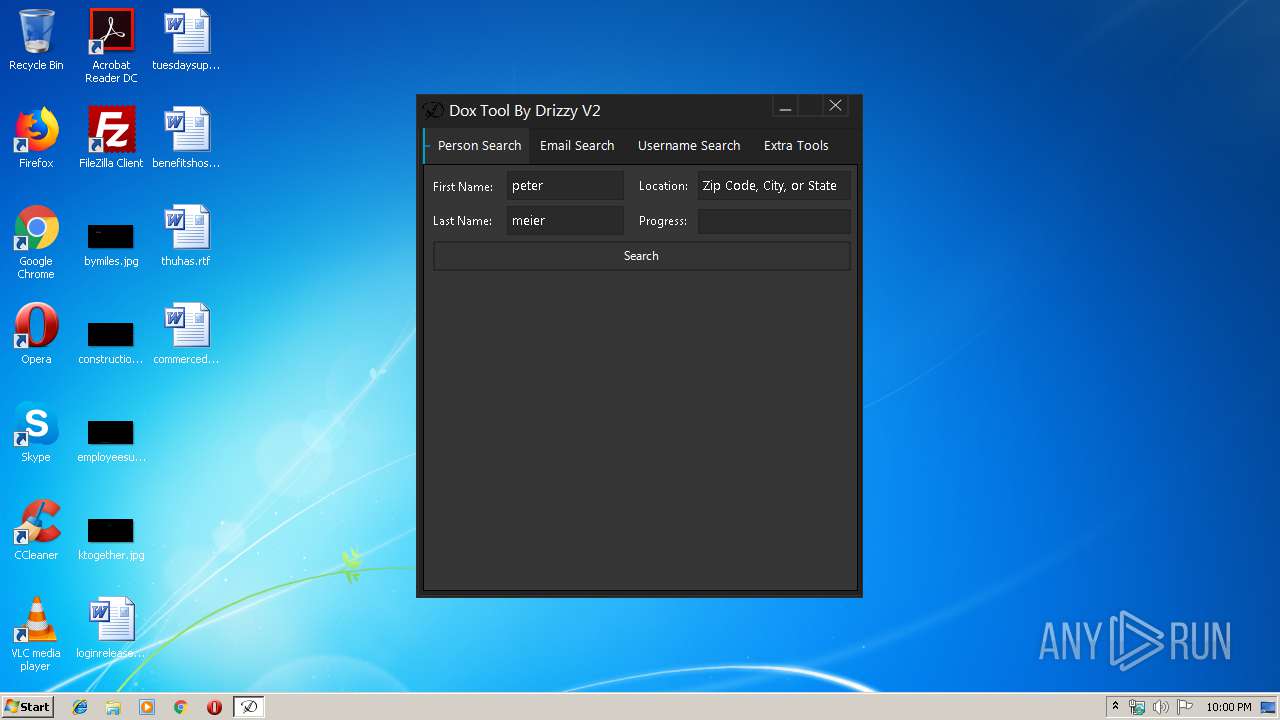
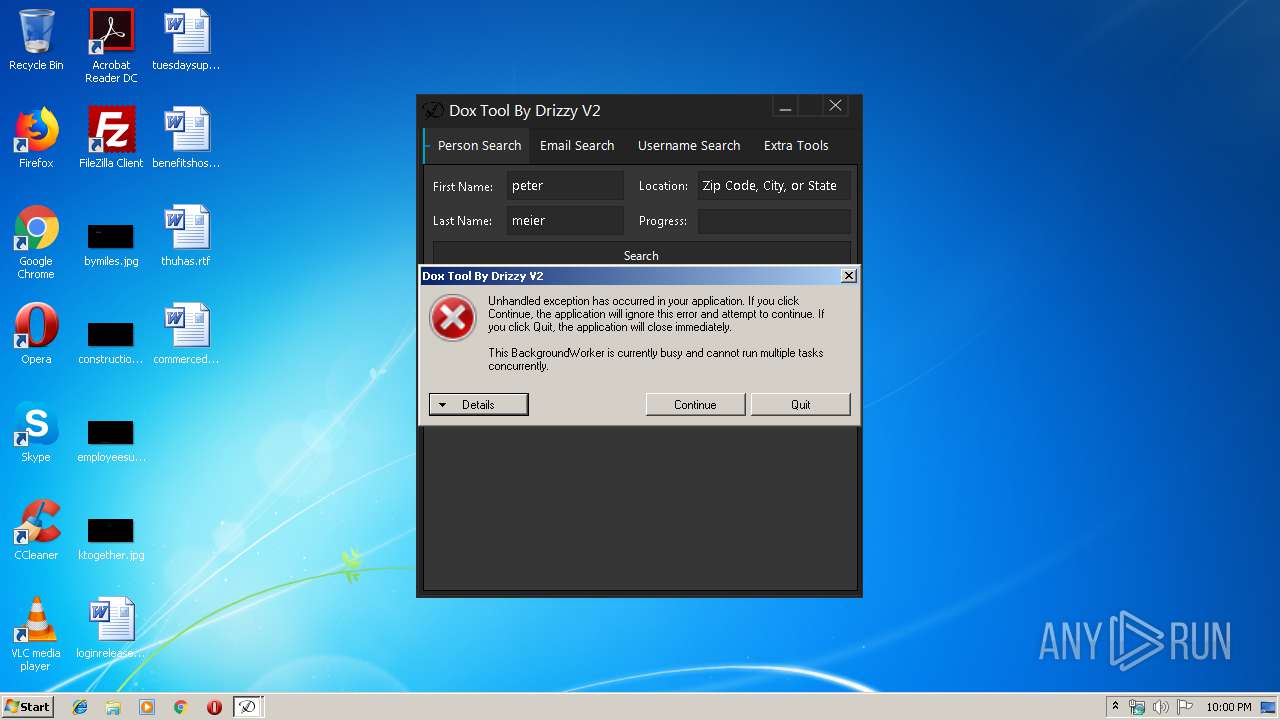
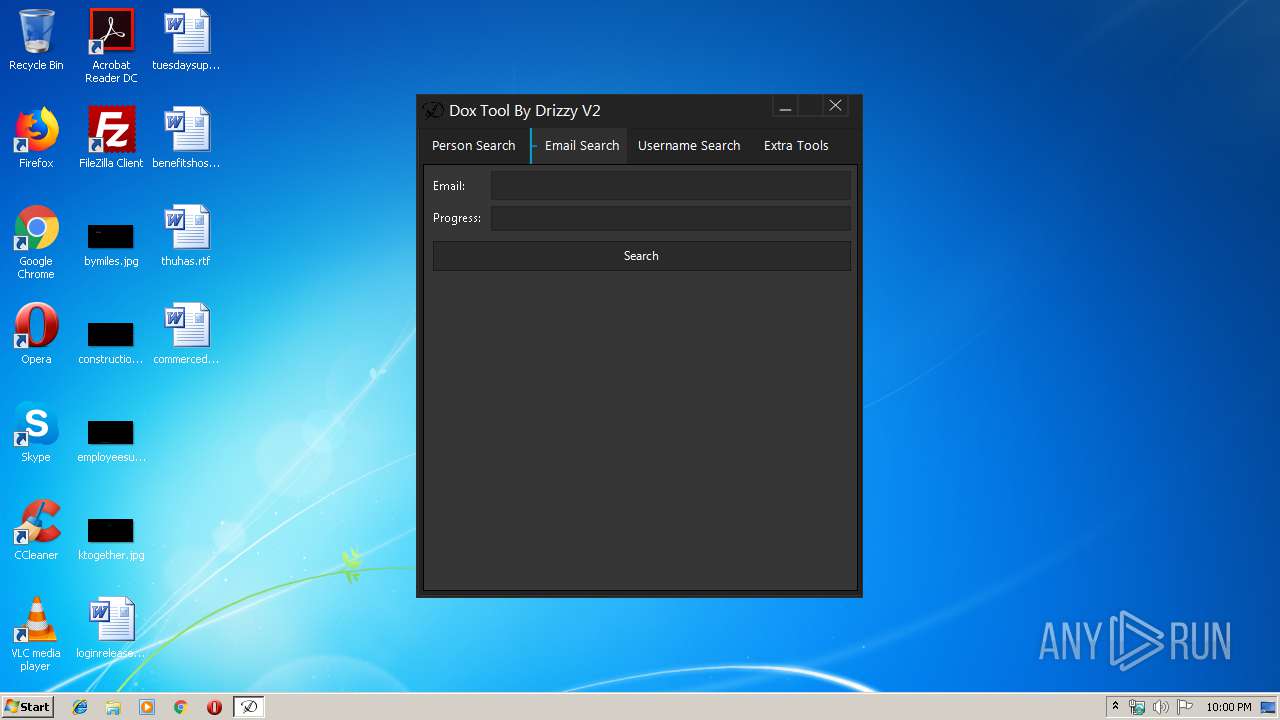
| File name: | Doxtool.exe |
| Full analysis: | https://app.any.run/tasks/14f58d21-67b0-41df-9c74-f01675e12d68 |
| Verdict: | No threats detected |
| Analysis date: | November 12, 2019, 21:59:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 578320B3A257D683631543D86230470D |
| SHA1: | 10A64C18573BC14E7FCB7DD9D4A584A9692E6744 |
| SHA256: | 79CF470EB6BC450E26AF11FE3DECAB3039765BD72612EB792922172CD1481592 |
| SSDEEP: | 3072:jOBcgIbP9ix7o2eHTs/yT9TVfSMYoH4otOc:7nbPZ2eHTs/s9JfDYohO |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (55.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21) |
| .scr | | | Windows screen saver (9.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:05 20:14:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 166400 |
| InitializedDataSize: | 28672 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2a9ea |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
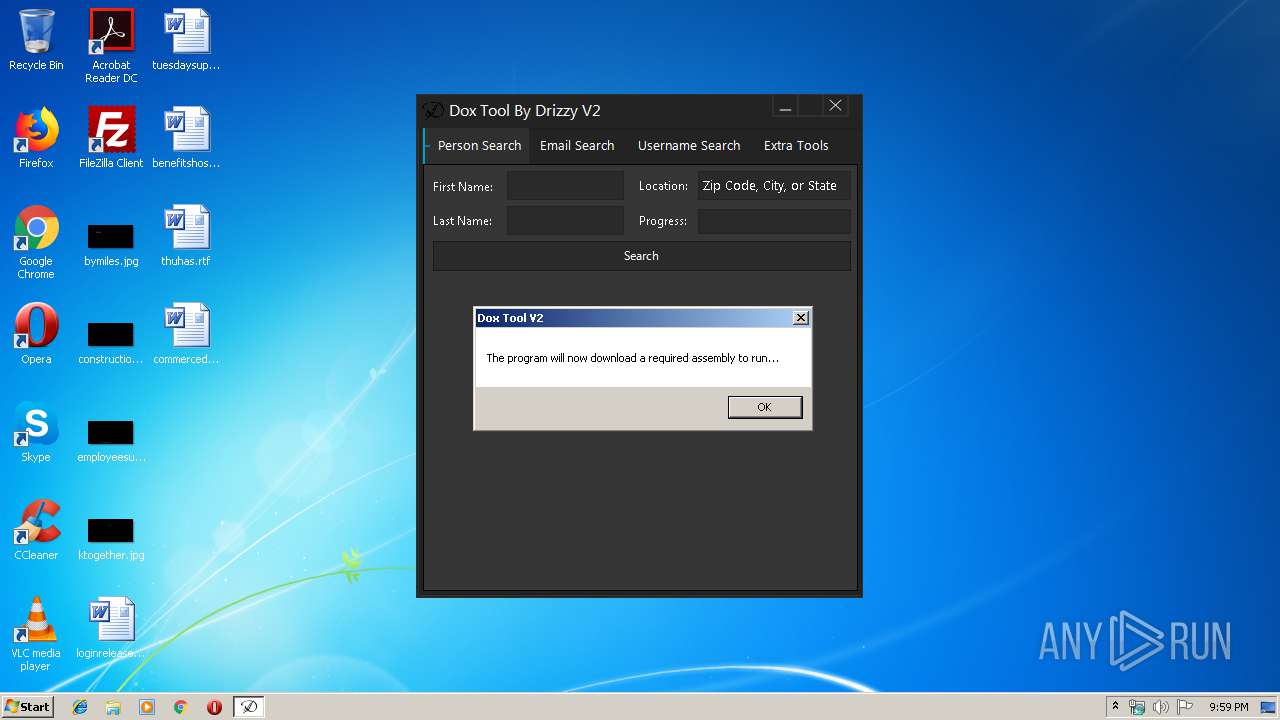
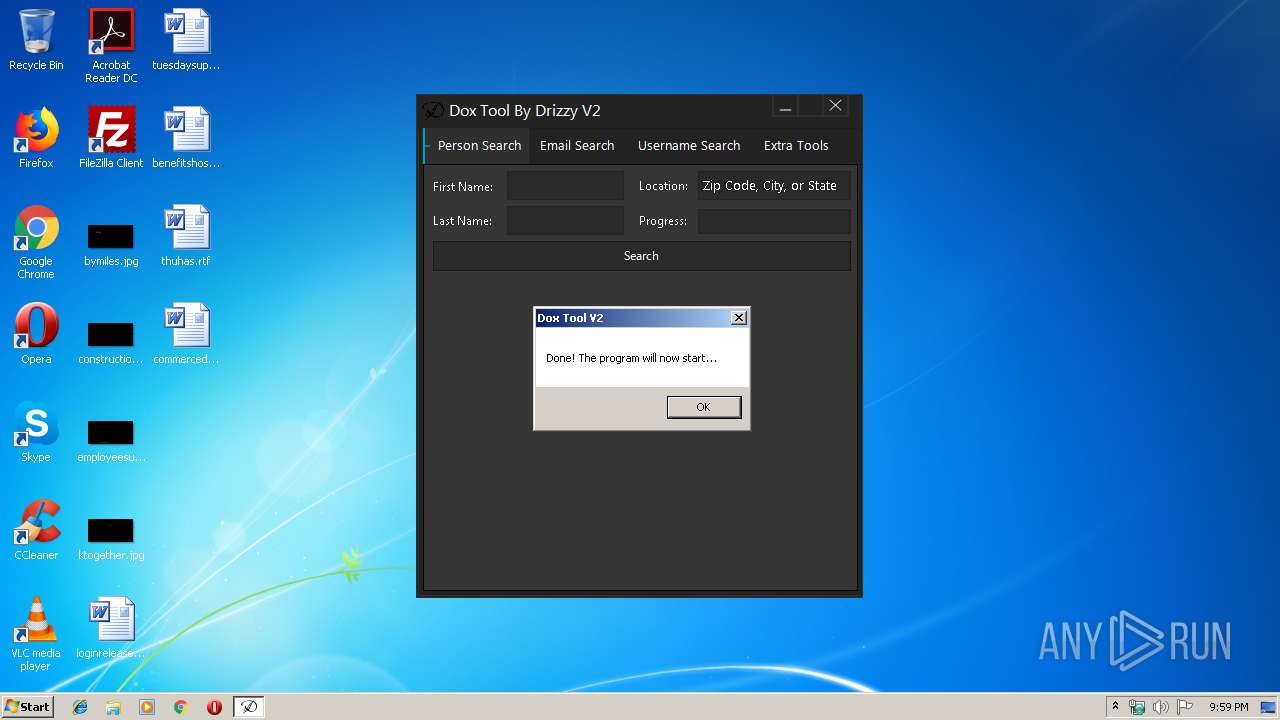
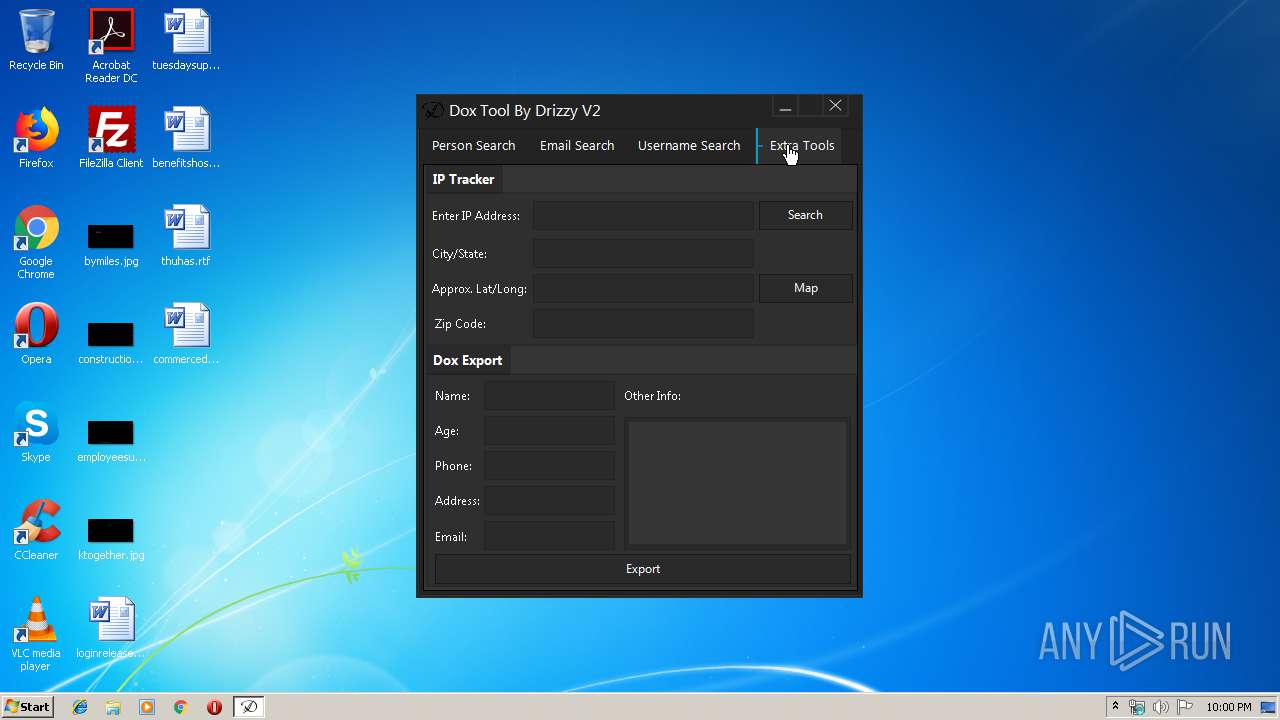
| FileDescription: | Dox Tool V2 |
| FileVersion: | 2.0.0.0 |
| InternalName: | Dox Tool V2.exe |
| LegalCopyright: | Copyright © 2016 |
| LegalTrademarks: | - |
| OriginalFileName: | Dox Tool V2.exe |
| ProductName: | Dox Tool V2 |
| ProductVersion: | 2.0.0.0 |
| AssemblyVersion: | 2.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Jul-2016 18:14:43 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Dox Tool V2 |
| FileVersion: | 2.0.0.0 |
| InternalName: | Dox Tool V2.exe |
| LegalCopyright: | Copyright © 2016 |
| LegalTrademarks: | - |
| OriginalFilename: | Dox Tool V2.exe |
| ProductName: | Dox Tool V2 |
| ProductVersion: | 2.0.0.0 |
| Assembly Version: | 2.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 05-Jul-2016 18:14:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000289F0 | 0x00028A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.50246 |
.rsrc | 0x0002C000 | 0x00006D20 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.19563 |
.reloc | 0x00034000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.29478 | 812 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 1.09353 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 1.24794 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 1.3723 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 1.52287 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.64638 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
34
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Users\admin\AppData\Local\Temp\Doxtool.exe" | C:\Users\admin\AppData\Local\Temp\Doxtool.exe | explorer.exe | ||||||||||||
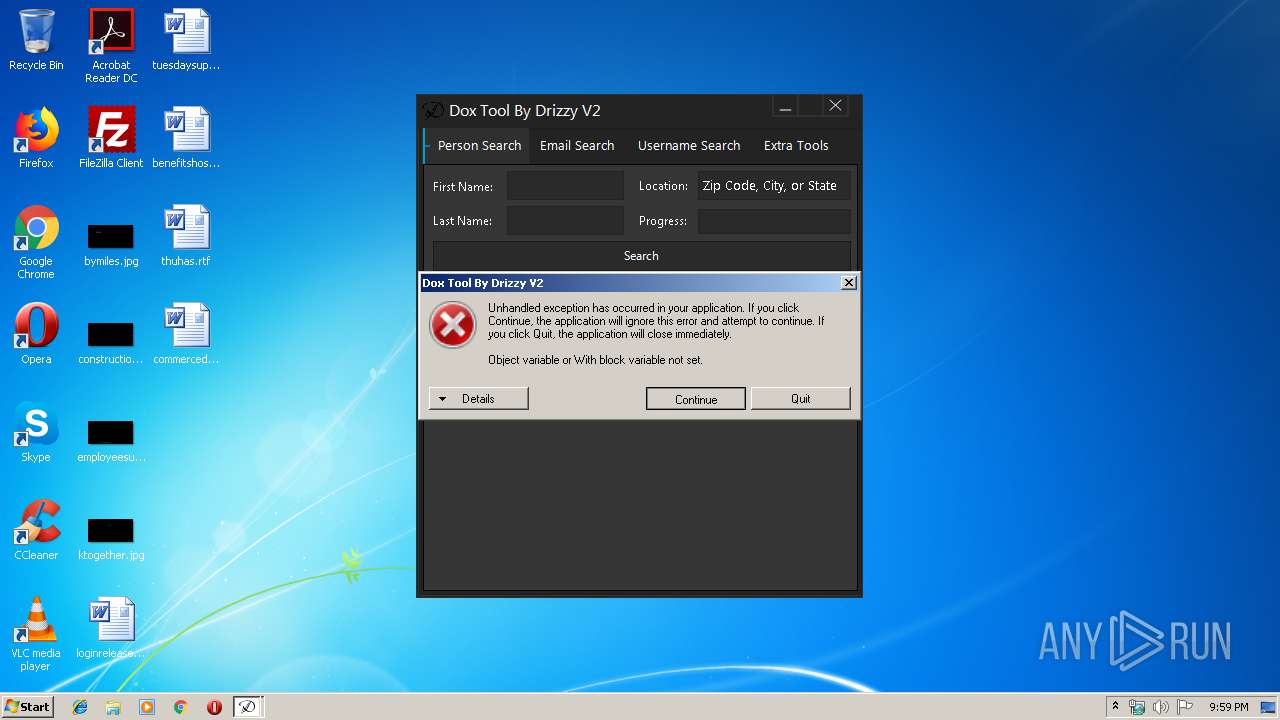
User: admin Integrity Level: MEDIUM Description: Dox Tool V2 Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
Total events
63
Read events
36
Write events
27
Delete events
0
Modification events
| (PID) Process: | (504) Doxtool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Doxtool_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (504) Doxtool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Doxtool_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (504) Doxtool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Doxtool_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (504) Doxtool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Doxtool_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (504) Doxtool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Doxtool_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (504) Doxtool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Doxtool_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (504) Doxtool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Doxtool_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (504) Doxtool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Doxtool_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (504) Doxtool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Doxtool_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (504) Doxtool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Doxtool_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
4
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 504 | Doxtool.exe | C:\Users\admin\AppData\Local\Temp\CabCC7.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | Doxtool.exe | C:\Users\admin\AppData\Local\Temp\TarCC8.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | Doxtool.exe | C:\Users\admin\AppData\Local\Temp\CabCC9.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | Doxtool.exe | C:\Users\admin\AppData\Local\Temp\TarCCA.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | Doxtool.exe | C:\Users\admin\AppData\Local\Temp\CabD58.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | Doxtool.exe | C:\Users\admin\AppData\Local\Temp\TarD59.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | Doxtool.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94308059B57B3142E455B38A6EB92015 | binary | |
MD5:— | SHA256:— | |||
| 504 | Doxtool.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\94308059B57B3142E455B38A6EB92015 | compressed | |
MD5:5AD071A3917588E8CD883B123B395B21 | SHA256:DE62965C15528DA598B0079D2D20D953DD6F71B13A23807BFF0666D03F69C0FA | |||
| 504 | Doxtool.exe | C:\Users\admin\AppData\Local\Temp\Newtonsoft.Json.dll | html | |
MD5:BD86FD629A5A134239668827AD08EA3B | SHA256:F996E7BFD10C1FAA5C8C8232E11E22E3B4C1BF4F2F39FC80A9A1D42FDEE182F6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
7
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
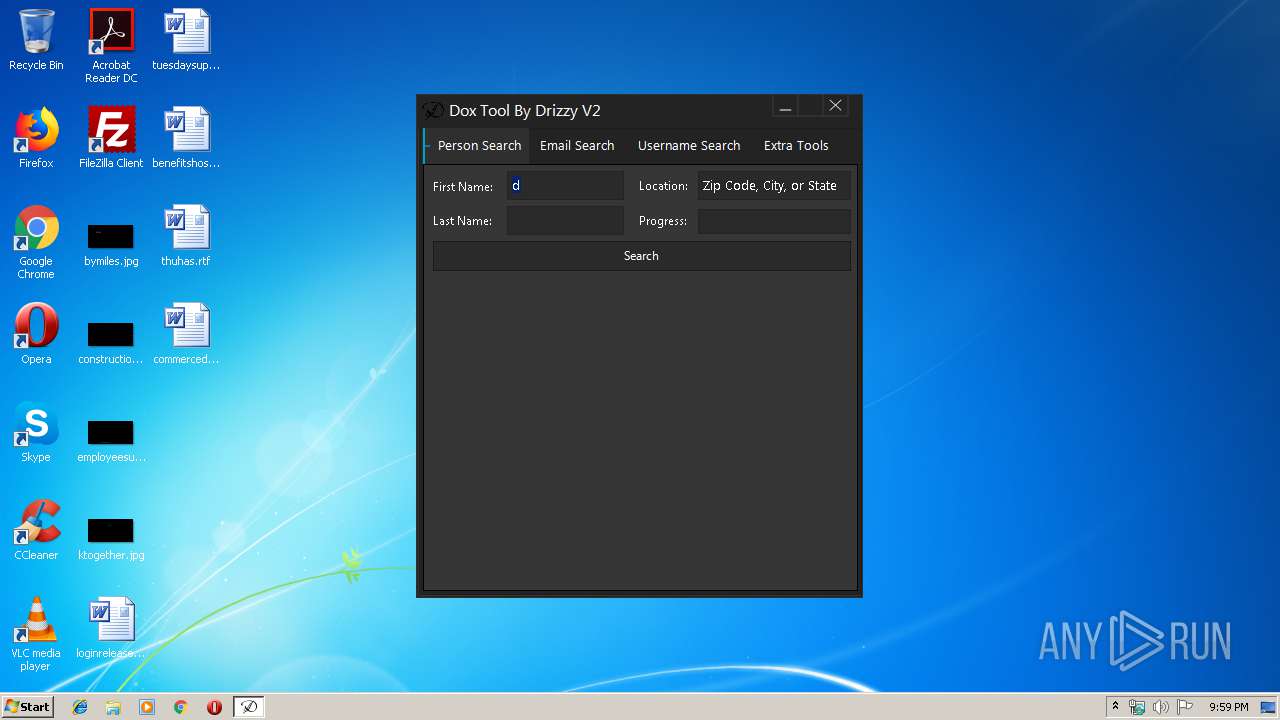
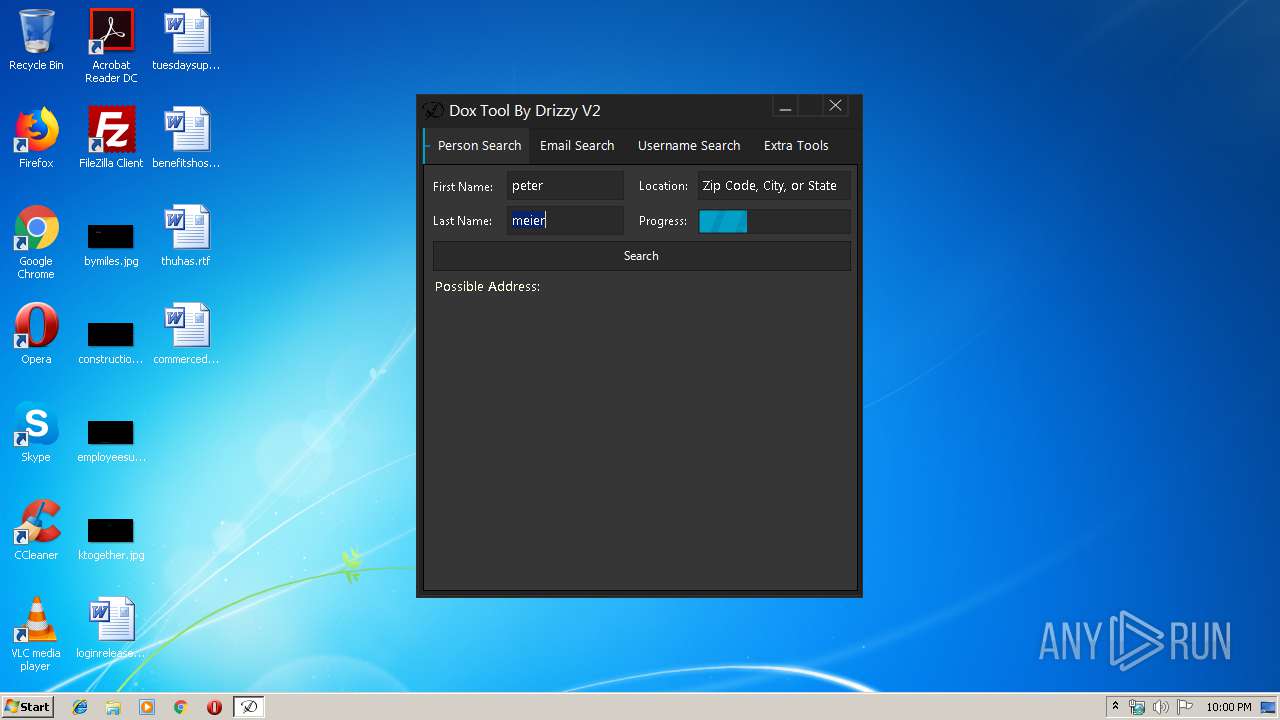
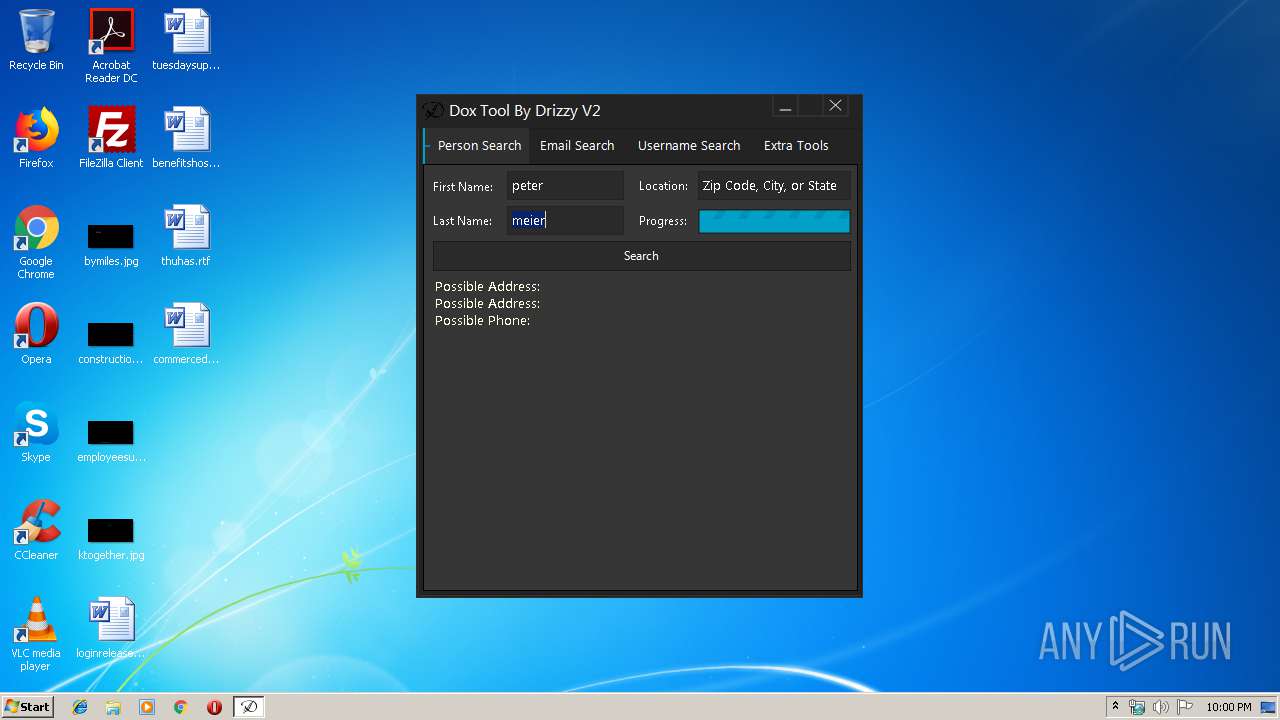
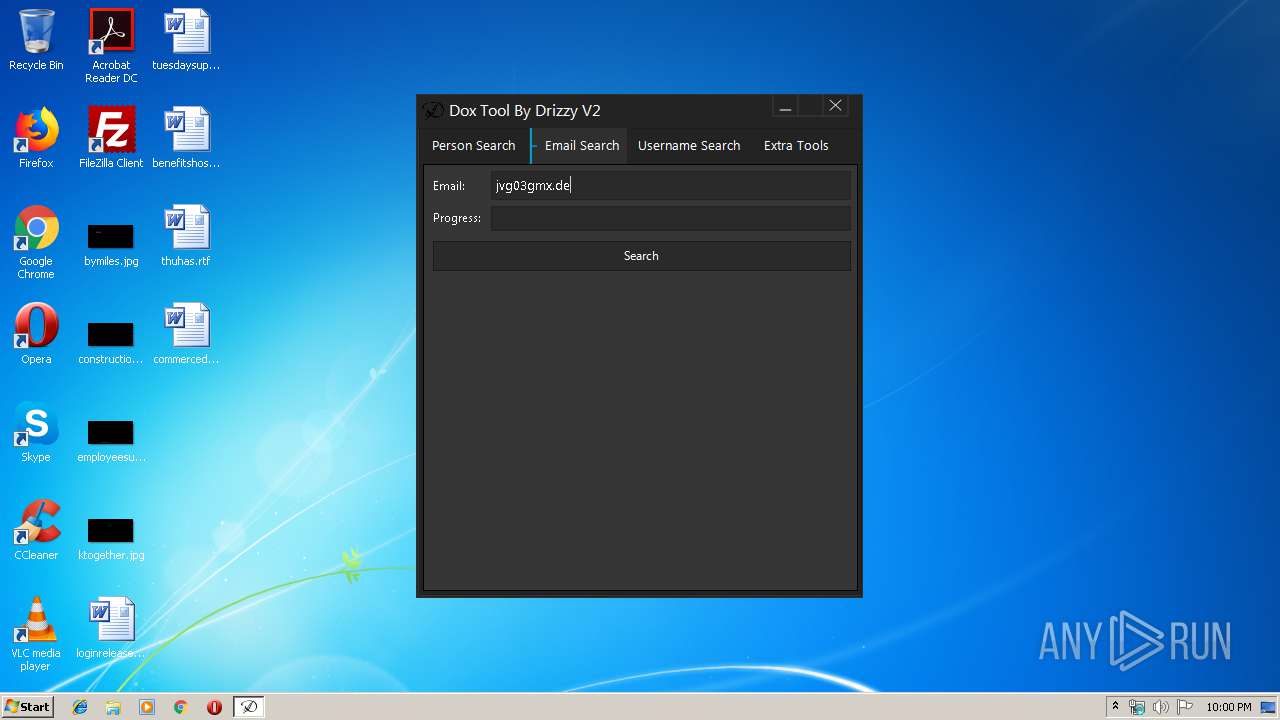
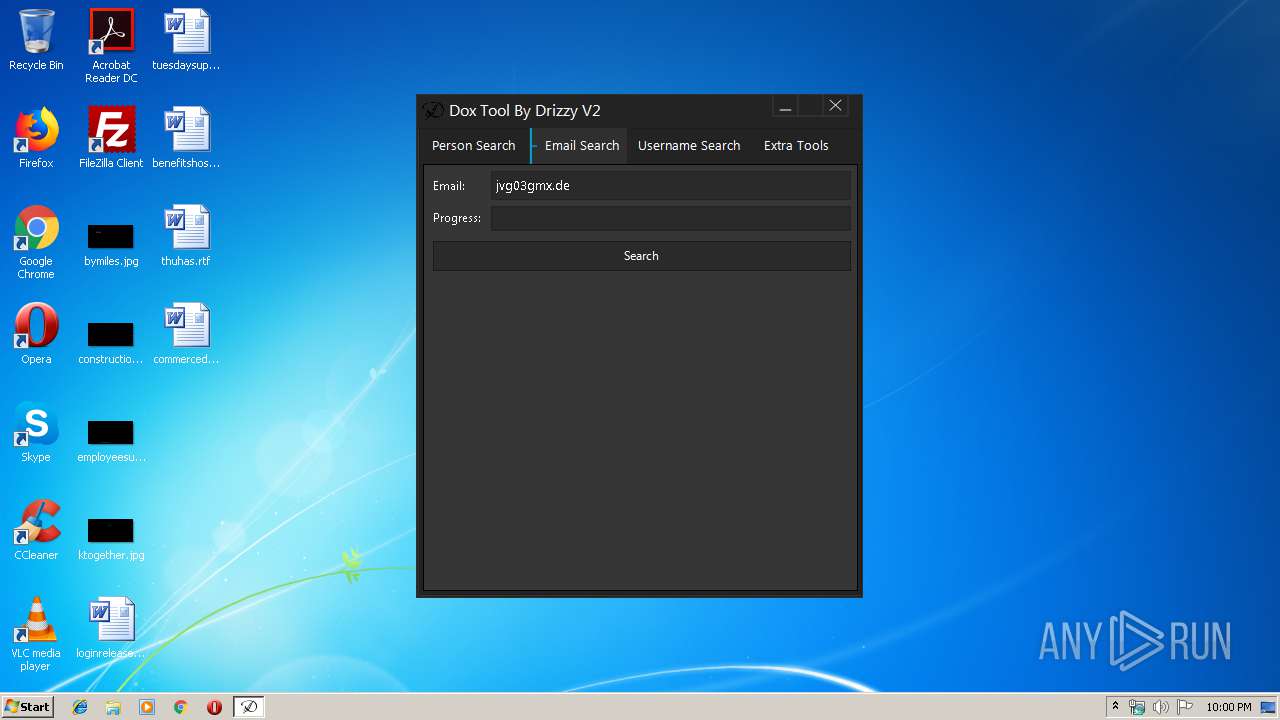
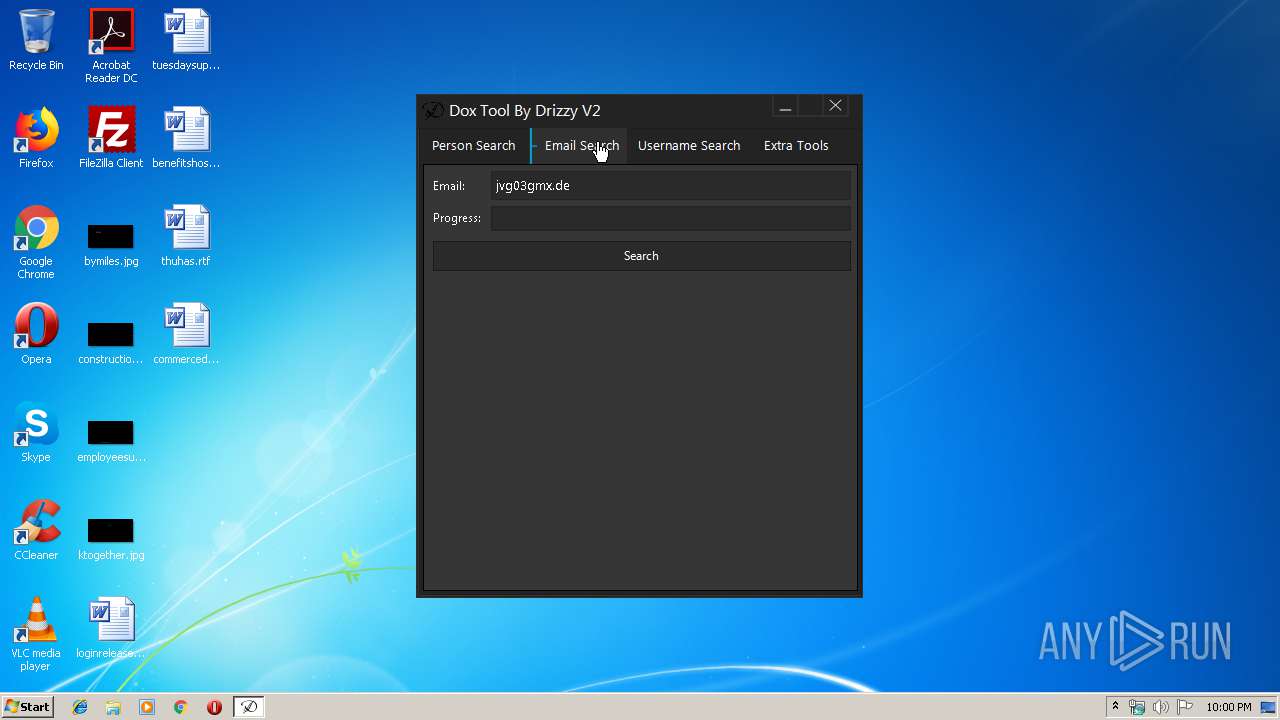
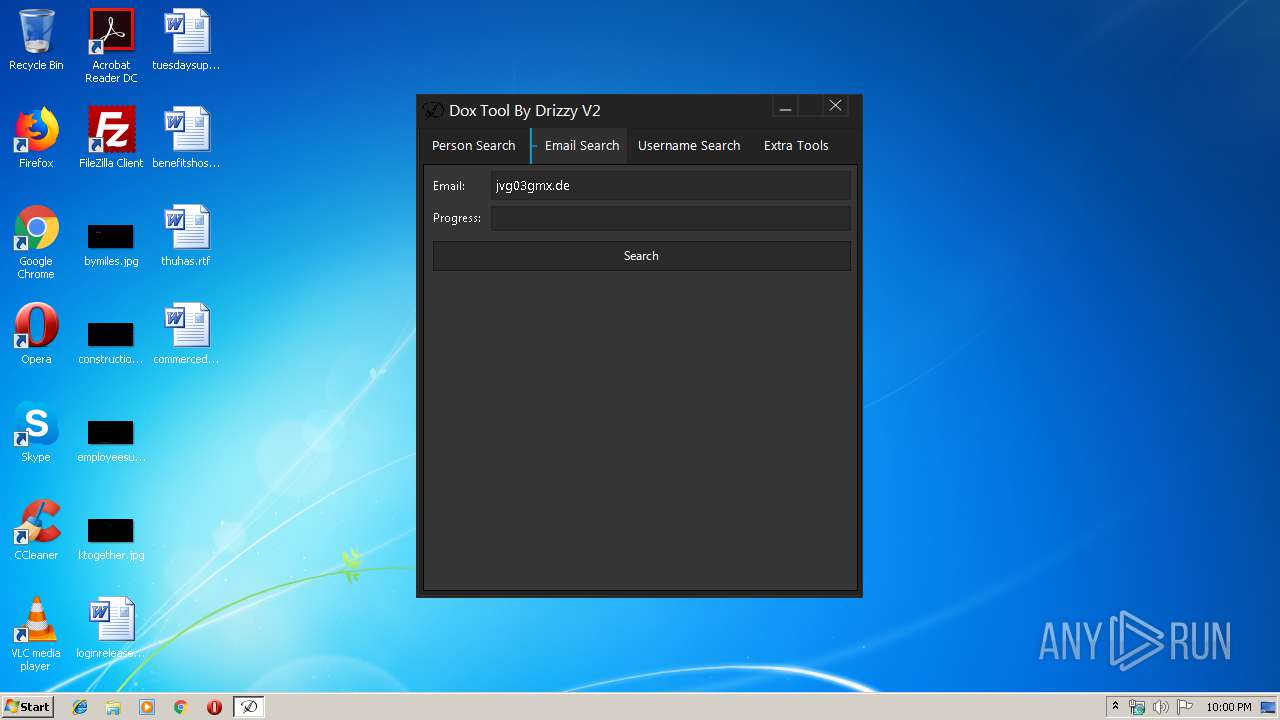
504 | Doxtool.exe | GET | 301 | 208.115.108.116:80 | http://www.zabasearch.com/people/peter+meier/Zip%20Code,%20City,%20or%20State | US | — | — | malicious |
504 | Doxtool.exe | GET | 200 | 52.38.68.18:80 | http://www.411.com/name/peter-meier/Zip%20Code,%20City,%20or%20State | US | html | 1.37 Kb | unknown |
504 | Doxtool.exe | GET | 200 | 8.253.95.249:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
504 | Doxtool.exe | 104.24.127.84:80 | drizzybot.com | Cloudflare Inc | US | shared |
504 | Doxtool.exe | 169.45.189.53:80 | 10digits.us | SoftLayer Technologies Inc. | NL | unknown |
504 | Doxtool.exe | 107.154.108.166:443 | whitepages.plus | Incapsula Inc | US | unknown |
504 | Doxtool.exe | 52.38.68.18:80 | www.411.com | Amazon.com, Inc. | US | unknown |
504 | Doxtool.exe | 208.115.108.116:80 | www.zabasearch.com | Wowrack.com | US | unknown |
504 | Doxtool.exe | 208.115.108.116:443 | www.zabasearch.com | Wowrack.com | US | unknown |
504 | Doxtool.exe | 8.253.95.249:80 | www.download.windowsupdate.com | Global Crossing | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
drizzybot.com |
| malicious |
10digits.us |
| unknown |
whitepages.plus |
| suspicious |
www.411.com |
| unknown |
www.zabasearch.com |
| malicious |
www.download.windowsupdate.com |
| whitelisted |