| File name: | TLauncher-MCL.exe |
| Full analysis: | https://app.any.run/tasks/ad300f05-cb97-4267-b3c7-7f371be8622c |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2020, 07:16:47 |
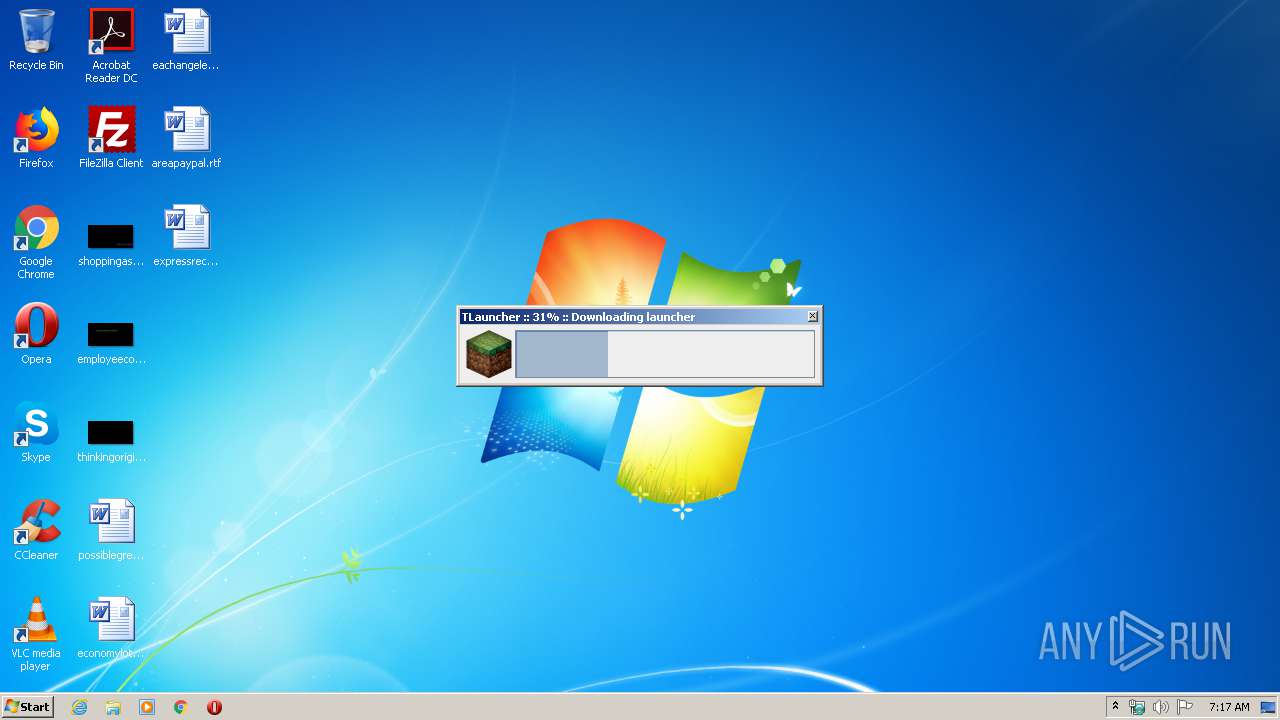
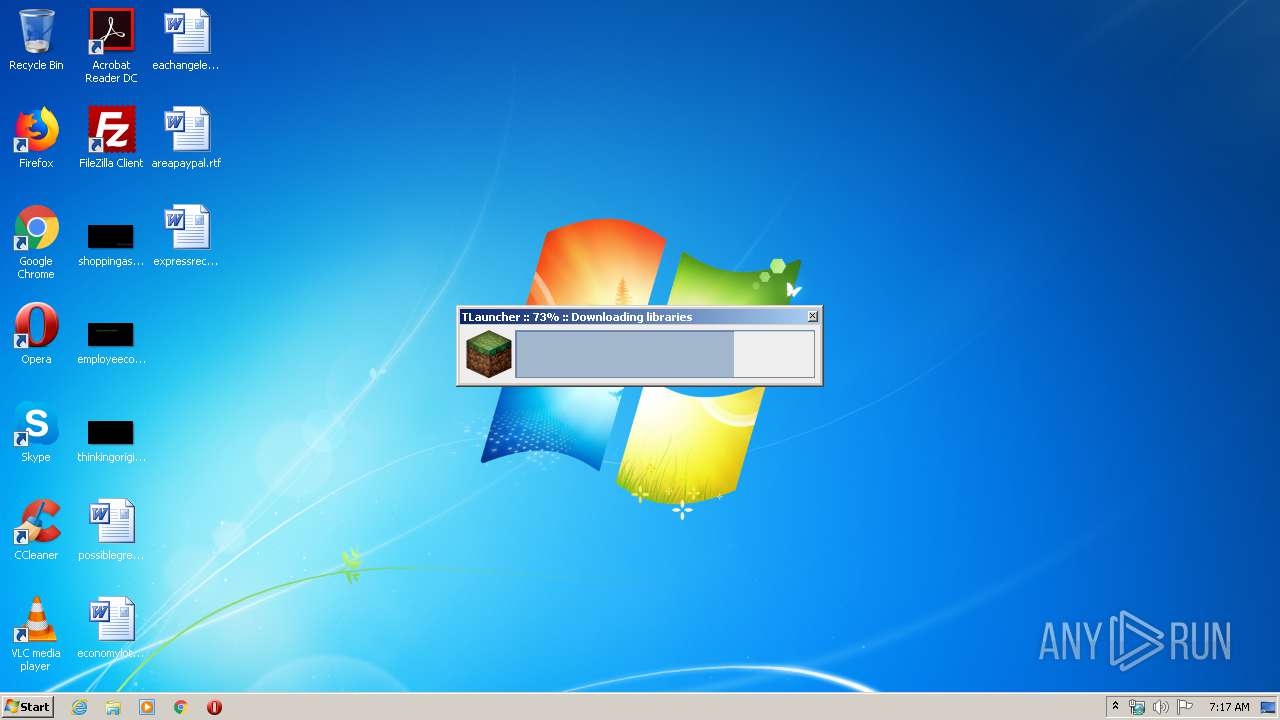
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | A8A3A5A77FA7A0FDA9D0E9833B812CB3 |
| SHA1: | 64C1D78C188DA796E5674A6073292D9156FB2BC5 |
| SHA256: | 796E104FC91175E0592C11B07098856E86CEAA5D33EFAB1BF46420B8B5047250 |
| SSDEEP: | 12288:qyIVjAFZwJxEhK8G9+ubm8Q+Fl4nMtYrTWNtjQoV7szQuksoTEMz62Fi:eVjAexEh0cubm8jY8tjQoSzDoQH2Fi |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes JAVA applets
- TLauncher-MCL.exe (PID: 3988)
- javaw.exe (PID: 2808)
Creates files in the user directory
- java.exe (PID: 3308)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:09:07 01:16:48+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 25088 |
| InitializedDataSize: | 377856 |
| UninitializedDataSize: | 36864 |
| EntryPoint: | 0x1290 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.5.13.0 |
| ProductVersionNumber: | 1.5.13.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | - |
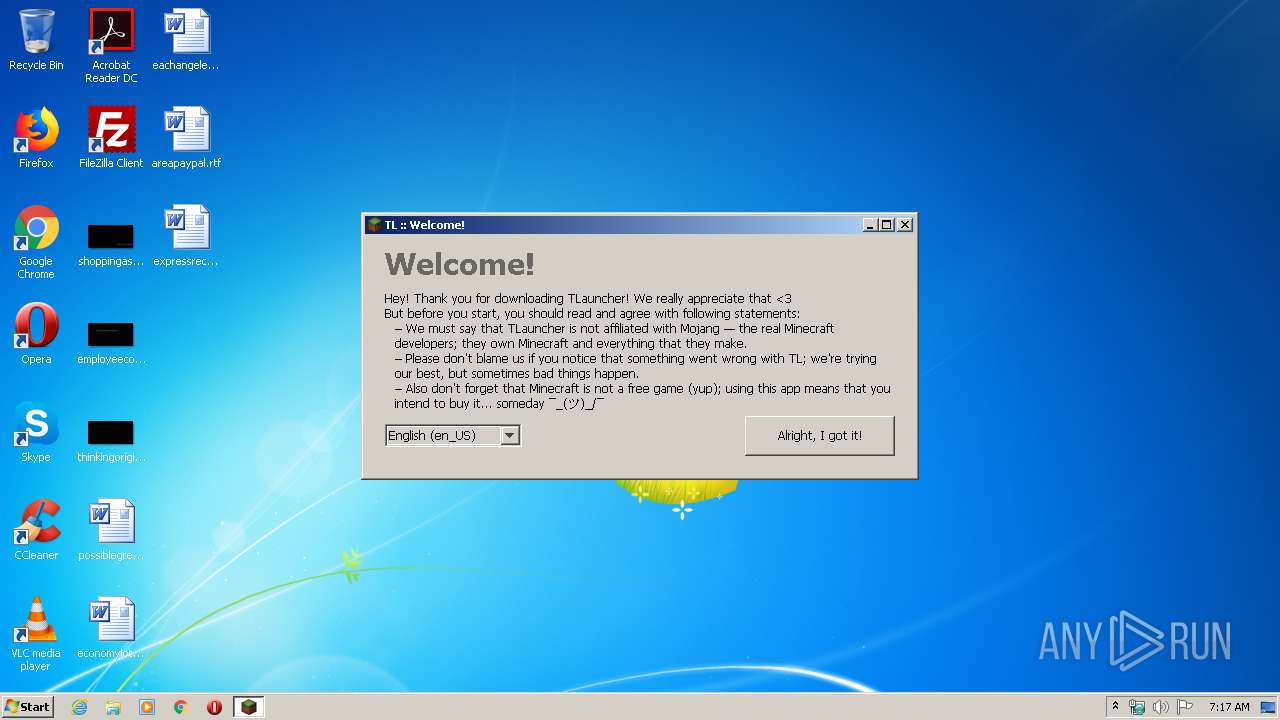
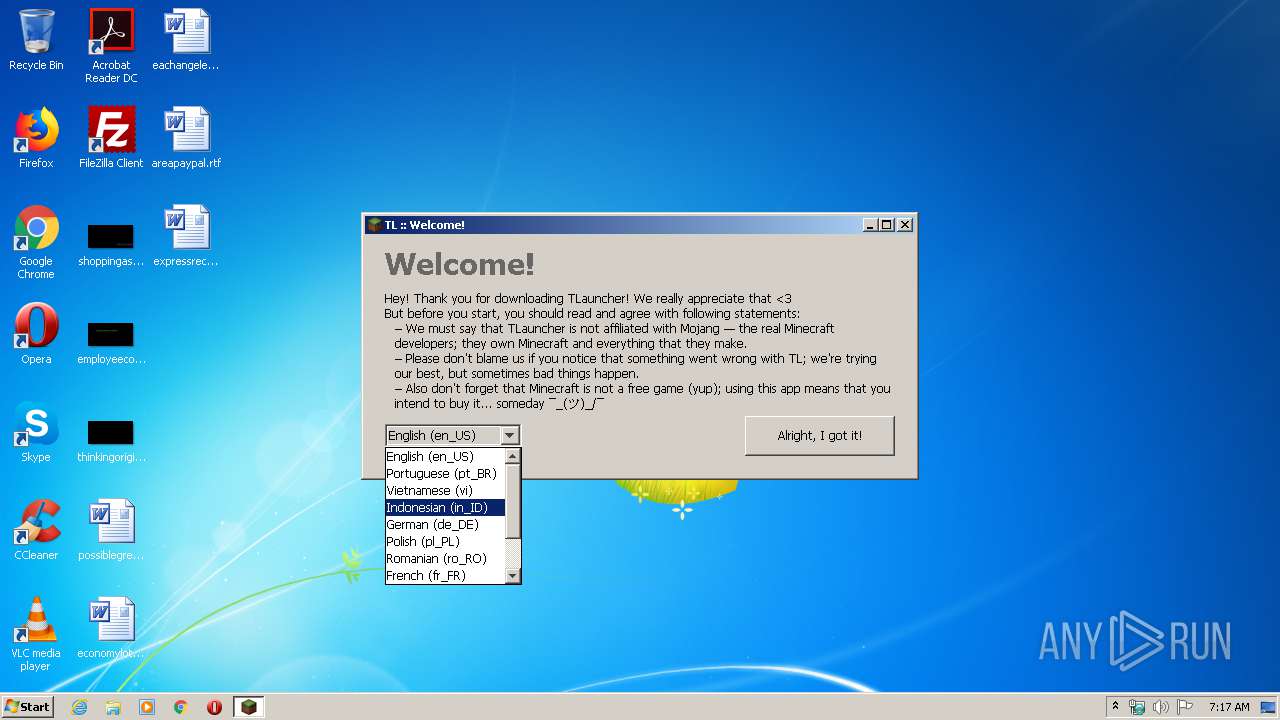
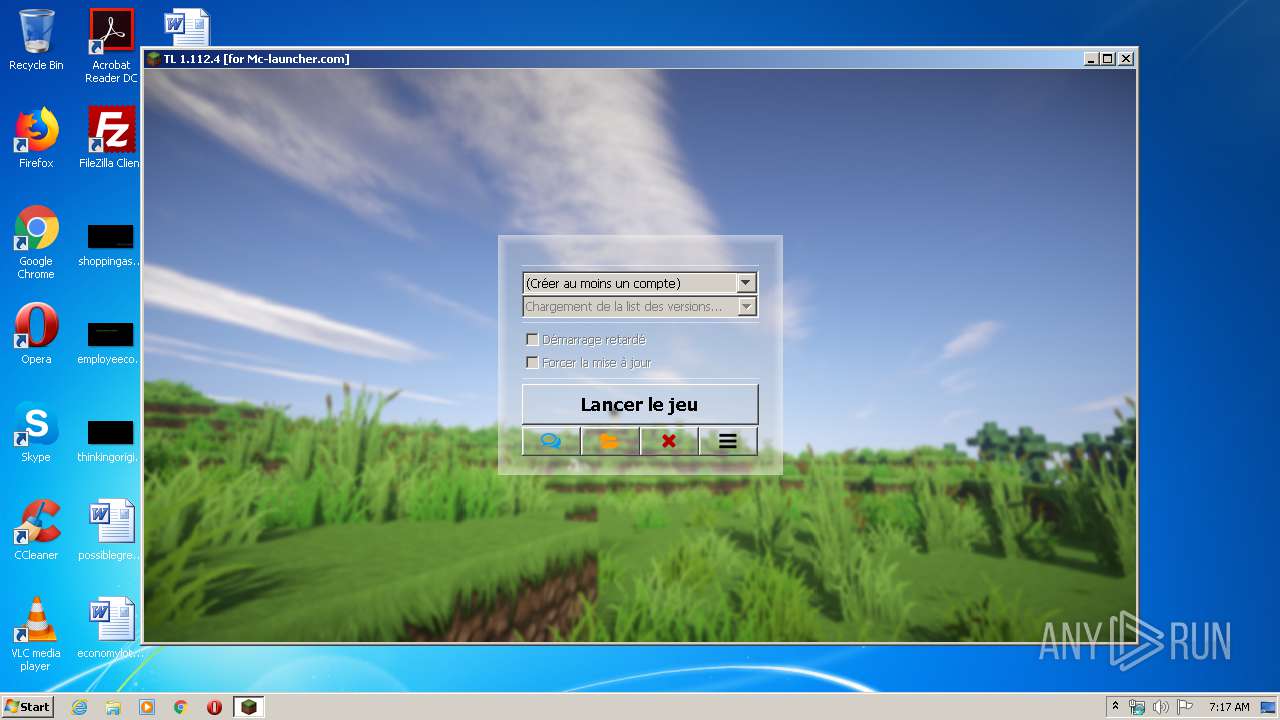
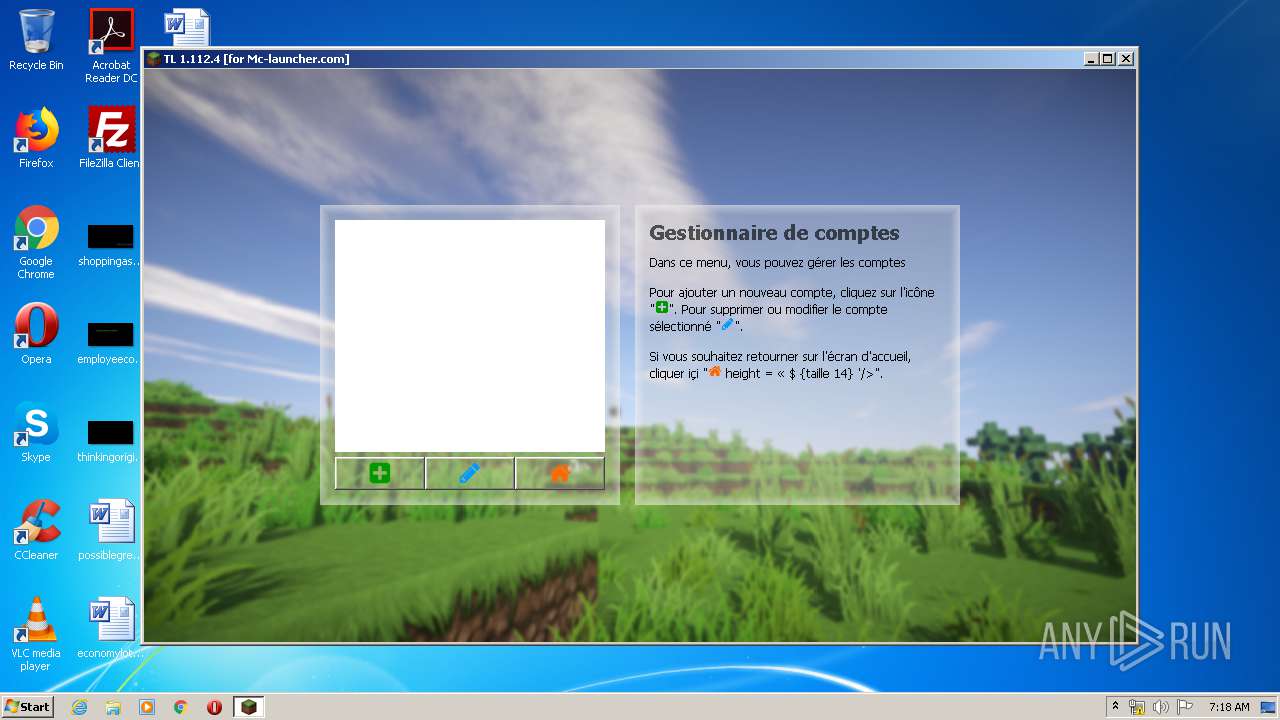
| FileDescription: | Free Minecraft launcher |
| FileVersion: | 1.5.13+master |
| InternalName: | tlauncher-mcl |
| LegalCopyright: | 2016 |
| LegalTrademarks: | - |
| OriginalFileName: | TLauncher-MCL.exe |
| ProductName: | TLauncher for MC-Launcher.com |
| ProductVersion: | 1.5.13+master |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Sep-2017 23:16:48 |
| Detected languages: |
|
| CompanyName: | - |
| FileDescription: | Free Minecraft launcher |
| FileVersion: | 1.5.13+master |
| InternalName: | tlauncher-mcl |
| LegalCopyright: | 2016 |
| LegalTrademarks: | - |
| OriginalFilename: | TLauncher-MCL.exe |
| ProductName: | TLauncher for MC-Launcher.com |
| ProductVersion: | 1.5.13+master |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 06-Sep-2017 23:16:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006080 | 0x00006200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.98217 |
.data | 0x00008000 | 0x00000040 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.163808 |
.rdata | 0x00009000 | 0x00000510 | 0x00000600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.01355 |
.bss | 0x0000A000 | 0x00008E30 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00013000 | 0x00000AA8 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.65264 |
.rsrc | 0x00014000 | 0x0005AEA0 | 0x0005B000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.28605 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.37232 | 788 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
3 | 5.46449 | 9640 | UNKNOWN | Process Default Language | RT_ICON |
4 | 5.39665 | 16936 | UNKNOWN | Process Default Language | RT_ICON |
5 | 5.29937 | 67624 | UNKNOWN | Process Default Language | RT_ICON |
6 | 5.24859 | 270376 | UNKNOWN | Process Default Language | RT_ICON |
8 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
10 | 3.2597 | 31 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2808 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\TLauncher-MCL.exe" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | TLauncher-MCL.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3308 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -Xmx128m -Dfile.encoding=UTF-8 -classpath C:\Users\admin\AppData\Local\Temp\TLauncher-MCL.exe ru.turikhay.tlauncher.bootstrap.Bootstrap | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3988 | "C:\Users\admin\AppData\Local\Temp\TLauncher-MCL.exe" | C:\Users\admin\AppData\Local\Temp\TLauncher-MCL.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Free Minecraft launcher Exit code: 0 Version: 1.5.13+master Modules
| |||||||||||||||
Total events
24
Read events
23
Write events
1
Delete events
0
Modification events
| (PID) Process: | (3308) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: java.exe | |||
Executable files
16
Suspicious files
20
Text files
21
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3308 | java.exe | C:\Users\admin\AppData\Local\Temp\tlauncher4119126061870659870.tmp | java | |
MD5:— | SHA256:— | |||
| 3308 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2808 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3308 | java.exe | C:\Users\admin\AppData\Roaming\.tlauncher\bin\mcl.jar | java | |
MD5:— | SHA256:— | |||
| 3308 | java.exe | C:\Users\admin\AppData\Roaming\.tlauncher\bin\lib\org\tukaani\xz\1.5\xz-1.5.jar | java | |
MD5:51050E595B308C4AEC8AC314F66E18BC | SHA256:86F30FA8775FA3A62CDB39D1ED78A6019164C1058864048D42CBEE244E26E840 | |||
| 3308 | java.exe | C:\Users\admin\AppData\Local\Temp\tlauncher8045670636575118178.tmp | java | |
MD5:51050E595B308C4AEC8AC314F66E18BC | SHA256:86F30FA8775FA3A62CDB39D1ED78A6019164C1058864048D42CBEE244E26E840 | |||
| 3308 | java.exe | C:\Users\admin\AppData\Local\Temp\tlauncher5174705264473138240.tmp | java | |
MD5:39C6476E4DE3D4F90AD4CA0DDCA48EC2 | SHA256:26C5856E954B5F864DB76F13B86919B59C6EECF9FD930B96BAA8884626BAF2F5 | |||
| 3308 | java.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 3308 | java.exe | C:\Users\admin\AppData\Roaming\.tlauncher\bin\lib\com\github\zafarkhaja\java-semver\0.9.0\java-semver-0.9.0.jar | compressed | |
MD5:9417096FF6A9DB74DB273ABBDA0F334E | SHA256:2218C73B40F9AF98B570D084420C1B4A81332297BD7FC27DDD552E903BE8E93C | |||
| 3308 | java.exe | C:\Users\admin\AppData\Local\Temp\tlauncher601475327151074885.tmp | compressed | |
MD5:5134A2350F58890FFB9DB0B40047195D | SHA256:2D43EB5EA9E133D2EE2405CC14F5EE08951B8361302FDD93494A3A997B508D32 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
34
DNS requests
11
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3308 | java.exe | GET | 200 | 188.40.26.206:80 | http://u.tlauncher.ru/stats/?client=e8e2e5ed-3b31-44e1-a551-51d2c6b9736a&version=1.112.4%2Bmaster&brand=for%20Mc-launcher.com&os=windows&locale=fr_FR&action=beacon | DE | — | — | suspicious |
3308 | java.exe | GET | 200 | 213.186.33.186:80 | http://tlauncherrepo.com/mcl/launcher/da32d22d9b36fed28f933af09c949b4357c3bdbe14a16ada8c94cb421eb4cf9d.jar | FR | java | 2.63 Mb | suspicious |
3308 | java.exe | GET | 200 | 5.254.23.67:80 | http://cdn.turikhay.ru/tlauncher/mcl/bootstrap.json | RO | text | 4.97 Kb | suspicious |
3308 | java.exe | GET | 200 | 188.40.26.206:80 | http://u.tlauncher.ru/repo/libraries/com/getsentry/raven/raven/7.8.1/raven-7.8.1.jar | DE | compressed | 120 Kb | suspicious |
3308 | java.exe | GET | 200 | 213.186.33.186:80 | http://tlauncherrepo.com/repo/versions/versions.json | FR | text | 16.2 Kb | suspicious |
3308 | java.exe | GET | 200 | 188.40.26.206:80 | http://u.tlauncher.ru/repo/versions/versions.json | DE | text | 16.2 Kb | suspicious |
3308 | java.exe | GET | 200 | 188.40.26.206:80 | http://u.tlauncher.ru/repo/libraries/org/apache/commons/commons-lang3/3.4/commons-lang3-3.4.jar | DE | compressed | 424 Kb | suspicious |
3308 | java.exe | GET | 200 | 188.40.26.206:80 | http://u.tlauncher.ru/repo/libraries/org/tukaani/xz/1.5/xz-1.5.jar | DE | java | 97.2 Kb | suspicious |
3308 | java.exe | GET | 200 | 188.40.26.206:80 | http://u.tlauncher.ru/repo/libraries/net/sf/jopt-simple/jopt-simple/4.9/jopt-simple-4.9.jar | DE | java | 64.9 Kb | suspicious |
3308 | java.exe | GET | 200 | 188.40.26.206:80 | http://u.tlauncher.ru/repo/libraries/com/google/code/gson/gson/2.7/gson-2.7.jar | DE | compressed | 226 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3308 | java.exe | 5.254.23.67:80 | cdn.turikhay.ru | — | RO | unknown |
3308 | java.exe | 213.186.33.186:443 | tlauncherrepo.com | OVH SAS | FR | suspicious |
3308 | java.exe | 188.40.26.206:443 | u.tlauncher.ru | Hetzner Online GmbH | DE | suspicious |
— | — | 185.178.208.161:443 | tlaun.ch | Ddos-guard Ltd | RU | suspicious |
3308 | java.exe | 213.186.33.186:80 | tlauncherrepo.com | OVH SAS | FR | suspicious |
3308 | java.exe | 188.40.26.206:80 | u.tlauncher.ru | Hetzner Online GmbH | DE | suspicious |
3308 | java.exe | 195.201.80.5:443 | sentry.ely.by | Awanti Ltd. | RU | unknown |
3308 | java.exe | 99.86.1.139:443 | launchermeta.mojang.com | AT&T Services, Inc. | US | unknown |
— | — | 188.40.26.206:80 | u.tlauncher.ru | Hetzner Online GmbH | DE | suspicious |
3308 | java.exe | 52.217.40.182:443 | s3.amazonaws.com | Amazon.com, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.turikhay.ru |
| suspicious |
tlauncherrepo.com |
| unknown |
u.tlauncher.ru |
| suspicious |
turikhay.ru |
| malicious |
tlaun.ch |
| unknown |
repo.tlauncher.ru |
| suspicious |
launchermeta.mojang.com |
| whitelisted |
s3.amazonaws.com |
| shared |
sentry.ely.by |
| unknown |
account.ely.by |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3308 | java.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3308 | java.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3308 | java.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3308 | java.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3308 | java.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3308 | java.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3308 | java.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3308 | java.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3308 | java.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3308 | java.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |