| File name: | drw_trial.exe |
| Full analysis: | https://app.any.run/tasks/b8d2e2c6-6a52-480d-bc31-43cd004f8013 |
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2019, 05:39:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B1C0BB58FF955EA05D3F0D4144D52695 |
| SHA1: | F14D50264F96F8D8F458771C2C9151F492FD28DC |
| SHA256: | 7952E217B9BDC176B1C924FB05BD75D7285F049FB698C1079A4F446CD37B6451 |
| SSDEEP: | 393216:PJraaoOmJLibdJAIXlIybsKCxK6KVl85NgOdbIlH5AWGPTGOTqxmA:PJr1pmsfAaIybsKCk6y8XgrlH5fOTqxm |
MALICIOUS
Application was dropped or rewritten from another process
- DRW.exe (PID: 3836)
- DRWUI.exe (PID: 3360)
Loads dropped or rewritten executable
- DRW.exe (PID: 3836)
- DRWUI.exe (PID: 3360)
SUSPICIOUS
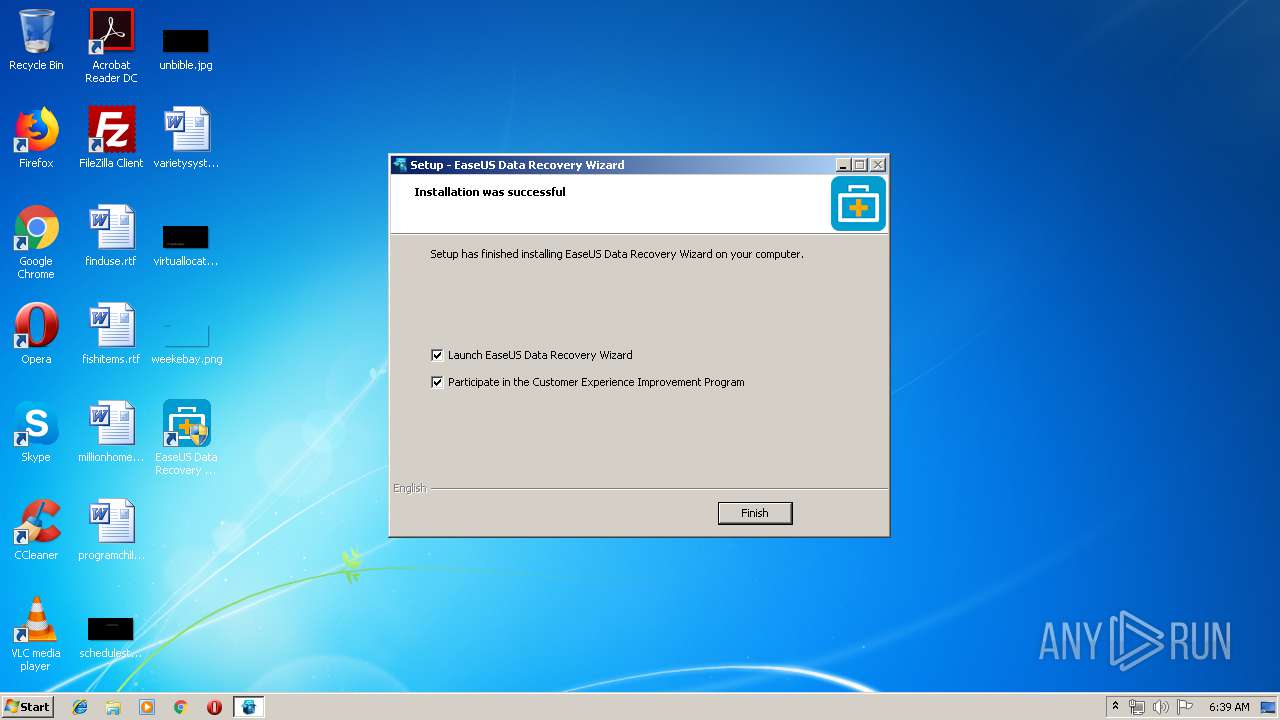
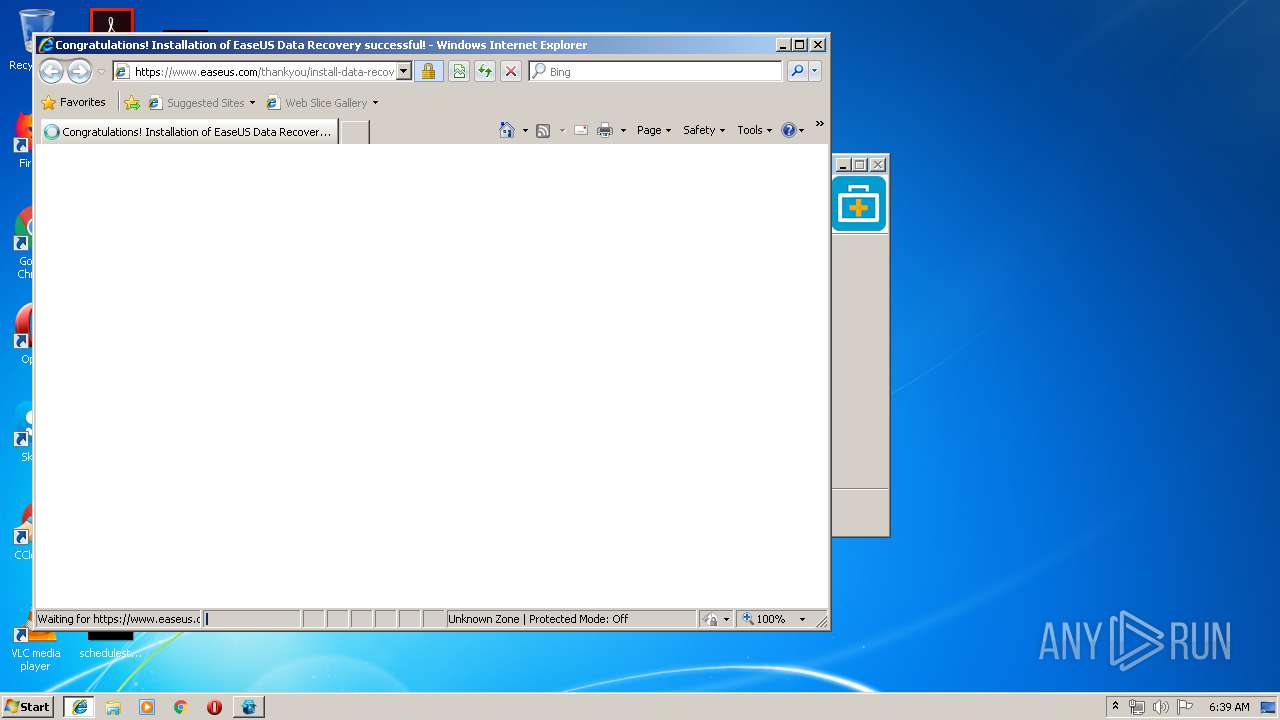
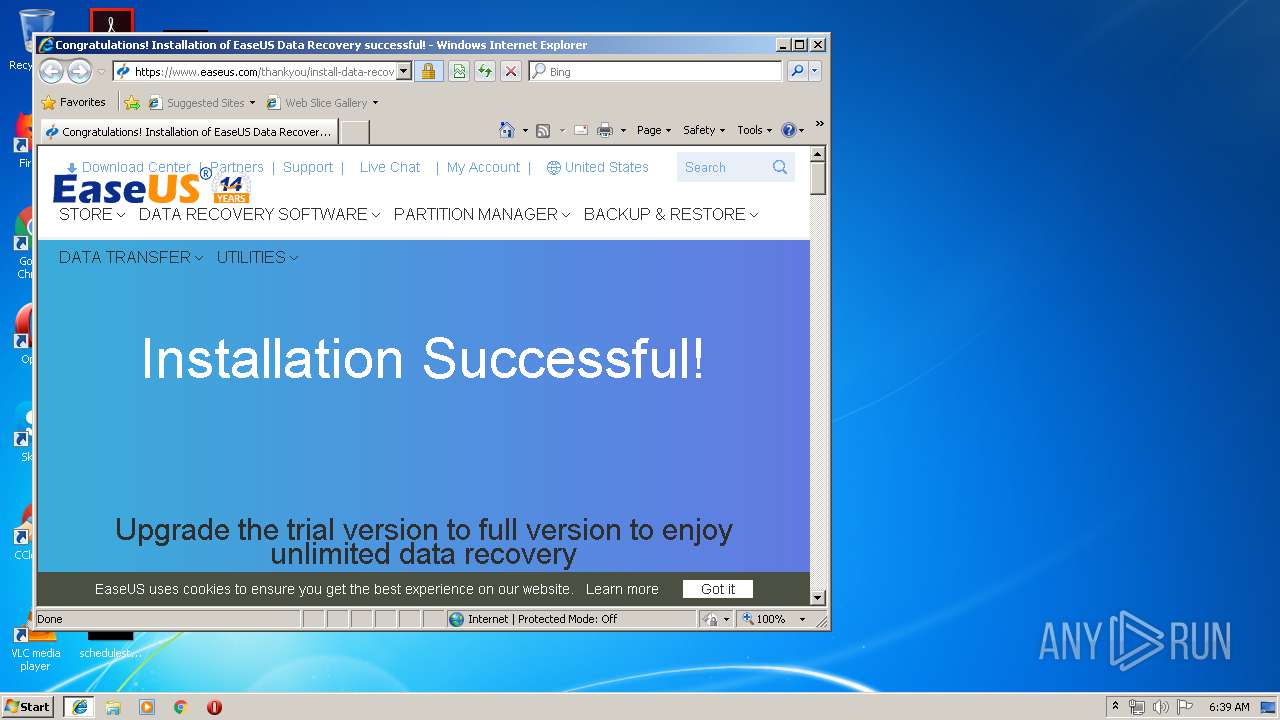
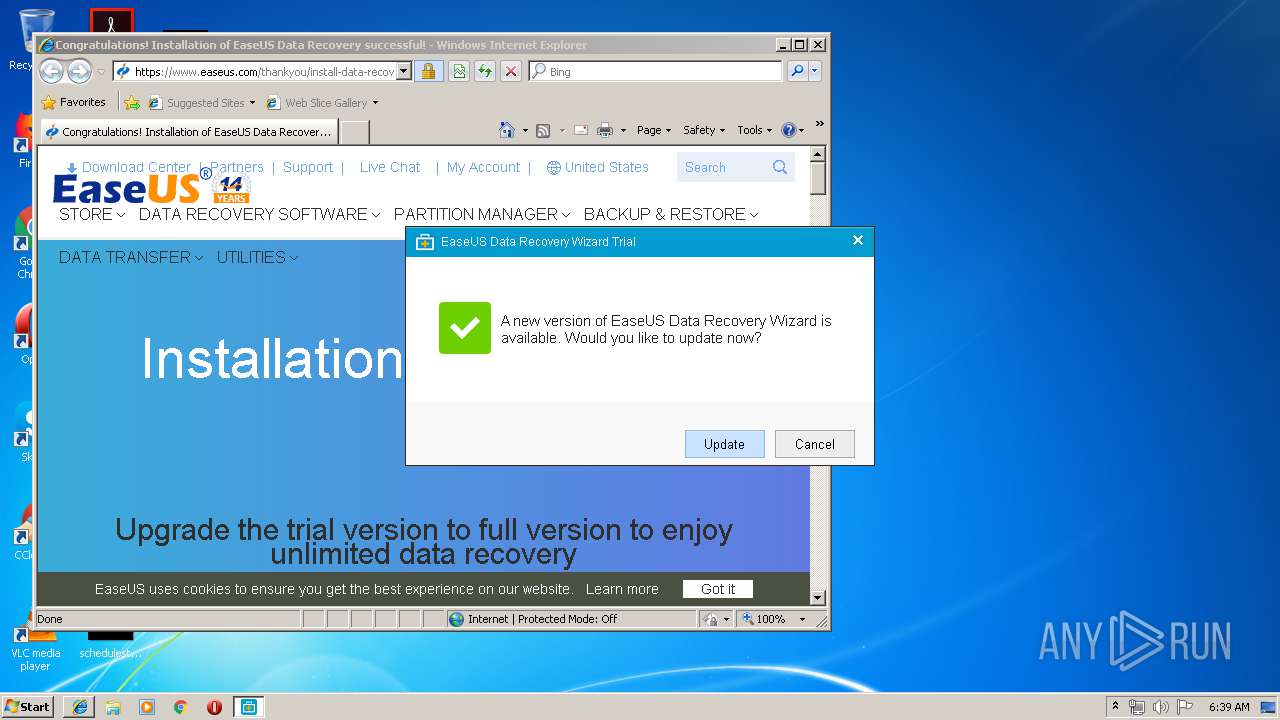
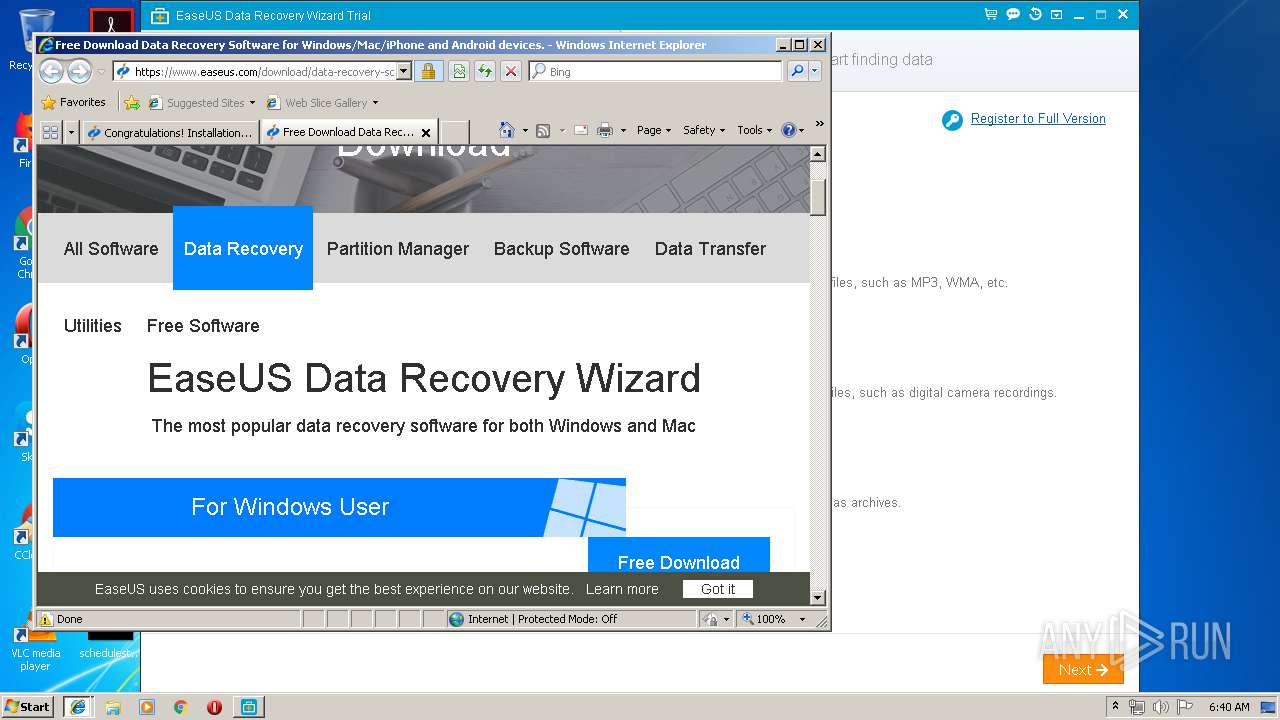
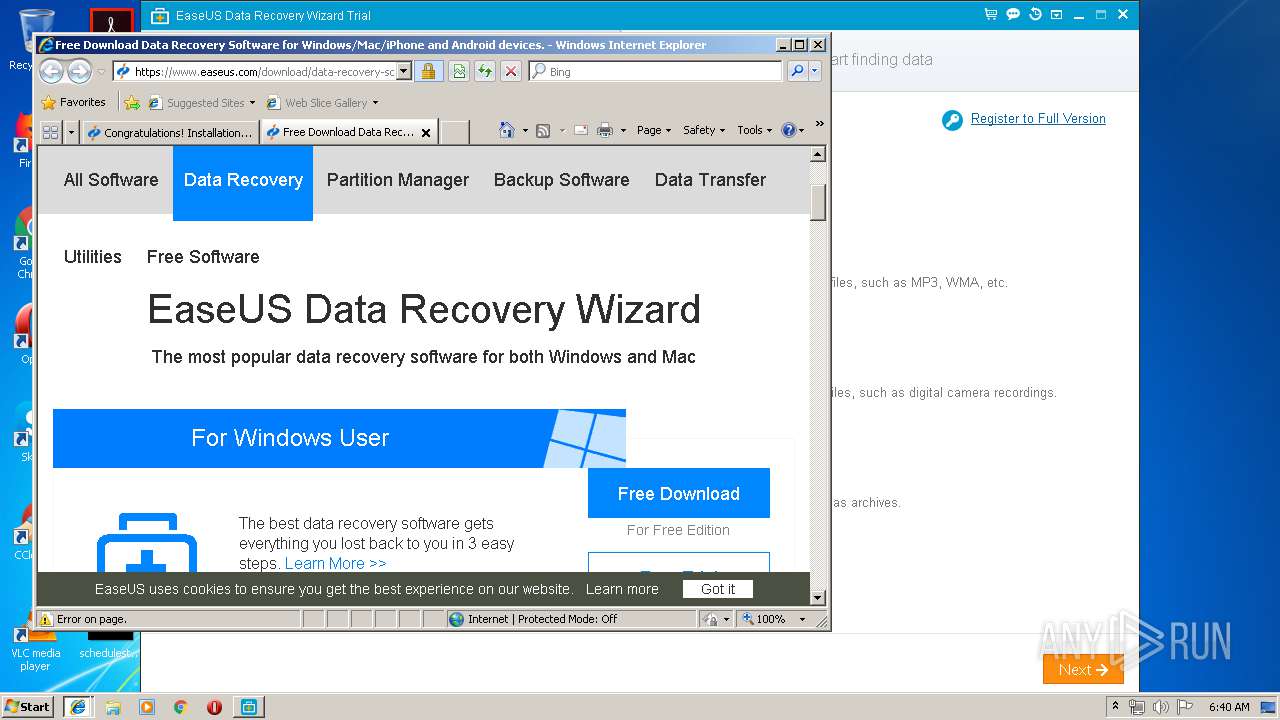
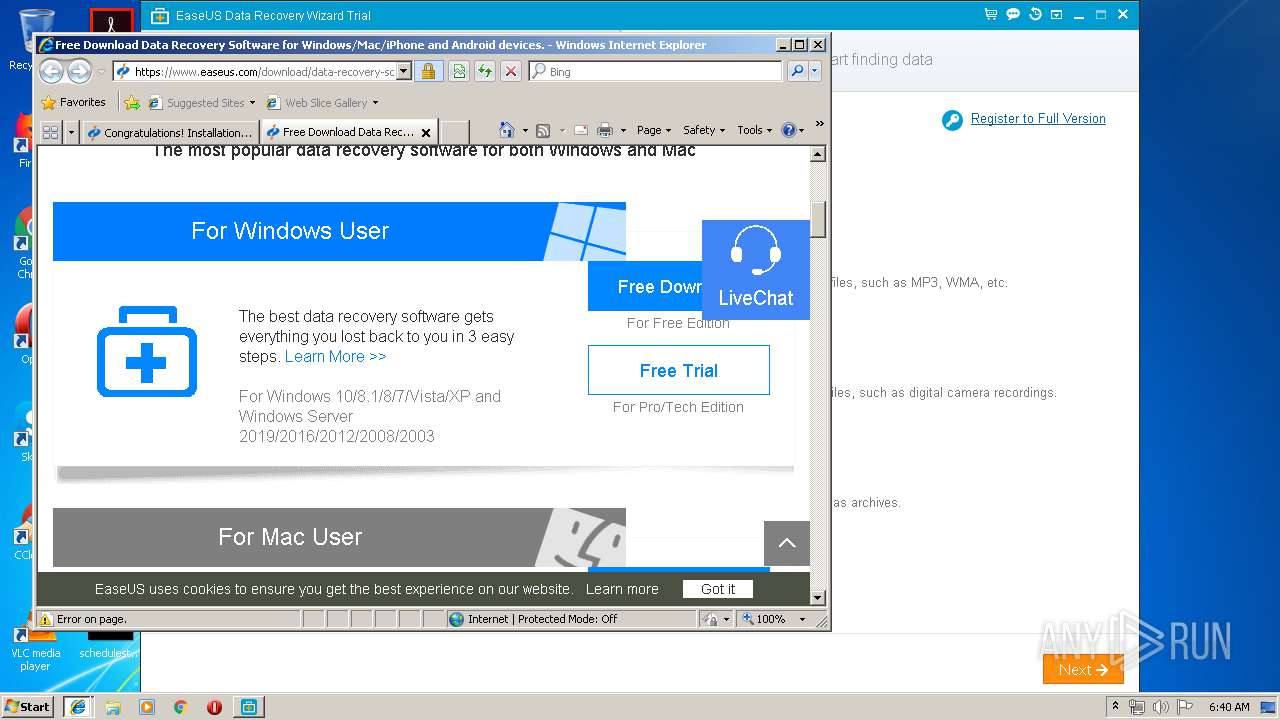
Starts Internet Explorer
- drw_trial.tmp (PID: 3324)
Creates files in the user directory
- drw_trial.tmp (PID: 3324)
Executable content was dropped or overwritten
- drw_trial.tmp (PID: 3324)
- drw_trial.exe (PID: 2280)
Reads the Windows organization settings
- drw_trial.tmp (PID: 3324)
Reads Windows owner or organization settings
- drw_trial.tmp (PID: 3324)
Creates files in the program directory
- DRW.exe (PID: 3836)
- DRWUI.exe (PID: 3360)
Low-level read access rights to disk partition
- DRWUI.exe (PID: 3360)
INFO
Loads dropped or rewritten executable
- drw_trial.tmp (PID: 3324)
Application launched itself
- iexplore.exe (PID: 2876)
Creates a software uninstall entry
- drw_trial.tmp (PID: 3324)
Changes settings of System certificates
- iexplore.exe (PID: 1576)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1576)
Changes internet zones settings
- iexplore.exe (PID: 2876)
Creates files in the user directory
- iexplore.exe (PID: 1576)
- iexplore.exe (PID: 2268)
Reads internet explorer settings
- iexplore.exe (PID: 1576)
- iexplore.exe (PID: 2268)
Reads Internet Cache Settings
- iexplore.exe (PID: 2876)
- iexplore.exe (PID: 1576)
Application was dropped or rewritten from another process
- drw_trial.tmp (PID: 3324)
Creates files in the program directory
- drw_trial.tmp (PID: 3324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:01:15 09:22:50+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 65024 |
| InitializedDataSize: | 480768 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x113bc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
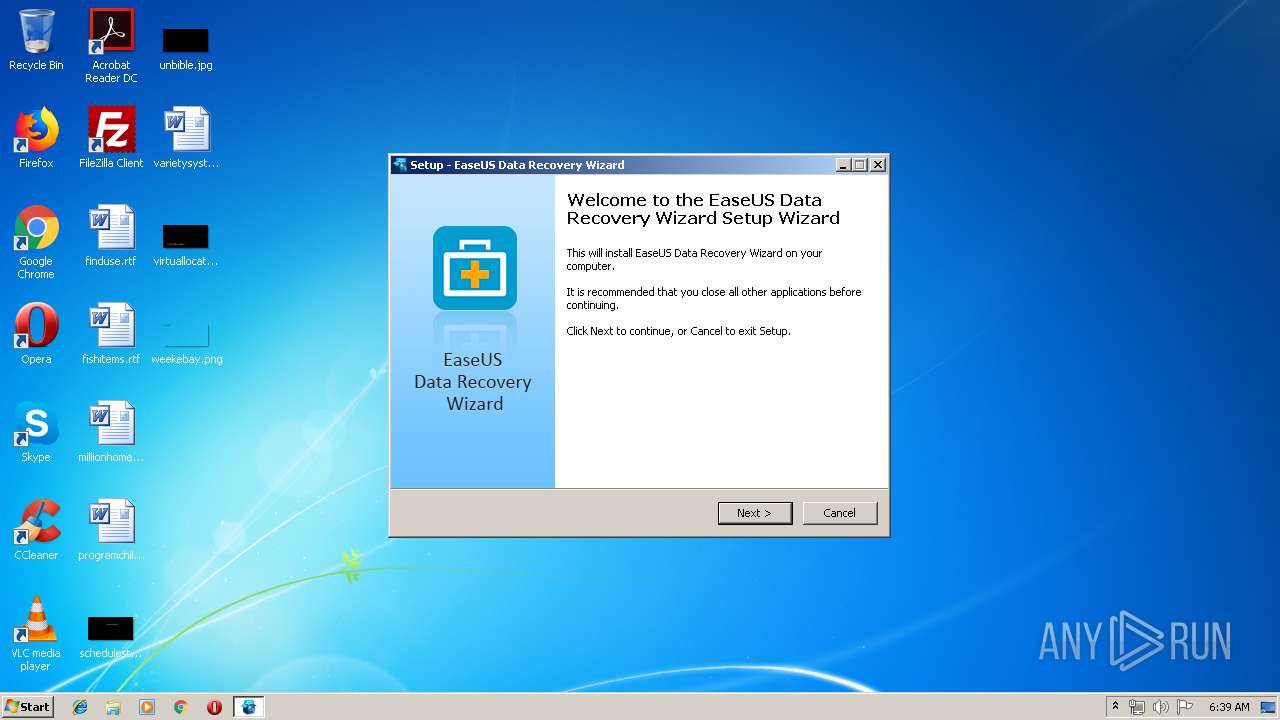
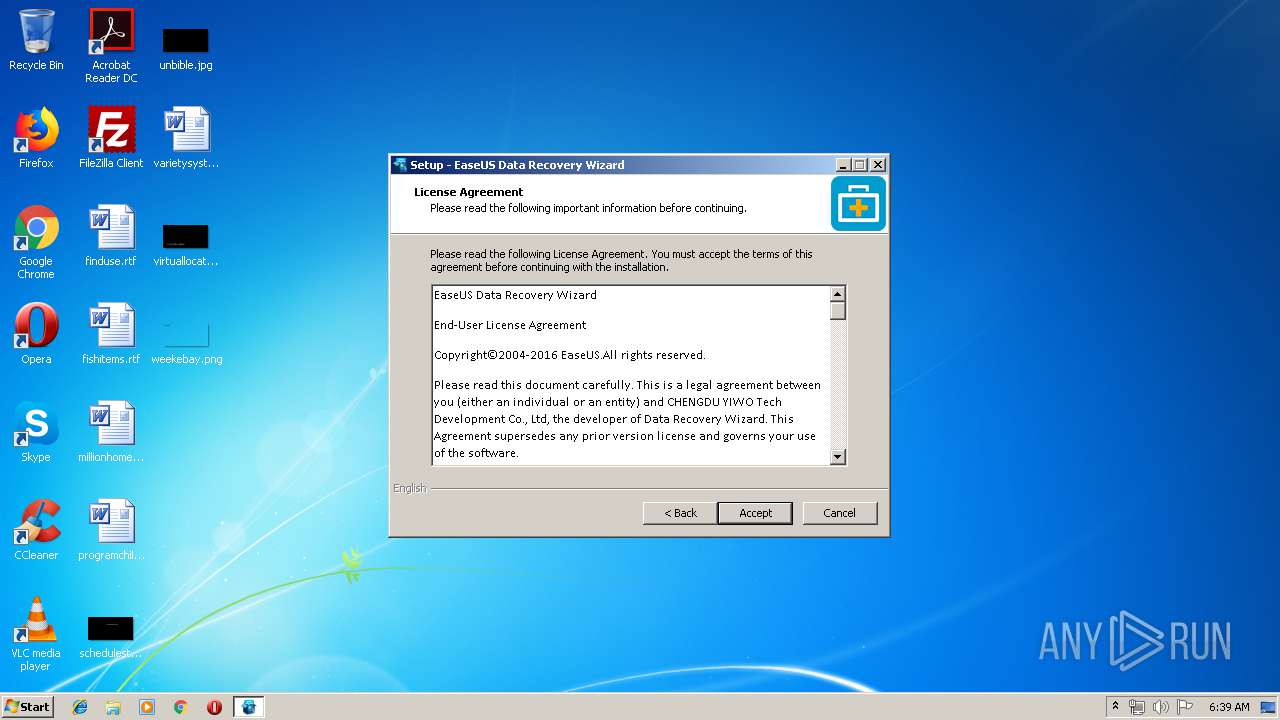
| CompanyName: | EaseUS |
| FileDescription: | EaseUS Data Recovery Wizard Setup |
| FileVersion: | |
| LegalCopyright: | Copyright (c) 2004-2016 EaseUS.ALL RIGHTS RESERVED. |
| ProductName: | EaseUS Data Recovery Wizard |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jan-2016 08:22:50 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | EaseUS |
| FileDescription: | EaseUS Data Recovery Wizard Setup |
| FileVersion: | - |
| LegalCopyright: | Copyright (c) 2004-2016 EaseUS.ALL RIGHTS RESERVED. |
| ProductName: | EaseUS Data Recovery Wizard |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 15-Jan-2016 08:22:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F134 | 0x0000F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39169 |
.itext | 0x00011000 | 0x00000B44 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.74305 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.24753 |
.bss | 0x00013000 | 0x000056B8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000DD0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97188 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00073778 | 0x00073800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.32805 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.15171 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.31372 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.56653 | 38056 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.52145 | 21640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.495 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.73355 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.76413 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.94844 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.82342 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
45
Monitored processes
8
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1576 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2876 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2876 CREDAT:14339 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2280 | "C:\Users\admin\AppData\Local\Temp\drw_trial.exe" | C:\Users\admin\AppData\Local\Temp\drw_trial.exe | explorer.exe | ||||||||||||
User: admin Company: EaseUS Integrity Level: HIGH Description: EaseUS Data Recovery Wizard Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | drw_trial.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
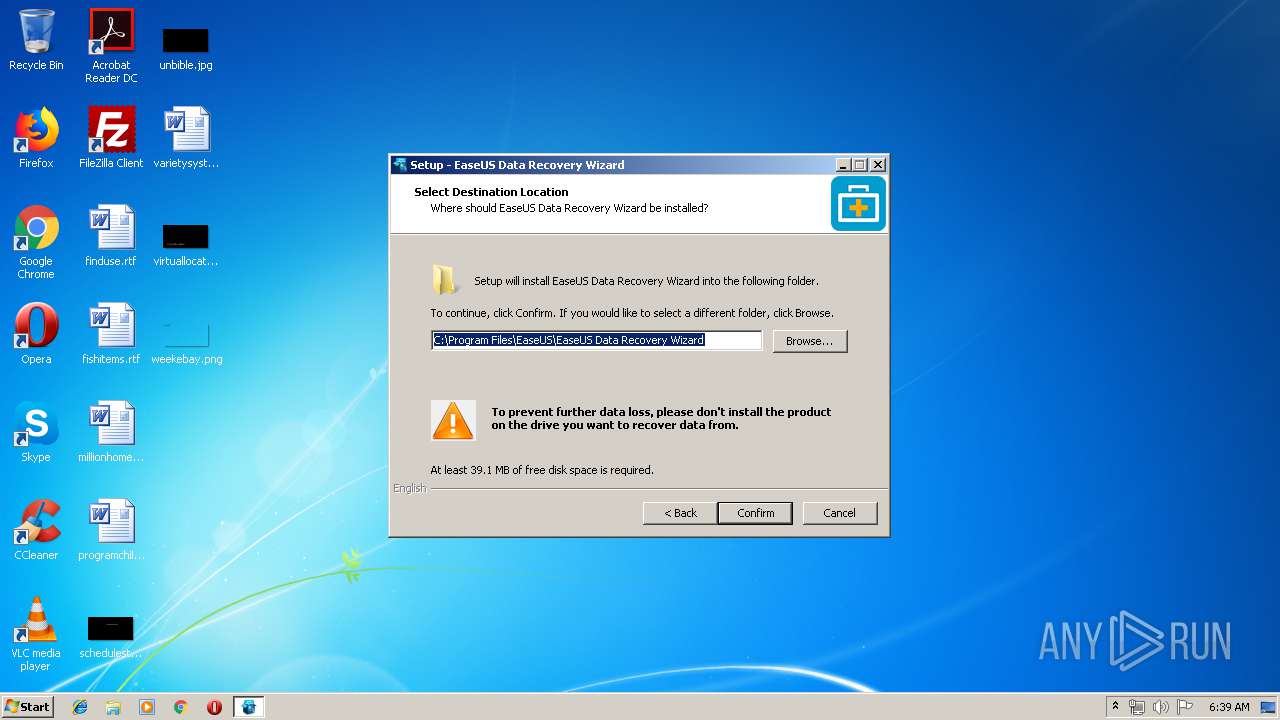
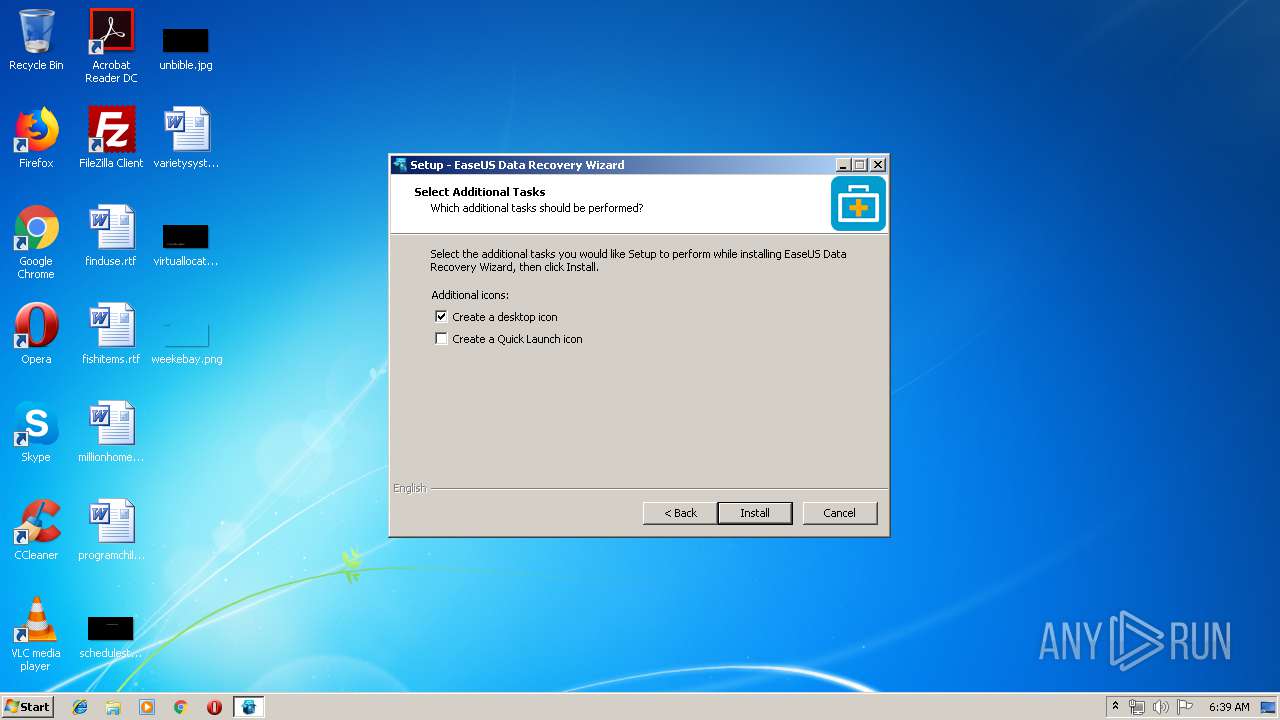
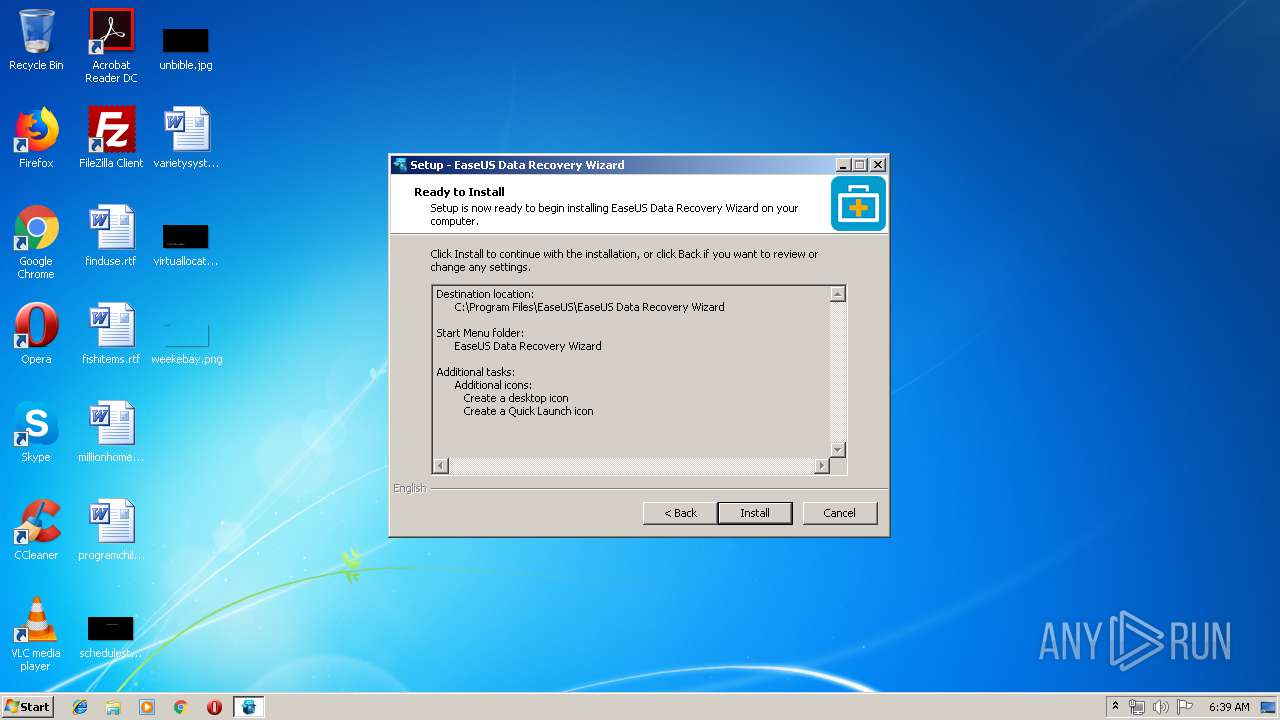
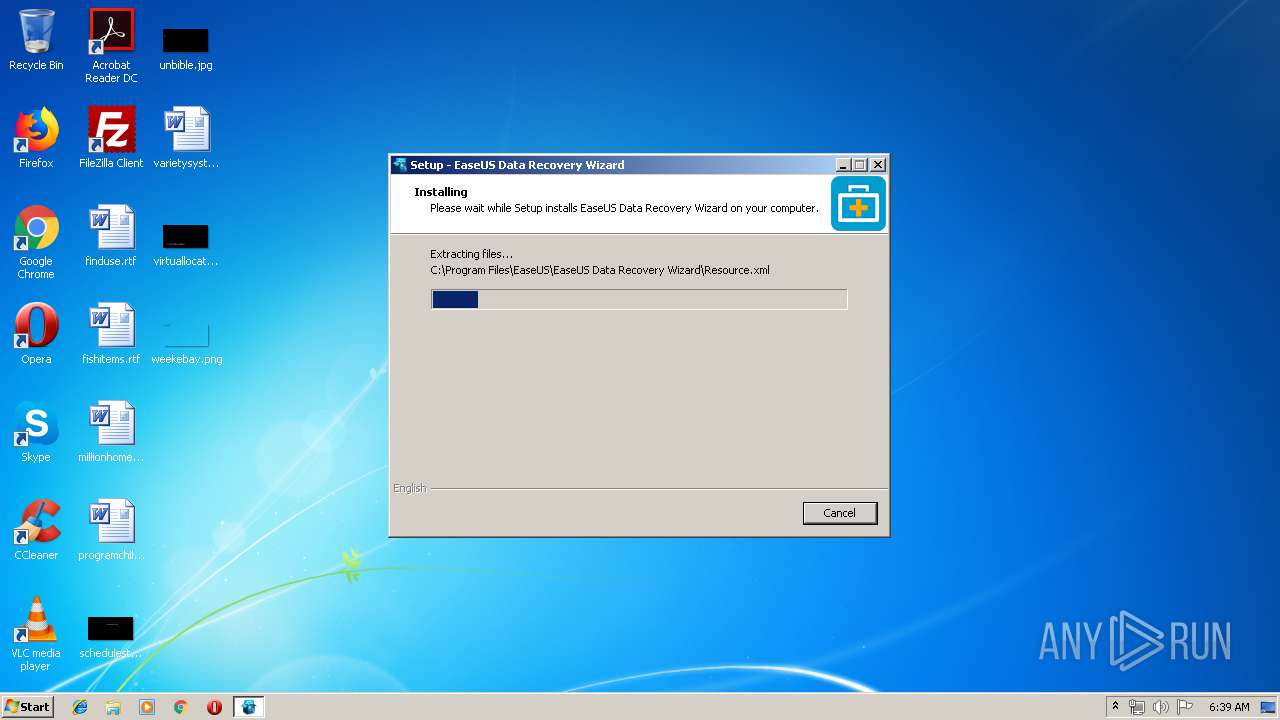
| 3324 | "C:\Users\admin\AppData\Local\Temp\is-45ARP.tmp\drw_trial.tmp" /SL5="$70158,15032751,546816,C:\Users\admin\AppData\Local\Temp\drw_trial.exe" | C:\Users\admin\AppData\Local\Temp\is-45ARP.tmp\drw_trial.tmp | drw_trial.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3360 | DRWUI | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\DRWUI.exe | DRW.exe | ||||||||||||
User: admin Company: CHENGDU YIWO Tech Development Co., Ltd Integrity Level: HIGH Description: EaseUS Data Recovery Wizard Exit code: 0 Version: 10, 2, 0 Modules
| |||||||||||||||
| 3480 | "C:\Users\admin\AppData\Local\Temp\drw_trial.exe" | C:\Users\admin\AppData\Local\Temp\drw_trial.exe | — | explorer.exe | |||||||||||
User: admin Company: EaseUS Integrity Level: MEDIUM Description: EaseUS Data Recovery Wizard Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
| 3836 | "C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\DRW.exe" | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\DRW.exe | — | drw_trial.tmp | |||||||||||
User: admin Company: CHENGDU YIWO Tech Development Co., Ltd Integrity Level: HIGH Description: EaseUS Data Recovery Wizard Exit code: 0 Version: 9.0.0 Modules
| |||||||||||||||
Total events
964
Read events
778
Write events
179
Delete events
7
Modification events
| (PID) Process: | (3324) drw_trial.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: FC0C0000E606F304CF24D501 | |||
| (PID) Process: | (3324) drw_trial.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 7541F4839D4EEE24E7D5BC91A8E640B54FCBA067DC1B6E2B924361F02F61FD0C | |||
| (PID) Process: | (3324) drw_trial.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3324) drw_trial.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\OfficeViewer.exe | |||
| (PID) Process: | (3324) drw_trial.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 79A4D2D9BA424991A70163CB6C7096D9D2689B02ABC35F30196BB5B4262F9832 | |||
| (PID) Process: | (3324) drw_trial.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\EASEUS\DRW\StartupCheck |
| Operation: | write | Name: | NotNeedCheck |
Value: 0 | |||
| (PID) Process: | (3324) drw_trial.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\EASEUS\DRW\Language |
| Operation: | write | Name: | Language |
Value: English.data | |||
| (PID) Process: | (3324) drw_trial.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\EASEUS\DRW\LanguageNum |
| Operation: | write | Name: | LanguageNum |
Value: 0 | |||
| (PID) Process: | (3324) drw_trial.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\EASEUS\EaseUS Data Recovery Wizard |
| Operation: | write | Name: | UpdateUrl |
Value: http://www.easeus.com/update/drw_eng/drw.ini | |||
| (PID) Process: | (3324) drw_trial.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\EASEUS\EaseUS Data Recovery Wizard |
| Operation: | write | Name: | SetUpPathName |
Value: C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\DRW.exe | |||
Executable files
34
Suspicious files
2
Text files
198
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3324 | drw_trial.tmp | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\is-FJQIO.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | drw_trial.tmp | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\is-LBG98.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | drw_trial.tmp | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\is-UUUFT.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | drw_trial.tmp | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\is-BFM0F.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | drw_trial.tmp | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\is-C85VI.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | drw_trial.tmp | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\is-5F1O7.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | drw_trial.tmp | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\is-BKG5Q.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | drw_trial.tmp | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\is-CPI4V.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | drw_trial.tmp | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\is-77590.tmp | — | |
MD5:— | SHA256:— | |||
| 3324 | drw_trial.tmp | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\is-80R6D.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
43
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
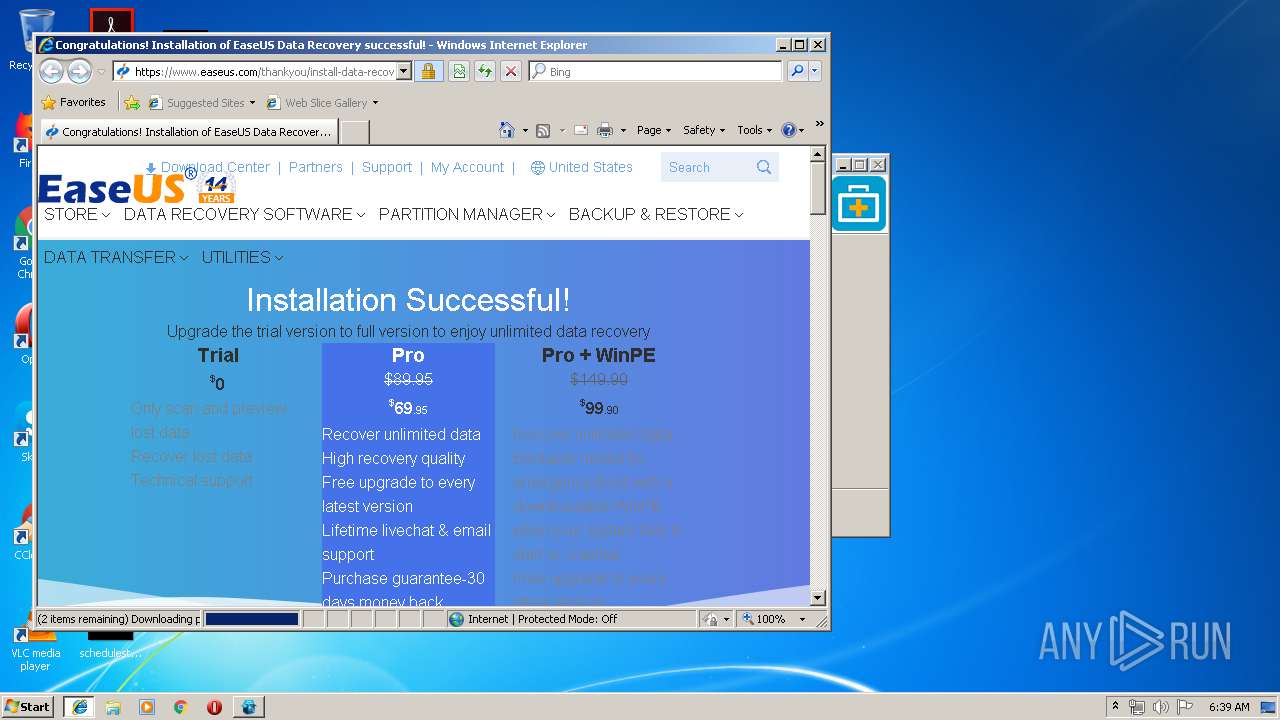
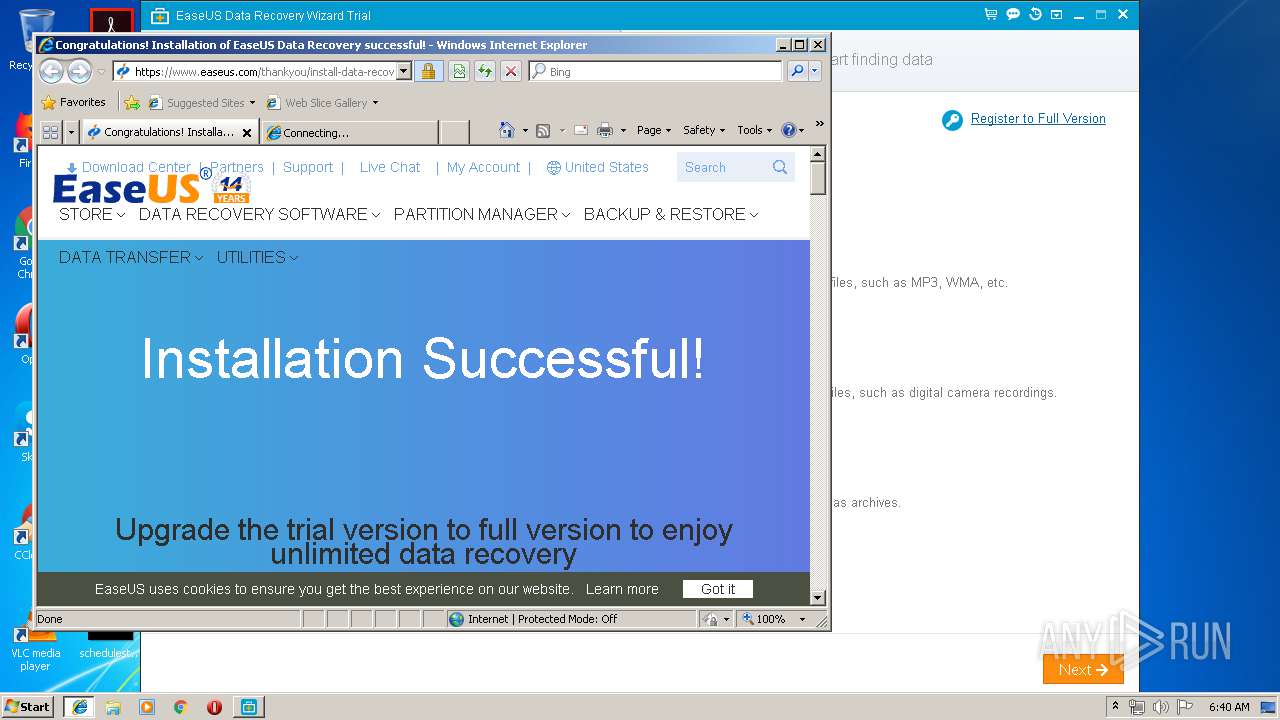
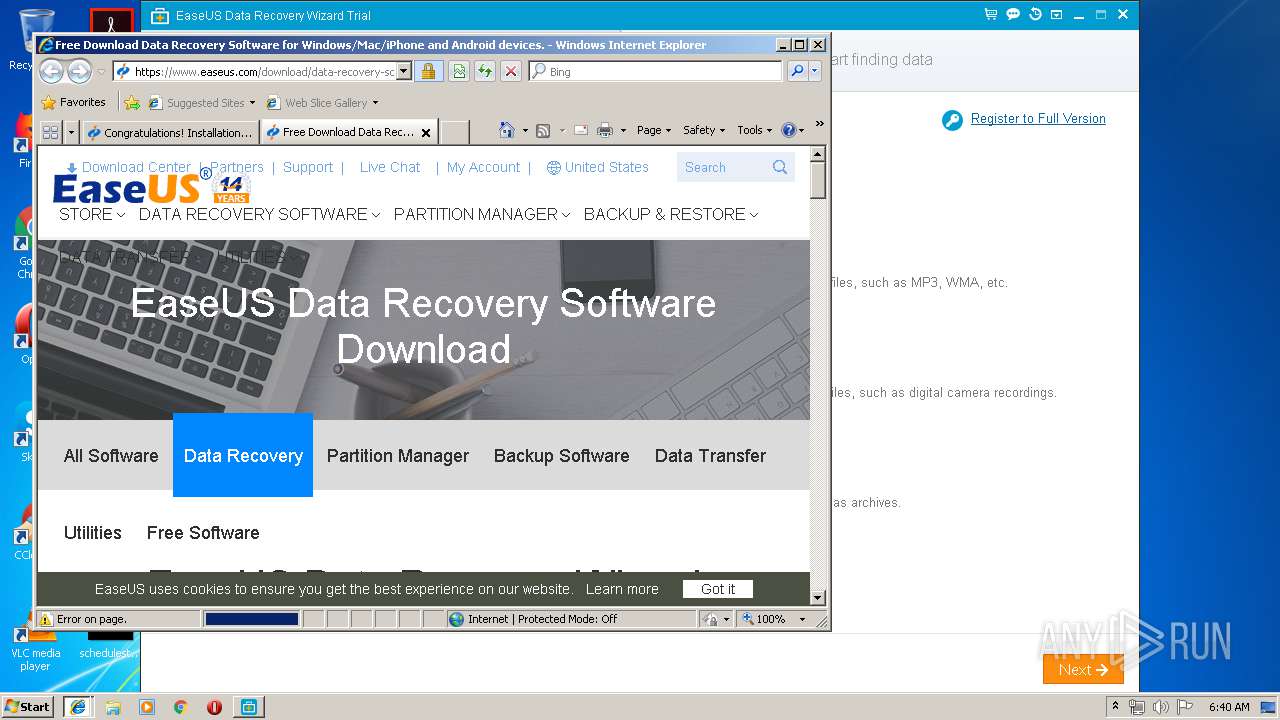
1576 | iexplore.exe | GET | 301 | 163.171.132.119:80 | http://www.easeus.com/thankyou/install-data-recovery-wizard-trial.htm | US | — | — | whitelisted |
2268 | iexplore.exe | GET | 301 | 163.171.132.119:80 | http://www.easeus.com/download/data-recovery-software.html | US | — | — | whitelisted |
3360 | DRWUI.exe | GET | 200 | 163.171.132.119:80 | http://www.easeus.com/update/drw_eng/drw.ini?time=132052271990130000 | US | ini | 139 b | whitelisted |
3324 | drw_trial.tmp | POST | 200 | 216.92.47.198:80 | http://track.easeus.com/product/index.php/?a=statistics&p_type=m_drw_infos | US | — | — | suspicious |
2876 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3324 | drw_trial.tmp | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
1576 | iexplore.exe | 163.171.132.119:80 | www.easeus.com | — | US | malicious |
2876 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 64.233.167.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
1576 | iexplore.exe | 172.217.18.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
— | — | 216.58.205.226:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
1576 | iexplore.exe | 1.199.92.84:443 | dn-growing.qbox.me | No.31,Jin-rong Street | CN | unknown |
— | — | 172.217.21.226:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
1576 | iexplore.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
1576 | iexplore.exe | 172.217.22.67:443 | www.google.at | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
track.easeus.com |
| suspicious |
www.easeus.com |
| whitelisted |
www.bing.com |
| whitelisted |
dn-growing.qbox.me |
| unknown |
www.google-analytics.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
www.googleadservices.com |
| whitelisted |
www.google.com |
| malicious |
googleads.g.doubleclick.net |
| whitelisted |
Threats
Process | Message |
|---|---|
drw_trial.tmp | 2019-06-17 06:39:54:263[UE] --Info. log level=3
|
drw_trial.tmp | 2019-06-17 06:39:54:263[UE] --Info. join=1
|
drw_trial.tmp | 2019-06-17 06:39:54:263[UE] --Info. top num =0
|
drw_trial.tmp | 2019-06-17 06:39:54:263[UE] --Info. try send=1
|
drw_trial.tmp | 2019-06-17 06:39:54:263[UE] --Info. InstallSpy. inst=03B9D850
|
drw_trial.tmp | 2019-06-17 06:39:54:263[UE] --Info. SetText. id=0x3 (3), text=1, inst=03B9D850
|
drw_trial.tmp | 2019-06-17 06:39:54:263[UE] --Info. SetValue. id=0x2 (2), val=1, inst=03B9D850
|
drw_trial.tmp | 2019-06-17 06:39:54:263[UE] --Info. SetText. id=0x5101 (20737), text=DRW 10.2 Trial, inst=03B9D850
|
drw_trial.tmp | 2019-06-17 06:39:54:278[UE] --Info. url=http://track.easeus.com/product/index.php/?a=statistics&p_type=m_drw_infos
|
drw_trial.tmp | 2019-06-17 06:39:54:278[UE] --Info. send data=uid=7995B914-D2AD-4E19-A44C-3A00CF8EB616&ue=1&codeinstall=1&processors=4&memory=3583&ipaddress=ip-test&os=Windows 7 Professional, Service Pack 1&timezone=GMT-00:00(GMT Standard Time)&install_version=DRW 10.2 Trial
|