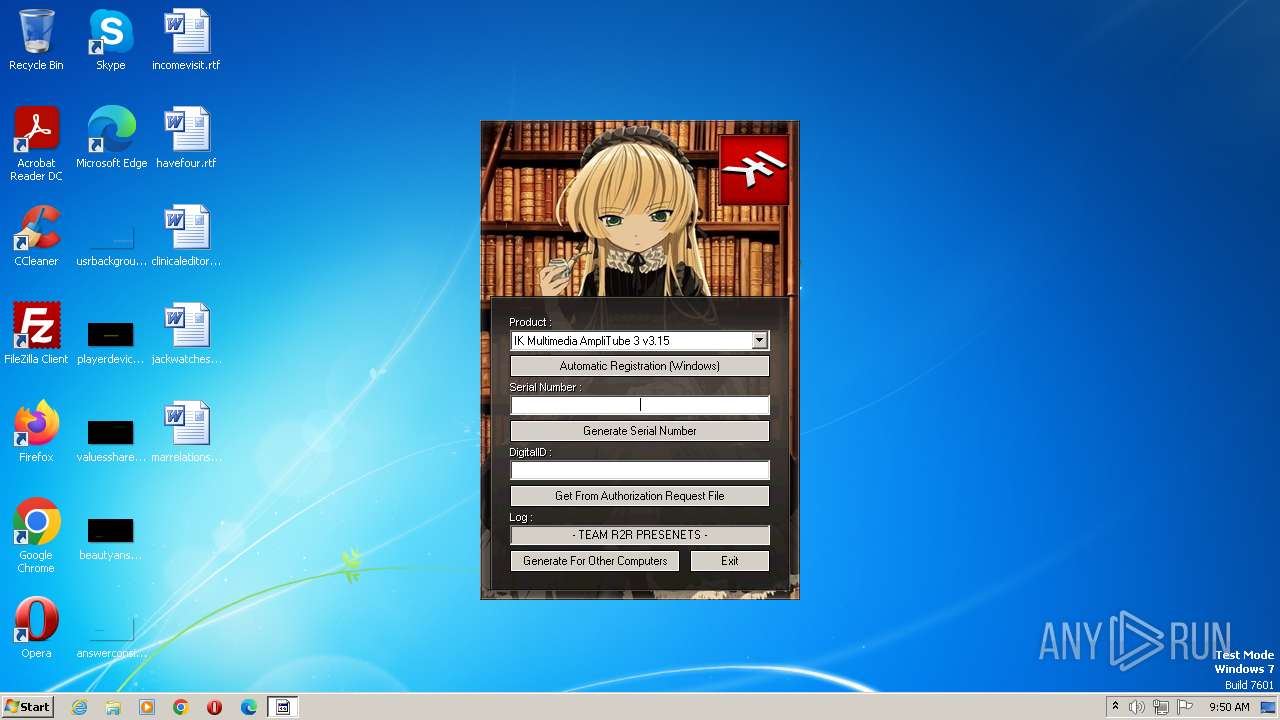
| File name: | IK_Multimedia_Keygen.exe |
| Full analysis: | https://app.any.run/tasks/af79e75c-7687-4a0d-b977-8d048ac04252 |
| Verdict: | Malicious activity |
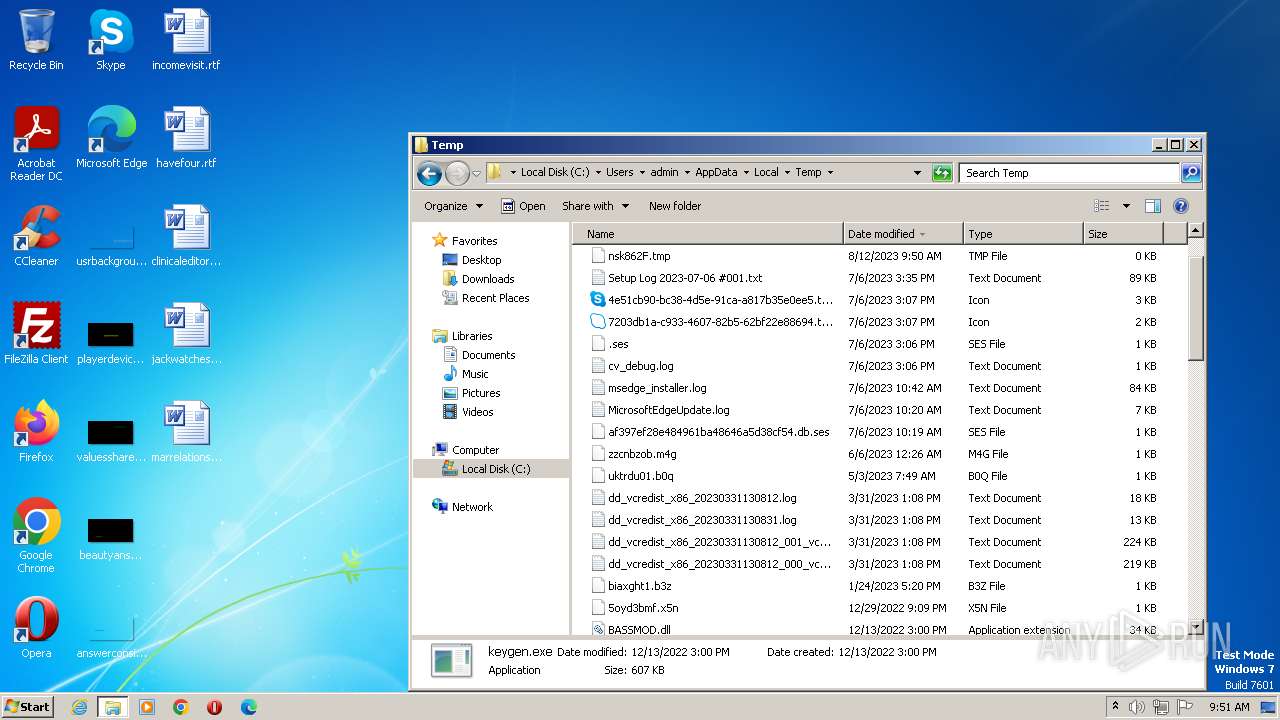
| Analysis date: | August 12, 2023, 08:50:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 154702D5F61A1FAFF5EFE6D561D383EC |
| SHA1: | CCF53CA79B8C6D29CD9380DF84D31CB51BDF89FC |
| SHA256: | 795755D7F4C592F5190BFA769984E13D3A8BA5D08DEB3D88002DCA60CF709AE5 |
| SSDEEP: | 12288:XYkc9t2Sll/aksMf8ZqBebQM1Q9Krpyp2bDP:XYkcL5aSfCqQbT1WKbDP |
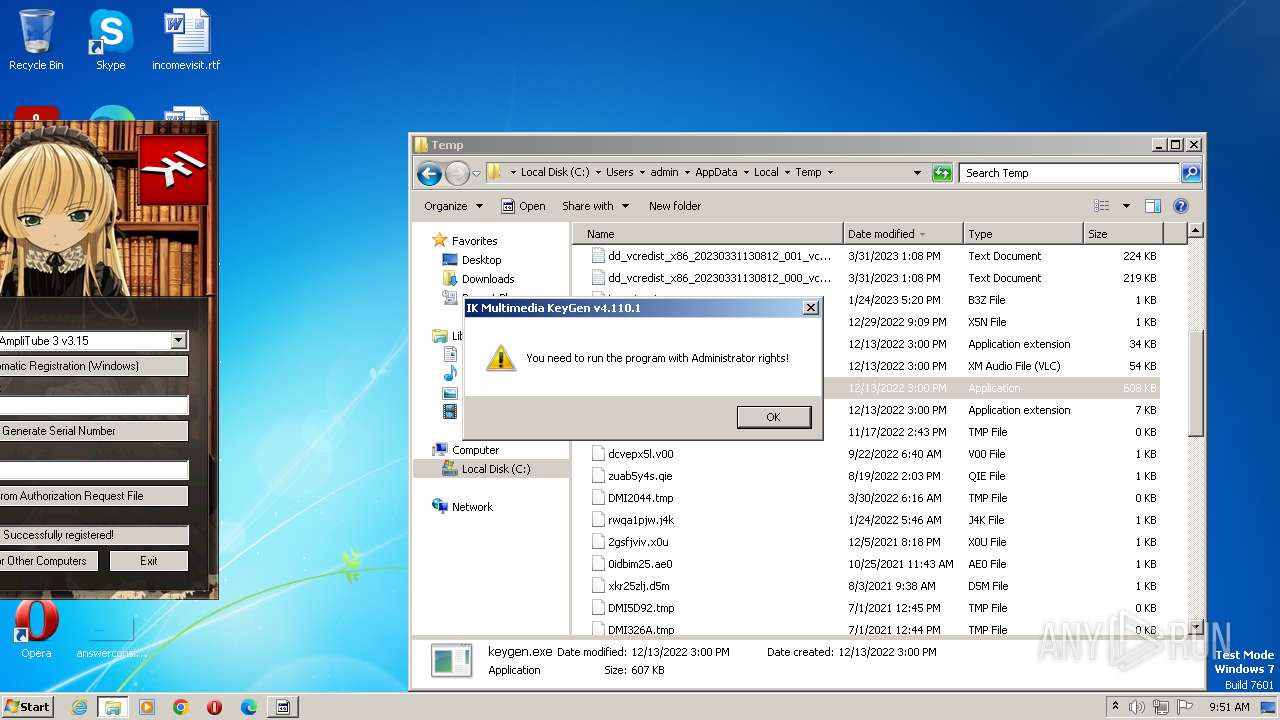
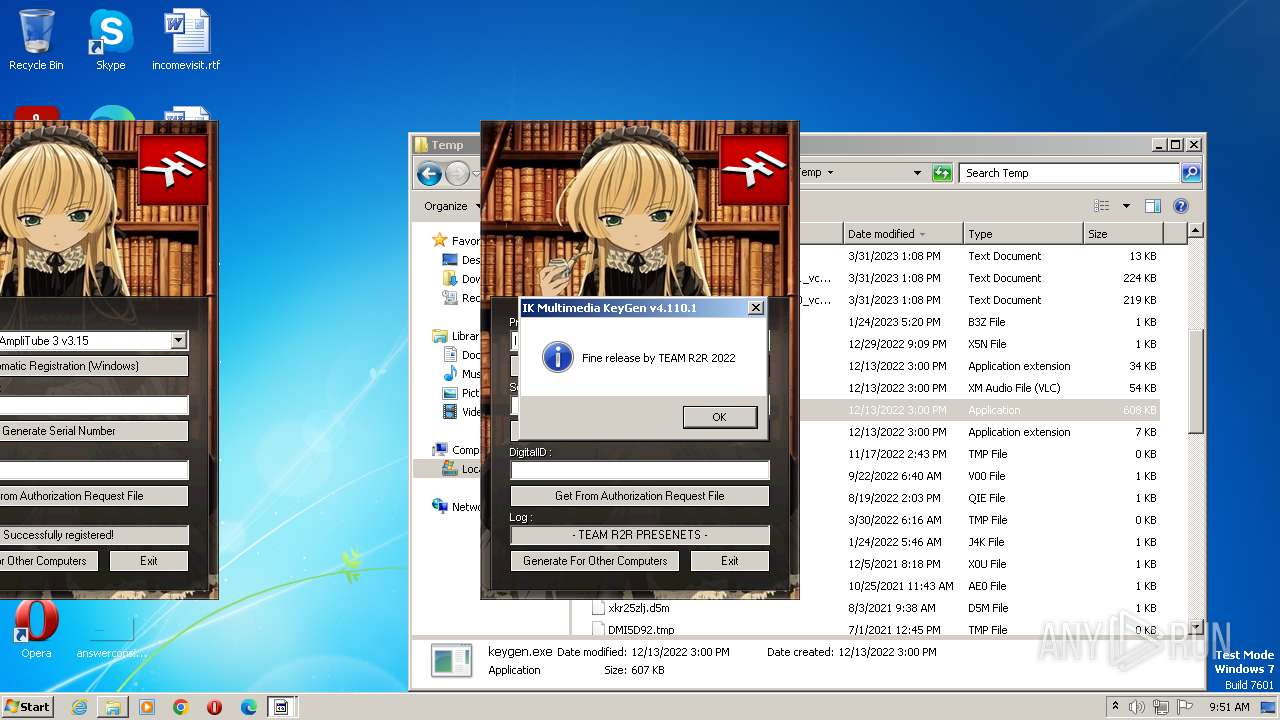
MALICIOUS
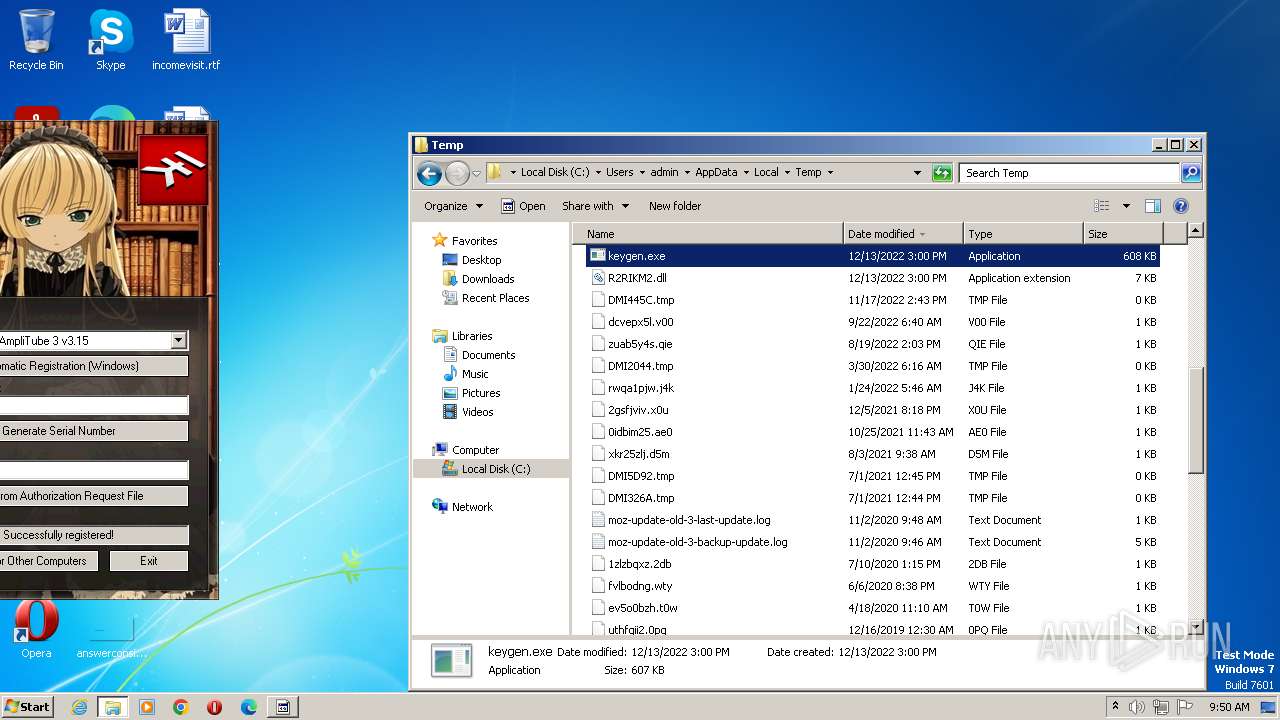
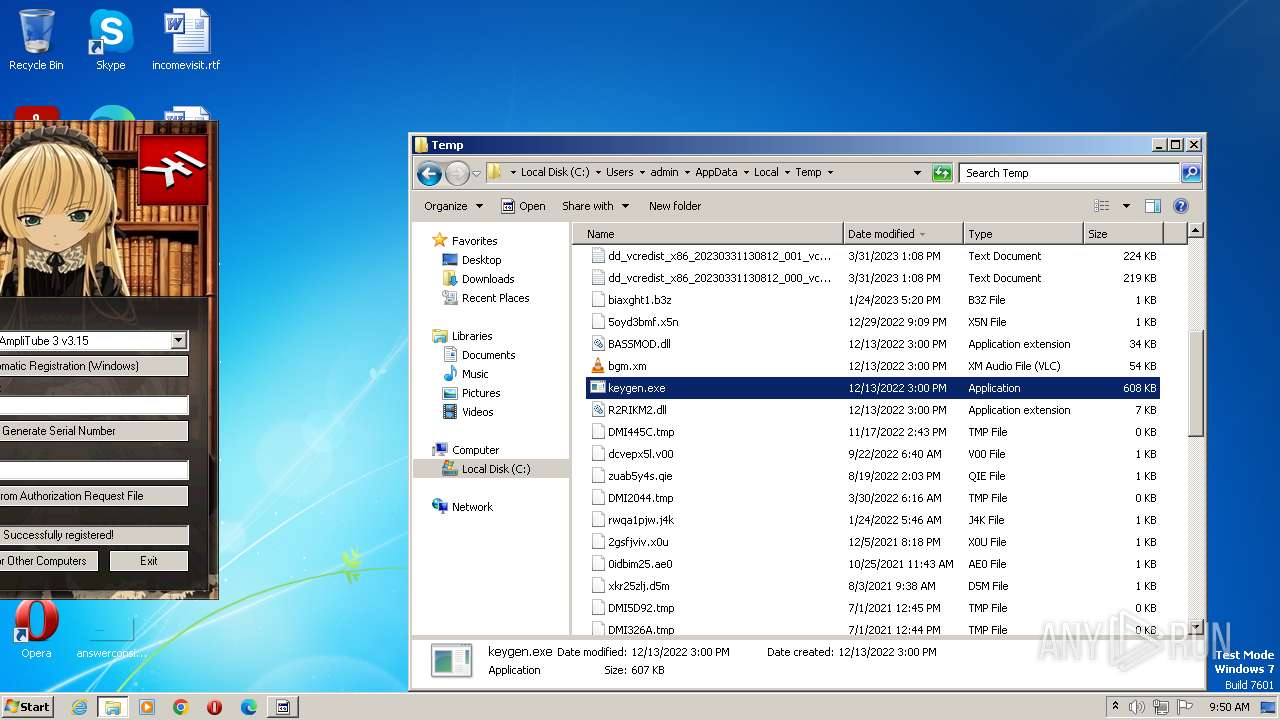
Loads dropped or rewritten executable
- keygen.exe (PID: 1208)
- keygen.exe (PID: 1028)
- keygen.exe (PID: 2424)
Application was dropped or rewritten from another process
- keygen.exe (PID: 1208)
- keygen.exe (PID: 2424)
- keygen.exe (PID: 1028)
SUSPICIOUS
Executable content was dropped or overwritten
- IK_Multimedia_Keygen.exe (PID: 2696)
INFO
Checks supported languages
- IK_Multimedia_Keygen.exe (PID: 2696)
- keygen.exe (PID: 1208)
- keygen.exe (PID: 1028)
- keygen.exe (PID: 2424)
The process checks LSA protection
- IK_Multimedia_Keygen.exe (PID: 2696)
- keygen.exe (PID: 1208)
- explorer.exe (PID: 3680)
- keygen.exe (PID: 1028)
Reads the computer name
- IK_Multimedia_Keygen.exe (PID: 2696)
- keygen.exe (PID: 1208)
- keygen.exe (PID: 1028)
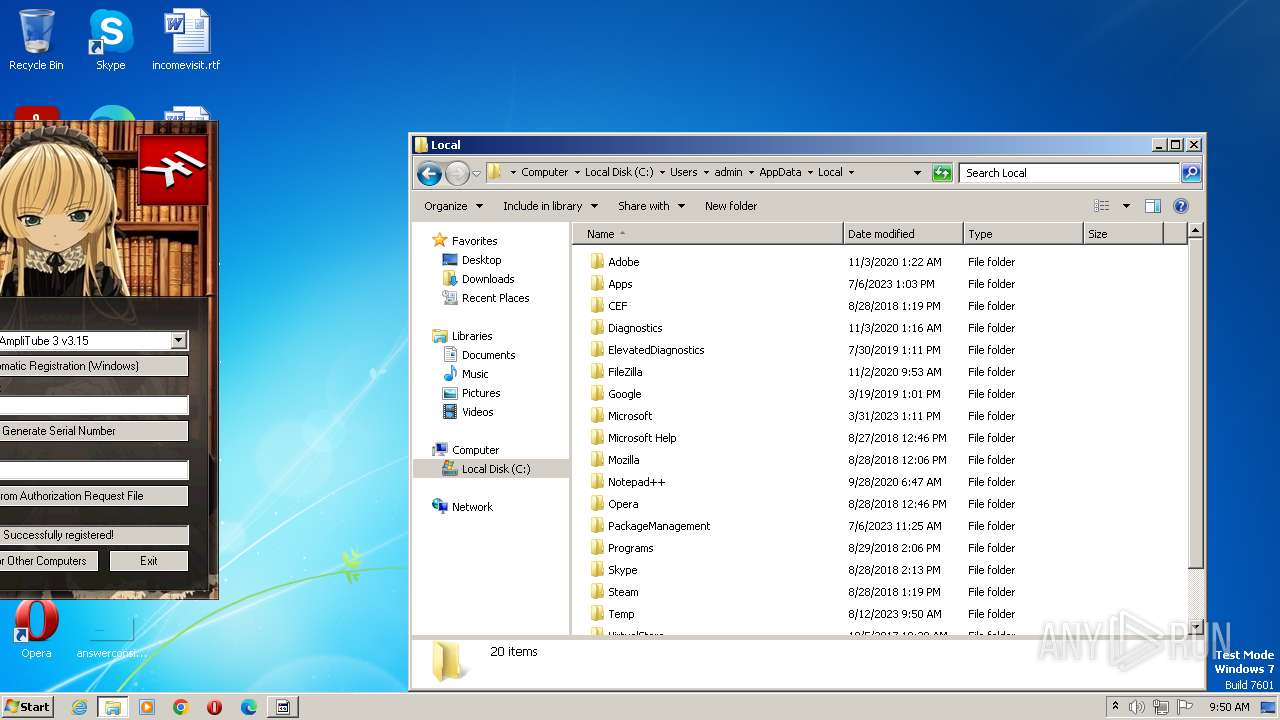
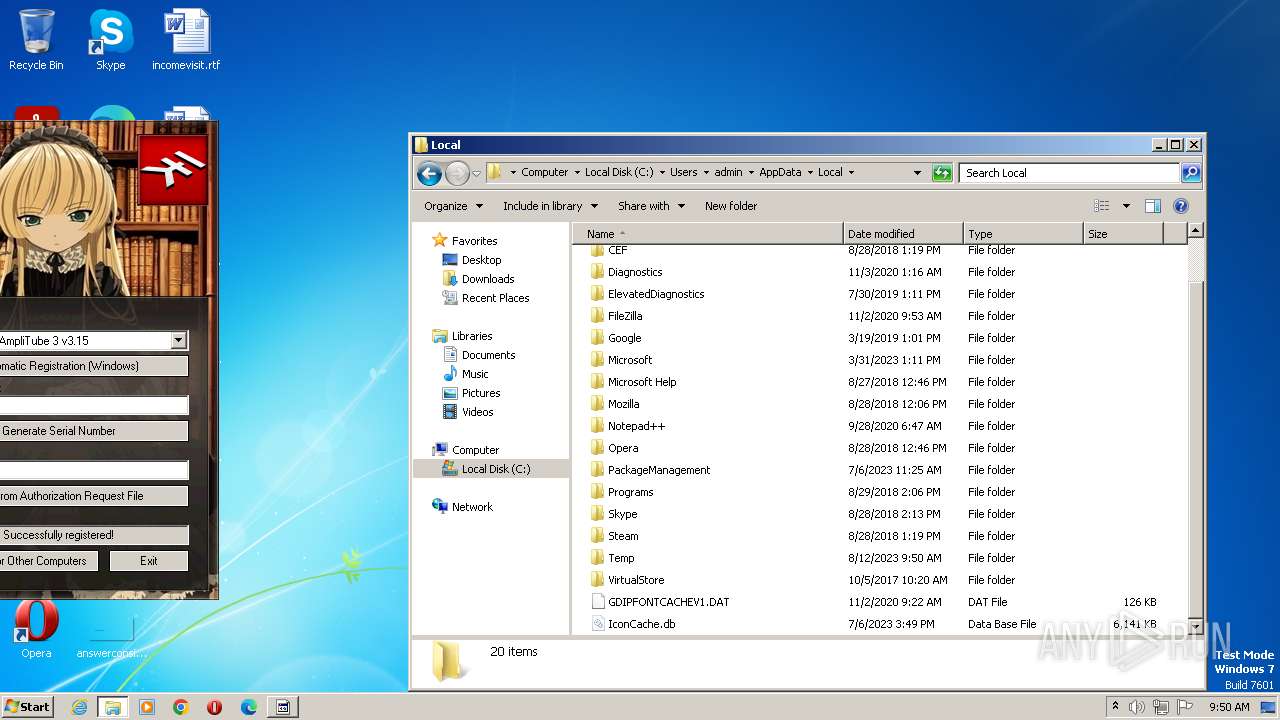
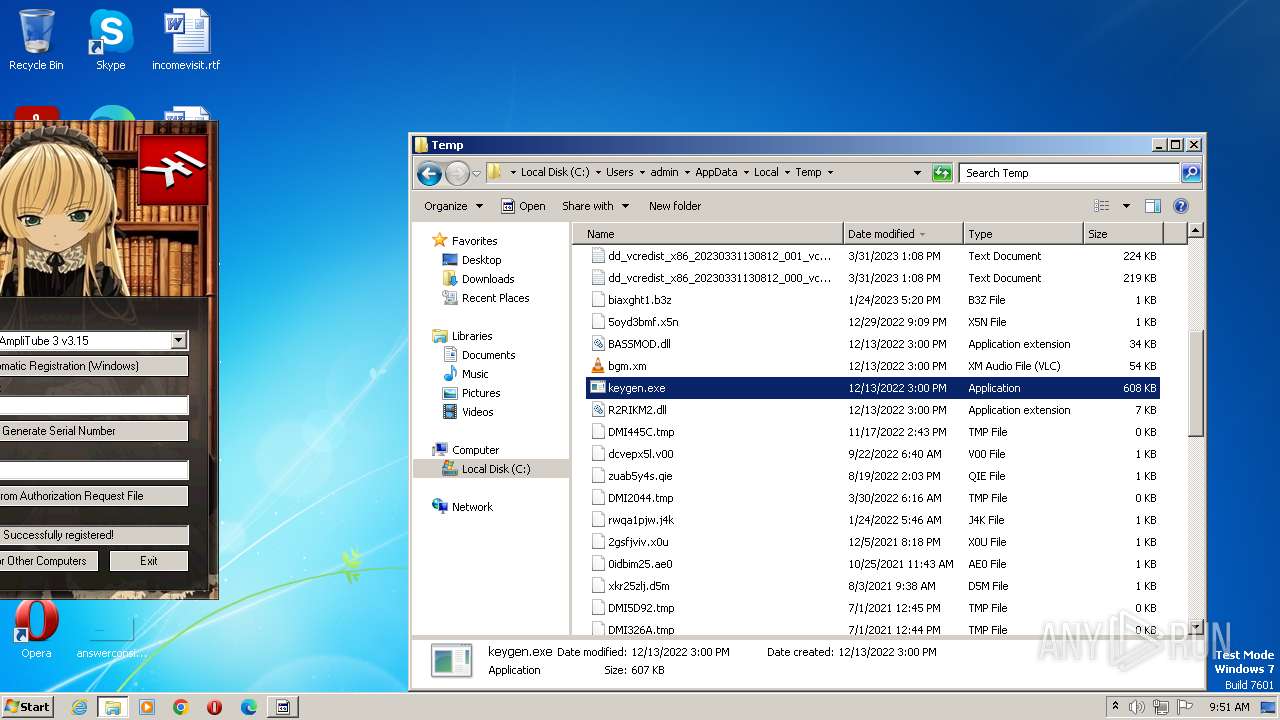
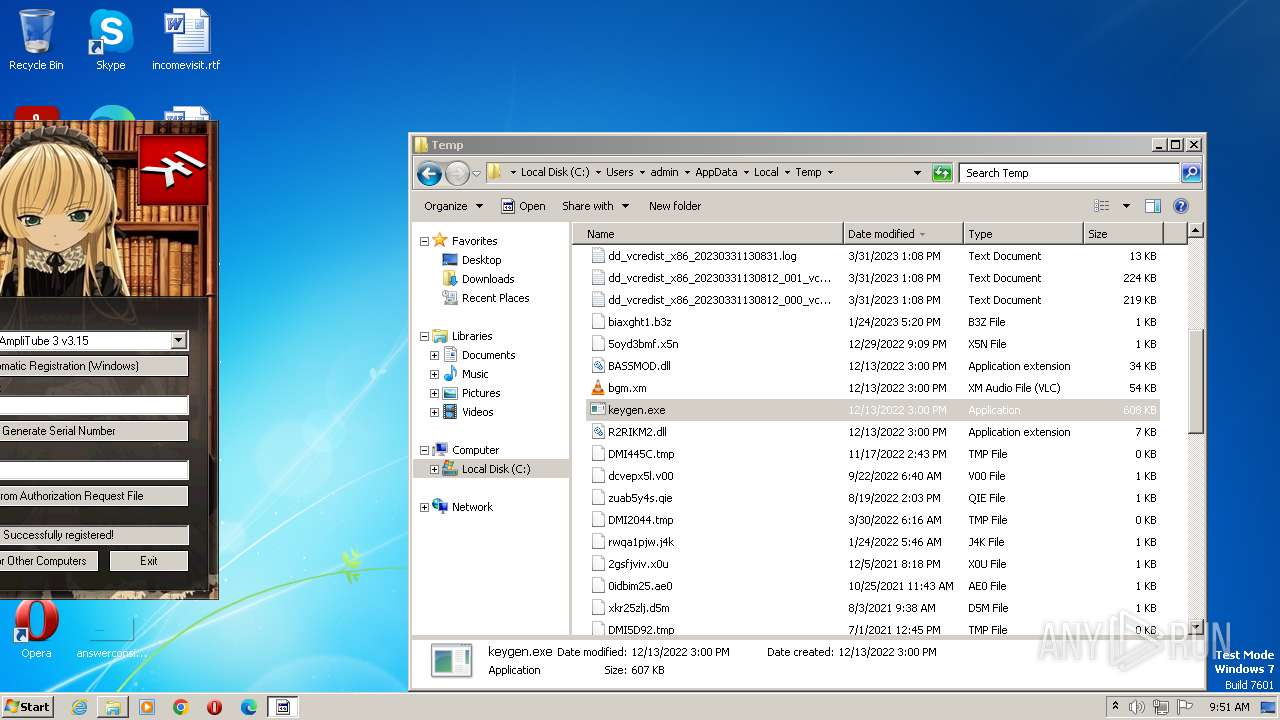
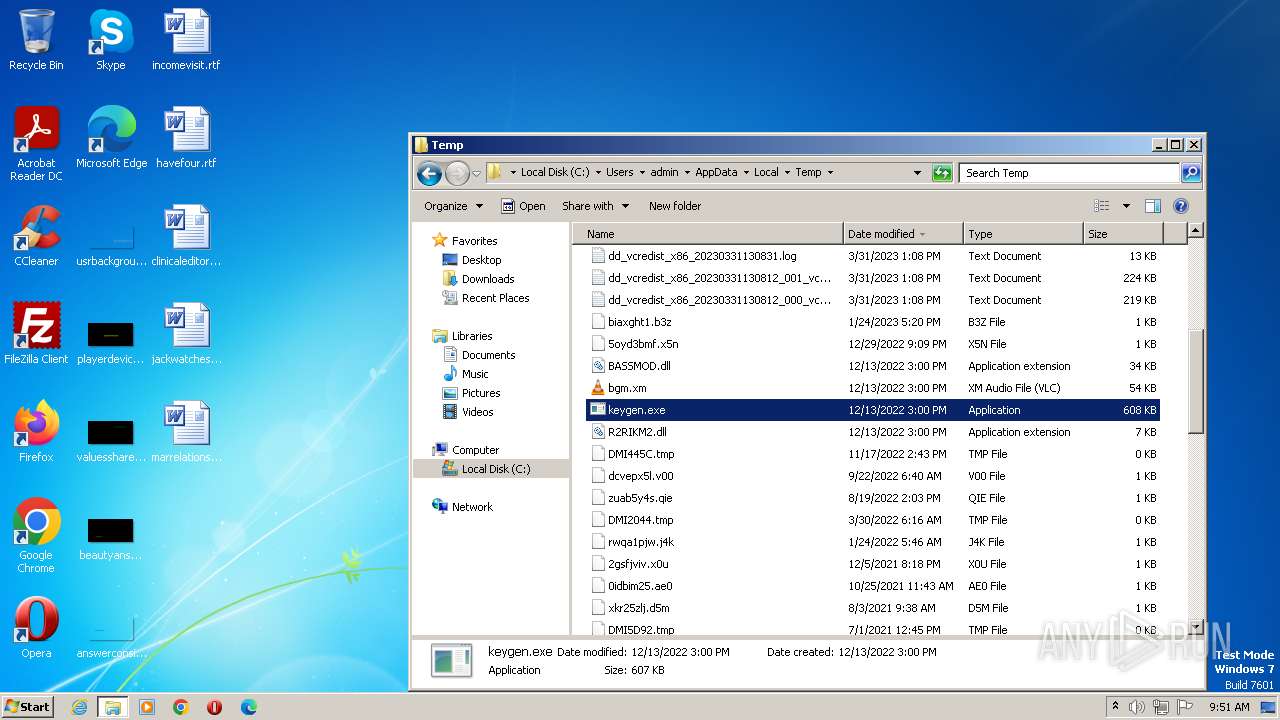
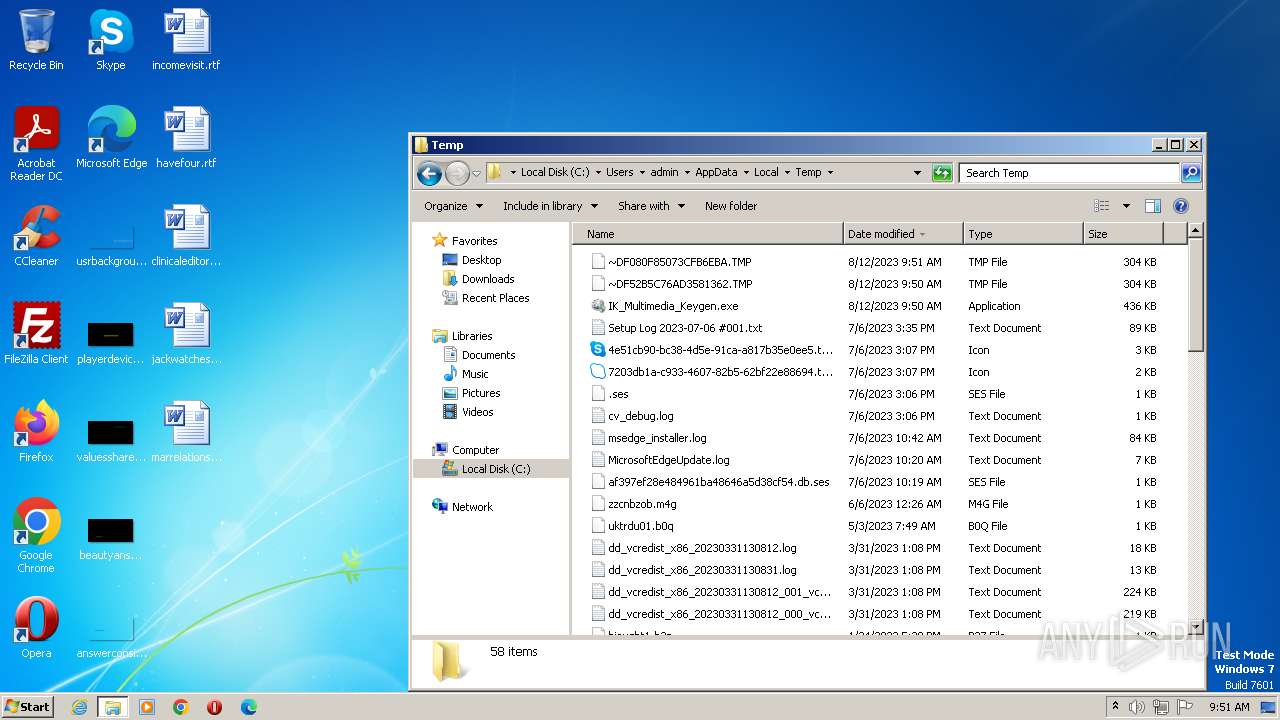
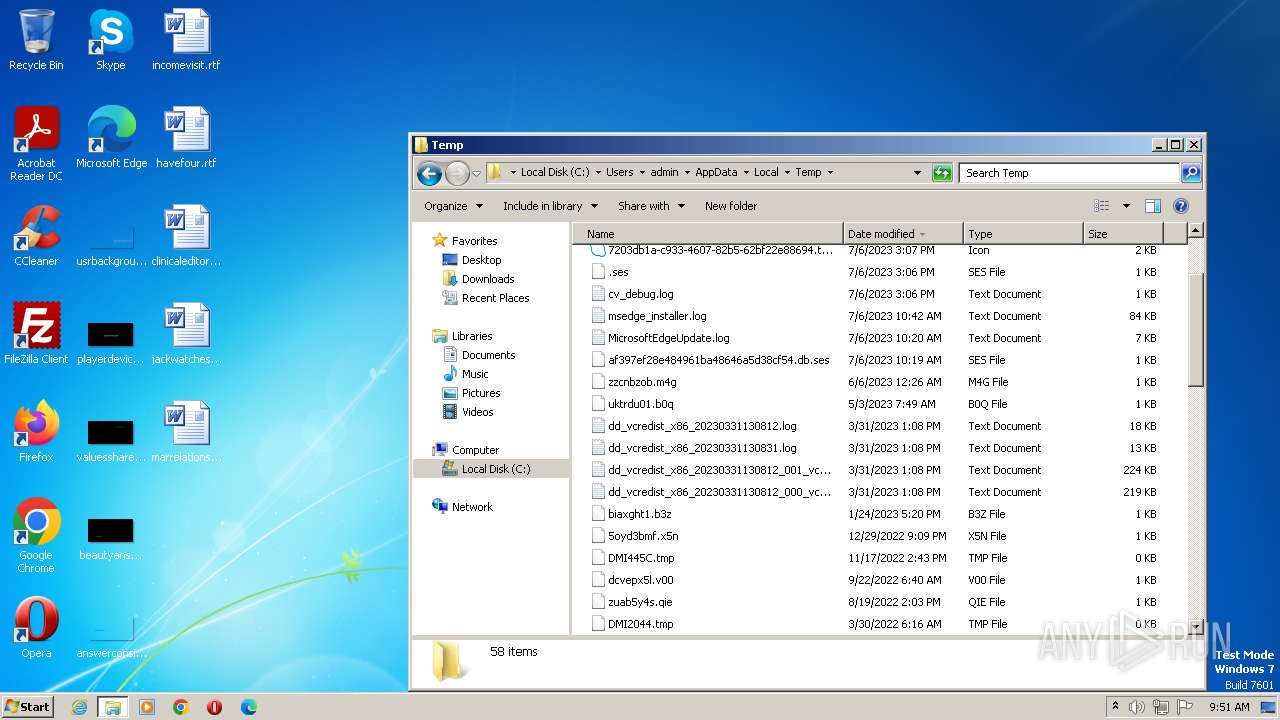
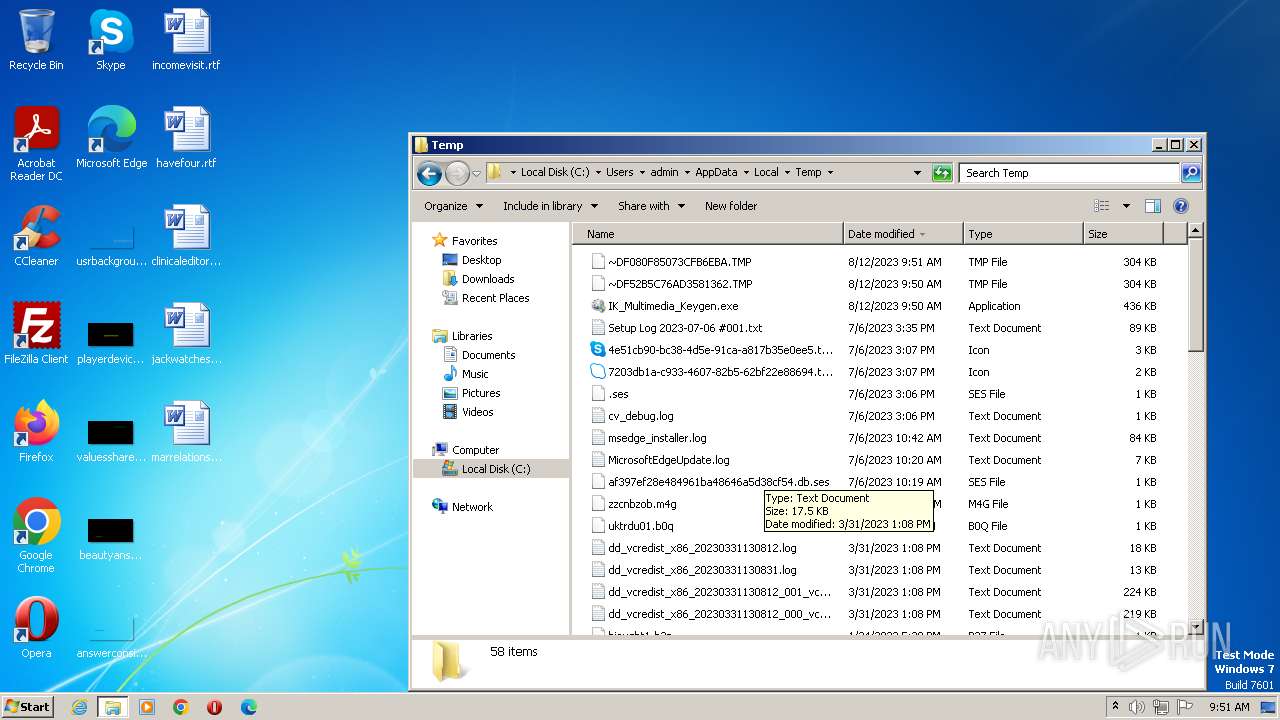
Create files in a temporary directory
- IK_Multimedia_Keygen.exe (PID: 2696)
- keygen.exe (PID: 1208)
- keygen.exe (PID: 1028)
Reads the machine GUID from the registry
- keygen.exe (PID: 1208)
- keygen.exe (PID: 1028)
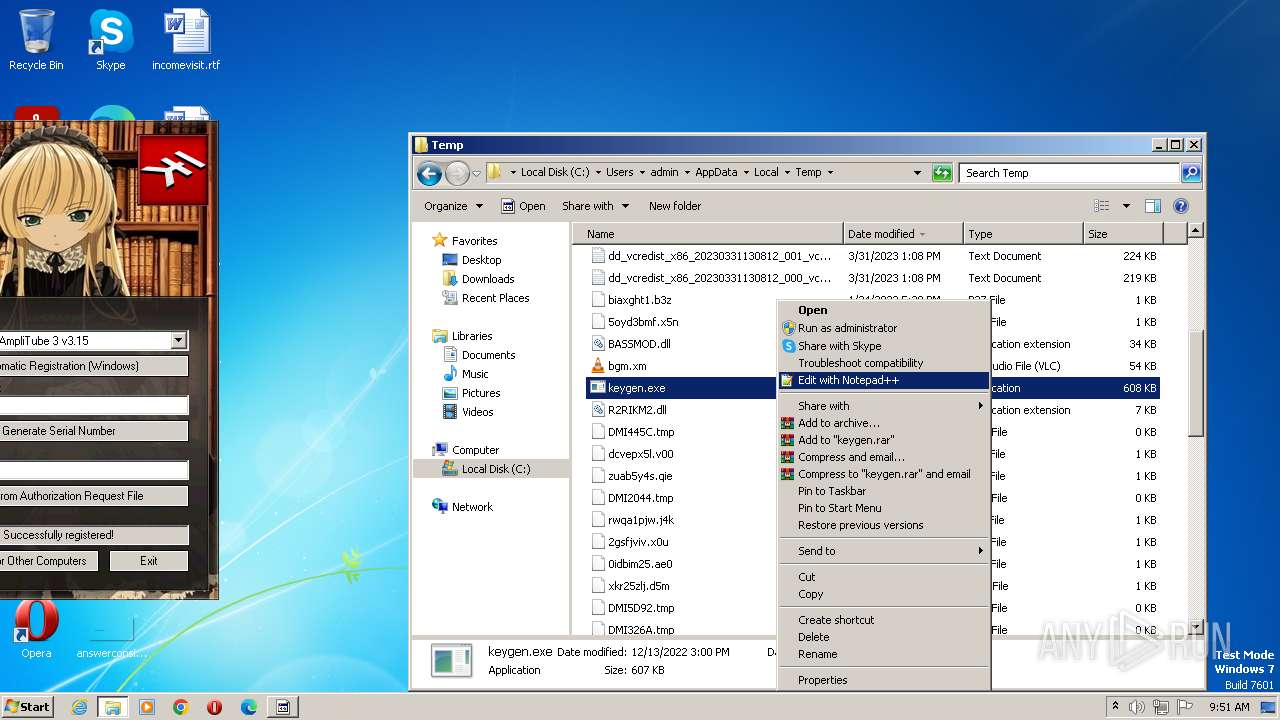
Manual execution by a user
- explorer.exe (PID: 3680)
- keygen.exe (PID: 2424)
- keygen.exe (PID: 1028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x3640 |
| UninitializedDataSize: | 2048 |
| InitializedDataSize: | 141824 |
| CodeSize: | 26624 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2021:09:25 21:56:47+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Sep-2021 21:56:47 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Sep-2021 21:56:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006676 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41746 |
.rdata | 0x00008000 | 0x0000139A | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14107 |
.data | 0x0000A000 | 0x00020378 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.11058 |
.ndata | 0x0002B000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003B000 | 0x00022910 | 0x00022A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.06472 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28747 | 841 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.92764 | 54264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.51849 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 4.75617 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 4.93004 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 5.08765 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.8213 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
47
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
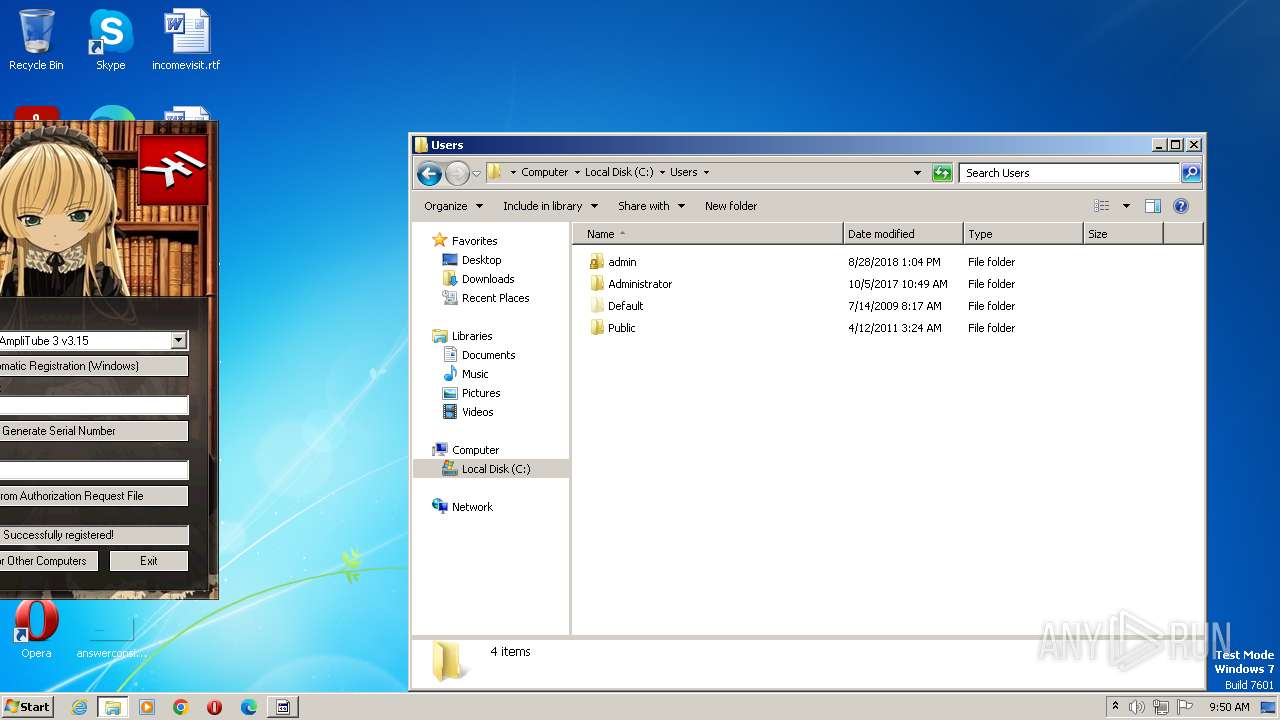
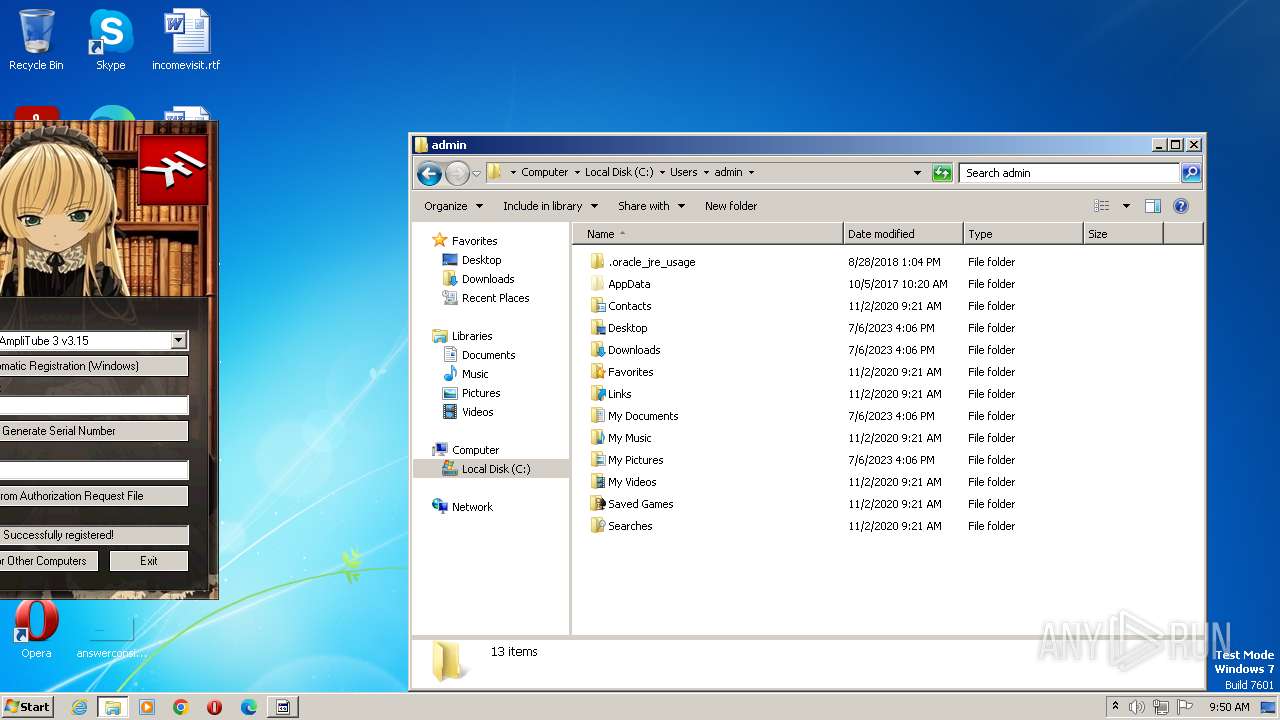
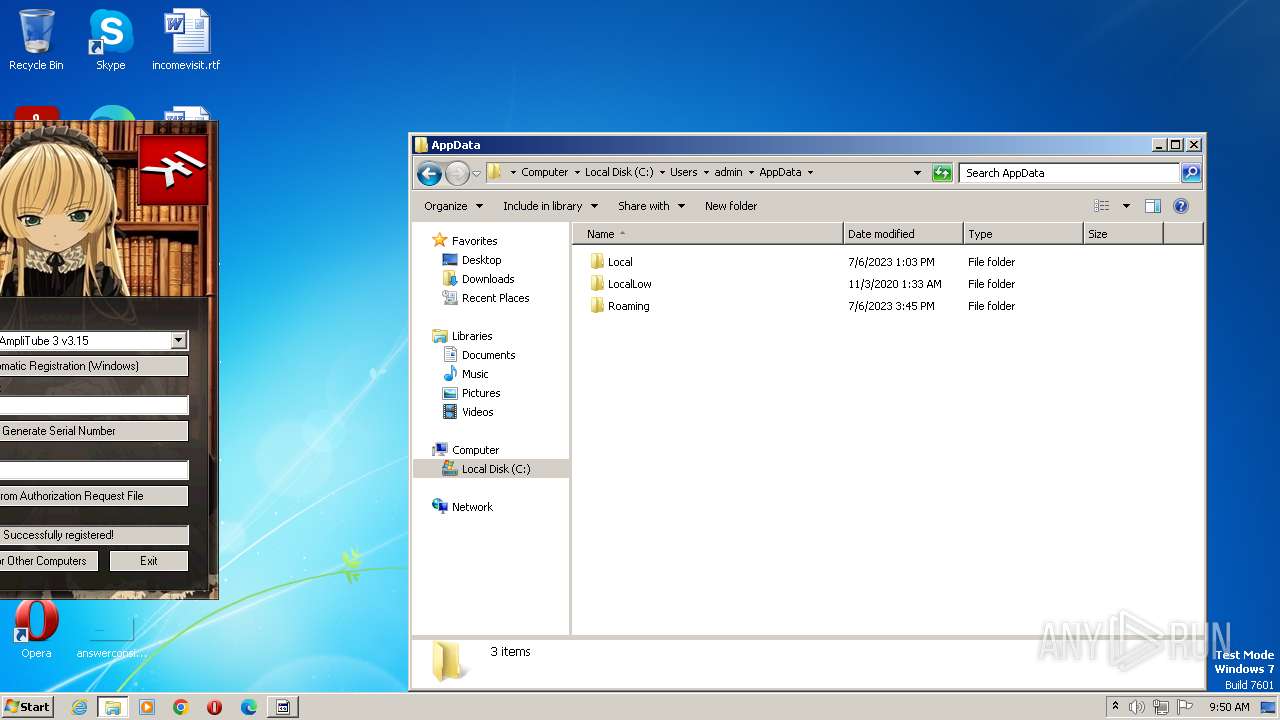
| 1028 | "C:\Users\admin\AppData\Local\Temp\keygen.exe" | C:\Users\admin\AppData\Local\Temp\keygen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1208 | C:\Users\admin\AppData\Local\Temp\keygen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | — | IK_Multimedia_Keygen.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1872 | "C:\Users\admin\AppData\Local\Temp\IK_Multimedia_Keygen.exe" | C:\Users\admin\AppData\Local\Temp\IK_Multimedia_Keygen.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2424 | "C:\Users\admin\AppData\Local\Temp\keygen.exe" | C:\Users\admin\AppData\Local\Temp\keygen.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2696 | "C:\Users\admin\AppData\Local\Temp\IK_Multimedia_Keygen.exe" | C:\Users\admin\AppData\Local\Temp\IK_Multimedia_Keygen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3680 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 877
Read events
9 605
Write events
272
Delete events
0
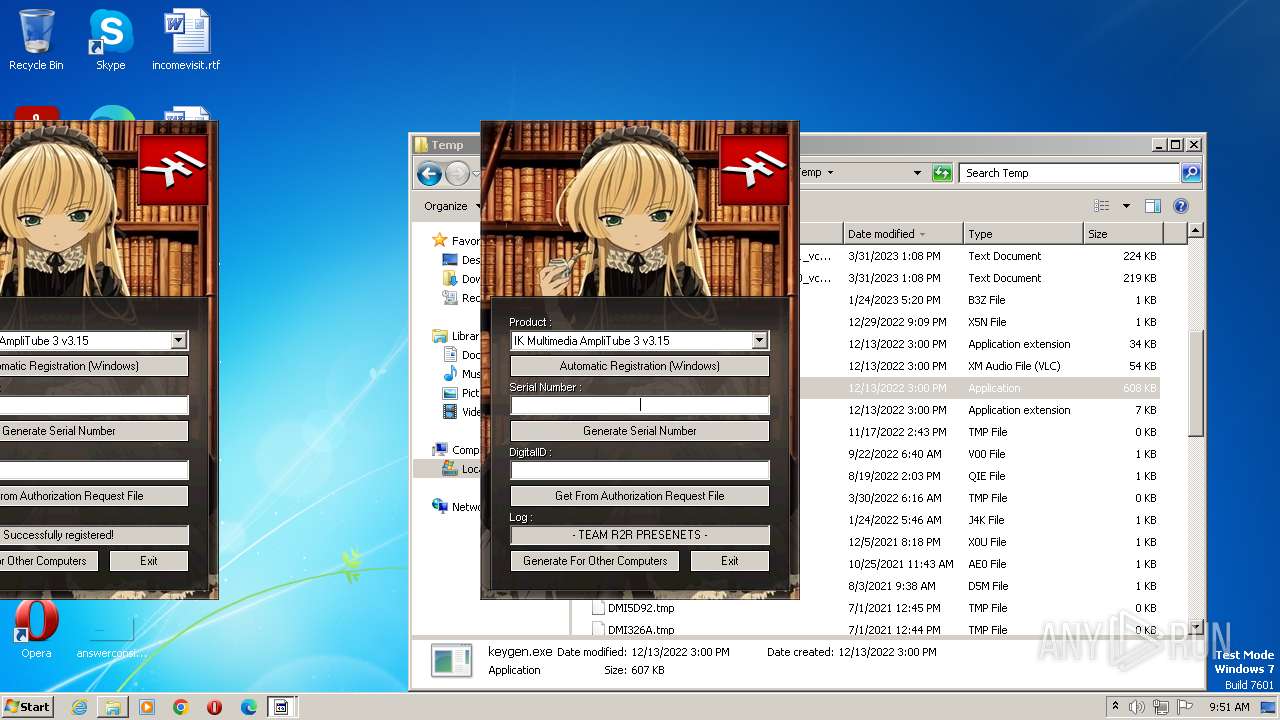
Modification events
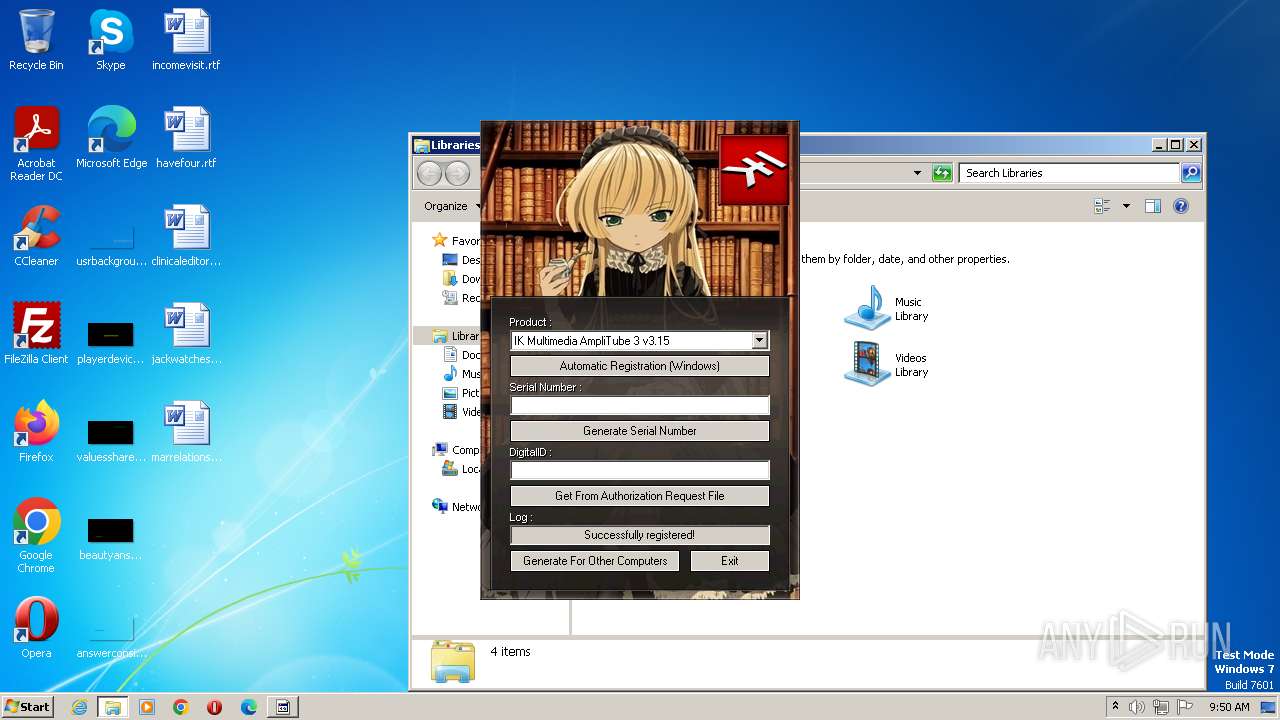
| (PID) Process: | (1208) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | SerialNumber |
Value: ACS30-38H12211-79719 | |||
| (PID) Process: | (1208) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | AuthCode |
Value: 9LA7KUP5-5MPC-V019-C1FF-FLXSECM0 | |||
| (PID) Process: | (1208) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | UserSerial |
Value: CLA10-82B11130-31702 | |||
| (PID) Process: | (1208) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | 48e7b721-d57a-4c34-813b-95d8091d5eda |
Value: 78A1096DC554AE315BD78A1F814A4C82 | |||
| (PID) Process: | (1208) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | 907ecdf1-15be-4f41-b56d-2705e7bb89ae |
Value: 2DEE5B313EEF294221D0D39E39AD439D | |||
| (PID) Process: | (1208) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | 96b57f95-4380-444a-8c0a-fbcc9bef1dd9 |
Value: 1E3727551D9E70A90270DC9E5B7A38F6 | |||
| (PID) Process: | (1208) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | 58dbec22-58e0-464c-8c04-91fb9d9973e2 |
Value: 0C2D59620AEF2C06B45C905C43A109E9 | |||
| (PID) Process: | (1208) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | 305c9b6b-04cf-4673-b58a-e62afb4fefcb |
Value: 30F949B0F52FAE55A95F5E8047DB018F | |||
| (PID) Process: | (1208) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | 510f6d25-6ec4-417b-bf58-0f8028209cce |
Value: 2CA369D8E5BCCC70BEDA4C6ABF040E80 | |||
| (PID) Process: | (1208) keygen.exe | Key: | HKEY_CURRENT_USER\Software\IK Multimedia\AmpliTube 3 |
| Operation: | write | Name: | 395ed825-f3e8-40c1-8d69-34d8b23c9100 |
Value: 0258B4DDD6B5CF8999A35FFBF1F7AE48 | |||
Executable files
3
Suspicious files
2
Text files
0
Unknown types
0
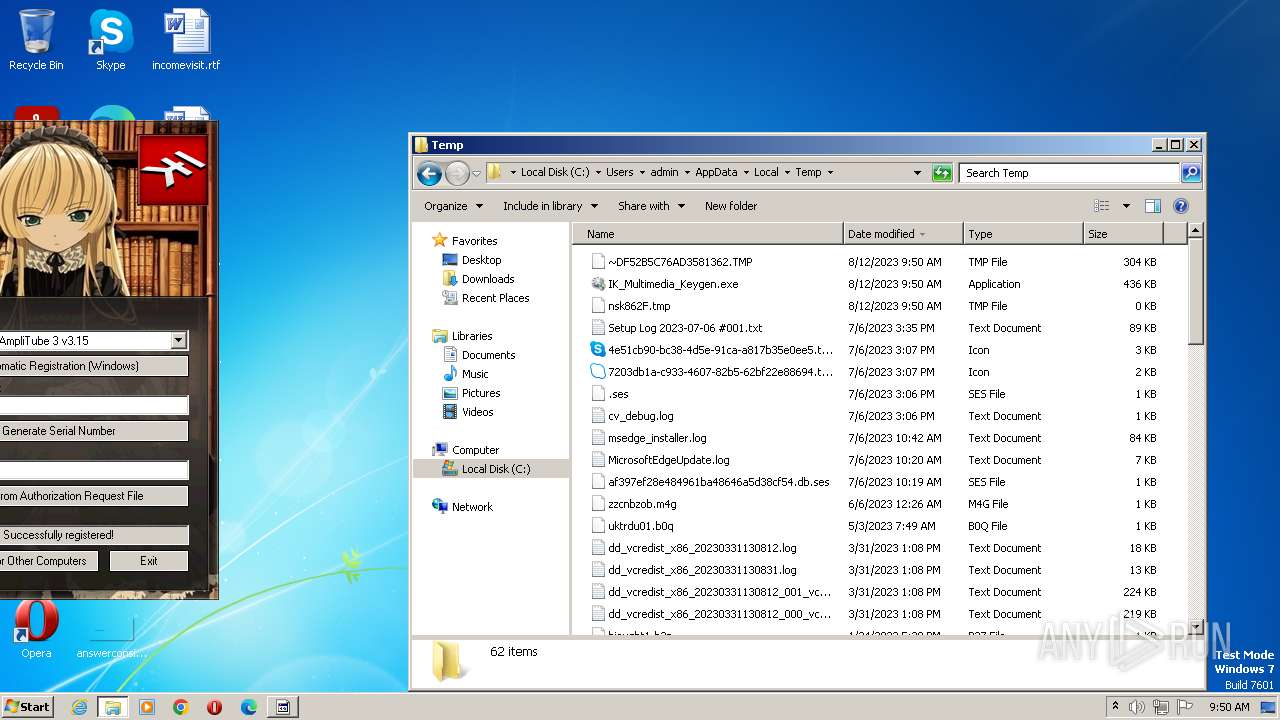
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2696 | IK_Multimedia_Keygen.exe | C:\Users\admin\AppData\Local\Temp\bgm.xm | binary | |
MD5:A30878984AF33EE69ACE5CF8E330B974 | SHA256:498EADC5B3D65AAF34B8496954C3362F033297C489D7EF4559CBA8890C530171 | |||
| 2696 | IK_Multimedia_Keygen.exe | C:\Users\admin\AppData\Local\Temp\R2RIKM2.dll | executable | |
MD5:D6B65AB5773E227E8E880CBAA8513304 | SHA256:34AFB8018F77CA1C3F0ADCCEADF04E6FA3DA1BD2FE728F358D896E33C652ADB8 | |||
| 2696 | IK_Multimedia_Keygen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | executable | |
MD5:8C31C0F0EBBB44F4561D53A82408DE90 | SHA256:35F40DE16025CE17291F23CB4056C685399B4C4A30CF95ECEBBDC2D6E3E7C058 | |||
| 2696 | IK_Multimedia_Keygen.exe | C:\Users\admin\AppData\Local\Temp\BASSMOD.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
| 1028 | keygen.exe | C:\Users\admin\AppData\Local\Temp\~DF080F85073CFB6EBA.TMP | binary | |
MD5:59707E31C48220E185E8F6C3FD5626AC | SHA256:BDEA437F00F17E4050DFCE638680F845EDA37788909979604B9EF2C7EC258381 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report