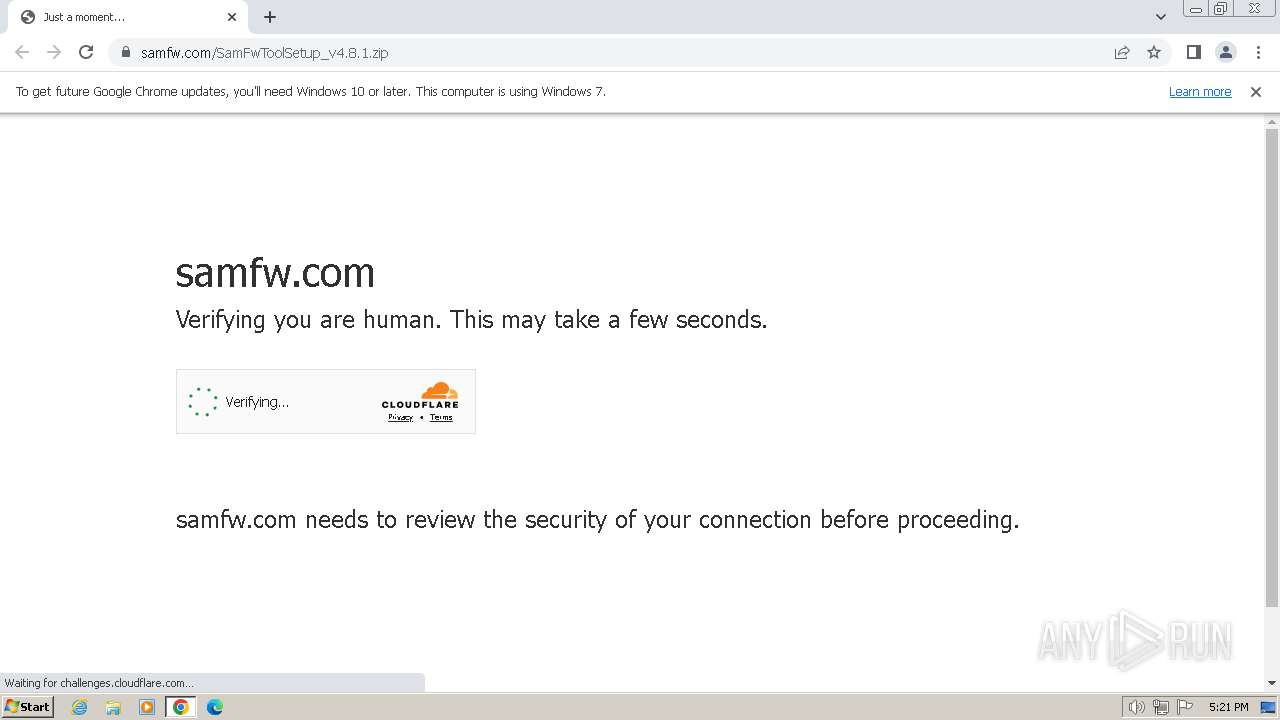
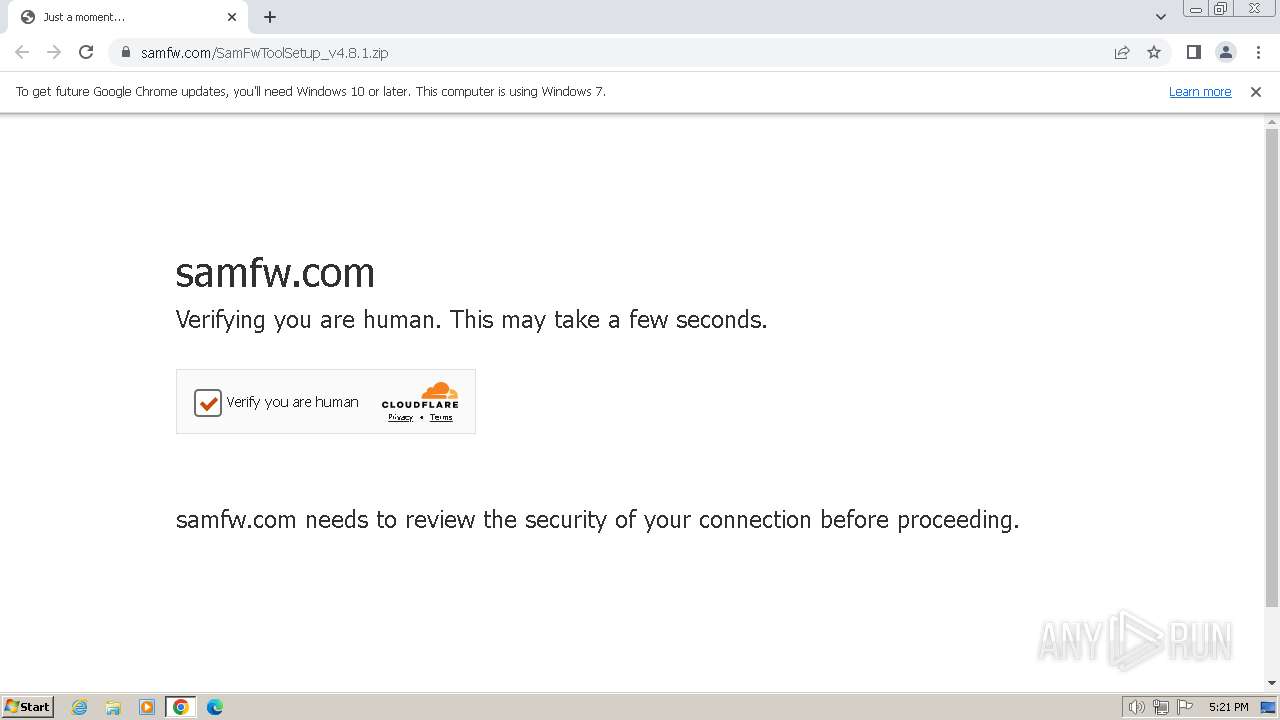
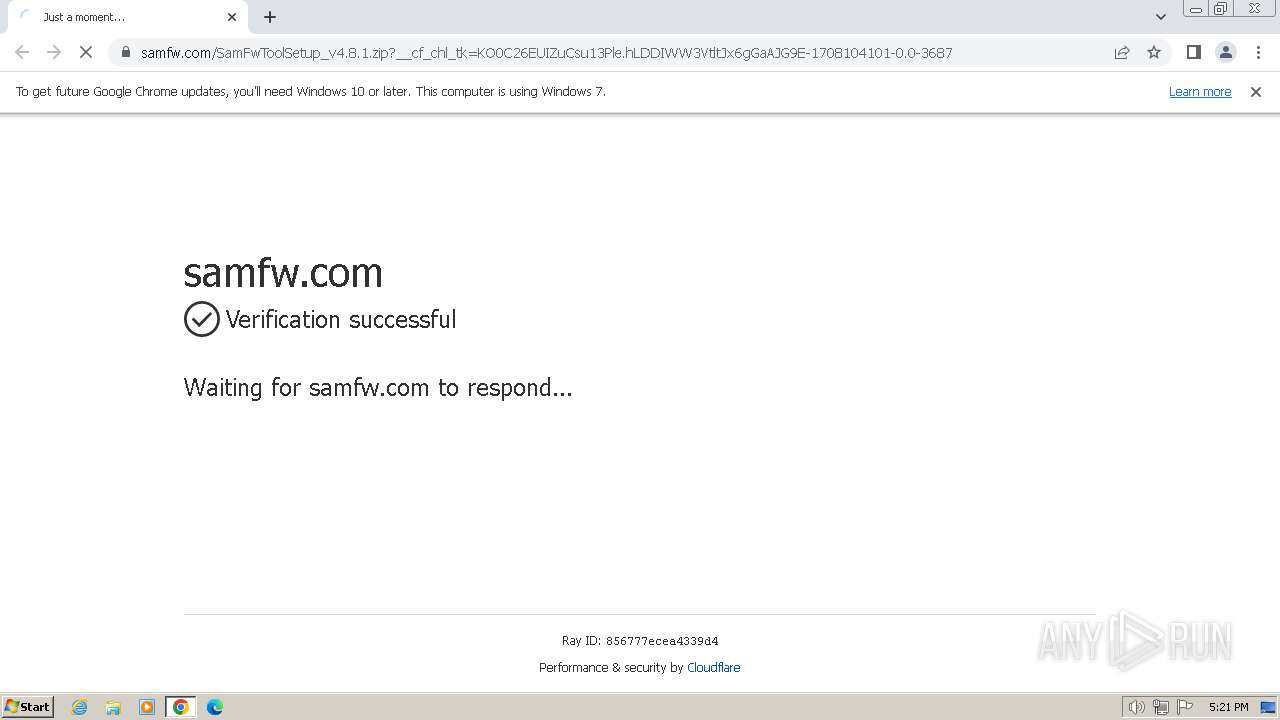
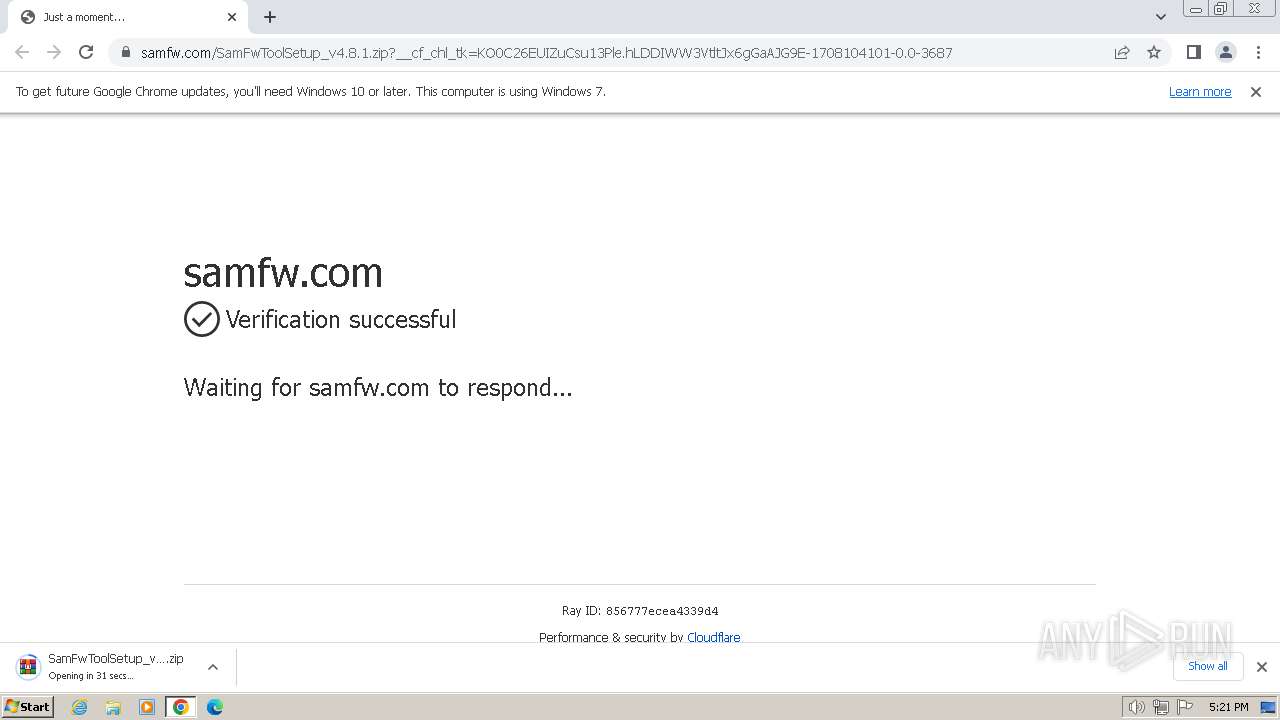
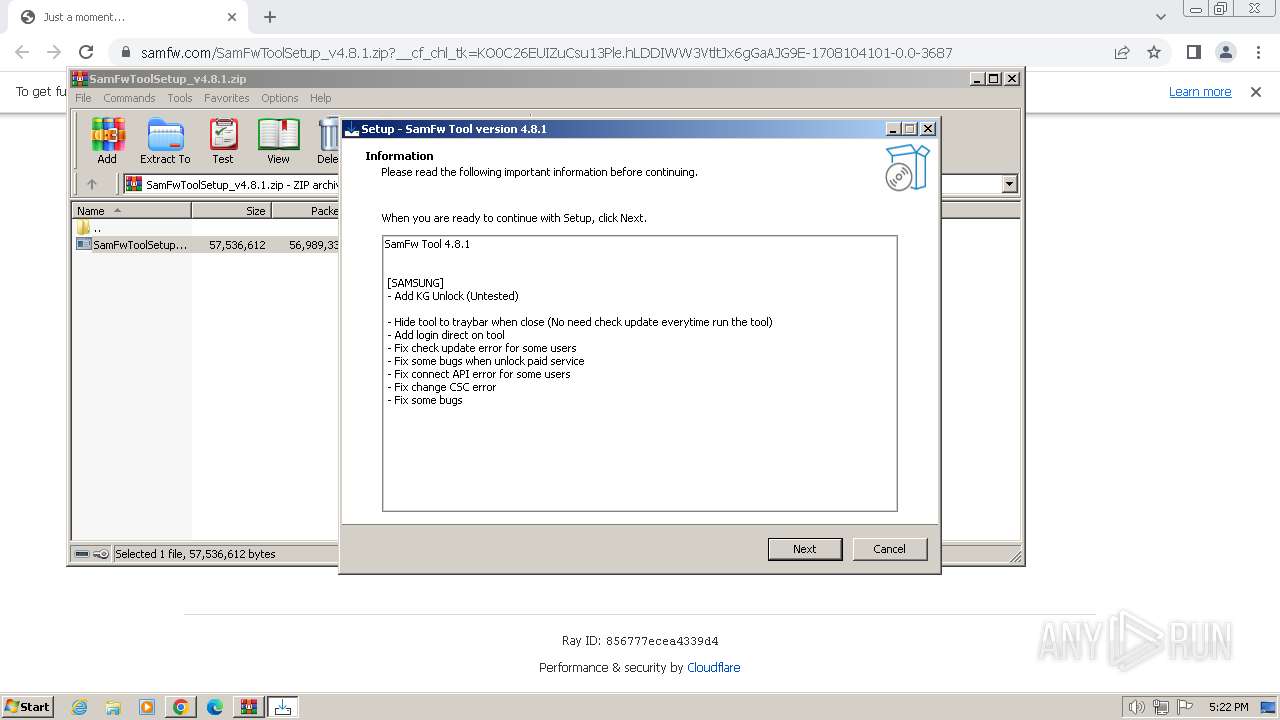
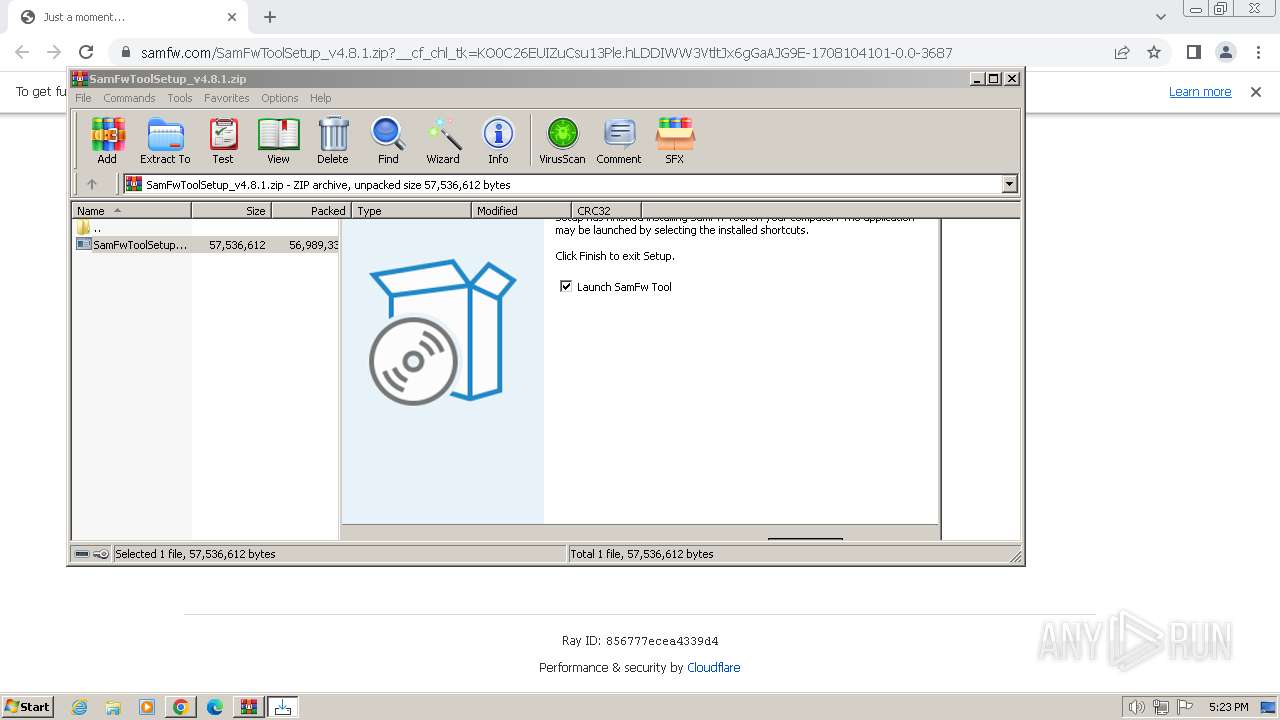
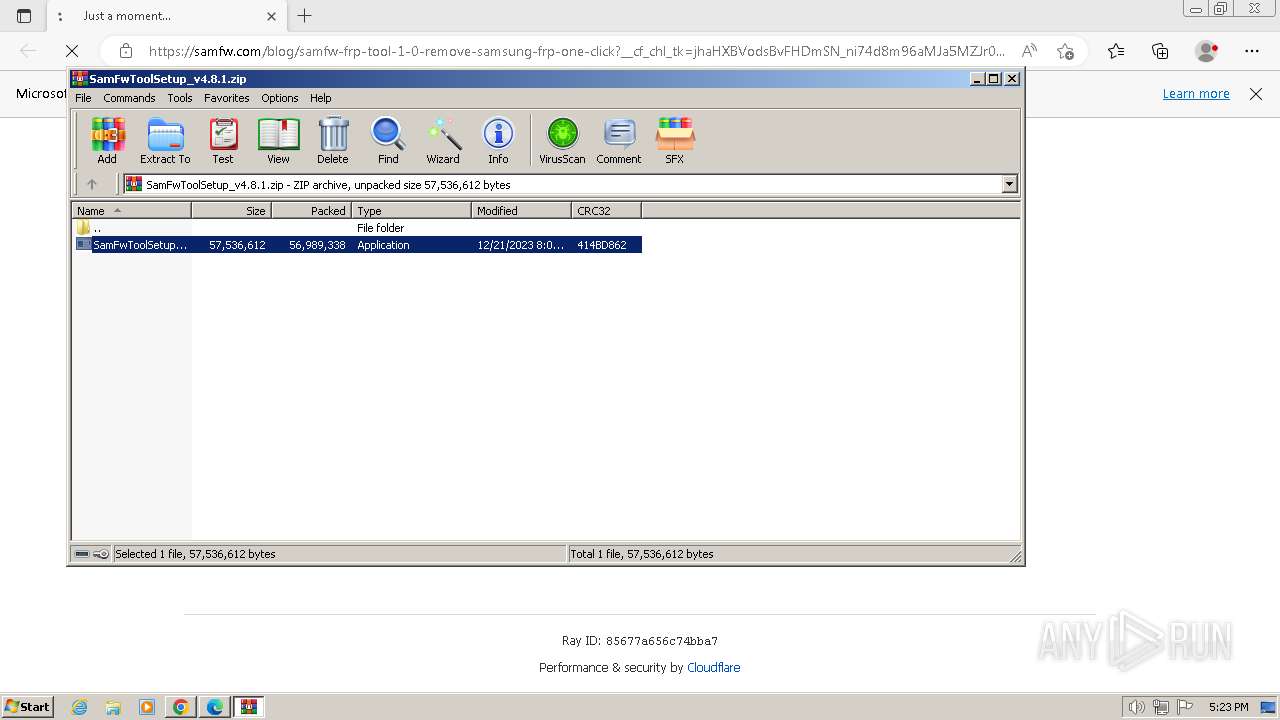
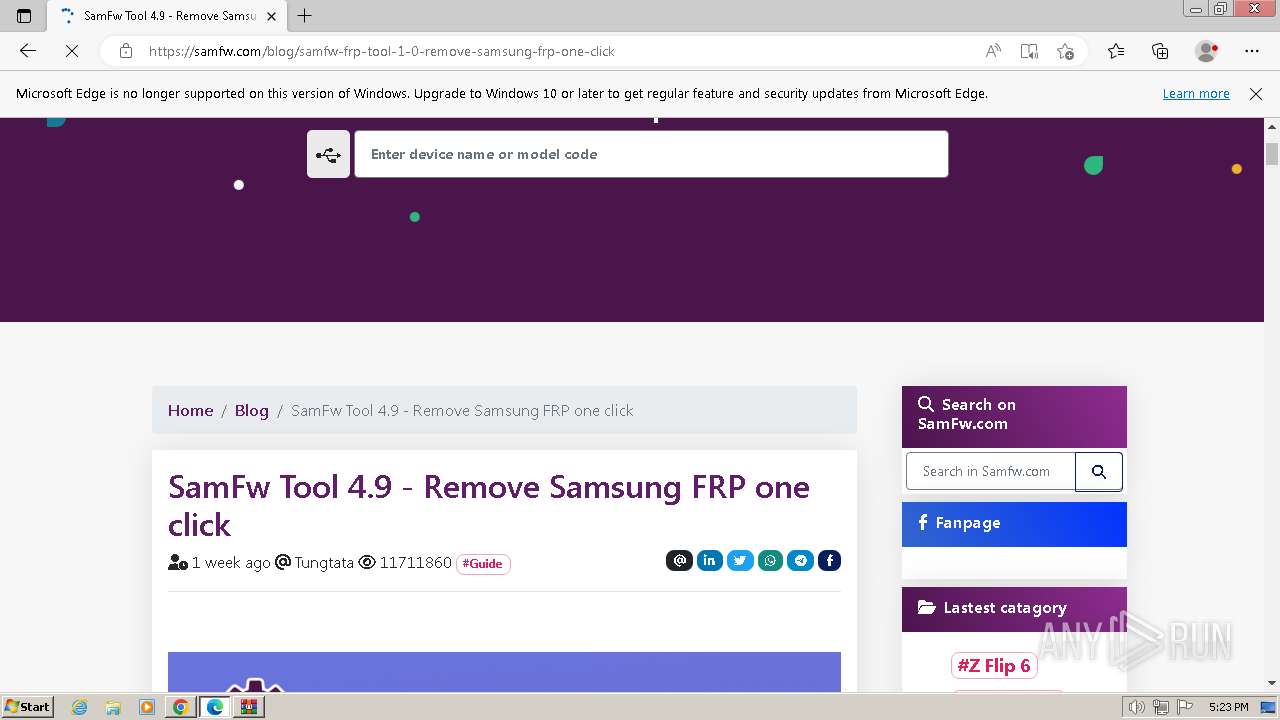
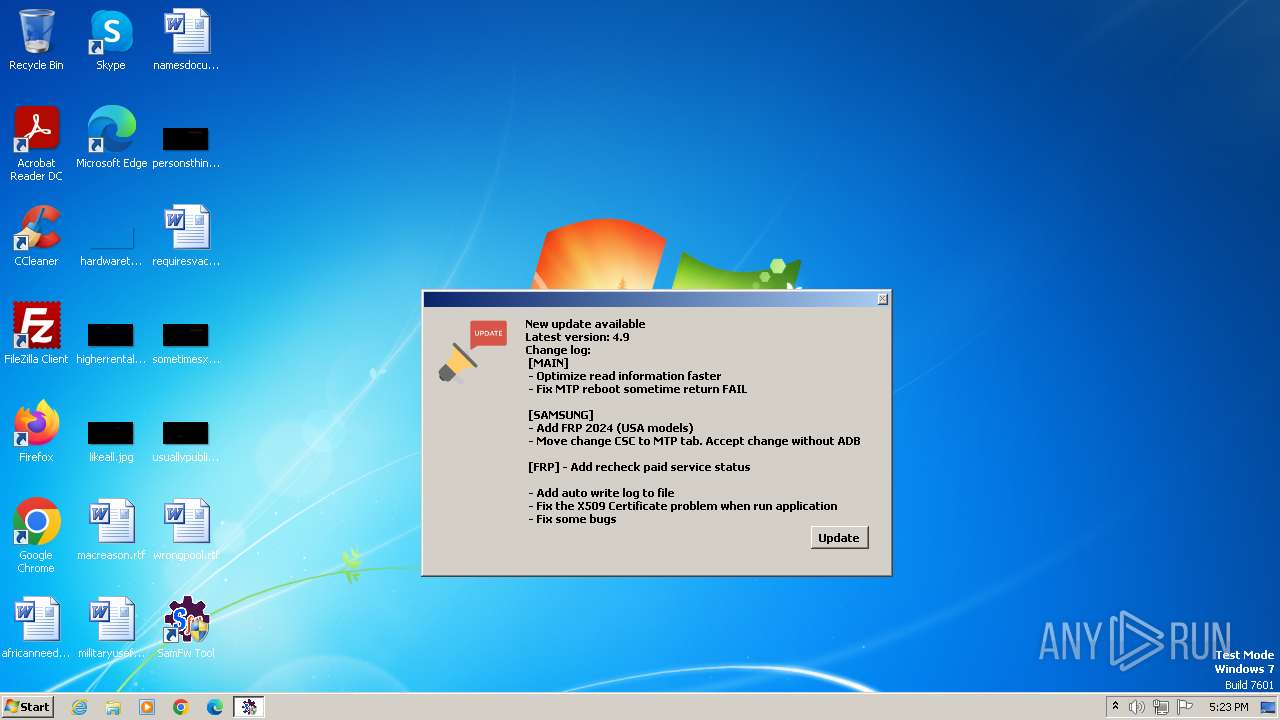
| URL: | https://samfw.com/SamFwToolSetup_v4.8.1.zip |
| Full analysis: | https://app.any.run/tasks/bc65a75d-4c43-4f95-9cf1-f4caef6bd23b |
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2024, 17:21:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D8400E37A15A8DC53A56B2ED5A4050C6 |
| SHA1: | B0F529F5DF4AAA84523993E5D86D960AED32C134 |
| SHA256: | 7A03CC35DBBBD7EE62E157B32BDF286BAA6EE35FBC40674045C67B008DB8B4BF |
| SSDEEP: | 3:N8JtyKG1zpGRLaYVn:2LE1zpGY4n |
MALICIOUS
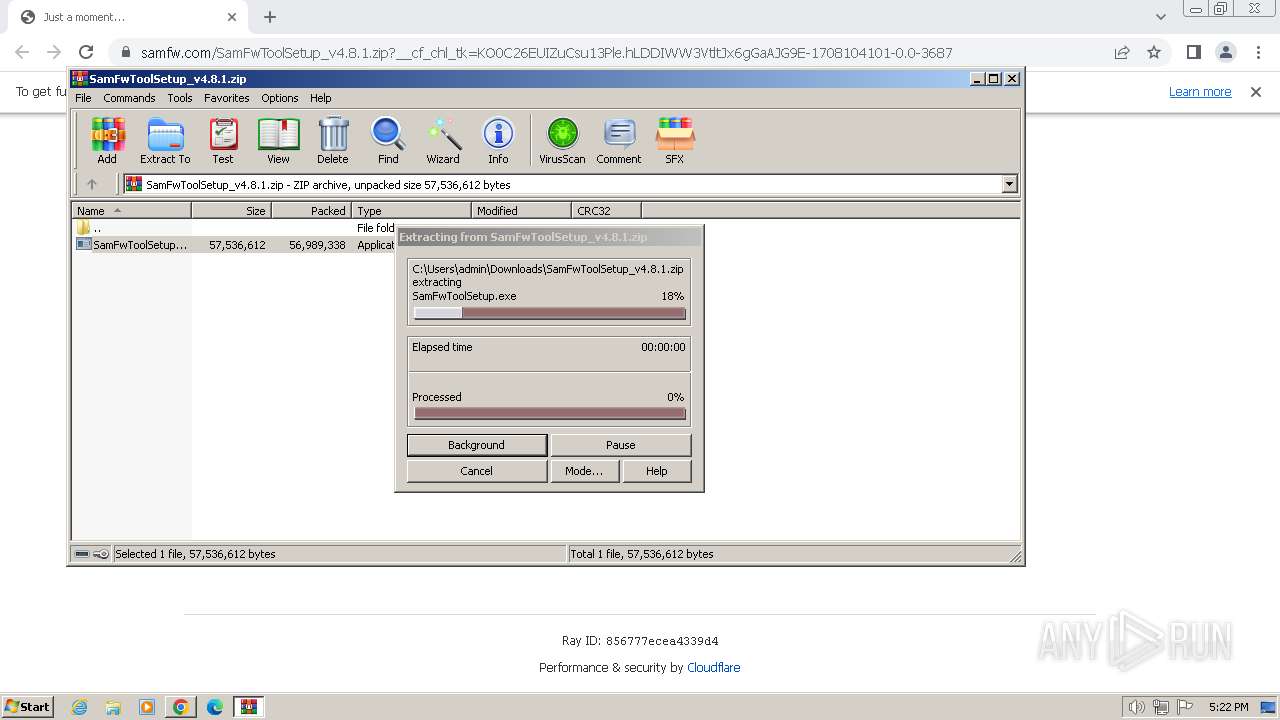
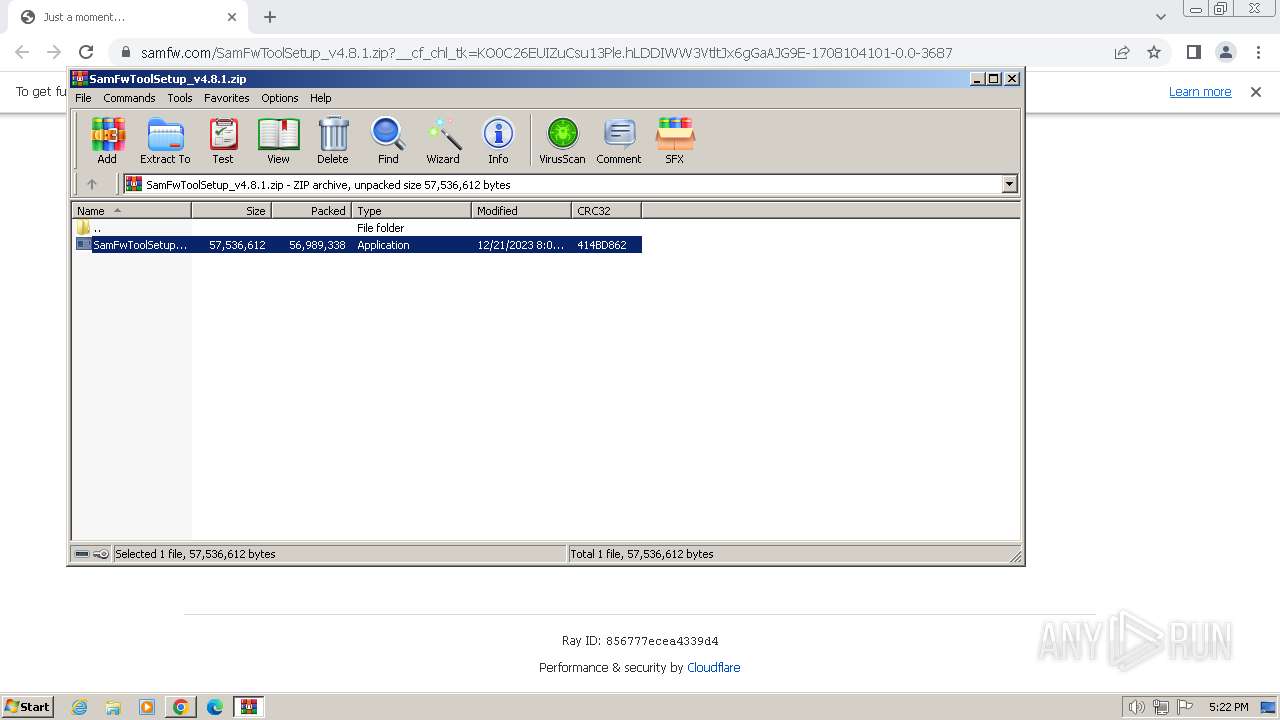
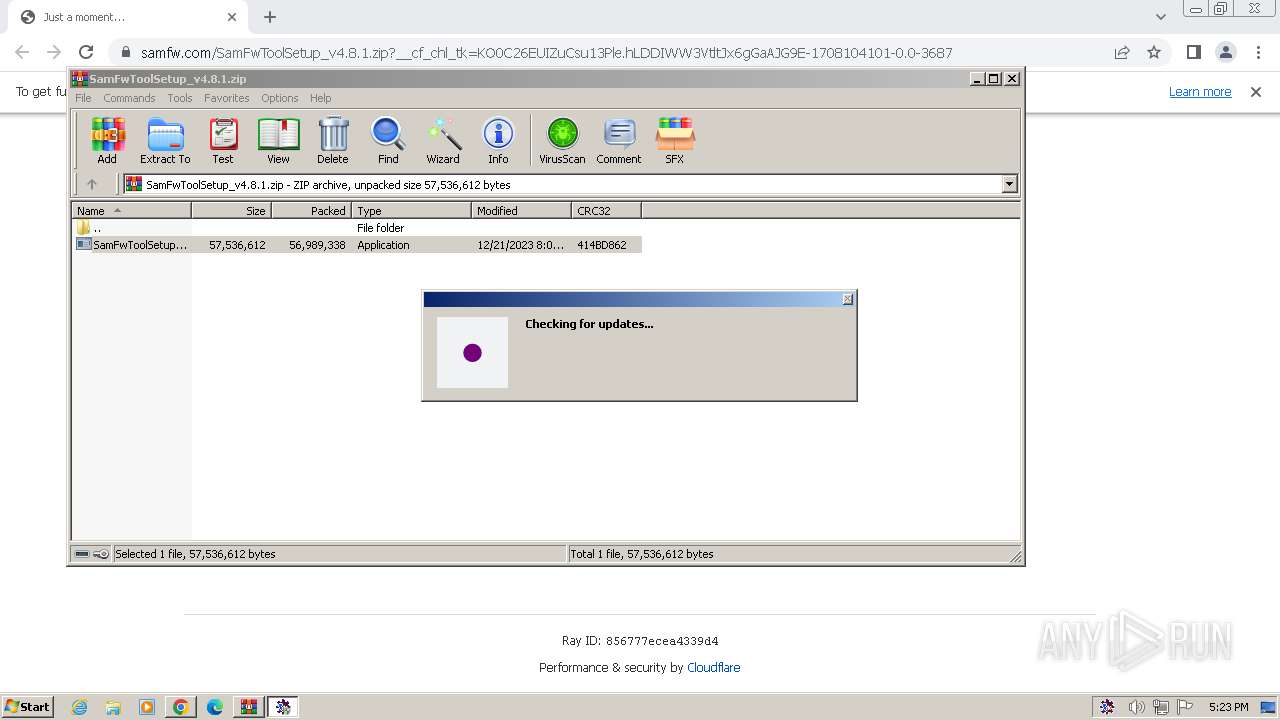
Drops the executable file immediately after the start
- SamFwToolSetup.exe (PID: 1628)
- SamFwToolSetup.exe (PID: 2828)
- SamFwToolSetup.tmp (PID: 1392)
- 7za.exe (PID: 3440)
Detects Cygwin installation
- 7za.exe (PID: 3440)
SUSPICIOUS
Reads security settings of Internet Explorer
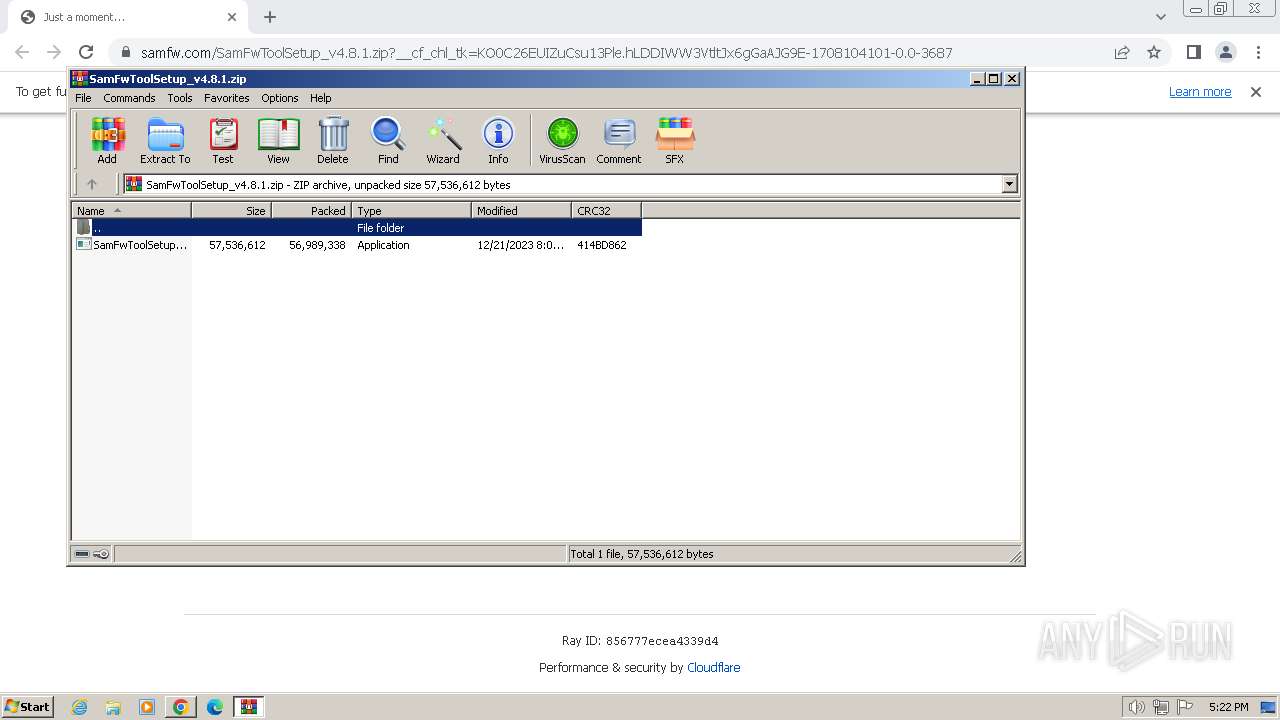
- WinRAR.exe (PID: 2376)
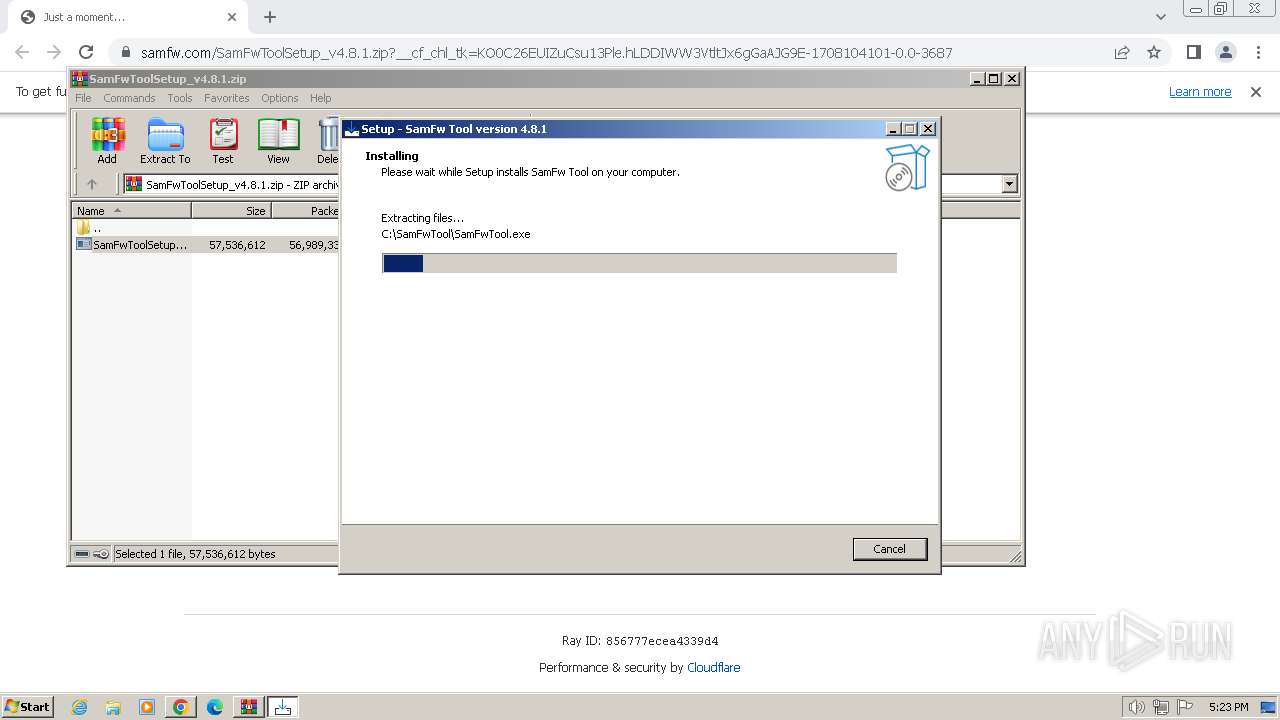
Executable content was dropped or overwritten
- SamFwToolSetup.exe (PID: 1628)
- SamFwToolSetup.exe (PID: 2828)
- SamFwToolSetup.tmp (PID: 1392)
- 7za.exe (PID: 3440)
Reads the Windows owner or organization settings
- SamFwToolSetup.tmp (PID: 1392)
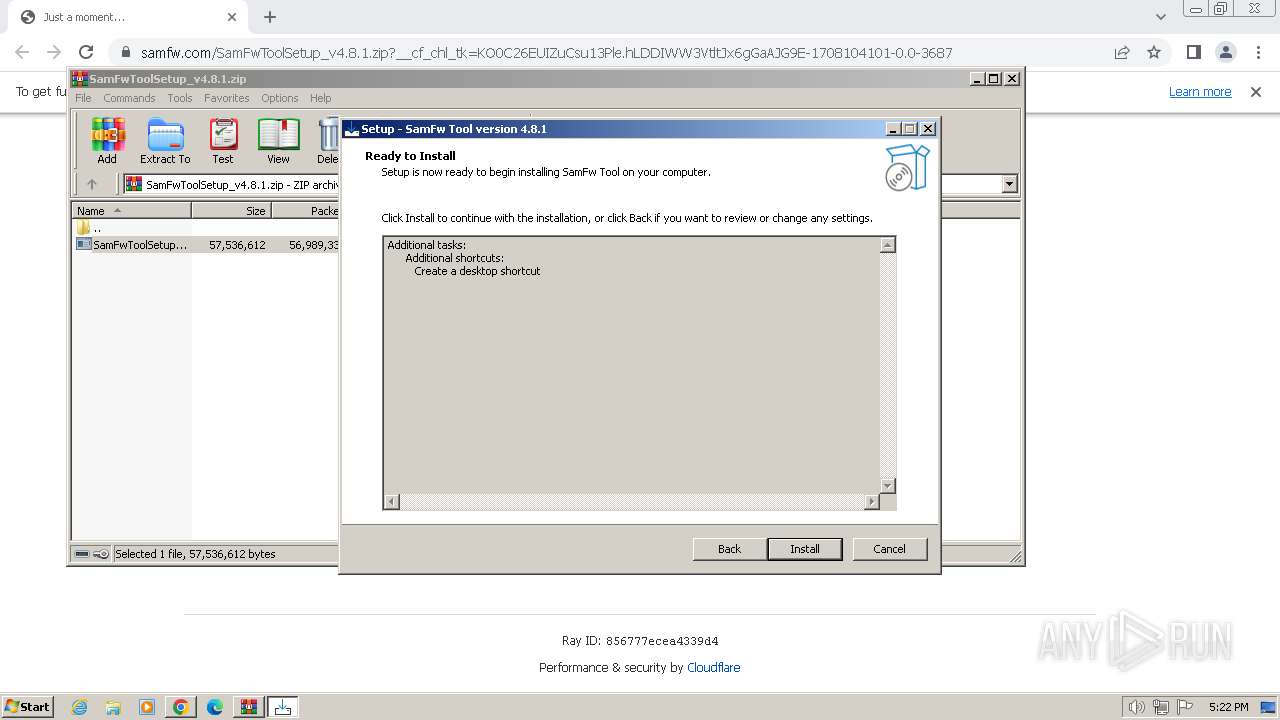
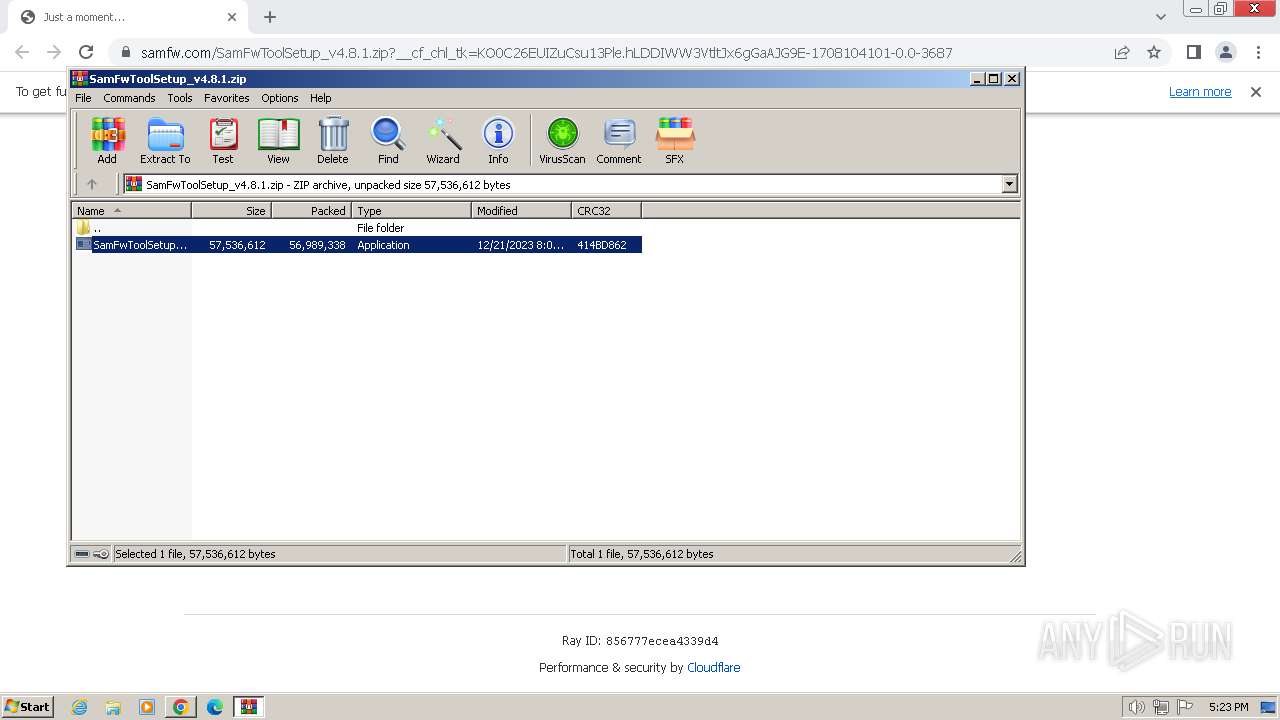
Drops 7-zip archiver for unpacking
- SamFwToolSetup.tmp (PID: 1392)
- 7za.exe (PID: 3440)
The process creates files with name similar to system file names
- 7za.exe (PID: 3440)
Process drops legitimate windows executable
- 7za.exe (PID: 3440)
Drops a system driver (possible attempt to evade defenses)
- 7za.exe (PID: 3440)
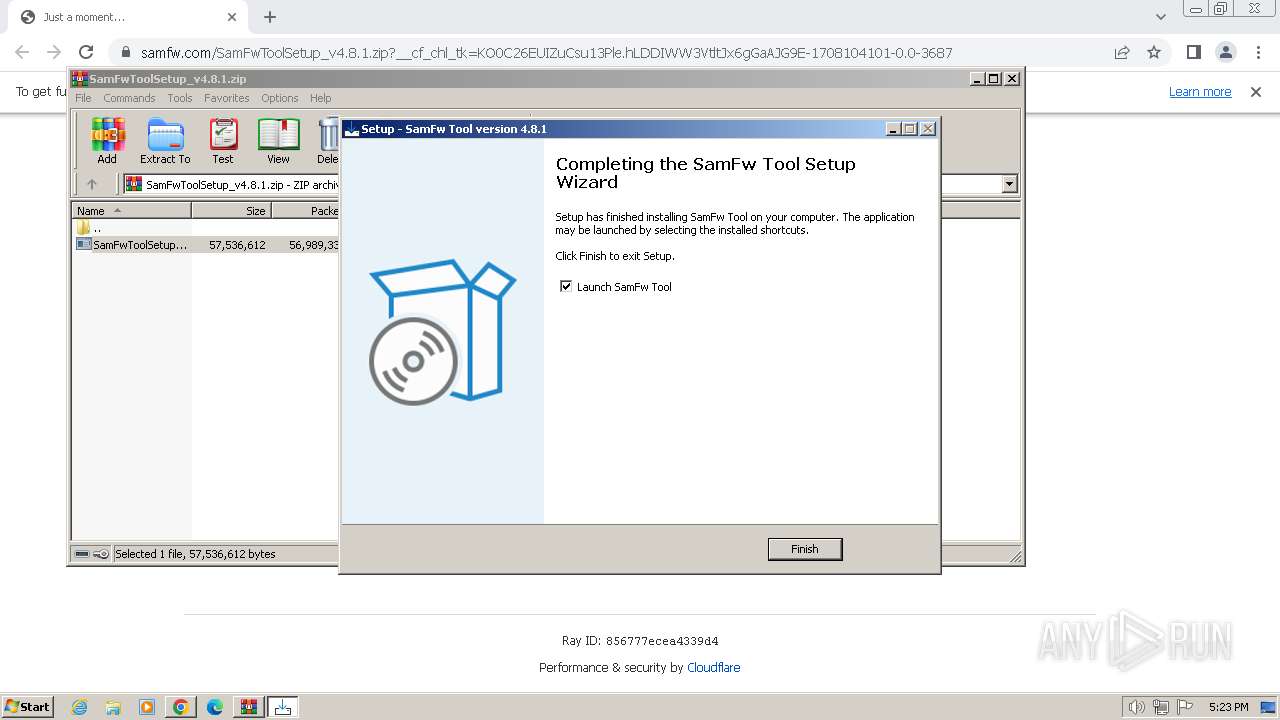
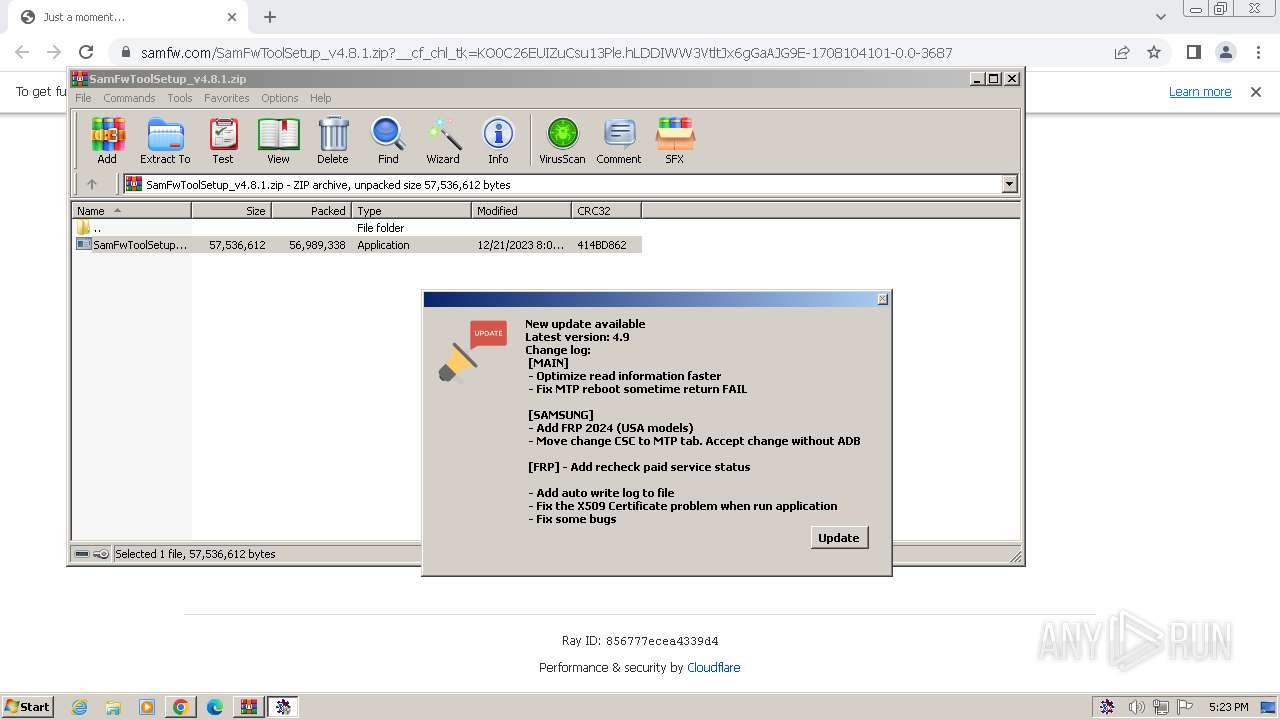
Reads the Internet Settings
- SamFwTool.exe (PID: 3052)
- SamFwTool.exe (PID: 3084)
Reads settings of System Certificates
- SamFwTool.exe (PID: 3084)
- SamFwTool.exe (PID: 3052)
Adds/modifies Windows certificates
- SamFwTool.exe (PID: 3052)
INFO
Application launched itself
- chrome.exe (PID: 3700)
- msedge.exe (PID: 3268)
- msedge.exe (PID: 2596)
Checks supported languages
- SamFwToolSetup.exe (PID: 1628)
- SamFwToolSetup.tmp (PID: 3232)
- SamFwToolSetup.exe (PID: 2828)
- SamFwToolSetup.tmp (PID: 1392)
- 7za.exe (PID: 3440)
- SamFwTool.exe (PID: 3052)
- SamFwTool.exe (PID: 3084)
Create files in a temporary directory
- SamFwToolSetup.exe (PID: 1628)
- SamFwToolSetup.exe (PID: 2828)
- SamFwTool.exe (PID: 3052)
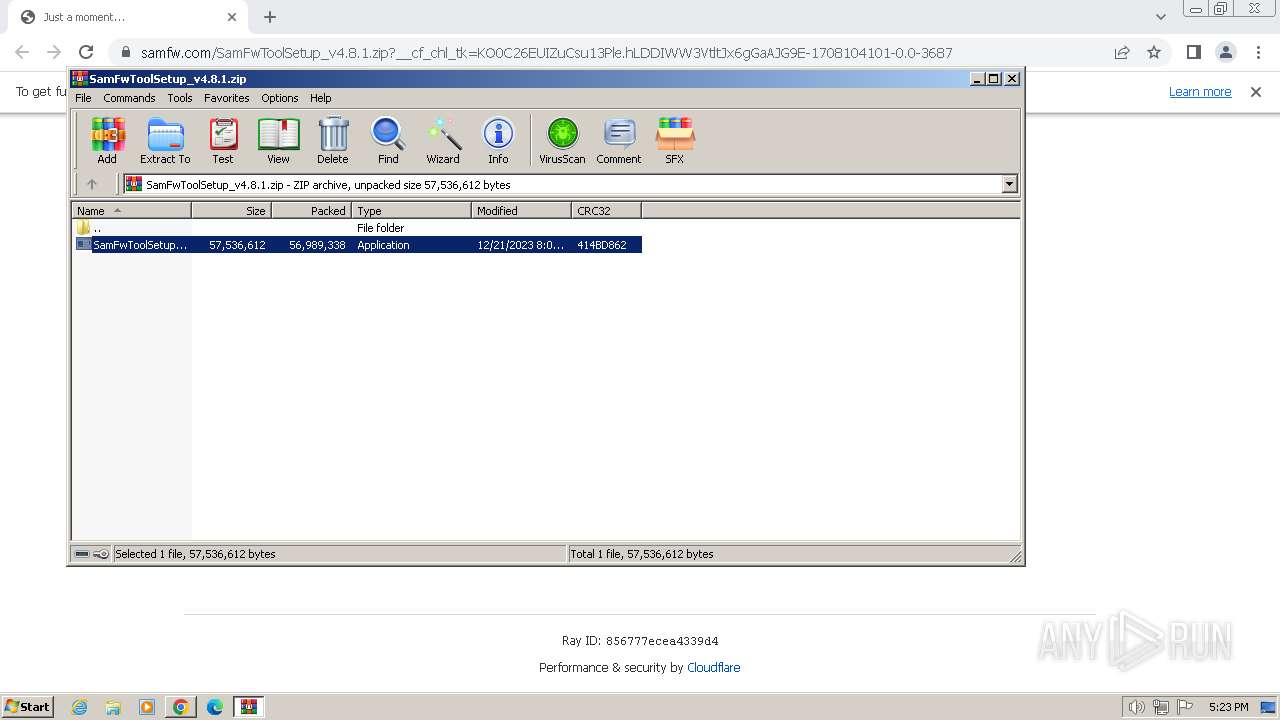
The process uses the downloaded file
- chrome.exe (PID: 3556)
- WinRAR.exe (PID: 2376)
Reads the computer name
- SamFwToolSetup.tmp (PID: 3232)
- SamFwToolSetup.tmp (PID: 1392)
- 7za.exe (PID: 3440)
- SamFwTool.exe (PID: 3052)
- SamFwTool.exe (PID: 3084)
Creates files in the program directory
- SamFwToolSetup.tmp (PID: 1392)
- SamFwTool.exe (PID: 3052)
Creates a software uninstall entry
- SamFwToolSetup.tmp (PID: 1392)
Reads the machine GUID from the registry
- SamFwTool.exe (PID: 3052)
- SamFwTool.exe (PID: 3084)
Reads Environment values
- SamFwTool.exe (PID: 3052)
- SamFwTool.exe (PID: 3084)
Executable content was dropped or overwritten
- chrome.exe (PID: 3520)
Drops the executable file immediately after the start
- chrome.exe (PID: 3520)
Manual execution by a user
- SamFwTool.exe (PID: 3084)
- SamFwTool.exe (PID: 2052)
- msedge.exe (PID: 2596)
Reads the software policy settings
- SamFwTool.exe (PID: 3084)
- SamFwTool.exe (PID: 3052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
98
Monitored processes
53
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=948 --field-trial-handle=1148,i,16821348934265601683,5471089166173920409,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1644 --field-trial-handle=1380,i,3128613052071584644,16920848958285896585,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=1416 --field-trial-handle=1380,i,3128613052071584644,16920848958285896585,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1324 --field-trial-handle=1380,i,3128613052071584644,16920848958285896585,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --mojo-platform-channel-handle=3636 --field-trial-handle=1380,i,3128613052071584644,16920848958285896585,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1476 --field-trial-handle=1380,i,3128613052071584644,16920848958285896585,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1392 | "C:\Users\admin\AppData\Local\Temp\is-34SJ8.tmp\SamFwToolSetup.tmp" /SL5="$2100E6,56697704,832512,C:\Users\admin\AppData\Local\Temp\Rar$EXa2376.13298\SamFwToolSetup.exe" /SPAWNWND=$150154 /NOTIFYWND=$1101B6 | C:\Users\admin\AppData\Local\Temp\is-34SJ8.tmp\SamFwToolSetup.tmp | SamFwToolSetup.exe | ||||||||||||
User: admin Company: SamFw.com Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1628 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2376.13298\SamFwToolSetup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2376.13298\SamFwToolSetup.exe | WinRAR.exe | ||||||||||||
User: admin Company: SamFw.com Integrity Level: MEDIUM Description: SamFw Tool Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=2972 --field-trial-handle=1148,i,16821348934265601683,5471089166173920409,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2016 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2168 --field-trial-handle=1380,i,3128613052071584644,16920848958285896585,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
28 278
Read events
28 005
Write events
247
Delete events
26
Modification events
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
50
Suspicious files
90
Text files
128
Unknown types
84
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f3a7.TMP | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF17f56c.TMP | text | |
MD5:C5B082BC8EA6A9BD1DC6782C00A79605 | SHA256:6168A9E585264DE05DEE1B67427B1BC277F1B83B9297184EFACC5D3BB061ABDE | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF17f6a4.TMP | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\601e9407-2036-4d07-821b-6f5cad77cf3a.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF180441.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
89
DNS requests
105
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 6.16 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 9.98 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 10.0 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 10.1 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 14.1 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 79.2 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 35.8 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 165 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 363 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3700 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3464 | chrome.exe | 172.217.218.84:443 | accounts.google.com | GOOGLE | US | unknown |
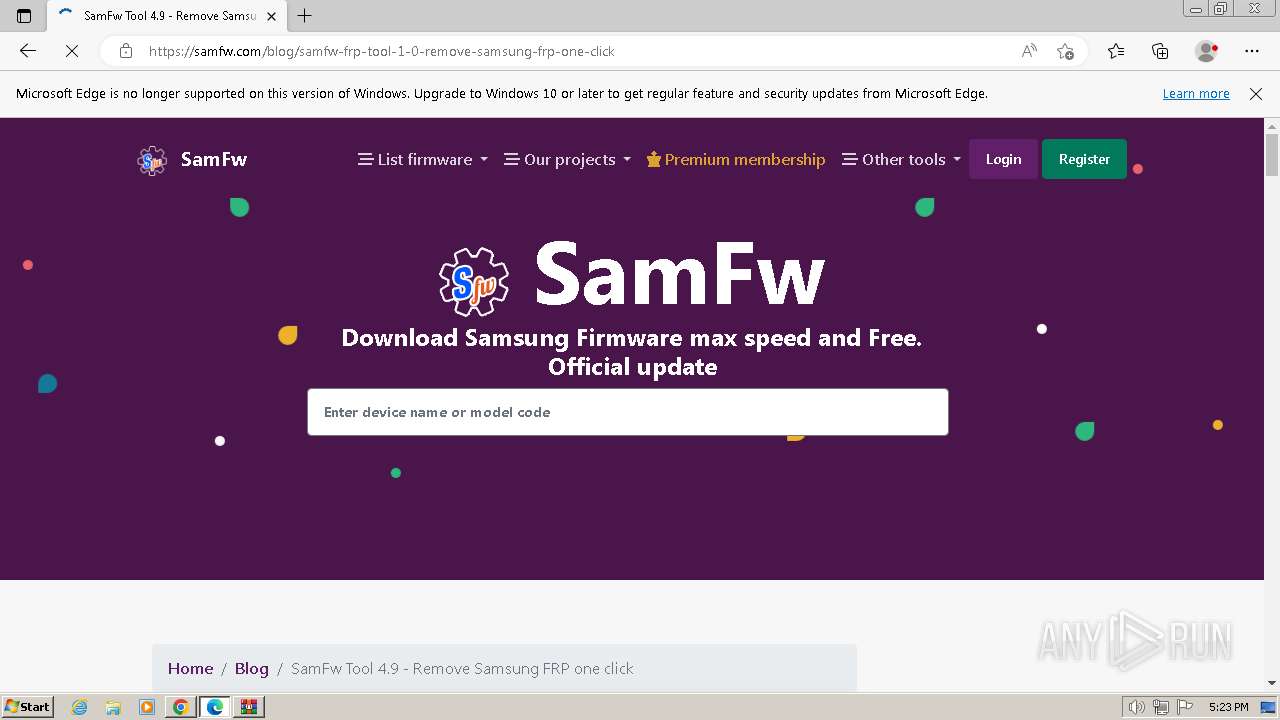
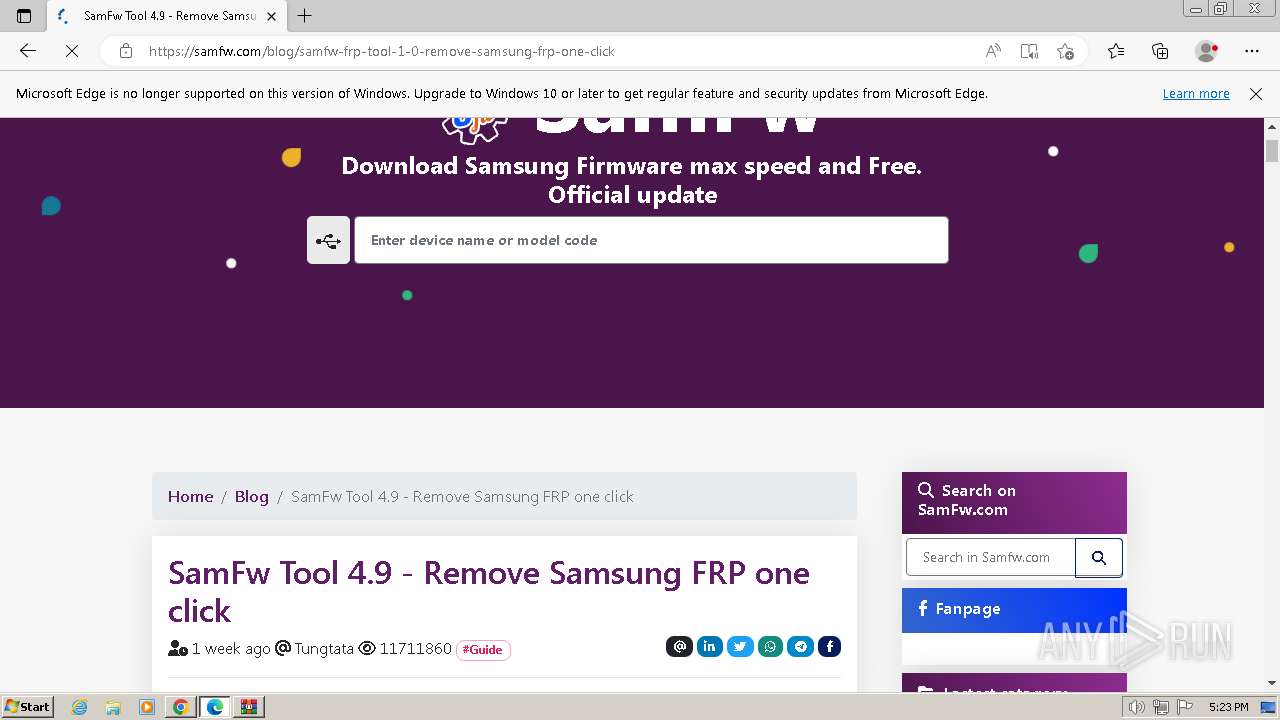
3464 | chrome.exe | 188.114.96.3:443 | samfw.com | CLOUDFLARENET | NL | unknown |
3464 | chrome.exe | 35.190.80.1:443 | a.nel.cloudflare.com | GOOGLE | US | unknown |
3464 | chrome.exe | 104.16.57.101:443 | static.cloudflareinsights.com | CLOUDFLARENET | — | unknown |
3464 | chrome.exe | 104.17.3.184:443 | challenges.cloudflare.com | CLOUDFLARENET | — | unknown |
3464 | chrome.exe | 104.17.2.184:443 | challenges.cloudflare.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
samfw.com |
| unknown |
a.nel.cloudflare.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
challenges.cloudflare.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
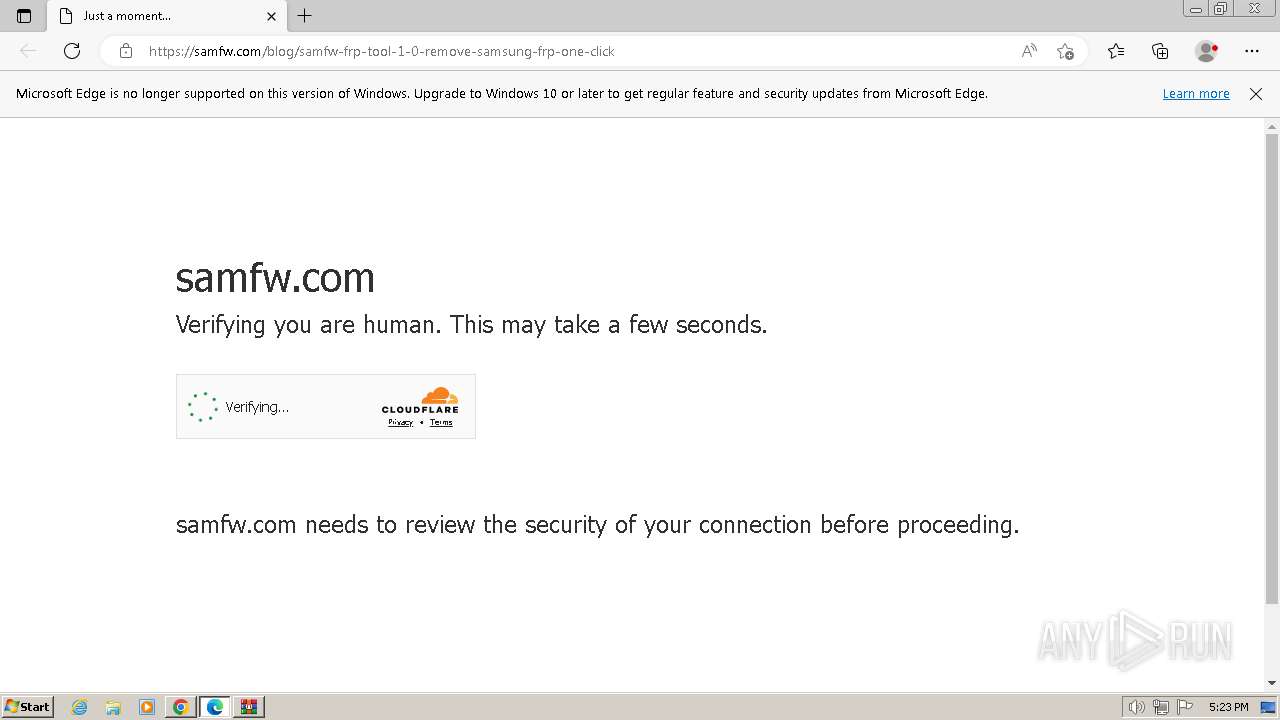
3464 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
3464 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
1340 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1340 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
1340 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |