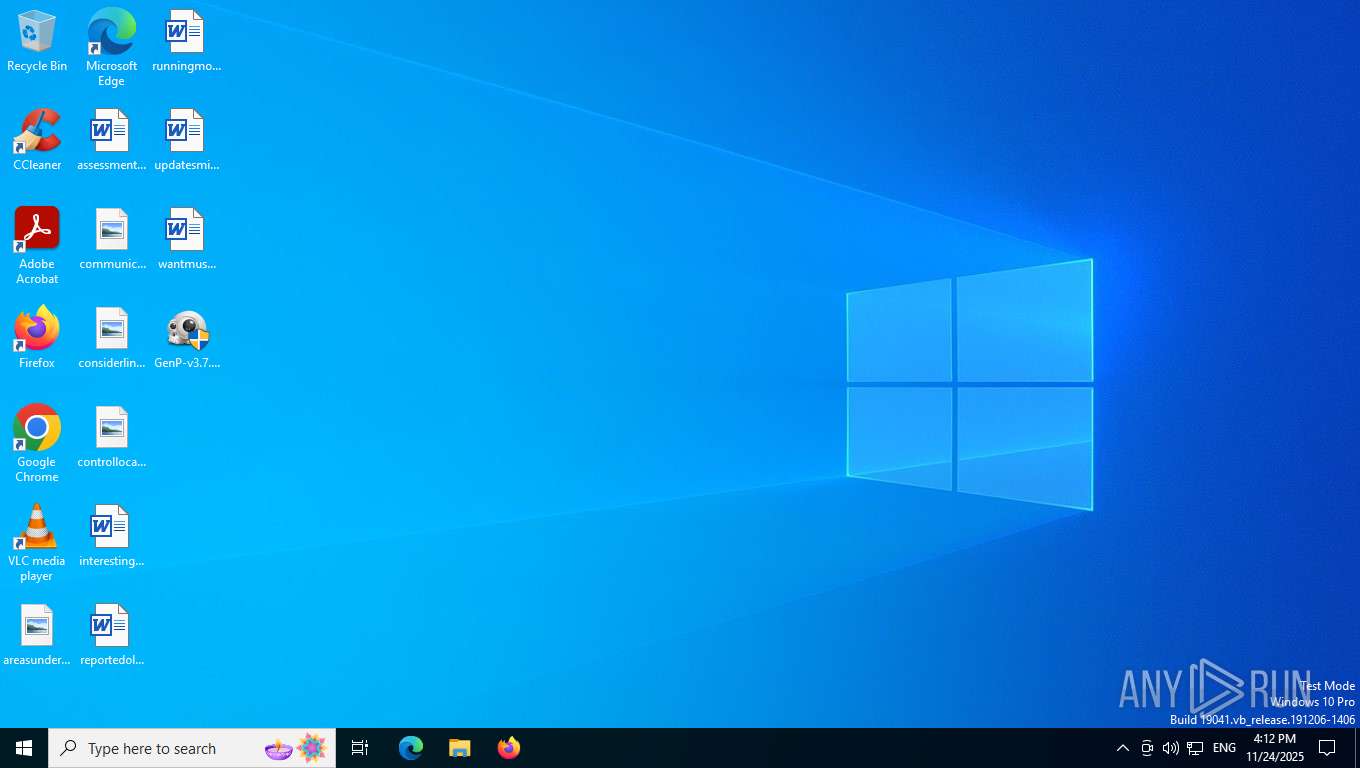
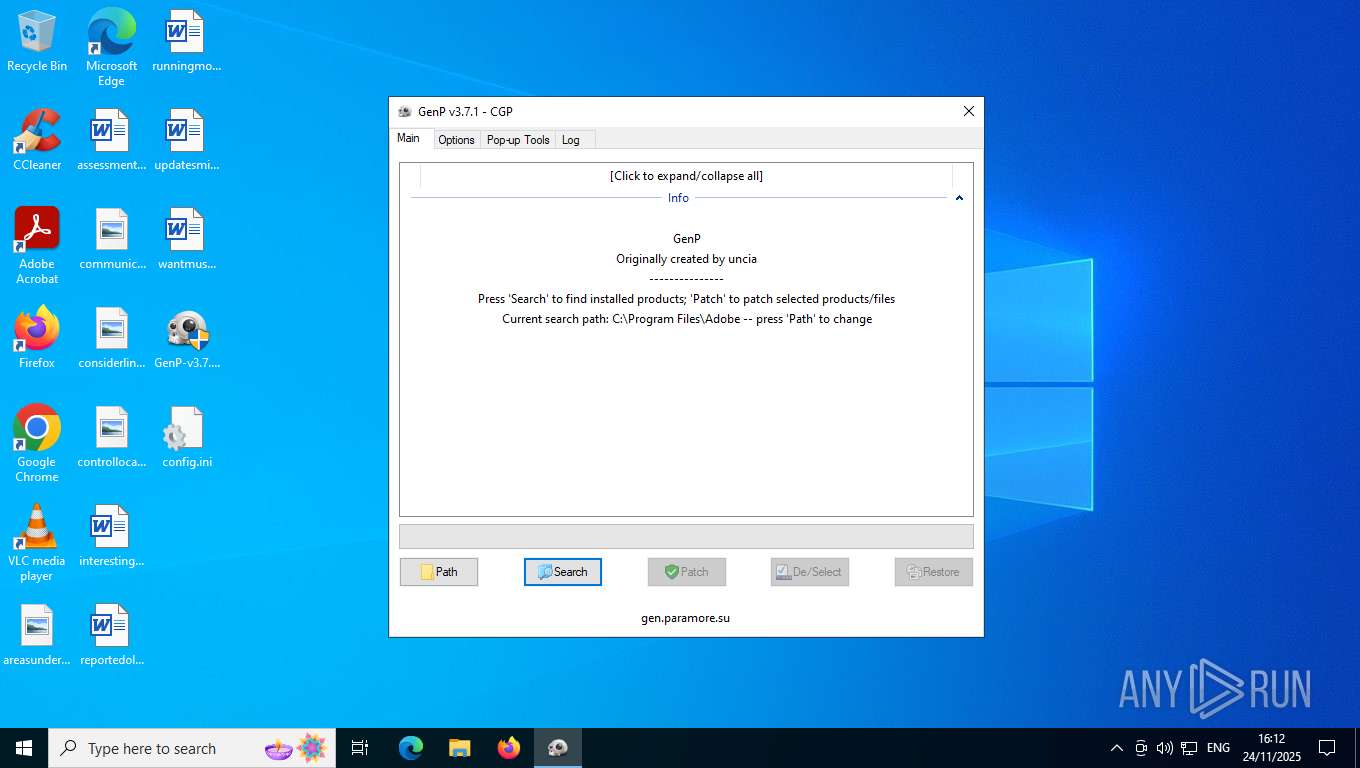
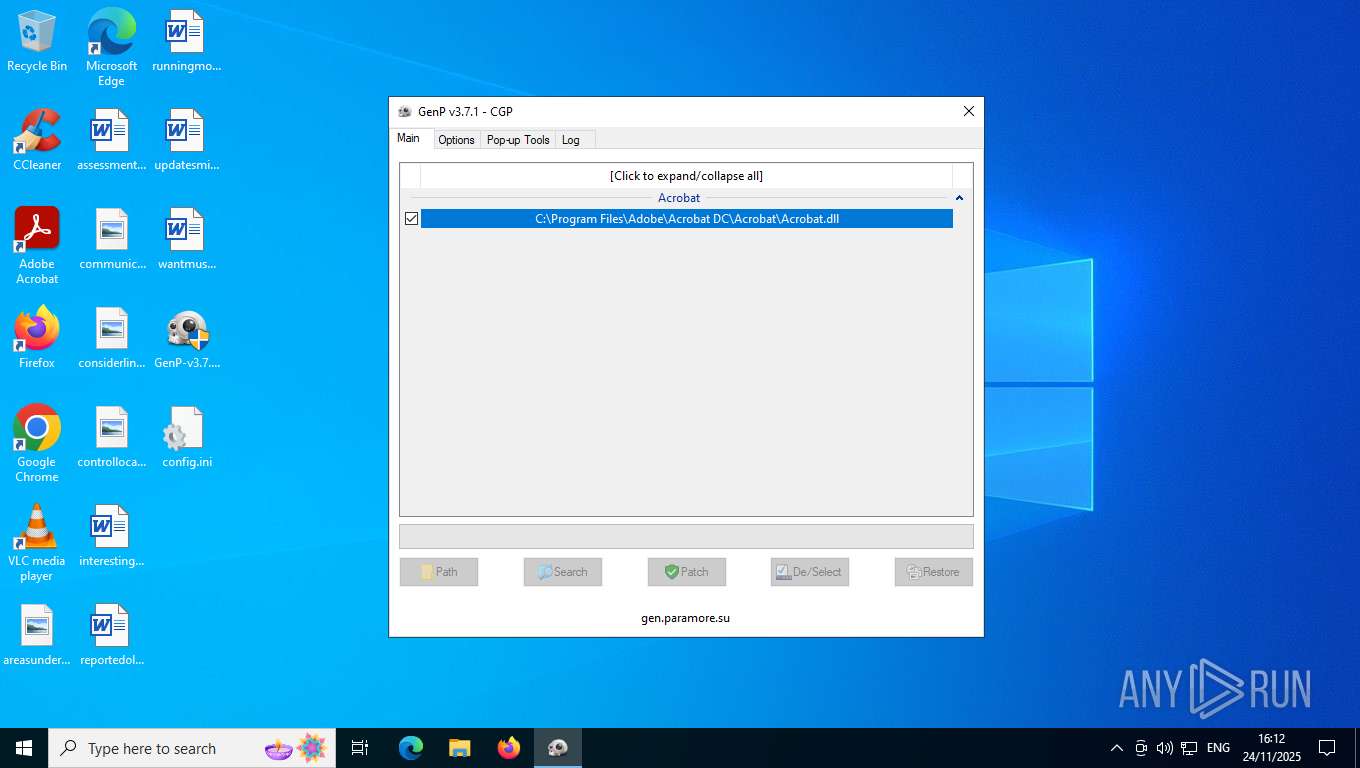
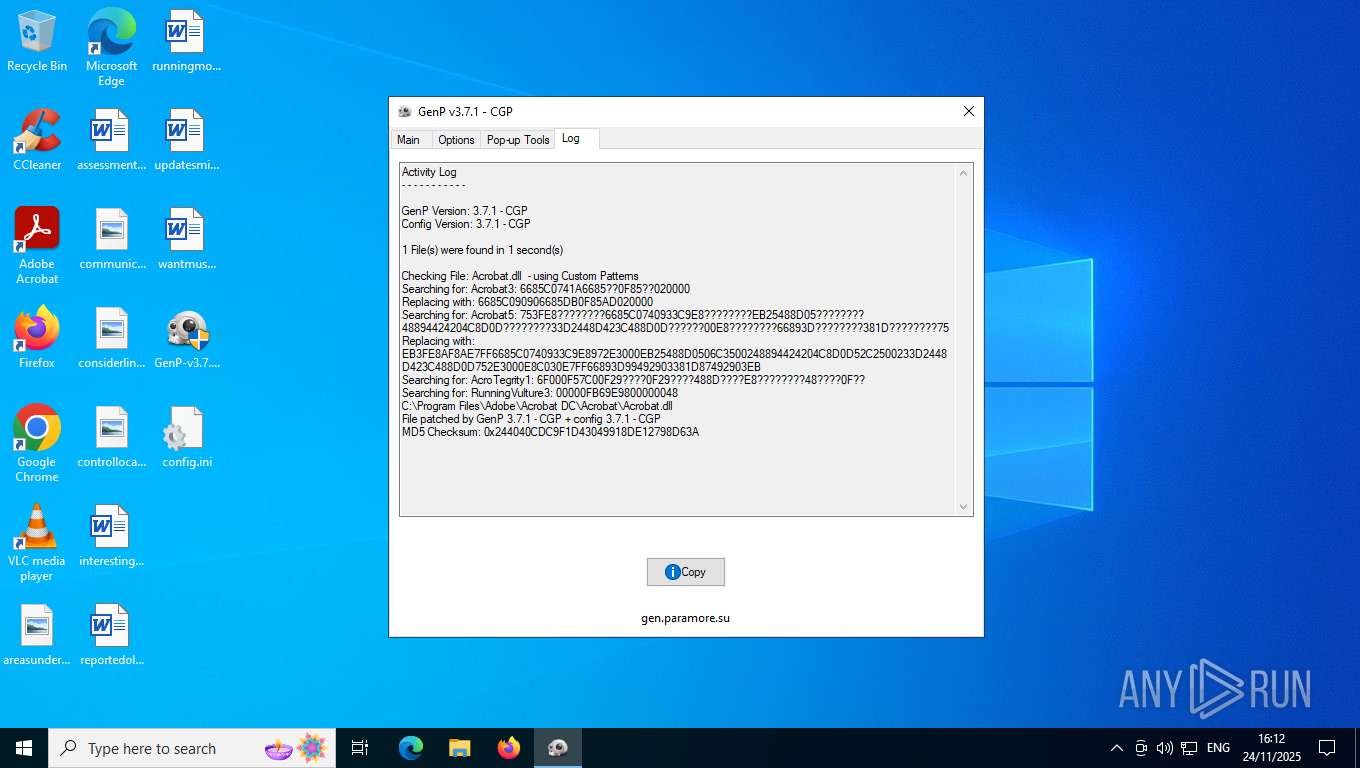
| File name: | GenP-v3.7.1.exe |
| Full analysis: | https://app.any.run/tasks/865fe7fd-1ec8-4e35-995d-30fe1020ce9c |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2025, 16:12:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 3 sections |
| MD5: | 7E4F27D40A70D78FEDFE7E0EBFF28AE1 |
| SHA1: | 7CB6262C23830708DBD11BDCB1203DF130478553 |
| SHA256: | 797253ADD1F9FDE1ECDBC49B02F4529746AA1B6005FCBD3817ADDDCF3E295EB9 |
| SSDEEP: | 49152:HetKmupSfNHjl4ClQaig25jSHY7GvXiADpB/7mP9HhIHAI/KlNKYOJCTOB2U20wI:+tKDpSRjVKjg25j1Shp181hWOKYYCTOl |
MALICIOUS
No malicious indicators.SUSPICIOUS
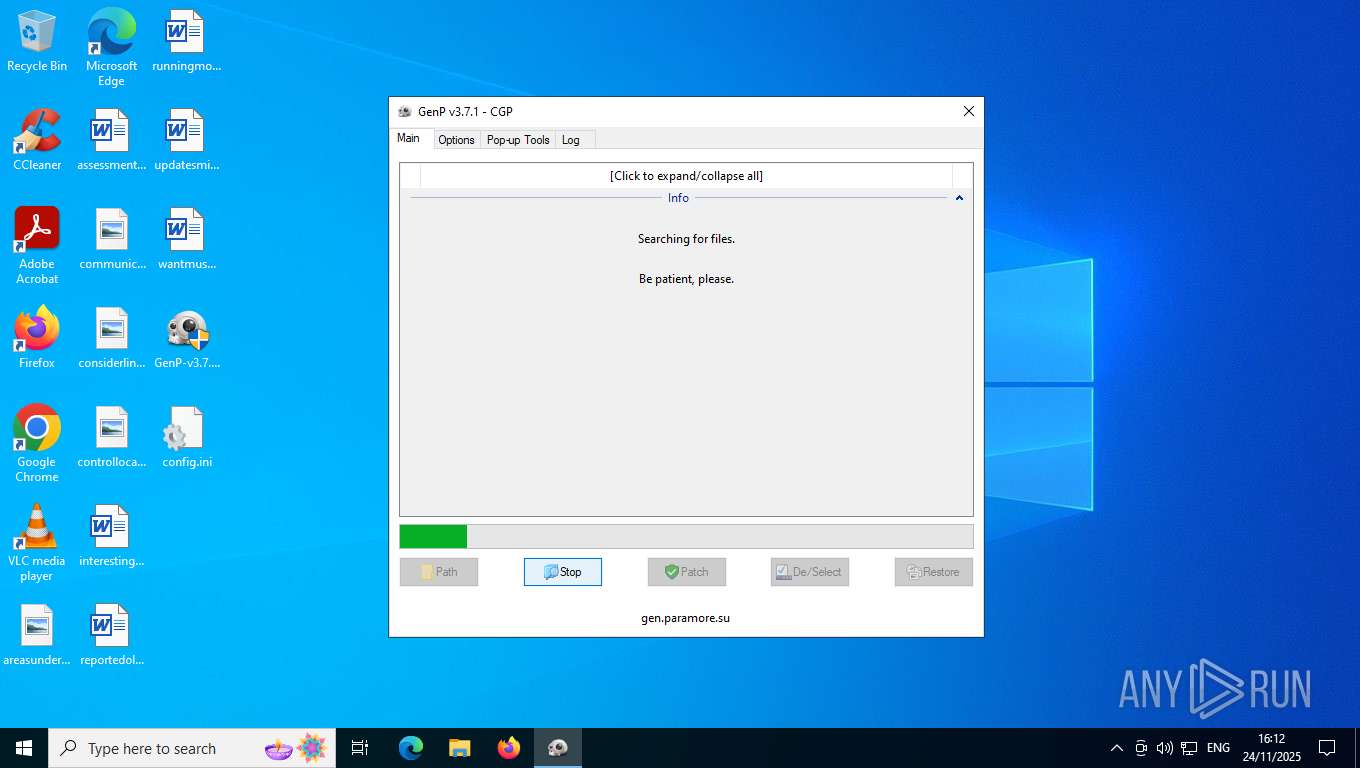
There is functionality for taking screenshot (YARA)
- GenP-v3.7.1.exe (PID: 7224)
INFO
Reads the computer name
- GenP-v3.7.1.exe (PID: 7224)
The sample compiled with english language support
- GenP-v3.7.1.exe (PID: 7224)
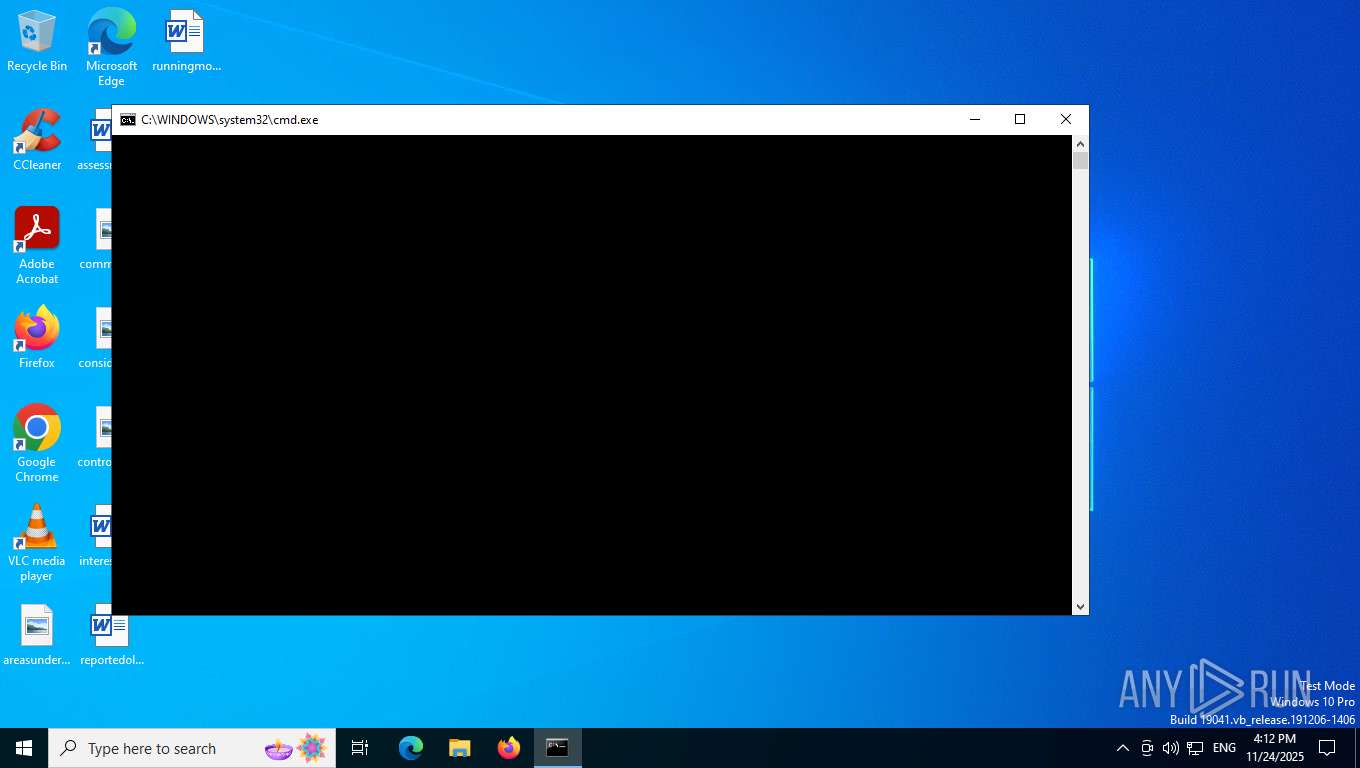
Create files in a temporary directory
- GenP-v3.7.1.exe (PID: 7224)
Checks supported languages
- GenP-v3.7.1.exe (PID: 7224)
Reads mouse settings
- GenP-v3.7.1.exe (PID: 7224)
UPX packer has been detected
- GenP-v3.7.1.exe (PID: 7224)
Reads the machine GUID from the registry
- GenP-v3.7.1.exe (PID: 7224)
The process uses AutoIt
- GenP-v3.7.1.exe (PID: 7224)
Creates files in the program directory
- GenP-v3.7.1.exe (PID: 7224)
Checks proxy server information
- slui.exe (PID: 7412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (87.1) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.4) |
| .exe | | | DOS Executable Generic (6.4) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:10:31 02:27:30+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 421888 |
| InitializedDataSize: | 1105920 |
| UninitializedDataSize: | 1740800 |
| EntryPoint: | 0x20fe70 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.7.1.0 |
| ProductVersionNumber: | 3.7.1.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 3.7.1.0 |
| Comments: | GenP |
| FileDescription: | GenP |
| ProductName: | GenP |
| ProductVersion: | 3.7.1 |
| CompanyName: | GenP |
| LegalCopyright: | GenP 2025 |
| LegalTradeMarks: | GenP 2025 |
Total processes
168
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 4048 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 5184 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UCPDMgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6264 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=134.0.6985.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x298,0x29c,0x2a0,0x274,0x2a4,0x102c460,0x102c46c,0x102c478 | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
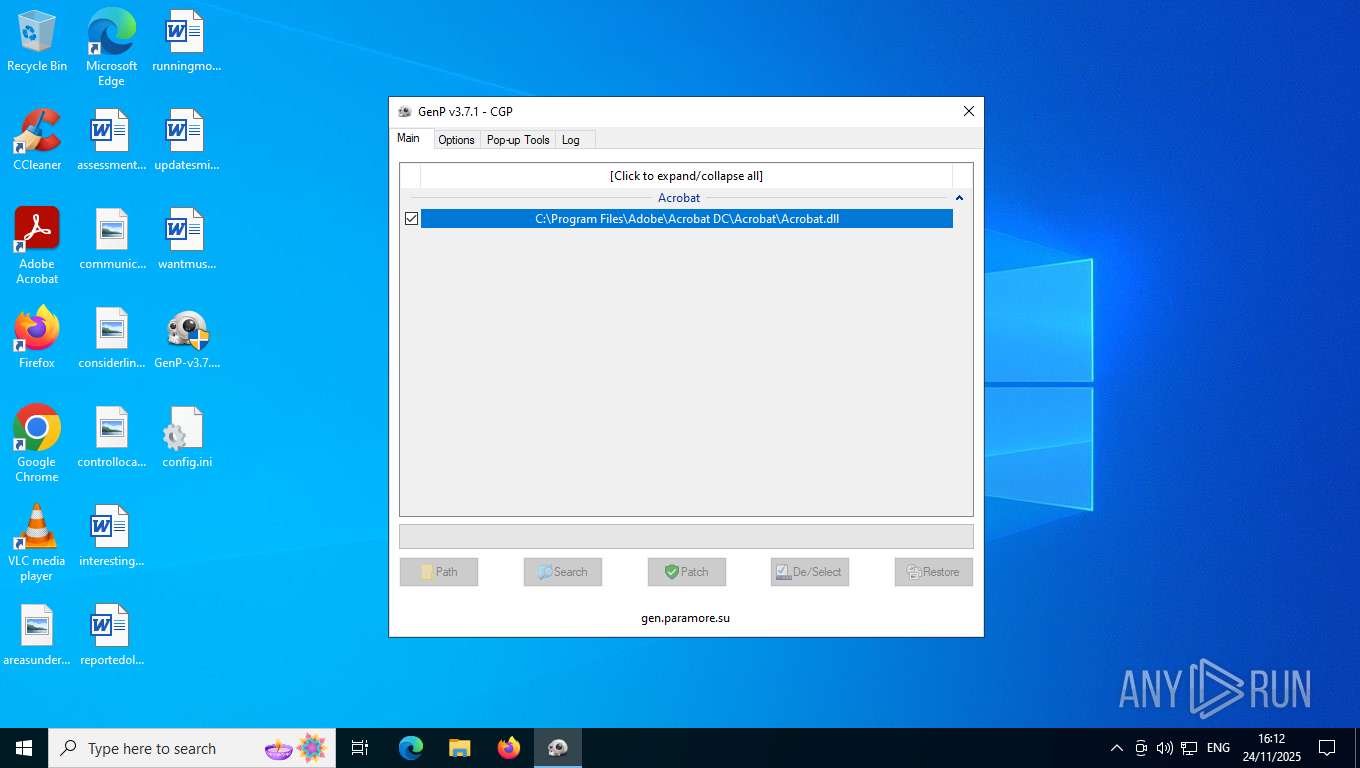
| 7224 | "C:\Users\admin\Desktop\GenP-v3.7.1.exe" | C:\Users\admin\Desktop\GenP-v3.7.1.exe | explorer.exe | ||||||||||||
User: admin Company: GenP Integrity Level: HIGH Description: GenP Version: 3.7.1.0 Modules
| |||||||||||||||
| 7412 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7920 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 7948 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UCPDMgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8156 | "C:\Users\admin\Desktop\GenP-v3.7.1.exe" | C:\Users\admin\Desktop\GenP-v3.7.1.exe | — | explorer.exe | |||||||||||
User: admin Company: GenP Integrity Level: MEDIUM Description: GenP Exit code: 3221226540 Version: 3.7.1.0 Modules
| |||||||||||||||
Total events
3 625
Read events
3 625
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
1
Text files
1
Unknown types
0
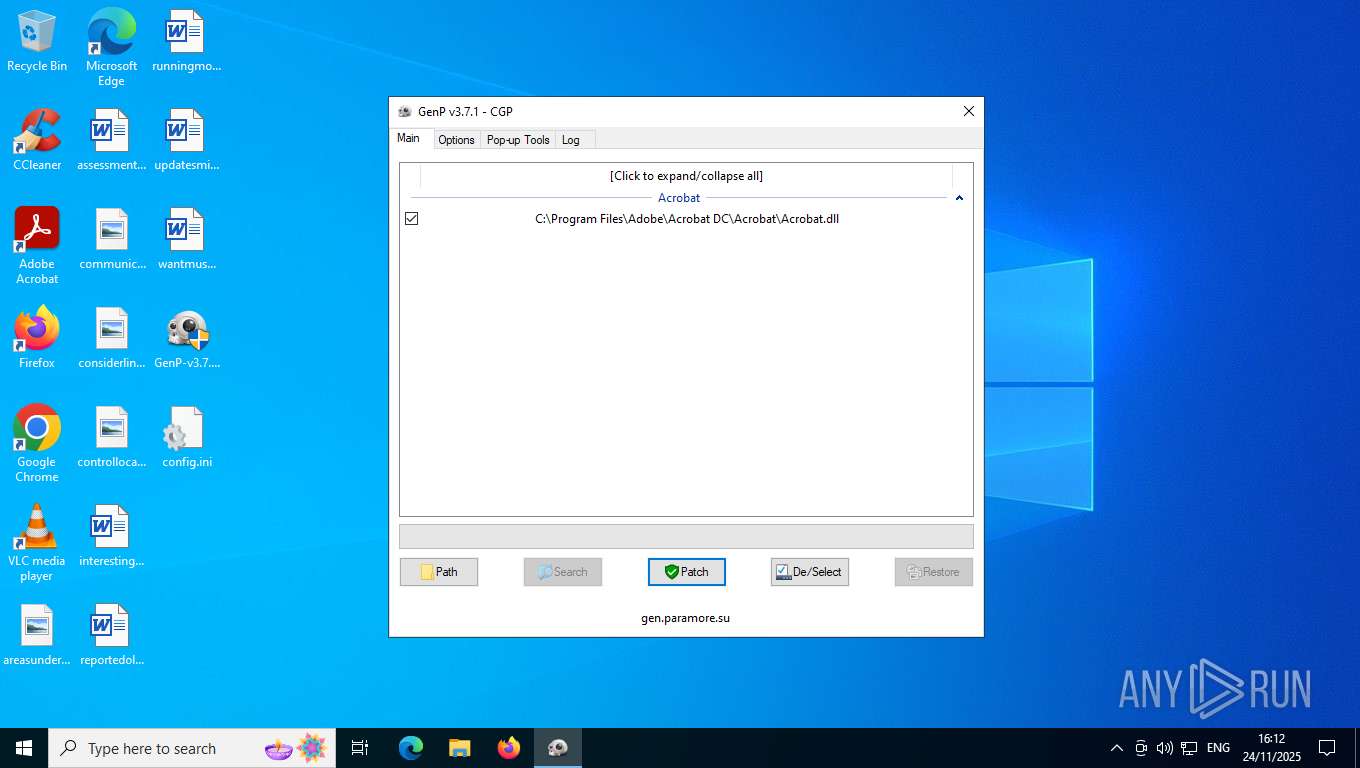
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
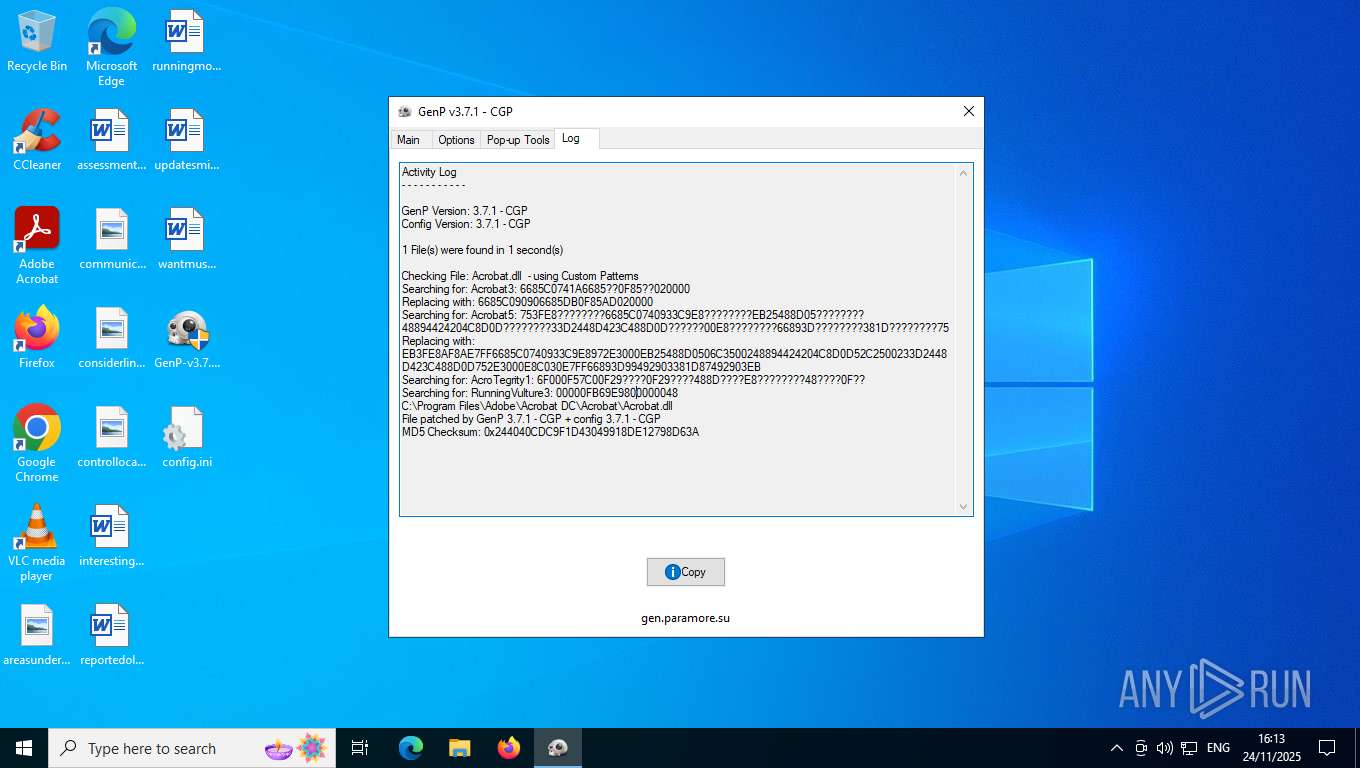
| 7224 | GenP-v3.7.1.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll.bak | — | |
MD5:— | SHA256:— | |||
| 7224 | GenP-v3.7.1.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.dll | — | |
MD5:— | SHA256:— | |||
| 7224 | GenP-v3.7.1.exe | C:\Users\admin\Desktop\config.ini | text | |
MD5:A1C2977DBFD3343D1C2575E9967B532C | SHA256:49EB049A9C13F4C0A57F66CB1BE275D13A5AA3B5814C25E71DDF211B3A54BA79 | |||
| 7224 | GenP-v3.7.1.exe | C:\Users\admin\AppData\Local\Temp\aut37DD.tmp | binary | |
MD5:4CA755DBF9F7EF7B7C651396508C6CF8 | SHA256:14385A5E5B7F7E1047EE8A459A2A4EA06BD15C2692C6732196CAD48C66A8C188 | |||
| 6264 | updater.exe | C:\Program Files (x86)\Google\GoogleUpdater\updater.log | text | |
MD5:C80CCBBD12BA21F5B0AFAC7913DF6697 | SHA256:8362B1AB349C52C5FDCBFFEC1E467F8DB19961D87A90A696891948C102224AF2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
85
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5596 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
1664 | svchost.exe | GET | 200 | 2.16.164.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
— | — | POST | 200 | 20.190.159.129:443 | https://login.live.com/RST2.srf | US | xml | 10.3 Kb | unknown |
— | — | POST | 200 | 40.126.31.2:443 | https://login.live.com/RST2.srf | US | xml | 10.3 Kb | unknown |
— | — | POST | 200 | 20.190.159.2:443 | https://login.live.com/RST2.srf | US | xml | 10.3 Kb | unknown |
— | — | POST | 200 | 40.126.31.71:443 | https://login.live.com/RST2.srf | US | xml | 11.0 Kb | unknown |
— | — | GET | 200 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | compressed | 29.1 Kb | unknown |
2328 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | NL | binary | 813 b | whitelisted |
2328 | SIHClient.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | DE | binary | 824 b | whitelisted |
2328 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | NL | binary | 814 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.204.152:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 2.16.164.42:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1664 | svchost.exe | 2.16.164.42:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.164.42:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4916 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |