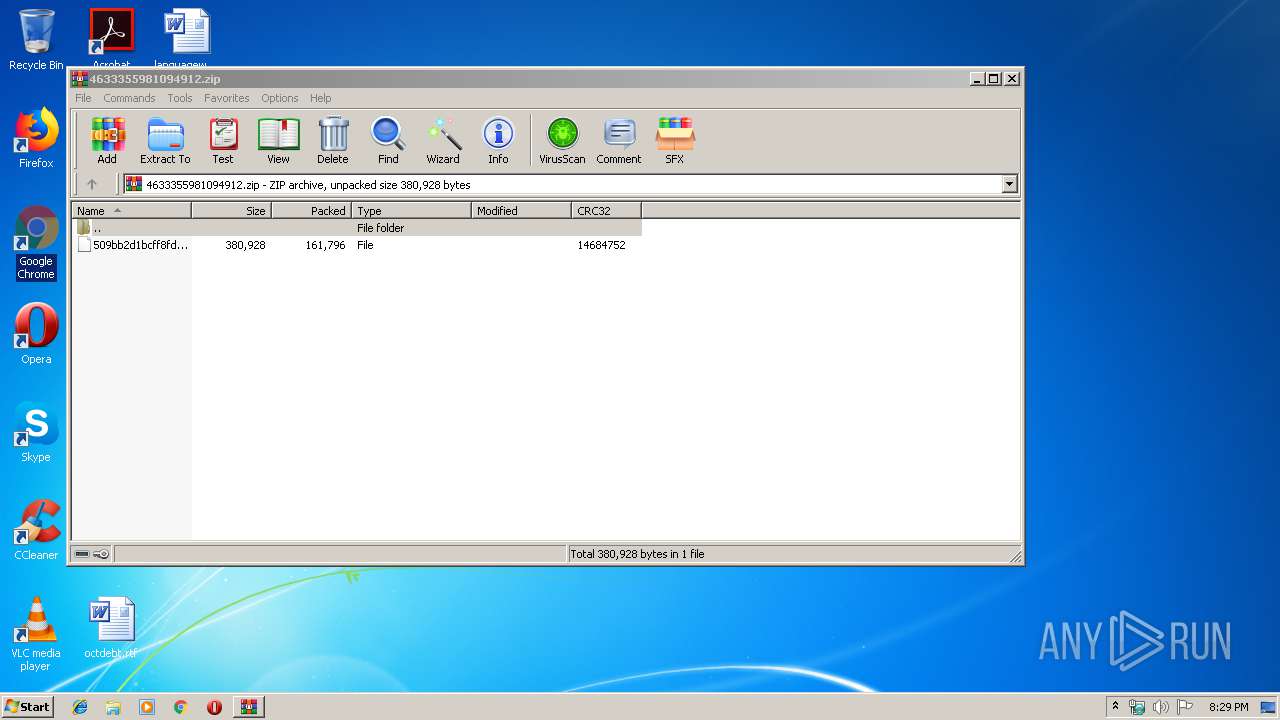
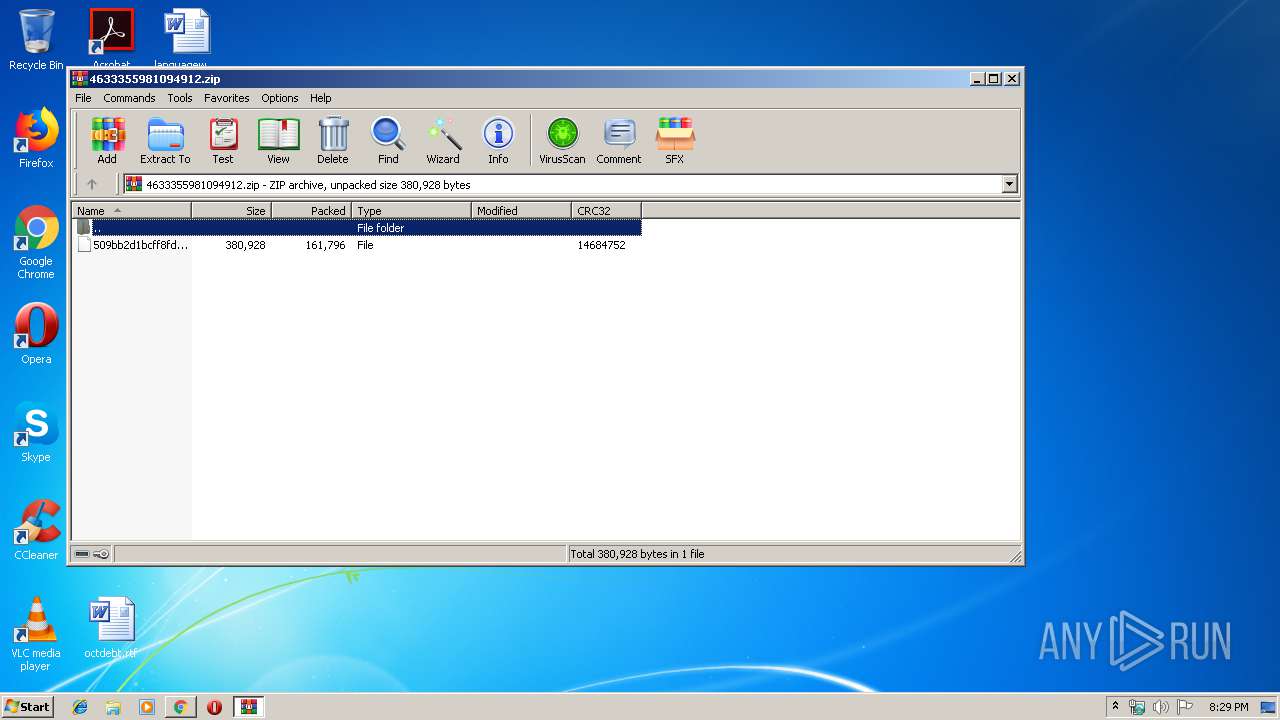
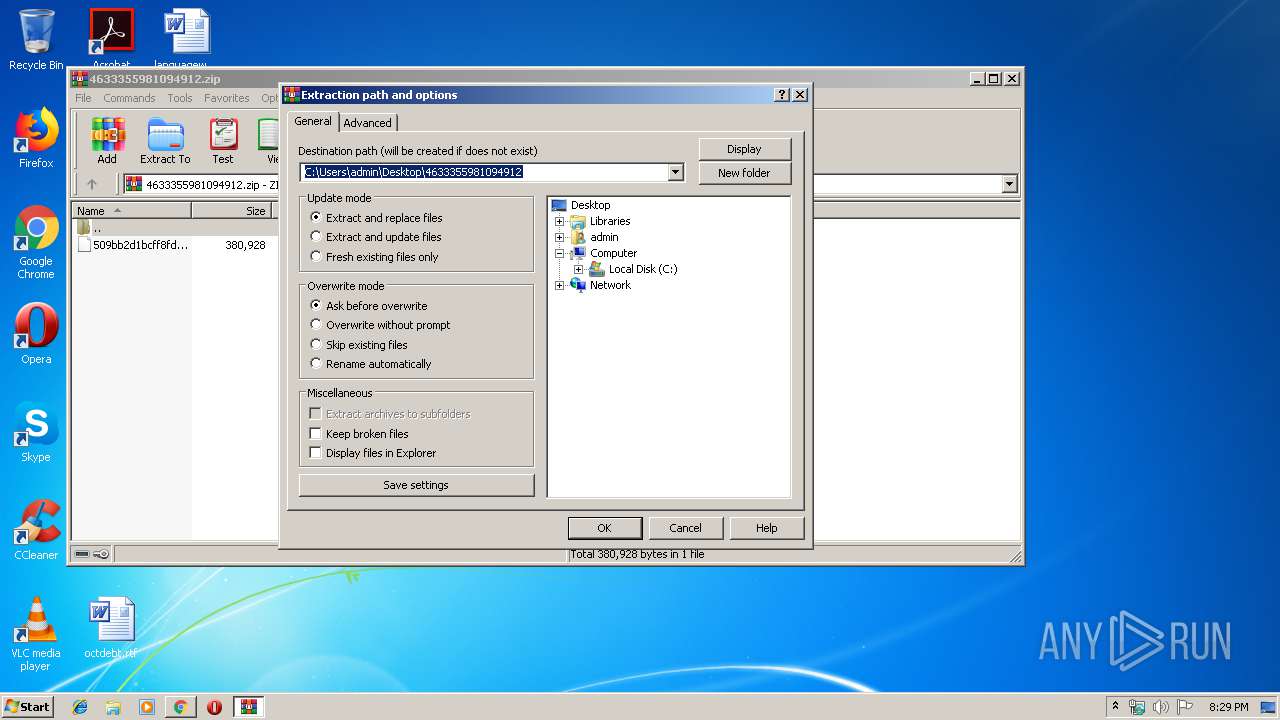
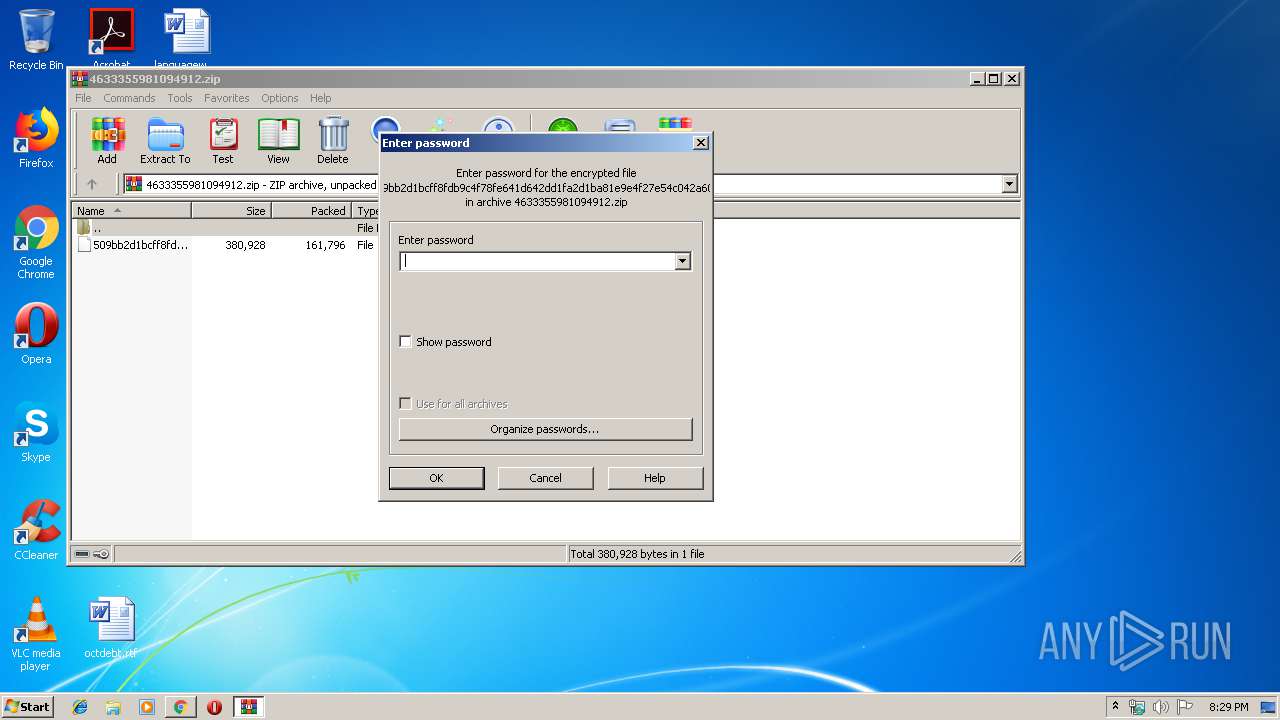
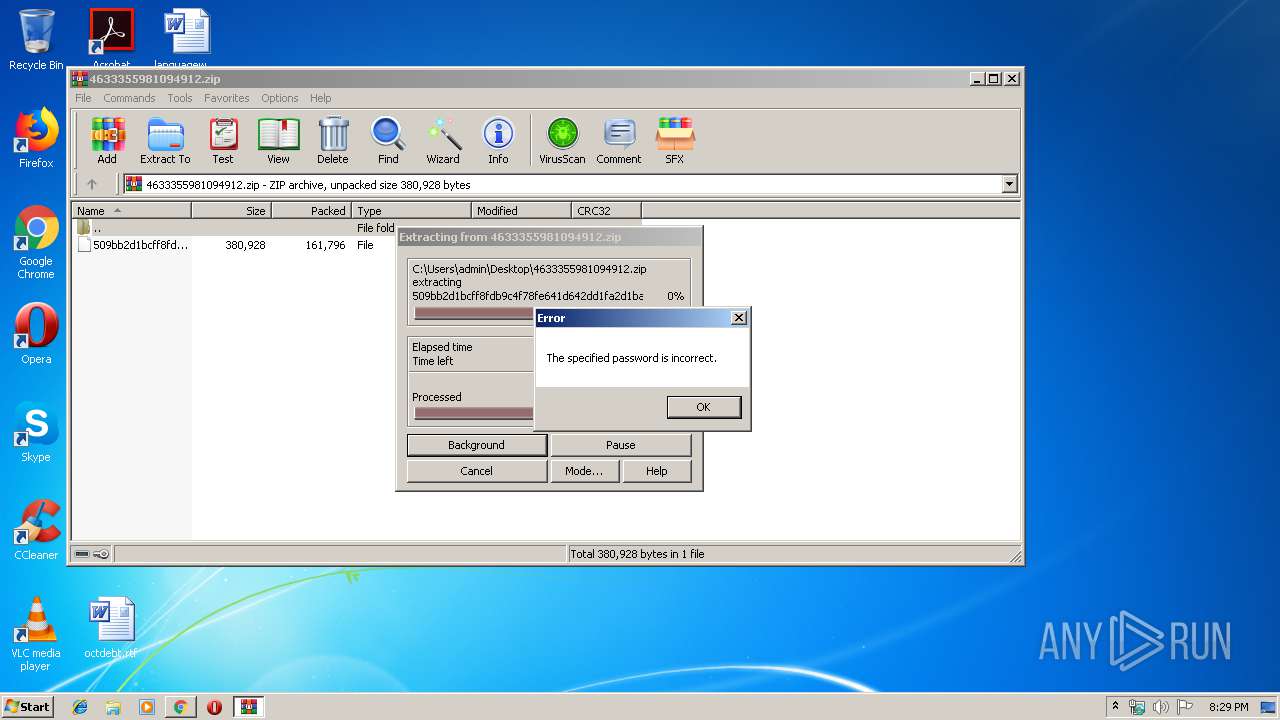
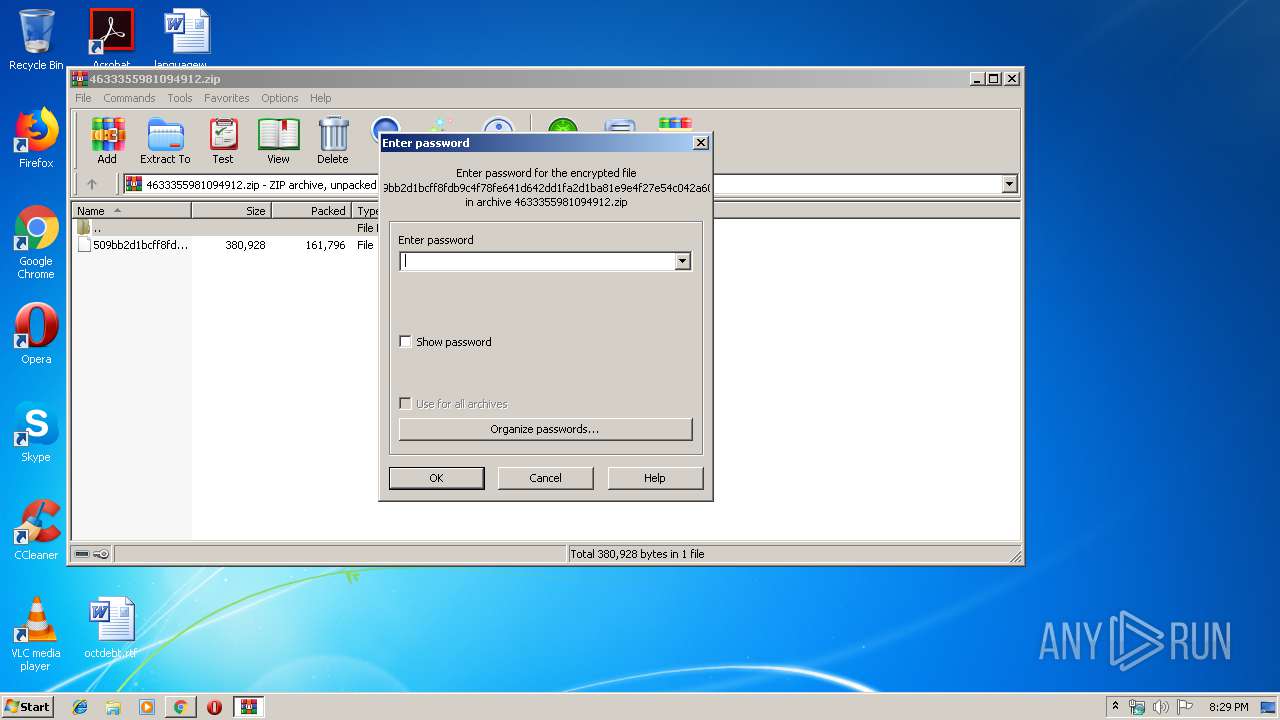
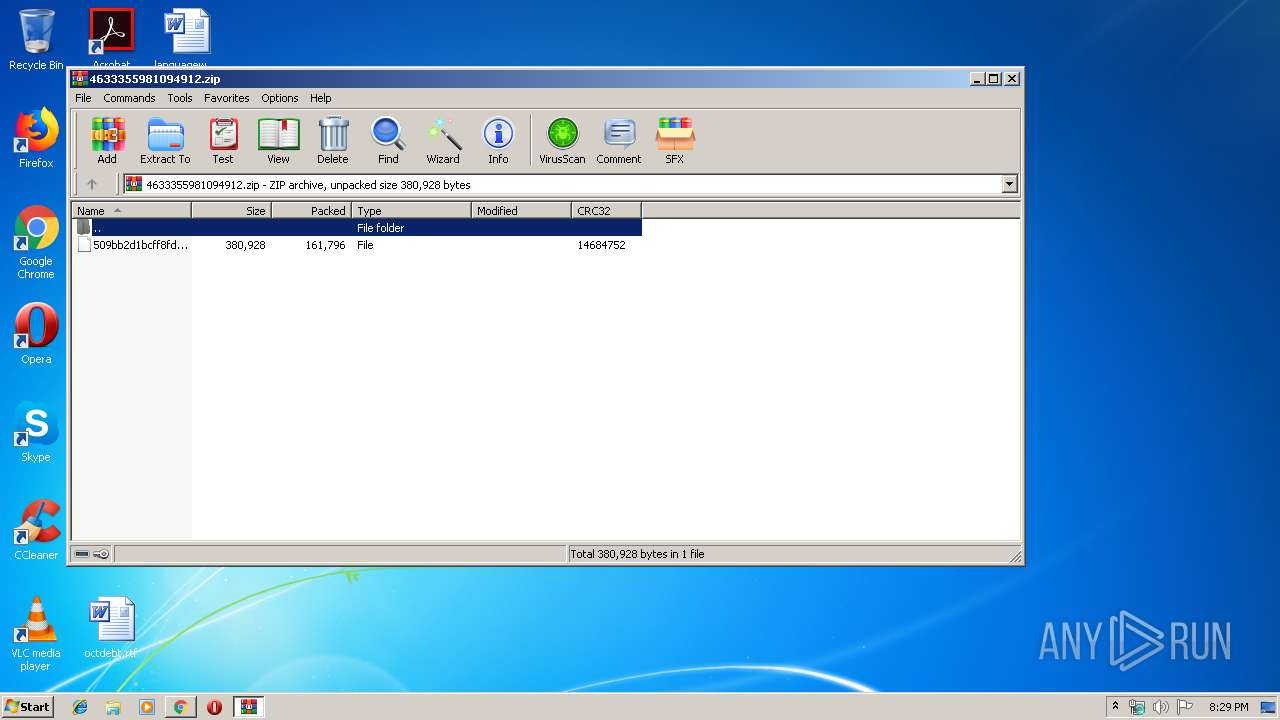
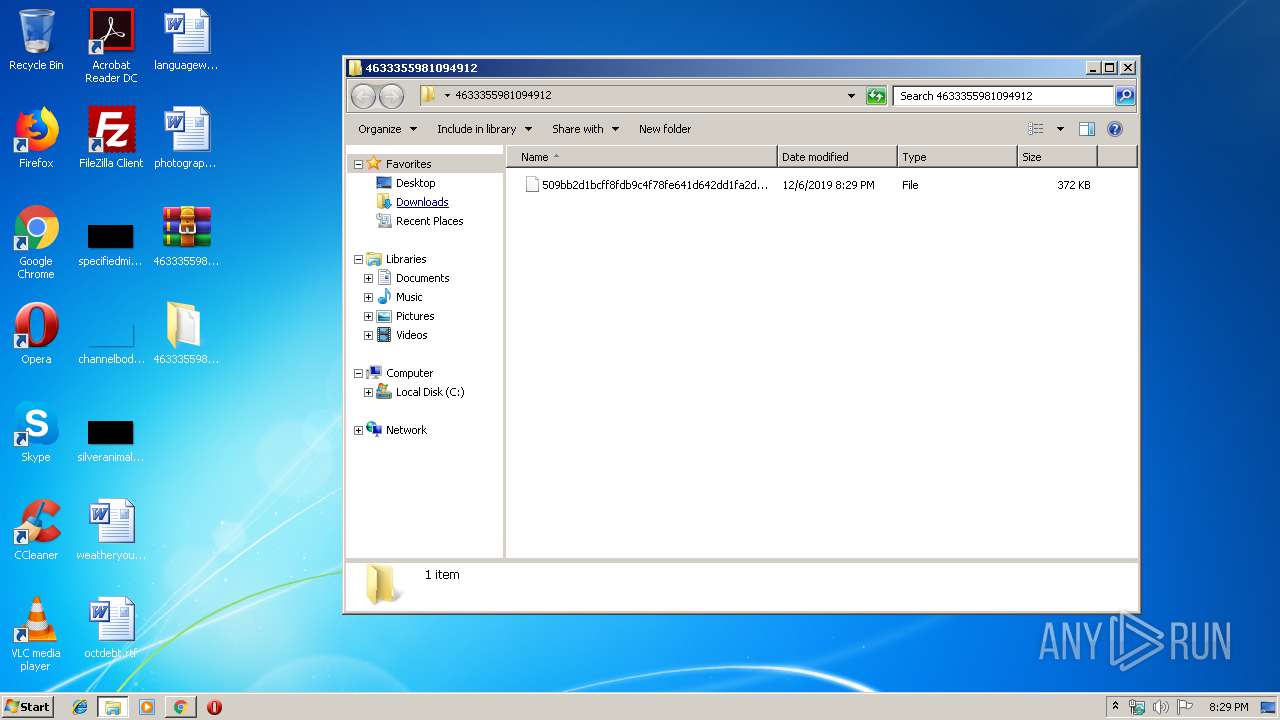
| File name: | 4633355981094912.zip |
| Full analysis: | https://app.any.run/tasks/da6e0409-1106-4659-81f6-5e0d6da120d5 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 20:28:35 |
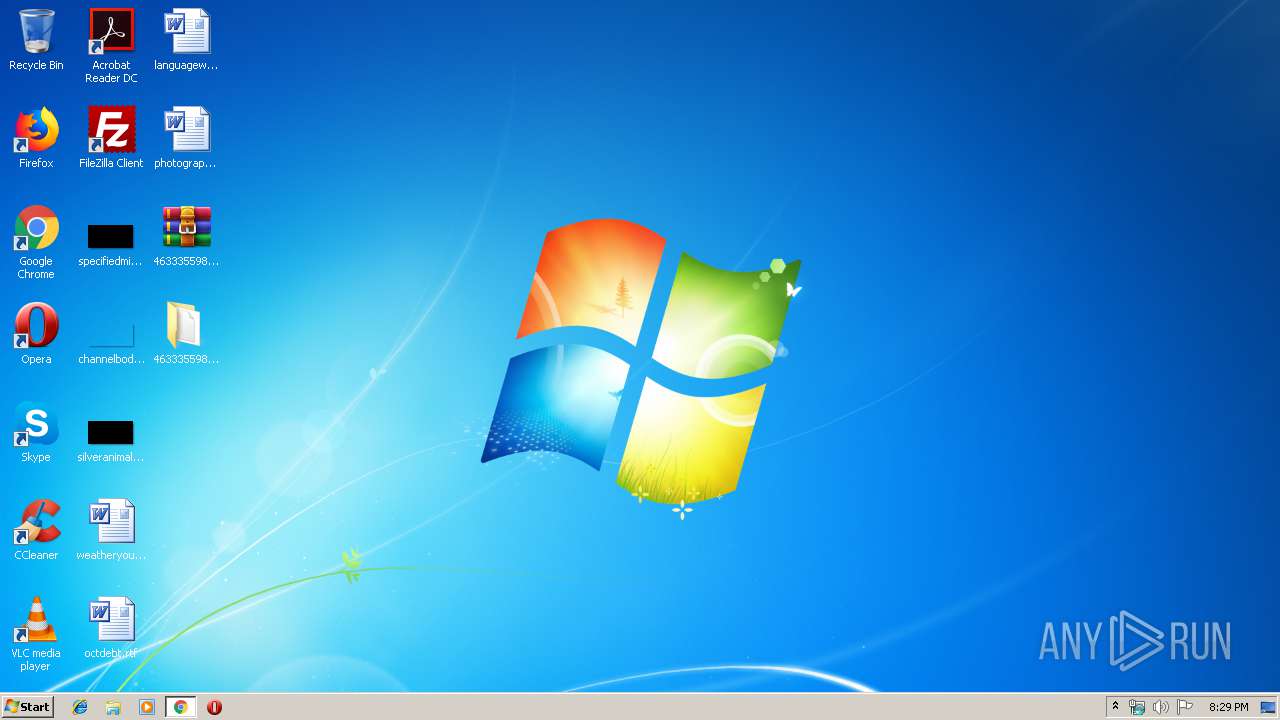
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 598A6C62548F528D4C77C7C9C89F9C8D |
| SHA1: | B715F9D84CCC89DE362188CAA5376F26434D7626 |
| SHA256: | 79FB1ADD0B7A12F916EF5E382C22E5C2D243509CB4707A946711A66968166EAE |
| SSDEEP: | 3072:gVaXacPZJuoDkAuR4/ovwTFdAOa663d/4E9NaceBC1qdP4hGUbO+W19kYX1d9rG:3jhzDAR4/CGfAB3v+0XkUbibvldhG |
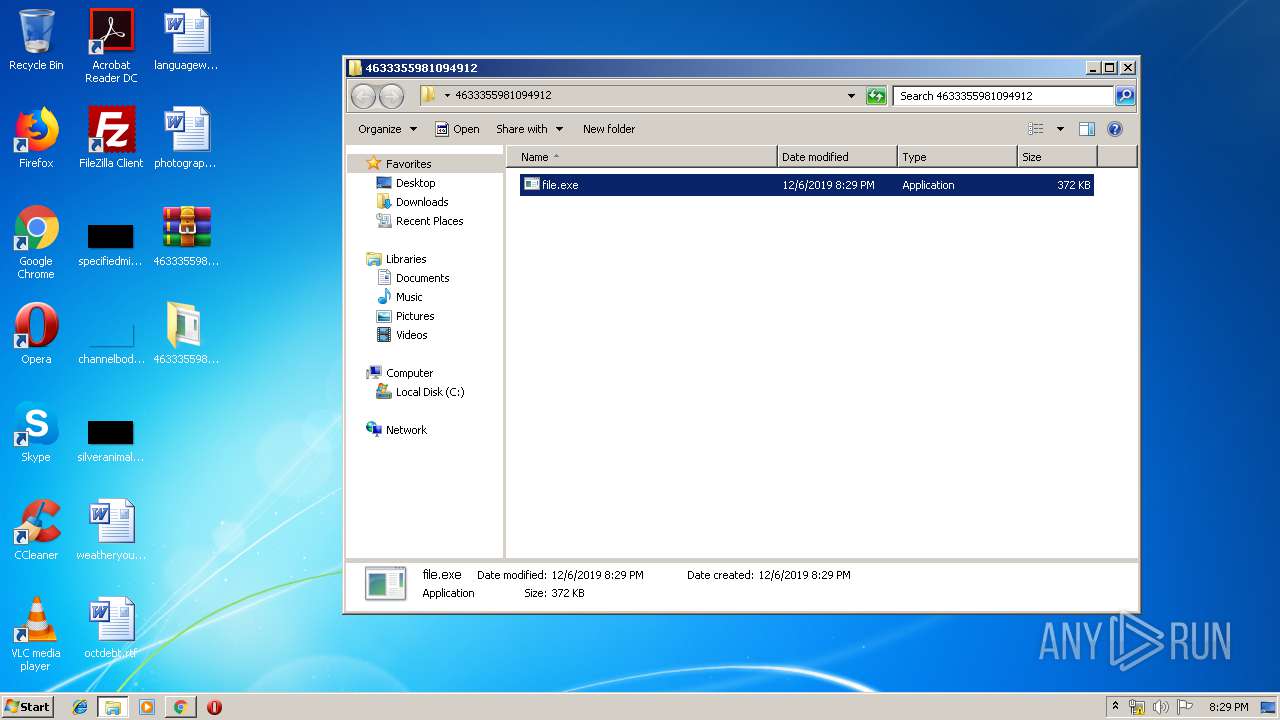
MALICIOUS
Application was dropped or rewritten from another process
- file.exe (PID: 3652)
- file.exe (PID: 2240)
- serialfunc.exe (PID: 3780)
- serialfunc.exe (PID: 836)
Emotet process was detected
- file.exe (PID: 2240)
EMOTET was detected
- serialfunc.exe (PID: 836)
Changes the autorun value in the registry
- serialfunc.exe (PID: 836)
Connects to CnC server
- serialfunc.exe (PID: 836)
SUSPICIOUS
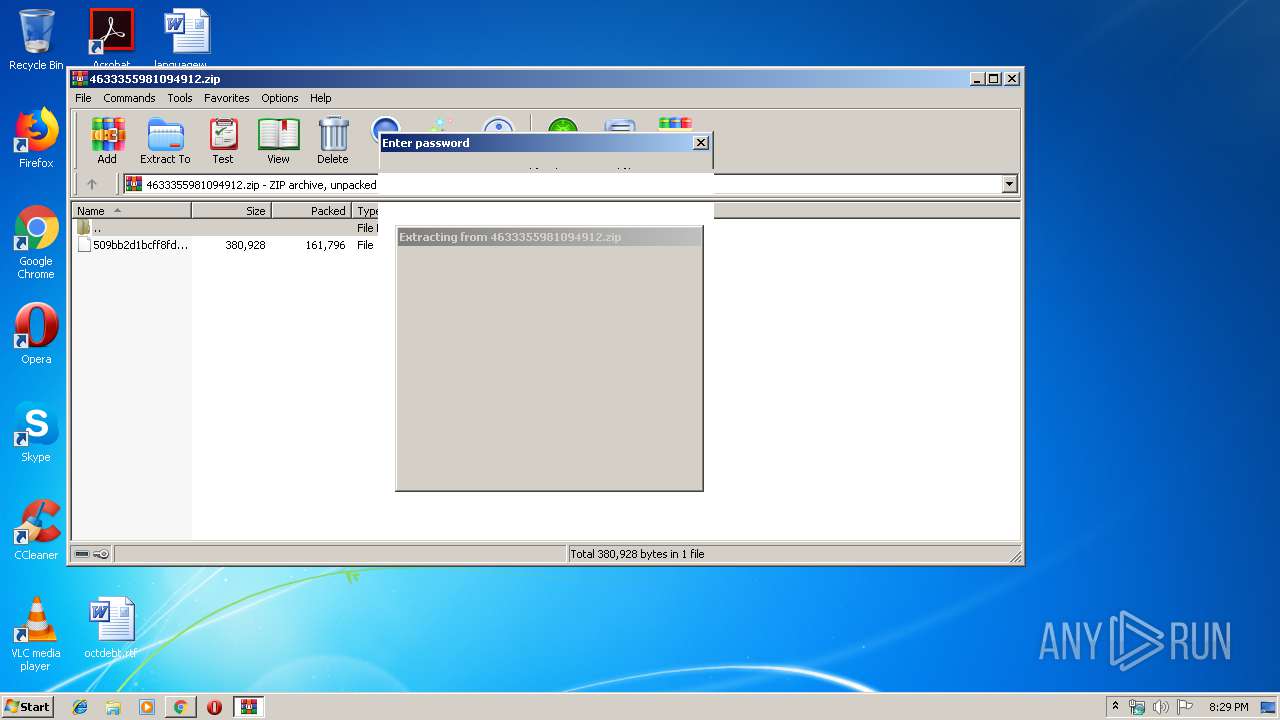
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1892)
- file.exe (PID: 2240)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2852)
Application launched itself
- serialfunc.exe (PID: 3780)
- file.exe (PID: 3652)
Starts itself from another location
- file.exe (PID: 2240)
Connects to server without host name
- serialfunc.exe (PID: 836)
Creates files in the program directory
- firefox.exe (PID: 2776)
INFO
Application launched itself
- chrome.exe (PID: 2852)
- firefox.exe (PID: 2776)
- firefox.exe (PID: 1740)
Reads settings of System Certificates
- chrome.exe (PID: 1048)
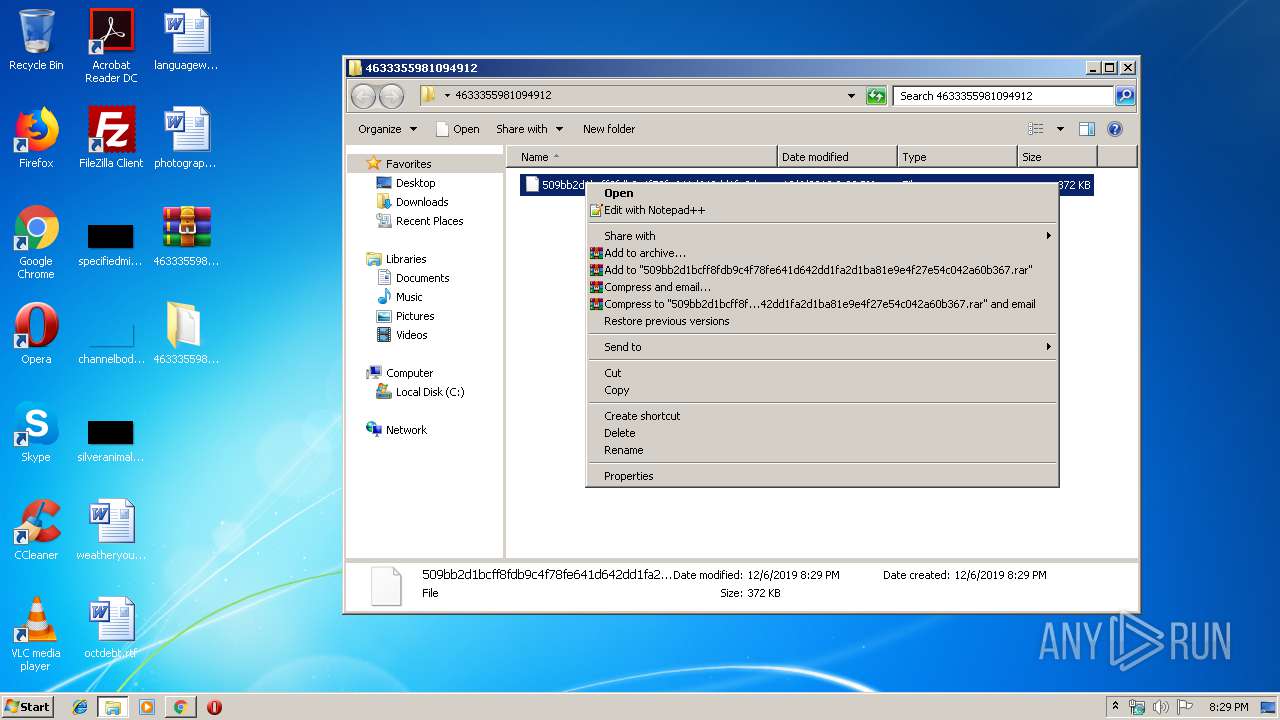
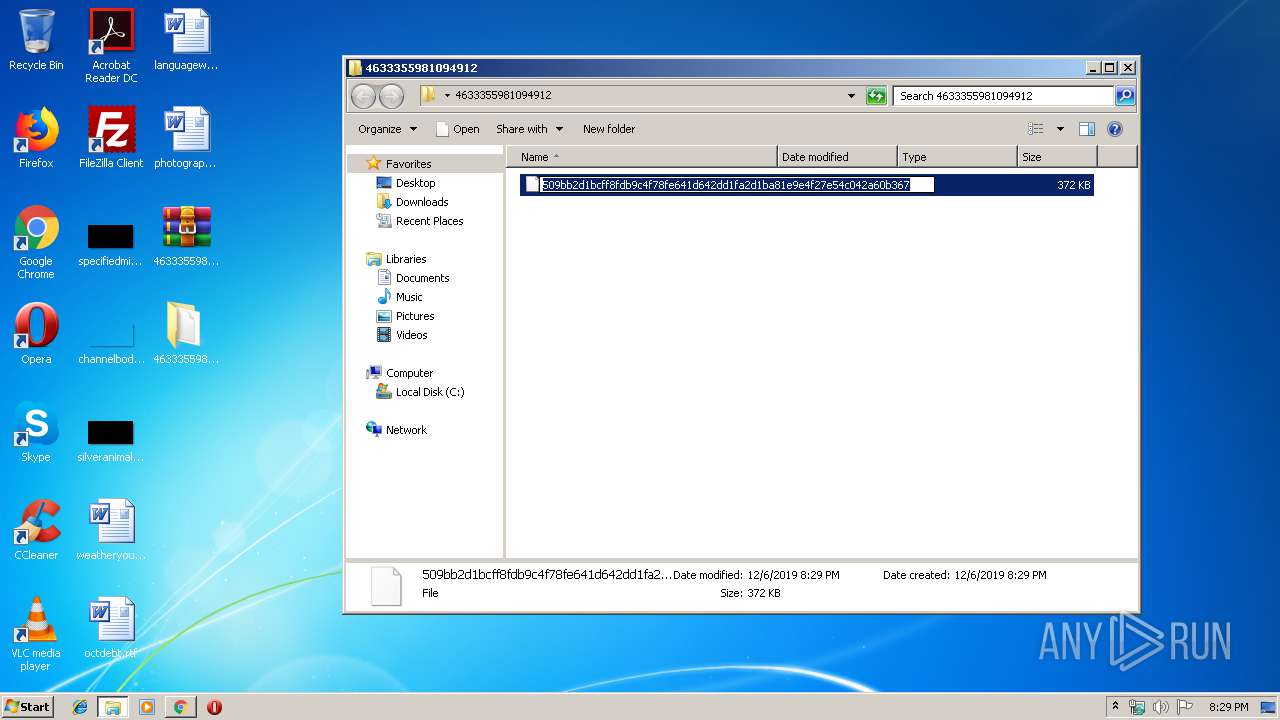
Manual execution by user
- file.exe (PID: 3652)
- chrome.exe (PID: 2852)
- firefox.exe (PID: 1740)
Reads the hosts file
- chrome.exe (PID: 2852)
- chrome.exe (PID: 1048)
Reads CPU info
- firefox.exe (PID: 2776)
Creates files in the user directory
- firefox.exe (PID: 2776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x14684752 |
| ZipCompressedSize: | 161796 |
| ZipUncompressedSize: | 380928 |
| ZipFileName: | 509bb2d1bcff8fdb9c4f78fe641d642dd1fa2d1ba81e9e4f27e54c042a60b367 |
Total processes
80
Monitored processes
42
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,8813184782462158769,2379528594615622027,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2646403361082392811 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,8813184782462158769,2379528594615622027,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11819984825611848403 --mojo-platform-channel-handle=3360 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,8813184782462158769,2379528594615622027,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14332882327751164619 --mojo-platform-channel-handle=3412 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,8813184782462158769,2379528594615622027,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12734542076919445859 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,8813184782462158769,2379528594615622027,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12134422498817222019 --mojo-platform-channel-handle=1620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,8813184782462158769,2379528594615622027,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5661001602156868173 --mojo-platform-channel-handle=3608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,8813184782462158769,2379528594615622027,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3845693374337150123 --mojo-platform-channel-handle=3508 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,8813184782462158769,2379528594615622027,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12575442733214571044 --mojo-platform-channel-handle=3800 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,8813184782462158769,2379528594615622027,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16167493905594629787 --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 442
Read events
1 306
Write events
131
Delete events
5
Modification events
| (PID) Process: | (1892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1892) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\4633355981094912.zip | |||
Executable files
2
Suspicious files
115
Text files
297
Unknown types
61
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d101cf78-45c8-483d-9bf1-806070a342bc.tmp | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF39d396.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
53
DNS requests
124
Threats
35
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
836 | serialfunc.exe | POST | — | 83.136.245.190:8080 | http://83.136.245.190:8080/taskbar/between/add/ | RU | — | — | malicious |
2776 | firefox.exe | POST | 200 | 216.58.211.99:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
1048 | chrome.exe | GET | 302 | 172.217.17.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
1048 | chrome.exe | GET | 302 | 172.217.17.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
836 | serialfunc.exe | POST | — | 165.227.156.155:443 | http://165.227.156.155:443/scripts/prov/ | DE | — | — | malicious |
2776 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2776 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2776 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1048 | chrome.exe | GET | 200 | 74.125.100.104:80 | http://r3---sn-5hnekn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=192.42.116.16&mm=28&mn=sn-5hnekn7z&ms=nvh&mt=1575664098&mv=m&mvi=2&pl=22&shardbypass=yes | US | crx | 293 Kb | whitelisted |
836 | serialfunc.exe | POST | — | 192.241.255.77:8080 | http://192.241.255.77:8080/sym/tpt/add/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1048 | chrome.exe | 172.217.17.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
1048 | chrome.exe | 172.217.17.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1048 | chrome.exe | 172.217.20.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1048 | chrome.exe | 172.217.17.46:443 | apis.google.com | Google Inc. | US | whitelisted |
1048 | chrome.exe | 172.217.17.78:443 | ogs.google.com | Google Inc. | US | whitelisted |
1048 | chrome.exe | 172.217.19.196:443 | www.google.com | Google Inc. | US | whitelisted |
1048 | chrome.exe | 172.217.17.35:443 | www.google.nl | Google Inc. | US | whitelisted |
1048 | chrome.exe | 74.125.100.104:80 | r3---sn-5hnekn7z.gvt1.com | Google Inc. | US | whitelisted |
1048 | chrome.exe | 172.217.17.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1048 | chrome.exe | 172.217.17.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.nl |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
836 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 3 |
836 | serialfunc.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
836 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
836 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 23 |
836 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
836 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 4 |
836 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
836 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
836 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 13 |
836 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
21 ETPRO signatures available at the full report