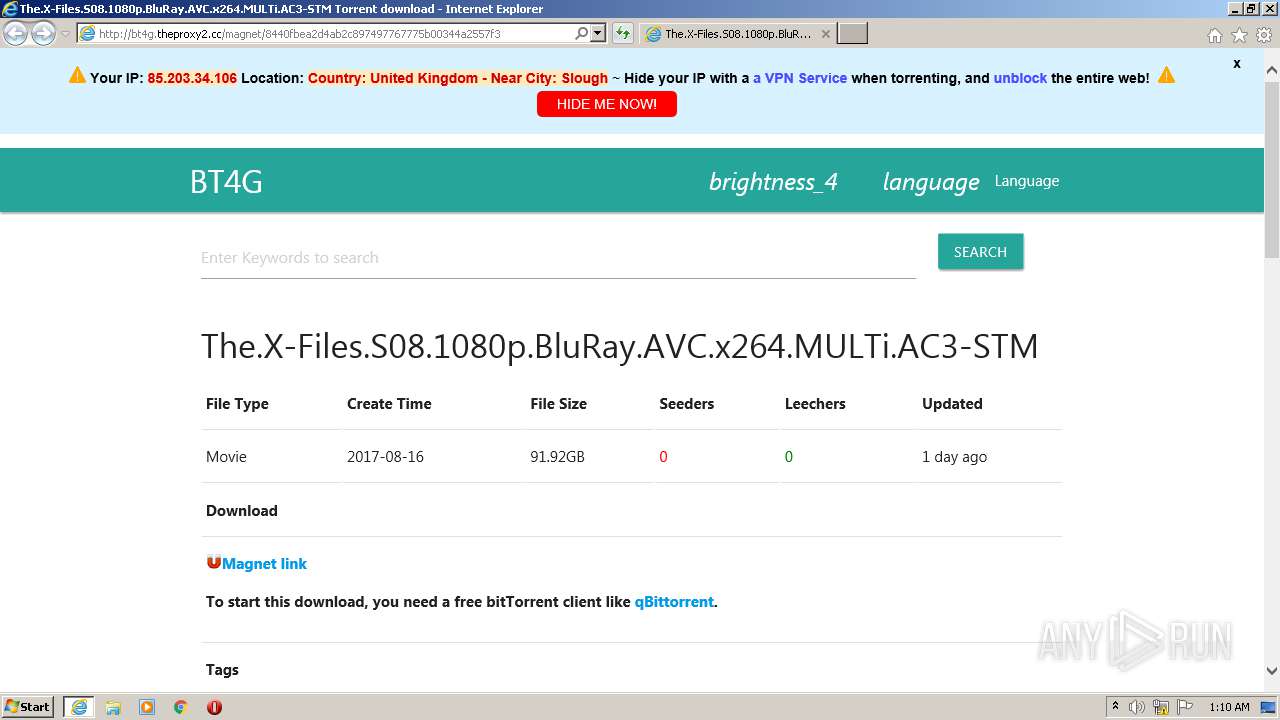
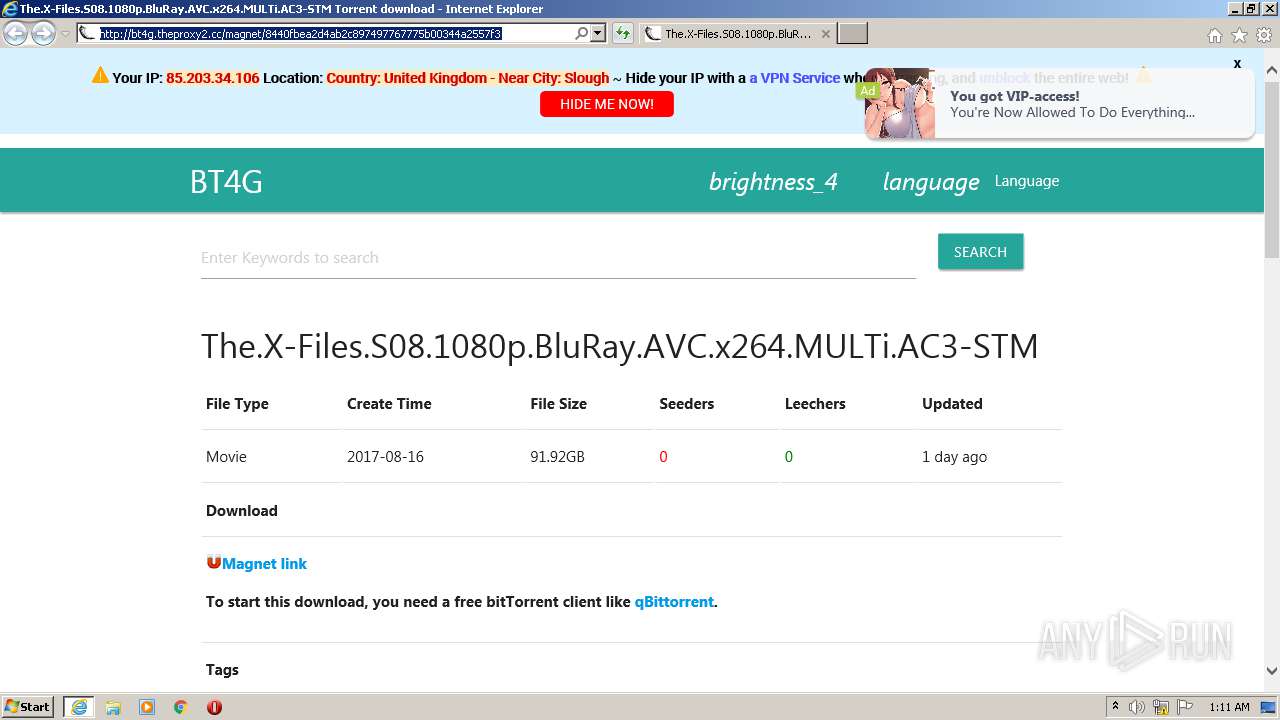
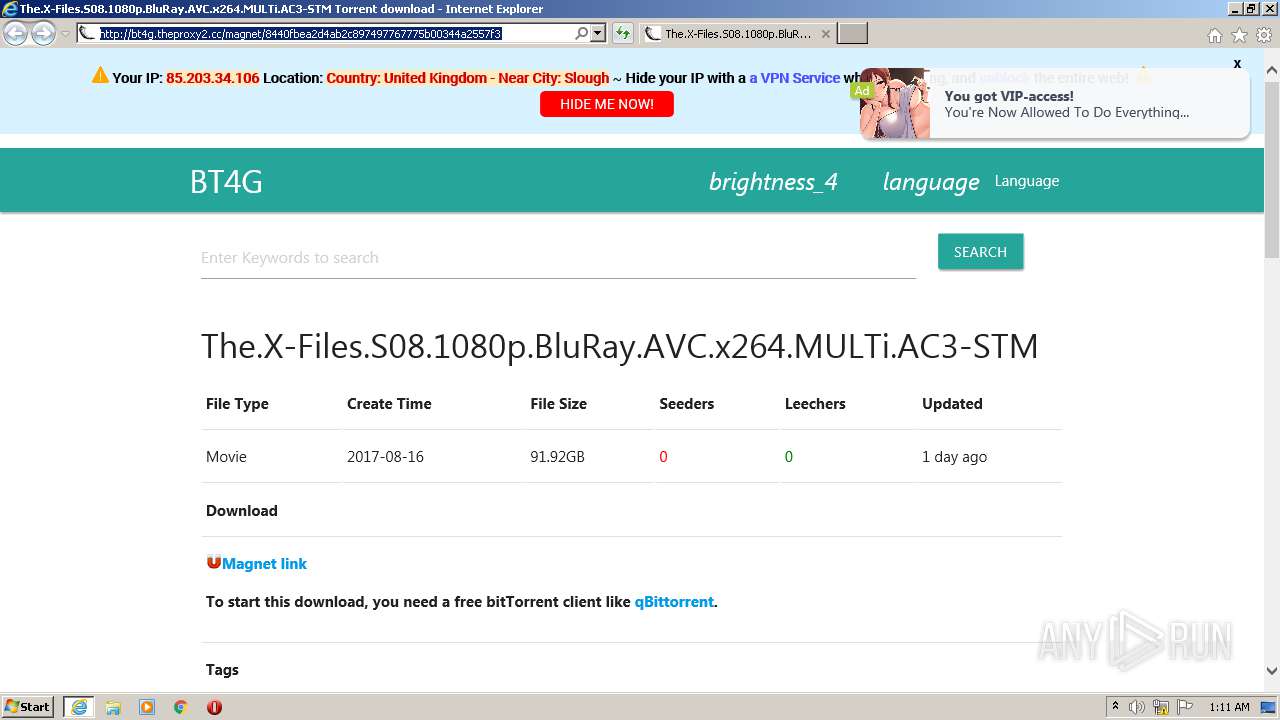
| URL: | http://bt4g.theproxy2.cc/magnet/8440fbea2d4ab2c897497767775b00344a2557f3 |
| Full analysis: | https://app.any.run/tasks/ab5d889f-21c3-4e87-aaaa-20390f67e13c |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2021, 00:10:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0145A7E8B24868B51F04156ECFD48DE9 |
| SHA1: | 013244946B47E86ECF8478C3C3B406A5AB741D37 |
| SHA256: | 79EAA6BC238731D3B9BC633C60151BB5DE5DF7A5B9B23D51D53F0698453194D4 |
| SSDEEP: | 3:N1KcYRNp2RDxRoERkXHSRcSG+3+oDW:CccExe+XRcJeW |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 1824)
Reads settings of System Certificates
- iexplore.exe (PID: 3644)
- iexplore.exe (PID: 1824)
Changes settings of System certificates
- iexplore.exe (PID: 1824)
Creates files in the user directory
- iexplore.exe (PID: 3644)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1824)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3644)
Reads internet explorer settings
- iexplore.exe (PID: 3644)
Application launched itself
- iexplore.exe (PID: 1824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
34
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1824 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://bt4g.theproxy2.cc/magnet/8440fbea2d4ab2c897497767775b00344a2557f3" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3644 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1824 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 735
Read events
1 489
Write events
244
Delete events
2
Modification events
| (PID) Process: | (3644) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 618380458 | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30886577 | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1824) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
76
Text files
94
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3644 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9F89.tmp | — | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9F8A.tmp | — | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\644B8874112055B5E195ECB0E8F243A4 | — | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\q1[1].js | text | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\8440fbea2d4ab2c897497767775b00344a2557f3[1].htm | html | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\magnet[1].png | image | |
MD5:7E97D174506CC8402D3C7B6FC0B92549 | SHA256:DEB2042BCDE92E374E620460125EAEA3F5C160F35BF25D5DCA43D3666484C902 | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\style[1].css | text | |
MD5:1D39B1ECFEA11E909DA349142CBC69DB | SHA256:F975C58A44A0664D8E15017761D5A8200EB329157C443102D748ED306EF1131C | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\GLEO8300.txt | — | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\zpp3[1].js | text | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75B56E8F3F007D60568781FDA44E713D | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
89
DNS requests
44
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3644 | iexplore.exe | GET | 302 | 172.67.145.231:80 | http://bt4g.theproxy2.cc/b/?https://cdnjs.cloudflare.com/ajax/libs/materialize/1.0.0/css/materialize.min.css | US | — | — | suspicious |
3644 | iexplore.exe | GET | 200 | 172.67.145.231:80 | http://bt4g.theproxy2.cc/magnet/8440fbea2d4ab2c897497767775b00344a2557f3 | US | html | 3.86 Kb | suspicious |
3644 | iexplore.exe | GET | 200 | 172.67.145.231:80 | http://bt4g.theproxy2.cc/zpp/zpp3.js | US | text | 13.7 Kb | suspicious |
3644 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
— | — | GET | 200 | 172.67.145.231:80 | http://bt4g.theproxy2.cc/q1.js?q22q2q33333 | US | text | 6.31 Kb | suspicious |
3644 | iexplore.exe | GET | 200 | 2.16.186.10:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
3644 | iexplore.exe | GET | 200 | 139.45.197.239:80 | http://totentacruelor.com/5/2632704 | US | text | 18.5 Kb | malicious |
3644 | iexplore.exe | GET | 200 | 2.16.186.10:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
3644 | iexplore.exe | GET | 200 | 2.16.186.10:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
3644 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3644 | iexplore.exe | 172.67.194.179:443 | ecma.sidebyx.com | — | US | unknown |
3644 | iexplore.exe | 139.45.197.237:80 | inpagepush.com | — | US | malicious |
3644 | iexplore.exe | 192.243.59.12:80 | softwarepastel.com | DataWeb Global Group B.V. | US | malicious |
3644 | iexplore.exe | 88.85.66.220:443 | oupaumul.net | Webzilla B.V. | NL | unknown |
3644 | iexplore.exe | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3644 | iexplore.exe | 172.67.145.231:80 | bt4g.theproxy2.cc | — | US | suspicious |
3644 | iexplore.exe | 2.16.186.10:80 | crl.identrust.com | Akamai International B.V. | — | whitelisted |
3644 | iexplore.exe | 2.16.186.11:80 | r3.o.lencr.org | Akamai International B.V. | — | whitelisted |
3644 | iexplore.exe | 104.21.94.42:80 | matomo.hellohi.me | Cloudflare Inc | US | unknown |
3644 | iexplore.exe | 104.21.94.42:443 | matomo.hellohi.me | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bt4g.theproxy2.cc |
| suspicious |
totentacruelor.com |
| malicious |
ecma.sidebyx.com |
| suspicious |
oupaumul.net |
| suspicious |
inpagepush.com |
| whitelisted |
softwarepastel.com |
| malicious |
cdnjs.cloudflare.com |
| whitelisted |
crl.identrust.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r3.o.lencr.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |