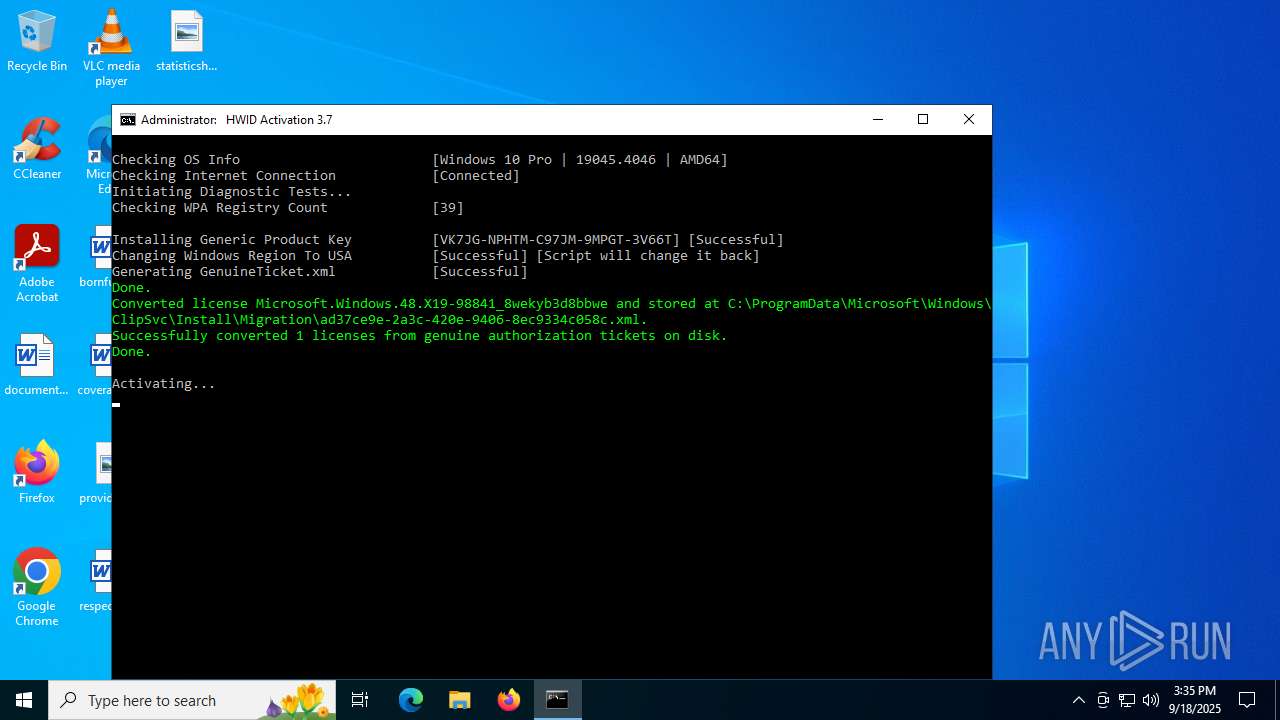
| File name: | HWID_Activation.cmd |
| Full analysis: | https://app.any.run/tasks/da10af48-c93e-4efb-95f0-d84231ce8937 |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2025, 15:33:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (376), with CRLF line terminators |
| MD5: | ED762B7CEBF01278C987DB20147692A8 |
| SHA1: | C66AB582EA9DDC8D31FB8D66FB4E260EC7E0FC83 |
| SHA256: | 796BE291F3A71A7148BA6BAEBAF500F9BC339DCDF7CE12A5B446E35D8A792624 |
| SSDEEP: | 1536:pD/8u/n/9Zv/DaKRf8VhEg6jj/flC2kq7wfmjKJvK5Ifrrc2LiXf6s:pD/3/n/3/l/gfOX5ITK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts SC.EXE for service management
- cmd.exe (PID: 5876)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 6160)
Windows service management via SC.EXE
- sc.exe (PID: 4692)
- sc.exe (PID: 1660)
- sc.exe (PID: 4884)
- sc.exe (PID: 2312)
- sc.exe (PID: 2992)
- sc.exe (PID: 3636)
- sc.exe (PID: 4520)
- sc.exe (PID: 6648)
- sc.exe (PID: 6212)
- sc.exe (PID: 6772)
- sc.exe (PID: 4232)
- sc.exe (PID: 3624)
- sc.exe (PID: 3960)
- sc.exe (PID: 4700)
- sc.exe (PID: 4884)
- sc.exe (PID: 4024)
- sc.exe (PID: 6808)
- sc.exe (PID: 1636)
- sc.exe (PID: 2760)
- sc.exe (PID: 5628)
- sc.exe (PID: 6180)
- sc.exe (PID: 1300)
- sc.exe (PID: 760)
- sc.exe (PID: 1232)
- sc.exe (PID: 4912)
- sc.exe (PID: 7048)
- sc.exe (PID: 6460)
- sc.exe (PID: 2076)
- sc.exe (PID: 4708)
- sc.exe (PID: 3656)
- sc.exe (PID: 6304)
- sc.exe (PID: 1040)
- sc.exe (PID: 5724)
- sc.exe (PID: 3760)
- sc.exe (PID: 6876)
- sc.exe (PID: 4788)
- sc.exe (PID: 5288)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5876)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 6160)
Application launched itself
- cmd.exe (PID: 5084)
- cmd.exe (PID: 4692)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 2032)
- cmd.exe (PID: 6160)
- powershell.exe (PID: 4528)
- powershell.exe (PID: 3636)
- ClipUp.exe (PID: 1872)
- powershell.exe (PID: 4692)
- powershell.exe (PID: 4012)
- powershell.exe (PID: 7104)
- cmd.exe (PID: 5876)
Executing commands from a ".bat" file
- powershell.exe (PID: 1880)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 5876)
- cmd.exe (PID: 6160)
Executing commands from ".cmd" file
- cmd.exe (PID: 5780)
- powershell.exe (PID: 1880)
- cmd.exe (PID: 6160)
- cmd.exe (PID: 5876)
Executes script without checking the security policy
- powershell.exe (PID: 3948)
- powershell.exe (PID: 1880)
- powershell.exe (PID: 6512)
- powershell.exe (PID: 2972)
- powershell.exe (PID: 4084)
- powershell.exe (PID: 6732)
- powershell.exe (PID: 4528)
- powershell.exe (PID: 5236)
- powershell.exe (PID: 4476)
- powershell.exe (PID: 7084)
- powershell.exe (PID: 3956)
- powershell.exe (PID: 3656)
- powershell.exe (PID: 3572)
- powershell.exe (PID: 3736)
- powershell.exe (PID: 1604)
- powershell.exe (PID: 3760)
- powershell.exe (PID: 3636)
- powershell.exe (PID: 4692)
- powershell.exe (PID: 7104)
- powershell.exe (PID: 4684)
- powershell.exe (PID: 4012)
Hides command output
- cmd.exe (PID: 6292)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 4580)
- cmd.exe (PID: 1880)
- cmd.exe (PID: 2760)
- cmd.exe (PID: 7116)
- cmd.exe (PID: 1660)
- cmd.exe (PID: 1068)
- cmd.exe (PID: 6856)
- cmd.exe (PID: 3740)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 6164)
- cmd.exe (PID: 4800)
- cmd.exe (PID: 7020)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 6292)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 4476)
- cmd.exe (PID: 6160)
- cmd.exe (PID: 1660)
- cmd.exe (PID: 1816)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 5876)
- cmd.exe (PID: 6292)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 6868)
- cmd.exe (PID: 6160)
- cmd.exe (PID: 4476)
- powershell.exe (PID: 4528)
- cmd.exe (PID: 1660)
- cmd.exe (PID: 2324)
- powershell.exe (PID: 3636)
- cmd.exe (PID: 1816)
- powershell.exe (PID: 4692)
- powershell.exe (PID: 7104)
- powershell.exe (PID: 4012)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5876)
- cmd.exe (PID: 6292)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 6868)
- cmd.exe (PID: 4476)
- powershell.exe (PID: 4528)
- cmd.exe (PID: 6160)
- cmd.exe (PID: 1660)
- cmd.exe (PID: 2324)
- powershell.exe (PID: 3636)
- powershell.exe (PID: 4692)
- powershell.exe (PID: 7104)
- cmd.exe (PID: 1816)
- powershell.exe (PID: 4012)
Converts TXT file into a string
- powershell.exe (PID: 3948)
- powershell.exe (PID: 6512)
- powershell.exe (PID: 4084)
- powershell.exe (PID: 3656)
- powershell.exe (PID: 3760)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 3948)
- powershell.exe (PID: 6512)
- powershell.exe (PID: 4084)
- powershell.exe (PID: 3656)
- powershell.exe (PID: 3760)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 3948)
- powershell.exe (PID: 6512)
- powershell.exe (PID: 4084)
- powershell.exe (PID: 3656)
- powershell.exe (PID: 3760)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5780)
- cmd.exe (PID: 6160)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 536)
- cmd.exe (PID: 6160)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 4580)
Probably file/command deobfuscation
- cmd.exe (PID: 4476)
- cmd.exe (PID: 1816)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 4528)
- powershell.exe (PID: 3636)
- powershell.exe (PID: 4692)
- powershell.exe (PID: 7104)
- powershell.exe (PID: 4012)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6160)
- cmd.exe (PID: 1068)
- cmd.exe (PID: 6856)
- cmd.exe (PID: 6164)
Creates a scheduled task using COM
- cmd.exe (PID: 2324)
- powershell.exe (PID: 3736)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 6160)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 3760)
INFO
Checks operating system version
- cmd.exe (PID: 5780)
- cmd.exe (PID: 6160)
- cmd.exe (PID: 5876)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 3948)
- powershell.exe (PID: 6512)
- powershell.exe (PID: 4084)
- powershell.exe (PID: 3656)
- powershell.exe (PID: 3760)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 3948)
- powershell.exe (PID: 6512)
- powershell.exe (PID: 4084)
- powershell.exe (PID: 3656)
- powershell.exe (PID: 3760)
Checks supported languages
- mode.com (PID: 1740)
- mode.com (PID: 4168)
- mode.com (PID: 6164)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 3396)
- WMIC.exe (PID: 7008)
- WMIC.exe (PID: 5188)
- WMIC.exe (PID: 6856)
- WMIC.exe (PID: 6220)
- WMIC.exe (PID: 6512)
- WMIC.exe (PID: 5988)
- WMIC.exe (PID: 5764)
- WMIC.exe (PID: 5188)
- WMIC.exe (PID: 2964)
- WMIC.exe (PID: 2076)
- WMIC.exe (PID: 3656)
- WMIC.exe (PID: 4540)
- WMIC.exe (PID: 5652)
Creates files in the program directory
- cmd.exe (PID: 6160)
- ClipUp.exe (PID: 3580)
- powershell.exe (PID: 3760)
Create files in a temporary directory
- ClipUp.exe (PID: 3580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
414
Monitored processes
277
Malicious processes
7
Suspicious processes
17
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | cmd /c "wmic path Win32_ComputerSystem get CreationClassName /value" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | C:\WINDOWS\System32\cmd.exe /c reg query "HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\Environment" /v PROCESSOR_ARCHITECTURE | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo Ready " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Version 5.1 -s -NoLogo -NoProfile | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 4294967295 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 760 | sc start KeyIso | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 868 | reg query HKLM\SYSTEM\CurrentControlSet\Services\Winmgmt /v DependOnService | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | C:\WINDOWS\System32\cmd.exe /c ping -n 1 l.root-servers.net | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | sc query KeyIso | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1044 | reg query HKLM\SYSTEM\CurrentControlSet\Services\LicenseManager /v ImagePath | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | reg query HKLM\SYSTEM\CurrentControlSet\Services\KeyIso /v ObjectName | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
124 513
Read events
124 504
Write events
2
Delete events
7
Modification events
| (PID) Process: | (1604) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International\Geo |
| Operation: | write | Name: | Name |
Value: US | |||
| (PID) Process: | (1604) powershell.exe | Key: | HKEY_CURRENT_USER\Control Panel\International\Geo |
| Operation: | write | Name: | Nation |
Value: 244 | |||
| (PID) Process: | (4916) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\ExtendedProperties |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4916) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production\Property |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4916) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production\Token\{D6D5A677-0872-4AB0-9442-BB792FCE85C5} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4916) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production\Token |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4916) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive\production |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4916) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL\Immersive |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4916) reg.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\IdentityCRL |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
1
Text files
56
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1880 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_p1vkhqpt.ld4.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1880 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4oeoq4cp.n2x.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3948 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_b3yrkkaa.1cd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6512 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jexievcg.obd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1880 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:83CCB40412E67A2E3F45181EF68DC9B5 | SHA256:CE701E67605E2300D105228B680BA887306F7A78B901754FF520DDD92DD1F9FA | |||
| 3948 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pktjp4e2.urz.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6512 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_r4mpjv1d.hdz.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2972 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fikz3vlz.yro.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2972 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ah43r3an.jyk.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4084 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wqauzpqe.f0u.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
45
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.5:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.67:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | unknown |
— | — | POST | 400 | 40.126.31.67:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | unknown |
— | — | POST | 400 | 40.126.31.2:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | unknown |
— | — | POST | 400 | 40.126.31.71:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | unknown |
— | — | POST | 400 | 20.190.159.129:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | unknown |
— | — | POST | 400 | 20.190.159.64:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | unknown |
— | — | POST | 400 | 40.126.31.128:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | unknown |
— | — | POST | 400 | 20.190.159.75:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.5:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7040 | svchost.exe | 20.190.160.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6024 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
activated.win |
| unknown |
updatecheck37.activated.win |
| unknown |
l.root-servers.net |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |