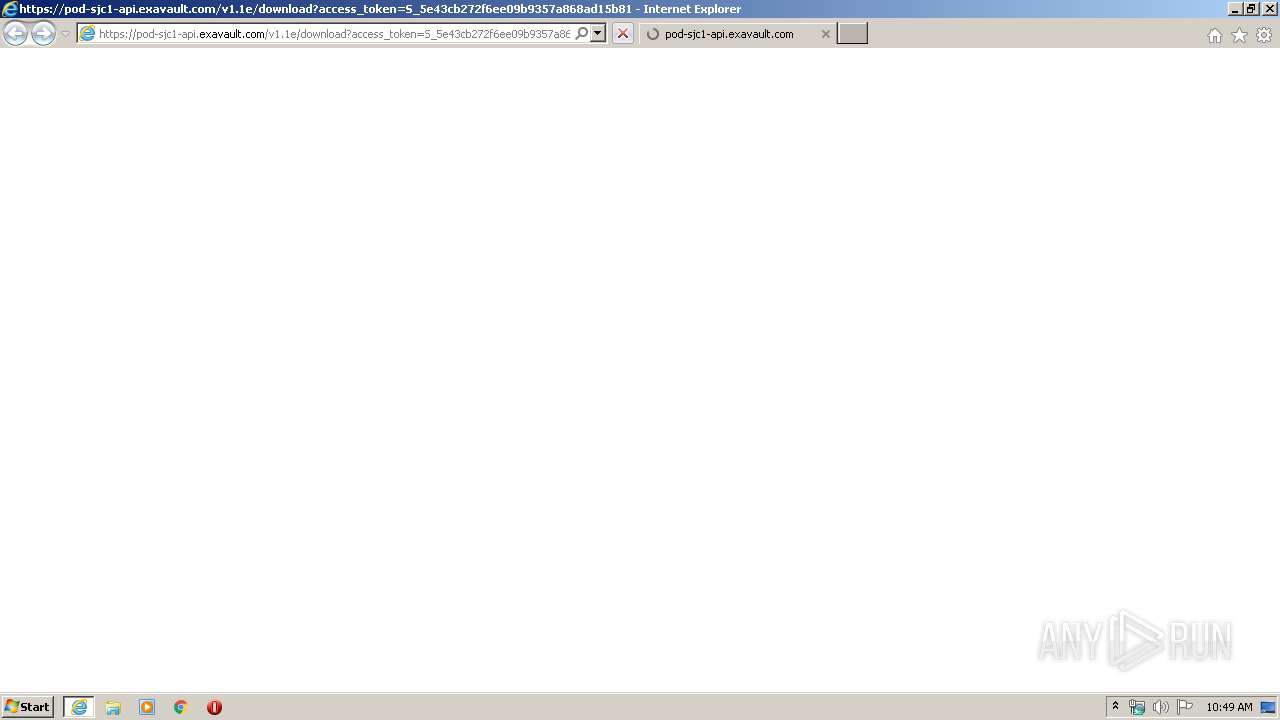
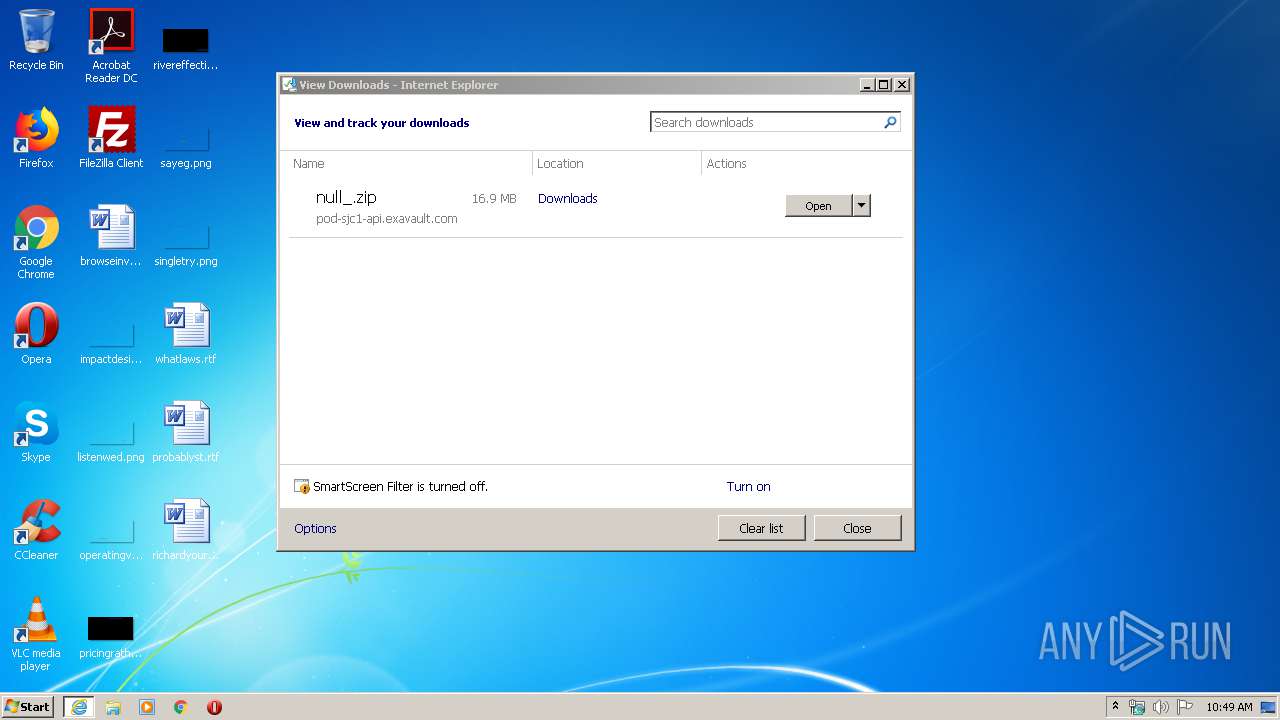
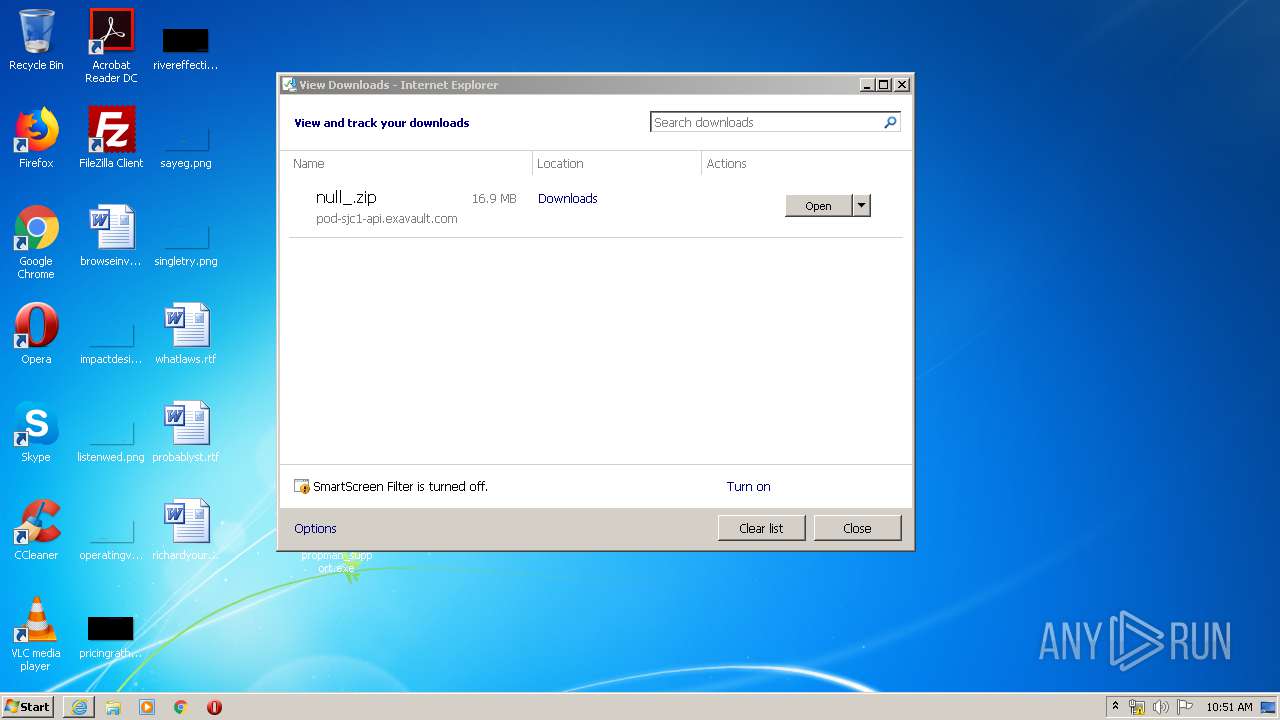
| URL: | https://pod-sjc1-api.exavault.com/v1.1e/download?access_token=S_5e43cb272f6ee09b9357a868ad15b81391a5b1cbdbaa6&filePaths[]=%2Fpropman_support.exe&downloadName=null<https://pod-sjc1-api.exavault.com/v1.1e/download?access_token=S_5e43cb272f6ee09b9357a868ad15b81391a5b1cbdbaa6&filePaths%5b%5d=%2Fpropman_support.exe&downloadName=null> |
| Full analysis: | https://app.any.run/tasks/c78ff0f9-b7aa-4d82-9766-c3c541135b15 |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2020, 10:49:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 662CE26D4FE962737609F956F48CA402 |
| SHA1: | ED09ED05C6BFFD8B165AD696C132ABFD6B501A6B |
| SHA256: | 796E582138F8E70743BA40E29C476643B572442C34E0D4EFDFF68A9FA0A82FE8 |
| SSDEEP: | 6:2OhGRDDoLTURWuAVWHRcUZ5tTfxXJiyCBLADqhAHIOhGRDDoLTURWuAVWHRcUZ5P:2oUQLTIzAVWHRlZP7fIKqzoUQLTIzAVc |
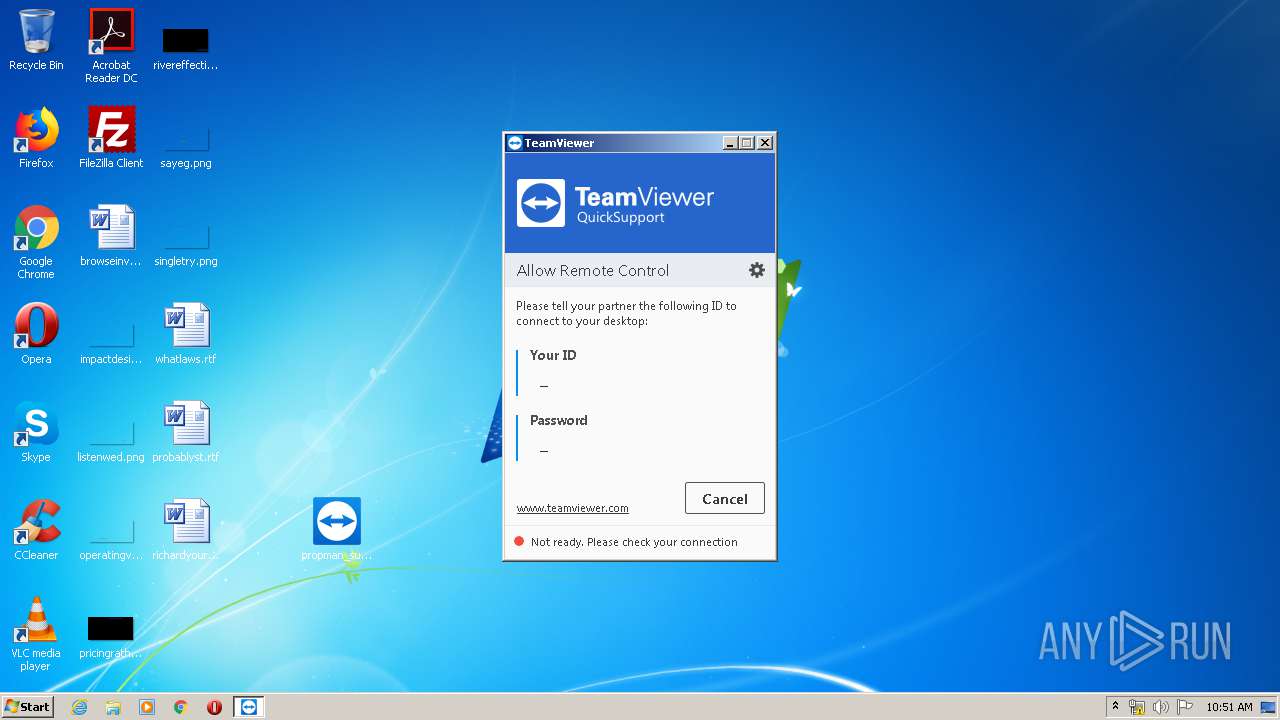
MALICIOUS
Loads dropped or rewritten executable
- propman_support.exe (PID: 1912)
- TeamViewer.exe (PID: 3608)
- TeamViewer.exe (PID: 1024)
- tv_w32.exe (PID: 2544)
Application was dropped or rewritten from another process
- propman_support.exe (PID: 1912)
- tv_w32.exe (PID: 2544)
Changes settings of System certificates
- mshta.exe (PID: 2508)
- TeamViewer.exe (PID: 1024)
SUSPICIOUS
Creates files in the user directory
- TeamViewer.exe (PID: 3608)
- mshta.exe (PID: 2508)
Application launched itself
- TeamViewer.exe (PID: 3608)
Executable content was dropped or overwritten
- propman_support.exe (PID: 1912)
Connects to unusual port
- TeamViewer.exe (PID: 1024)
Starts MSHTA.EXE for opening HTA or HTMLS files
- TeamViewer.exe (PID: 1024)
Reads Internet Cache Settings
- mshta.exe (PID: 2508)
Adds / modifies Windows certificates
- mshta.exe (PID: 2508)
- TeamViewer.exe (PID: 1024)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3352)
- iexplore.exe (PID: 2776)
Reads settings of System Certificates
- TeamViewer.exe (PID: 1024)
- iexplore.exe (PID: 2776)
- iexplore.exe (PID: 3352)
- mshta.exe (PID: 2508)
Manual execution by user
- propman_support.exe (PID: 1912)
Creates files in the user directory
- iexplore.exe (PID: 3352)
Reads internet explorer settings
- mshta.exe (PID: 2508)
Changes internet zones settings
- iexplore.exe (PID: 3352)
Application launched itself
- iexplore.exe (PID: 3352)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3352)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3352)
Changes settings of System certificates
- iexplore.exe (PID: 3352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
8
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
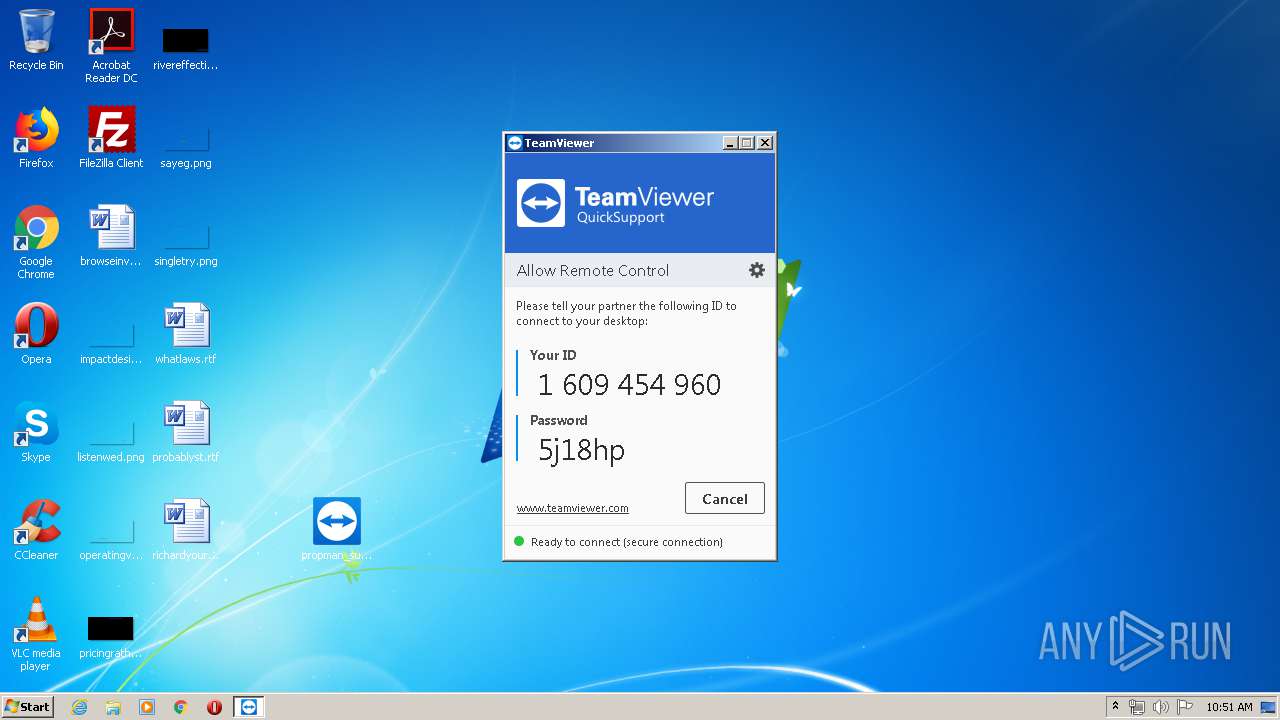
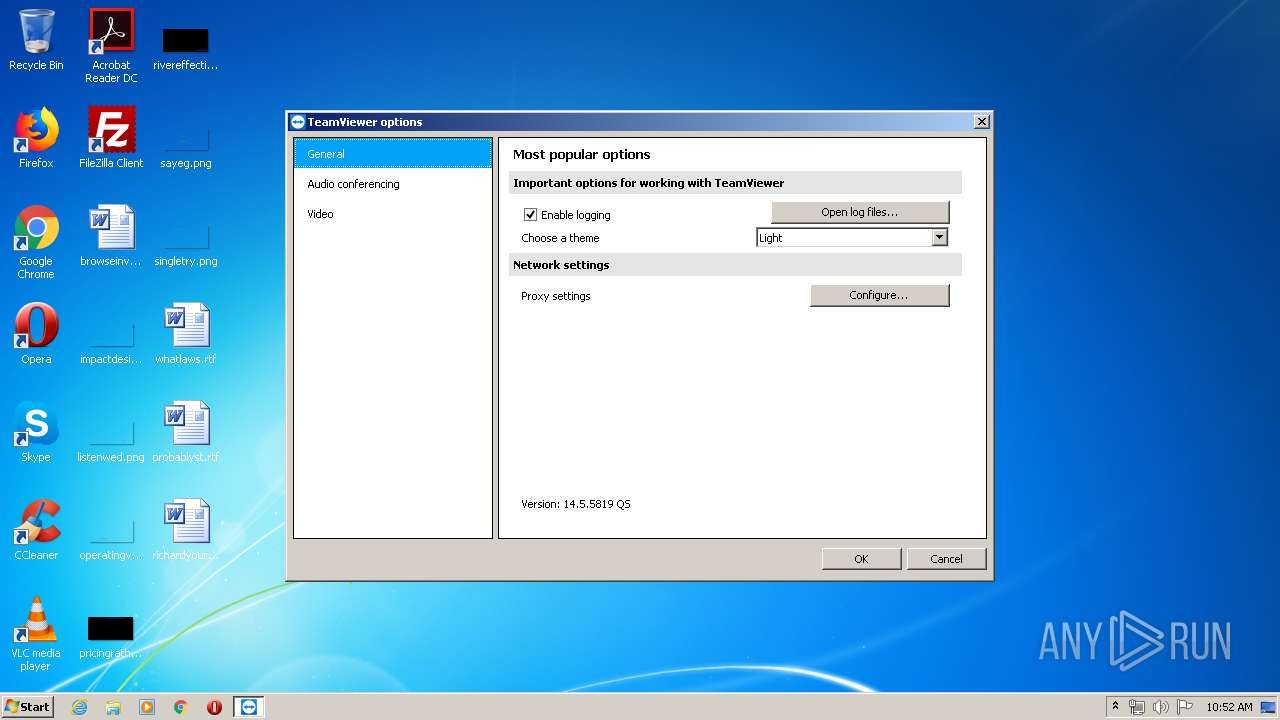
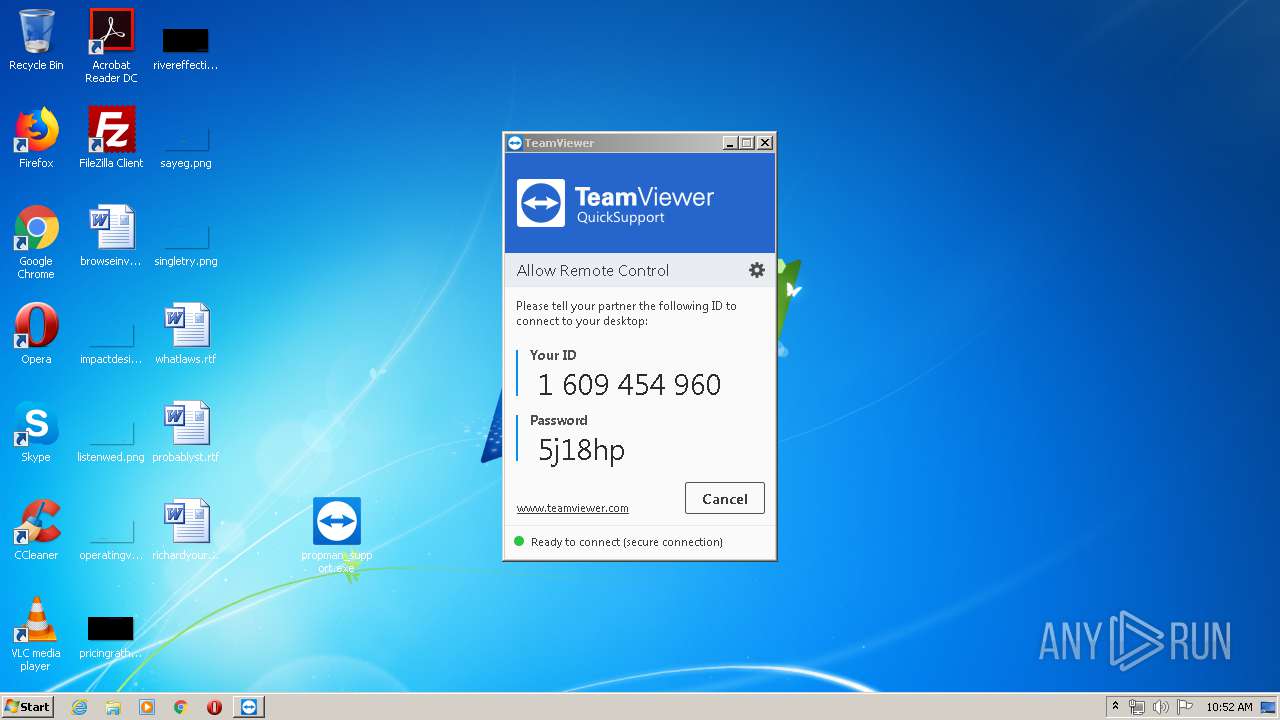
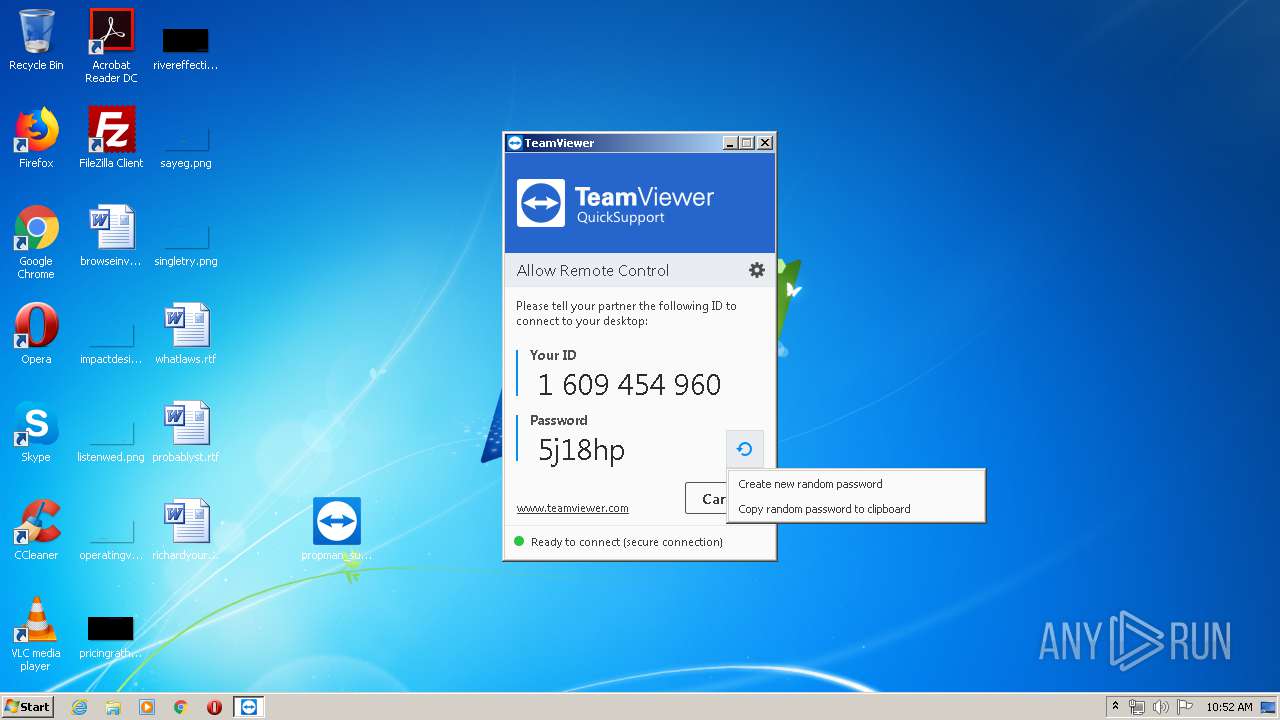
| 1024 | "C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer.exe" --dre | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer.exe | TeamViewer.exe | ||||||||||||
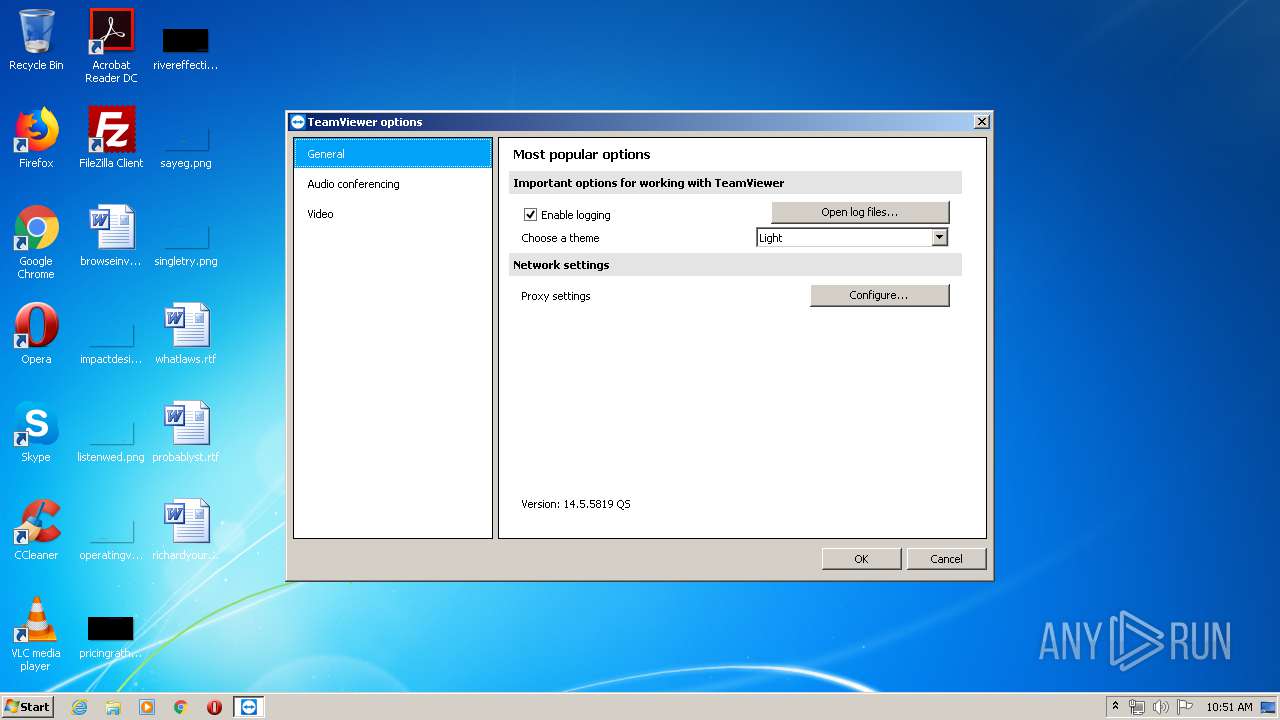
User: admin Company: TeamViewer GmbH Integrity Level: HIGH Description: TeamViewer 14 Exit code: 0 Version: 14.5.5819.0 Modules
| |||||||||||||||
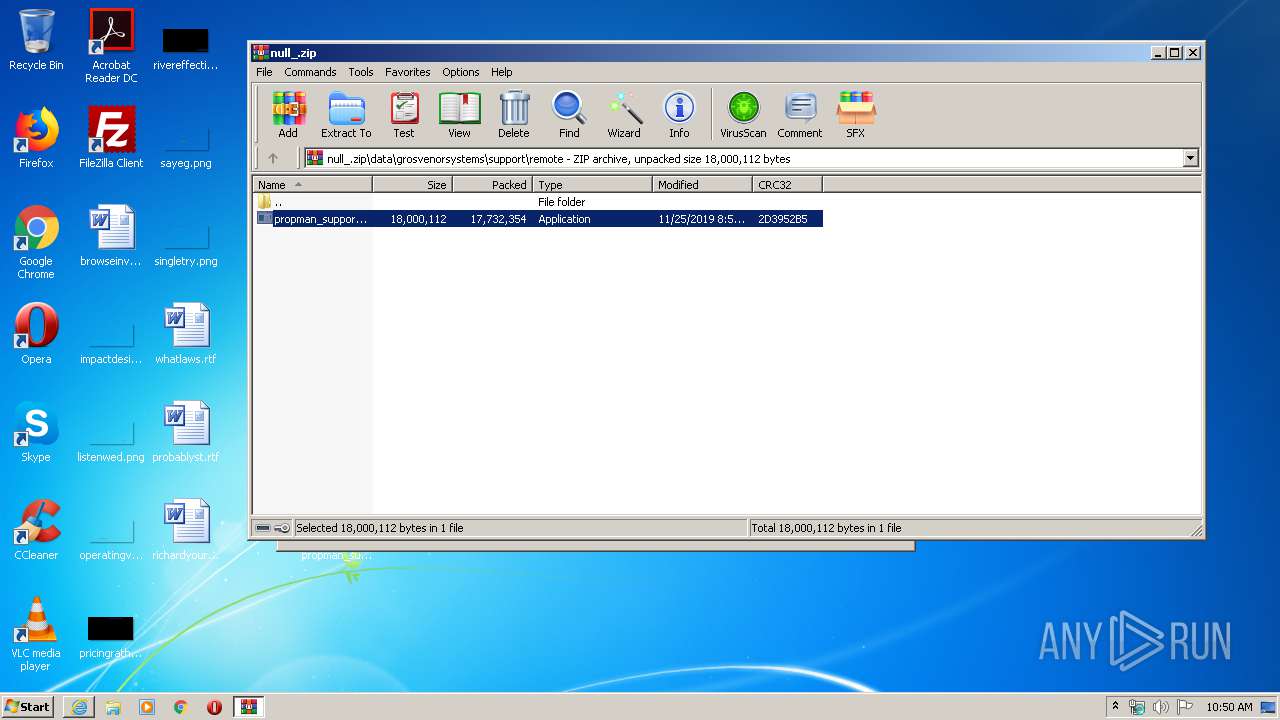
| 1912 | "C:\Users\admin\Desktop\propman_support.exe" | C:\Users\admin\Desktop\propman_support.exe | explorer.exe | ||||||||||||
User: admin Company: TeamViewer Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2508 | "C:\Windows\system32\mshta.exe" C:\Users\admin\AppData\Local\Temp\TeamViewer\7.hta | C:\Windows\system32\mshta.exe | TeamViewer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2544 | "C:\Users\admin\AppData\Local\Temp\TeamViewer\tv_w32.exe" --action hooks --log C:\Users\admin\AppData\Roaming\TeamViewer\TeamViewer14_Logfile.log | C:\Users\admin\AppData\Local\Temp\TeamViewer\tv_w32.exe | TeamViewer.exe | ||||||||||||
User: SYSTEM Company: TeamViewer GmbH Integrity Level: SYSTEM Description: TeamViewer 14 Exit code: 0 Version: 14.5.5819.0 Modules
| |||||||||||||||
| 2776 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3352 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
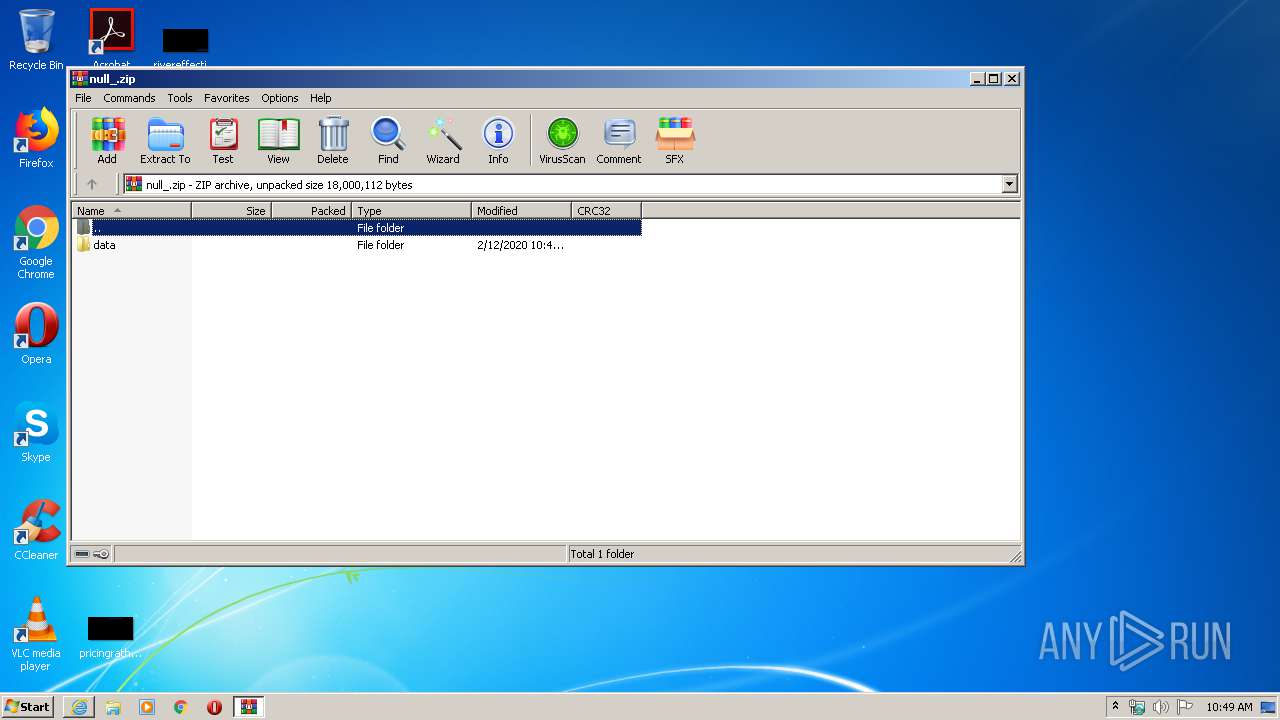
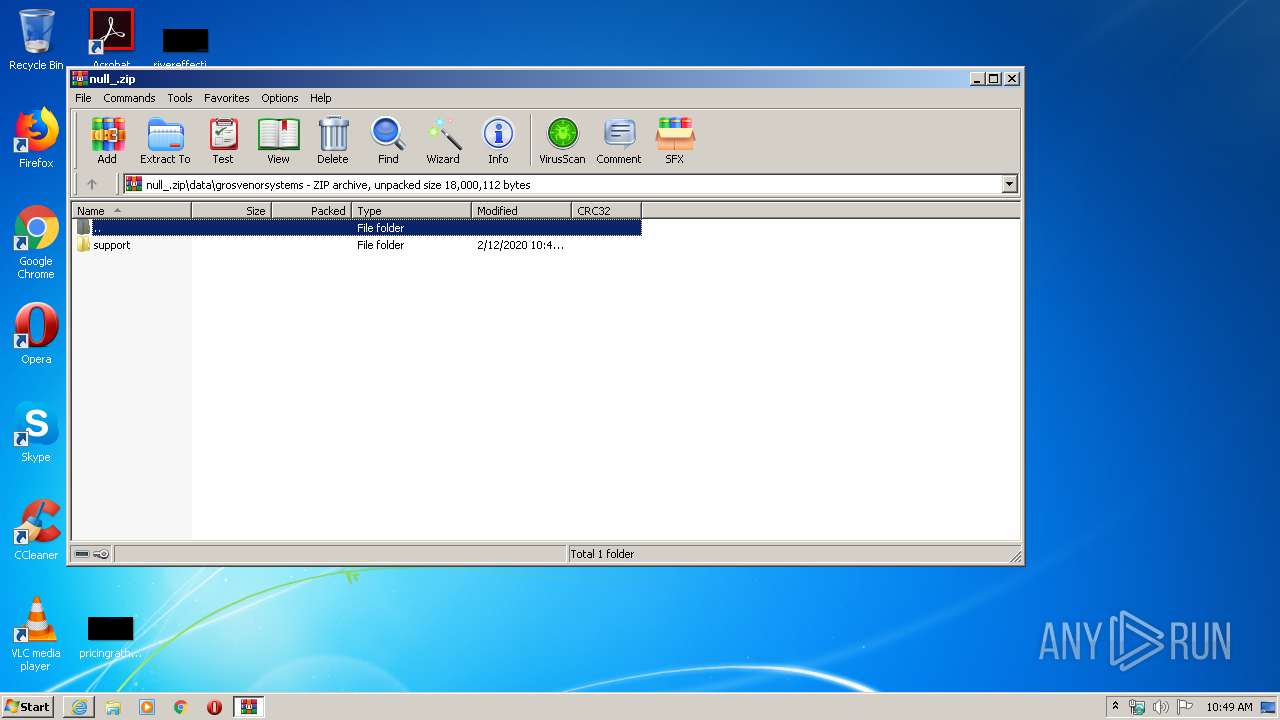
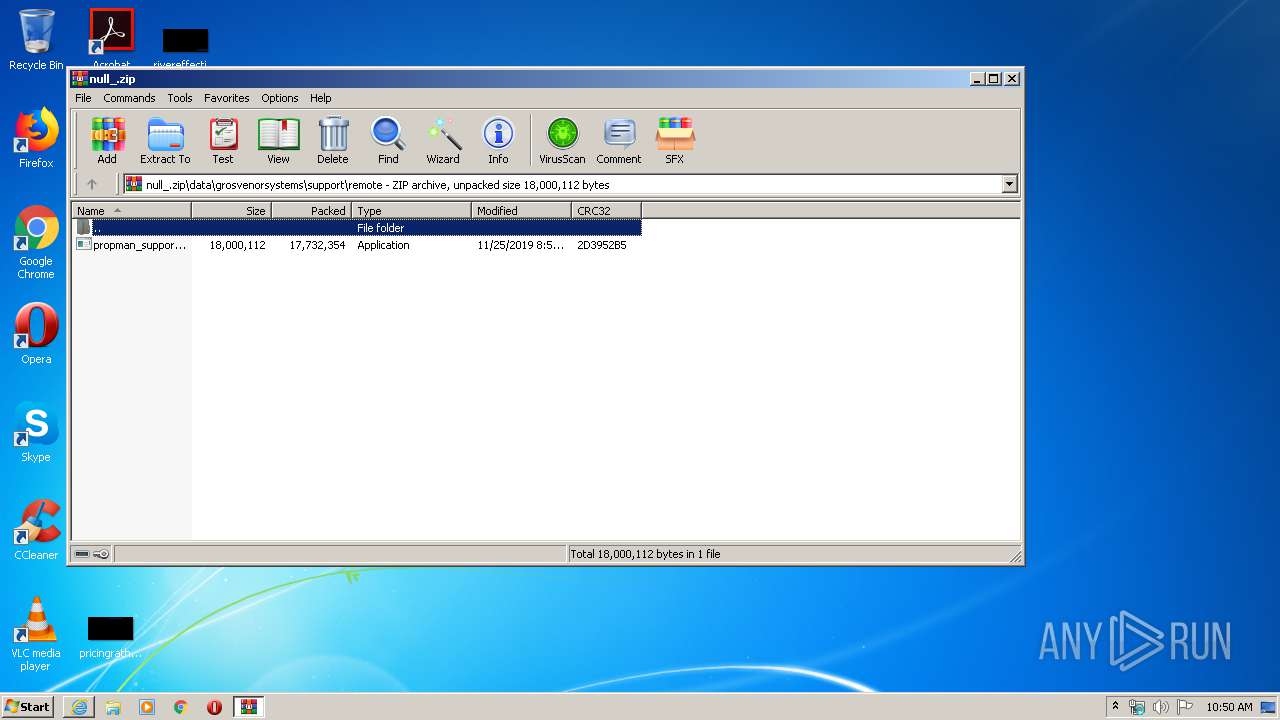
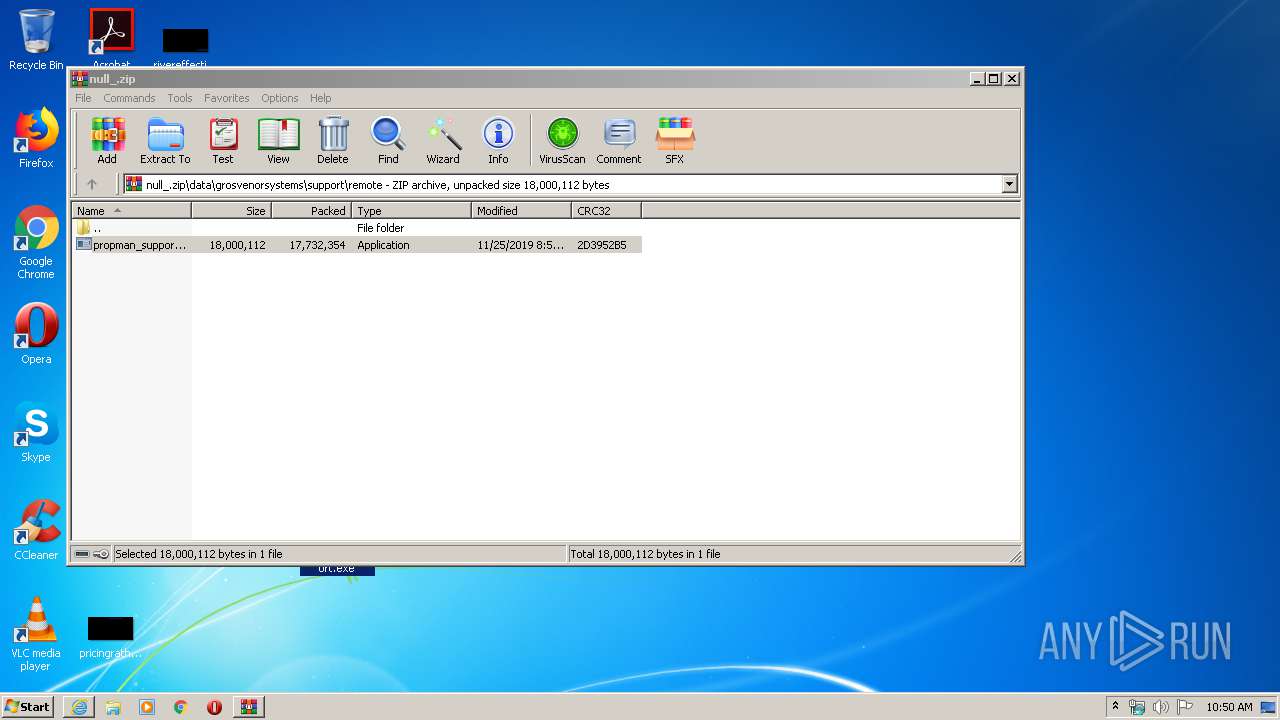
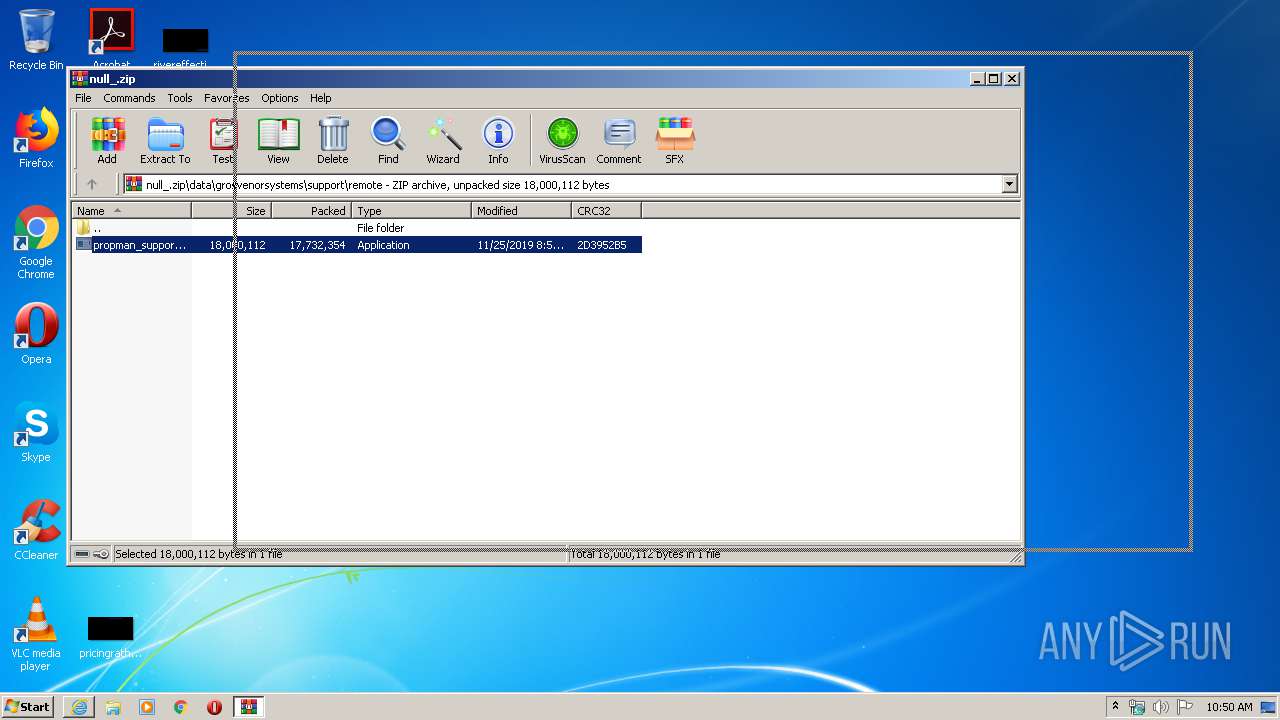
| 3312 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\null_.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3352 | "C:\Program Files\Internet Explorer\iexplore.exe" https://pod-sjc1-api.exavault.com/v1.1e/download?access_token=S_5e43cb272f6ee09b9357a868ad15b81391a5b1cbdbaa6&filePaths[]=%2Fpropman_support.exe&downloadName=null<https://pod-sjc1-api.exavault.com/v1.1e/download?access_token=S_5e43cb272f6ee09b9357a868ad15b81391a5b1cbdbaa6&filePaths%5b%5d=%2Fpropman_support.exe&downloadName=null> | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3608 | "C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer.exe" | C:\Users\admin\AppData\Local\Temp\TeamViewer\TeamViewer.exe | — | propman_support.exe | |||||||||||
User: admin Company: TeamViewer GmbH Integrity Level: MEDIUM Description: TeamViewer 14 Exit code: 0 Version: 14.5.5819.0 Modules
| |||||||||||||||
Total events
10 926
Read events
2 663
Write events
5 926
Delete events
2 337
Modification events
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 680338770 | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30794130 | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3352) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
46
Suspicious files
33
Text files
27
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3352 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2776 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab96AA.tmp | — | |
MD5:— | SHA256:— | |||
| 2776 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar96AB.tmp | — | |
MD5:— | SHA256:— | |||
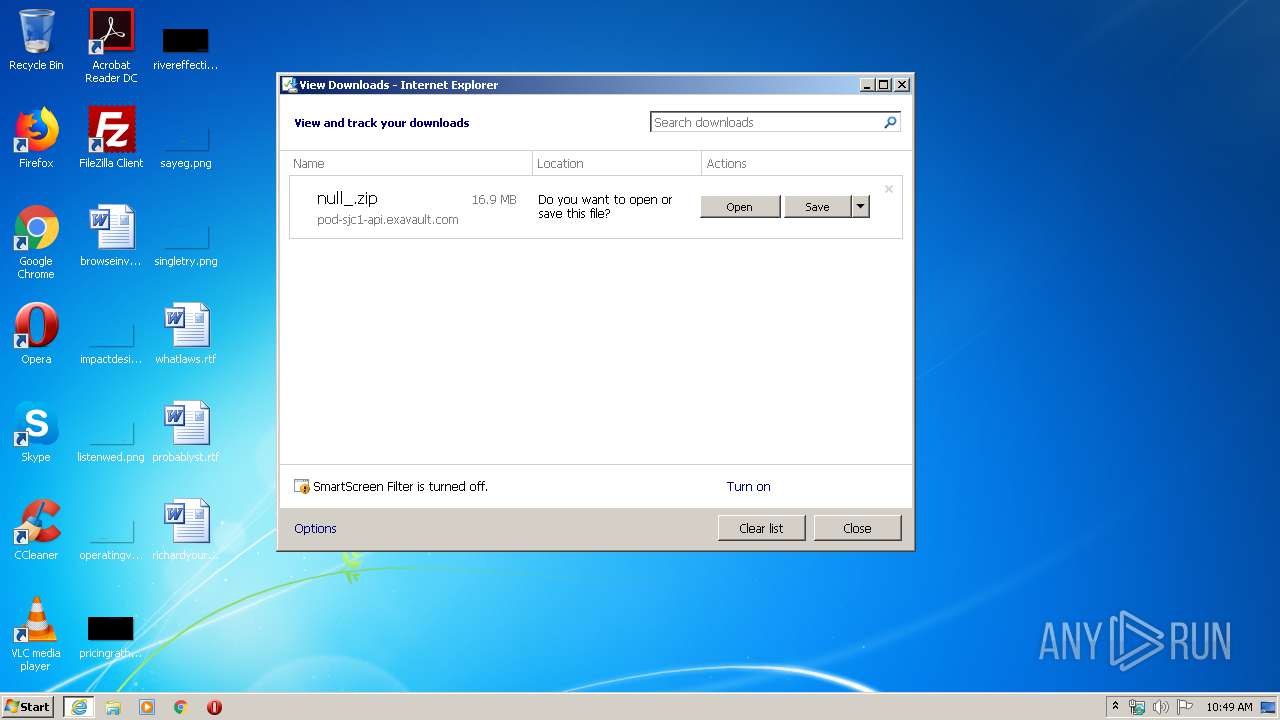
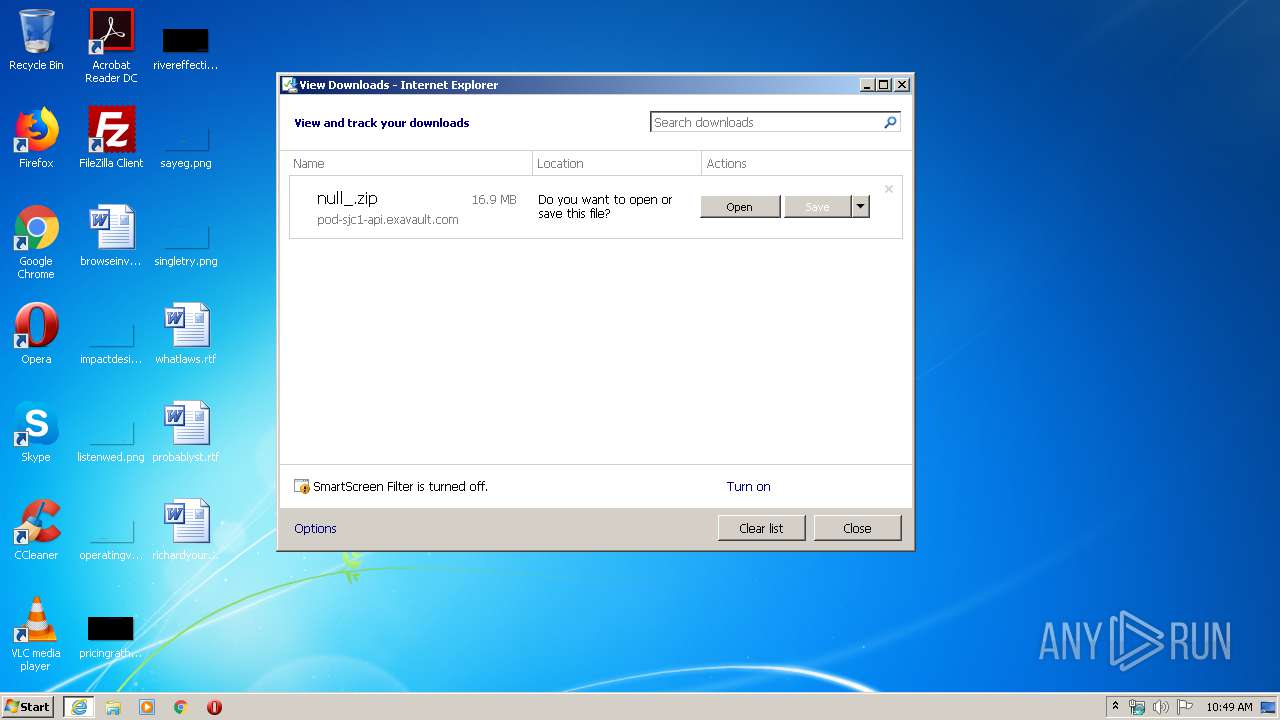
| 2776 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\null_[1].zip | — | |
MD5:— | SHA256:— | |||
| 2776 | iexplore.exe | C:\Users\admin\Downloads\null_.zip.qcw5v5x.partial | — | |
MD5:— | SHA256:— | |||
| 3352 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD45E259170C193E8.TMP | — | |
MD5:— | SHA256:— | |||
| 3352 | iexplore.exe | C:\Users\admin\Downloads\null_.zip.qcw5v5x.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3312.10989\data\grosvenorsystems\support\remote\propman_support.exe | — | |
MD5:— | SHA256:— | |||
| 3352 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab55D.tmp | — | |
MD5:— | SHA256:— | |||
| 3352 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar55E.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
29
DNS requests
18
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3352 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3352 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2508 | mshta.exe | GET | 301 | 104.16.62.16:80 | http://www.teamviewer.com/company/shutdown.aspx?version=14.5.5819%20QS | US | — | — | shared |
3352 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2508 | mshta.exe | GET | 301 | 104.16.62.16:80 | http://www.teamviewer.com/favicon.ico | US | — | — | shared |
2776 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://crl.usertrust.com/AddTrustExternalCARoot.crl | US | der | 673 b | whitelisted |
2776 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEDaCXn%2B1pIGTfvbRc2u5PKY%3D | US | der | 727 b | whitelisted |
2508 | mshta.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR64T7ooMQqLLQoy%2BemBUYZQOKh6QQUkK9qOpRaC9iQ6hJWc99DtDoo2ucCEDhlnzqWGFiLX8YW2xB7zIE%3D | US | der | 471 b | whitelisted |
2776 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQLqIKj6Gi5thHaqKC1ECU9aXsCRQQUmvMr2s%2BtT7YvuypISCoStxtCwSQCEQD4gBugh5QXD6kw7td%2BUvel | US | der | 472 b | whitelisted |
2776 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3352 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2776 | iexplore.exe | 67.208.93.236:443 | pod-sjc1-api.exavault.com | InfoRelay Online Systems, Inc. | US | unknown |
2776 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
3352 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3352 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3352 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1024 | TeamViewer.exe | 178.255.154.140:5938 | router3.teamviewer.com | ANEXIA Internetdienstleistungs GmbH | CZ | suspicious |
1024 | TeamViewer.exe | 52.232.106.174:443 | client.teamviewer.com | Microsoft Corporation | NL | whitelisted |
2508 | mshta.exe | 104.16.62.16:80 | www.teamviewer.com | Cloudflare Inc | US | shared |
2508 | mshta.exe | 104.16.62.16:443 | www.teamviewer.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pod-sjc1-api.exavault.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
crl.usertrust.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1024 | TeamViewer.exe | Potential Corporate Privacy Violation | REMOTE [PTsecurity] TeamViewer |
1024 | TeamViewer.exe | Potential Corporate Privacy Violation | REMOTE [PTsecurity] TeamViewer |
2 ETPRO signatures available at the full report