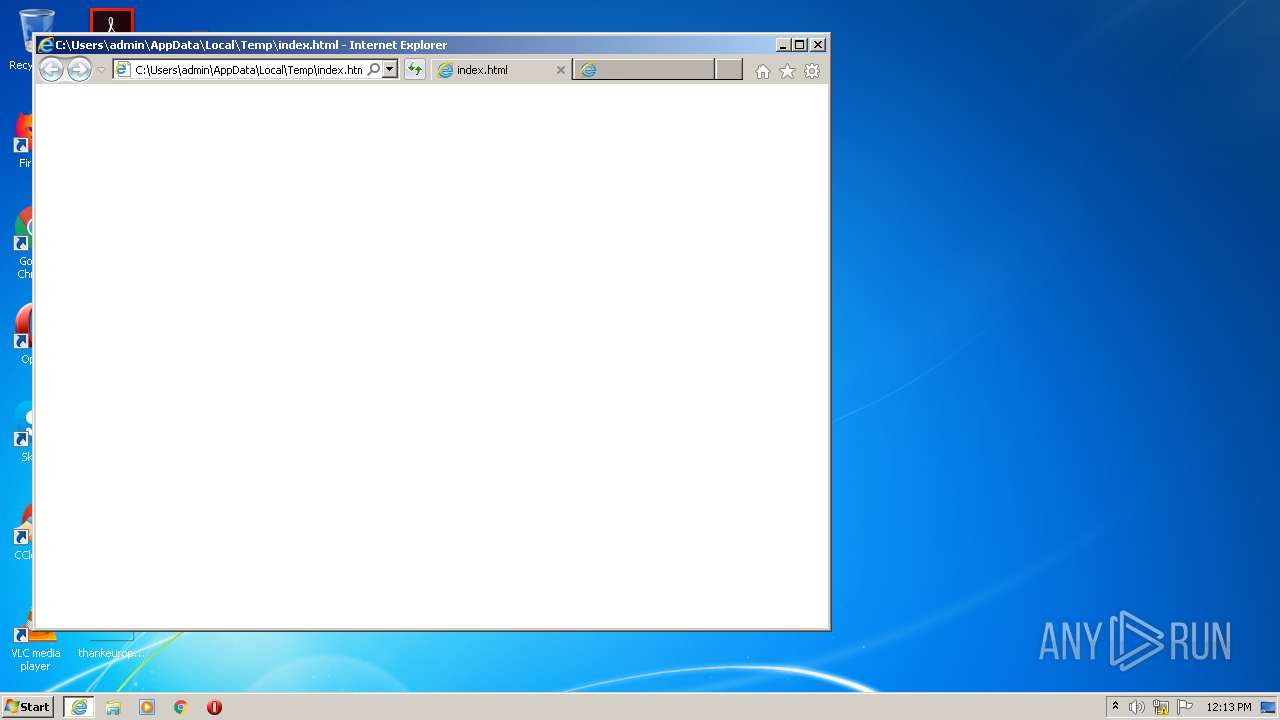
| download: | index.html |
| Full analysis: | https://app.any.run/tasks/39175428-4cdc-49f6-a8bb-8065bf9f00a9 |
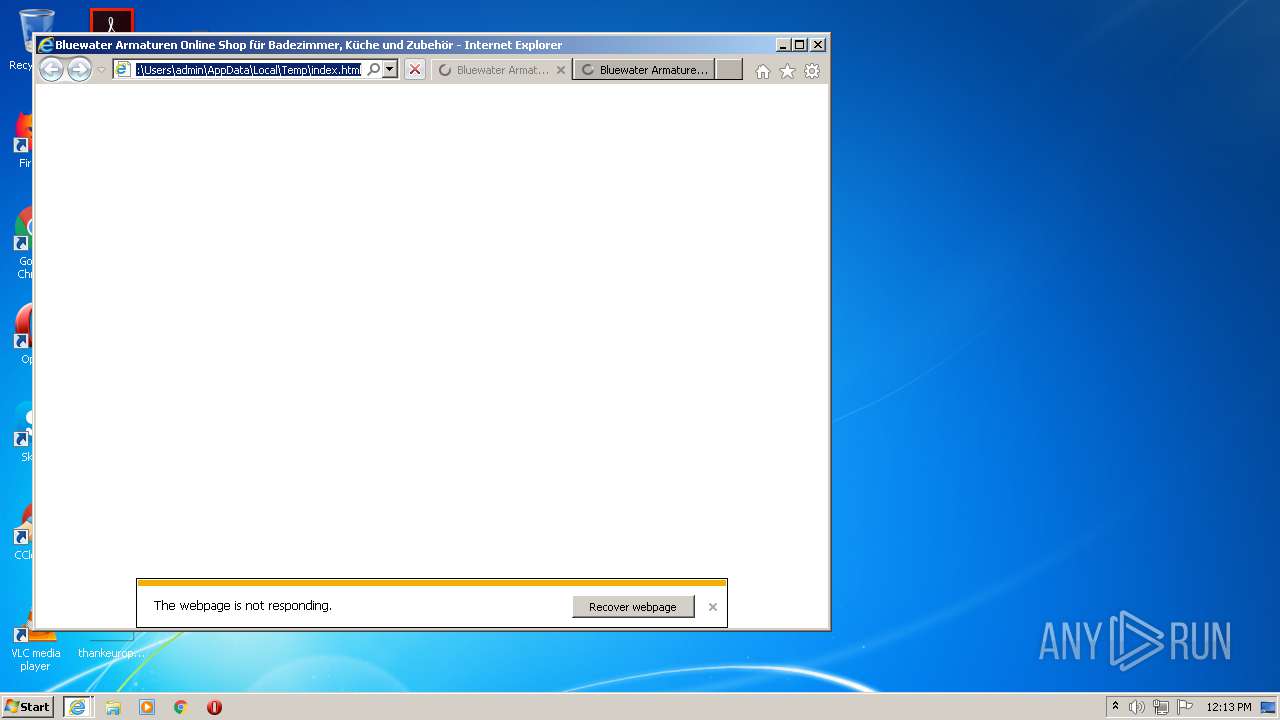
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 11:13:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with no line terminators |
| MD5: | 8C3BD0B3B84AA9F2708EB8FAEF166716 |
| SHA1: | ECDE3B8290F7D1286164864083D119F09E24E7D5 |
| SHA256: | 794811F86388804256DE15F90B6AB37B3928B7AB3D5AC3C0990562A9908B601A |
| SSDEEP: | 49152:G+AwlHVLTYOi/NC0QwPlfLQje0XqSWObp:G+AwlHVLCG |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2180)
- iexplore.exe (PID: 3828)
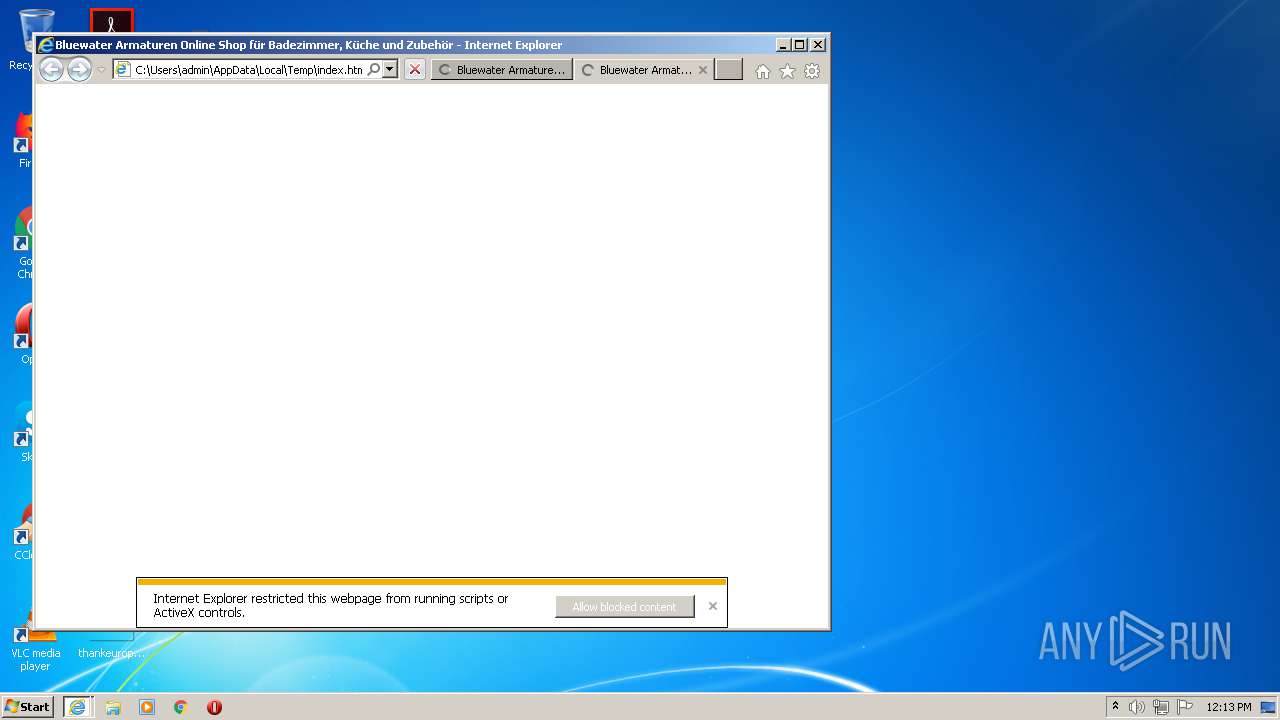
Changes internet zones settings
- iexplore.exe (PID: 2180)
Application launched itself
- iexplore.exe (PID: 2180)
- chrome.exe (PID: 2960)
Reads internet explorer settings
- iexplore.exe (PID: 1540)
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 3828)
Reads settings of System Certificates
- iexplore.exe (PID: 1540)
- iexplore.exe (PID: 3348)
- chrome.exe (PID: 3540)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1540)
- iexplore.exe (PID: 3348)
Changes settings of System certificates
- iexplore.exe (PID: 1540)
- iexplore.exe (PID: 3348)
Manual execution by user
- chrome.exe (PID: 2960)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 1540)
Creates files in the user directory
- iexplore.exe (PID: 3828)
Reads the hosts file
- chrome.exe (PID: 3540)
- chrome.exe (PID: 2960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .aiml | | | Artificial Intelligence Markup Language (48.3) |
|---|---|---|
| .htm/html | | | HyperText Markup Language with DOCTYPE (41.6) |
| .html | | | HyperText Markup Language (9.9) |
Total processes
63
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f15a9d0,0x6f15a9e0,0x6f15a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,1525368545402674451,12095122575007716819,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4020097276695392615 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3616 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,1525368545402674451,12095122575007716819,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7094974420653042226 --mojo-platform-channel-handle=3324 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2180 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,1525368545402674451,12095122575007716819,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15637654459262521029 --mojo-platform-channel-handle=3432 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,1525368545402674451,12095122575007716819,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10746275838330922503 --mojo-platform-channel-handle=3440 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,1525368545402674451,12095122575007716819,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2861938006957397320 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,1525368545402674451,12095122575007716819,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5825782454071093998 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,1525368545402674451,12095122575007716819,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11545850602808900893 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2796 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 181
Read events
1 928
Write events
242
Delete events
11
Modification events
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3458324058 | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30840602 | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2180) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
176
Text files
348
Unknown types
91
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1540 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabC42B.tmp | — | |
MD5:— | SHA256:— | |||
| 1540 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarC42C.tmp | — | |
MD5:— | SHA256:— | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabD9F5.tmp | — | |
MD5:— | SHA256:— | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabD9F6.tmp | — | |
MD5:— | SHA256:— | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabD9F8.tmp | — | |
MD5:— | SHA256:— | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabD9F9.tmp | — | |
MD5:— | SHA256:— | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabD9F7.tmp | — | |
MD5:— | SHA256:— | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarD9FA.tmp | — | |
MD5:— | SHA256:— | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarD9FE.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
172
DNS requests
66
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
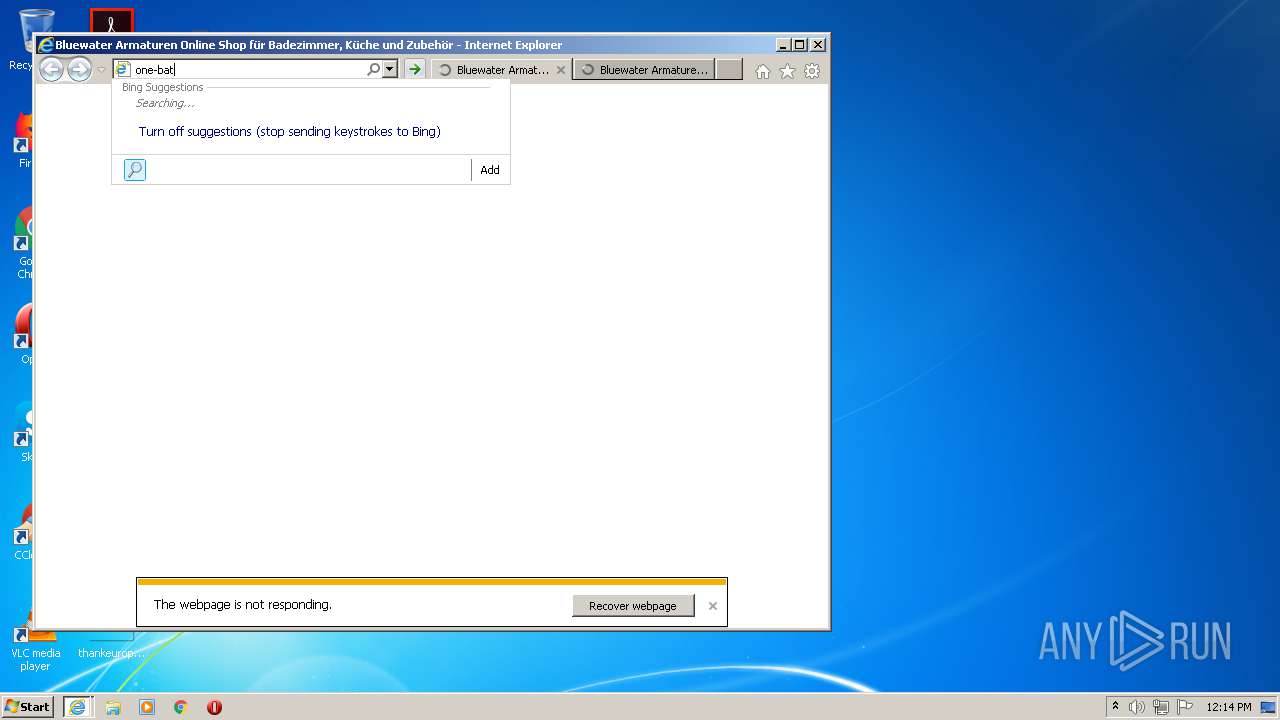
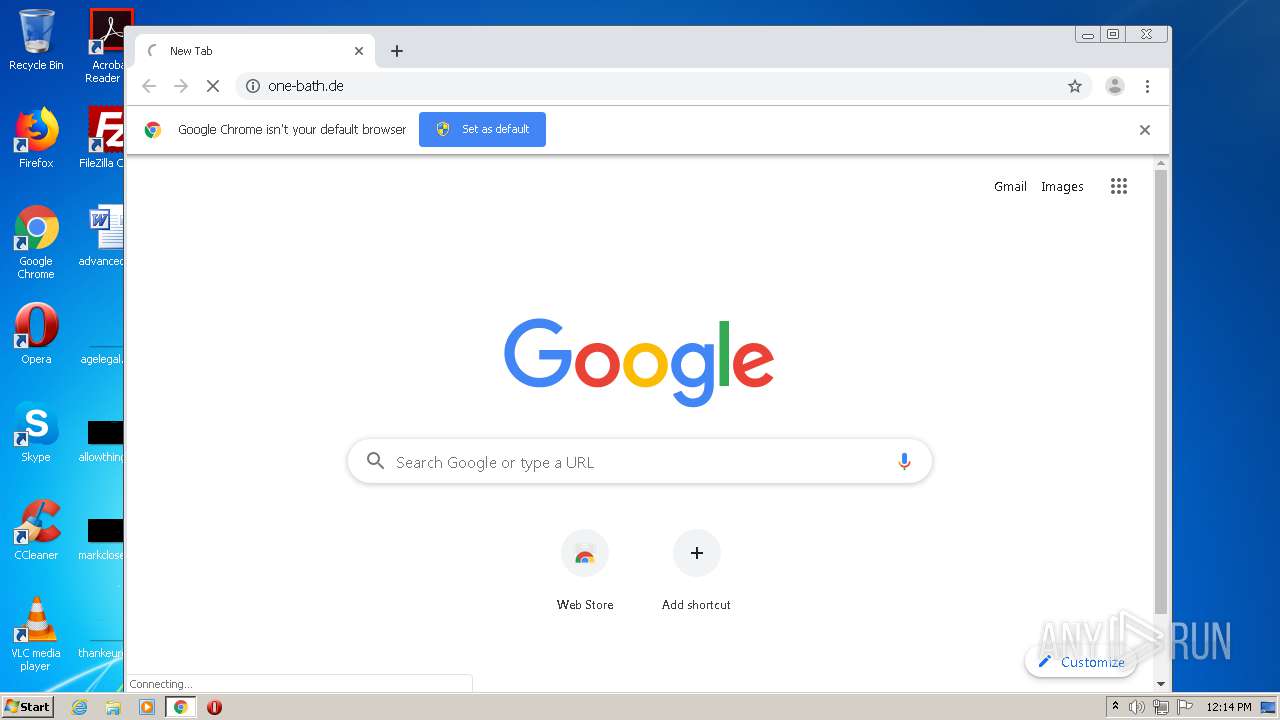
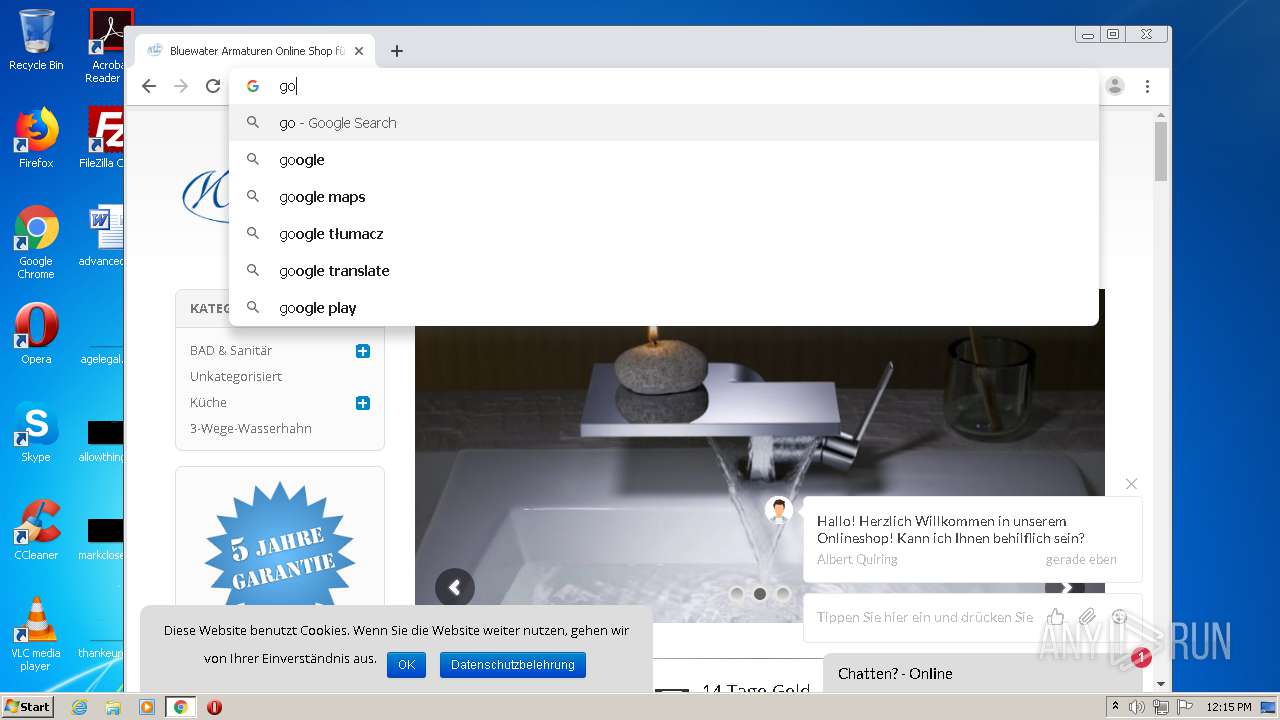
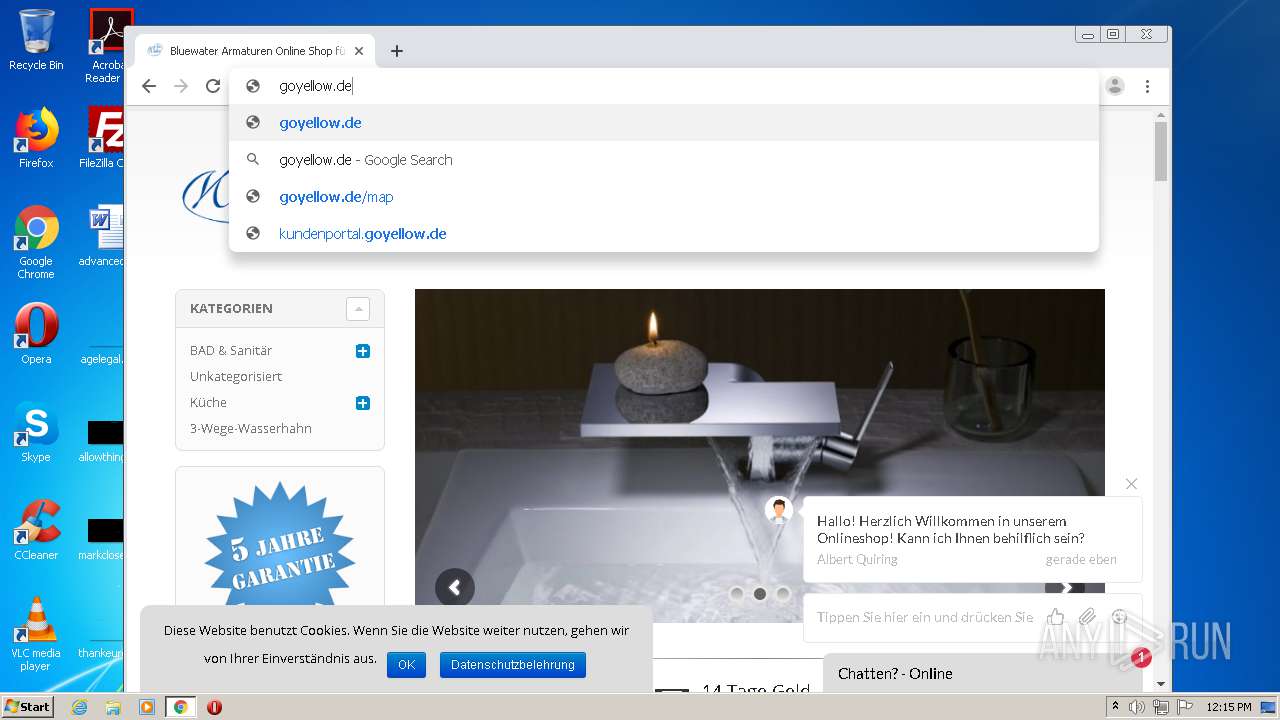
3828 | iexplore.exe | GET | — | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=one-bath.&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
3828 | iexplore.exe | GET | — | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=one-bath.d&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
1540 | iexplore.exe | GET | 200 | 192.35.177.64:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | US | der | 1.07 Kb | whitelisted |
1540 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
1540 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
3348 | iexplore.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1540 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
3348 | iexplore.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1540 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
3348 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTIyCPRUzvKHRw7iRE1lF%2BfcLu%2FjgQUypJnUmHervy6Iit%2FHIdMJftvmVgCEA63n6xXHv%2Fu7MoyaFE8tzc%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
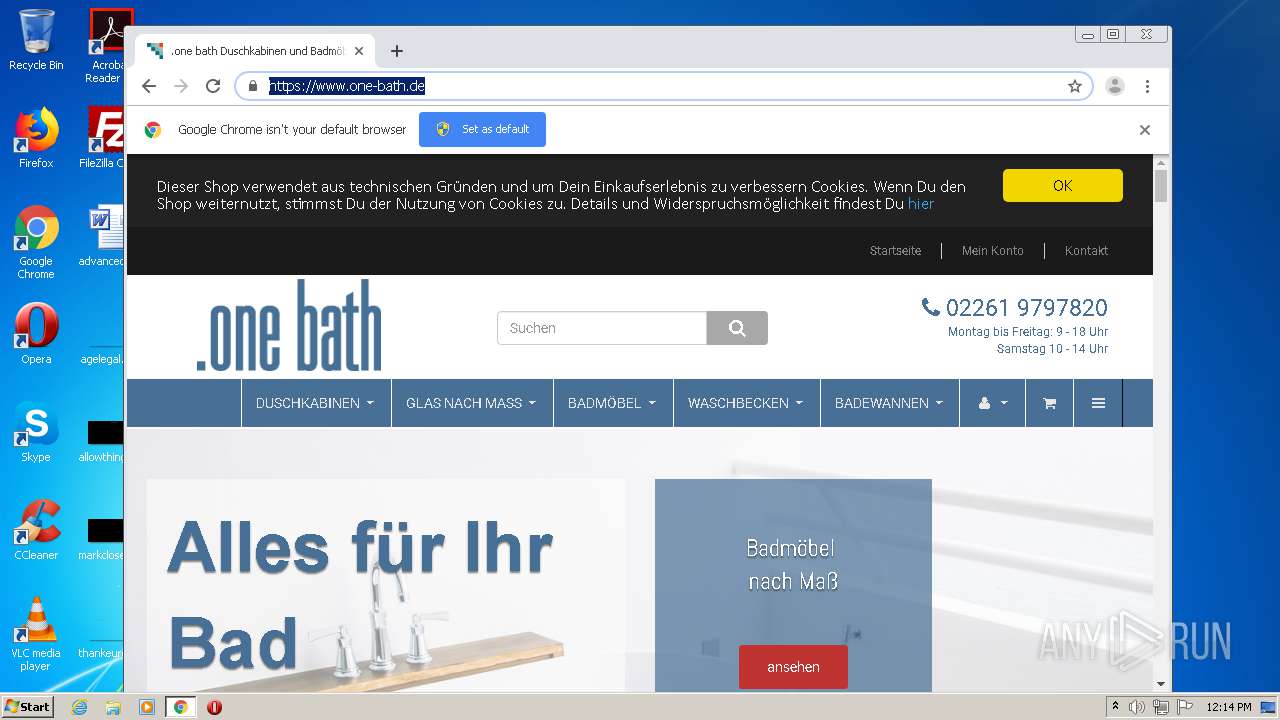
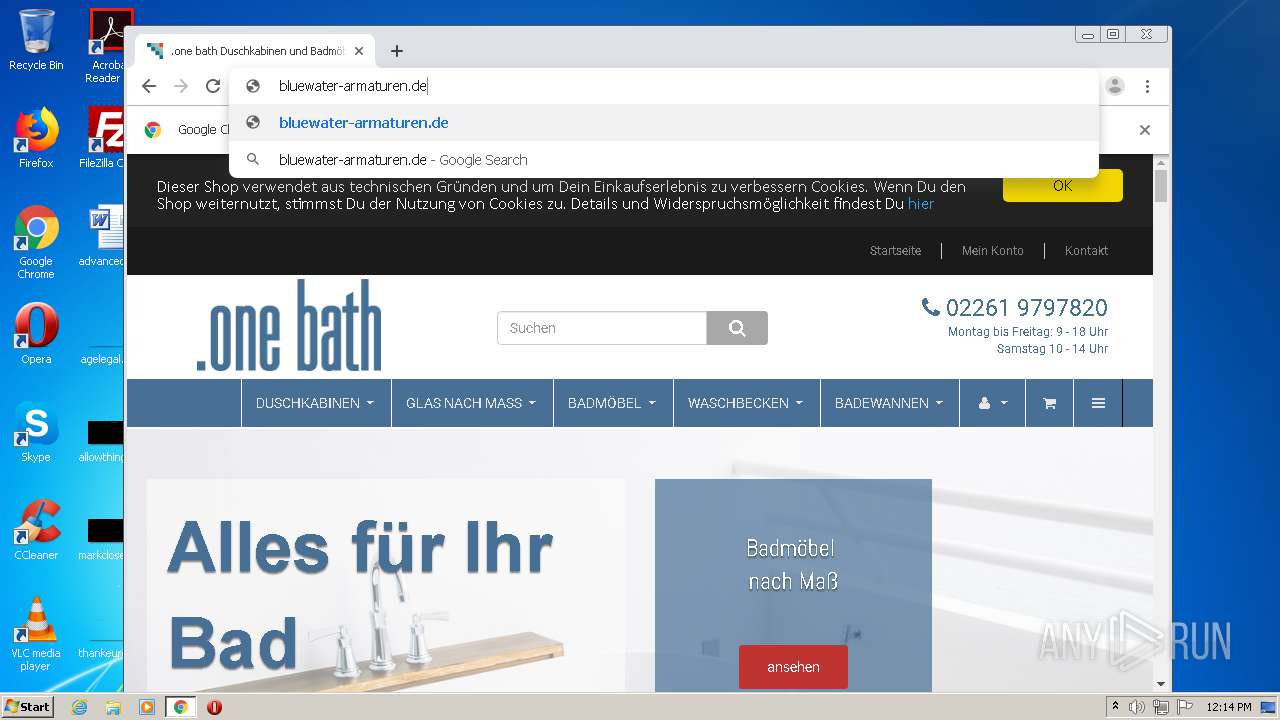
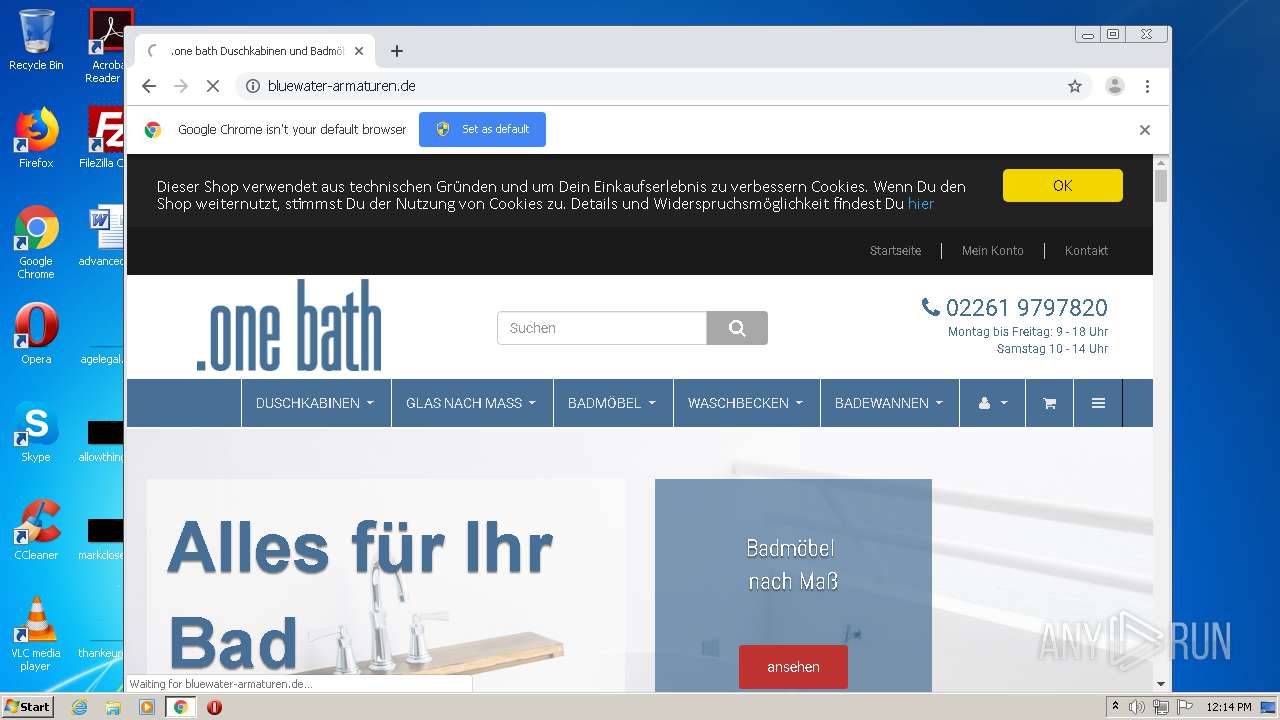
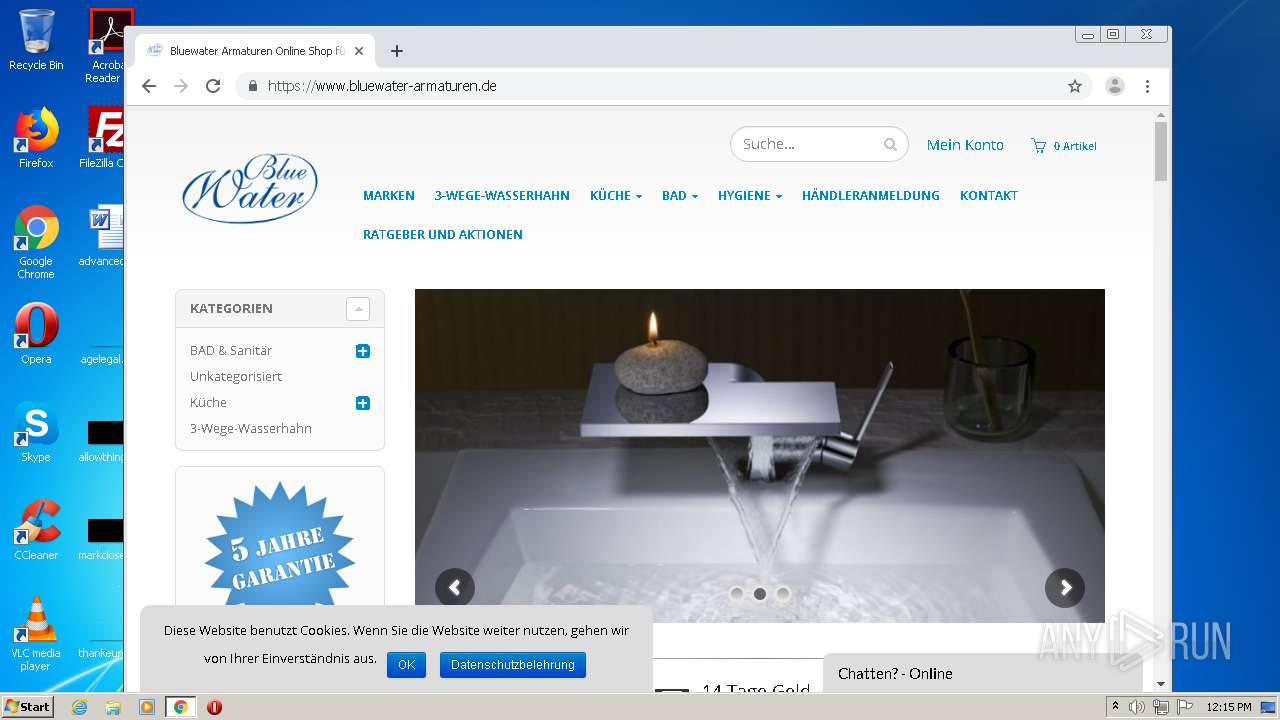
4 | System | 94.130.228.16:445 | www.bluewater-armaturen.de | Hetzner Online GmbH | DE | unknown |
1540 | iexplore.exe | 94.130.228.16:443 | www.bluewater-armaturen.de | Hetzner Online GmbH | DE | unknown |
4 | System | 94.130.228.16:139 | www.bluewater-armaturen.de | Hetzner Online GmbH | DE | unknown |
2180 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1540 | iexplore.exe | 2.16.186.35:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
1540 | iexplore.exe | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
3348 | iexplore.exe | 94.130.228.16:443 | www.bluewater-armaturen.de | Hetzner Online GmbH | DE | unknown |
1540 | iexplore.exe | 192.35.177.64:80 | crl.identrust.com | IdenTrust | US | malicious |
1540 | iexplore.exe | 85.13.145.212:443 | www.haendlerbund.de | Neue Medien Muennich GmbH | DE | unknown |
3348 | iexplore.exe | 85.13.145.212:443 | www.haendlerbund.de | Neue Medien Muennich GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bluewater-armaturen.de |
| unknown |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
crl.identrust.com |
| whitelisted |
www.haendlerbund.de |
| unknown |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |