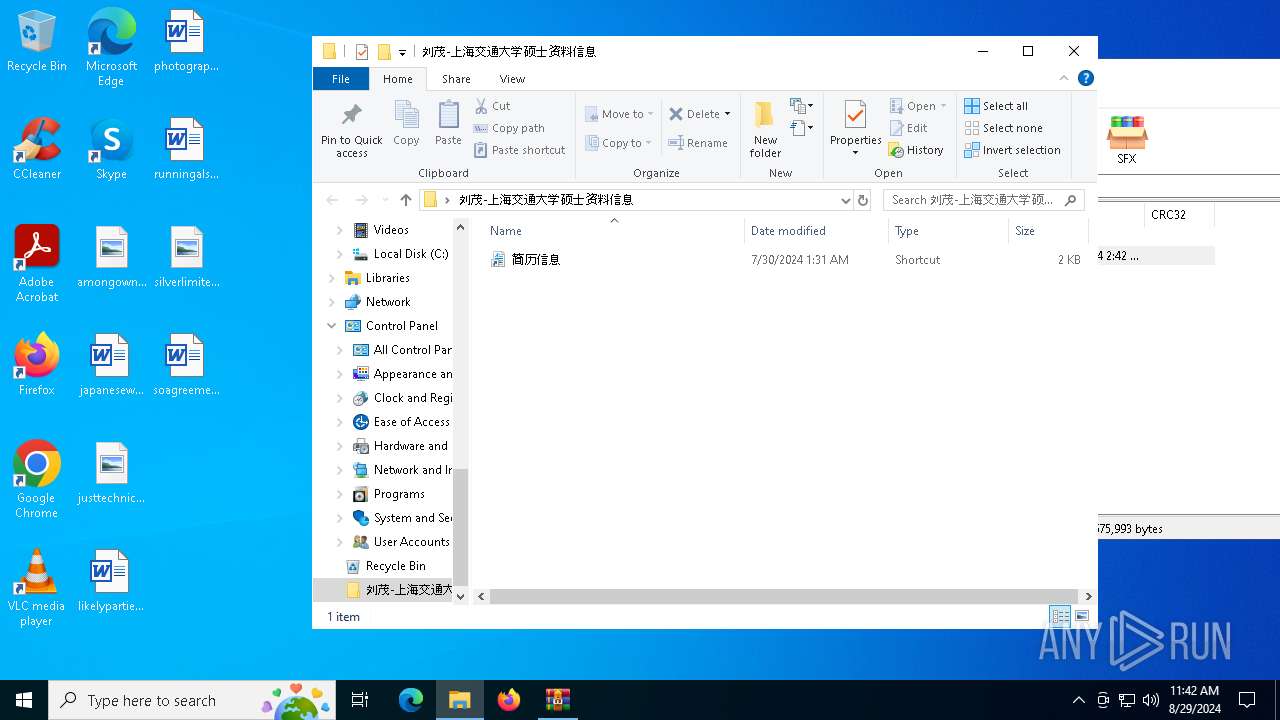
| File name: | 刘茂-上海交通大学硕士资料信息.zip |
| Full analysis: | https://app.any.run/tasks/2ed1ac37-a477-4eaf-93d9-b49bf0ccc5e1 |
| Verdict: | Malicious activity |
| Analysis date: | August 29, 2024, 11:41:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | F7C4A850987AF95F5FE7EDFD250BAEC7 |
| SHA1: | 6A2975E9FED4208897239DD34B67DE7536C3B13F |
| SHA256: | 793E56E7320A7F9542D31D360A50222F4A3850A06A1654D5442ED391EE6F58A4 |
| SSDEEP: | 98304:iYxoNArqvRxlv9Zl9dPgHo6Kuhr2bHwakHcZZxjJtkZNHU0wlacUnF+kt3GKTH5w:ZQ0YM6B32kfthqDmE3UX |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes an FTP script from a file
- ftp.exe (PID: 2136)
Process drops python dynamic module
- WinRAR.exe (PID: 7164)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 7164)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7164)
Starts CMD.EXE for commands execution
- ftp.exe (PID: 2136)
Loads Python modules
- pythonw.exe (PID: 6876)
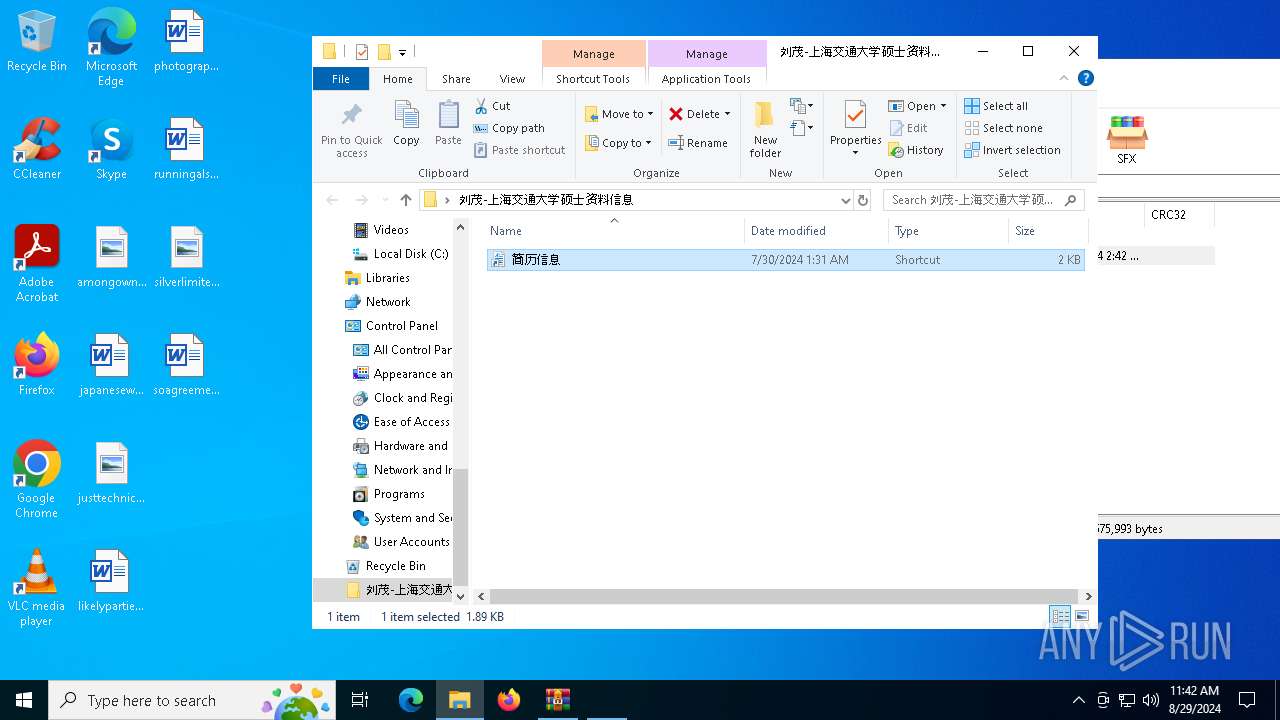
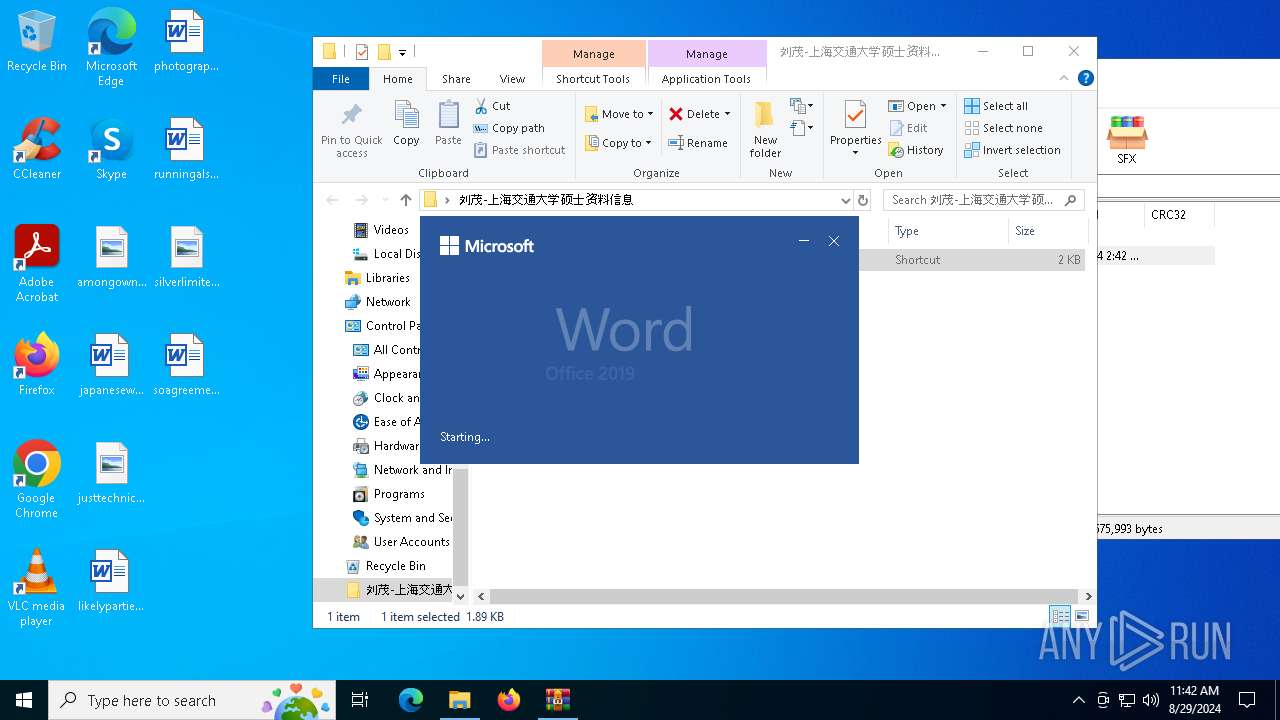
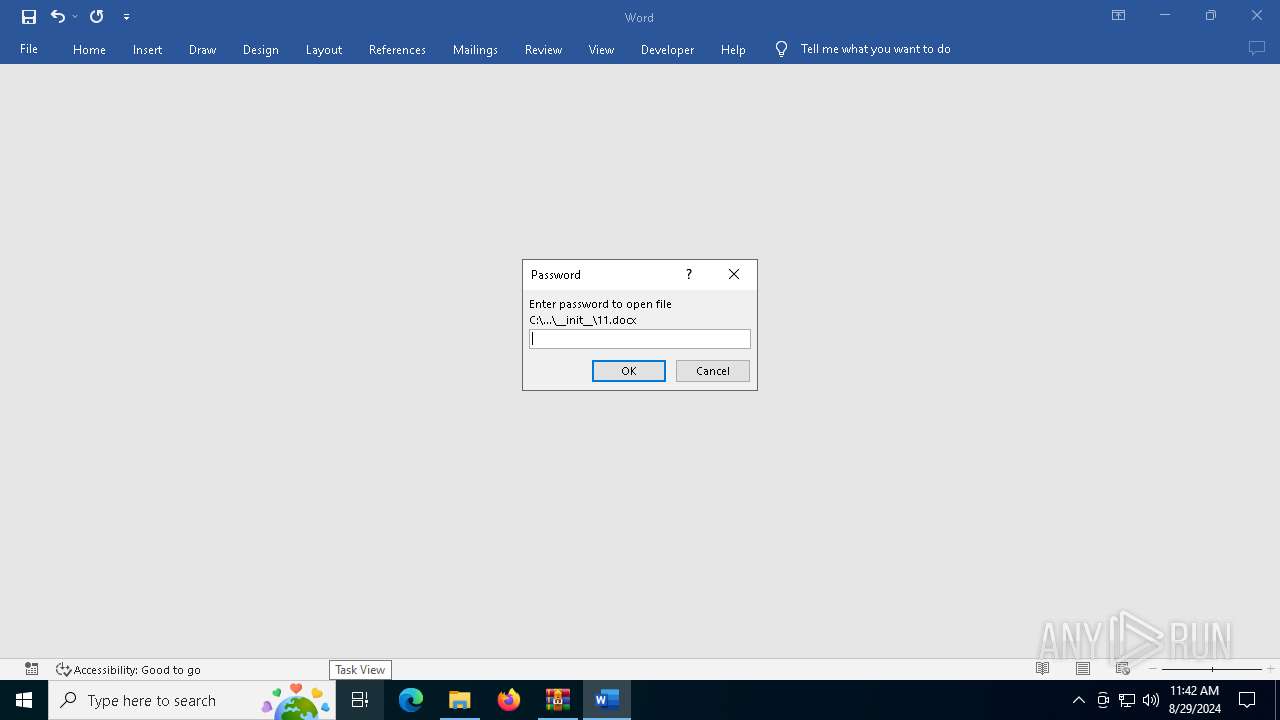
Suspicious WINWORD start
- WINWORD.EXE (PID: 6956)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 7164)
- cmd.exe (PID: 4760)
- WINWORD.EXE (PID: 6956)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7164)
Manual execution by a user
- ftp.exe (PID: 2136)
Reads the machine GUID from the registry
- pythonw.exe (PID: 6876)
Checks supported languages
- pythonw.exe (PID: 6876)
Reads the computer name
- pythonw.exe (PID: 6876)
Checks proxy server information
- pythonw.exe (PID: 6876)
- slui.exe (PID: 4276)
Reads the software policy settings
- slui.exe (PID: 5988)
- slui.exe (PID: 4276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
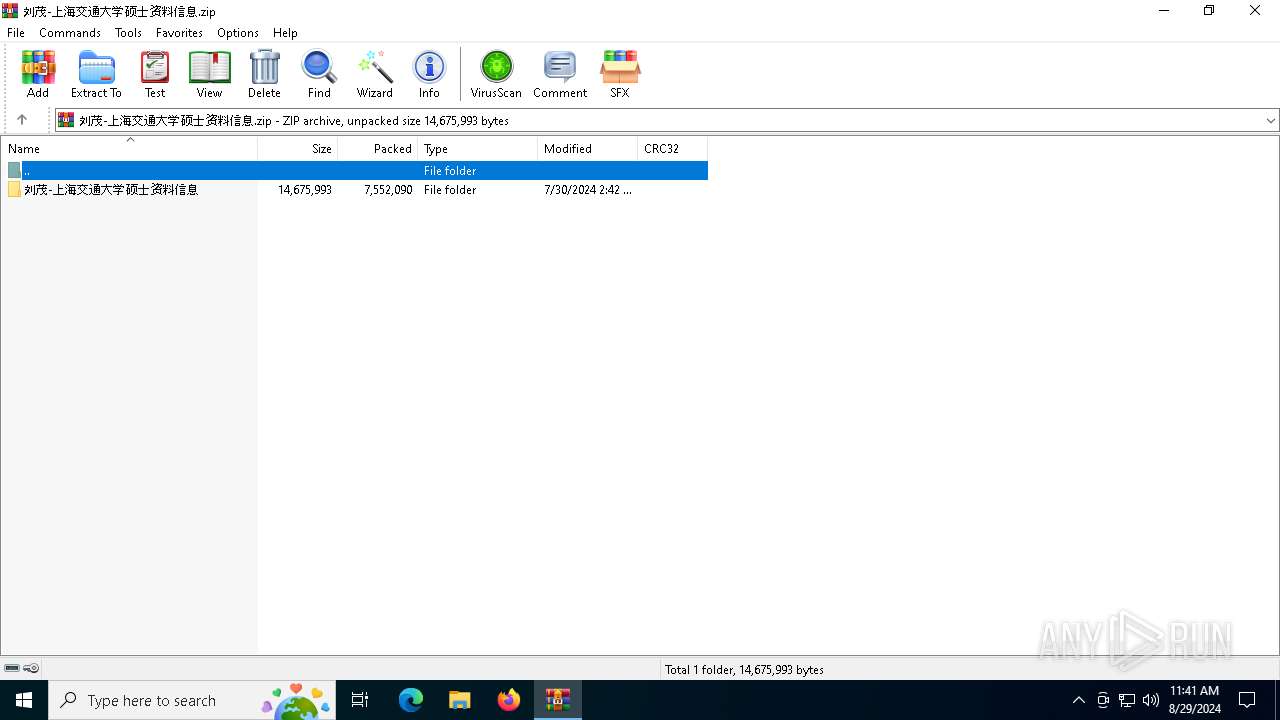
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:07:30 10:42:00 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | ??ï-?Ϻ???ͨ??ѧ˶ʿ??????Ϣ/ |
Total processes
142
Monitored processes
12
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2132 | C:\WINDOWS\system32\cmd.exe /C start /b __init__\pythonw.exe __init__\main.pyw | C:\Windows\System32\cmd.exe | — | ftp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\Windows\System32\ftp.exe" -""s:__init__\WeChatWin.dll | C:\Windows\System32\ftp.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File Transfer Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4276 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4760 | C:\WINDOWS\system32\cmd.exe /C start /b __init__\11.docx | C:\Windows\System32\cmd.exe | — | ftp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5988 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6444 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ftp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6648 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6876 | __init__\pythonw.exe __init__\main.pyw | C:\Users\admin\Desktop\刘茂-上海交通大学硕士资料信息\__init__\pythonw.exe | cmd.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 1 Version: 3.7.5rc1 Modules
| |||||||||||||||
| 6884 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 802
Read events
14 530
Write events
264
Delete events
8
Modification events
| (PID) Process: | (7164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (7164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (7164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (7164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\刘茂-上海交通大学硕士资料信息.zip | |||
| (PID) Process: | (7164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4760) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.docx\OpenWithProgids |
| Operation: | write | Name: | Word.Document.12 |
Value: | |||
| (PID) Process: | (4760) cmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Microsoft Office\Root\VFS\ProgramFilesCommonX64\Microsoft Shared\Office16\oregres.dll,-3 |
Value: &Open | |||
Executable files
26
Suspicious files
10
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7164.3212\刘茂-上海交通大学硕士资料信息\__init__\libssl-1_1.dll | executable | |
MD5:FE1F3632AF98E7B7A2799E3973BA03CF | SHA256:1CE7BA99E817C1C2D71BC88A1BDD6FCAD82AA5C3E519B91EBD56C96F22E3543B | |||
| 7164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7164.3212\刘茂-上海交通大学硕士资料信息\__init__\11.docx | binary | |
MD5:B93AAA92DFEE1E8C7083AE7EBF3E69BA | SHA256:EE336B4F788842D2E7F922D64D8CF5E36A35C8B3BF053FD5542493E8F15AFCCC | |||
| 7164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7164.3212\刘茂-上海交通大学硕士资料信息\__init__\main.pyw | text | |
MD5:3DDA327D22AFC76A74B1EF93C553596B | SHA256:318166BD6F42CD542DD9FD5357A2C767CA695A8BBF944BA3851B1D1D95D6B3ED | |||
| 7164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7164.3212\刘茂-上海交通大学硕士资料信息\__init__\vcruntime140.dll | executable | |
MD5:0C583614EB8FFB4C8C2D9E9880220F1D | SHA256:6CADB4FEF773C23B511ACC8B715A084815C6E41DD8C694BC70090A97B3B03FB9 | |||
| 7164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7164.3212\刘茂-上海交通大学硕士资料信息\__init__\new 1.py | text | |
MD5:2A6318E0772D6FC62576CE12F5C46741 | SHA256:7E64FF1F3822F8E7822E63BFFAC7DFC92B3A3E16513AE27AA19F3E2D0E2217F2 | |||
| 7164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7164.3212\刘茂-上海交通大学硕士资料信息\__init__\WeChatWin.dll | text | |
MD5:C39D2B20314263B831CD0256ADC72058 | SHA256:66A3F4BADD04A0287E196F93FECAC50DA9475F176FB8D59EE55E4D2F4371199B | |||
| 7164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7164.3212\刘茂-上海交通大学硕士资料信息\__init__\pythonw.exe | executable | |
MD5:5A4477CA24D6C51E061BE2F8FD7FCC5A | SHA256:7C0C039F8EF7BA13A68334EF7FD5F8922AB21E5BD43A52EBBA5750A7D7F9358E | |||
| 7164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7164.3212\刘茂-上海交通大学硕士资料信息\__init__\pyexpat.pyd | executable | |
MD5:33B1AB9A8D925F41F409233499BBBAF7 | SHA256:946F8E40FD4A8AF4F2758AB599703D8659FFB049F7F631B9C8CA95625F1F7785 | |||
| 7164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7164.3212\刘茂-上海交通大学硕士资料信息\__init__\main.py | text | |
MD5:3DDA327D22AFC76A74B1EF93C553596B | SHA256:318166BD6F42CD542DD9FD5357A2C767CA695A8BBF944BA3851B1D1D95D6B3ED | |||
| 7164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7164.3212\刘茂-上海交通大学硕士资料信息\__init__\select.pyd | executable | |
MD5:57F9F839BD4A751A236E6526EF8AEBA6 | SHA256:119CAB3BAD47EADBAFB9E8B0BD456A514FE85FB3A278B48295DF9569D94B0703 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
35
DNS requests
21
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1776 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6956 | WINWORD.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
2700 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2700 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
608 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6264 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
608 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6876 | pythonw.exe | 118.31.219.202:443 | kuulzx6ba7l.oss-cn-hangzhou.aliyuncs.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
1776 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1776 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
kuulzx6ba7l.oss-cn-hangzhou.aliyuncs.com |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6876 | pythonw.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
1 ETPRO signatures available at the full report