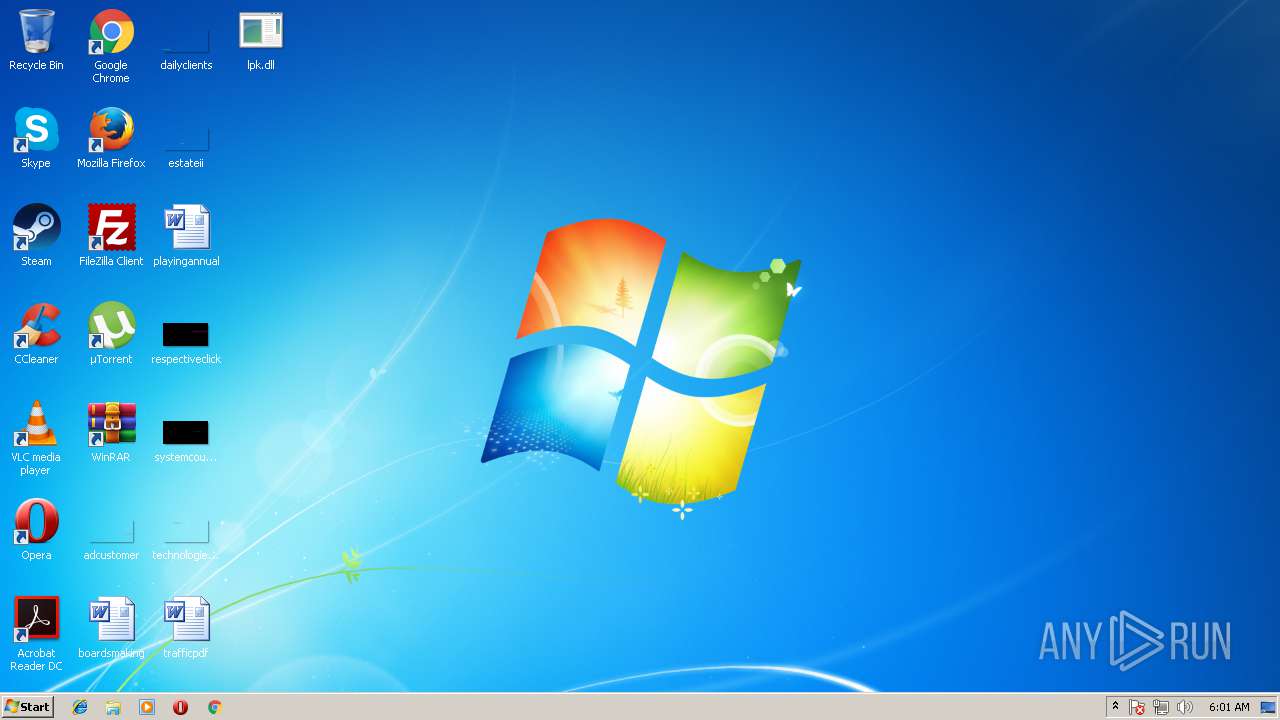
| File name: | lpk.dll |
| Full analysis: | https://app.any.run/tasks/97c6e3af-c3af-4690-a93b-c10e50737d12 |
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2018, 05:01:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | DF4D2FA38084A819DA7872C69F321C58 |
| SHA1: | 484FEA6E2735364A2C8EDD5E1E6437FEFCED6B3E |
| SHA256: | 79888946752FD130CE76FE731F323709707854AD6A3E3F6FCA347FDCA70F0819 |
| SSDEEP: | 768:7ojY9P4EOdb8snjaYsRQVfDbZgoWyHBojY9Po:OmgEOdAsnfZgoWyHUmg |
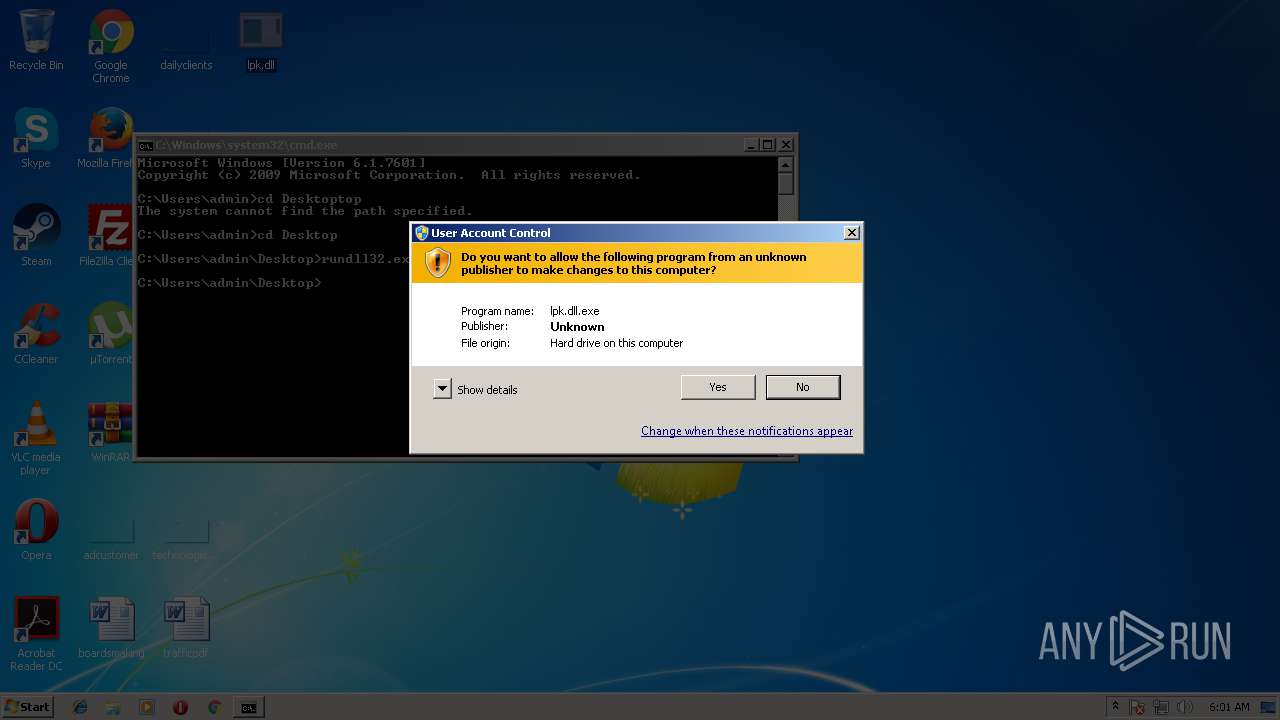
MALICIOUS
Application was dropped or rewritten from another process
- hrl403A.tmp (PID: 4092)
Loads dropped or rewritten executable
- explorer.exe (PID: 1380)
- svchost.exe (PID: 880)
- consent.exe (PID: 3736)
Runs app for hidden code execution
- explorer.exe (PID: 1380)
SUSPICIOUS
Executable content was dropped or overwritten
- hrl403A.tmp (PID: 4092)
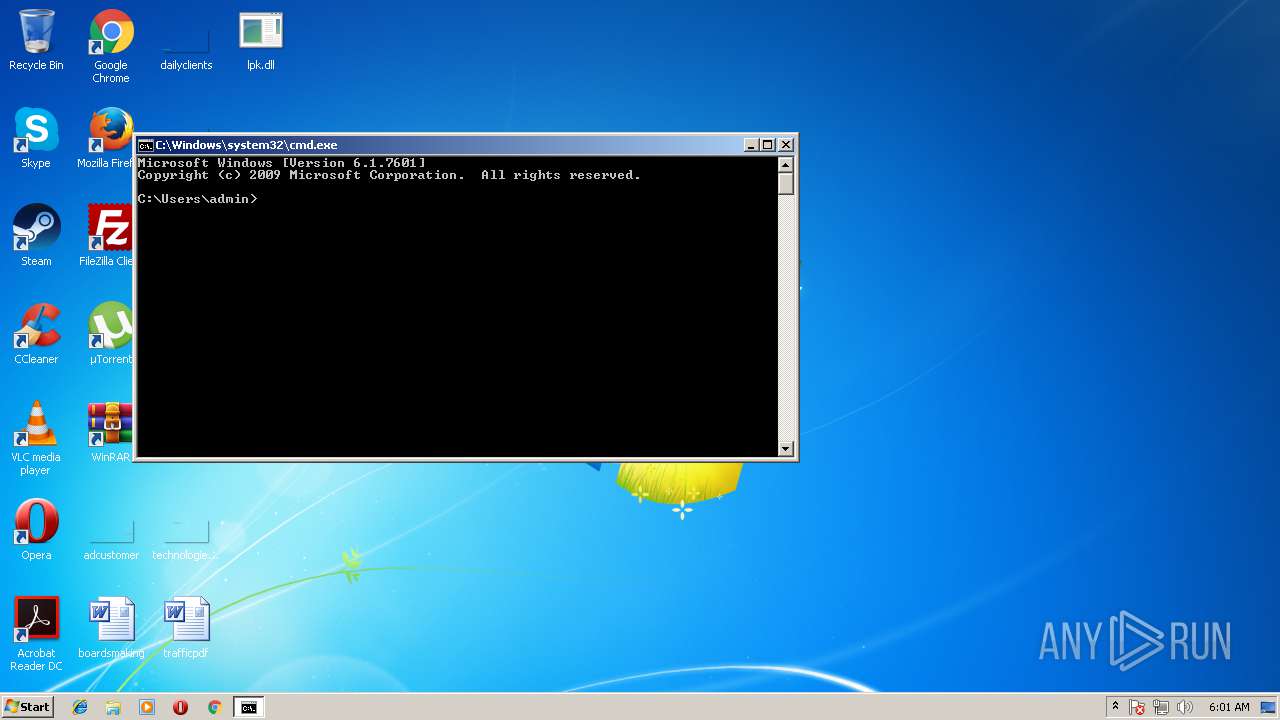
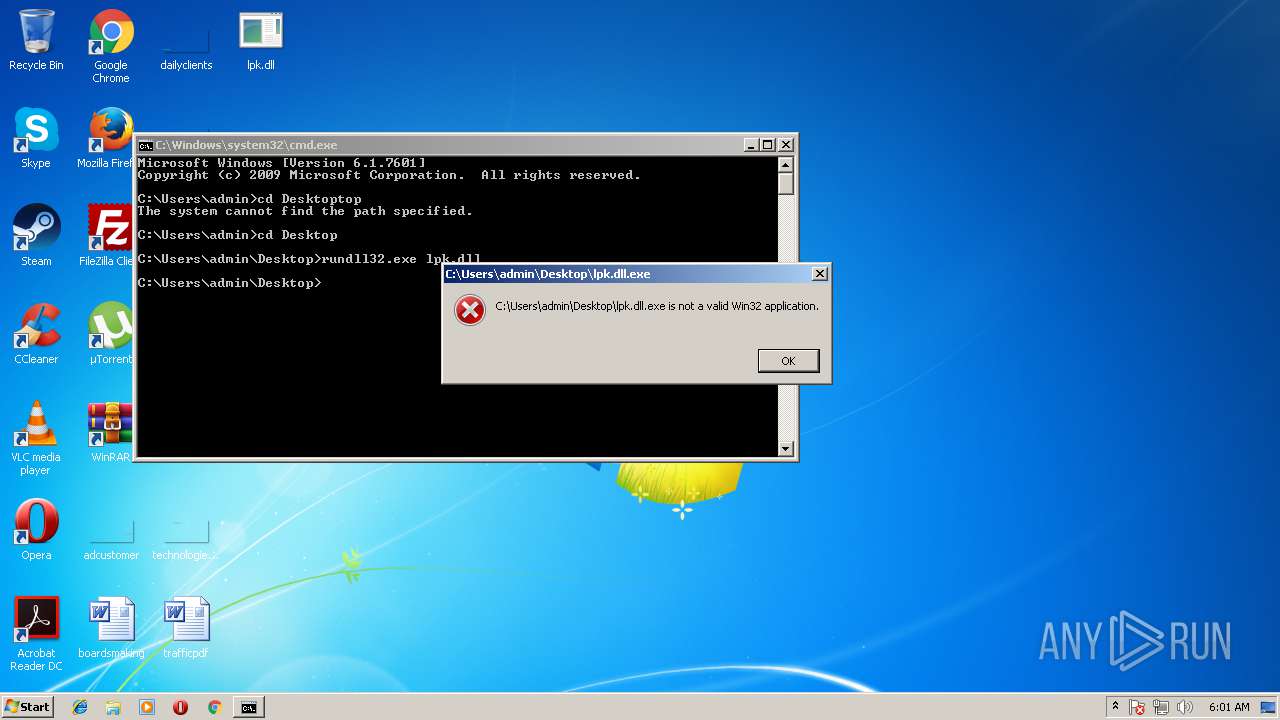
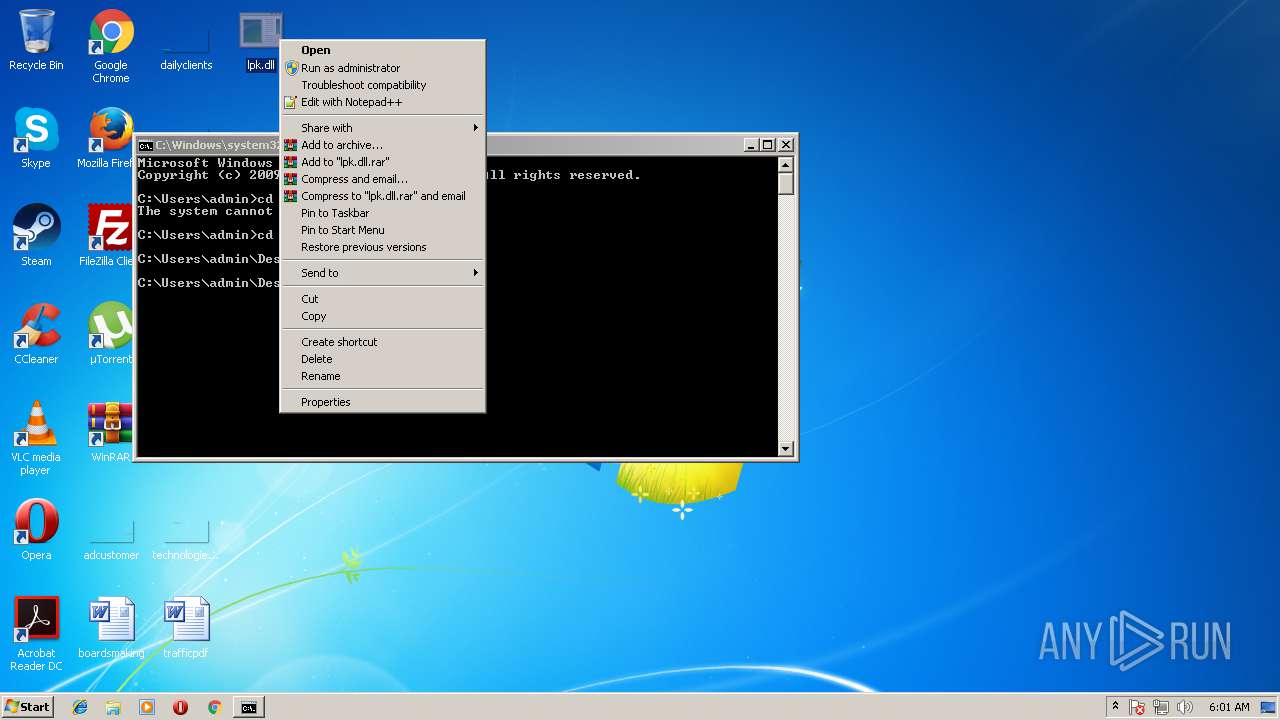
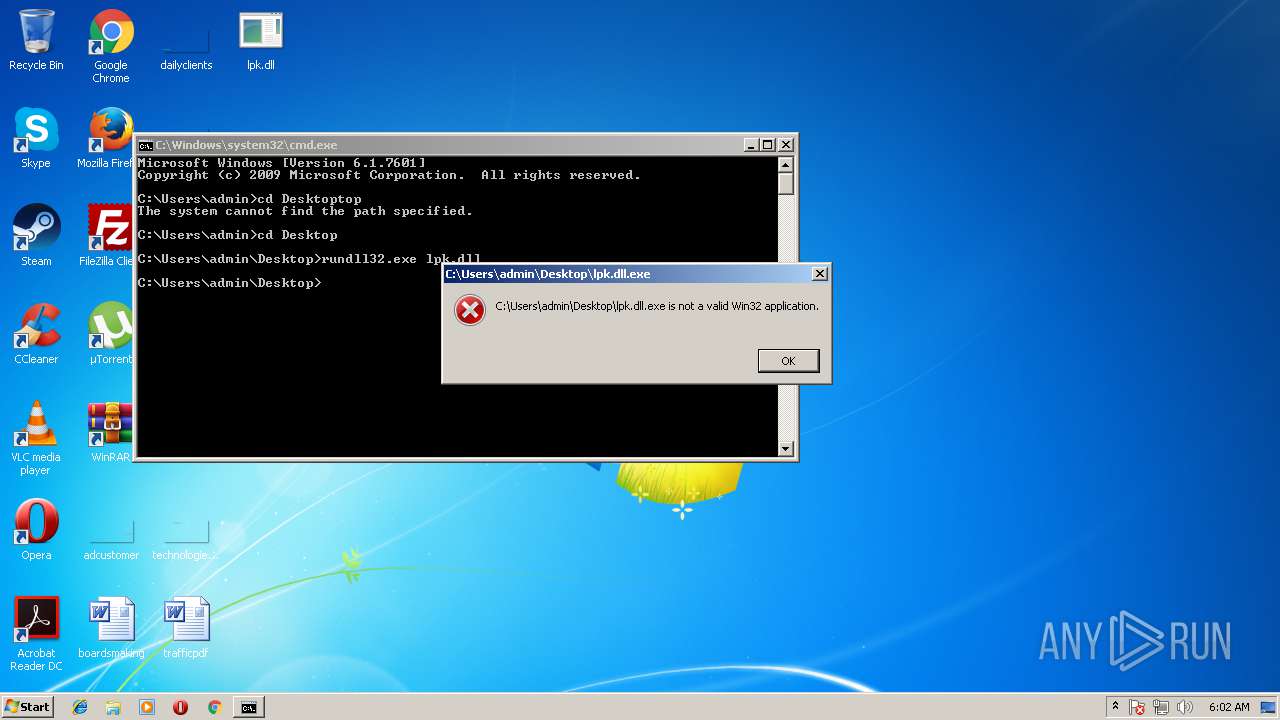
Starts application with an unusual extension
- rundll32.exe (PID: 384)
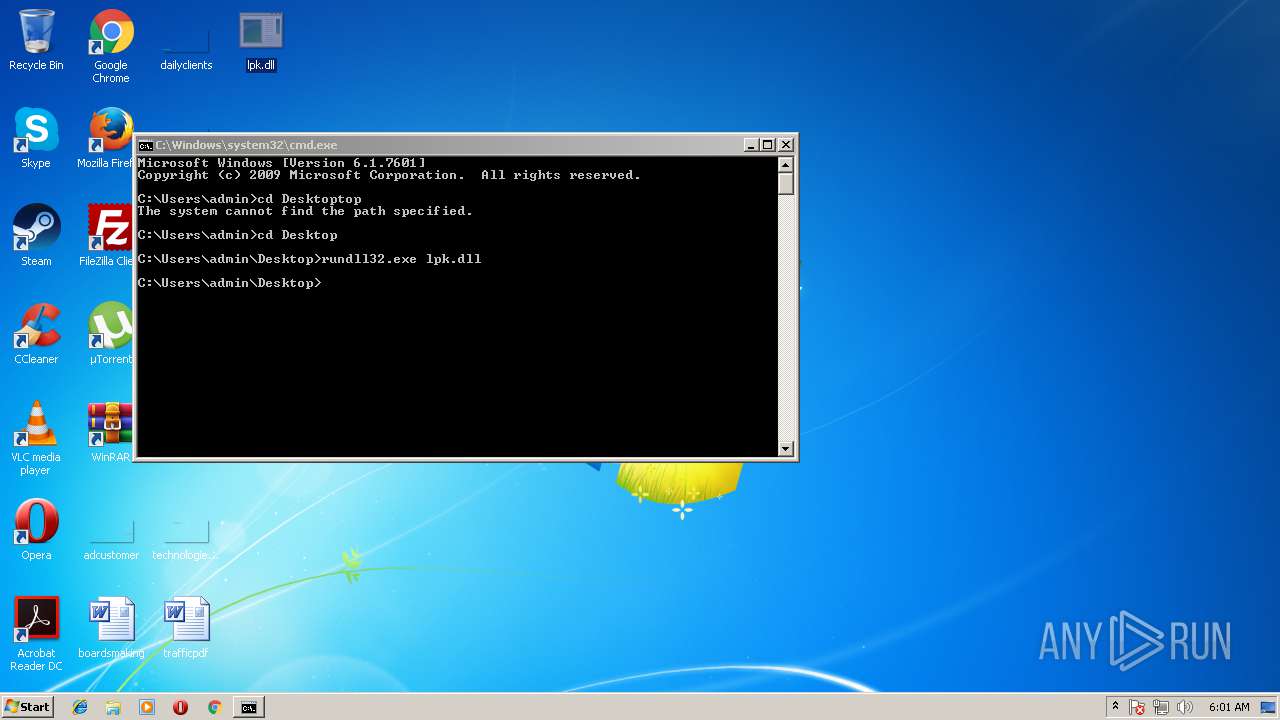
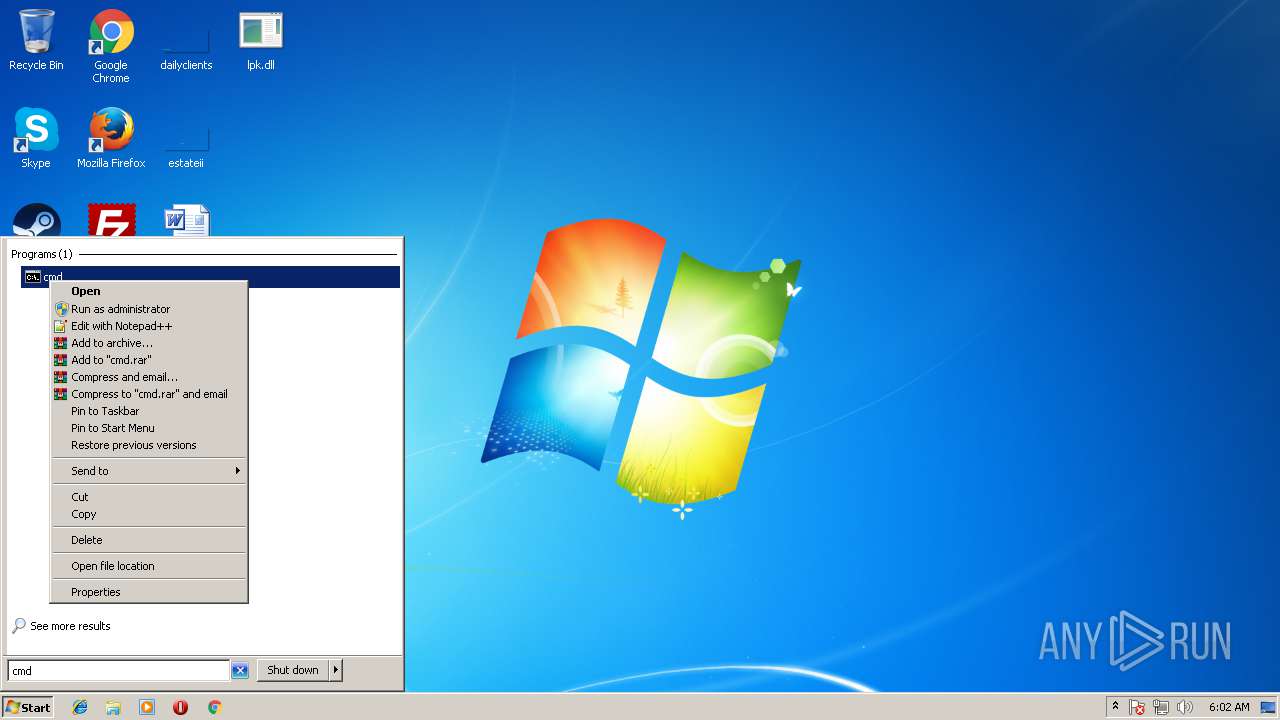
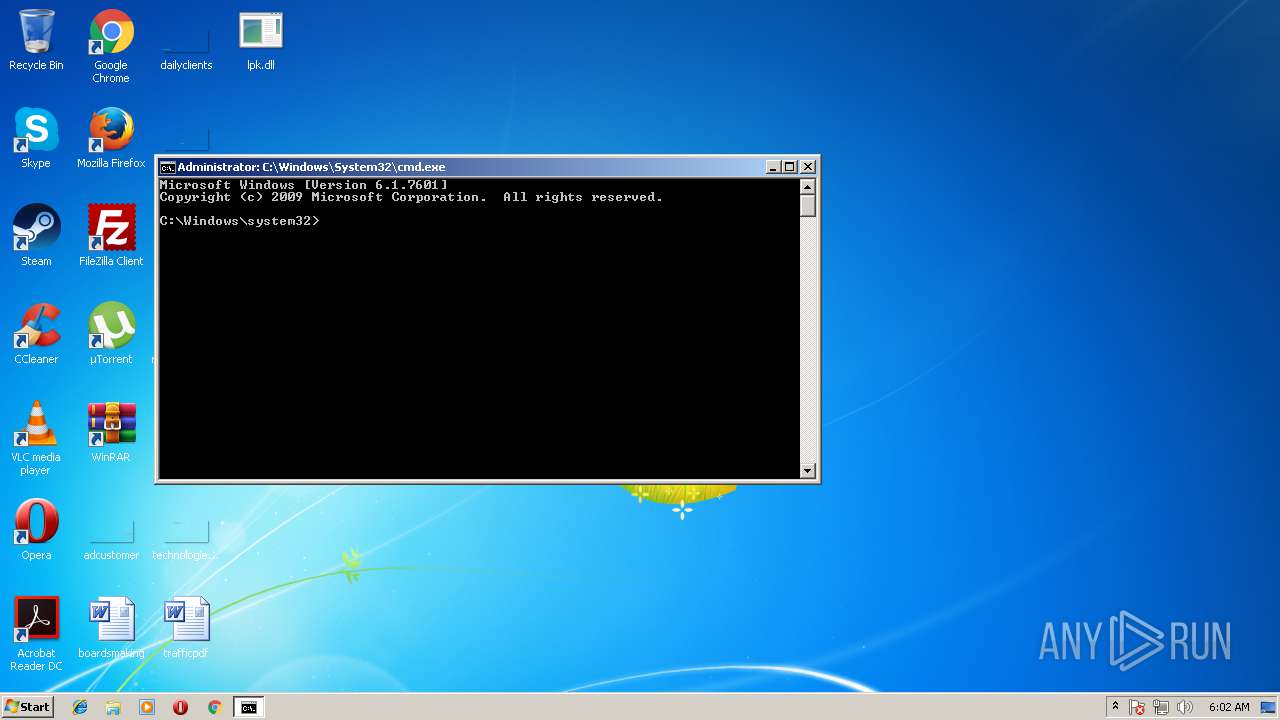
Starts CMD.EXE for commands execution
- explorer.exe (PID: 1380)
INFO
Loads main object executable
- rundll32.exe (PID: 384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:06:08 11:59:36+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 3072 |
| InitializedDataSize: | 40448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1a32 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Jun-2010 09:59:36 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 08-Jun-2010 09:59:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000B2C | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.54695 |
.rdata | 0x00002000 | 0x000009C9 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.84826 |
.data | 0x00003000 | 0x000002A0 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00004000 | 0x00009094 | 0x00009200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.89258 |
.reloc | 0x0000E000 | 0x000001EE | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.09183 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
101 | 3.25163 | 12 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
102 | 5.88342 | 36864 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
LpkTabbedTextOut | 1 | 0x00001AF0 |
LpkDllInitialize | 2 | 0x00001AF6 |
LpkDrawTextEx | 3 | 0x00001AFC |
LpkEditControl | 4 | 0x00003250 |
LpkExtTextOut | 5 | 0x00001B02 |
LpkGetCharacterPlacement | 6 | 0x00001B08 |
LpkGetTextExtentExPoint | 7 | 0x00001B0E |
LpkInitialize | 8 | 0x00001B14 |
LpkPSMTextOut | 9 | 0x00001B1A |
LpkUseGDIWidthCache | 10 | 0x00001B20 |
Total processes
46
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 384 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\Desktop\lpk.dll.exe", LpkTabbedTextOut | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 880 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2720 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3588 | rundll32.exe lpk.dll | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
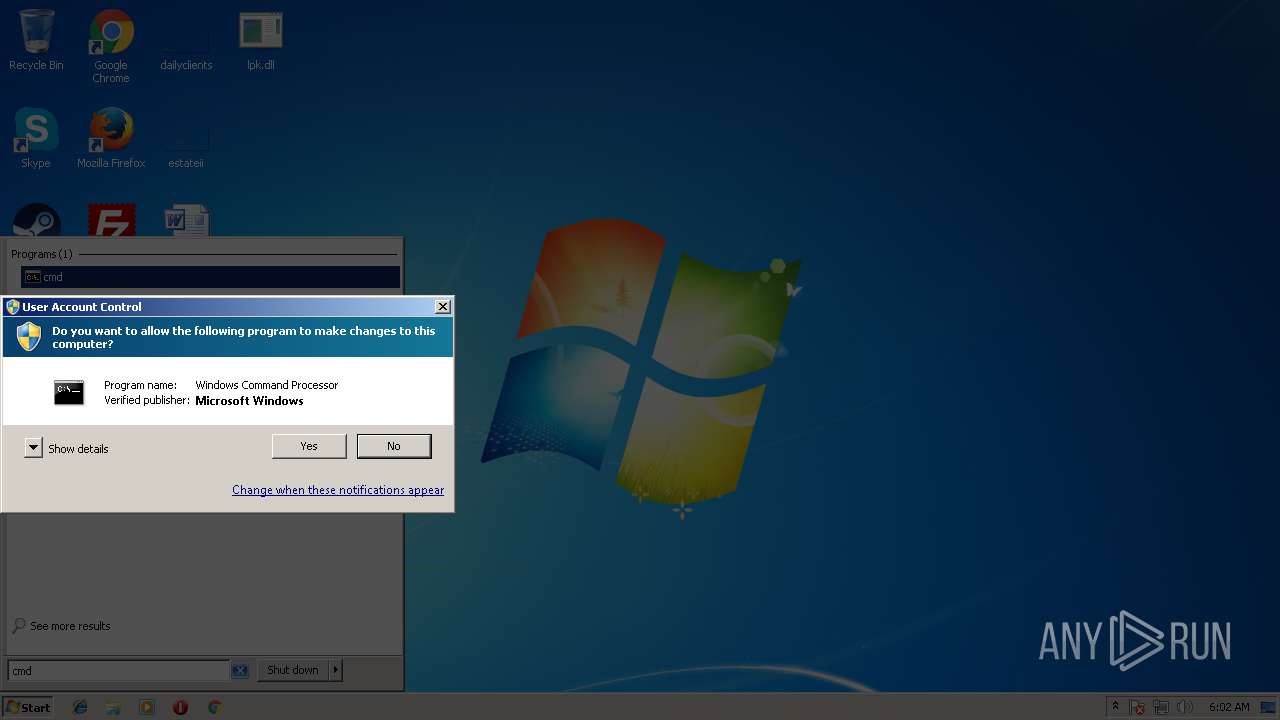
| 3736 | consent.exe 880 282 001F9A80 | C:\Windows\system32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 3221225547 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4064 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4092 | C:\Users\admin\AppData\Local\Temp\hrl403A.tmp | C:\Users\admin\AppData\Local\Temp\hrl403A.tmp | rundll32.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 719
Read events
1 119
Write events
600
Delete events
0
Modification events
| (PID) Process: | (1380) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1380) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\pzq.rkr |
Value: 00000000020000000100000069900000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFE0685689422DD40100000000 | |||
| (PID) Process: | (1380) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004D0000007100000041CC18000A00000009000000B64206007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C0072006500670065006400690074002E0065007800650000004D00D8674D003076B90618AB4E000100000068E9E101F0E9E101FCEFE101EDE00B77347B1800FEFFFFFFE72F0F77822E0F770000000004EBE1010000000078EAE1010000000078EAE1017800000030EAE101FE720F773CEBE10160EDE101780000001800000078EAE101000000004CEAE10151EE0F77F48EF6760000000004EBE1011E00000070EAE10120EF0F773076B9060AA50E771E0000000000000004EBE10100000000F88EF676F0EAE101D6A810778CEAE101A4EAE101000000000000000000004D003076B9065A008A004E76B9060A001900011B8A11A4EAE10100000000010500001876B90611000000A045500098455000E82C0F7754EBE1011000000034EB0000A2F8B40EE4EAE1018291597534EBE101049300008EF8B40EF8EAE101B69C597508934D025C0000000401000098F5E10158F5E10111000000A04550009845500098F5E101785BE203FA4FEE730000000088EB00004EF9B40E38EBE1018291597588EBE1013CEBE101279559750000000004934D0264EBE101CD94597504934D0210ECE101788E4D02E194597500000000788E4D0210ECE1016CEBE101070000002B000000BA2904007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000070EAE101FFFFFFFFE0B55100FFFFFFFF90492B7500000000000000000CEAE101D5742775000400000000000070EAE101FFFFFFFFE0B55100FFFFFFFFD0155200D4165200D8B551003CEAE1012FB1587580B08B757CF7E101381E597514635975A016500070EAE101308351007000000052F8B40E50EAE101BE6A5975A016500070EAE101000000007CECE1016F625975A016500070EAE10100000400000000807C625975A016500063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E00670011000000A04550009845500073006F00660074005C00690034EB0000A2F8B40EE4EAE1018291597534EBE101049300008EF8B40EF8EAE101B69C597508934D024C06000010EBE101788E4D021CEBE10111000000A04550009845500010EBE101BCEBE101B8EBE101988E4D0288EB00004EF9B40E38EBE1018291597588EBE1013CEBE101279559750000000004934D0264EBE101CD94597504934D0210ECE101788E4D02E194597500000000788E4D0210ECE1016CEBE101070000002B000000BA2904007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000070EAE101FFFFFFFFE0B55100FFFFFFFF90492B7500000000000000000CEAE101D5742775000400000000000070EAE101FFFFFFFFE0B55100FFFFFFFFD0155200D4165200D8B551003CEAE1012FB1587580B08B757CF7E101381E597514635975A016500070EAE101308351007000000052F8B40E50EAE101BE6A5975A016500070EAE101000000007CECE1016F625975A016500070EAE10100000400000000807C625975A016500063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E00670011000000A04550009845500073006F00660074005C00690034EB0000A2F8B40EE4EAE1018291597534EBE101049300008EF8B40EF8EAE101B69C597508934D024C06000010EBE101788E4D021CEBE10111000000A04550009845500010EBE101BCEBE101B8EBE101988E4D0288EB00004EF9B40E38EBE1018291597588EBE1013CEBE101279559750000000004934D0264EBE101CD94597504934D0210ECE101788E4D02E194597500000000788E4D0210ECE1016CEBE101 | |||
| (PID) Process: | (1380) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\pzq.rkr |
Value: 0000000002000000010000000EDB0000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFE0685689422DD40100000000 | |||
| (PID) Process: | (1380) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004D00000071000000E61619000A00000009000000B64206007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C0072006500670065006400690074002E0065007800650000004D00D8674D003076B90618AB4E000100000068E9E101F0E9E101FCEFE101EDE00B77347B1800FEFFFFFFE72F0F77822E0F770000000004EBE1010000000078EAE1010000000078EAE1017800000030EAE101FE720F773CEBE10160EDE101780000001800000078EAE101000000004CEAE10151EE0F77F48EF6760000000004EBE1011E00000070EAE10120EF0F773076B9060AA50E771E0000000000000004EBE10100000000F88EF676F0EAE101D6A810778CEAE101A4EAE101000000000000000000004D003076B9065A008A004E76B9060A001900011B8A11A4EAE10100000000010500001876B90611000000A045500098455000E82C0F7754EBE1011000000034EB0000A2F8B40EE4EAE1018291597534EBE101049300008EF8B40EF8EAE101B69C597508934D025C0000000401000098F5E10158F5E10111000000A04550009845500098F5E101785BE203FA4FEE730000000088EB00004EF9B40E38EBE1018291597588EBE1013CEBE101279559750000000004934D0264EBE101CD94597504934D0210ECE101788E4D02E194597500000000788E4D0210ECE1016CEBE101070000002B000000BA2904007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000070EAE101FFFFFFFFE0B55100FFFFFFFF90492B7500000000000000000CEAE101D5742775000400000000000070EAE101FFFFFFFFE0B55100FFFFFFFFD0155200D4165200D8B551003CEAE1012FB1587580B08B757CF7E101381E597514635975A016500070EAE101308351007000000052F8B40E50EAE101BE6A5975A016500070EAE101000000007CECE1016F625975A016500070EAE10100000400000000807C625975A016500063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E00670011000000A04550009845500073006F00660074005C00690034EB0000A2F8B40EE4EAE1018291597534EBE101049300008EF8B40EF8EAE101B69C597508934D024C06000010EBE101788E4D021CEBE10111000000A04550009845500010EBE101BCEBE101B8EBE101988E4D0288EB00004EF9B40E38EBE1018291597588EBE1013CEBE101279559750000000004934D0264EBE101CD94597504934D0210ECE101788E4D02E194597500000000788E4D0210ECE1016CEBE101070000002B000000BA2904007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000070EAE101FFFFFFFFE0B55100FFFFFFFF90492B7500000000000000000CEAE101D5742775000400000000000070EAE101FFFFFFFFE0B55100FFFFFFFFD0155200D4165200D8B551003CEAE1012FB1587580B08B757CF7E101381E597514635975A016500070EAE101308351007000000052F8B40E50EAE101BE6A5975A016500070EAE101000000007CECE1016F625975A016500070EAE10100000400000000807C625975A016500063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E00670011000000A04550009845500073006F00660074005C00690034EB0000A2F8B40EE4EAE1018291597534EBE101049300008EF8B40EF8EAE101B69C597508934D024C06000010EBE101788E4D021CEBE10111000000A04550009845500010EBE101BCEBE101B8EBE101988E4D0288EB00004EF9B40E38EBE1018291597588EBE1013CEBE101279559750000000004934D0264EBE101CD94597504934D0210ECE101788E4D02E194597500000000788E4D0210ECE1016CEBE101 | |||
| (PID) Process: | (1380) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | @sendmail.dll,-21 |
Value: Desktop (create shortcut) | |||
| (PID) Process: | (1380) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | @zipfldr.dll,-10148 |
Value: Compressed (zipped) folder | |||
| (PID) Process: | (1380) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | @sendmail.dll,-4 |
Value: Mail recipient | |||
| (PID) Process: | (1380) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\FXSRESM.dll,-120 |
Value: Fax recipient | |||
| (PID) Process: | (1380) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\WFS.exe |
Value: Microsoft Windows Fax and Scan | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 384 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\hrl403A.tmp | — | |
MD5:— | SHA256:— | |||
| 880 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 4092 | hrl403A.tmp | C:\Users\admin\AppData\Local\Temp\SOFTWARE.LOG | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report