| URL: | https://kr.cyberlink.com/prog/trial/user-add.do?source=direct&ProductId=1&ostype=Windows |
| Full analysis: | https://app.any.run/tasks/f60faee1-9841-46e6-856e-3c4b1e5e6e24 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 13:28:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 648DBEAC87526B54E998B787C461A405 |
| SHA1: | 41712B145BF11C7E856BFF41416A45BADF1626D7 |
| SHA256: | 7994A365D3F3A33663D0338E763023B5F389CA07A1BC4740899D337FD52308D5 |
| SSDEEP: | 3:N8SLGnXIbK9ZMFEM7b6pKQGKuvAC8SW:2SLGYGMFbb6pKQGKjSW |
MALICIOUS
Adds path to the Windows Defender exclusion list
- WDExclusionPathTool.exe (PID: 904)
- cmd.exe (PID: 3416)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- Setup.exe (PID: 6988)
The process creates files with name similar to system file names
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- 7z.exe (PID: 4872)
Process drops legitimate windows executable
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- PowerDVD_23.0.1825.62_GM3_ES_Essential_DVD240430-03.exe (PID: 6156)
- 7z.exe (PID: 4872)
- vcredist_x64.exe (PID: 6356)
- vcredist_x64.exe (PID: 5096)
- vcredist_x86.exe (PID: 6084)
- vcredist_x86.exe (PID: 3524)
- msiexec.exe (PID: 3816)
- VC_redist.x86.exe (PID: 6164)
The process drops C-runtime libraries
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- PowerDVD_23.0.1825.62_GM3_ES_Essential_DVD240430-03.exe (PID: 6156)
- 7z.exe (PID: 4872)
- msiexec.exe (PID: 3816)
Executable content was dropped or overwritten
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- PowerDVD_23.0.1825.62_GM3_ES_Essential_DVD240430-03.exe (PID: 6156)
- Setup.exe (PID: 6988)
- 7z.exe (PID: 4872)
- vcredist_x64.exe (PID: 5096)
- vcredist_x64.exe (PID: 6356)
- vcredist_x86.exe (PID: 3524)
- vcredist_x86.exe (PID: 6084)
- VC_redist.x86.exe (PID: 6164)
- 7z.exe (PID: 4300)
- VC_redist.x86.exe (PID: 4052)
- 7z.exe (PID: 3172)
Reads security settings of Internet Explorer
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- PowerDVD_23.0.1825.62_GM3_ES_Essential_DVD240430-03.exe (PID: 6156)
- Setup.exe (PID: 6988)
- vcredist_x64.exe (PID: 6356)
- vcredist_x86.exe (PID: 3524)
Checks Windows Trust Settings
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- Setup.exe (PID: 6988)
- vcredist_x64.exe (PID: 6356)
- msiexec.exe (PID: 3816)
- vcredist_x86.exe (PID: 3524)
Drops 7-zip archiver for unpacking
- PowerDVD_23.0.1825.62_GM3_ES_Essential_DVD240430-03.exe (PID: 6156)
Uses REG/REGEDIT.EXE to modify registry
- Setup.exe (PID: 6988)
Starts a Microsoft application from unusual location
- vcredist_x64.exe (PID: 6356)
- vcredist_x64.exe (PID: 5096)
- vcredist_x86.exe (PID: 3524)
- vcredist_x86.exe (PID: 6084)
- VC_redist.x86.exe (PID: 6164)
- VC_redist.x86.exe (PID: 4052)
Application launched itself
- vcredist_x64.exe (PID: 6356)
- vcredist_x86.exe (PID: 3524)
Searches for installed software
- dllhost.exe (PID: 6864)
Executes as Windows Service
- VSSVC.exe (PID: 6932)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3816)
Reads the date of Windows installation
- WDExclusionPathTool.exe (PID: 904)
Starts CMD.EXE for commands execution
- WDExclusionPathTool.exe (PID: 904)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 3416)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3416)
Process drops python dynamic module
- 7z.exe (PID: 3172)
INFO
The sample compiled with chinese language support
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- PowerDVD_23.0.1825.62_GM3_ES_Essential_DVD240430-03.exe (PID: 6156)
- 7z.exe (PID: 4872)
- msiexec.exe (PID: 3816)
- 7z.exe (PID: 4300)
- 7z.exe (PID: 3172)
The process uses the downloaded file
- chrome.exe (PID: 6508)
- PowerDVD_23.0.1825.62_GM3_ES_Essential_DVD240430-03.exe (PID: 6156)
Executable content was dropped or overwritten
- chrome.exe (PID: 6508)
- msiexec.exe (PID: 3816)
Application launched itself
- chrome.exe (PID: 6508)
The sample compiled with english language support
- chrome.exe (PID: 6508)
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- PowerDVD_23.0.1825.62_GM3_ES_Essential_DVD240430-03.exe (PID: 6156)
- 7z.exe (PID: 4872)
- vcredist_x64.exe (PID: 5096)
- vcredist_x64.exe (PID: 6356)
- msiexec.exe (PID: 3816)
- vcredist_x86.exe (PID: 3524)
- vcredist_x86.exe (PID: 6084)
- VC_redist.x86.exe (PID: 6164)
- VC_redist.x86.exe (PID: 4052)
- 7z.exe (PID: 3172)
- 7z.exe (PID: 4300)
Reads the computer name
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- PowerDVD_23.0.1825.62_GM3_ES_Essential_DVD240430-03.exe (PID: 6156)
- Setup.exe (PID: 6988)
- 7z.exe (PID: 4872)
- vcredist_x64.exe (PID: 5096)
- vcredist_x64.exe (PID: 6356)
- vcredist_x86.exe (PID: 3524)
- VC_redist.x86.exe (PID: 4052)
- WDExclusionPathTool.exe (PID: 904)
- 7z.exe (PID: 3172)
Process checks computer location settings
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- PowerDVD_23.0.1825.62_GM3_ES_Essential_DVD240430-03.exe (PID: 6156)
- Setup.exe (PID: 6988)
- WDExclusionPathTool.exe (PID: 904)
Checks supported languages
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- PowerDVD_23.0.1825.62_GM3_ES_Essential_DVD240430-03.exe (PID: 6156)
- 7z.exe (PID: 4872)
- Setup.exe (PID: 6988)
- vcredist_x64.exe (PID: 5096)
- vcredist_x64.exe (PID: 6356)
- msiexec.exe (PID: 3816)
- vcredist_x86.exe (PID: 3524)
- VC_redist.x86.exe (PID: 4052)
- WDExclusionPathTool.exe (PID: 904)
- 7z.exe (PID: 6196)
- 7z.exe (PID: 3172)
Creates files in the program directory
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- 7z.exe (PID: 4872)
- Setup.exe (PID: 6988)
Checks proxy server information
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- Setup.exe (PID: 6988)
- vcredist_x64.exe (PID: 6356)
Reads the machine GUID from the registry
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- Setup.exe (PID: 6988)
- vcredist_x64.exe (PID: 6356)
- msiexec.exe (PID: 3816)
- vcredist_x86.exe (PID: 3524)
Reads the software policy settings
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- Setup.exe (PID: 6988)
- vcredist_x64.exe (PID: 6356)
Creates files or folders in the user directory
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
Sends debugging messages
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
- regedit.exe (PID: 2800)
- Setup.exe (PID: 6988)
- WDExclusionPathTool.exe (PID: 904)
Create files in a temporary directory
- PowerDVD_23.0.1825.62_GM3_ES_Essential_DVD240430-03.exe (PID: 6156)
- vcredist_x64.exe (PID: 5096)
- Setup.exe (PID: 6988)
- CyberLink_PowerDVD_Downloader.exe (PID: 6244)
Manages system restore points
- SrTasks.exe (PID: 1220)
The sample compiled with german language support
- msiexec.exe (PID: 3816)
- 7z.exe (PID: 4300)
The sample compiled with french language support
- msiexec.exe (PID: 3816)
- 7z.exe (PID: 4300)
The sample compiled with russian language support
- msiexec.exe (PID: 3816)
- 7z.exe (PID: 4300)
The sample compiled with Italian language support
- msiexec.exe (PID: 3816)
- 7z.exe (PID: 4300)
The sample compiled with spanish language support
- msiexec.exe (PID: 3816)
- 7z.exe (PID: 4300)
Creates a software uninstall entry
- msiexec.exe (PID: 3816)
The sample compiled with japanese language support
- msiexec.exe (PID: 3816)
- 7z.exe (PID: 4300)
The sample compiled with korean language support
- msiexec.exe (PID: 3816)
- 7z.exe (PID: 4300)
The sample compiled with portuguese language support
- 7z.exe (PID: 4300)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5544)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
176
Monitored processes
42
Malicious processes
6
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4880 --field-trial-handle=1932,i,5037799384712278696,7530067560922538086,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 904 | "C:\ProgramData\SUPPORTDIR\20250110_133105_6988\x64\WDExclusionPathTool.exe" -Add "C:\Program Files\CyberLink\PowerDVD23" | C:\ProgramData\SUPPORTDIR\20250110_133105_6988\x64\WDExclusionPathTool.exe | Setup.exe | ||||||||||||
User: admin Company: CyberLink Corp. Integrity Level: HIGH Description: WDExclusionPathTool Exit code: 1 Version: 1,0,0,0 Modules
| |||||||||||||||
| 1220 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5496 --field-trial-handle=1932,i,5037799384712278696,7530067560922538086,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7z.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | "C:\WINDOWS\SysWOW64\Regedit.exe" /s "C:\ProgramData\install_clap\{1BB40144-36AC-4A7C-AF6A-A0F9DA57FC76}\PDVDSubTemp.reg" | C:\Windows\SysWOW64\regedit.exe | Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3000 | "C:\Users\admin\Downloads\CyberLink_PowerDVD_Downloader.exe" | C:\Users\admin\Downloads\CyberLink_PowerDVD_Downloader.exe | — | chrome.exe | |||||||||||
User: admin Company: CyberLink Corp. Integrity Level: MEDIUM Description: CyberLink Downloader Exit code: 3221226540 Version: 4.0.0.1310 Modules
| |||||||||||||||
| 3172 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\7z.exe" x "C:\Users\admin\AppData\Local\Temp\RarSFX0\Data3.7z" -o"C:\Program Files\CyberLink\PowerDVD23" -aoa | C:\Users\admin\AppData\Local\Temp\RarSFX0\7z.exe | Setup.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Console Version: 21.07 Modules
| |||||||||||||||
| 3416 | "C:\Windows\System32\cmd.exe" /NOCONSOLE /C PowerShell Add-MpPreference -ExclusionPath "\"C:\Program Files\CyberLink\PowerDVD23\"" | C:\Windows\System32\cmd.exe | — | WDExclusionPathTool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
32 330
Read events
31 418
Write events
840
Delete events
72
Modification events
| (PID) Process: | (6508) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6508) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6508) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6508) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6508) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6396) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000E0C435A16363DB01 | |||
| (PID) Process: | (6244) CyberLink_PowerDVD_Downloader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Installer\NSIS_CL_DOWNLOADER |
| Operation: | write | Name: | ProcessID |
Value: 6244 | |||
| (PID) Process: | (6244) CyberLink_PowerDVD_Downloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6244) CyberLink_PowerDVD_Downloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6244) CyberLink_PowerDVD_Downloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\CyberLink\CBE |
| Operation: | write | Name: | UUID |
Value: S-1-5-21-1693682860-607145093-2874071422-1001-321A6979-B77C-476F-A9C5-2839653D9ACE | |||
Executable files
315
Suspicious files
300
Text files
936
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF135e21.TMP | — | |
MD5:— | SHA256:— | |||
| 6508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF135e21.TMP | — | |
MD5:— | SHA256:— | |||
| 6508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF135e30.TMP | — | |
MD5:— | SHA256:— | |||
| 6508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF135e30.TMP | — | |
MD5:— | SHA256:— | |||
| 6508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF135e30.TMP | — | |
MD5:— | SHA256:— | |||
| 6508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6508 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF135e30.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
63
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6244 | CyberLink_PowerDVD_Downloader.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQlOydjtpho0%2Bholo77zGjGxETUEQQU8JyF%2FaKffY%2FJaLvV1IlNHb7TkP8CEAVFaTHLrLGXEit%2BIwEWZ1o%3D | unknown | — | — | whitelisted |
6728 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3700 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6356 | vcredist_x64.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
3700 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6356 | vcredist_x64.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | — | — | whitelisted |
6356 | vcredist_x64.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.73:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4308 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.73:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5064 | SearchApp.exe | 2.23.227.221:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6904 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6508 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
kr.cyberlink.com |
| whitelisted |
accounts.google.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
update.cyberlink.com |
| whitelisted |
Threats
Process | Message |
|---|---|
CyberLink_PowerDVD_Downloader.exe | [UpdateThread] Patch INI: |
CyberLink_PowerDVD_Downloader.exe | [UpdateThread] Install Path C:\Program Files\CyberLink\PowerDVD23, Total File count 0 |
CyberLink_PowerDVD_Downloader.exe | [UpdateThread] Page Count: 5, Freq: 5 |
CyberLink_PowerDVD_Downloader.exe | [UpdateThread] StartUpdate |
CyberLink_PowerDVD_Downloader.exe | [UpdateThread] Ini Path: C:\ProgramData\SUPPORTDIR\20250110_132920_6244\Setup\Utility\Promotion\Enu\Promotion.ini |
CyberLink_PowerDVD_Downloader.exe | [UpdateThread] Image: 459424, Title: 524964, Wording: 393926, Show: 1 |
CyberLink_PowerDVD_Downloader.exe | [UpdateThread] Image Folder: C:\ProgramData\SUPPORTDIR\20250110_132920_6244\Setup\Utility\Promotion\image |
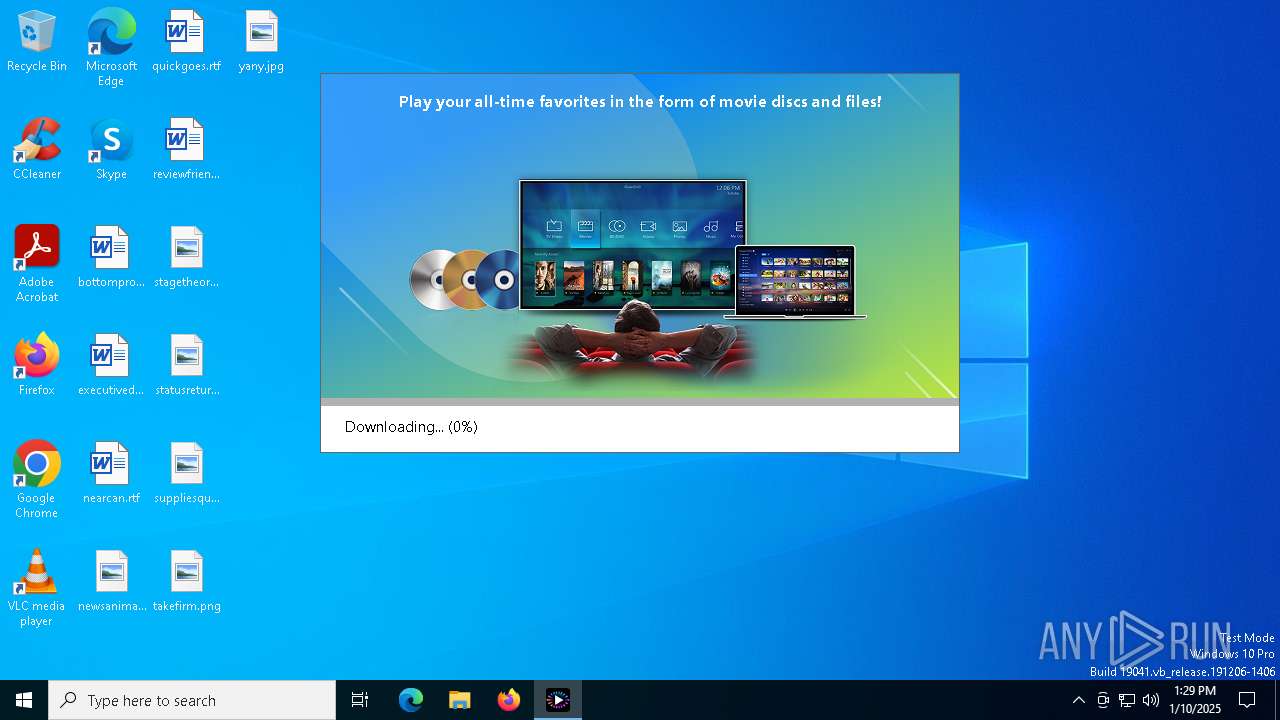
CyberLink_PowerDVD_Downloader.exe | [UpdateThread] Page 1 Image: C:\ProgramData\SUPPORTDIR\20250110_132920_6244\Setup\Utility\Promotion\image\image_001.jpg |
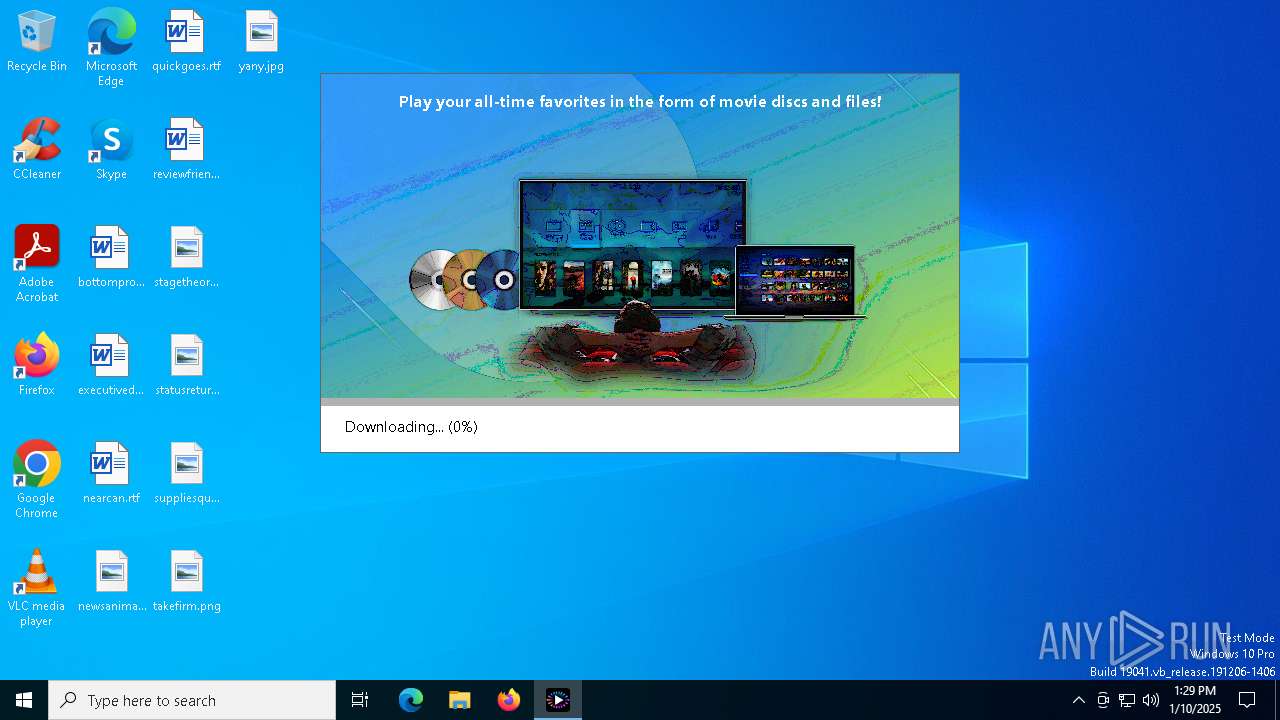
CyberLink_PowerDVD_Downloader.exe | [UpdateThread] Progress: 0, Percent: 0, Complete String: Downloading |
CyberLink_PowerDVD_Downloader.exe | [UpdateThread] Image Width: 640, Height: 324 |