| download: | SIlZl49933 |
| Full analysis: | https://app.any.run/tasks/03b53065-1788-4369-aae6-0fe89e202a91 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2020, 18:48:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DB94F4B28F37752167A872FFF15175DB |
| SHA1: | A5DBD0699FAE06E900DD32B0D4CEEAF62A6A5793 |
| SHA256: | 79459F5A79CABB422D06B09482D8CAA017551BF648503E05429C8568EC04379B |
| SSDEEP: | 6144:eT2ZfcAZDQvEL9QdUW1UWKUWc197qo1D+:k2ZC8SdUAUHUn19Ool |
MALICIOUS
Emotet process was detected
- SIlZl49933.exe (PID: 976)
Connects to CnC server
- serialfunc.exe (PID: 3640)
EMOTET was detected
- serialfunc.exe (PID: 3640)
Changes the autorun value in the registry
- serialfunc.exe (PID: 3640)
SUSPICIOUS
Starts itself from another location
- SIlZl49933.exe (PID: 976)
Application launched itself
- SIlZl49933.exe (PID: 640)
- serialfunc.exe (PID: 2436)
- serialfunc.exe (PID: 3640)
Connects to server without host name
- serialfunc.exe (PID: 3640)
Executable content was dropped or overwritten
- SIlZl49933.exe (PID: 976)
Connects to unusual port
- serialfunc.exe (PID: 3640)
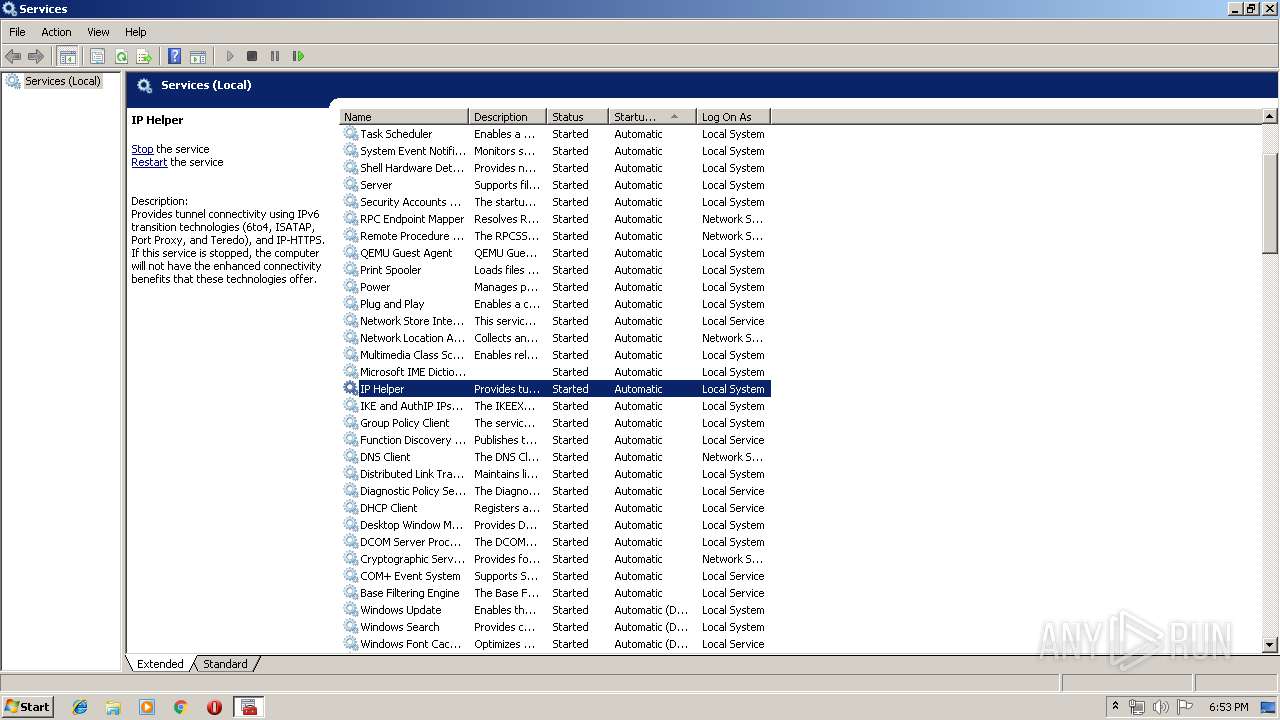
Reads internet explorer settings
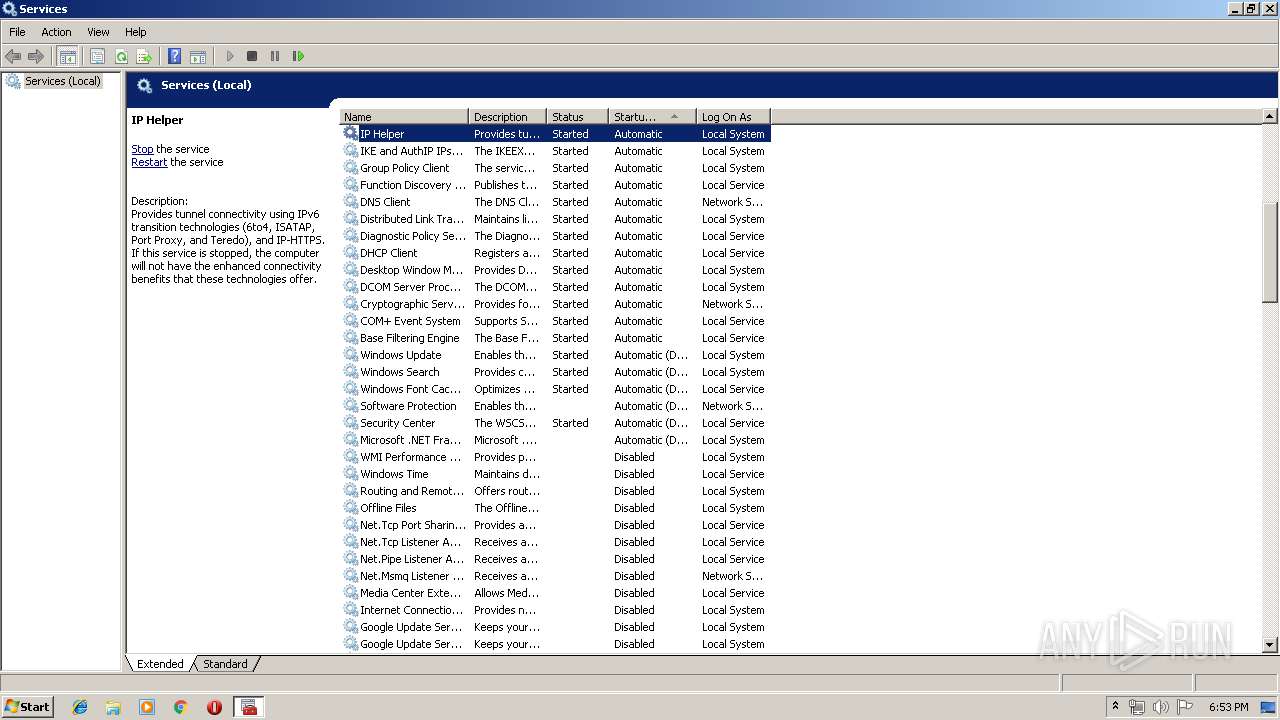
- mmc.exe (PID: 436)
Connects to SMTP port
- serialfunc.exe (PID: 3640)
INFO
Reads Microsoft Office registry keys
- serialfunc.exe (PID: 3232)
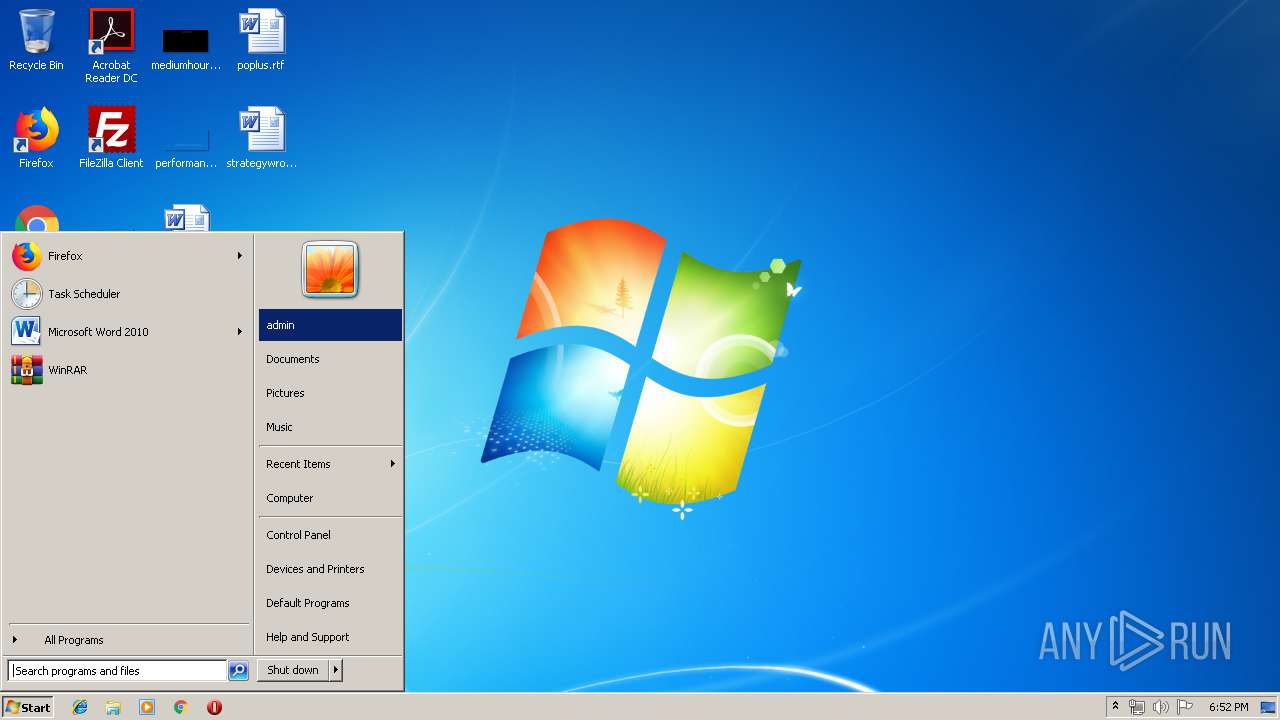
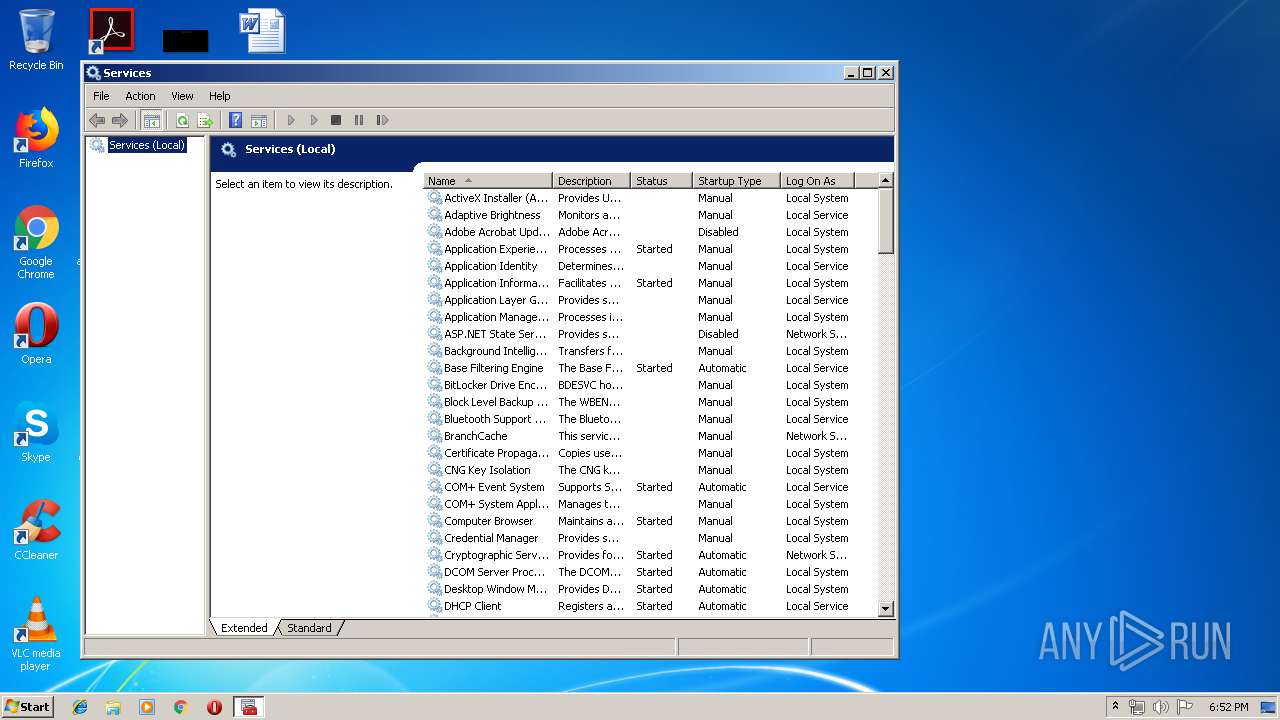
Manual execution by user
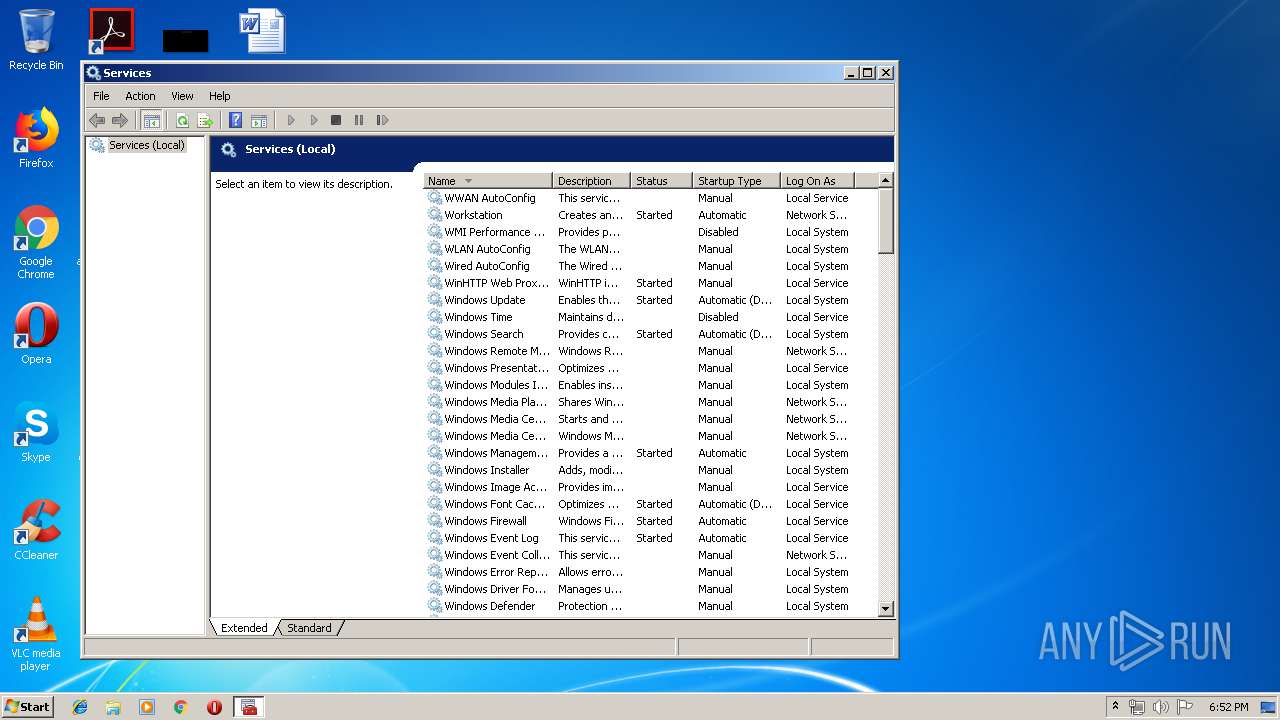
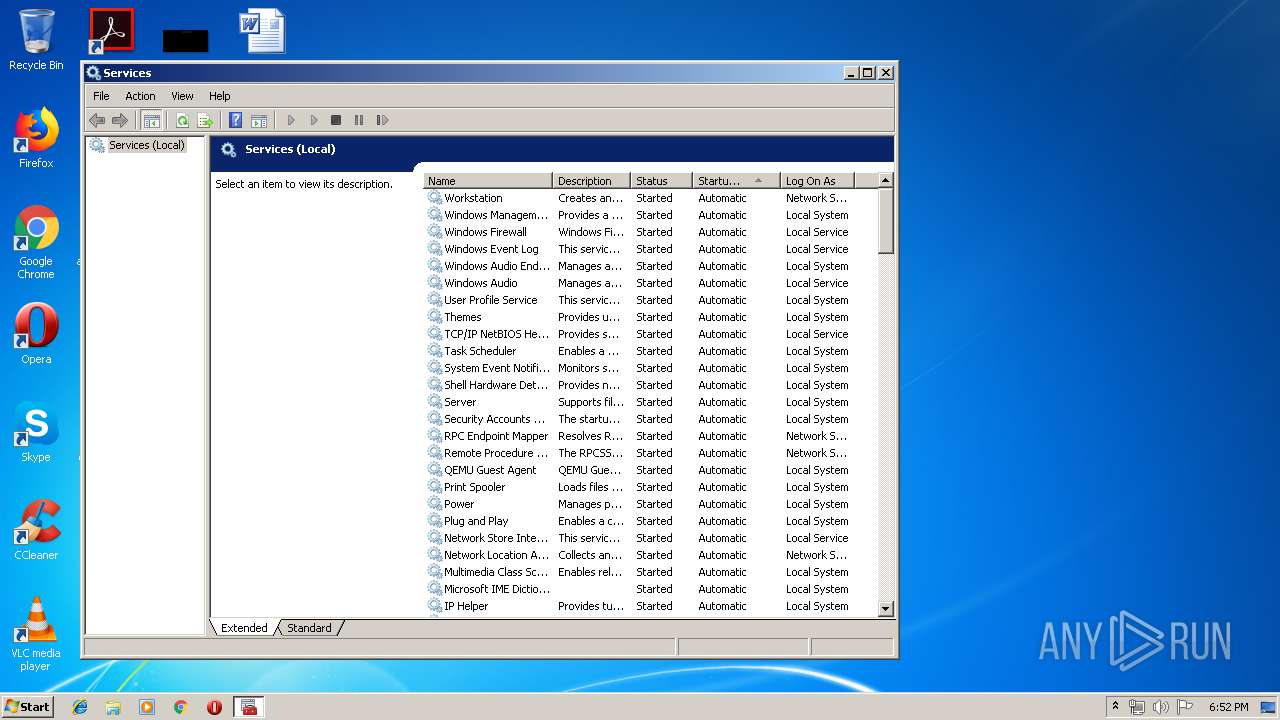
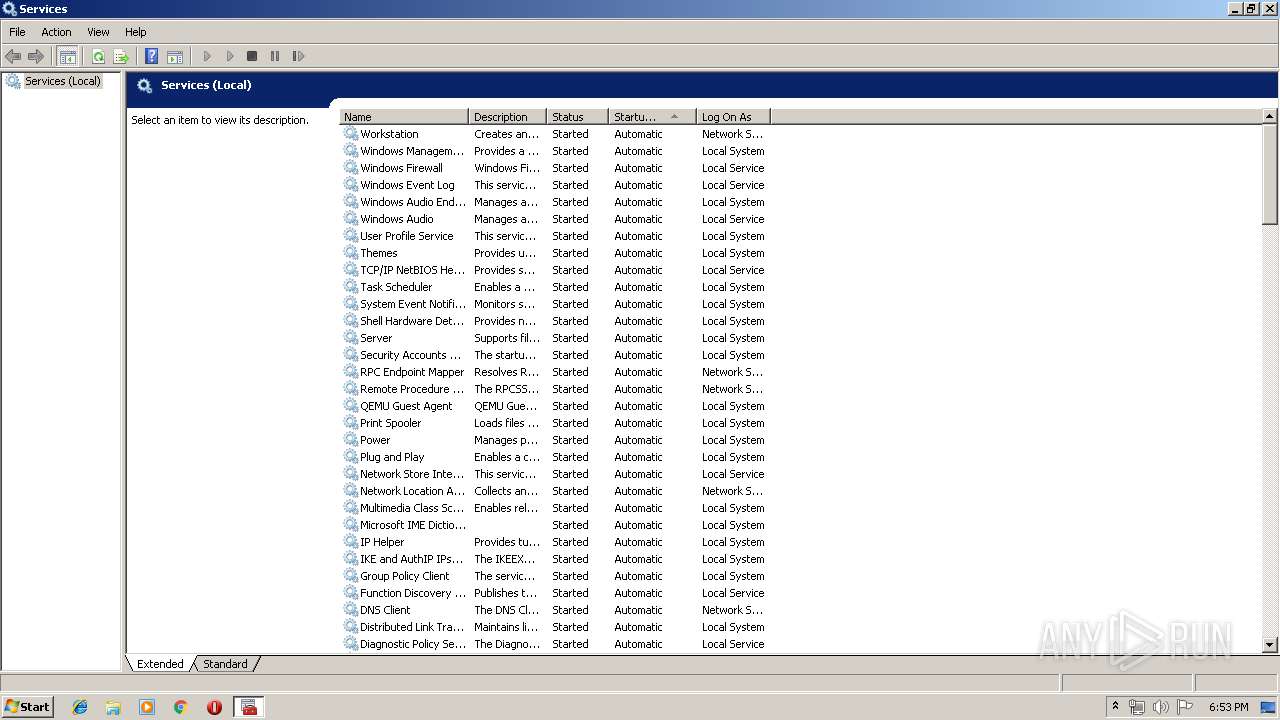
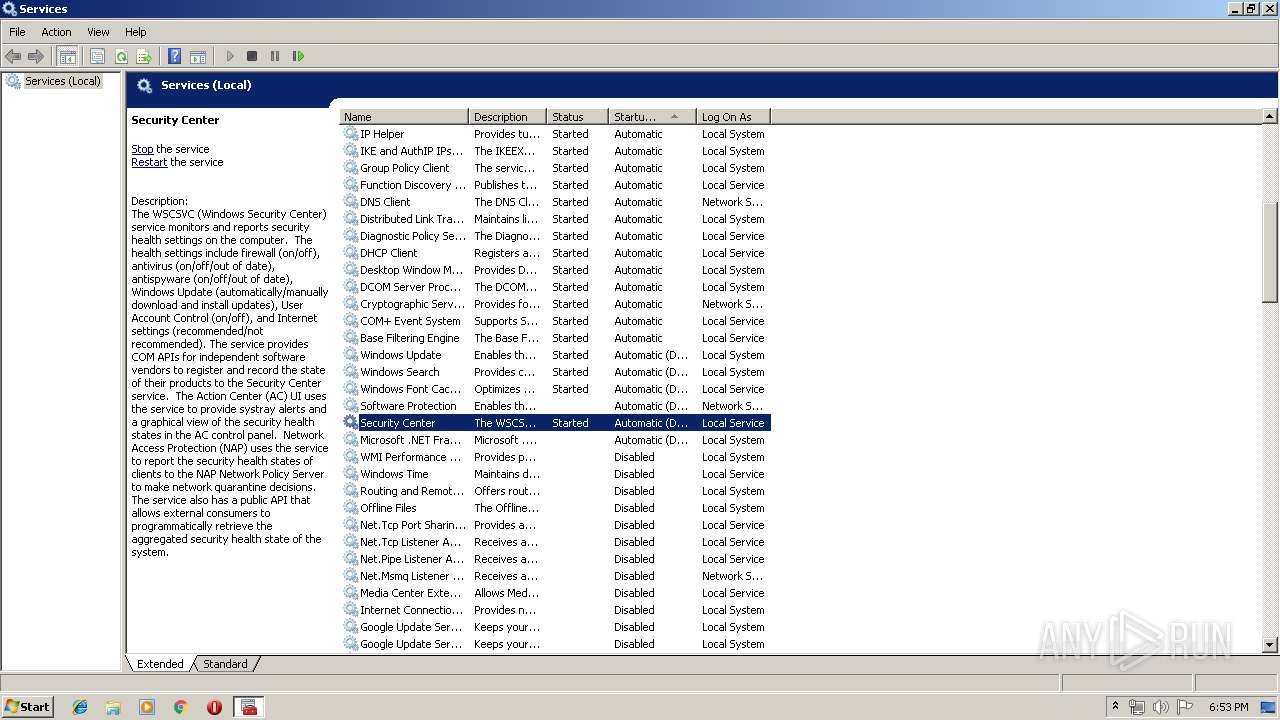
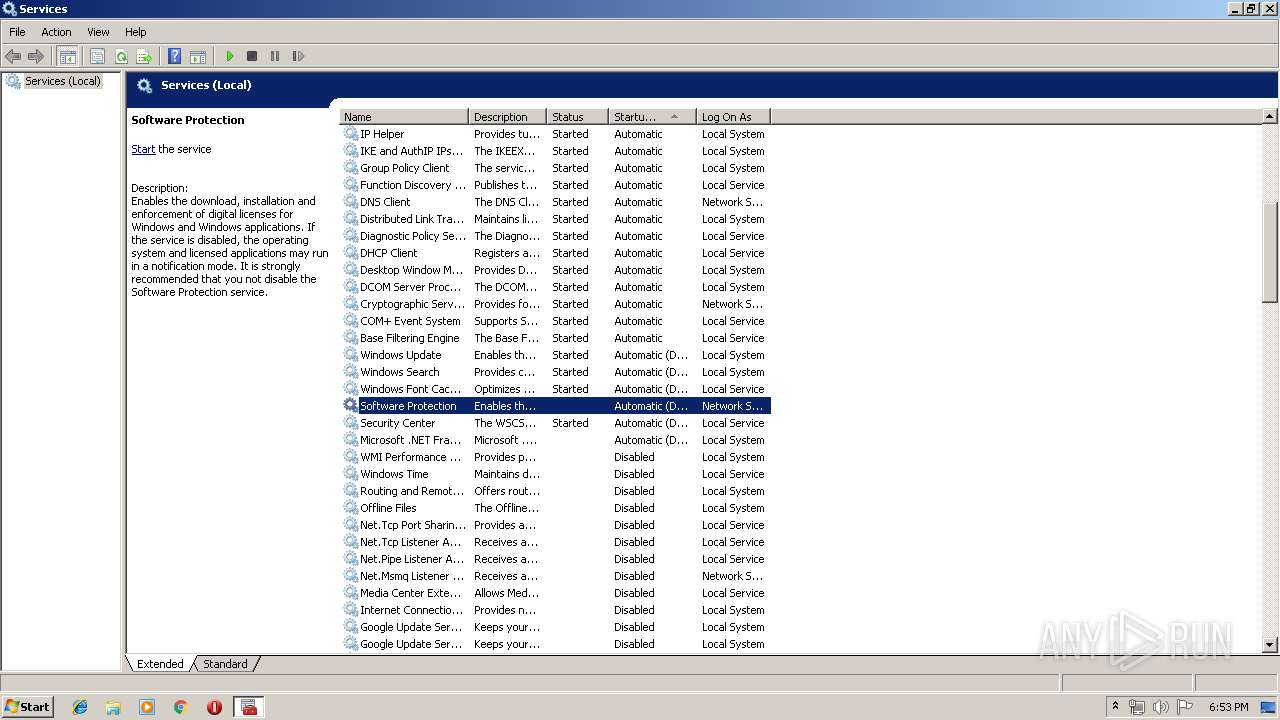
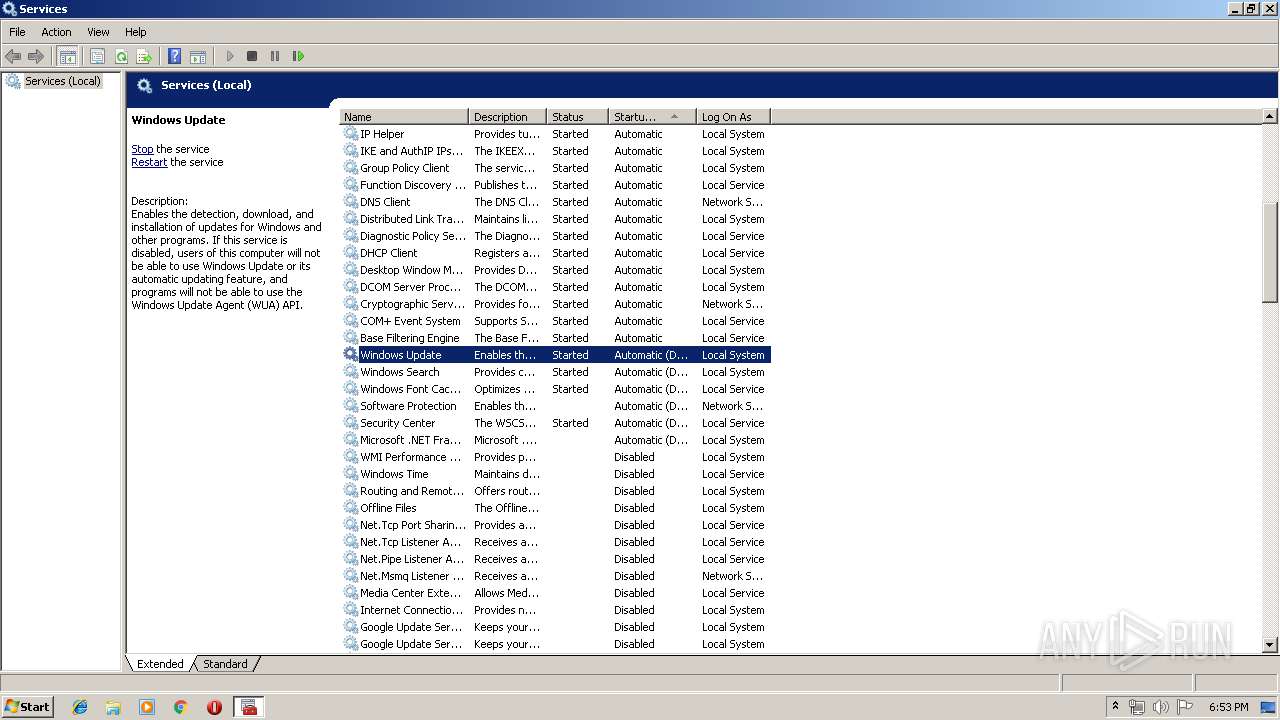
- mmc.exe (PID: 504)
- mmc.exe (PID: 436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (38.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (28.2) |
| .exe | | | Win64 Executable (generic) (25) |
| .exe | | | Win32 Executable (generic) (4) |
| .exe | | | Generic Win/DOS Executable (1.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:17 10:50:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 114688 |
| InitializedDataSize: | 237568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8ae6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | PromptEdit_Demo MFC Application |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | PromptEdit_Demo |
| LegalCopyright: | Copyright (C) 2002 |
| LegalTrademarks: | - |
| OriginalFileName: | PromptEdit_Demo.EXE |
| ProductName: | PromptEdit_Demo Application |
| ProductVersion: | 1, 0, 0, 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Jan-2020 09:50:38 |
| Detected languages: |
|
| CompanyName: | - |
| FileDescription: | PromptEdit_Demo MFC Application |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | PromptEdit_Demo |
| LegalCopyright: | Copyright (C) 2002 |
| LegalTrademarks: | - |
| OriginalFilename: | PromptEdit_Demo.EXE |
| ProductName: | PromptEdit_Demo Application |
| ProductVersion: | 1, 0, 0, 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 17-Jan-2020 09:50:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001BA84 | 0x0001C000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.34598 |
.rdata | 0x0001D000 | 0x000067C6 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.67718 |
.data | 0x00024000 | 0x00005134 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.5113 |
.rsrc | 0x0002A000 | 0x0002CB10 | 0x0002D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.79245 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.36015 | 820 | UNKNOWN | English - United States | RT_VERSION |
2 | 3.68558 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 3.4754 | 488 | UNKNOWN | English - United States | RT_ICON |
4 | 2.97205 | 296 | UNKNOWN | English - United States | RT_ICON |
5 | 2.25983 | 168 | UNKNOWN | English - United States | RT_ICON |
6 | 4.57142 | 3752 | UNKNOWN | English - United States | RT_ICON |
7 | 4.726 | 2216 | UNKNOWN | English - United States | RT_ICON |
8 | 4.9116 | 1736 | UNKNOWN | English - United States | RT_ICON |
9 | 3.43845 | 1384 | UNKNOWN | English - United States | RT_ICON |
10 | 1.50219 | 1160 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll (delay-loaded) |
OLEAUT32.dll |
SHLWAPI.dll |
USER32.dll |
WINSPOOL.DRV |
Total processes
44
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\services.msc" | C:\Windows\system32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 504 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\services.msc" | C:\Windows\system32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 640 | "C:\Users\admin\AppData\Local\Temp\SIlZl49933.exe" | C:\Users\admin\AppData\Local\Temp\SIlZl49933.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 976 | --4f8a91d0 | C:\Users\admin\AppData\Local\Temp\SIlZl49933.exe | SIlZl49933.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2436 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | SIlZl49933.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3232 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\BC02.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3640 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
353
Read events
286
Write events
66
Delete events
1
Modification events
| (PID) Process: | (3640) serialfunc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serialfunc_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3640) serialfunc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serialfunc_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3640) serialfunc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serialfunc_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3640) serialfunc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serialfunc_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3640) serialfunc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serialfunc_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3640) serialfunc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serialfunc_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3640) serialfunc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serialfunc_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3640) serialfunc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3640) serialfunc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serialfunc_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3640) serialfunc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
1
Suspicious files
0
Text files
4
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3232 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 3232 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 3232 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~honey@pot.com.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 3232 | serialfunc.exe | C:\Users\admin\AppData\Local\Temp\BC02.tmp | — | |
MD5:— | SHA256:— | |||
| 3232 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | pst | |
MD5:— | SHA256:— | |||
| 976 | SIlZl49933.exe | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | executable | |
MD5:— | SHA256:— | |||
| 3232 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\honey@pot.com.pst | pst | |
MD5:— | SHA256:— | |||
| 3232 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\Outlook.pst | pst | |
MD5:E9D05E43651DCF539A81499170703F39 | SHA256:C7ABAAF29D6F58F66BEAE8DDE519F4EC3C98C1C118A483E6B9C8812CFB39150A | |||
| 436 | mmc.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\views[1] | html | |
MD5:A726593A8261930E4786375106FC6BFE | SHA256:E6BFDFBB9A0649EA9D38DE4255C355C581097E6A1035A54943260B22AD45F172 | |||
| 436 | mmc.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\views[1] | text | |
MD5:BEE1758A485085BB8A121EB74BA7E96F | SHA256:EDCAD5B1CE8A304B70B8C9EA57D4AEAB740D979FFA59243B943011CB1BA4D57E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
205
DNS requests
242
Threats
84
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3640 | serialfunc.exe | POST | — | 98.199.196.197:80 | http://98.199.196.197/cUrtGSyC | US | — | — | malicious |
3640 | serialfunc.exe | POST | 200 | 188.85.143.170:80 | http://188.85.143.170/ASi41s | ES | binary | 148 b | malicious |
3640 | serialfunc.exe | POST | 200 | 188.85.143.170:80 | http://188.85.143.170/UPUF | ES | binary | 1.55 Mb | malicious |
3640 | serialfunc.exe | POST | 200 | 51.77.113.100:7080 | http://51.77.113.100:7080/ASi41s | GB | binary | 148 b | malicious |
3640 | serialfunc.exe | POST | — | 51.77.113.100:7080 | http://51.77.113.100:7080/VAob1ocP763Rs | GB | — | — | malicious |
3640 | serialfunc.exe | POST | 200 | 51.77.113.100:7080 | http://51.77.113.100:7080/YD8qRRjpSq | GB | binary | 188 Kb | malicious |
3640 | serialfunc.exe | POST | 200 | 51.77.113.100:7080 | http://51.77.113.100:7080/ASi41s | GB | binary | 148 b | malicious |
3640 | serialfunc.exe | POST | 200 | 51.77.113.100:7080 | http://51.77.113.100:7080/1e7VVSp6Q3inF0 | GB | binary | 188 Kb | malicious |
3640 | serialfunc.exe | POST | — | 51.77.113.100:7080 | http://51.77.113.100:7080/J3PhovzUI | GB | — | — | malicious |
3640 | serialfunc.exe | POST | 200 | 51.77.113.100:7080 | http://51.77.113.100:7080/50KNMn5zrIOtRwFZJ | GB | binary | 3.56 Mb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3640 | serialfunc.exe | 188.85.143.170:80 | — | Vodafone Spain | ES | malicious |
3640 | serialfunc.exe | 51.77.113.100:7080 | — | — | GB | malicious |
3640 | serialfunc.exe | 98.199.196.197:80 | — | Comcast Cable Communications, LLC | US | malicious |
3640 | serialfunc.exe | 200.55.224.98:25 | mail.etapanet.net | ETAPA EP | EC | unknown |
3640 | serialfunc.exe | 74.125.206.109:465 | smtp.gmail.com | Google Inc. | US | whitelisted |
3640 | serialfunc.exe | 102.133.229.205:25 | incoming.zol.co.zw | — | — | unknown |
3640 | serialfunc.exe | 216.16.142.227:465 | mail.computertrendz.net | Cox Communications Inc. | US | unknown |
3640 | serialfunc.exe | 204.16.7.124:587 | smtp.incomisa.com.br | Ultranet Telecomunicações Ltda | US | unknown |
3640 | serialfunc.exe | 5.150.137.171:587 | mail.regitaly.it | KPNQWest Italia S.p.a. | IT | unknown |
3640 | serialfunc.exe | 74.125.206.109:587 | smtp.gmail.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
smtp.incomisa.com.br |
| unknown |
mail.regitaly.it |
| unknown |
mail.dmicorp.ws |
| unknown |
smtp.gmail.com |
| malicious |
mail.etapanet.net |
| unknown |
smtp.mail.ctc.jp |
| unknown |
mail.computertrendz.net |
| unknown |
smtpout.secureserver.net |
| malicious |
mail.100natural.com.mx |
| unknown |
incoming.zol.co.zw |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3640 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3640 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3640 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3640 | serialfunc.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
3640 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3640 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3640 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3640 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3640 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3640 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |