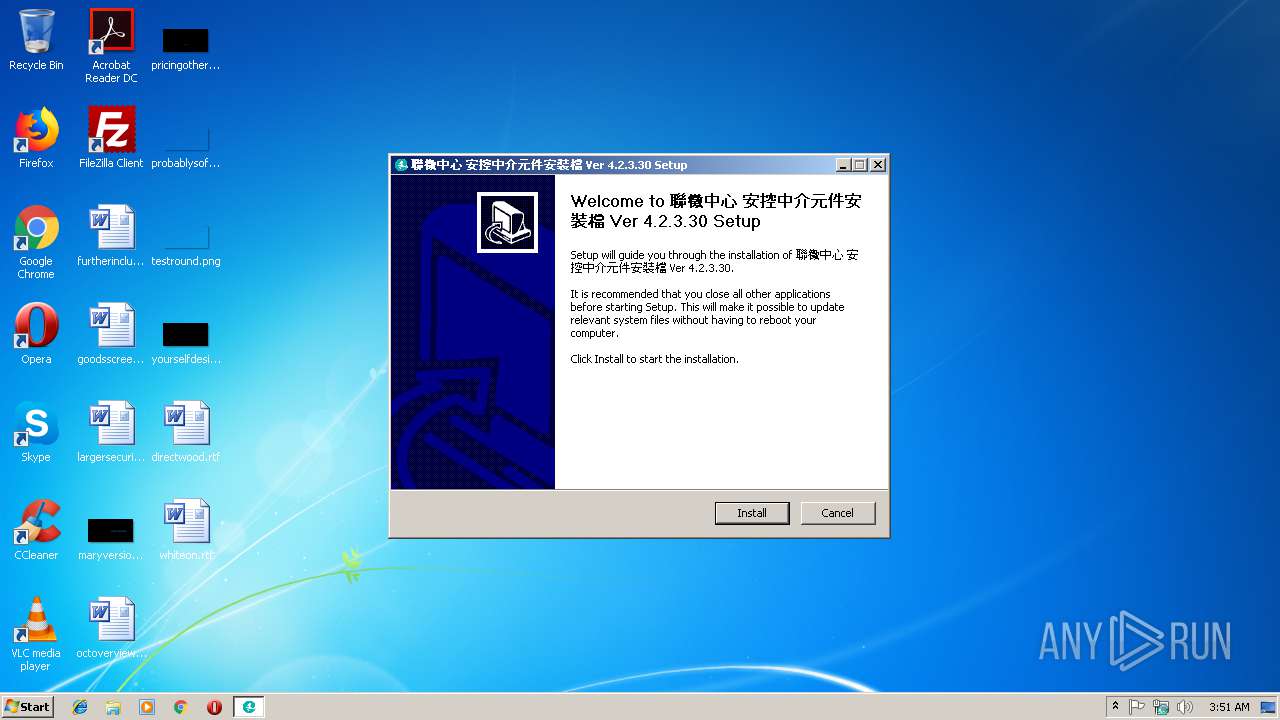
| File name: | JCICSecMiddleware_v4_2_3_30.exe |
| Full analysis: | https://app.any.run/tasks/cae70cea-2543-4b31-9d71-e8412b13b949 |
| Verdict: | Malicious activity |
| Analysis date: | November 13, 2018, 03:50:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
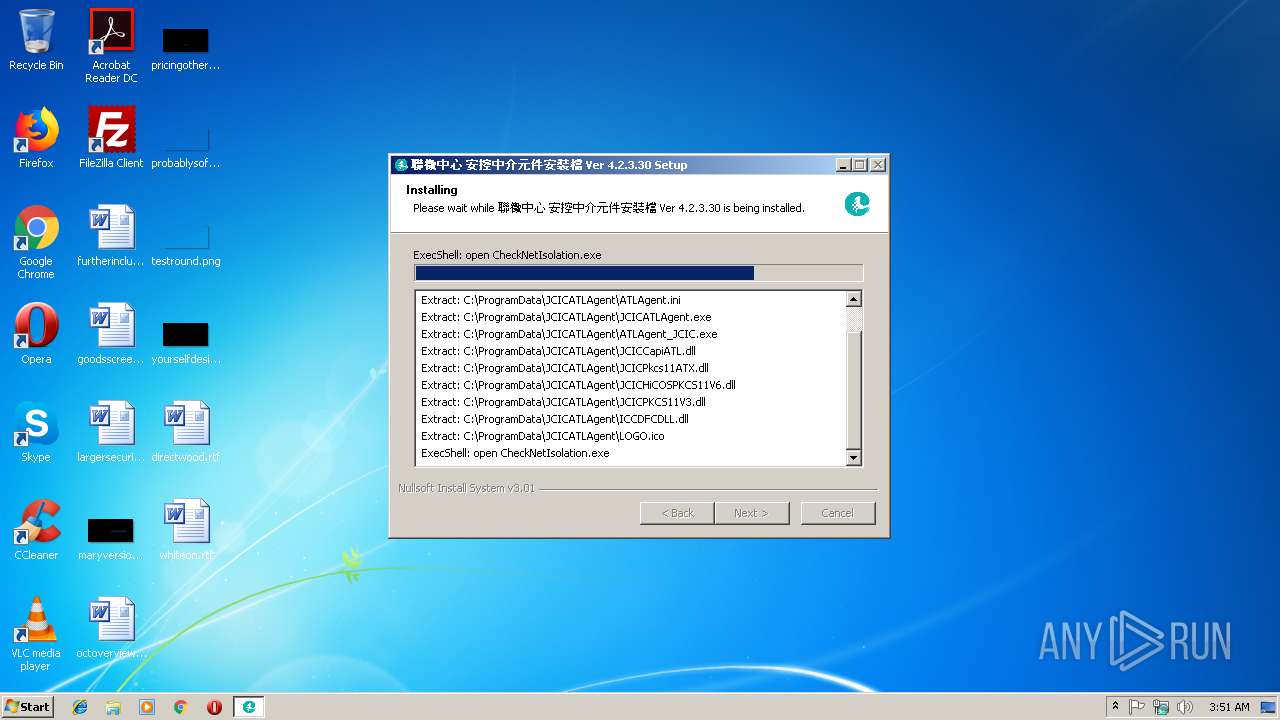
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 3DE528ADD27A1E208DFF3883D59E9DE7 |
| SHA1: | 69280AF182AC443AD0A8E64A7E8F6B11C0AE1D77 |
| SHA256: | 796D24F1E72DC9305A678026A1ABD650D64D5FF72D80143B203170651A3B1AE0 |
| SSDEEP: | 196608:YH6P0uHAx5WhUPjPHybMZhykOay4gCkydf8NxNEks65Wm4Pfsg8oVIOOMi4HVUH2:YHTUAx5WhkHybMZOay4gNyJXfsg8SOMP |
MALICIOUS
Loads dropped or rewritten executable
- JCICSecMiddleware_v4_2_3_30.exe (PID: 2384)
Application was dropped or rewritten from another process
- ns5B9B.tmp (PID: 1996)
- ns5D61.tmp (PID: 3728)
- ns5ED9.tmp (PID: 3388)
- ns6022.tmp (PID: 3984)
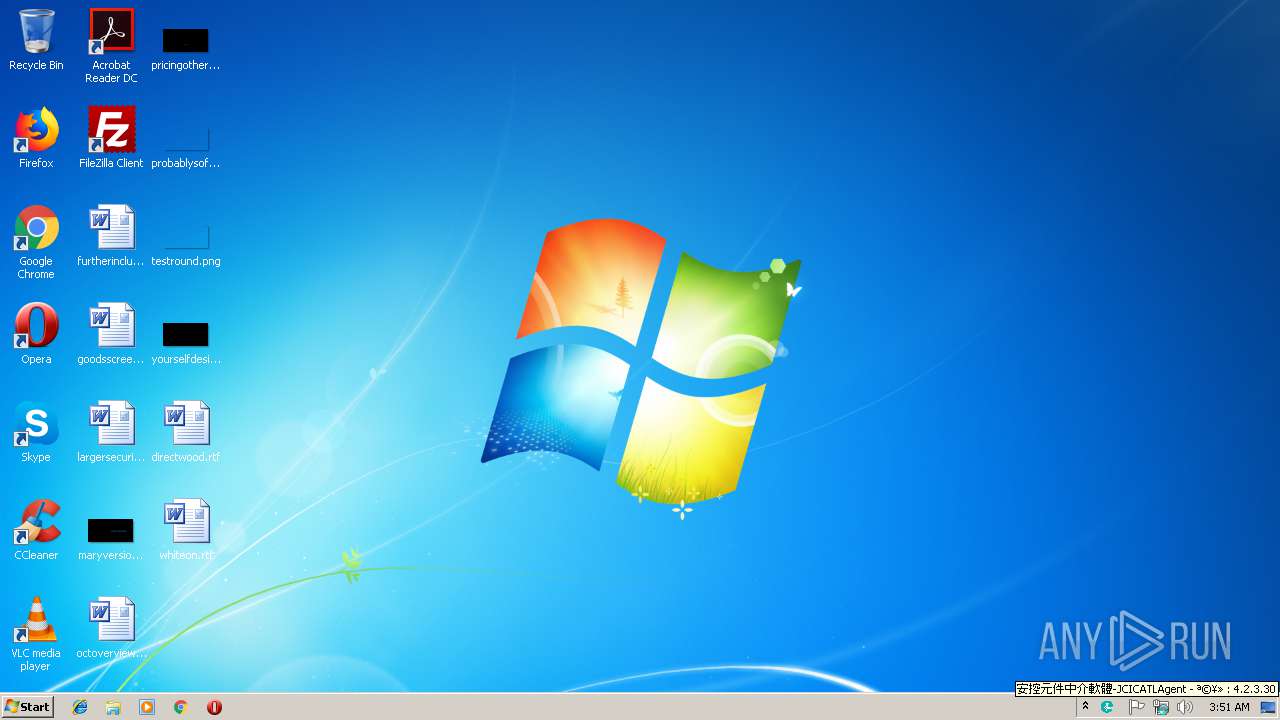
- JCICATLAgent.exe (PID: 3524)
- JCICATLAgent.exe (PID: 2148)
- JCICATLAgent.exe (PID: 1632)
Changes settings of System certificates
- JCICSecMiddleware_v4_2_3_30.exe (PID: 2384)
Changes the autorun value in the registry
- JCICSecMiddleware_v4_2_3_30.exe (PID: 2384)
SUSPICIOUS
Uses TASKLIST.EXE to query information about running processes
- ns5B9B.tmp (PID: 1996)
- ns6022.tmp (PID: 3984)
- ns5ED9.tmp (PID: 3388)
- ns5D61.tmp (PID: 3728)
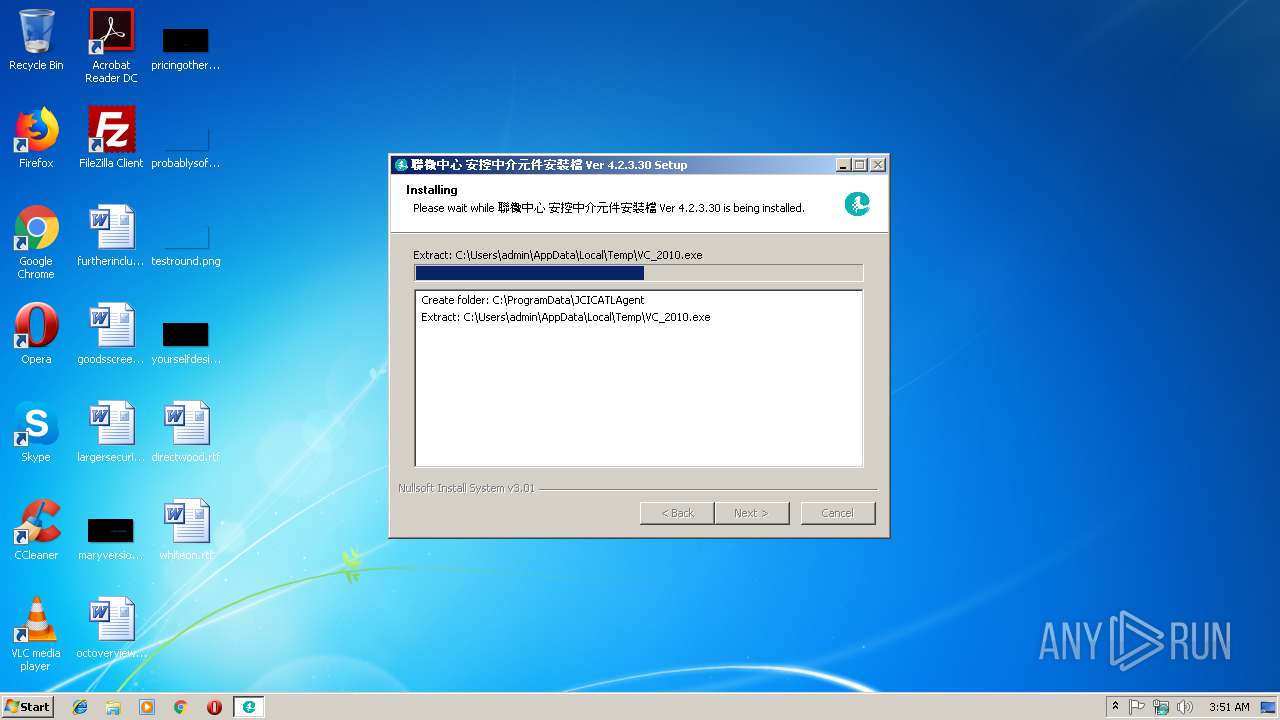
Executable content was dropped or overwritten
- JCICSecMiddleware_v4_2_3_30.exe (PID: 2384)
Starts application with an unusual extension
- JCICSecMiddleware_v4_2_3_30.exe (PID: 2384)
Creates files in the program directory
- JCICSecMiddleware_v4_2_3_30.exe (PID: 2384)
Creates files in the user directory
- JCICATLAgent.exe (PID: 2148)
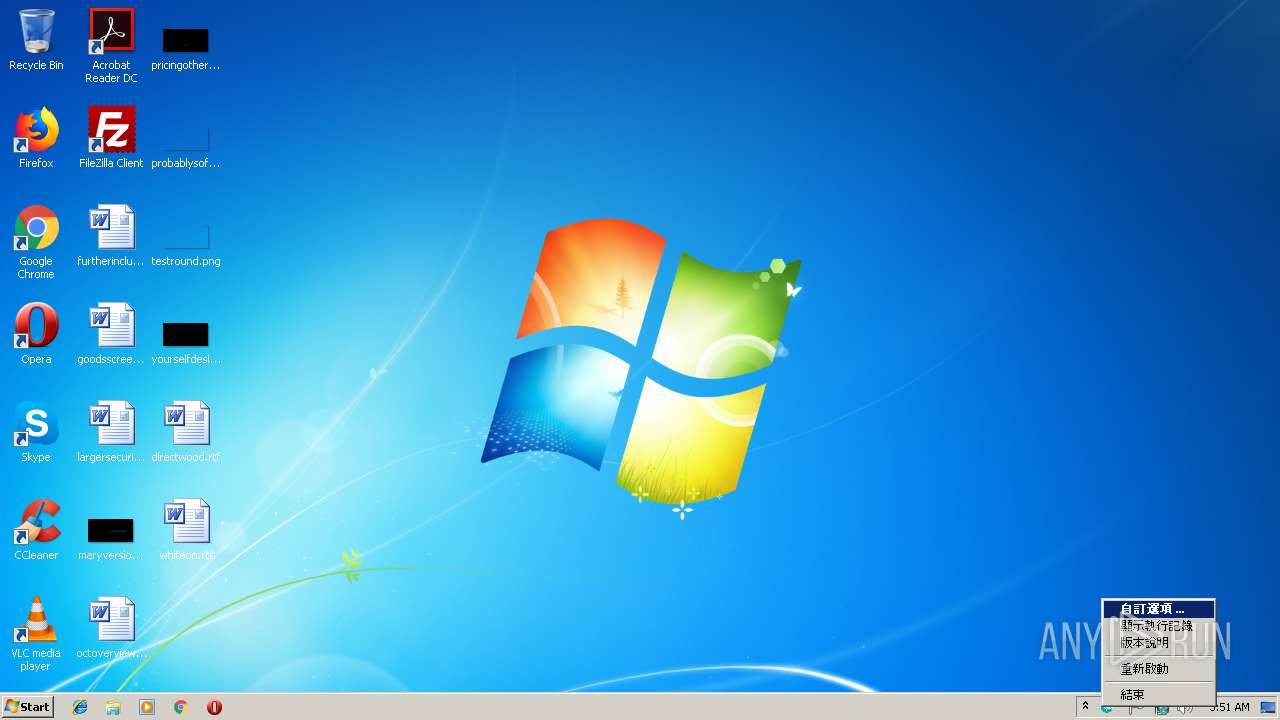
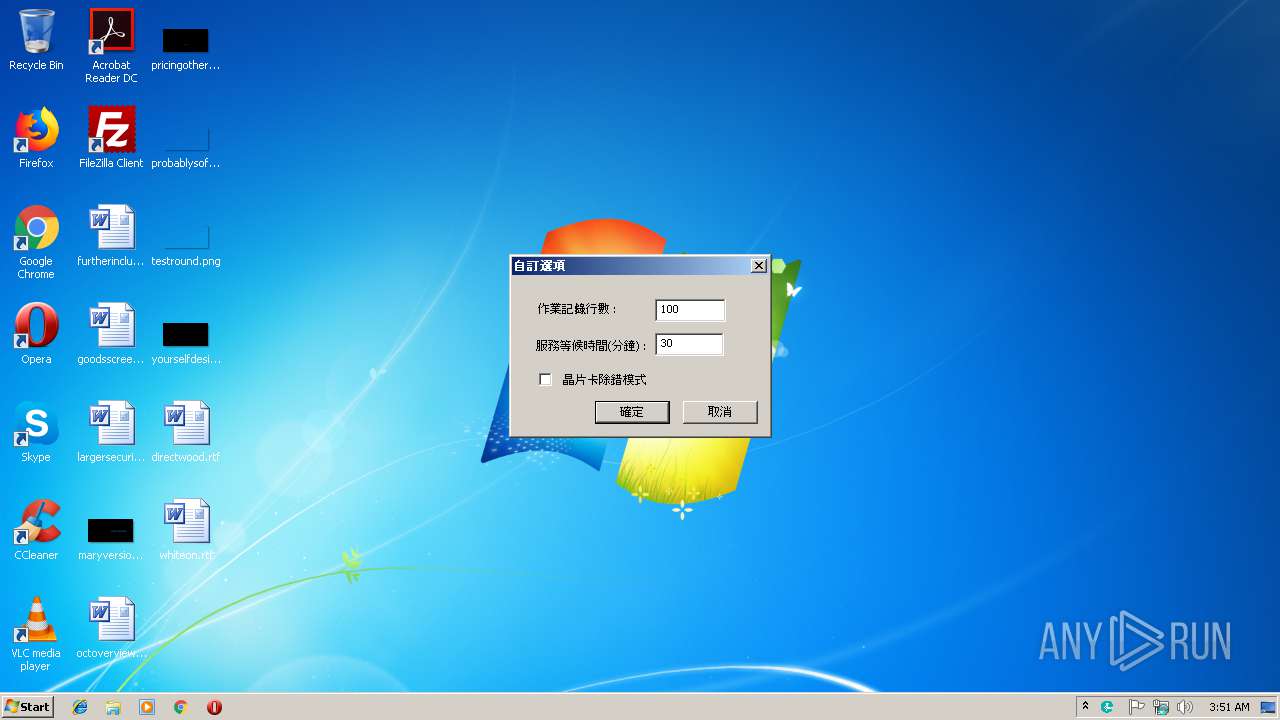
Creates a software uninstall entry
- JCICSecMiddleware_v4_2_3_30.exe (PID: 2384)
Application launched itself
- JCICATLAgent.exe (PID: 2148)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:11 22:50:48+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x344a |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.2.3.30 |
| ProductVersionNumber: | 4.2.3.30 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Traditional) |
| CharacterSet: | Windows, Taiwan (Big5) |
| CompanyName: | 聯徵中心 |
| FileDescription: | 聯徵中心元件安裝程式 |
| FileVersion: | 4.2.3.30 |
| LegalCopyright: | 2016 臺灣網路認證股份有限公司版權所有 c |
| LegalTrademarks: | - |
| ProductName: | 聯徵中心 安控中介元件 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2016 21:50:48 |
| Detected languages: |
|
| CompanyName: | 聯徵中心 |
| FileDescription: | 聯徵中心元件安裝程式 |
| FileVersion: | 4.2.3.30 |
| LegalCopyright: | 2016 臺灣網路認證股份有限公司版權所有 c |
| LegalTrademarks: | - |
| ProductName: | 聯徵中心 安控中介元件 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2016 21:50:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000061F1 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47707 |
.rdata | 0x00008000 | 0x000013A4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.163 |
.data | 0x0000A000 | 0x00020338 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.97456 |
.ndata | 0x0002B000 | 0x00016000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00041000 | 0x00005FC0 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.79629 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28813 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 0 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.98572 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
51
Monitored processes
13
Malicious processes
1
Suspicious processes
1
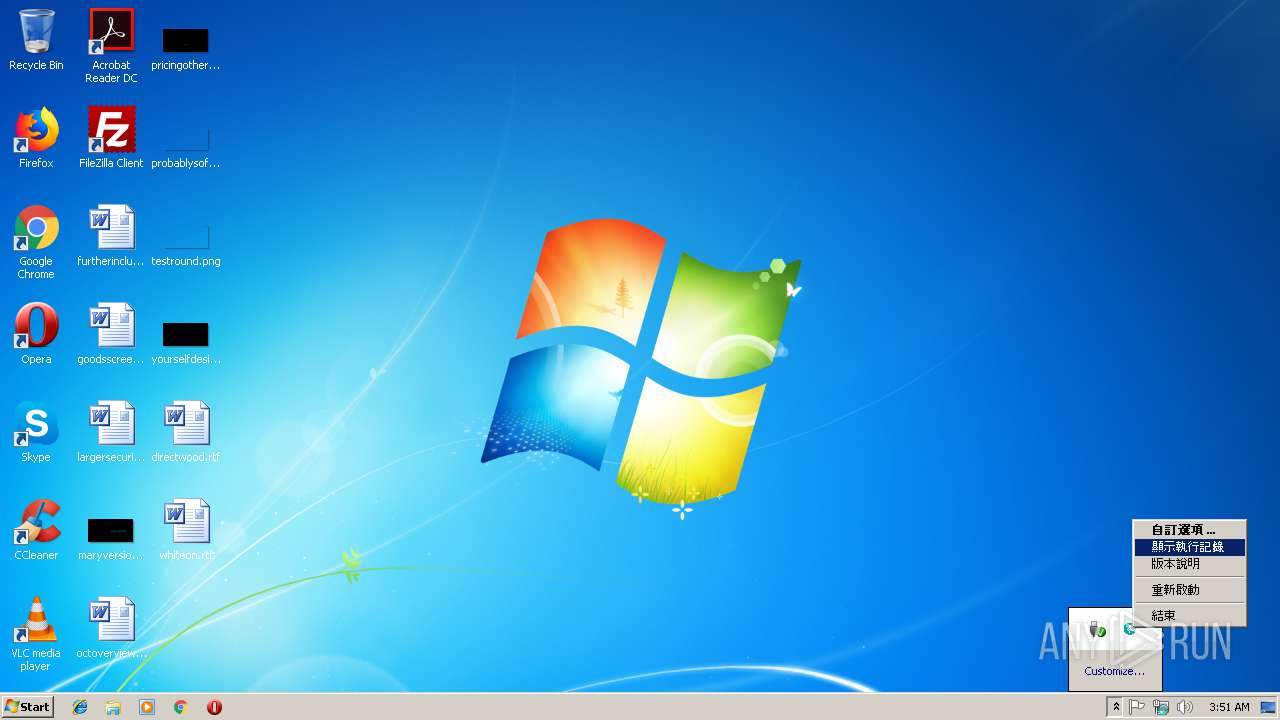
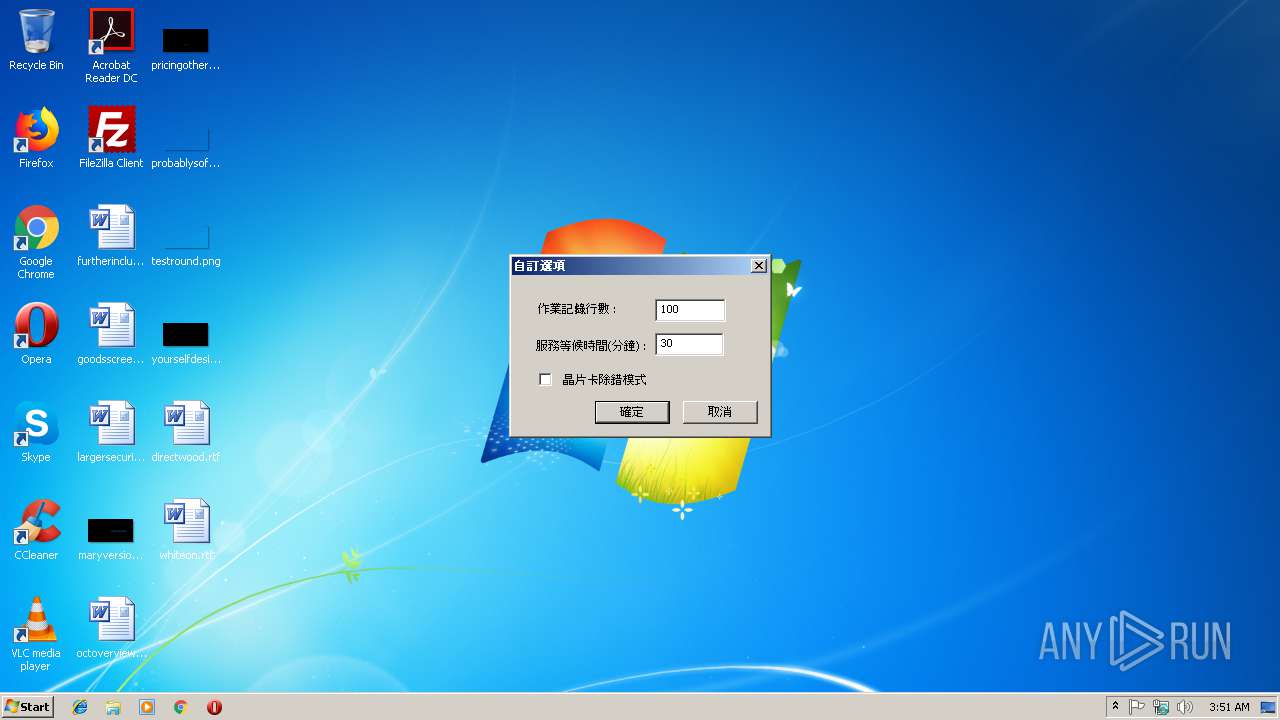
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 980 | tasklist.exe /NH /FI "IMAGENAME eq firefox.exe" | C:\Windows\system32\tasklist.exe | — | ns6022.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1632 | C:\ProgramData\JCICATLAgent\JCICATLAgent.exe | C:\ProgramData\JCICATLAgent\JCICATLAgent.exe | — | JCICATLAgent.exe | |||||||||||
User: admin Company: 臺灣網路認證 Integrity Level: MEDIUM Description: 安控中介軟體服務程式 Exit code: 0 Version: 4.2.3.30 Modules
| |||||||||||||||
| 1996 | "C:\Users\admin\AppData\Local\Temp\nse4AB2.tmp\ns5B9B.tmp" tasklist.exe /NH /FI "IMAGENAME eq ATLAgent_JCIC.exe" | C:\Users\admin\AppData\Local\Temp\nse4AB2.tmp\ns5B9B.tmp | — | JCICSecMiddleware_v4_2_3_30.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2148 | "C:\ProgramData\JCICATLAgent\JCICATLAgent.exe" | C:\ProgramData\JCICATLAgent\JCICATLAgent.exe | — | explorer.exe | |||||||||||
User: admin Company: 臺灣網路認證 Integrity Level: MEDIUM Description: 安控中介軟體服務程式 Exit code: 0 Version: 4.2.3.30 Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\AppData\Local\Temp\JCICSecMiddleware_v4_2_3_30.exe" | C:\Users\admin\AppData\Local\Temp\JCICSecMiddleware_v4_2_3_30.exe | explorer.exe | ||||||||||||
User: admin Company: 聯徵中心 Integrity Level: HIGH Description: 聯徵中心元件安裝程式 Exit code: 0 Version: 4.2.3.30 Modules
| |||||||||||||||
| 2416 | tasklist.exe /NH /FI "IMAGENAME eq chrome.exe" | C:\Windows\system32\tasklist.exe | — | ns5ED9.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3388 | "C:\Users\admin\AppData\Local\Temp\nse4AB2.tmp\ns5ED9.tmp" tasklist.exe /NH /FI "IMAGENAME eq chrome.exe" | C:\Users\admin\AppData\Local\Temp\nse4AB2.tmp\ns5ED9.tmp | — | JCICSecMiddleware_v4_2_3_30.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3396 | tasklist.exe /NH /FI "IMAGENAME eq ATLAgent_JCIC.exe" | C:\Windows\system32\tasklist.exe | — | ns5B9B.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3524 | "C:\ProgramData\JCICATLAgent\JCICATLAgent.exe" | C:\ProgramData\JCICATLAgent\JCICATLAgent.exe | — | explorer.exe | |||||||||||
User: admin Company: 臺灣網路認證 Integrity Level: MEDIUM Description: 安控中介軟體服務程式 Exit code: 0 Version: 4.2.3.30 Modules
| |||||||||||||||
| 3728 | "C:\Users\admin\AppData\Local\Temp\nse4AB2.tmp\ns5D61.tmp" tasklist.exe /NH /FI "IMAGENAME eq JCICATLAgent.exe" | C:\Users\admin\AppData\Local\Temp\nse4AB2.tmp\ns5D61.tmp | — | JCICSecMiddleware_v4_2_3_30.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
402
Read events
396
Write events
6
Delete events
0
Modification events
| (PID) Process: | (2384) JCICSecMiddleware_v4_2_3_30.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\ED39A078ABCB6D3314F4298EF7BC83D087B722E1 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000C7E710F49C6798FC772A0C1A141EB7870F0000000100000020000000ED9520BD5029B6C2FB6962B98B5B3942117D227E5153C2DD29F0F2CA1935816814000000010000001400000030AB4DBD18278412A78FF4588FF991455C65F5B7190000000100000010000000EDDFC589AA0A04C4A8E3CBA6C653DA3F030000000100000014000000ED39A078ABCB6D3314F4298EF7BC83D087B722E1200000000100000058030000308203543082023CA00302010202051234567890300D06092A864886F70D01010B0500301431123010060355040313096C6F63616C686F7374301E170D3137303432303130343930305A170D3338303432303130343930305A301431123010060355040313096C6F63616C686F737430820122300D06092A864886F70D01010105000382010F003082010A0282010100F3C25AA49DE8F8E0BB2CE8AE67C3D0F780FB0B706B4EF7558B0C4690199D68C83122BC03CA70A7939A43408BC9DE1DD08DB19F648C352619FB4A601ABD505B6428CD5ED46EBA0EEB17AC0380AF426E13FDB81EB4F5EDBB26B2CF0291E3187B4E2DA54A334D0CD60A7621E67ABC45C947C79A7EEDCABCE23B3EE177CBE6138B3483EB0D47CCCE64FD43E614AC525008089797F2727247D5E0C43510ABEC07C7C75620F88C36457130652F5D76279667DFDE407BCBD73FCE0083FD836E2C81938A219824BC37F60141DC1D04E0461F5E5A8CD4ECBBAC7B0286E0584082B5FEF4A2C13B7B5EF2F0A68FE3661BEC2F39CDB3656A50CA6082F383C5A542D48D162D230203010001A381AC3081A9301D0603551D0E0416041430AB4DBD18278412A78FF4588FF991455C65F5B730400603551D2304393037801430AB4DBD18278412A78FF4588FF991455C65F5B7A118A416301431123010060355040313096C6F63616C686F737482051234567890300E0603551D0F0101FF0404030205A030200603551D250101FF0416301406082B0601050507030106082B0601050507030230140603551D11040D300B82096C6F63616C686F7374300D06092A864886F70D01010B050003820101009D3E25589B57210DD70731E04BAF2F2E13B07496BA953FC7FEC55FDB2101C74DCEEF39B9489521E8A2160CAEFFB198BB8AA55A35C3C8E8E1AA9DCD35FF54657166285EC49BC1F3DA517C79A82EBA4DE8F80A84700C832256145EC72678979DFA3A680F60E1EADE513337F2F2B74326D92B07BF0F6EC64D9C1390C880A05BFA2C65860F73E1C9B96B878D11EEC3BCBFD55D982E3072E516C3330C9A11E92798AD2DE9F808AA55D6E8E9F580F8F16B573D9D73A87A13EF930D7A8D9C4971CD2283760D9EA5A9605A580C3F48990ACBC4D52A4D35A8F8B2DF0604772A92C186014CFEB94B815EA1886B3A86C5F2B621F5946F4DC83F60426DD24674230B817830F2 | |||
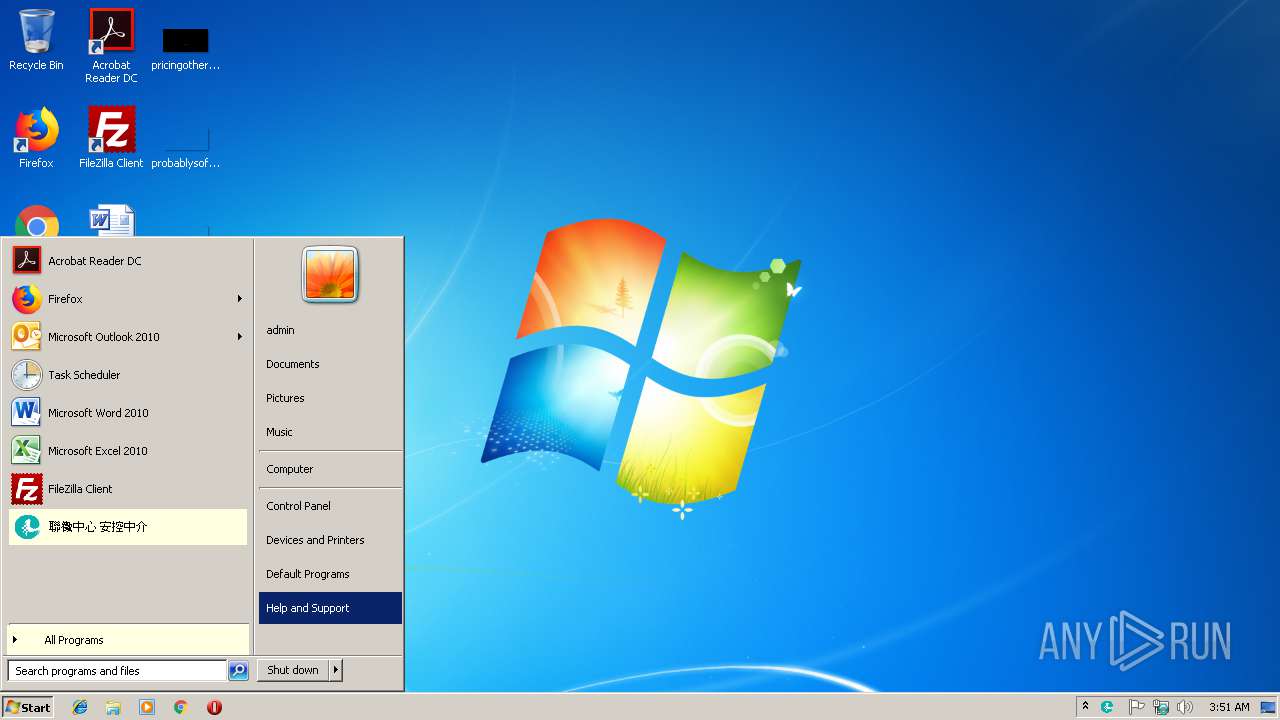
| (PID) Process: | (2384) JCICSecMiddleware_v4_2_3_30.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | JCICATLAgent |
Value: C:\ProgramData\JCICATLAgent\JCICATLAgent.exe | |||
| (PID) Process: | (2384) JCICSecMiddleware_v4_2_3_30.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\JCICATLAgent |
| Operation: | write | Name: | DisplayName |
Value: 聯徵中心 安控中介元件 (remove only) | |||
| (PID) Process: | (2384) JCICSecMiddleware_v4_2_3_30.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\JCICATLAgent |
| Operation: | write | Name: | DisplayIcon |
Value: C:\ProgramData\JCICATLAgent\LOGO.ico | |||
| (PID) Process: | (2384) JCICSecMiddleware_v4_2_3_30.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\JCICATLAgent |
| Operation: | write | Name: | UninstallString |
Value: C:\ProgramData\JCICATLAgent\Uninstall.exe | |||
| (PID) Process: | (2384) JCICSecMiddleware_v4_2_3_30.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\JCICATLAgent |
| Operation: | write | Name: | Publisher |
Value: 聯徵中心 | |||
Executable files
17
Suspicious files
0
Text files
30
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2384 | JCICSecMiddleware_v4_2_3_30.exe | C:\Users\admin\AppData\Local\Temp\nse4AB2.tmp\ns5B9B.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | JCICSecMiddleware_v4_2_3_30.exe | C:\Users\admin\AppData\Local\Temp\nse4AB2.tmp\ns5D61.tmp | executable | |
MD5:— | SHA256:— | |||
| 2384 | JCICSecMiddleware_v4_2_3_30.exe | C:\Users\admin\AppData\Local\Temp\nse4AB2.tmp\ns6022.tmp | executable | |
MD5:— | SHA256:— | |||
| 2384 | JCICSecMiddleware_v4_2_3_30.exe | C:\Users\admin\AppData\Local\Temp\nse4AB2.tmp\ns5ED9.tmp | executable | |
MD5:— | SHA256:— | |||
| 2384 | JCICSecMiddleware_v4_2_3_30.exe | C:\Users\admin\AppData\Local\Temp\nse4AB2.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 2384 | JCICSecMiddleware_v4_2_3_30.exe | C:\ProgramData\JCICATLAgent\JCICCapiATL.dll | executable | |
MD5:— | SHA256:— | |||
| 2384 | JCICSecMiddleware_v4_2_3_30.exe | C:\Users\admin\AppData\Local\Temp\nso4AB1.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | JCICSecMiddleware_v4_2_3_30.exe | C:\Users\admin\AppData\Local\Temp\nse4AB2.tmp\UserInfo.dll | executable | |
MD5:1B446B36F5B4022D50FFDC0CF567B24A | SHA256:2862C7BC7F11715CEBDEA003564A0D70BF42B73451E2B672110E1392EC392922 | |||
| 2384 | JCICSecMiddleware_v4_2_3_30.exe | C:\Users\admin\AppData\Local\Temp\nse4AB2.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2384 | JCICSecMiddleware_v4_2_3_30.exe | C:\Users\admin\AppData\Local\Temp\nse4AB2.tmp\System.dll | executable | |
MD5:17ED1C86BD67E78ADE4712BE48A7D2BD | SHA256:BD046E6497B304E4EA4AB102CAB2B1F94CE09BDE0EEBBA4C59942A732679E4EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report