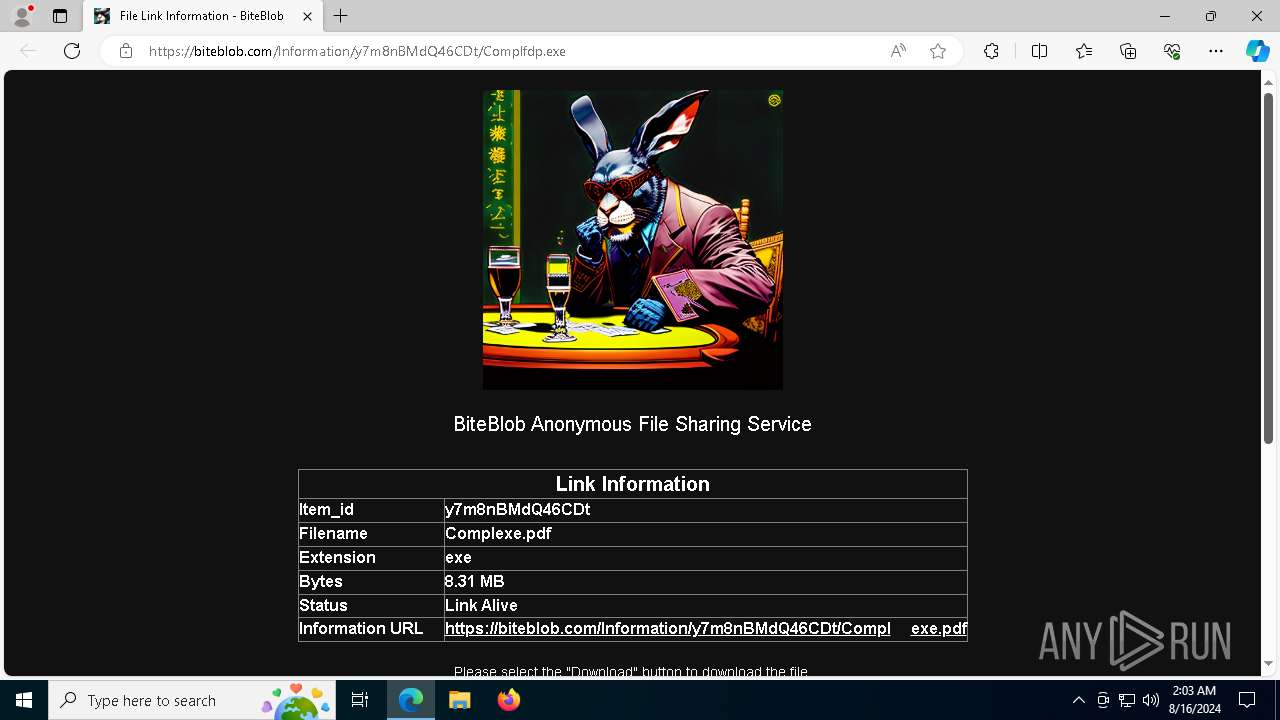
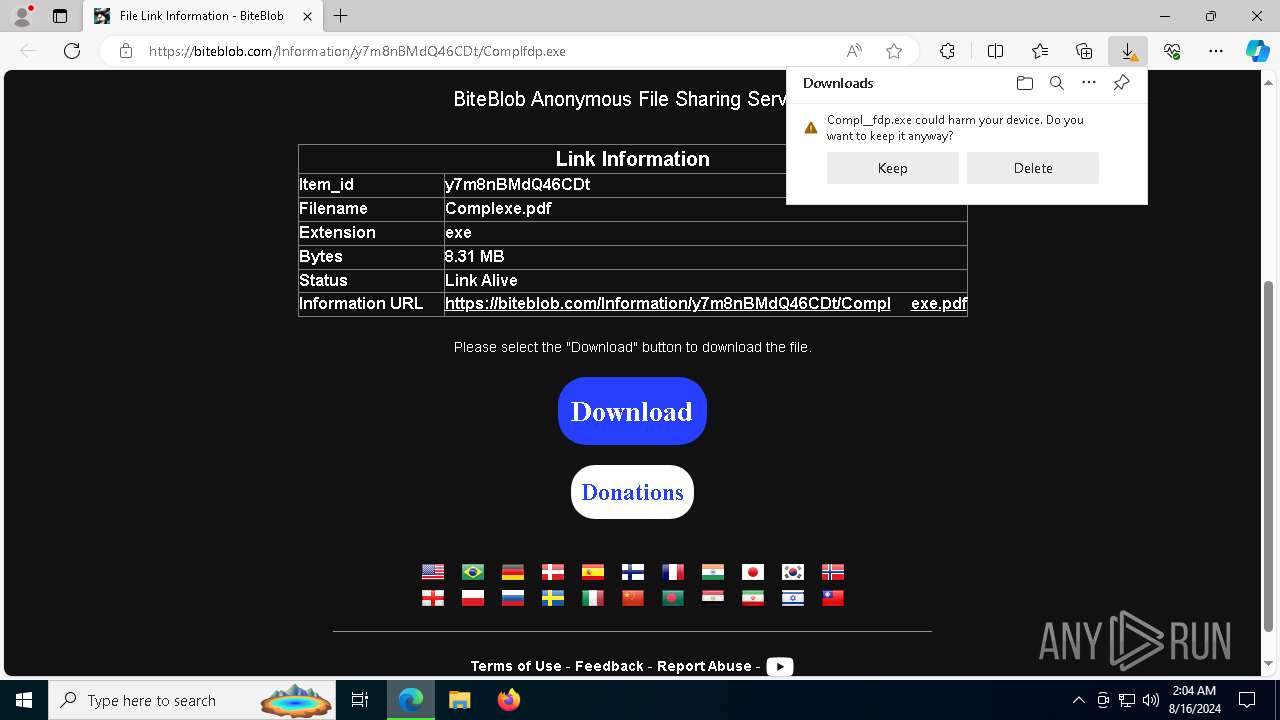
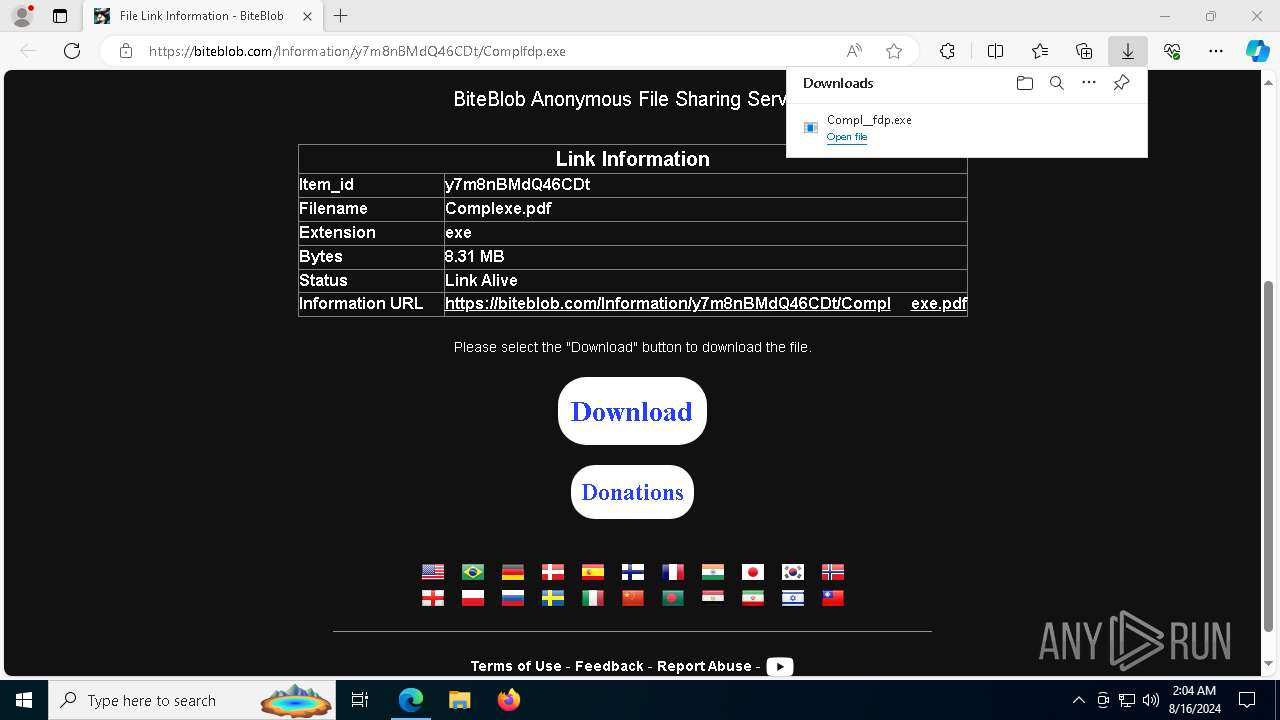
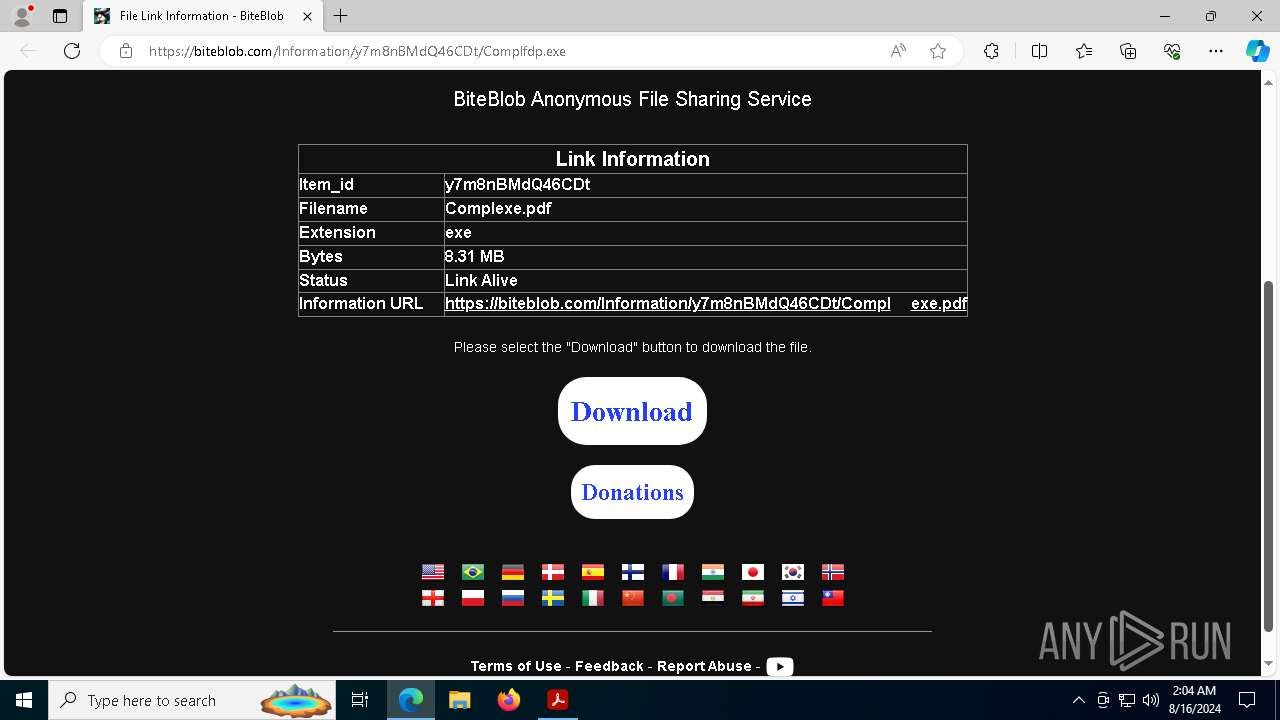
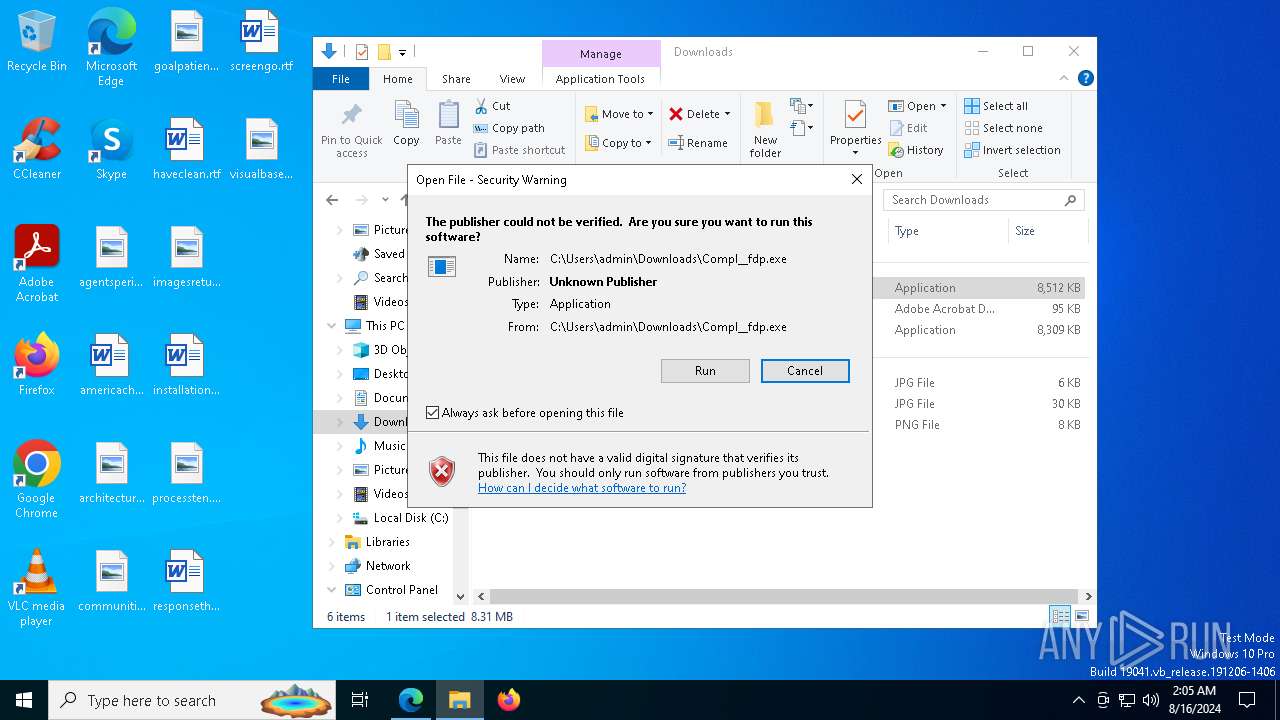
| URL: | https://biteblob.com/Information/y7m8nBMdQ46CDt/Complfdp.exe |
| Full analysis: | https://app.any.run/tasks/f8c8eb51-b660-4cc6-a3d4-0b055ab75795 |
| Verdict: | Malicious activity |
| Analysis date: | August 16, 2024, 02:03:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CD8FE999221B73CB306CC75A6F401851 |
| SHA1: | FD13378219D5C32A8E036B8ECF65F0A6D574B07E |
| SHA256: | 7A090D2D1B29B1C5081931AE8764878EEA79D1D64438C1D9DBCDE4C4C4FCA9A5 |
| SSDEEP: | 3:N8ay4PMKLKcZIyoZLN:2a1MK+c5OJ |
MALICIOUS
Adds path to the Windows Defender exclusion list
- decoded_file.exe (PID: 2360)
- decoded_file.exe (PID: 8940)
- decoded_file.exe (PID: 6128)
- decoded_file.exe (PID: 1248)
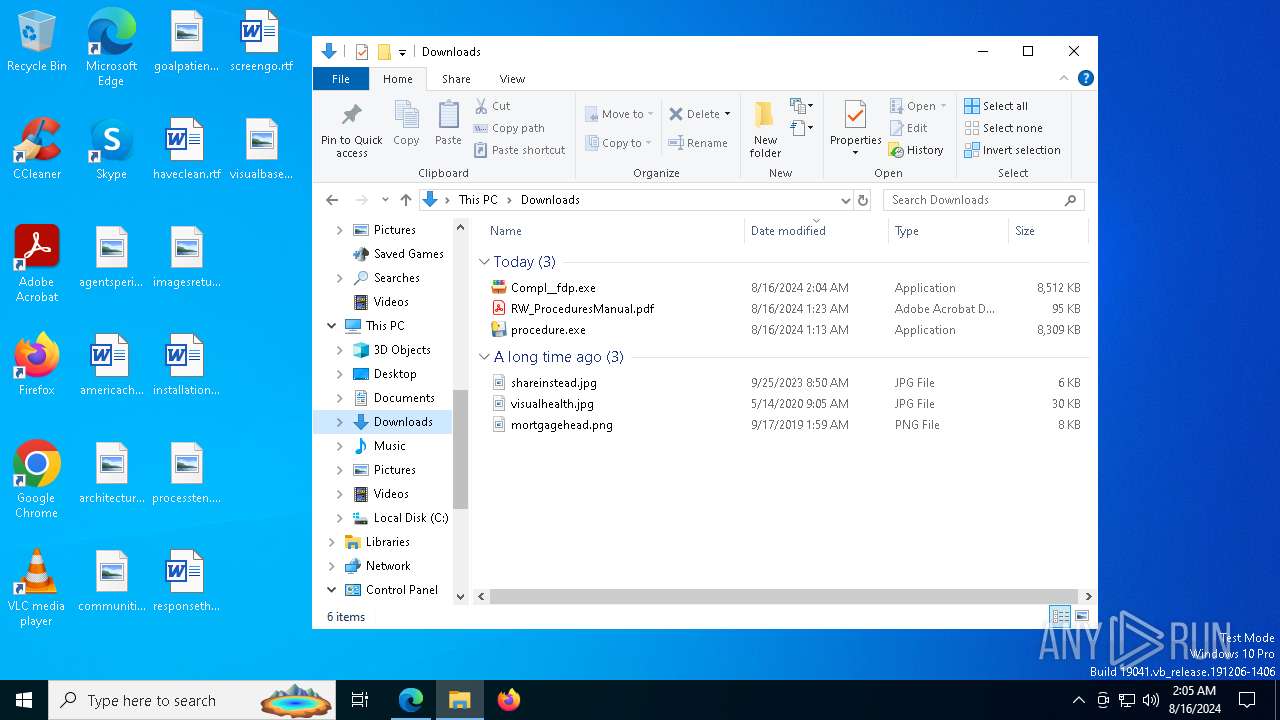
SUSPICIOUS
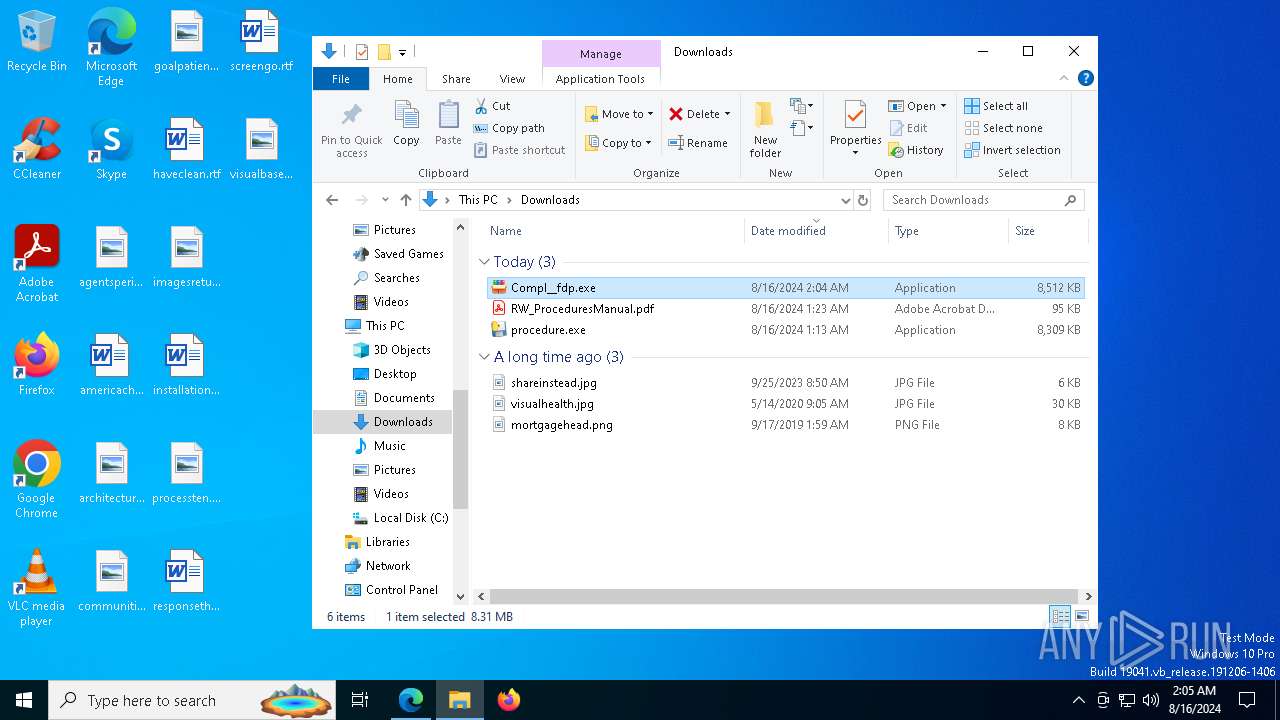
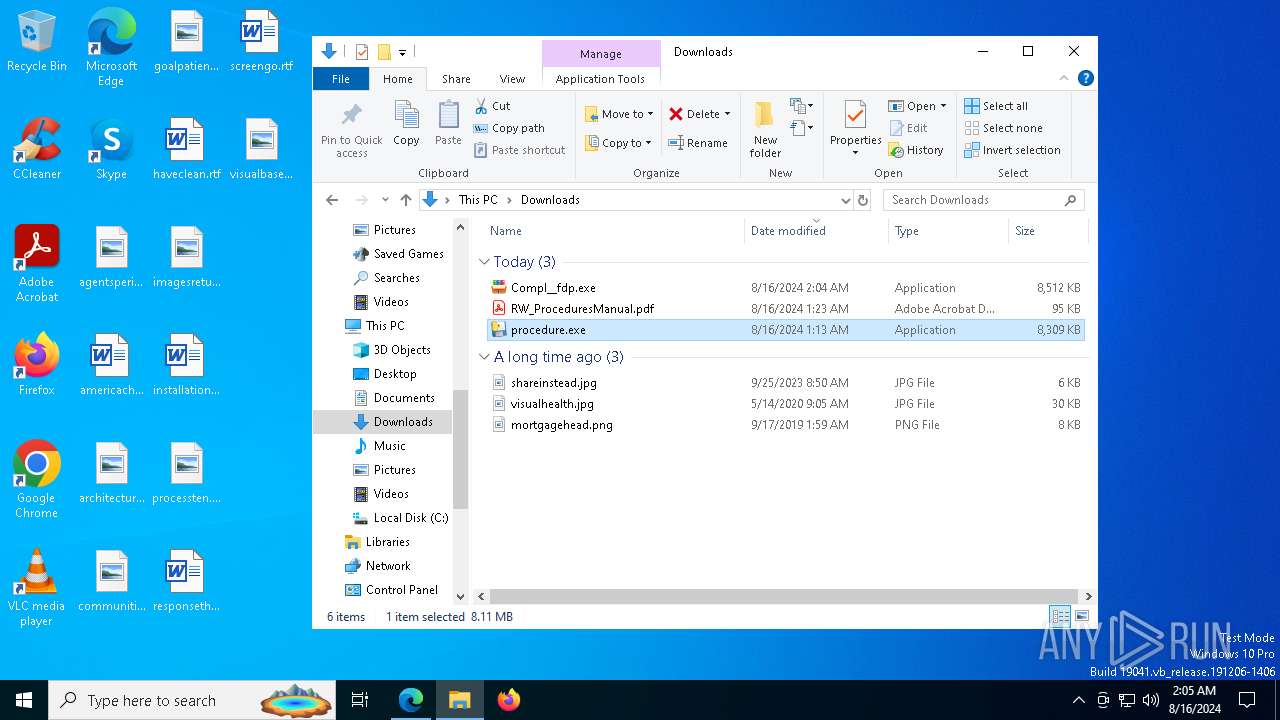
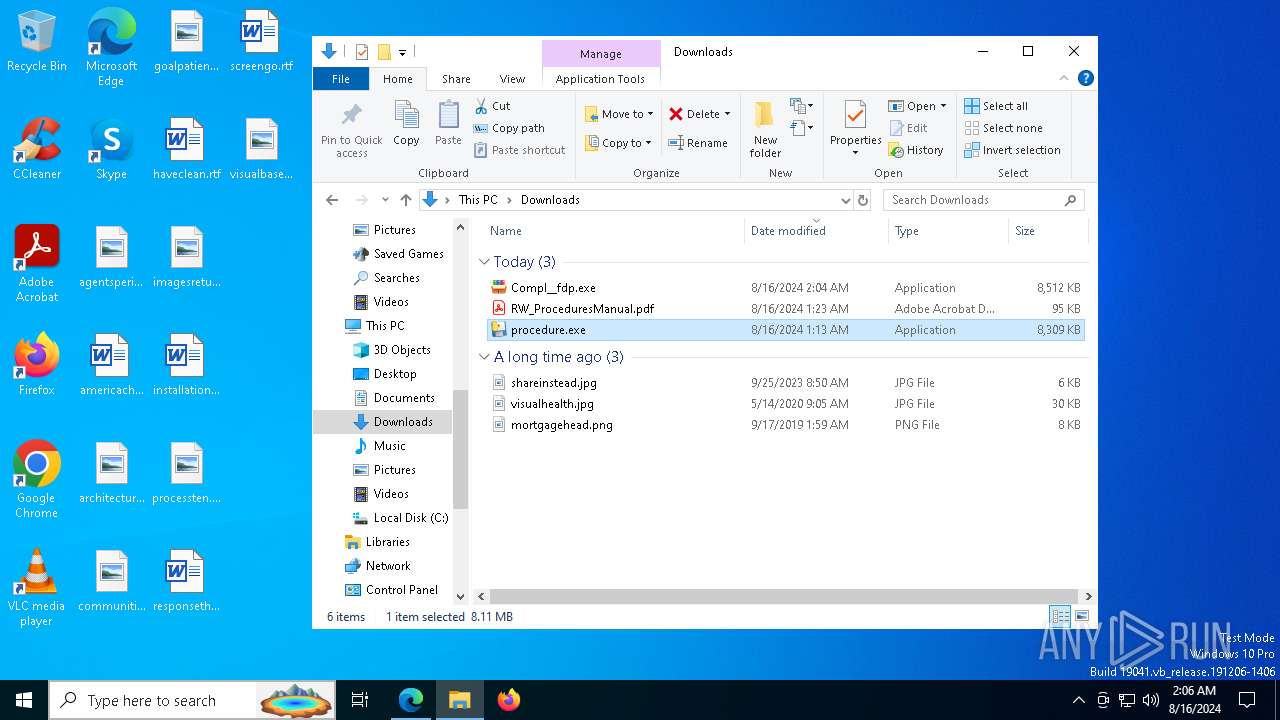
Executable content was dropped or overwritten
- Compl__fdp.exe (PID: 7524)
- procedure.exe (PID: 7408)
- procedure.exe (PID: 2852)
- procedure.exe (PID: 5400)
- procedure.exe (PID: 7112)
- procedure.exe (PID: 2136)
Reads the date of Windows installation
- Compl__fdp.exe (PID: 7524)
- decoded_file.exe (PID: 7996)
- Compl__fdp.exe (PID: 7444)
- decoded_file.exe (PID: 8220)
- decoded_file.exe (PID: 6140)
- decoded_file.exe (PID: 6172)
Drops the executable file immediately after the start
- Compl__fdp.exe (PID: 7524)
- procedure.exe (PID: 7408)
- procedure.exe (PID: 2852)
- procedure.exe (PID: 5400)
- procedure.exe (PID: 7112)
- procedure.exe (PID: 2136)
The process drops C-runtime libraries
- procedure.exe (PID: 7408)
- procedure.exe (PID: 5400)
- procedure.exe (PID: 7112)
- procedure.exe (PID: 2136)
Reads security settings of Internet Explorer
- Compl__fdp.exe (PID: 7524)
- decoded_file.exe (PID: 7996)
- Compl__fdp.exe (PID: 7444)
- decoded_file.exe (PID: 8220)
- decoded_file.exe (PID: 6140)
- decoded_file.exe (PID: 6172)
Process drops python dynamic module
- procedure.exe (PID: 7408)
- procedure.exe (PID: 5400)
- procedure.exe (PID: 7112)
- procedure.exe (PID: 2136)
Application launched itself
- procedure.exe (PID: 7408)
- decoded_file.exe (PID: 7996)
- procedure.exe (PID: 5400)
- decoded_file.exe (PID: 8220)
- procedure.exe (PID: 7112)
- procedure.exe (PID: 2136)
- decoded_file.exe (PID: 6140)
- decoded_file.exe (PID: 6172)
Loads Python modules
- procedure.exe (PID: 2852)
- procedure.exe (PID: 7516)
- procedure.exe (PID: 9012)
- procedure.exe (PID: 9136)
Process drops legitimate windows executable
- procedure.exe (PID: 7408)
- procedure.exe (PID: 5400)
- procedure.exe (PID: 7112)
- procedure.exe (PID: 2136)
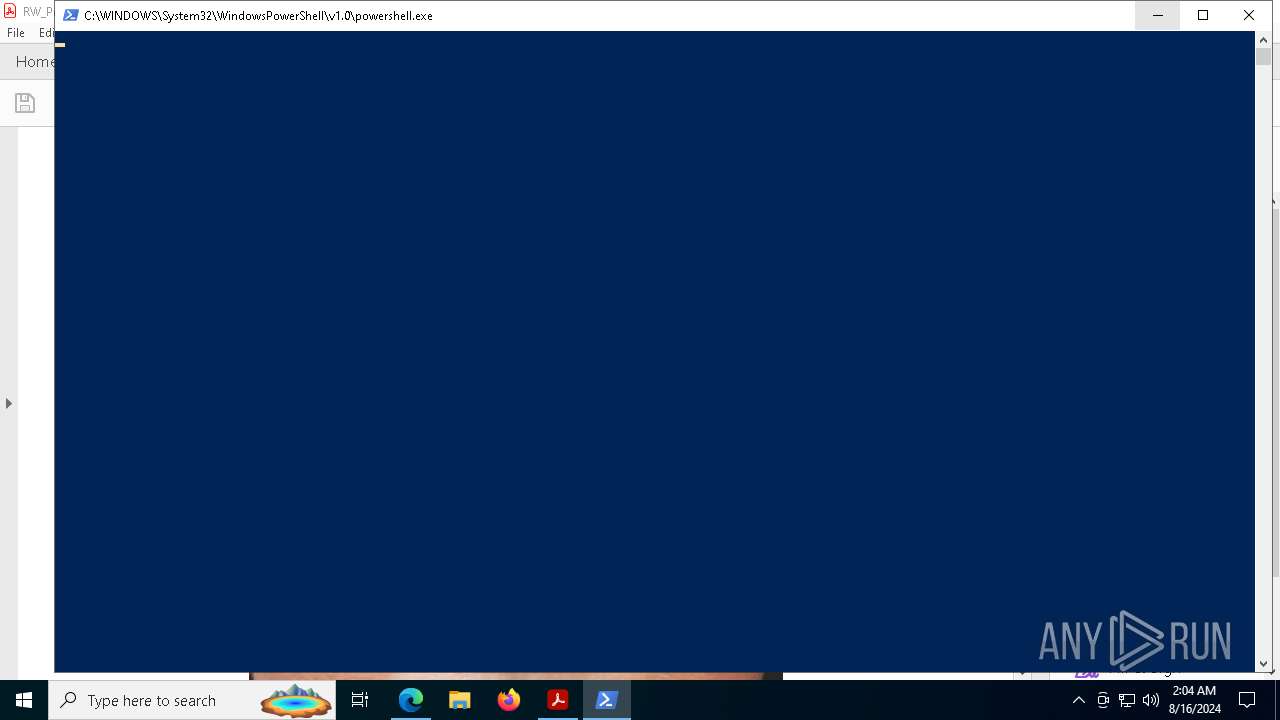
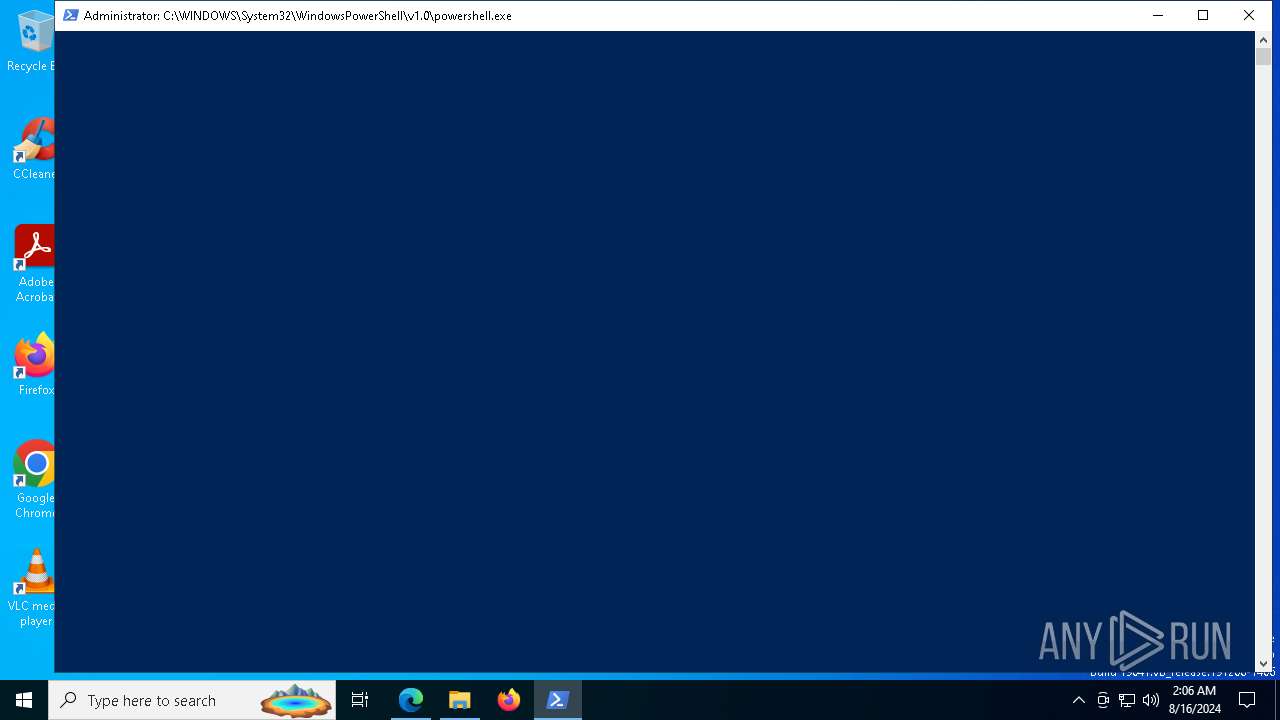
Starts POWERSHELL.EXE for commands execution
- decoded_file.exe (PID: 2360)
- decoded_file.exe (PID: 8940)
- decoded_file.exe (PID: 6128)
- decoded_file.exe (PID: 1248)
Script adds exclusion path to Windows Defender
- decoded_file.exe (PID: 2360)
- decoded_file.exe (PID: 8940)
- decoded_file.exe (PID: 6128)
- decoded_file.exe (PID: 1248)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 8016)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 6348)
Checks supported languages
- identity_helper.exe (PID: 6140)
- Compl__fdp.exe (PID: 7524)
- procedure.exe (PID: 7408)
- procedure.exe (PID: 2852)
- decoded_file.exe (PID: 2360)
- acrobat_sl.exe (PID: 2224)
- Compl__fdp.exe (PID: 7444)
- decoded_file.exe (PID: 7996)
- procedure.exe (PID: 7516)
- procedure.exe (PID: 5400)
- decoded_file.exe (PID: 8940)
- procedure.exe (PID: 7112)
- decoded_file.exe (PID: 8220)
- procedure.exe (PID: 9012)
- procedure.exe (PID: 2136)
- decoded_file.exe (PID: 6140)
- procedure.exe (PID: 9136)
- decoded_file.exe (PID: 6128)
- decoded_file.exe (PID: 6172)
- decoded_file.exe (PID: 1248)
Reads the computer name
- identity_helper.exe (PID: 6140)
- Compl__fdp.exe (PID: 7524)
- procedure.exe (PID: 7408)
- procedure.exe (PID: 2852)
- decoded_file.exe (PID: 7996)
- decoded_file.exe (PID: 2360)
- Compl__fdp.exe (PID: 7444)
- procedure.exe (PID: 5400)
- procedure.exe (PID: 7516)
- decoded_file.exe (PID: 8220)
- decoded_file.exe (PID: 8940)
- procedure.exe (PID: 7112)
- procedure.exe (PID: 2136)
- procedure.exe (PID: 9012)
- procedure.exe (PID: 9136)
- decoded_file.exe (PID: 6140)
- decoded_file.exe (PID: 6128)
- decoded_file.exe (PID: 6172)
- decoded_file.exe (PID: 1248)
Reads Environment values
- identity_helper.exe (PID: 6140)
The process uses the downloaded file
- msedge.exe (PID: 7460)
- msedge.exe (PID: 6348)
Executable content was dropped or overwritten
- msedge.exe (PID: 6348)
- msedge.exe (PID: 6680)
- AdobeARM.exe (PID: 7404)
Process checks computer location settings
- Compl__fdp.exe (PID: 7524)
- decoded_file.exe (PID: 7996)
- Compl__fdp.exe (PID: 7444)
- decoded_file.exe (PID: 8220)
- decoded_file.exe (PID: 6140)
- decoded_file.exe (PID: 6172)
Application launched itself
- msedge.exe (PID: 6348)
- Acrobat.exe (PID: 7424)
- AcroCEF.exe (PID: 7344)
- Acrobat.exe (PID: 5540)
- AcroCEF.exe (PID: 8600)
Create files in a temporary directory
- procedure.exe (PID: 7408)
- procedure.exe (PID: 2852)
- procedure.exe (PID: 5400)
- procedure.exe (PID: 7516)
- procedure.exe (PID: 7112)
- procedure.exe (PID: 2136)
- procedure.exe (PID: 9012)
- procedure.exe (PID: 9136)
Checks proxy server information
- procedure.exe (PID: 2852)
- procedure.exe (PID: 7516)
- procedure.exe (PID: 9012)
- procedure.exe (PID: 9136)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 2068)
- powershell.exe (PID: 8544)
- powershell.exe (PID: 4280)
Reads the software policy settings
- decoded_file.exe (PID: 2360)
- decoded_file.exe (PID: 8940)
- decoded_file.exe (PID: 6128)
- decoded_file.exe (PID: 1248)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8016)
- powershell.exe (PID: 2068)
- powershell.exe (PID: 8544)
- powershell.exe (PID: 4280)
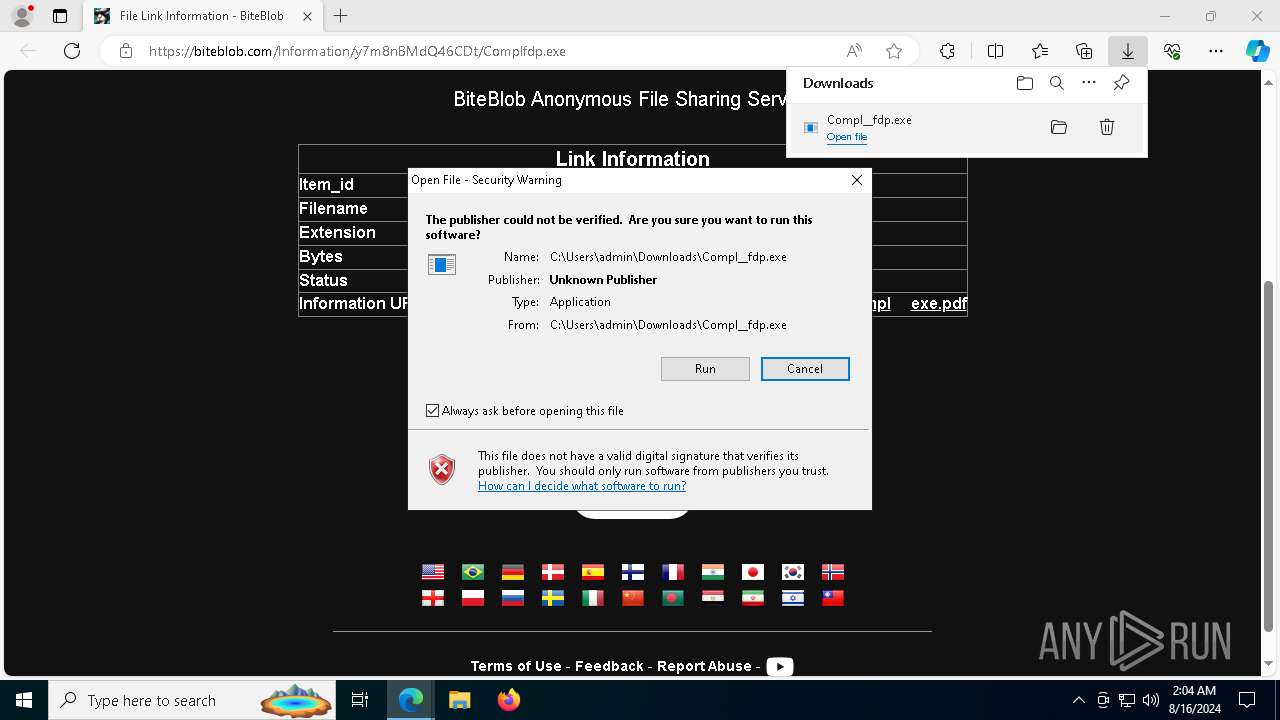
Manual execution by a user
- Compl__fdp.exe (PID: 7444)
- procedure.exe (PID: 7112)
- procedure.exe (PID: 2136)
Reads the machine GUID from the registry
- decoded_file.exe (PID: 2360)
- decoded_file.exe (PID: 8940)
- decoded_file.exe (PID: 6128)
- decoded_file.exe (PID: 1248)
PyInstaller has been detected (YARA)
- procedure.exe (PID: 5400)
- procedure.exe (PID: 9012)
- procedure.exe (PID: 7112)
- procedure.exe (PID: 2136)
- procedure.exe (PID: 9136)
Potential remote process memory writing (Base64 Encoded 'WriteProcessMemory')
- procedure.exe (PID: 9012)
- procedure.exe (PID: 9136)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- procedure.exe (PID: 9012)
- procedure.exe (PID: 9136)
Potential remote process memory reading (Base64 Encoded 'ReadProcessMemory')
- procedure.exe (PID: 9012)
- procedure.exe (PID: 9136)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- procedure.exe (PID: 9012)
- procedure.exe (PID: 9136)
Potential dynamic function import (Base64 Encoded 'GetProcAddress')
- procedure.exe (PID: 9012)
- procedure.exe (PID: 9136)
Potential library load (Base64 Encoded 'LoadLibrary')
- procedure.exe (PID: 9012)
- procedure.exe (PID: 9136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
238
Monitored processes
100
Malicious processes
6
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5336 --field-trial-handle=2524,i,7038255697424239964,12610429720956517576,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 752 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6444 --field-trial-handle=2524,i,7038255697424239964,12610429720956517576,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=renderer --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --first-renderer-process --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --touch-events=enabled --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=1684 --field-trial-handle=1604,i,15599330383733639304,3172363483561614622,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:1 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 1236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5168 --field-trial-handle=2524,i,7038255697424239964,12610429720956517576,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6532 --field-trial-handle=2524,i,7038255697424239964,12610429720956517576,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1248 | "C:\Users\admin\AppData\Local\Temp\decoded_file.exe" | C:\Users\admin\AppData\Local\Temp\decoded_file.exe | decoded_file.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5712 --field-trial-handle=2524,i,7038255697424239964,12610429720956517576,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2068 | powershell -Command "Add-MpPreference -ExclusionPath \"C:\\\"" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | decoded_file.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\Downloads\procedure.exe" | C:\Users\admin\Downloads\procedure.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat_sl.exe" | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrobat_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 22.3.20310.0 Modules
| |||||||||||||||
Total events
112 143
Read events
111 323
Write events
783
Delete events
37
Modification events
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
71
Suspicious files
534
Text files
149
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe53c9.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe53d8.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe53d8.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe53d8.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe53c9.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
176
DNS requests
67
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1360 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1360 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6184 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6340 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7404 | AdobeARM.exe | GET | 304 | 23.48.23.54:80 | http://acroipm2.adobe.com/assets/Owner/arm/ReportOwner.txt | unknown | — | — | whitelisted |
7404 | AdobeARM.exe | GET | 304 | 23.48.23.54:80 | http://acroipm2.adobe.com/assets/Owner/arm/ProcessMAU.txt | unknown | — | — | whitelisted |
7404 | AdobeARM.exe | GET | 404 | 23.48.23.54:80 | http://acroipm2.adobe.com/assets/Owner/arm/2024/8/OwnerAPI/Rdr.txt | unknown | — | — | whitelisted |
7404 | AdobeARM.exe | GET | 404 | 23.48.23.54:80 | http://acroipm2.adobe.com/assets/Owner/arm/2024/8/UC/Other.txt | unknown | — | — | whitelisted |
7404 | AdobeARM.exe | GET | 404 | 23.48.23.54:80 | http://acroipm2.adobe.com/assets/Owner/arm/33/adnme/NoValidReasonForAdnme.txt | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3140 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2464 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
6680 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6680 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6680 | msedge.exe | 71.179.14.4:443 | biteblob.com | UUNET | US | unknown |
6680 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
biteblob.com |
| unknown |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |