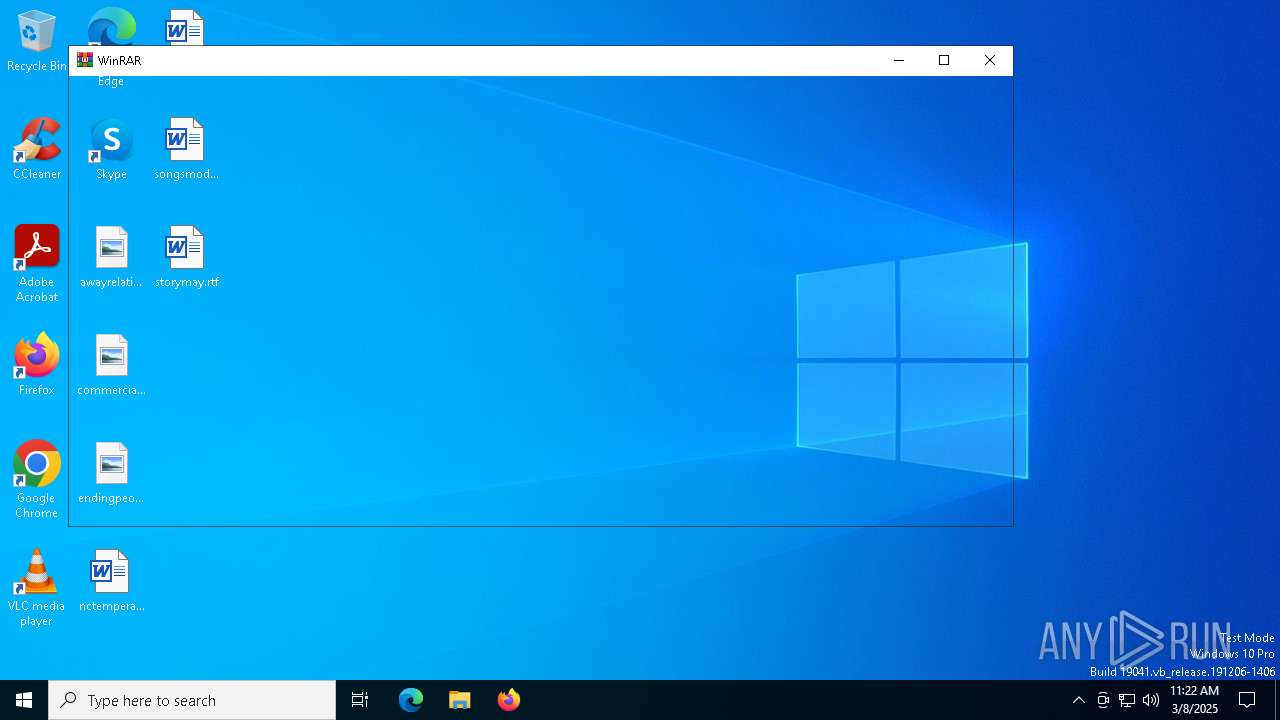
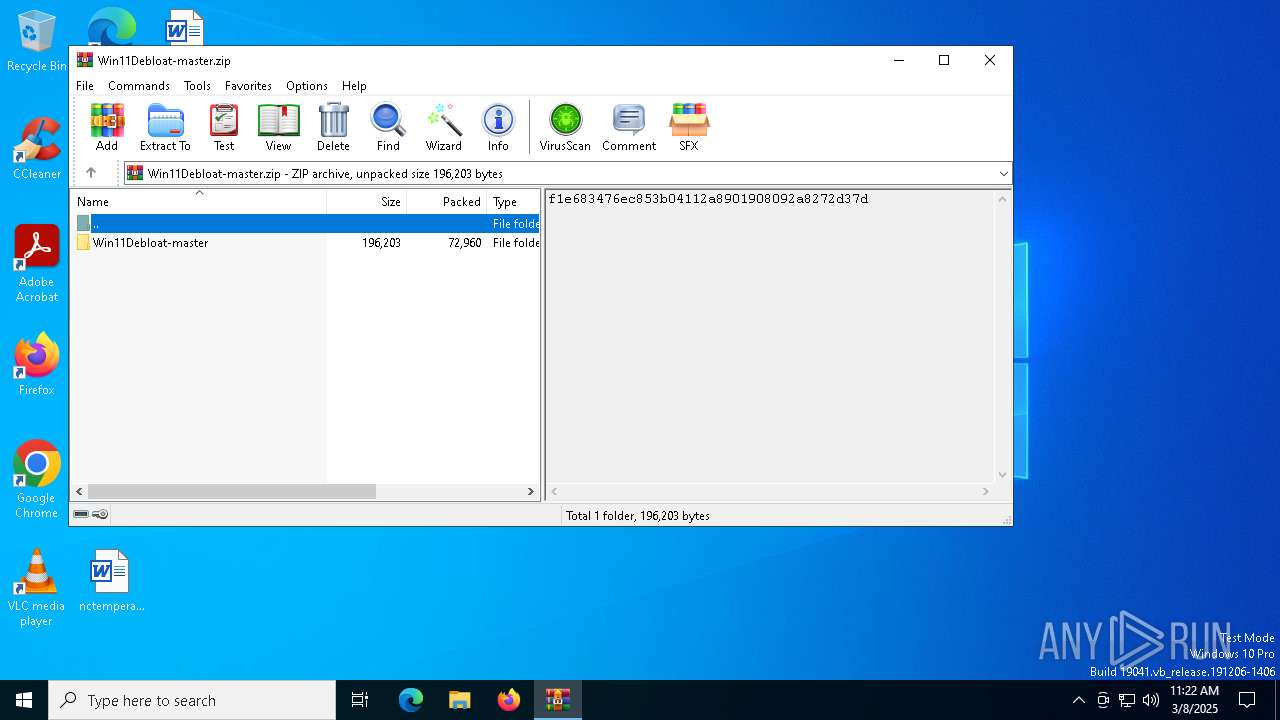
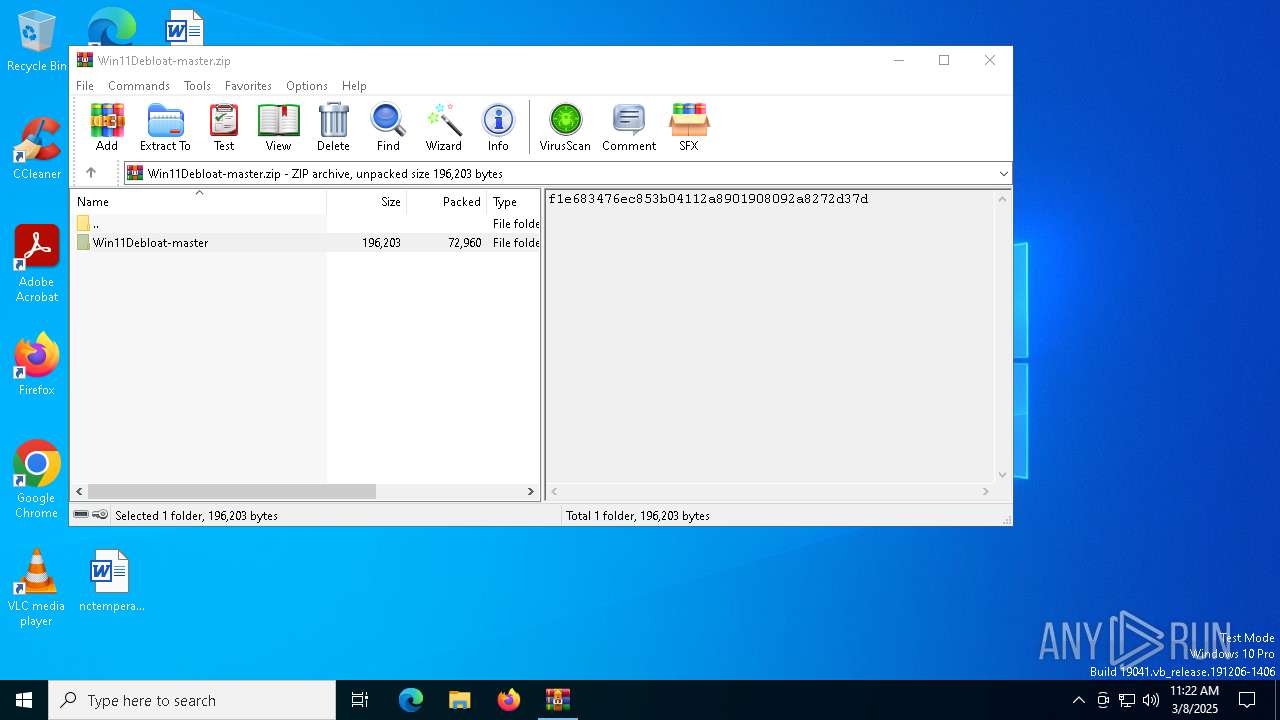
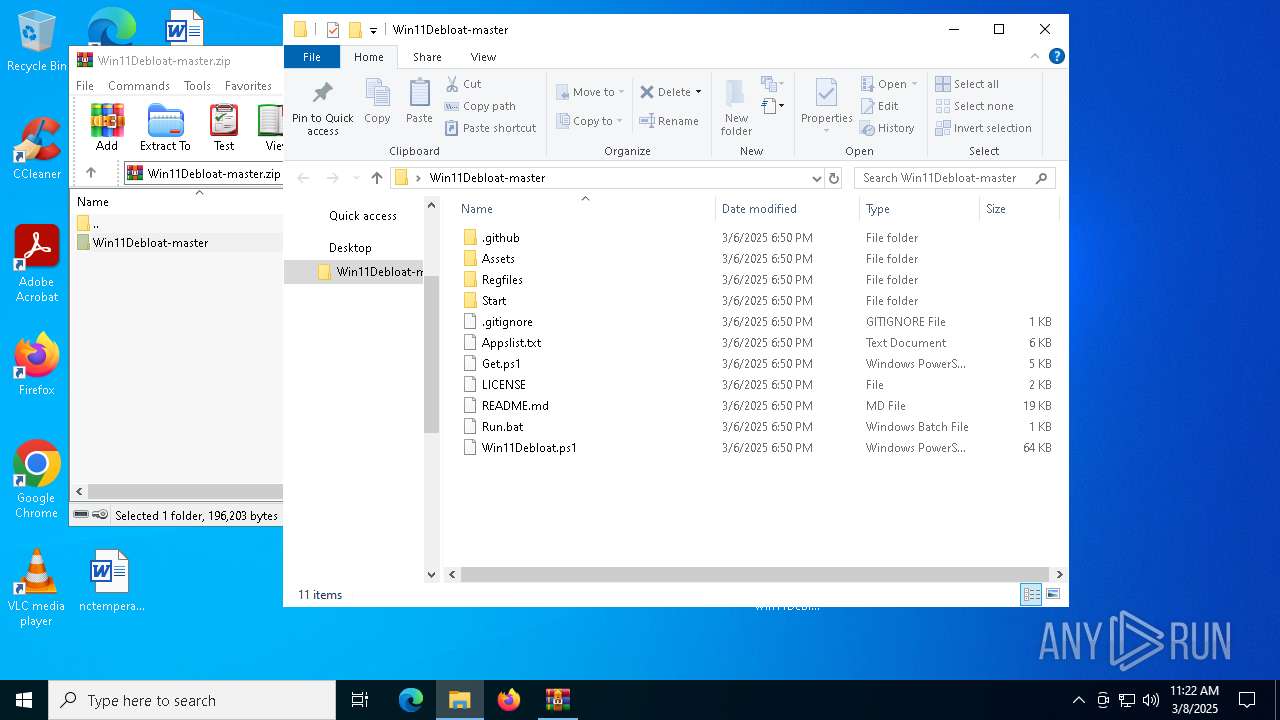
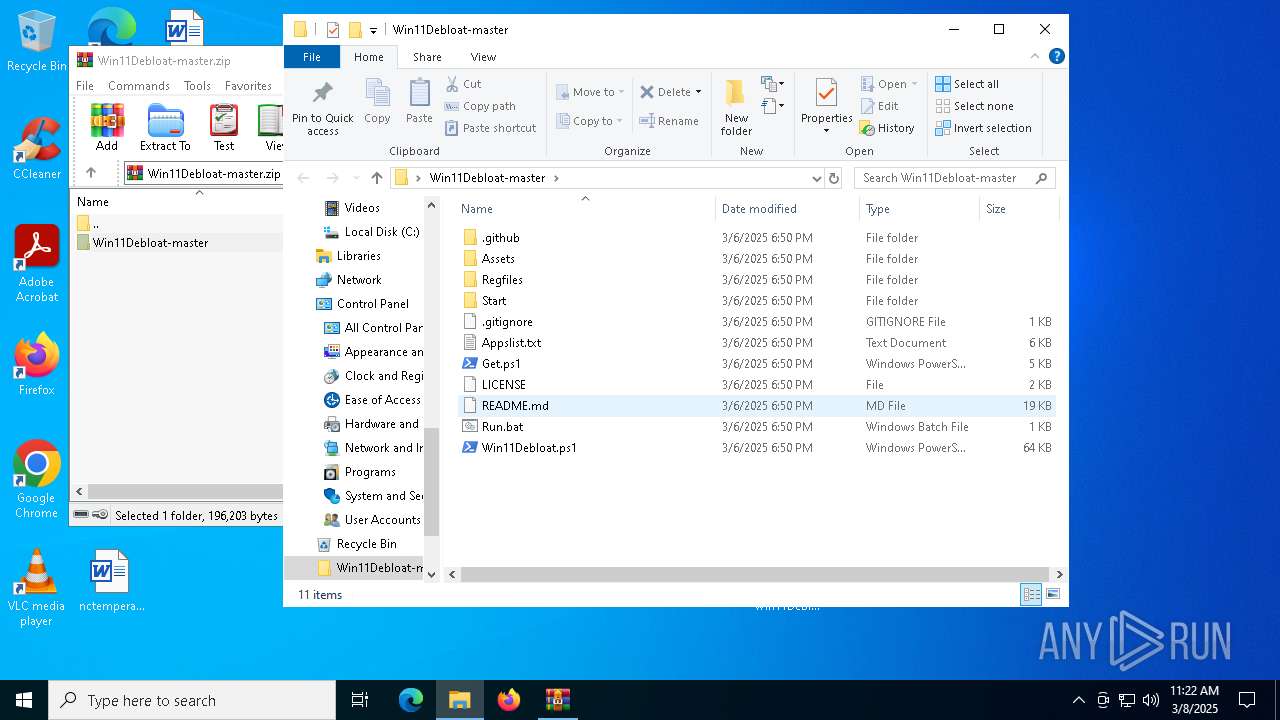
| File name: | Win11Debloat-master.zip |
| Full analysis: | https://app.any.run/tasks/12eea164-a661-40b9-87d5-37b0530b49d7 |
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2025, 11:22:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 0F2F9E549BF7807D59E899869F1A403A |
| SHA1: | BAB9DDA0E71F3BA308B433240D694660DB579BA1 |
| SHA256: | 7A0CAADDCE526FC6DADA3C0A577B7C3DBB72A7F4B2E979D74D0571628FD89824 |
| SSDEEP: | 1536:H9zqyFp7lW6Y4FvD9Wq9D7QH8mNFJu08c2ZO8qgdoA04Vg4+ibWCkNx:dzPvWq9D7QH8tDc2ZOfugTBCkNx |
MALICIOUS
Generic archive extractor
- svchost.exe (PID: 6456)
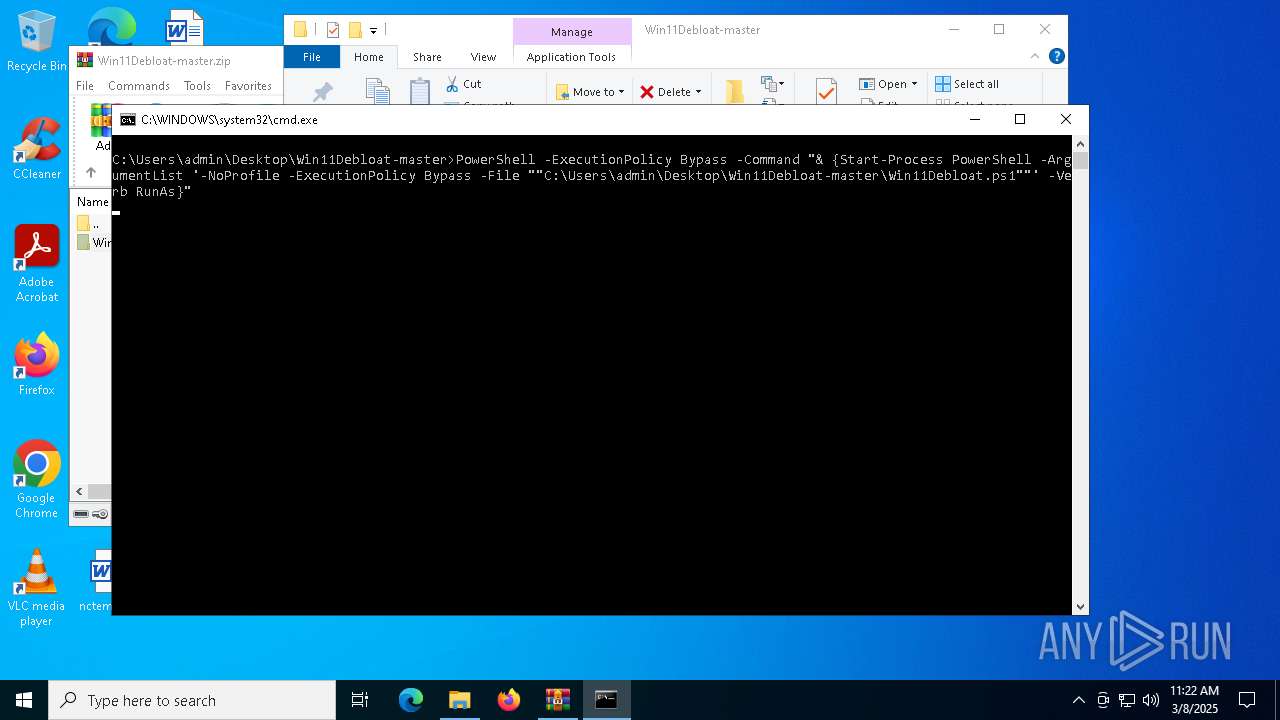
Bypass execution policy to execute commands
- powershell.exe (PID: 7928)
- powershell.exe (PID: 5376)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7696)
- powershell.exe (PID: 7928)
SUSPICIOUS
The process executes Powershell scripts
- cmd.exe (PID: 7696)
- powershell.exe (PID: 7928)
Starts process via Powershell
- powershell.exe (PID: 7928)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7696)
- powershell.exe (PID: 7928)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 6476)
- DismHost.exe (PID: 1660)
- DismHost.exe (PID: 7948)
- DismHost.exe (PID: 8012)
- DismHost.exe (PID: 2284)
- DismHost.exe (PID: 1324)
- DismHost.exe (PID: 7296)
- DismHost.exe (PID: 8000)
- DismHost.exe (PID: 7608)
- DismHost.exe (PID: 5936)
- DismHost.exe (PID: 5552)
- DismHost.exe (PID: 7592)
- DismHost.exe (PID: 6736)
- DismHost.exe (PID: 5968)
- DismHost.exe (PID: 7716)
- DismHost.exe (PID: 5116)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 7928)
Process drops legitimate windows executable
- powershell.exe (PID: 5376)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 5376)
The process creates files with name similar to system file names
- powershell.exe (PID: 5376)
Executable content was dropped or overwritten
- powershell.exe (PID: 5376)
Application launched itself
- powershell.exe (PID: 7928)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 2892)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8072)
- BackgroundTransferHost.exe (PID: 5008)
- BackgroundTransferHost.exe (PID: 920)
- BackgroundTransferHost.exe (PID: 7432)
- BackgroundTransferHost.exe (PID: 7772)
- svchost.exe (PID: 2892)
- rundll32.exe (PID: 6640)
- rundll32.exe (PID: 7640)
- rundll32.exe (PID: 5216)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5008)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5008)
- WaaSMedicAgent.exe (PID: 7996)
- consent.exe (PID: 6816)
- SIHClient.exe (PID: 5640)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5008)
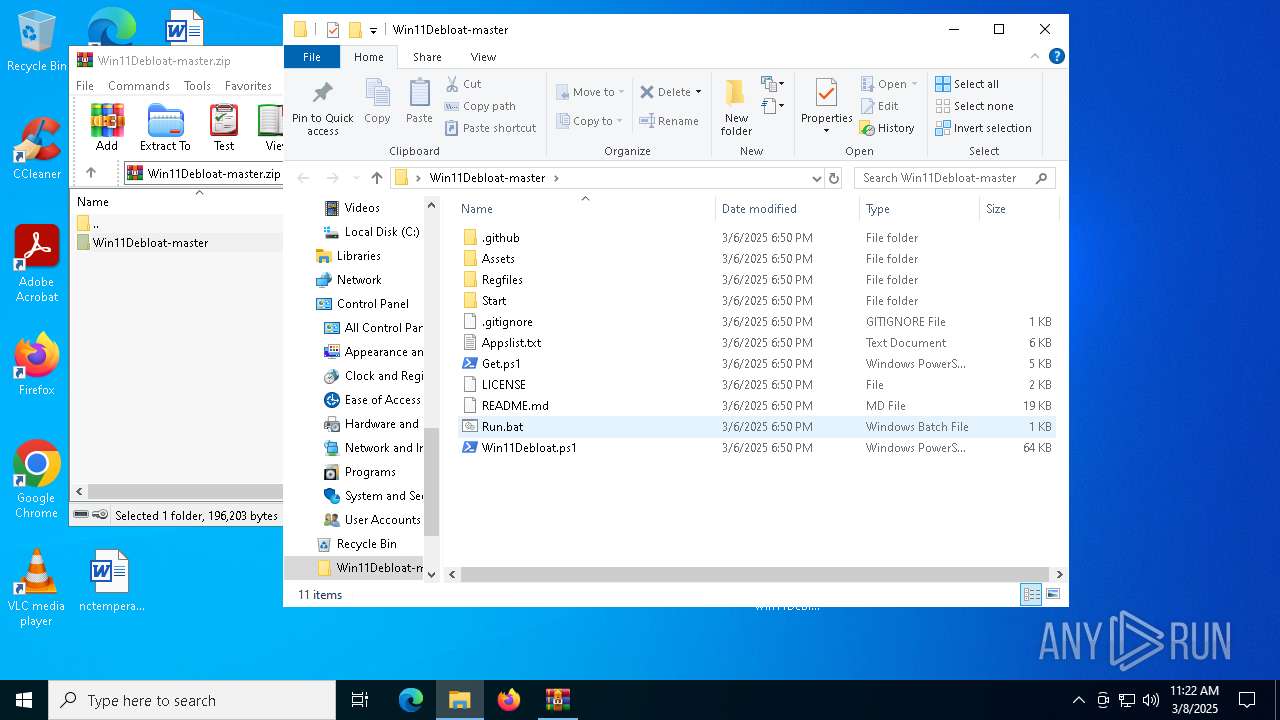
Manual execution by a user
- cmd.exe (PID: 7696)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5376)
The executable file from the user directory is run by the Powershell process
- DismHost.exe (PID: 1660)
- DismHost.exe (PID: 6476)
- DismHost.exe (PID: 7948)
- DismHost.exe (PID: 8012)
- DismHost.exe (PID: 2284)
- DismHost.exe (PID: 7608)
- DismHost.exe (PID: 1324)
- DismHost.exe (PID: 7296)
- DismHost.exe (PID: 8000)
- DismHost.exe (PID: 5936)
- DismHost.exe (PID: 5552)
- DismHost.exe (PID: 7592)
- DismHost.exe (PID: 6736)
- DismHost.exe (PID: 5968)
- DismHost.exe (PID: 7716)
- DismHost.exe (PID: 5116)
The sample compiled with english language support
- powershell.exe (PID: 5376)
Checks supported languages
- DismHost.exe (PID: 6476)
- DismHost.exe (PID: 1660)
- DismHost.exe (PID: 7948)
- DismHost.exe (PID: 8012)
- DismHost.exe (PID: 7608)
- DismHost.exe (PID: 1324)
- DismHost.exe (PID: 7296)
- DismHost.exe (PID: 2284)
- DismHost.exe (PID: 5936)
- DismHost.exe (PID: 5552)
- DismHost.exe (PID: 7592)
- DismHost.exe (PID: 8000)
- DismHost.exe (PID: 6736)
- DismHost.exe (PID: 5968)
- DismHost.exe (PID: 7716)
- DismHost.exe (PID: 5116)
Reads the computer name
- DismHost.exe (PID: 1660)
- DismHost.exe (PID: 6476)
- DismHost.exe (PID: 7948)
- DismHost.exe (PID: 8012)
- DismHost.exe (PID: 2284)
- DismHost.exe (PID: 7608)
- DismHost.exe (PID: 7296)
- DismHost.exe (PID: 1324)
- DismHost.exe (PID: 5936)
- DismHost.exe (PID: 5552)
- DismHost.exe (PID: 7592)
- DismHost.exe (PID: 8000)
- DismHost.exe (PID: 6736)
- DismHost.exe (PID: 5968)
- DismHost.exe (PID: 7716)
- DismHost.exe (PID: 5116)
Reads Environment values
- DismHost.exe (PID: 1660)
- DismHost.exe (PID: 6476)
- DismHost.exe (PID: 7948)
- DismHost.exe (PID: 8012)
- DismHost.exe (PID: 2284)
- DismHost.exe (PID: 7608)
- DismHost.exe (PID: 1324)
- DismHost.exe (PID: 7296)
- DismHost.exe (PID: 8000)
- DismHost.exe (PID: 5936)
- DismHost.exe (PID: 5552)
- DismHost.exe (PID: 7592)
- DismHost.exe (PID: 6736)
- DismHost.exe (PID: 5968)
- DismHost.exe (PID: 7716)
- DismHost.exe (PID: 5116)
Creates files in the program directory
- svchost.exe (PID: 2892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:03:06 10:50:34 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Win11Debloat-master/ |
Total processes
174
Monitored processes
86
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 648 | "C:\Program Files\Microsoft Update Health Tools\uhssvc.exe" | C:\Program Files\Microsoft Update Health Tools\uhssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Update Health Service Version: 10.0.19041.3626 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | rundll32.exe AppXDeploymentExtensions.OneCore.dll,ShellRefresh | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 860 | C:\WINDOWS\System32\svchost.exe -k LocalServiceNetworkRestricted -s RmSvc | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 956 | "ctfmon.exe" | C:\Windows\System32\ctfmon.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CTF Loader Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | C:\Users\admin\AppData\Local\Temp\786AF65A-3245-4638-B7A0-BC0B8D9B8880\dismhost.exe {139DDBBF-84DB-4C32-A972-E3818781442A} | C:\Users\admin\AppData\Local\Temp\786AF65A-3245-4638-B7A0-BC0B8D9B8880\DismHost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1572 | C:\WINDOWS\System32\svchost.exe -k netsvcs -p | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | C:\Users\admin\AppData\Local\Temp\6169C87E-504C-40BA-BA62-3B141FB1890A\dismhost.exe {0B40319E-8FC1-40F4-8EF2-9ECF84C3E096} | C:\Users\admin\AppData\Local\Temp\6169C87E-504C-40BA-BA62-3B141FB1890A\DismHost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1684 | C:\WINDOWS\System32\svchost.exe -k NetworkService -p -s WinRM | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2080 | C:\WINDOWS\System32\svchost.exe -k LocalServiceNetworkRestricted -p -s wscsvc | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
57 636
Read events
55 136
Write events
974
Delete events
1 526
Modification events
| (PID) Process: | (2996) svchost.exe | Key: | \REGISTRY\A\{6b84c8ab-e616-f9fc-89ca-c63c2f0ee491}\Root\InventoryDevicePnp |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (2996) svchost.exe | Key: | \REGISTRY\A\{6b84c8ab-e616-f9fc-89ca-c63c2f0ee491}\Root\InventoryDevicePnp\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2996) svchost.exe | Key: | \REGISTRY\A\{6b84c8ab-e616-f9fc-89ca-c63c2f0ee491}\Root\InventoryDeviceContainer |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (2996) svchost.exe | Key: | \REGISTRY\A\{6b84c8ab-e616-f9fc-89ca-c63c2f0ee491}\Root\InventoryDeviceContainer\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2996) svchost.exe | Key: | \REGISTRY\A\{6b84c8ab-e616-f9fc-89ca-c63c2f0ee491}\Root\InventoryDriverBinary |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (2996) svchost.exe | Key: | \REGISTRY\A\{6b84c8ab-e616-f9fc-89ca-c63c2f0ee491}\Root\InventoryDriverBinary\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2996) svchost.exe | Key: | \REGISTRY\A\{6b84c8ab-e616-f9fc-89ca-c63c2f0ee491}\Root\InventoryDeviceMediaClass |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (2996) svchost.exe | Key: | \REGISTRY\A\{6b84c8ab-e616-f9fc-89ca-c63c2f0ee491}\Root\InventoryDeviceMediaClass\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2996) svchost.exe | Key: | \REGISTRY\A\{6b84c8ab-e616-f9fc-89ca-c63c2f0ee491}\Root\DriverPackageExtended |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (2996) svchost.exe | Key: | \REGISTRY\A\{6b84c8ab-e616-f9fc-89ca-c63c2f0ee491}\Root\DriverPackageExtended\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
809
Suspicious files
62
Text files
114
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4996 | sppsvc.exe | C:\Windows\System32\spp\store\2.0\data.dat.tmp | binary | |
MD5:6BF72EF4B13772960CB993BC879A7278 | SHA256:43D3558A7A94E8E7528C352F836DB69F5F970AC1662E7E45228F1D660AED8ACA | |||
| 4996 | sppsvc.exe | C:\Windows\System32\spp\store\2.0\data.dat | binary | |
MD5:6BF72EF4B13772960CB993BC879A7278 | SHA256:43D3558A7A94E8E7528C352F836DB69F5F970AC1662E7E45228F1D660AED8ACA | |||
| 4996 | sppsvc.exe | C:\Windows\System32\spp\store\2.0\data.dat.bak | binary | |
MD5:6BF72EF4B13772960CB993BC879A7278 | SHA256:43D3558A7A94E8E7528C352F836DB69F5F970AC1662E7E45228F1D660AED8ACA | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.25780\Win11Debloat-master\LICENSE | text | |
MD5:9D25DD634D52D2DF35E37B96D32AB0FC | SHA256:22E6FEACBF3CF84858D5B4B7F3355CCFBE7BE6A8C633A41407AB41D0F0A8B4B8 | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.25780\Win11Debloat-master\Regfiles\Disable_Bing_Cortana_In_Search.reg | text | |
MD5:67E2D3B682A00FBA5C8ADB9BC9F92D72 | SHA256:C8BA77682A7BBB63D8999FA9E2CEC43EF5368DFFAE083142254495E8492DB8A8 | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.25780\Win11Debloat-master\Assets\menu.png | image | |
MD5:0133A5496DAD8797C80C1A3B07476E39 | SHA256:04899ED900F9809BDBBC4B426031A91ABE97B005D4F0F6B6B9F41DB8871D2543 | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.25780\Win11Debloat-master\Regfiles\Align_Taskbar_Left.reg | text | |
MD5:CC8DB3B8AE088278D69DA9E9CCDE09BE | SHA256:7E05AB7E0BBAC2D8125EE866BD24B00042A6B00AB7F64F095A0A6908E1174896 | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.25780\Win11Debloat-master\Regfiles\Disable_AI_Recall.reg | text | |
MD5:D15F16BCB329469EB254952724B6120B | SHA256:EF23B7E7F59A7754682BC8B1A48CD0DFECAB3863831ACA0A67BABC4D246FFE73 | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.25780\Win11Debloat-master\Regfiles\Disable_Chat_Taskbar.reg | text | |
MD5:EB157C5FC82EBF80449058FAB3D37676 | SHA256:F7FCAA50D7719D298DB2E7C06D5623924CFBB7E641FFBDAC16B7C69486430EF8 | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.25780\Win11Debloat-master\.github\FUNDING.yml | text | |
MD5:CE14B493F9279DE26175B9F3B3453B2B | SHA256:2230EA5712492396FE26C35023D05B560213B19C8247AE6289F3FE6663C088CE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
28
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7460 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5008 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5640 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5640 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5176 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7460 | backgroundTaskHost.exe | 20.199.58.43:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |