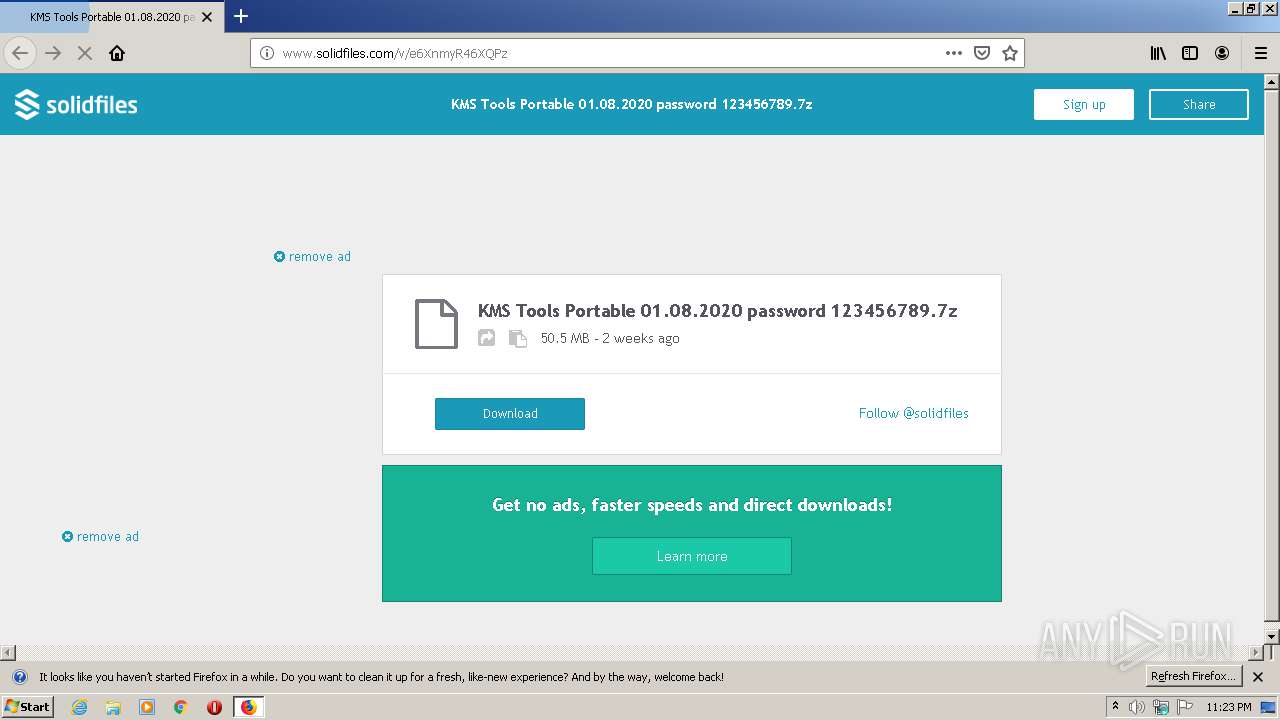
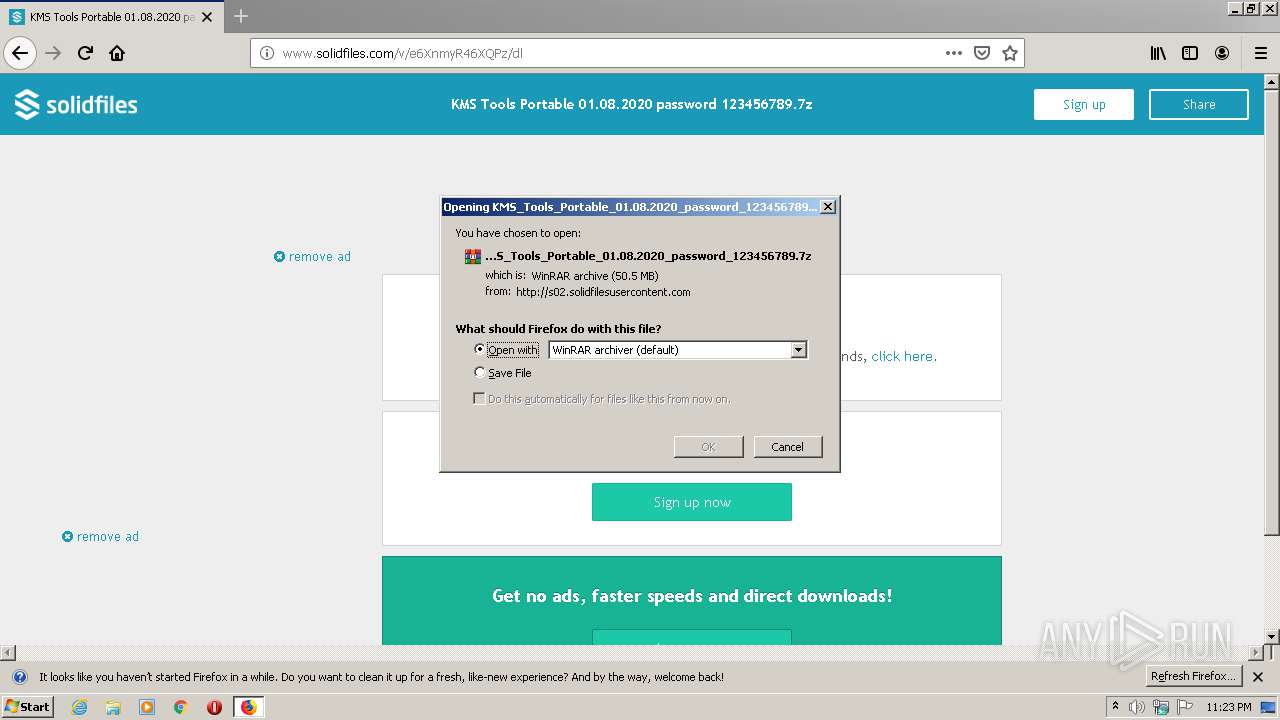
| URL: | http://www.solidfiles.com/v/e6XnmyR46XQPz |
| Full analysis: | https://app.any.run/tasks/28db40cb-888c-4ac9-8c60-91c68bebb51e |
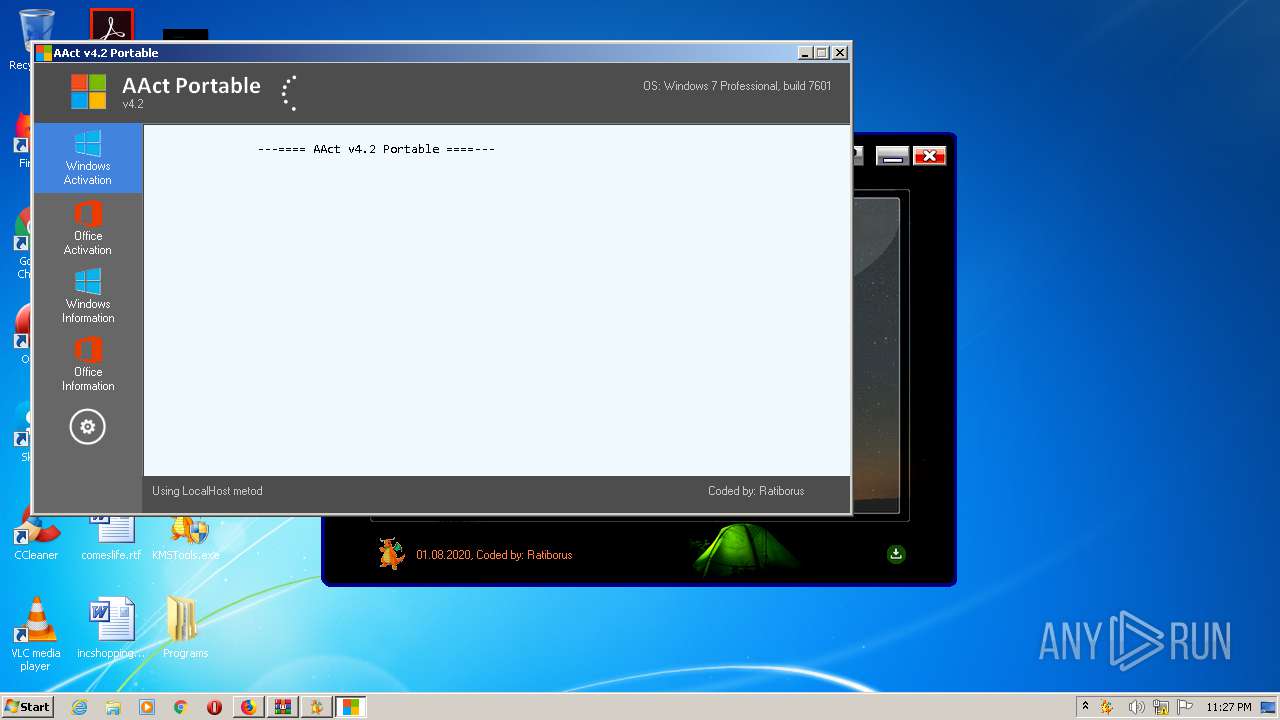
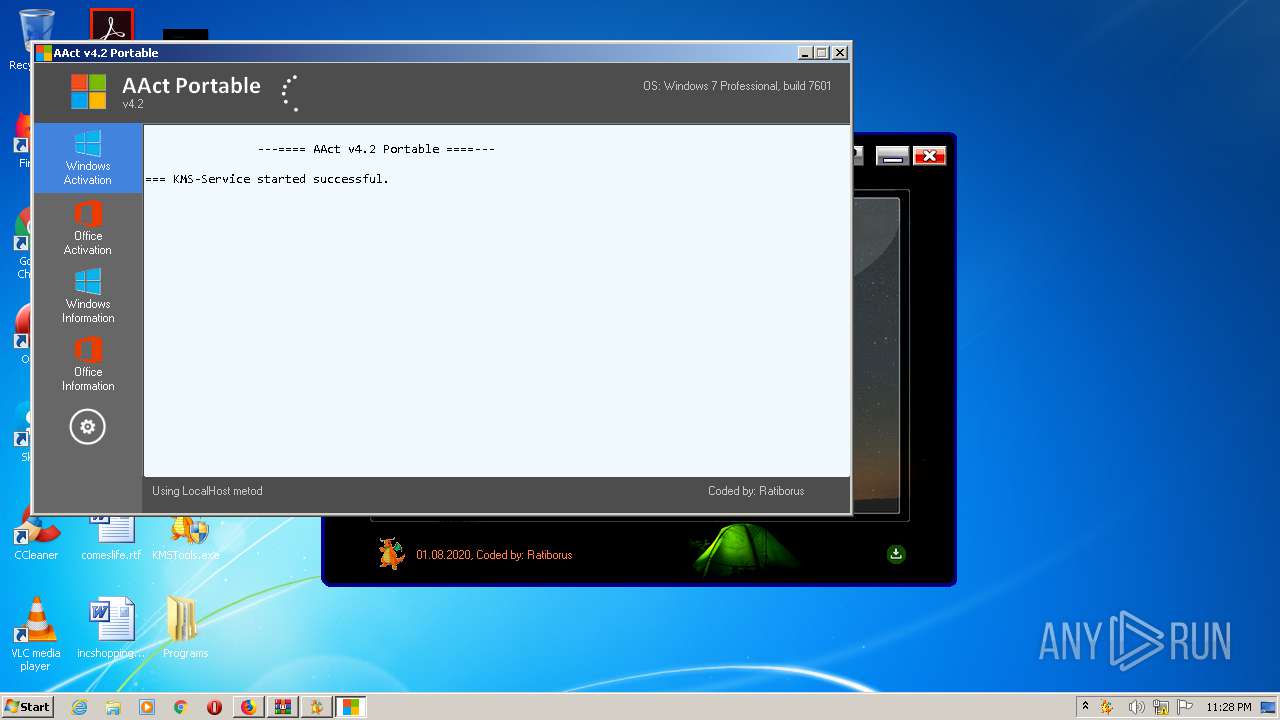
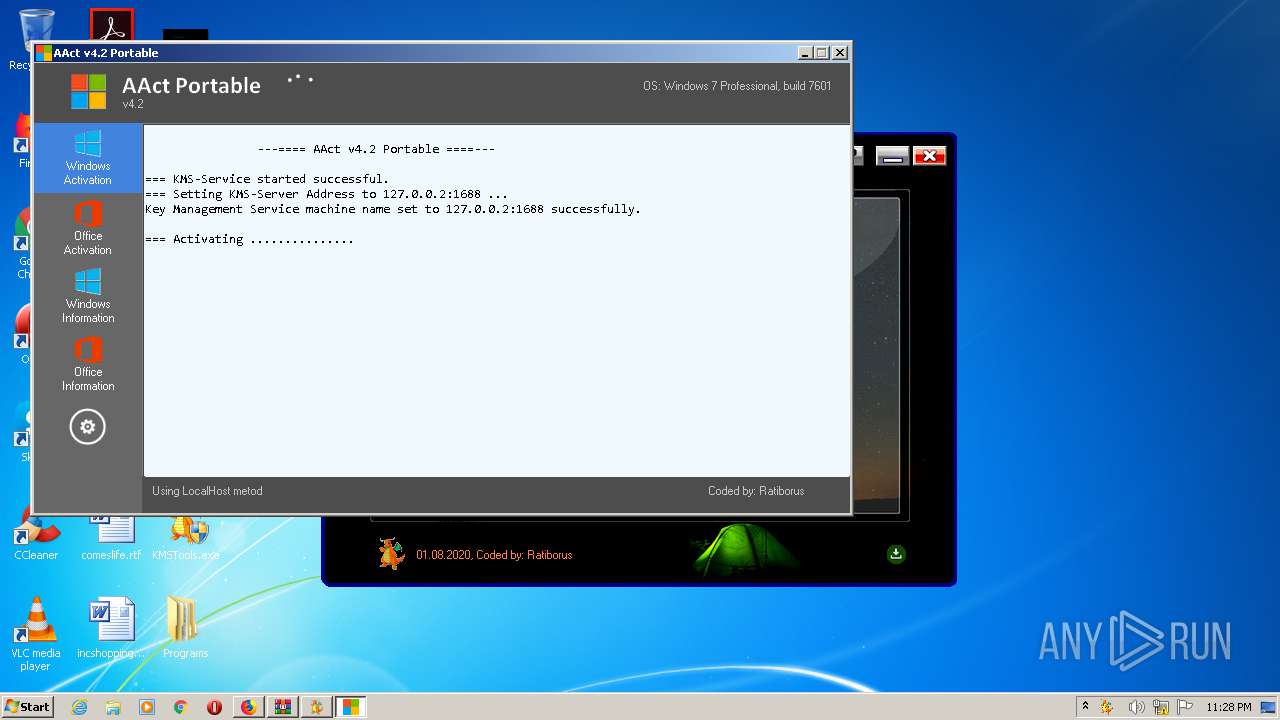
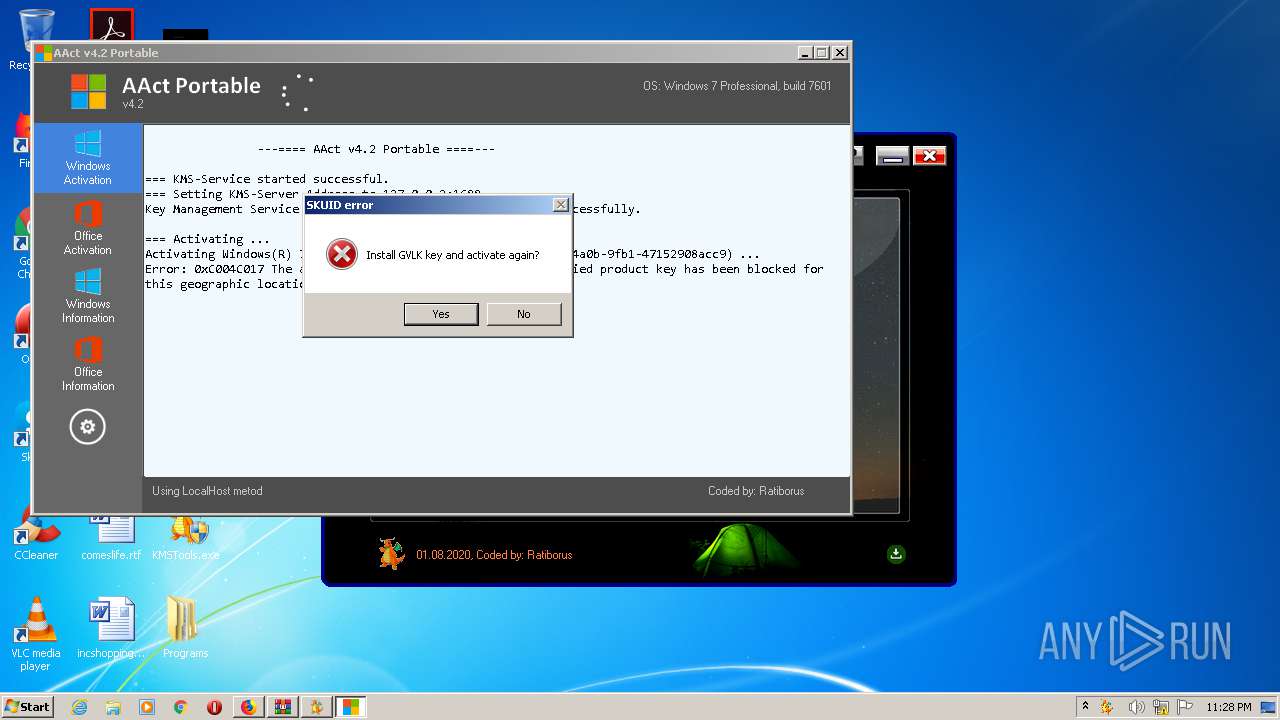
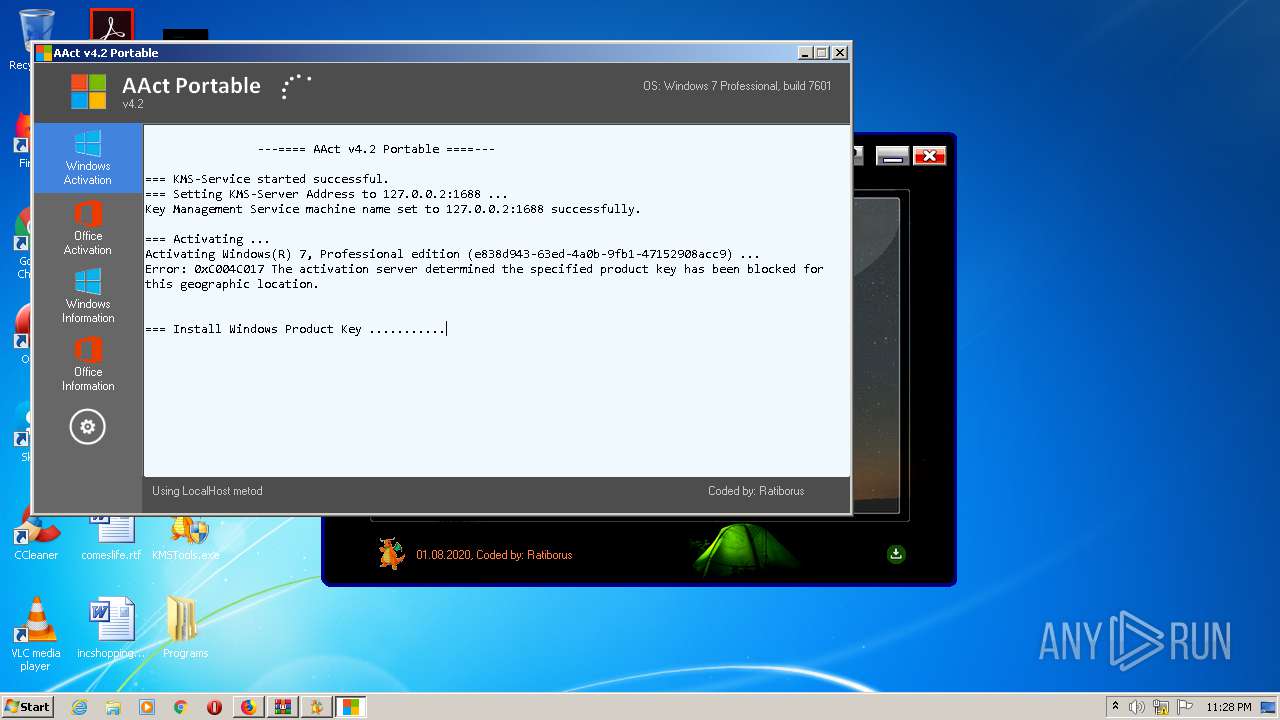
| Verdict: | Malicious activity |
| Analysis date: | August 15, 2020, 22:23:24 |
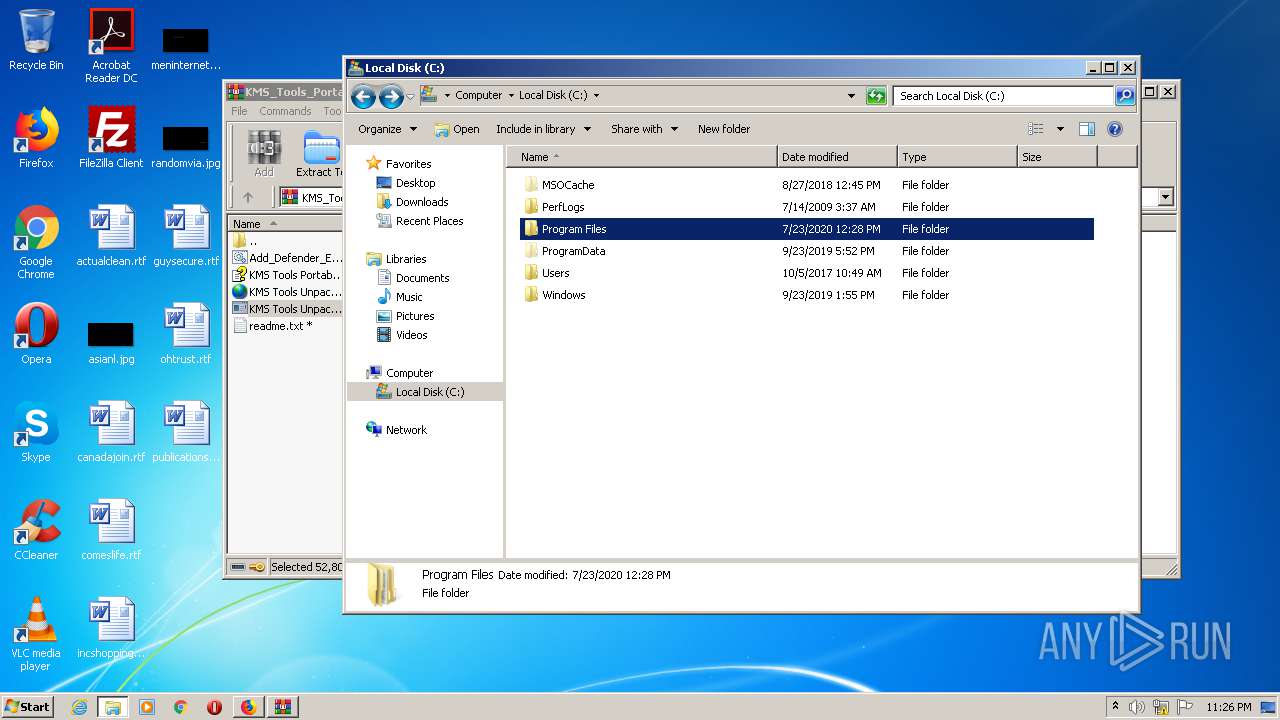
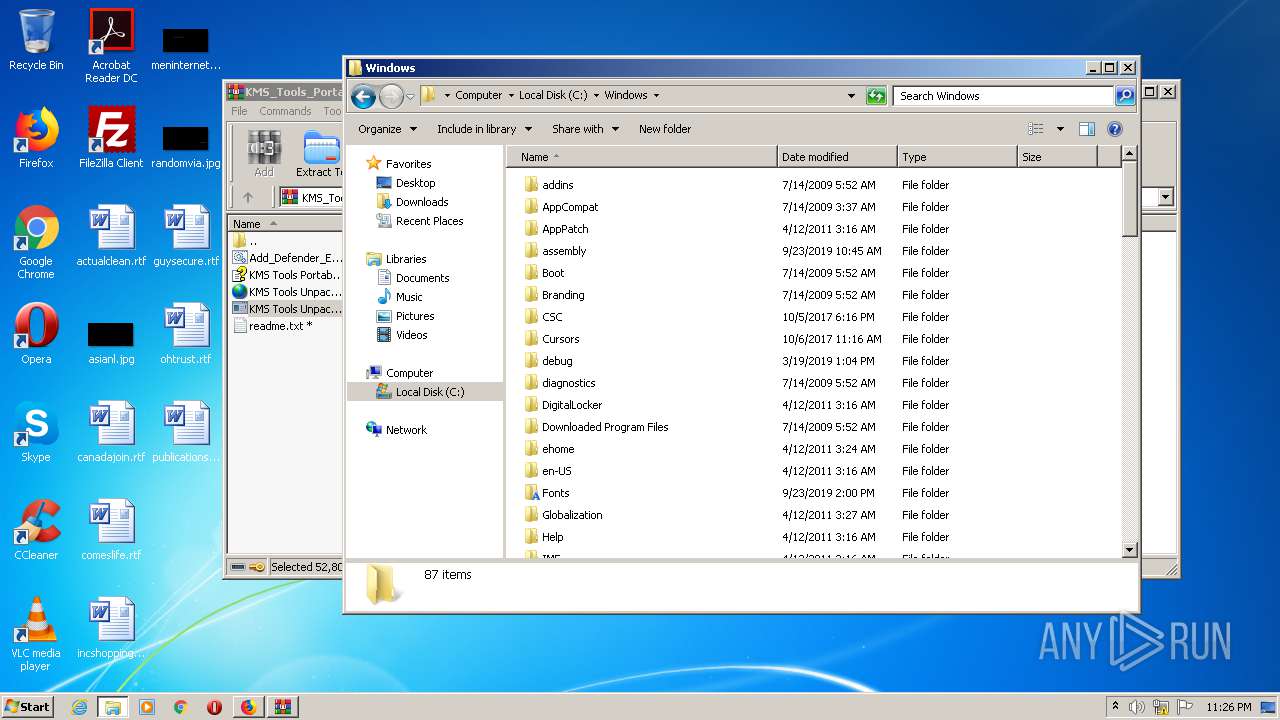
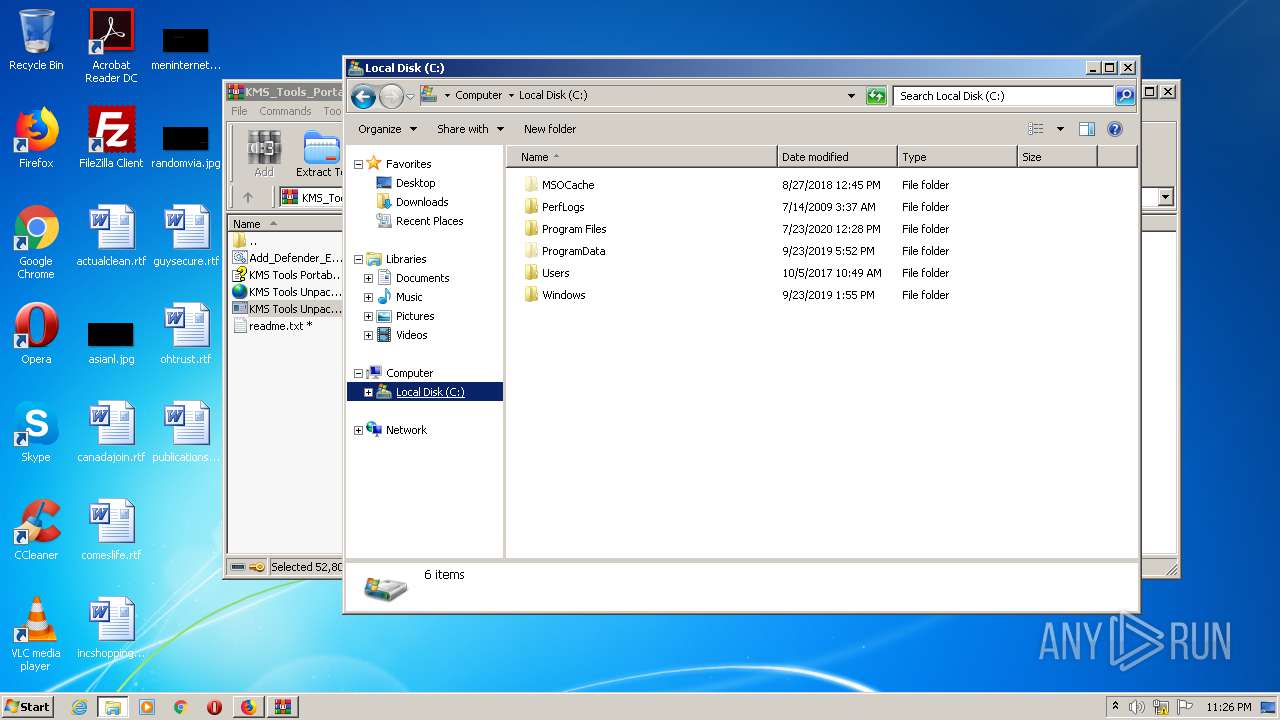
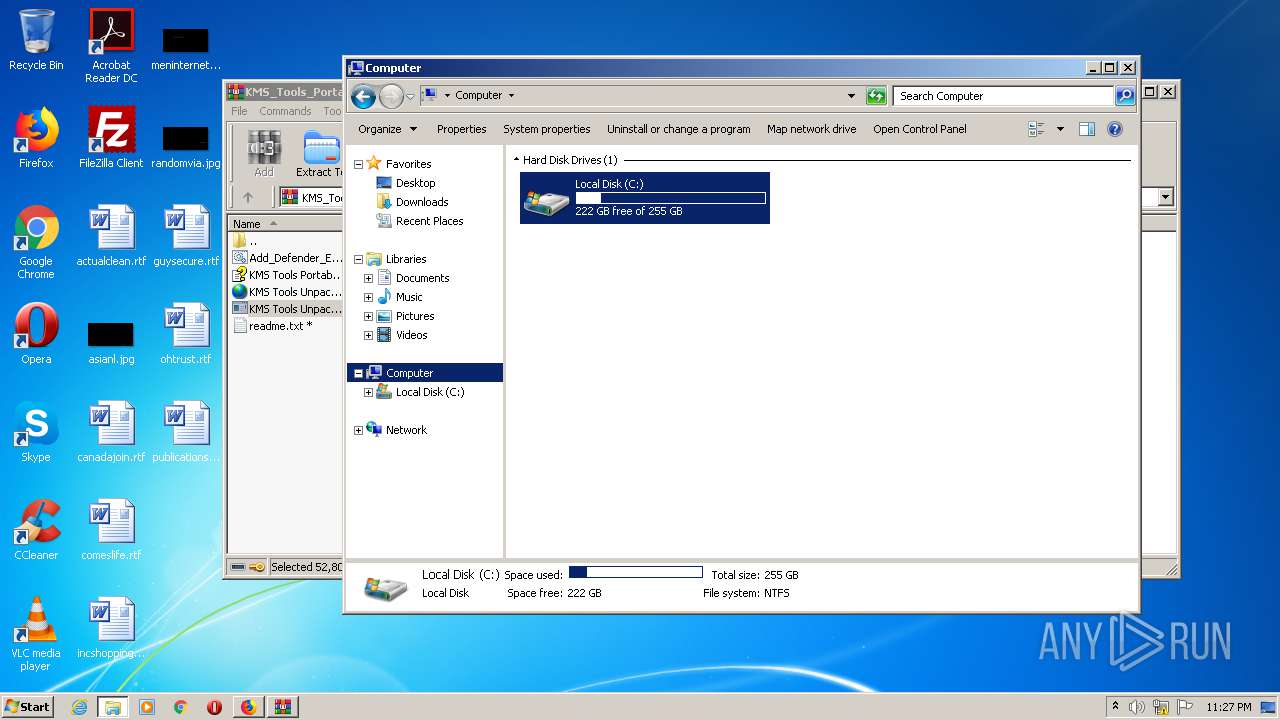
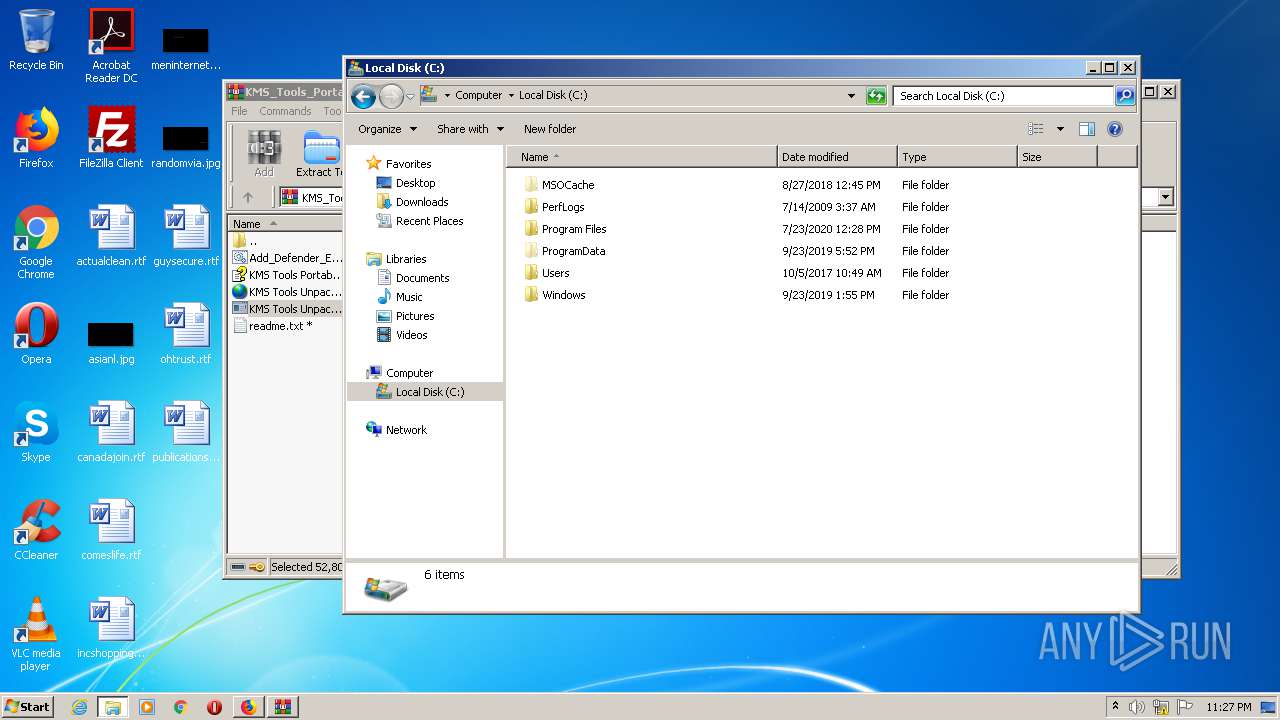
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
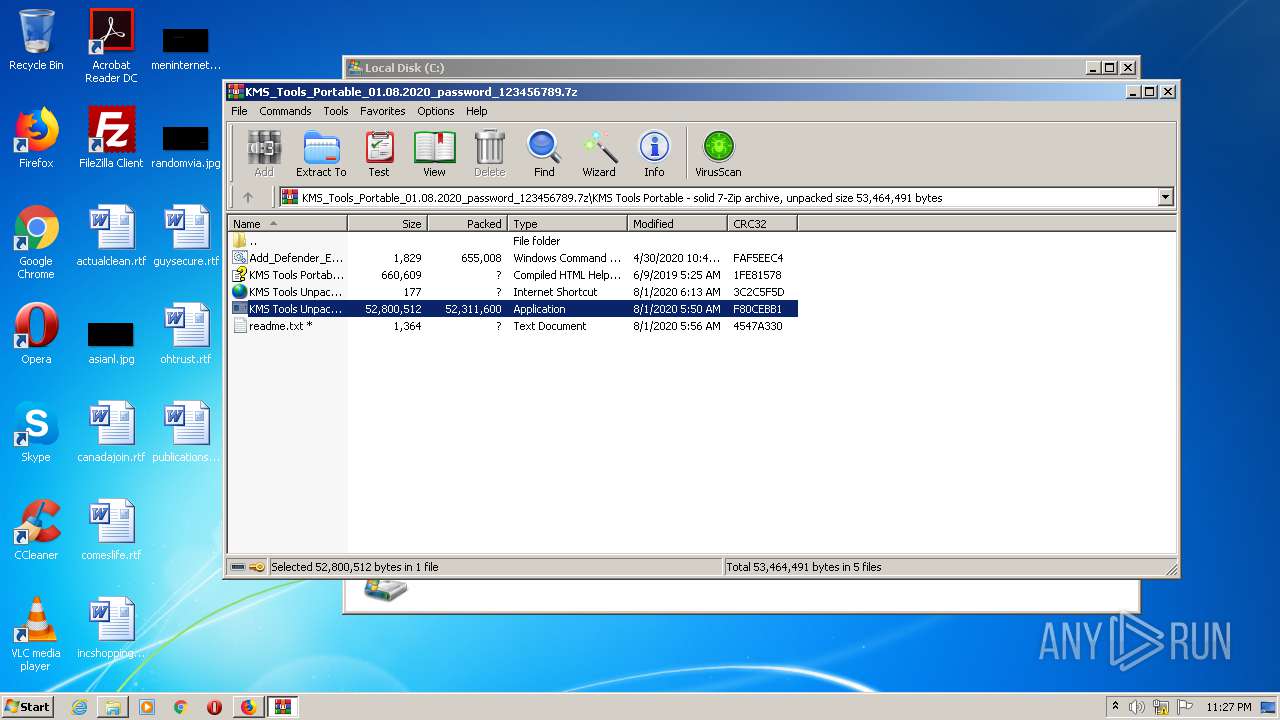
| MD5: | E7F042493F0DD7171C895B28450A4053 |
| SHA1: | 1FBDCF142780B0E9F0F77F17D4F081FF280ABA16 |
| SHA256: | 79C1A5160A8F904C6BA65A96384762B8638FA37A08B9A3D680155D26C4B6C5C2 |
| SSDEEP: | 3:N1KJS4kIK430V:Cc4k343e |
MALICIOUS
Application was dropped or rewritten from another process
- 7zaxxx.exe (PID: 2916)
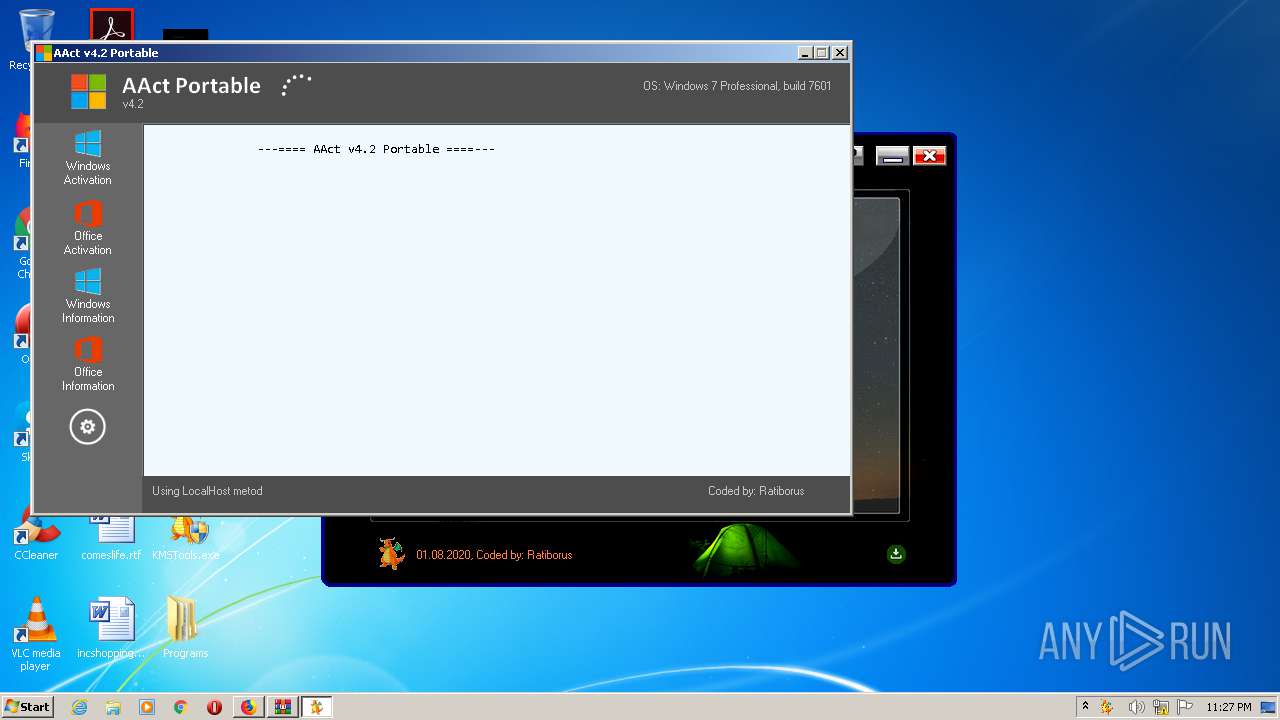
- AAct.exe (PID: 3448)
- KMSSS.exe (PID: 560)
SUSPICIOUS
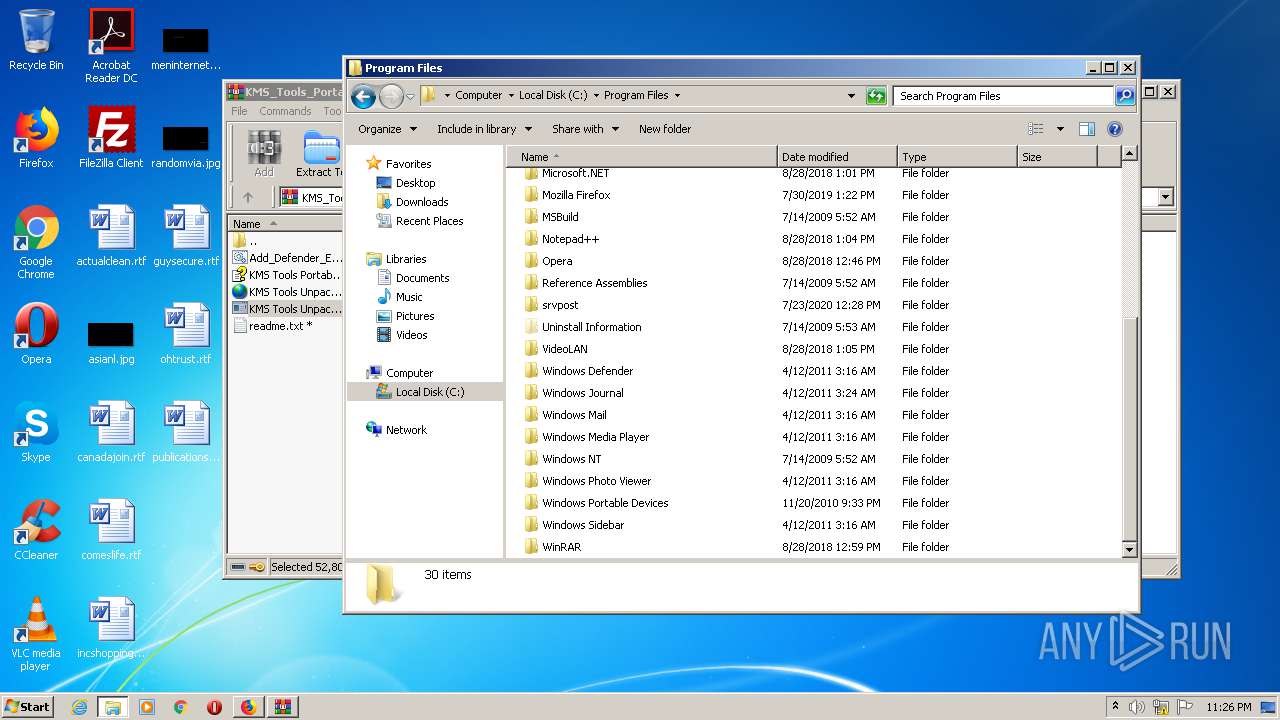
Creates files in the program directory
- firefox.exe (PID: 3968)
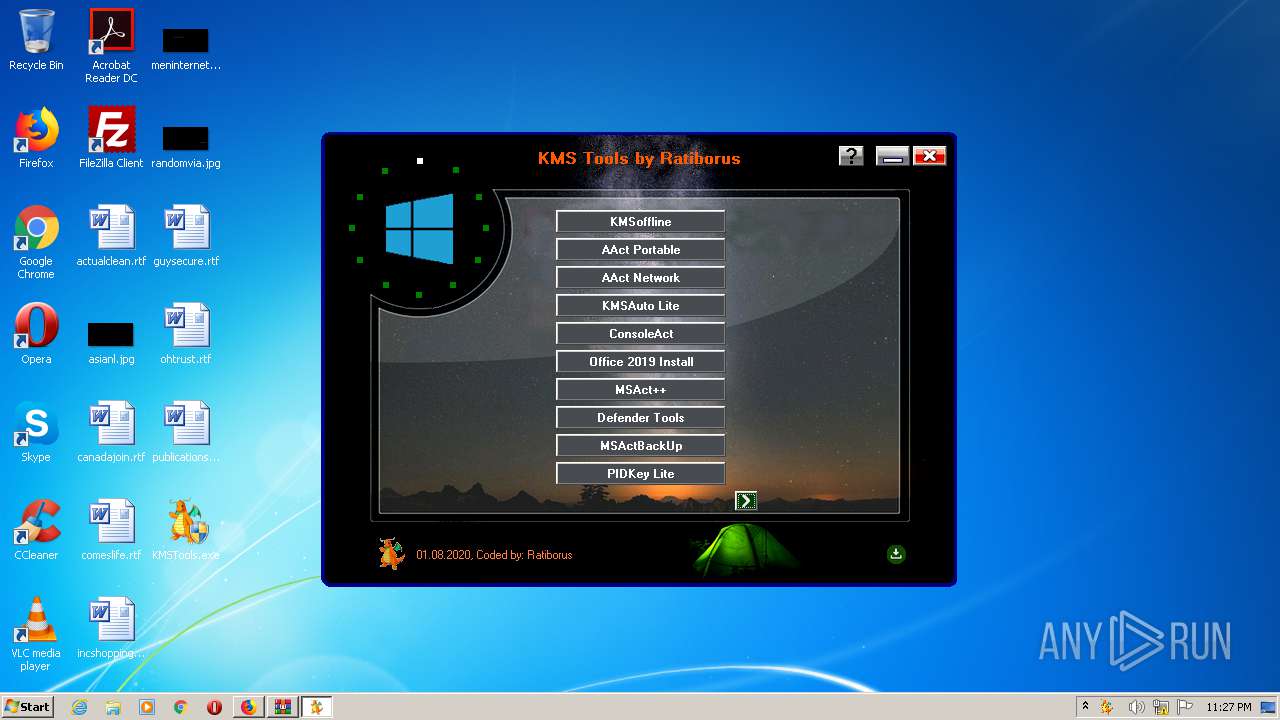
Starts CMD.EXE for commands execution
- KMSTools.exe (PID: 816)
- AAct.exe (PID: 3448)
Executable content was dropped or overwritten
- AAct.exe (PID: 3448)
- 7zaxxx.exe (PID: 2916)
- KMSTools.exe (PID: 816)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2128)
- cmd.exe (PID: 2464)
- cmd.exe (PID: 1448)
Executes scripts
- cmd.exe (PID: 1472)
- cmd.exe (PID: 308)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 3596)
- cmd.exe (PID: 1376)
- cmd.exe (PID: 2976)
- cmd.exe (PID: 2616)
- cmd.exe (PID: 2696)
- cmd.exe (PID: 3680)
Uses REG.EXE to modify Windows registry
- AAct.exe (PID: 3448)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2632)
INFO
Application launched itself
- firefox.exe (PID: 876)
- firefox.exe (PID: 3968)
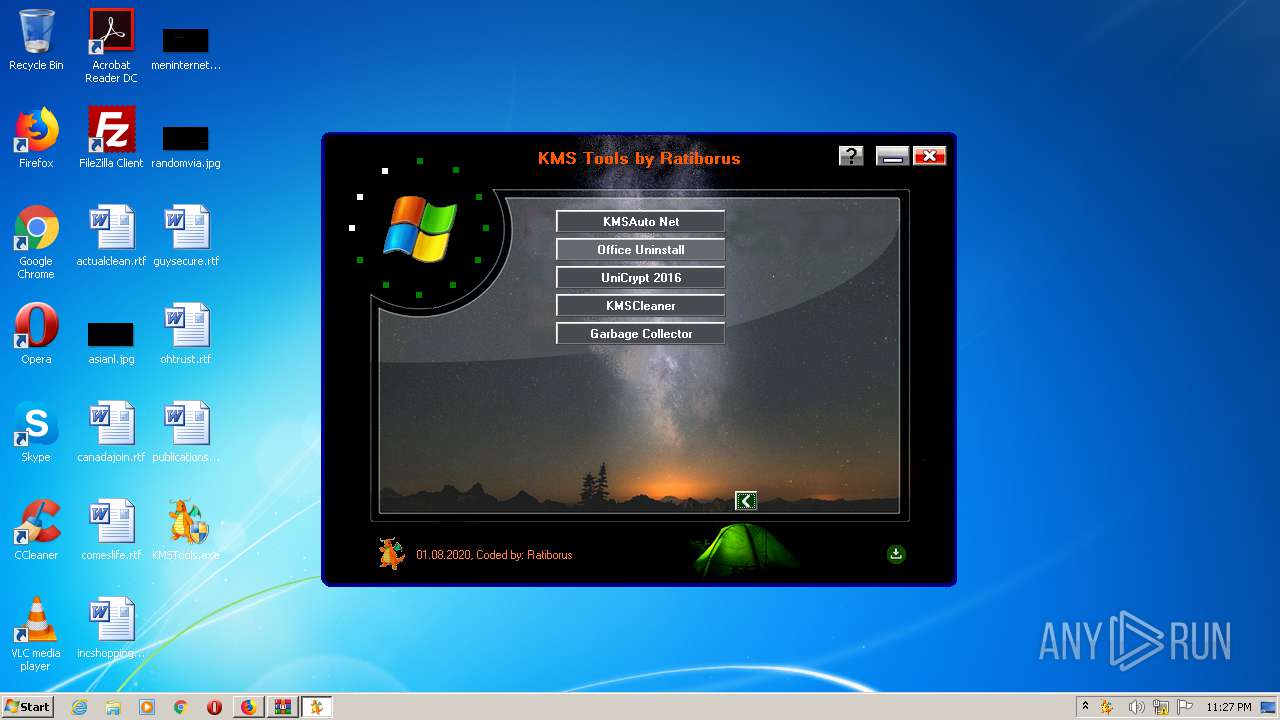
Manual execution by user
- KMSTools.exe (PID: 816)
- explorer.exe (PID: 1036)
- KMSTools.exe (PID: 2528)
Creates files in the user directory
- firefox.exe (PID: 3968)
Reads Internet Cache Settings
- firefox.exe (PID: 3968)
Reads CPU info
- firefox.exe (PID: 3968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
119
Monitored processes
46
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Windows\System32\cmd.exe" /c cscript.exe C:\Windows\System32\slmgr.vbs //NoLogo /act-type 0 | C:\Windows\System32\cmd.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 308 | "C:\Windows\System32\reg.exe" DELETE "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55c92734-d682-4d71-983e-d6ec3f16059f" /f | C:\Windows\System32\reg.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
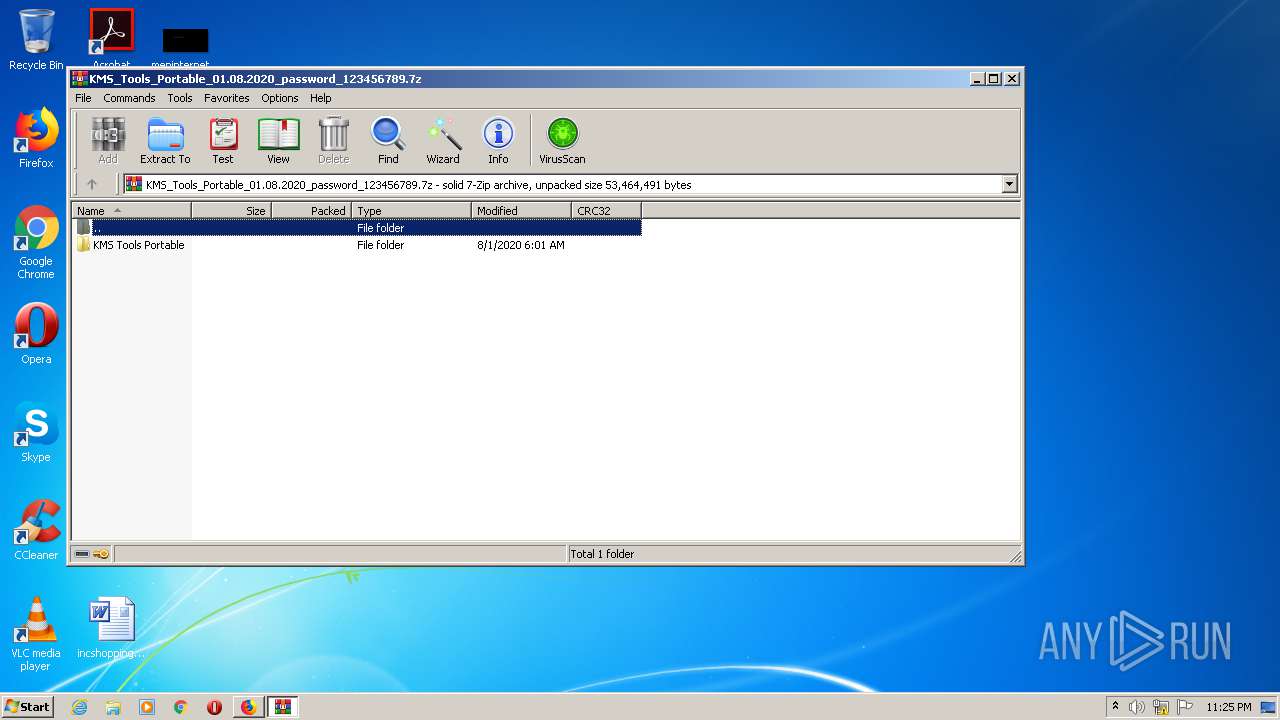
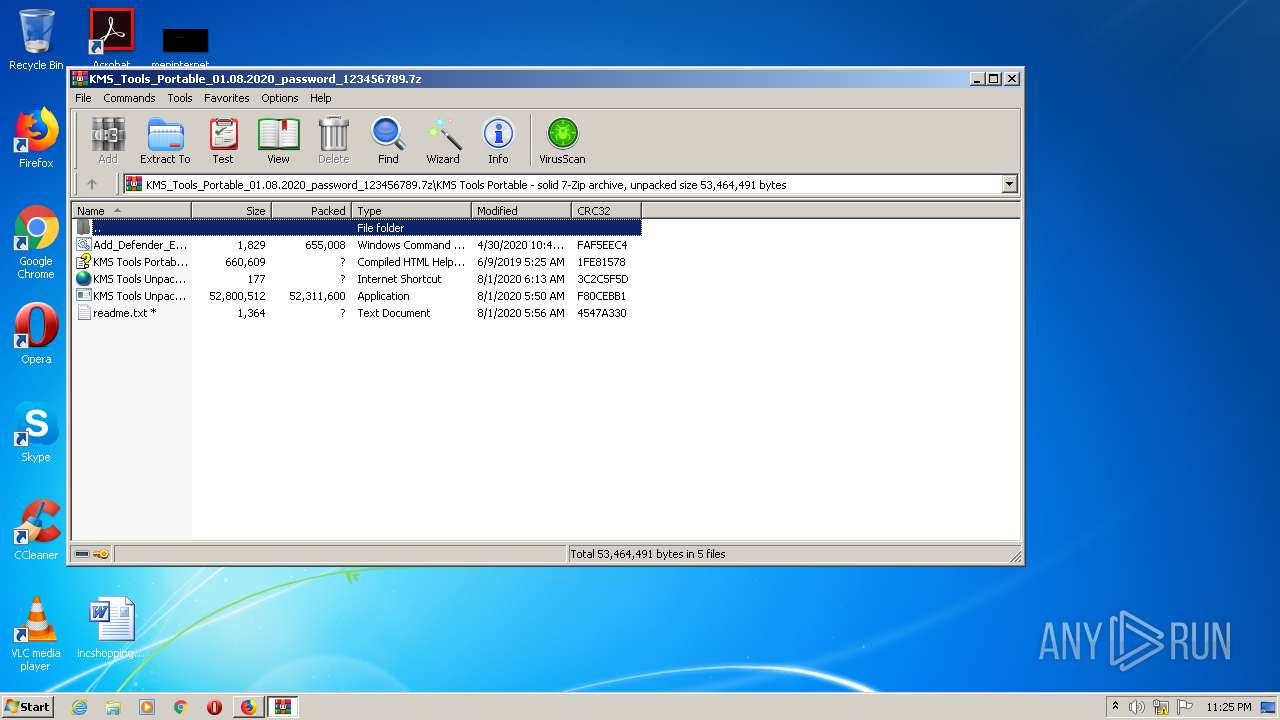
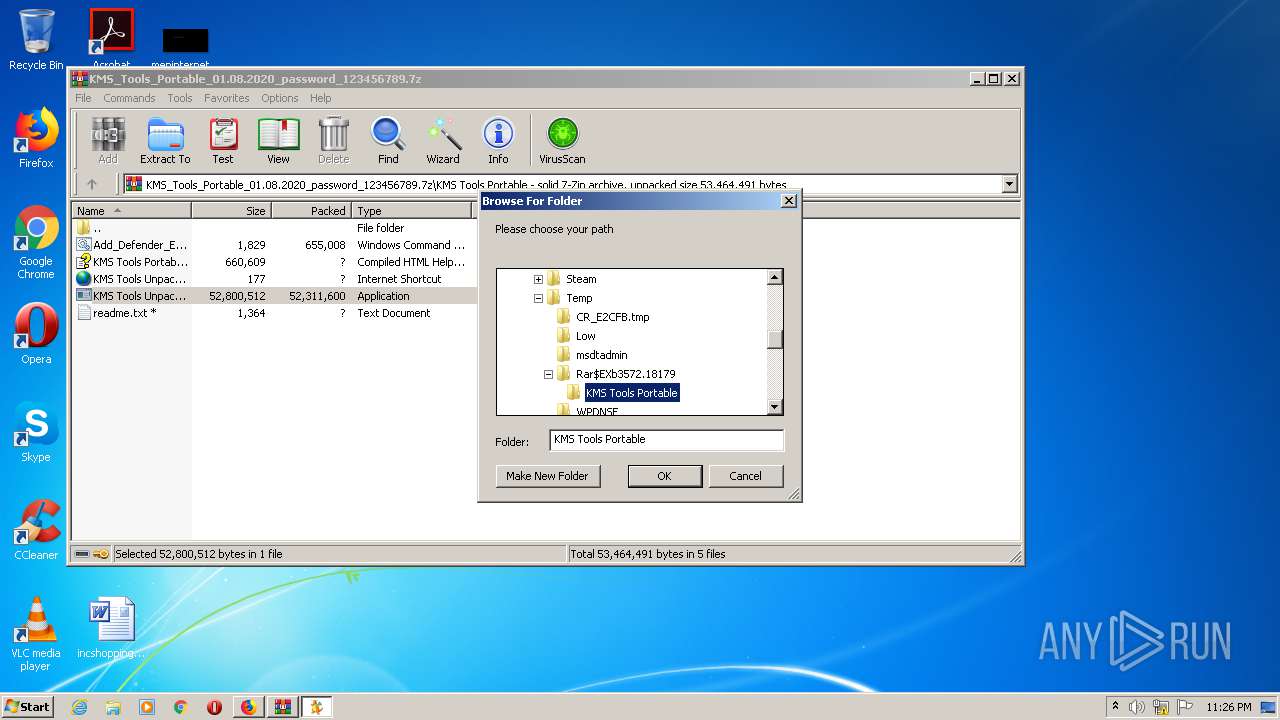
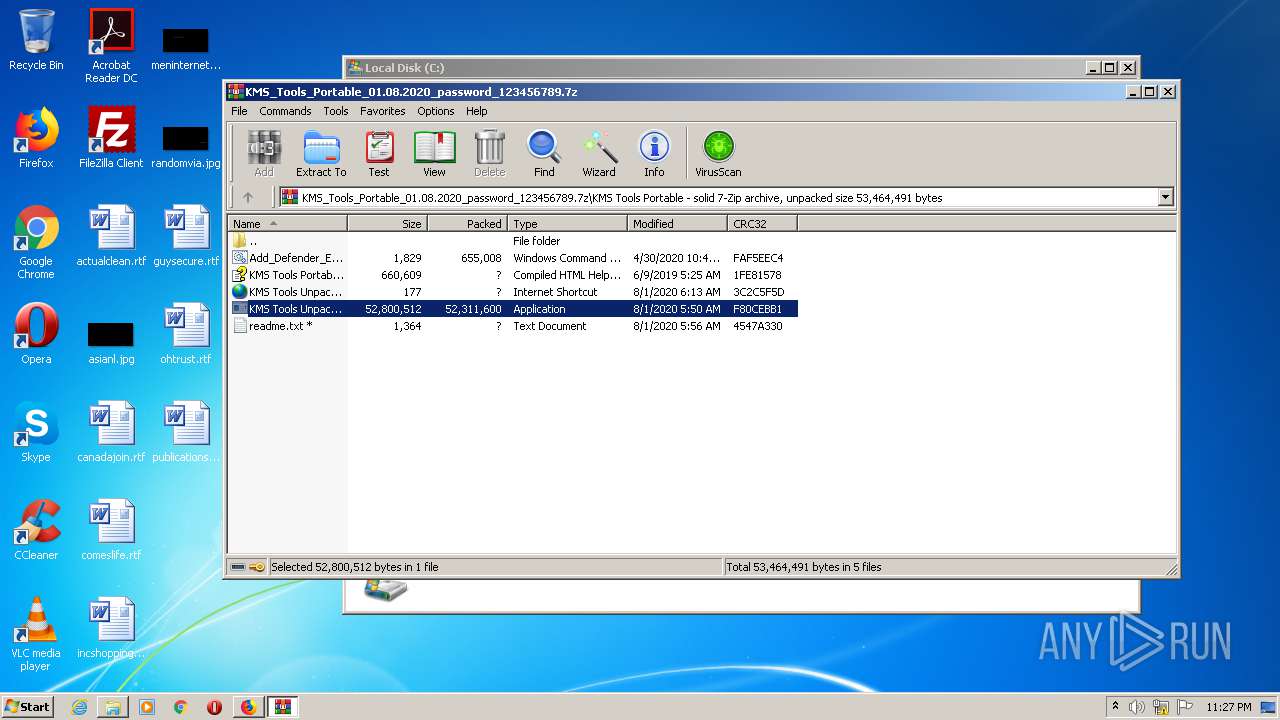
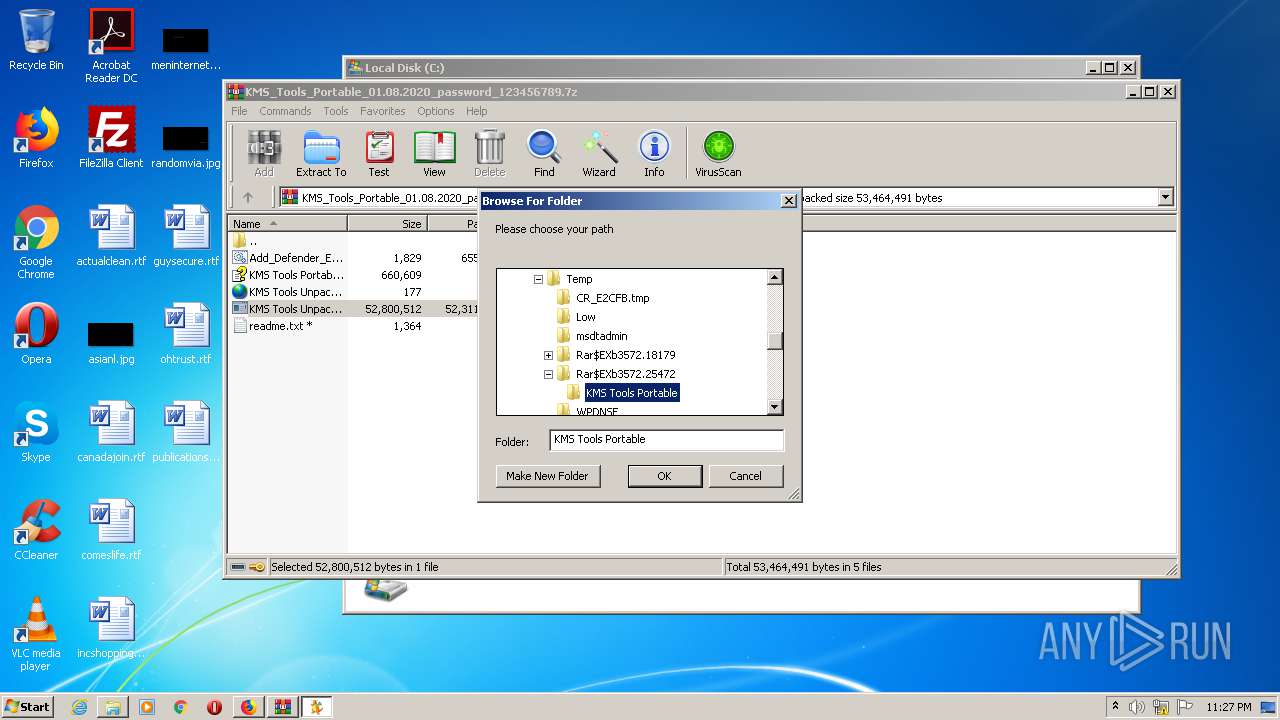
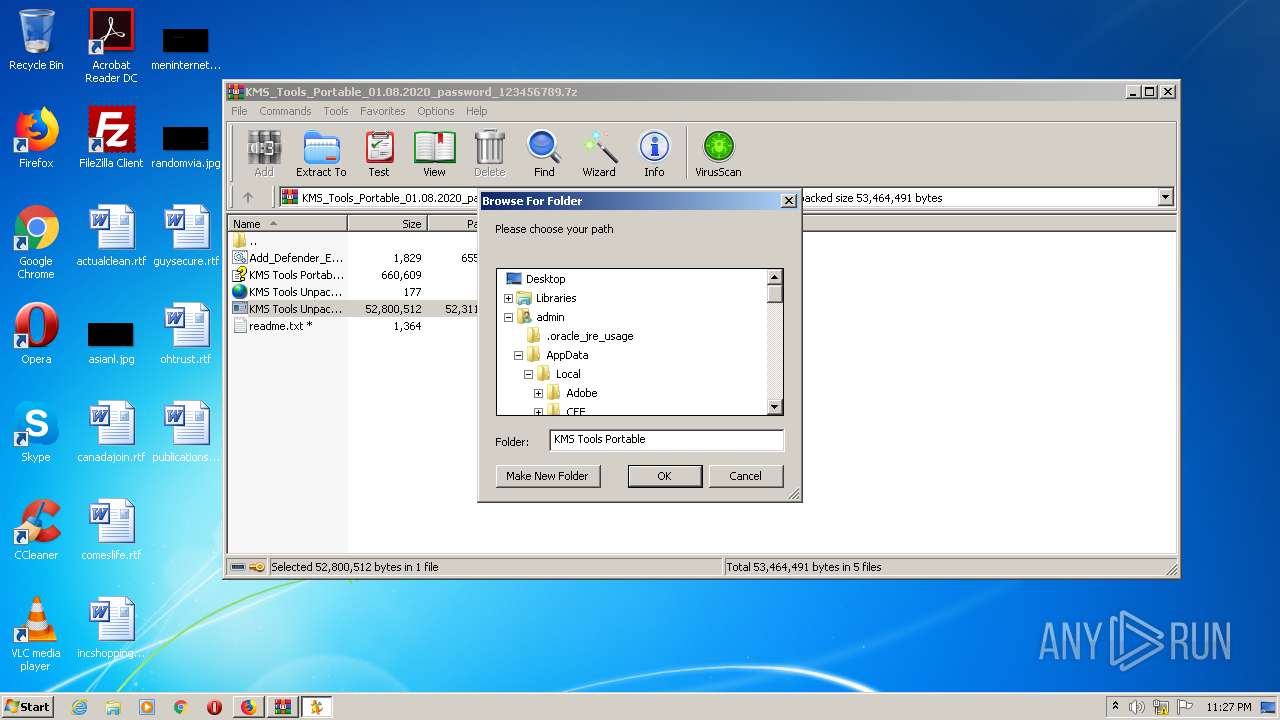
| 480 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3572.25472\KMS Tools Portable\KMS Tools Unpack.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3572.25472\KMS Tools Portable\KMS Tools Unpack.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
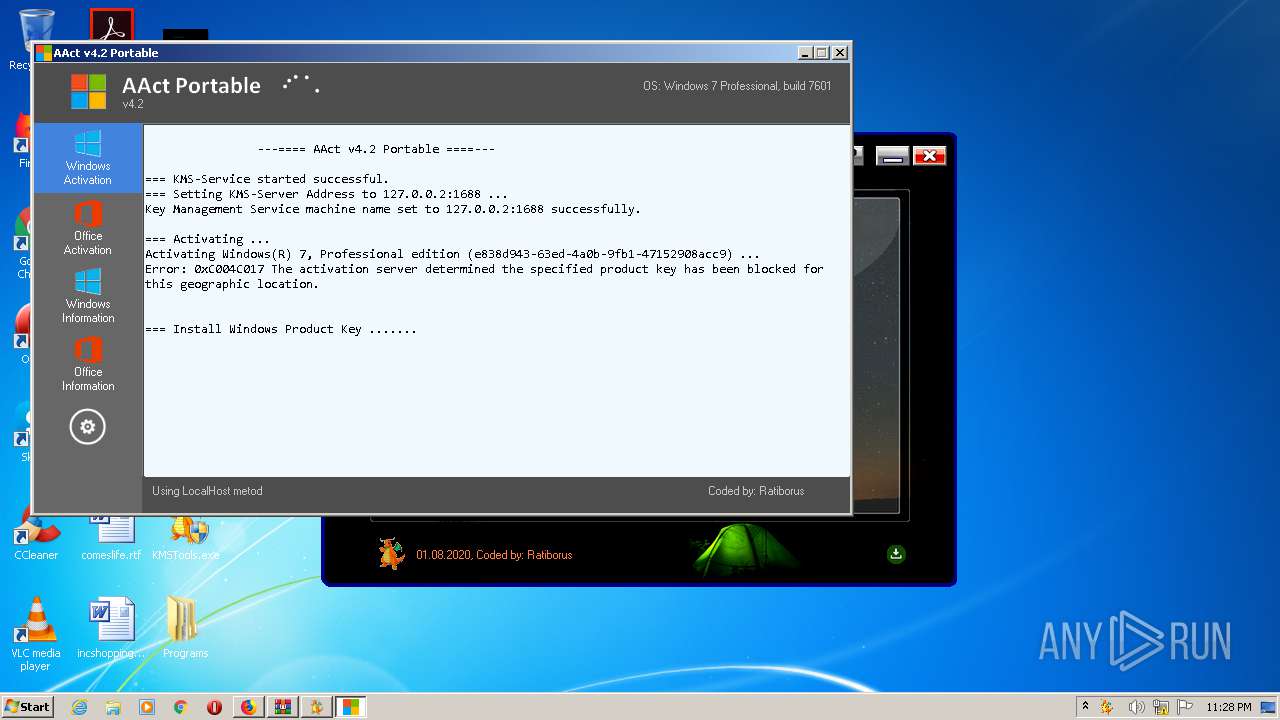
| 560 | "C:\Users\admin\Desktop\Programs\AAct v4.2 Portable\AAct_files\KMSSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -PO16 RandomKMSPID | C:\Users\admin\Desktop\Programs\AAct v4.2 Portable\AAct_files\KMSSS.exe | — | AAct.exe | |||||||||||
User: admin Company: MSFree Inc. Integrity Level: HIGH Description: KMS emulator by Ratiborus. Exit code: 1 Version: 2.0.7.0 Modules
| |||||||||||||||
| 816 | "C:\Users\admin\Desktop\KMSTools.exe" | C:\Users\admin\Desktop\KMSTools.exe | explorer.exe | ||||||||||||
User: admin Company: Ratiborus Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Mozilla Firefox\firefox.exe" "http://www.solidfiles.com/v/e6XnmyR46XQPz" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3968.13.1828859062\1985780185" -childID 2 -isForBrowser -prefsHandle 2912 -prefMapHandle 2916 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3968 "\\.\pipe\gecko-crash-server-pipe.3968" 2932 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1036 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1376 | "C:\Windows\System32\cmd.exe" /c cscript.exe C:\Windows\System32\slmgr.vbs //NoLogo /skms 127.0.0.2:1688 | C:\Windows\System32\cmd.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1448 | "C:\Windows\System32\cmd.exe" /c Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS protocol=TCP | C:\Windows\System32\cmd.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 543
Read events
2 337
Write events
206
Delete events
0
Modification events
| (PID) Process: | (3968) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 8B0B091A00000000 | |||
| (PID) Process: | (876) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 820B091A00000000 | |||
| (PID) Process: | (3968) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3968) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3968) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3968) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3968) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3968) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.7z\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
| (PID) Process: | (3572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3572) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
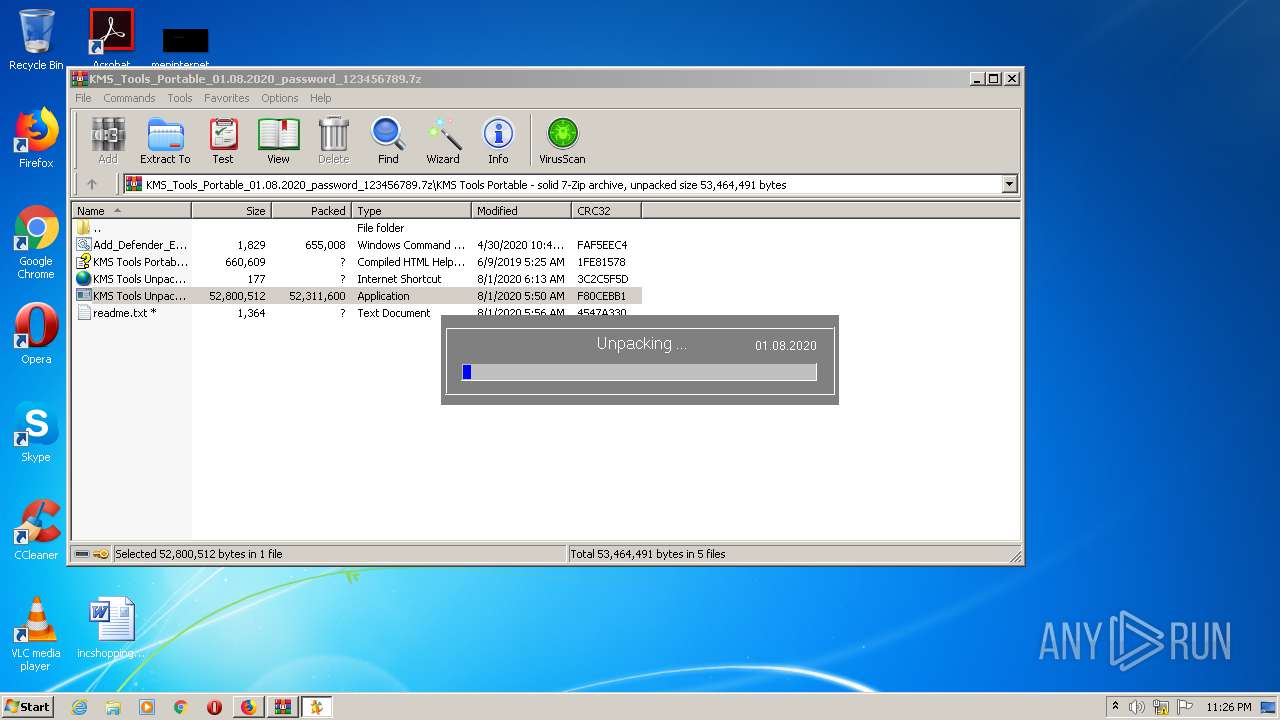
Executable files
4
Suspicious files
106
Text files
44
Unknown types
69
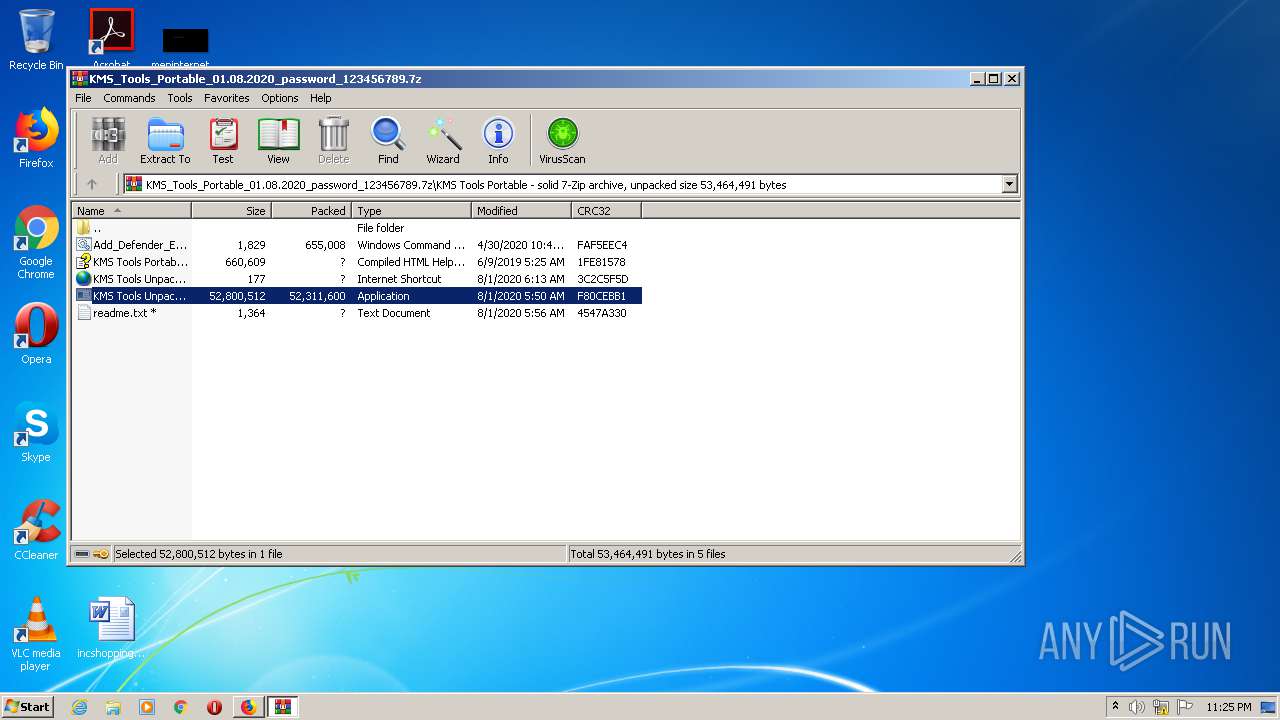
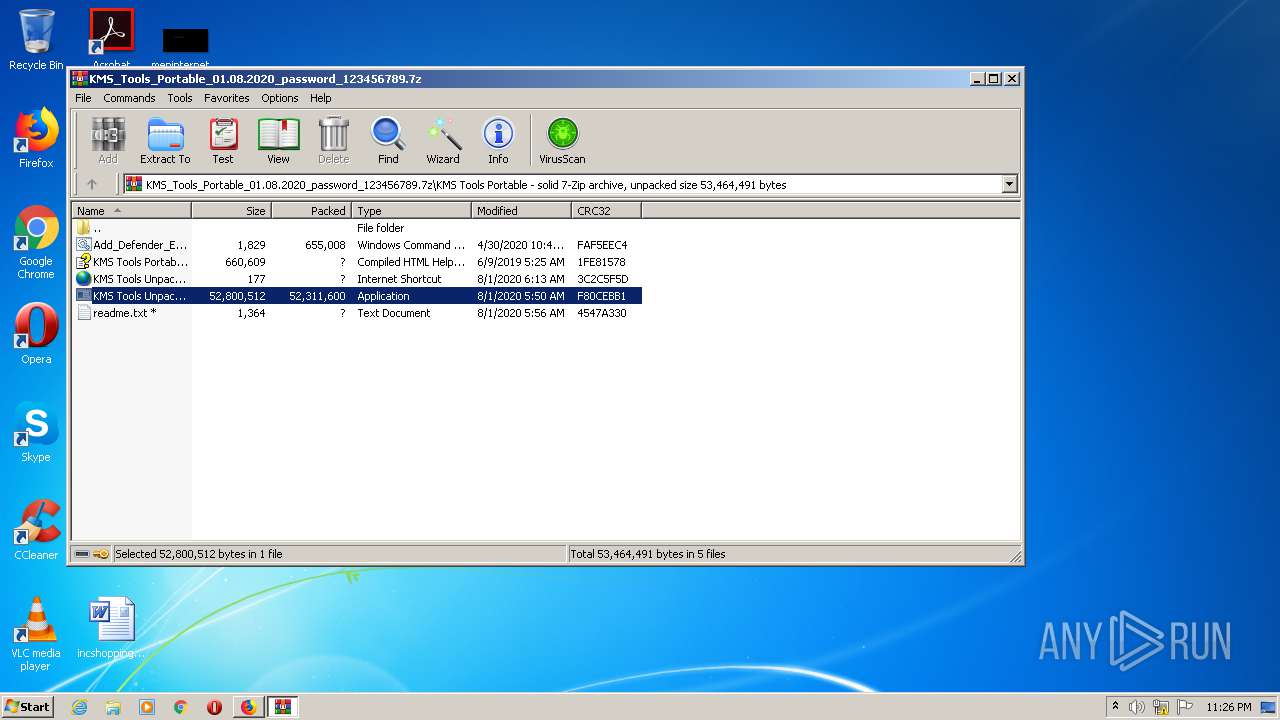
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3968 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3968 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3968 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3968 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 3968 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3968 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\969BAD0DF6DA7EE34191EEEFC0C6CB28477F96D1 | binary | |
MD5:— | SHA256:— | |||
| 3968 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3968 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\B990EC03E2A4EC56D5B56D3A0CCF66A636781AC1 | binary | |
MD5:— | SHA256:— | |||
| 3968 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
40
DNS requests
108
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
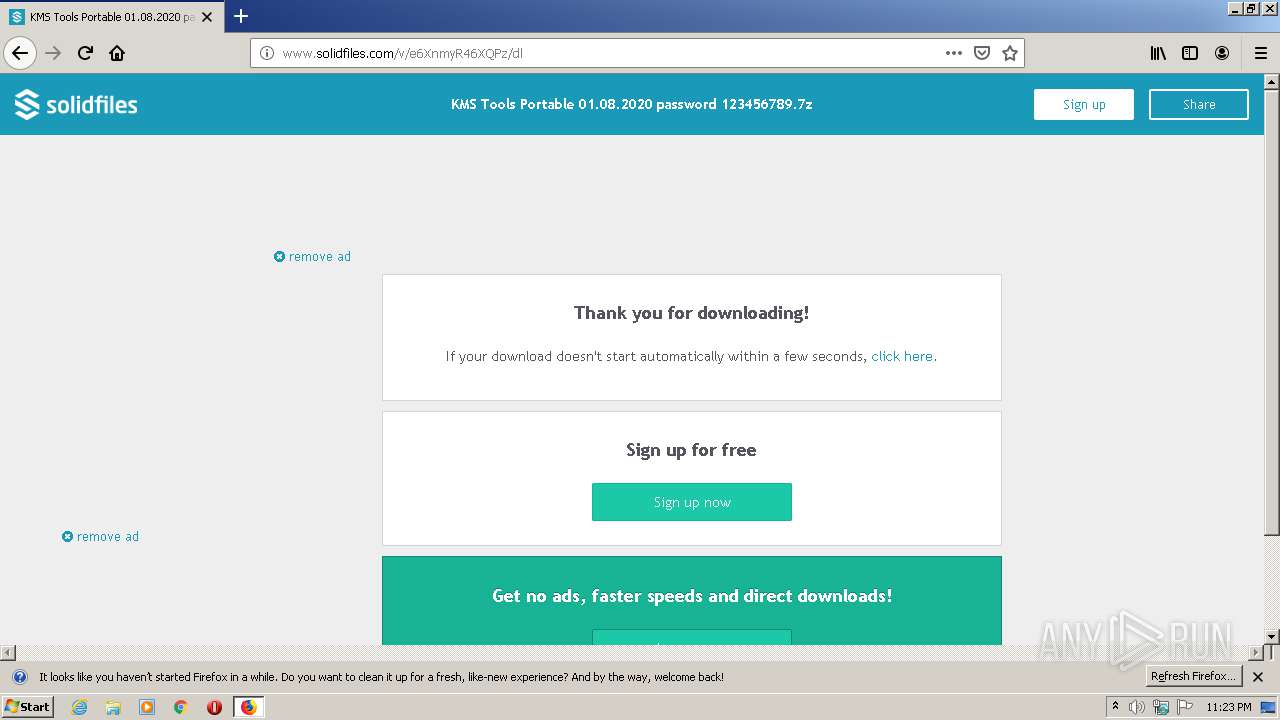
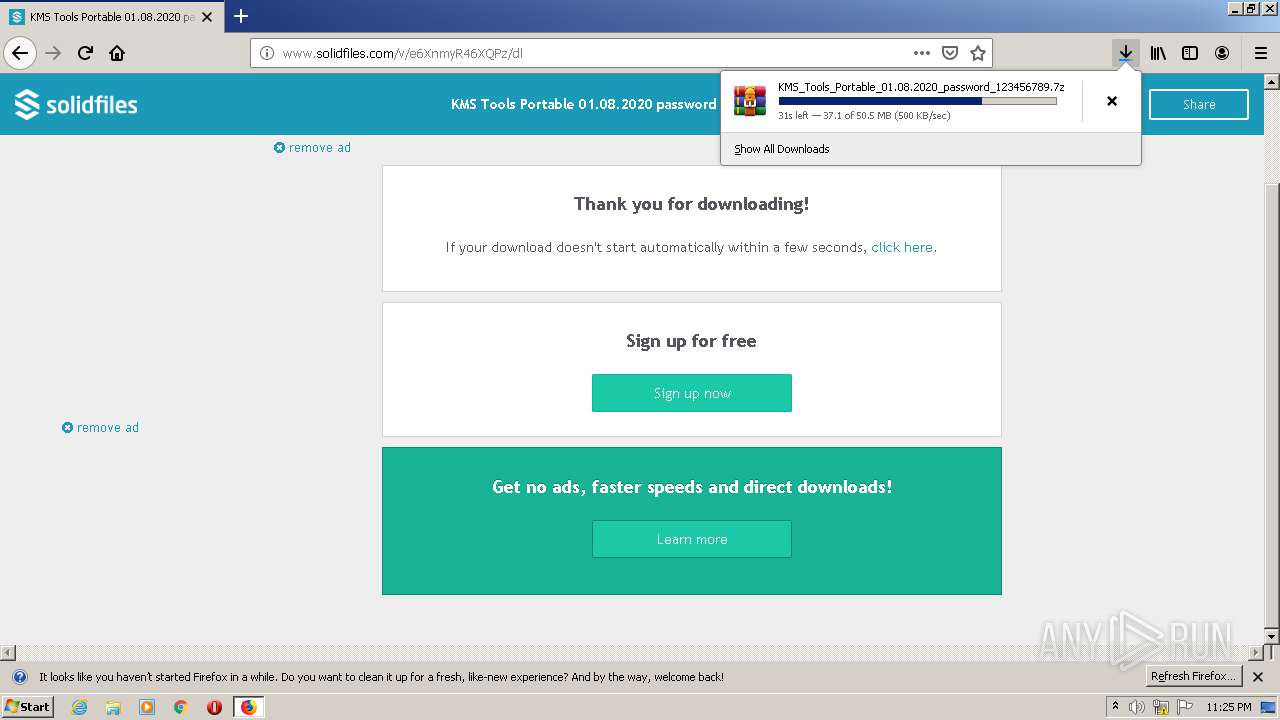
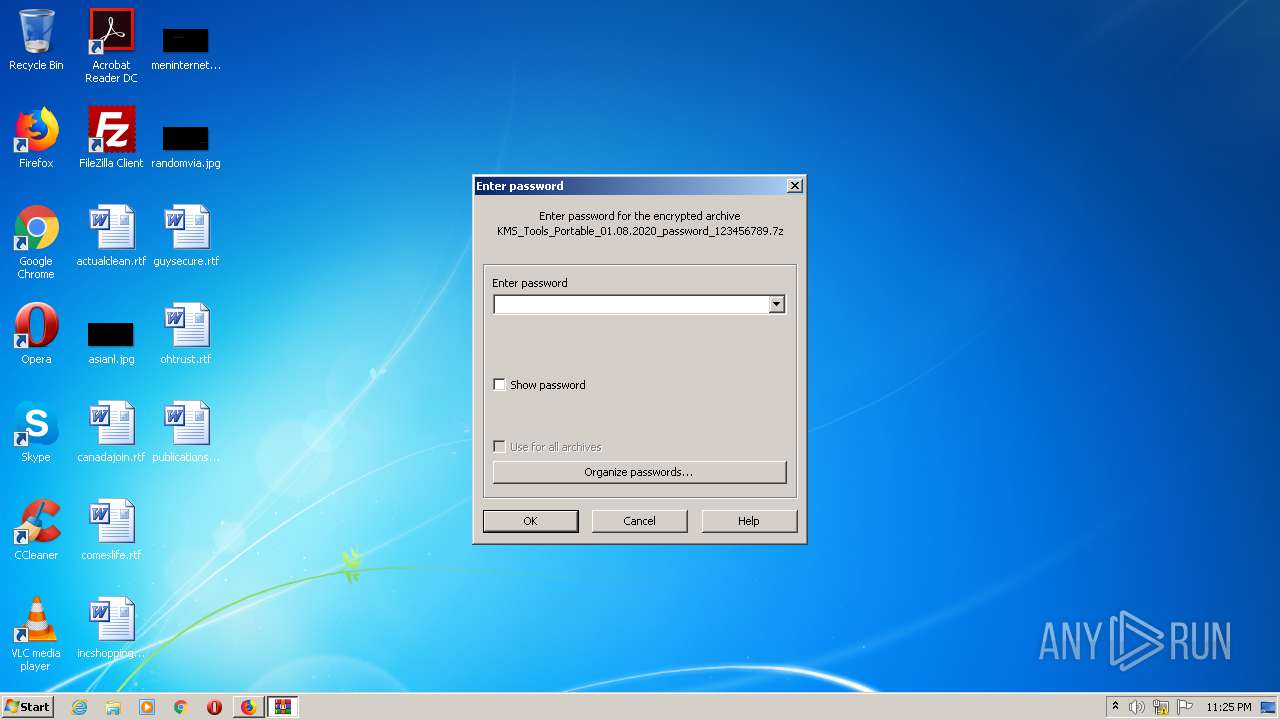
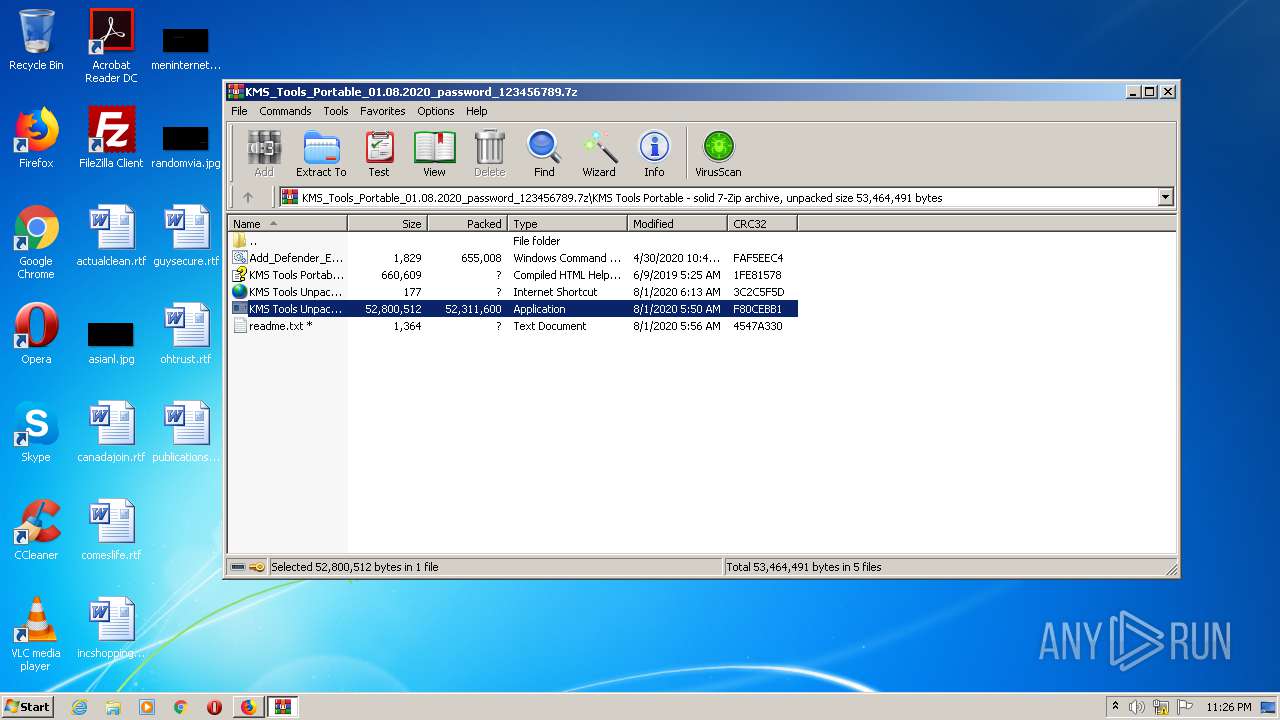
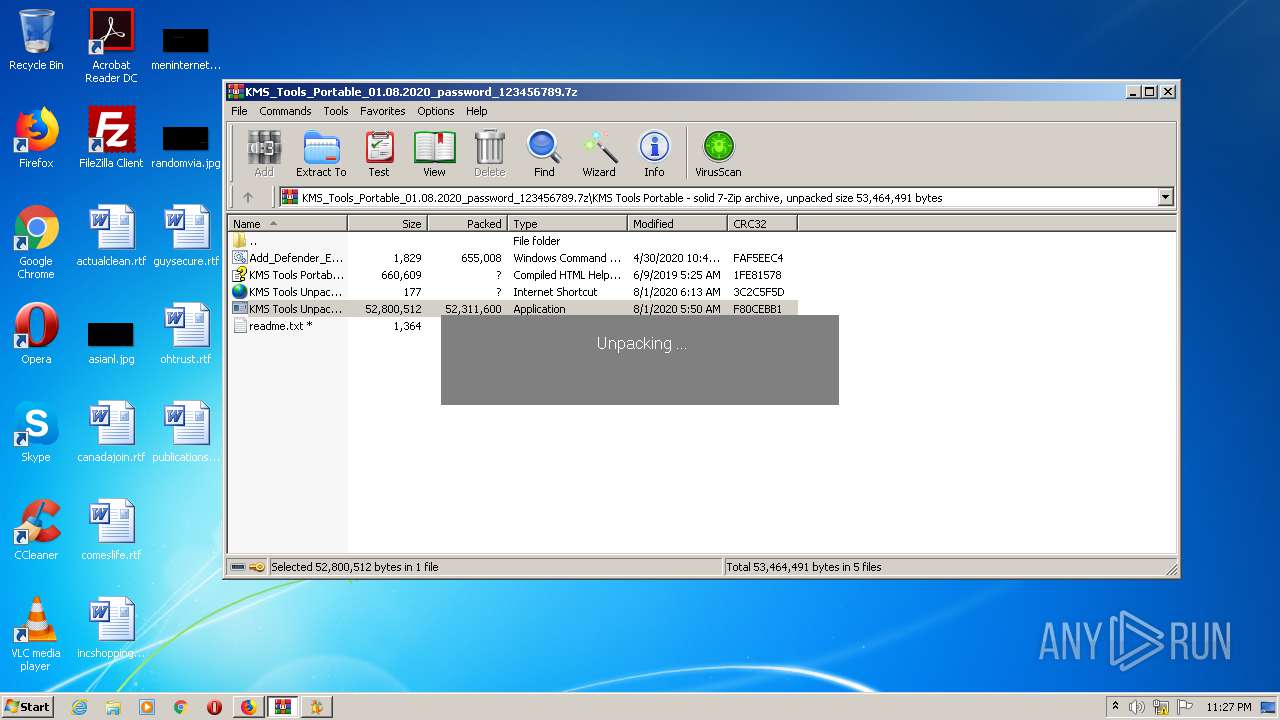
3968 | firefox.exe | GET | 200 | 93.115.87.59:80 | http://s02.solidfilesusercontent.com/NzdiNGEzNTlhMGFlMzM0ZGM1ZTNmNjYwZjc3NDI4OTJiNTJkNTA2ZDoxazc0YVU6UlVWUE1mUWNqN1NPSXp3R3Y0Smd6OXN1ZTdv/e6XnmyR46XQPz/KMS_Tools_Portable_01.08.2020_password_123456789.7z | RO | compressed | 50.5 Mb | suspicious |
3968 | firefox.exe | POST | 200 | 37.221.163.212:80 | http://www.solidfiles.com/v/e6XnmyR46XQPz/dl | RO | html | 14.1 Kb | suspicious |
3968 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 280 b | whitelisted |
3968 | firefox.exe | GET | 200 | 185.60.216.19:80 | http://connect.facebook.net/en_US/all.js | IE | text | 1.74 Kb | whitelisted |
3968 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3968 | firefox.exe | POST | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
3968 | firefox.exe | POST | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
3968 | firefox.exe | POST | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gts1o1core | US | der | 471 b | whitelisted |
3968 | firefox.exe | GET | 200 | 37.221.163.212:80 | http://www.solidfiles.com/v/e6XnmyR46XQPz | RO | html | 15.0 Kb | suspicious |
3968 | firefox.exe | POST | 200 | 216.58.207.35:80 | http://ocsp.pki.goog/gts1o1core | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3968 | firefox.exe | 2.16.177.88:80 | detectportal.firefox.com | Akamai International B.V. | — | suspicious |
3968 | firefox.exe | 37.221.163.212:80 | www.solidfiles.com | Voxility S.R.L. | RO | suspicious |
3968 | firefox.exe | 104.27.153.131:443 | solidfilescdn.com | Cloudflare Inc | US | unknown |
3968 | firefox.exe | 172.217.22.74:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3968 | firefox.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
3968 | firefox.exe | 143.204.202.20:443 | snippets.cdn.mozilla.net | — | US | suspicious |
3968 | firefox.exe | 172.217.23.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3968 | firefox.exe | 34.214.1.68:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
3968 | firefox.exe | 216.58.207.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3968 | firefox.exe | 66.102.1.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.solidfiles.com |
| suspicious |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
solidfilescdn.com |
| malicious |
maxcdn.bootstrapcdn.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cds.j3z9t3p6.hwcdn.net |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
3968 | firefox.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
3968 | firefox.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |