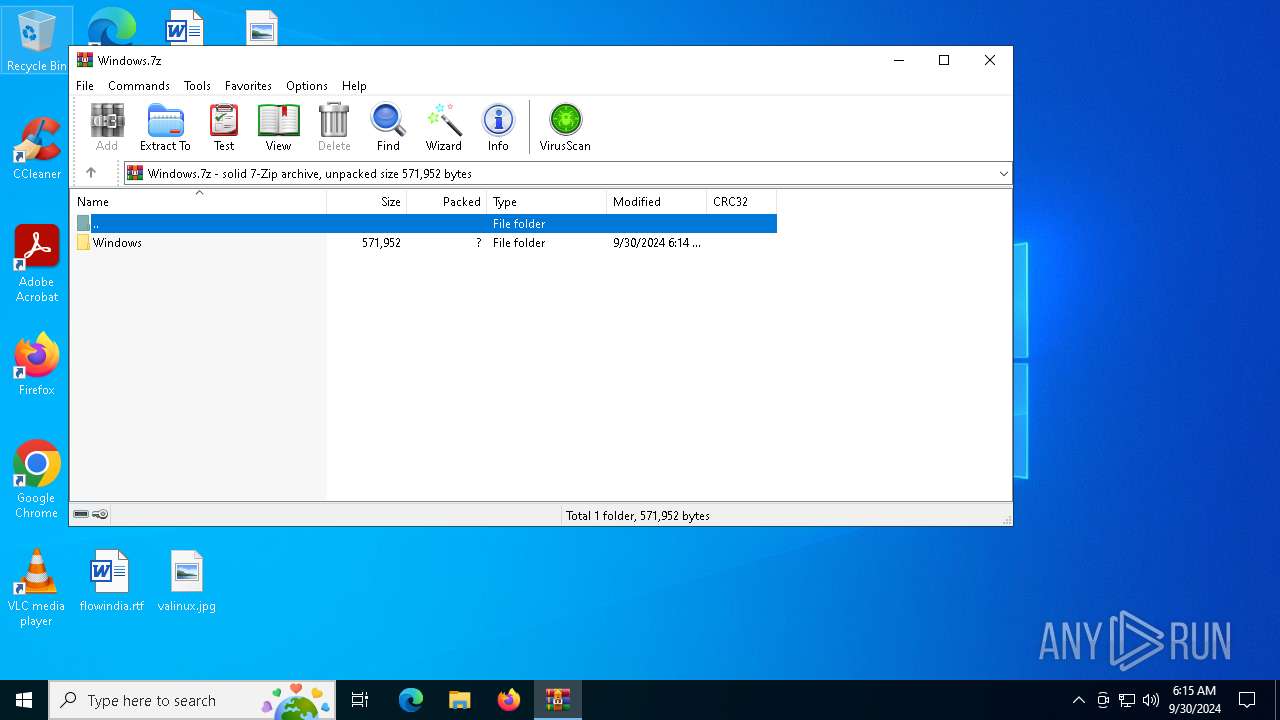
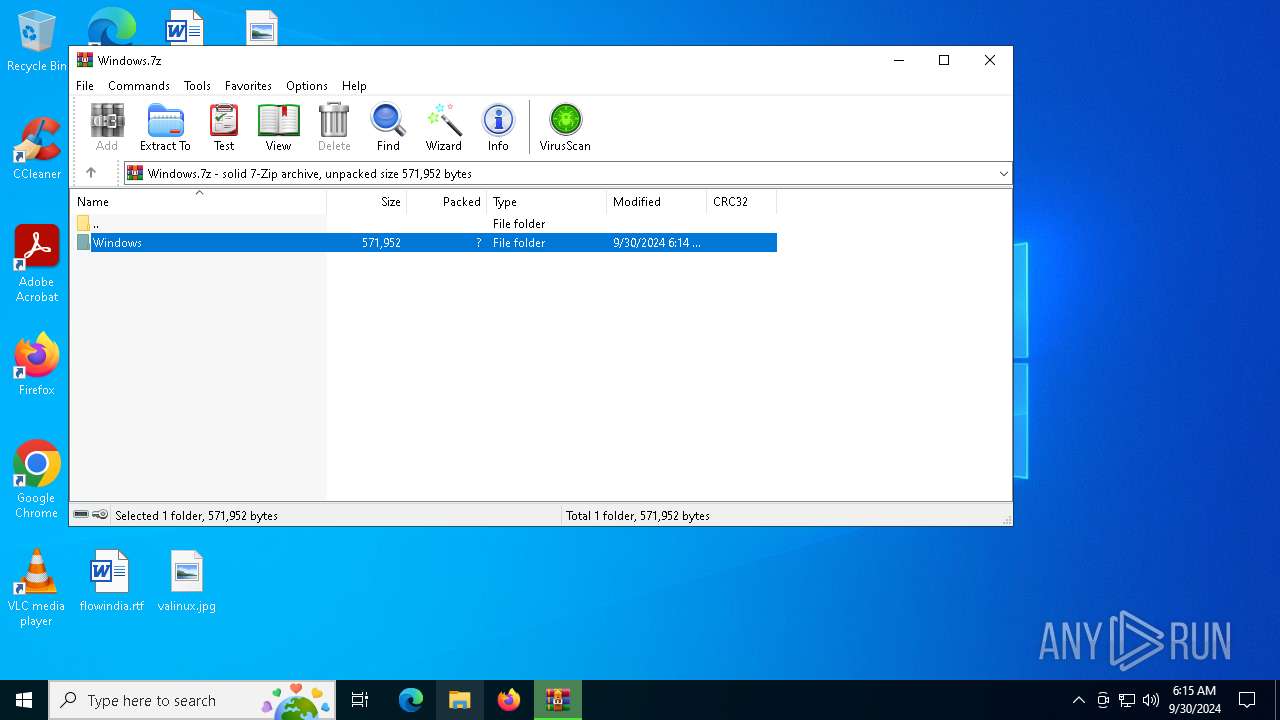
| File name: | Windows.7z |
| Full analysis: | https://app.any.run/tasks/769747f3-6cb7-4ee5-9b84-fd7401fb45a5 |
| Verdict: | Malicious activity |
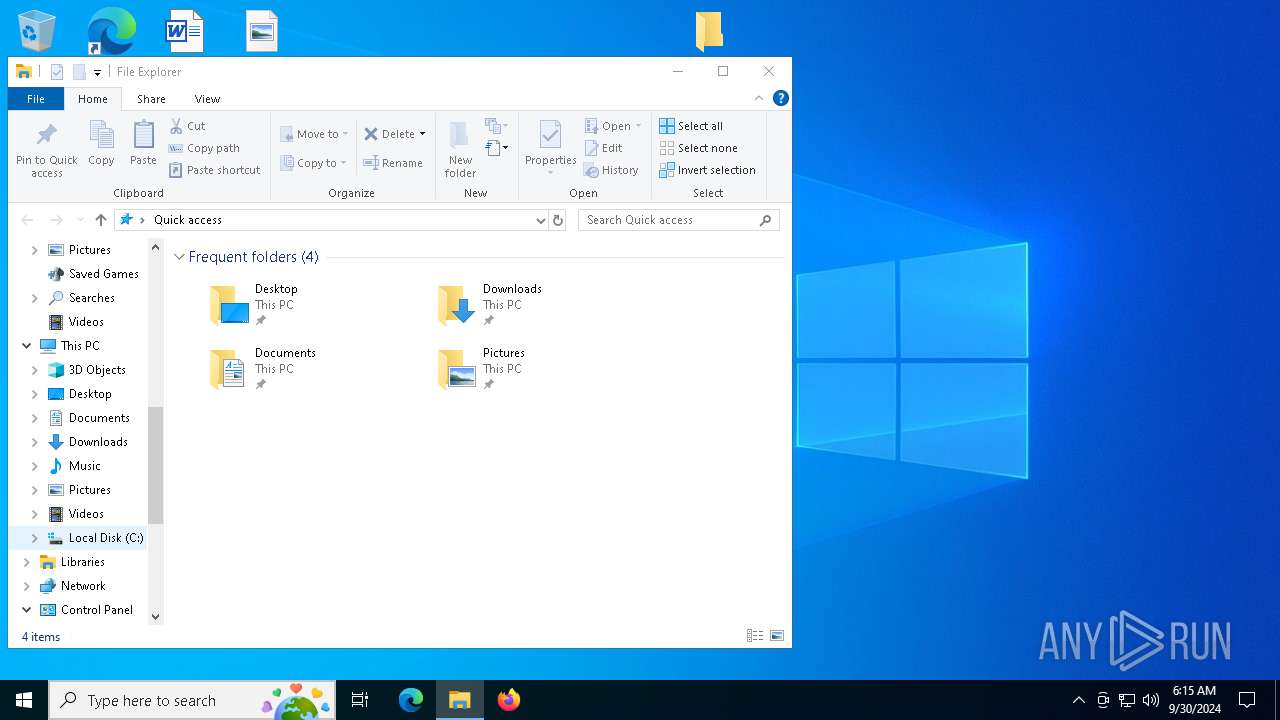
| Analysis date: | September 30, 2024, 06:15:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 7D4AB9D3112E960971A5E45D1C565C91 |
| SHA1: | 1FDDD542F9B103D508C5DA4CA1C683CF6698F23B |
| SHA256: | 7A2ABB63381E85D99996F54FF5865ECD786E22DD25A5234794C2D99FED5599E2 |
| SSDEEP: | 6144:AG5Y6FnPqUAB8jQN5WOmM8scdoUp1Ppc6IokqYFEvKH/X2:rjPqUAeUr9mMLcdoUTBxJTYFVHv2 |
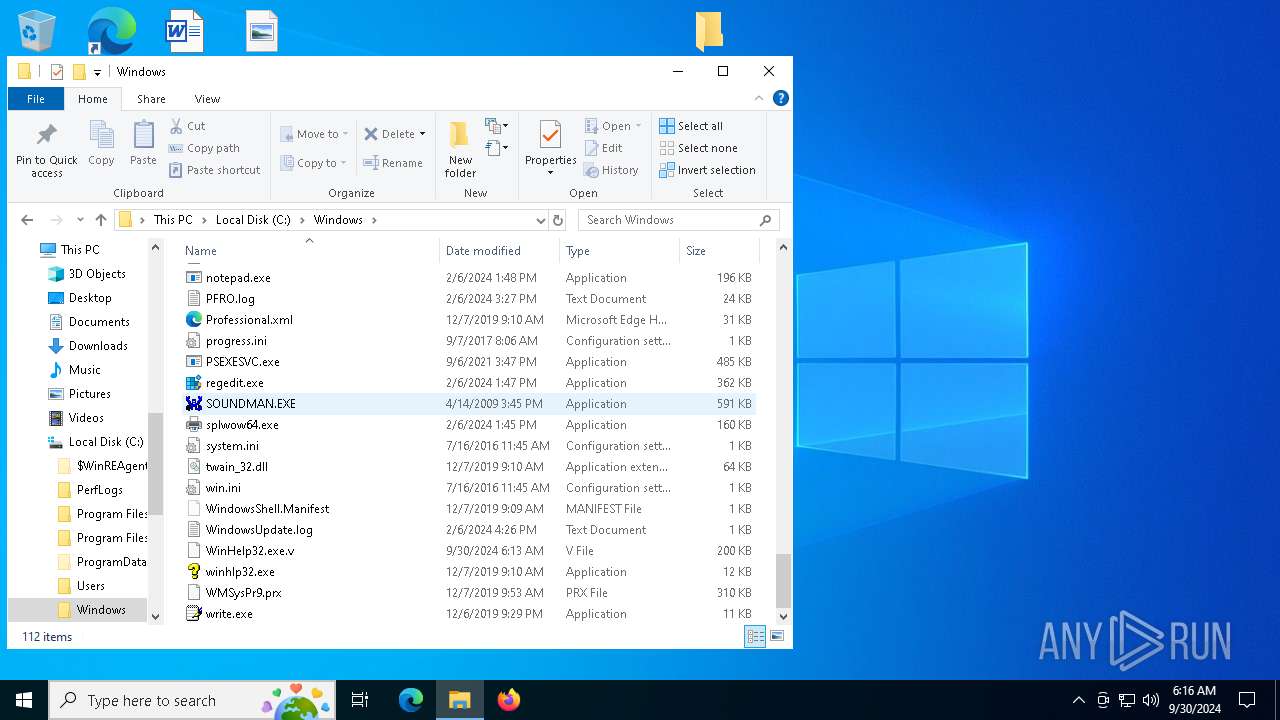
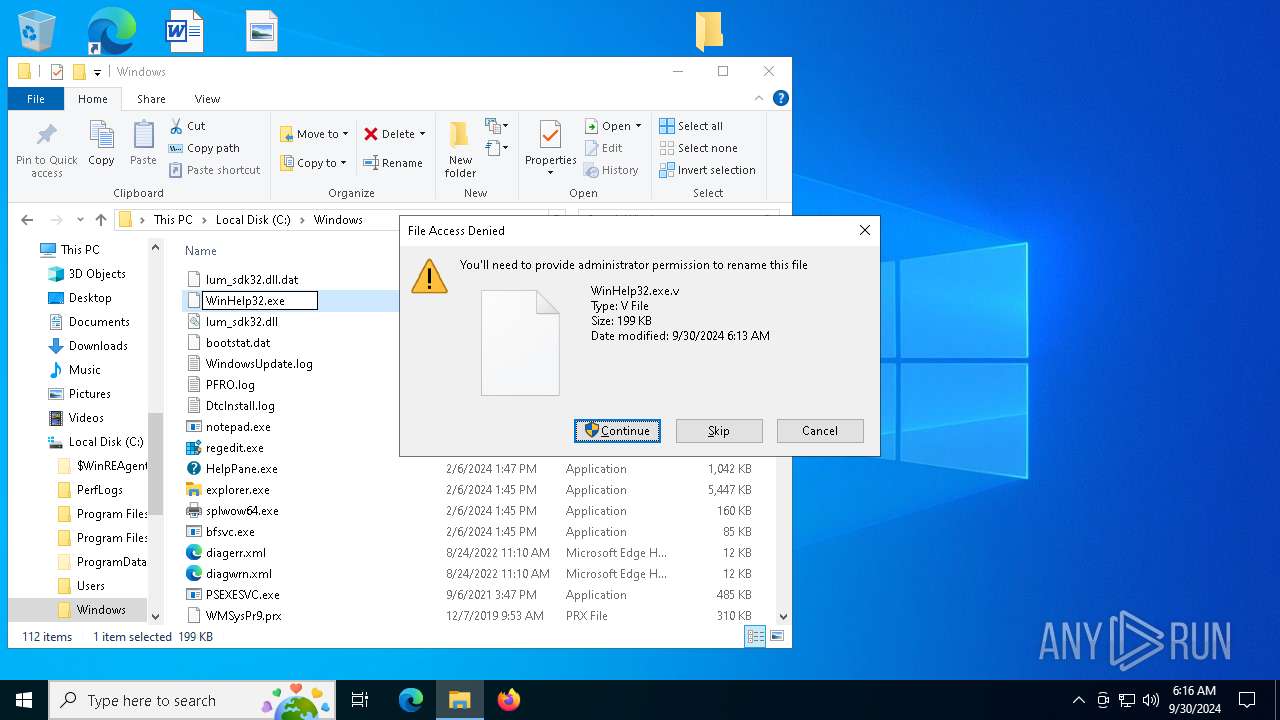
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 6544)
SUSPICIOUS
Executable content was dropped or overwritten
- dllhost.exe (PID: 1652)
- WinHelp32.exe (PID: 6200)
Executes as Windows Service
- WinHelp32.exe (PID: 6828)
Connects to unusual port
- svchost.exe (PID: 6936)
INFO
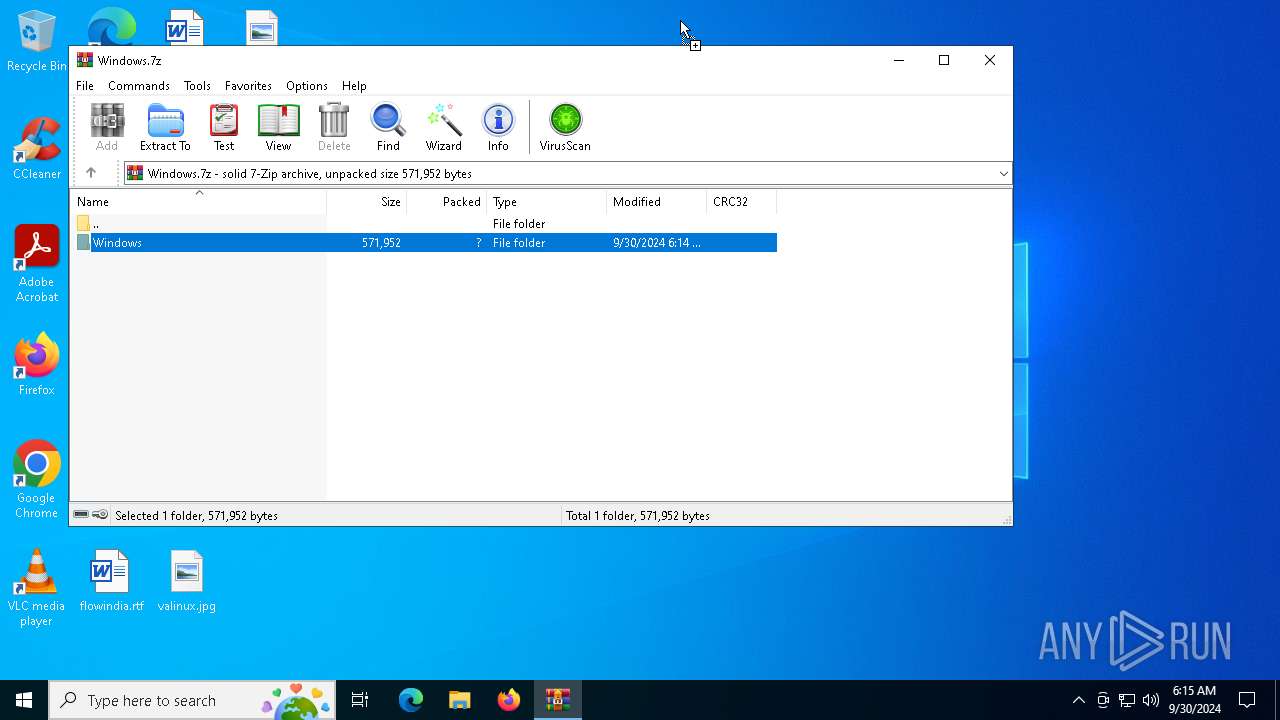
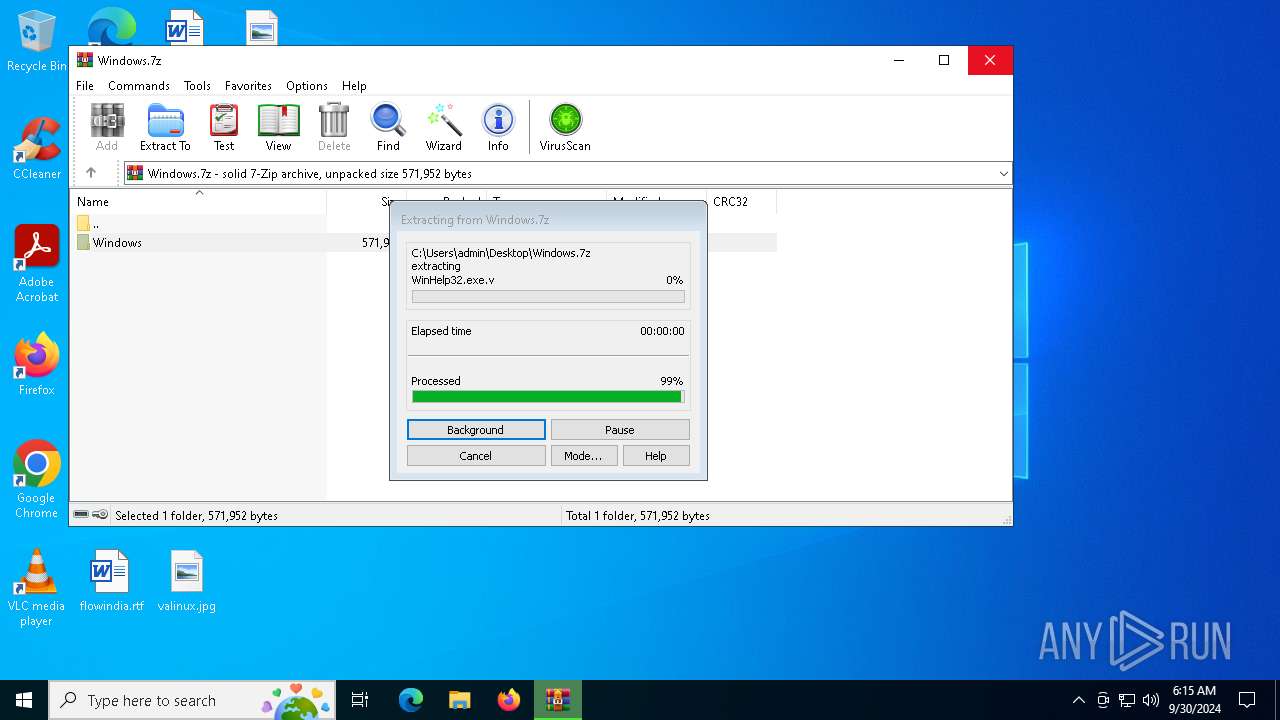
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6864)
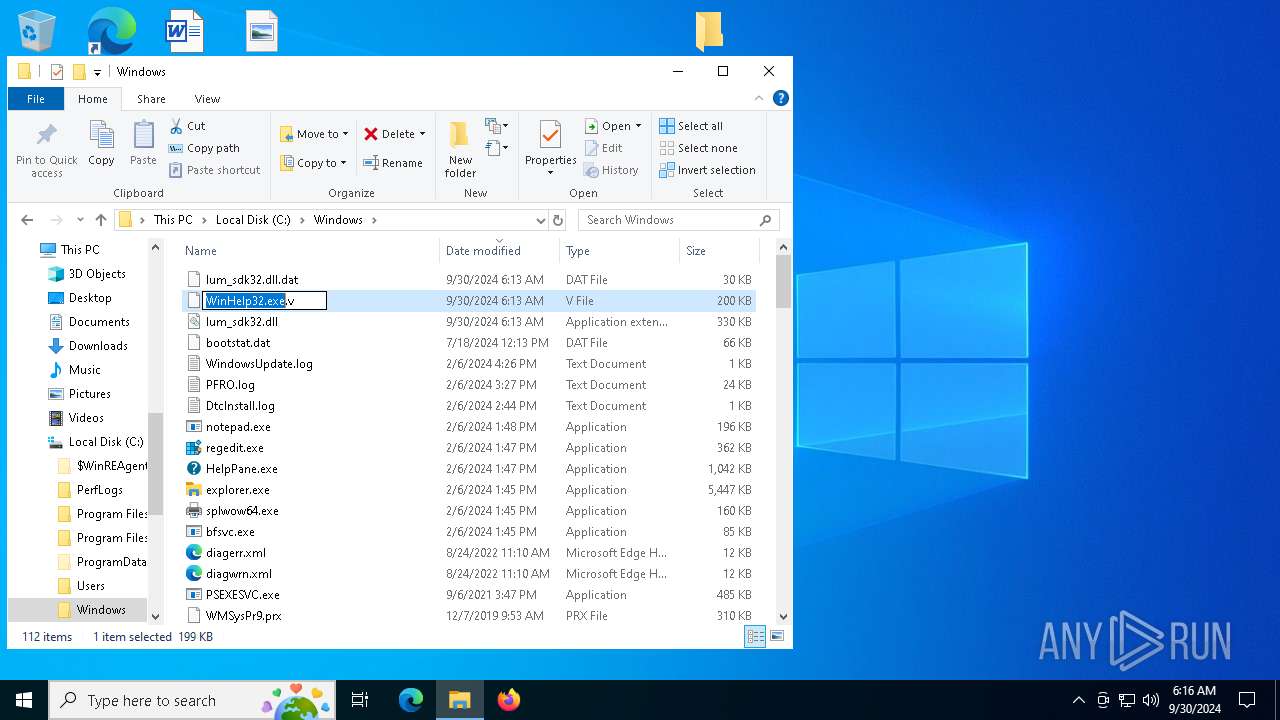
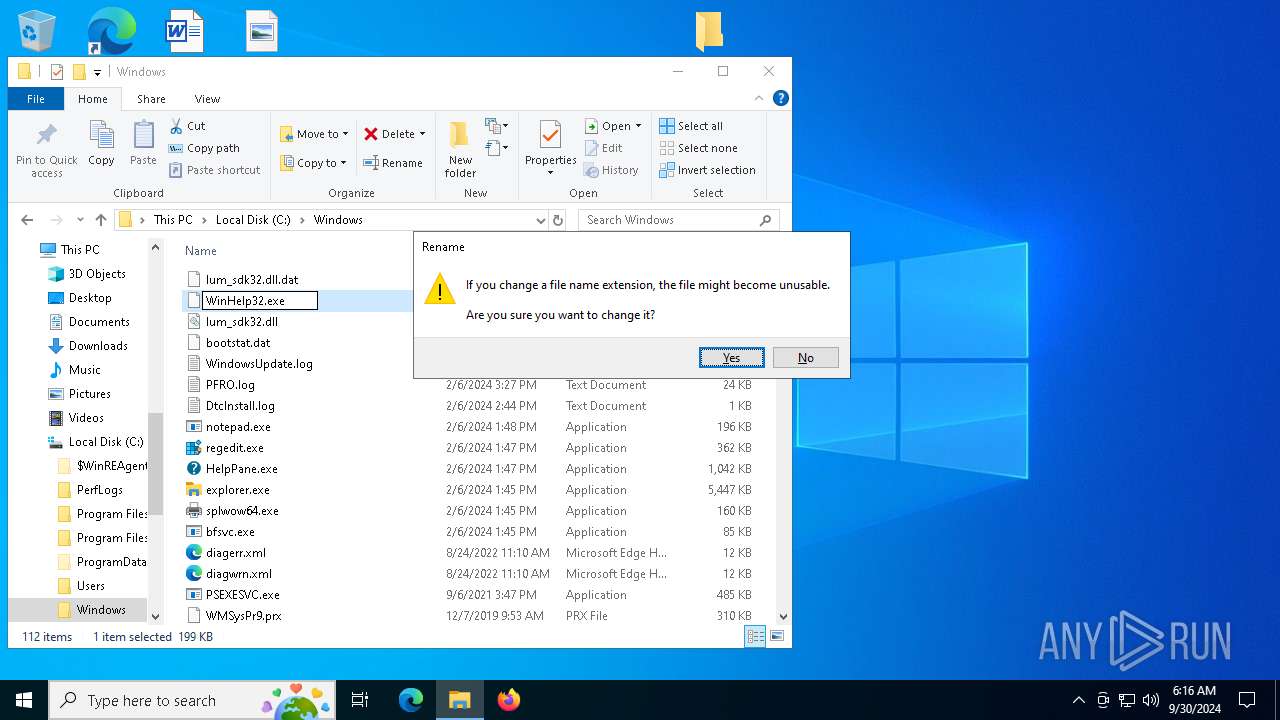
Manual execution by a user
- WinHelp32.exe (PID: 5524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
146
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1652 | C:\WINDOWS\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3784 | C:\WINDOWS\SysWOW64\dllhost.exe -ks | C:\Windows\SysWOW64\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
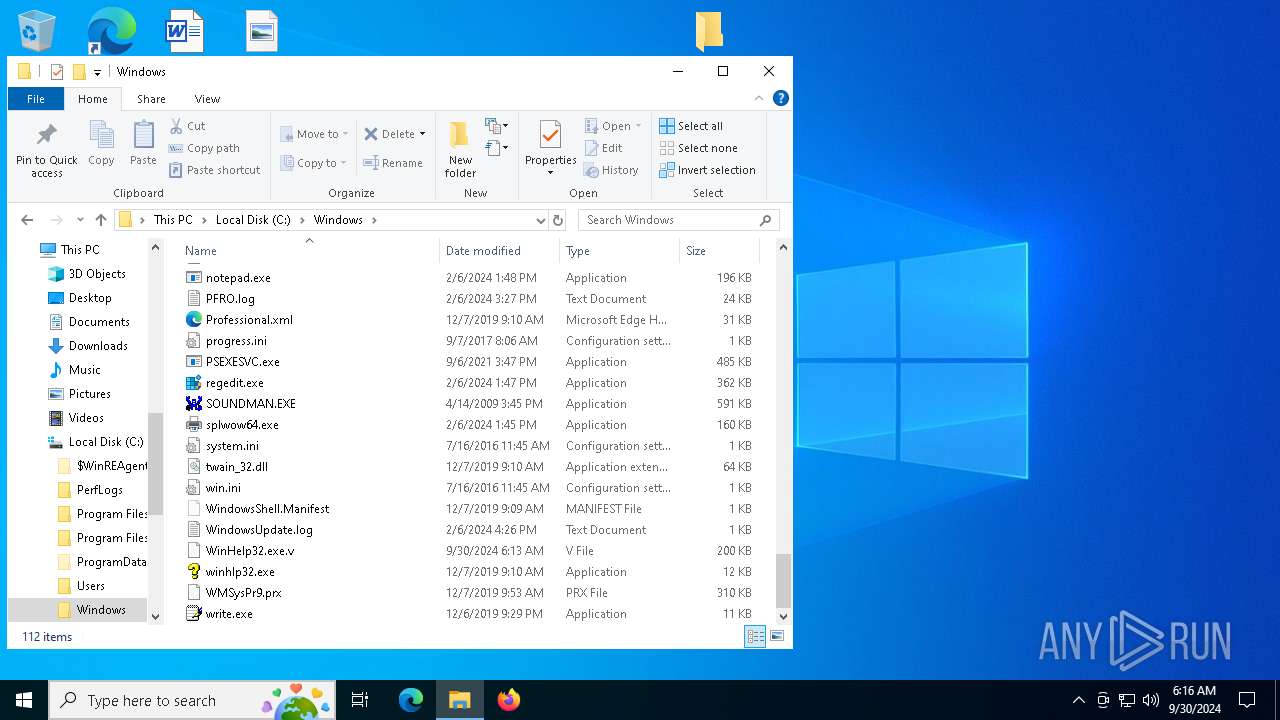
| 5524 | "C:\Windows\WinHelp32.exe" | C:\Windows\WinHelp32.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6200 | "C:\Windows\WinHelp32.exe" -Install | C:\Windows\WinHelp32.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6544 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6828 | C:\WINDOWS\WinHelp32.exe -svc | C:\Windows\WinHelp32.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
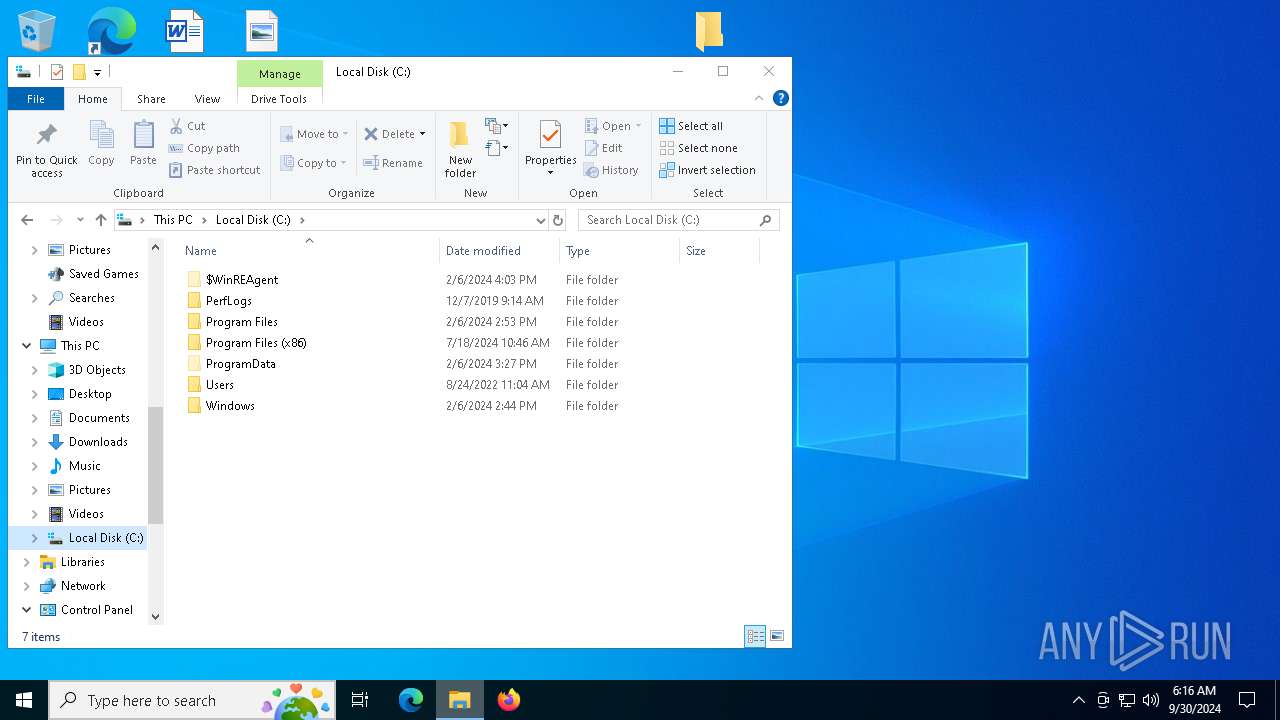
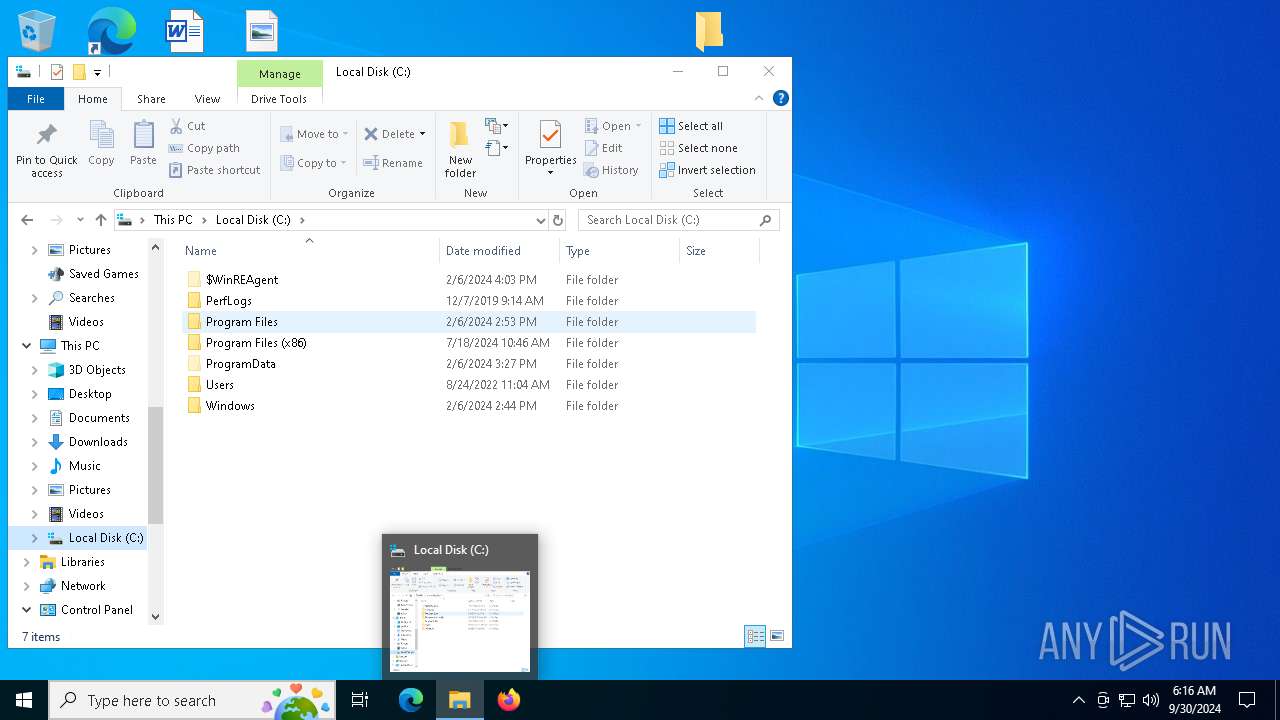
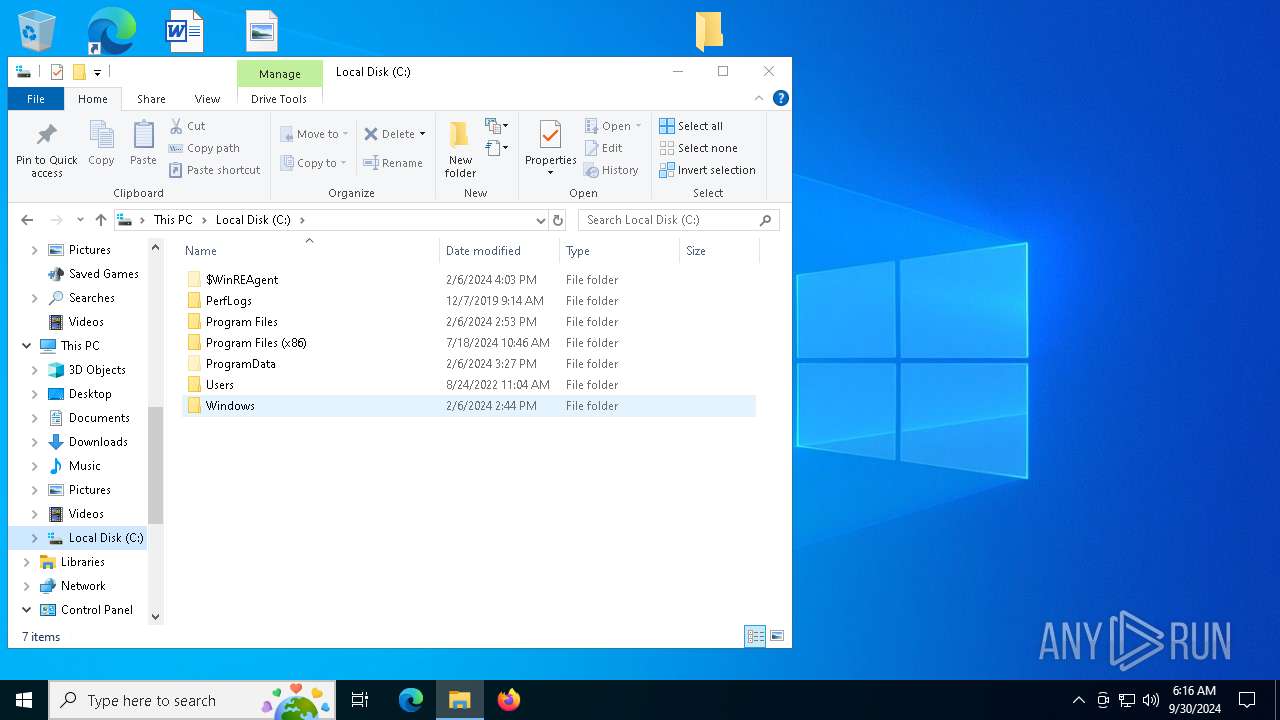
| 6864 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Windows.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6936 | C:\WINDOWS\SysWOW64\svchost.exe -k netsvcs | C:\Windows\SysWOW64\svchost.exe | WinHelp32.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 573
Read events
2 556
Write events
17
Delete events
0
Modification events
| (PID) Process: | (6864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Windows.7z | |||
| (PID) Process: | (6864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (6864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6864) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
Executable files
7
Suspicious files
3
Text files
0
Unknown types
0
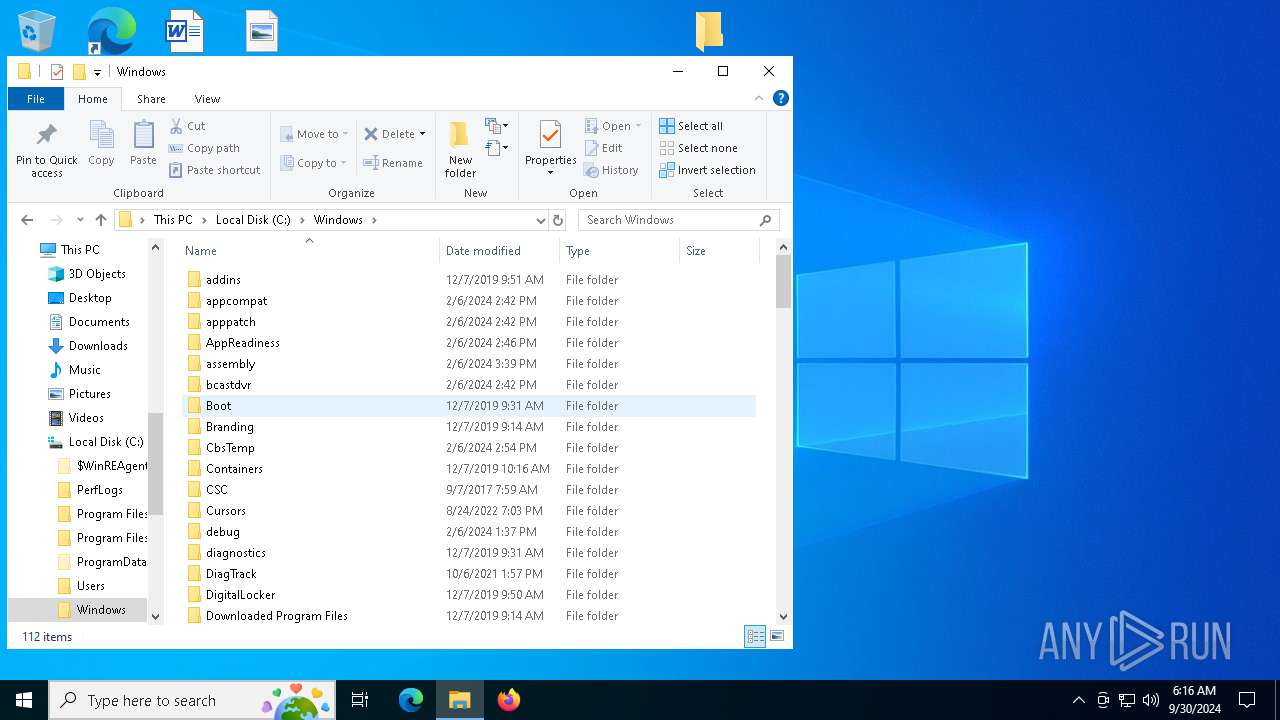
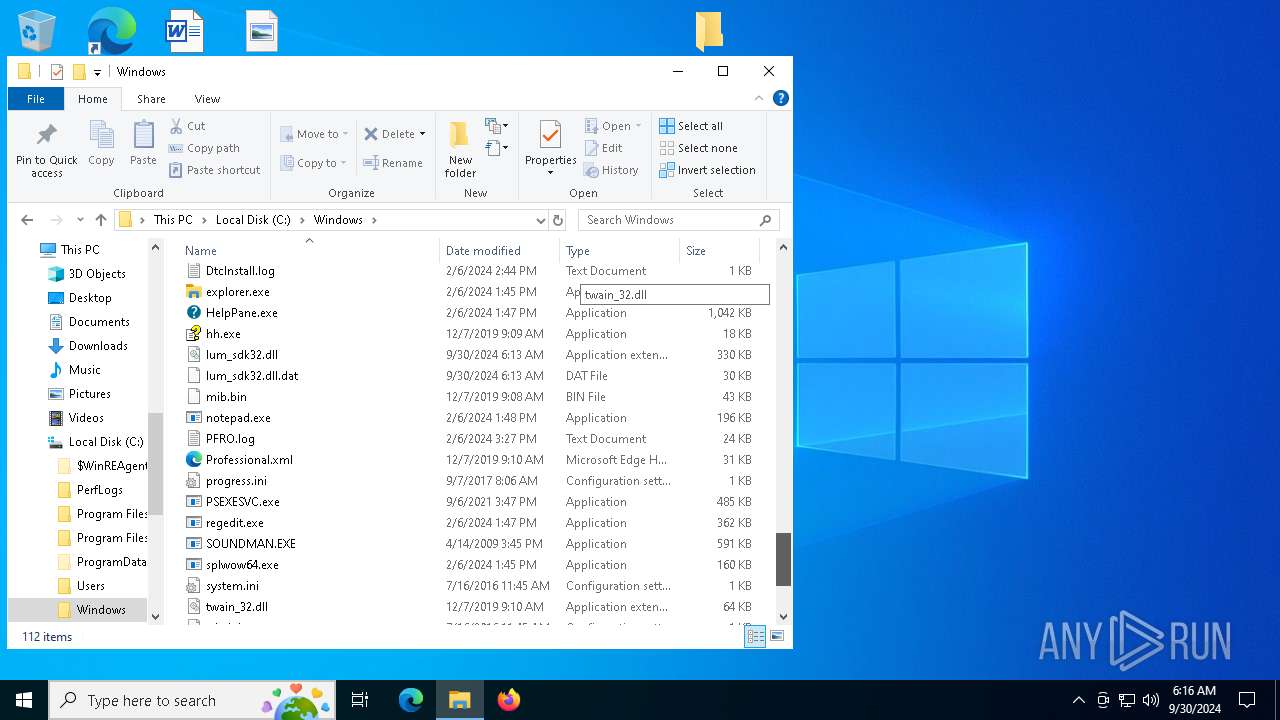
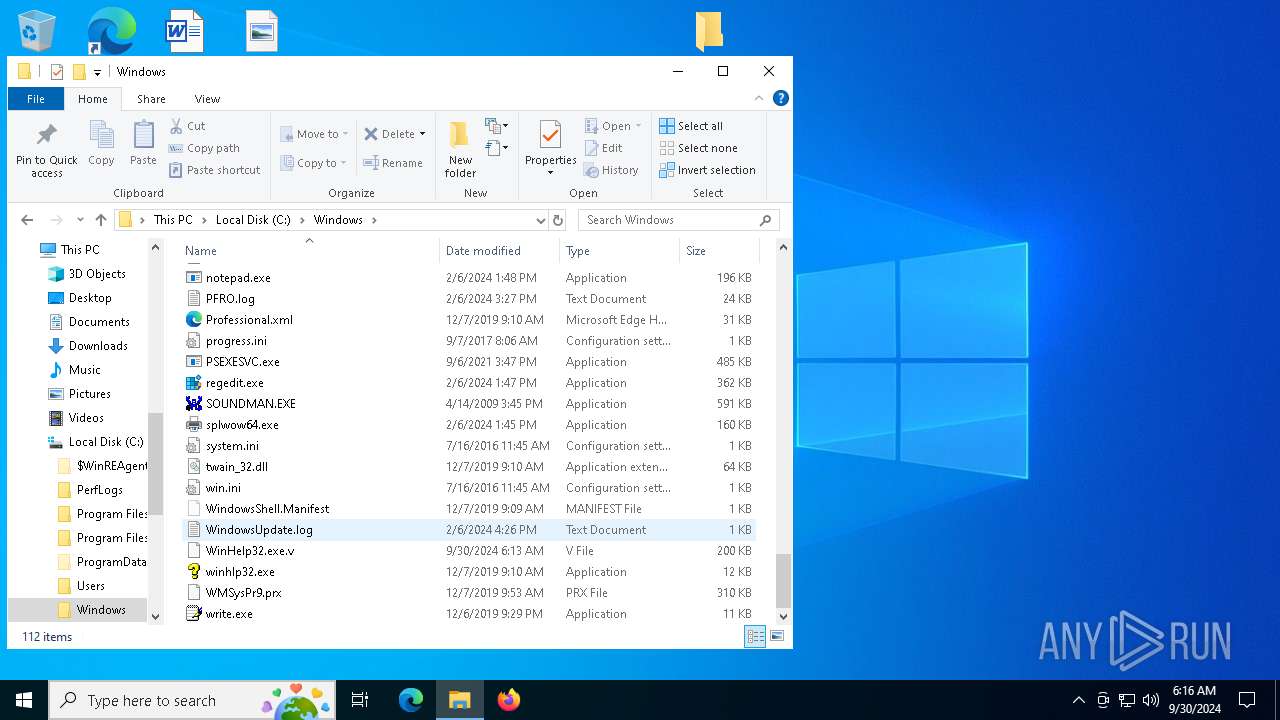
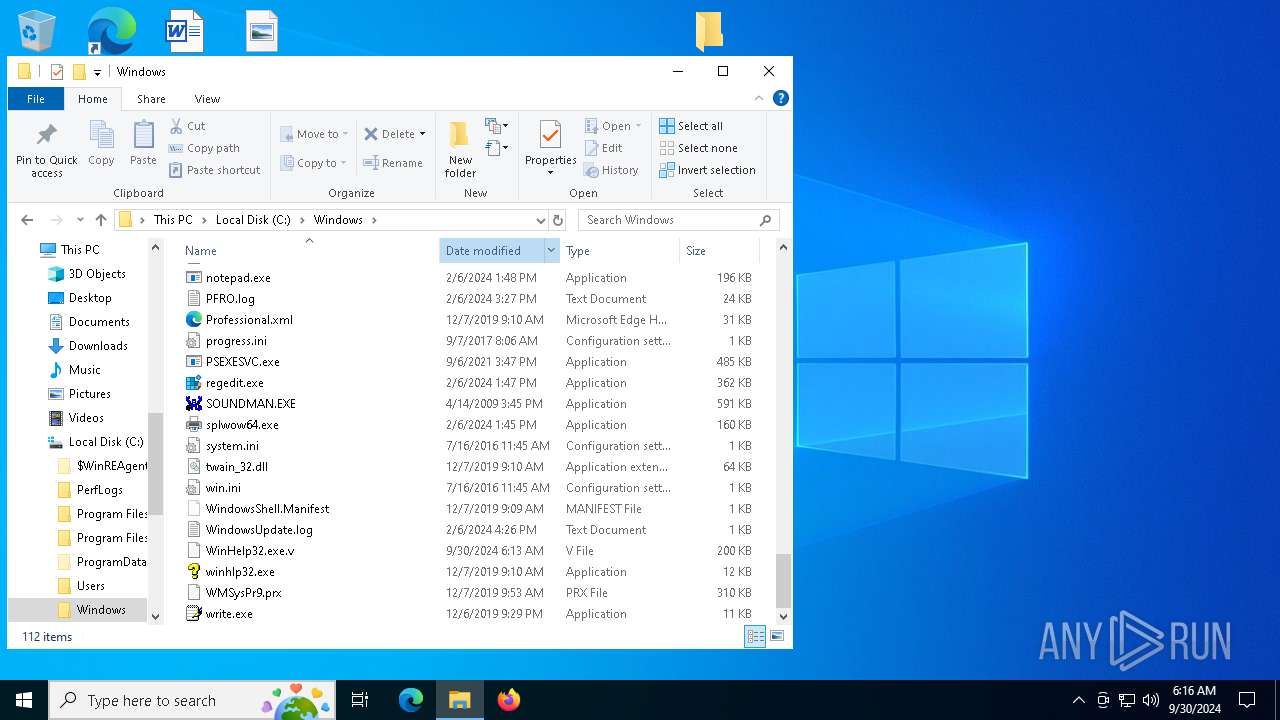
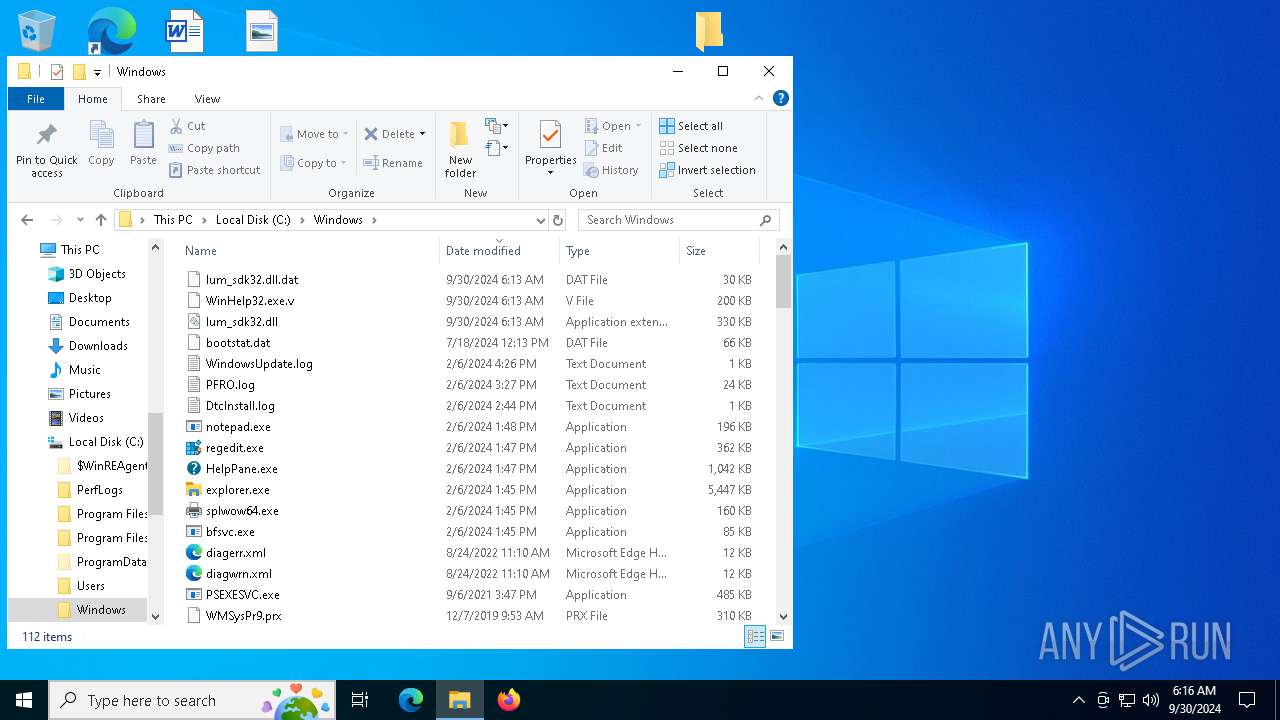
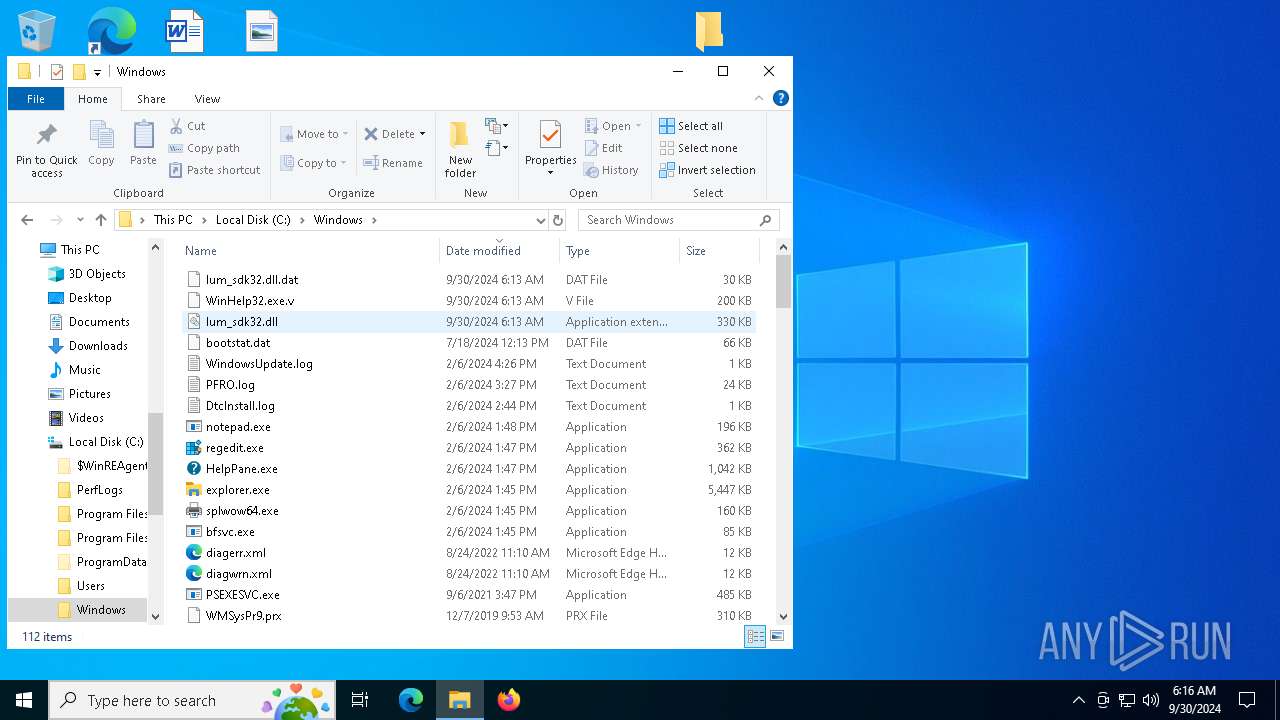
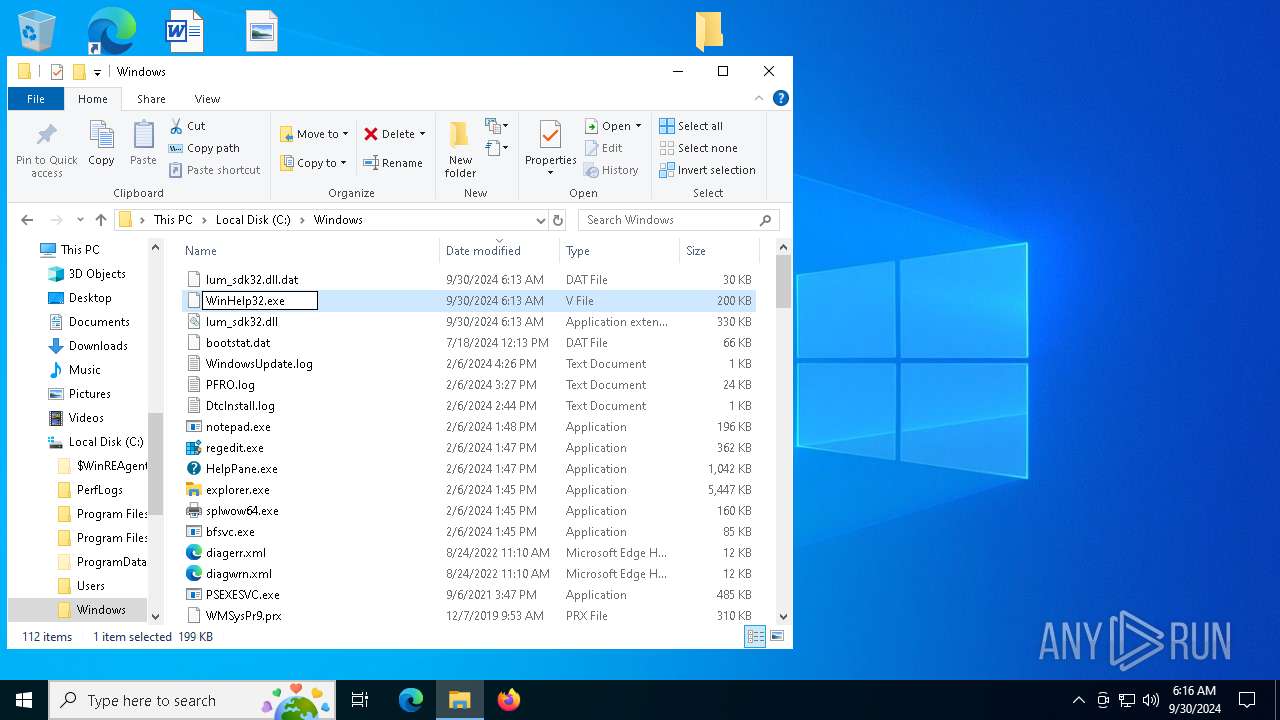
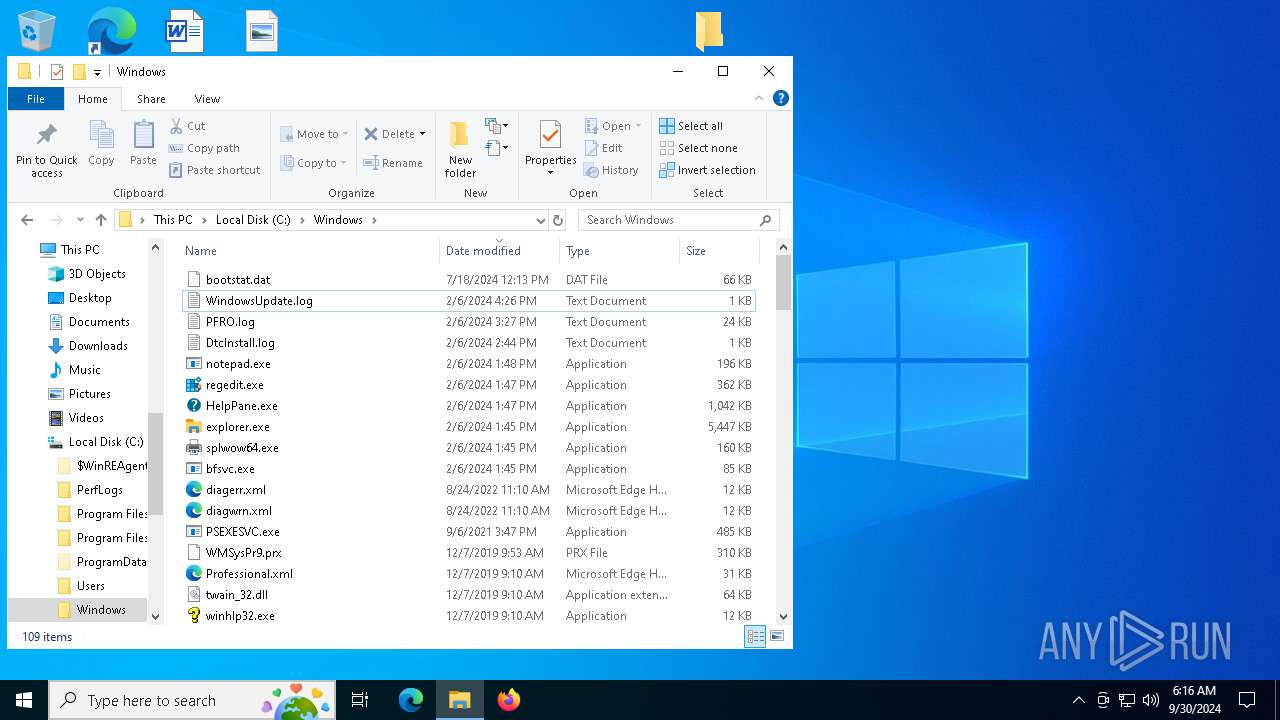
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6864.26286\Windows\WinHelp32.exe.v | executable | |
MD5:7F35E75EF4B13631C6F2355A48467613 | SHA256:28E9F726BF8C2710FF3C40B50FDB9D5EC2A60C0174E86D1D4E1960FD4DB1BFDE | |||
| 1652 | dllhost.exe | C:\Windows\lum_sdk32.dll | executable | |
MD5:05D525320399F2A9E058CBA5C5770345 | SHA256:9D2EC7782B85AE7C0A16F0F3CE61B3EB3E2FFEC72325D8FEE2C8103F69601D6B | |||
| 6864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6864.26286\Windows\lum_sdk32.dll.dat | binary | |
MD5:16453B46B2BC6D0159208EA75385DA93 | SHA256:87BA524C8C614BF71432168452B7335D10D515FA98CE1C943DE5E78DA3796CA8 | |||
| 1652 | dllhost.exe | C:\Windows\lum_sdk32.dll.dat | binary | |
MD5:16453B46B2BC6D0159208EA75385DA93 | SHA256:87BA524C8C614BF71432168452B7335D10D515FA98CE1C943DE5E78DA3796CA8 | |||
| 6864 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6864.26286\Windows\lum_sdk32.dll | executable | |
MD5:05D525320399F2A9E058CBA5C5770345 | SHA256:9D2EC7782B85AE7C0A16F0F3CE61B3EB3E2FFEC72325D8FEE2C8103F69601D6B | |||
| 1652 | dllhost.exe | C:\Windows\WinHelp32.exe | executable | |
MD5:7F35E75EF4B13631C6F2355A48467613 | SHA256:28E9F726BF8C2710FF3C40B50FDB9D5EC2A60C0174E86D1D4E1960FD4DB1BFDE | |||
| 1652 | dllhost.exe | C:\Windows\WinHelp32.exe.v | executable | |
MD5:7F35E75EF4B13631C6F2355A48467613 | SHA256:28E9F726BF8C2710FF3C40B50FDB9D5EC2A60C0174E86D1D4E1960FD4DB1BFDE | |||
| 6200 | WinHelp32.exe | C:\Windows\Temp\4206968.bak | binary | |
MD5:16453B46B2BC6D0159208EA75385DA93 | SHA256:87BA524C8C614BF71432168452B7335D10D515FA98CE1C943DE5E78DA3796CA8 | |||
| 6200 | WinHelp32.exe | C:\Windows\Temp\4206984.bak | executable | |
MD5:05D525320399F2A9E058CBA5C5770345 | SHA256:9D2EC7782B85AE7C0A16F0F3CE61B3EB3E2FFEC72325D8FEE2C8103F69601D6B | |||
| 6200 | WinHelp32.exe | C:\Windows\Temp\4206921.bak | executable | |
MD5:7F35E75EF4B13631C6F2355A48467613 | SHA256:28E9F726BF8C2710FF3C40B50FDB9D5EC2A60C0174E86D1D4E1960FD4DB1BFDE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
47
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1336 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3212 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4792 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4792 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4288 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4324 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4288 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1336 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |