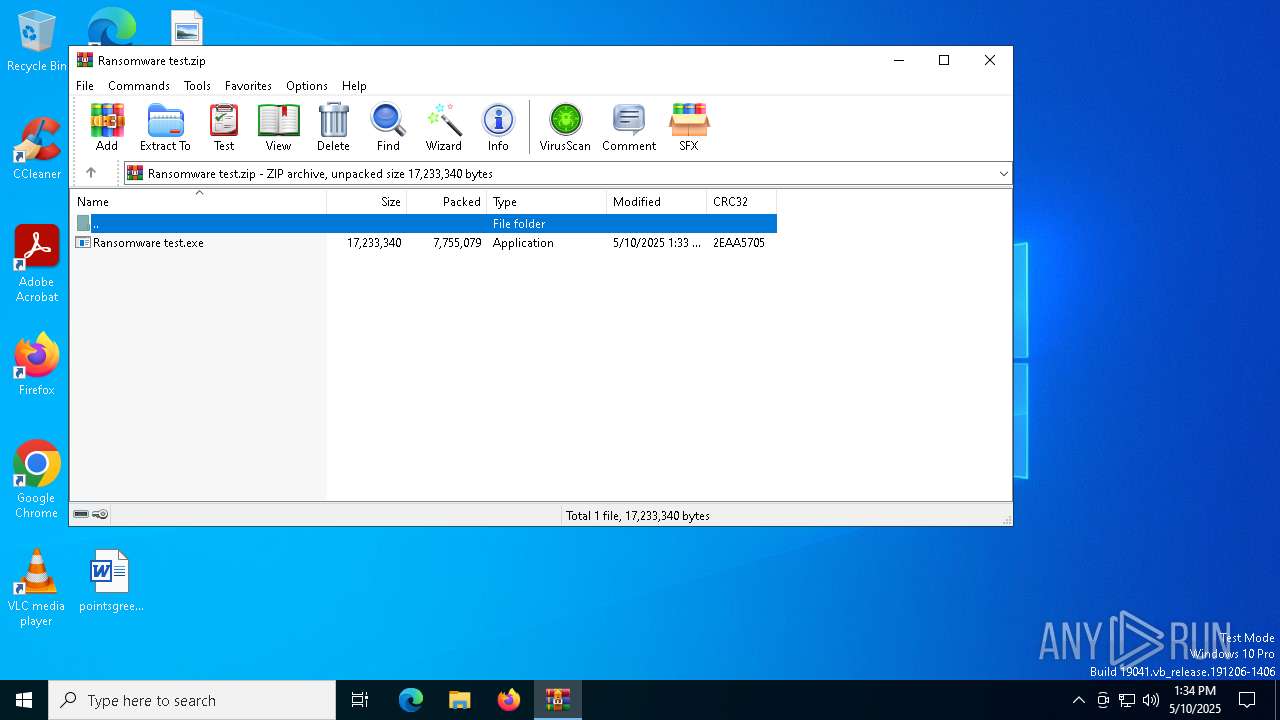
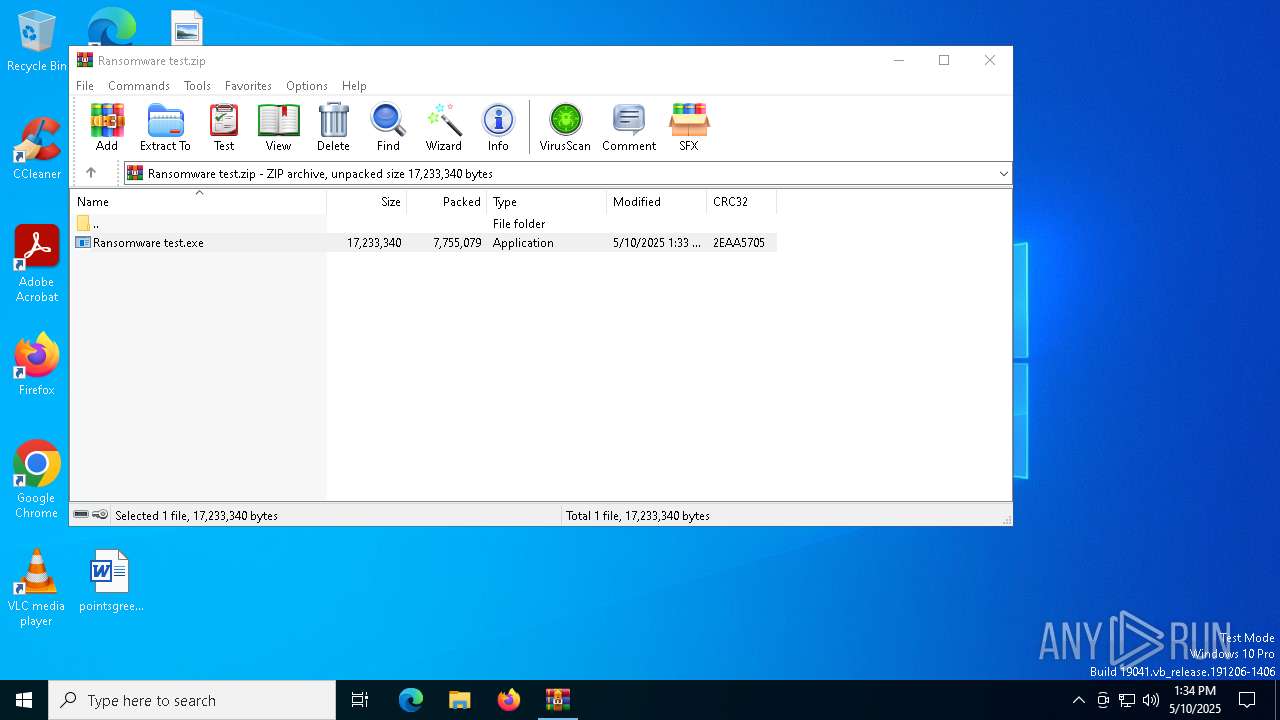
| File name: | Ransomware test.zip |
| Full analysis: | https://app.any.run/tasks/e431601d-bfe2-4aae-87eb-1b18acbdecf3 |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 13:34:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | CD2FC49CB75F34758D859E0F2D7E3D6A |
| SHA1: | 149DBFF653494CF064B2BC14867189AB030A6B43 |
| SHA256: | 7A230C448FFC1B72B0A6FD3B80A9308E11477BF445AF7DC0350D983D8D0BDF3E |
| SSDEEP: | 98304:AXh1cen/cxt/INygpGtw4UuMlRIbLTnpv8UoezMI130gFf4/u+a2mExzEDu4h3yH:+fqm5VPNaVVgA40XJmt |
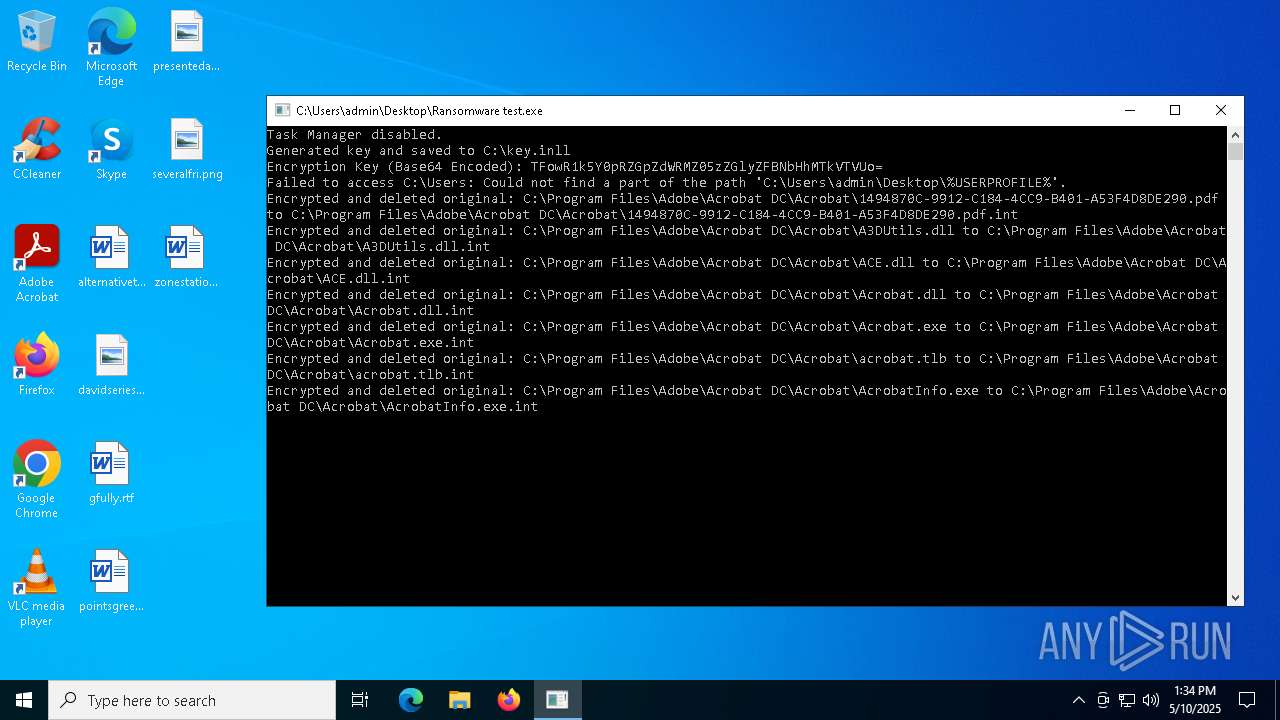
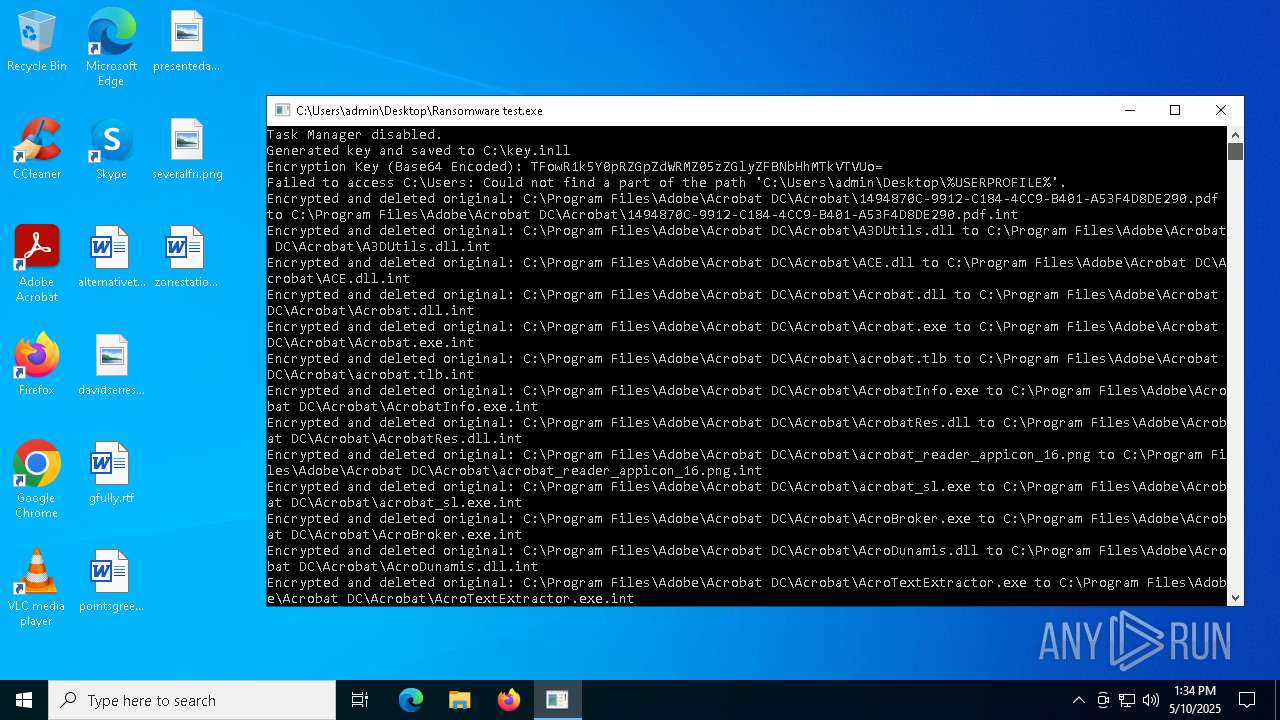
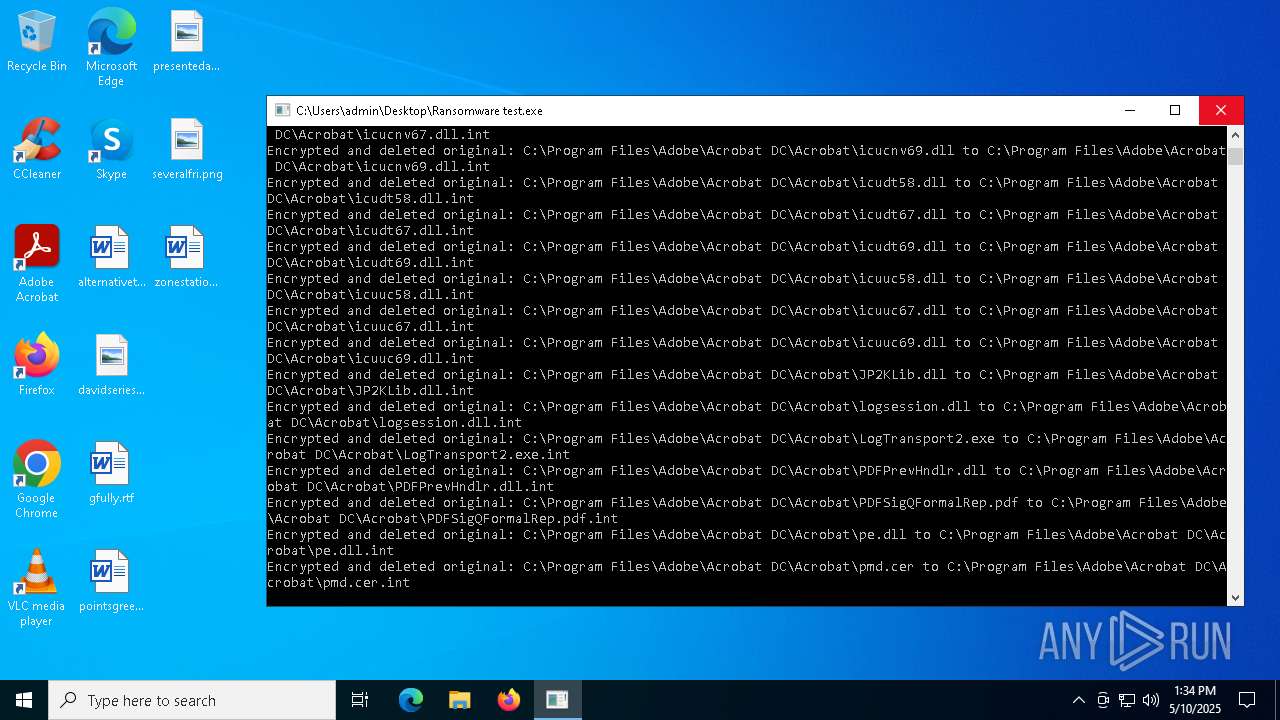
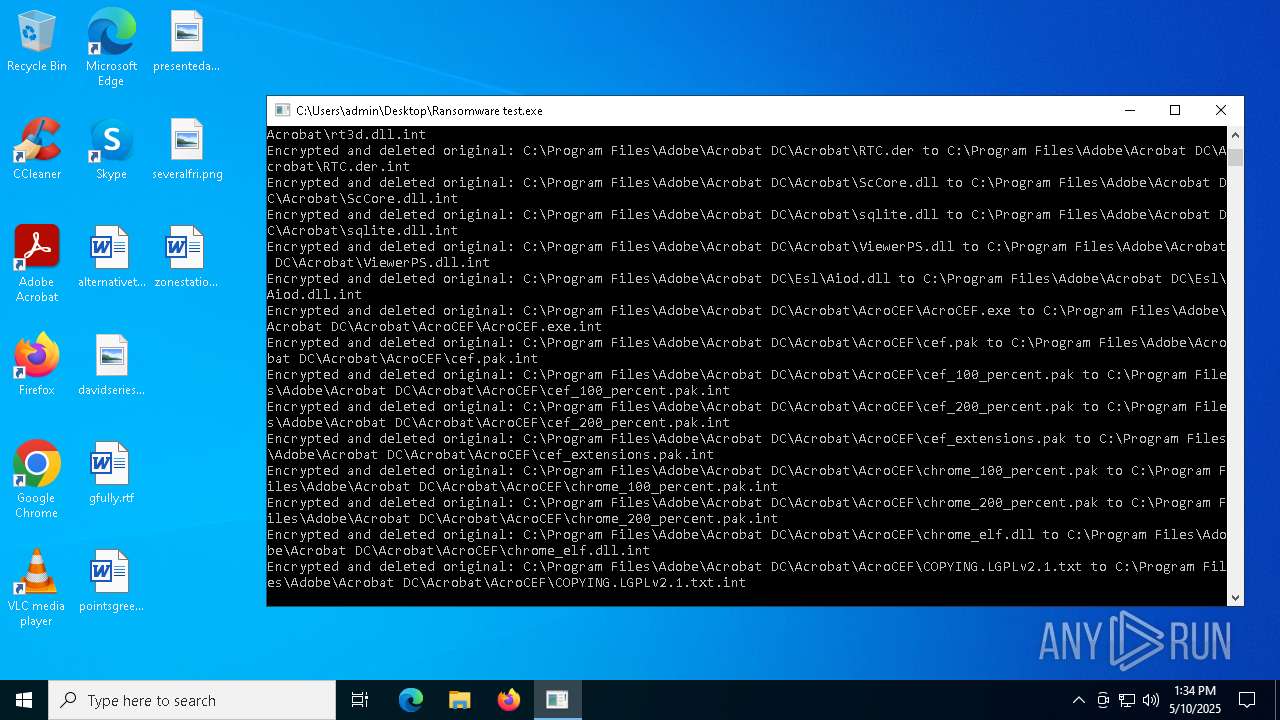
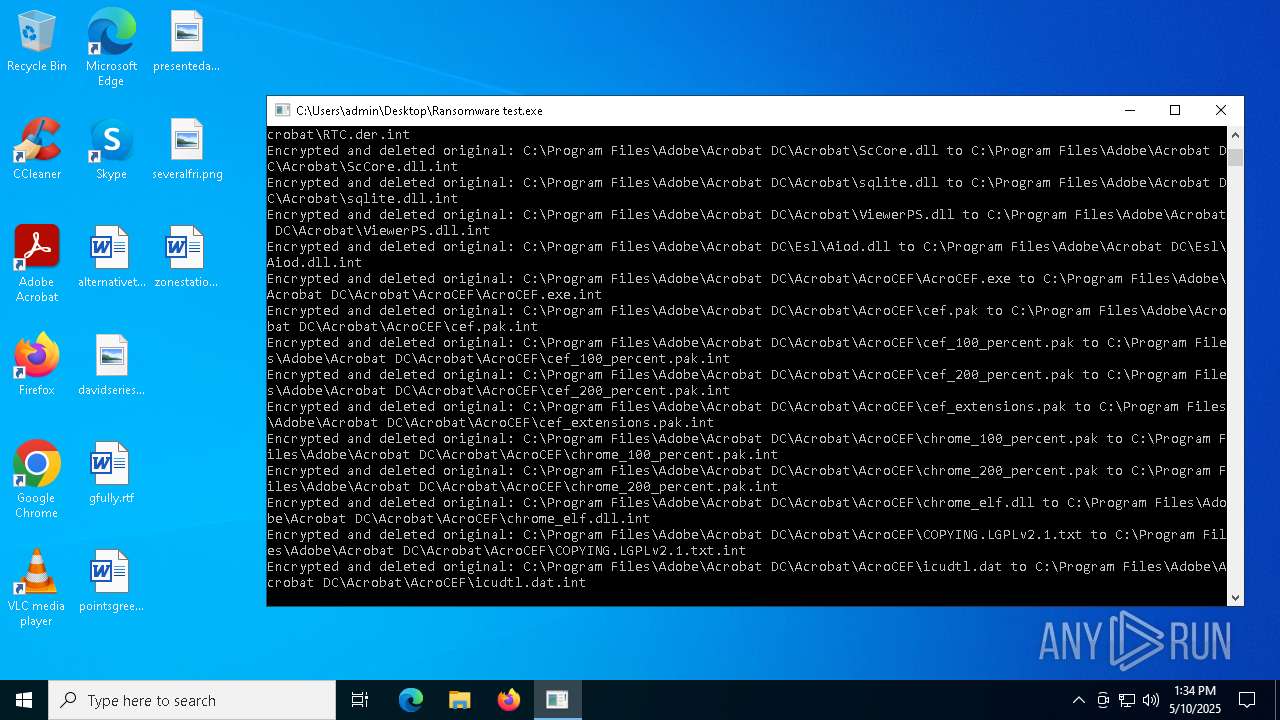
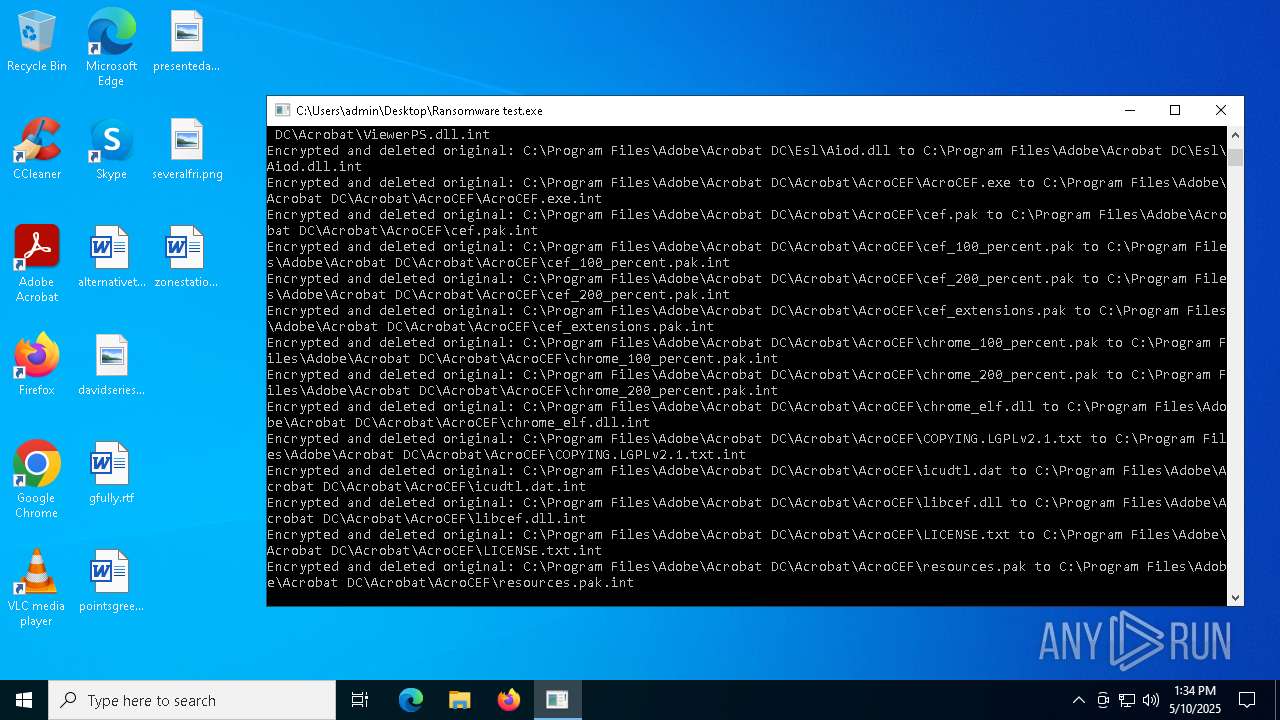
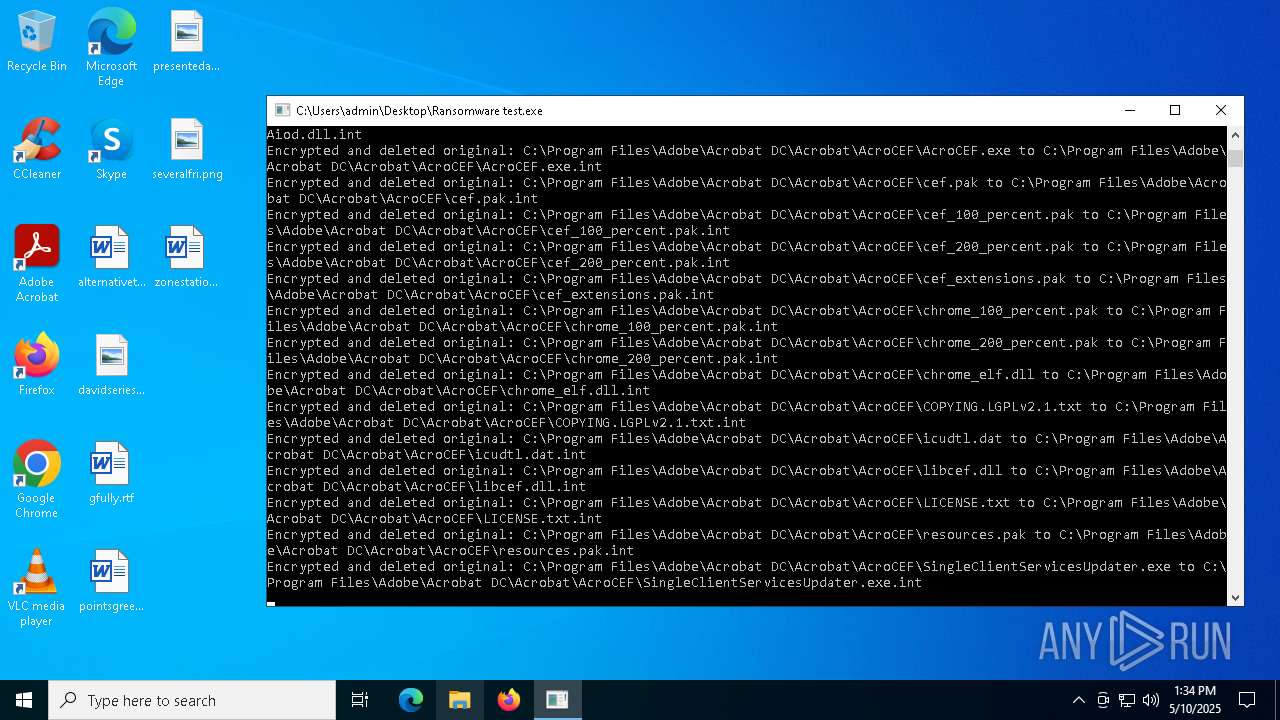
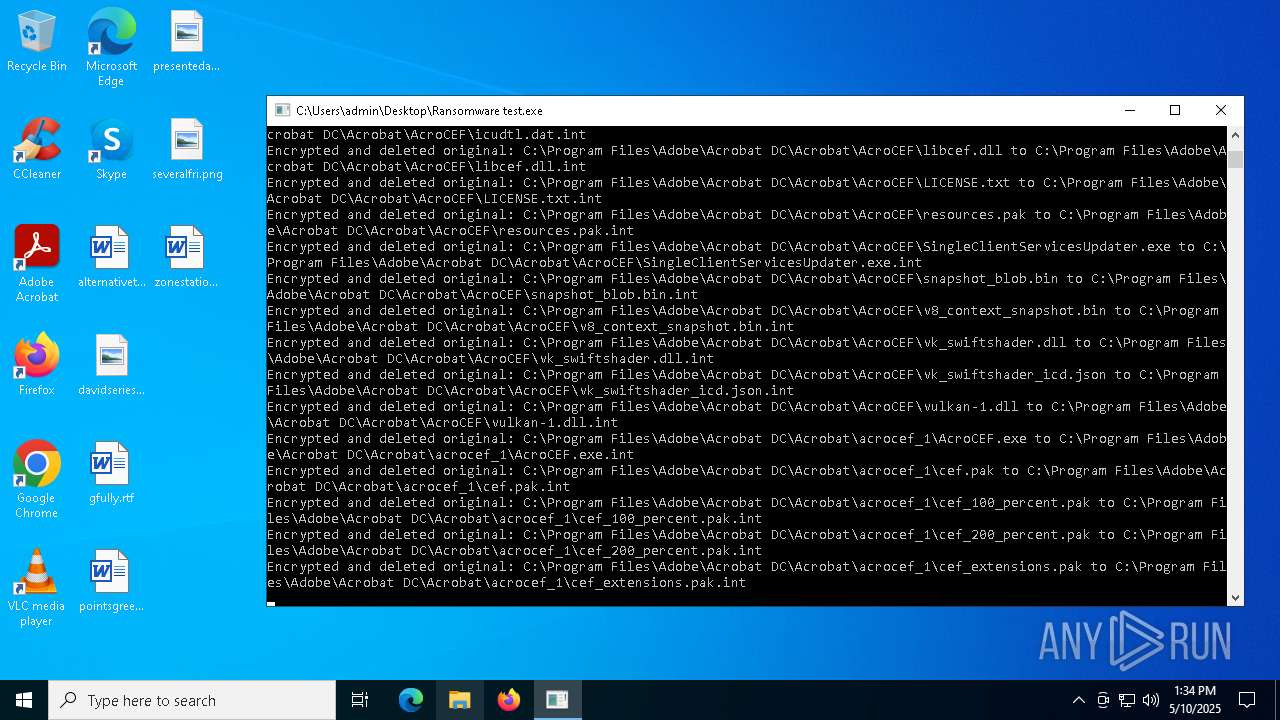
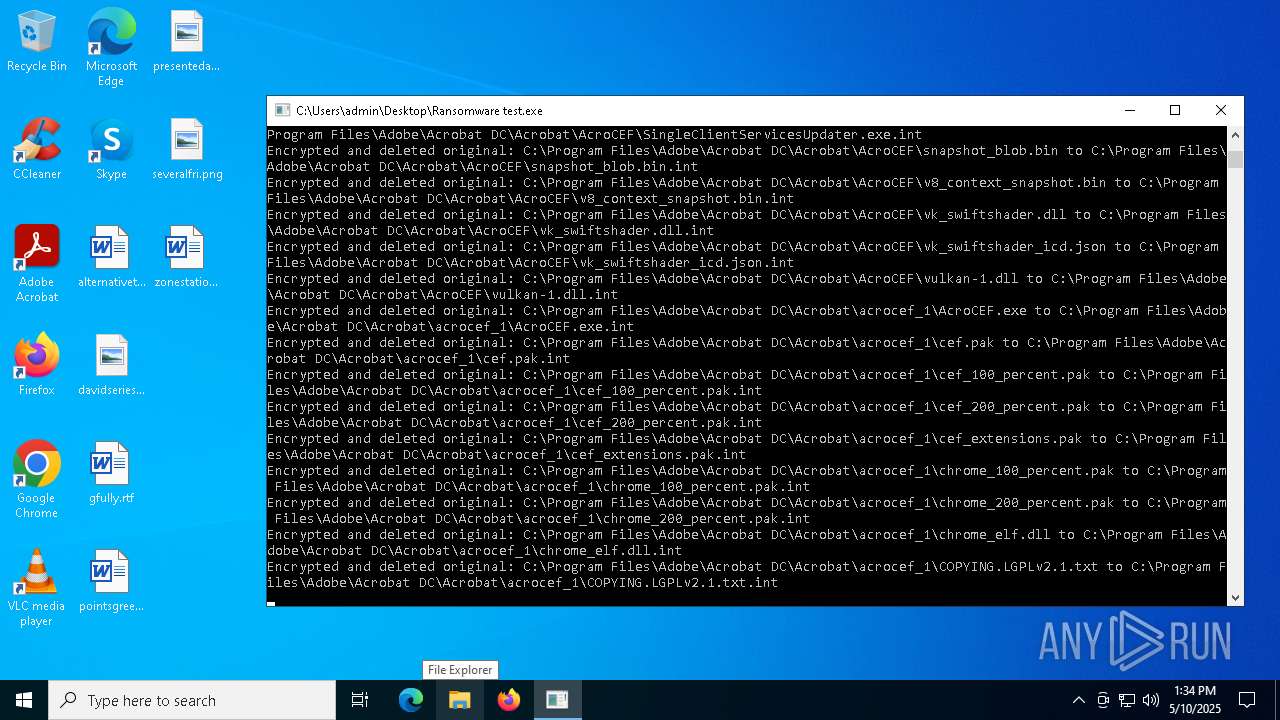
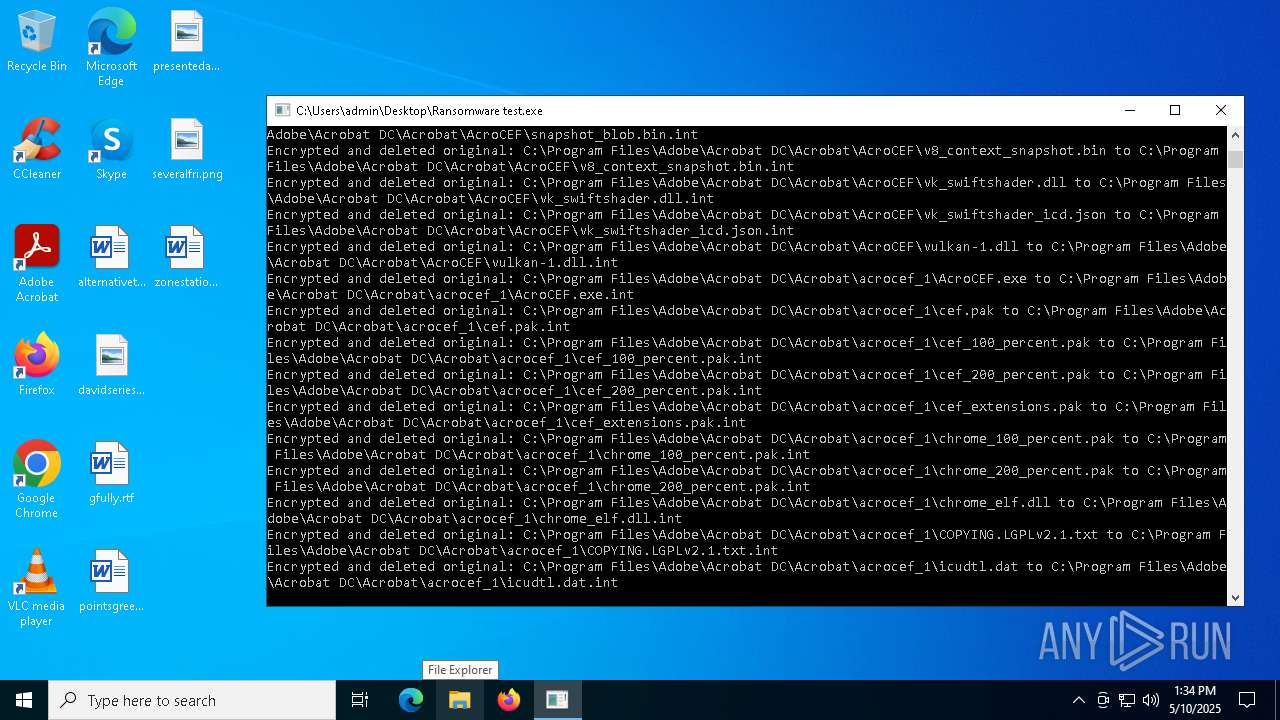
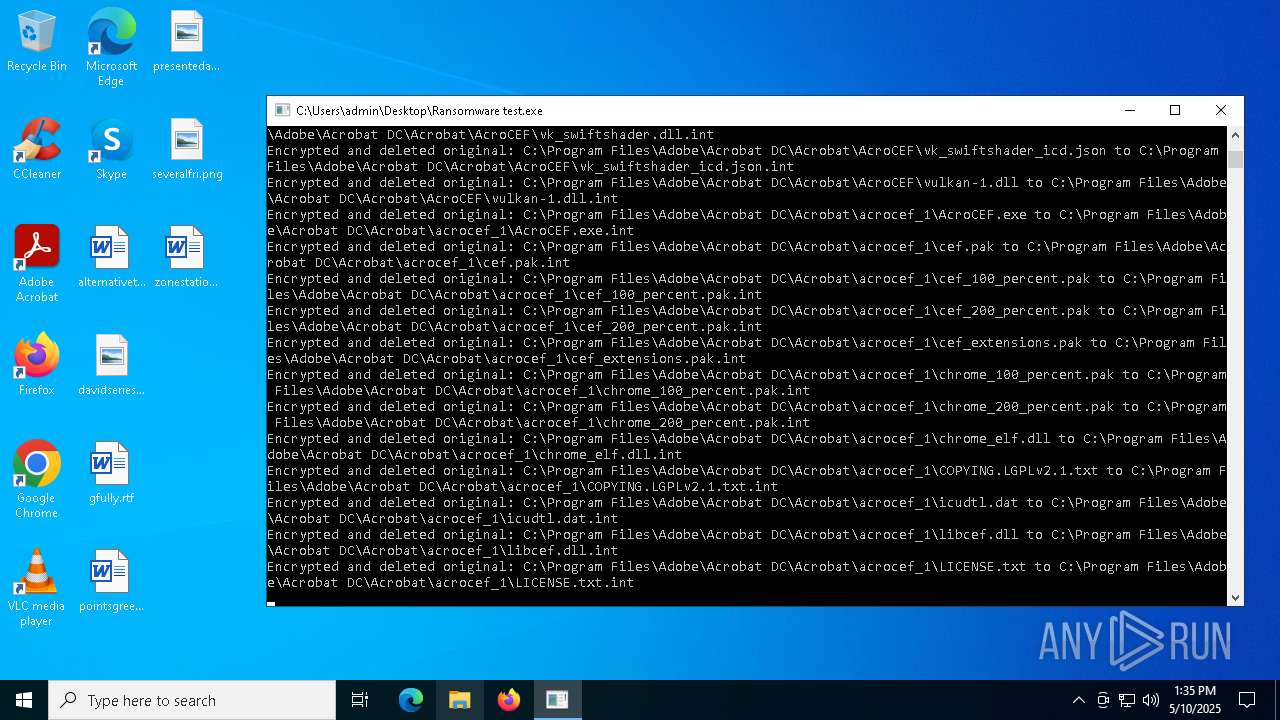
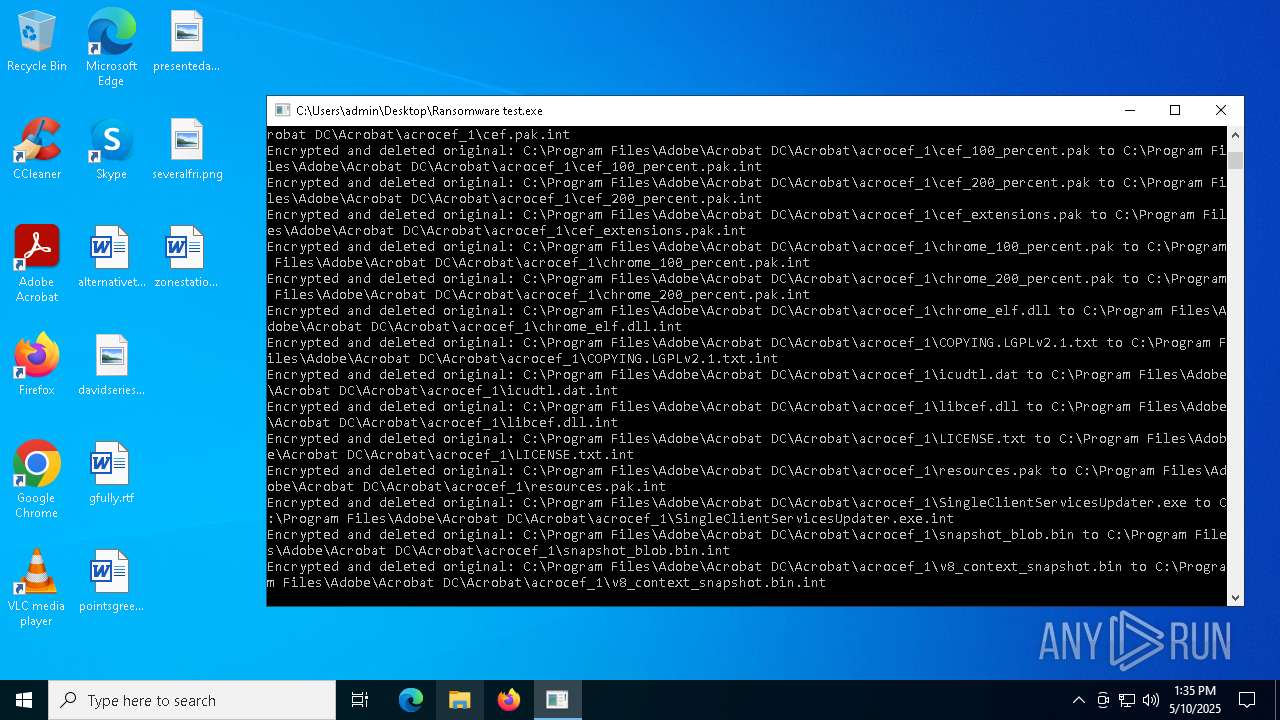
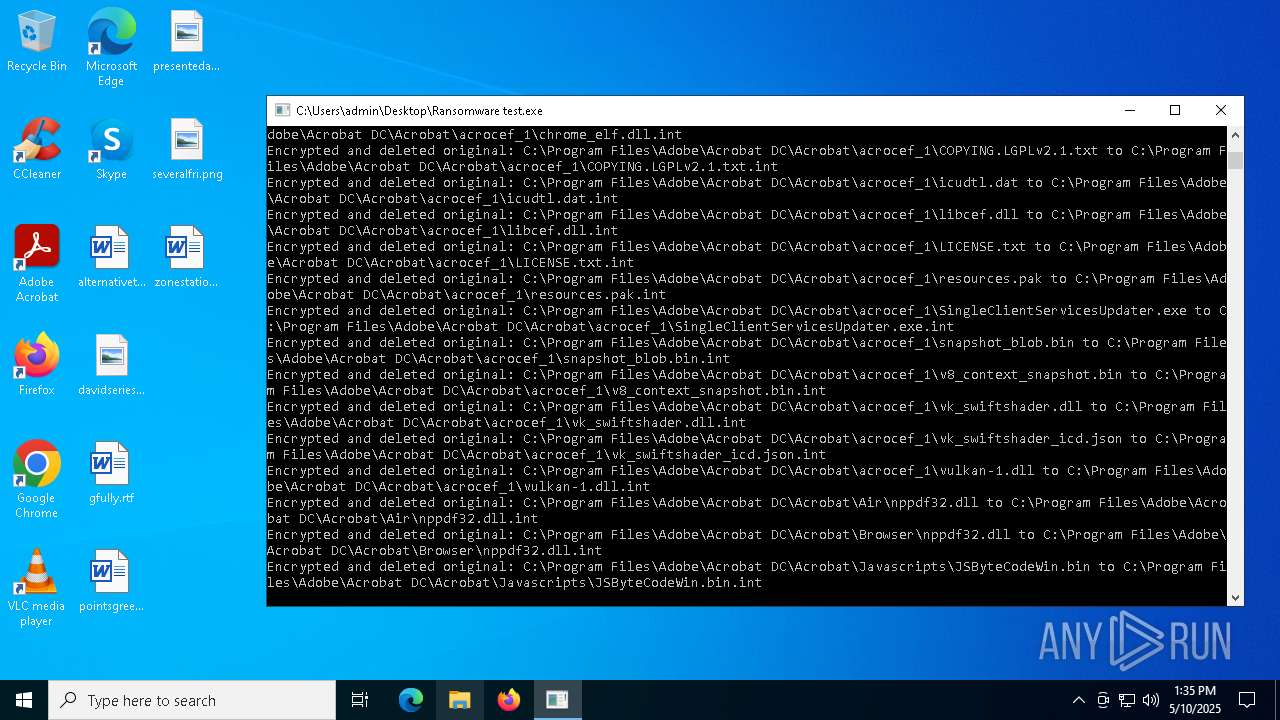
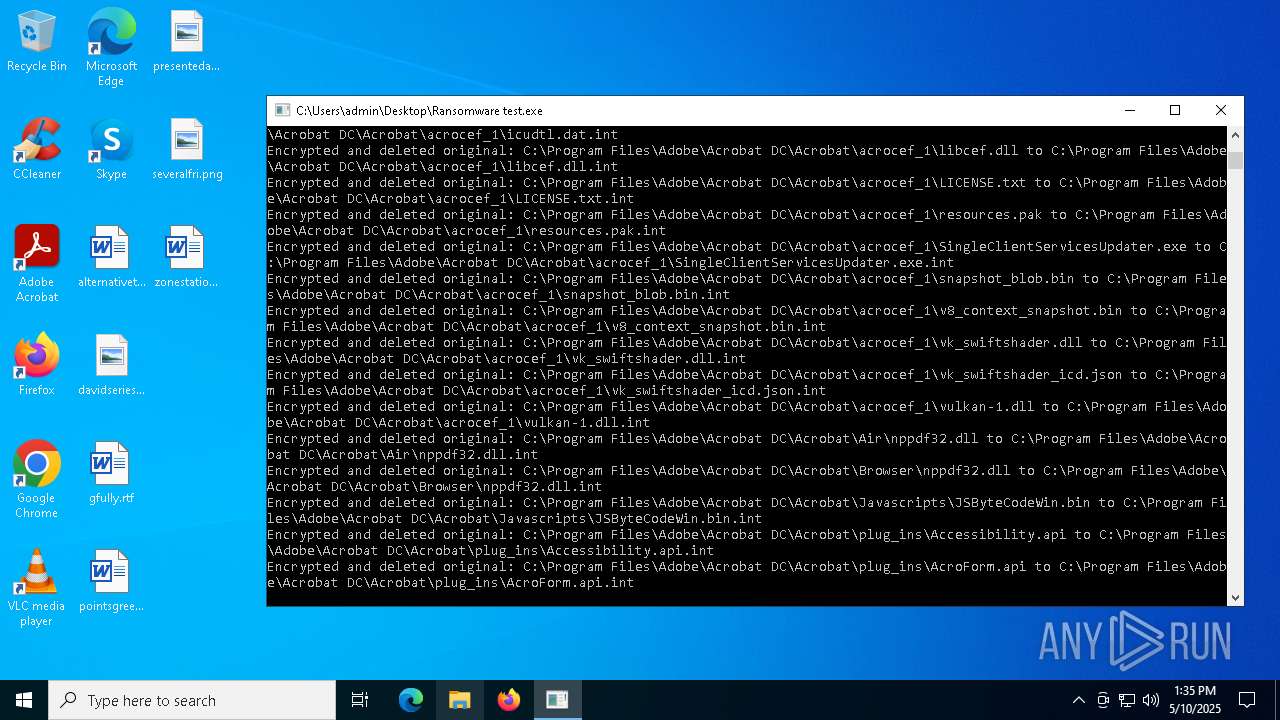
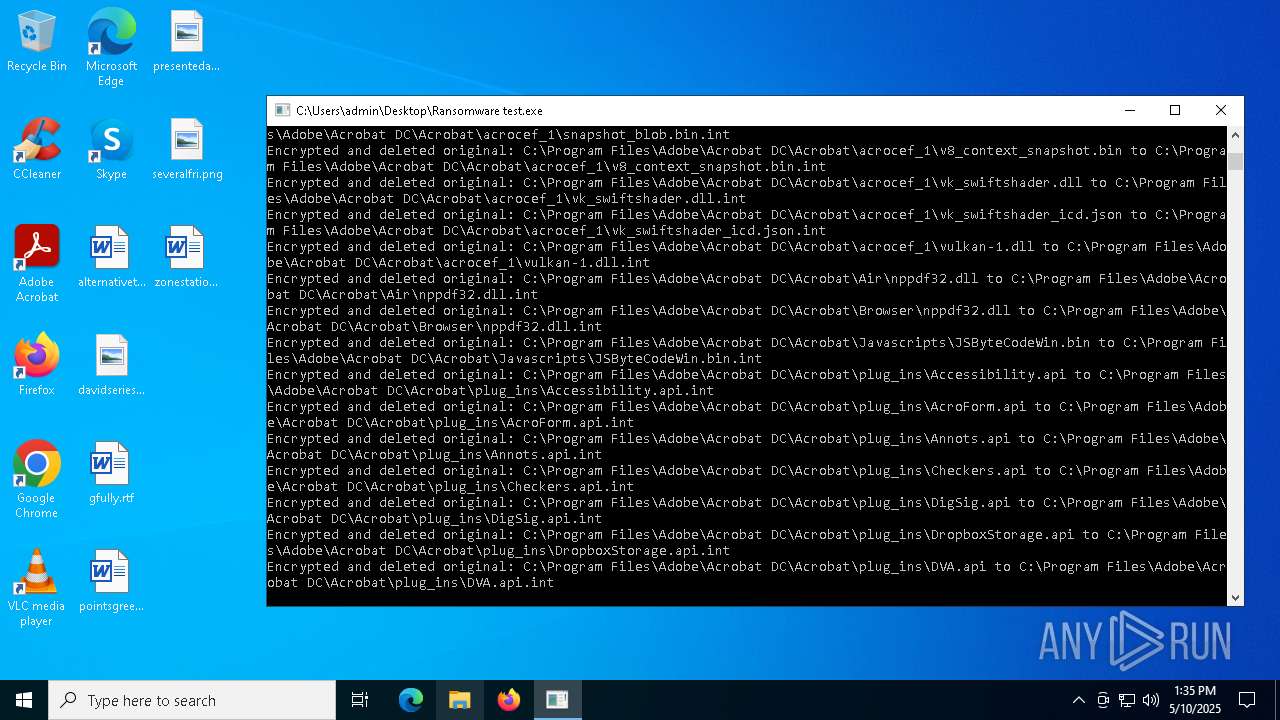
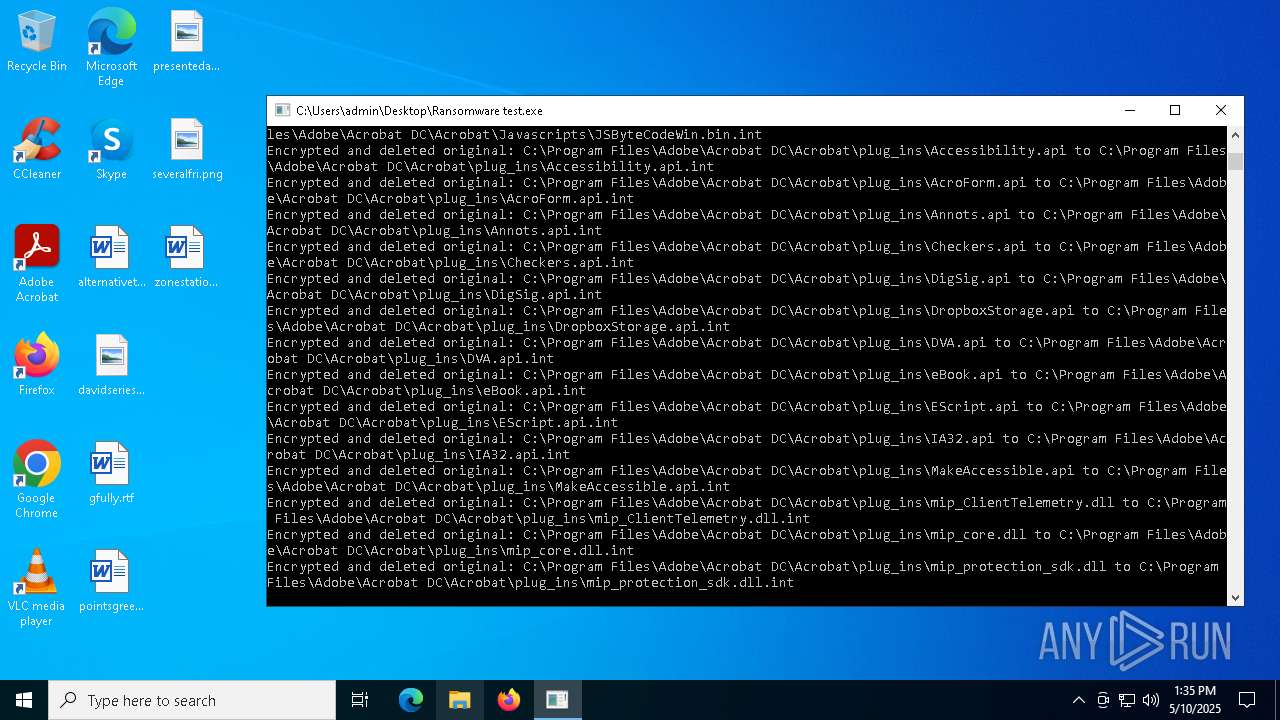
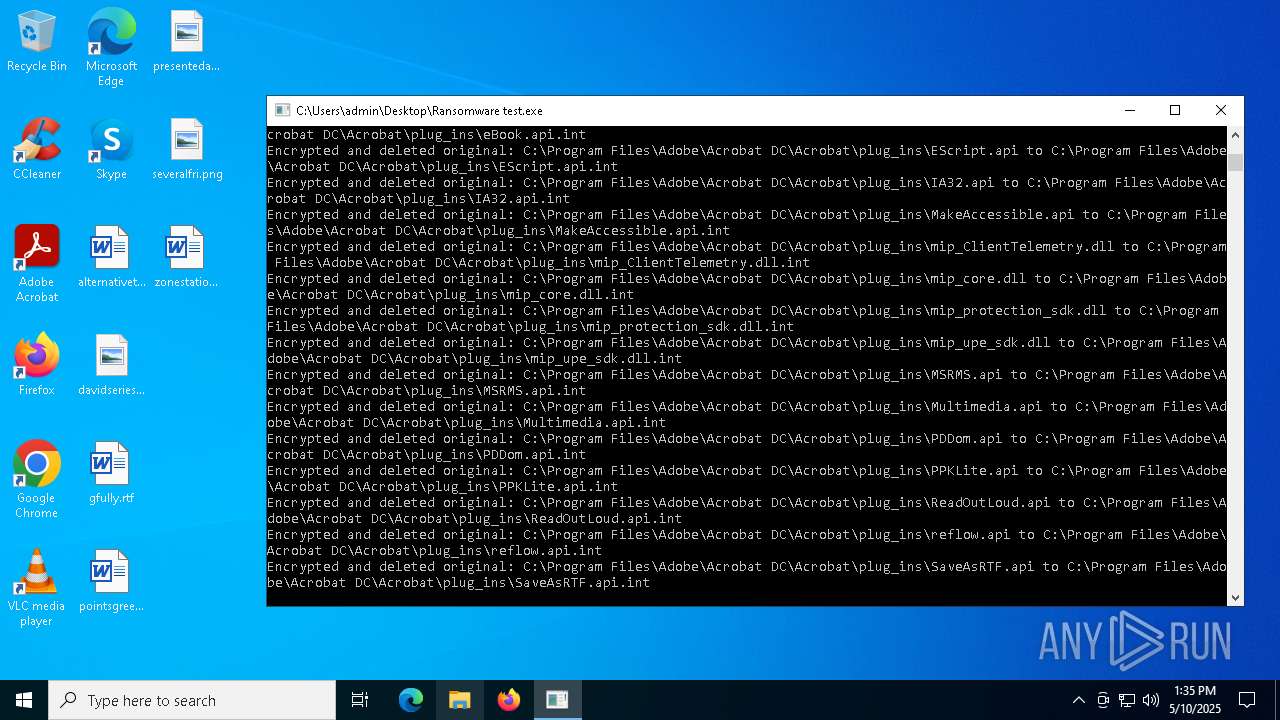
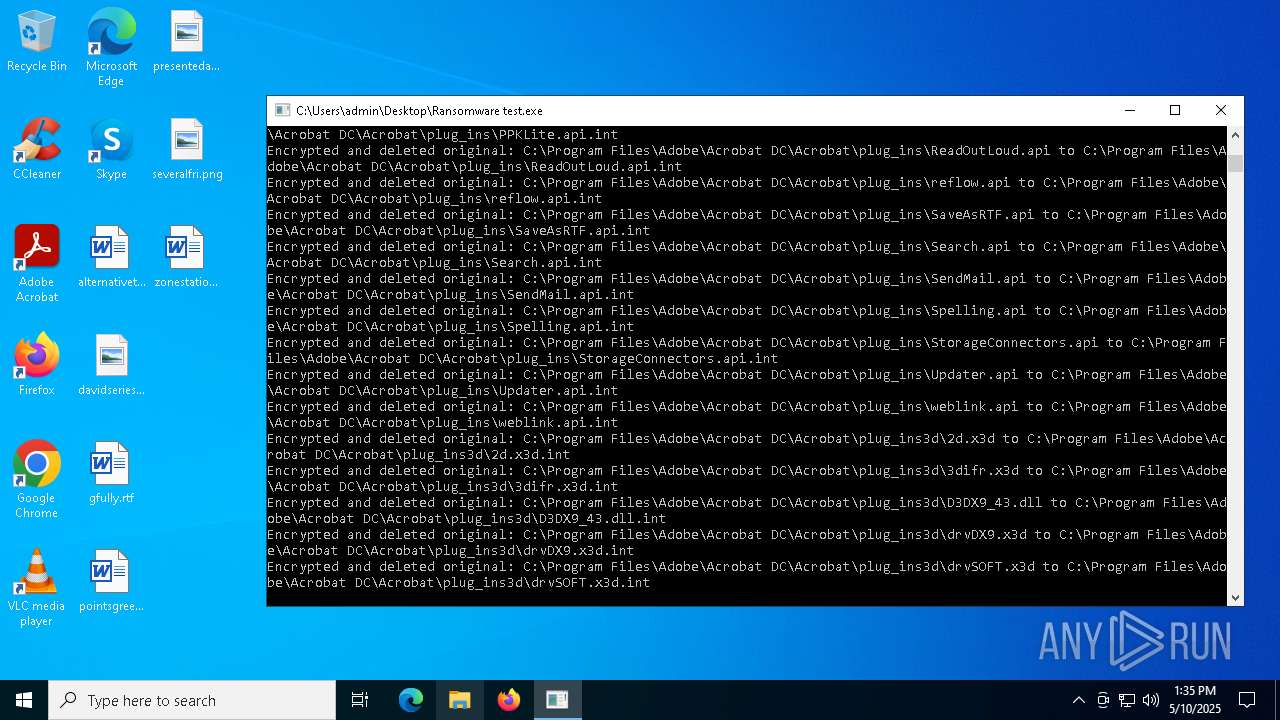
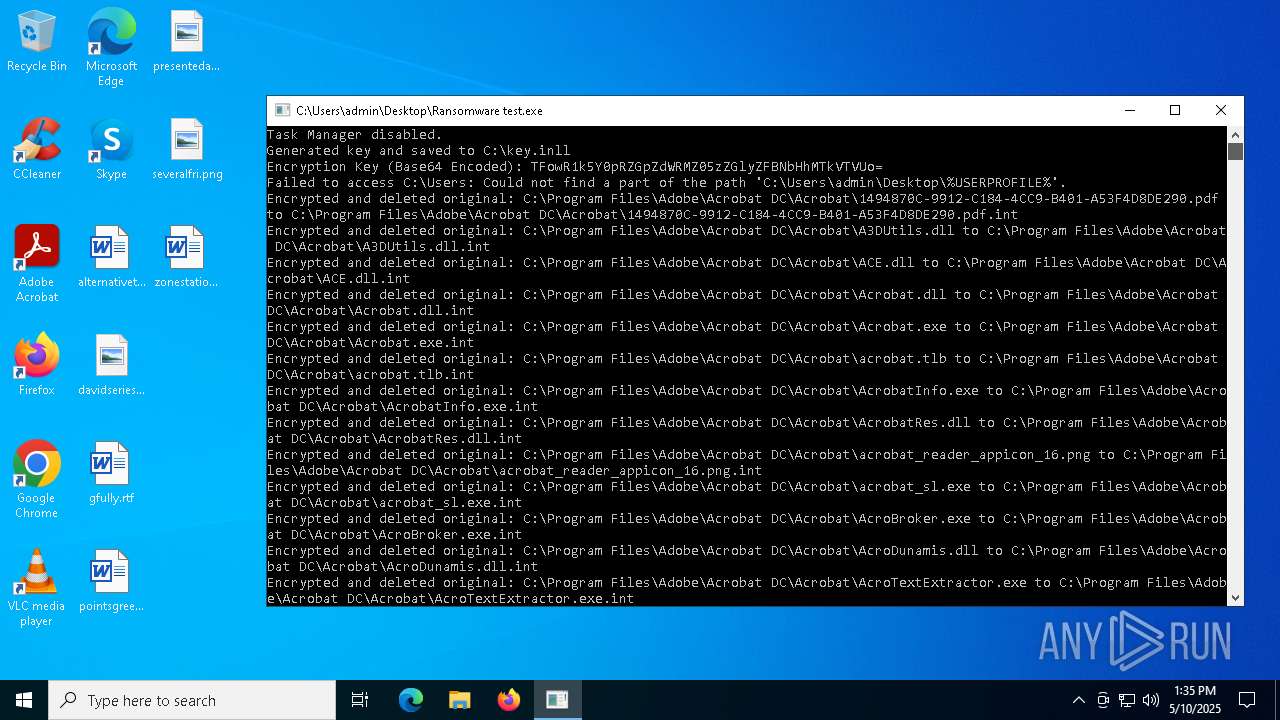
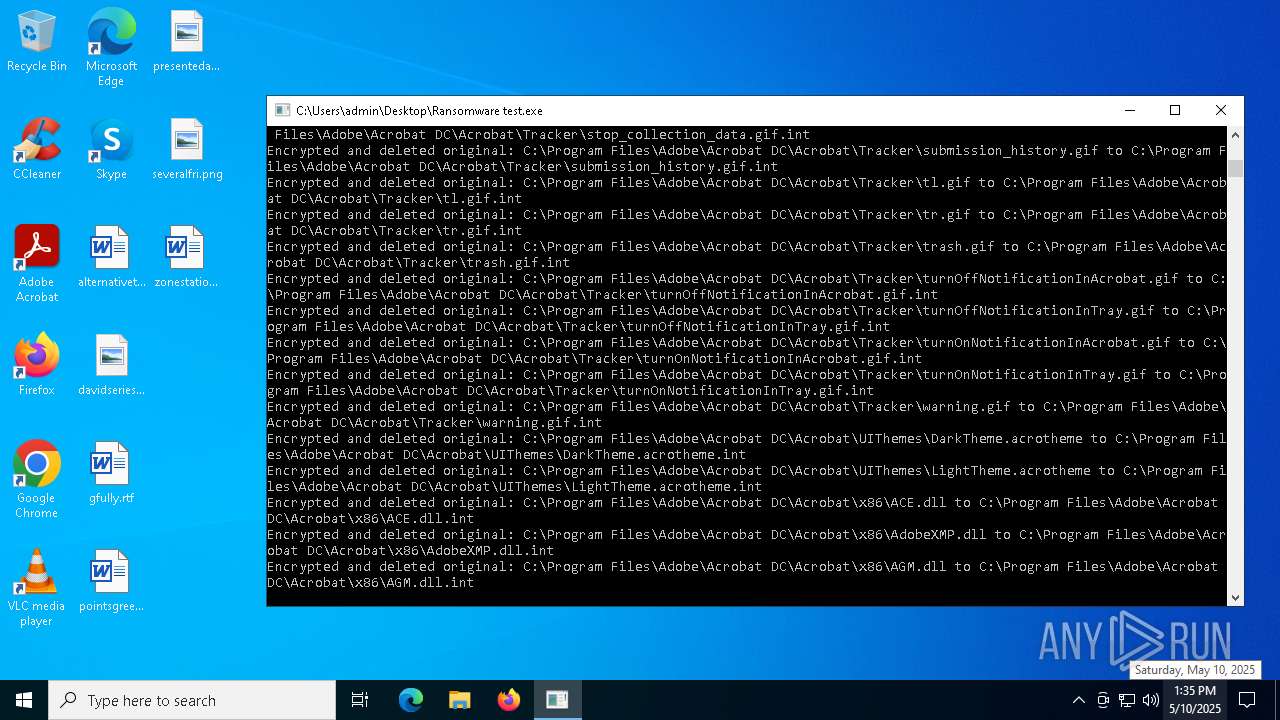
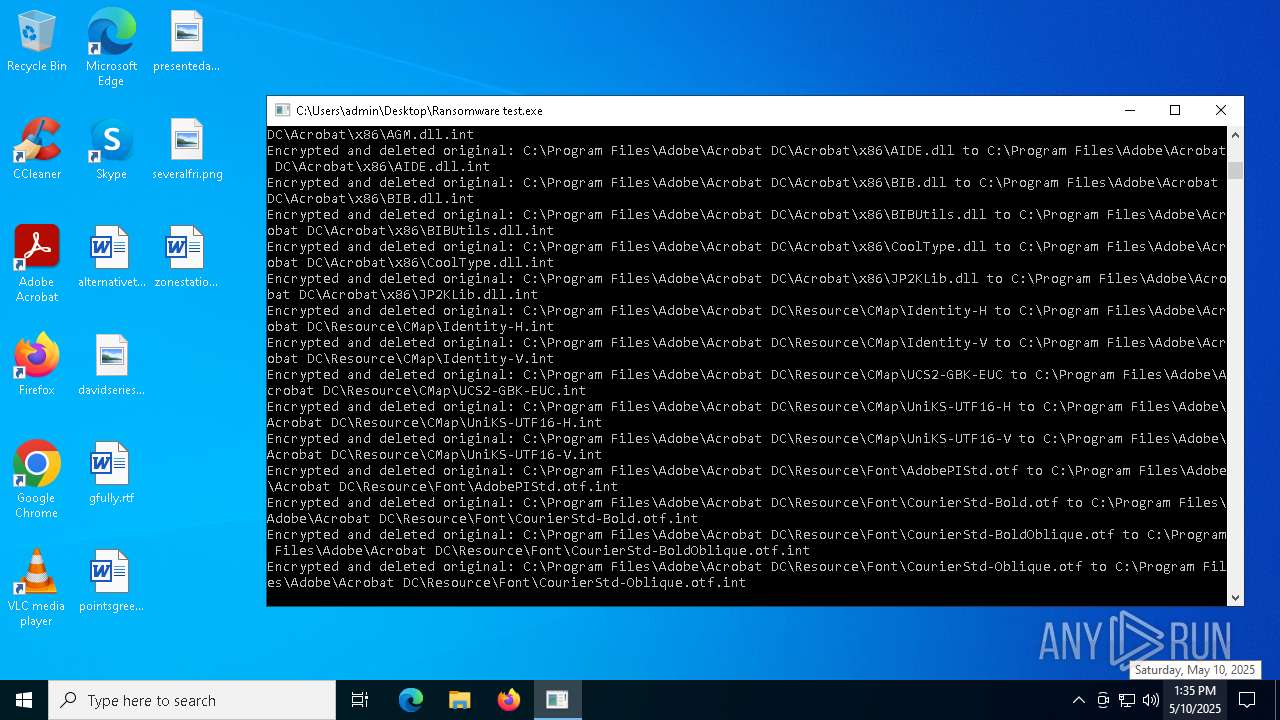
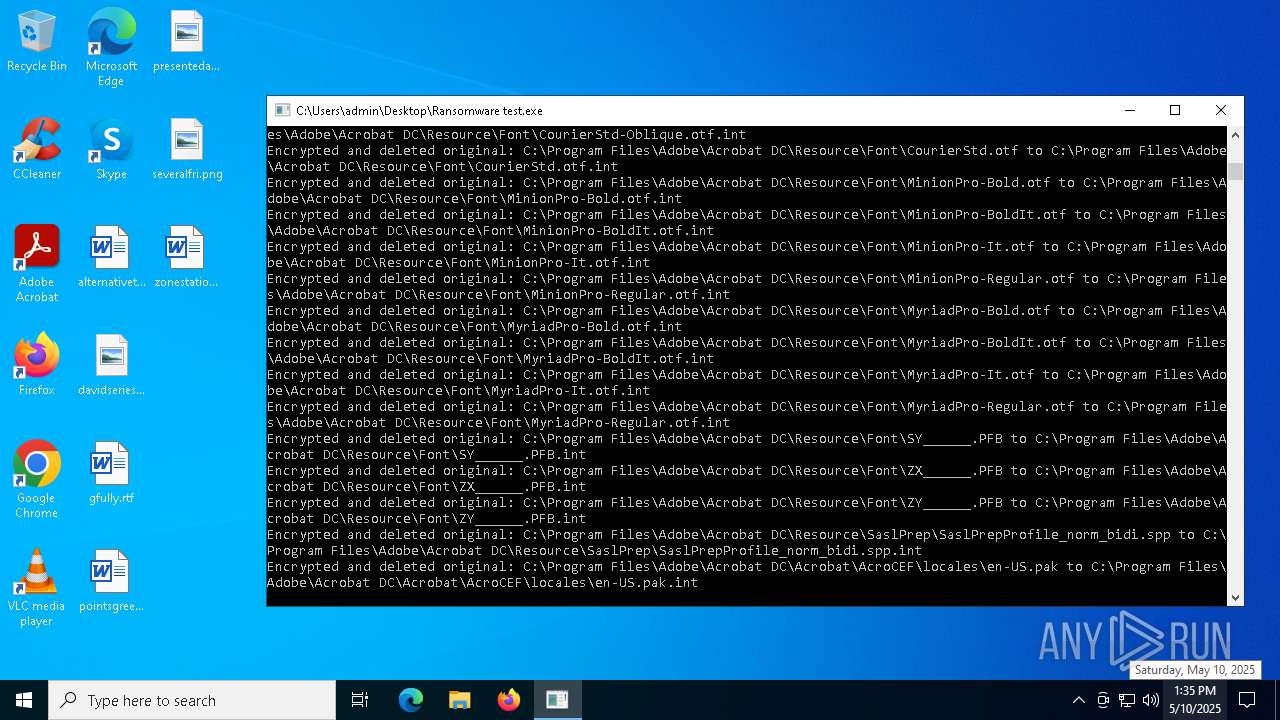
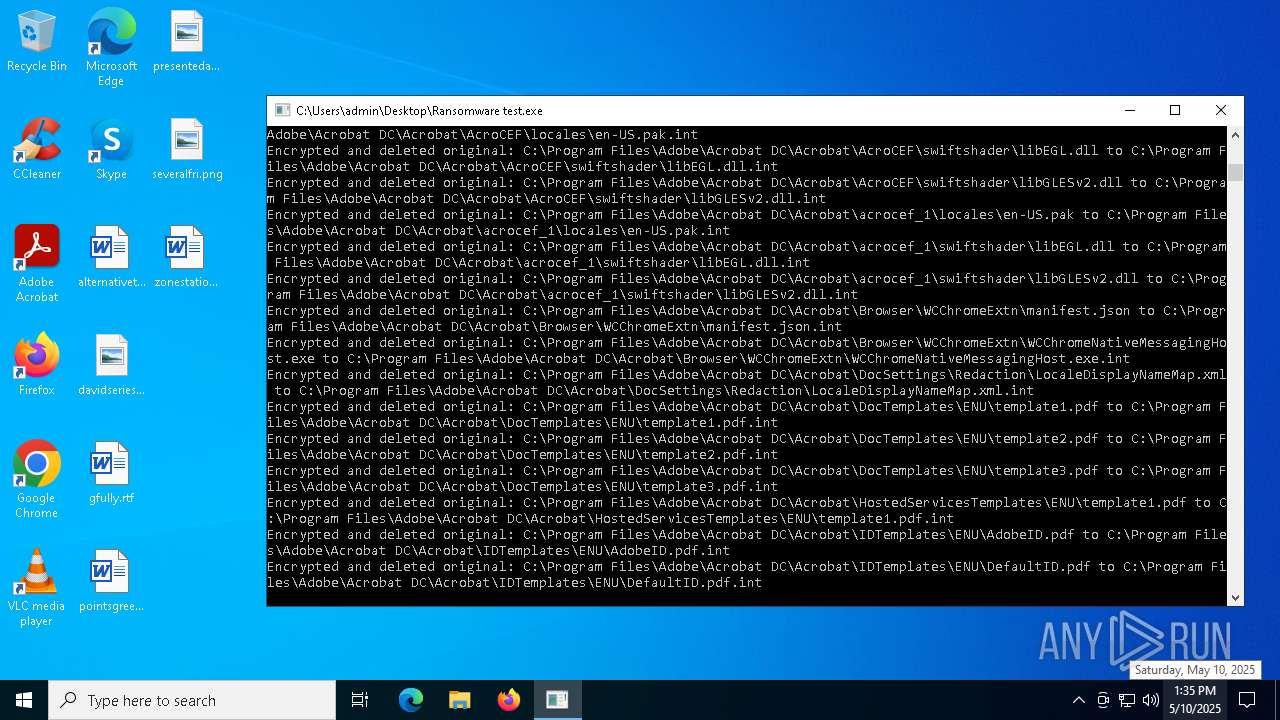
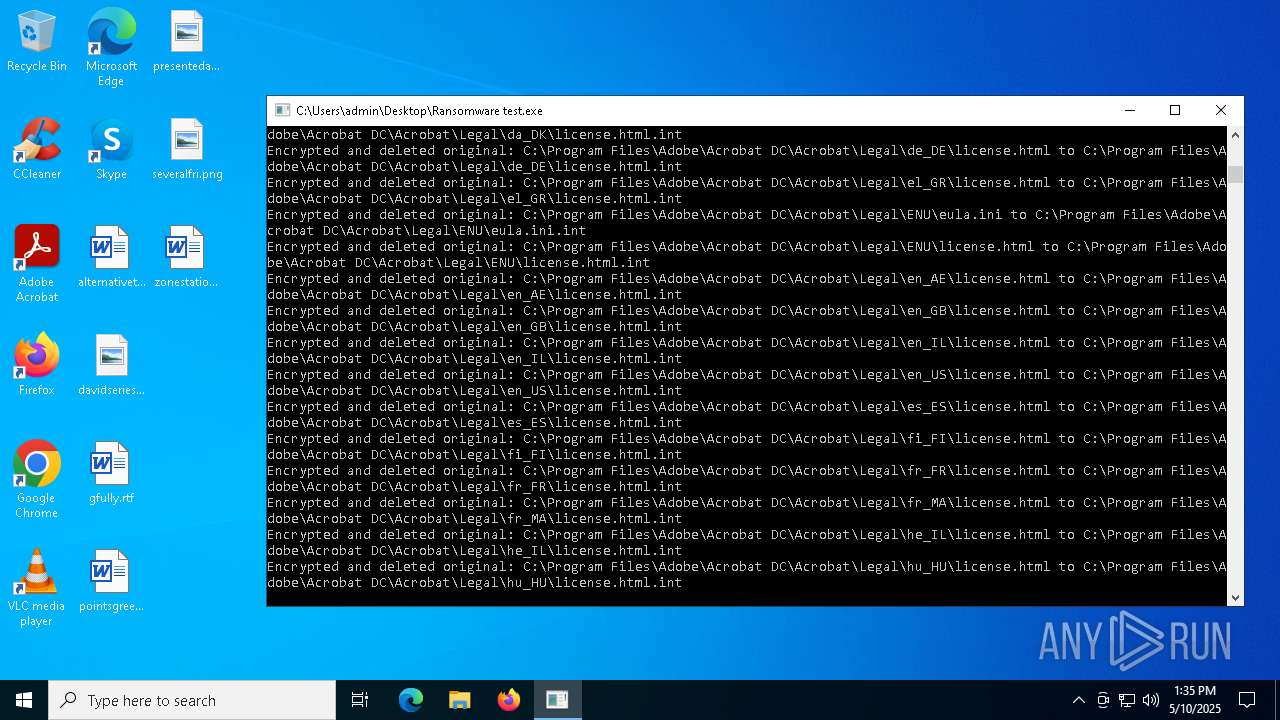
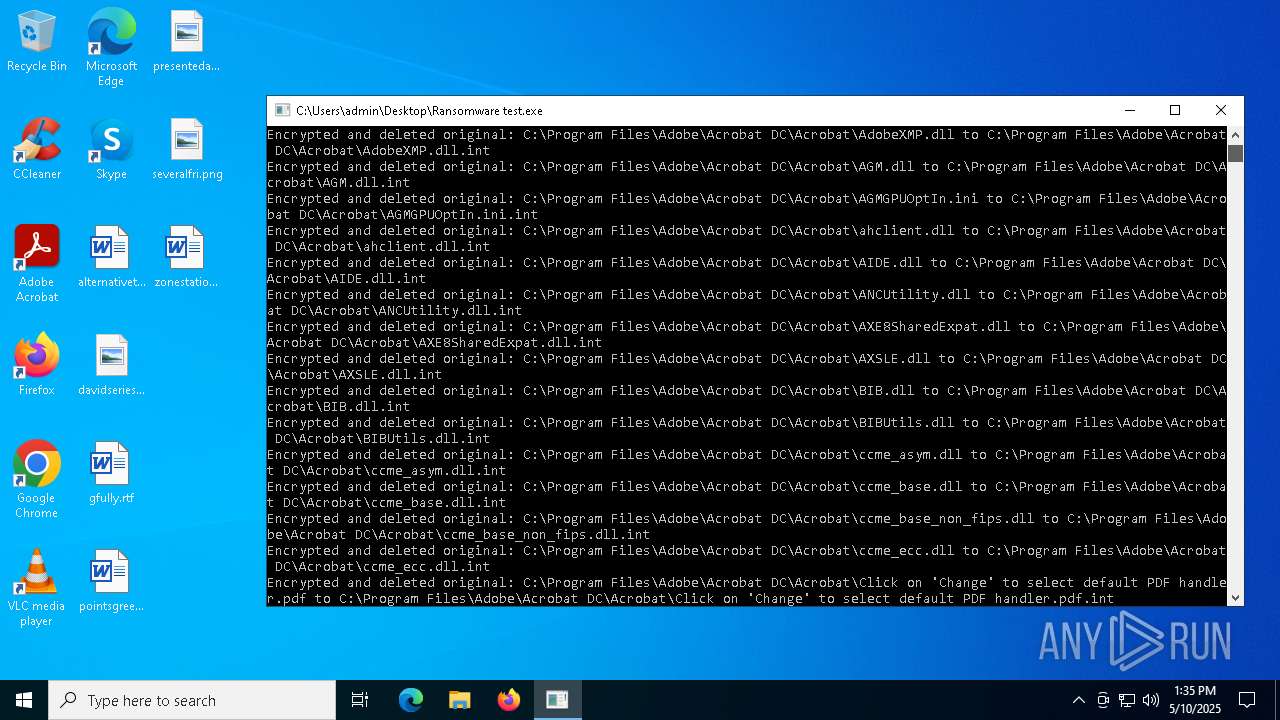
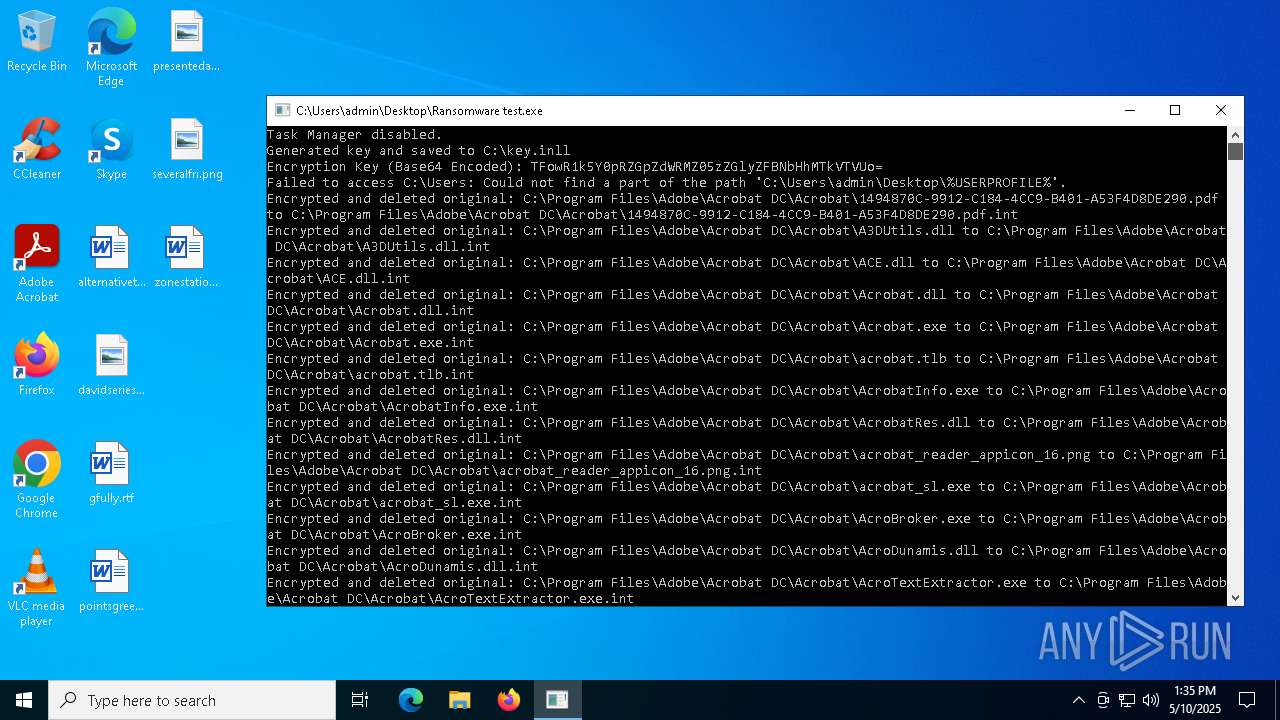
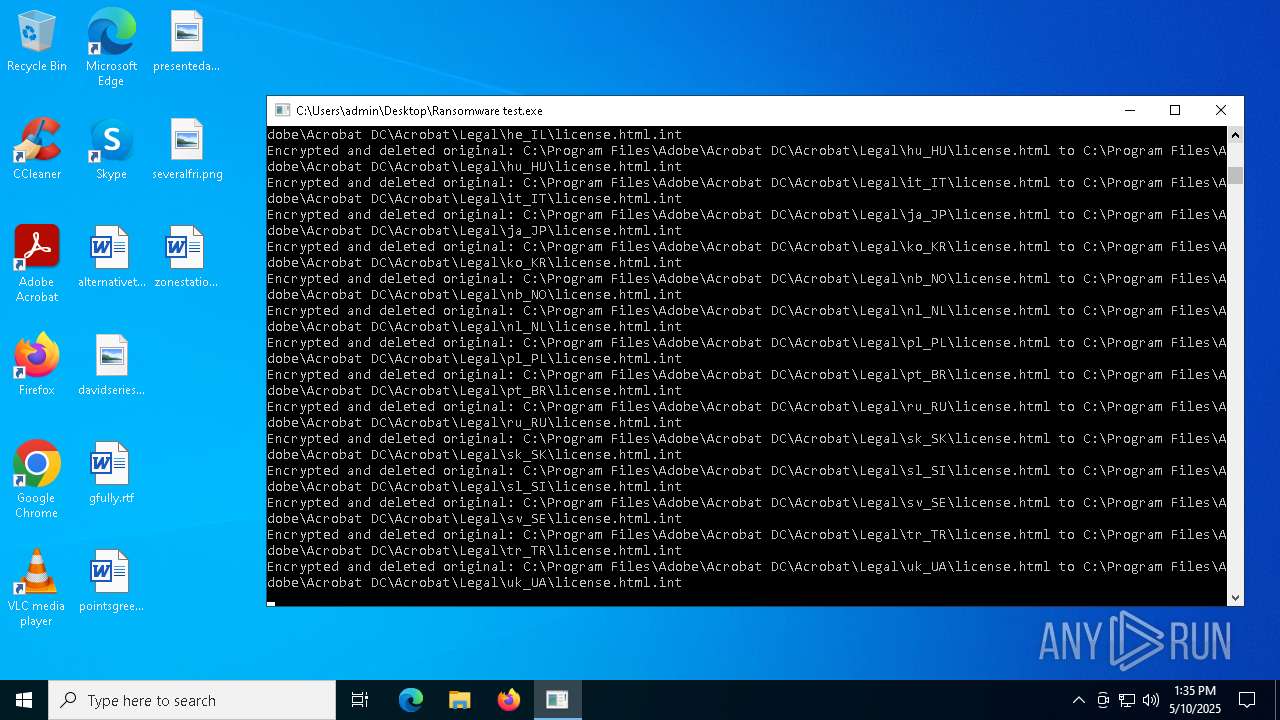
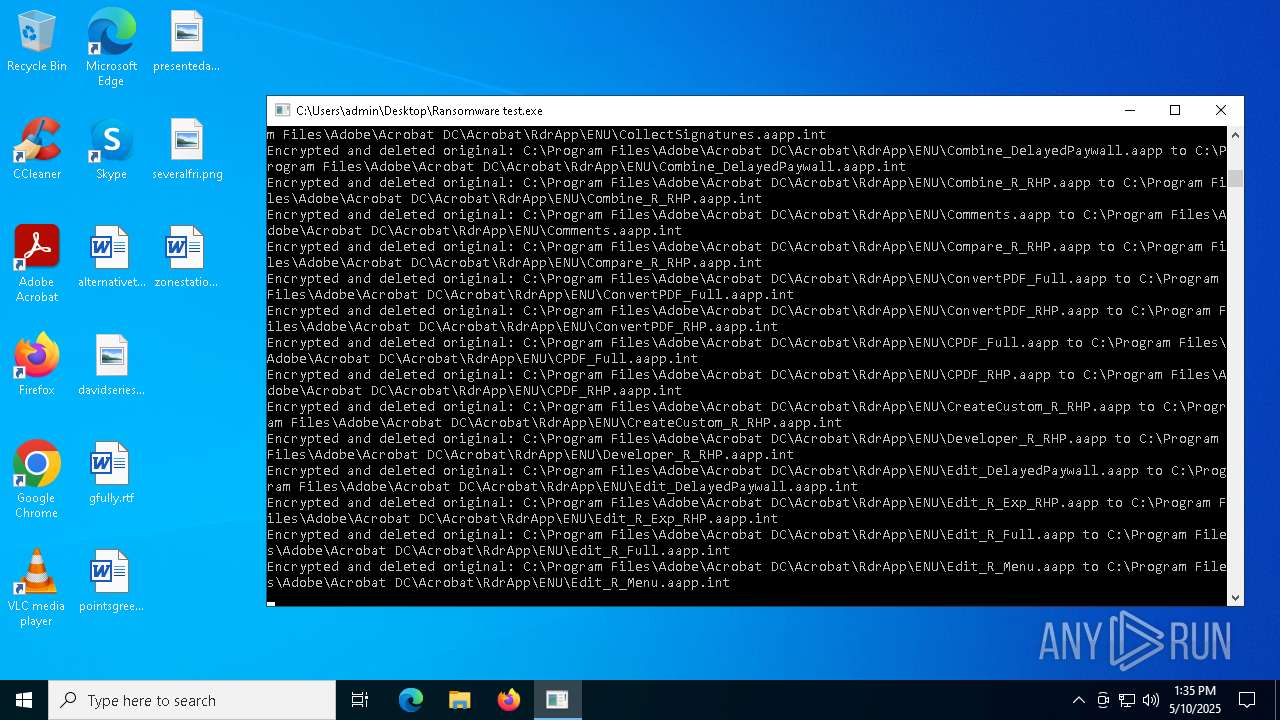
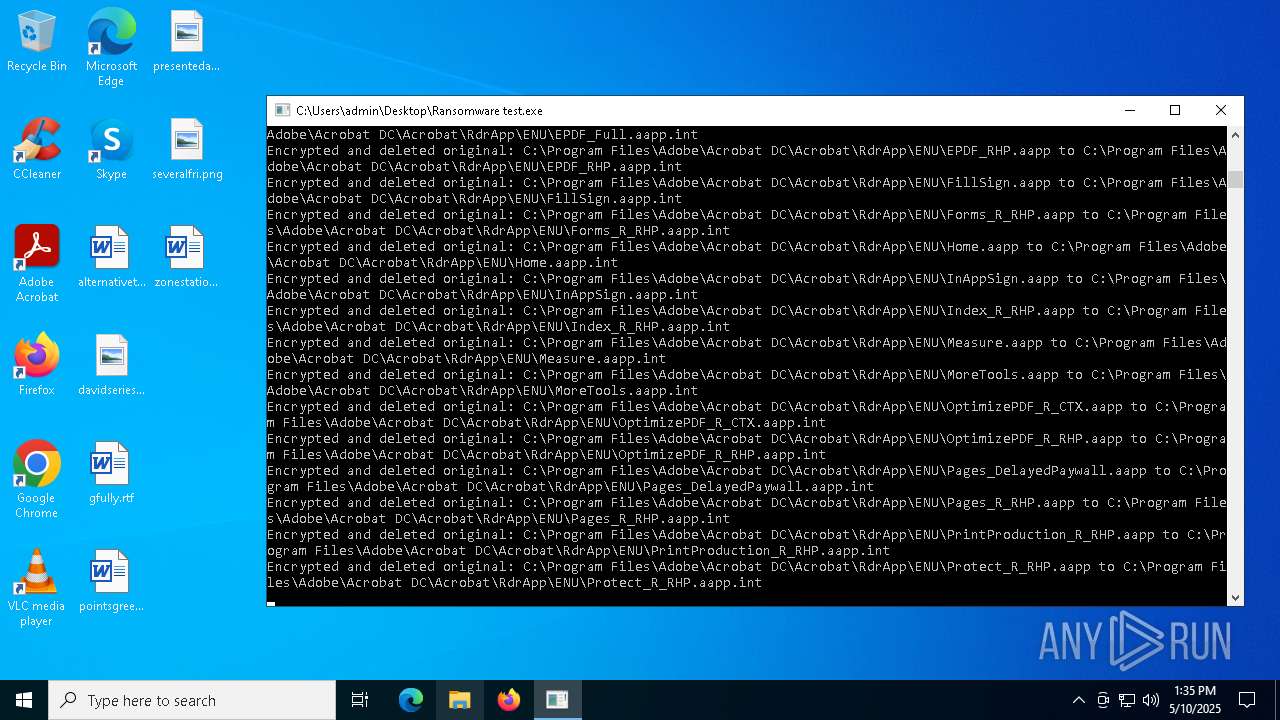
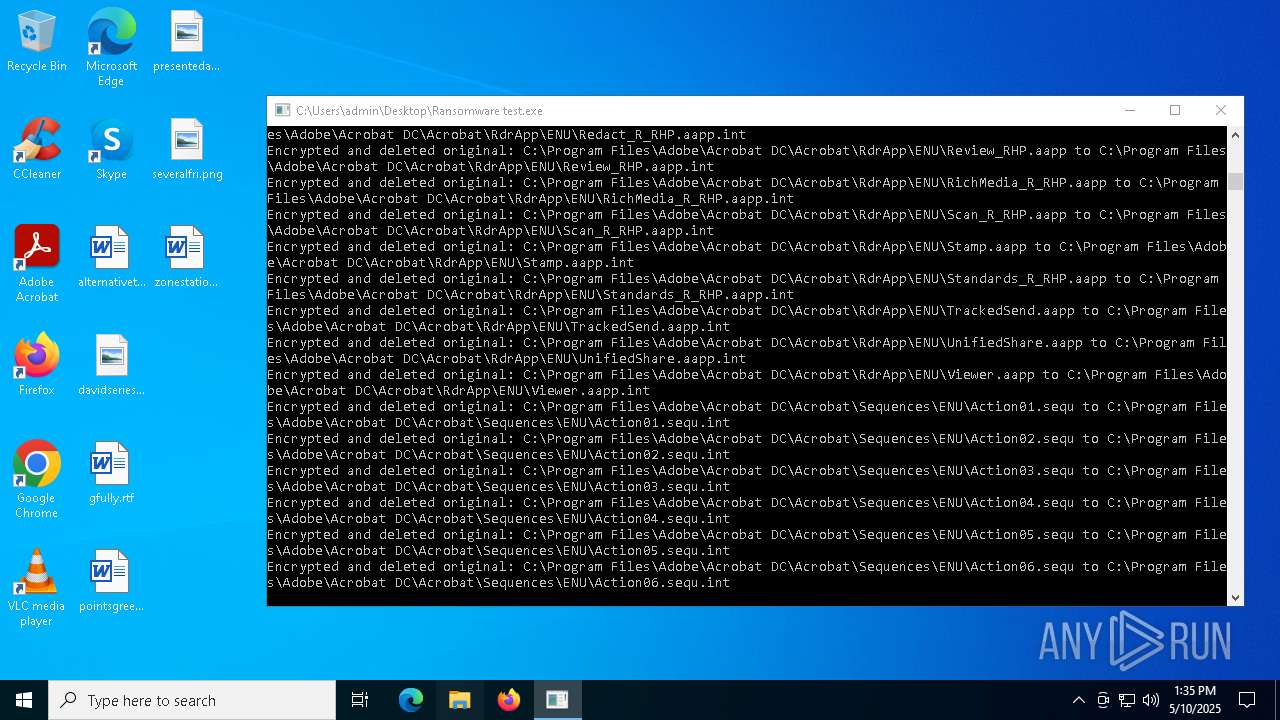
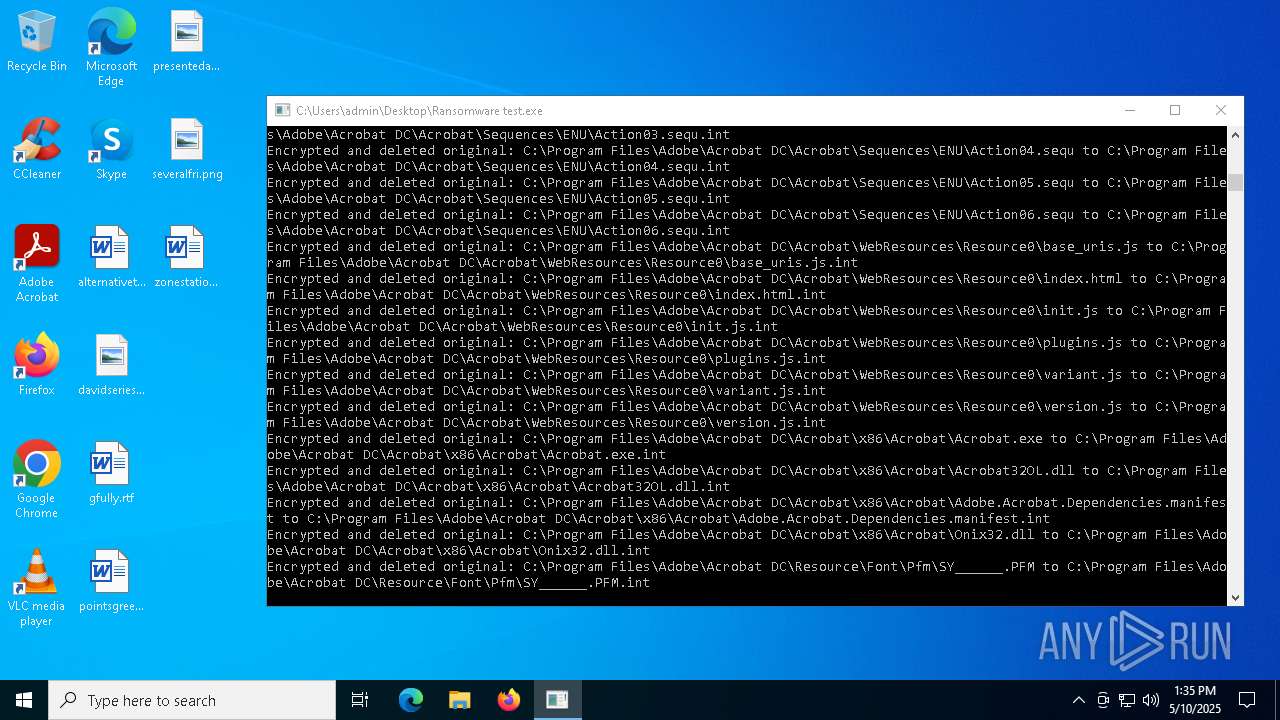
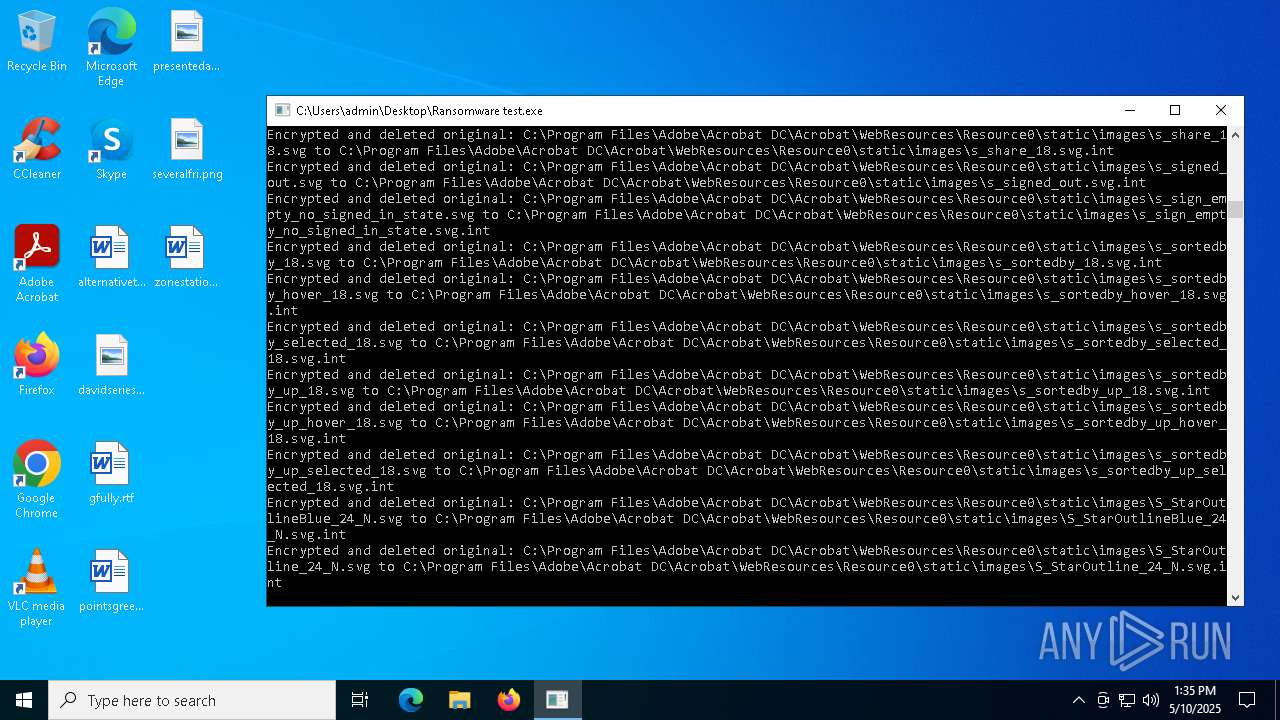
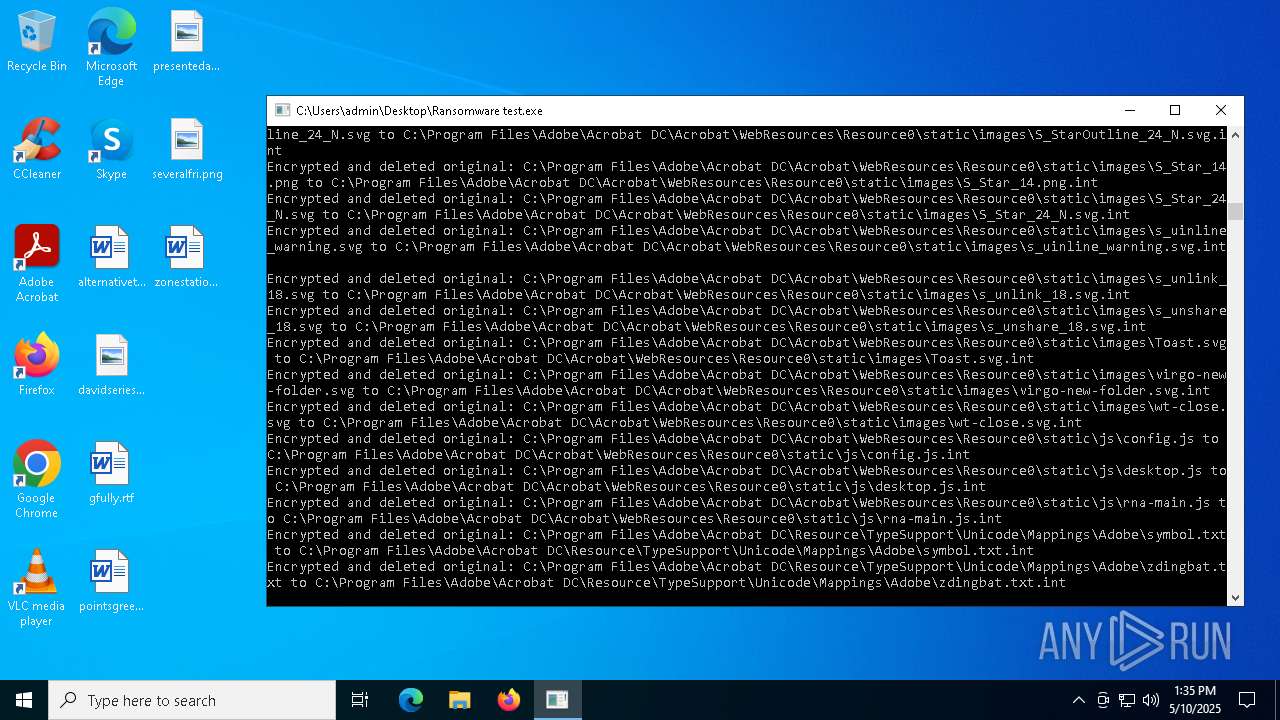
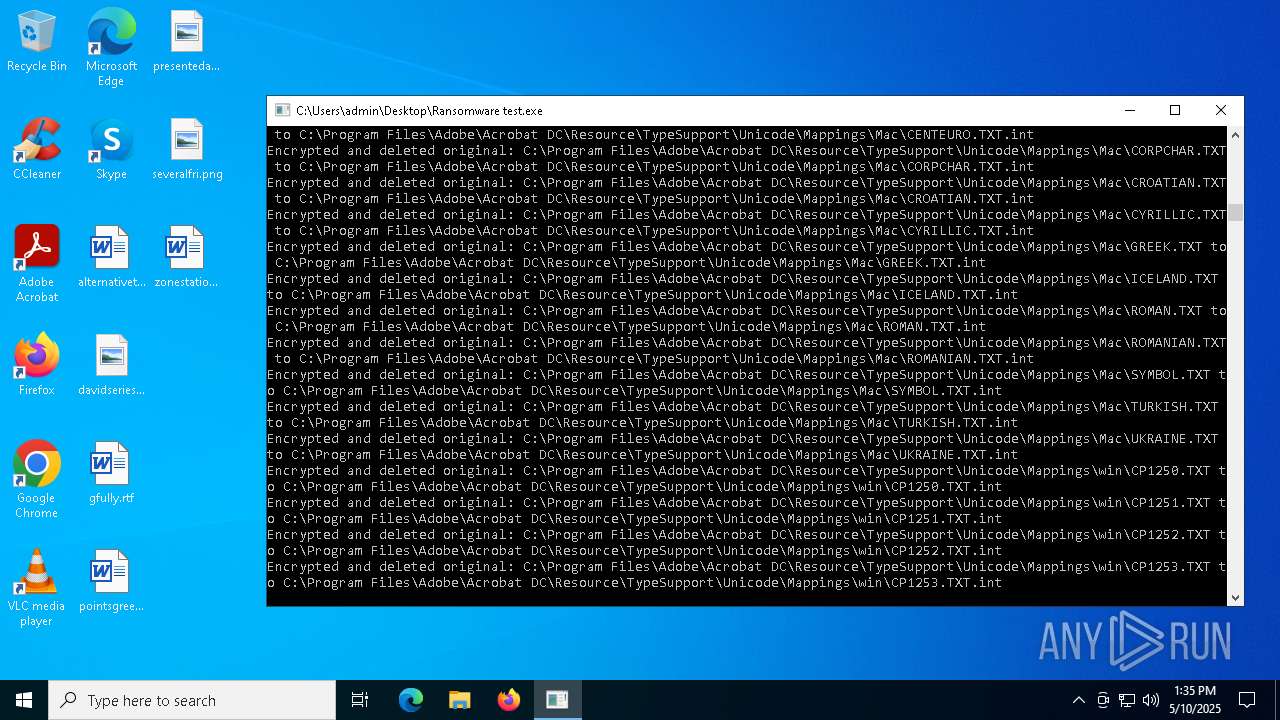
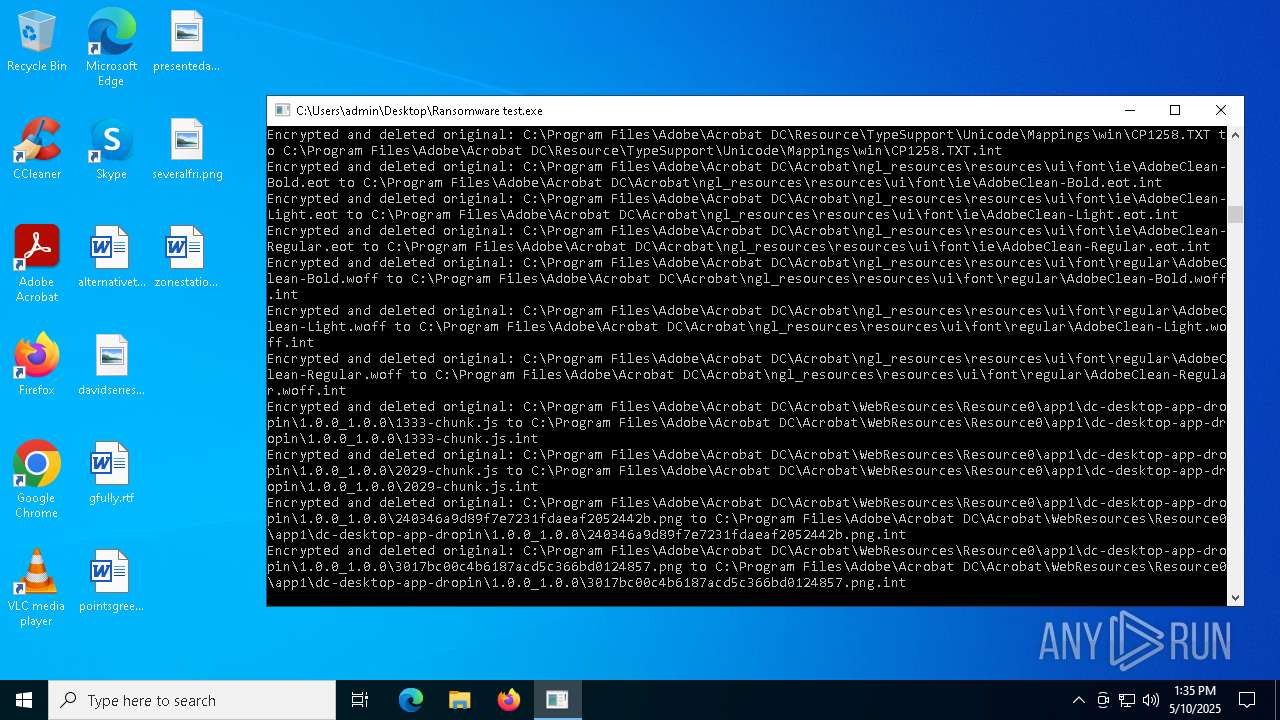
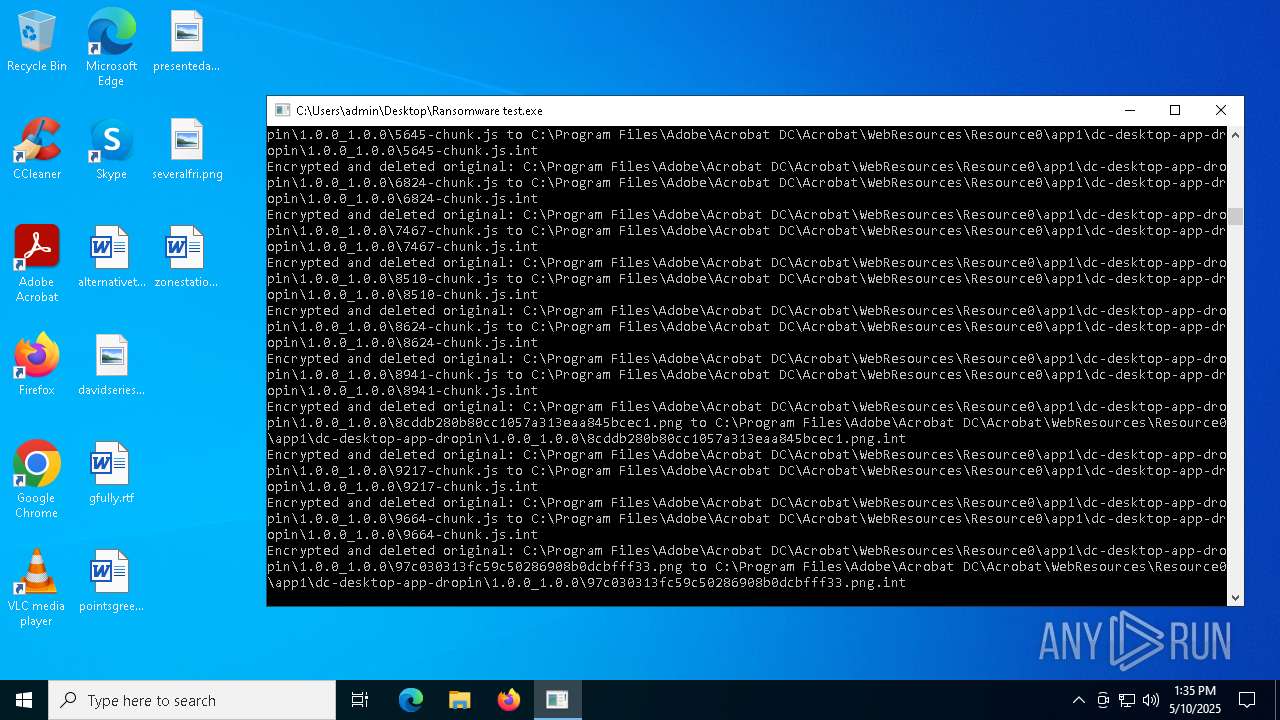
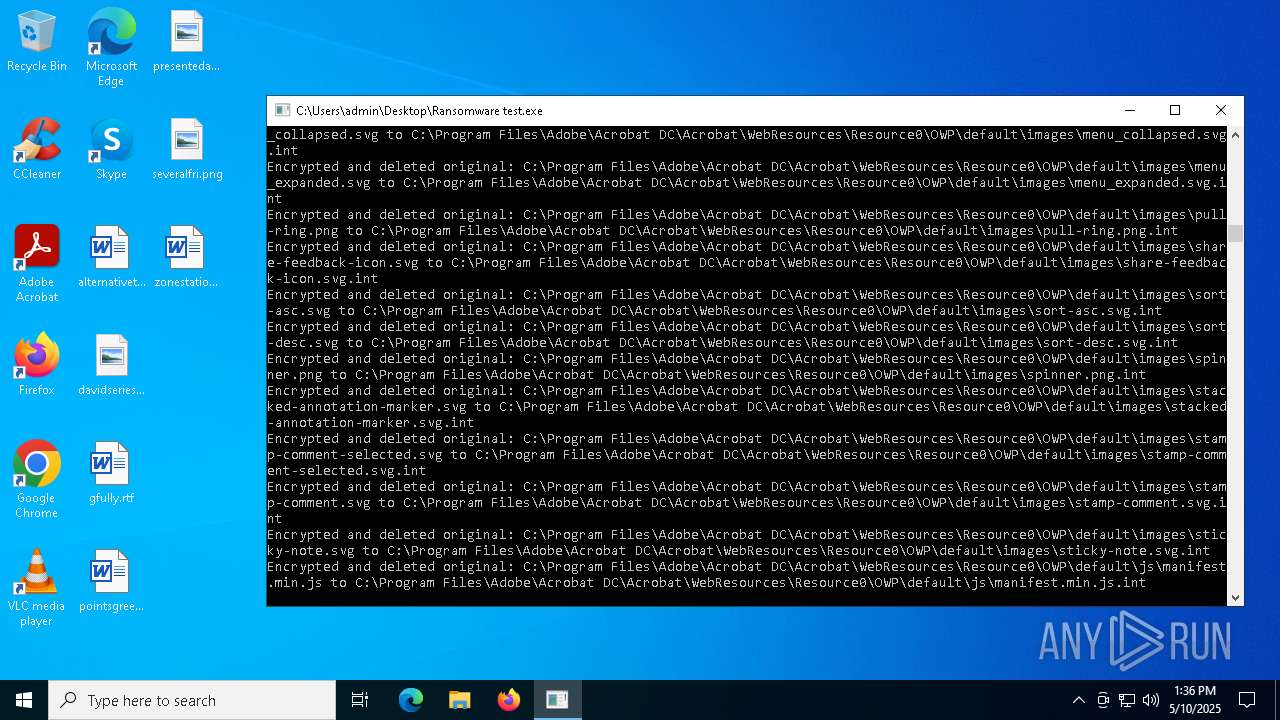
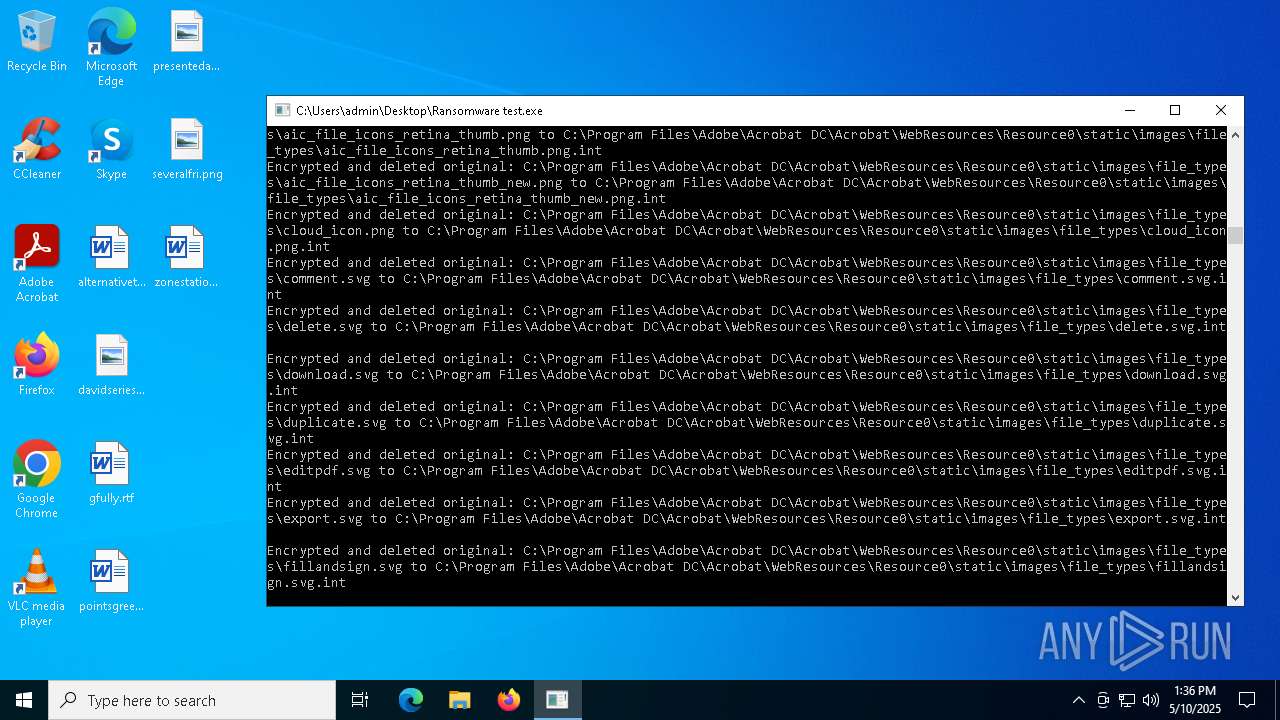
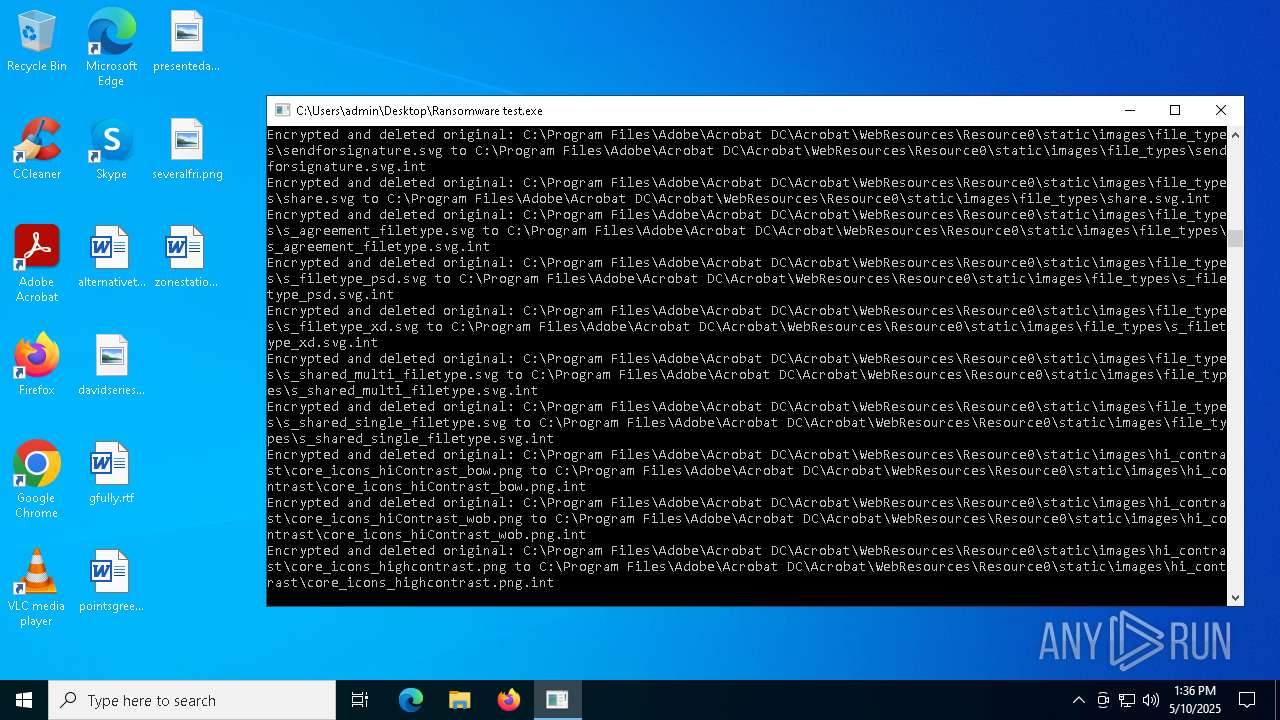
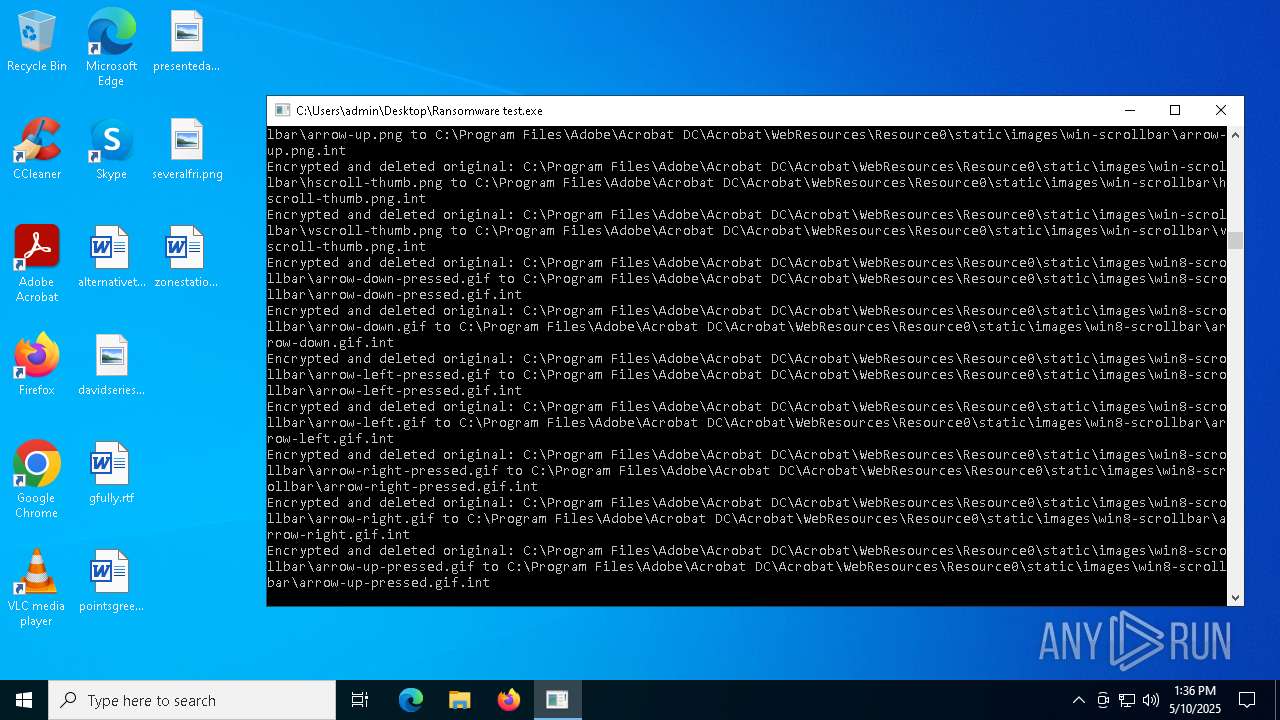
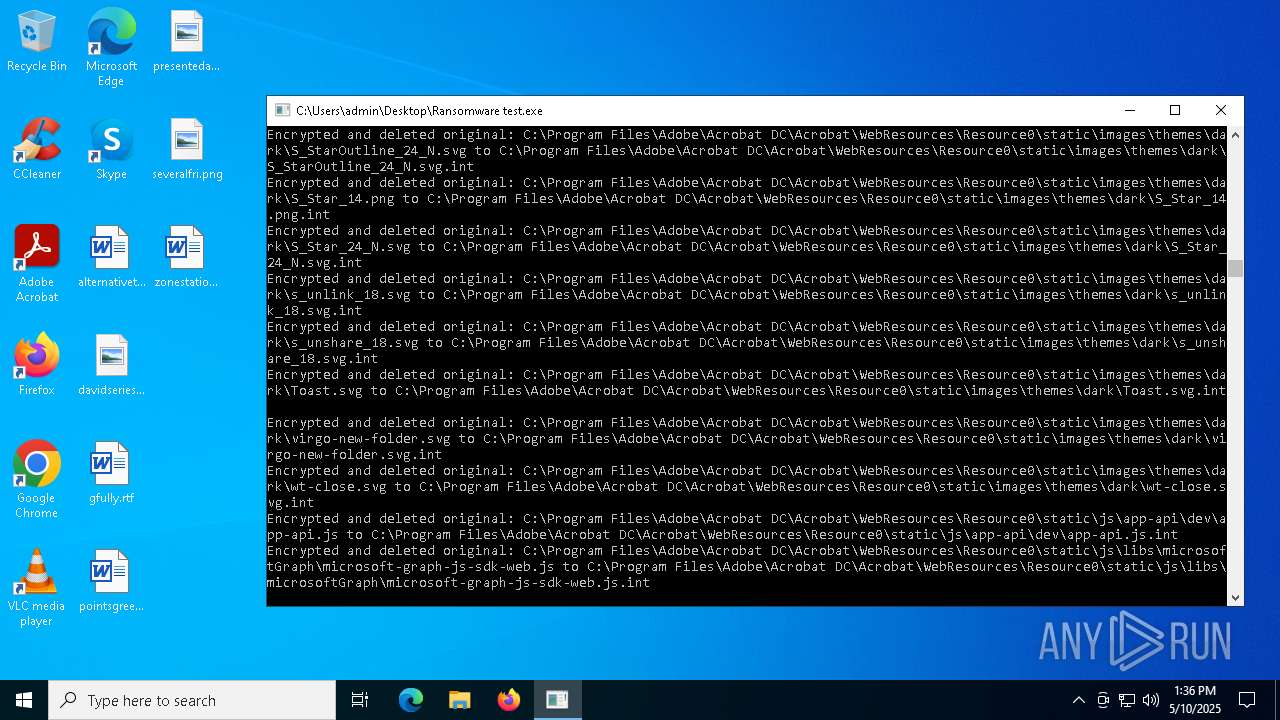
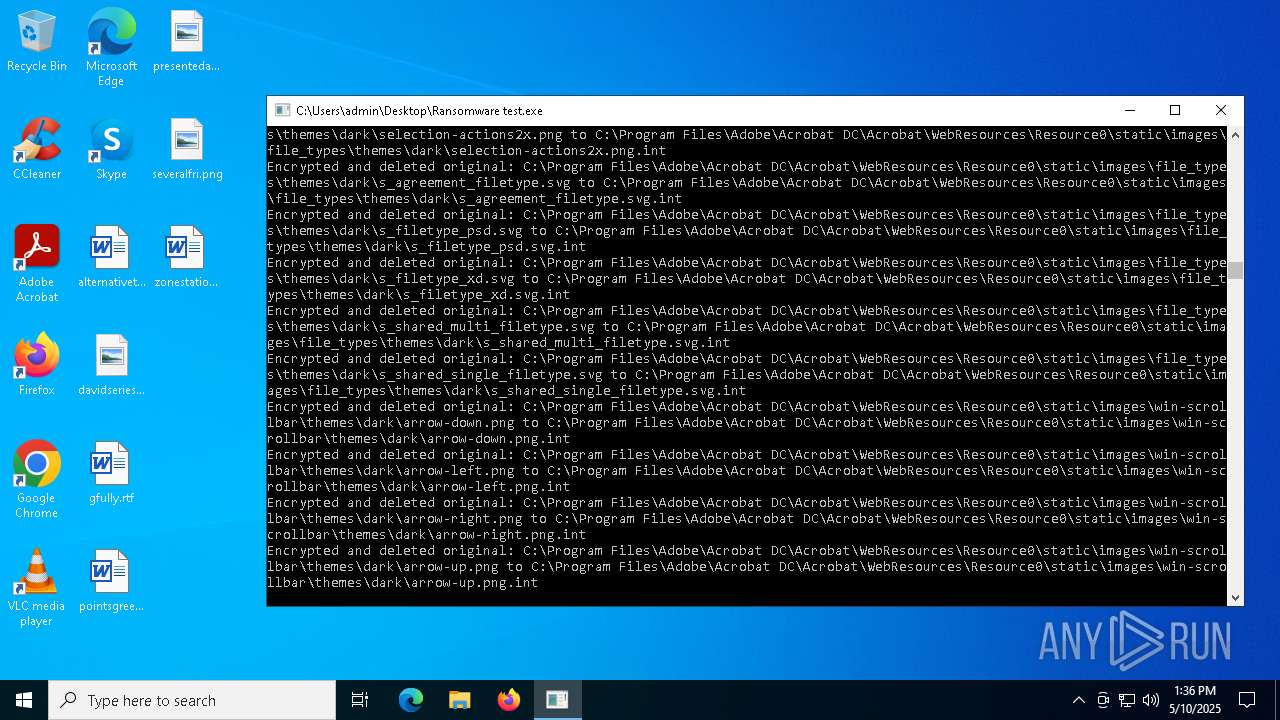
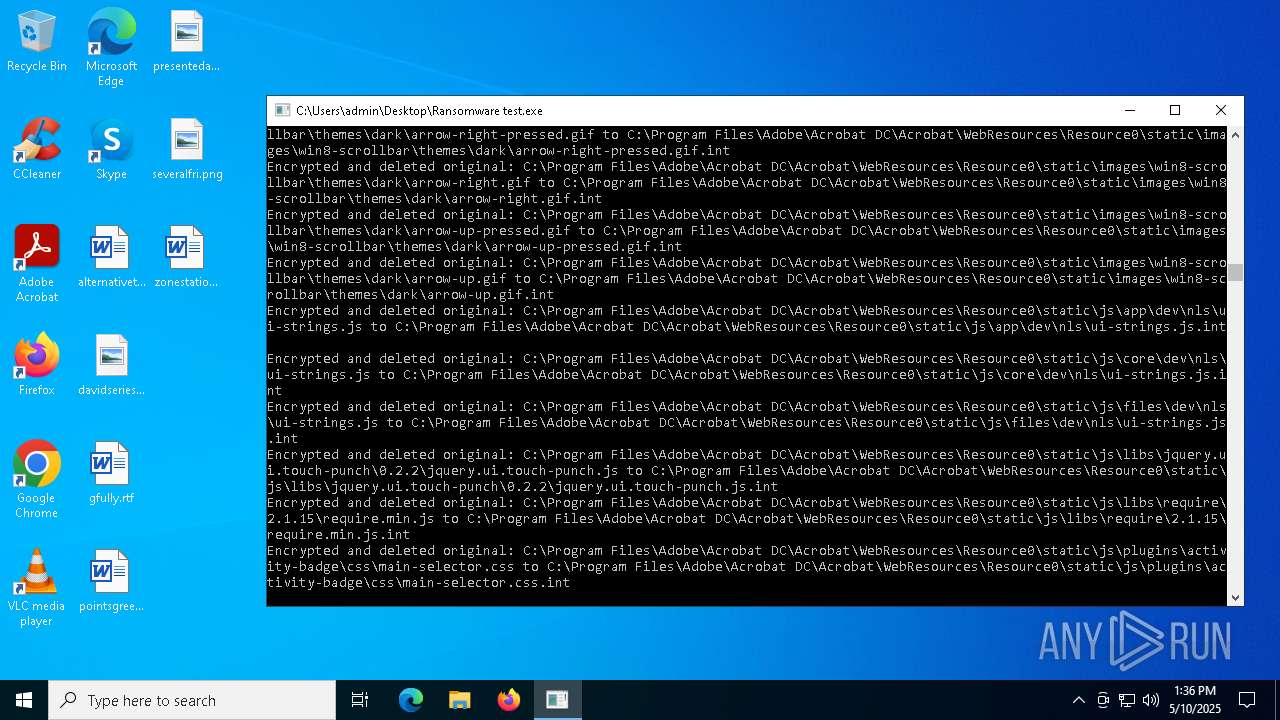
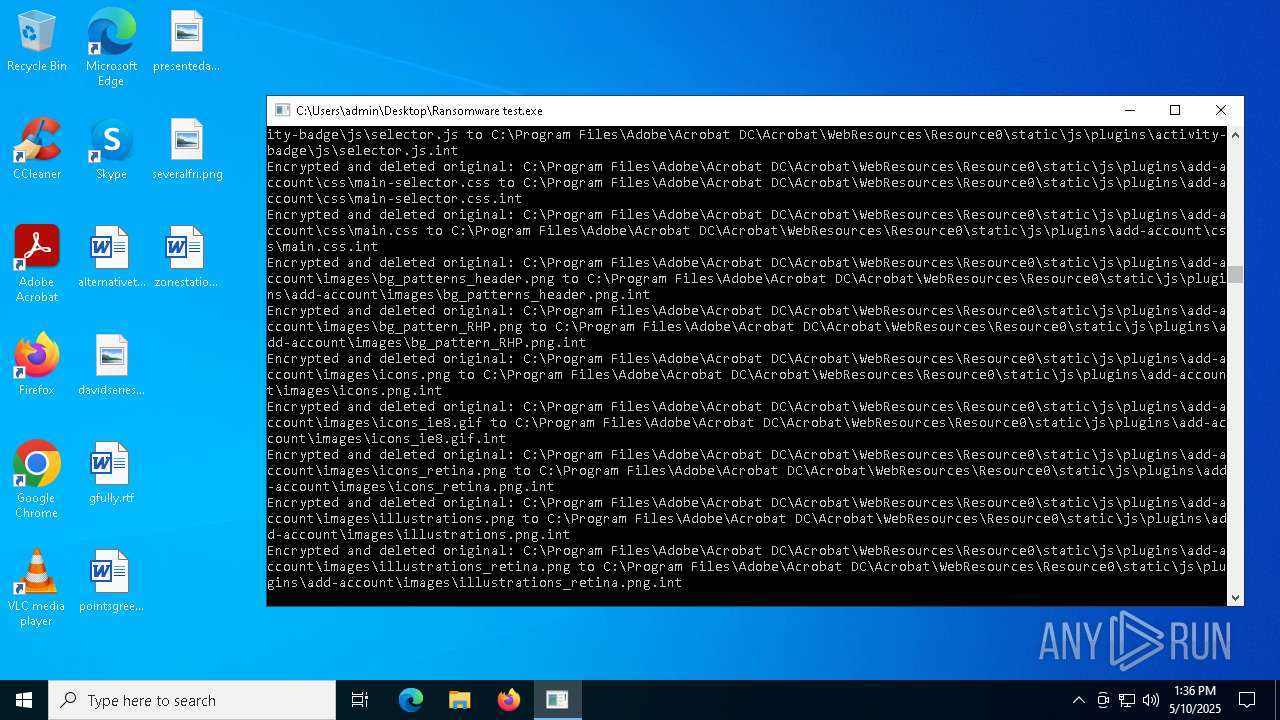
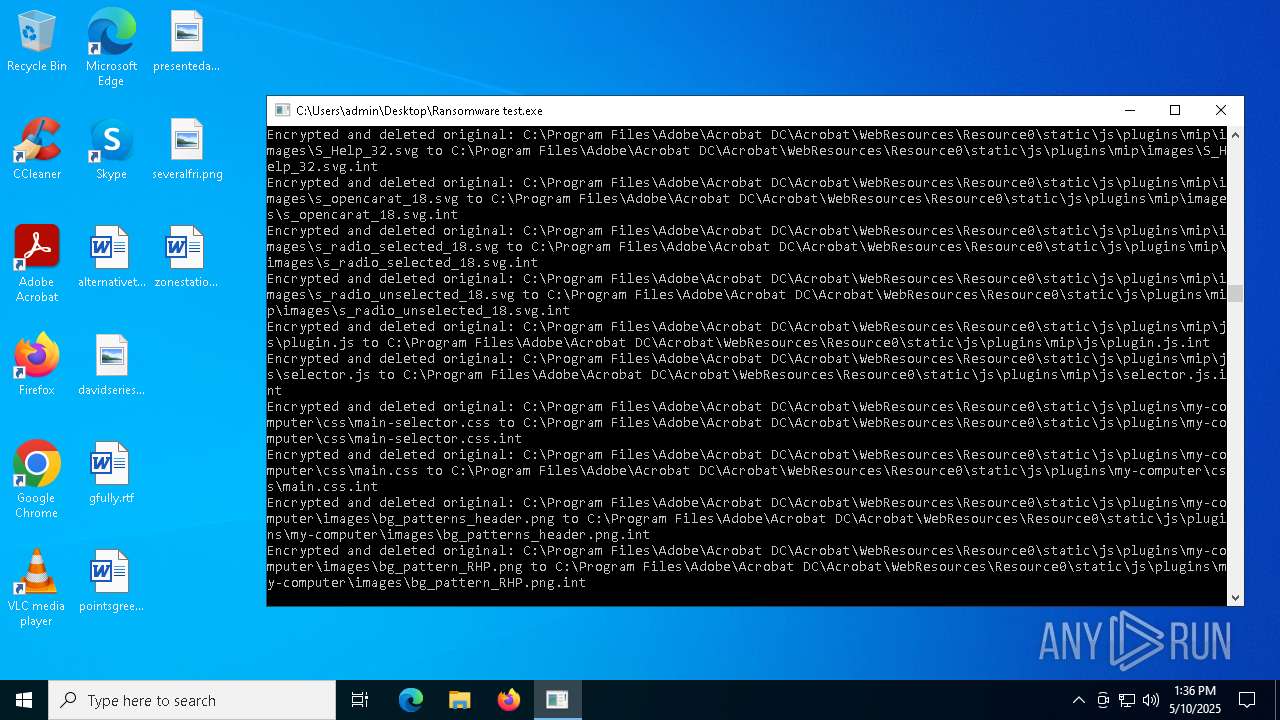
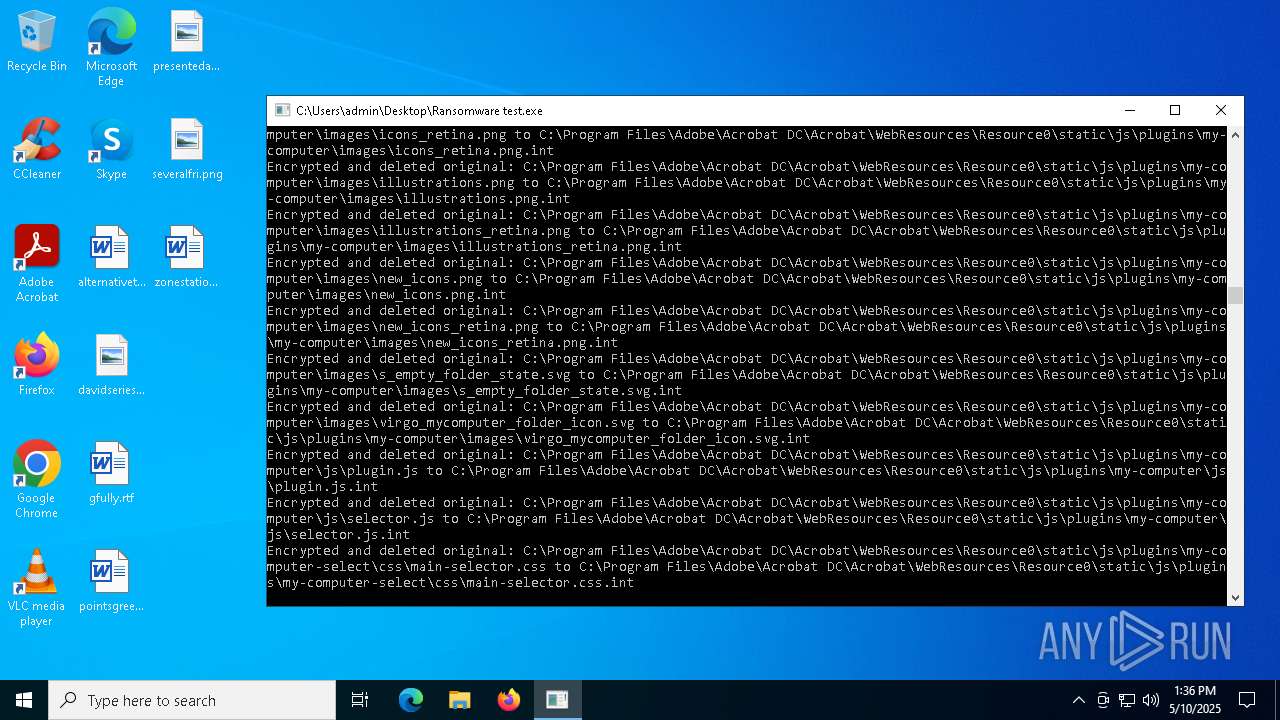
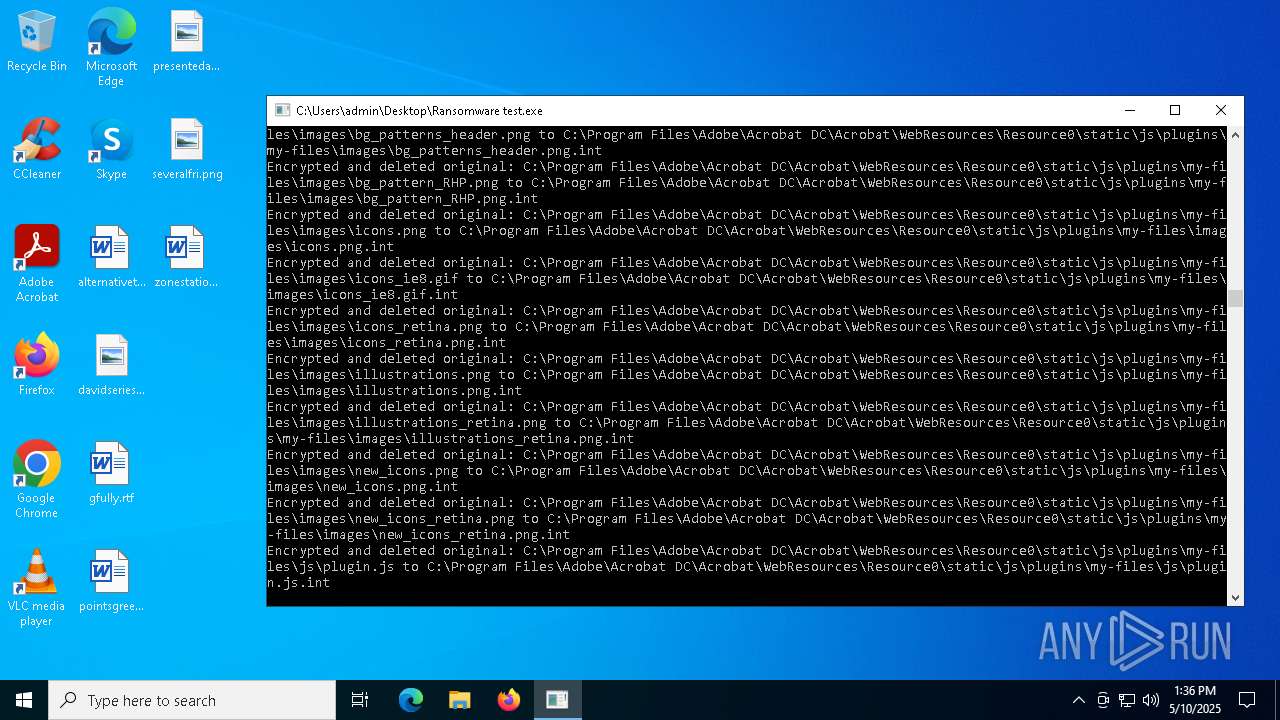
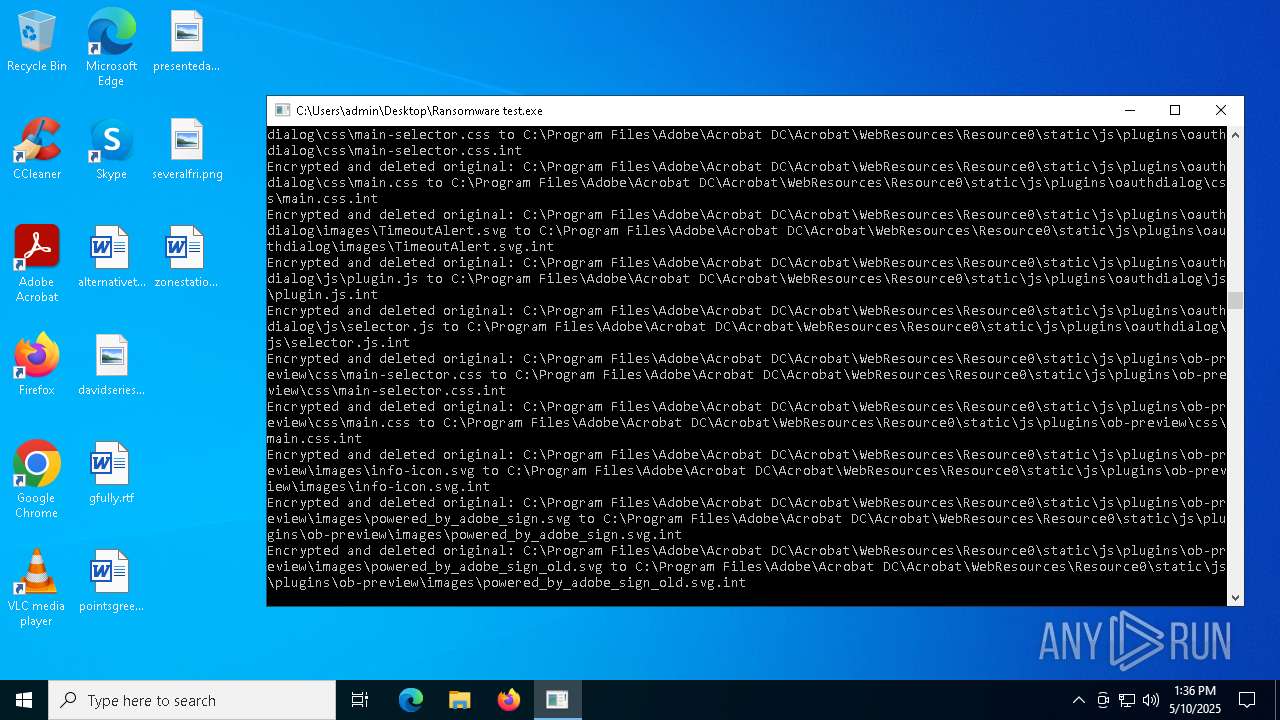
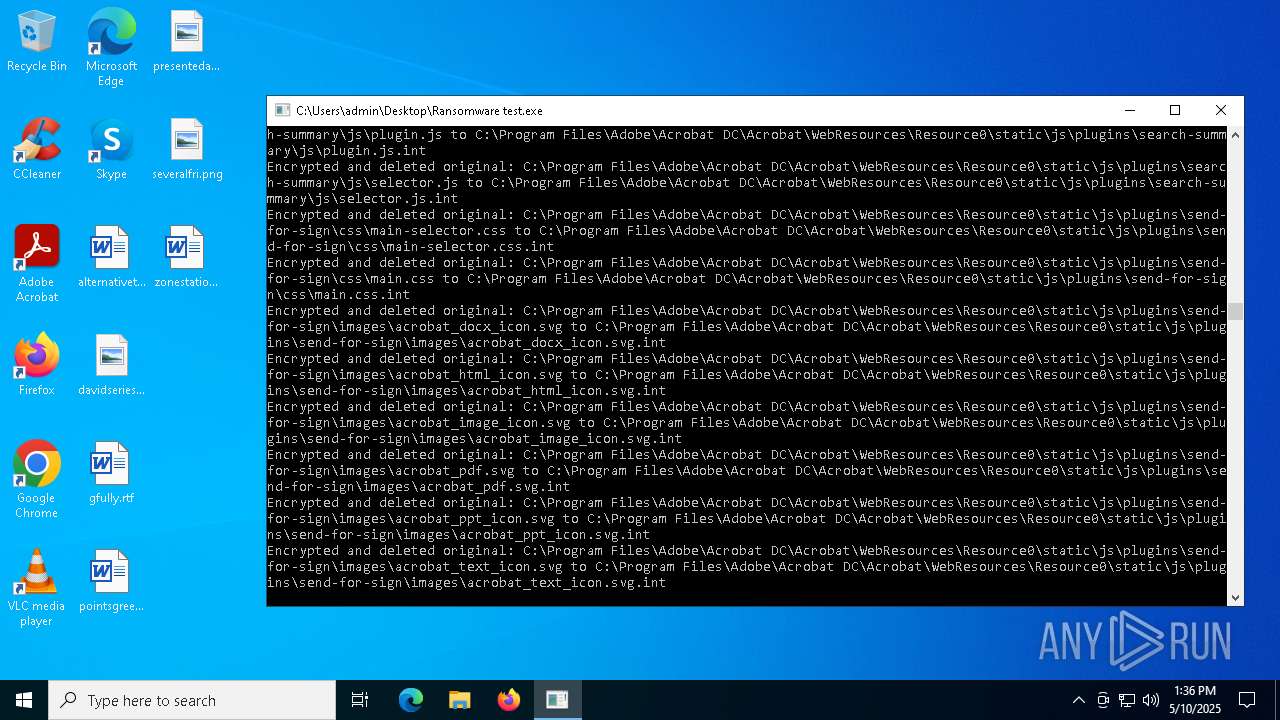
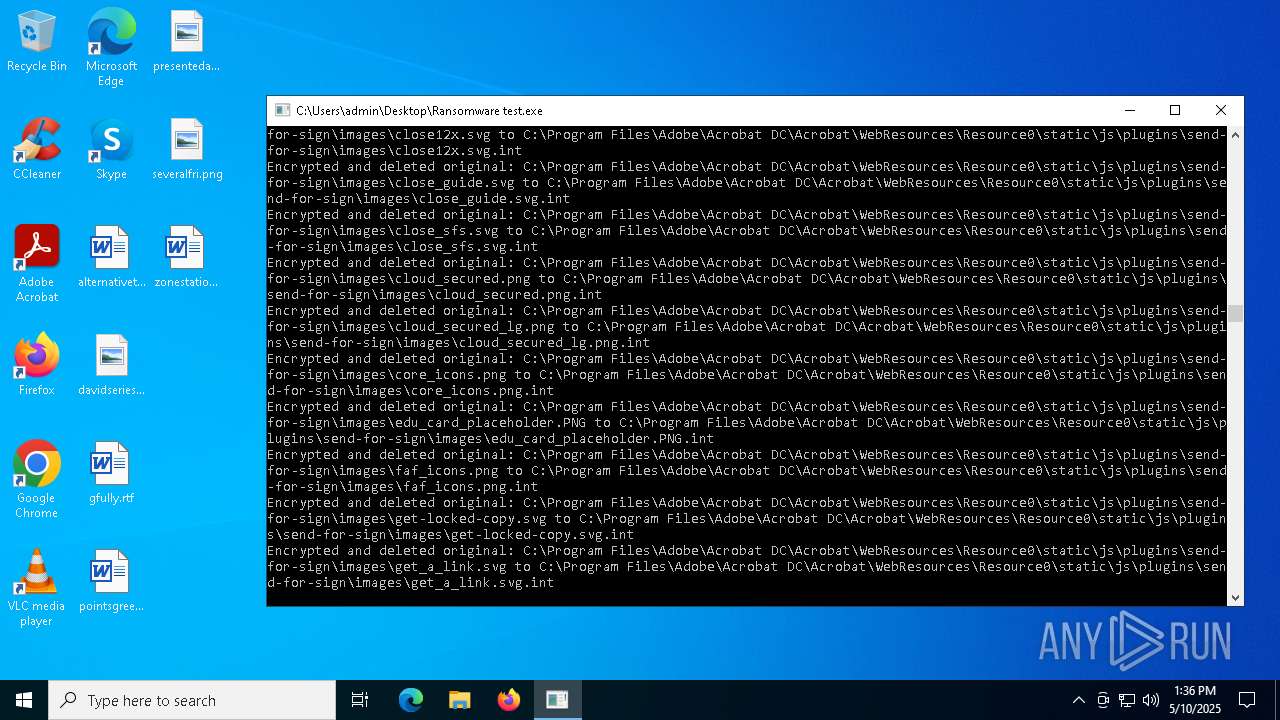
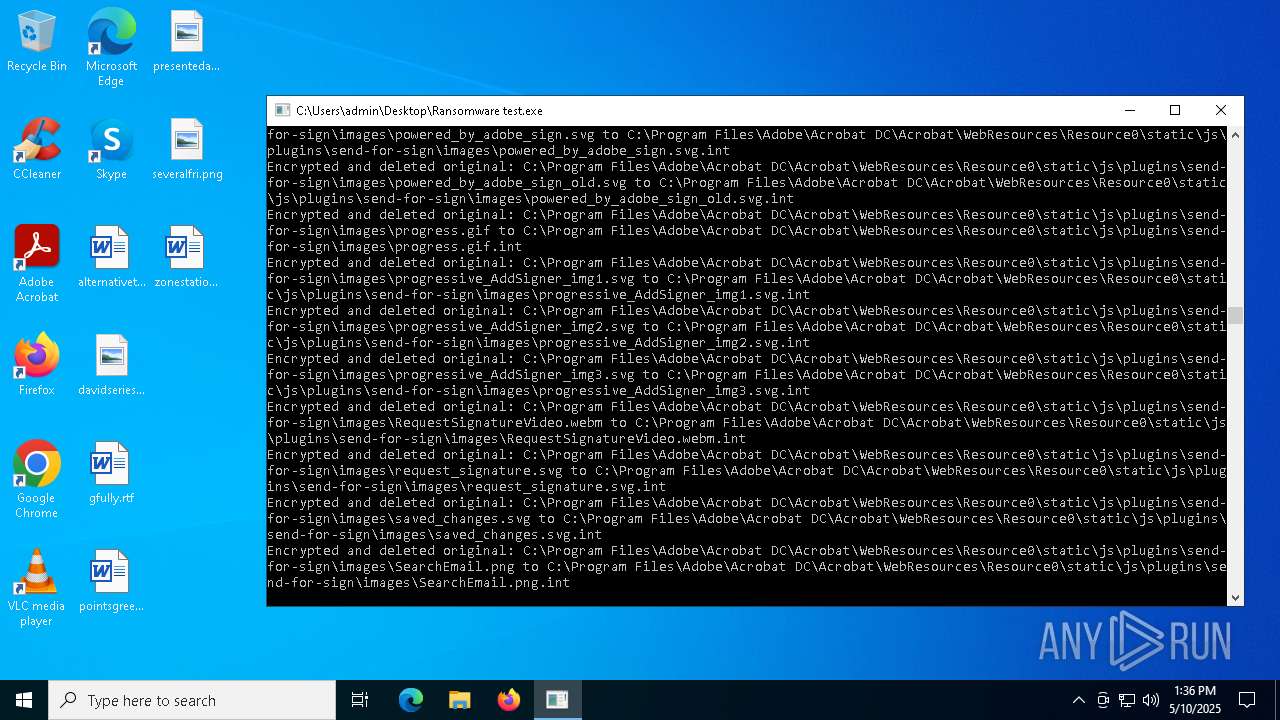
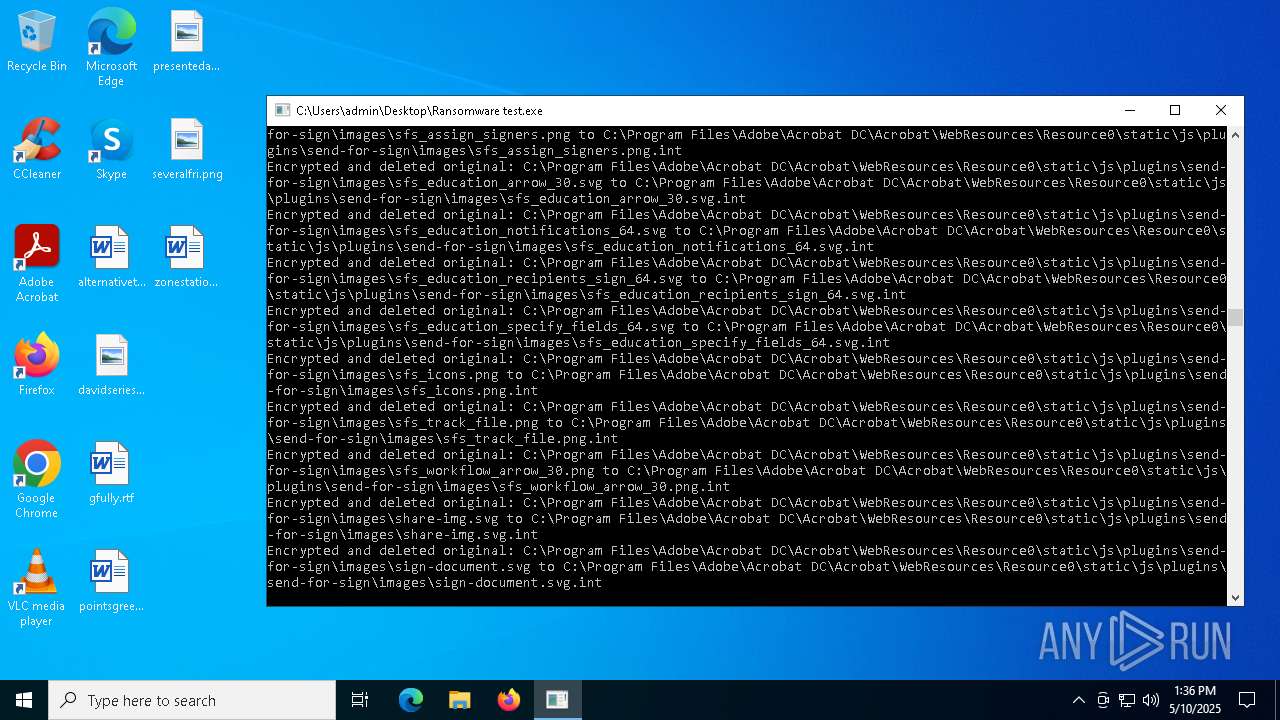
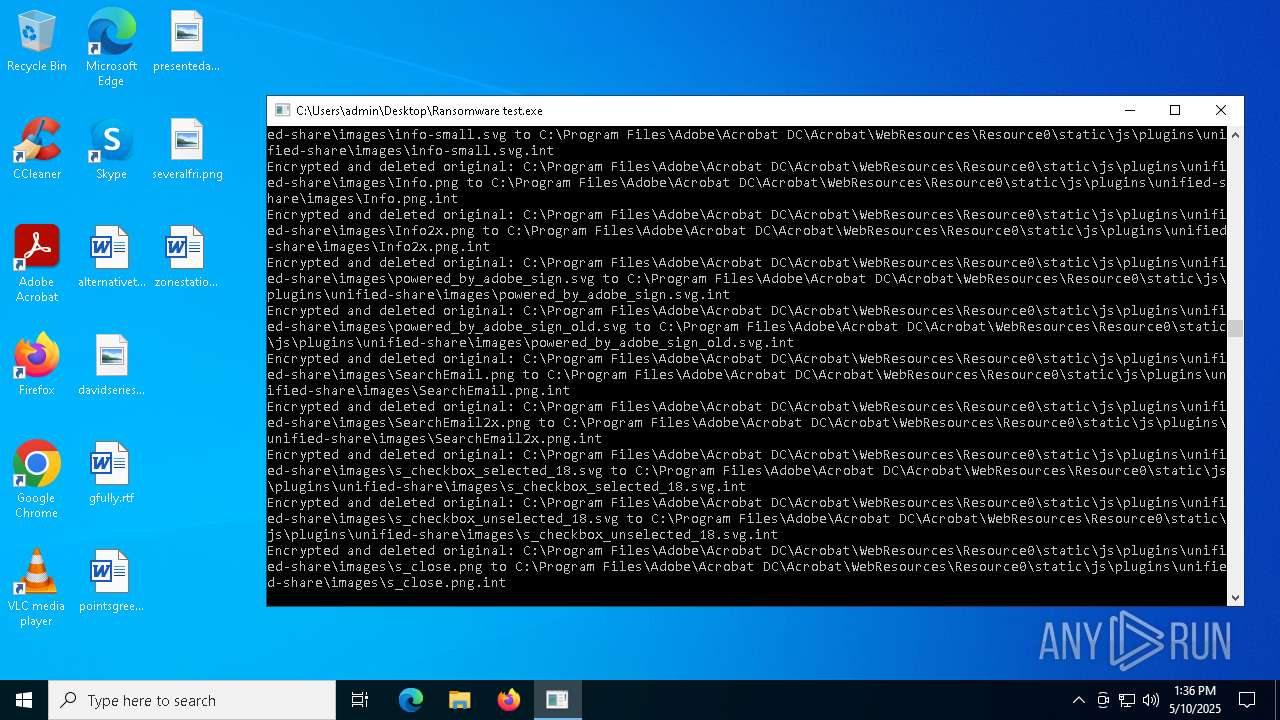
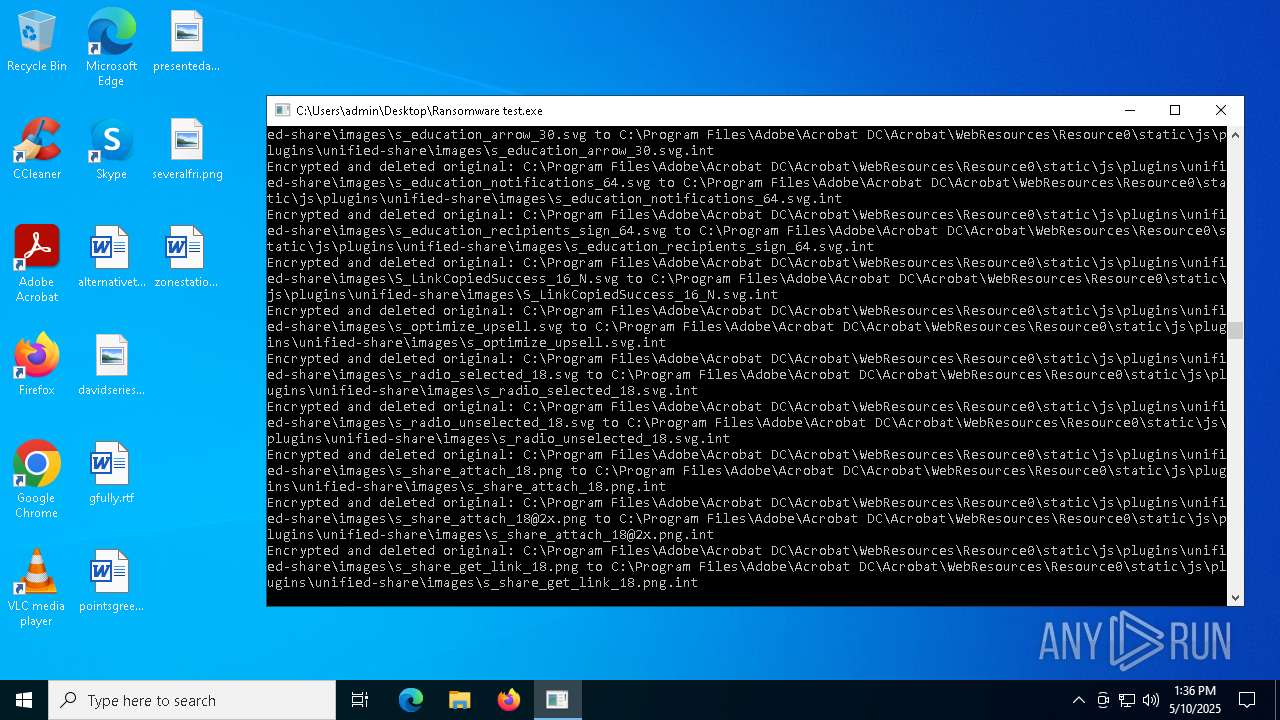
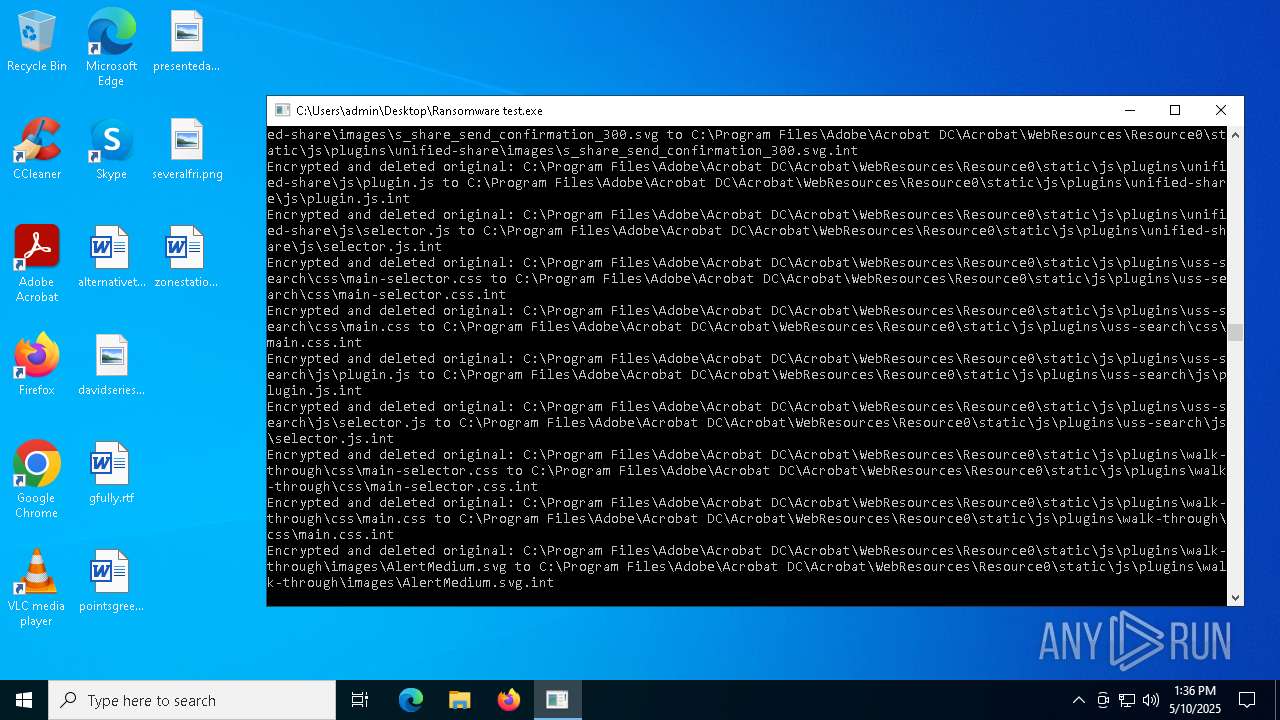
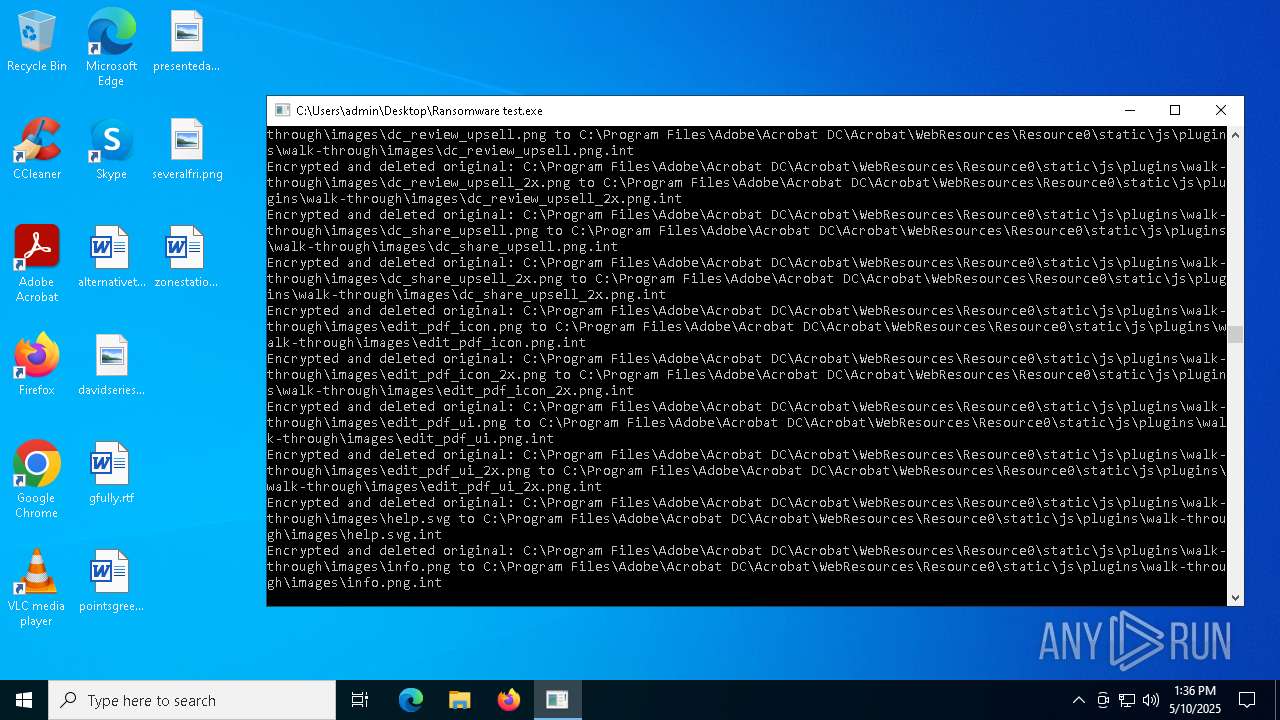
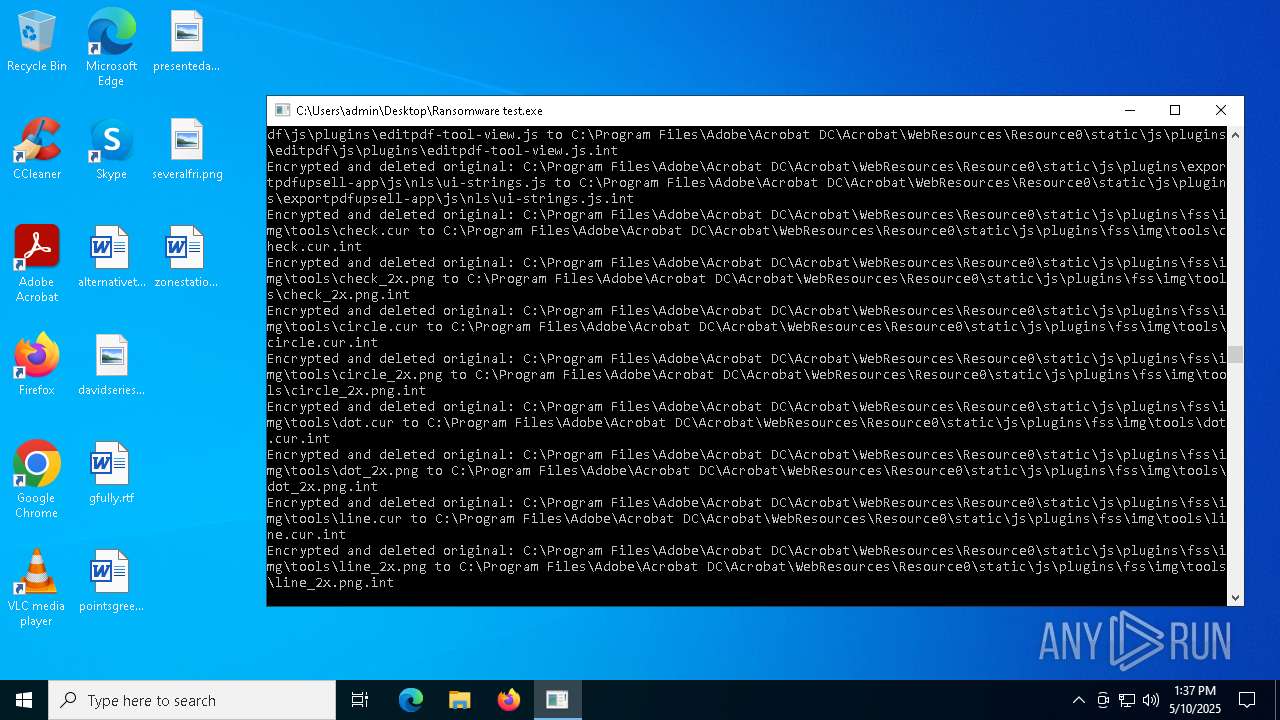
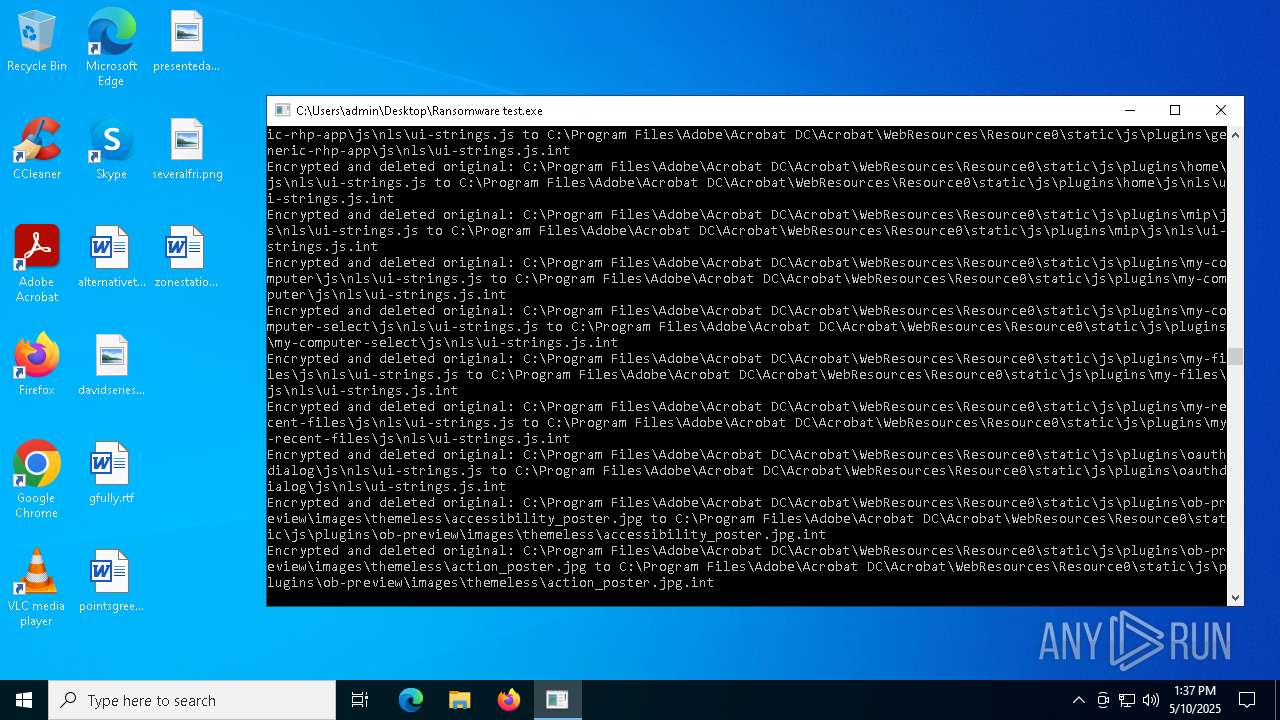
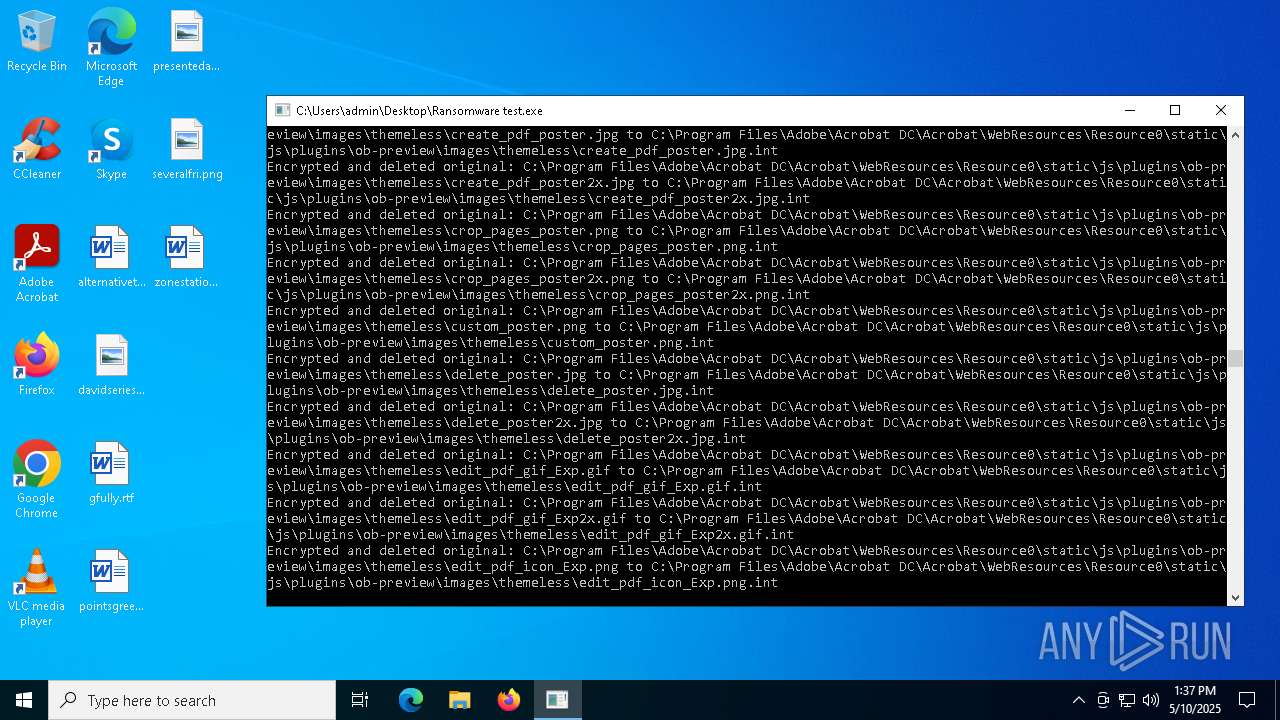
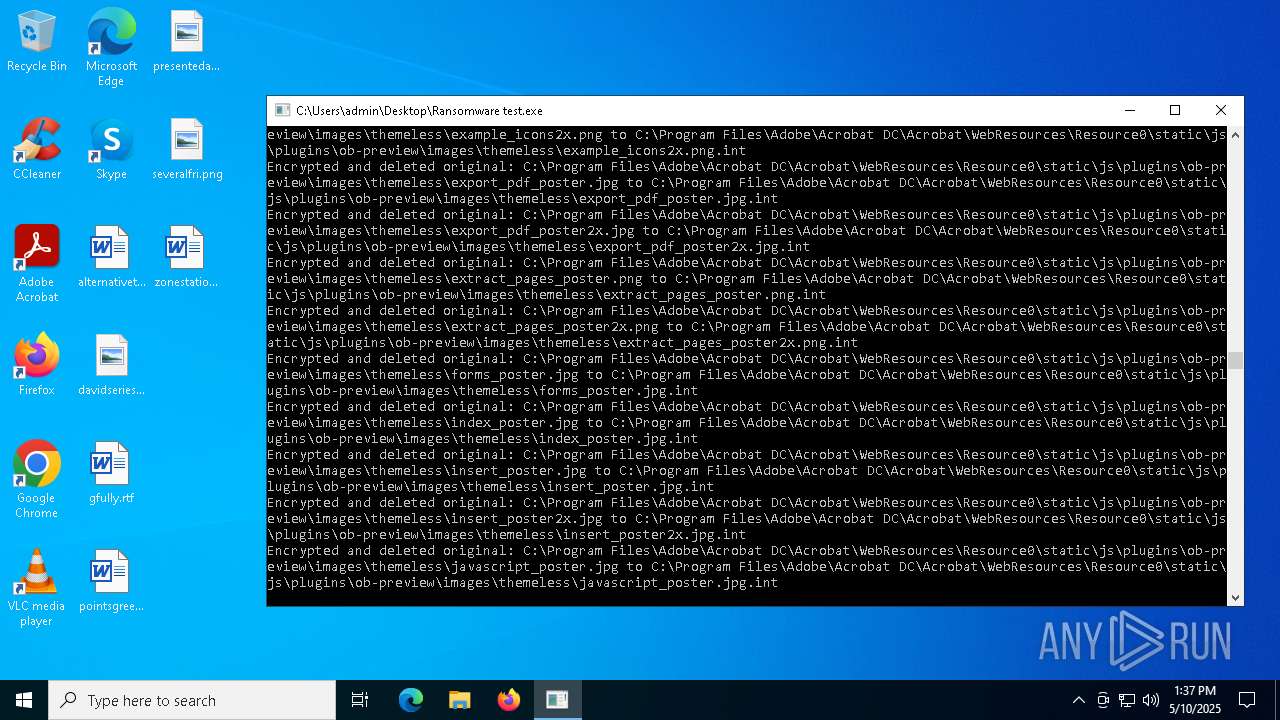
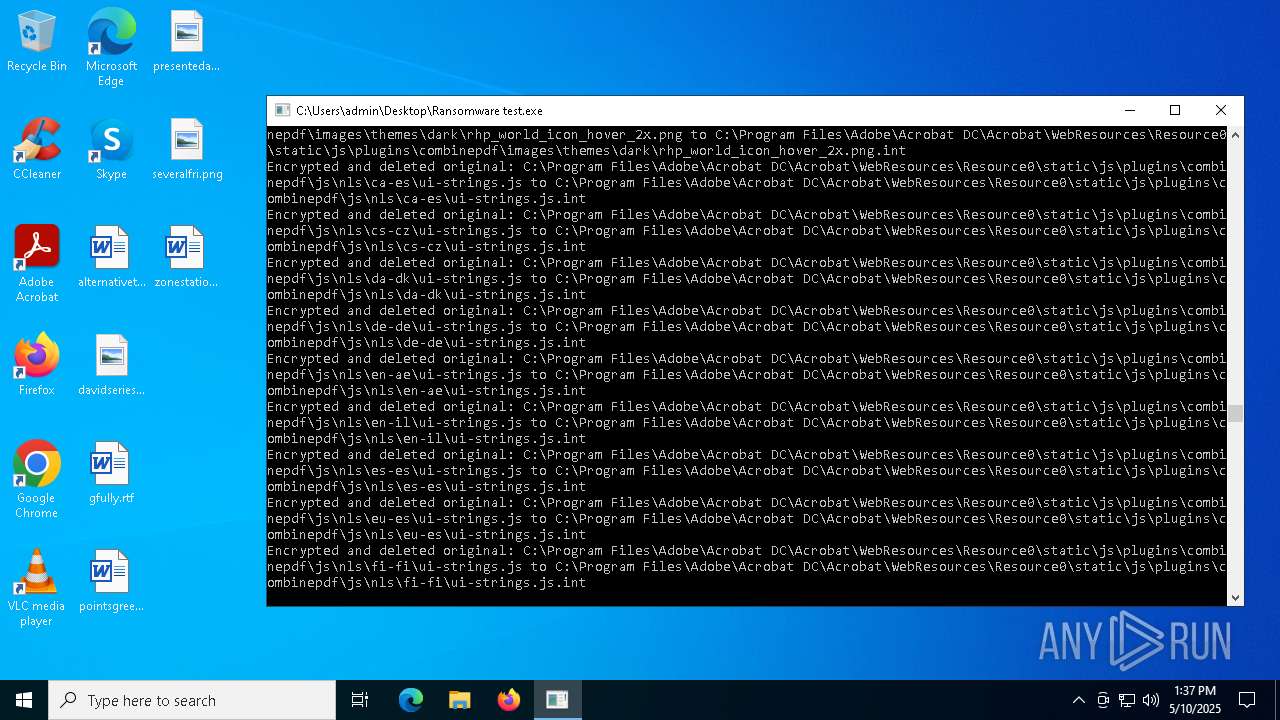
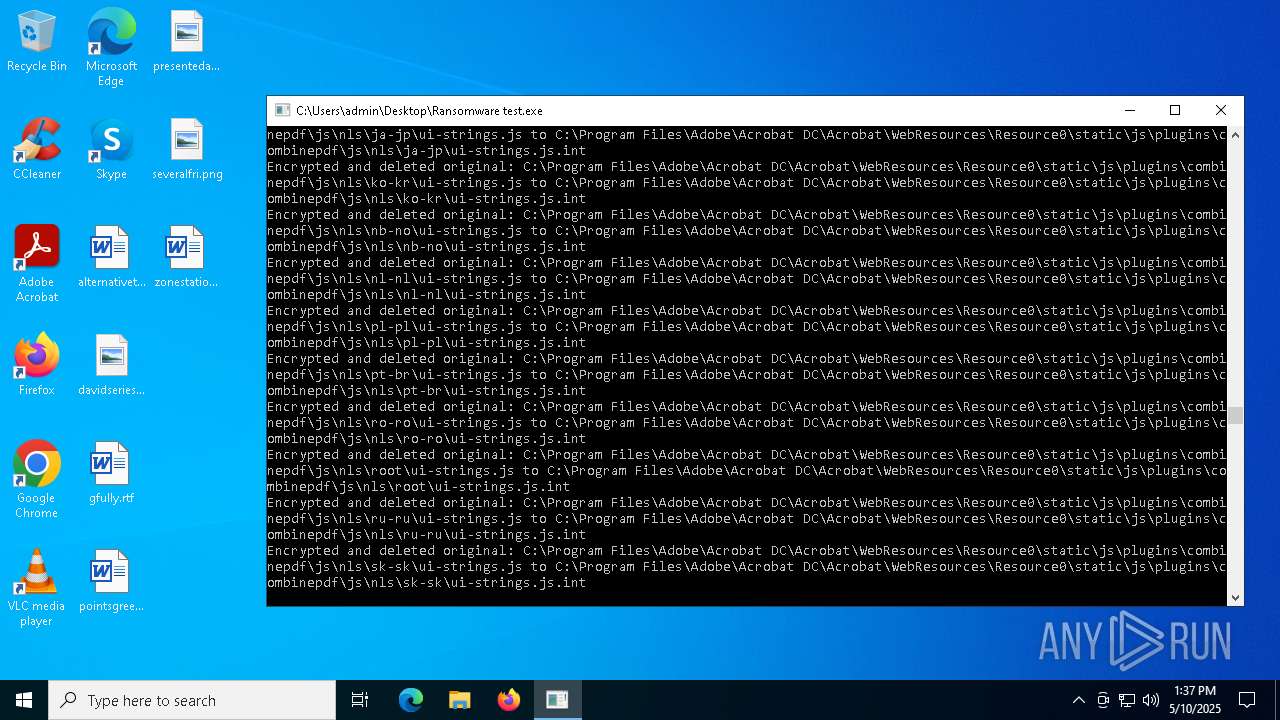
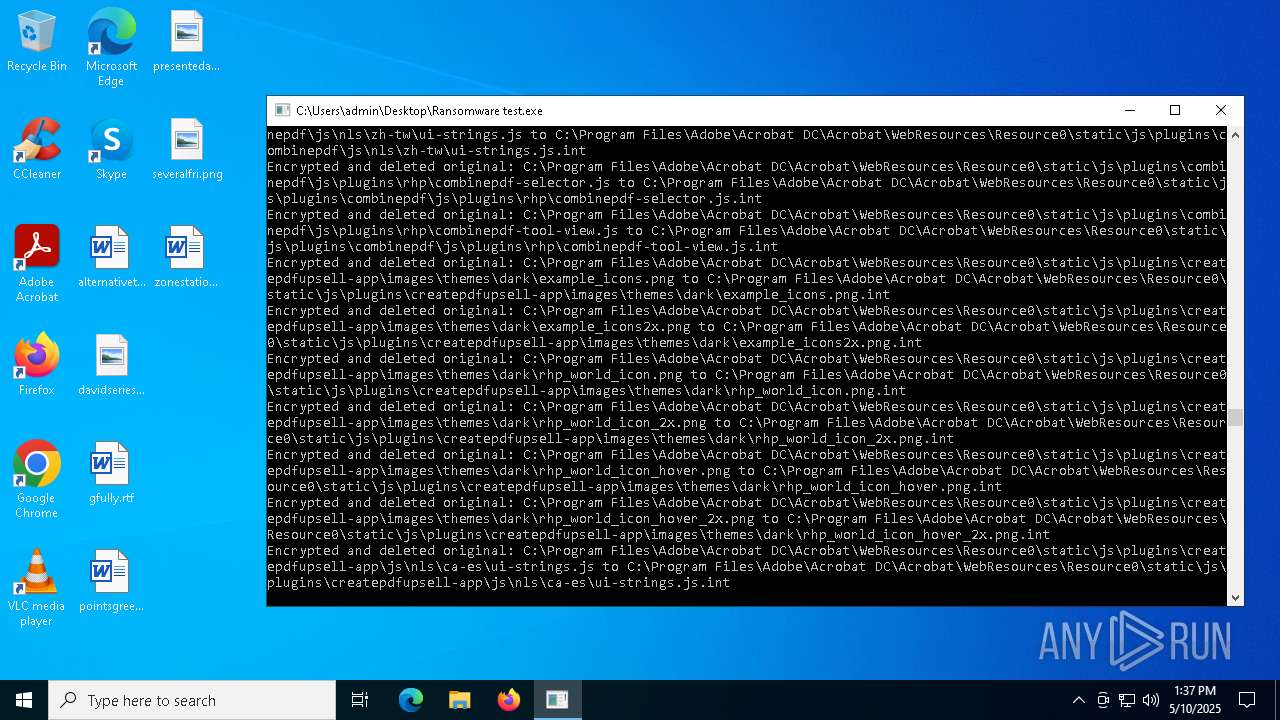
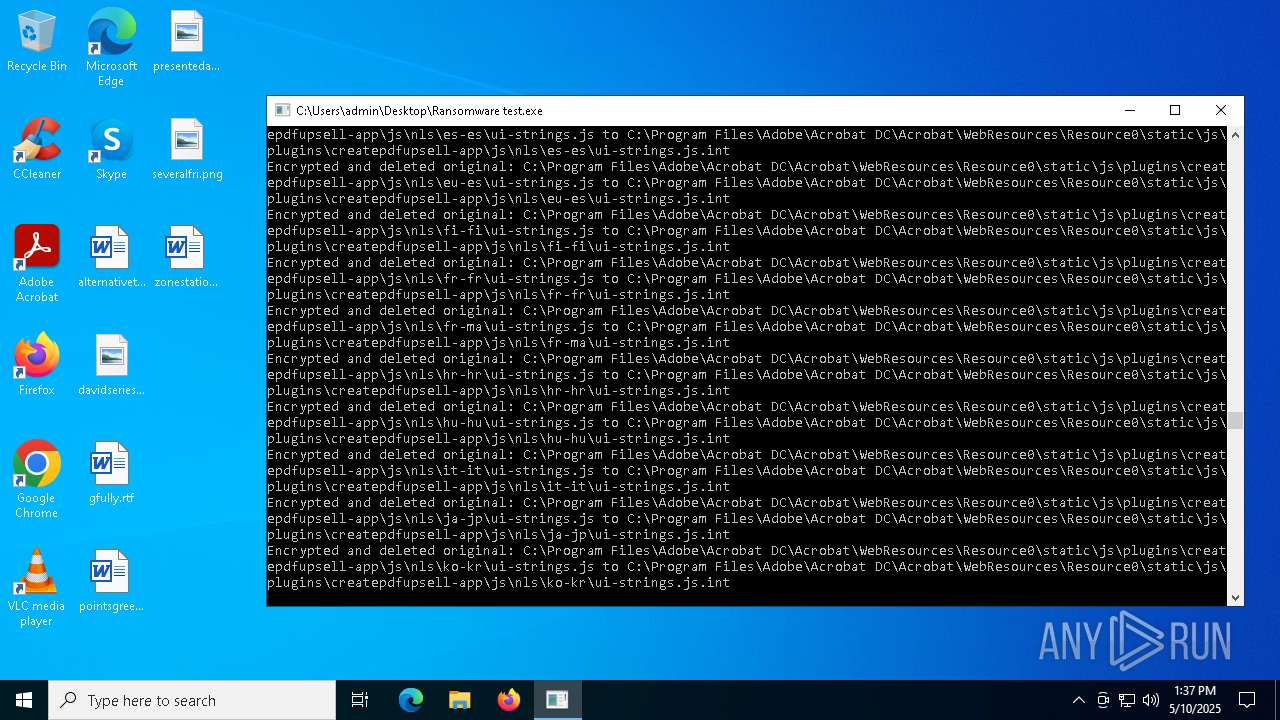
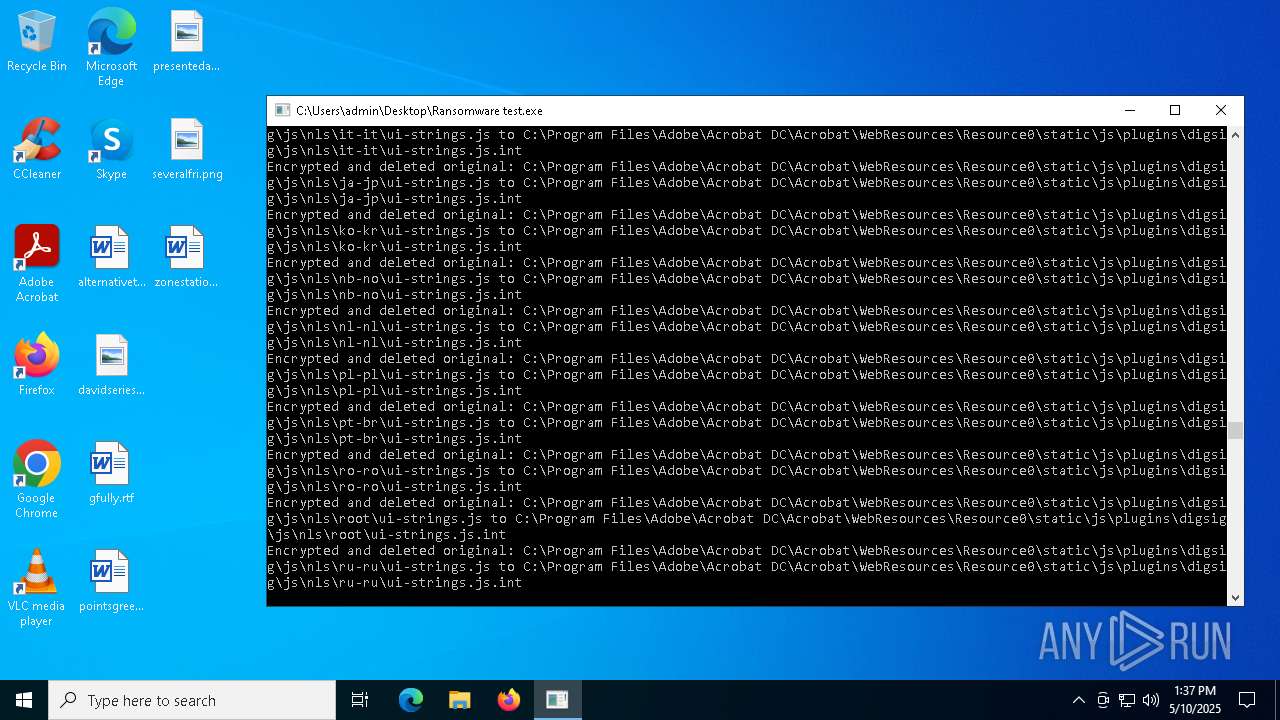
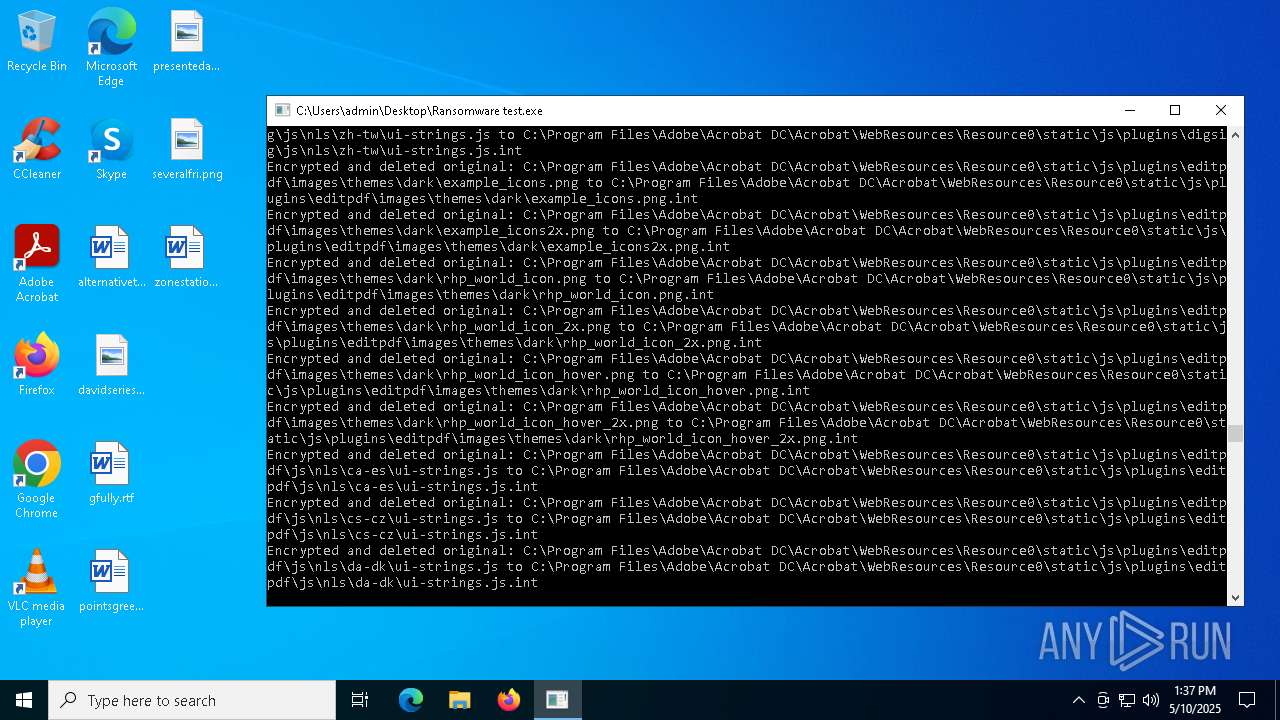
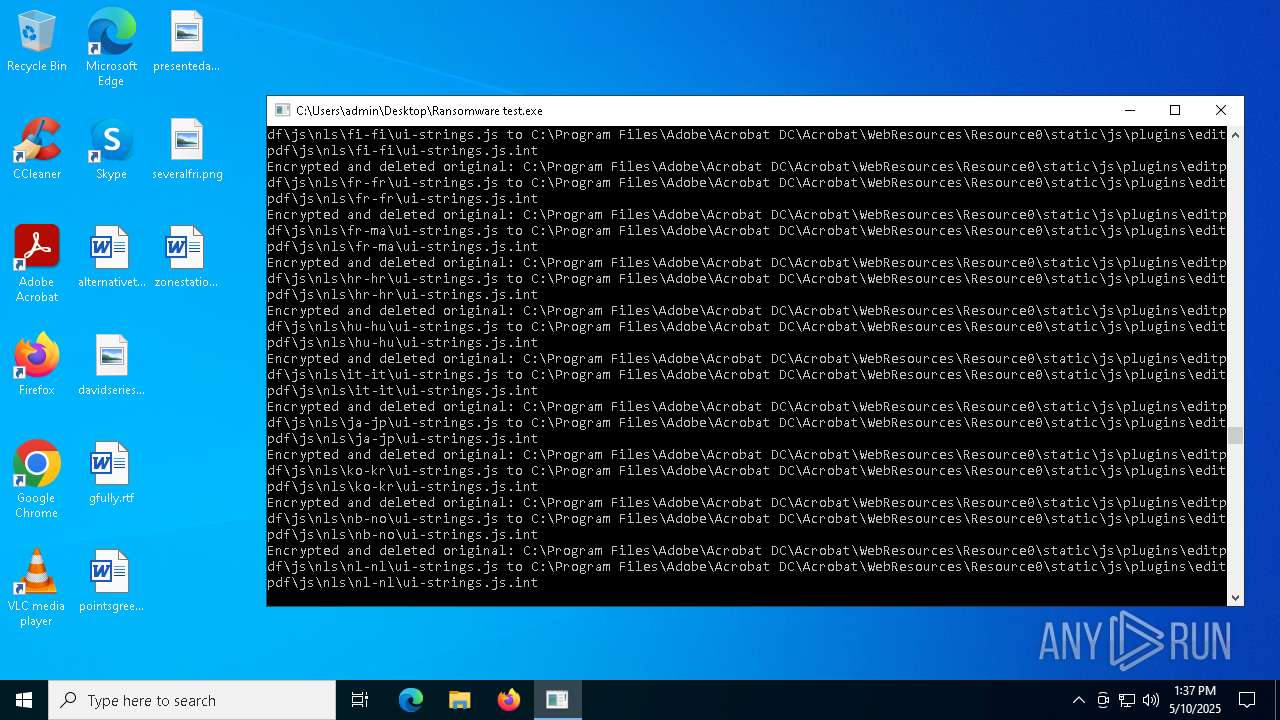
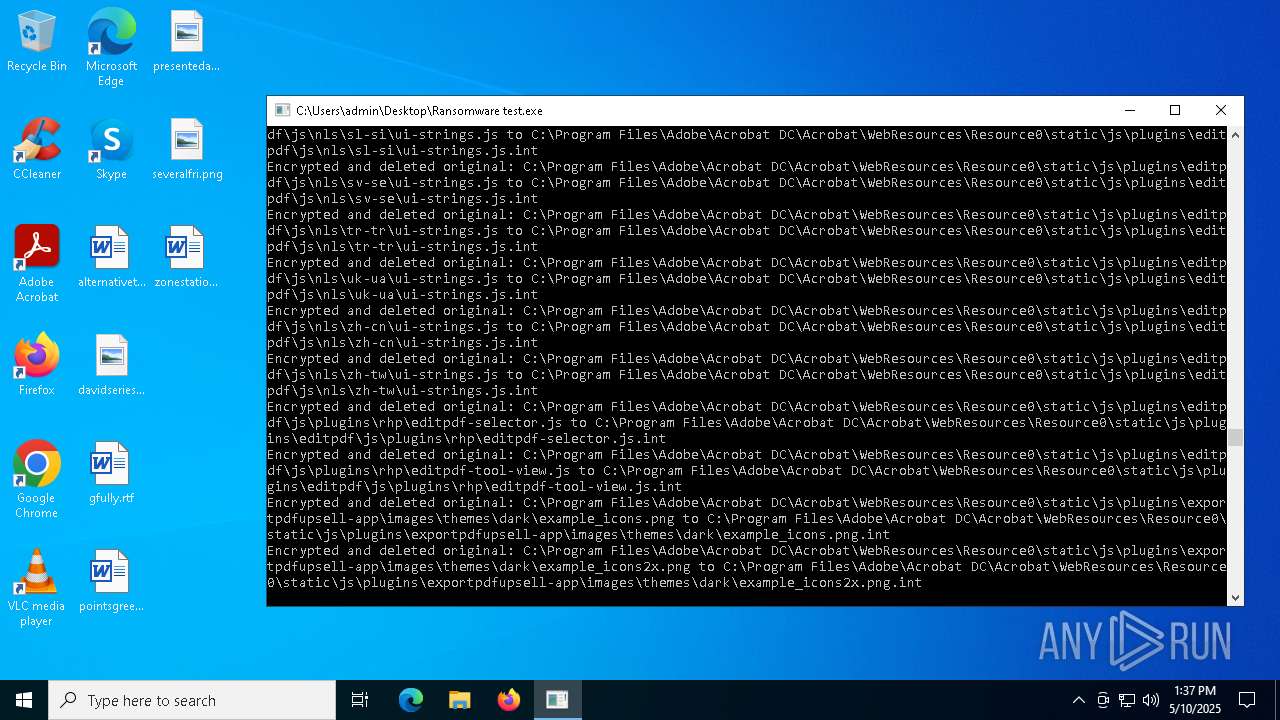
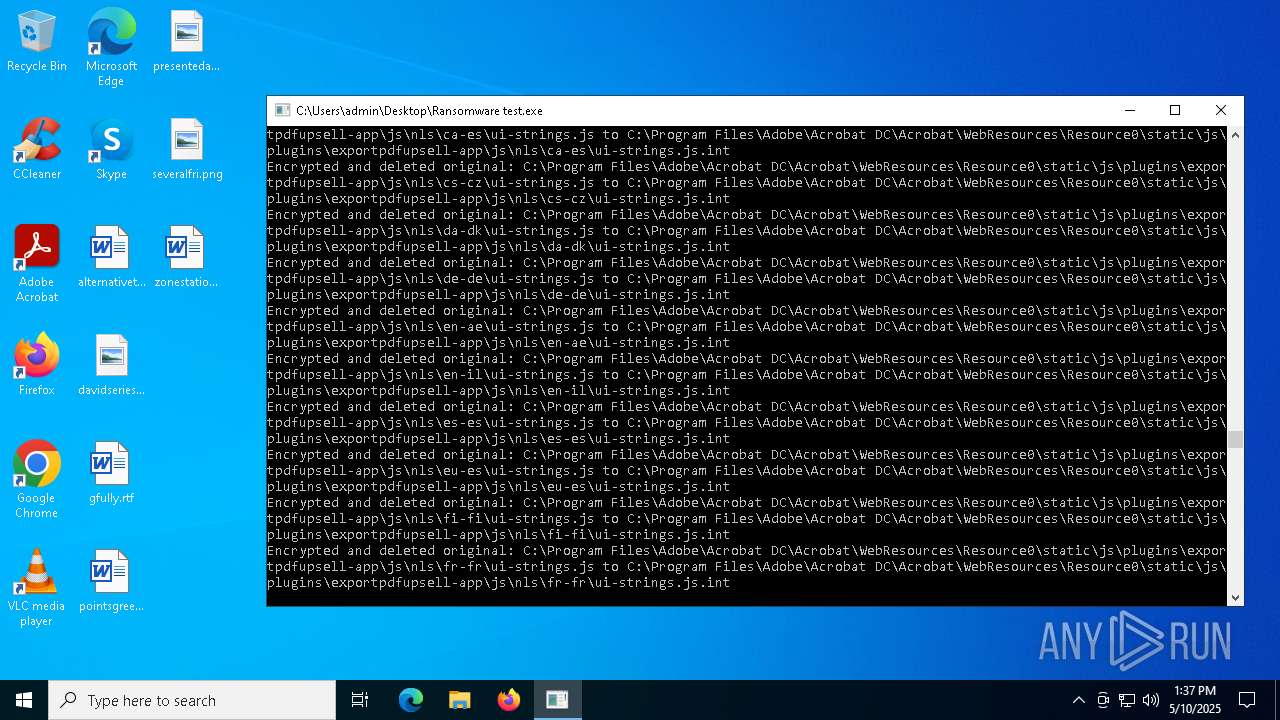
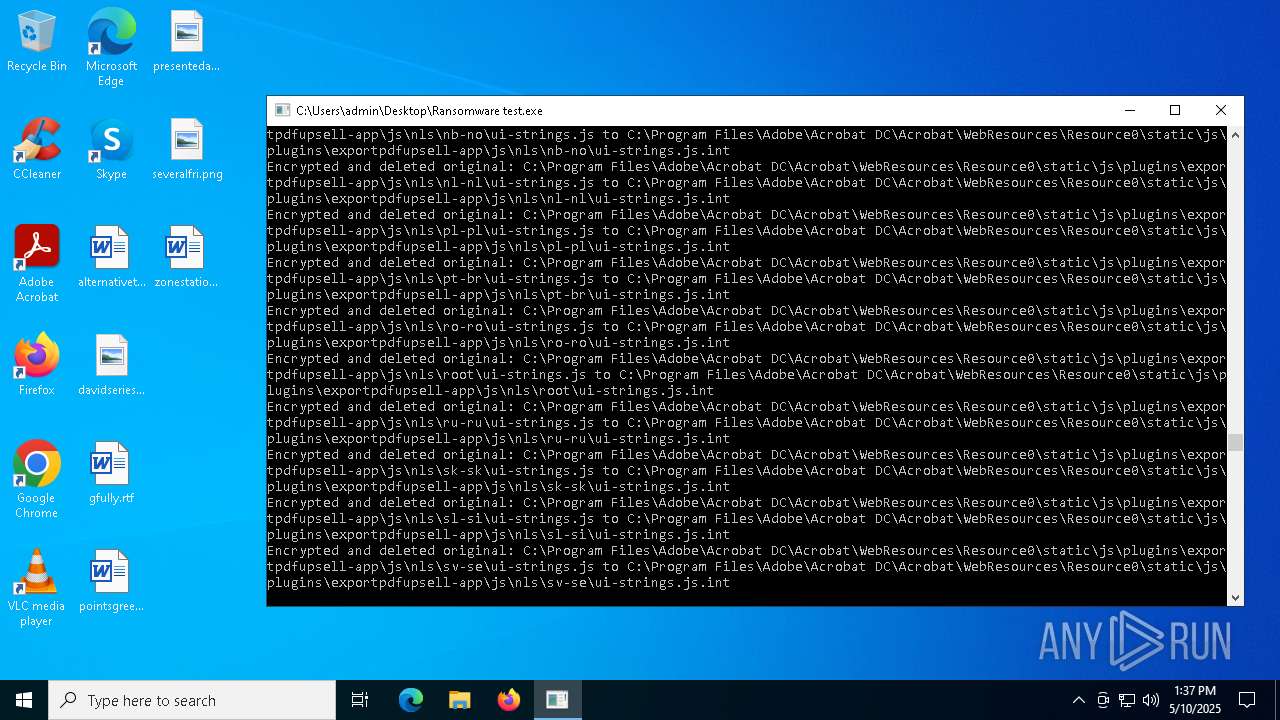
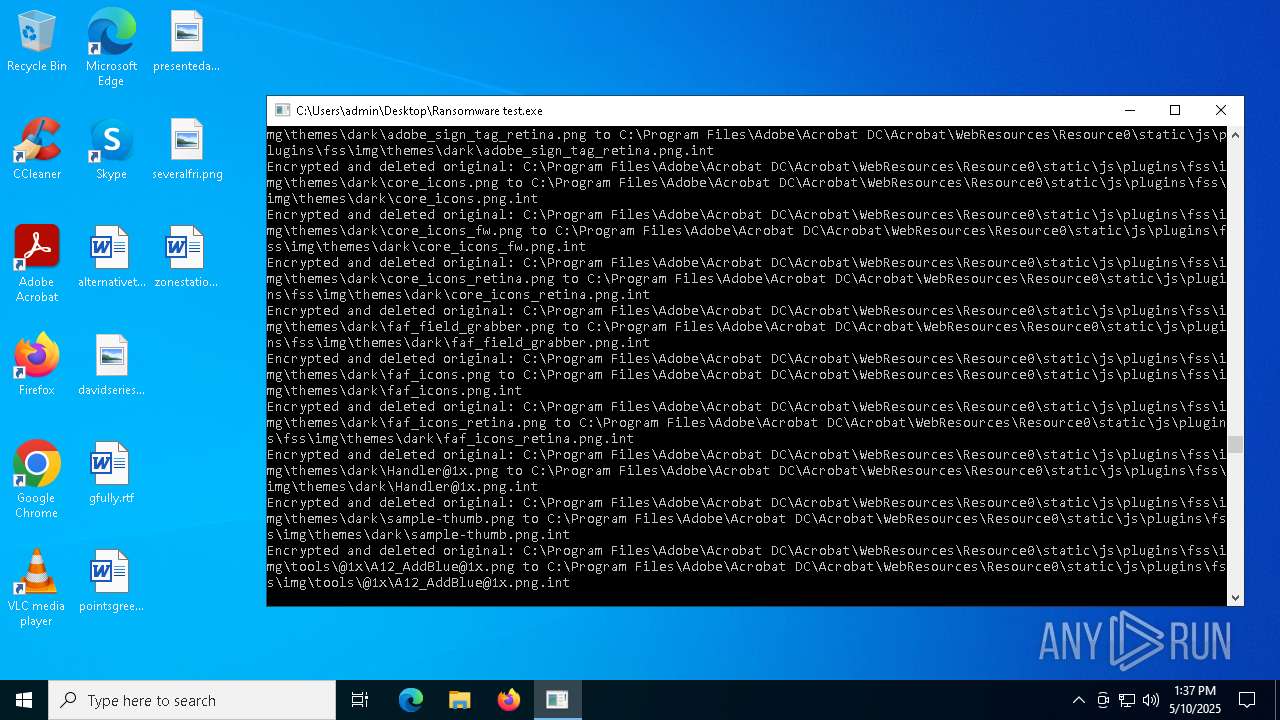
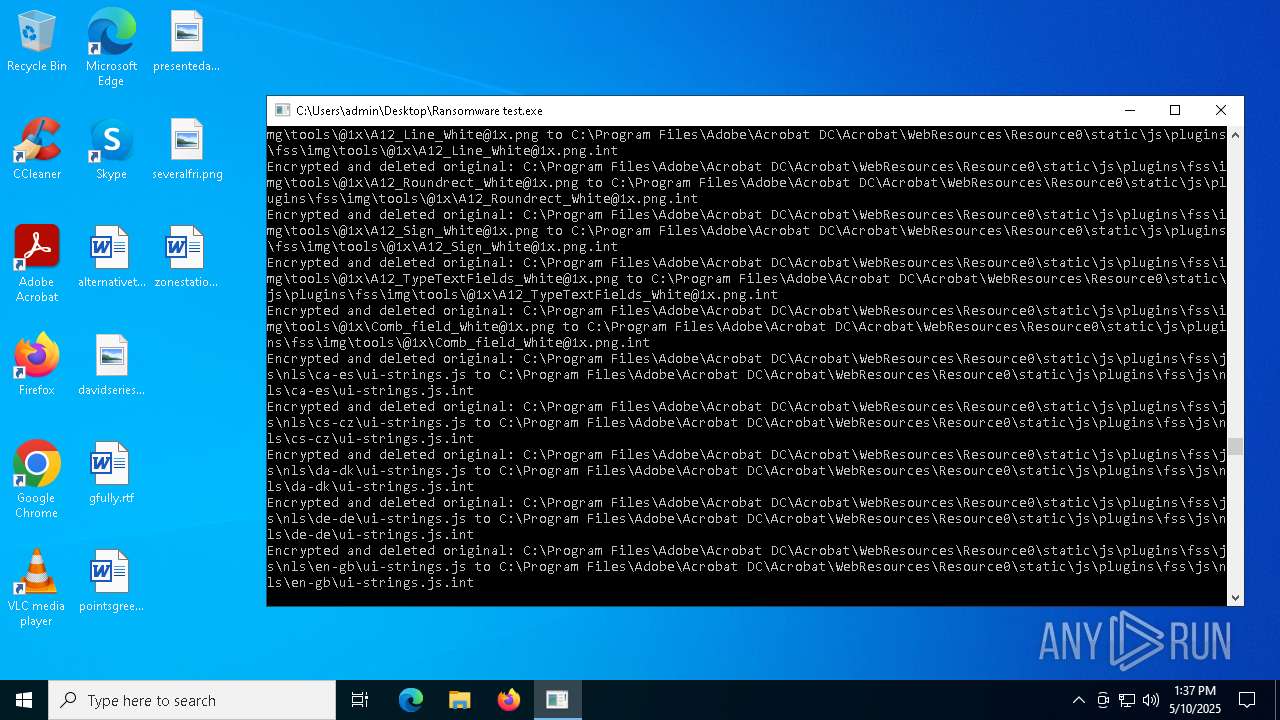
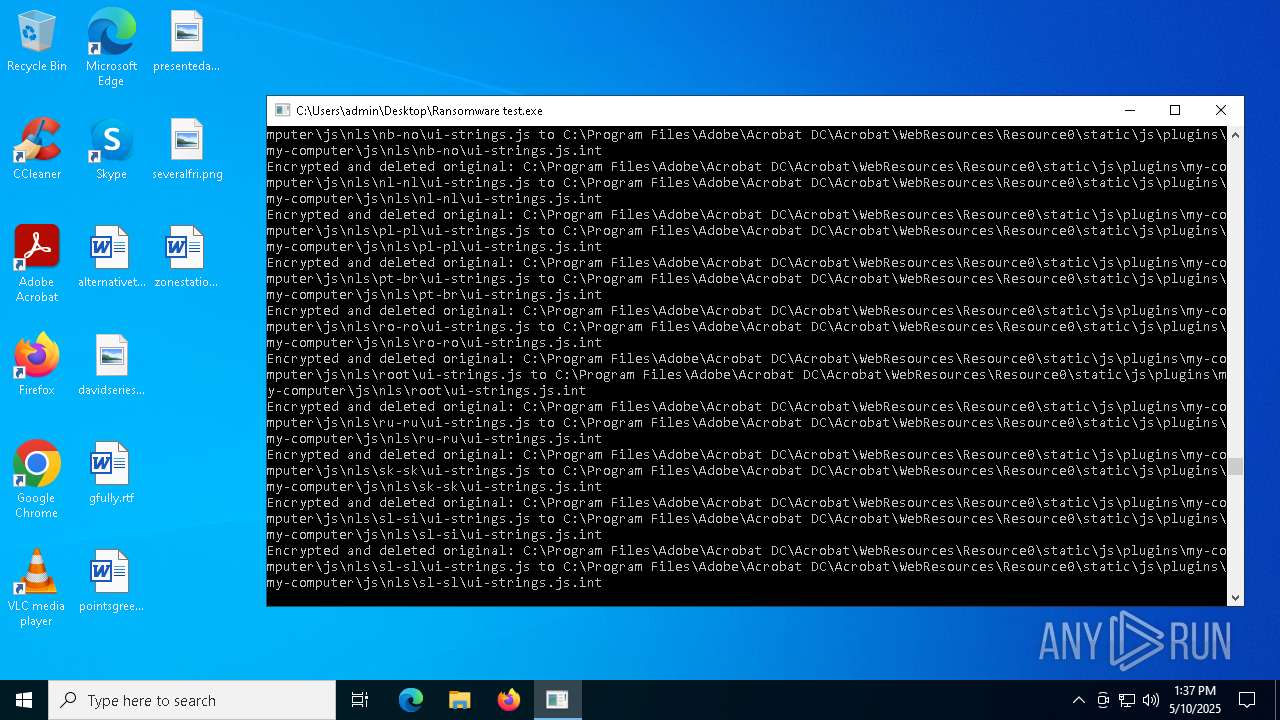
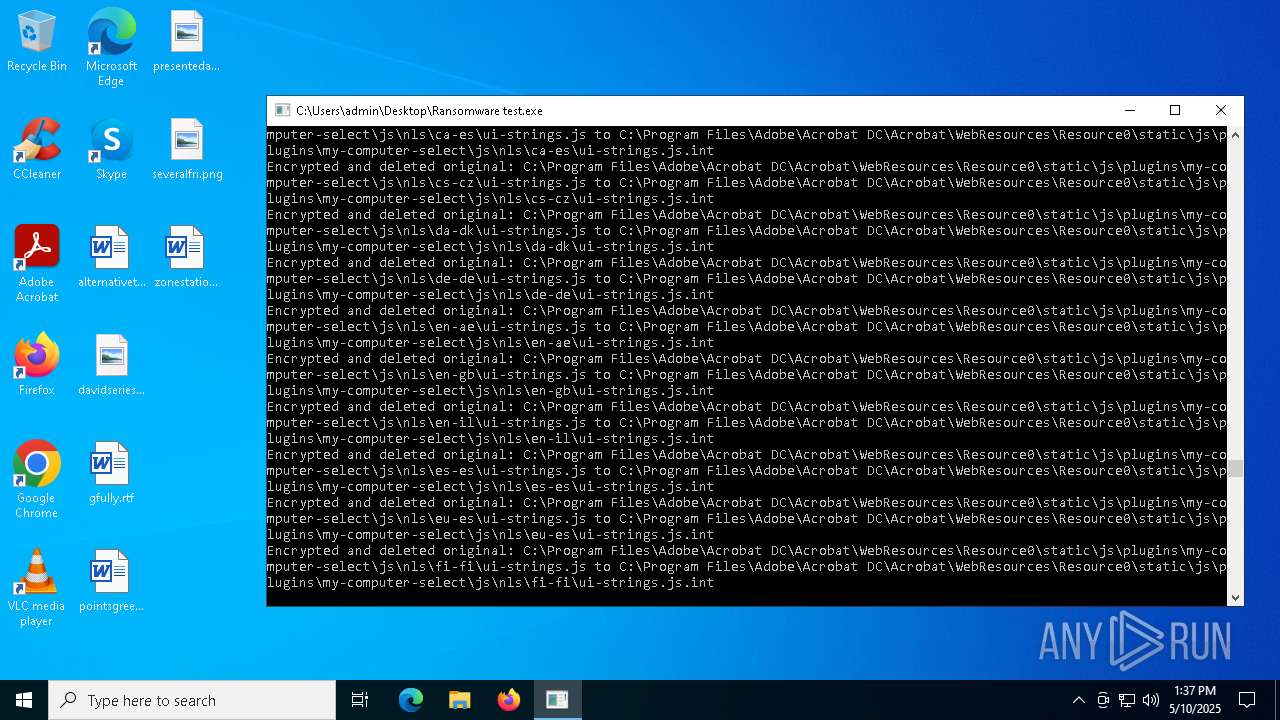
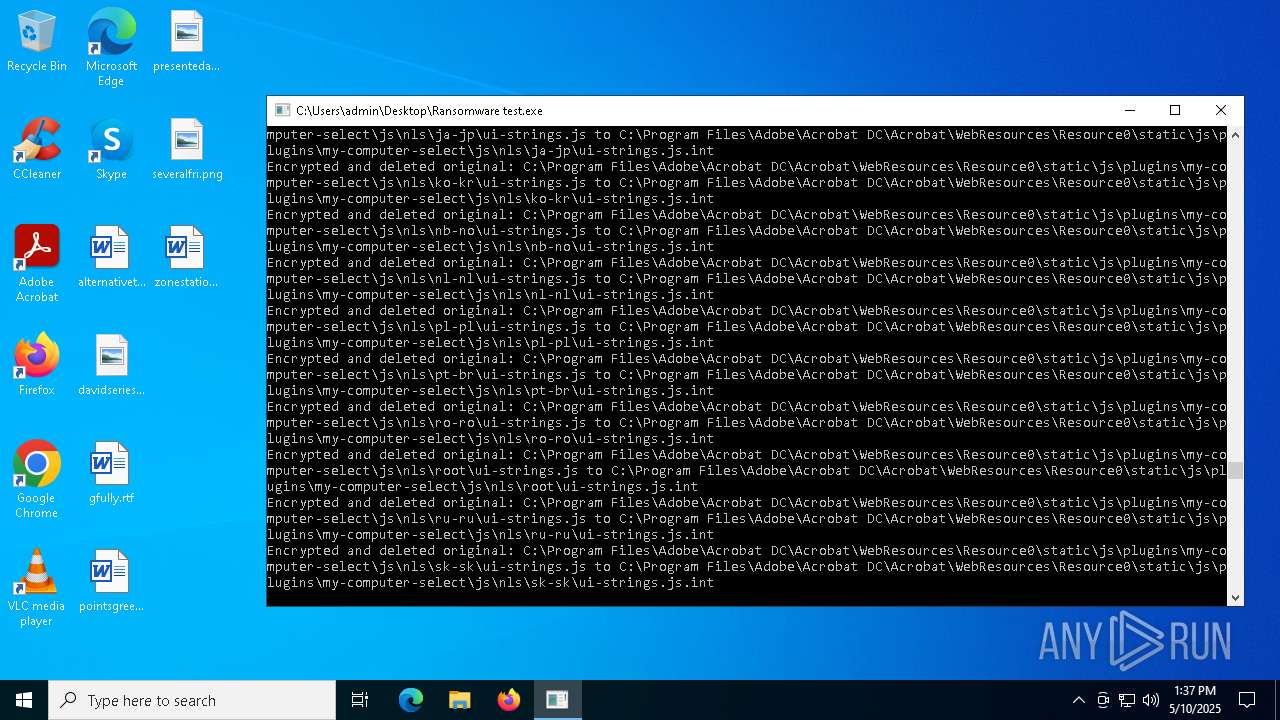
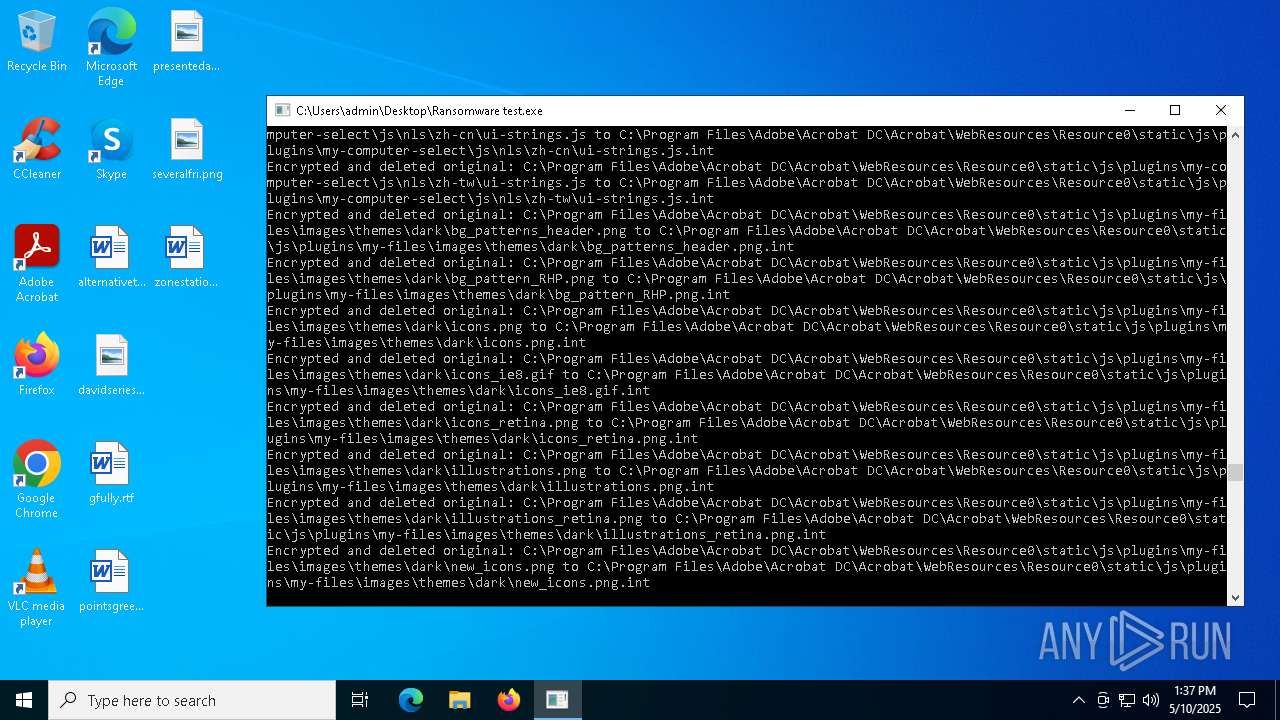
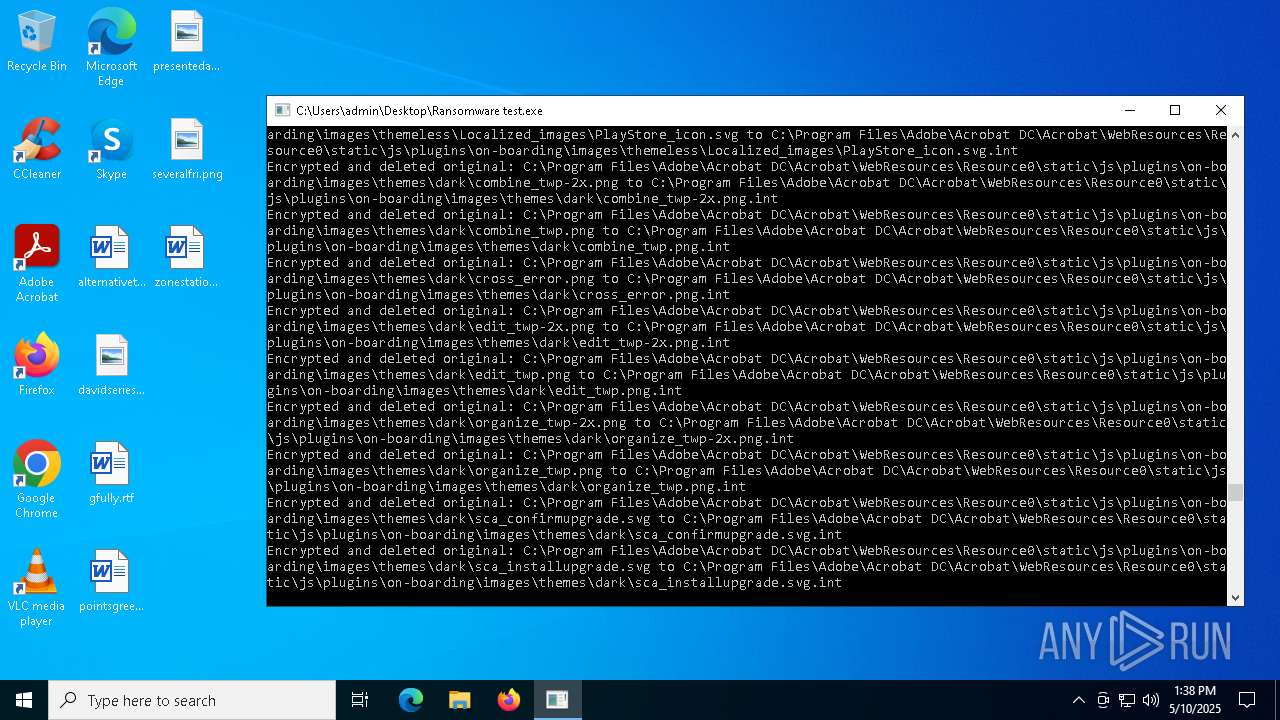
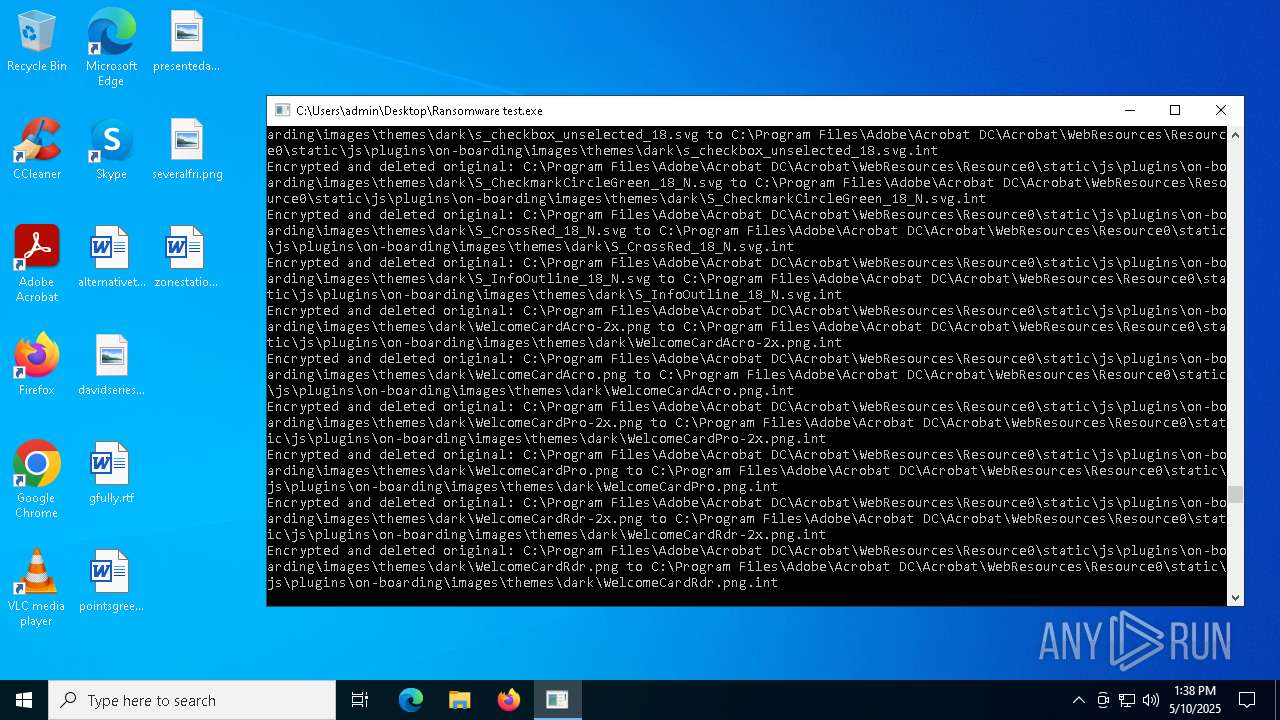
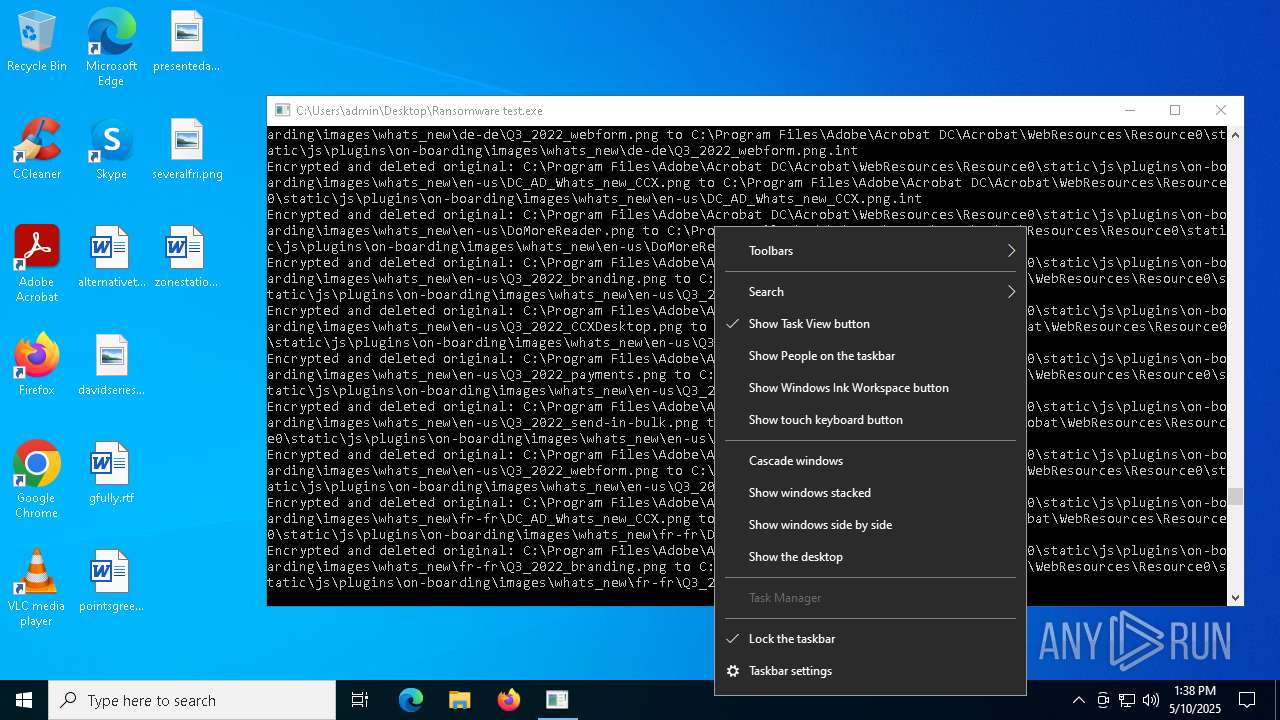
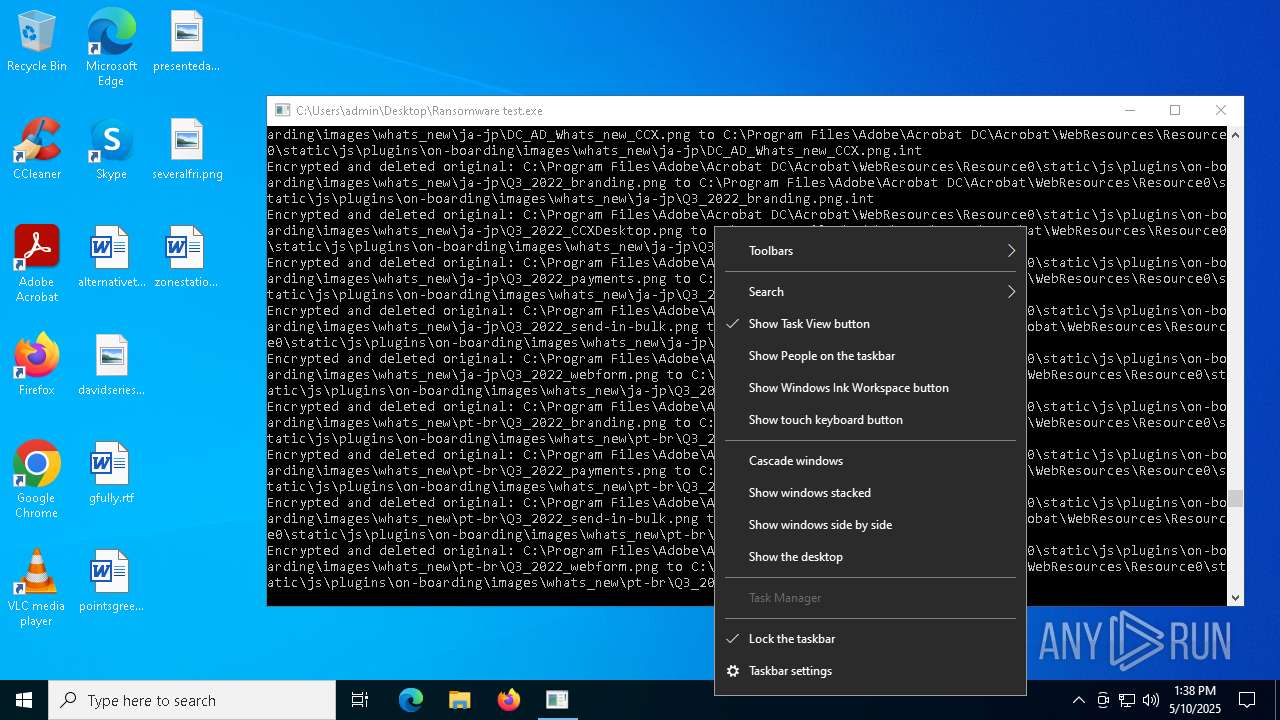
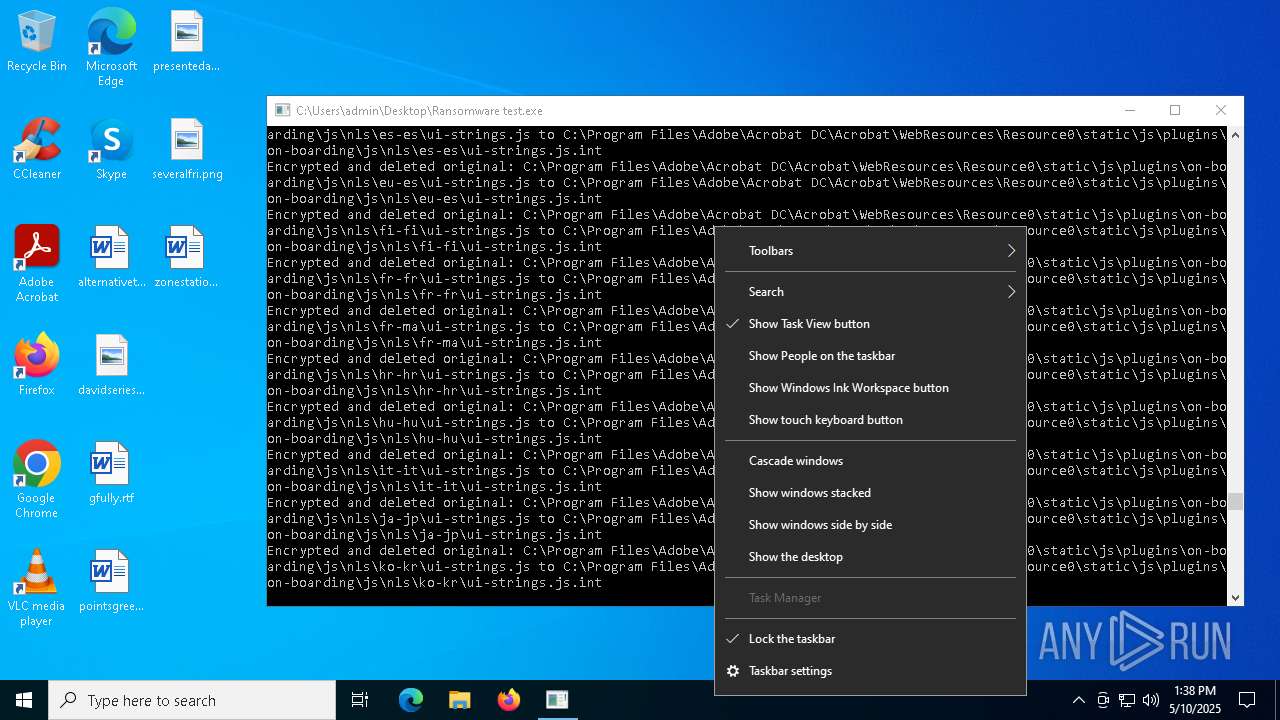
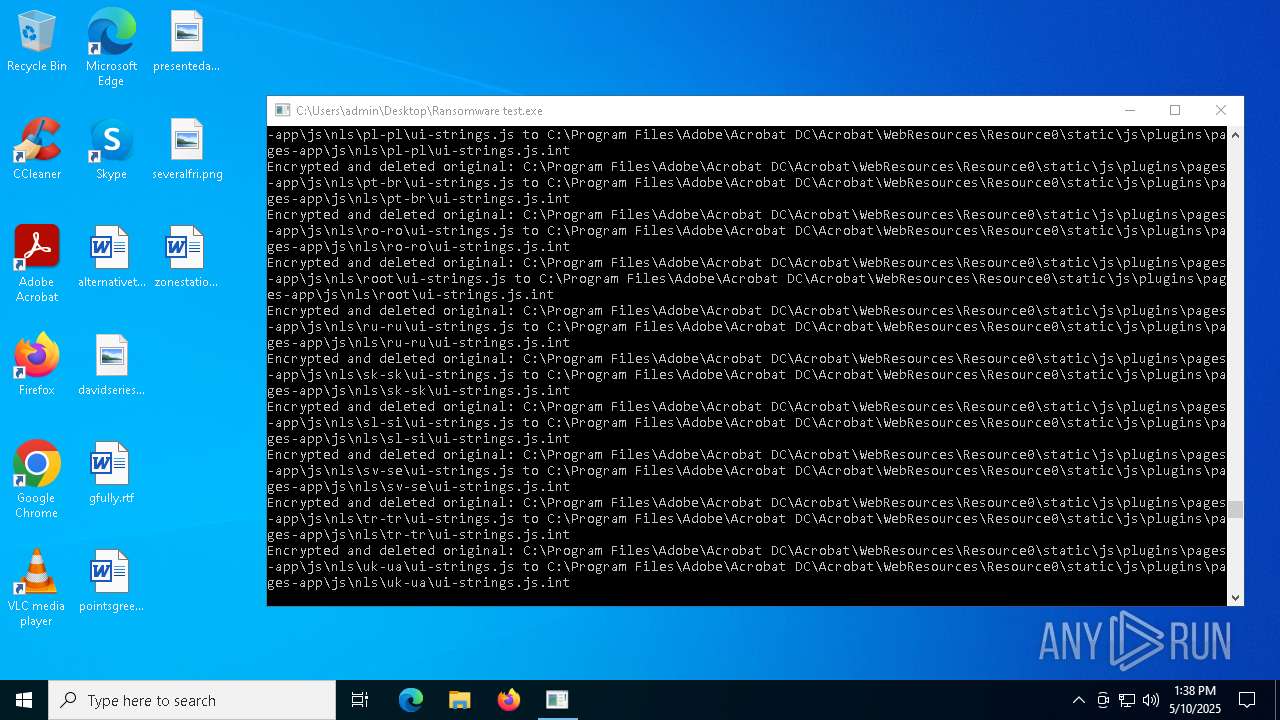
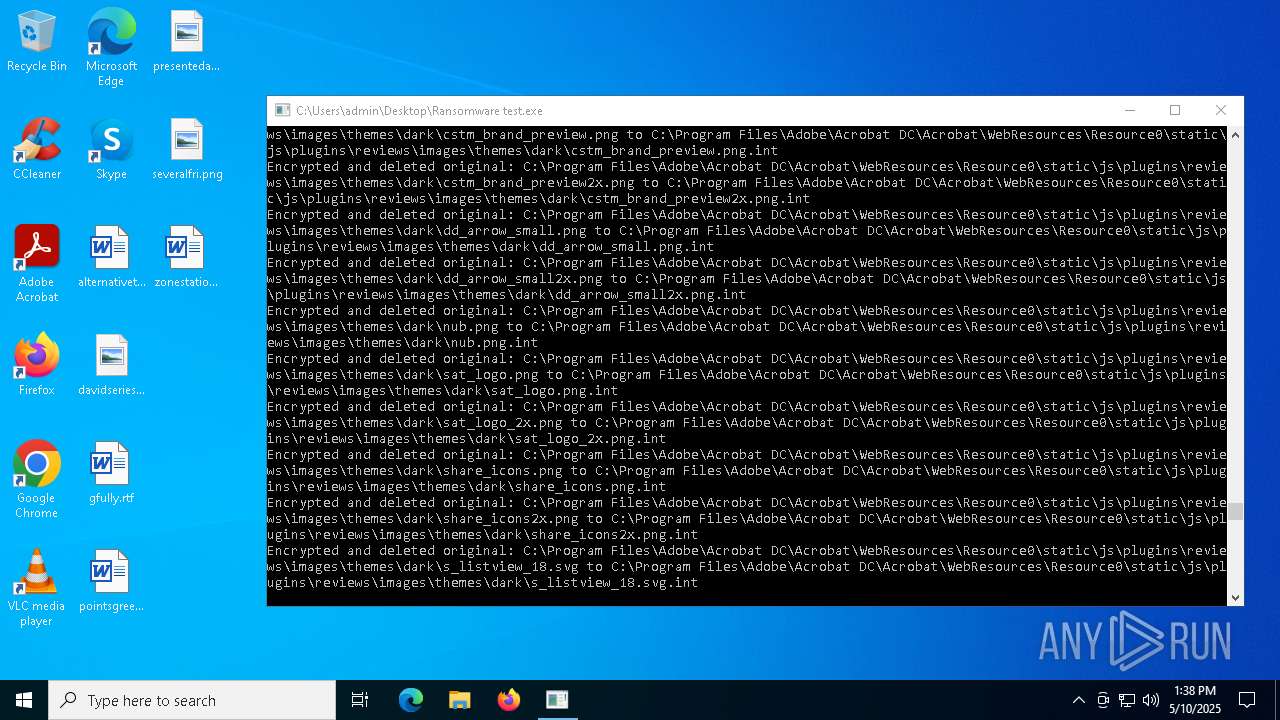
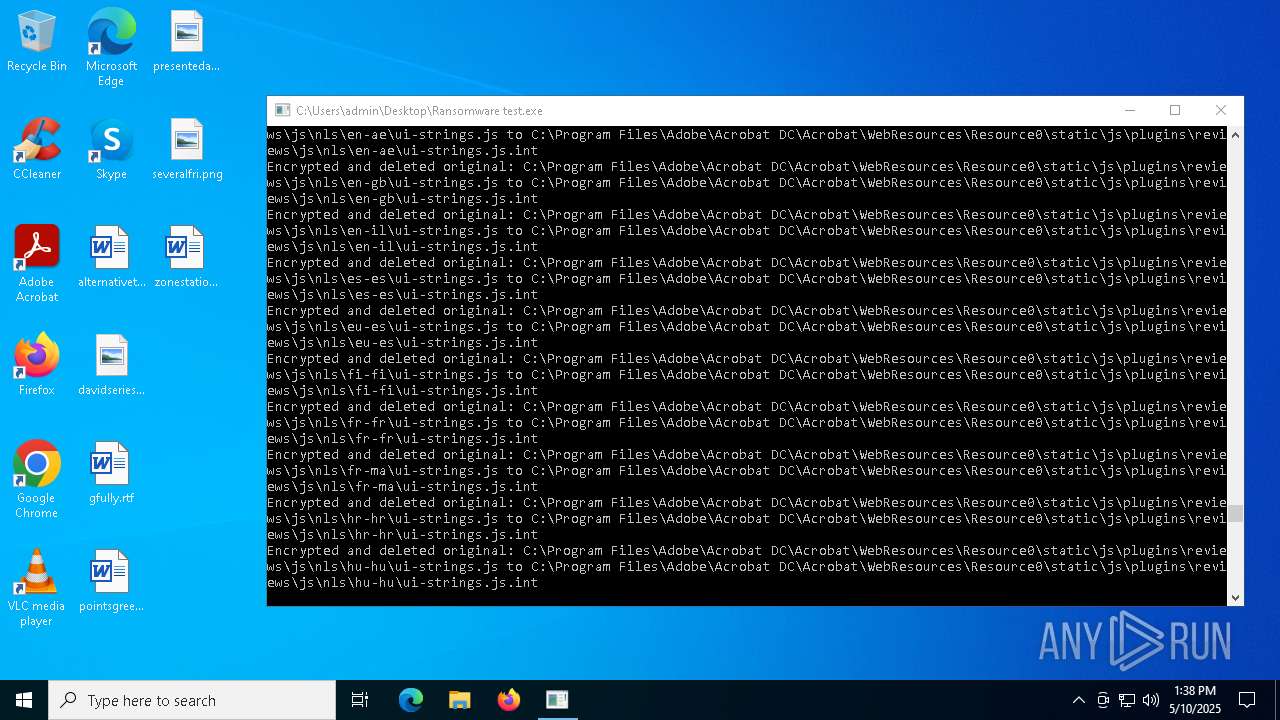
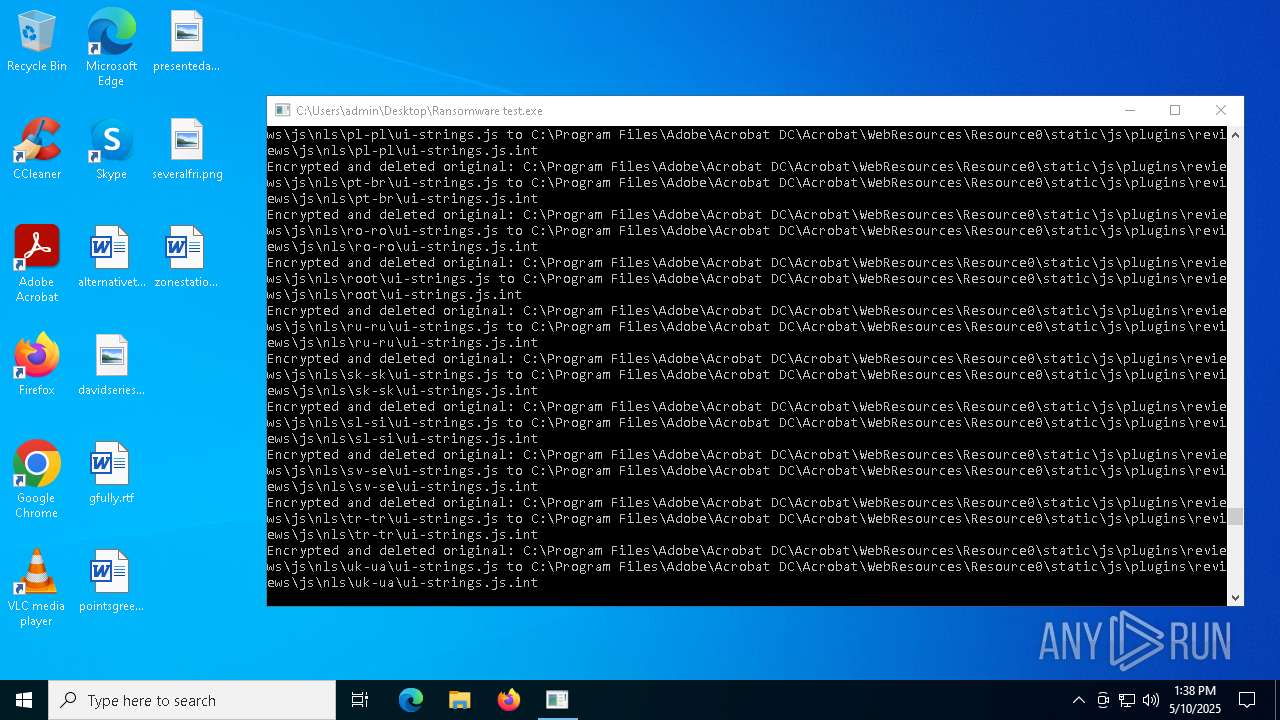
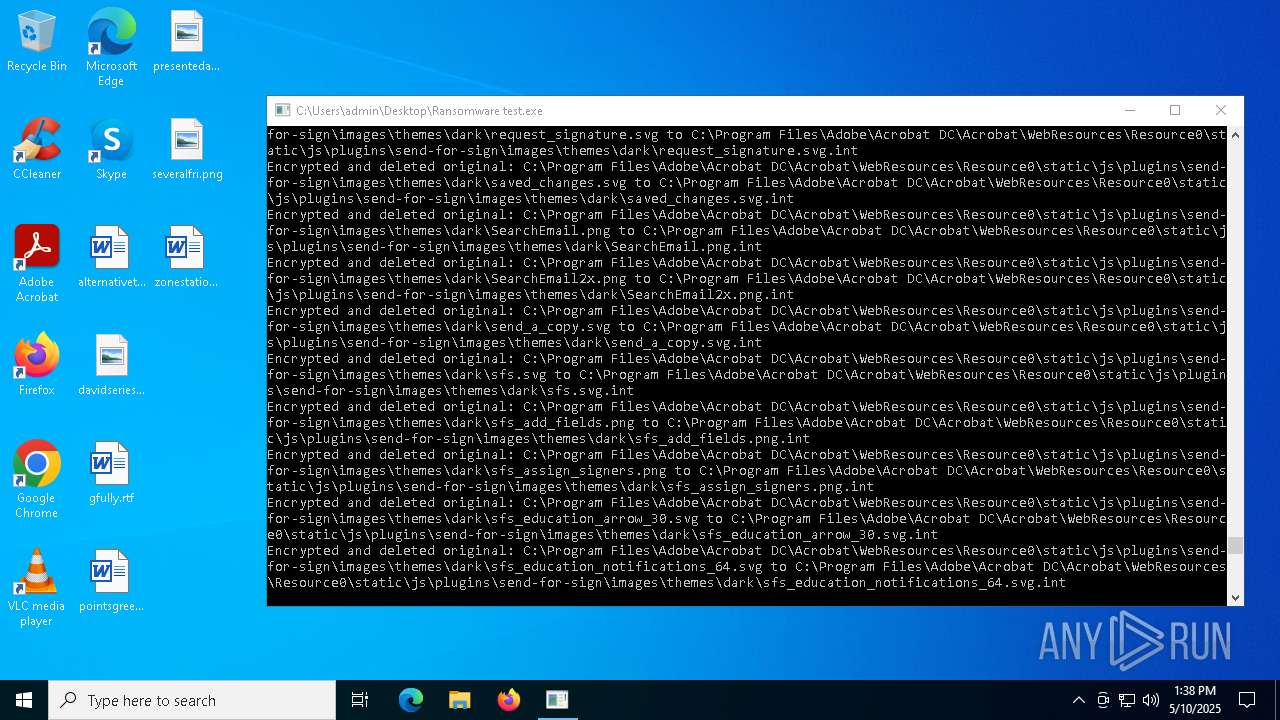
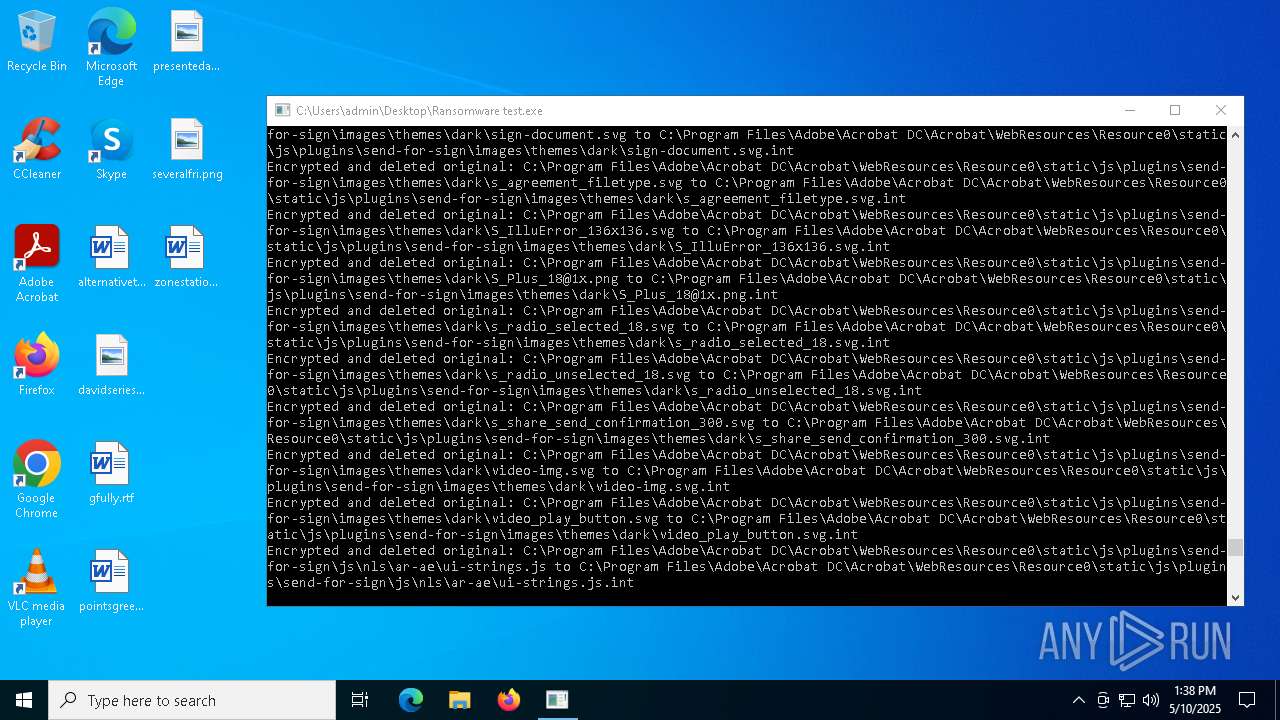
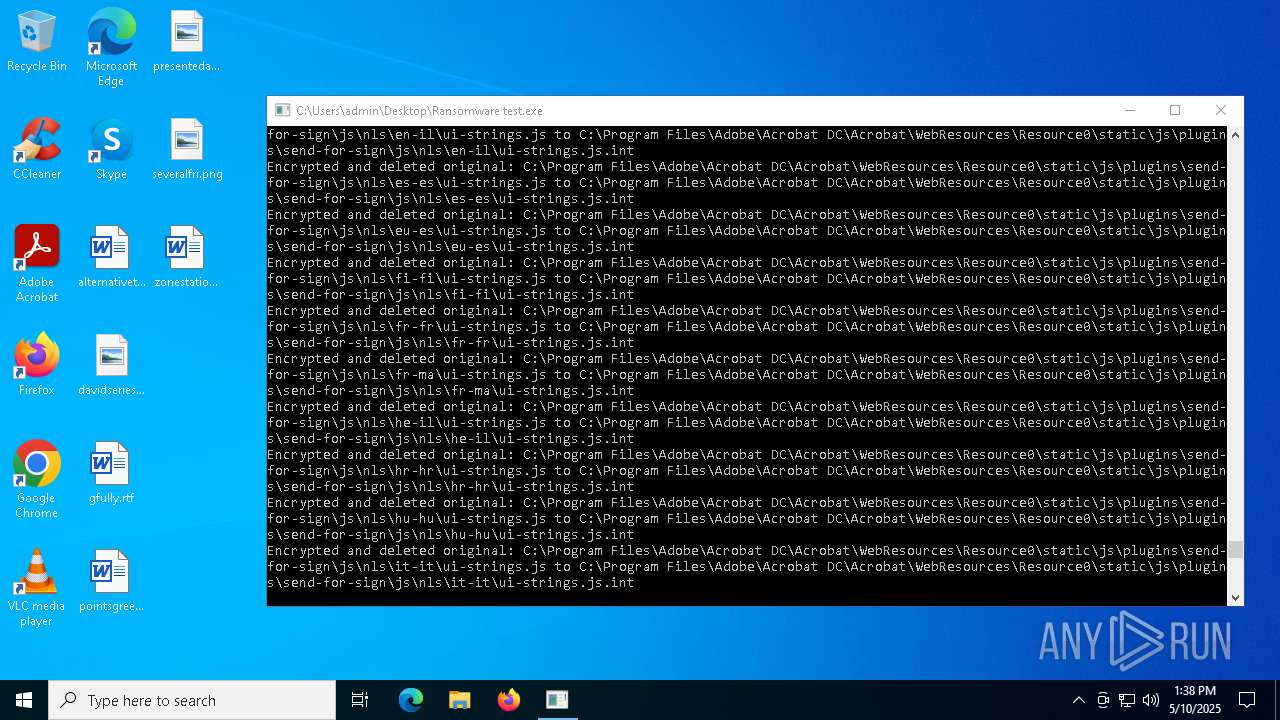
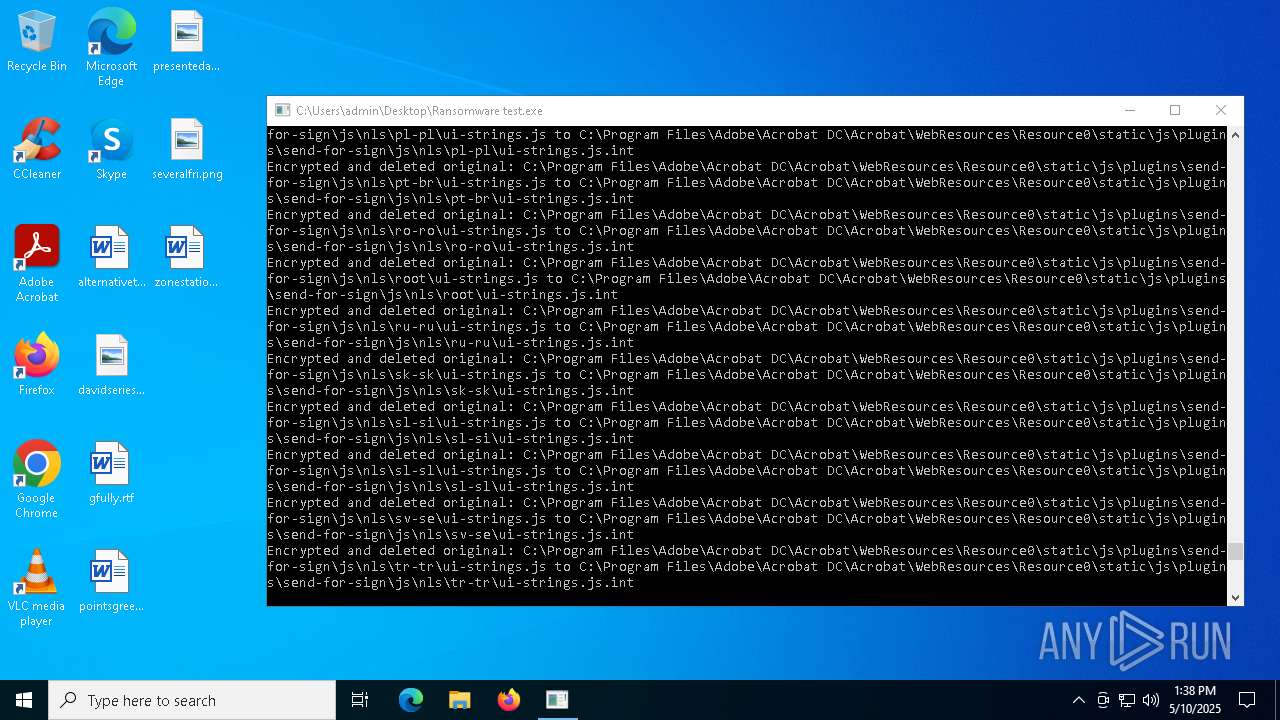
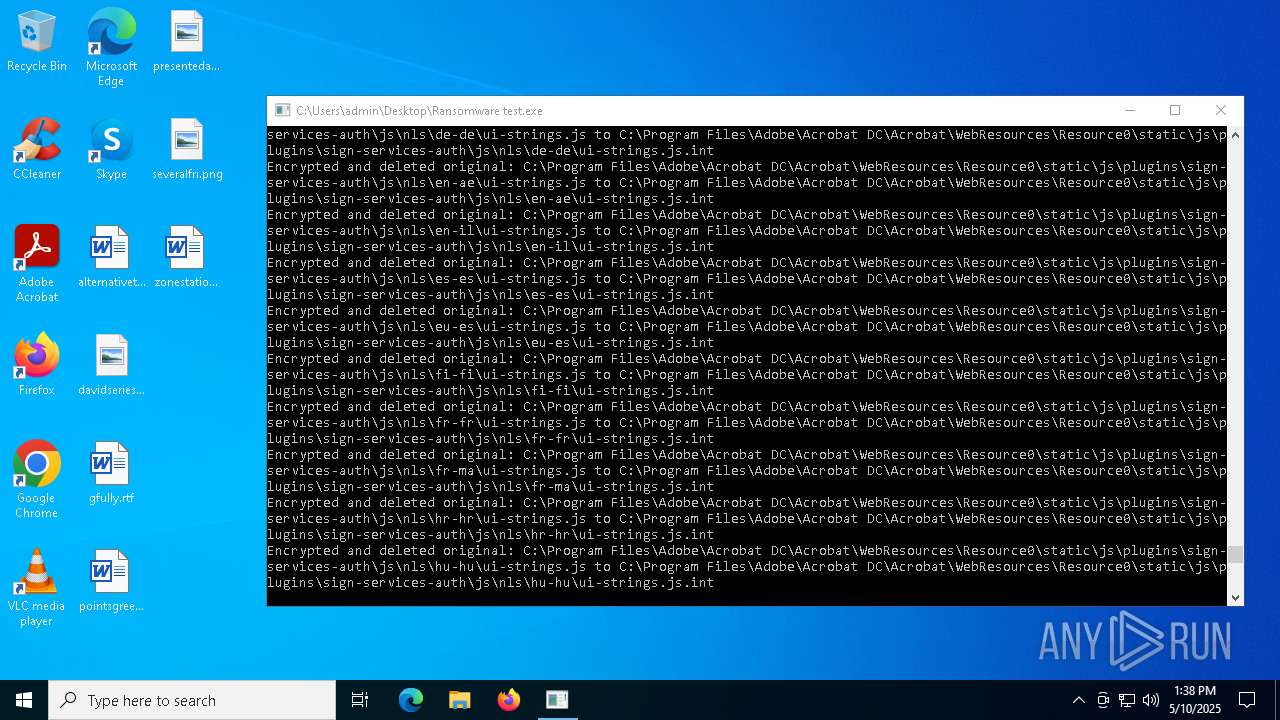
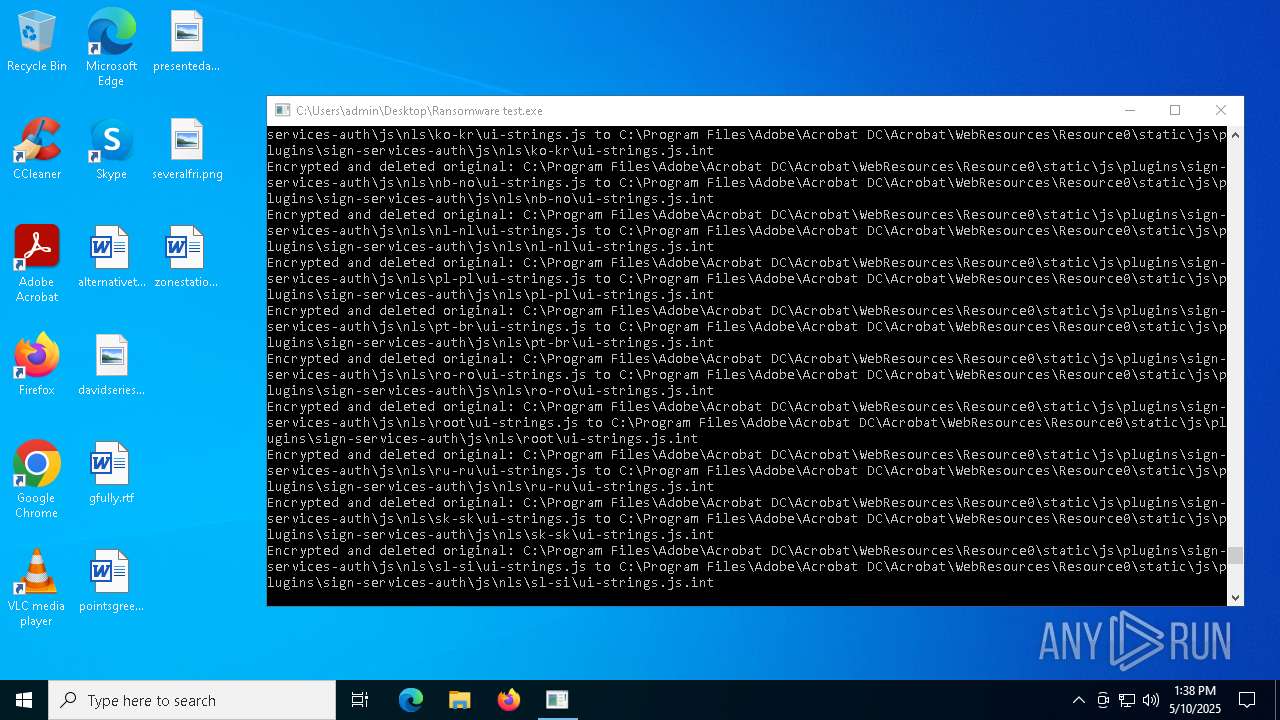
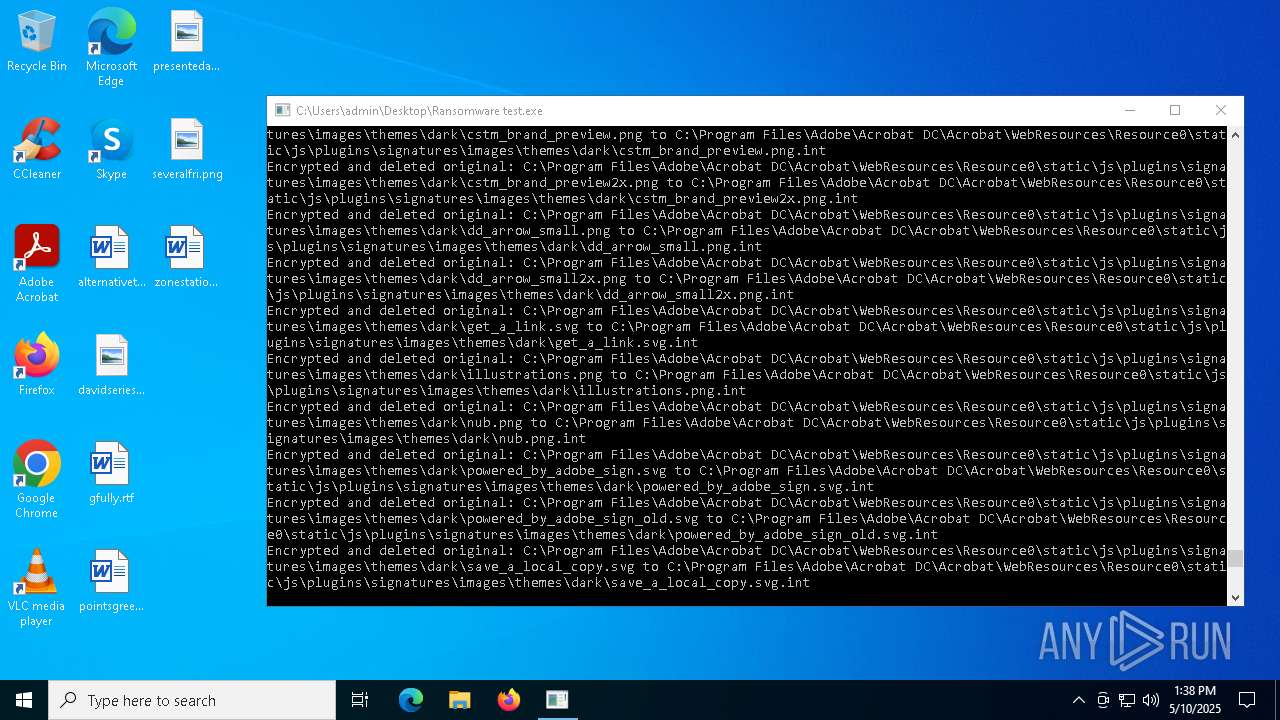
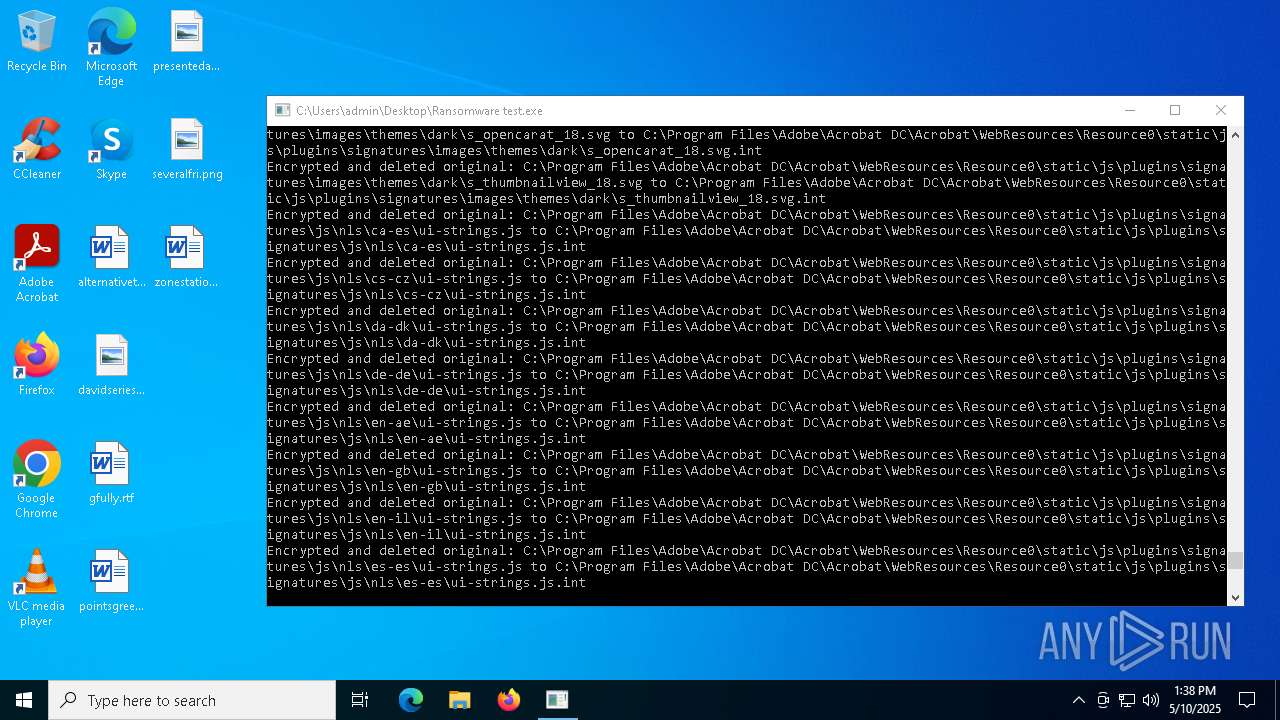
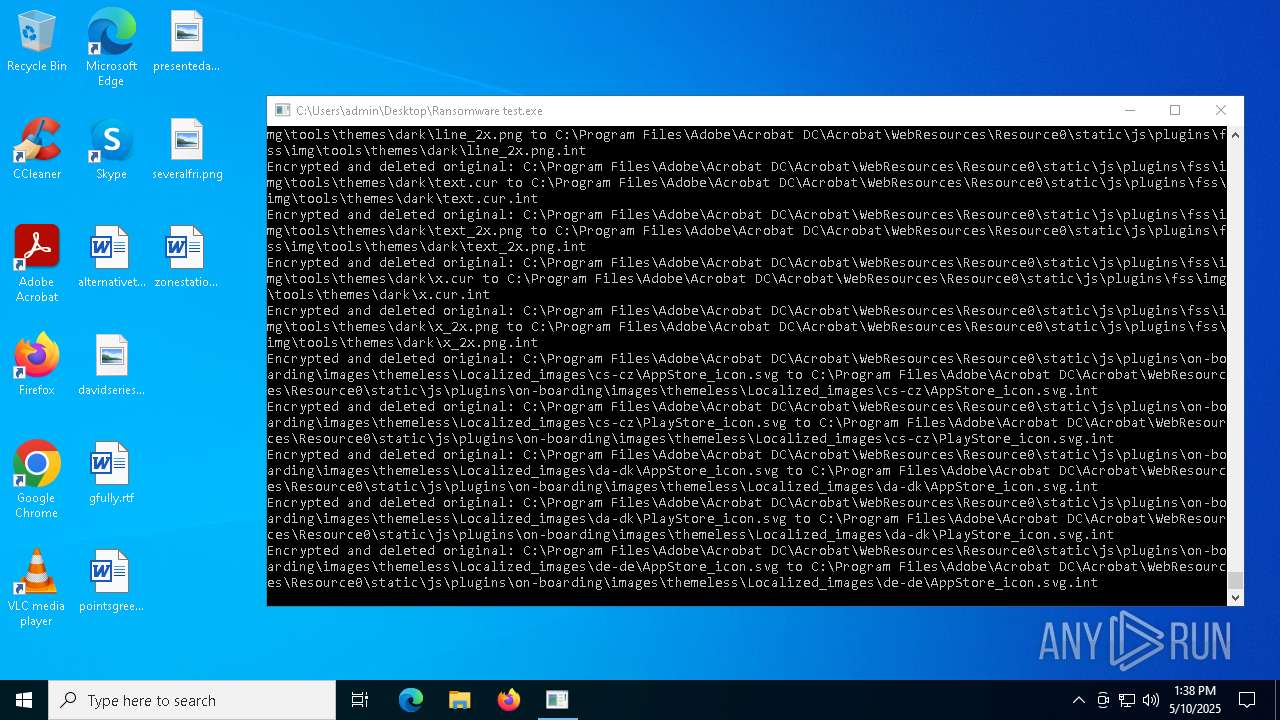
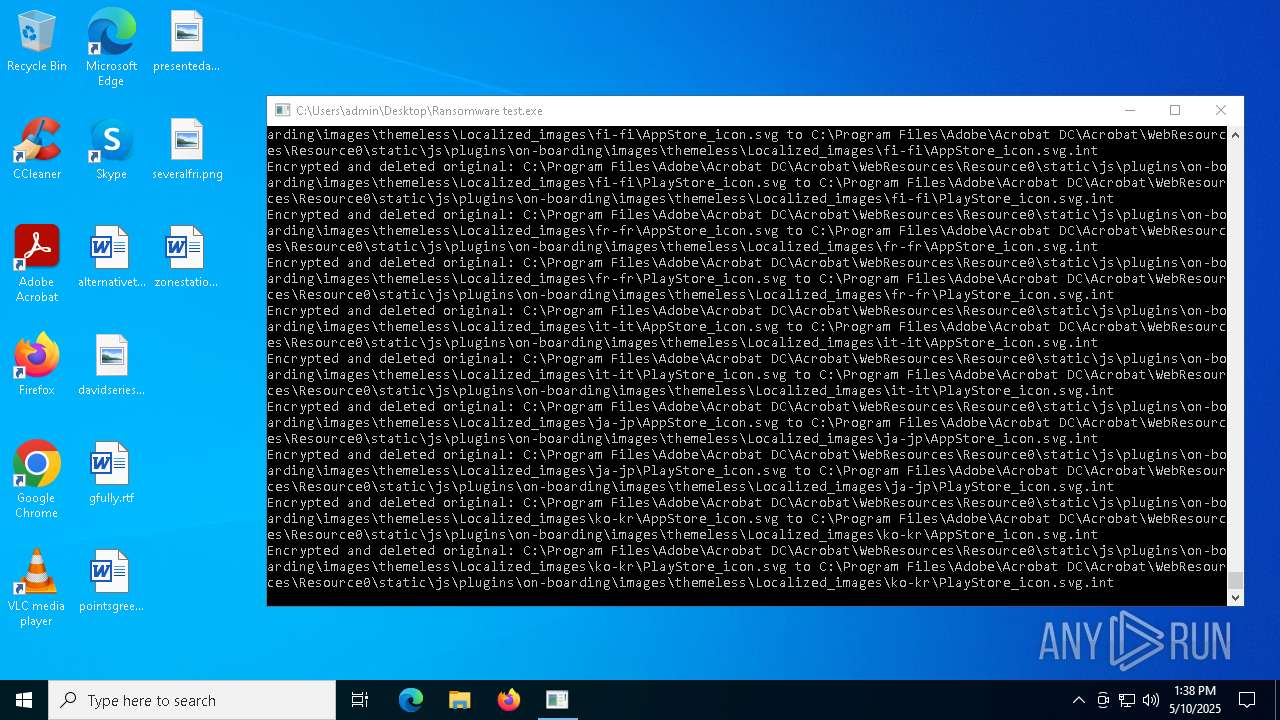
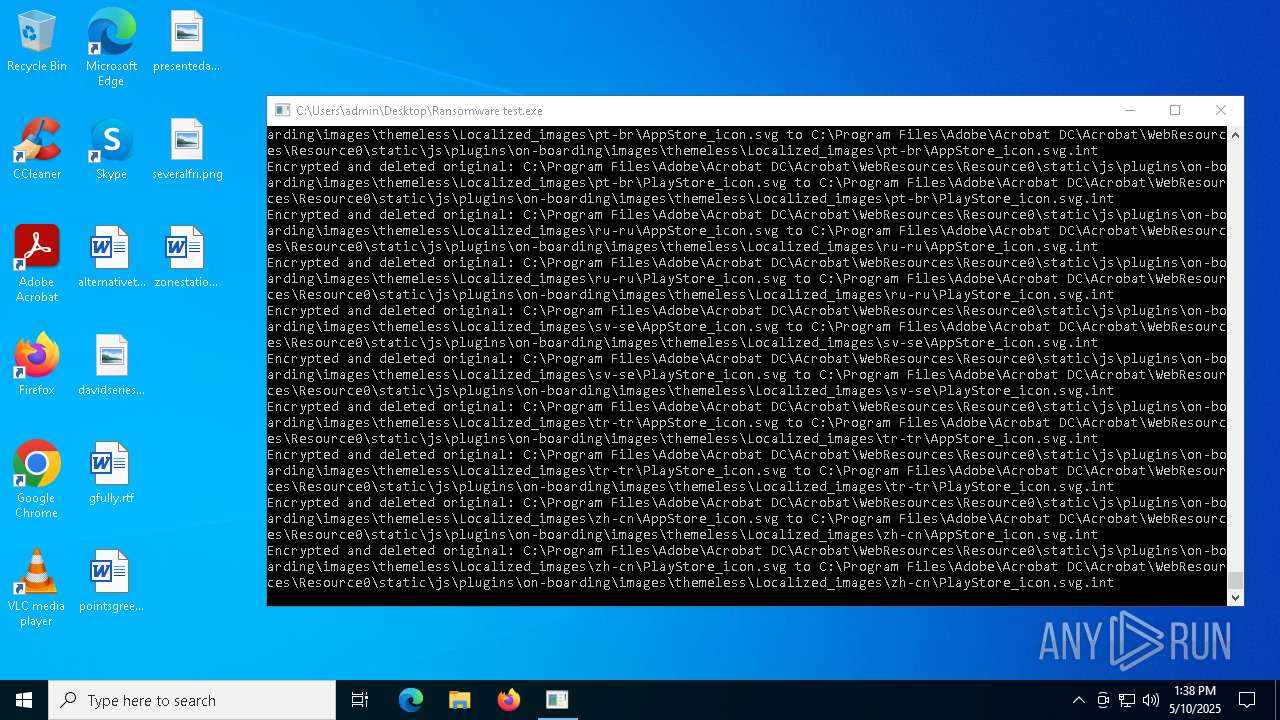
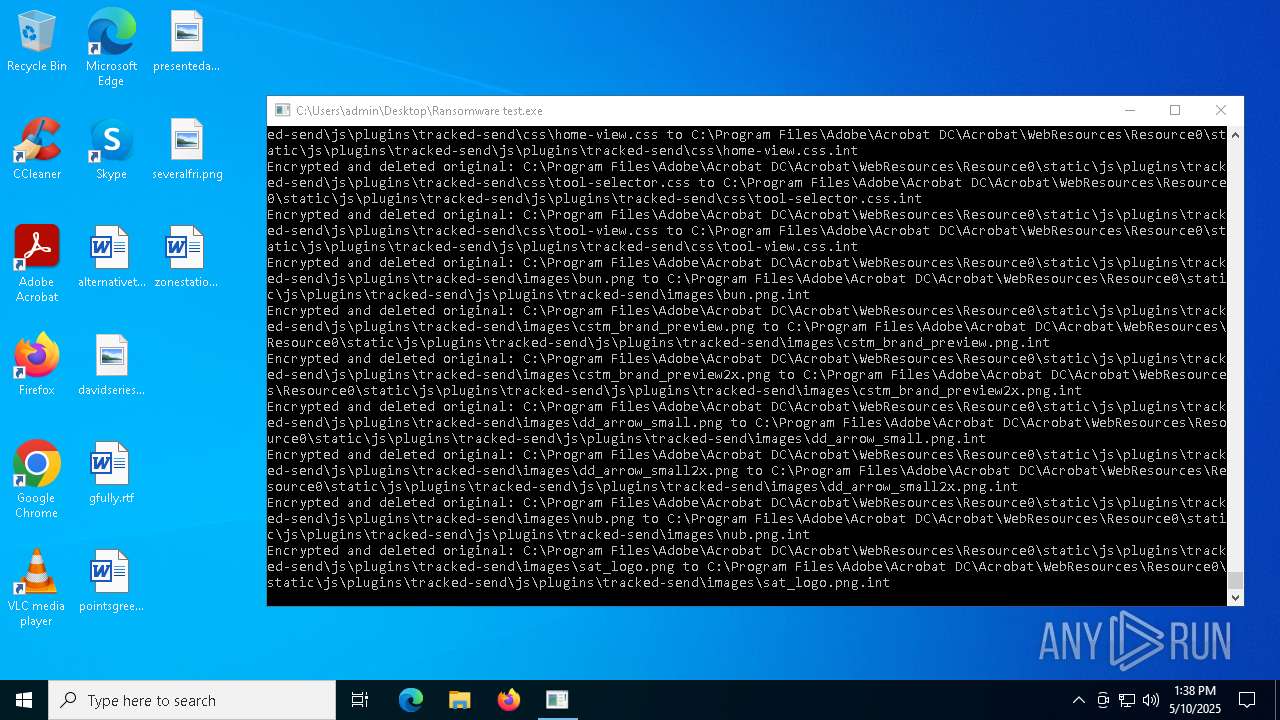
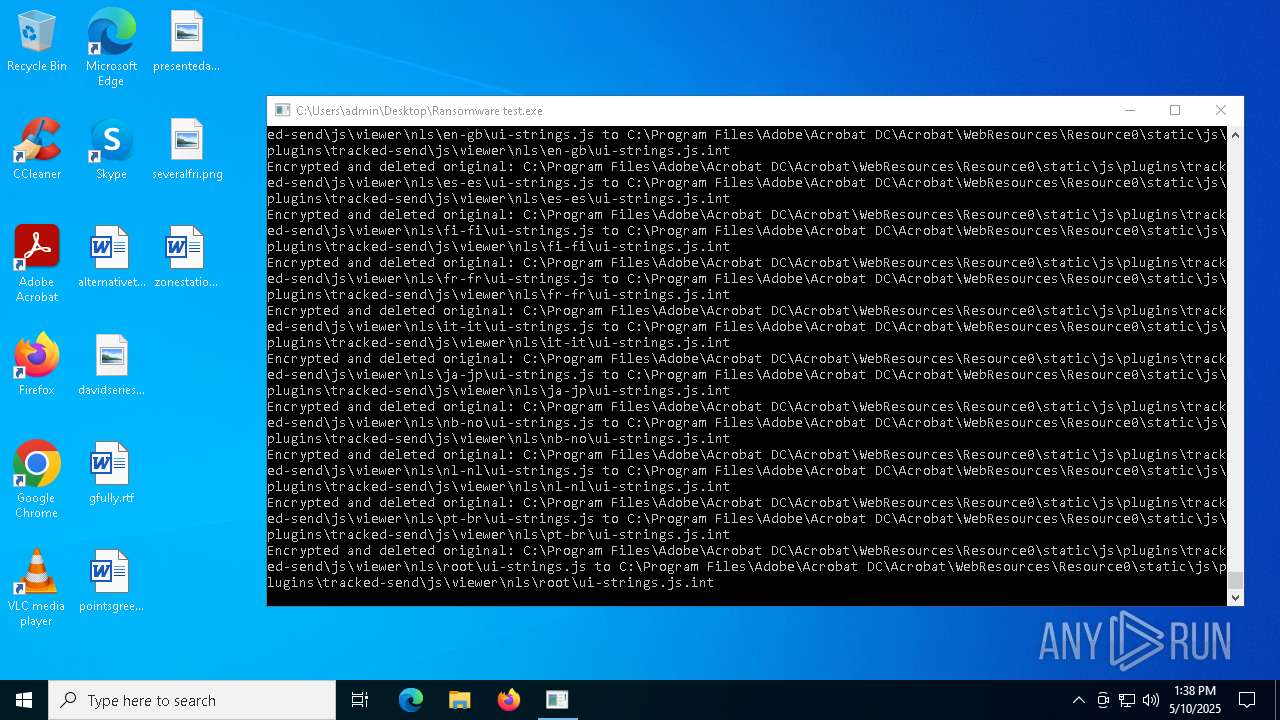
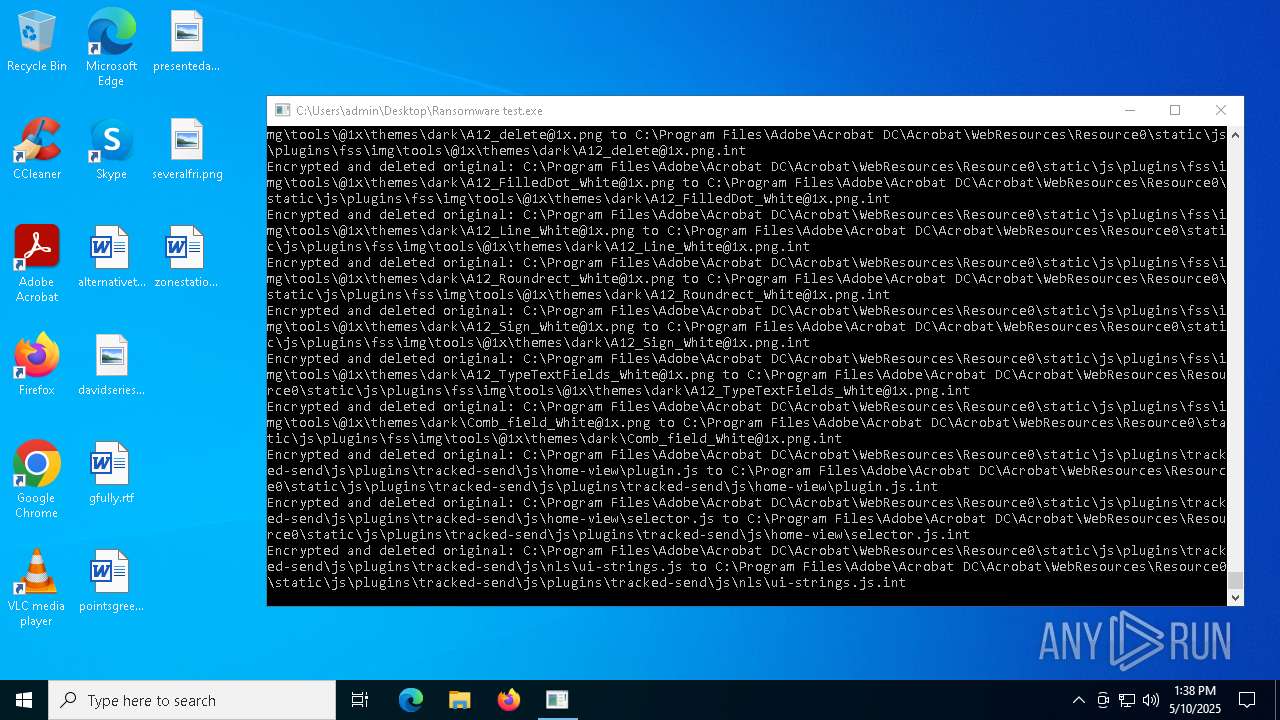
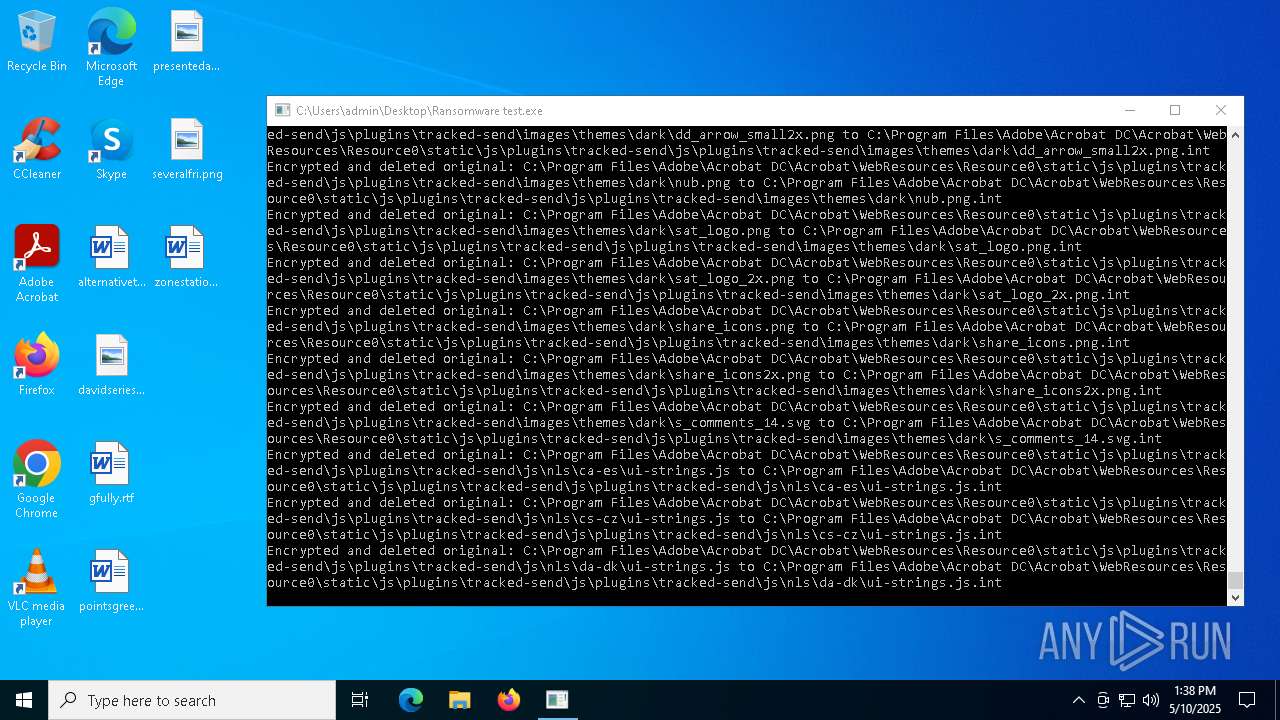
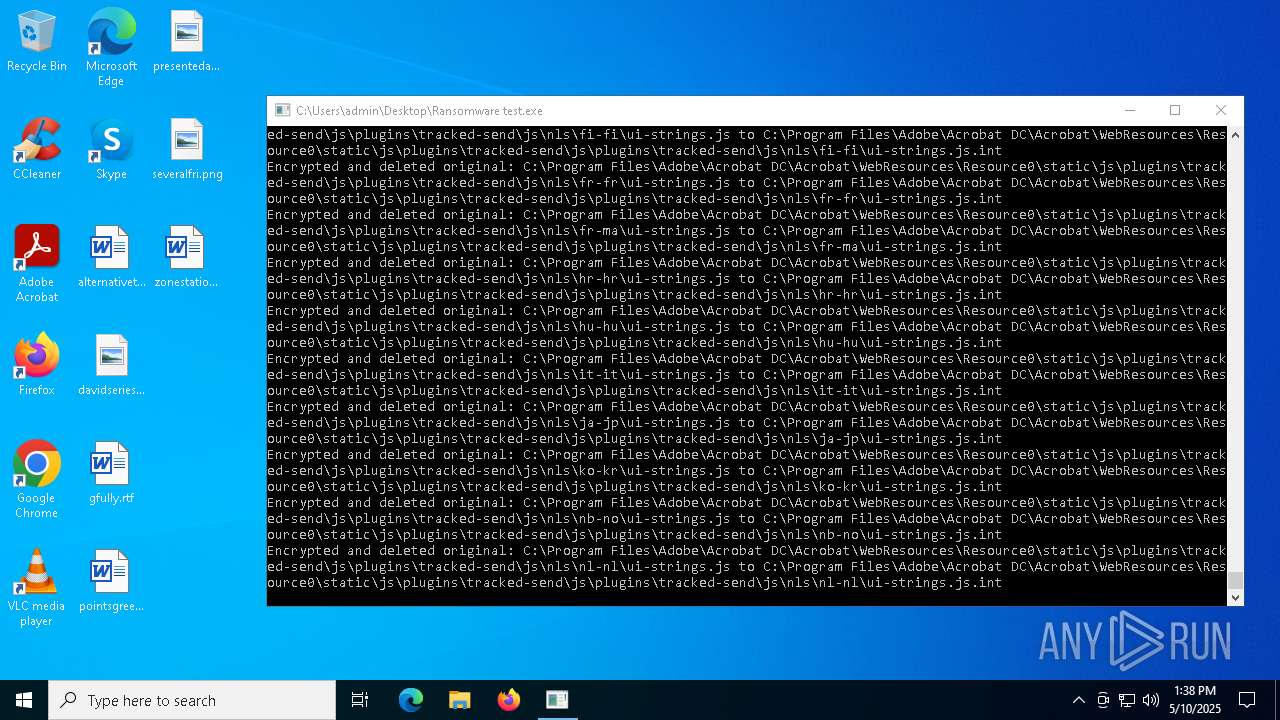
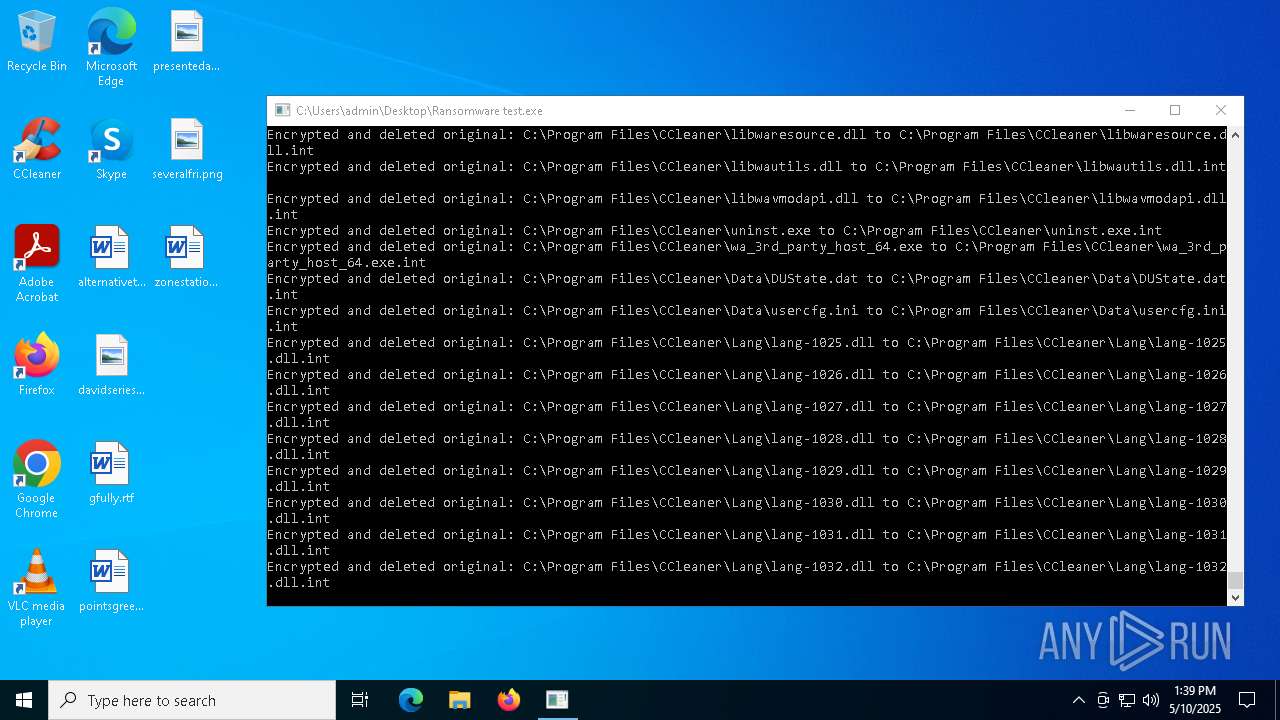
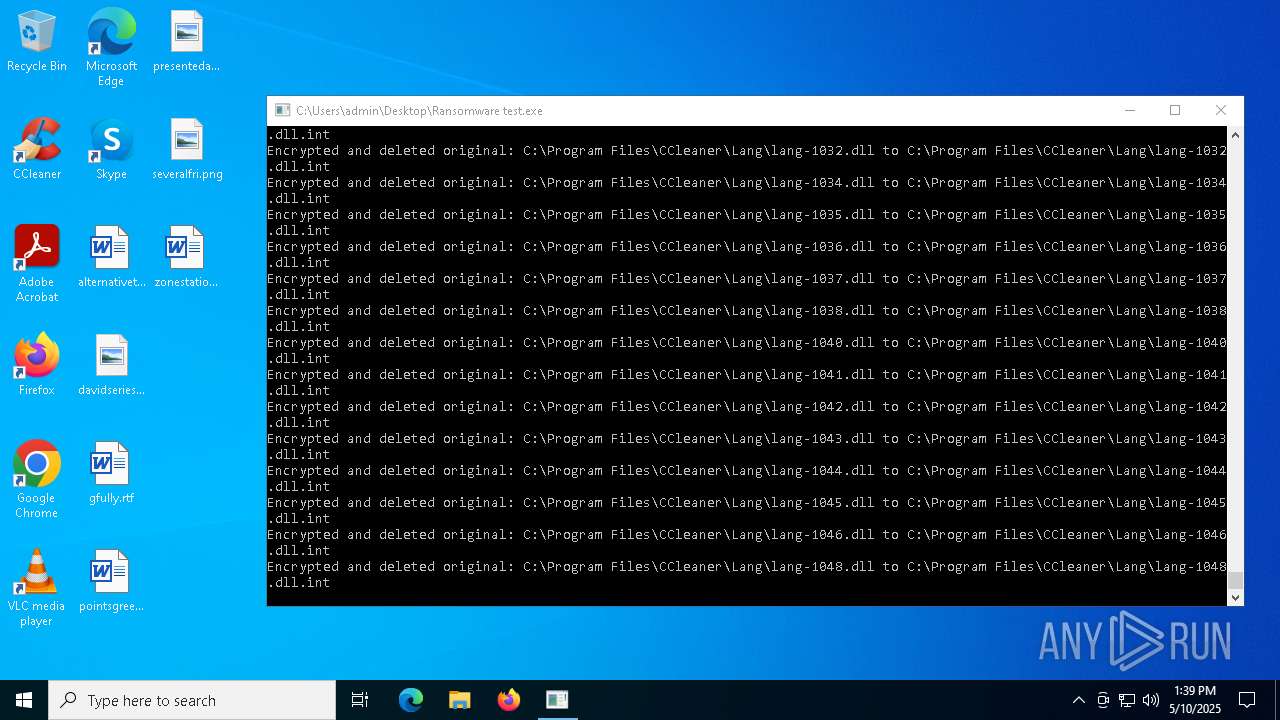
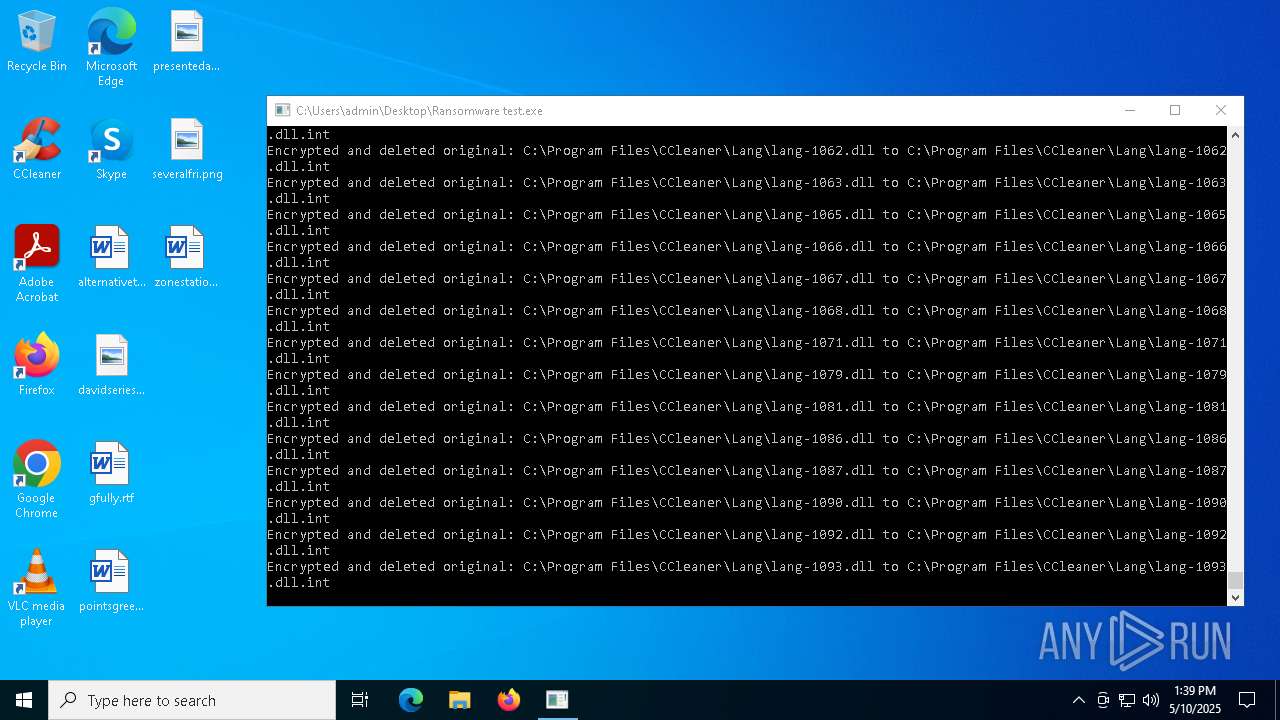
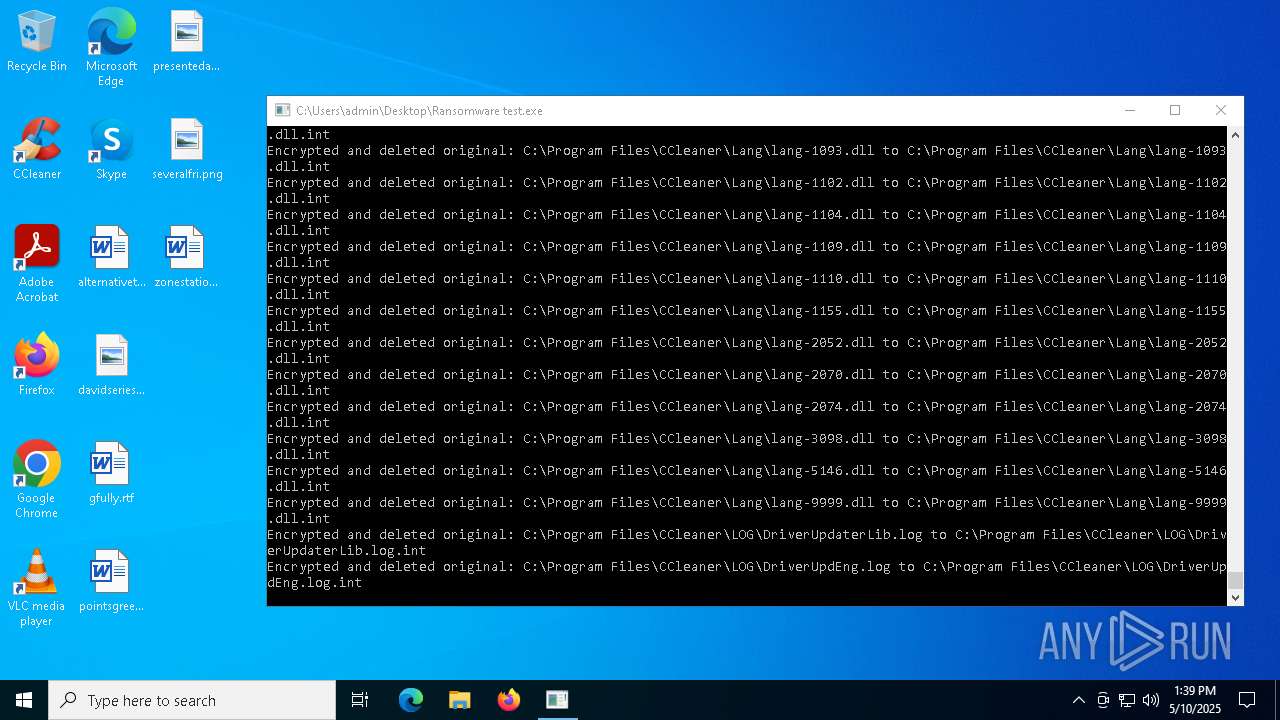
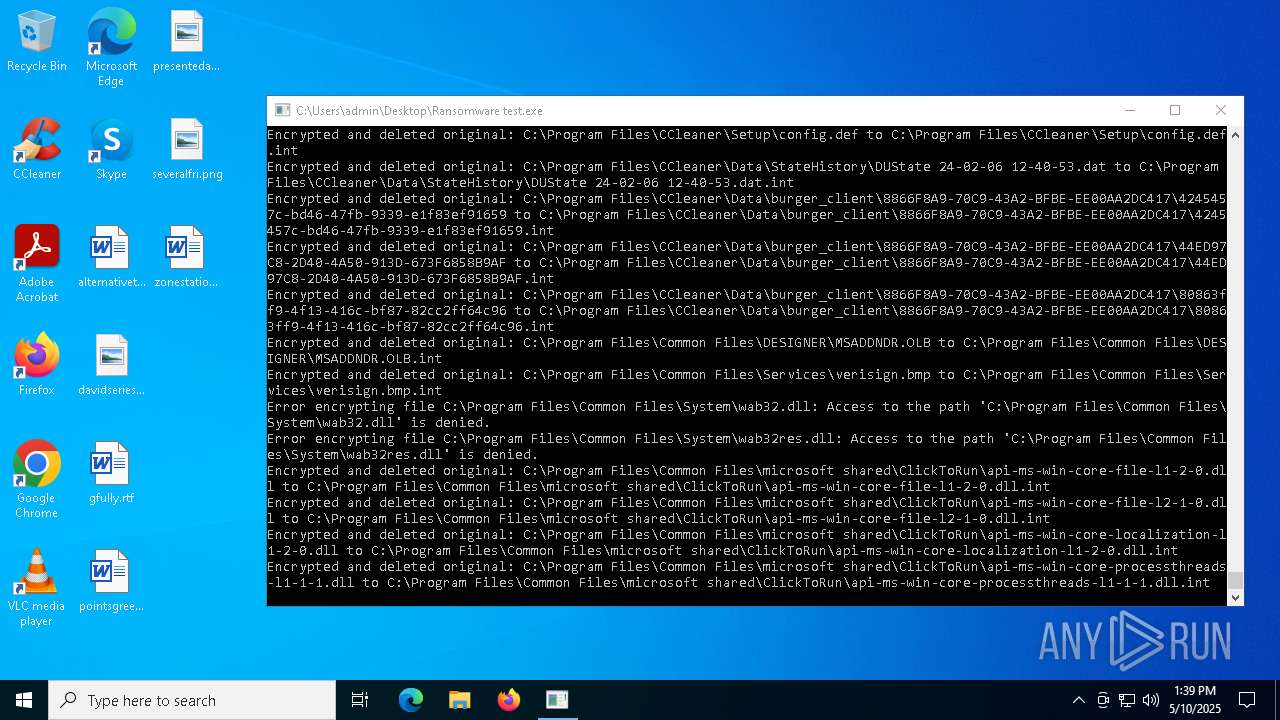
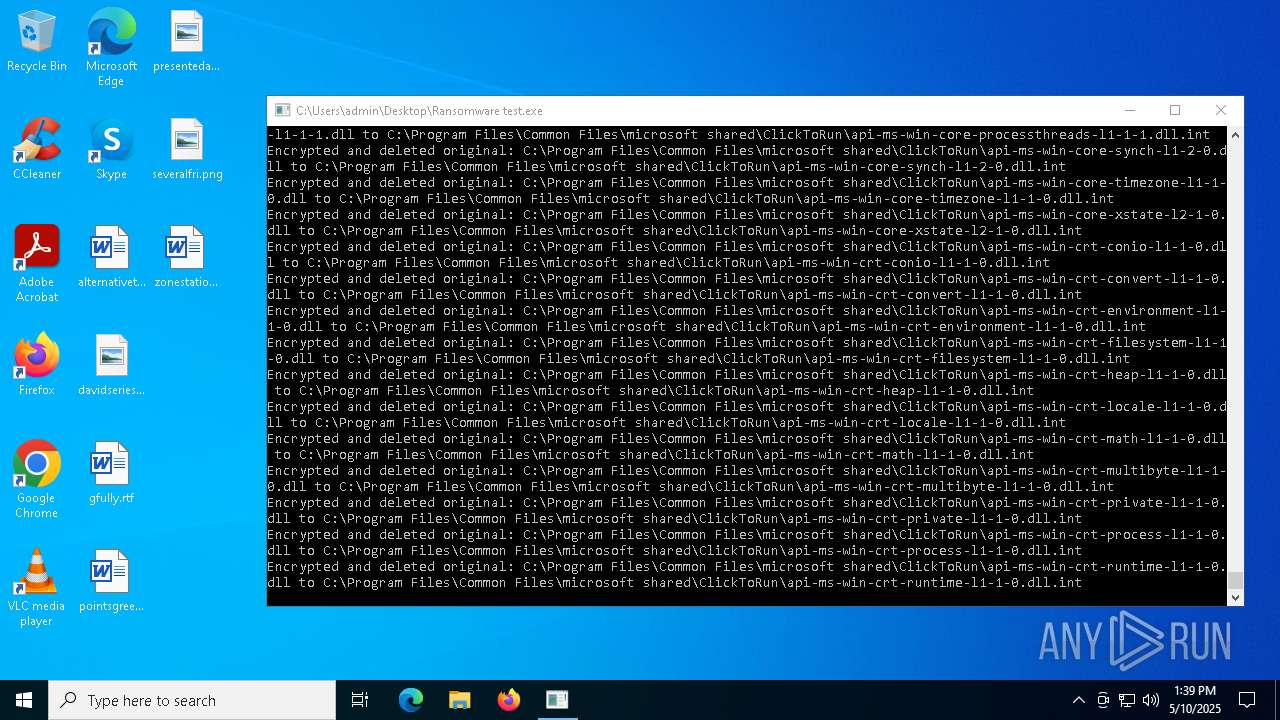
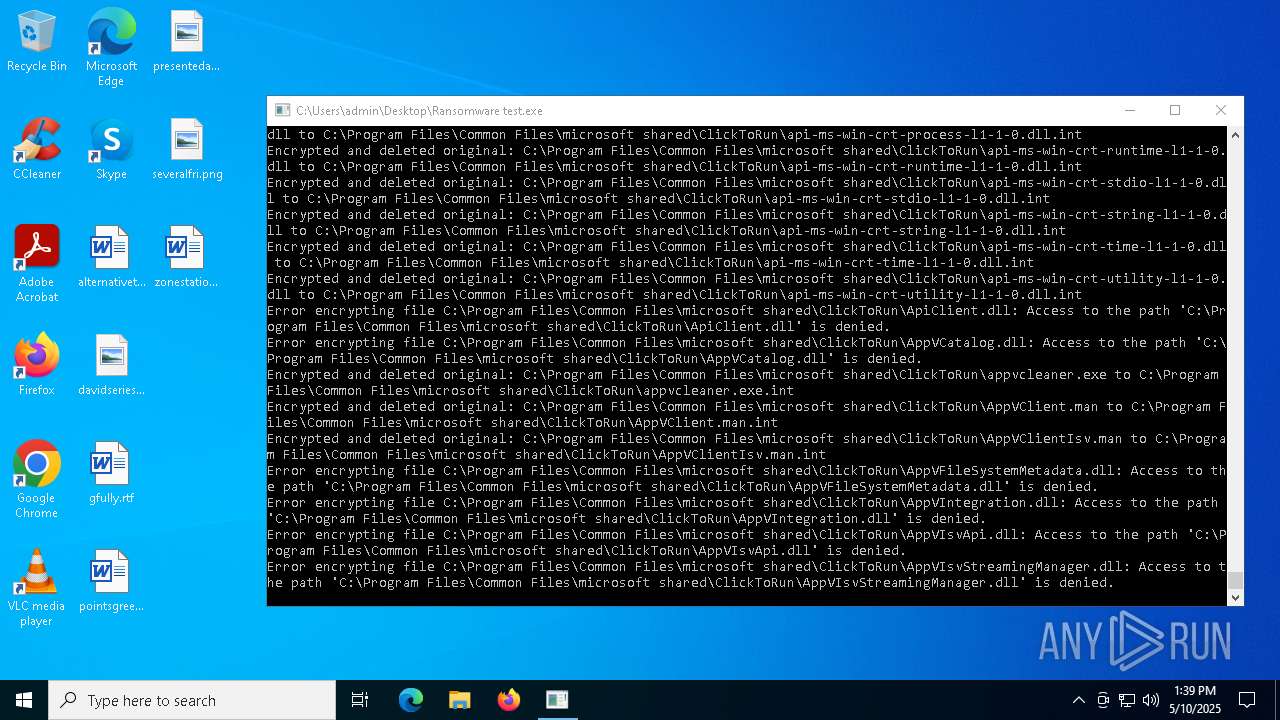
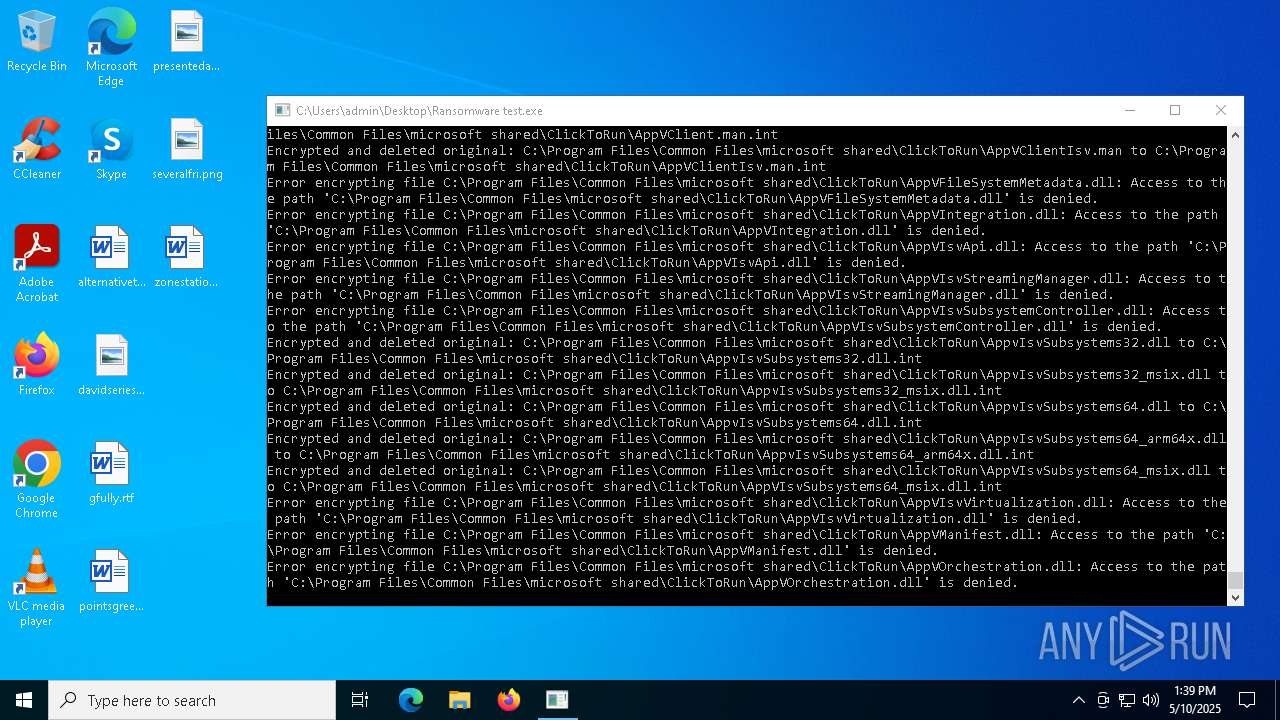
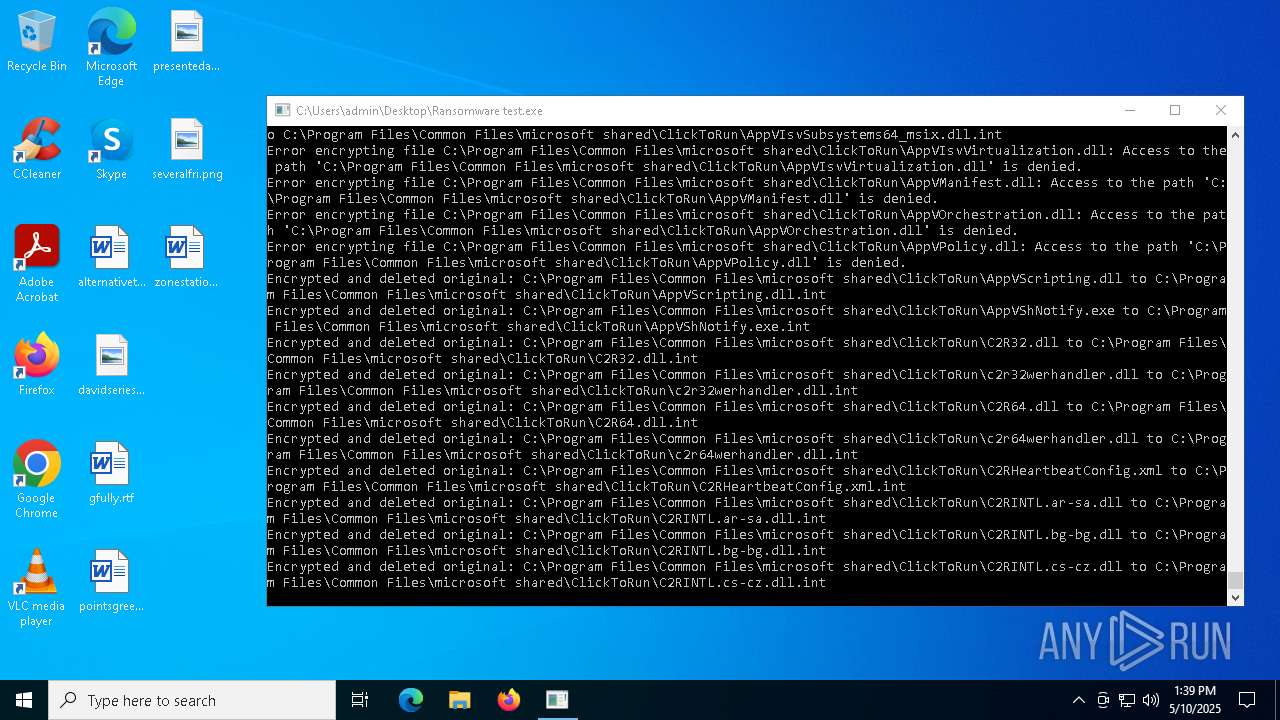
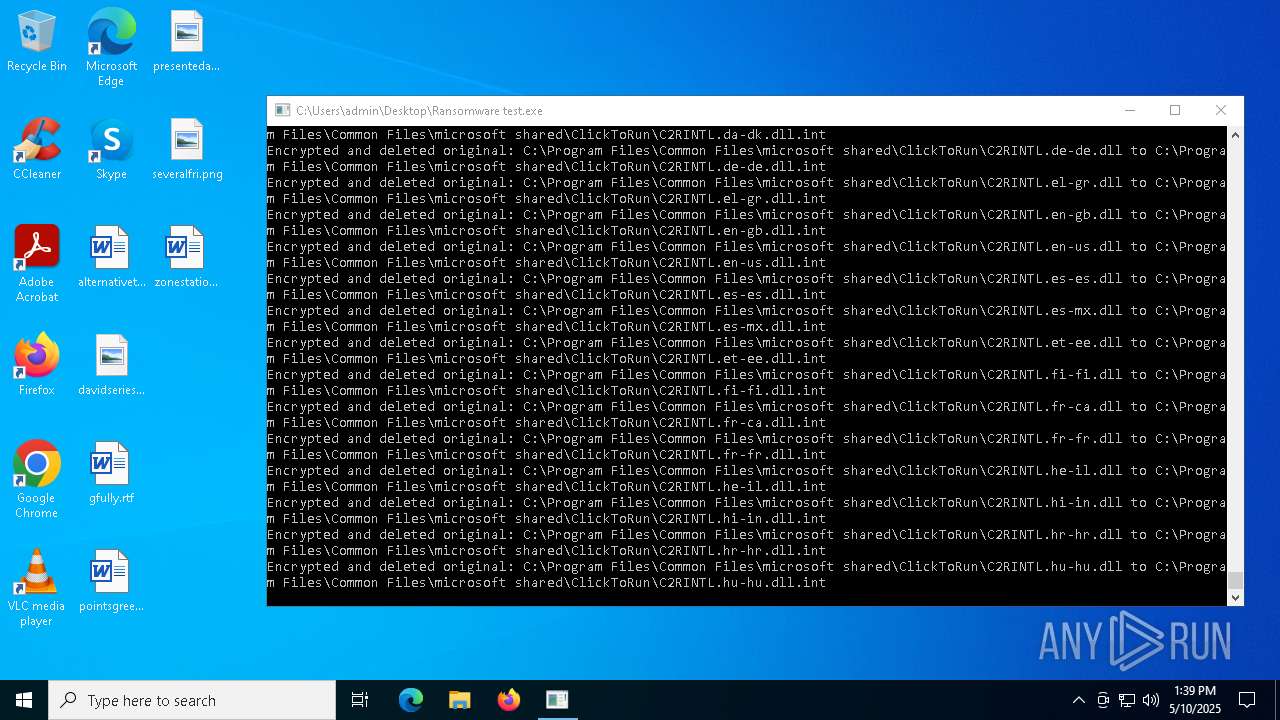
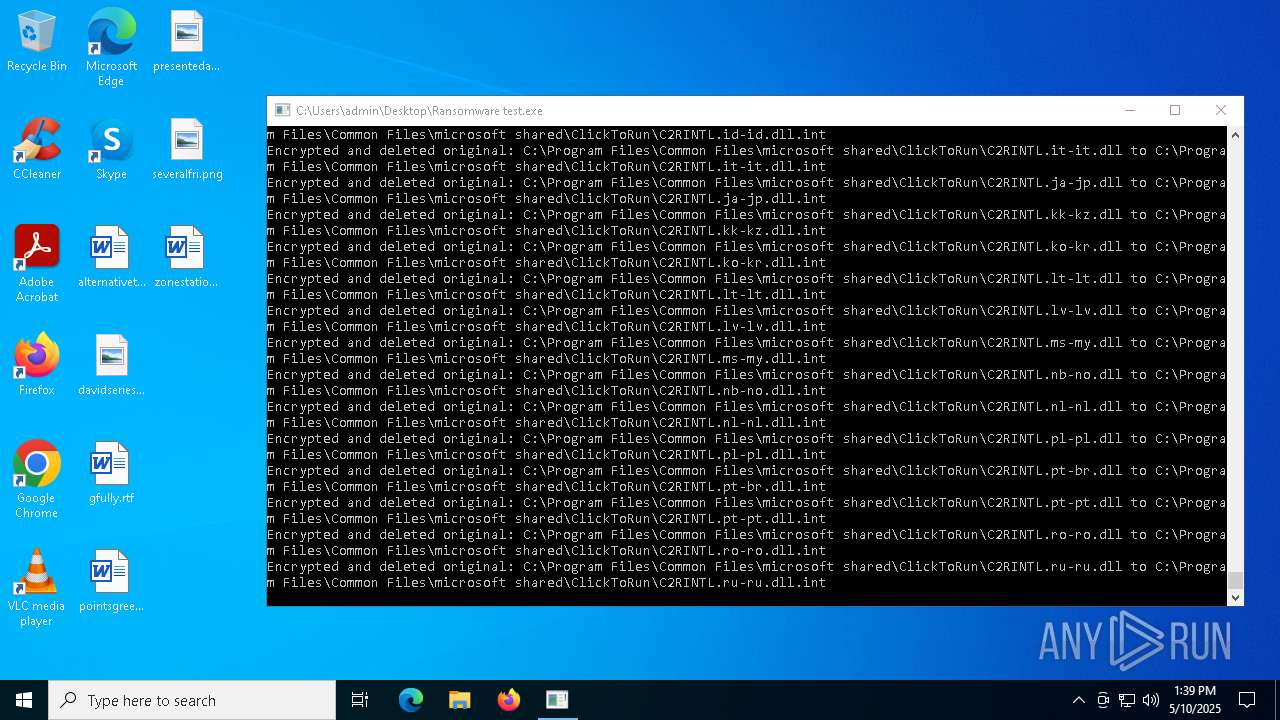
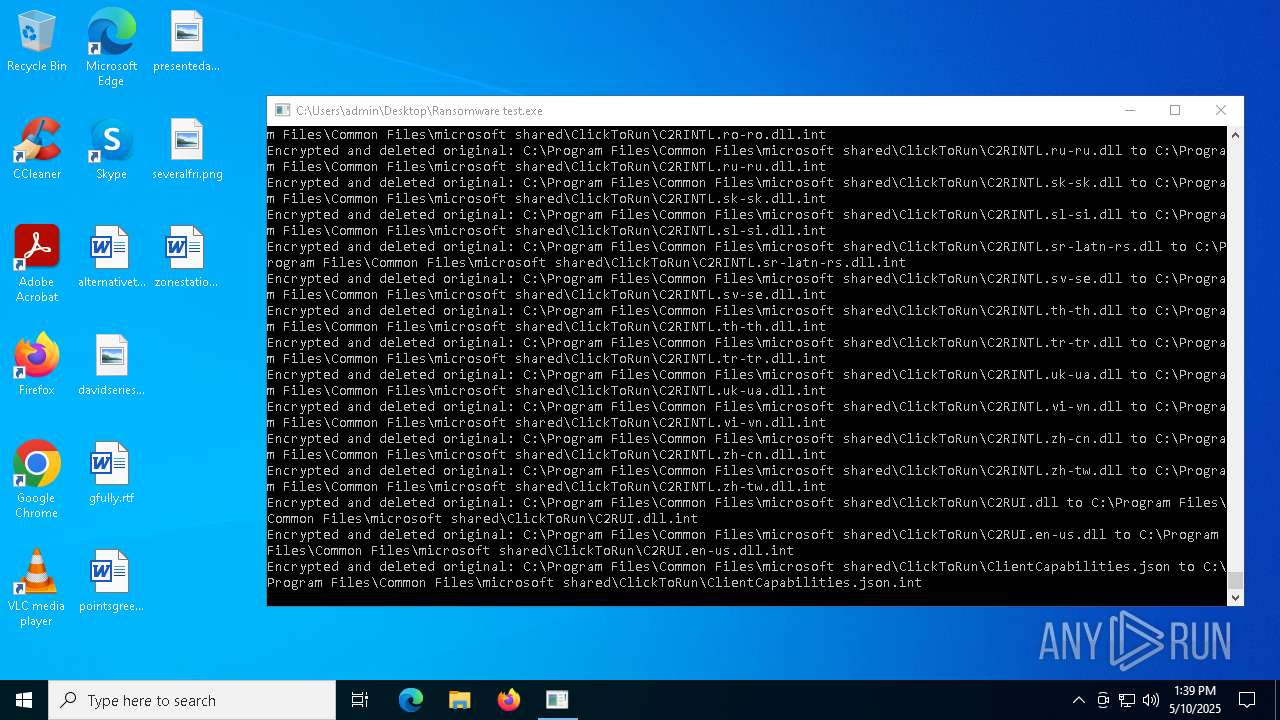
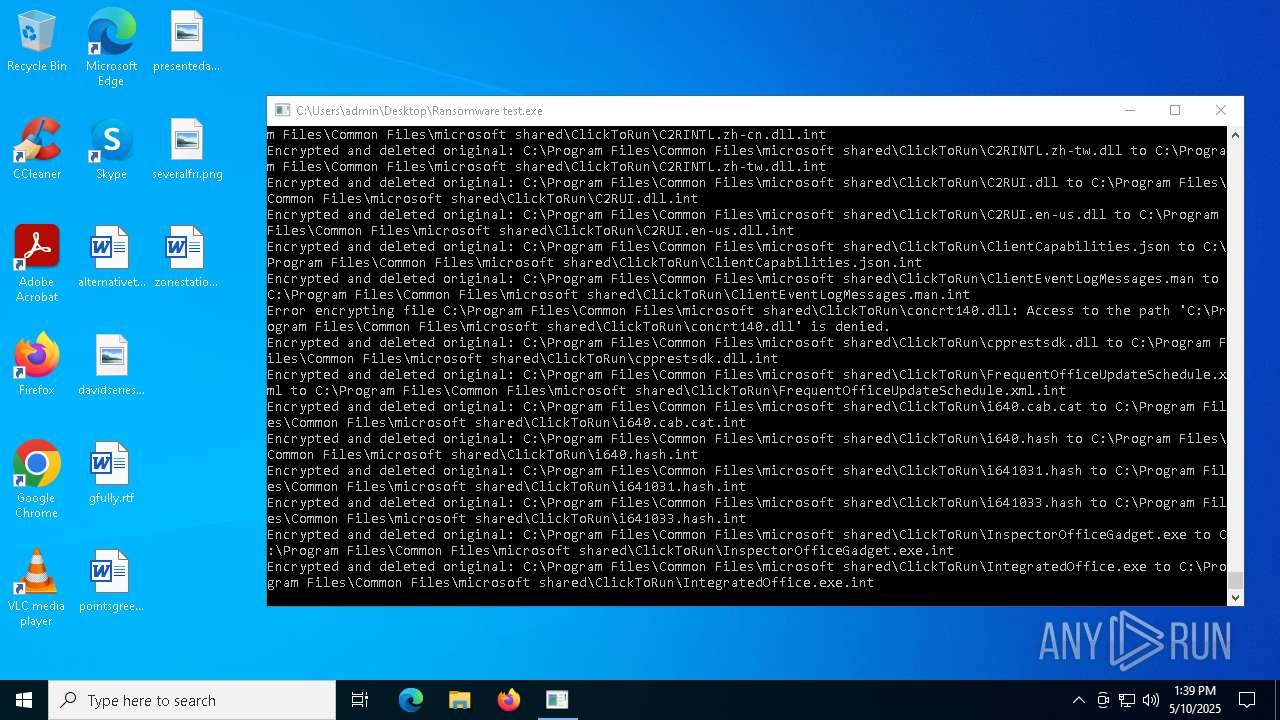
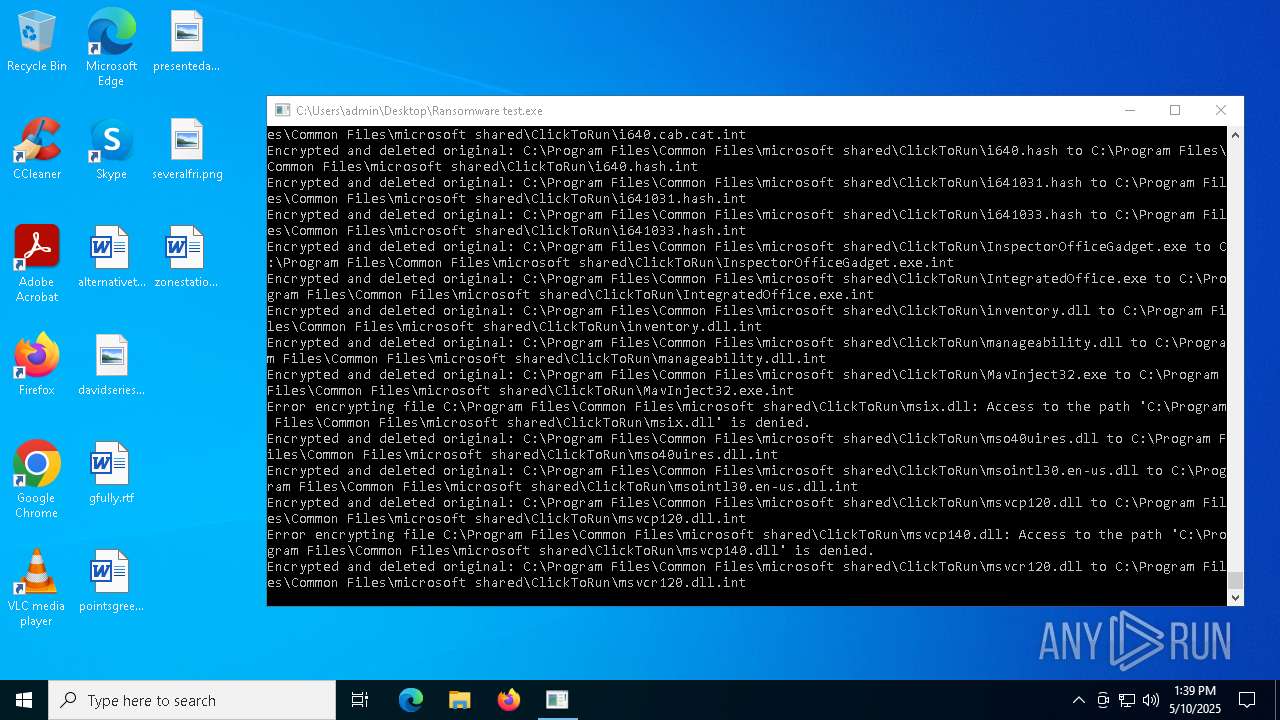
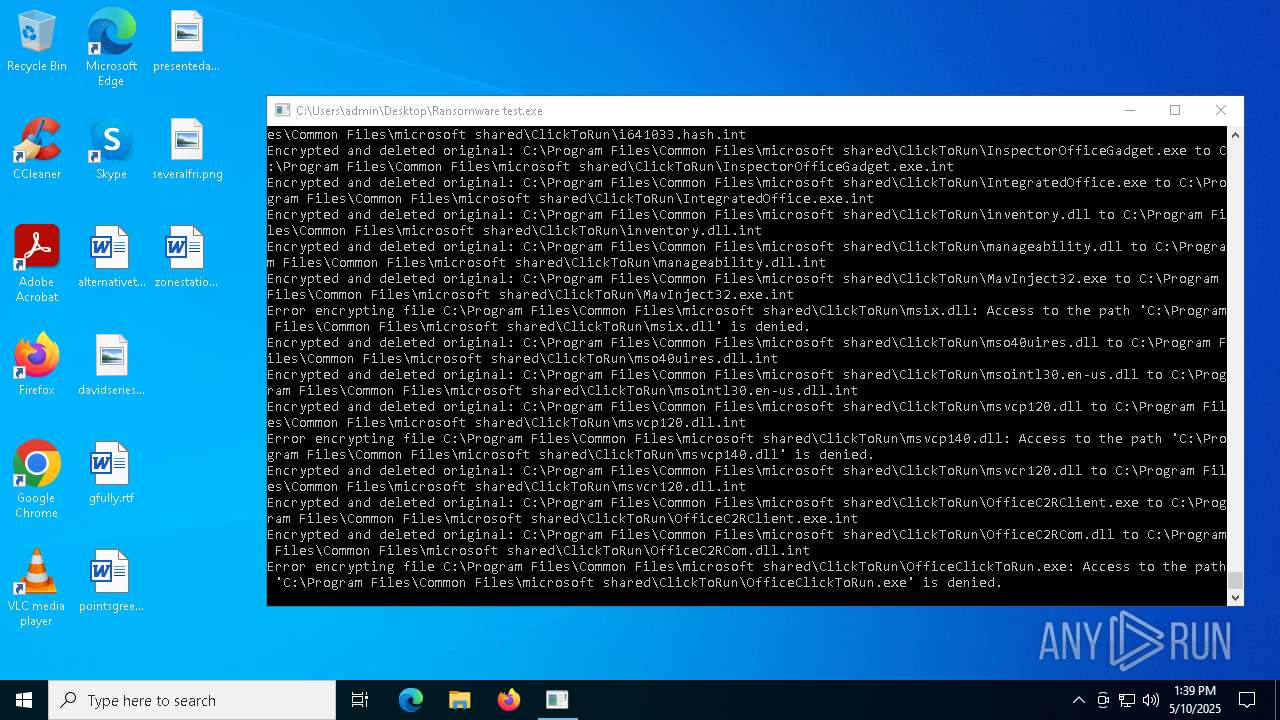
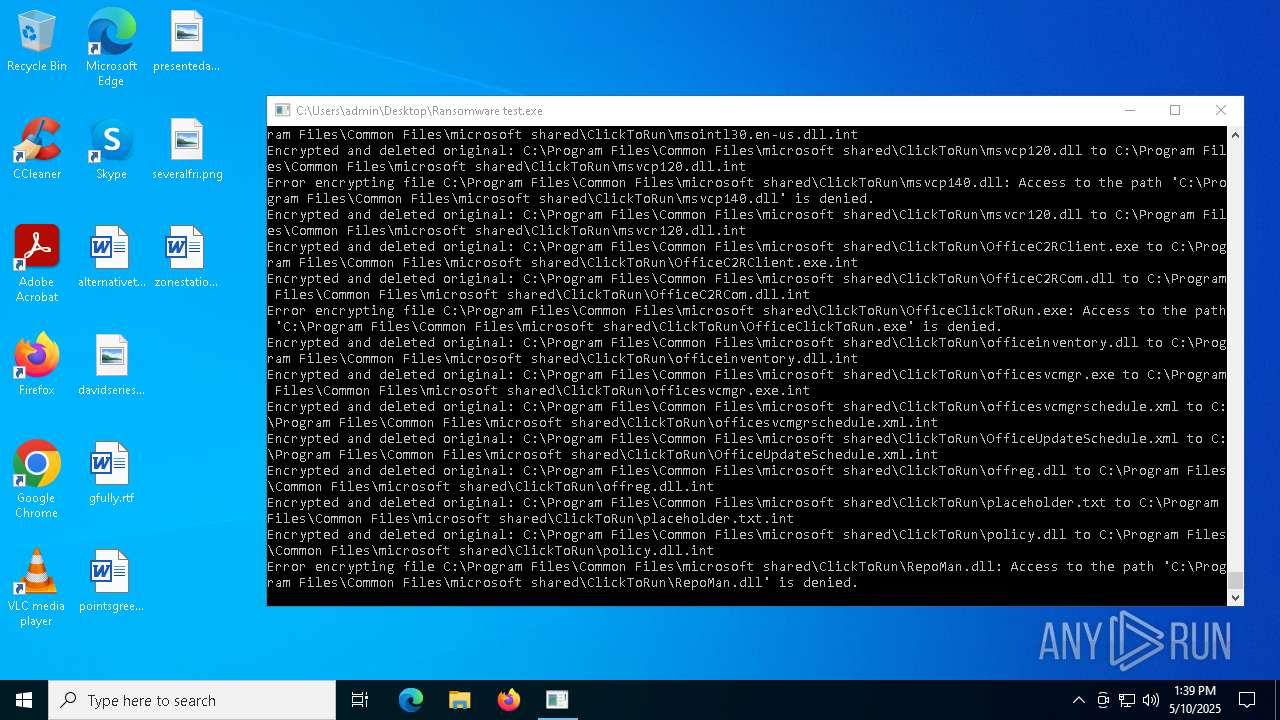
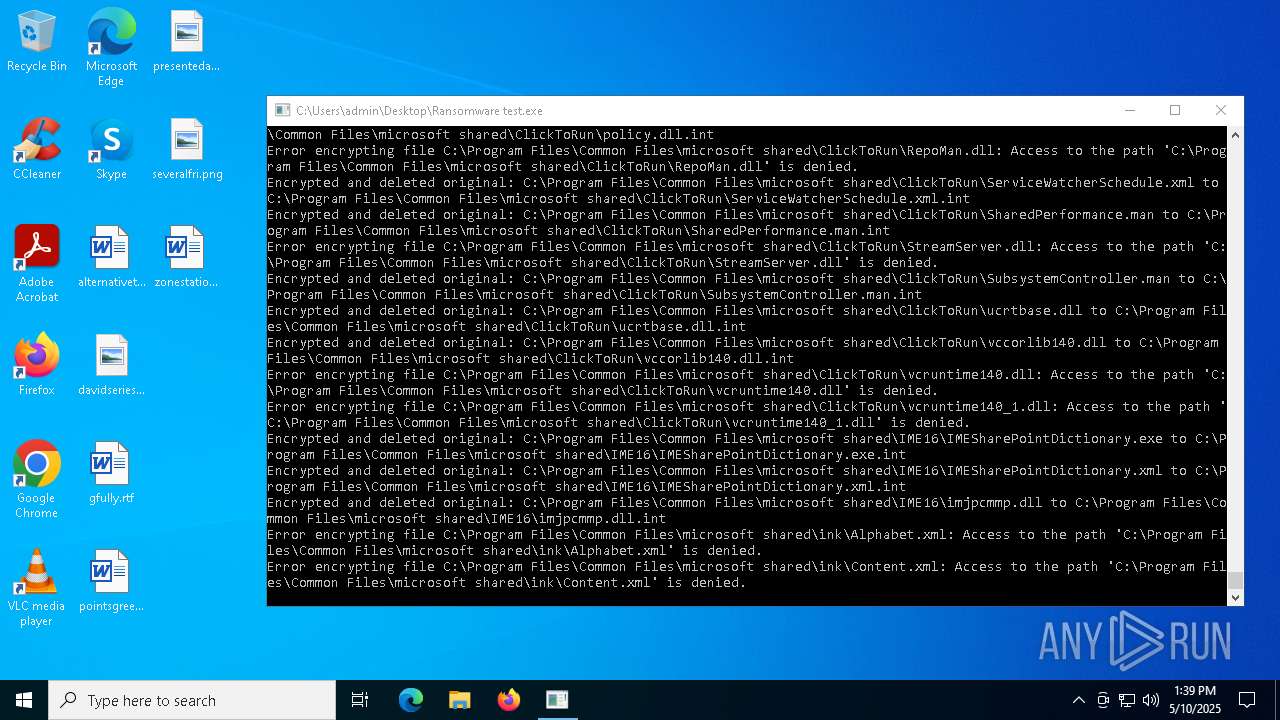
MALICIOUS
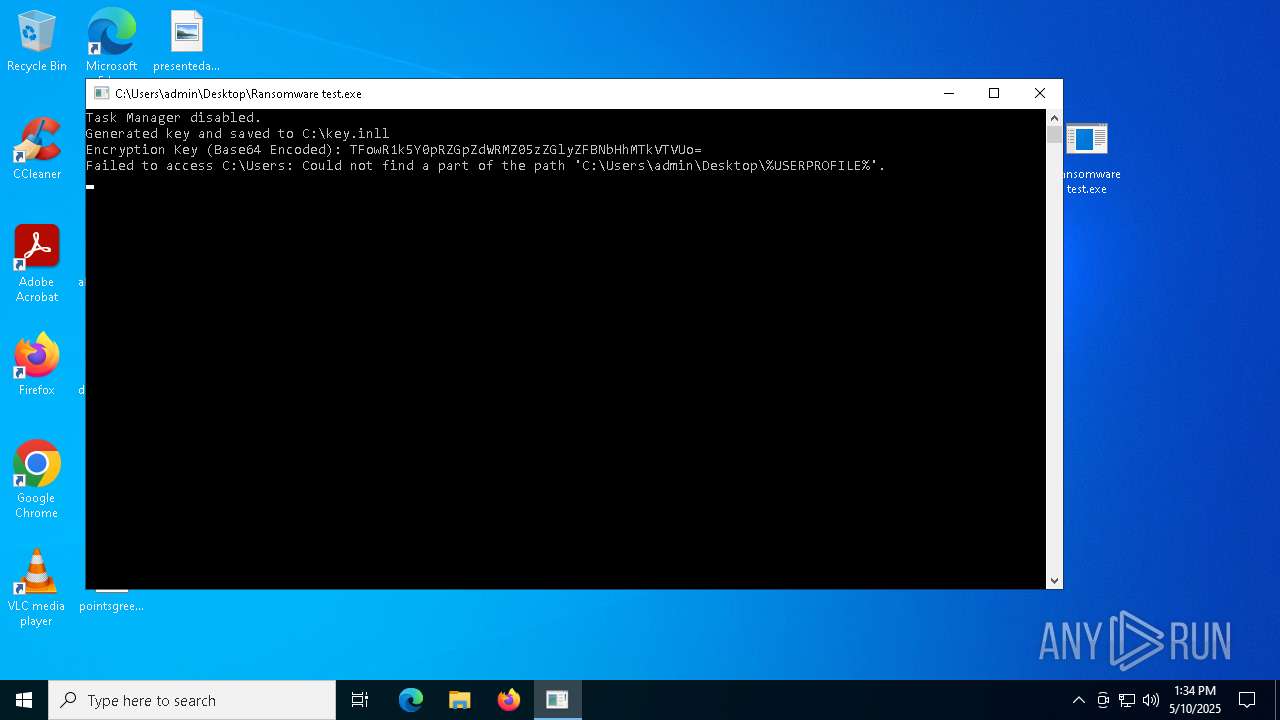
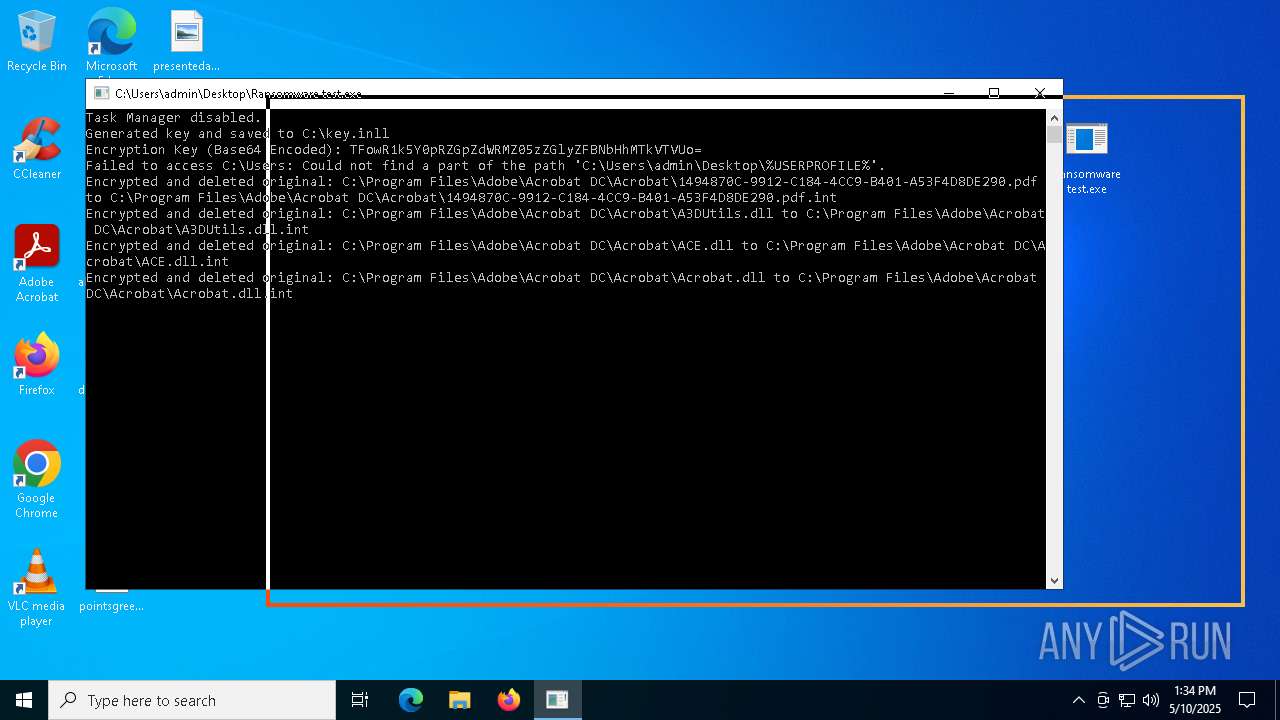
Disables task manager
- Ransomware test.exe (PID: 8172)
SUSPICIOUS
The process checks if it is being run in the virtual environment
- WinRAR.exe (PID: 7516)
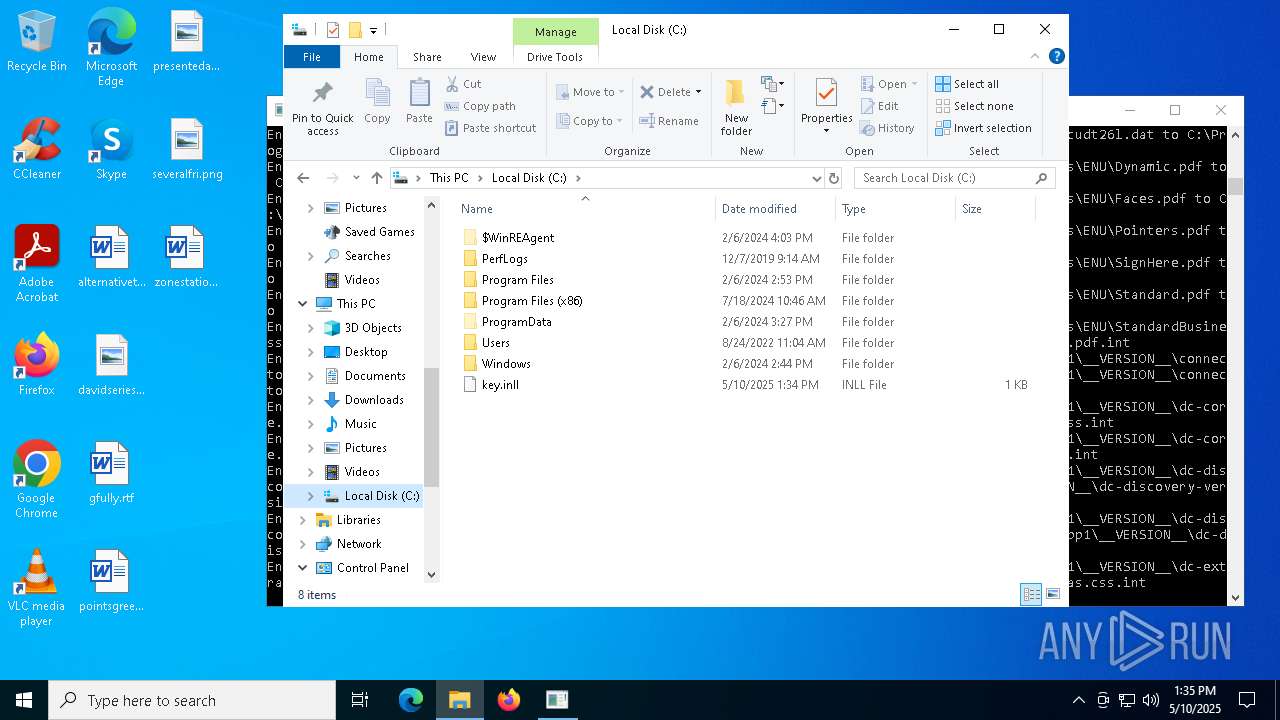
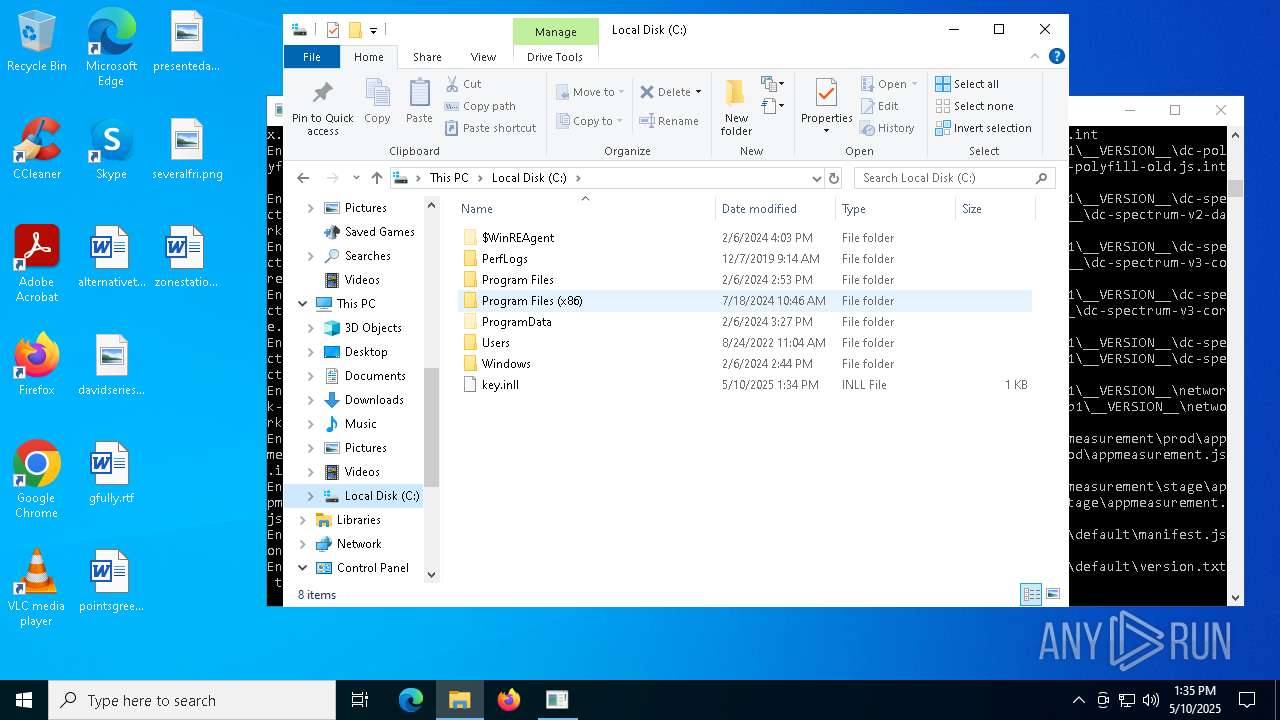
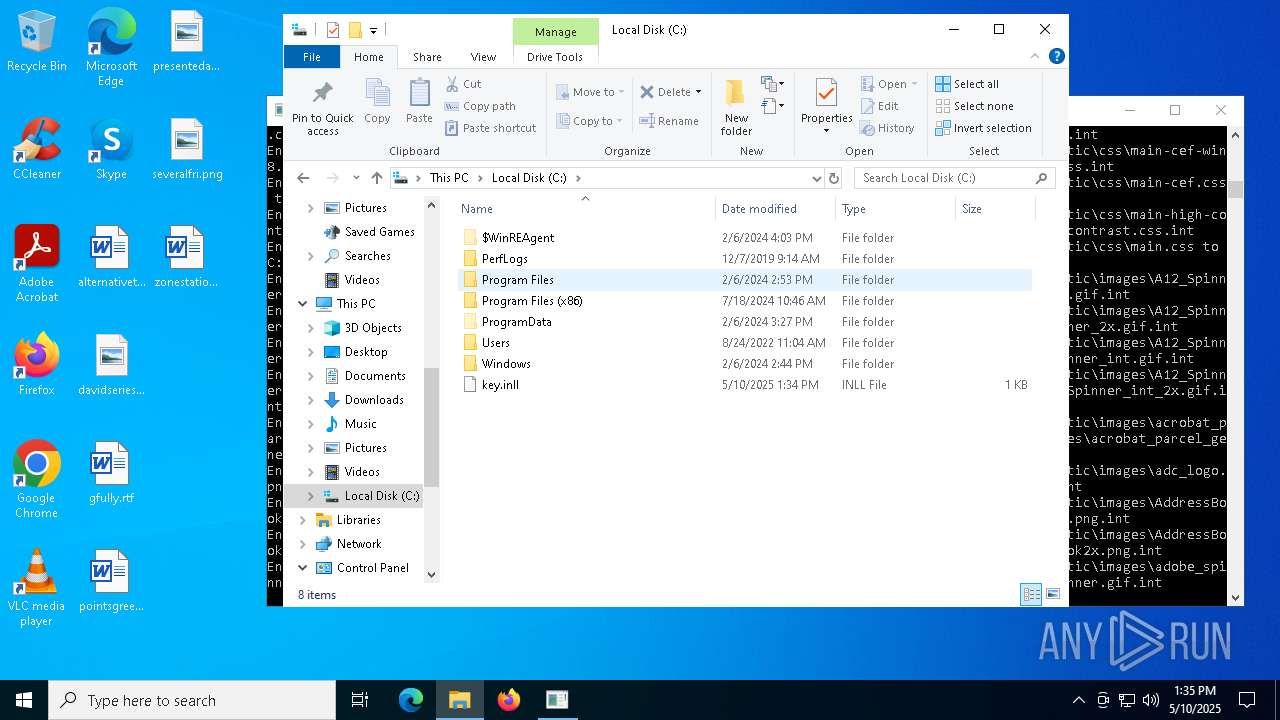
Creates file in the systems drive root
- Ransomware test.exe (PID: 8172)
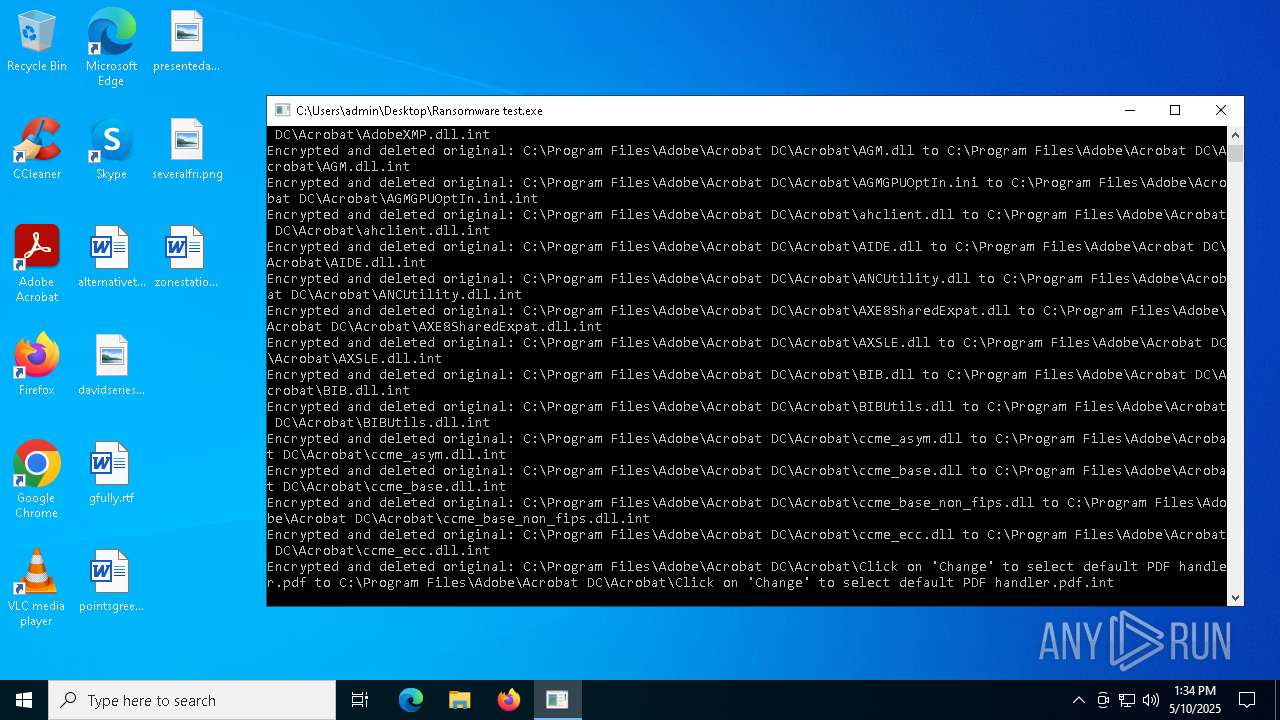
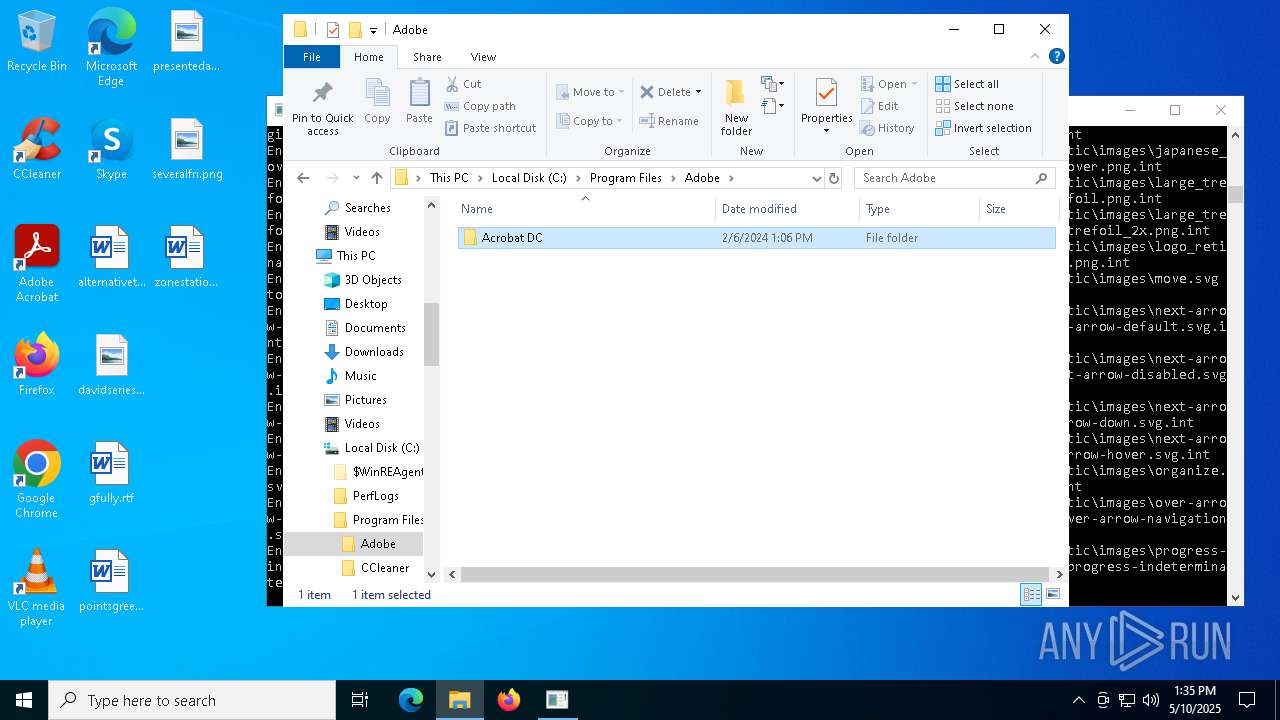
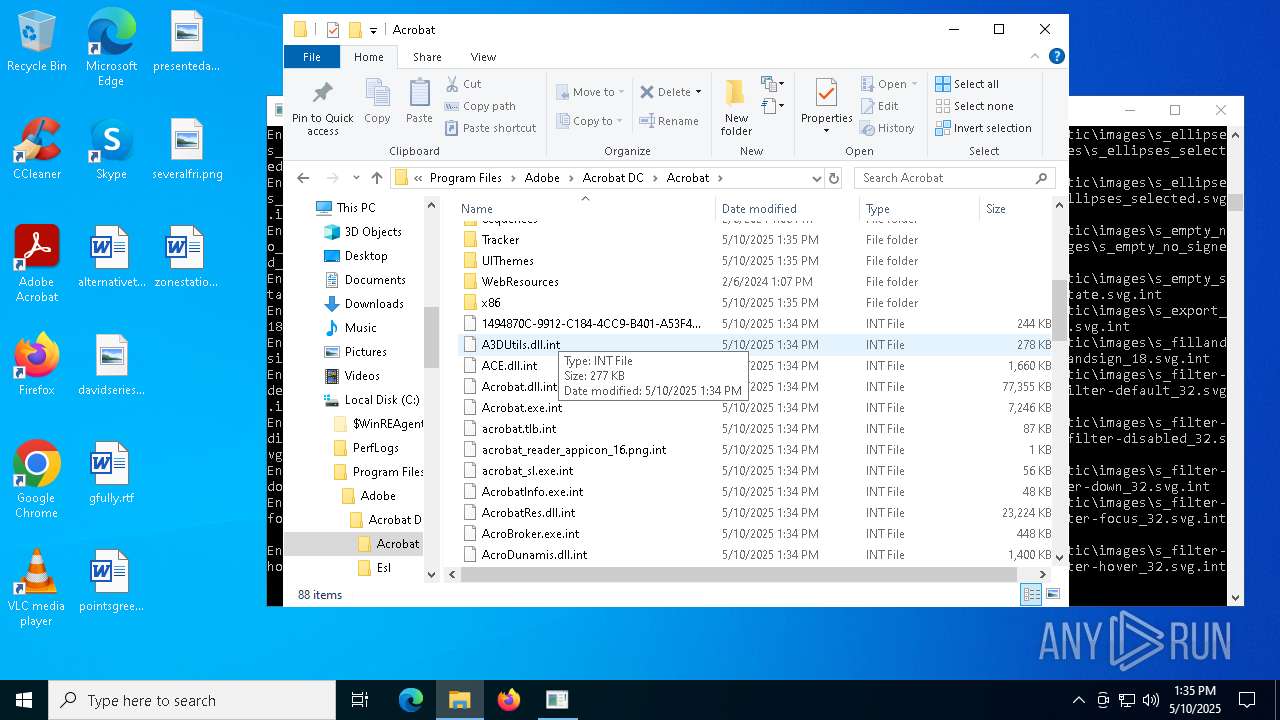
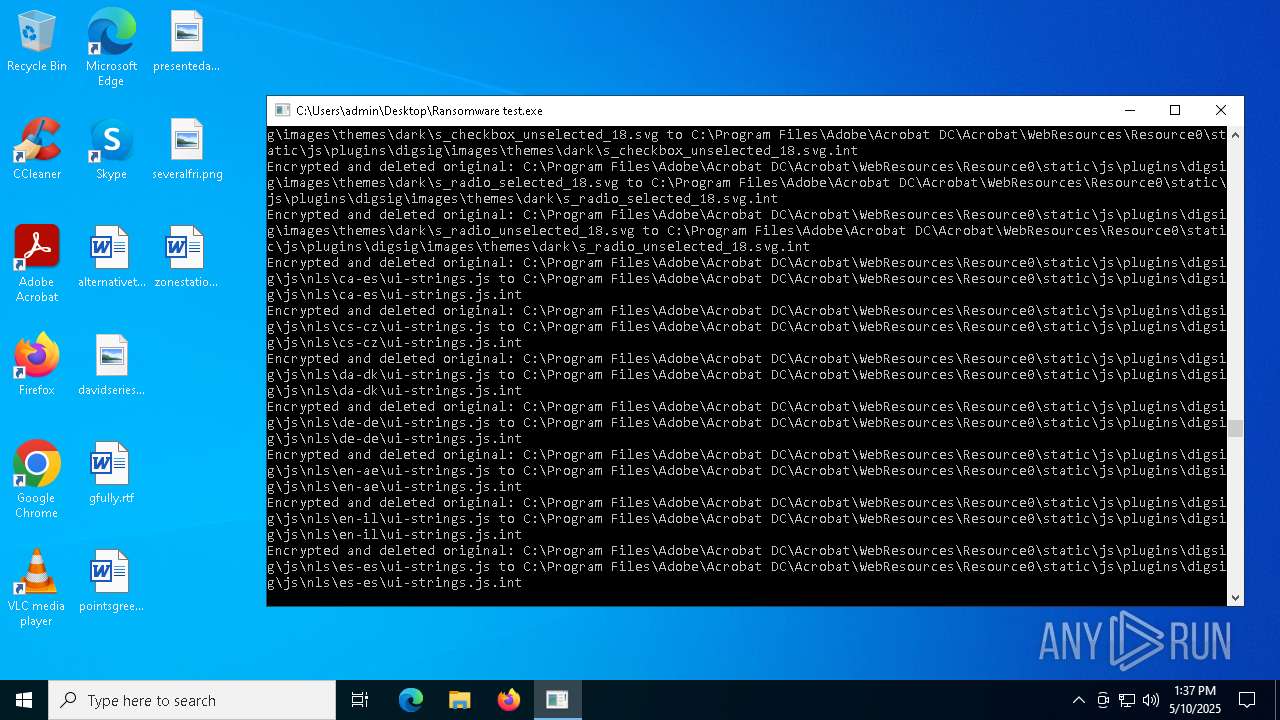
The process creates files with name similar to system file names
- Ransomware test.exe (PID: 8172)
INFO
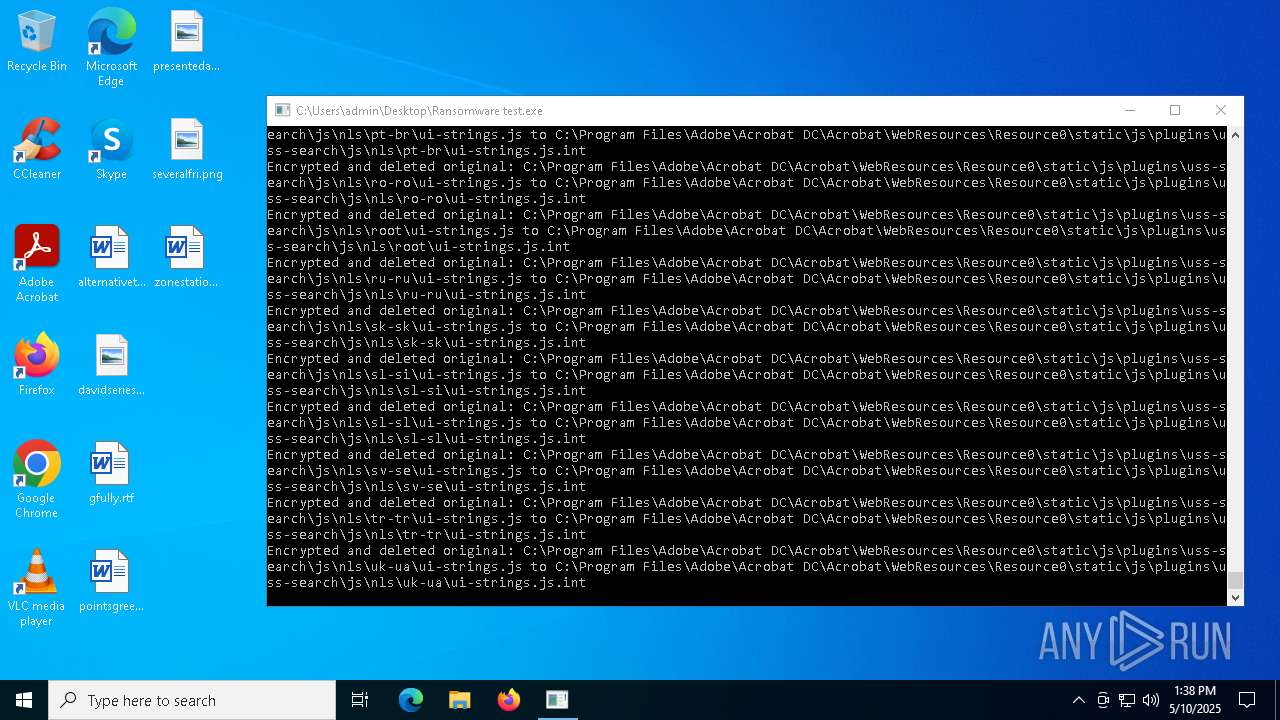
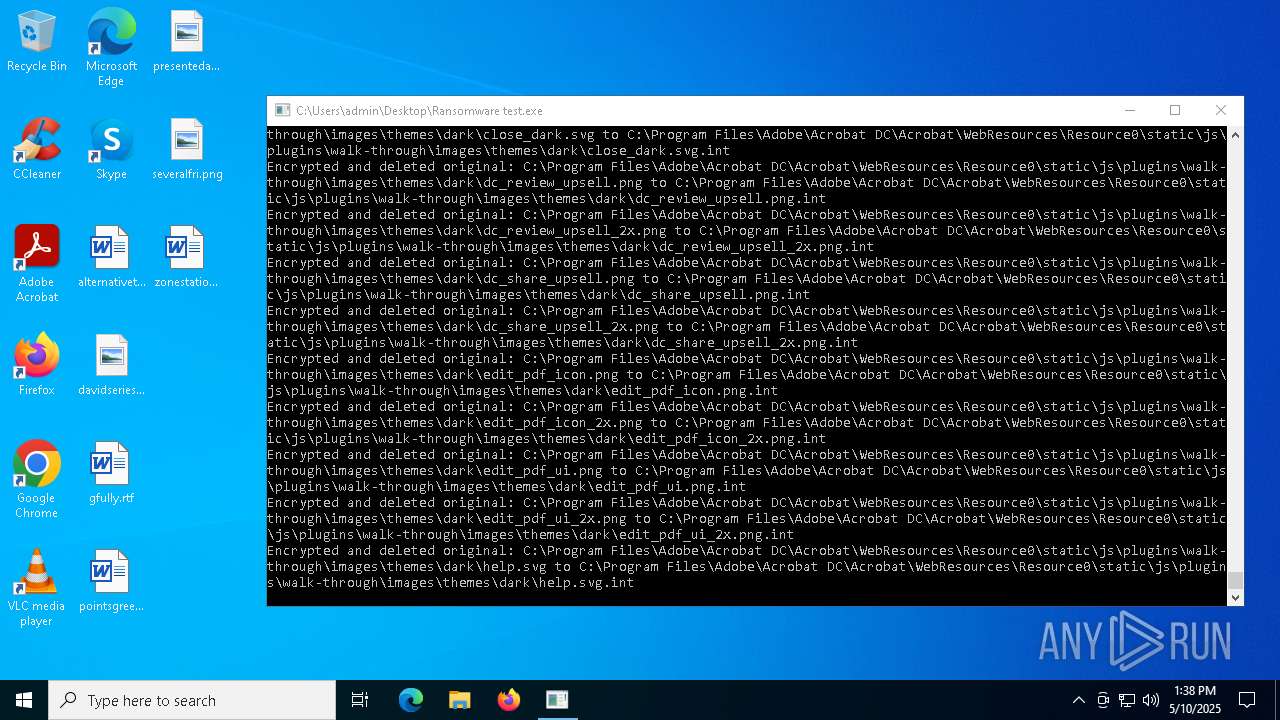
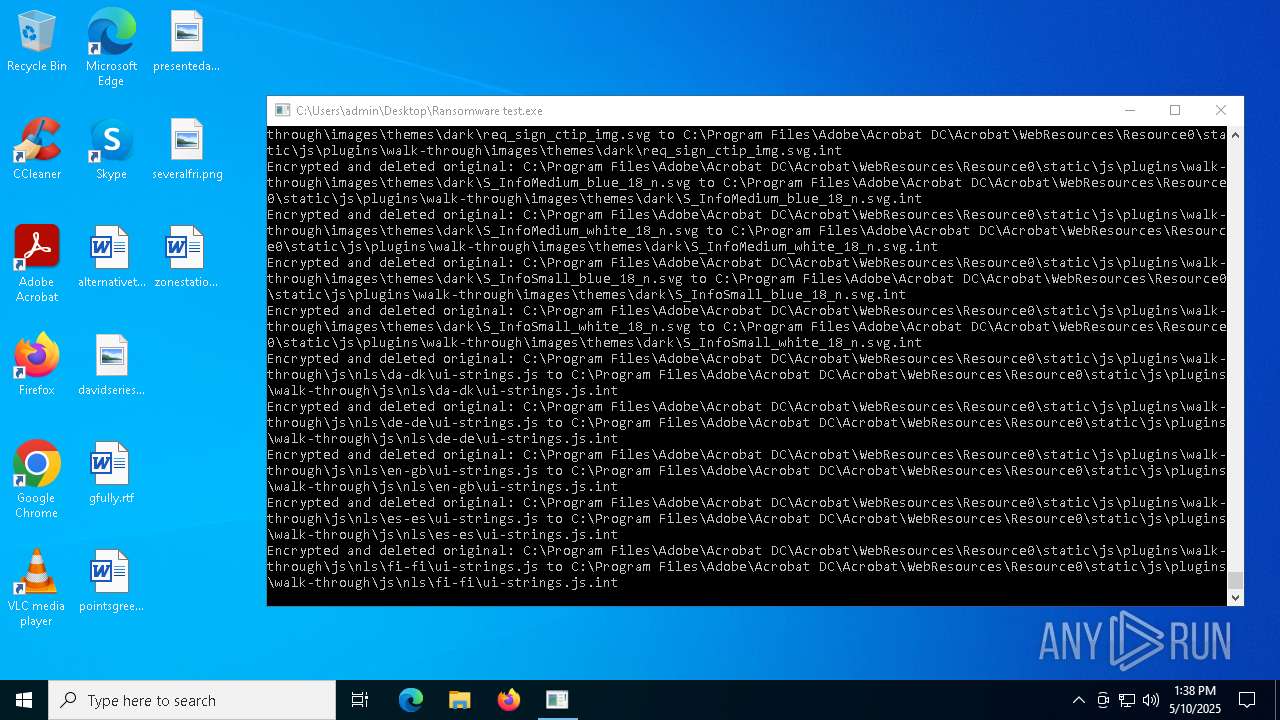
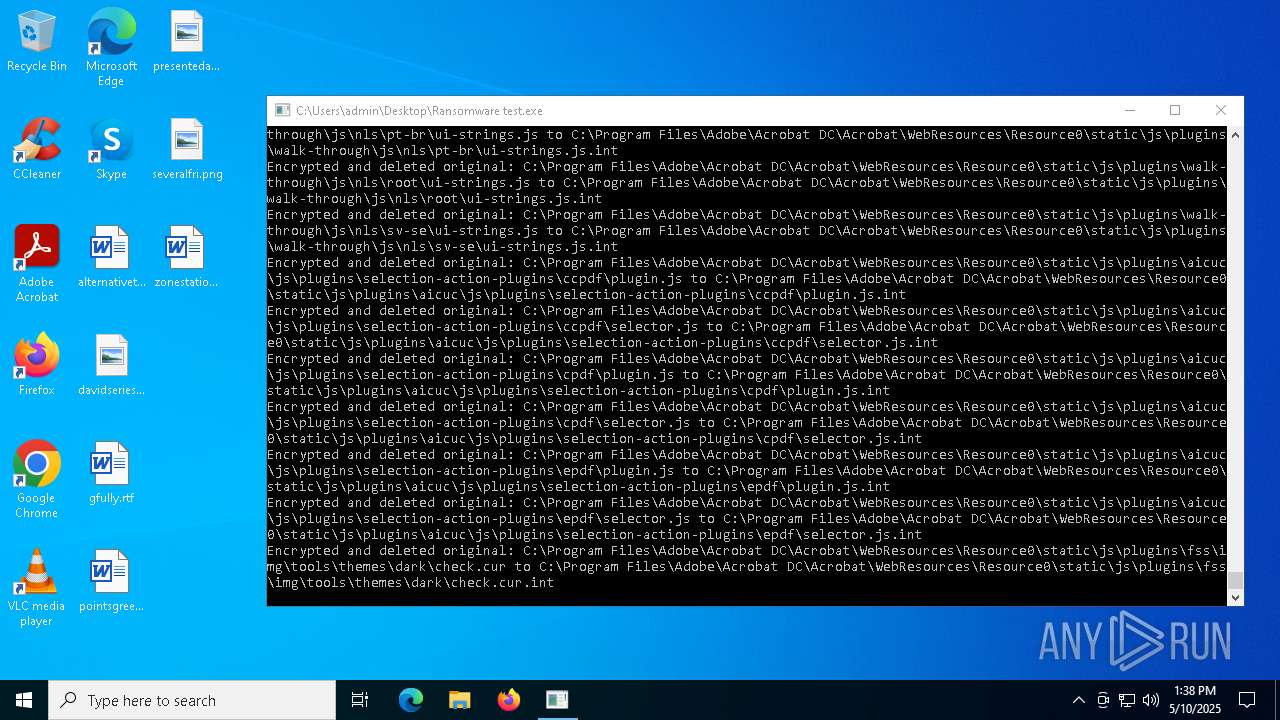
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7516)
Manual execution by a user
- Ransomware test.exe (PID: 8172)
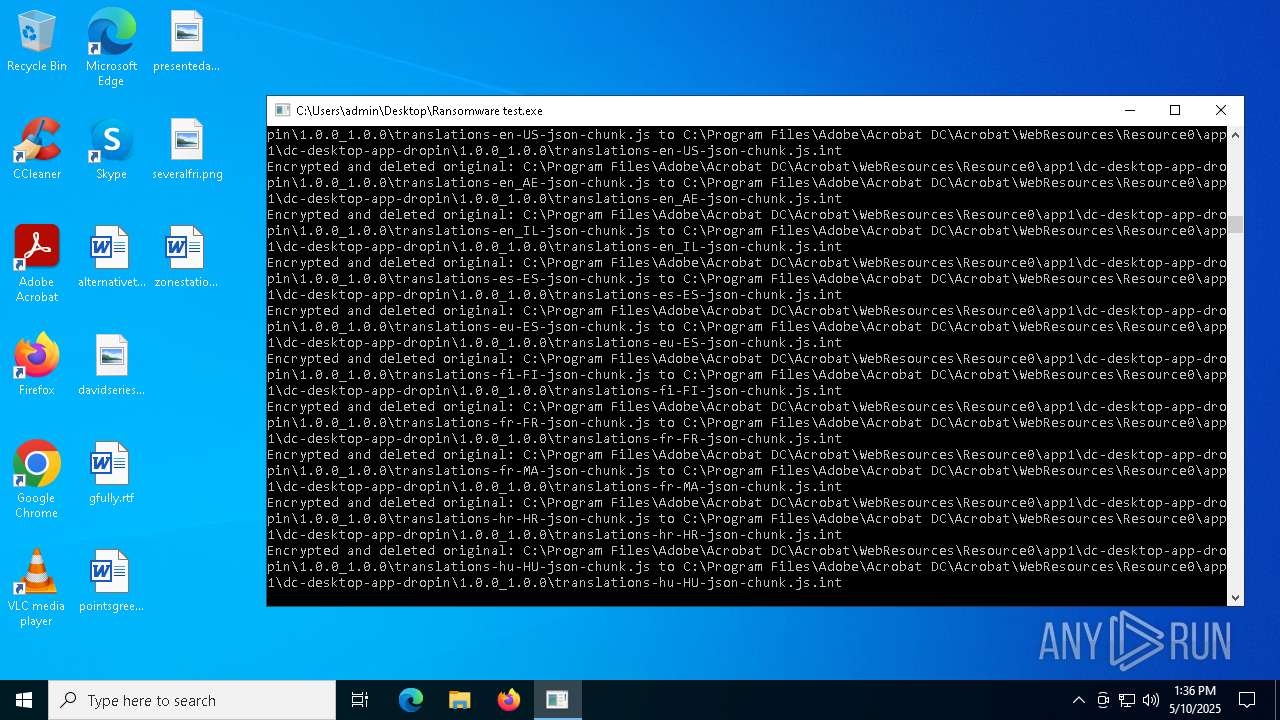
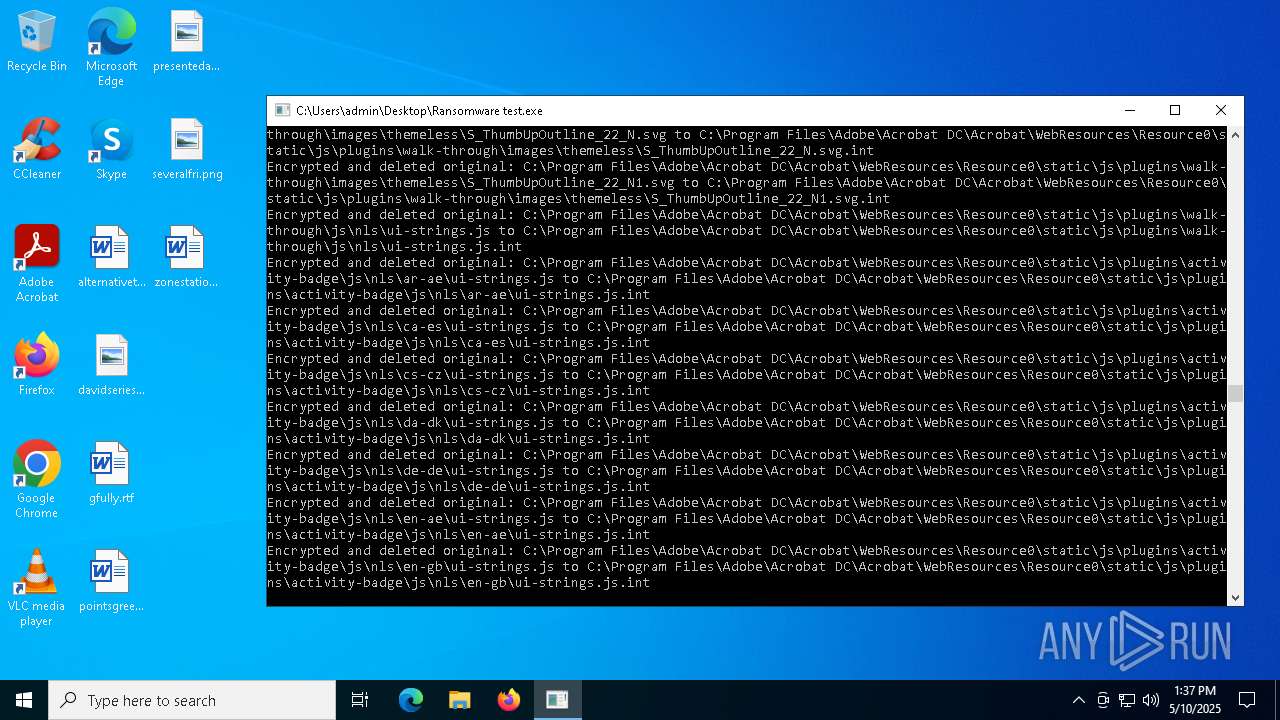
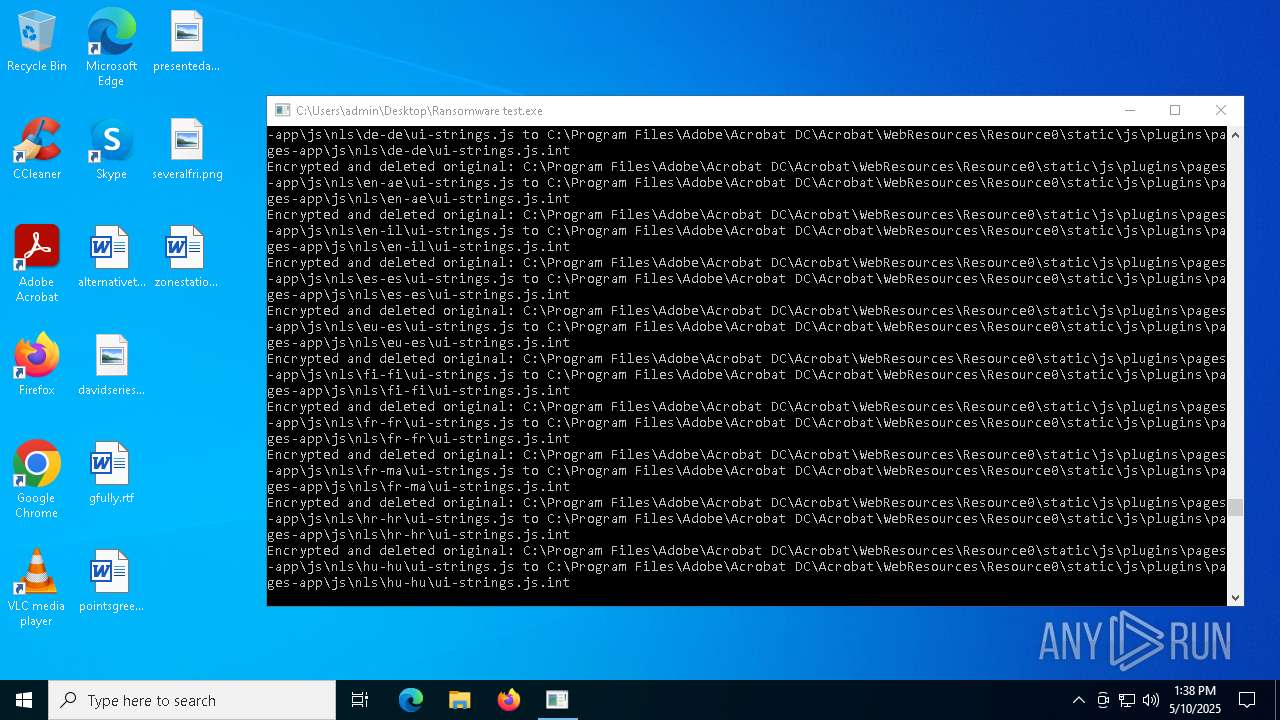
Checks supported languages
- Ransomware test.exe (PID: 8172)
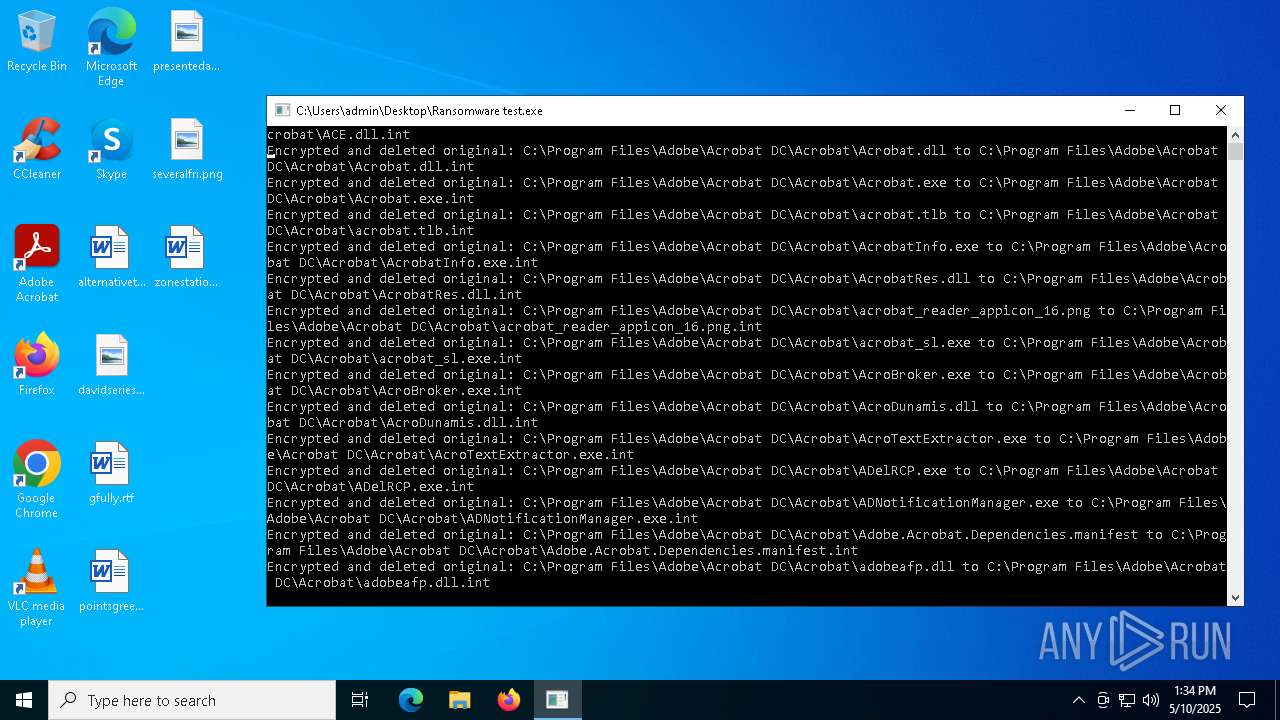
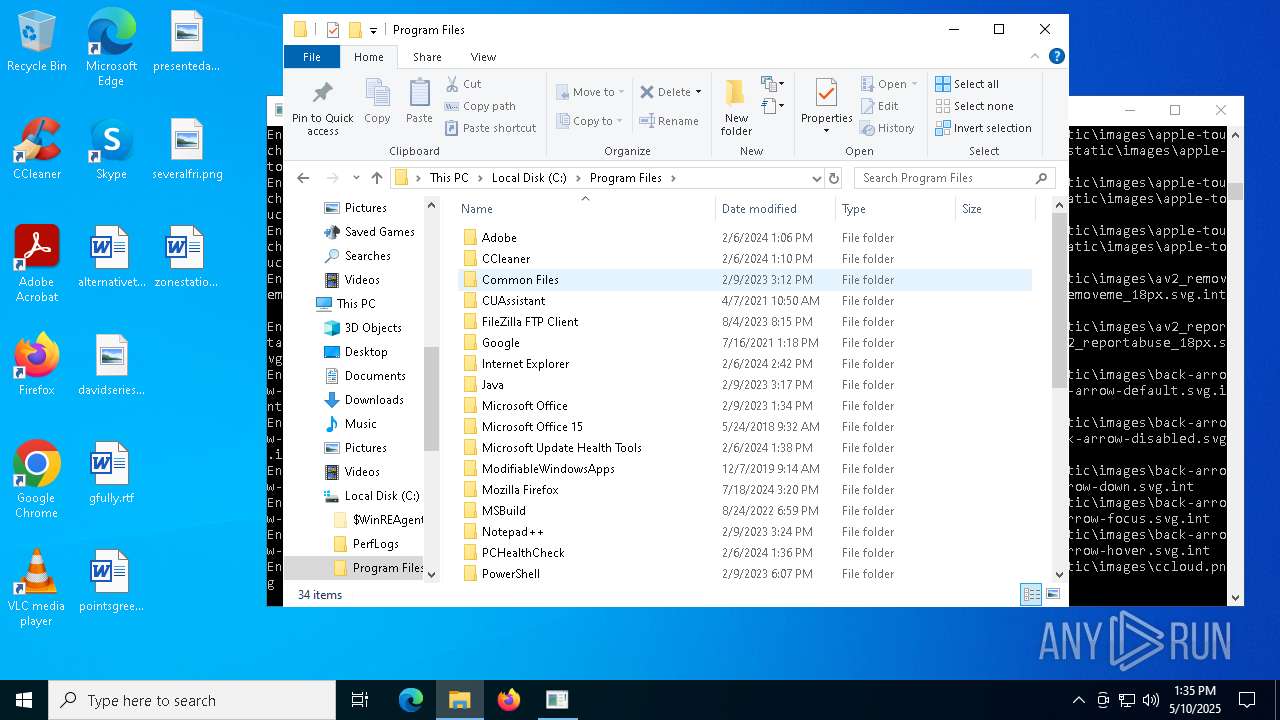
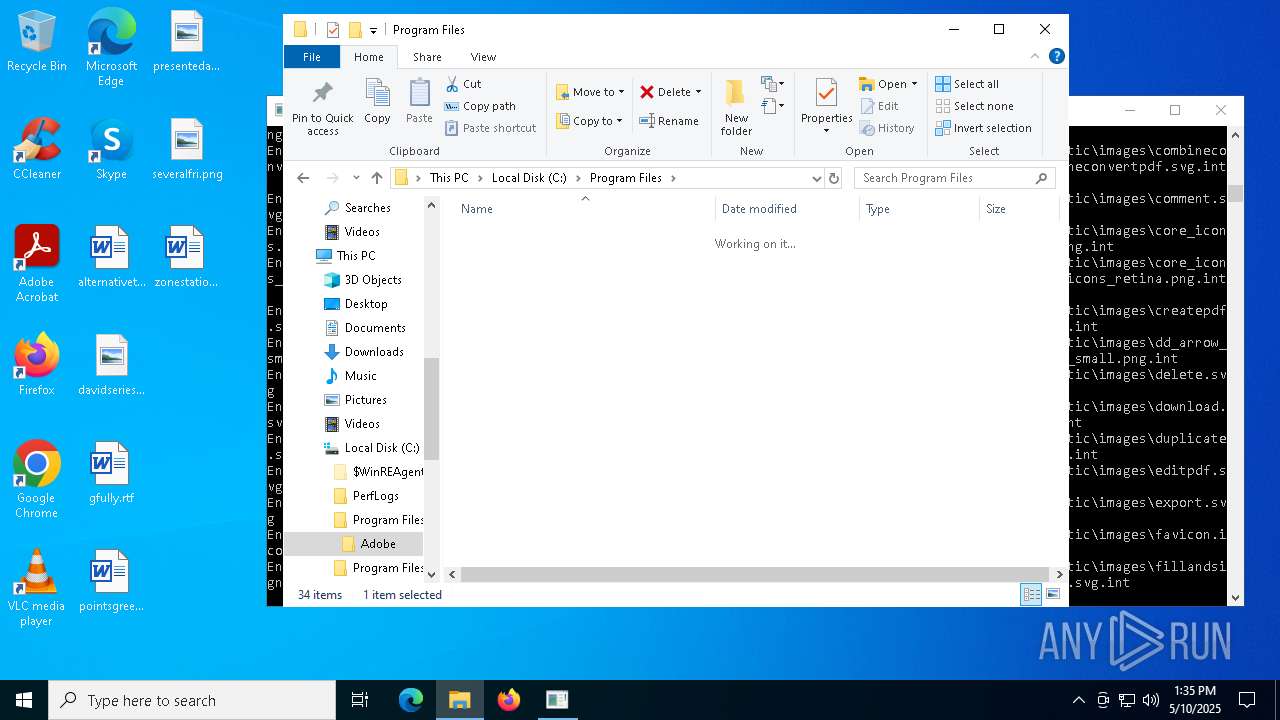
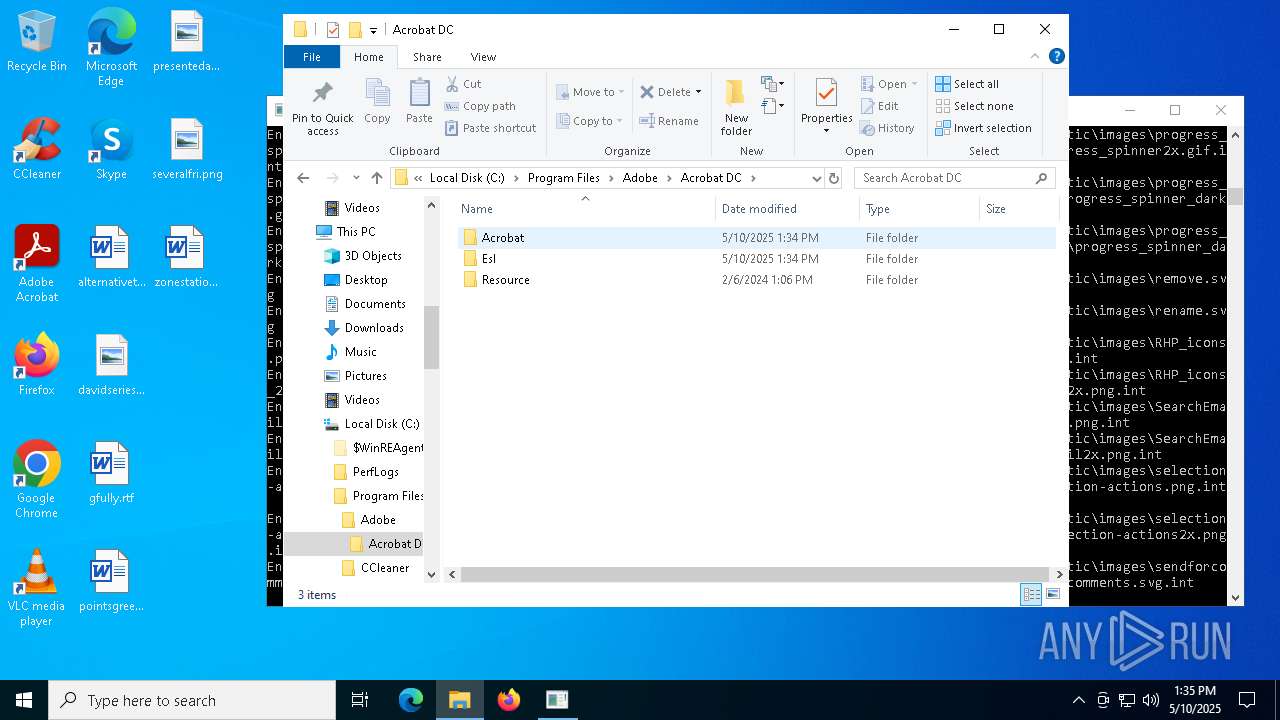
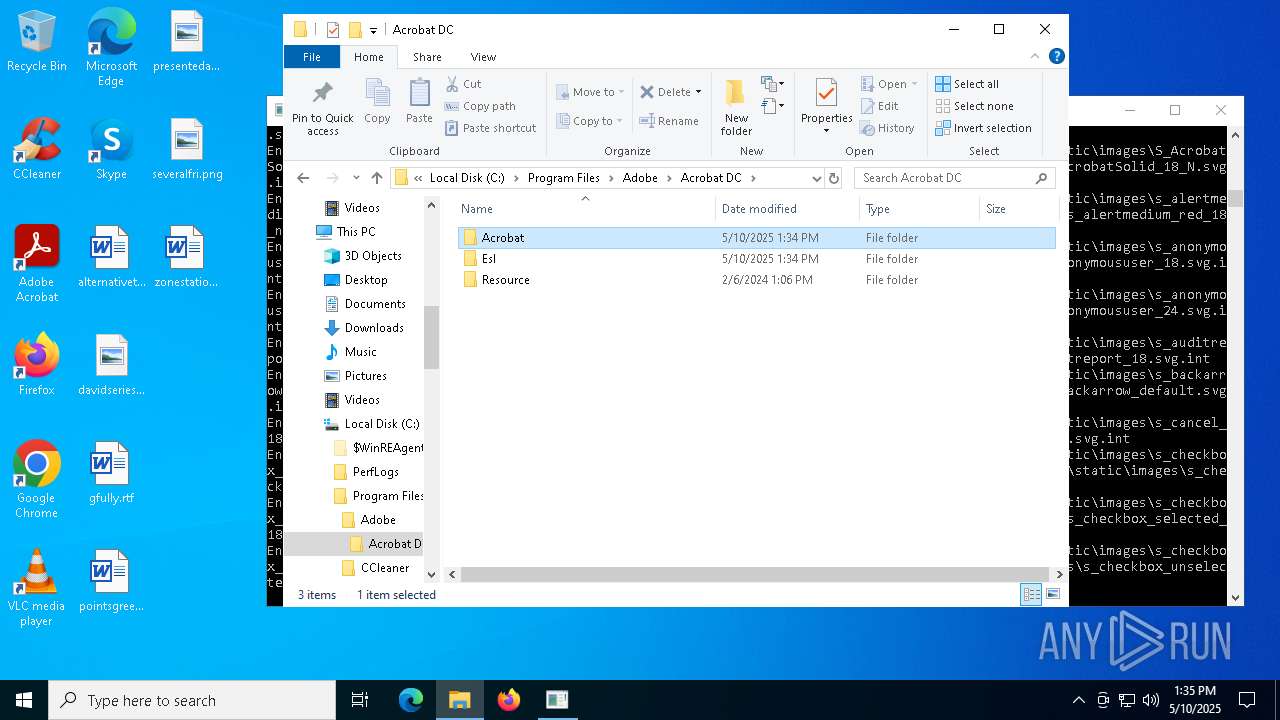
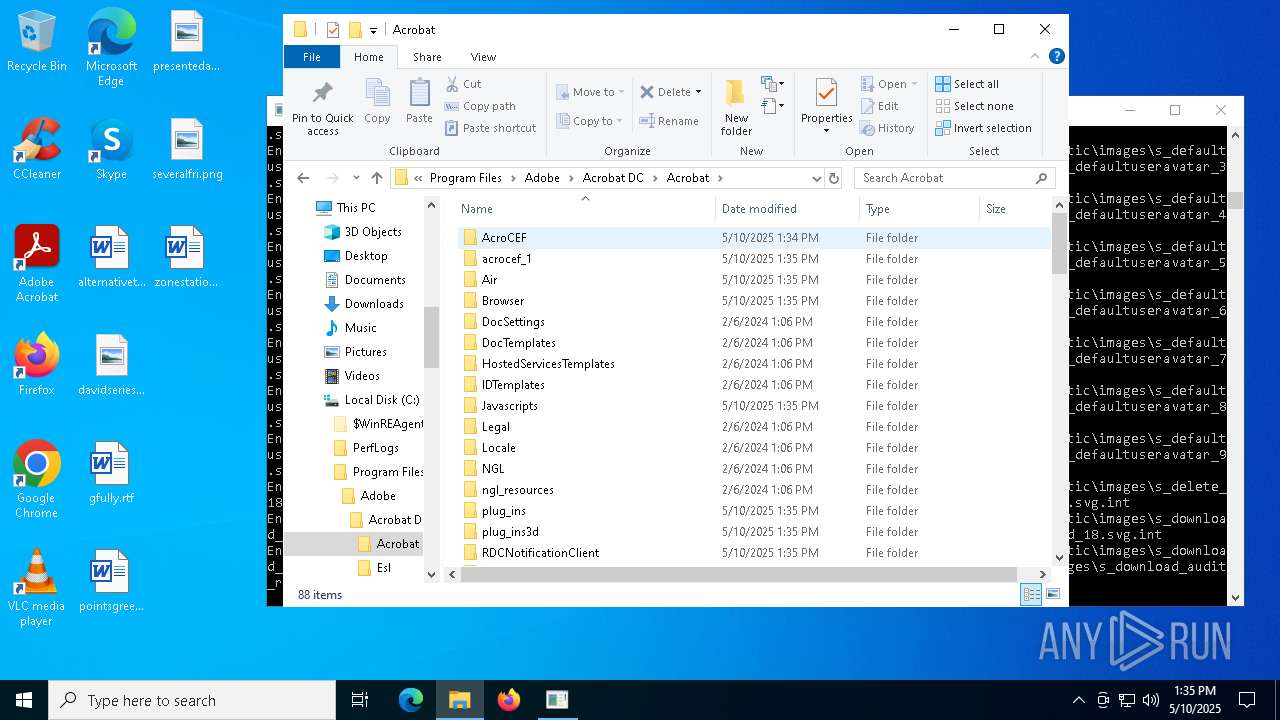
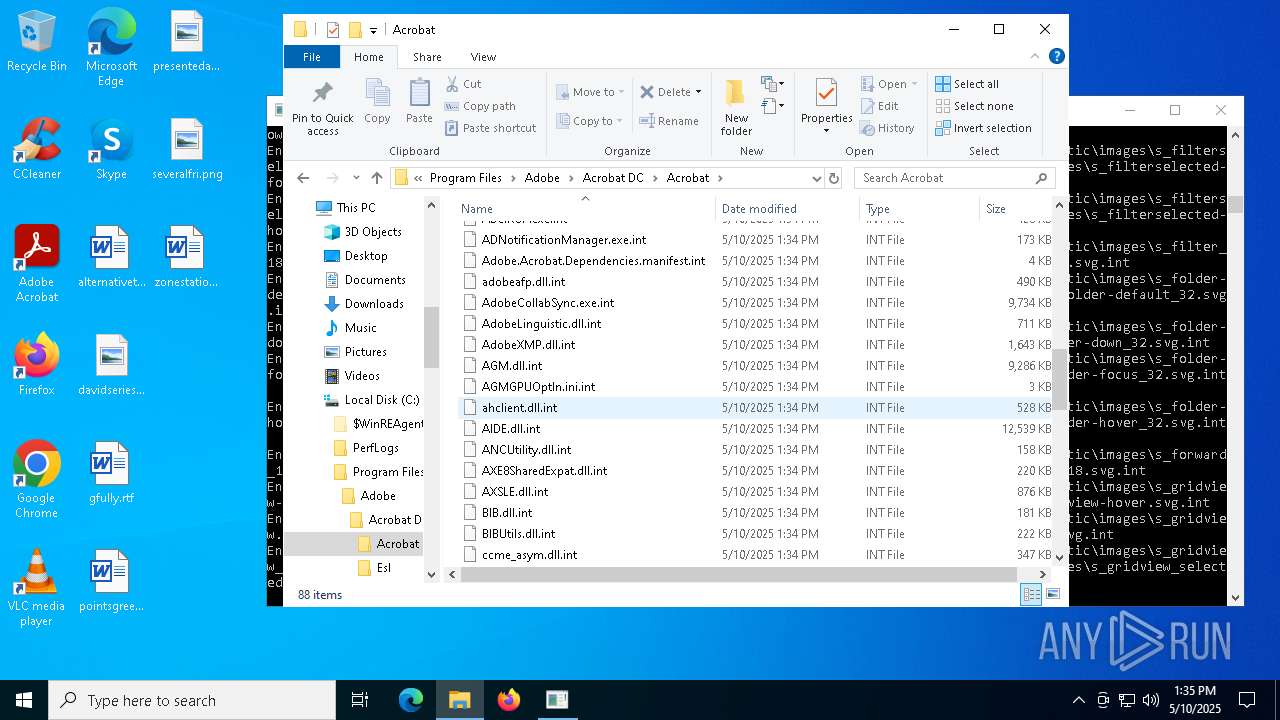
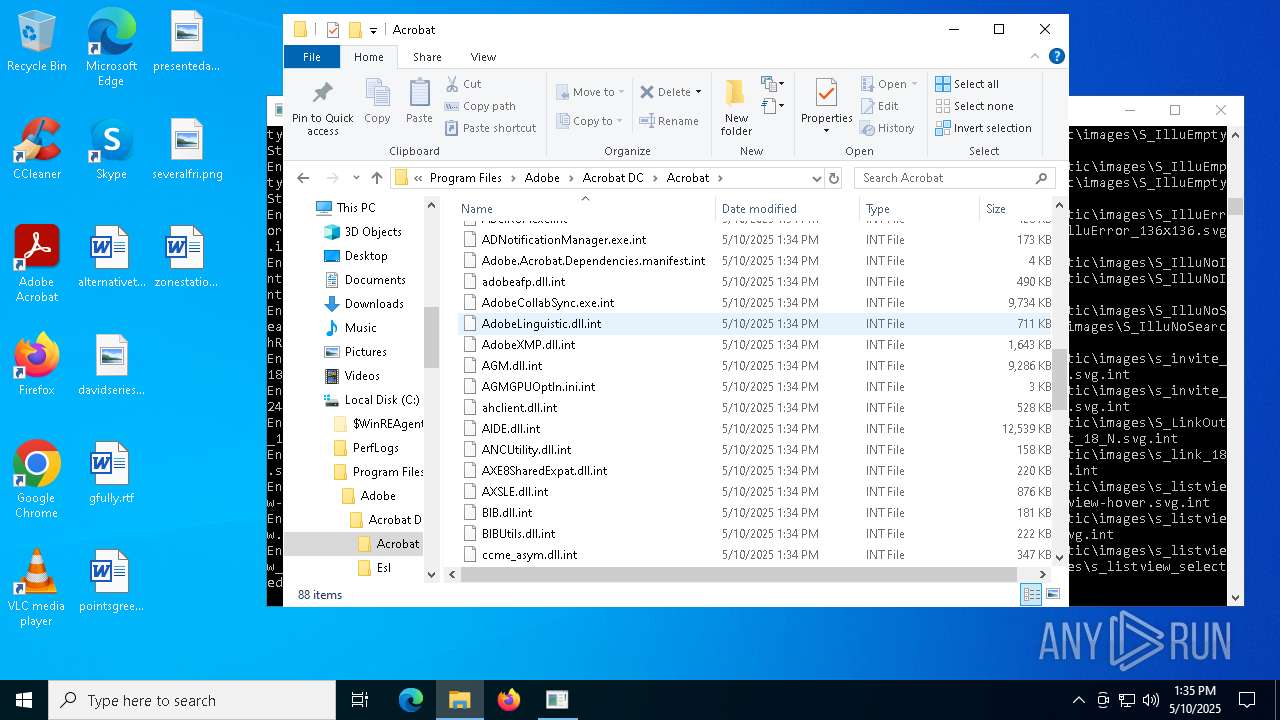
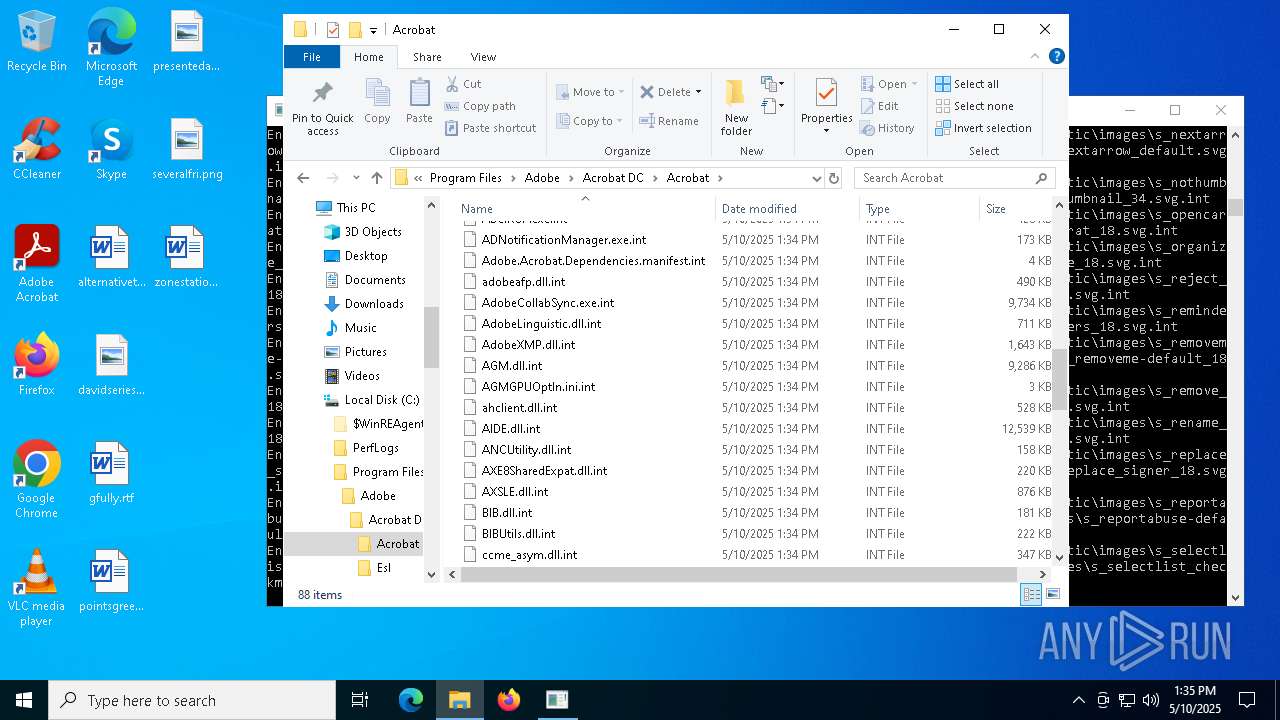
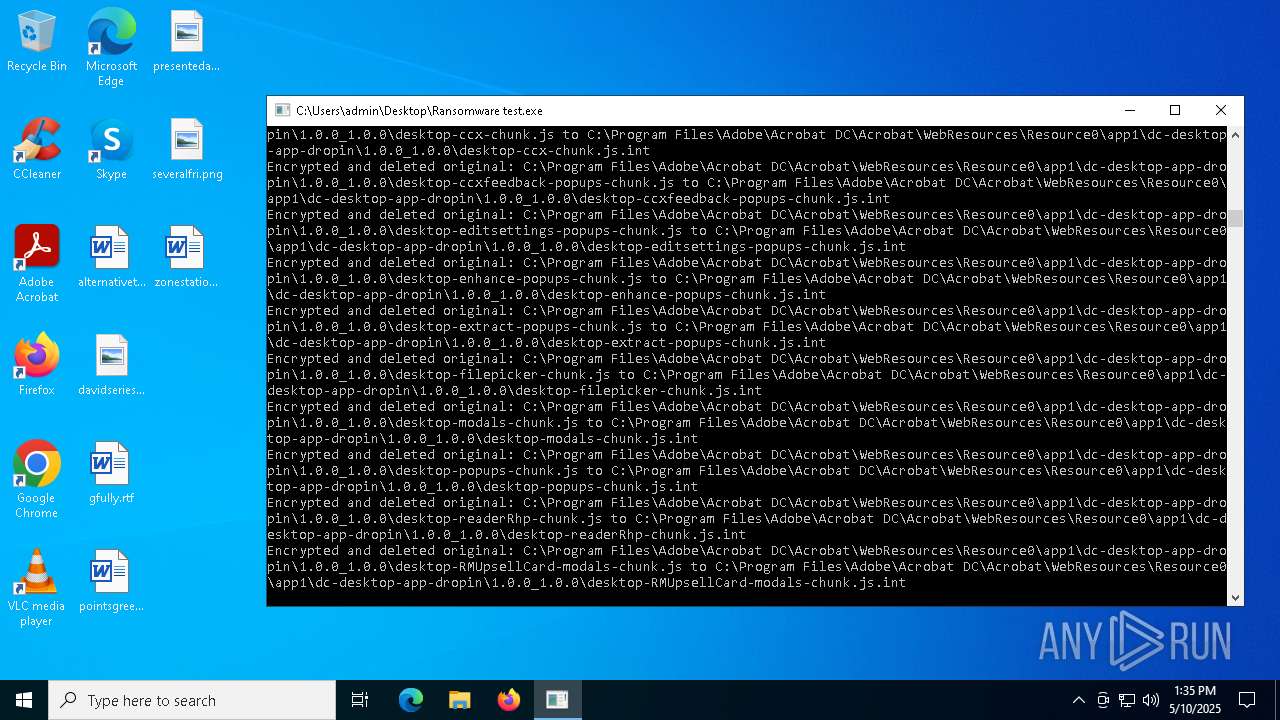
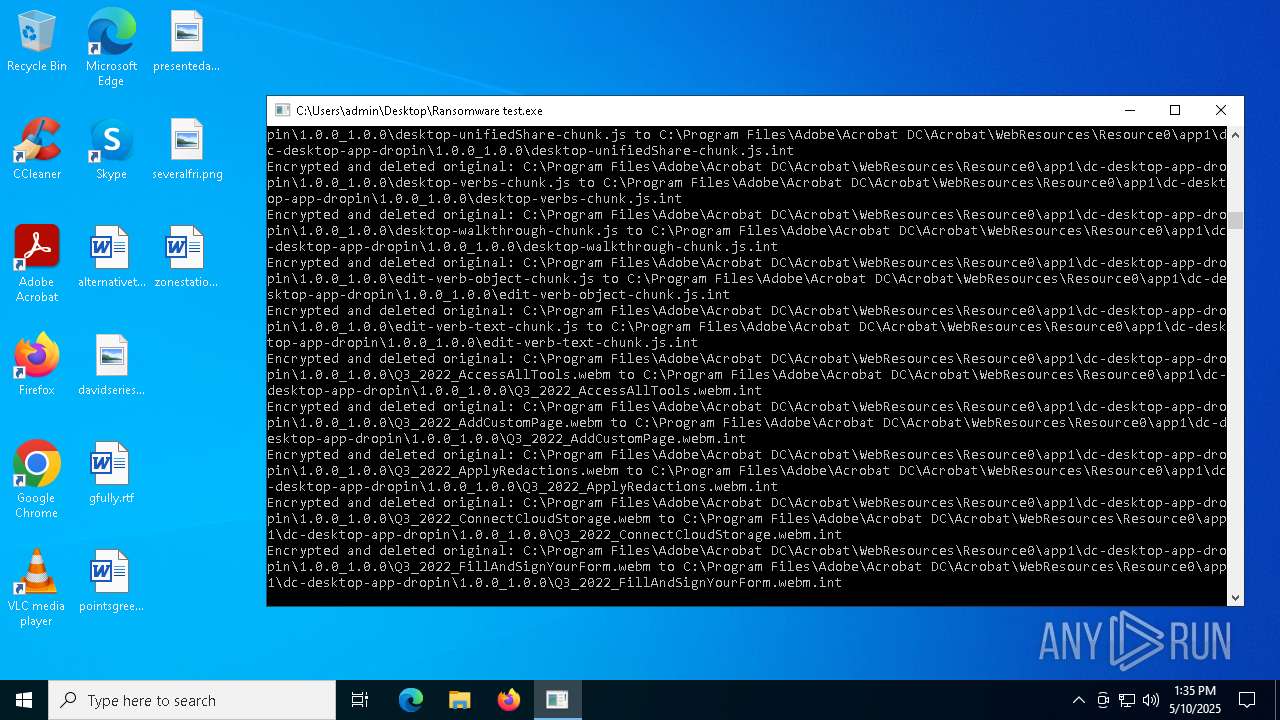
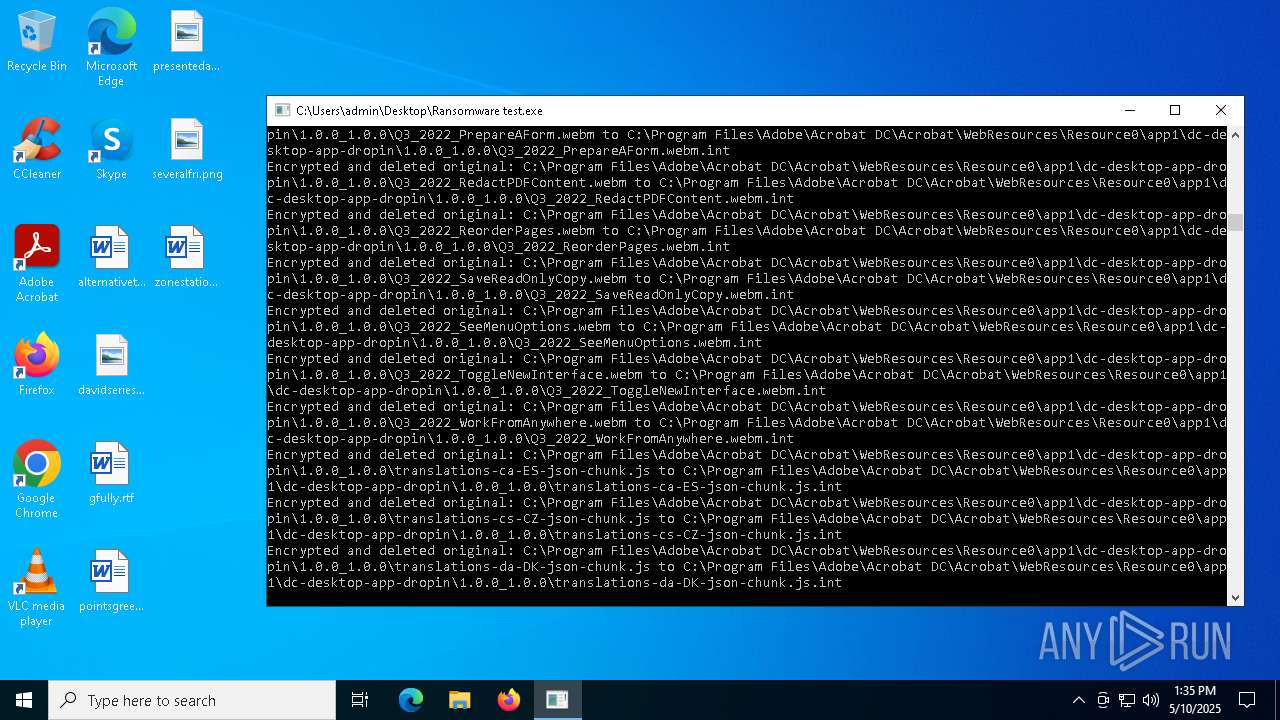
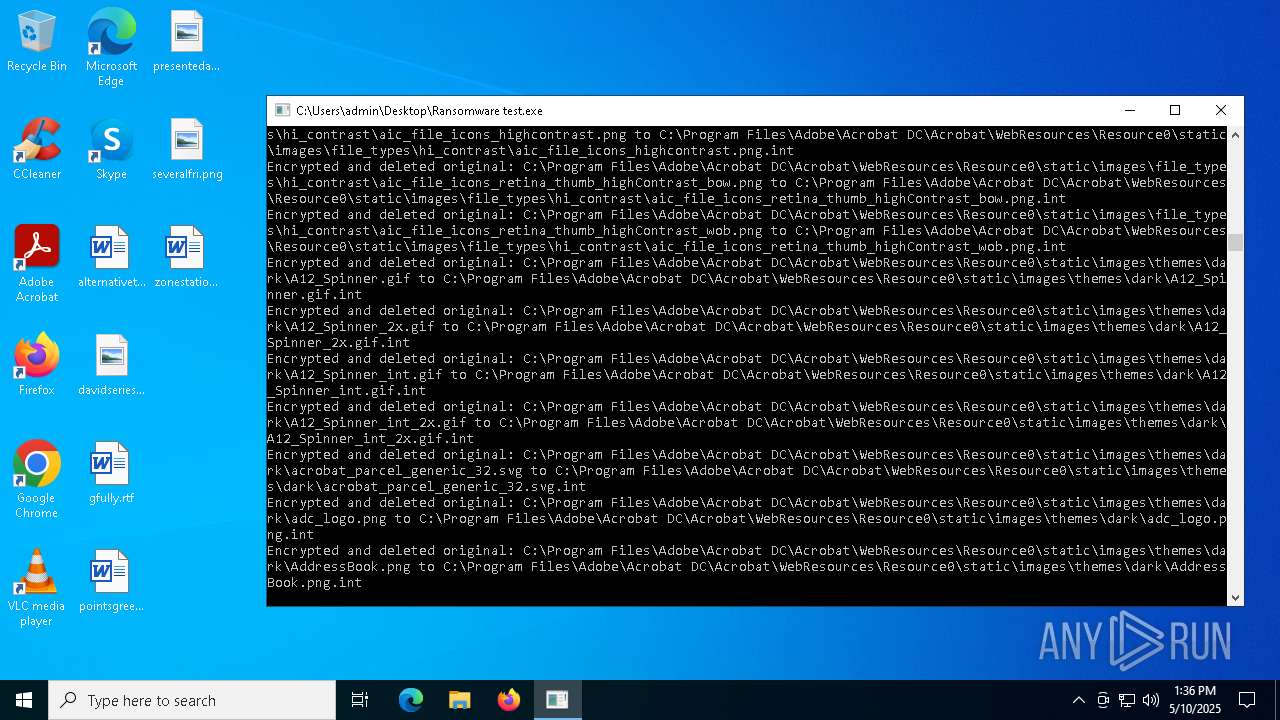
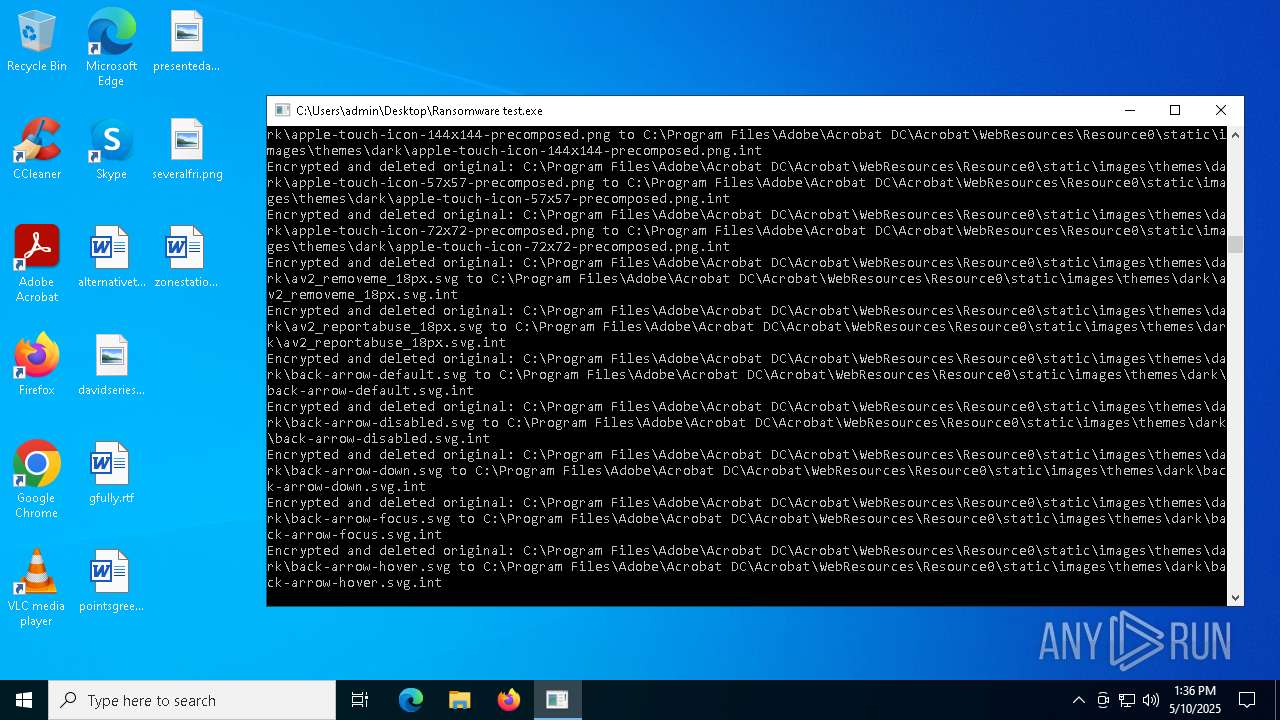
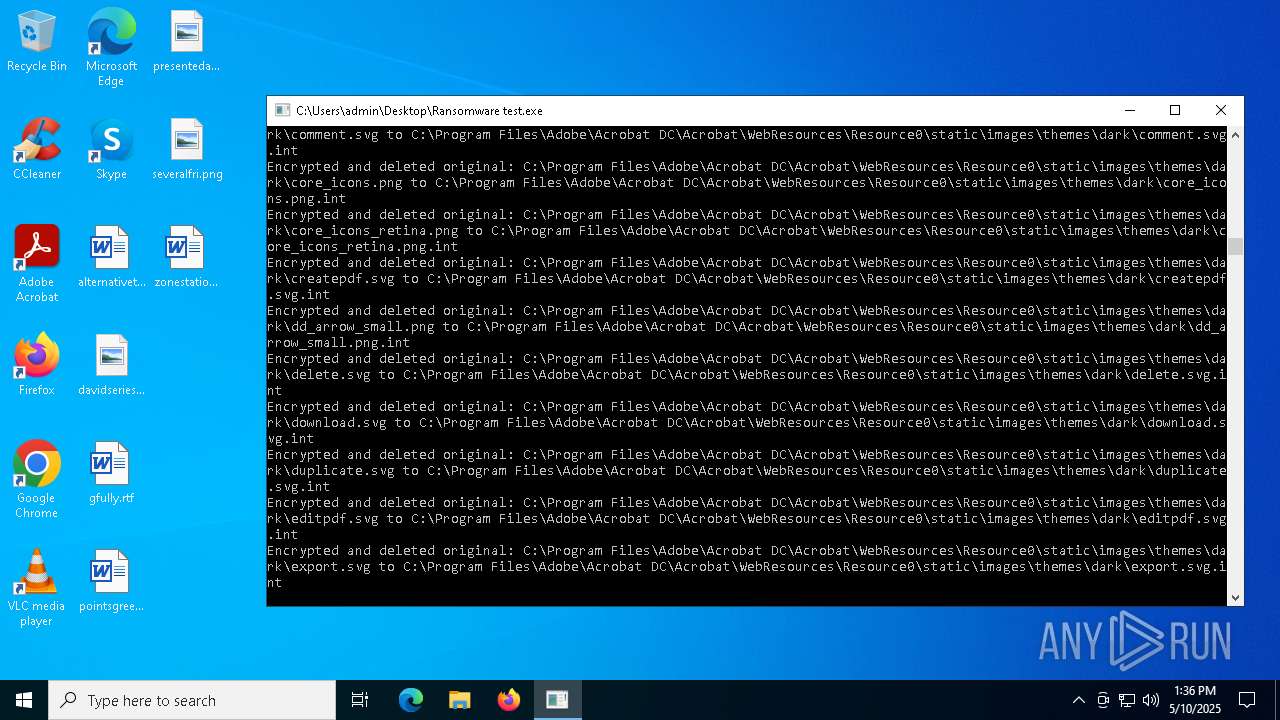
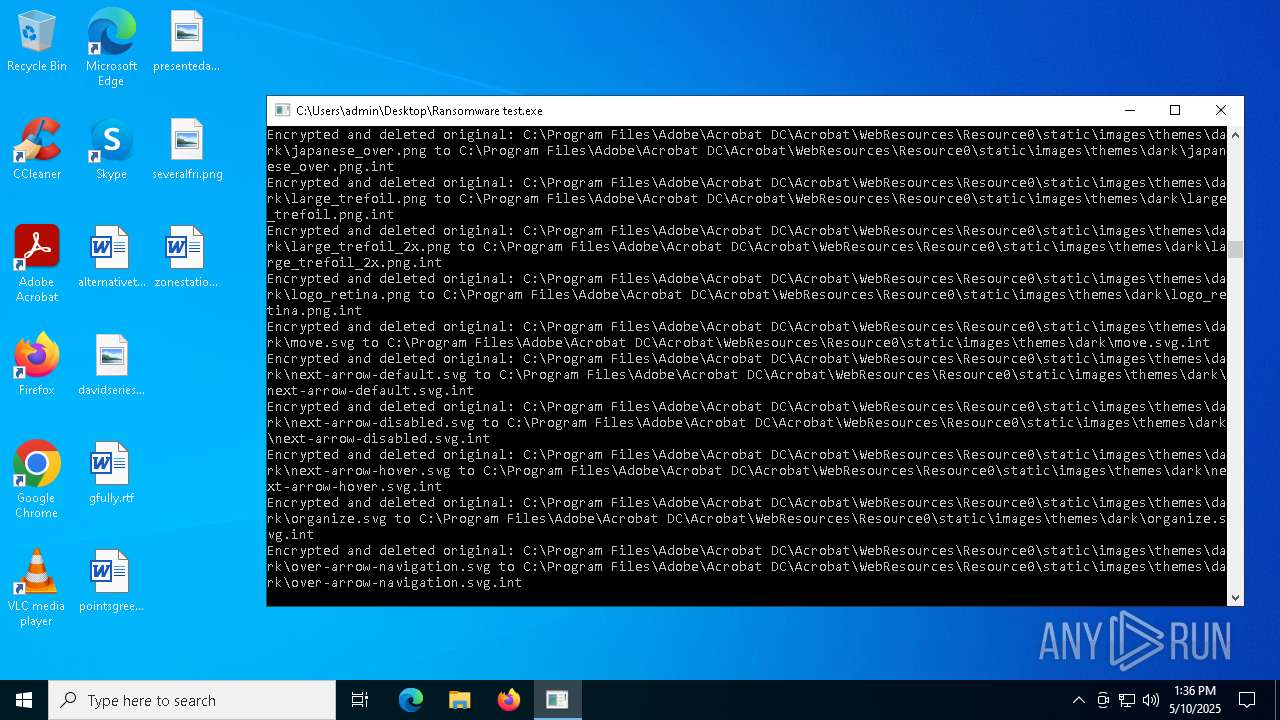
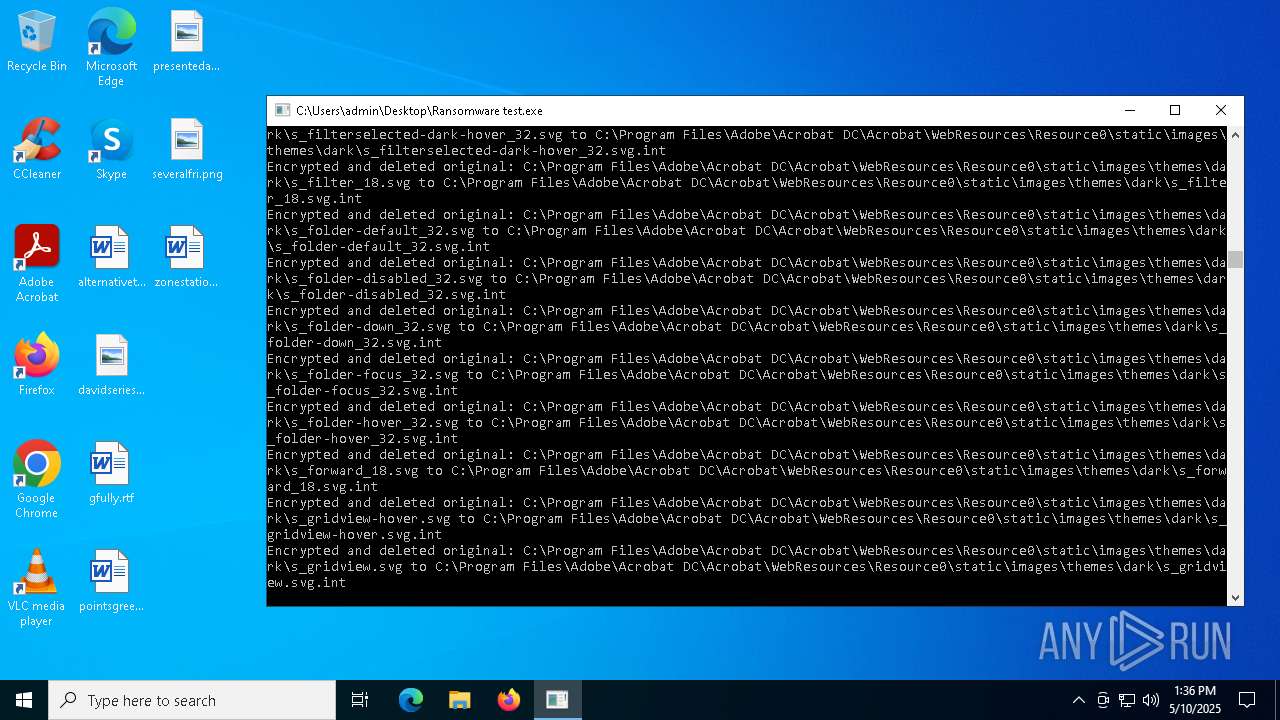
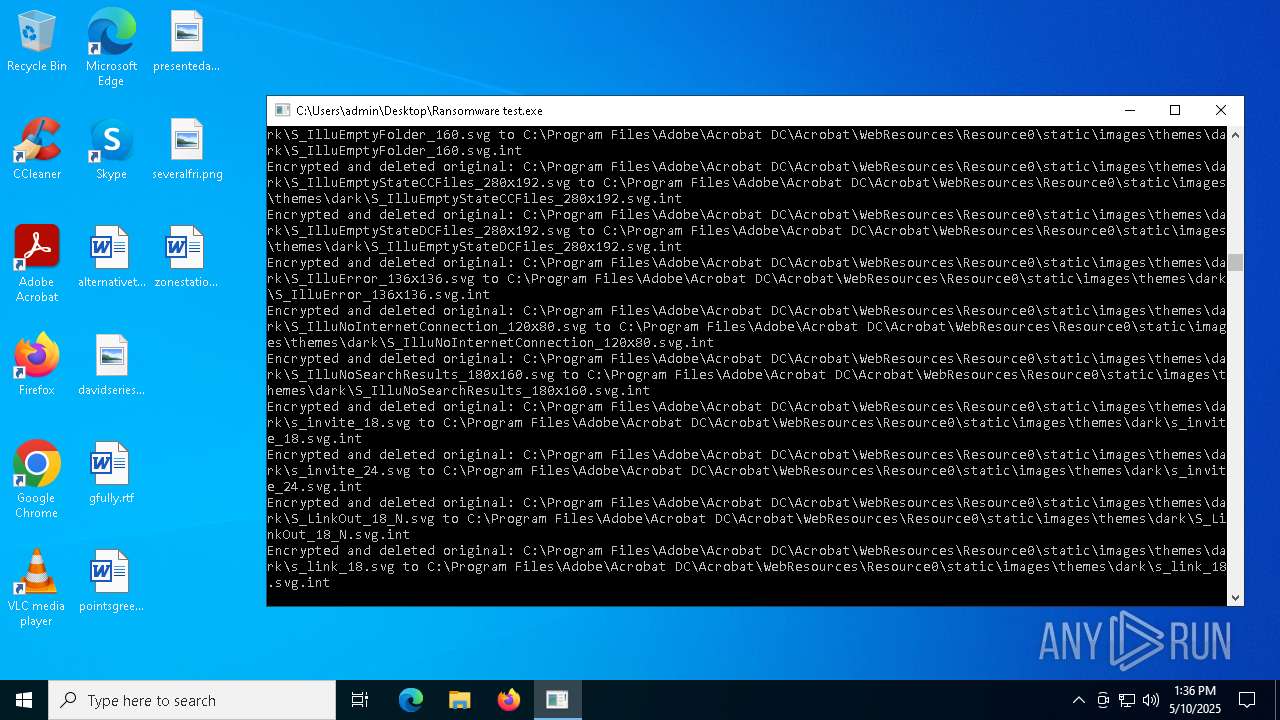
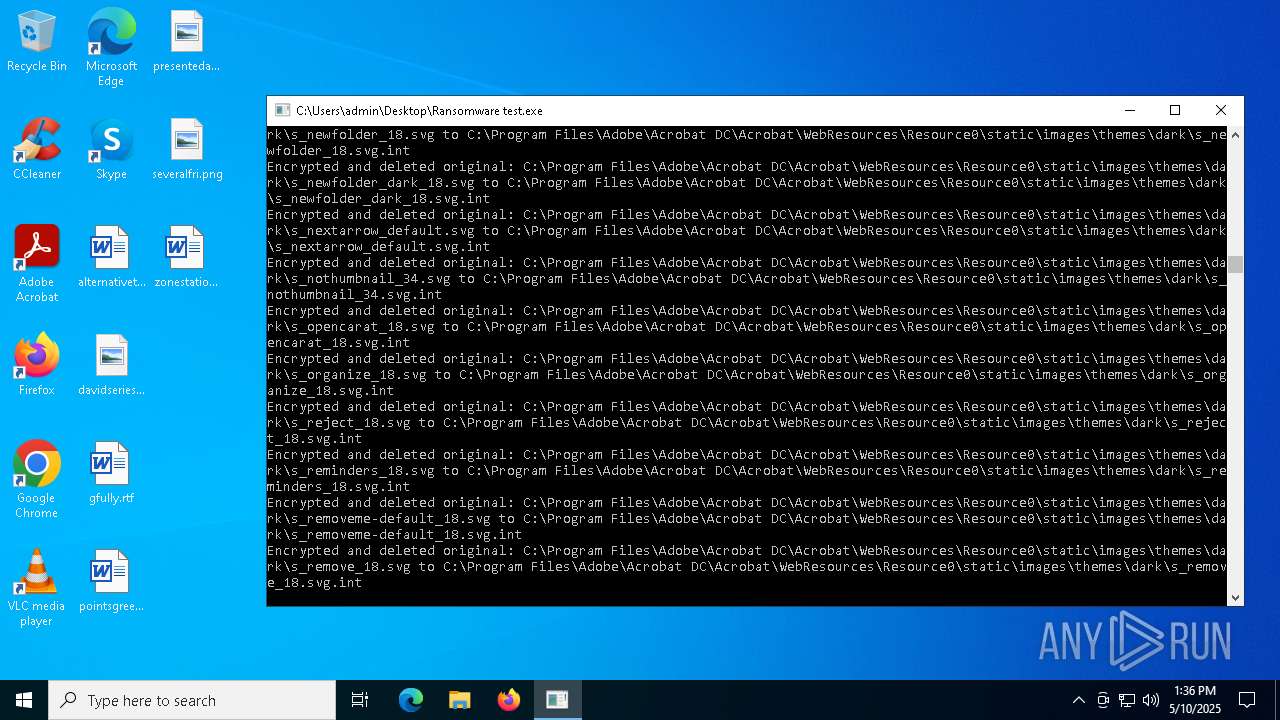
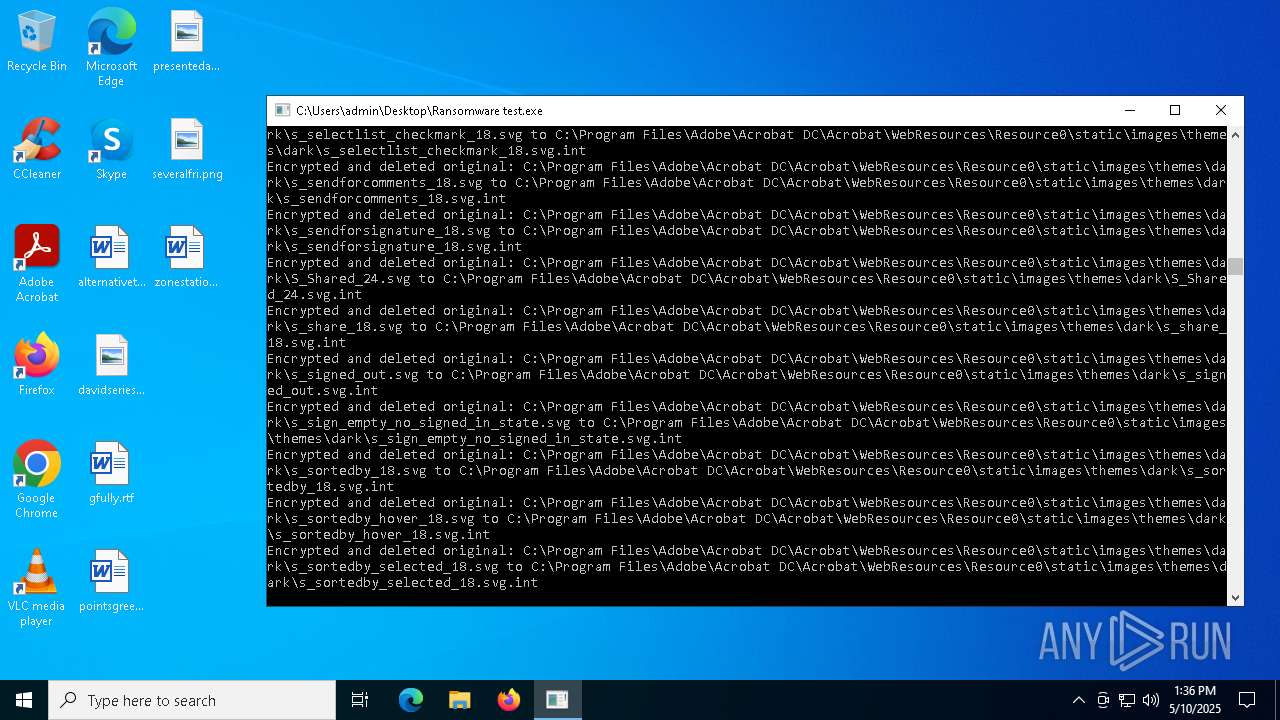
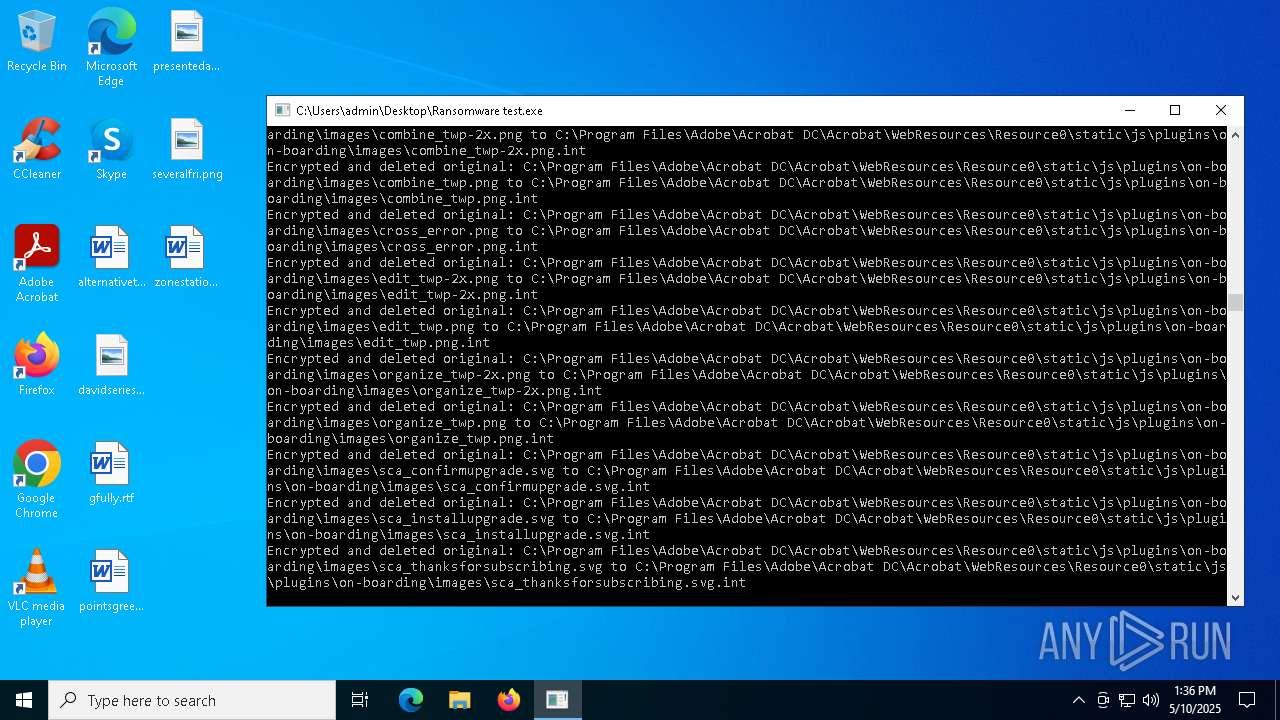
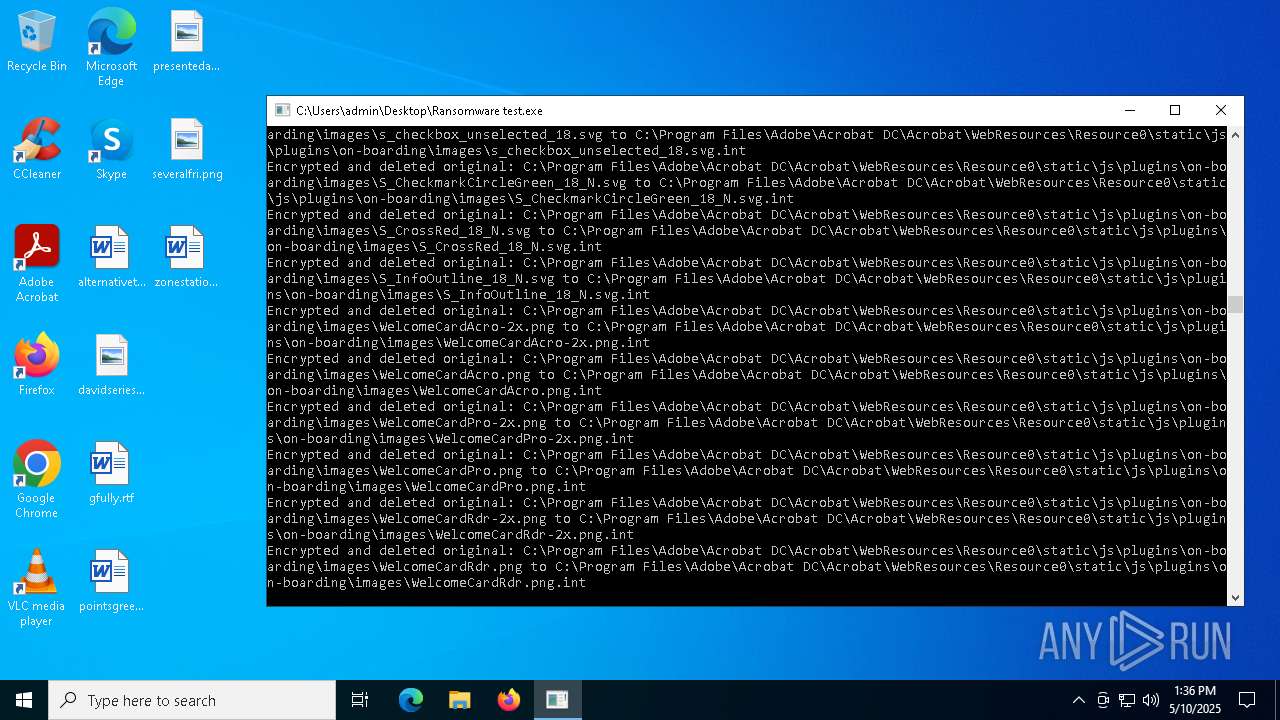
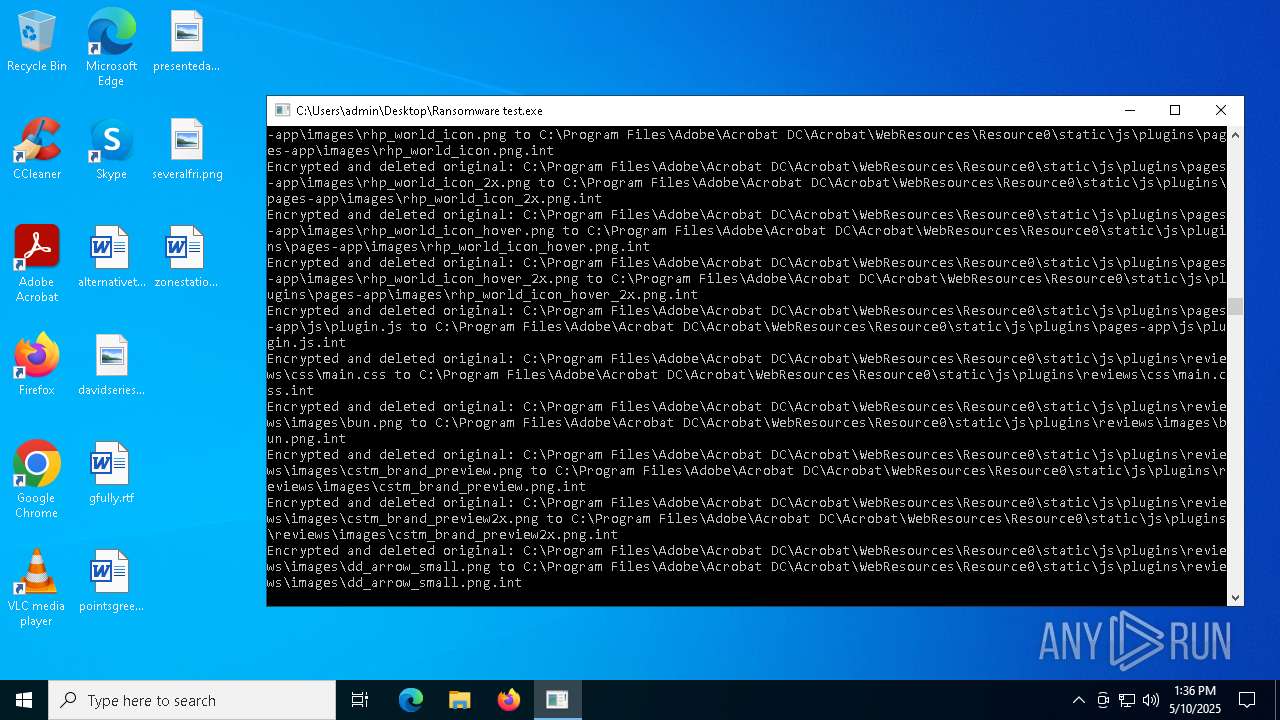
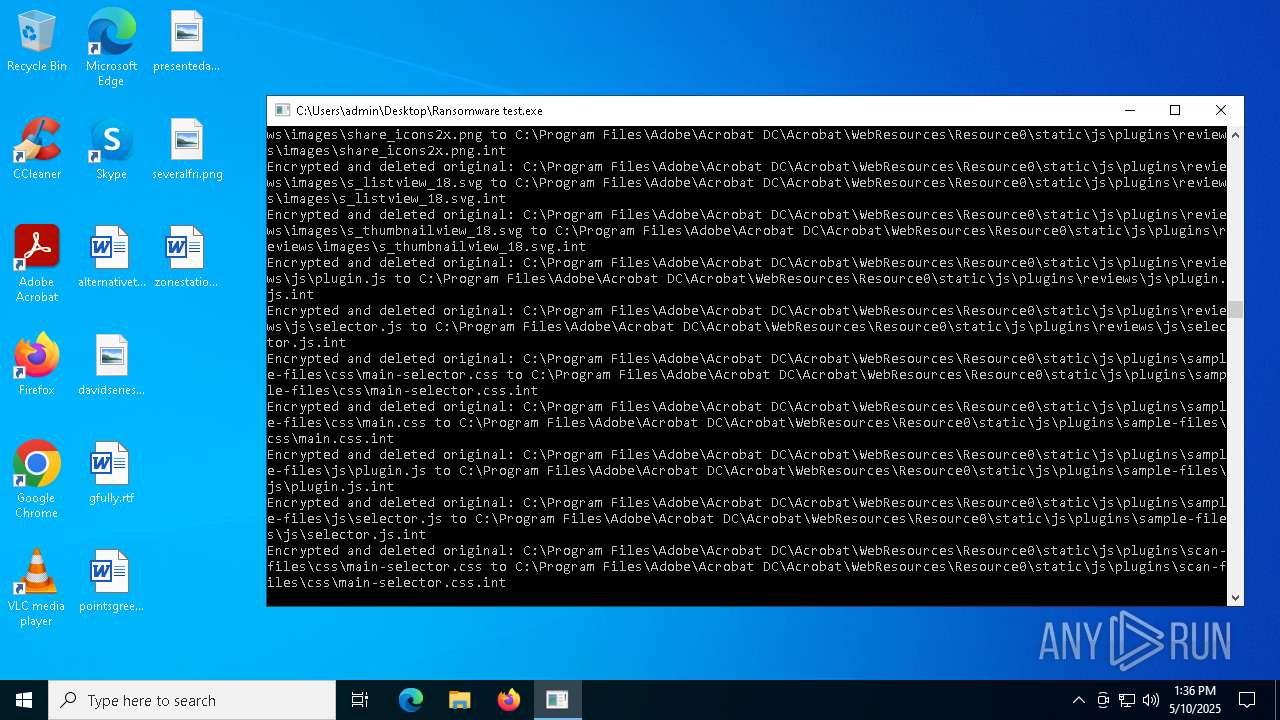
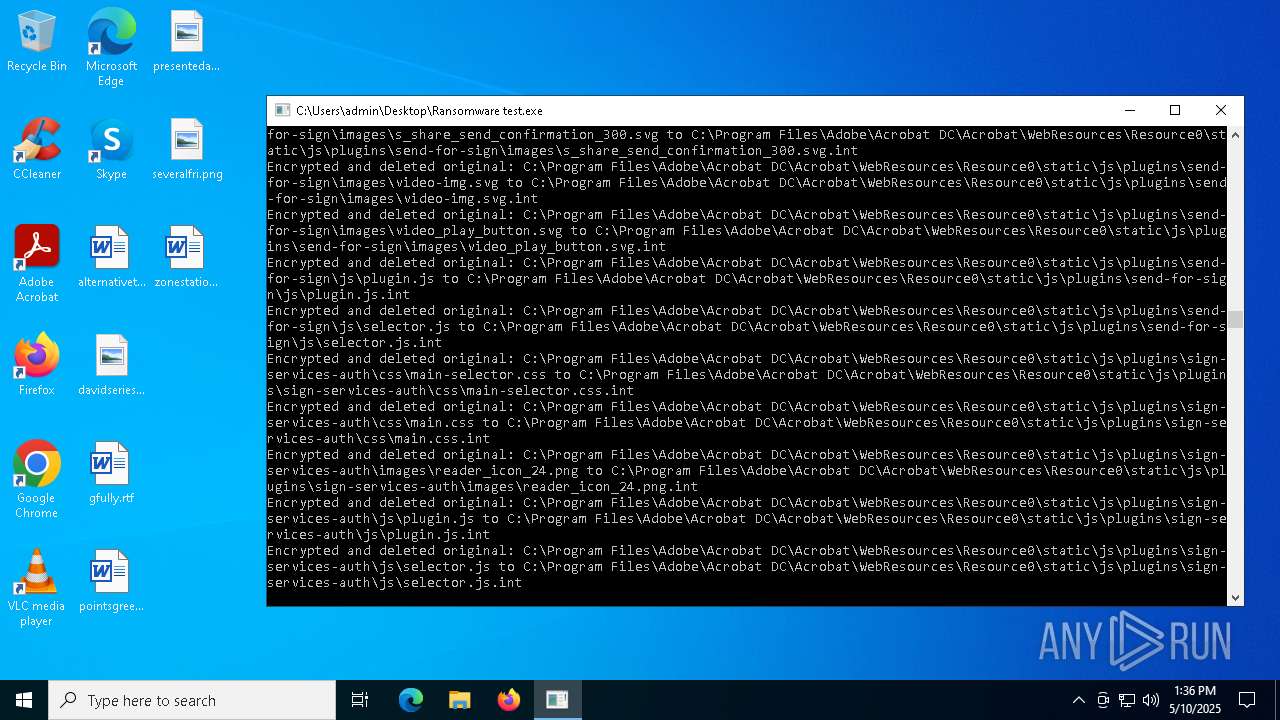
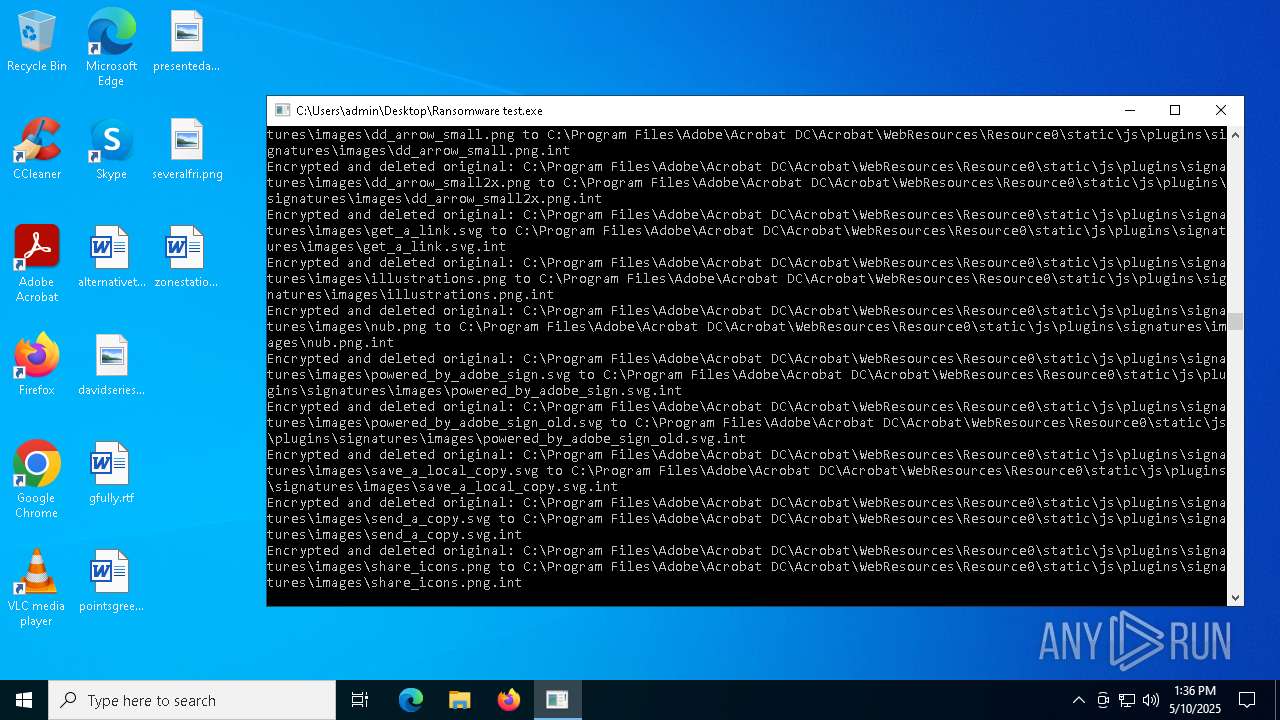
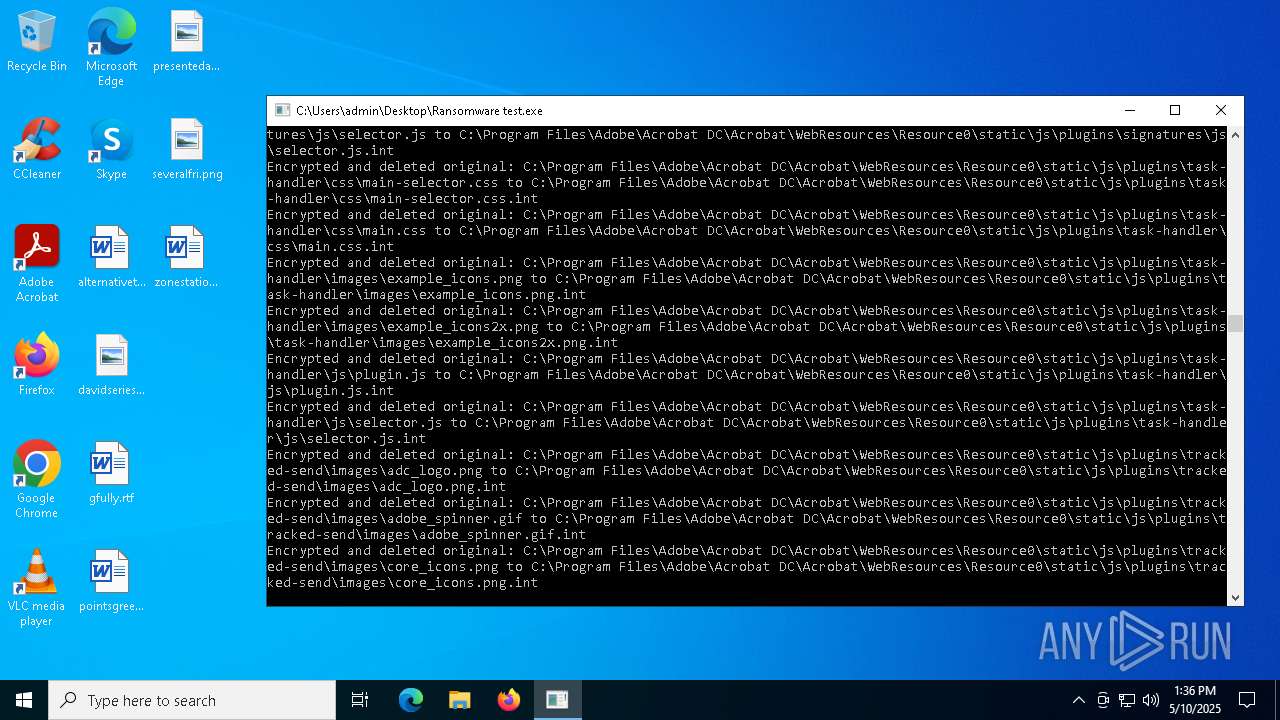
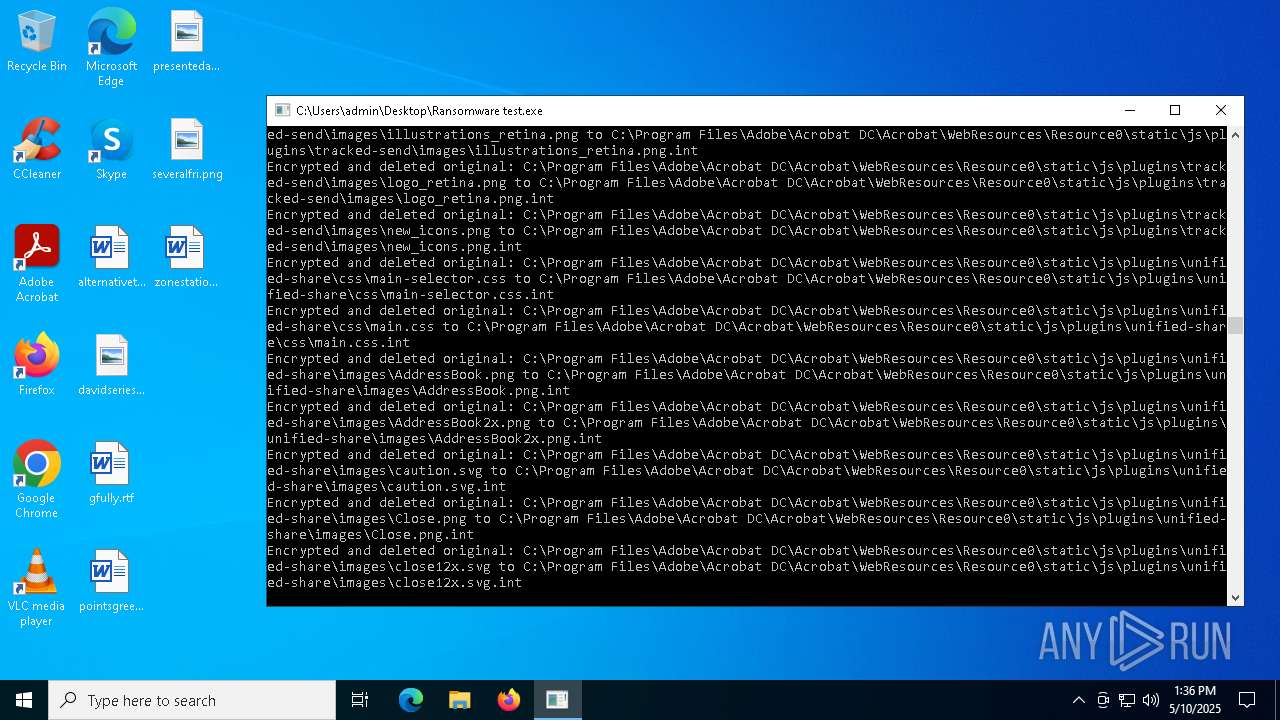
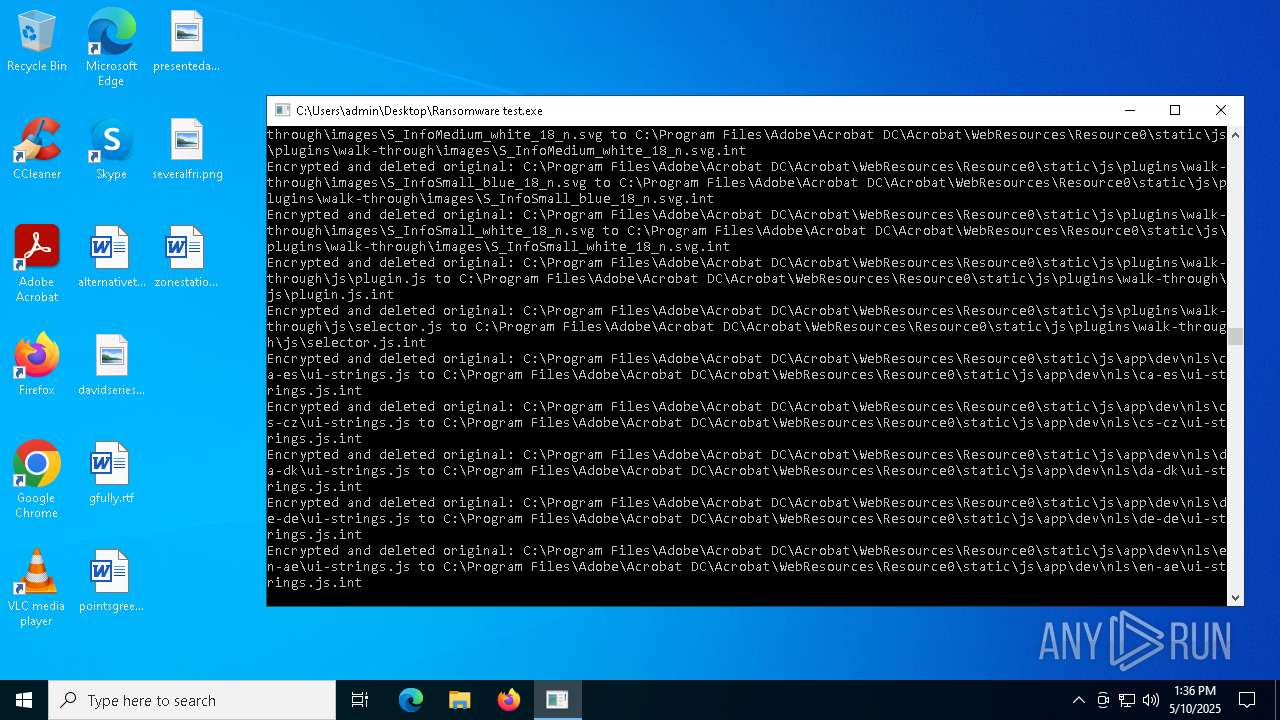
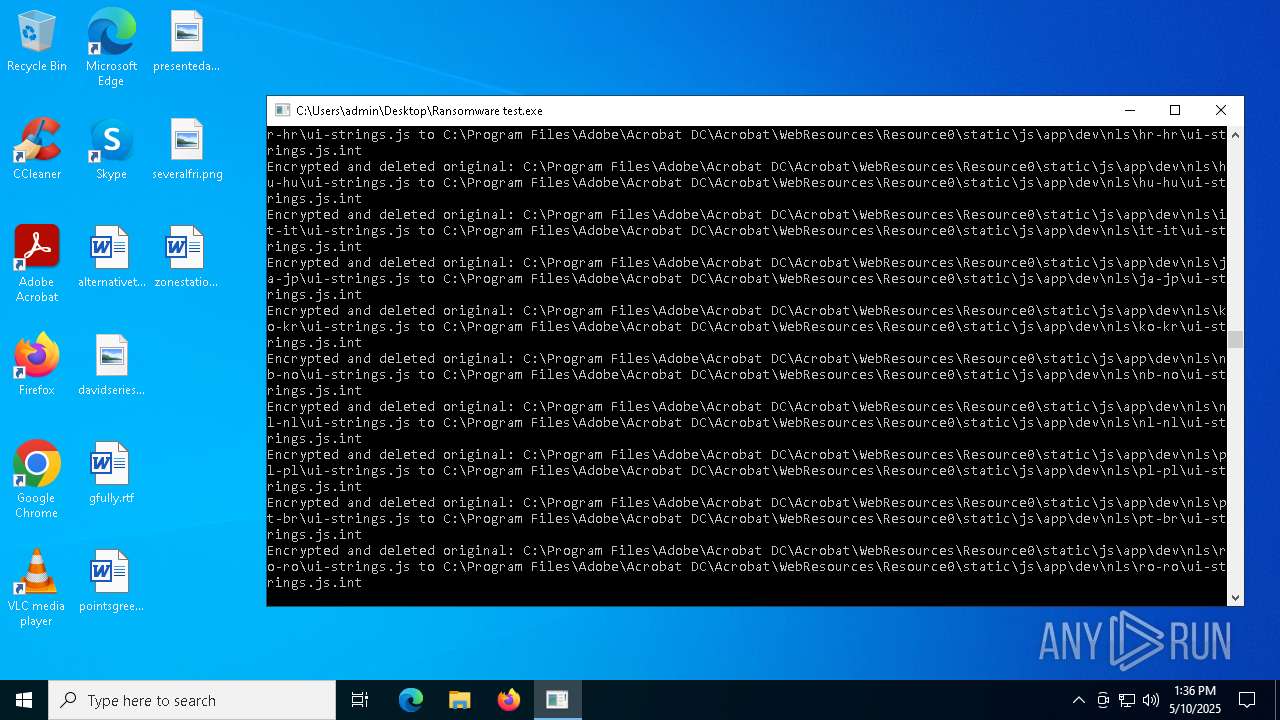
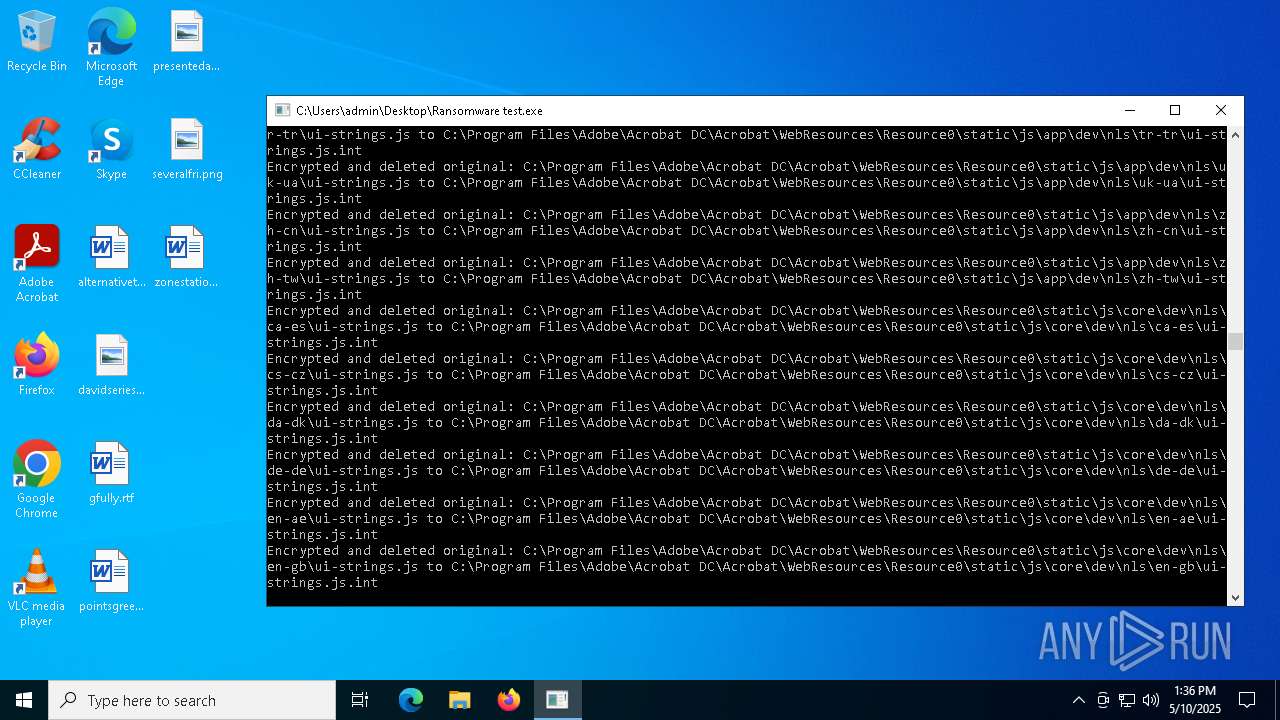
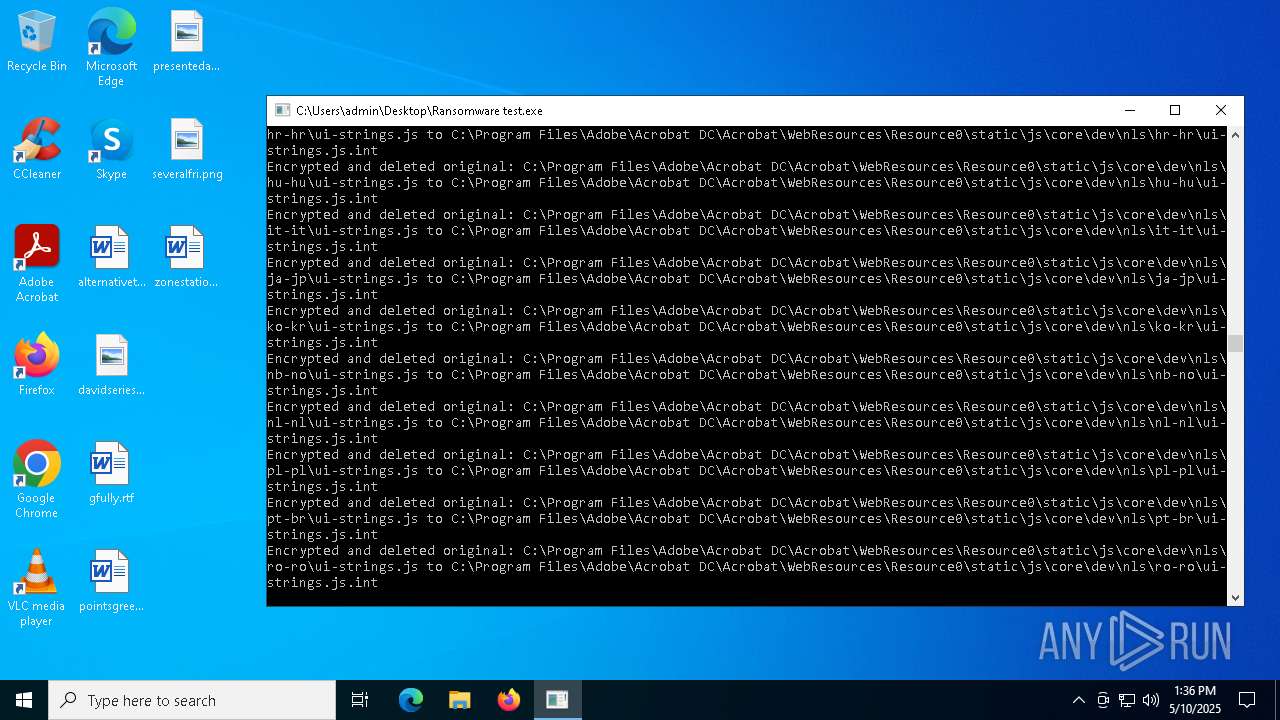
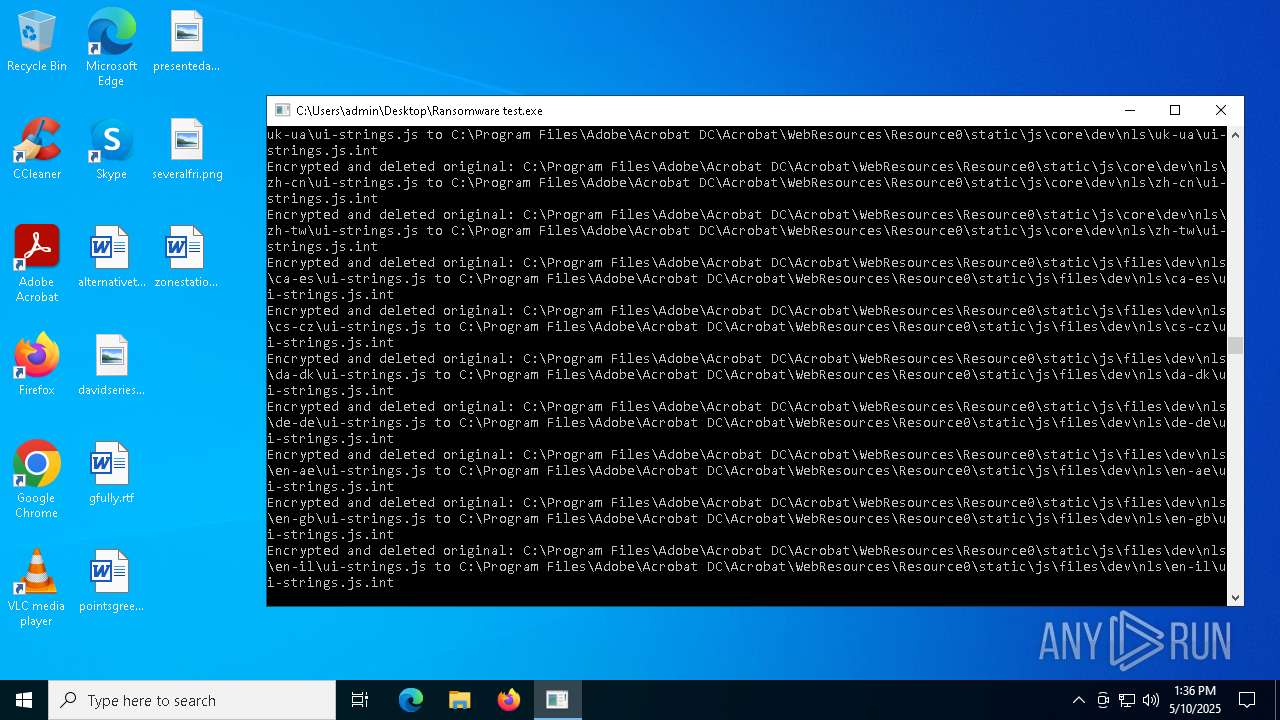
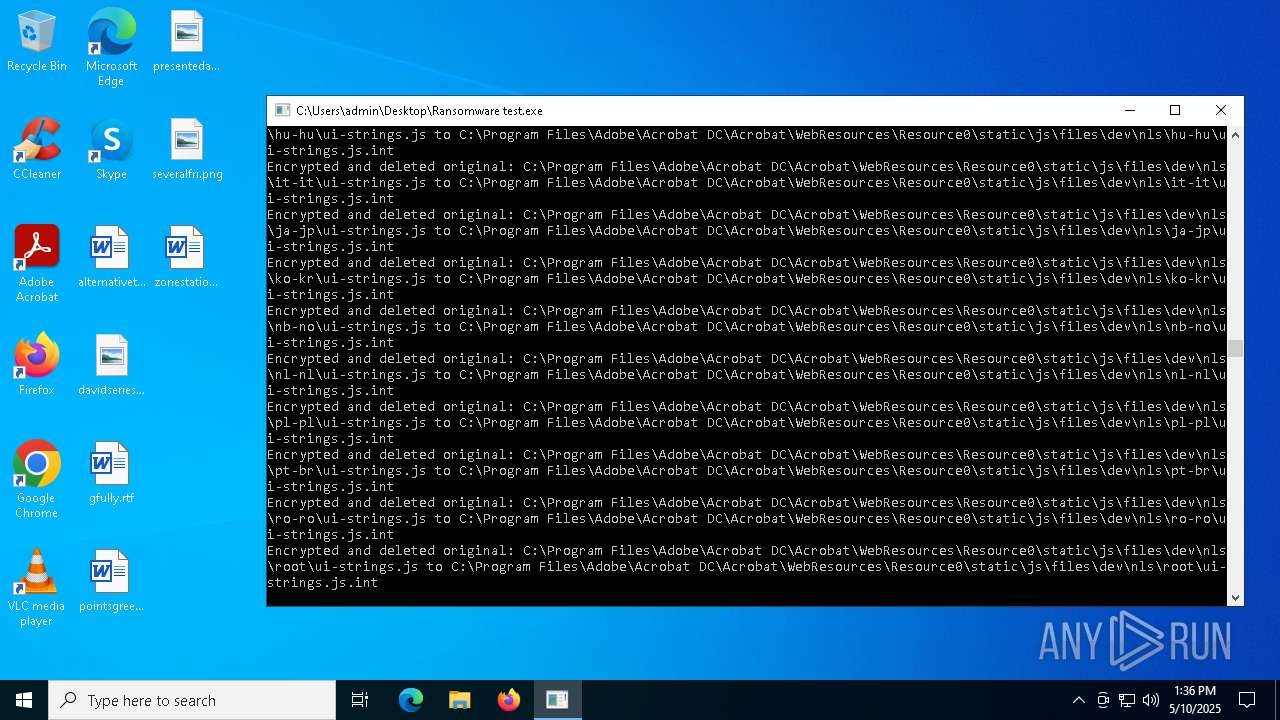
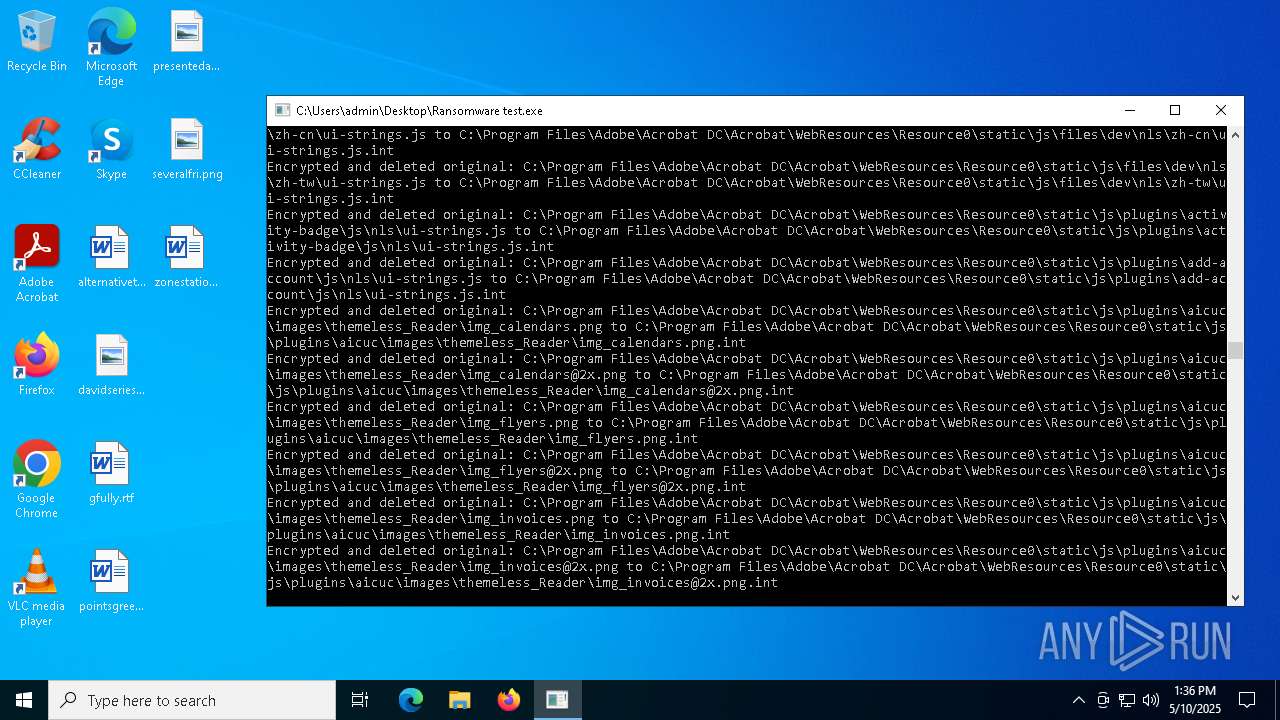
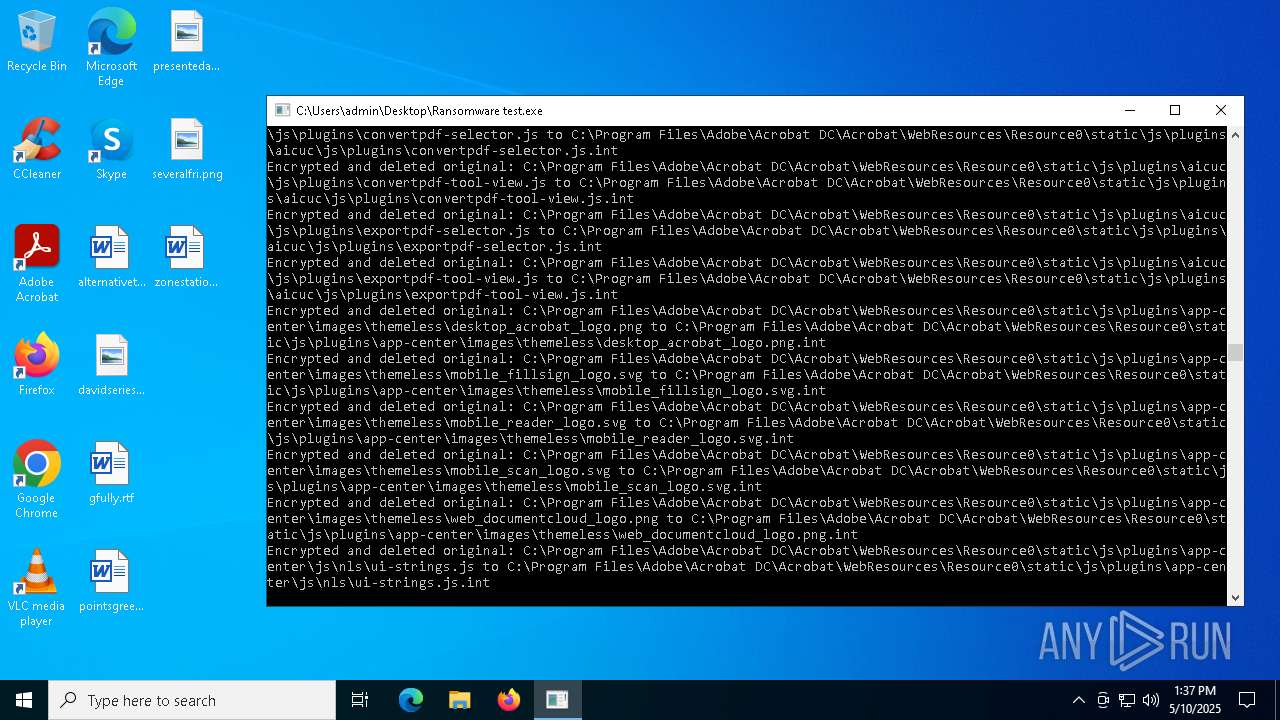
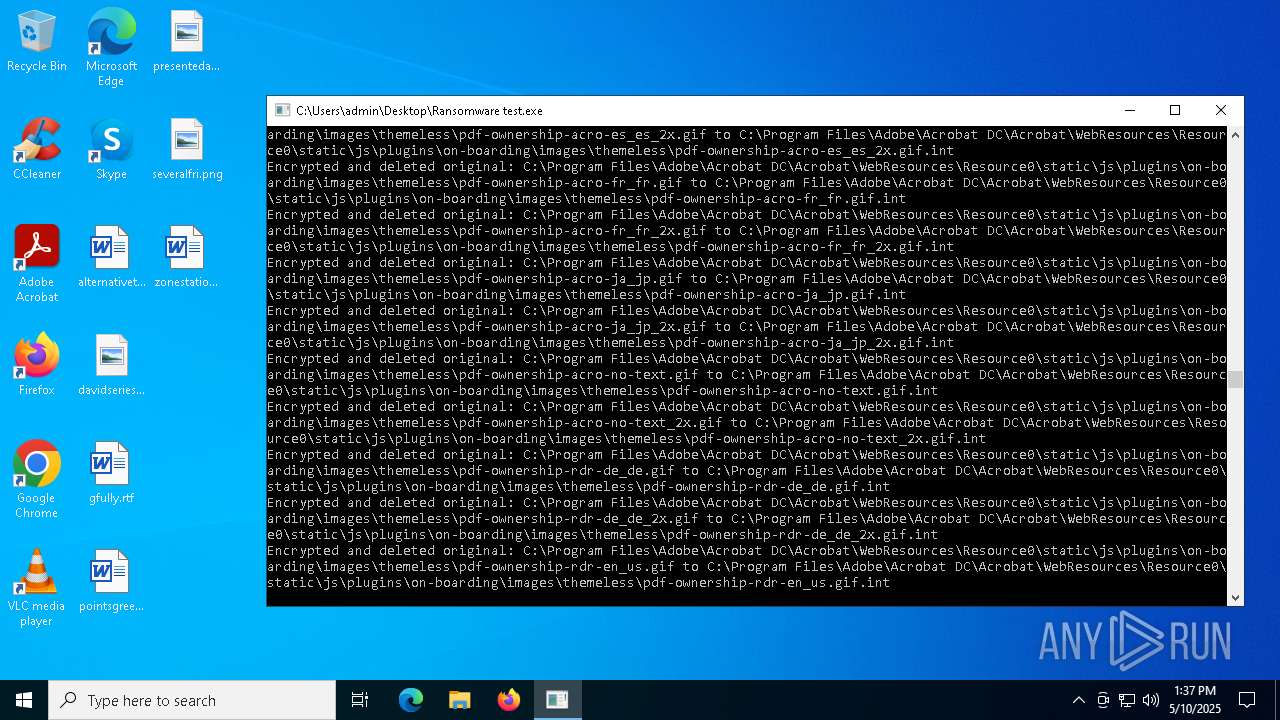
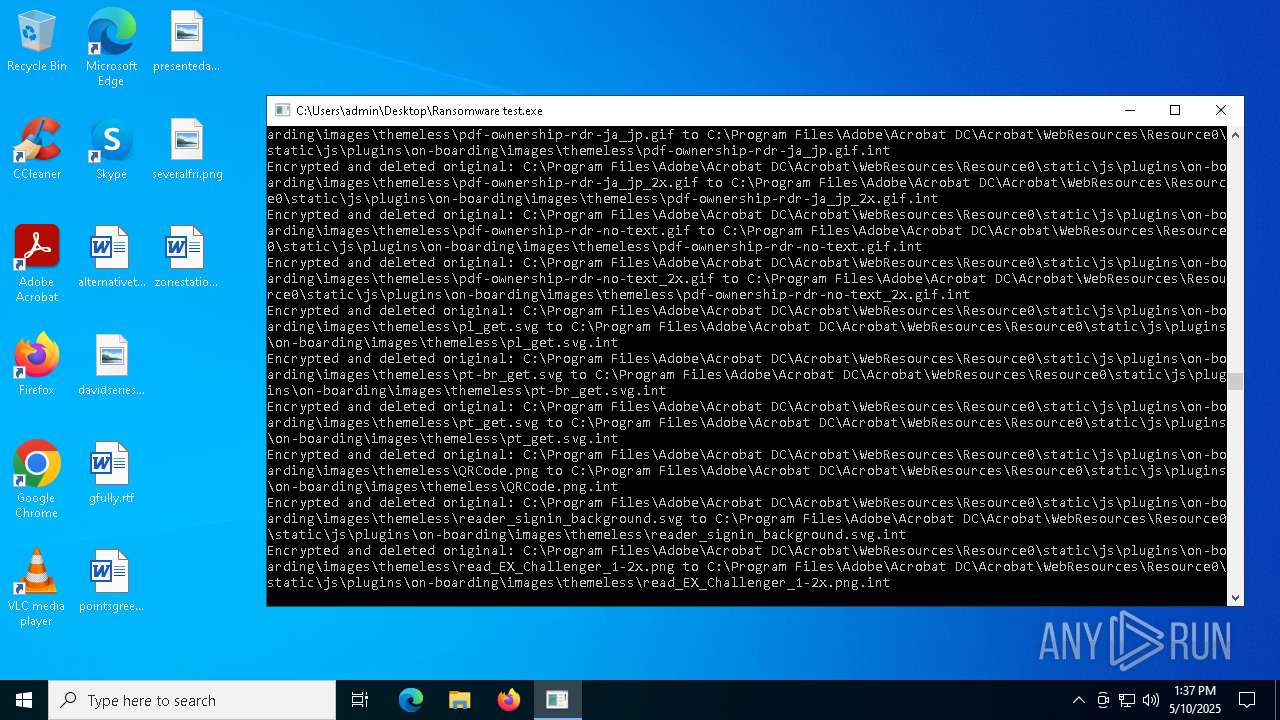
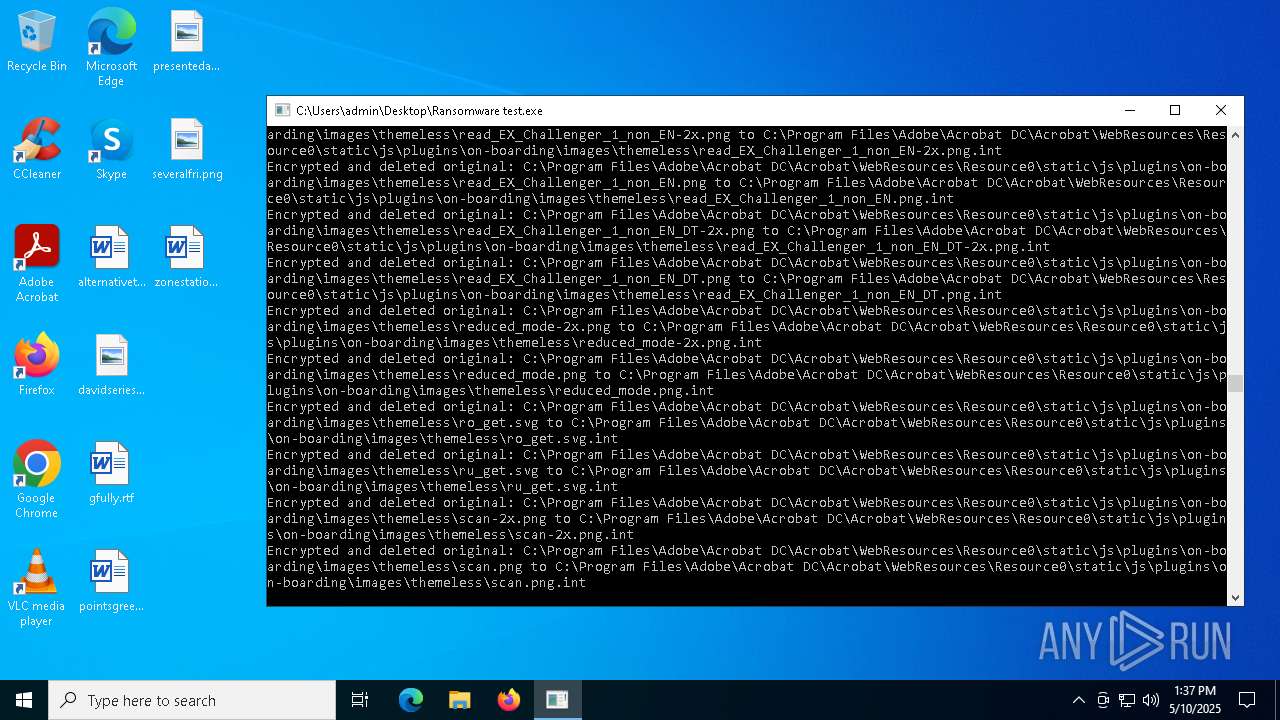
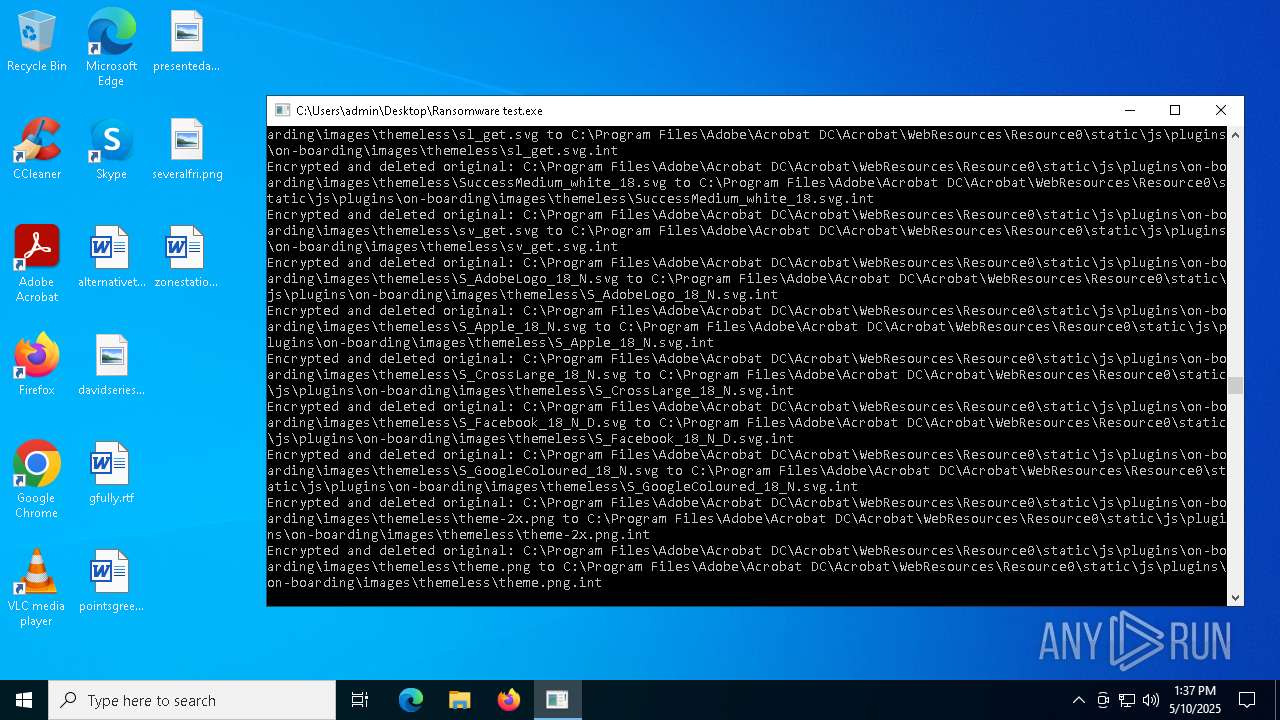
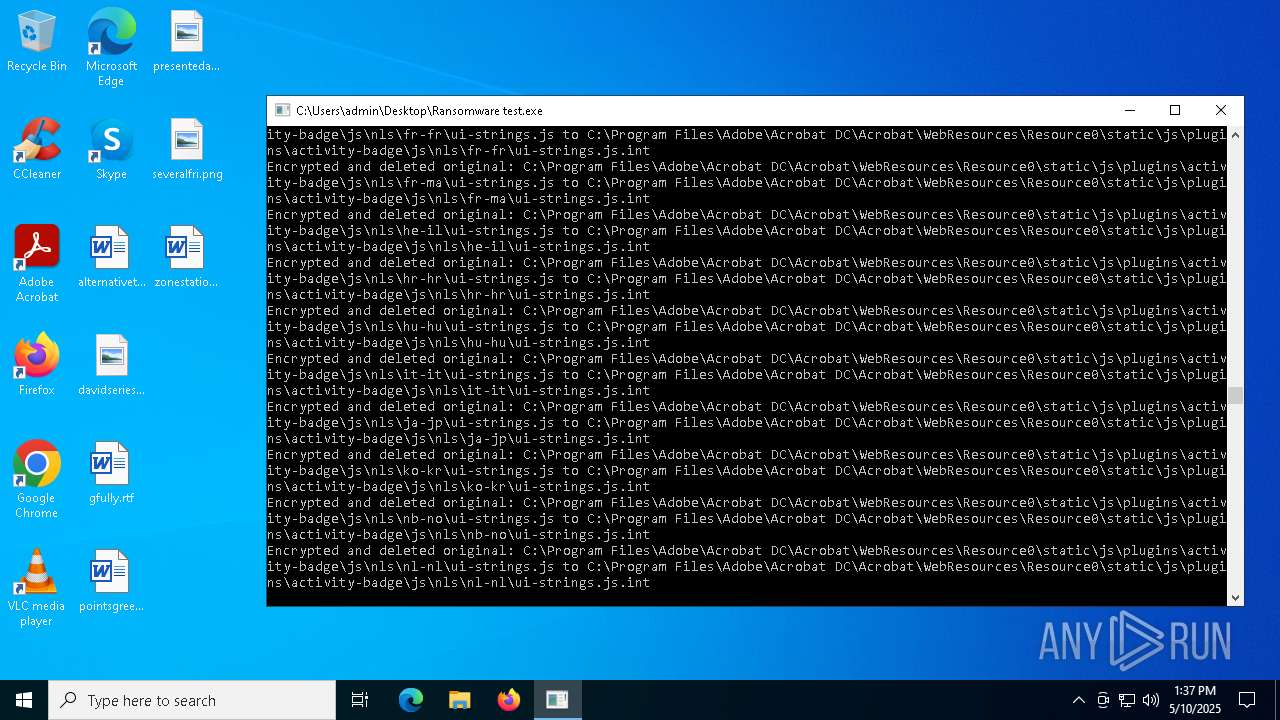
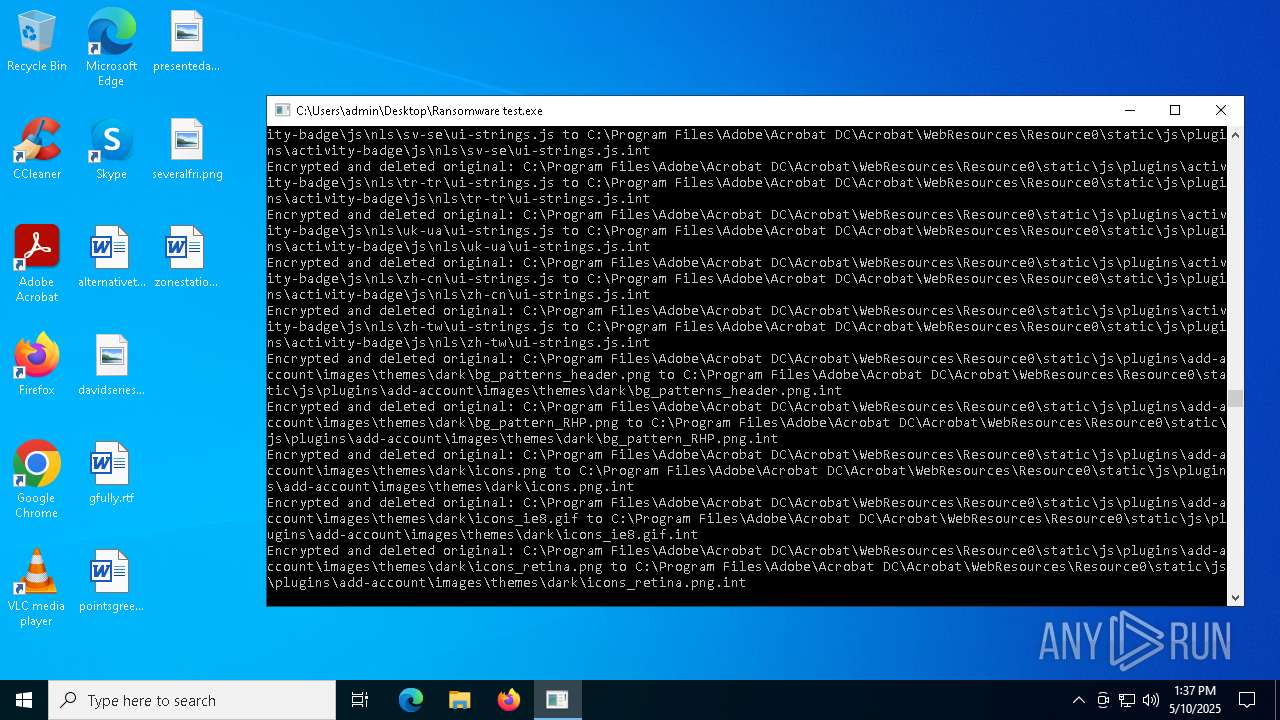
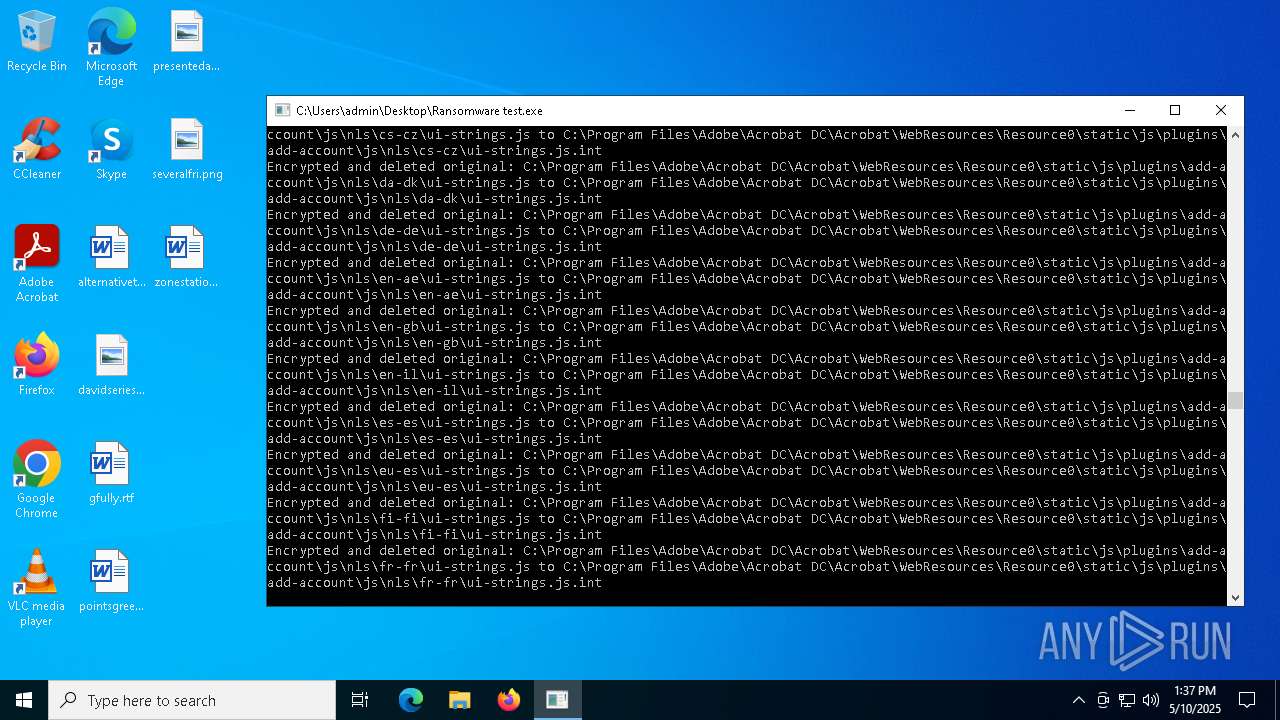
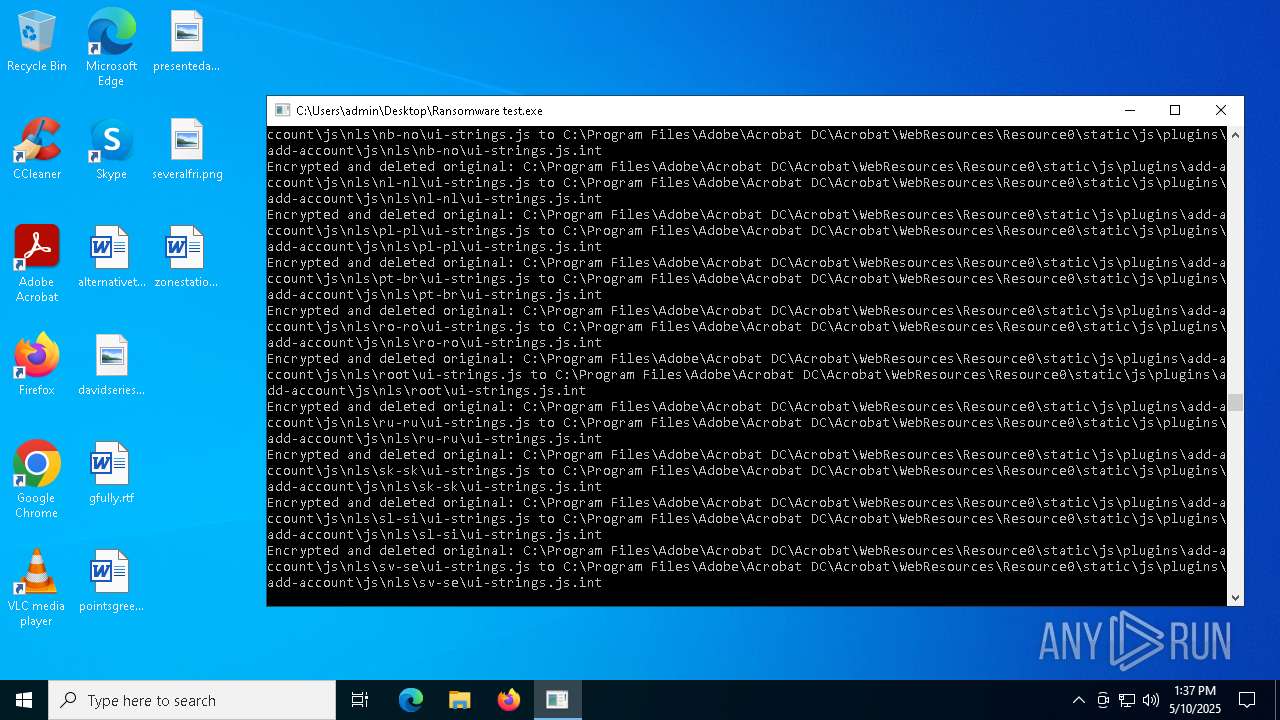
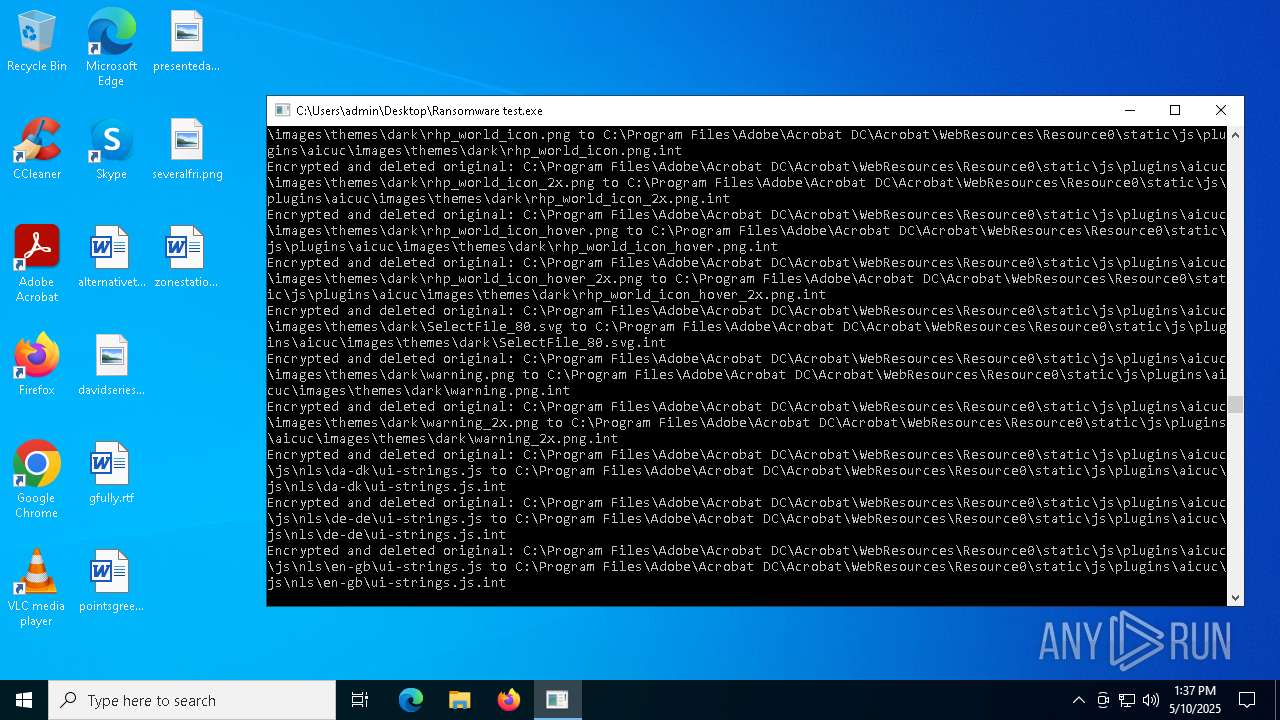
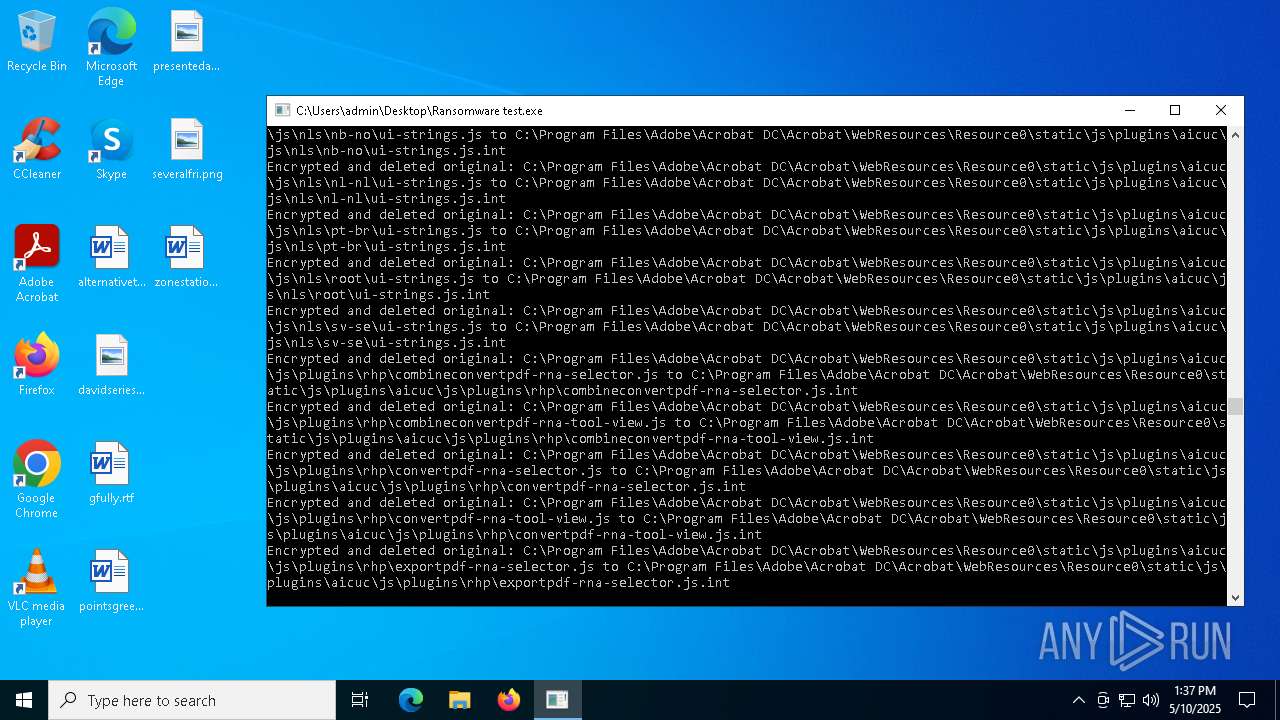
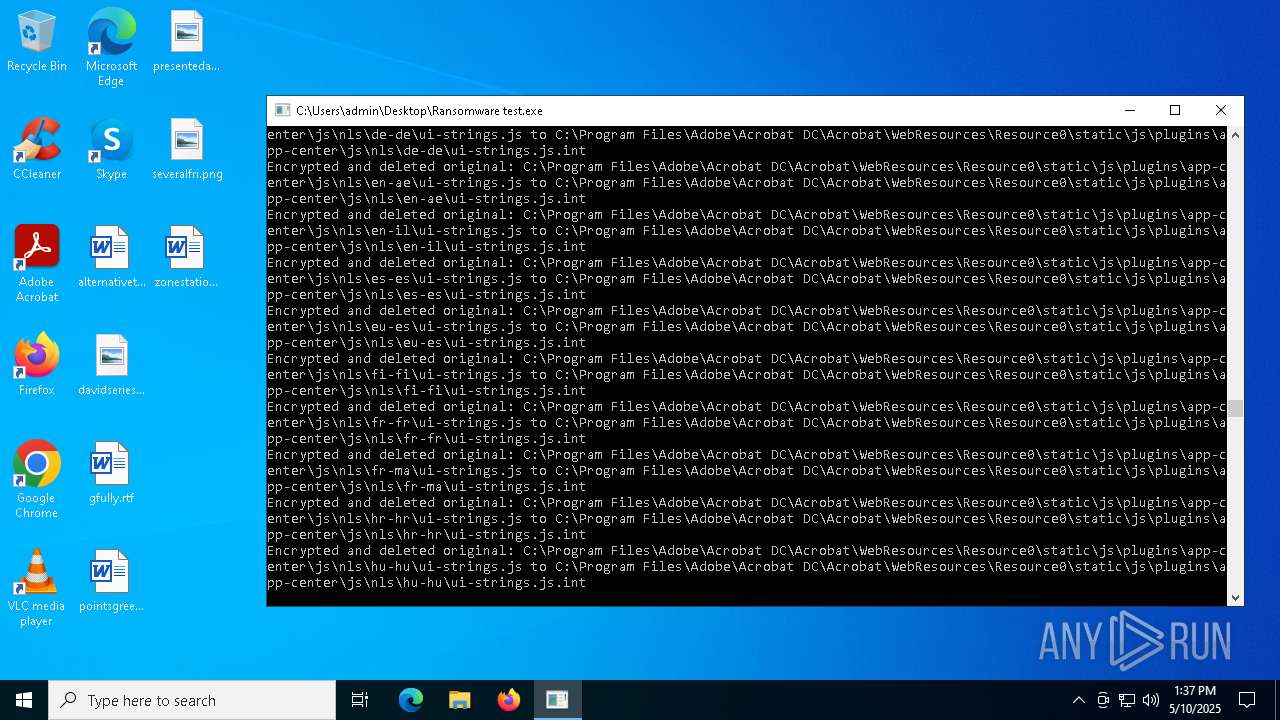
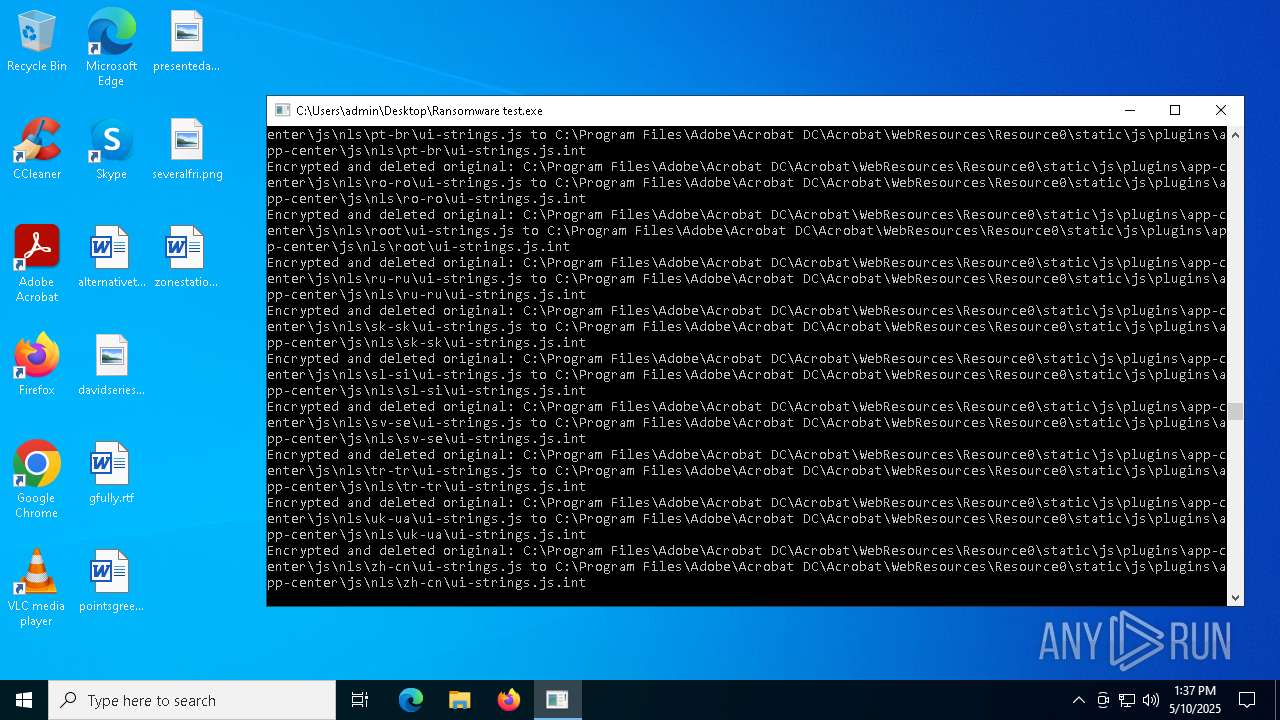
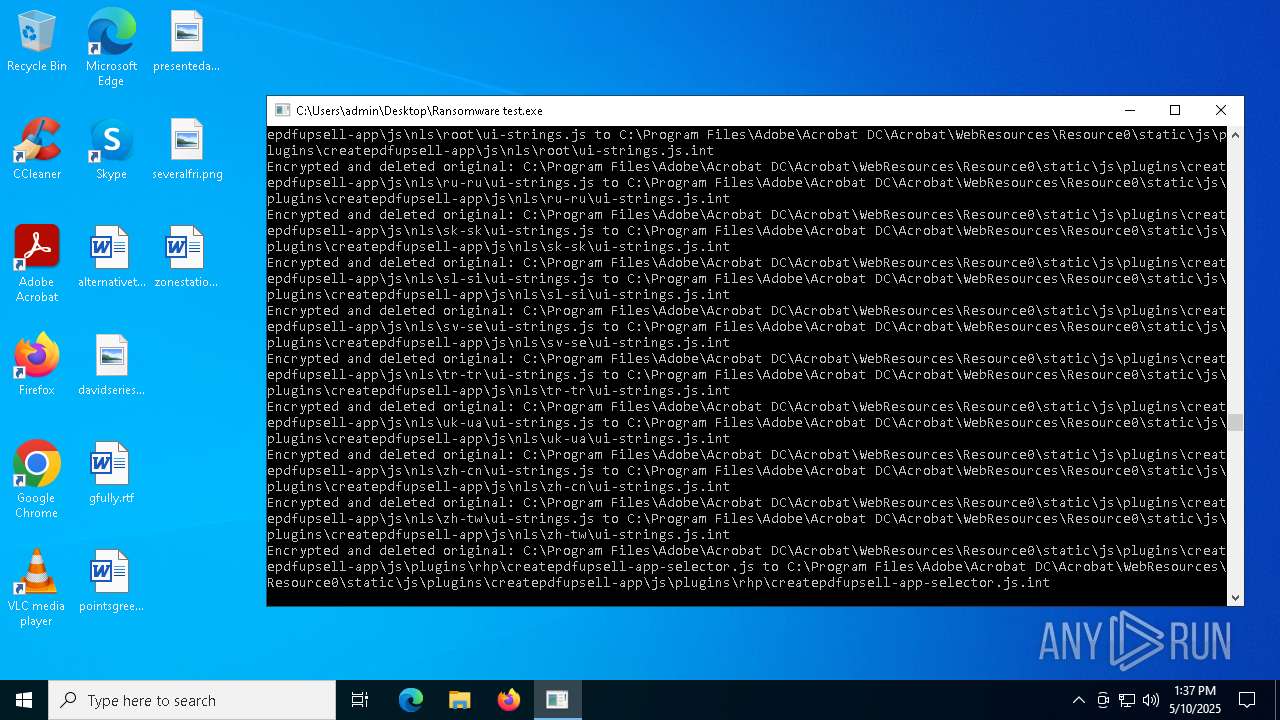
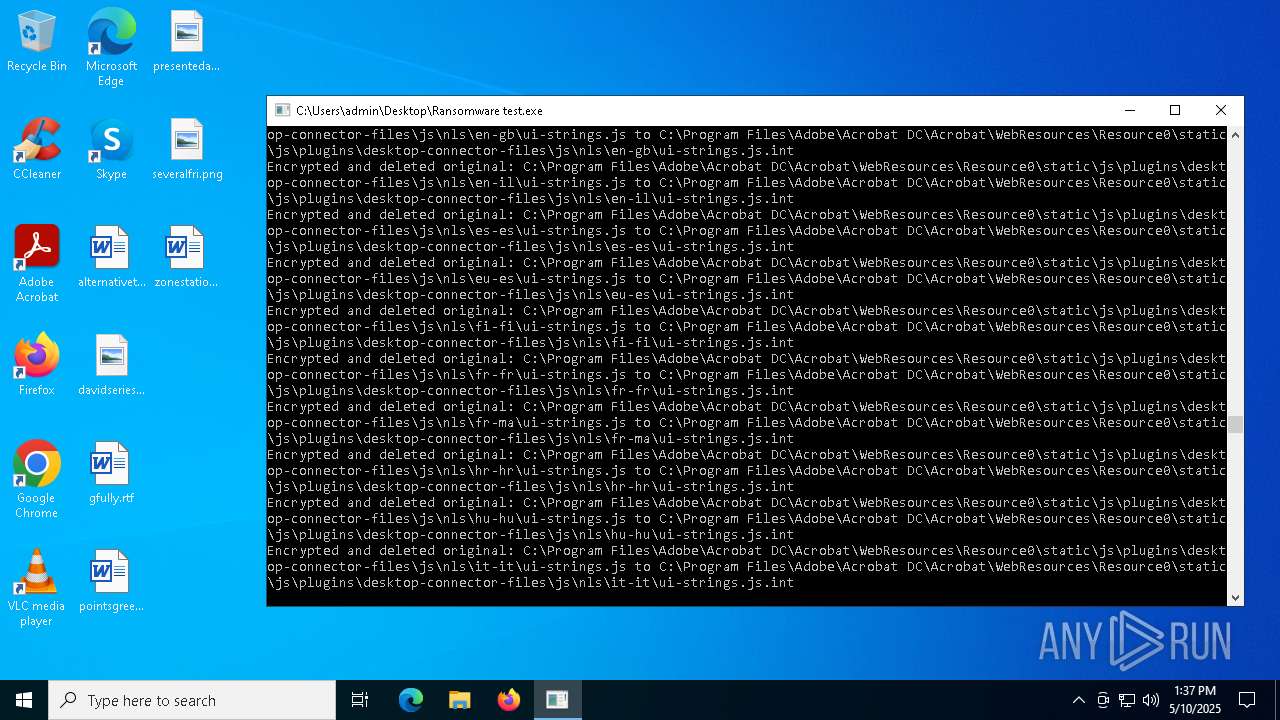
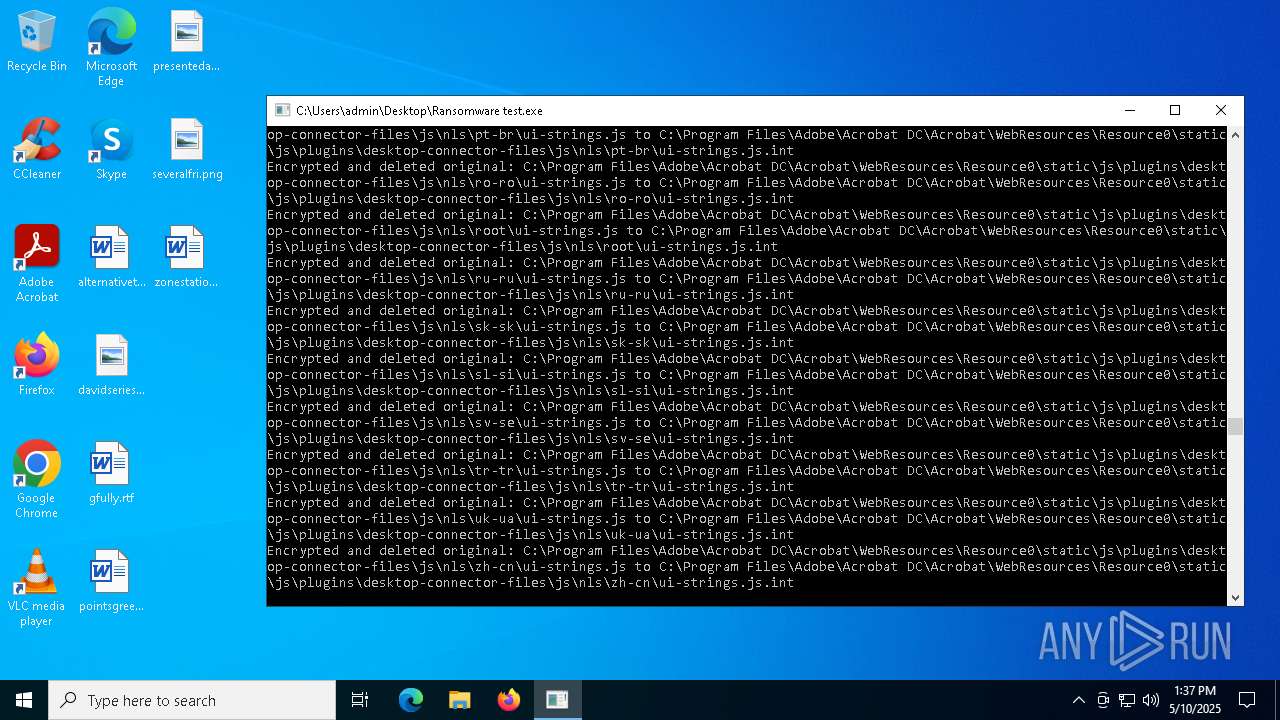
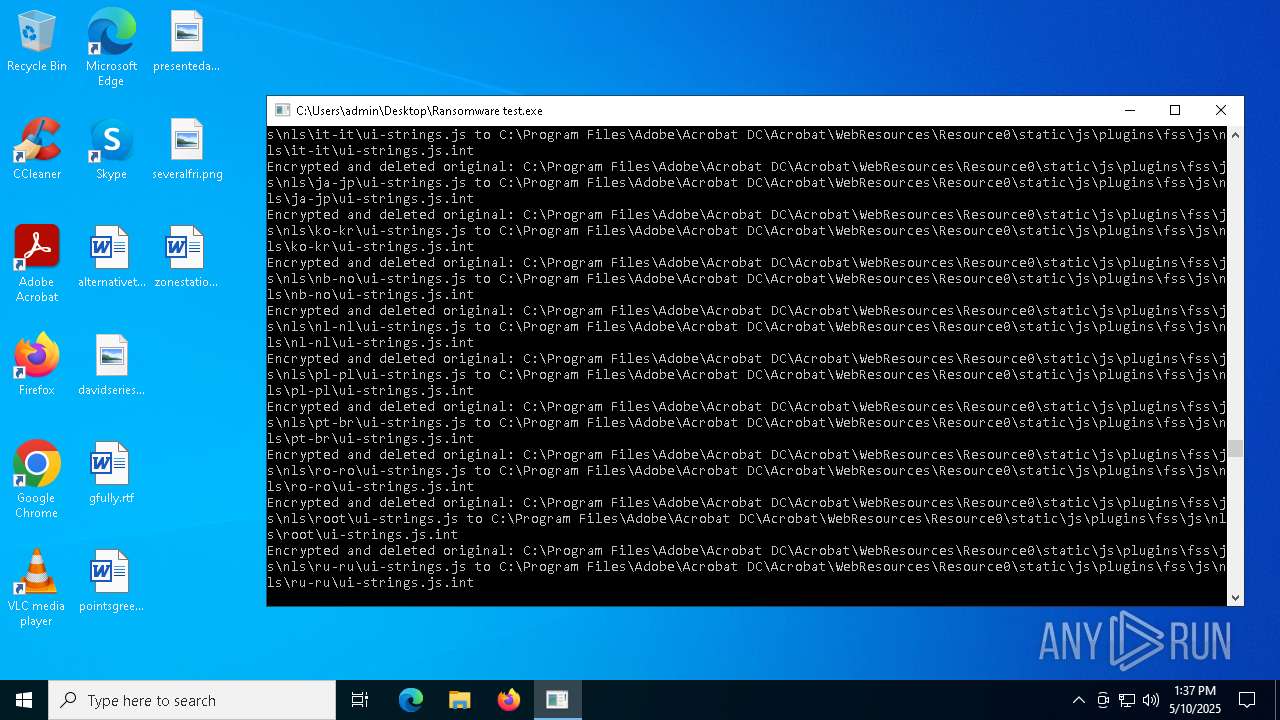
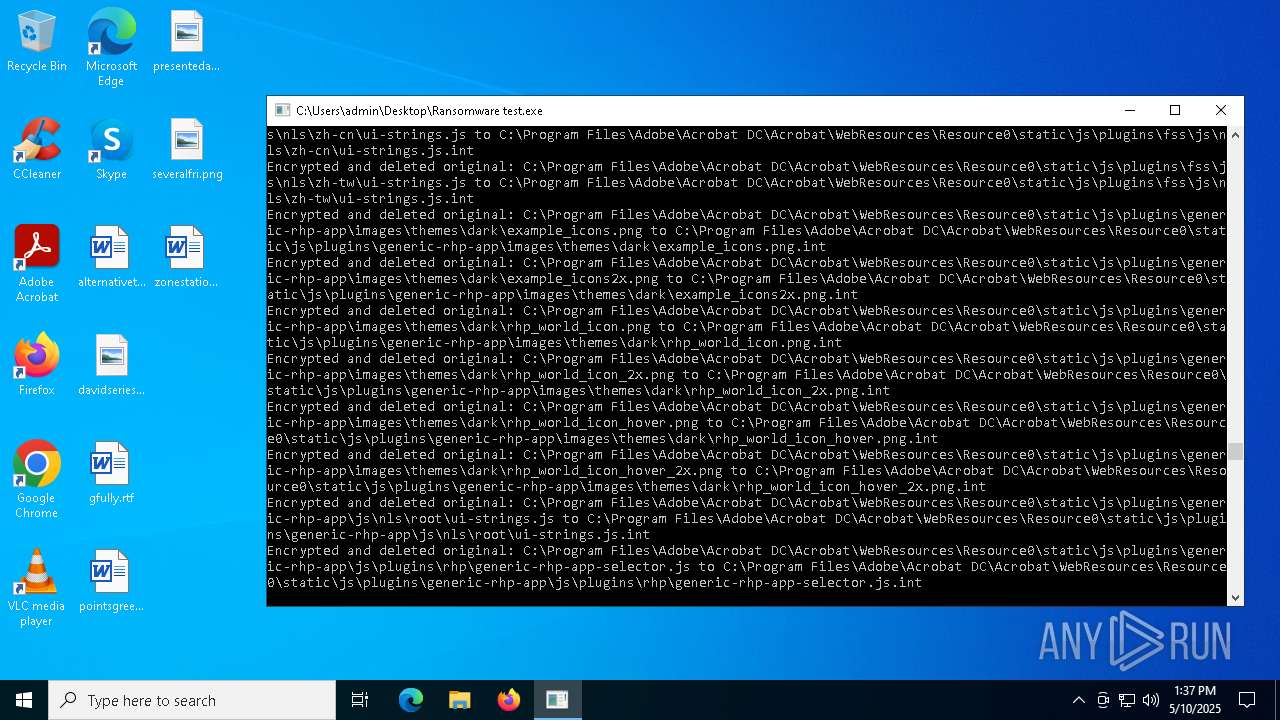
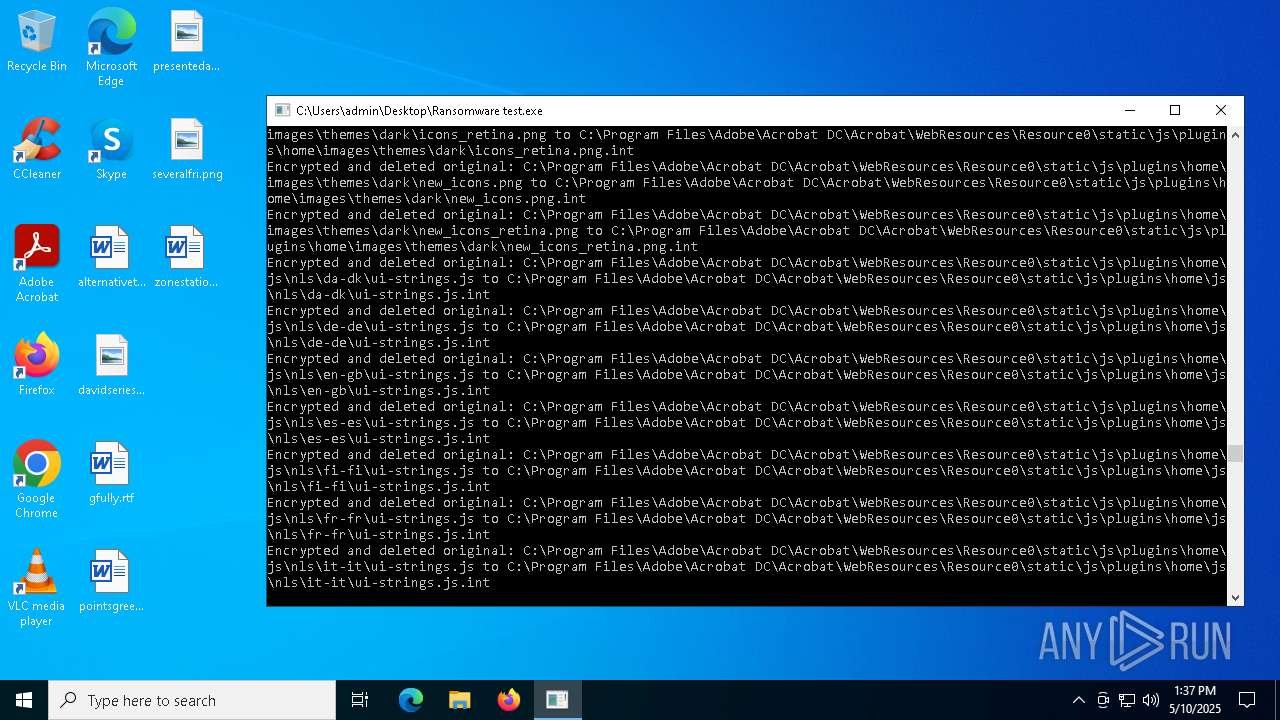
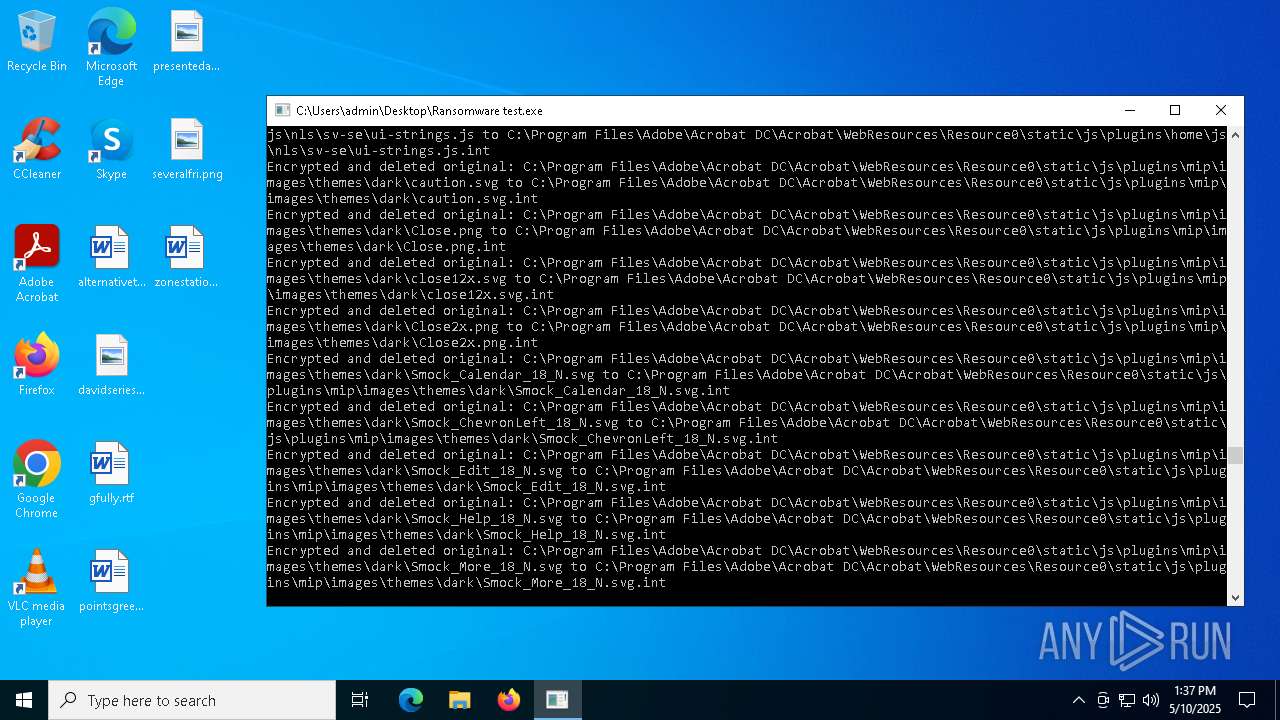
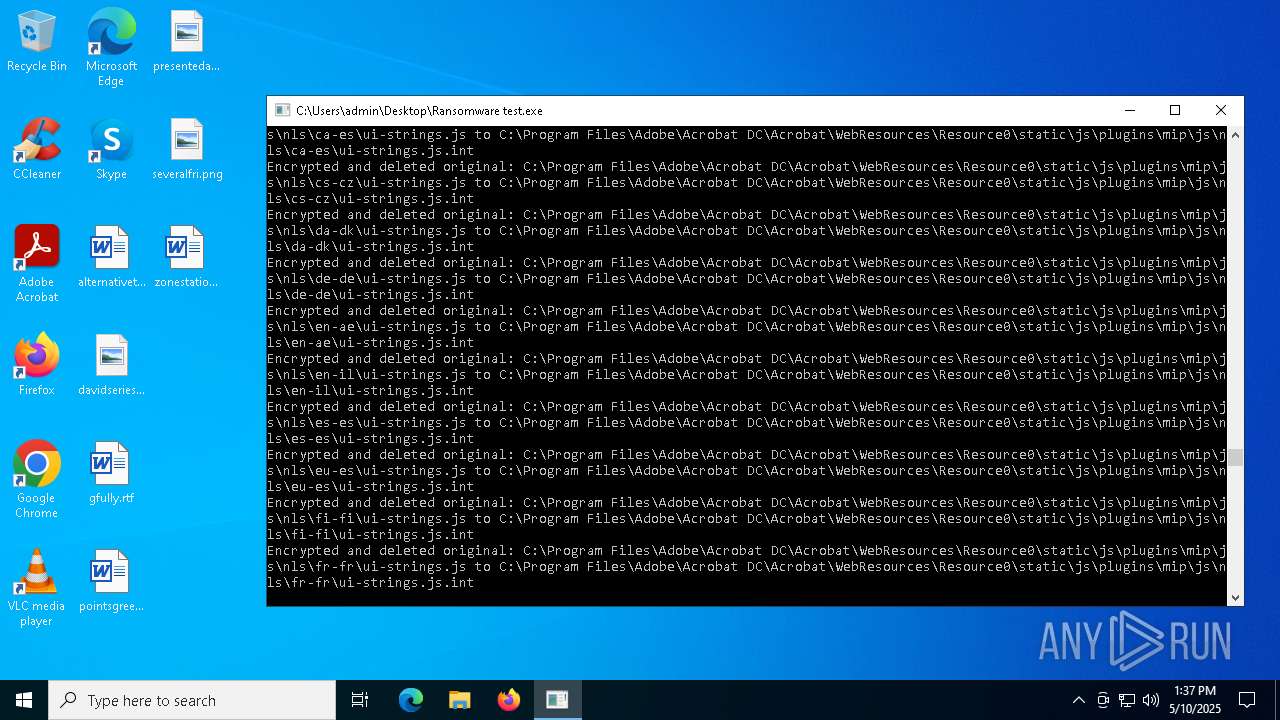
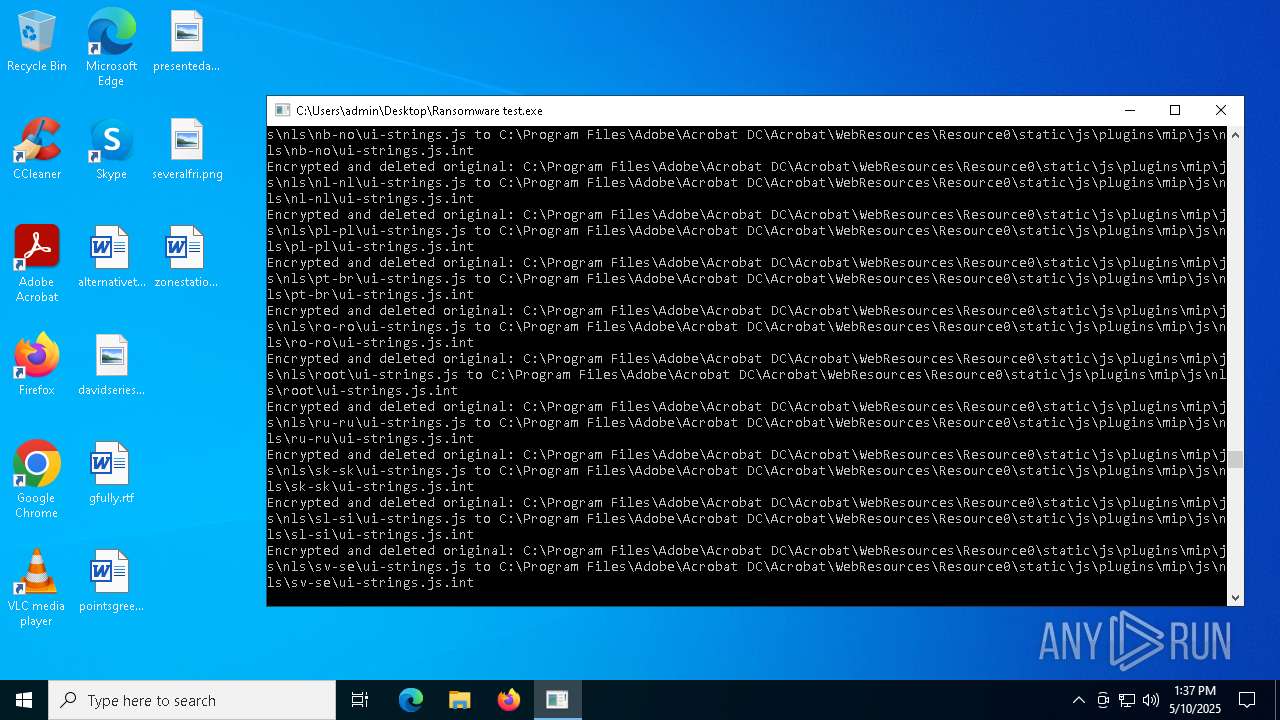
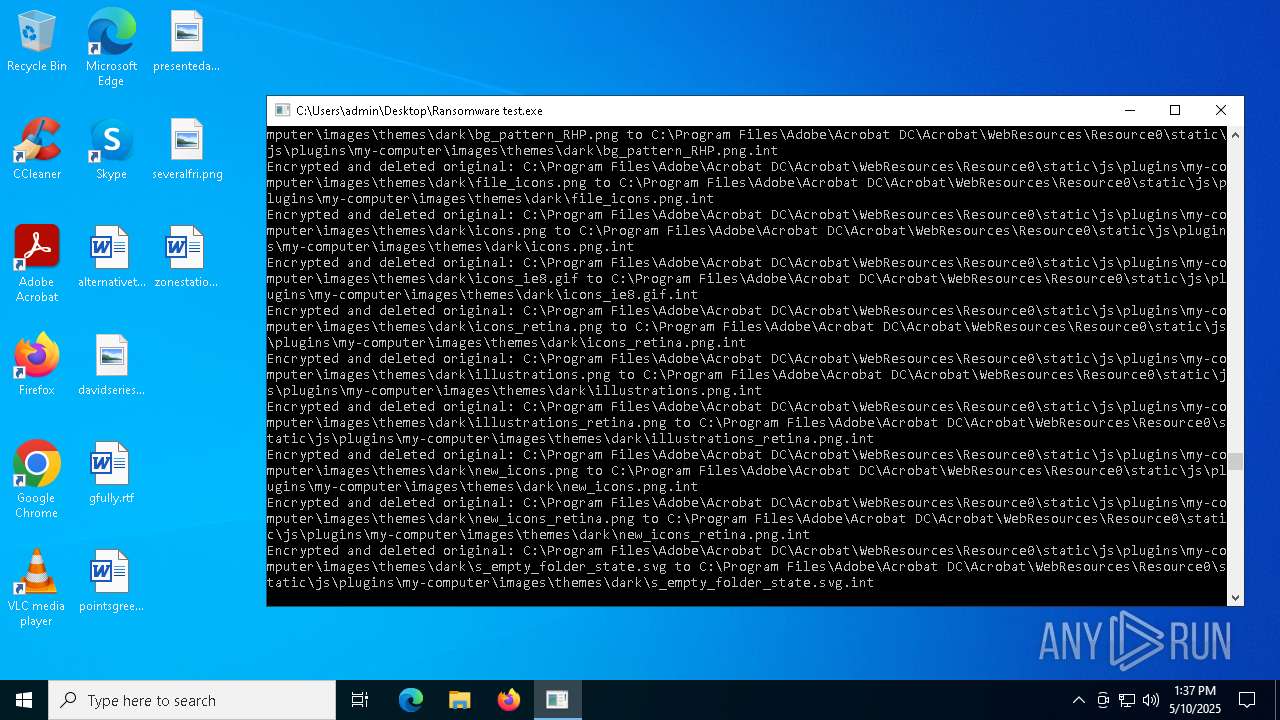
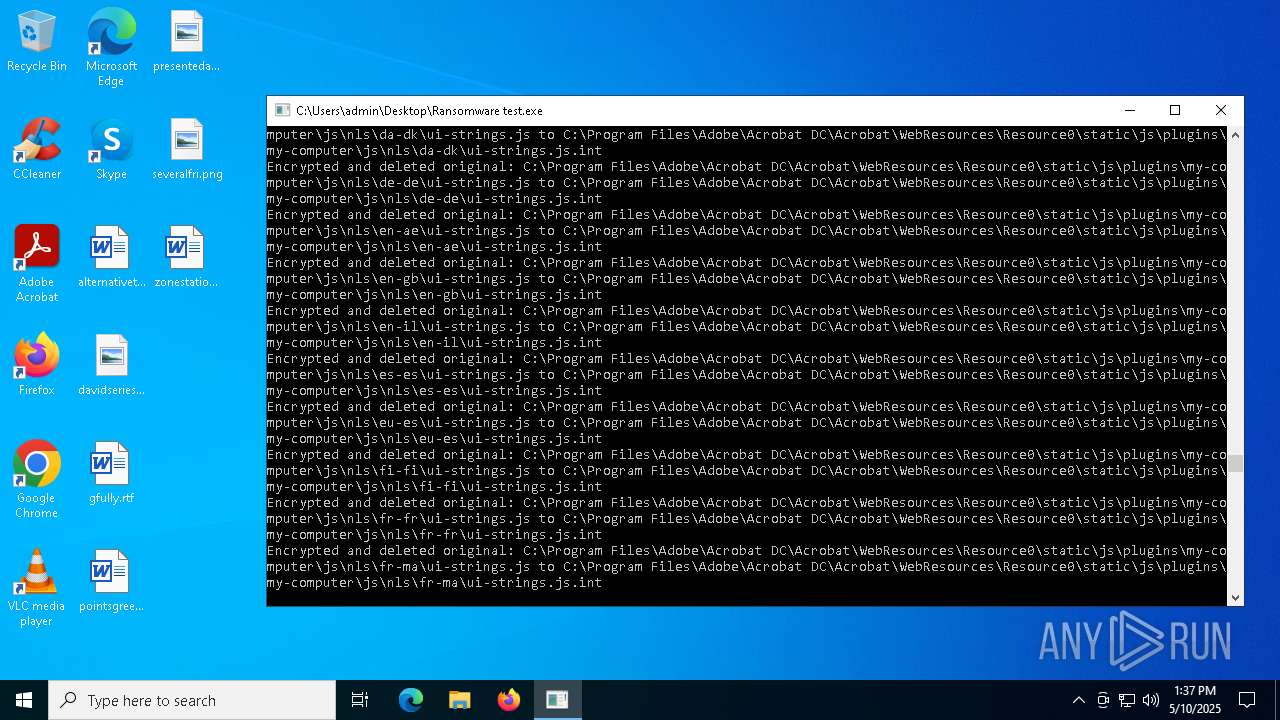
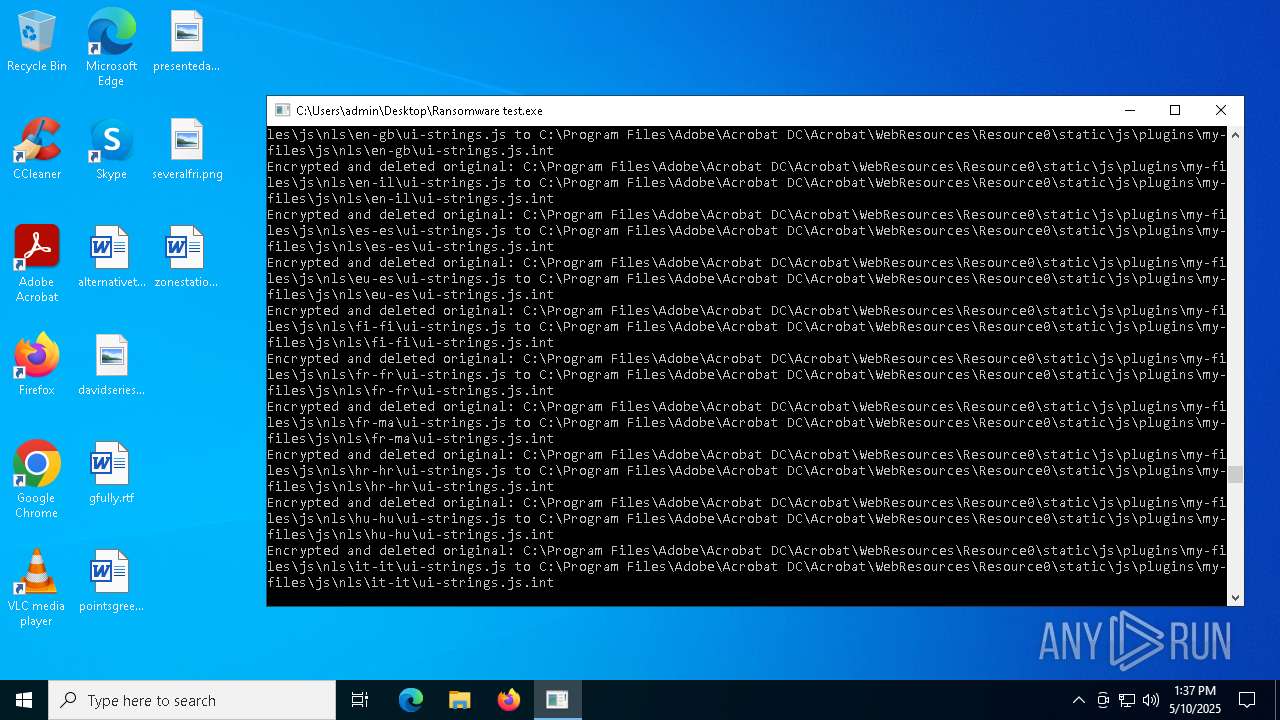
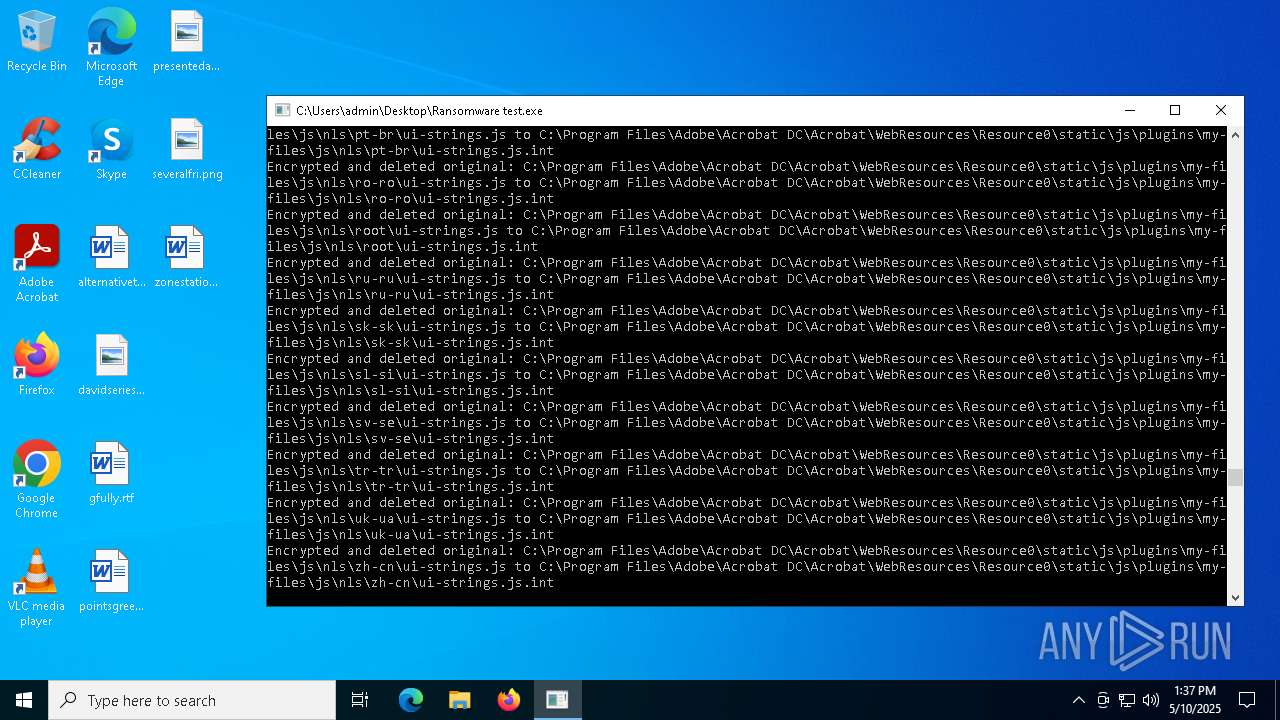
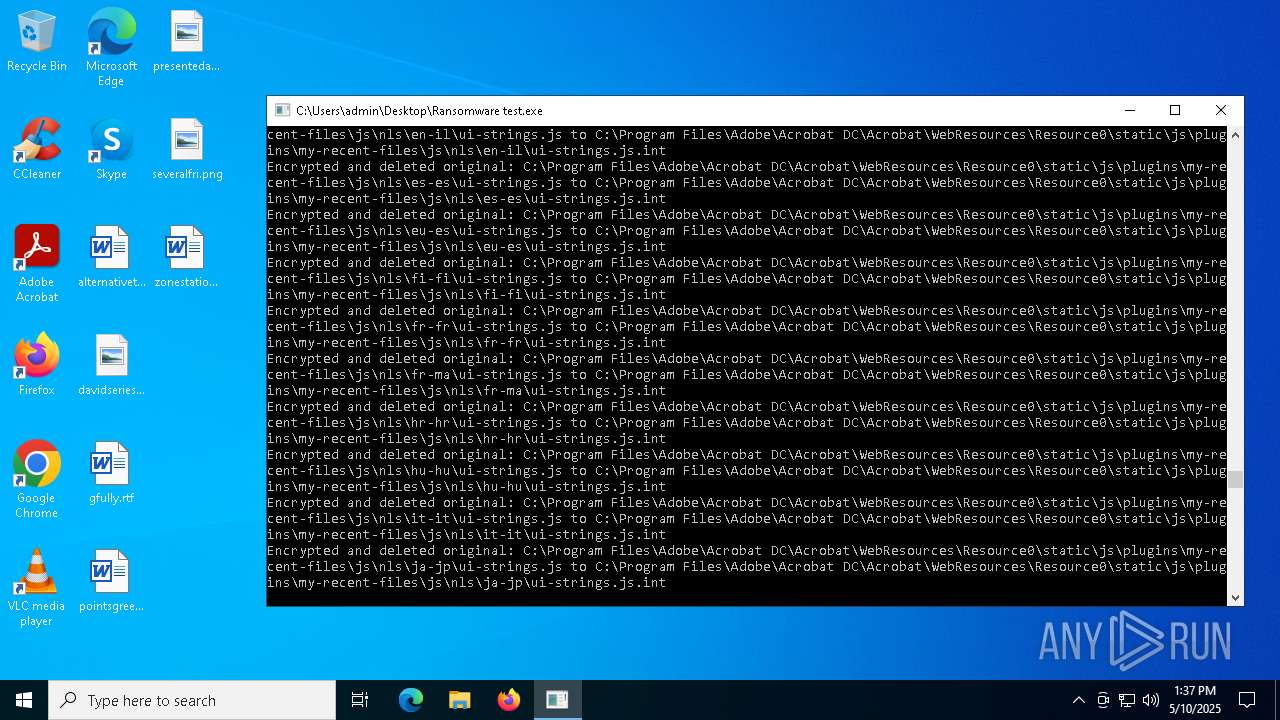
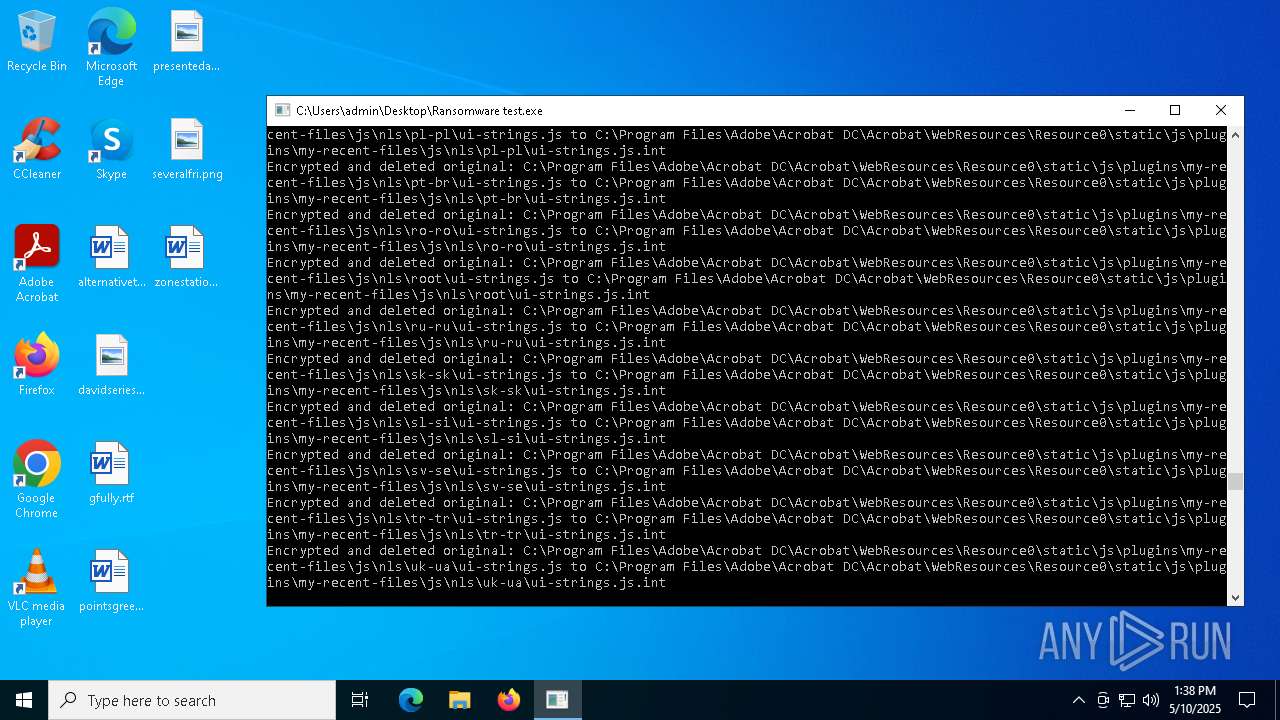
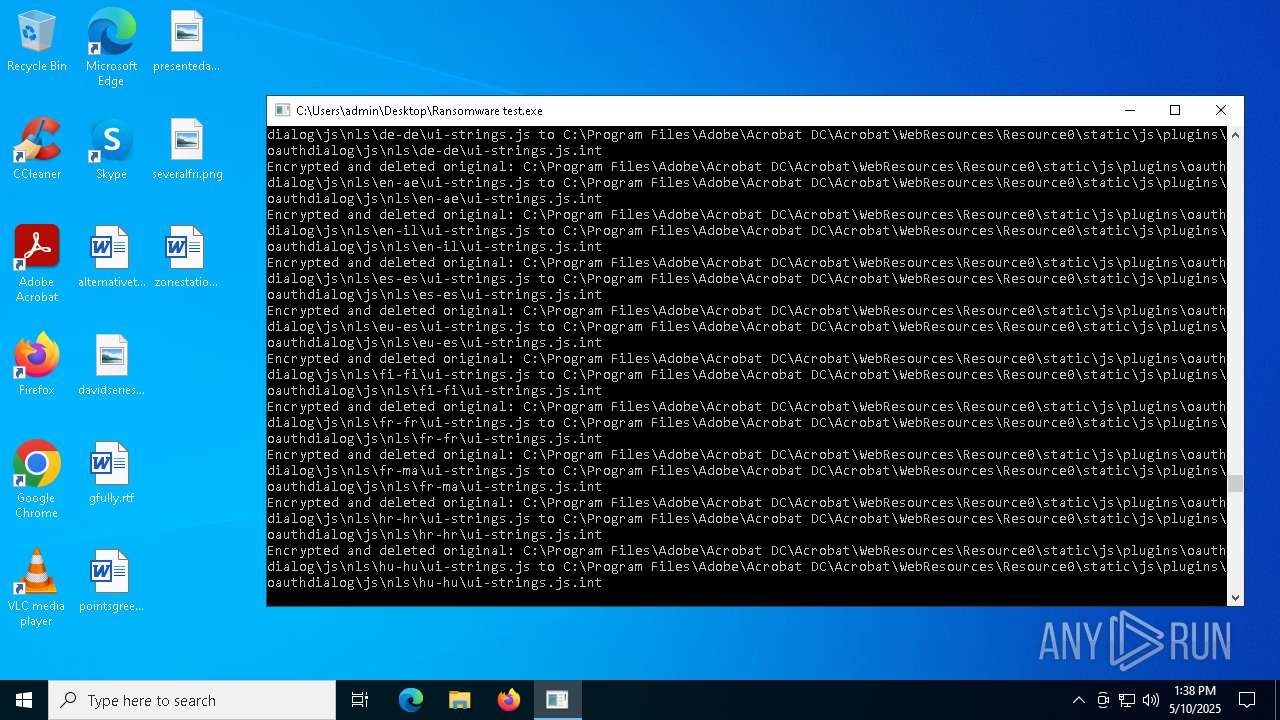
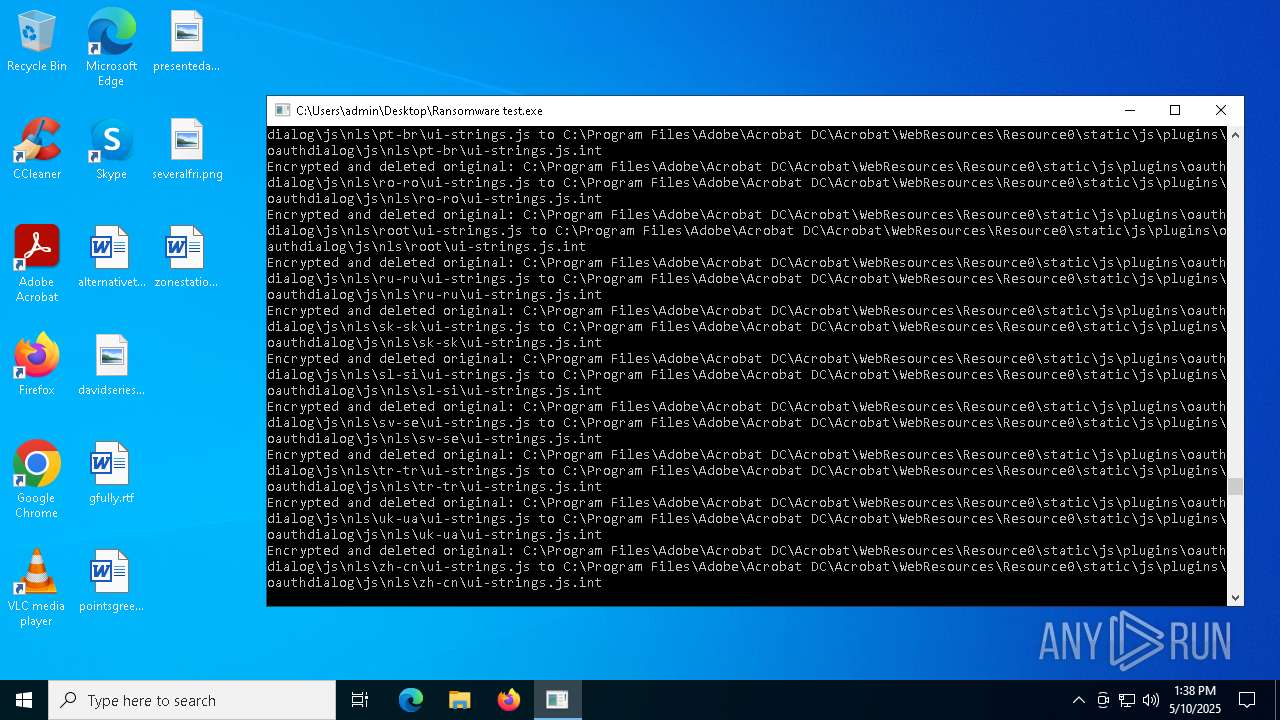
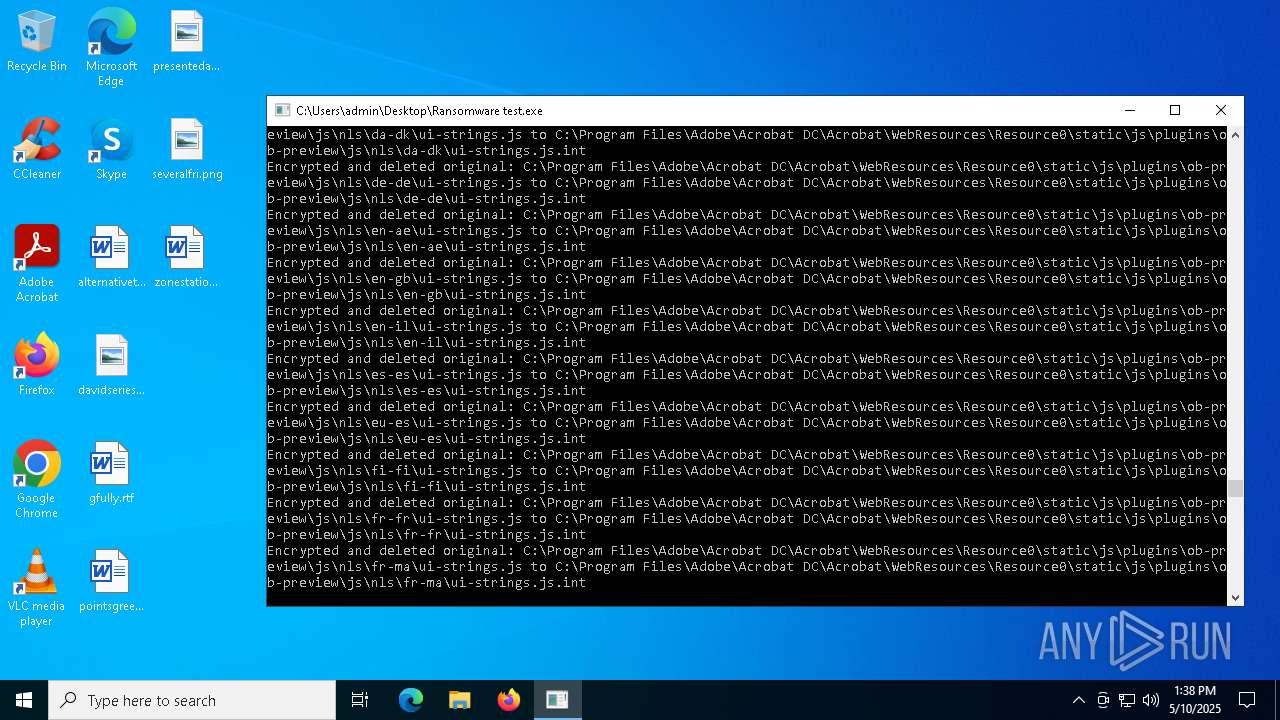
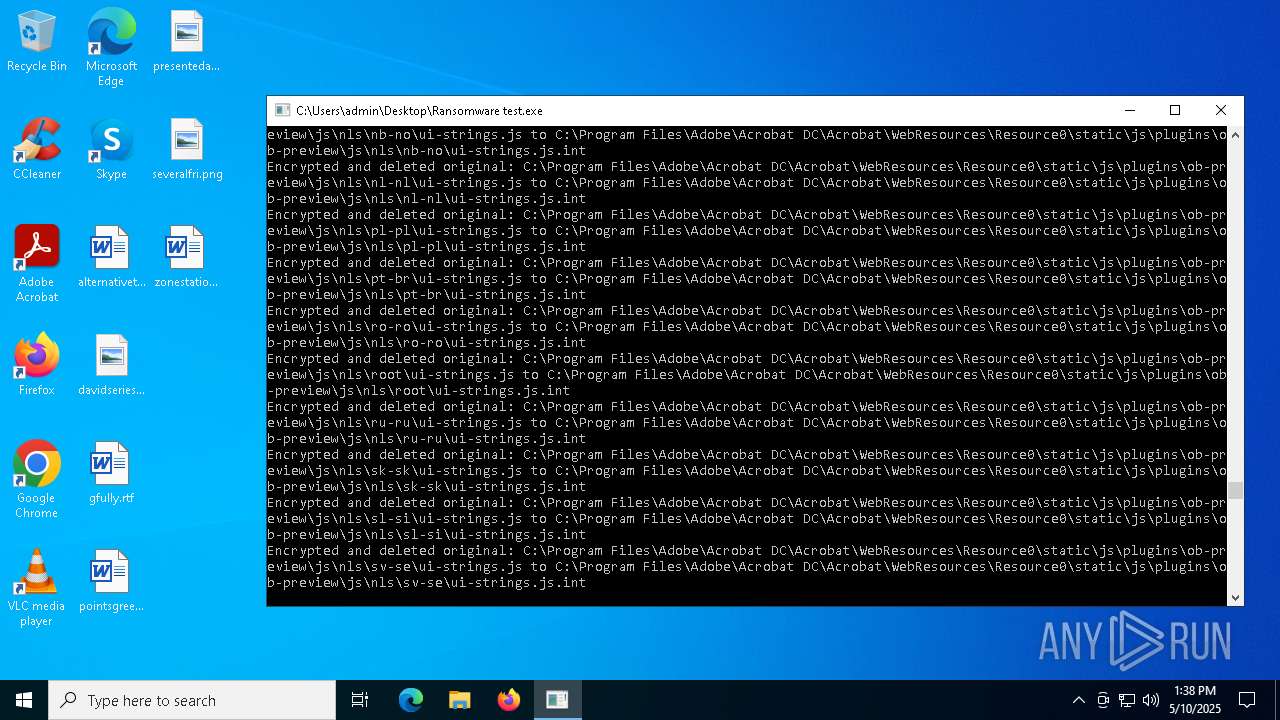
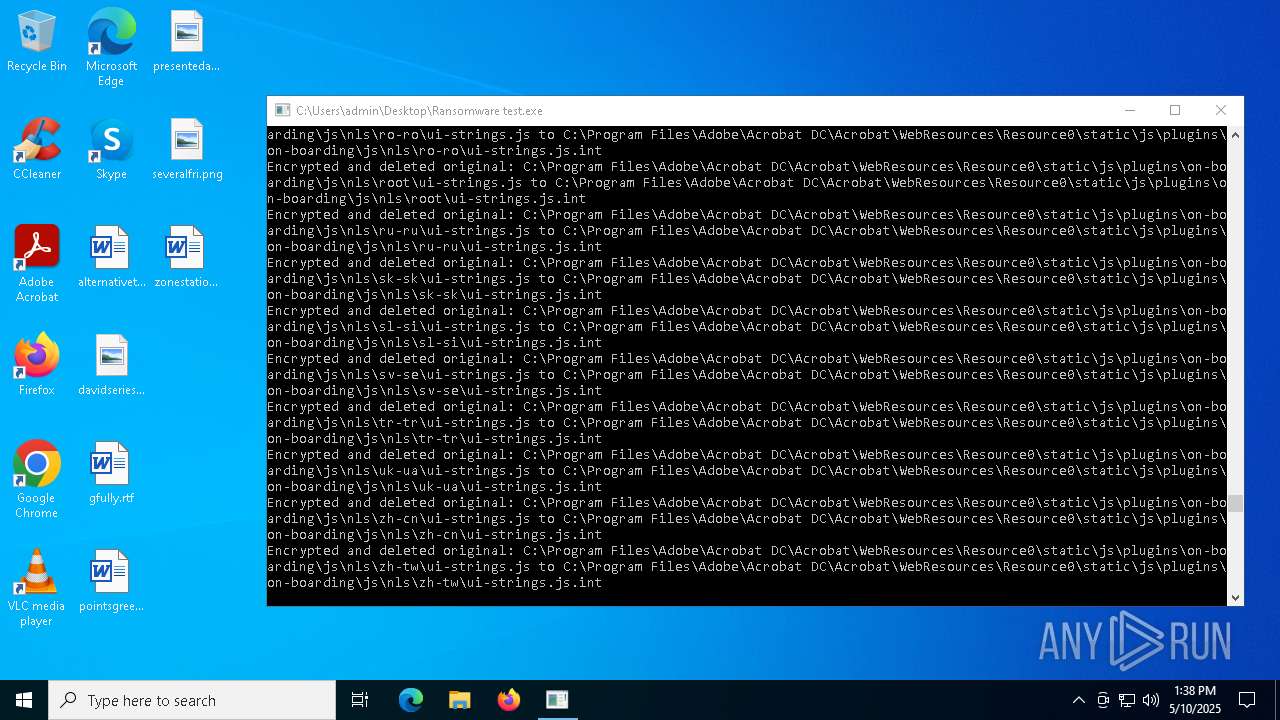
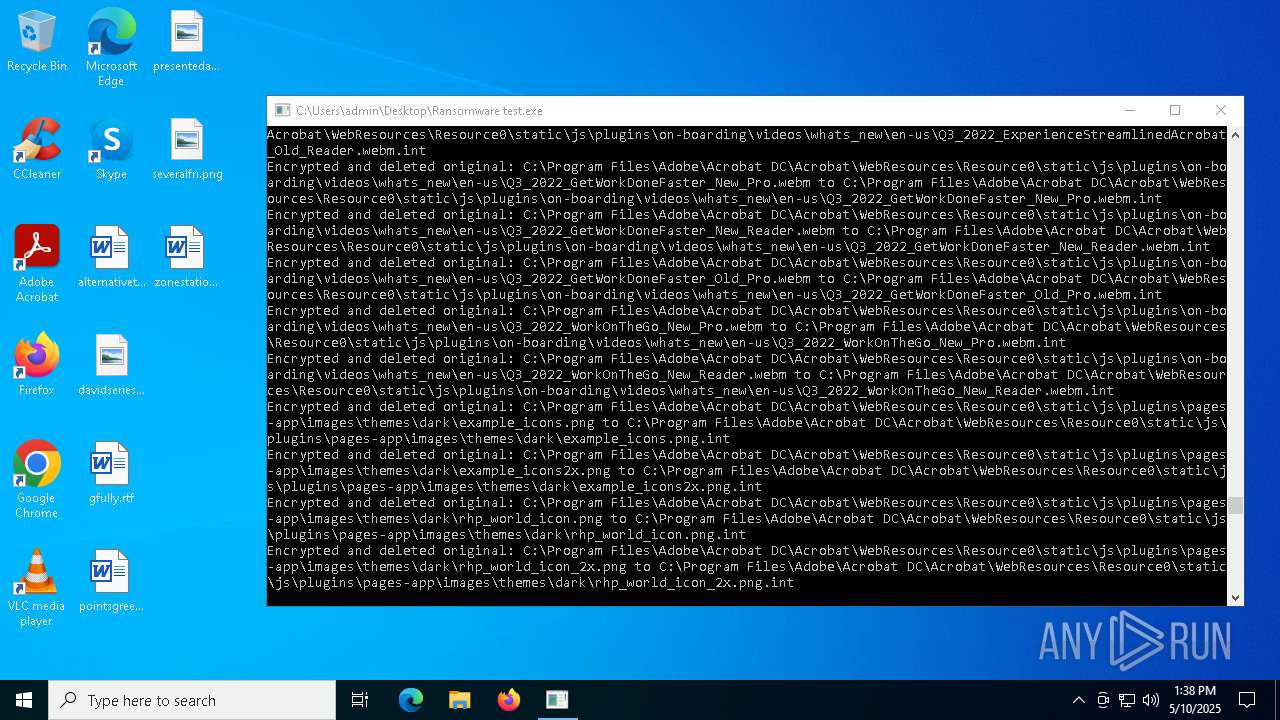
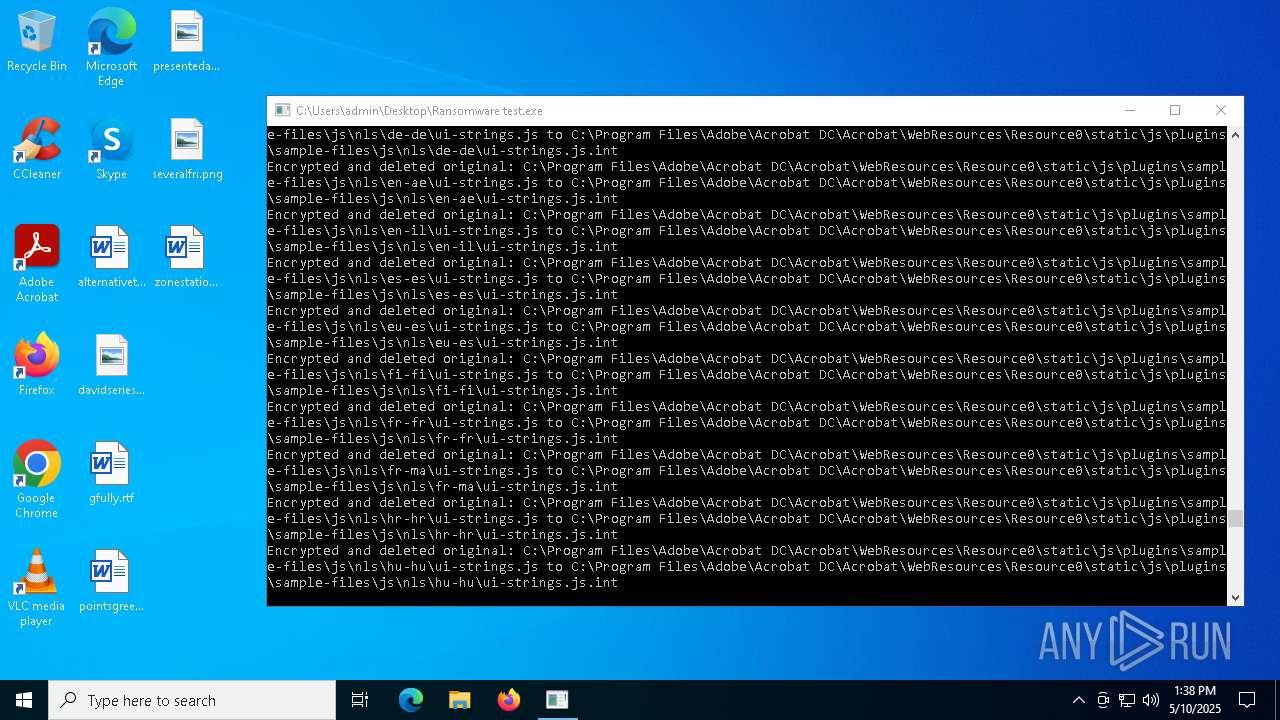
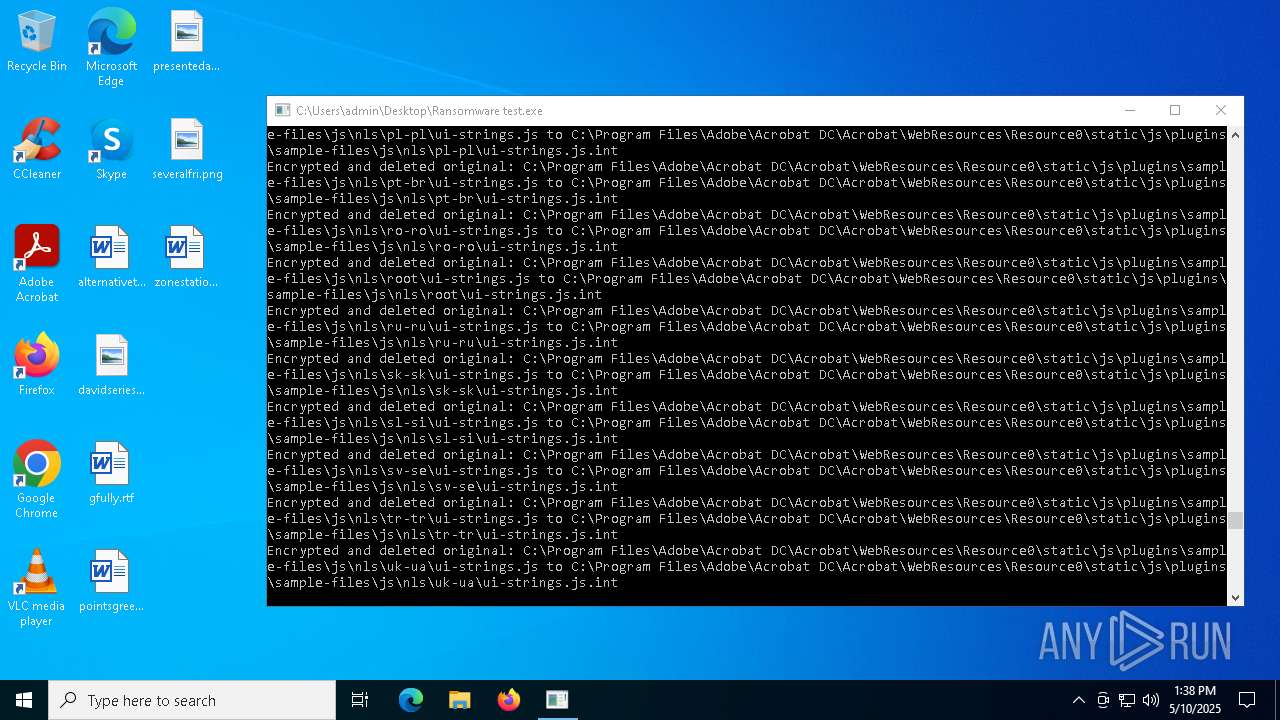
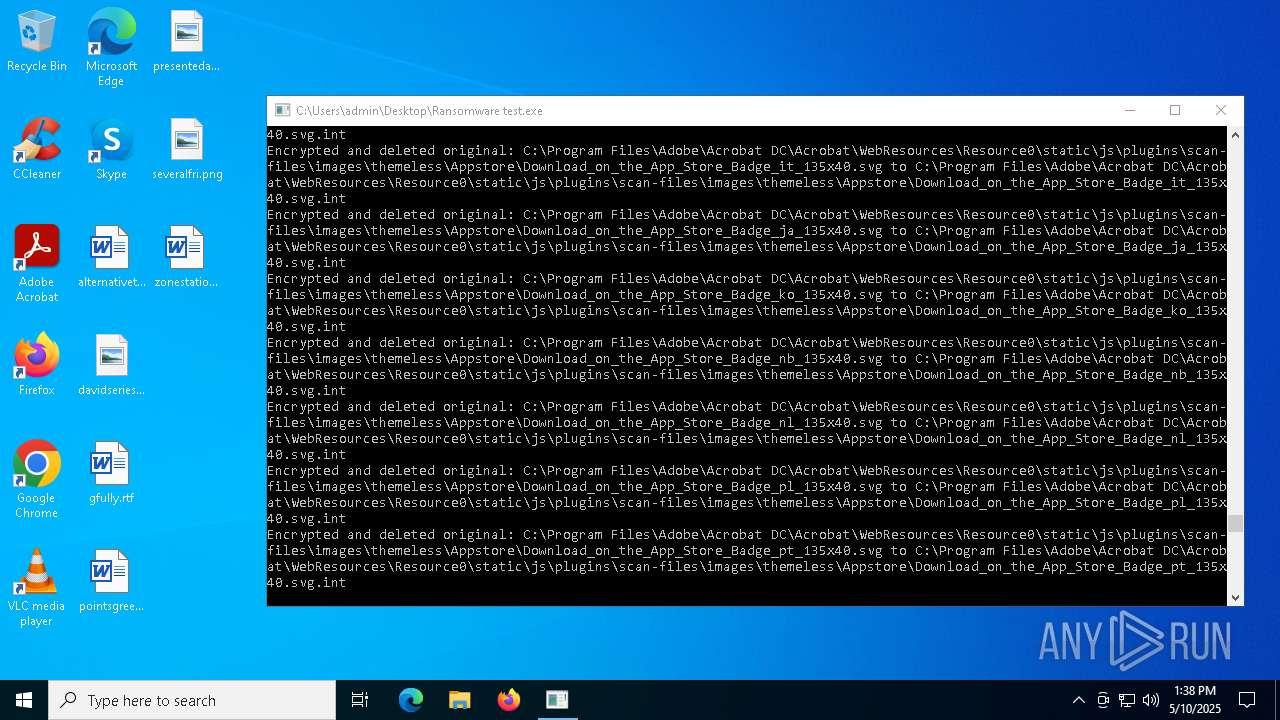
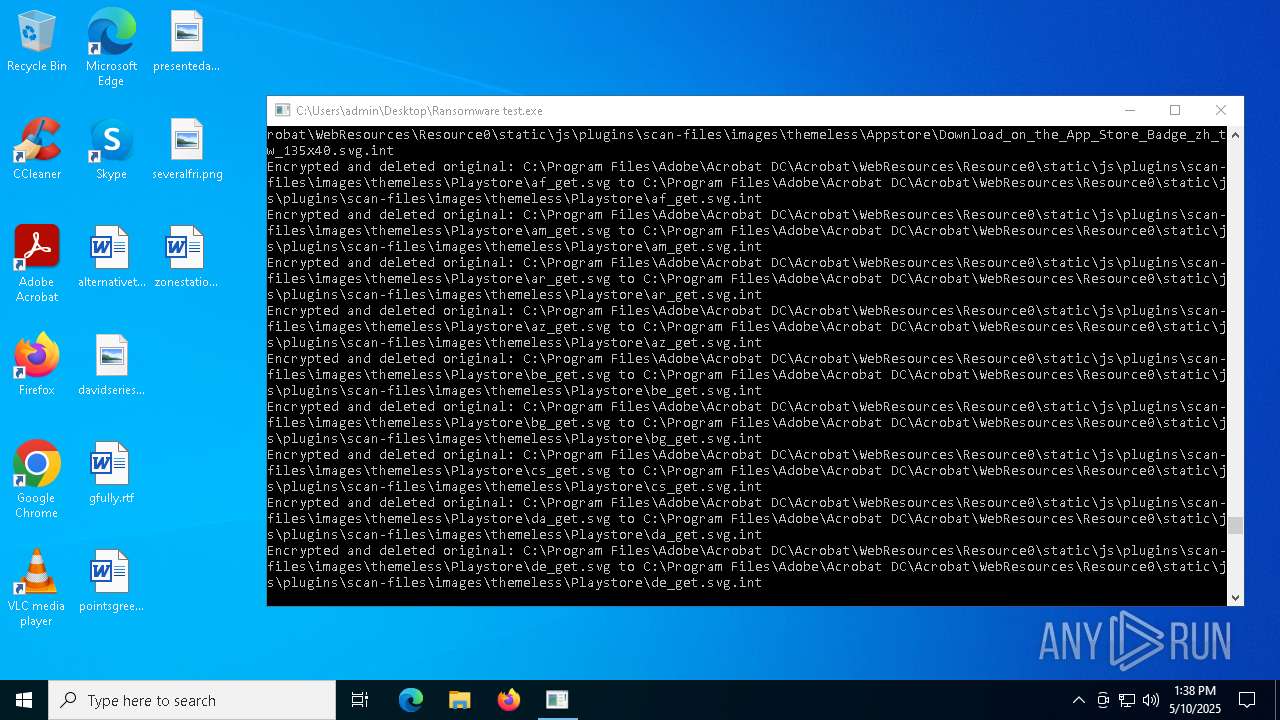
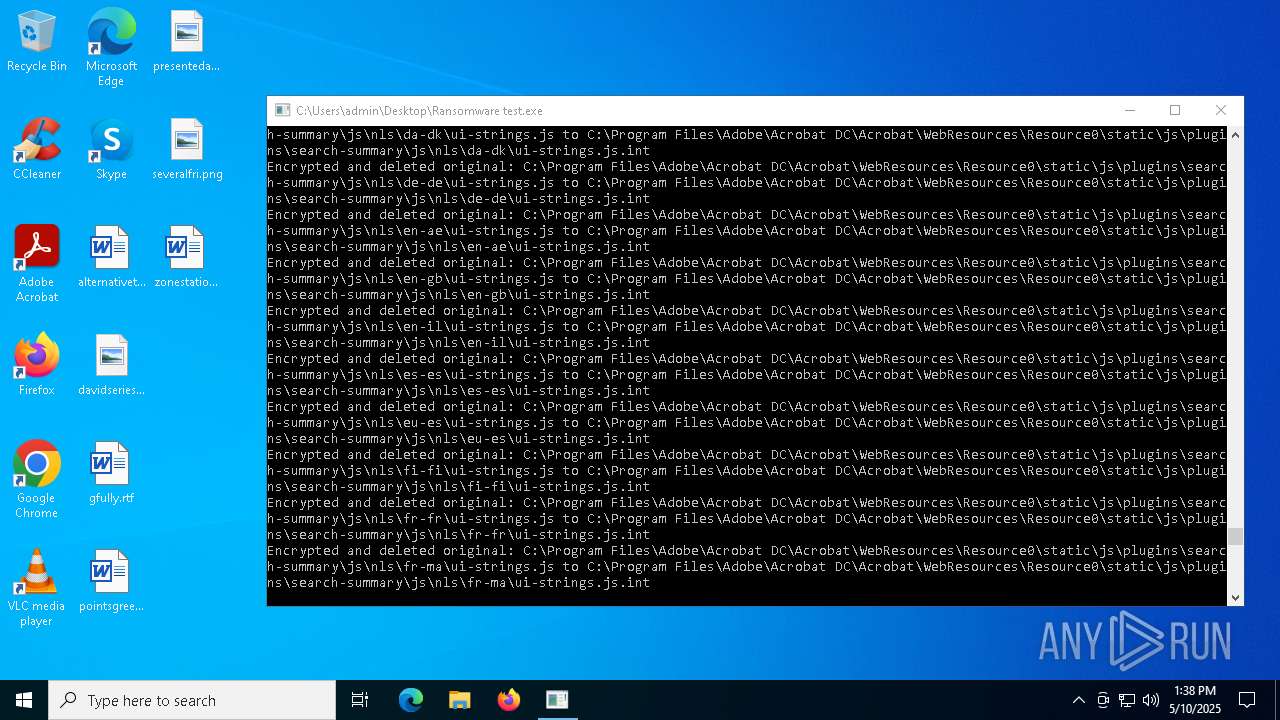
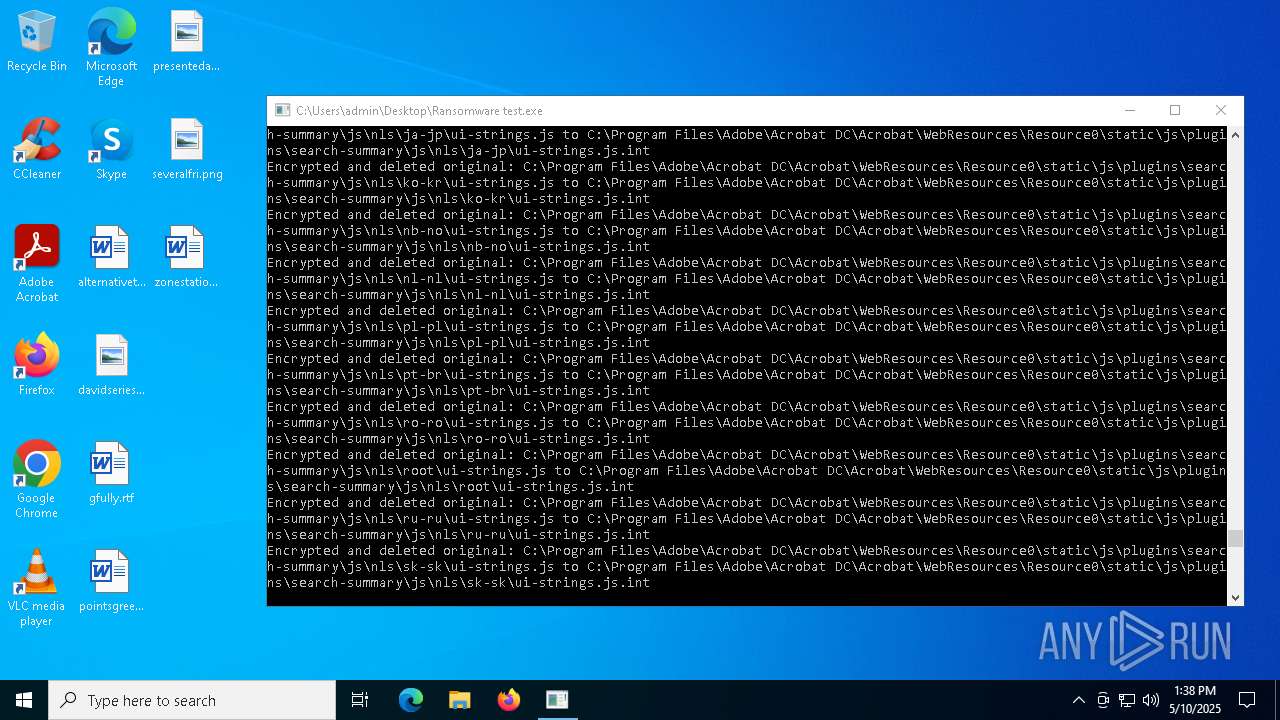
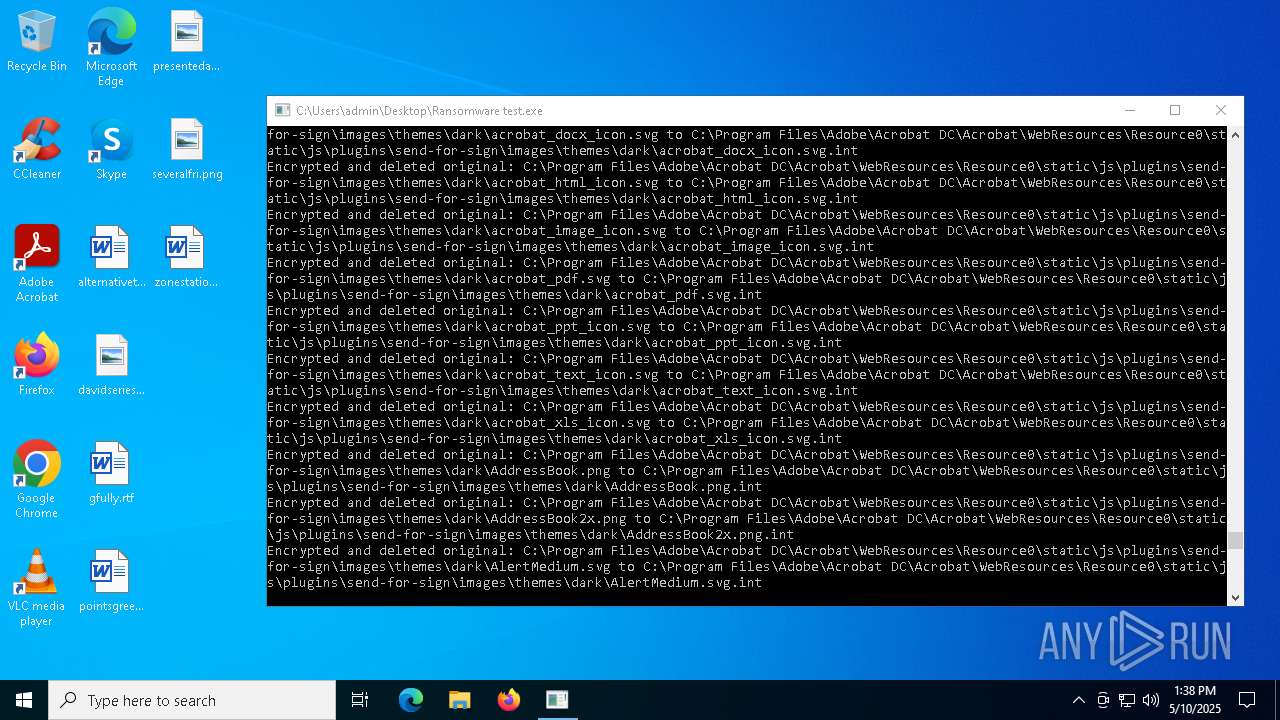
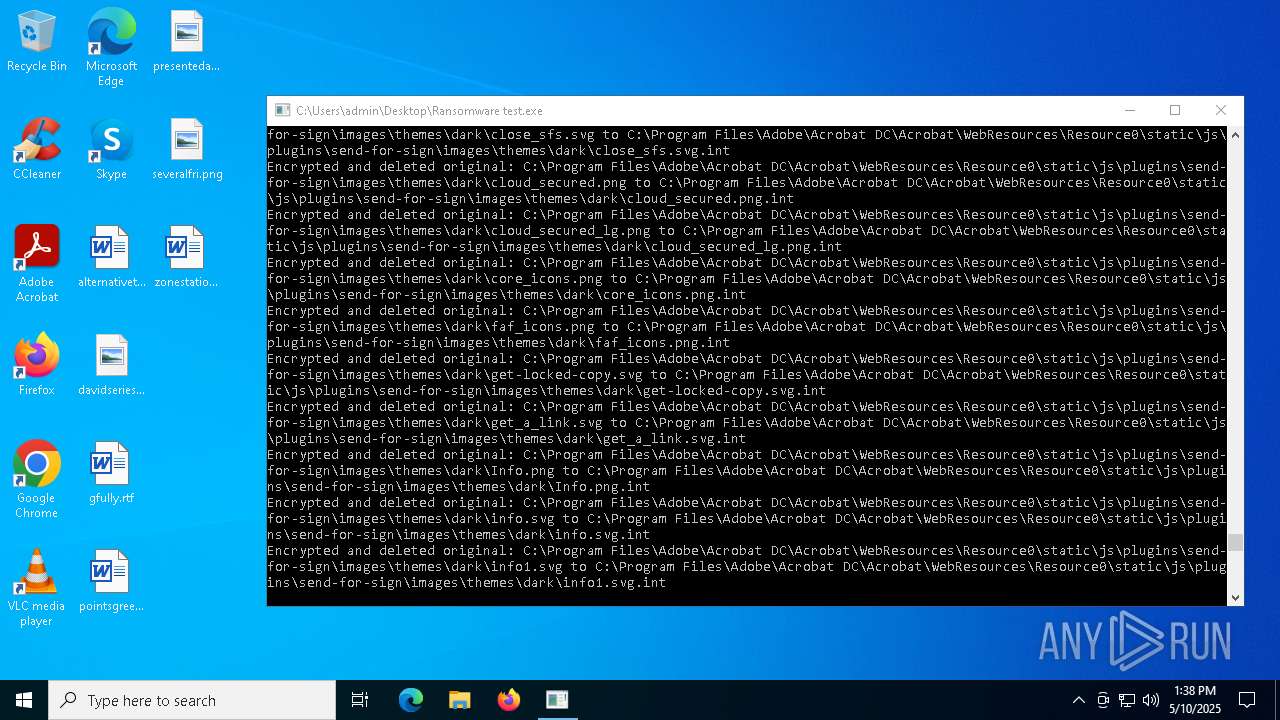
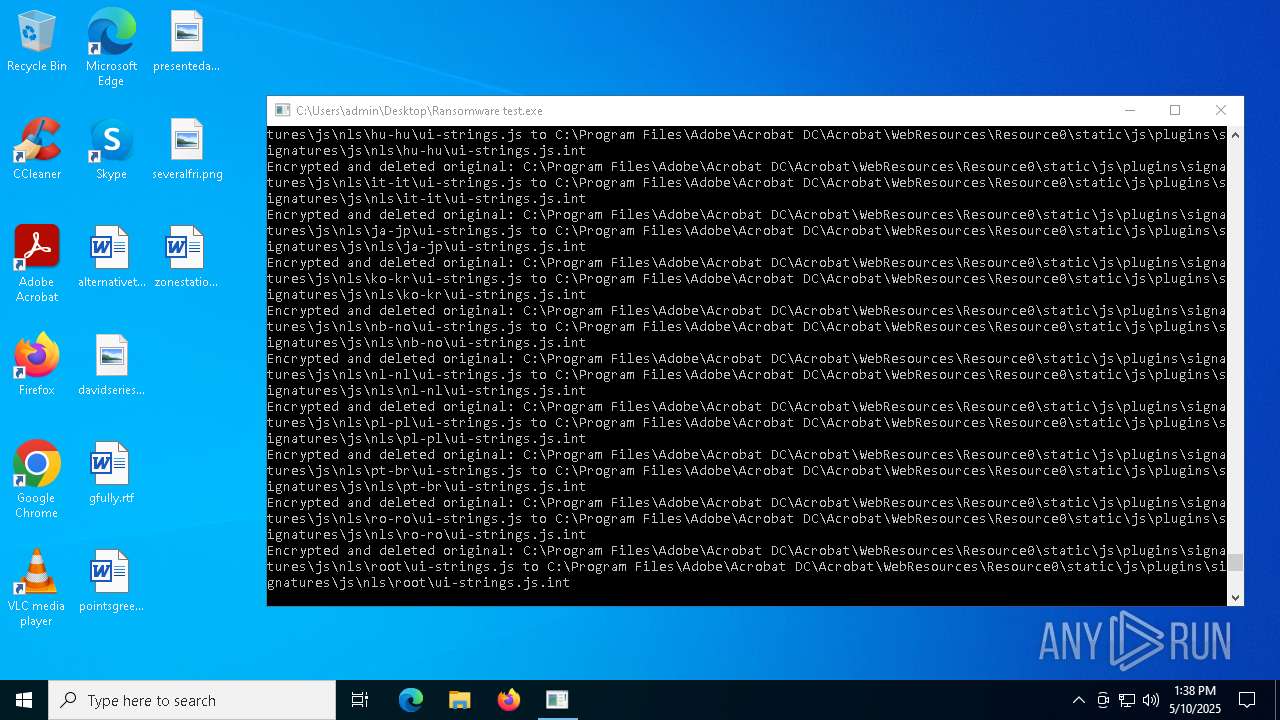
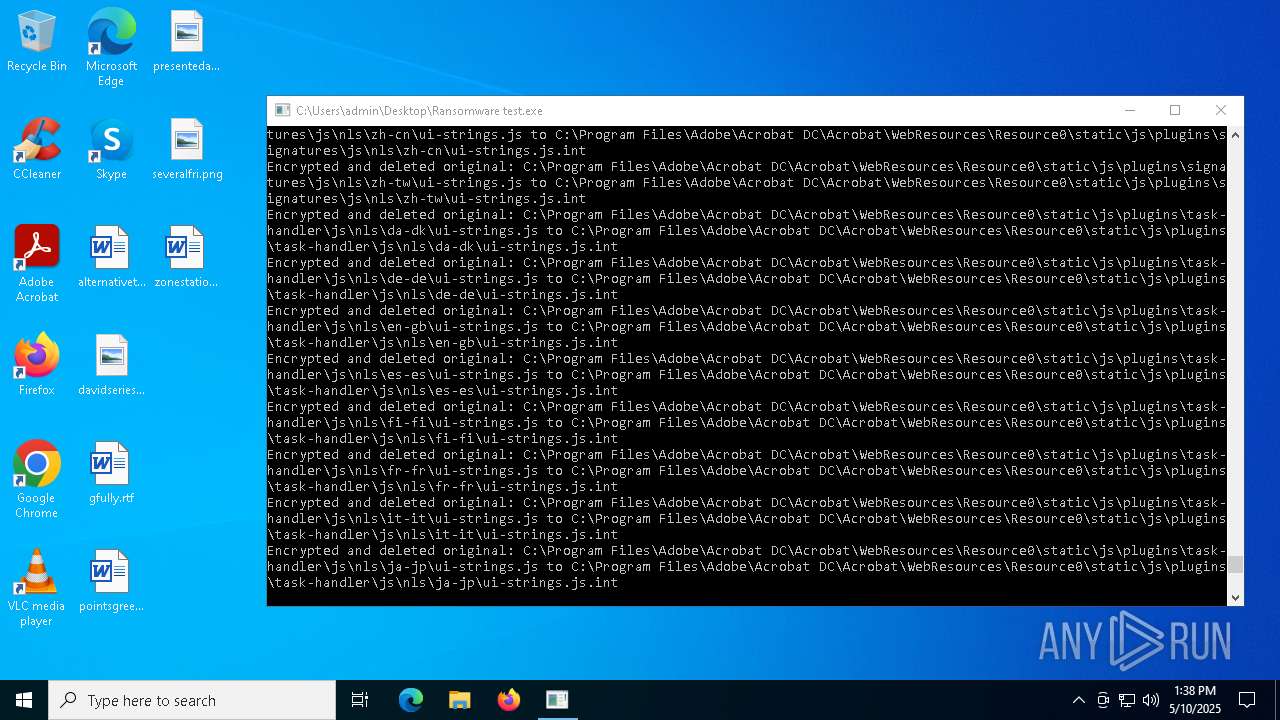
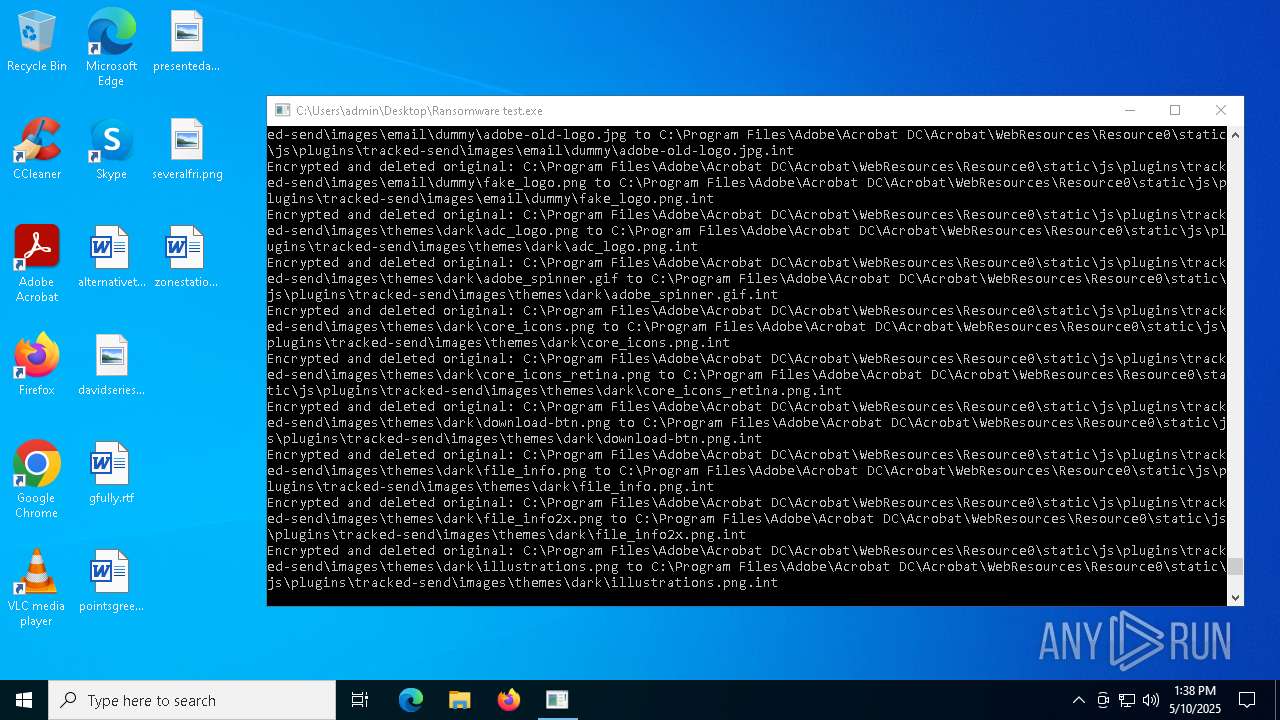
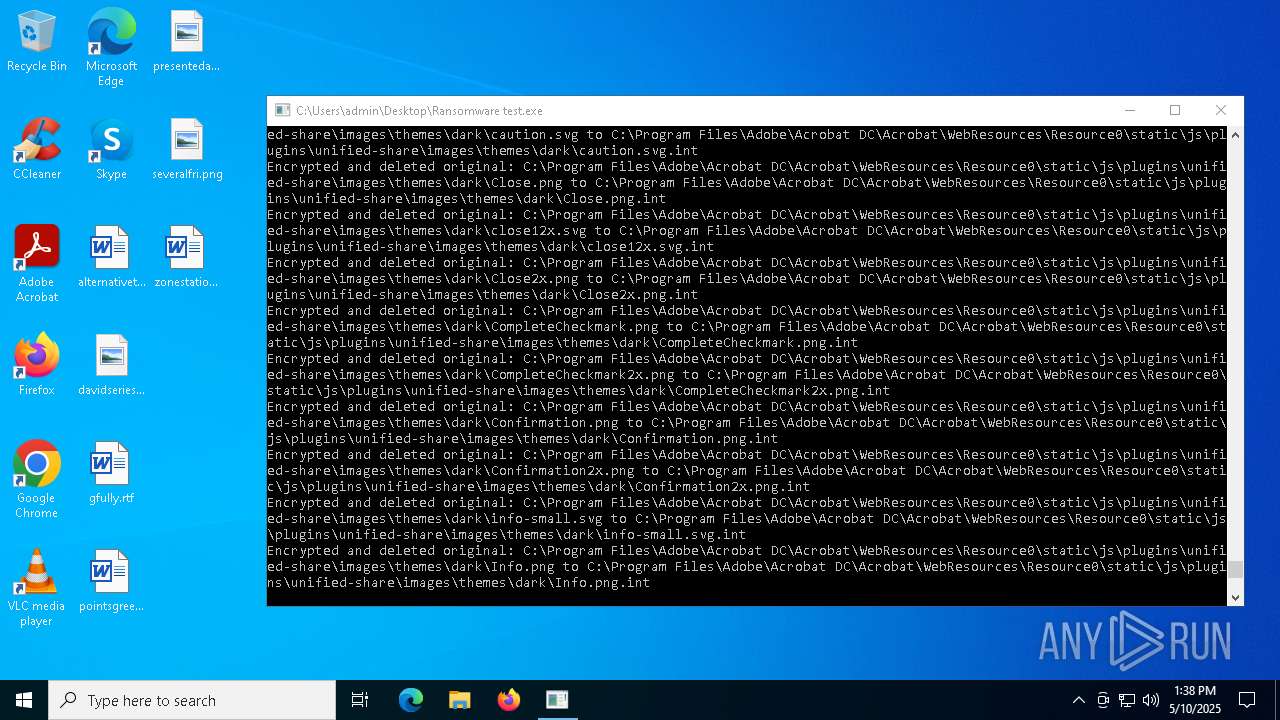
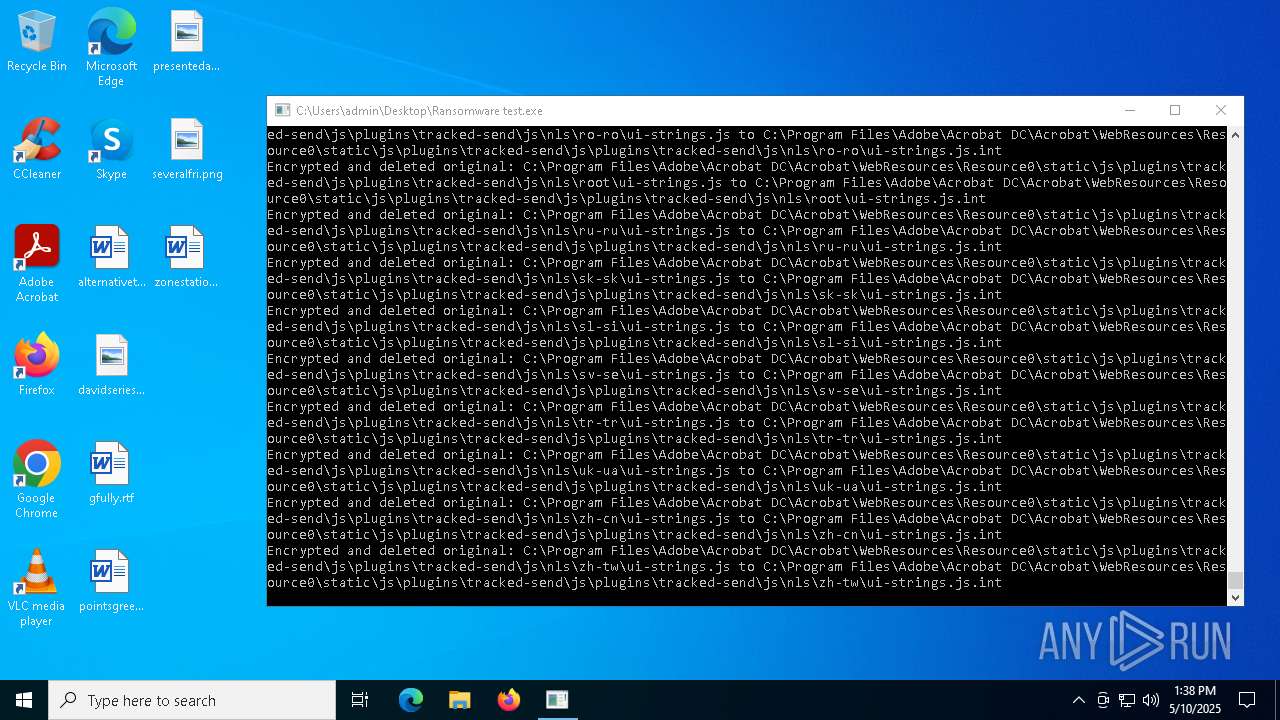
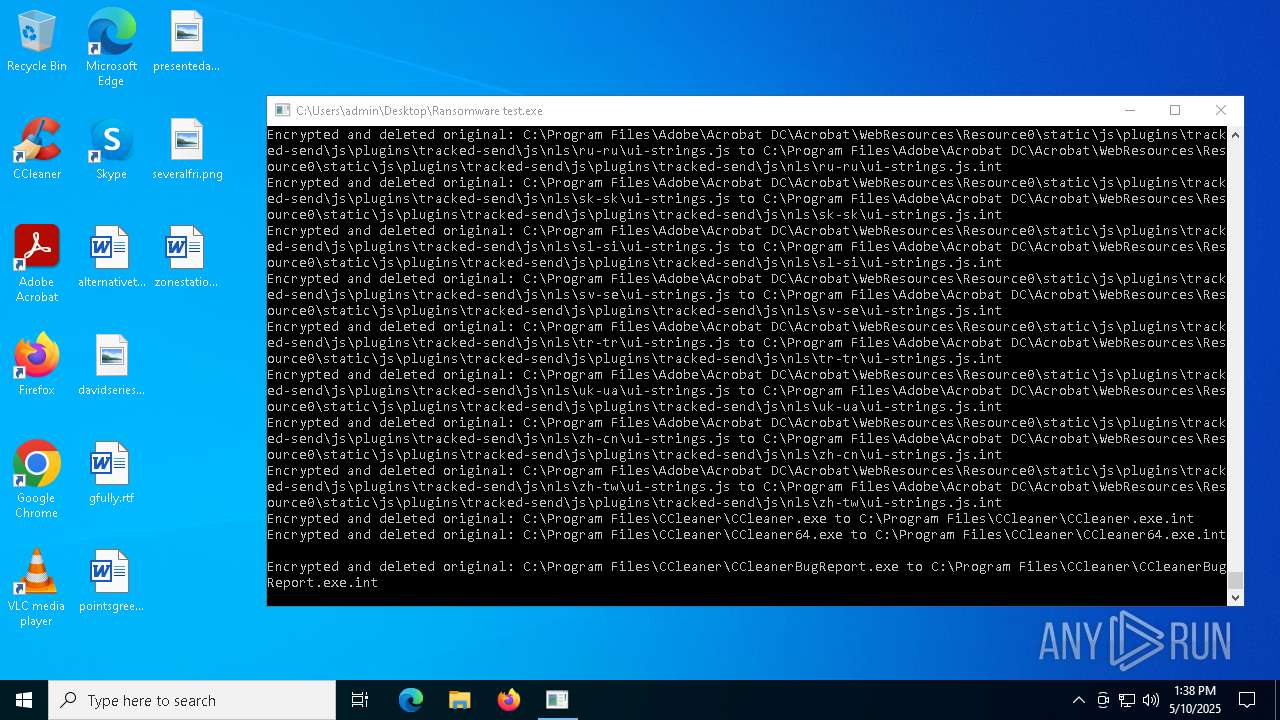
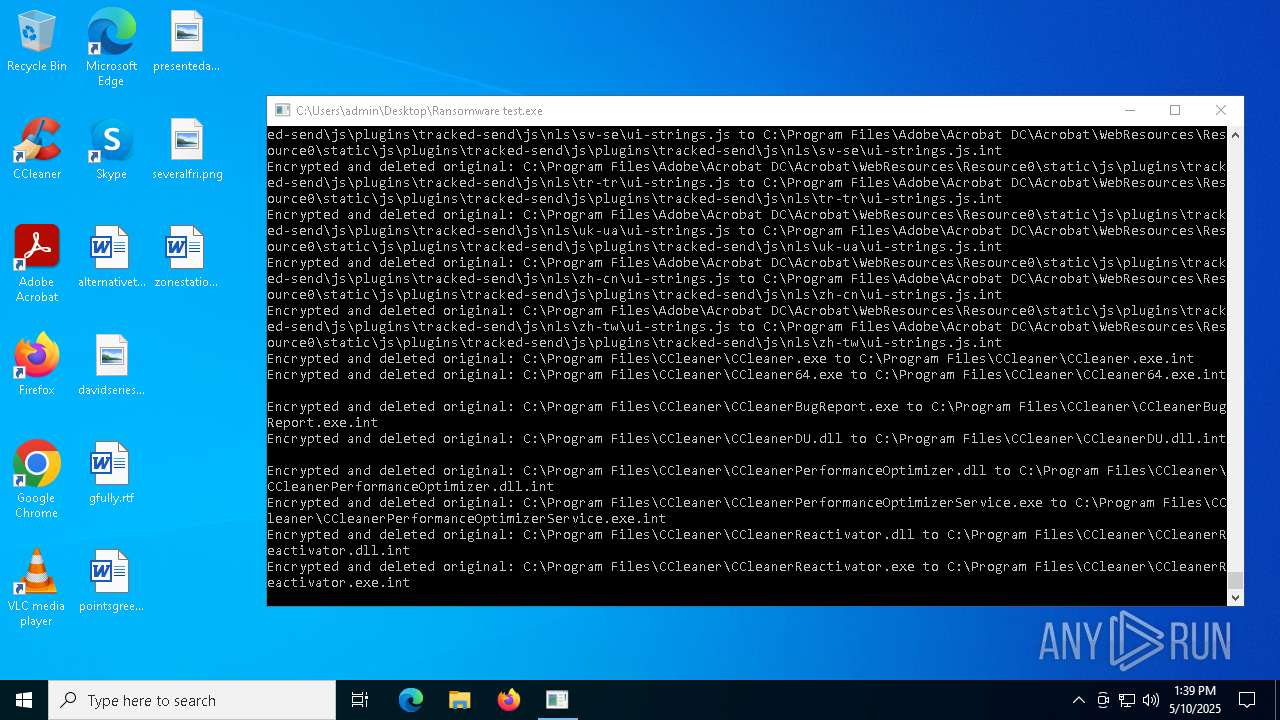
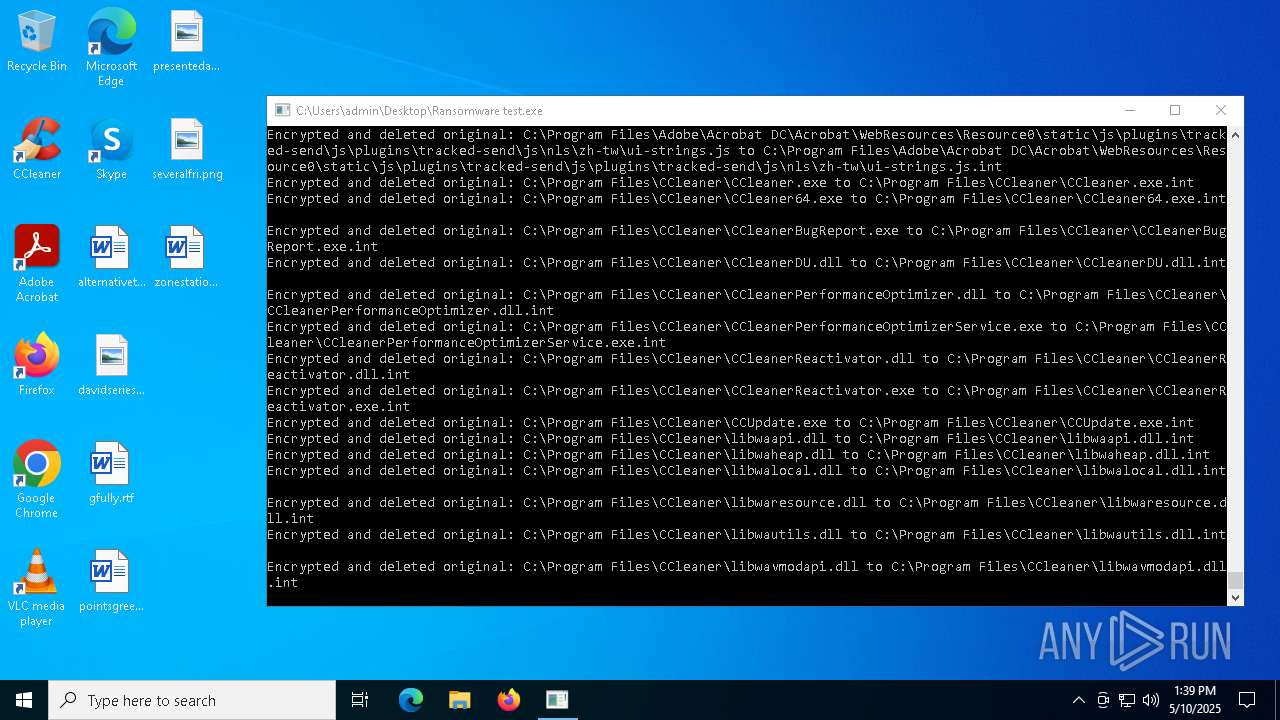
Creates files in the program directory
- Ransomware test.exe (PID: 8172)
Potential library load (Base64 Encoded 'LoadLibrary')
- Ransomware test.exe (PID: 8172)
Potential dynamic function import (Base64 Encoded 'GetProcAddress')
- Ransomware test.exe (PID: 8172)
Reads the software policy settings
- slui.exe (PID: 7708)
- slui.exe (PID: 6240)
Checks proxy server information
- slui.exe (PID: 6240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:10 15:33:44 |
| ZipCRC: | 0x2eaa5705 |
| ZipCompressedSize: | 7755079 |
| ZipUncompressedSize: | 17233340 |
| ZipFileName: | Ransomware test.exe |
Total processes
139
Monitored processes
7
Malicious processes
1
Suspicious processes
0
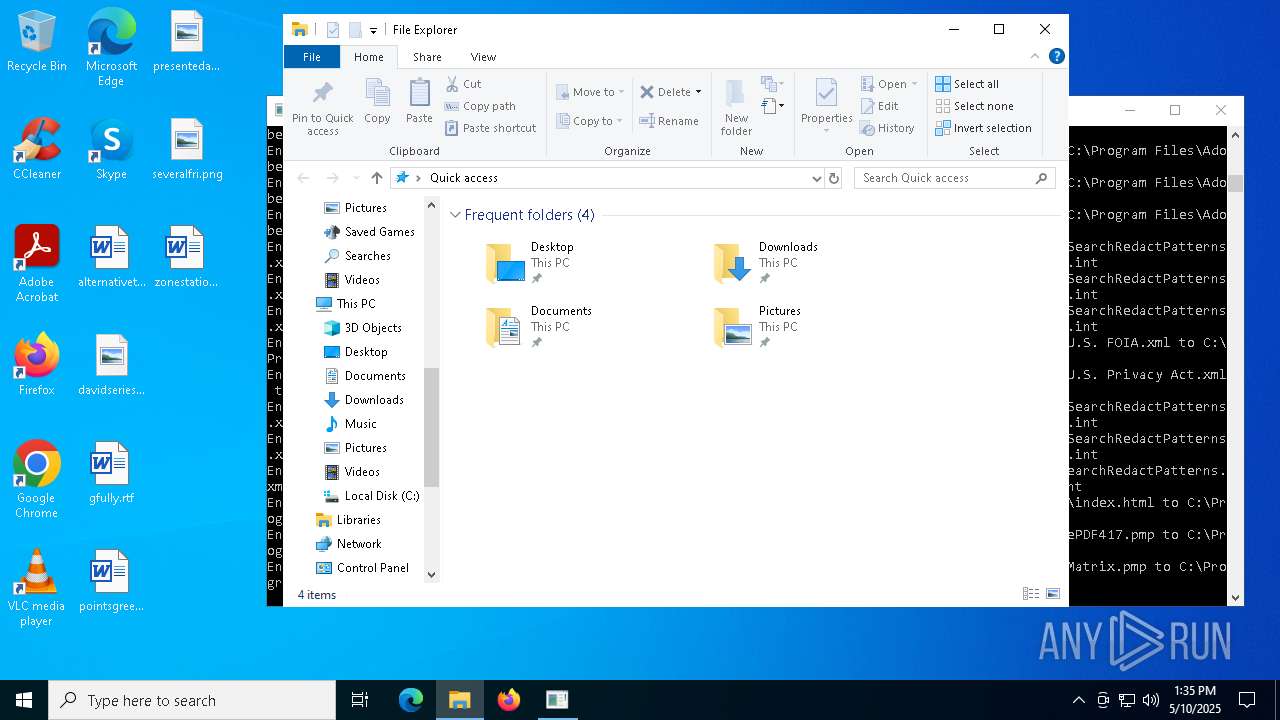
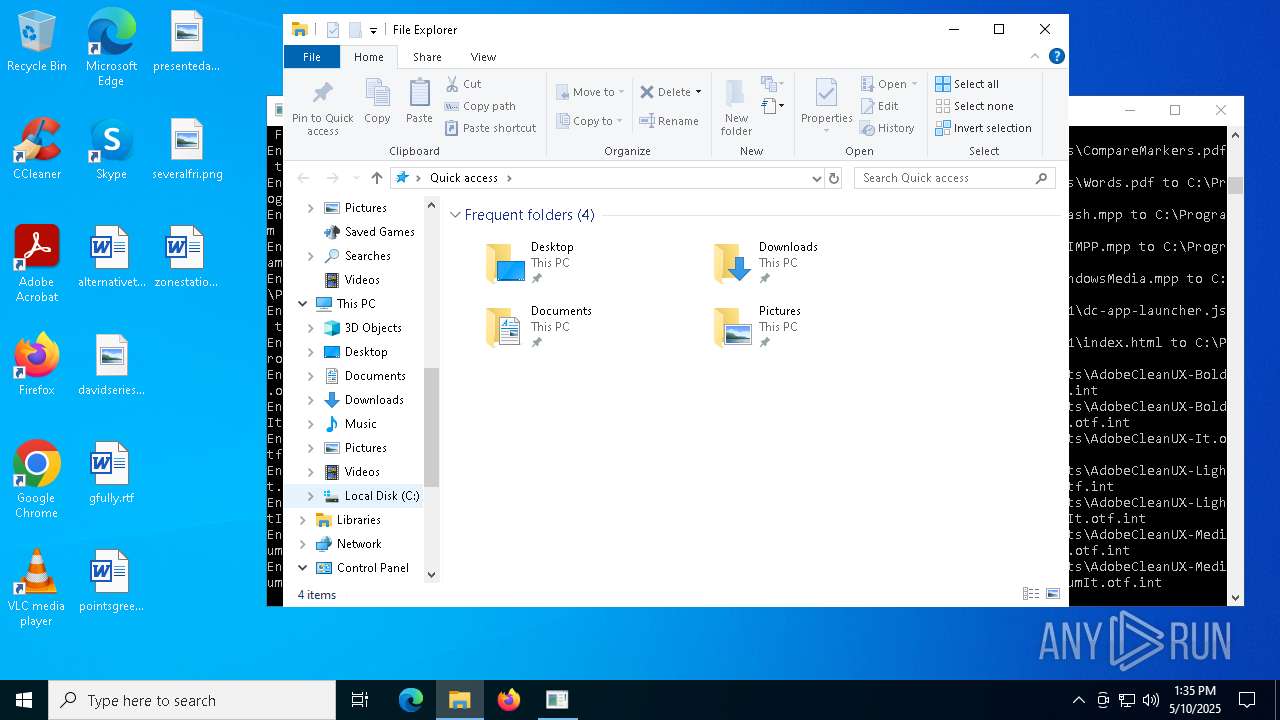
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5800 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6240 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7516 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Ransomware test.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7672 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7708 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8172 | "C:\Users\admin\Desktop\Ransomware test.exe" | C:\Users\admin\Desktop\Ransomware test.exe | explorer.exe | ||||||||||||
User: admin Company: Ransomware test Integrity Level: HIGH Description: Ransomware test Version: 1.0.0.0 Modules
| |||||||||||||||
| 8184 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Ransomware test.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 659
Read events
2 640
Write events
19
Delete events
0
Modification events
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Ransomware test.zip | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
1
Suspicious files
0
Text files
3 555
Unknown types
0
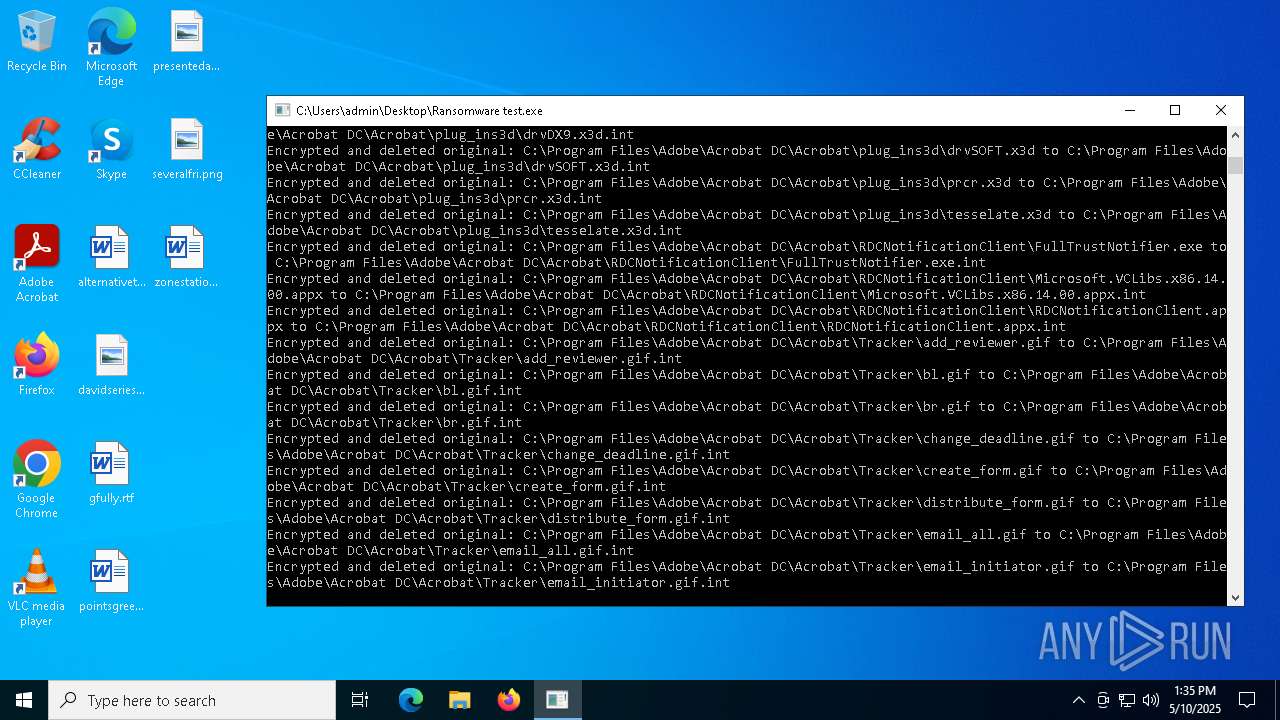
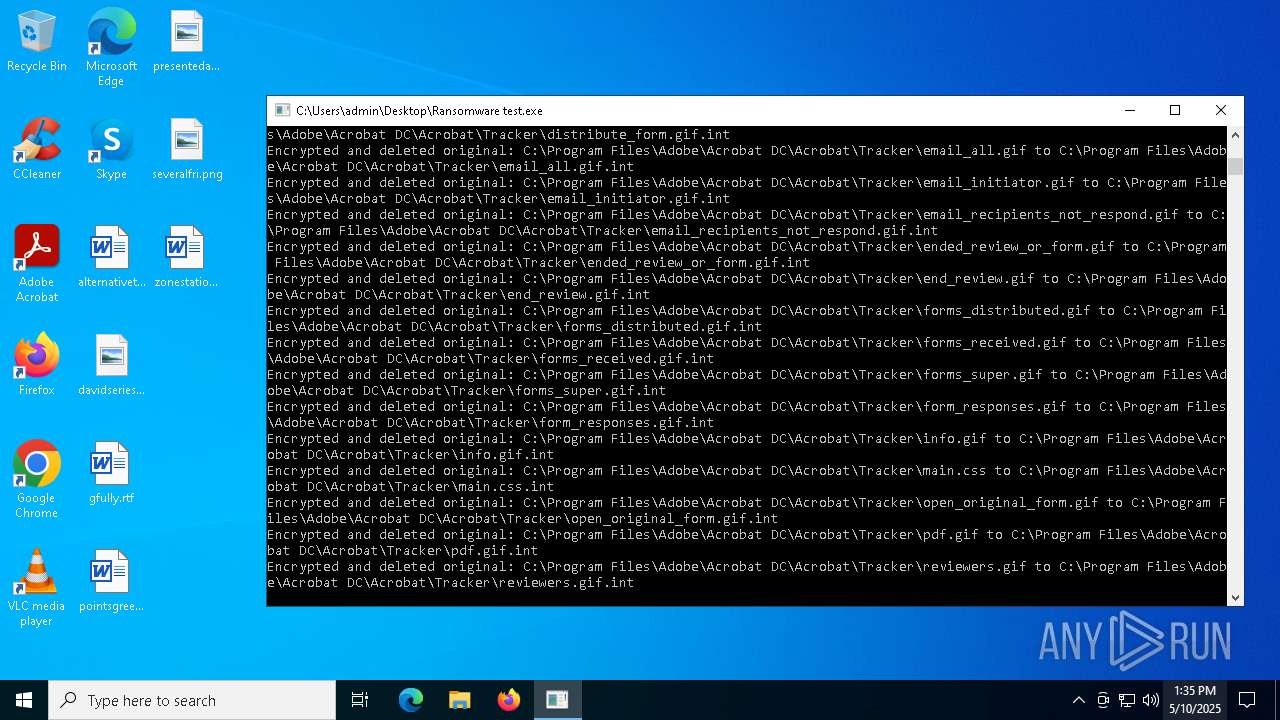
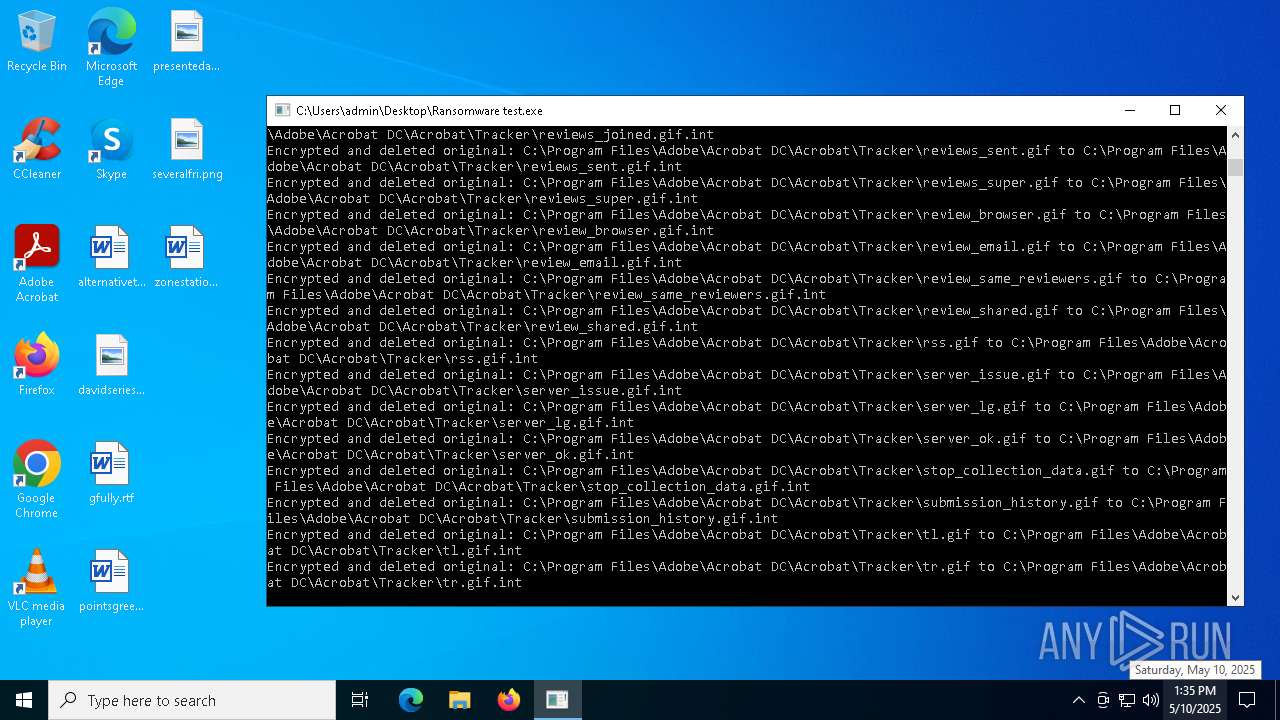
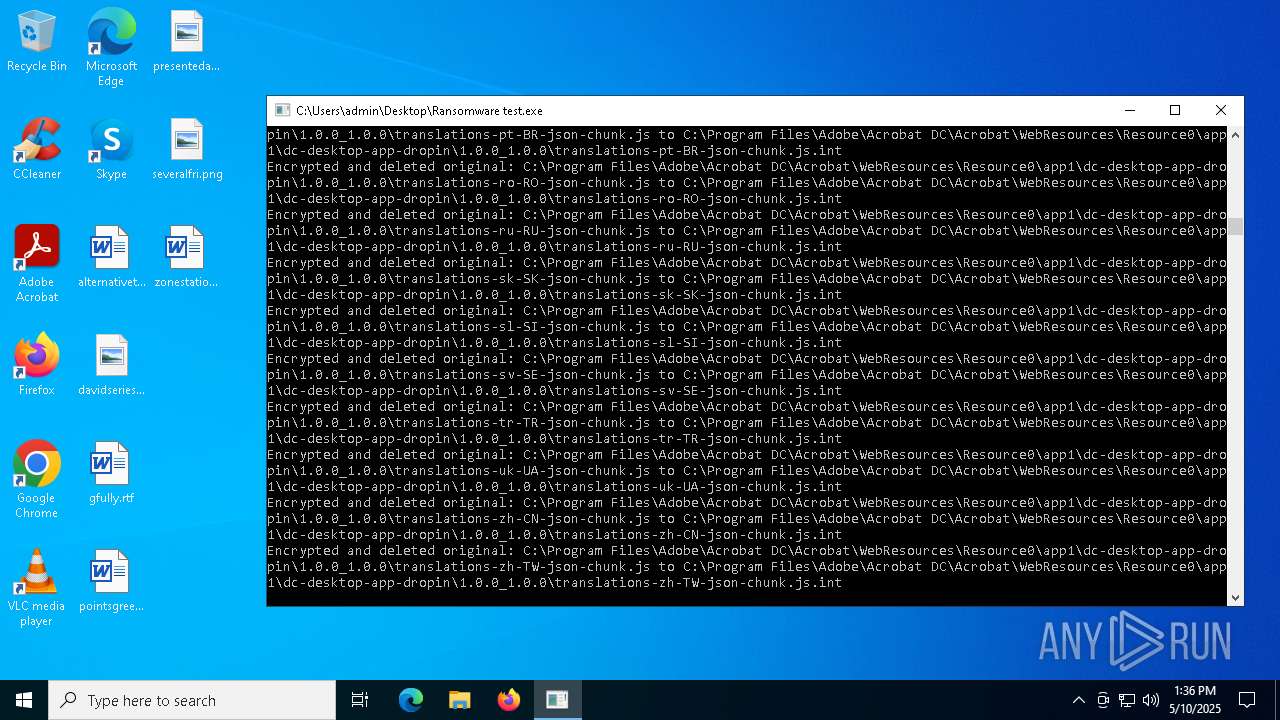
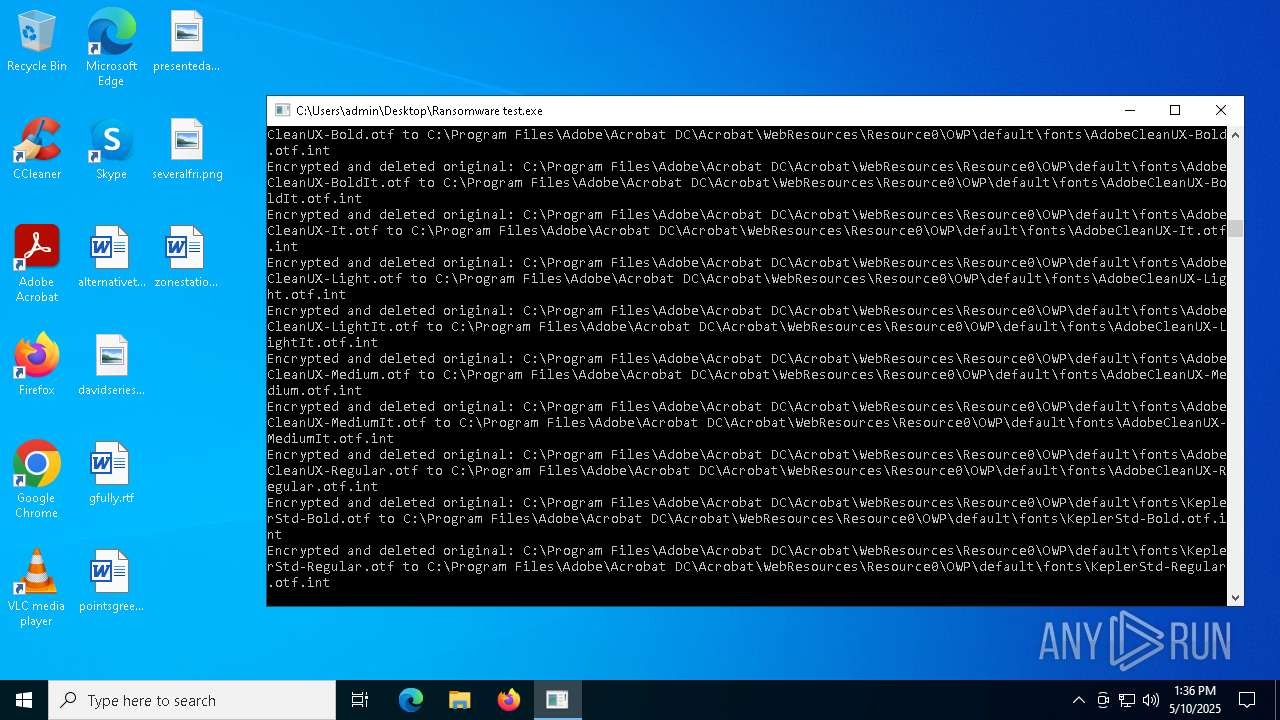
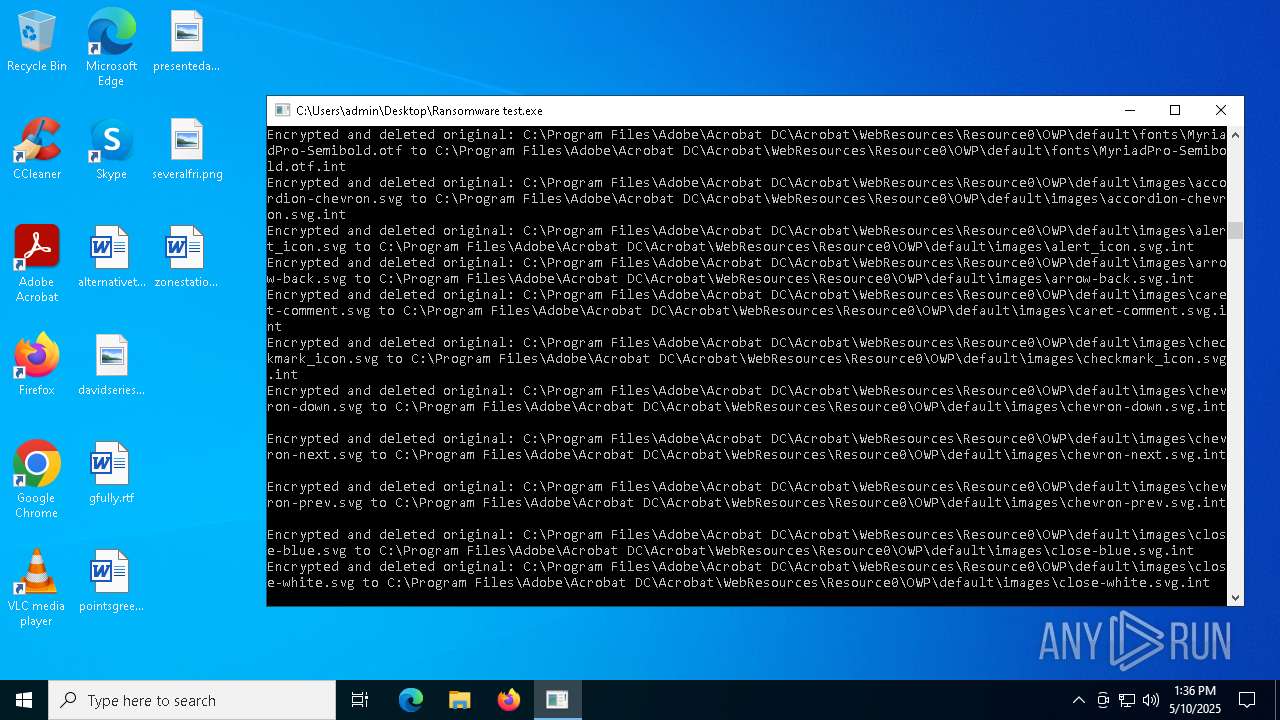
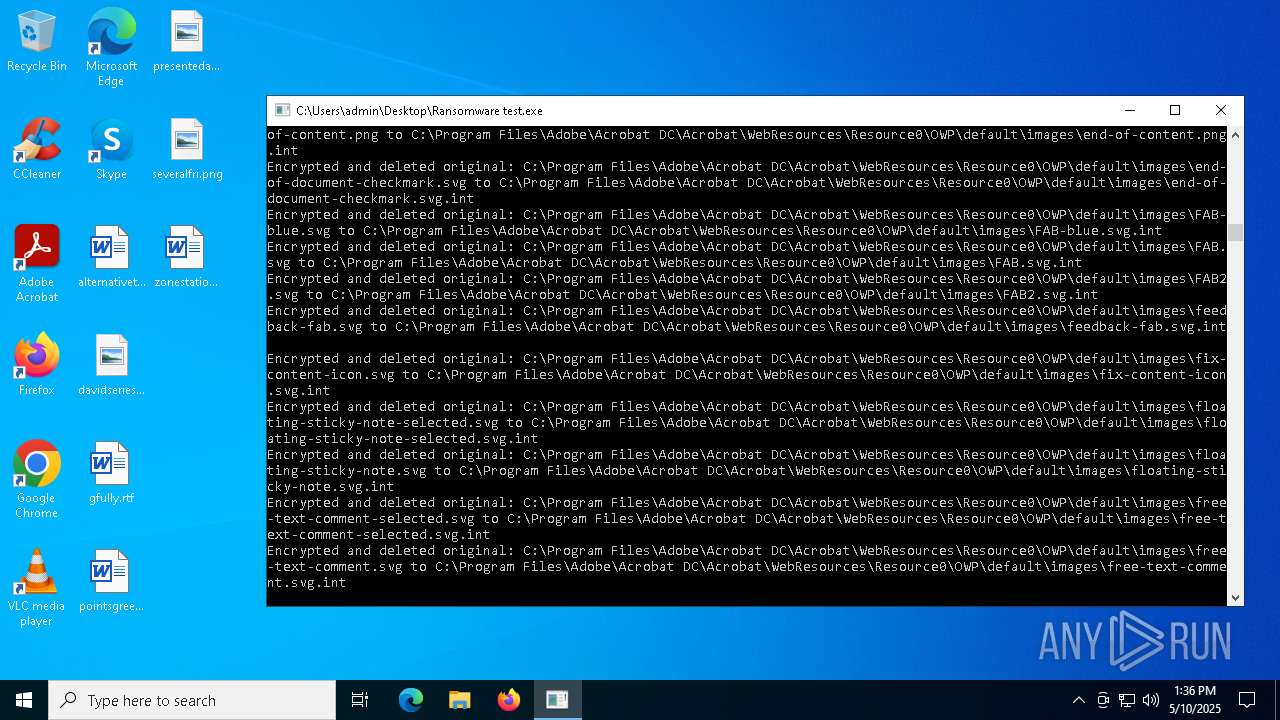
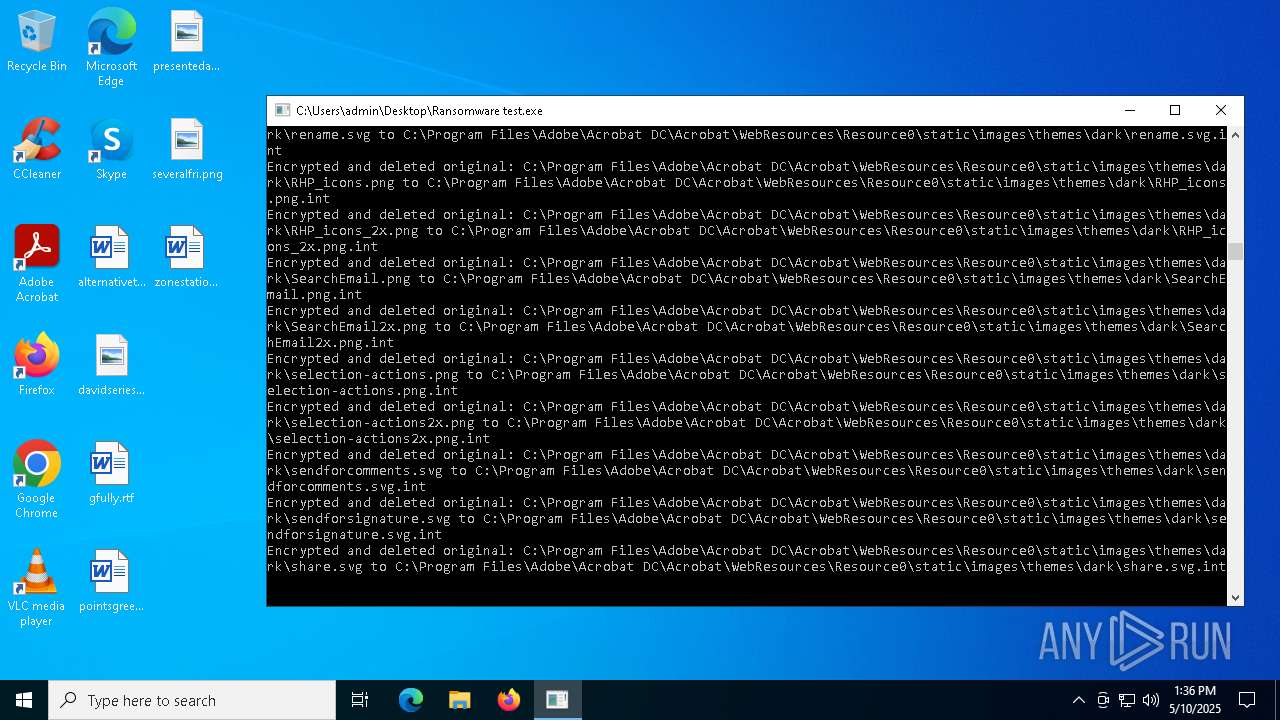
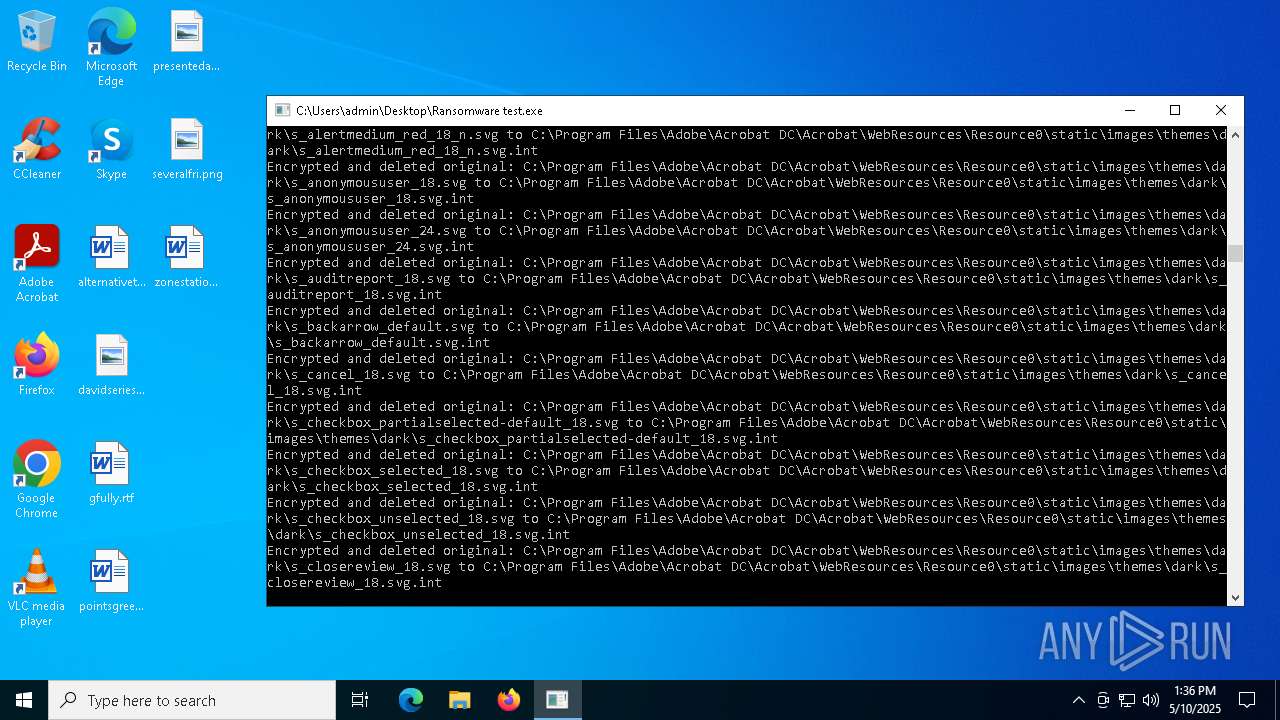
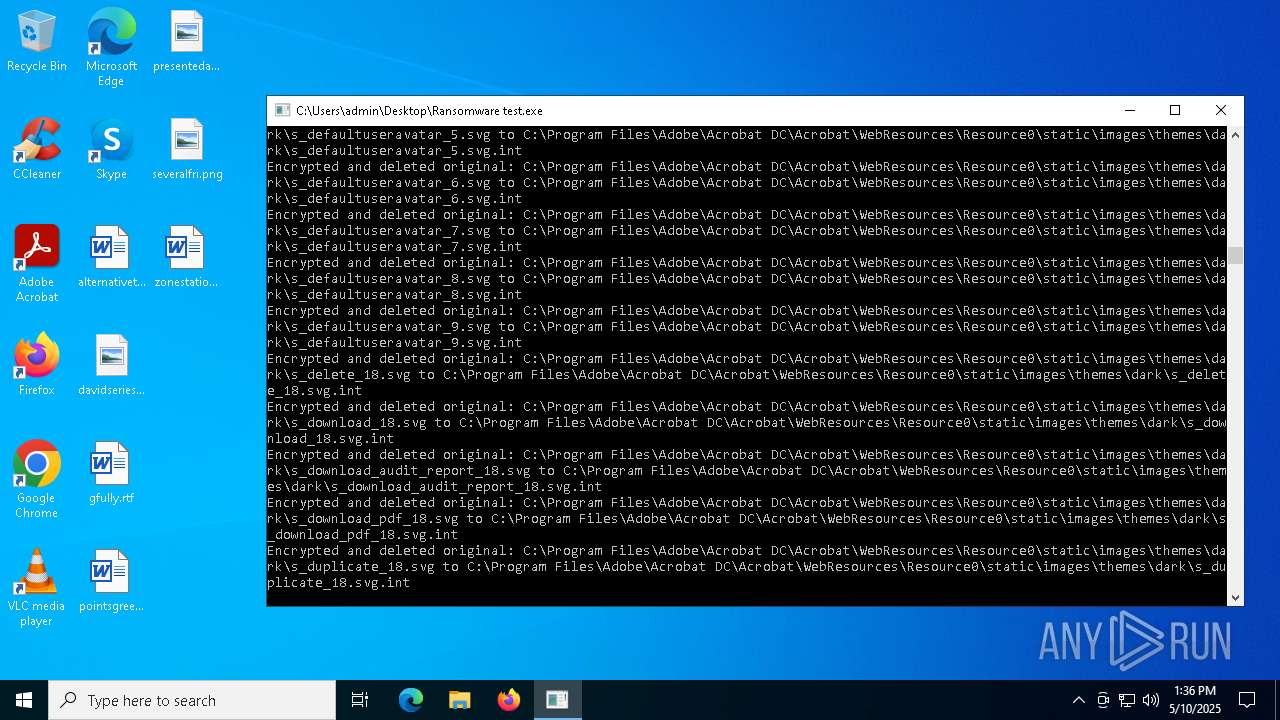
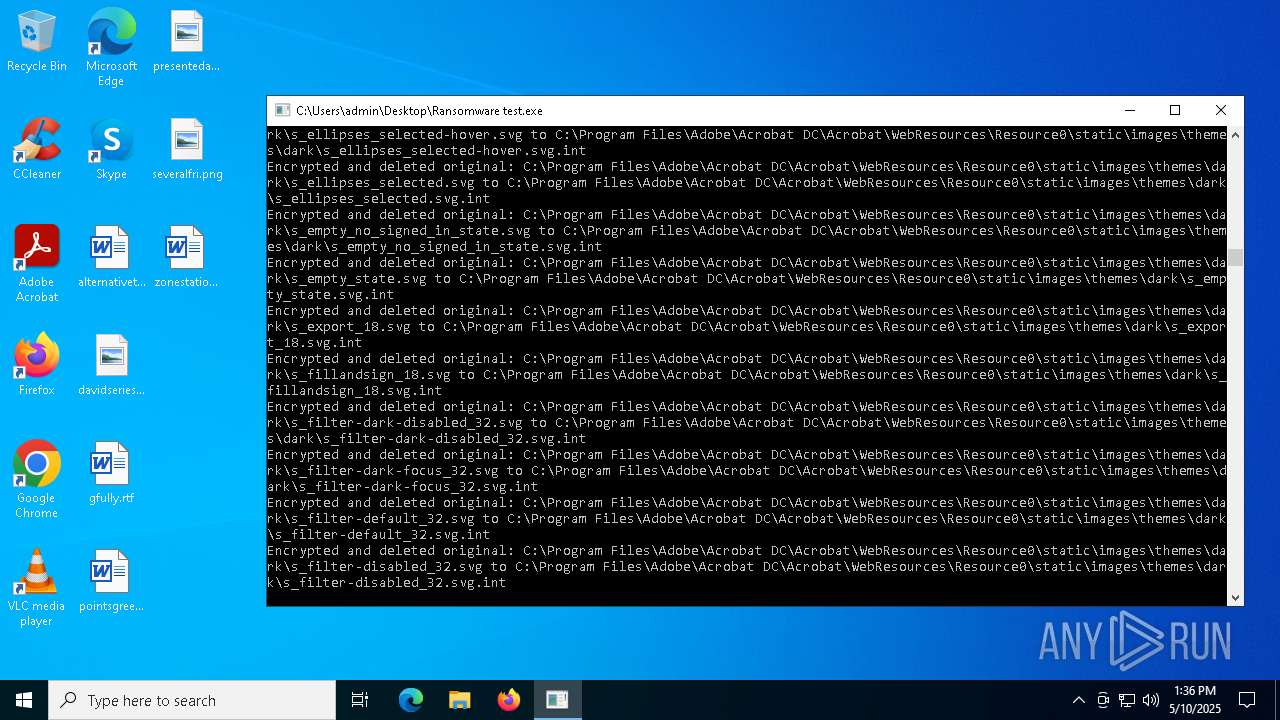
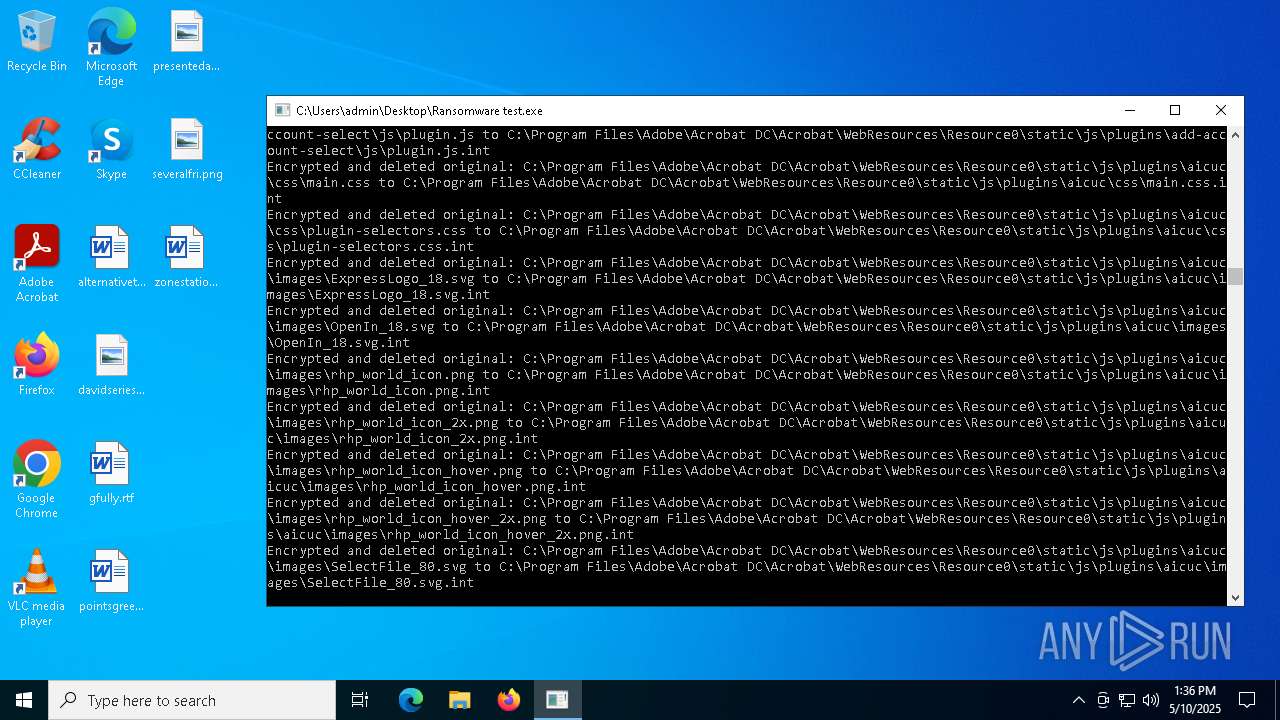
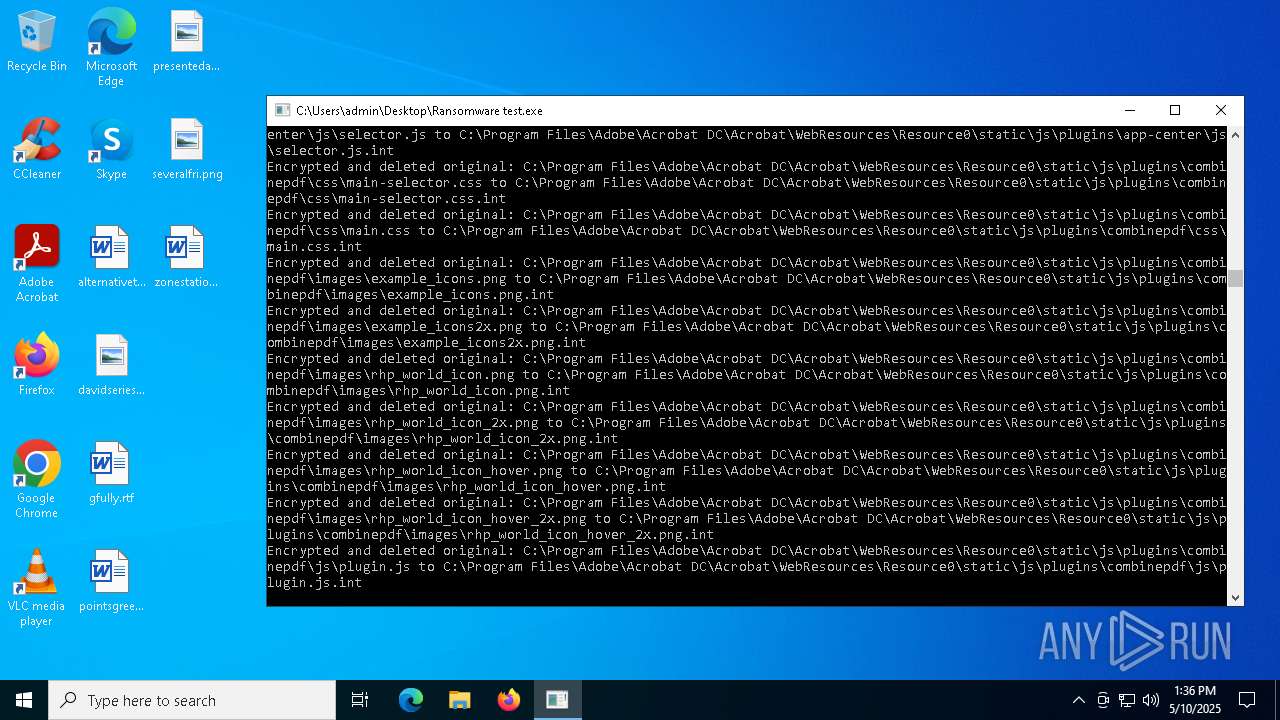
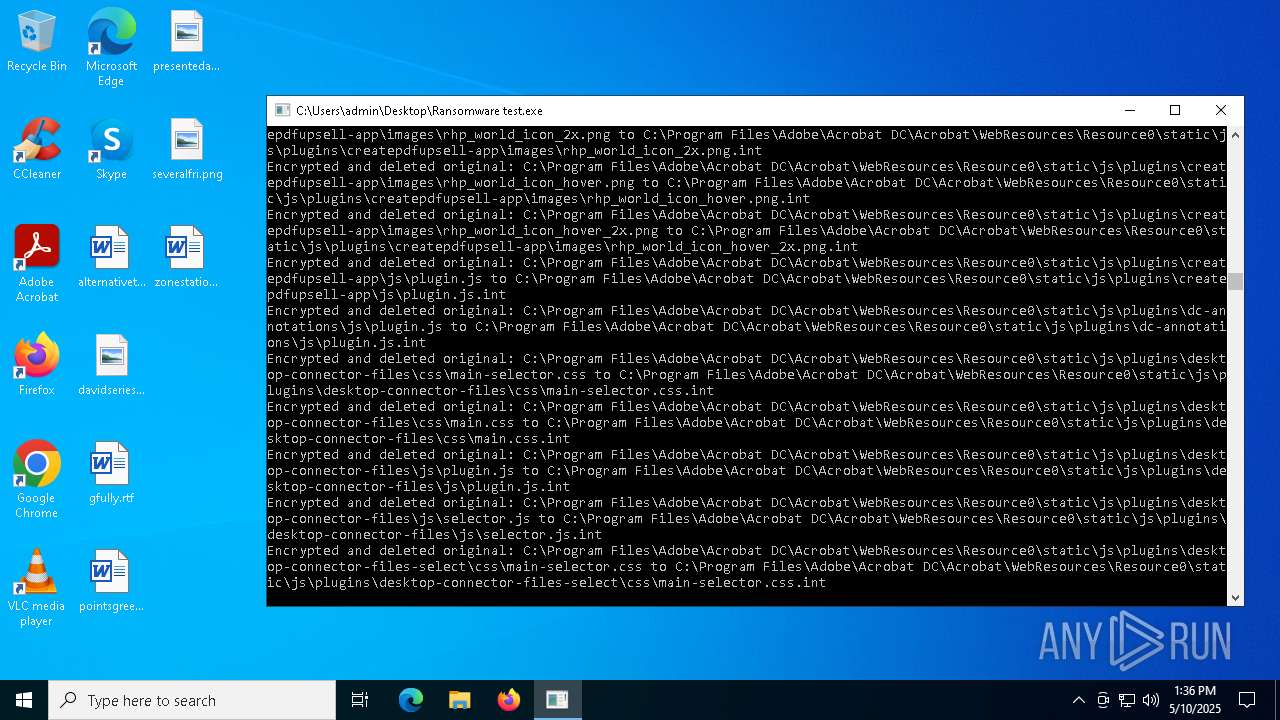
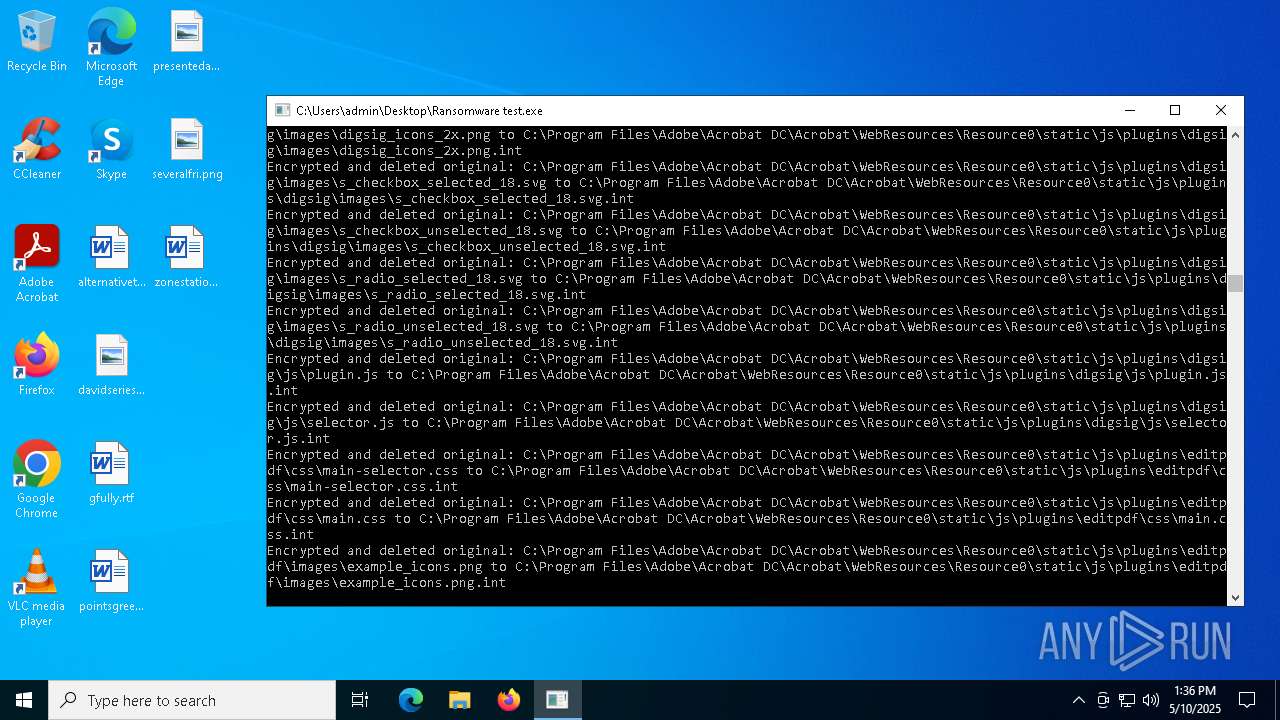
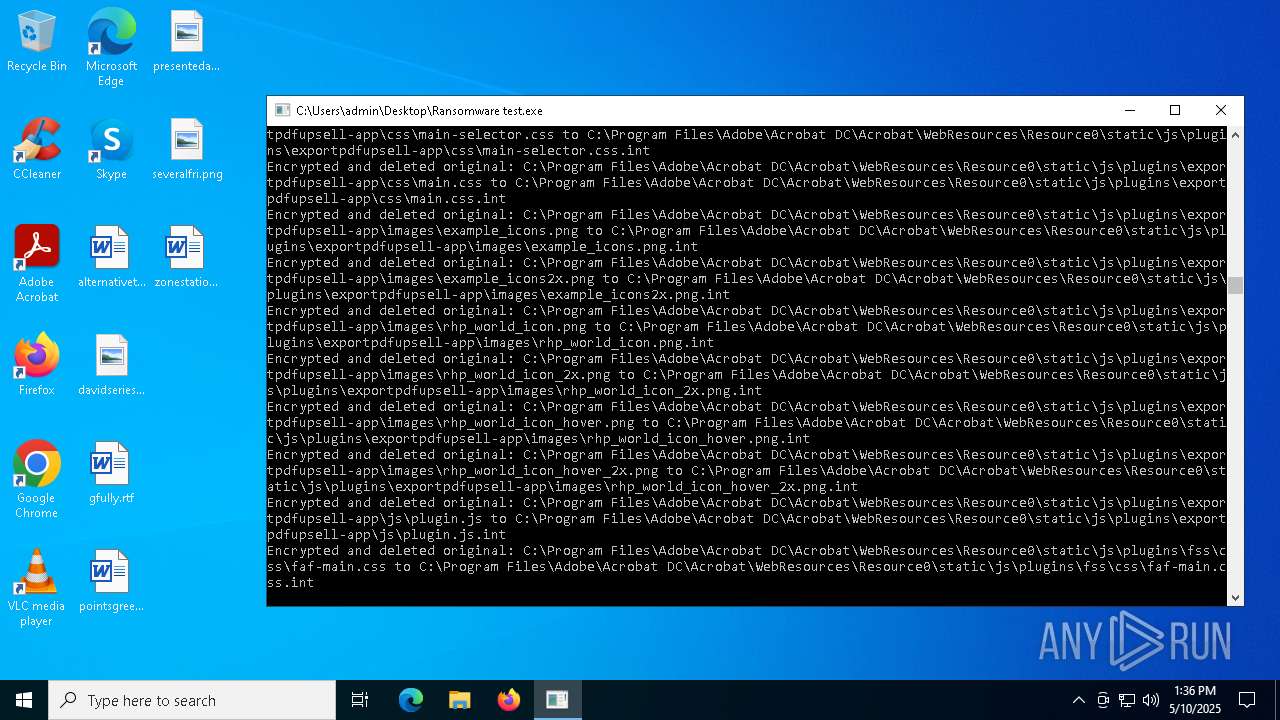
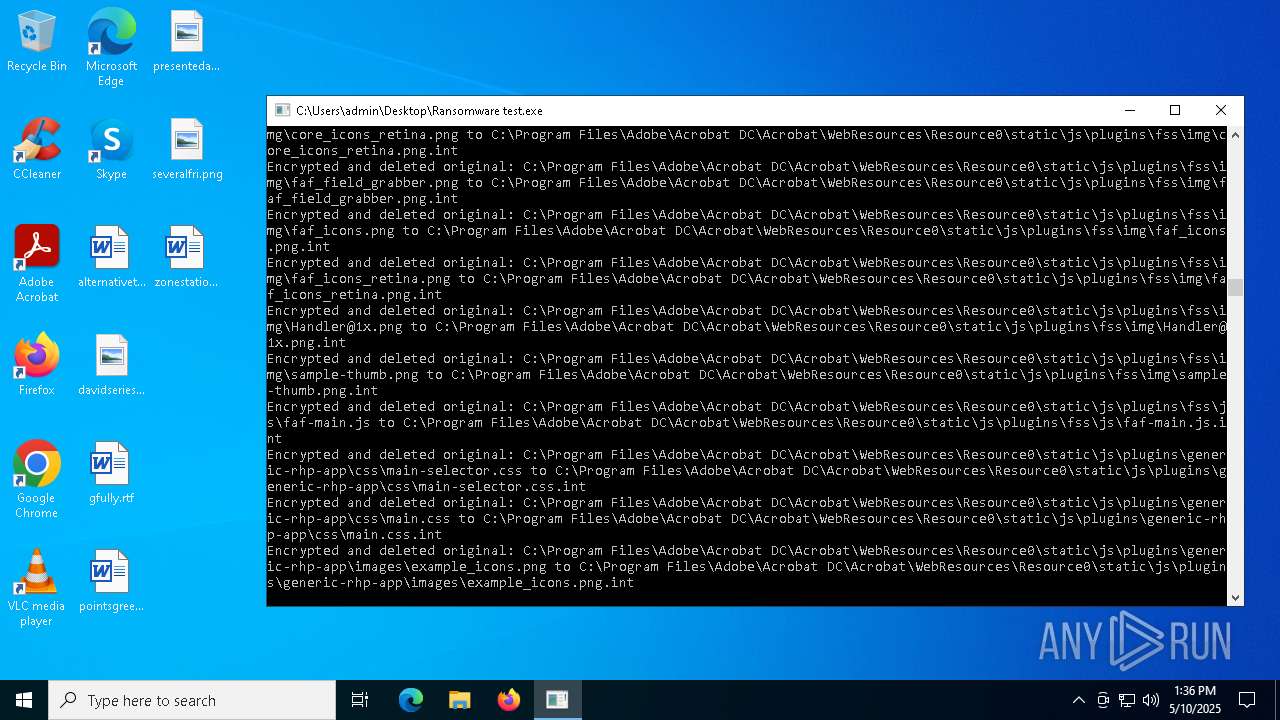
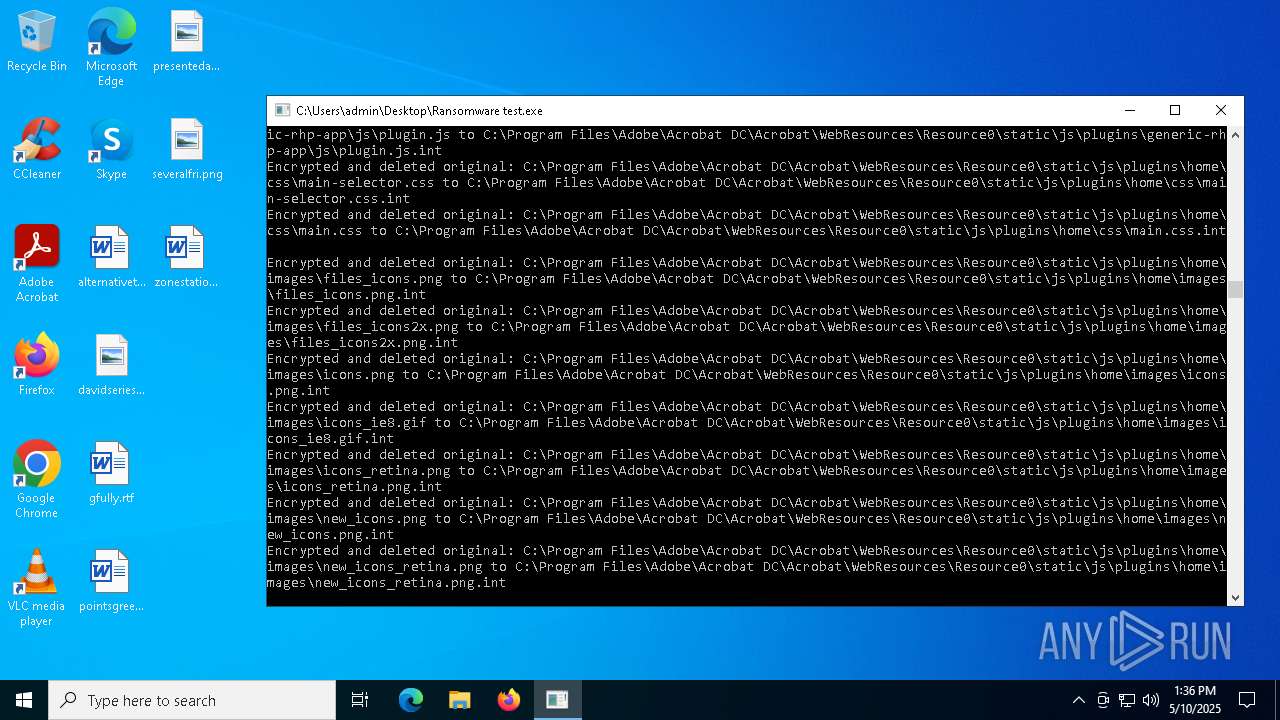
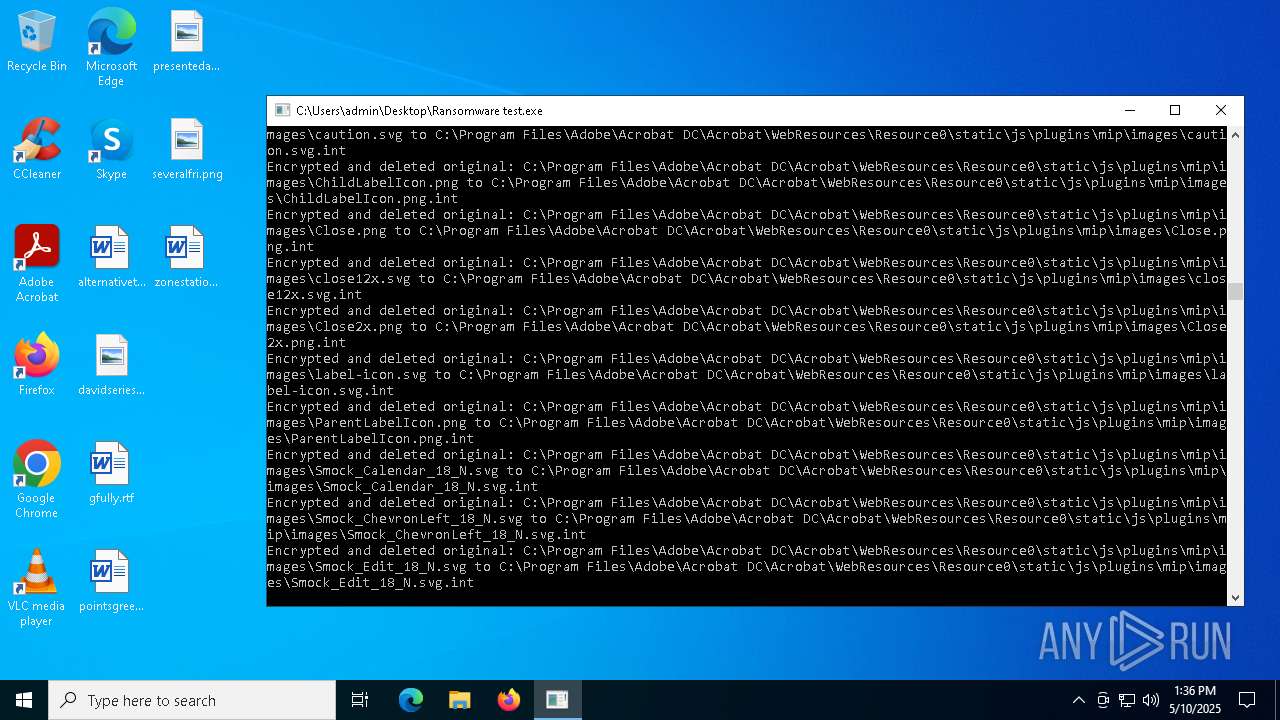
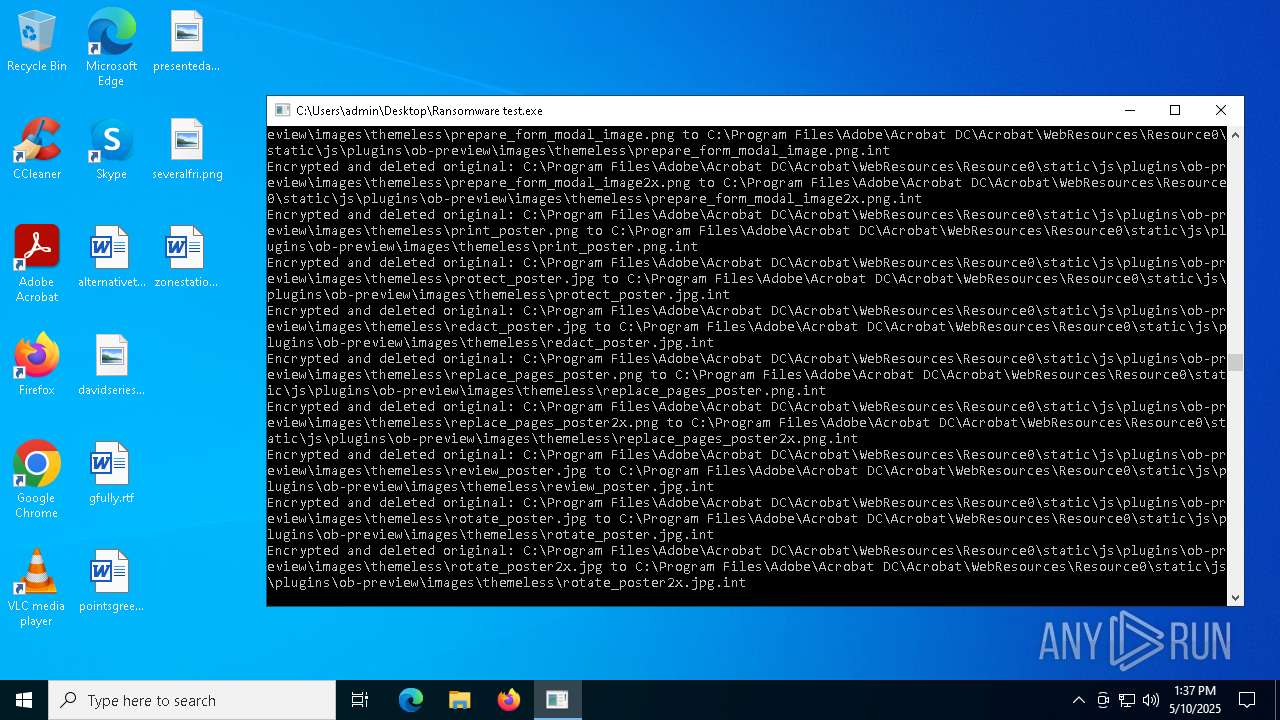
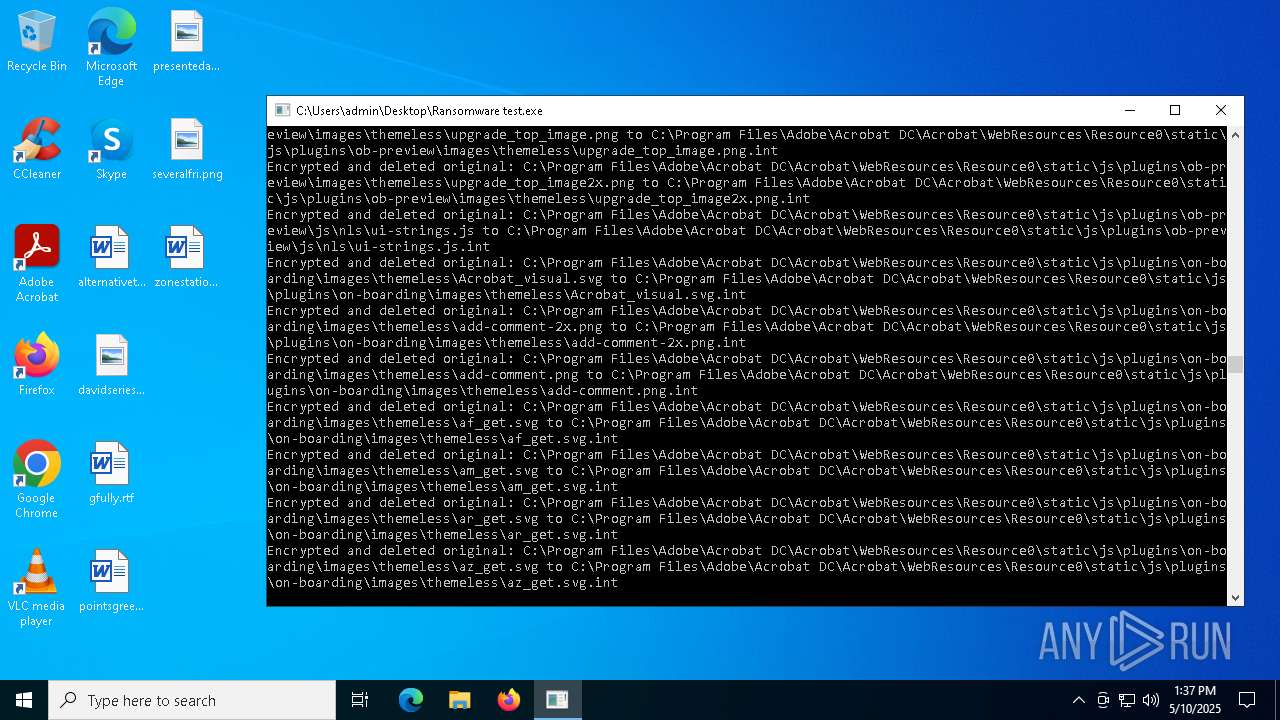
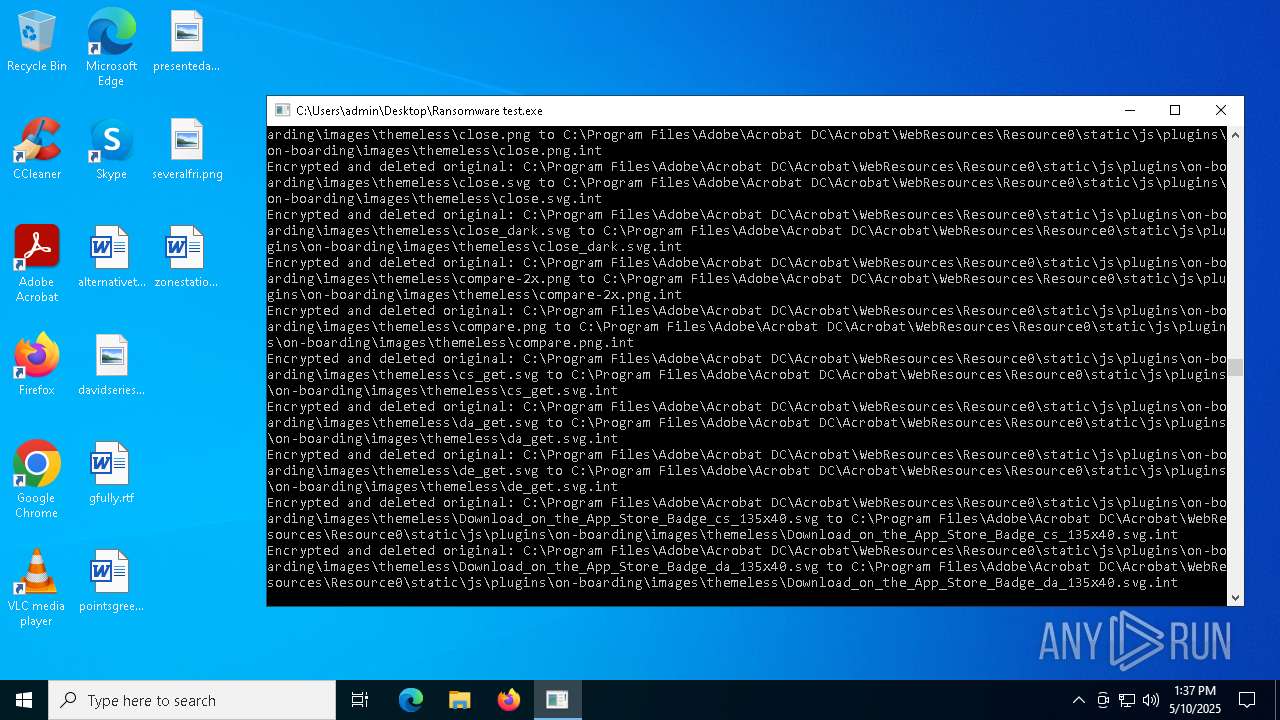
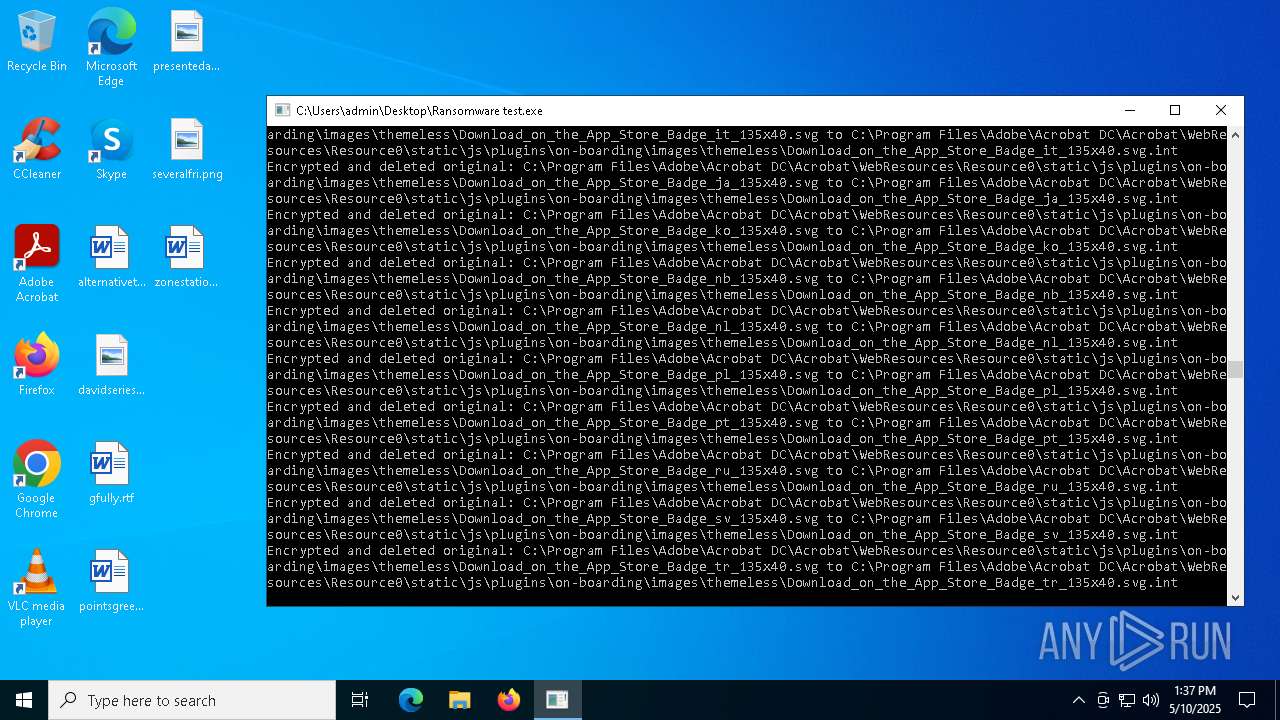
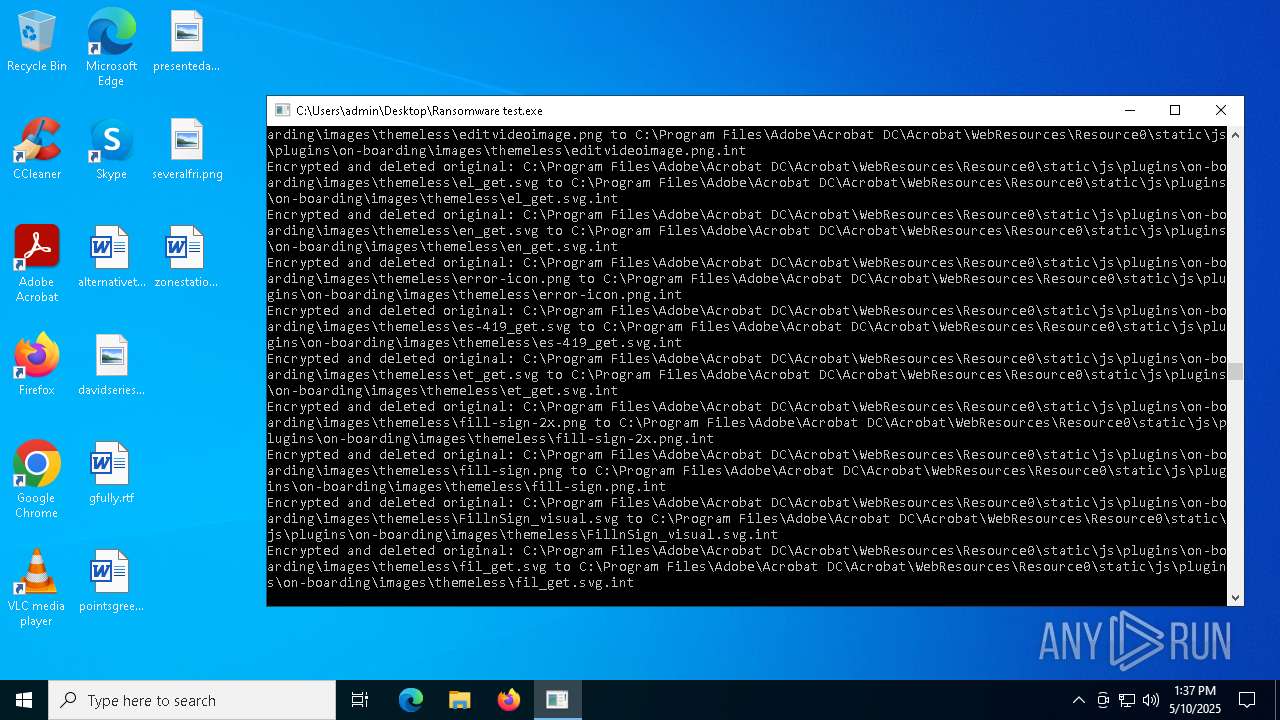
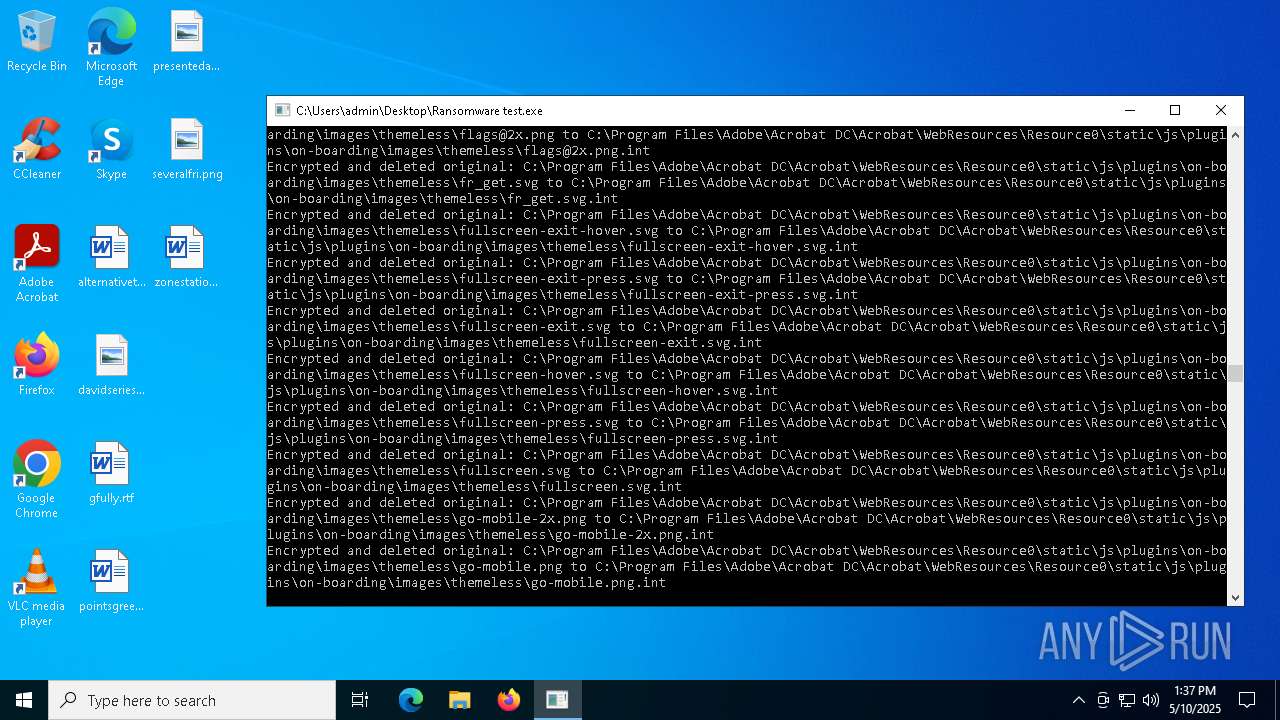
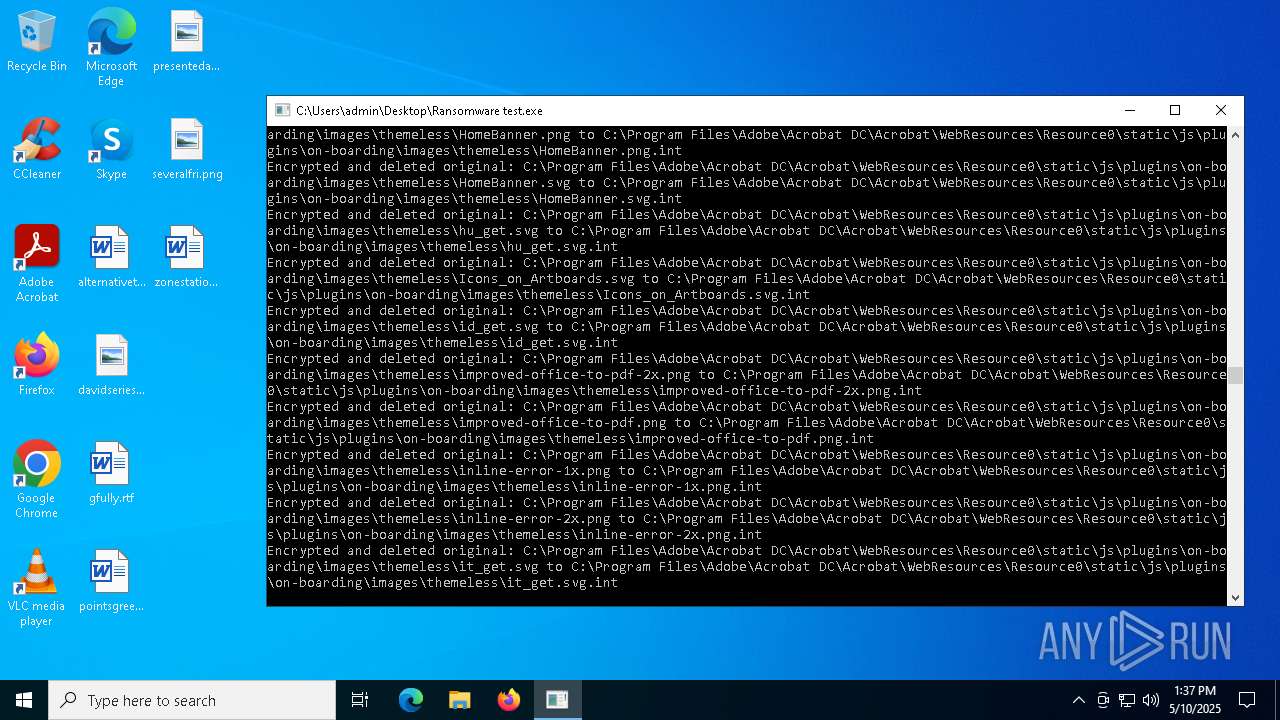
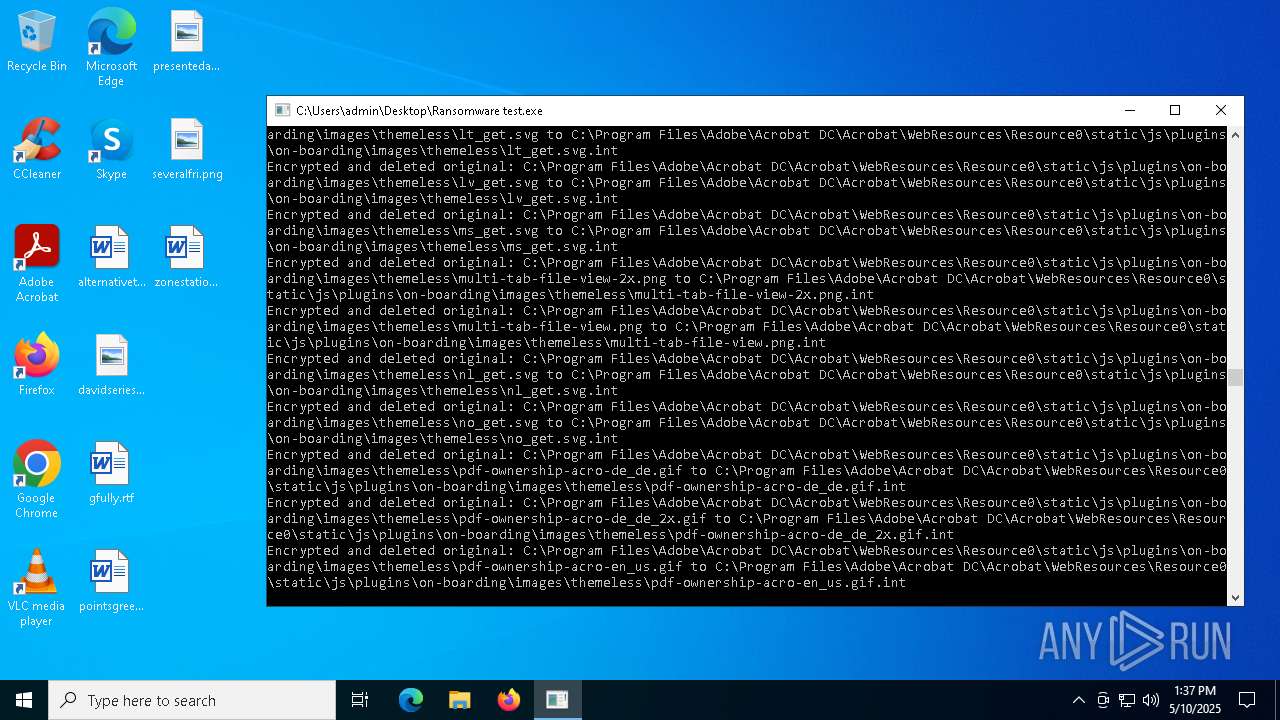
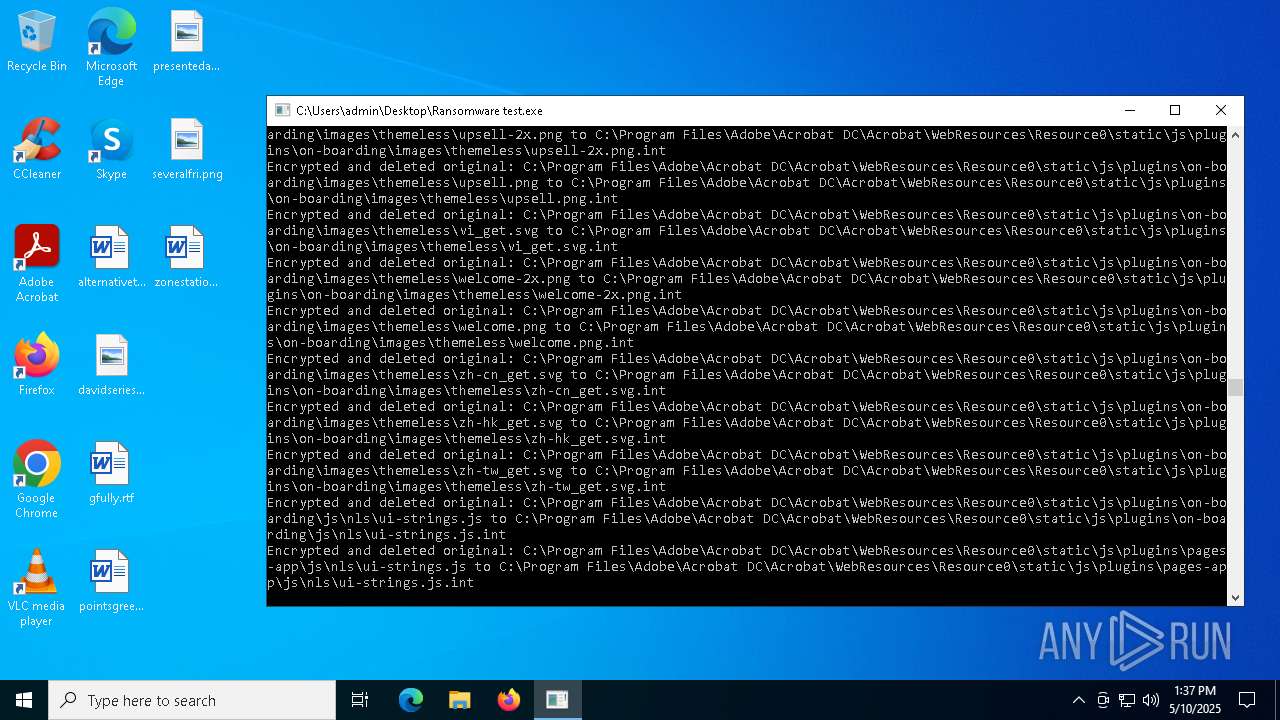
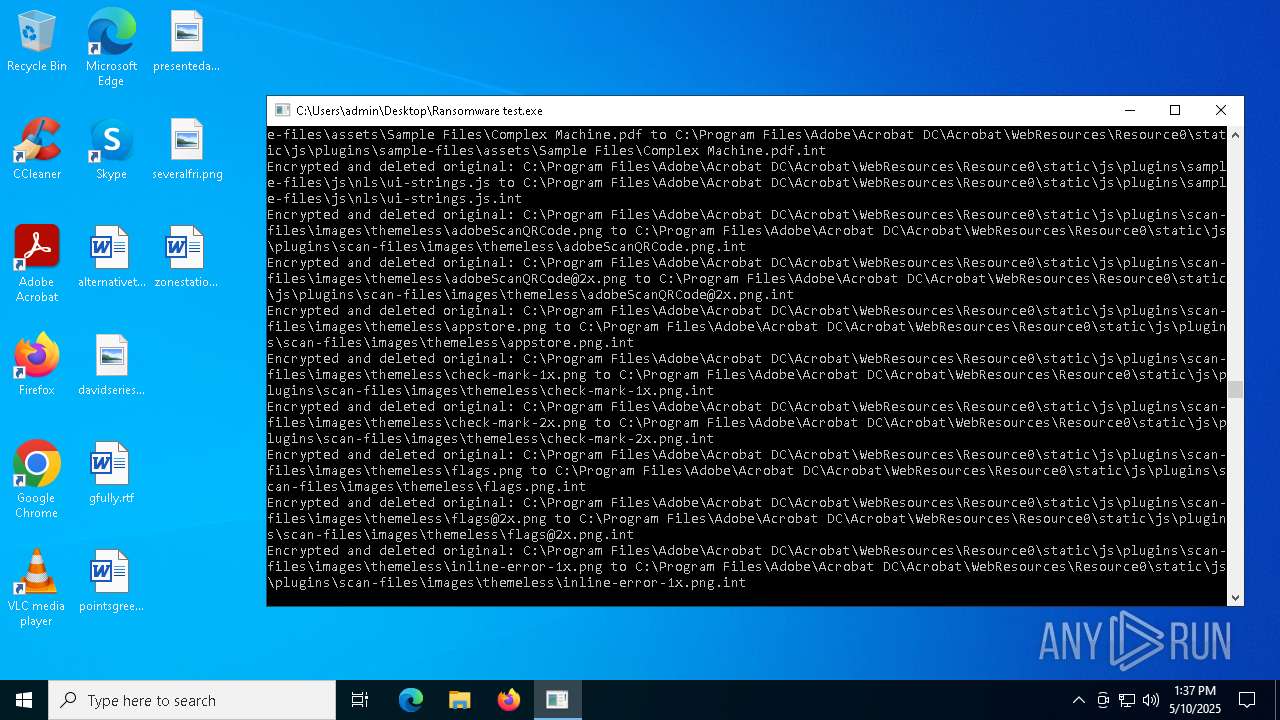
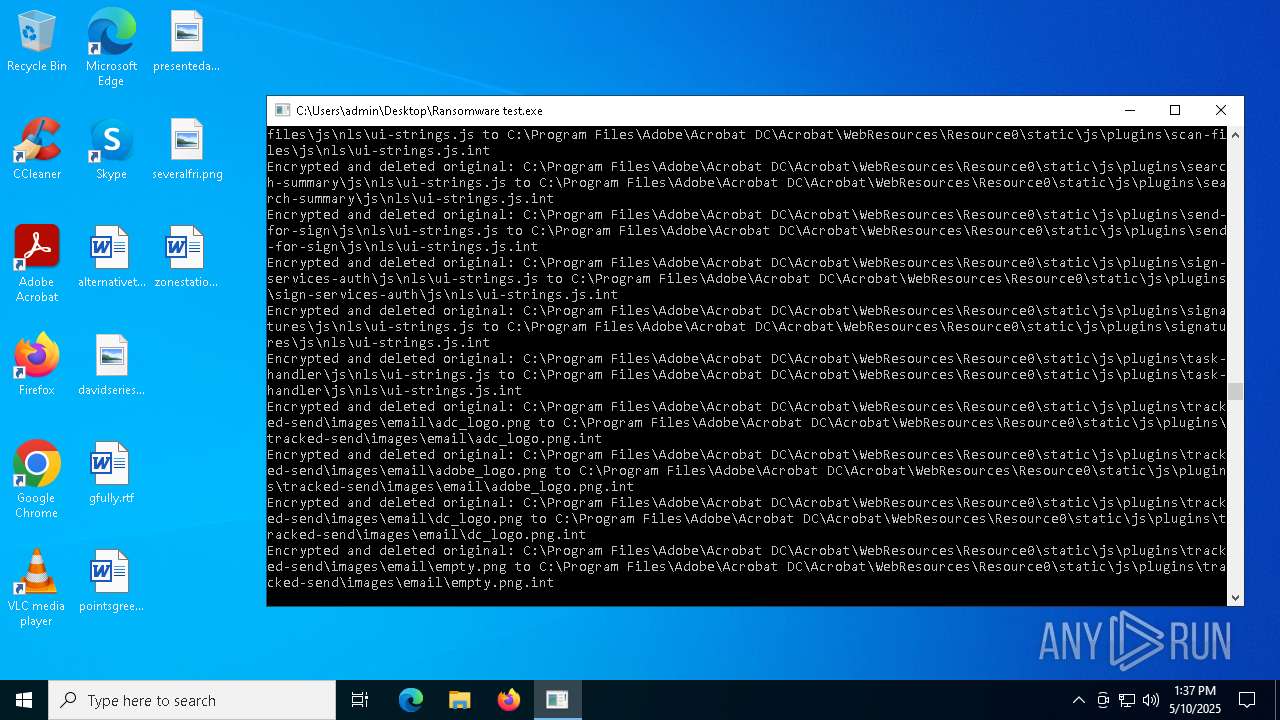
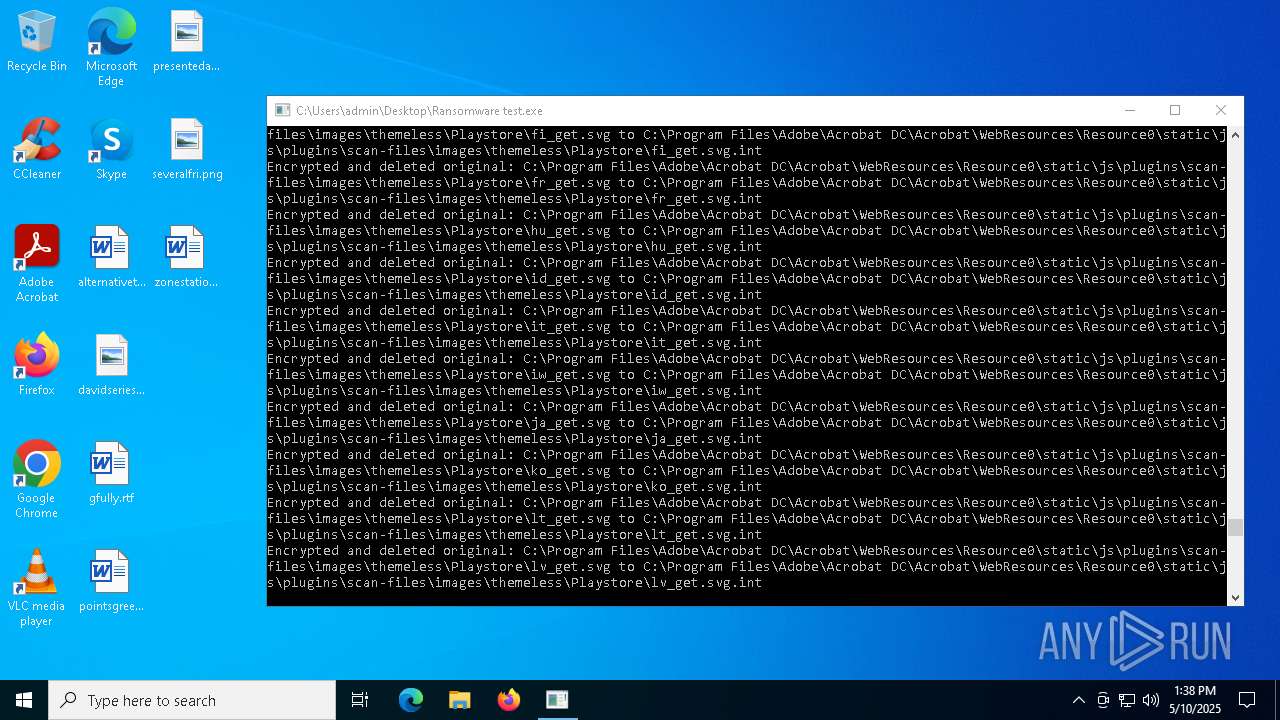
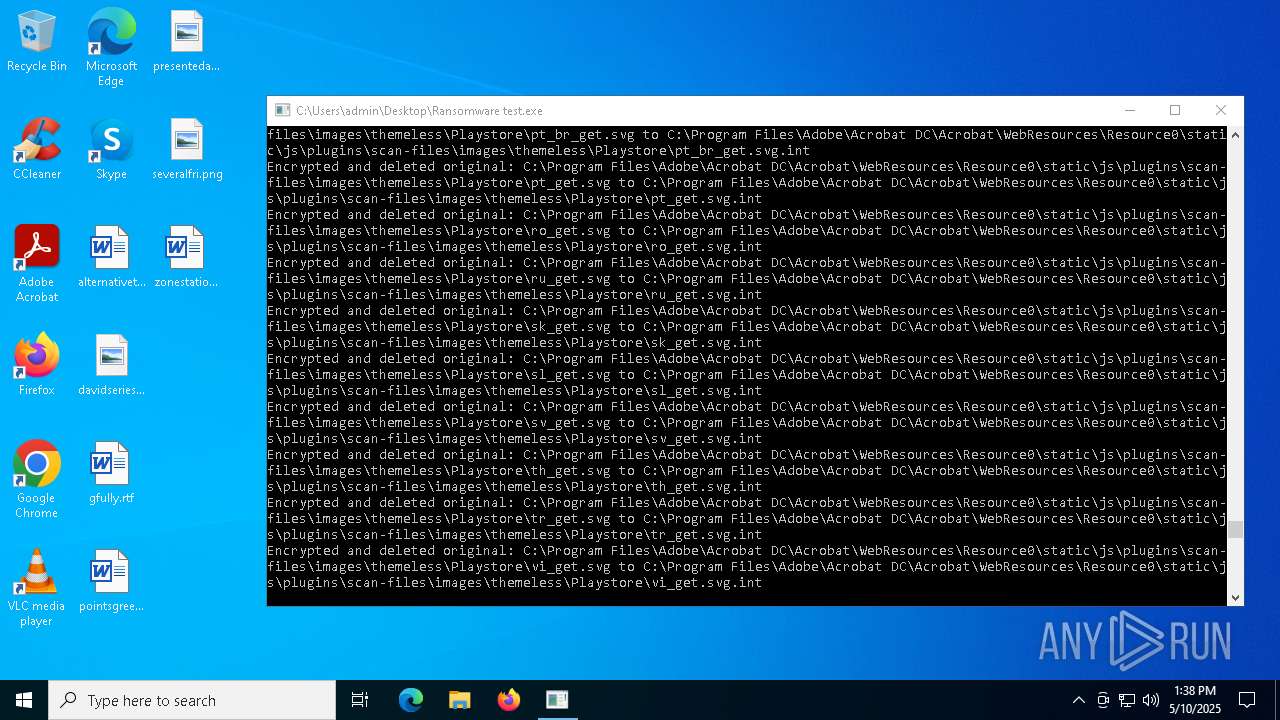
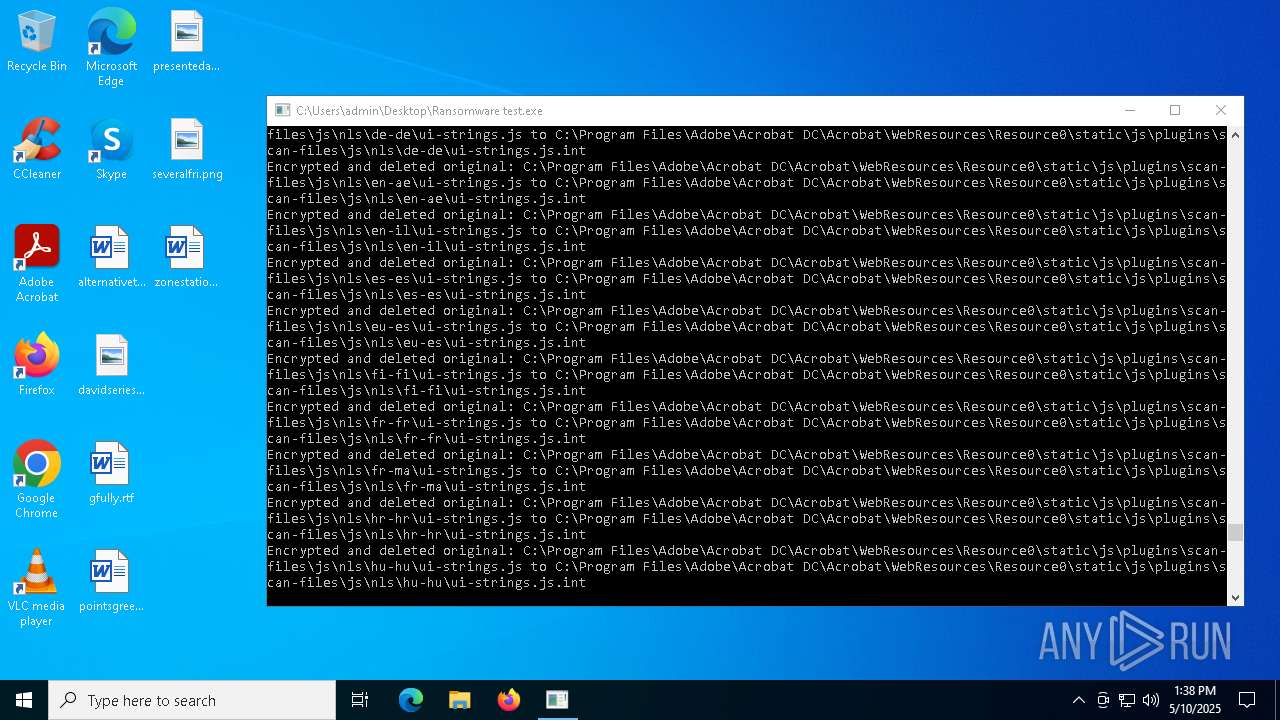
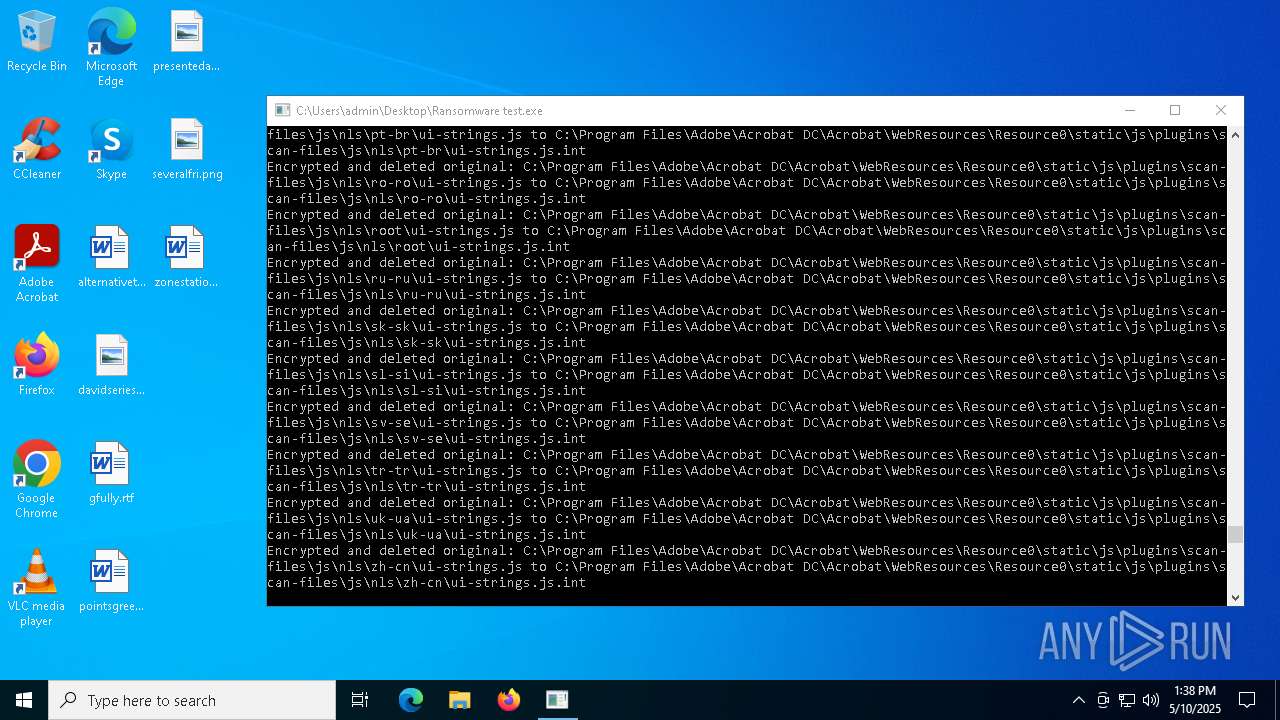
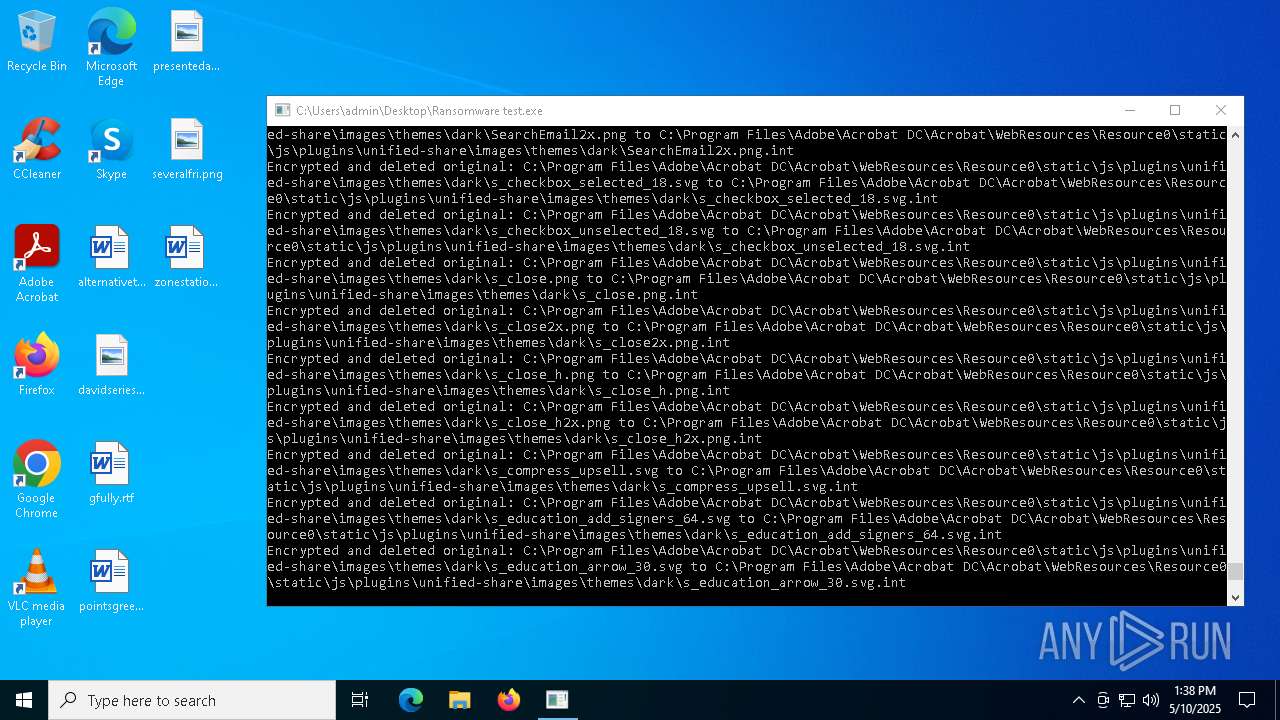
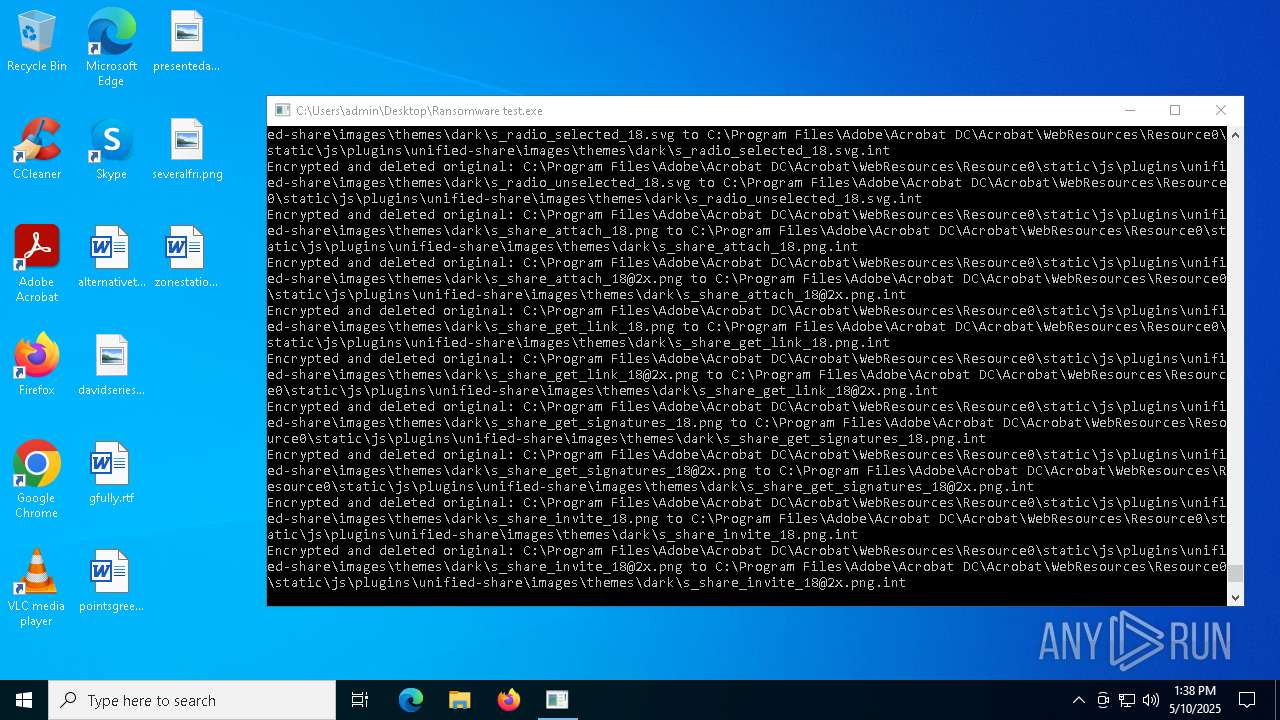
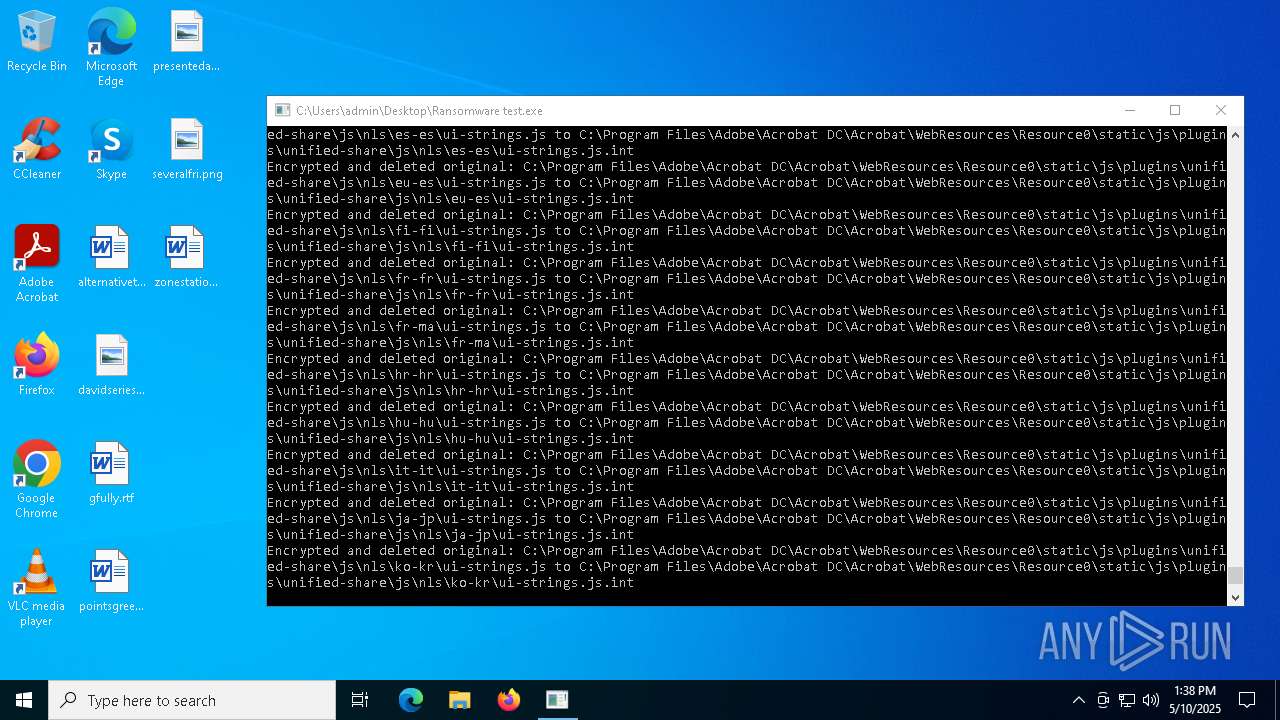
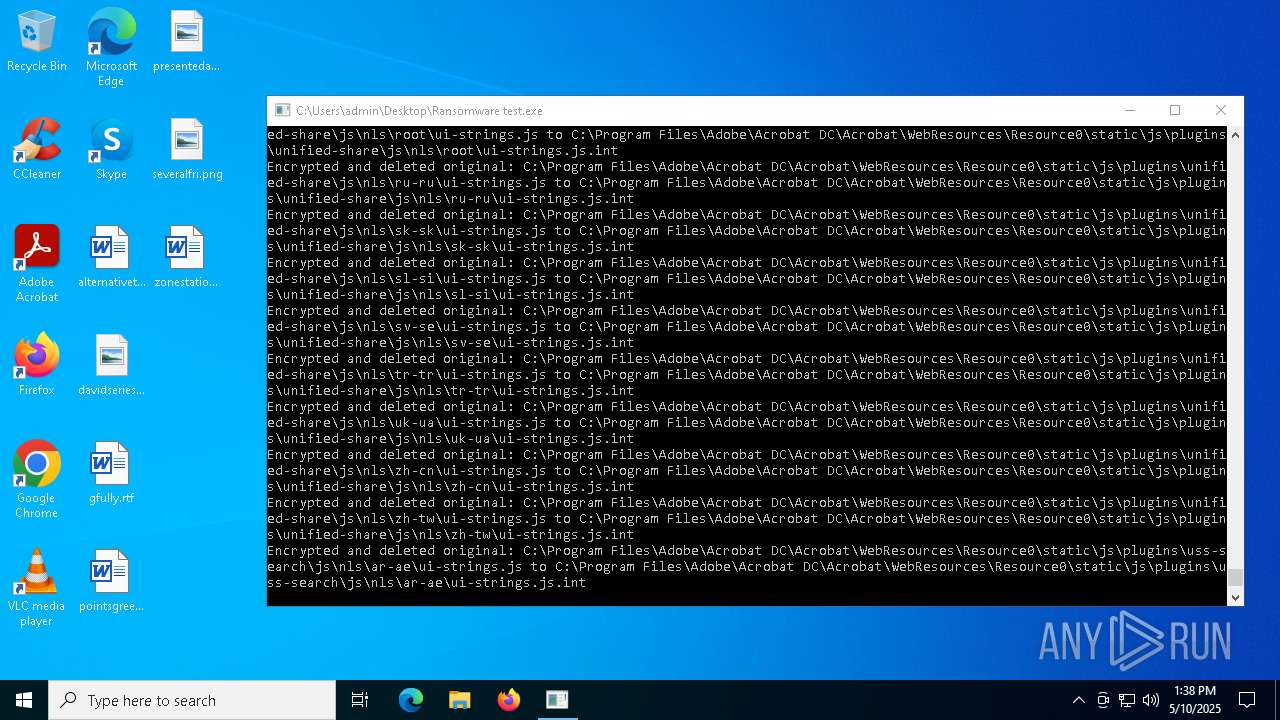
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8172 | Ransomware test.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll.int | — | |
MD5:— | SHA256:— | |||
| 8172 | Ransomware test.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe.int | — | |
MD5:— | SHA256:— | |||
| 8172 | Ransomware test.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\AcrobatRes.dll.int | — | |
MD5:— | SHA256:— | |||
| 8172 | Ransomware test.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\AdobeCollabSync.exe.int | — | |
MD5:— | SHA256:— | |||
| 8172 | Ransomware test.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\AGM.dll.int | — | |
MD5:— | SHA256:— | |||
| 8172 | Ransomware test.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrobat_reader_appicon_16.png.int | text | |
MD5:2DFAC6274A092FDBC4F0FFFF3F0266F0 | SHA256:D5C97C1A66F0094A0A9B3524F067FA0AB9B25A1881AAC4D05A7F62890BE6F91B | |||
| 8172 | Ransomware test.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\AIDE.dll.int | — | |
MD5:— | SHA256:— | |||
| 8172 | Ransomware test.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\AcroDunamis.dll.int | text | |
MD5:64BFA4AF636E4C476B9D20702C26CB24 | SHA256:959B884430F38FD0A3D26B9739D8EACCB4E251A1B6EB6318CD3B6043C56745F4 | |||
| 8172 | Ransomware test.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrobat.tlb.int | text | |
MD5:0B2B0D09DAADE2524DE06F54F42B4636 | SHA256:99DF0343C764A7A4CBC139FBF8AFB19A26E64CF23E2EAD5F067F0363FEA1C470 | |||
| 8172 | Ransomware test.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\AcrobatInfo.exe.int | text | |
MD5:AC3BFB4BAF71125B24AC63C76B29D677 | SHA256:93599513F74B812A118F5767CC6FB98935488DF8A23C8581E9FE5FC102FBAA2D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
25
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7476 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7476 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |