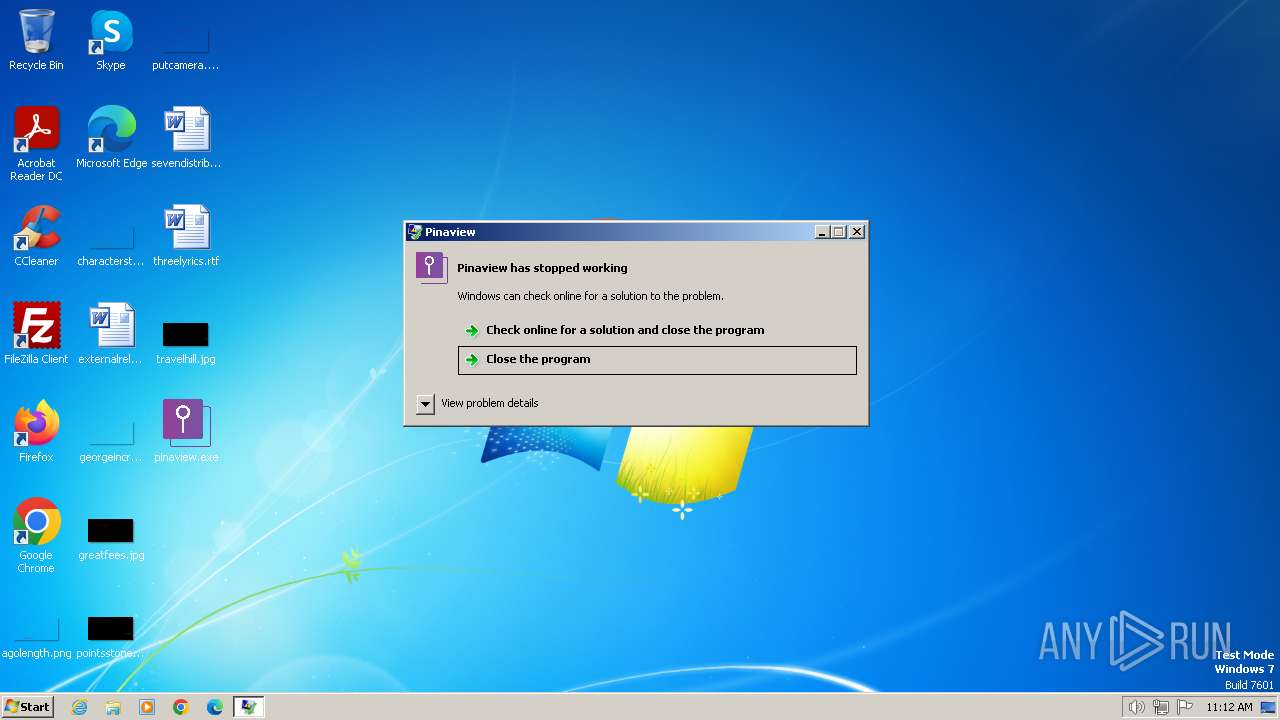
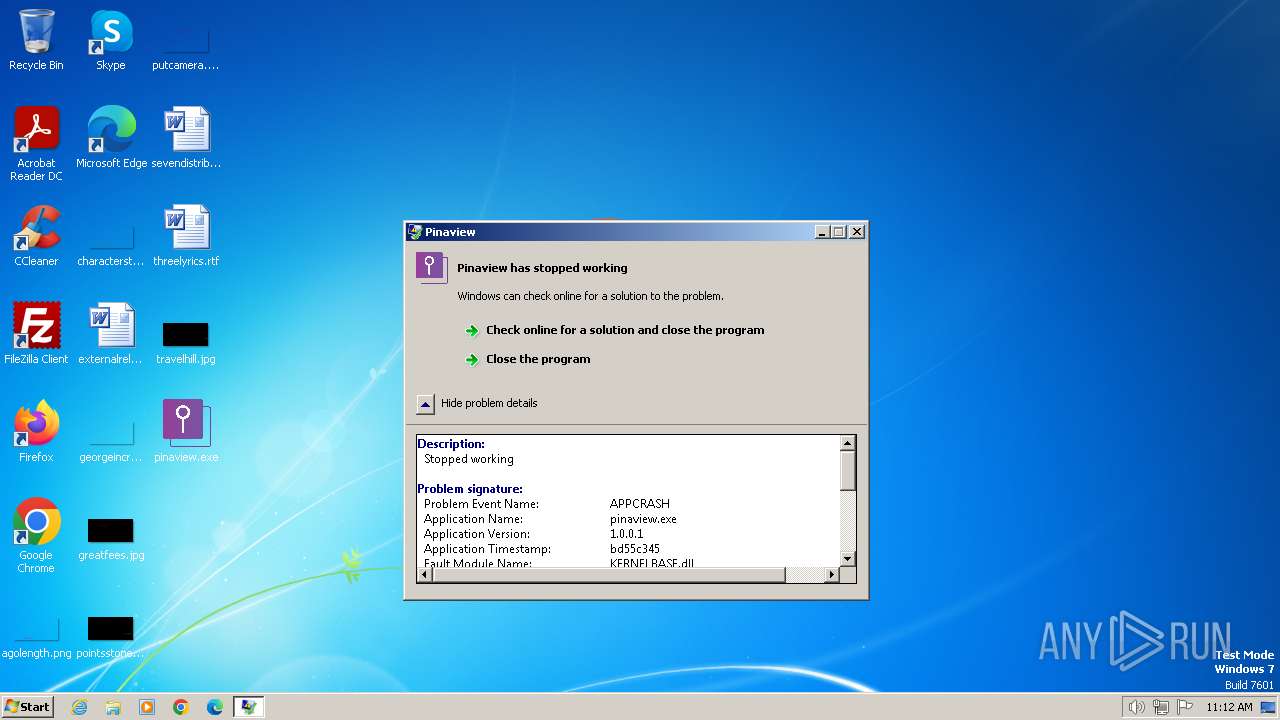
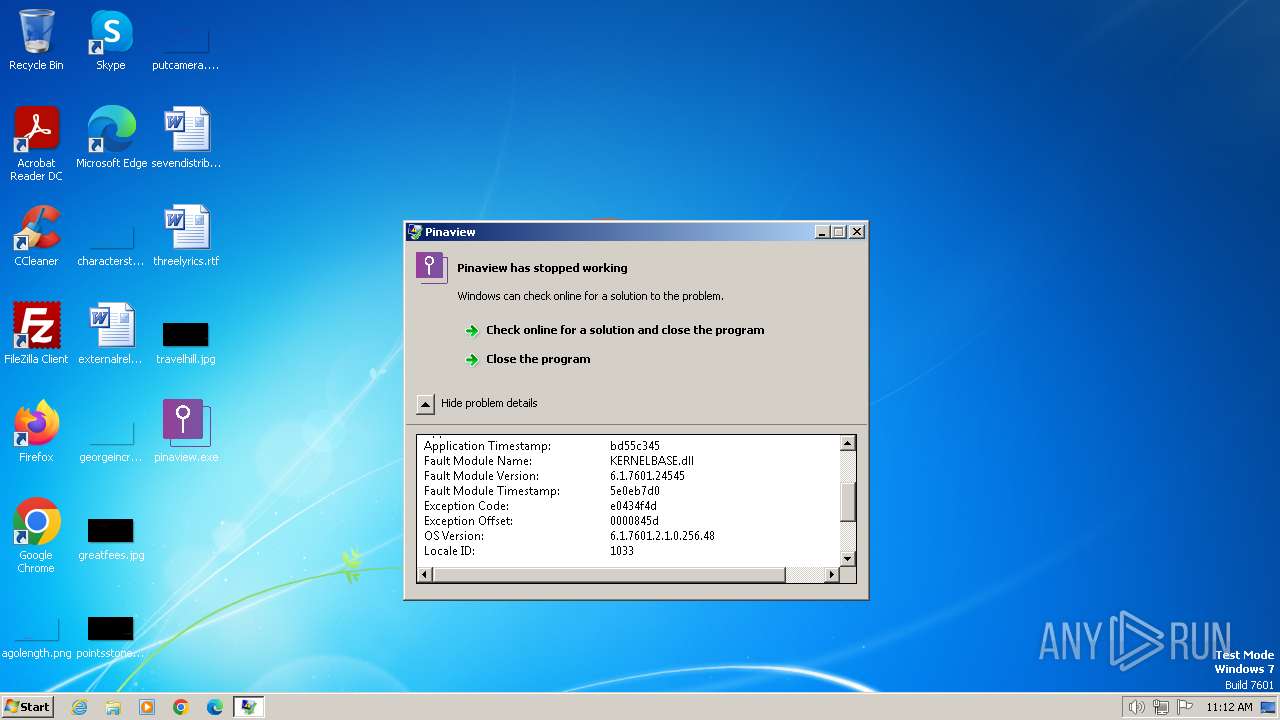
| File name: | pinaview.exe |
| Full analysis: | https://app.any.run/tasks/d2272e7a-6f13-4f01-a632-fd781966fb19 |
| Verdict: | Malicious activity |
| Analysis date: | March 26, 2024, 11:11:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2B91F950A19D1400811A51E815A11CB3 |
| SHA1: | D03BC107A7EA5408AE87A567B8C7A5DD03475033 |
| SHA256: | 79F2E9C5D489A5DADC0207D4E5BE8AE930AA829FA3990C94DCD37E12ED2ED9AF |
| SSDEEP: | 6144:+osAvdgb4BXuRfl7FQqOPXuRfl7FQqODXuRfl7FQqOfDXuRfl7FQqOVsCy6rbQ:+zAvrtuxl7FQqOfuxl7FQqODuxl7FQq1 |
MALICIOUS
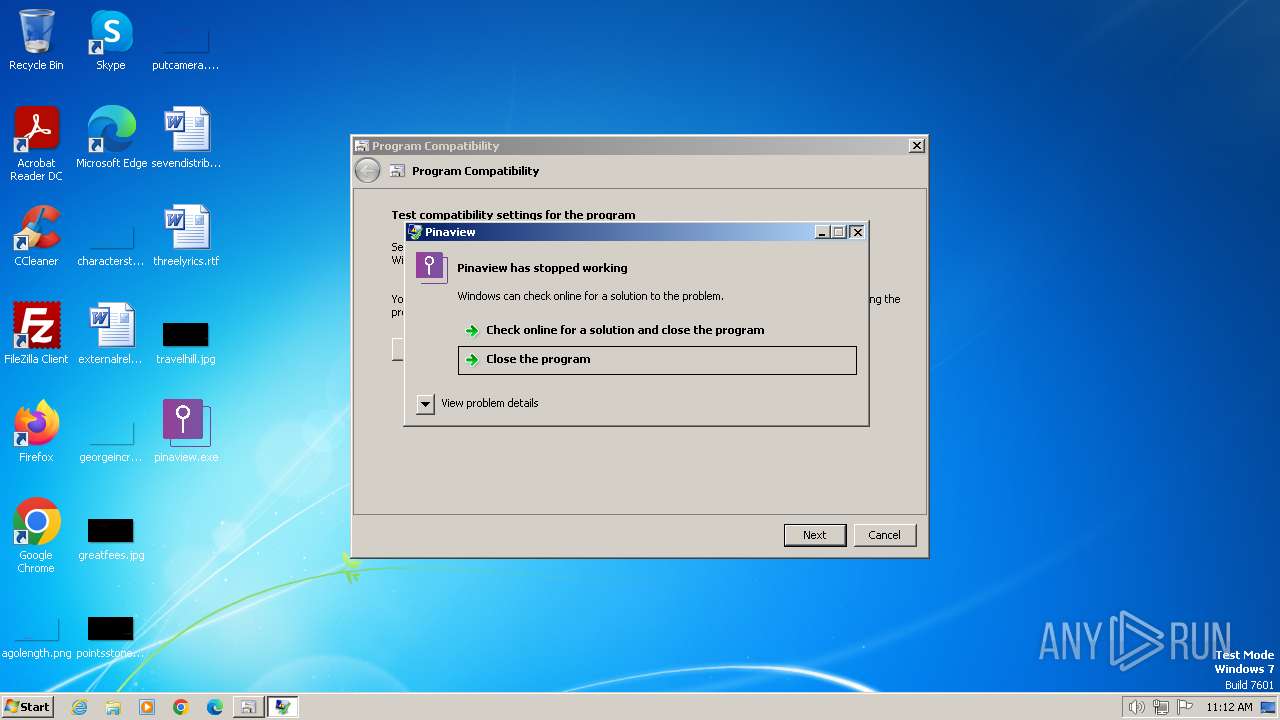
Drops the executable file immediately after the start
- pinaview.exe (PID: 3936)
- csc.exe (PID: 1572)
- csc.exe (PID: 1236)
- csc.exe (PID: 240)
- csc.exe (PID: 2112)
- csc.exe (PID: 3800)
- csc.exe (PID: 968)
Starts Visual C# compiler
- sdiagnhost.exe (PID: 2152)
- sdiagnhost.exe (PID: 1556)
SUSPICIOUS
Reads settings of System Certificates
- pinaview.exe (PID: 3936)
- dw20.exe (PID: 2232)
- msdt.exe (PID: 2364)
- msdt.exe (PID: 980)
- pinaview.exe (PID: 3620)
Checks Windows Trust Settings
- pinaview.exe (PID: 3936)
- pinaview.exe (PID: 3620)
Reads security settings of Internet Explorer
- pinaview.exe (PID: 3936)
- pinaview.exe (PID: 3620)
Reads the Internet Settings
- dw20.exe (PID: 2232)
- sdiagnhost.exe (PID: 2152)
- sdiagnhost.exe (PID: 1556)
- msdt.exe (PID: 980)
Process drops legitimate windows executable
- msdt.exe (PID: 2364)
- msdt.exe (PID: 980)
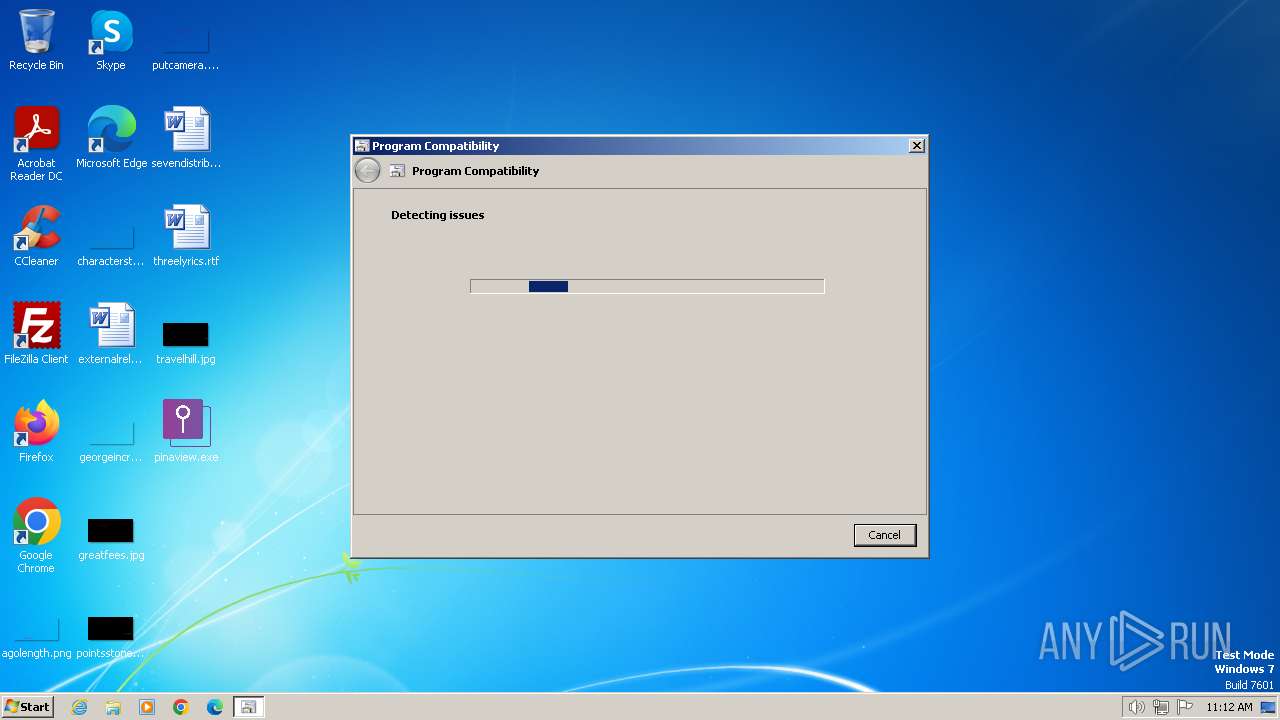
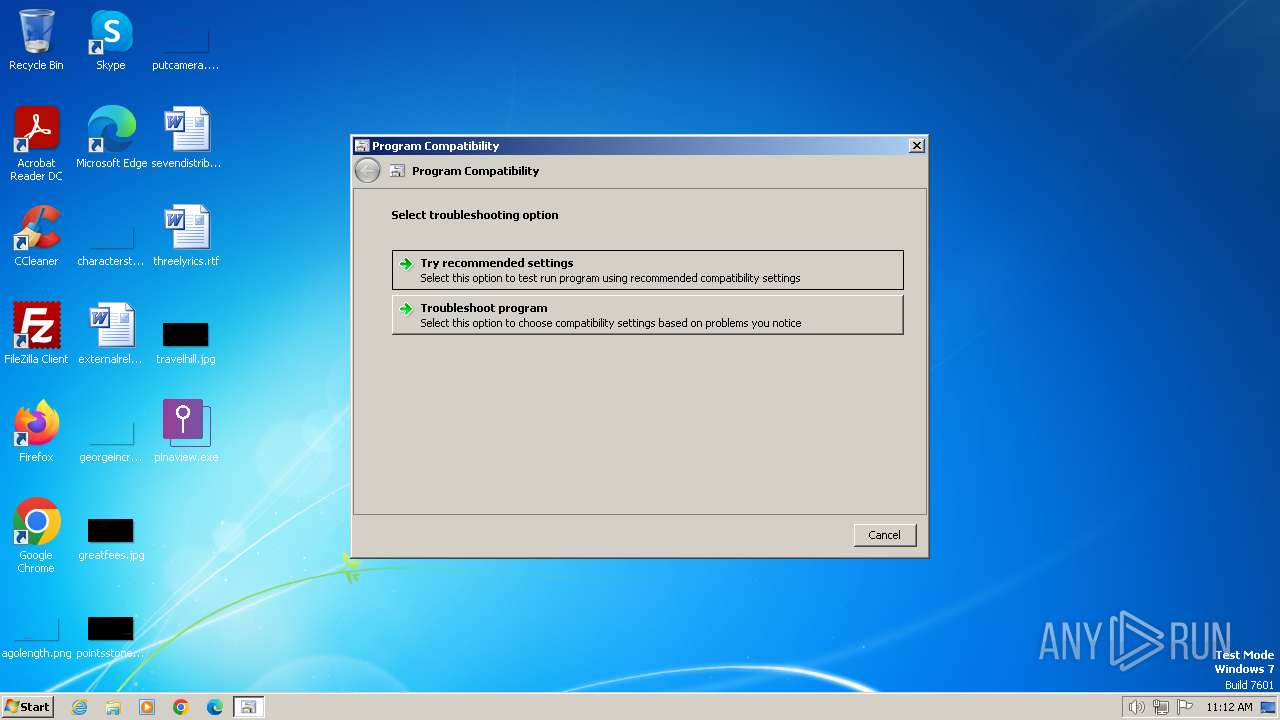
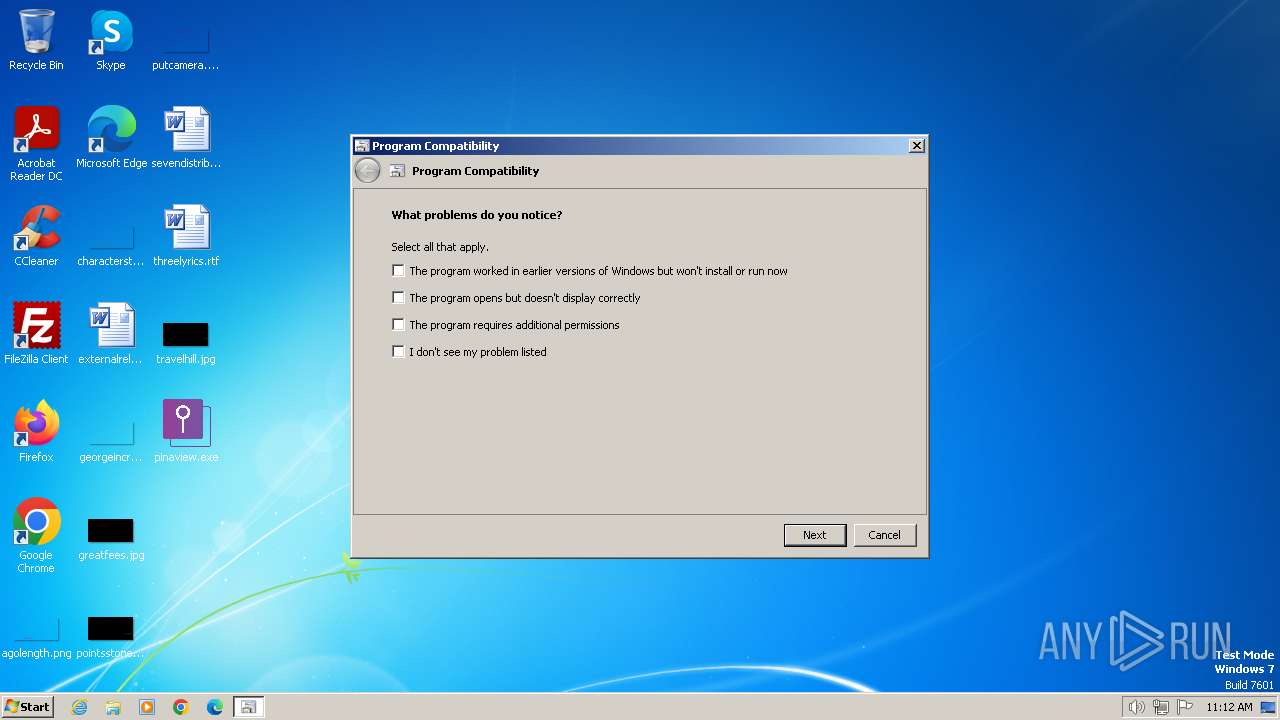
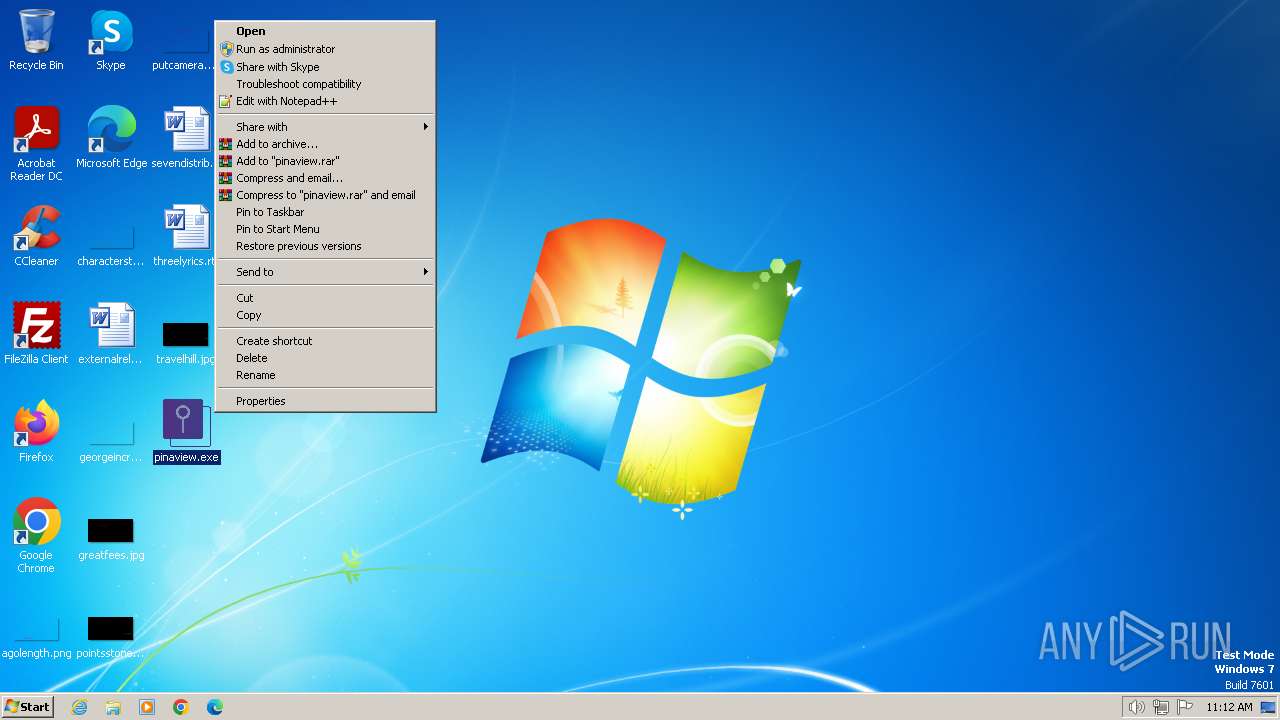
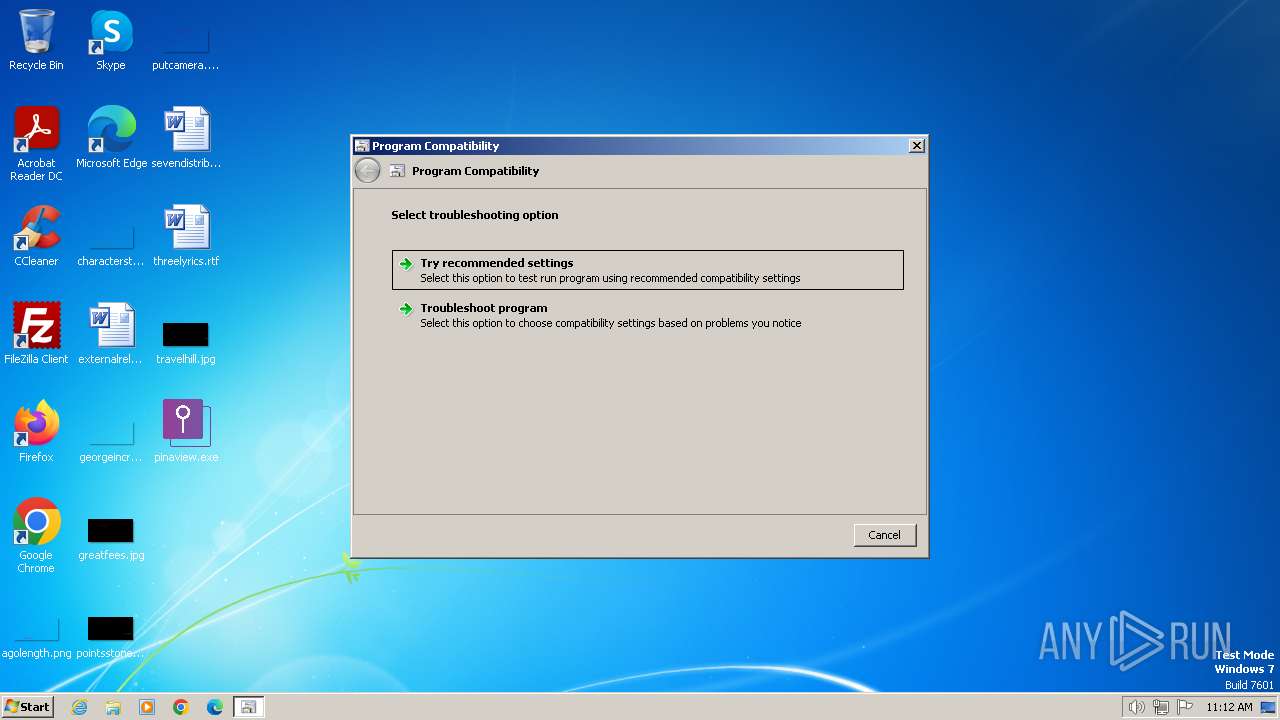
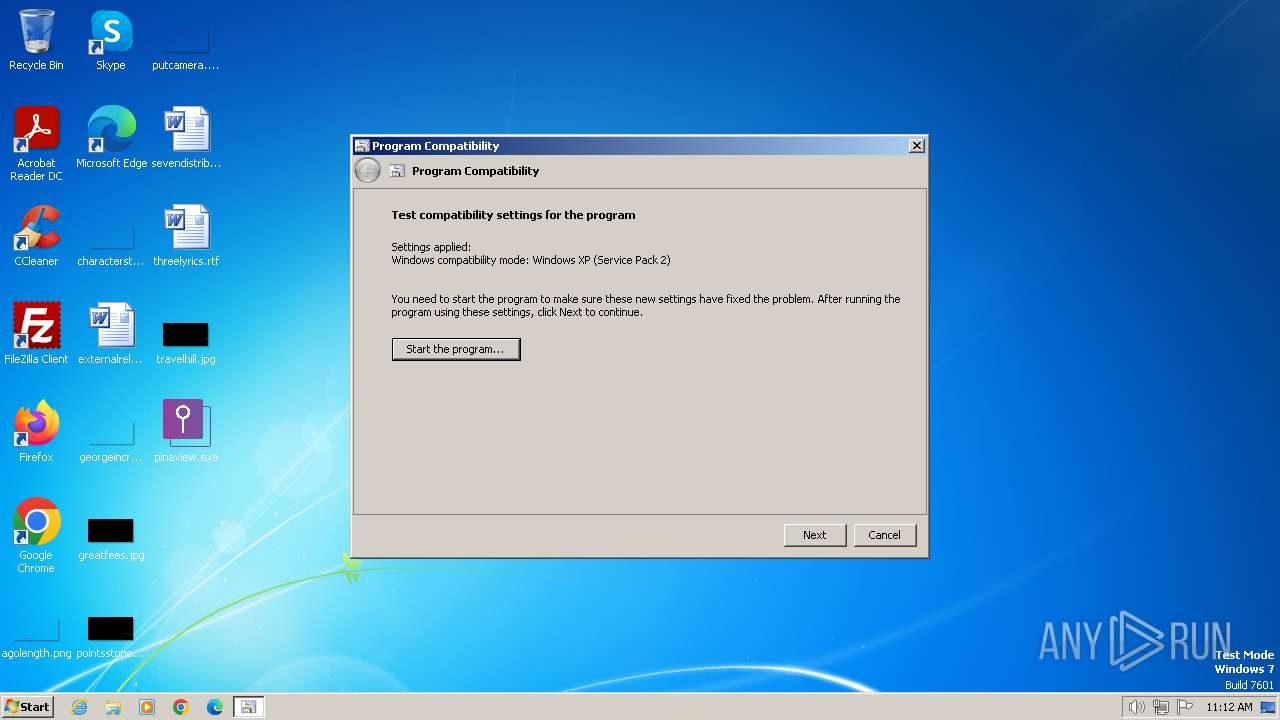
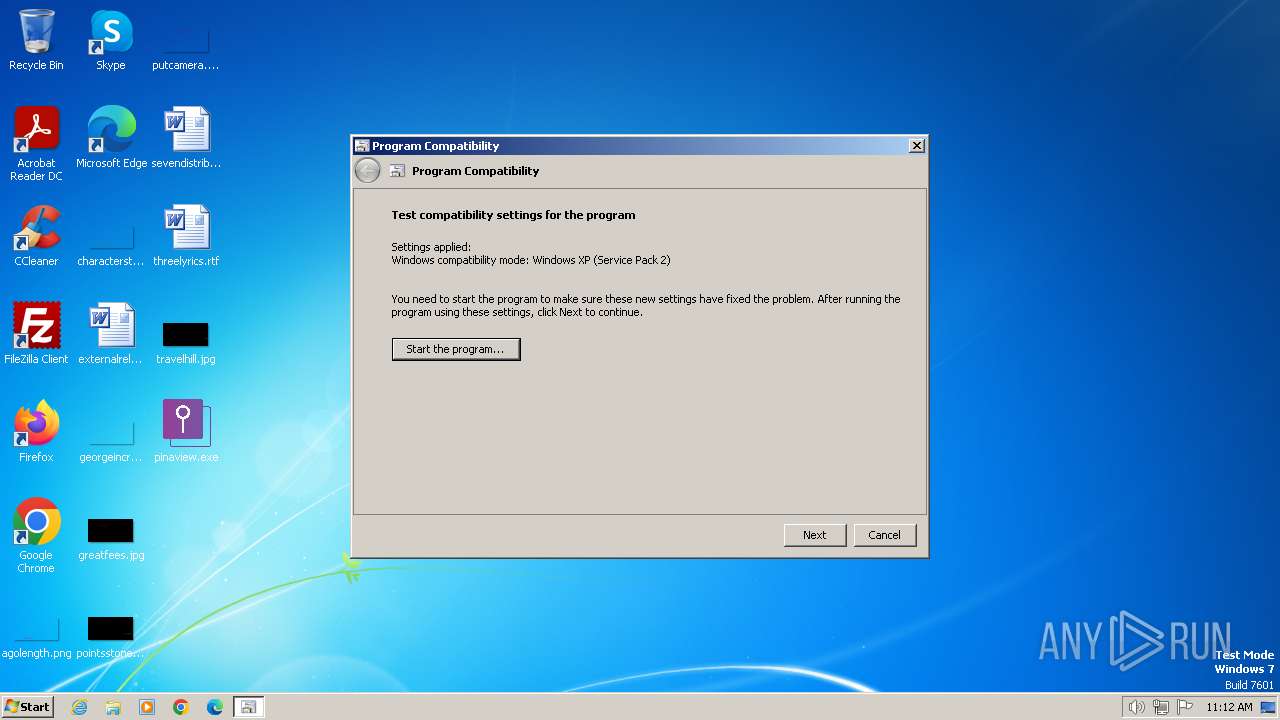
Probably uses Microsoft diagnostics tool to execute malicious payload
- pcwrun.exe (PID: 2688)
- pcwrun.exe (PID: 1844)
Uses .NET C# to load dll
- sdiagnhost.exe (PID: 2152)
- sdiagnhost.exe (PID: 1556)
The process executes via Task Scheduler
- pinaview.exe (PID: 1728)
- pinaview.exe (PID: 3620)
Uses RUNDLL32.EXE to load library
- msdt.exe (PID: 980)
Adds/modifies Windows certificates
- pinaview.exe (PID: 3620)
INFO
Checks supported languages
- pinaview.exe (PID: 3936)
- dw20.exe (PID: 2232)
- csc.exe (PID: 240)
- cvtres.exe (PID: 3912)
- cvtres.exe (PID: 1808)
- cvtres.exe (PID: 2432)
- csc.exe (PID: 1572)
- csc.exe (PID: 1236)
- csc.exe (PID: 2112)
- csc.exe (PID: 968)
- csc.exe (PID: 3800)
- cvtres.exe (PID: 2772)
- cvtres.exe (PID: 2972)
- cvtres.exe (PID: 2384)
- pinaview.exe (PID: 3620)
- dw20.exe (PID: 2568)
Reads the computer name
- pinaview.exe (PID: 3936)
- dw20.exe (PID: 2232)
- pinaview.exe (PID: 3620)
- dw20.exe (PID: 2568)
Reads the software policy settings
- pinaview.exe (PID: 3936)
- dw20.exe (PID: 2232)
- msdt.exe (PID: 2364)
- msdt.exe (PID: 980)
- pinaview.exe (PID: 3620)
Reads the machine GUID from the registry
- pinaview.exe (PID: 3936)
- dw20.exe (PID: 2232)
- csc.exe (PID: 240)
- csc.exe (PID: 1572)
- cvtres.exe (PID: 2432)
- cvtres.exe (PID: 1808)
- cvtres.exe (PID: 3912)
- csc.exe (PID: 1236)
- csc.exe (PID: 2112)
- csc.exe (PID: 968)
- cvtres.exe (PID: 2384)
- csc.exe (PID: 3800)
- cvtres.exe (PID: 2772)
- cvtres.exe (PID: 2972)
- pinaview.exe (PID: 3620)
- dw20.exe (PID: 2568)
Reads product name
- dw20.exe (PID: 2232)
Reads Environment values
- dw20.exe (PID: 2232)
Create files in a temporary directory
- dw20.exe (PID: 2232)
- pcwrun.exe (PID: 2688)
- msdt.exe (PID: 2364)
- sdiagnhost.exe (PID: 2152)
- csc.exe (PID: 240)
- cvtres.exe (PID: 2432)
- csc.exe (PID: 1236)
- cvtres.exe (PID: 1808)
- cvtres.exe (PID: 3912)
- csc.exe (PID: 1572)
- msdt.exe (PID: 980)
- sdiagnhost.exe (PID: 1556)
- pcwrun.exe (PID: 1844)
- csc.exe (PID: 968)
- cvtres.exe (PID: 2384)
- csc.exe (PID: 3800)
- cvtres.exe (PID: 2772)
- cvtres.exe (PID: 2972)
- csc.exe (PID: 2112)
Creates files or folders in the user directory
- dw20.exe (PID: 2232)
- msdt.exe (PID: 2364)
- msdt.exe (PID: 980)
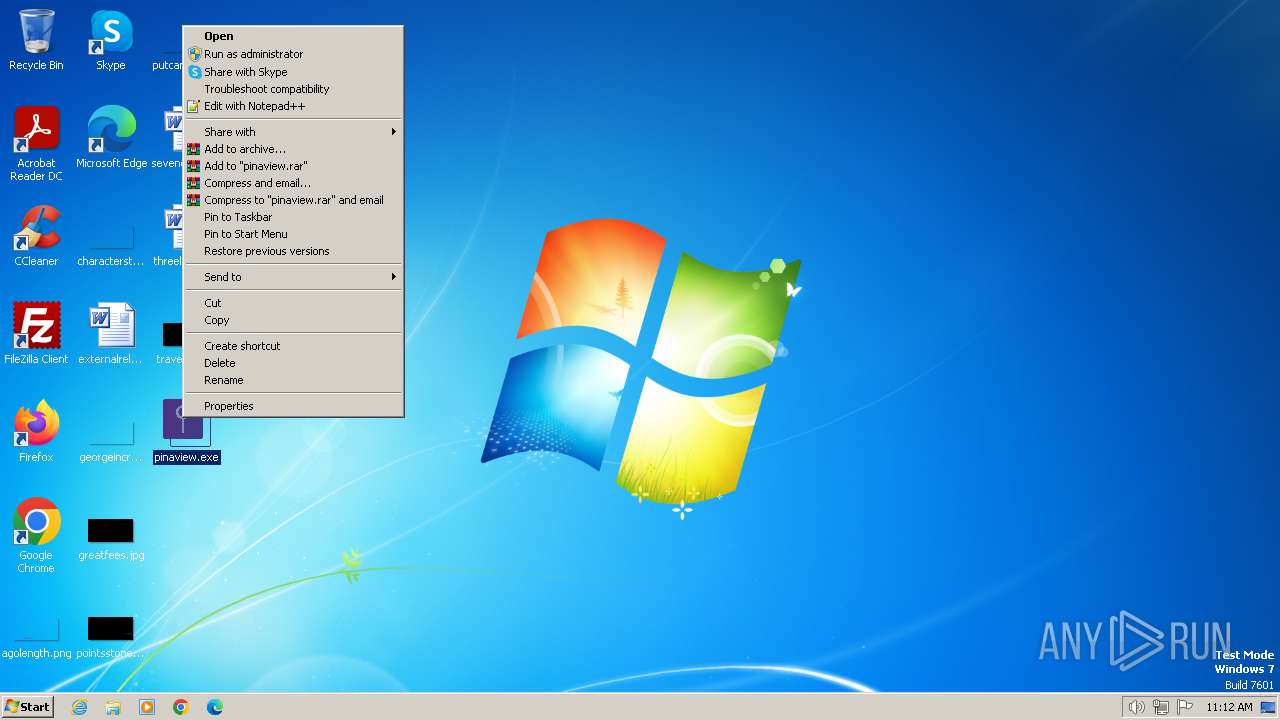
Manual execution by a user
- pcwrun.exe (PID: 2688)
- pcwrun.exe (PID: 1844)
Drops the executable file immediately after the start
- msdt.exe (PID: 2364)
- msdt.exe (PID: 980)
Reads security settings of Internet Explorer
- msdt.exe (PID: 2364)
- sdiagnhost.exe (PID: 2152)
- msdt.exe (PID: 980)
- sdiagnhost.exe (PID: 1556)
Creates files in the program directory
- dw20.exe (PID: 2568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2070:08:29 05:06:13+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 109568 |
| InitializedDataSize: | 25088 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1cb92 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Pinaview |
| FileVersion: | 1.0.0.1 |
| InternalName: | Pinaview.exe |
| LegalCopyright: | Copyright © 2023 |
| LegalTrademarks: | - |
| OriginalFileName: | Pinaview.exe |
| ProductName: | Pinaview |
| ProductVersion: | 1.0.0.1 |
| AssemblyVersion: | 1.0.0.1 |
Total processes
65
Monitored processes
24
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\le77fjbi.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 844 | "C:\Windows\System32\rundll32.exe" C:\Windows\system32\pcwutl.dll,CreateAndRunTask -path "C:\Users\admin\Desktop\pinaview.exe" | C:\Windows\System32\rundll32.exe | — | msdt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 968 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\-moyqb6r.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 980 | C:\Windows\System32\msdt.exe -path C:\Windows\diagnostics\index\PCWDiagnostic.xml -af C:\Users\admin\AppData\Local\Temp\PCWC3D8.xml /skip TRUE | C:\Windows\System32\msdt.exe | — | pcwrun.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1236 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\ybdrksxf.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1556 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1572 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\0bh89ahc.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1728 | C:\Users\admin\Desktop\pinaview.exe | C:\Users\admin\Desktop\pinaview.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Pinaview Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1808 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES8587.tmp" "c:\Users\admin\AppData\Local\Temp\CSC8586.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1844 | C:\Windows\system32\pcwrun.exe "C:\Users\admin\Desktop\pinaview.exe" | C:\Windows\System32\pcwrun.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Program Compatibility Troubleshooter Invoker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
24 925
Read events
24 776
Write events
130
Delete events
19
Modification events
| (PID) Process: | (3936) pinaview.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2232) dw20.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\Windows Error Reporting\Debug\UIHandles |
| Operation: | write | Name: | FirstLevelConsentDialog |
Value: 9C01130000000000 | |||
| (PID) Process: | (2232) dw20.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\Debug\UIHandles |
| Operation: | write | Name: | FirstLevelConsentDialog |
Value: 9C01130000000000 | |||
| (PID) Process: | (2232) dw20.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\Windows Error Reporting\Debug\UIHandles |
| Operation: | write | Name: | CheckingForSolutionDialog |
Value: 9C01130000000000 | |||
| (PID) Process: | (2232) dw20.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\Debug\UIHandles |
| Operation: | write | Name: | CheckingForSolutionDialog |
Value: 9C01130000000000 | |||
| (PID) Process: | (2232) dw20.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2232) dw20.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates |
| Operation: | delete value | Name: | 9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
Value: | |||
| (PID) Process: | (2232) dw20.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates\9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
| Operation: | write | Name: | Blob |
Value: 0F00000001000000200000009065F32AFC2CFEA7F452D2D6BE94D20C877EFC1C05433D9935696193FDCC05D80300000001000000140000009F6134C5FA75E4FDDE631B232BE961D6D4B97DB6200000000100000047030000308203433082022BA00302010202147327B7C17D5AE708EF73F1F45A79D78B4E99A29F300D06092A864886F70D01010B05003031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C084469676943657274301E170D3233303932393130353030335A170D3339303530383130353030335A3031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C08446967694365727430820122300D06092A864886F70D01010105000382010F003082010A0282010100D91B7A55548F44F3E97C493153B75B055695736B184640D7335A2E6218083B5A1BEE2695209350E57A3EB76FBC604CB3B250DF3D9D0C560D1FBDFE30108D233A3C555100BE1A3F8E543C0B253E06E91B6D5F9CB3A093009BC8B4D3A0EB19DB59E56DA7E3D637847970D6C2AEB4A1FCF3896A7C080FE68759BAA62E6AAA8B7C7CBDA176DDC72F8D259A16D3469E31F19D2959904611D730D7D26FCFED789A0C49698FDFABF3F6727D08C61A073BB11E85C96486D49B0E0D38364C008A5EB964F8813C5DF004F9E76D2F8DB90702D800032674959BF0DF823785419101CEA928A10ACBAE7E48FE19202F3CB7BCF416476D17CB64C5570FCED443BD75D9F2C632FF0203010001A3533051301D0603551D0E041604145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7301F0603551D230418301680145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7300F0603551D130101FF040530030101FF300D06092A864886F70D01010B05000382010100AF2218E4CA18144728FCC76EA14958061522FD4A018BED1A4BFCC5CCE70BC6AE9DF7D3795C9A010D53628E2B6E7C10D6B07E53546235A5EE480E5A434E312154BF1E39AAC27D2C18D4F41CBBECFE4538CEF93EF62C17D187A7F720F4A9478410D09620C9F8B293B5786A5440BC0743B7B7753CF66FBA498B7E083BC267597238DC031B9BB131F997D9B8164AAED0D6E328420E53E1969DA6CD035078179677A7177BB2BF9C87CF592910CD380E8501B92040A39469C782BA383BEAE498C060FCC7C429BC10B7B6B7A0659C9BE03DC13DB46C638CF5E3B22A303726906DC8DD91C64501EBFC282A3A497EC430CACC066EE4BF9C5C8F2F2A05D0C1921A9E3E85E3 | |||
| (PID) Process: | (2232) dw20.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates\9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
| Operation: | delete value | Name: | File |
Value: | |||
| (PID) Process: | (2232) dw20.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates\9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
10
Suspicious files
20
Text files
41
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2232 | dw20.exe | C:\Users\admin\AppData\Local\Temp\WER6879.tmp.WERInternalMetadata.xml | xml | |
MD5:— | SHA256:— | |||
| 2232 | dw20.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_pinaview.exe_62b6b69f4943e2554274d328b08492de4021184_08a06ffb\Report.wer | — | |
MD5:— | SHA256:— | |||
| 2688 | pcwrun.exe | C:\Users\admin\AppData\Local\Temp\PCW7F4D.xml | xml | |
MD5:— | SHA256:— | |||
| 2364 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_f7bc39ca-dcec-482c-85d4-2d88f64b6f71\DiagPackage.diagpkg | html | |
MD5:— | SHA256:— | |||
| 2364 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_f7bc39ca-dcec-482c-85d4-2d88f64b6f71\DiagPackage.dll | executable | |
MD5:— | SHA256:— | |||
| 2364 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_f7bc39ca-dcec-482c-85d4-2d88f64b6f71\RS_ProgramCompatibilityWizard.ps1 | text | |
MD5:— | SHA256:— | |||
| 2364 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_f7bc39ca-dcec-482c-85d4-2d88f64b6f71\TS_ProgramCompatibilityWizard.ps1 | text | |
MD5:— | SHA256:— | |||
| 2364 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_f7bc39ca-dcec-482c-85d4-2d88f64b6f71\VF_ProgramCompatibilityWizard.ps1 | text | |
MD5:— | SHA256:— | |||
| 2364 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_f7bc39ca-dcec-482c-85d4-2d88f64b6f71\en-US\CL_LocalizationData.psd1 | text | |
MD5:— | SHA256:— | |||
| 2364 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_f7bc39ca-dcec-482c-85d4-2d88f64b6f71\en-US\DiagPackage.dll.mui | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2232 | dw20.exe | 104.208.16.93:443 | watson.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
watson.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|