| File name: | smbsvcs.exe |
| Full analysis: | https://app.any.run/tasks/325030b2-112a-4a0f-a67d-51d14edc565c |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2019, 00:55:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 1615CE078261205940D64EBD523F7B7D |
| SHA1: | AF5BC84F20E9A3155954320E901929A1001221FC |
| SHA256: | 79D7BFECD662DDC7CF2FEFC1386708ABC381803E10E59F6B6E7C90C9A0D5CADE |
| SSDEEP: | 6144:kUm7Ahxe//ARObsty0zfqkfLfW4kFfevVpi4ySK2OKYYjLAdxs06e+aU64:kUm7Ahxs/A9y3kfLfW4021ybHCVRv |
MALICIOUS
Application was dropped or rewritten from another process
- twitch1.exe (PID: 496)
- svhost.exe (PID: 928)
Writes to a start menu file
- smbsvcs.exe (PID: 1728)
SUSPICIOUS
Executable content was dropped or overwritten
- cmd.exe (PID: 2212)
- smbsvcs.exe (PID: 1728)
Starts CMD.EXE for commands execution
- smbsvcs.exe (PID: 1728)
Creates files in the user directory
- cmd.exe (PID: 2212)
- smbsvcs.exe (PID: 1728)
- cmd.exe (PID: 3152)
Connects to unusual port
- svhost.exe (PID: 928)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:19 18:21:48+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 307200 |
| InitializedDataSize: | 238080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4ceea |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| CompanyWebsite: | http://argouml.tigris.org |
| FileDescription: | - |
| FileVersion: | 0.34 |
| LegalCopyright: | - |
| ProductName: | ArgoUML |
| ProductVersion: | 0.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jul-2019 16:21:48 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 19-Jul-2019 16:21:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0004AEF0 | 0x0004B000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.53125 |
.rsrc | 0x0004E000 | 0x00039E16 | 0x0003A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.42667 |
.reloc | 0x00088000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.13211 | 536 | Latin 1 / Western European | UNKNOWN | RT_VERSION |
2 | 5.18463 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.37528 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.3513 | 21640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.29562 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.47056 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.48187 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.65412 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 5.63554 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
mscoree.dll |
Total processes
45
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\Users\admin\AppData\Local\Temp\twitch1.exe" | C:\Users\admin\AppData\Local\Temp\twitch1.exe | — | smbsvcs.exe | |||||||||||
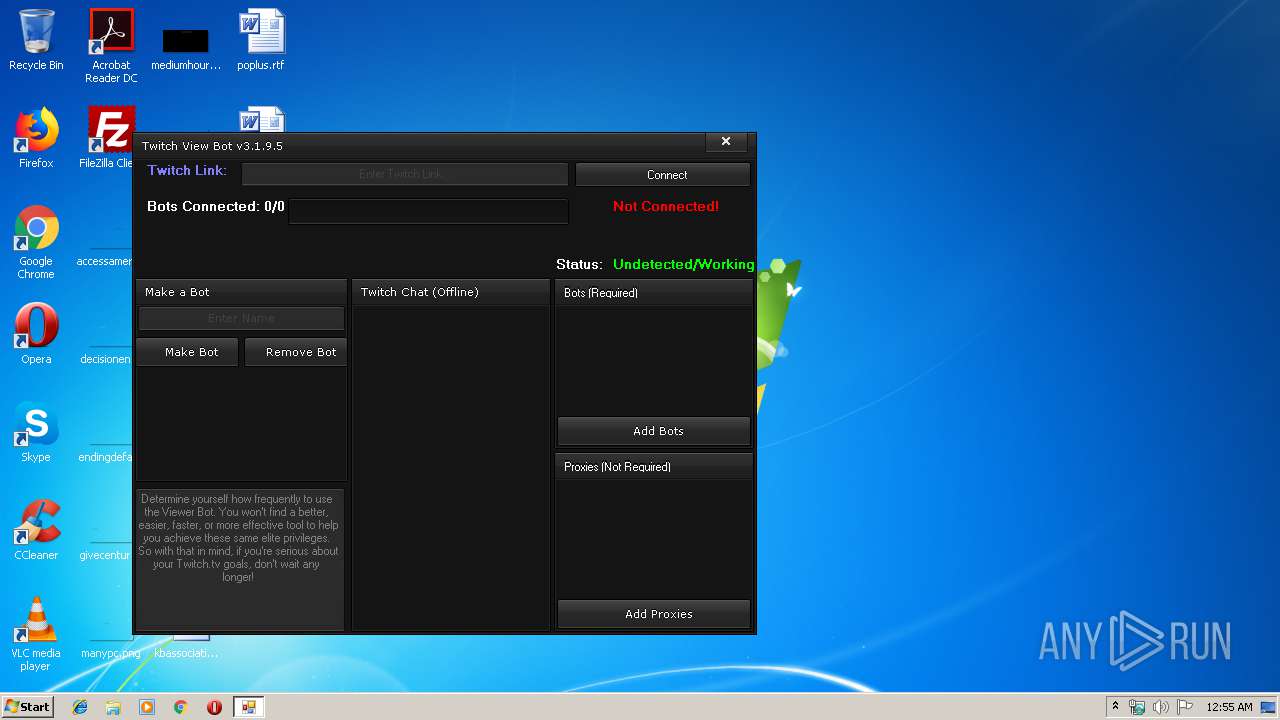
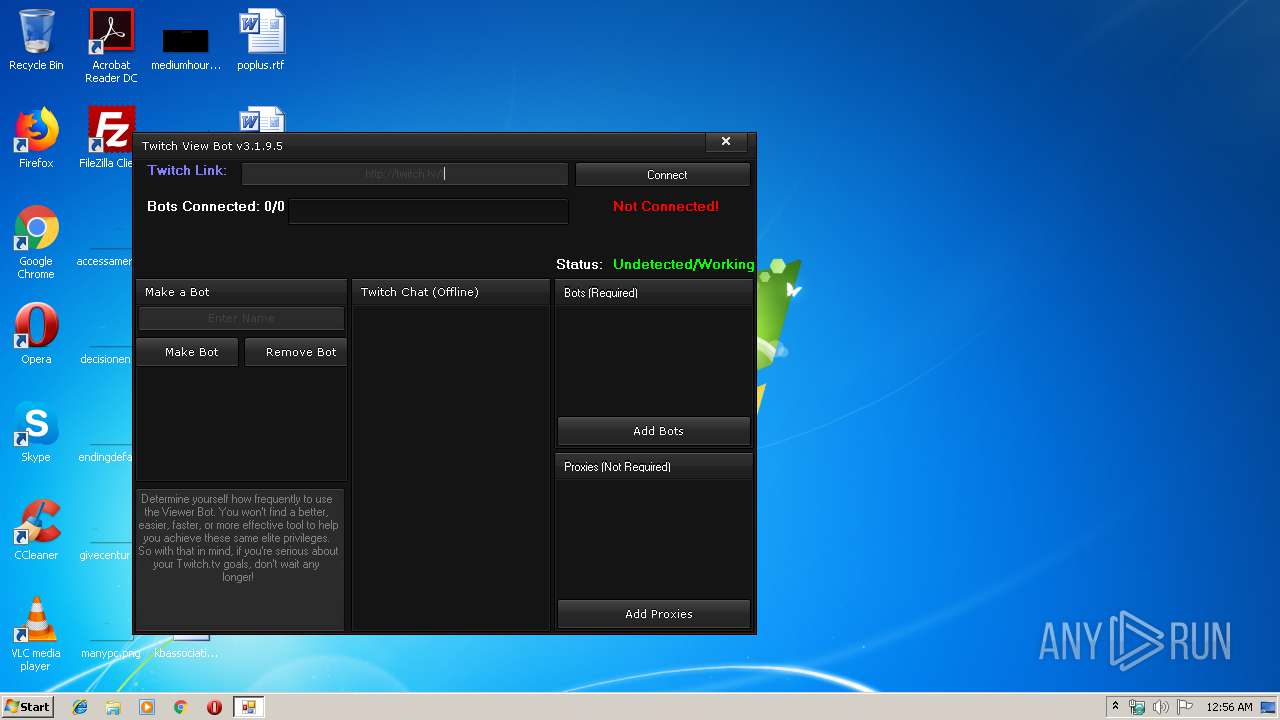
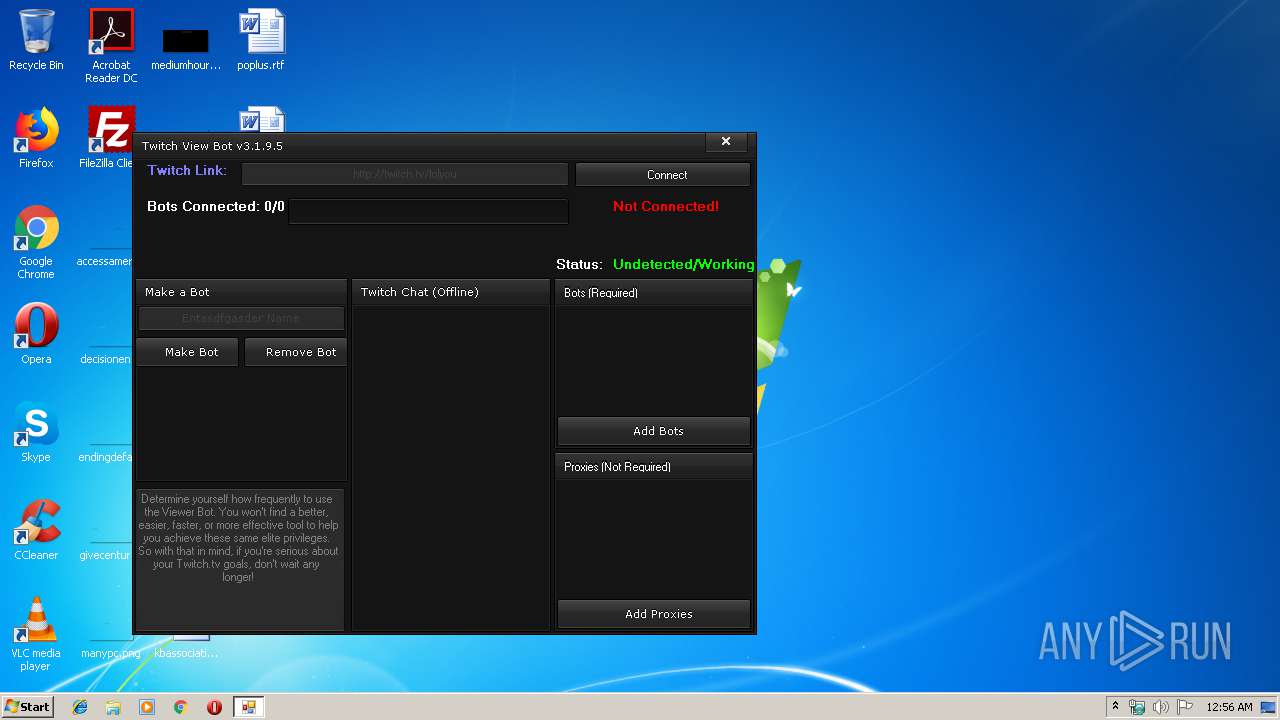
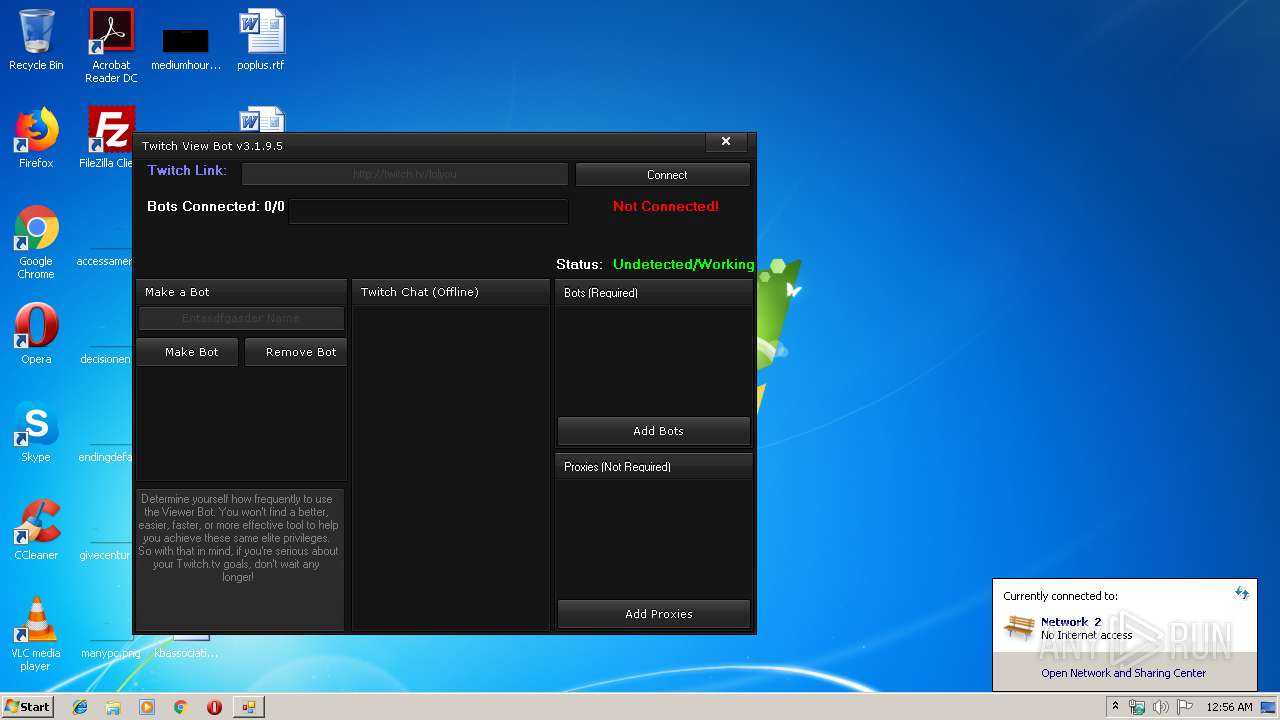
User: admin Integrity Level: MEDIUM Description: Twitch View Bot Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 928 | "C:\Users\admin\AppData\Local\Temp\svhost.exe" | C:\Users\admin\AppData\Local\Temp\svhost.exe | smbsvcs.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 9.0.30729.5420 Modules
| |||||||||||||||
| 1536 | timeout /t 60 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1728 | "C:\Users\admin\AppData\Local\Temp\smbsvcs.exe" | C:\Users\admin\AppData\Local\Temp\smbsvcs.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 0.34 Modules
| |||||||||||||||
| 2212 | "C:\Windows\System32\cmd.exe" /c copy "C:/Users/admin/AppData/Local/Temp/smbsvcs.exe" "%appdata%\winsys\smbsvcs.exe" /Y | C:\Windows\System32\cmd.exe | smbsvcs.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3152 | "C:\Windows\System32\cmd.exe" /c echo [zoneTransfer]ZoneID = 2 > %appdata%\winsys\smbsvcs.exe:Zone.Identifier | C:\Windows\System32\cmd.exe | — | smbsvcs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3836 | "C:\Windows\System32\cmd.exe" /c ren "%appdata%\winsys\smbsvcs.exe.jpg" smbsvcs.exe | C:\Windows\System32\cmd.exe | — | smbsvcs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4092 | cmd /c C:\Users\admin\AppData\Roaming\winsys\smbsvcs.exe.bat | C:\Windows\system32\cmd.exe | — | smbsvcs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
433
Read events
427
Write events
6
Delete events
0
Modification events
| (PID) Process: | (1728) smbsvcs.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1728) smbsvcs.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (928) svhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (928) svhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
Executable files
3
Suspicious files
0
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1728 | smbsvcs.exe | C:\Users\admin\AppData\Local\Temp\twitch1.exe | executable | |
MD5:— | SHA256:— | |||
| 1728 | smbsvcs.exe | C:\Users\admin\AppData\Roaming\winsys\smbsvcs.exe.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1728 | smbsvcs.exe | C:\Users\admin\AppData\Roaming\winsys\smbsvcs.exe.bat | text | |
MD5:— | SHA256:— | |||
| 2212 | cmd.exe | C:\Users\admin\AppData\Roaming\winsys\smbsvcs.exe | executable | |
MD5:— | SHA256:— | |||
| 1728 | smbsvcs.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\smbsvcs.exe.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1728 | smbsvcs.exe | C:\Users\admin\AppData\Local\Temp\svhost.exe | executable | |
MD5:32827E69B293B99013BBBE37D029245D | SHA256:9250B89157770E3AB59A2C7E2DD6B12B3C61D9B7C6620C3B4727E4BFFF10F01F | |||
| 3152 | cmd.exe | C:\Users\admin\AppData\Roaming\winsys\smbsvcs.exe:Zone.Identifier | text | |
MD5:130A75A932A2FE57BFEA6A65B88DA8F6 | SHA256:F2B79CAE559D6772AFC1C2ED9468988178F8B6833D5028A15DEA73CE47D0196E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
928 | svhost.exe | 185.16.207.4:5200 | — | Bandwidth Technologies Ltd | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |