
| 2088 | msiexec.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\RealVNC\RealVNC Viewer.lnk | binary | |
MD5:768791106896135CA6BD467F477BD473 | SHA256:892C29455DD66469AB054530B1B7EE1435717299F45420BE6DD8E2BB78C257CD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
15
DNS requests
1
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1384 | vncviewer.exe | 165.254.191.229:443 | hb-c.services.vnc.com | NTT-LTD-2914 | US | unknown |
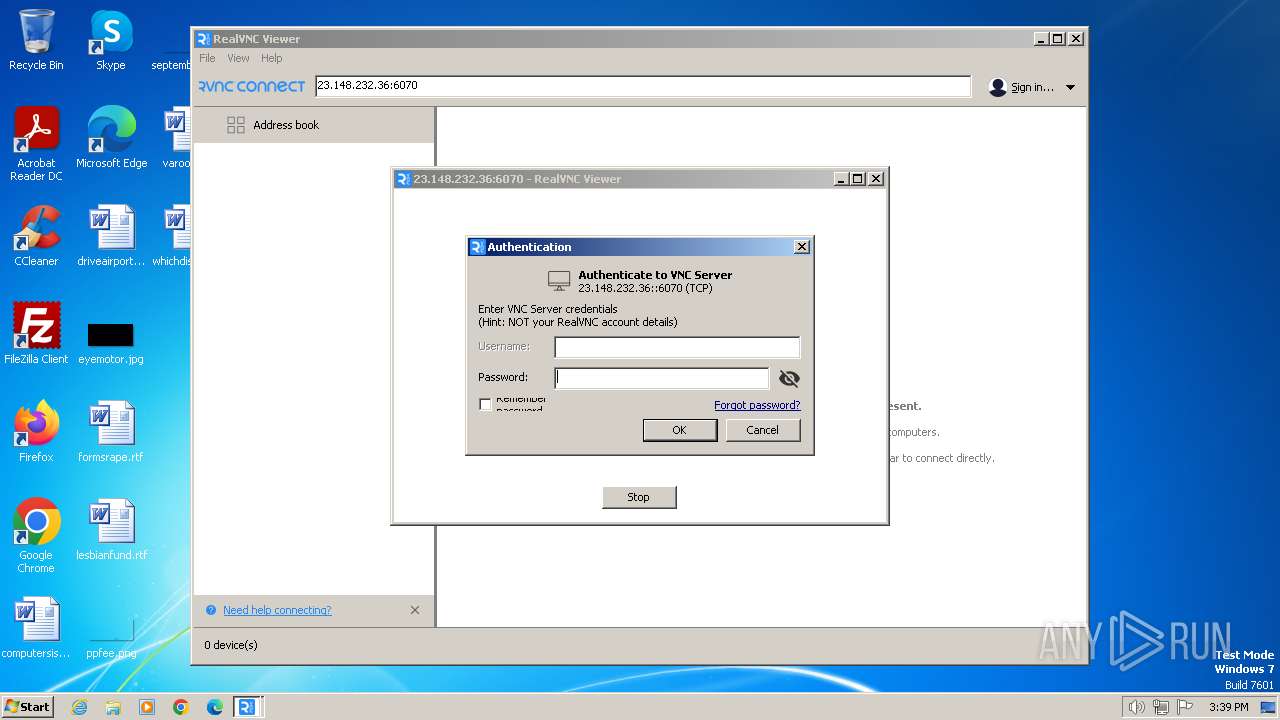
1984 | vncviewer.exe | 23.148.232.36:6070 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hb-c.services.vnc.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
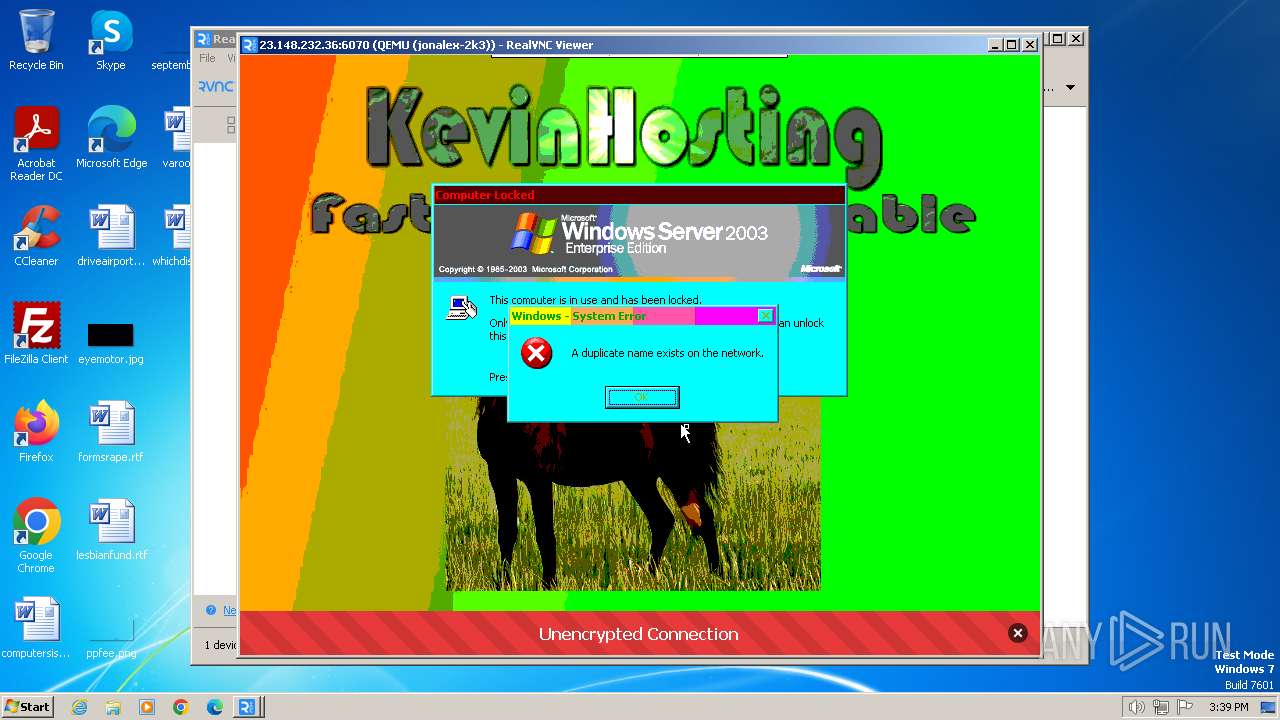
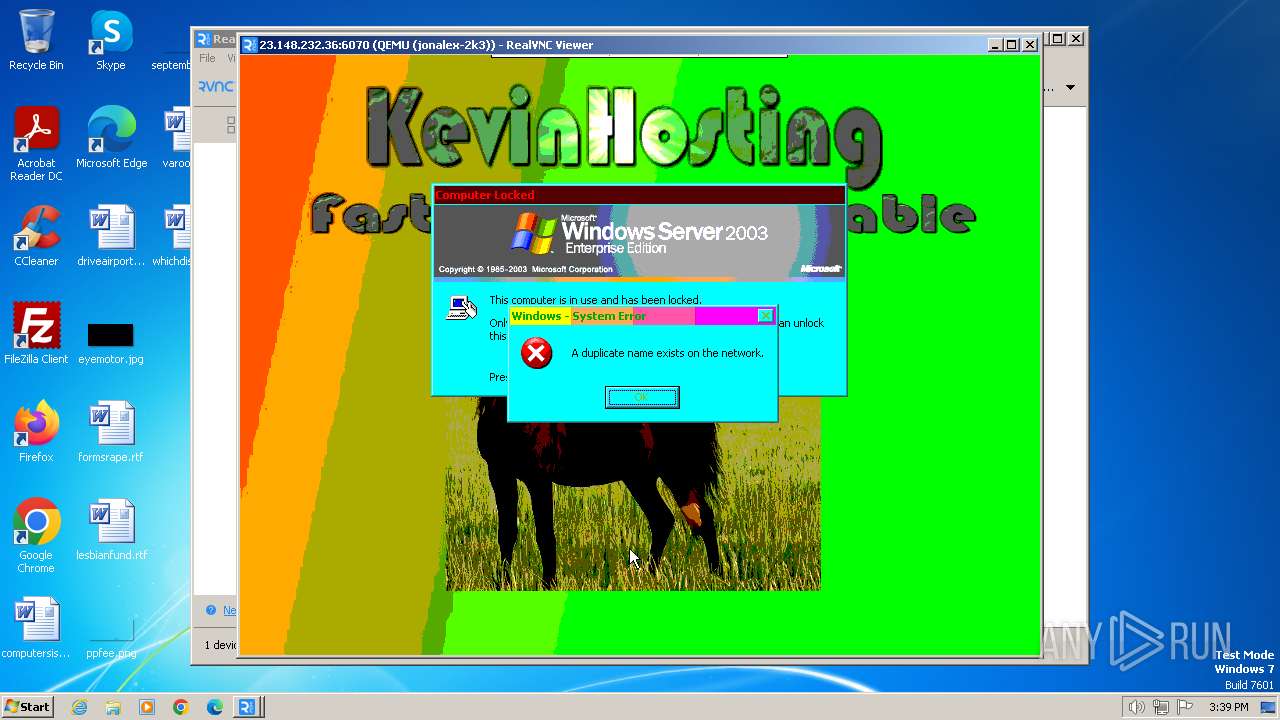
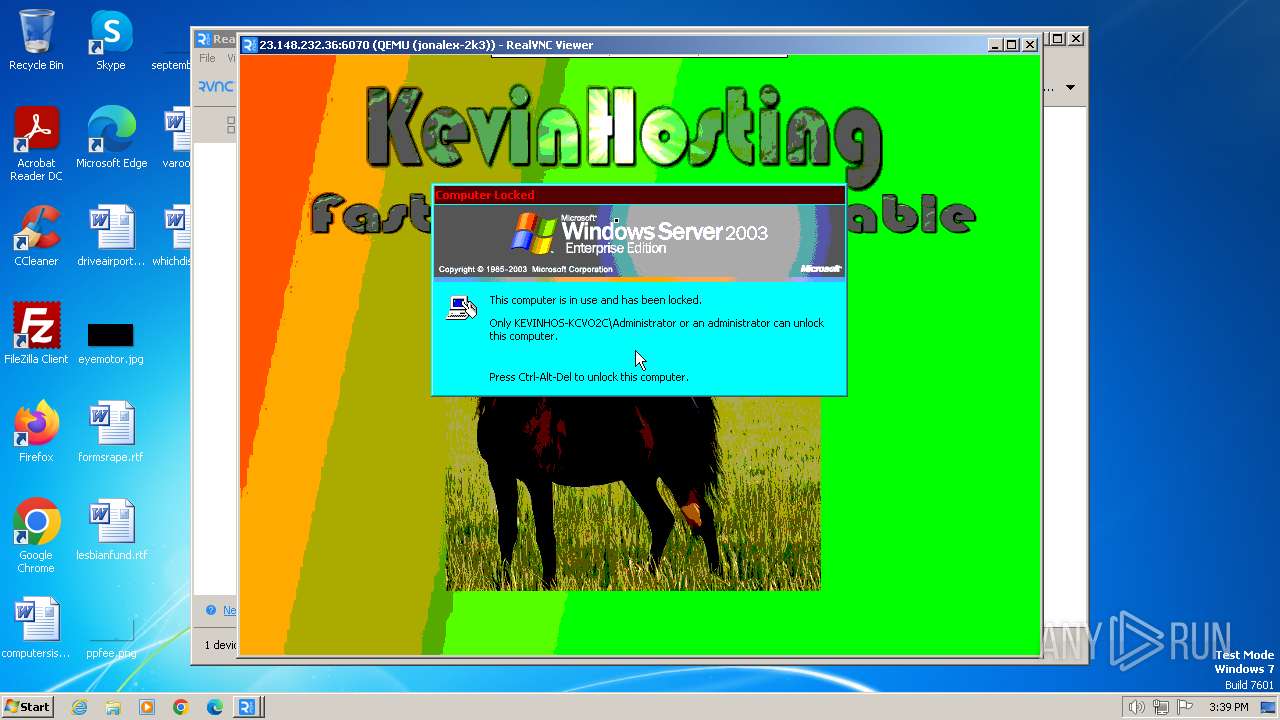
1984 | vncviewer.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] VNC negotiation was detected (ProtocolVersion message) |
1984 | vncviewer.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] VNC negotiation was detected (Server Security type - None) |