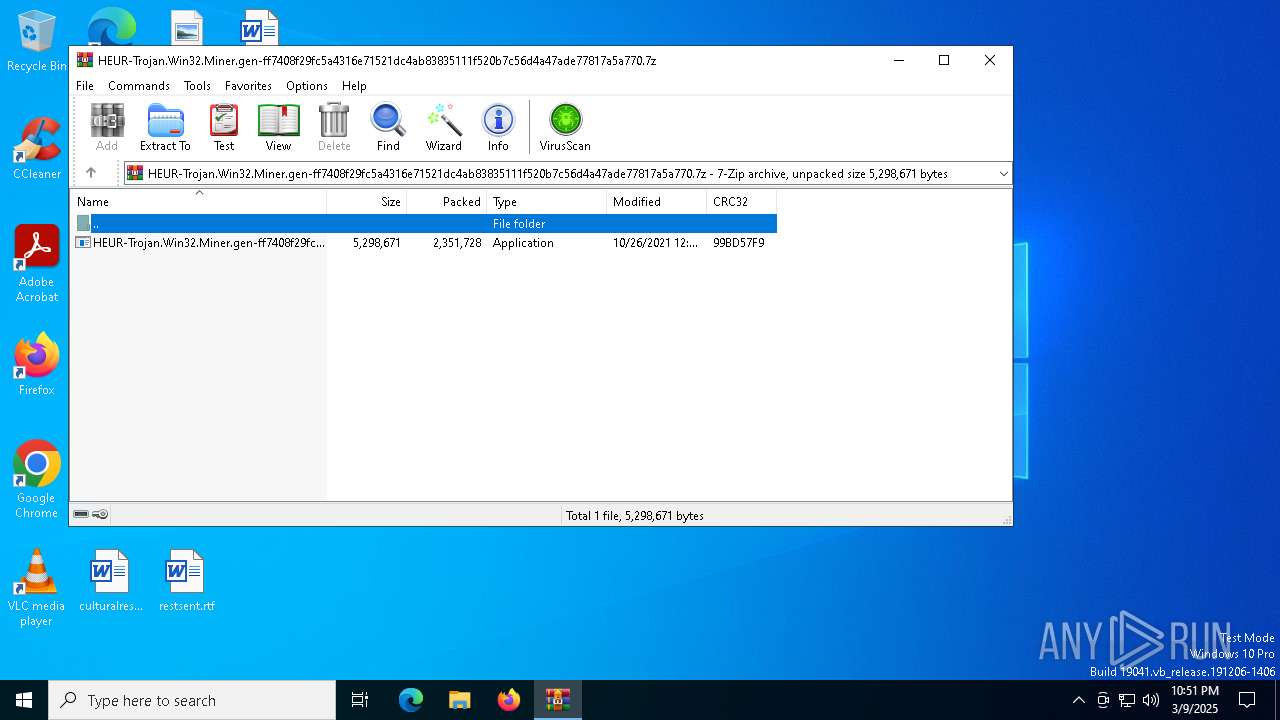
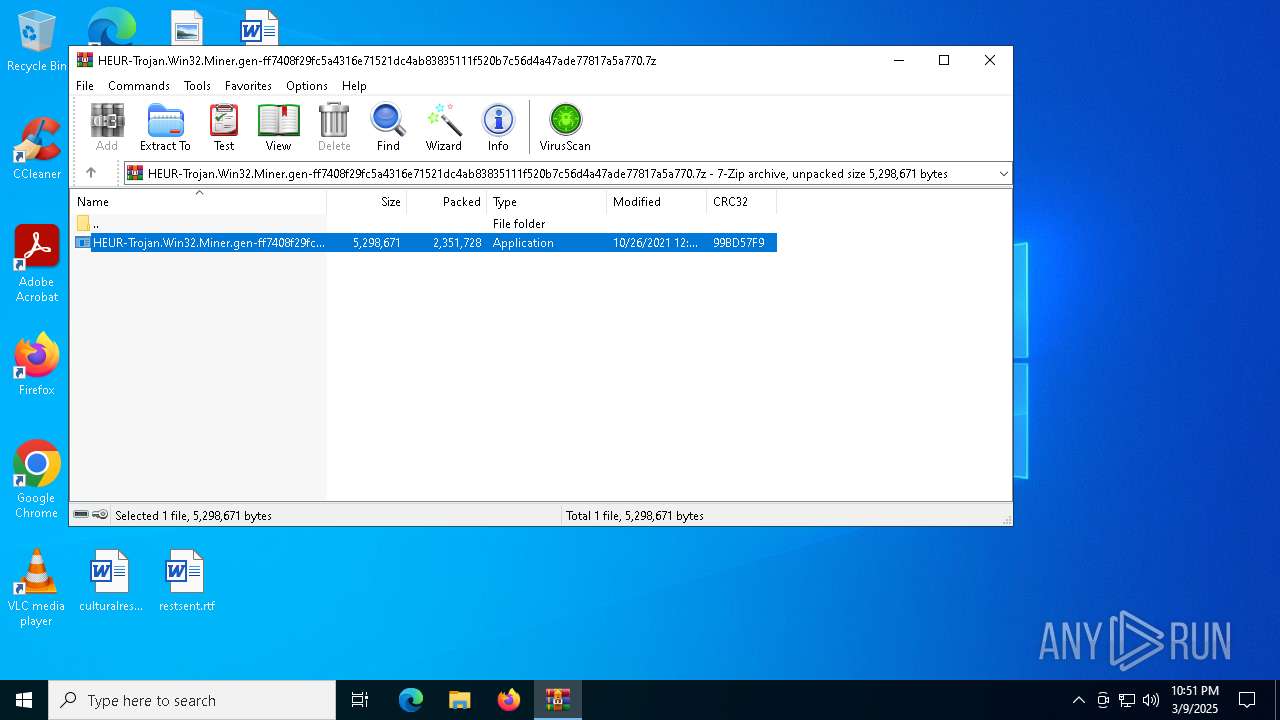
| File name: | HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.7z |
| Full analysis: | https://app.any.run/tasks/ec7c5f33-e9df-4b72-b690-75cd109f8644 |
| Verdict: | Malicious activity |
| Analysis date: | March 09, 2025, 22:51:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 522E99A6E05C65968D93CD60FE576006 |
| SHA1: | 7602C0DE74EFBF3E1AC2A876609C57B21B978E29 |
| SHA256: | 7A07581F835C645439580574B62D7FFD77C1F5F01E3A33DC6EE29EA0B8A49EAE |
| SSDEEP: | 98304:GRAH2n4jAPWIEYpbjzFRzTD9Xzlc9PFewnjb//Hdpt3pk15ha1uh96gfmNVfNzZw:tvXg |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 456)
Changes image file execution options
- aeycbxq.exe (PID: 8048)
Vulnerable driver has been detected
- aeycbxq.exe (PID: 8048)
Application was injected by another process
- dllhost.exe (PID: 8164)
- dllhost.exe (PID: 5384)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 8036)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 8088)
- powershell.exe (PID: 8096)
Runs injected code in another process
- powershell.exe (PID: 8088)
- powershell.exe (PID: 8096)
Deletes shadow copies
- cmd.exe (PID: 1012)
SUSPICIOUS
Starts CMD.EXE for commands execution
- HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.exe (PID: 720)
- aeycbxq.exe (PID: 8048)
- cmd.exe (PID: 8036)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 728)
Executable content was dropped or overwritten
- HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.exe (PID: 720)
- aeycbxq.exe (PID: 8048)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 6676)
Reads security settings of Internet Explorer
- aeycbxq.exe (PID: 8048)
Drops a system driver (possible attempt to evade defenses)
- aeycbxq.exe (PID: 8048)
Invokes assembly entry point (POWERSHELL)
- powershell.exe (PID: 8088)
- powershell.exe (PID: 8096)
The process executes via Task Scheduler
- powershell.exe (PID: 8088)
- powershell.exe (PID: 8096)
Executes as Windows Service
- aeycbxq.exe (PID: 8048)
Application launched itself
- cmd.exe (PID: 8068)
- cmd.exe (PID: 8036)
- cmd.exe (PID: 728)
Uses WMIC.EXE
- cmd.exe (PID: 1012)
- cmd.exe (PID: 1388)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 6740)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 5072)
- cmd.exe (PID: 3132)
- cmd.exe (PID: 8136)
Uses WMIC.EXE for persistence
- cmd.exe (PID: 1388)
- cmd.exe (PID: 1012)
INFO
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8168)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8168)
- BackgroundTransferHost.exe (PID: 7960)
- BackgroundTransferHost.exe (PID: 5576)
- BackgroundTransferHost.exe (PID: 7688)
- WMIC.exe (PID: 2088)
- WMIC.exe (PID: 1128)
- WMIC.exe (PID: 8188)
- WMIC.exe (PID: 2268)
- WMIC.exe (PID: 8076)
- WMIC.exe (PID: 5720)
- BackgroundTransferHost.exe (PID: 1164)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 456)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 8168)
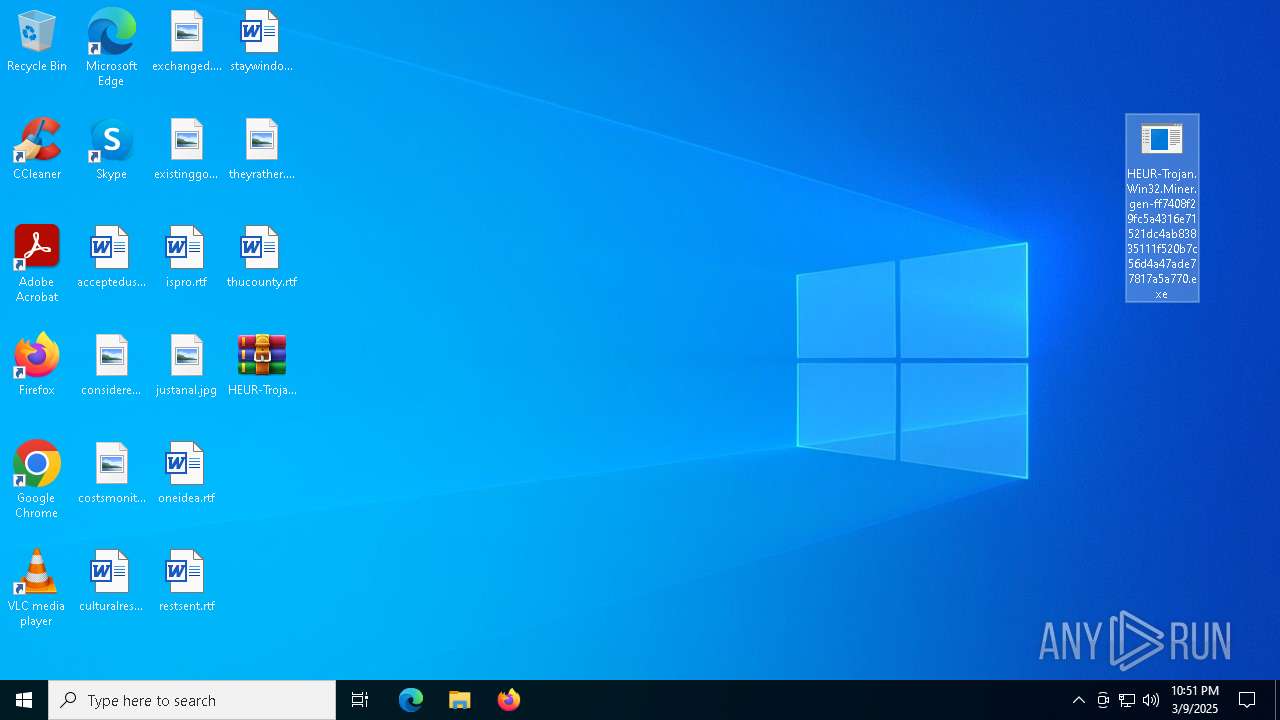
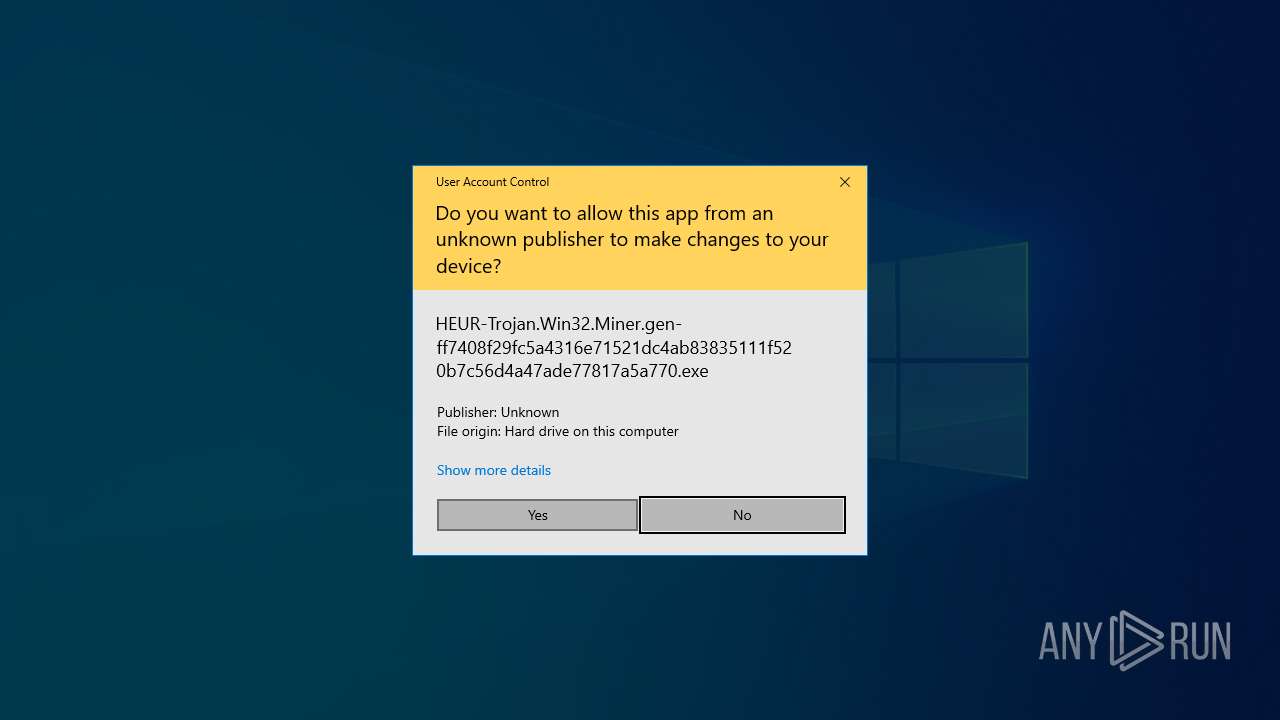
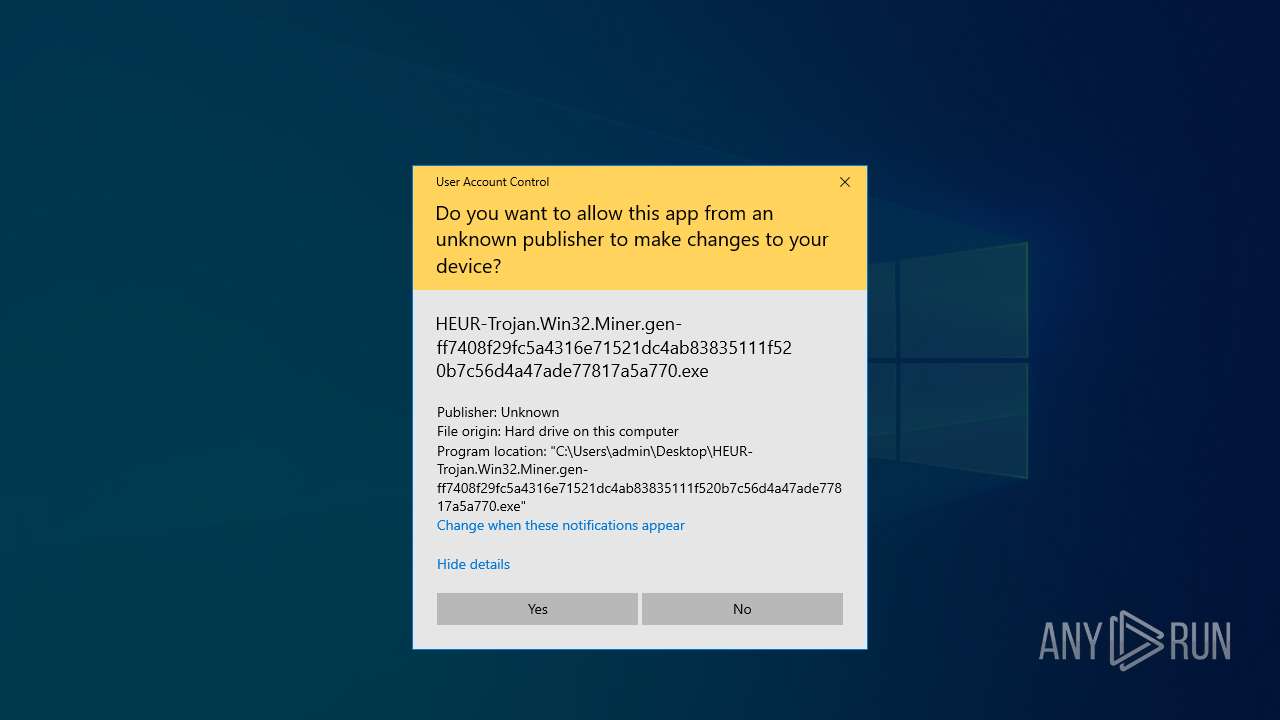
Manual execution by a user
- HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.exe (PID: 720)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 8168)
Checks supported languages
- HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.exe (PID: 720)
- aeycbxq.exe (PID: 8024)
- aeycbxq.exe (PID: 8048)
- rgapba.exe (PID: 8060)
Reads the machine GUID from the registry
- HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.exe (PID: 720)
- aeycbxq.exe (PID: 8024)
- aeycbxq.exe (PID: 8048)
Reads the computer name
- HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.exe (PID: 720)
- aeycbxq.exe (PID: 8024)
- aeycbxq.exe (PID: 8048)
- rgapba.exe (PID: 8060)
The sample compiled with japanese language support
- aeycbxq.exe (PID: 8048)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 8096)
- powershell.exe (PID: 8088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2021:10:26 12:07:02+00:00 |
| ArchivedFileName: | HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.exe |
Total processes
183
Monitored processes
50
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
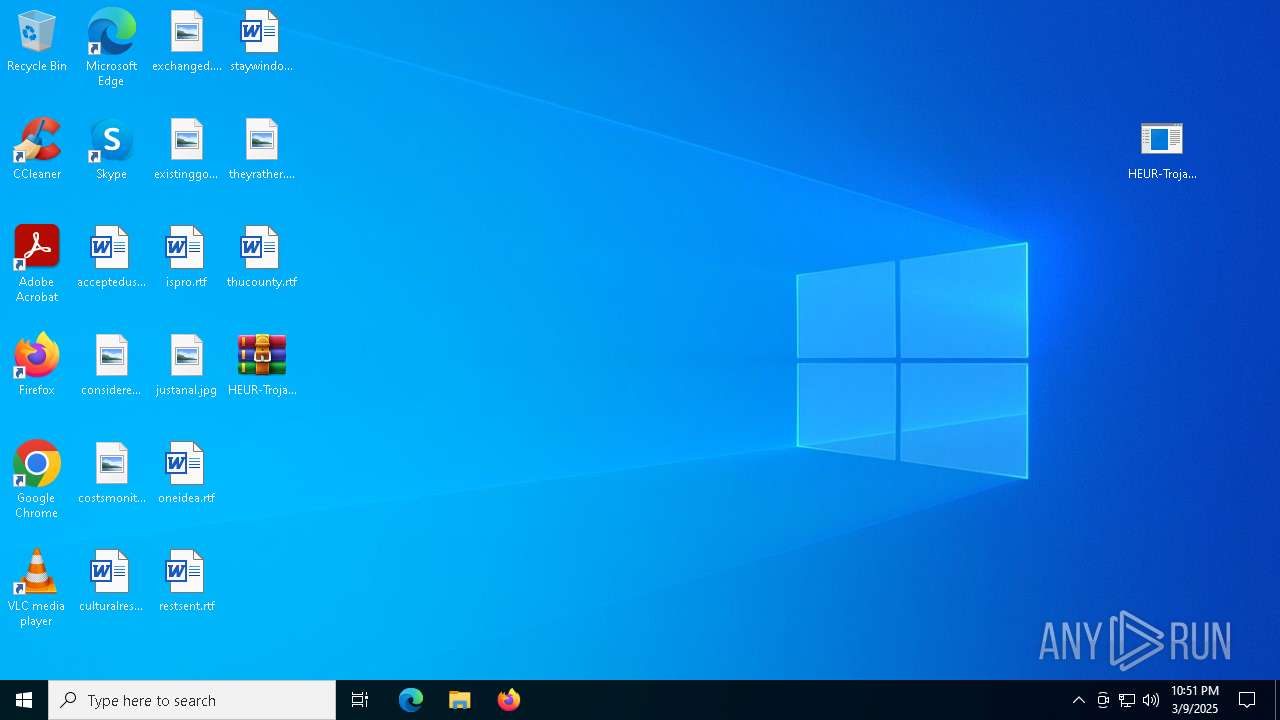
| 456 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 720 | "C:\Users\admin\Desktop\HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.exe" | C:\Users\admin\Desktop\HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 728 | cmd.exe /c cmd /c powercfg -setactive 3a00554b-ff08-4495-aa2b-6bede4497714 | C:\Windows\SysWOW64\cmd.exe | — | aeycbxq.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | cmd /c wmic /NAMESPACE:"\\root\subscription" PATH __EventFilter WHERE Name="vgarvfrp" DELETE & wmic /NAMESPACE:"\\root\subscription" PATH CommandLineEventConsumer WHERE Name="iafrhbxw" DELETE & wmic /NAMESPACE:"\\root\subscription" PATH __FilterToConsumerBinding WHERE Filter="__EventFilter.Name='vgarvfrp'" DELETE | C:\Windows\SysWOW64\cmd.exe | — | aeycbxq.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | wmic /NAMESPACE:"\\root\subscription" PATH __FilterToConsumerBinding WHERE Filter="__EventFilter.Name='vgarvfrp'" DELETE | C:\Windows\SysWOW64\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | cmd /c wmic /NAMESPACE:"\\root\subscription" PATH __EventFilter CREATE Name="vgarvfrp", EventNameSpace="root\cimv2",QueryLanguage="WQL", Query="SELECT * FROM __InstanceModificationEvent WITHIN 30 WHERE TargetInstance ISA 'Win32_PerfFormattedData_PerfOS_System'" & wmic /NAMESPACE:"\\root\subscription" PATH CommandLineEventConsumer CREATE Name="iafrhbxw",CommandLineTemplate="c:\windows\ime\sadxinz\rnmcgu.exe" & wmic /NAMESPACE:"\\root\subscription" PATH __FilterToConsumerBinding CREATE Filter="__EventFilter.Name="vgarvfrp"", Consumer="CommandLineEventConsumer.Name="iafrhbxw"" | C:\Windows\SysWOW64\cmd.exe | — | aeycbxq.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | wmic /NAMESPACE:"\\root\subscription" PATH __EventFilter CREATE Name="vgarvfrp", EventNameSpace="root\cimv2",QueryLanguage="WQL", Query="SELECT * FROM __InstanceModificationEvent WITHIN 30 WHERE TargetInstance ISA 'Win32_PerfFormattedData_PerfOS_System'" | C:\Windows\SysWOW64\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | powercfg -import c:\windows\fonts\ijcfroq\BestPower.pow | C:\Windows\SysWOW64\powercfg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 792
Read events
14 736
Write events
56
Delete events
0
Modification events
| (PID) Process: | (456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.7z | |||
| (PID) Process: | (456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
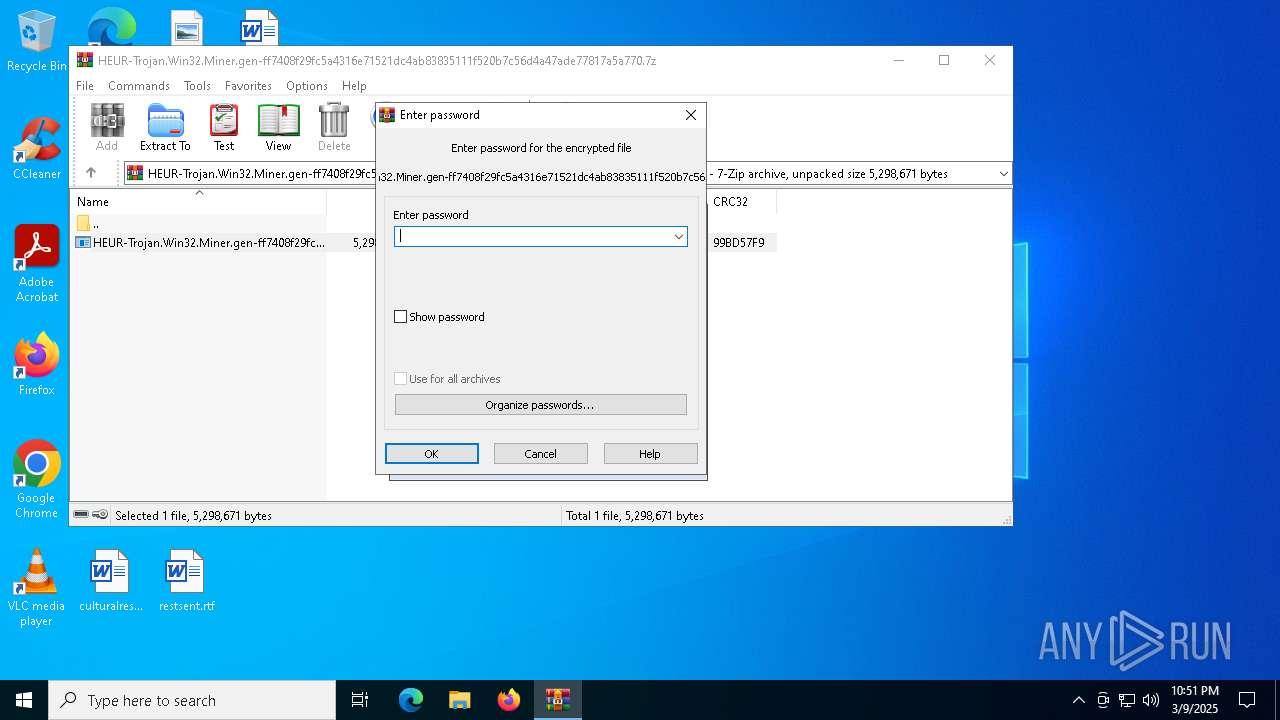
| (PID) Process: | (456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7960) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
8
Suspicious files
12
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8168 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\6dd00b06-46ed-4105-a80f-2e4de258d9eb.down_data | — | |
MD5:— | SHA256:— | |||
| 456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb456.671\HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.exe | executable | |
MD5:57FE58507801A0D22379B8CE7557FBF3 | SHA256:FF7408F29FC5A4316E71521DC4AB83835111F520B7C56D4A47ADE77817A5A770 | |||
| 720 | HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.exe | C:\Windows\Fonts\ijcfroq\aeycbxq.exe | executable | |
MD5:57FE58507801A0D22379B8CE7557FBF3 | SHA256:FF7408F29FC5A4316E71521DC4AB83835111F520B7C56D4A47ADE77817A5A770 | |||
| 8168 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:F2F58B09BA736A8FB4009C83538D4CE4 | SHA256:293C8E191BCD472DE81FEC2947405AFCFBCEE847AD436633DBC9E4DB03BF5130 | |||
| 8168 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\81b8af6d-49fb-4436-a86a-5ef4f5edd005.61c76225-95f0-4e49-a044-25a77f66fc0d.down_meta | binary | |
MD5:13D4085636D924A117F3595FA4B0CE43 | SHA256:27ABD70CD2A9D58AAC3D67C402D2A0010073E9BF1843CE6D5EE96CF7DB307FAE | |||
| 8168 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\81b8af6d-49fb-4436-a86a-5ef4f5edd005.up_meta_secure | binary | |
MD5:8CF62C928A82E21740C3E61CA7890054 | SHA256:203DDA99DF9C52E0EF5C7A3417596B93200A092B052858ECB30809FD4A9ABB31 | |||
| 8048 | aeycbxq.exe | C:\Windows\Fonts\dvduzyza\iwwdqqi.exe | executable | |
MD5:1FE7050A8B9C83E76AD33A4069AA5122 | SHA256:961E875381E957BB401D1F161FA0323C84AEBB65EE2C8788FBF667694E6BBB43 | |||
| 8168 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\6dd00b06-46ed-4105-a80f-2e4de258d9eb.61c76225-95f0-4e49-a044-25a77f66fc0d.down_meta | binary | |
MD5:13D4085636D924A117F3595FA4B0CE43 | SHA256:27ABD70CD2A9D58AAC3D67C402D2A0010073E9BF1843CE6D5EE96CF7DB307FAE | |||
| 8168 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:AD65BBA990E9A146C8789184B44B3332 | SHA256:C57BBFD31CE81C873E766C5DEEE854B02BFF08020DF9BE1A3B4562BD67CC932D | |||
| 720 | HEUR-Trojan.Win32.Miner.gen-ff7408f29fc5a4316e71521dc4ab83835111f520b7c56d4a47ade77817a5a770.exe | C:\Users\admin\AppData\Local\Temp\1112437\....\TemporaryFile | executable | |
MD5:57FE58507801A0D22379B8CE7557FBF3 | SHA256:FF7408F29FC5A4316E71521DC4AB83835111F520B7C56D4A47ADE77817A5A770 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
27
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7172 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8168 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
616 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
616 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
7172 | backgroundTaskHost.exe | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7172 | backgroundTaskHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
8168 | BackgroundTransferHost.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
hutao.halorick.club |
| malicious |
hutao.lulululu.shop |
| unknown |
hutao.oppomm.club |
| unknown |