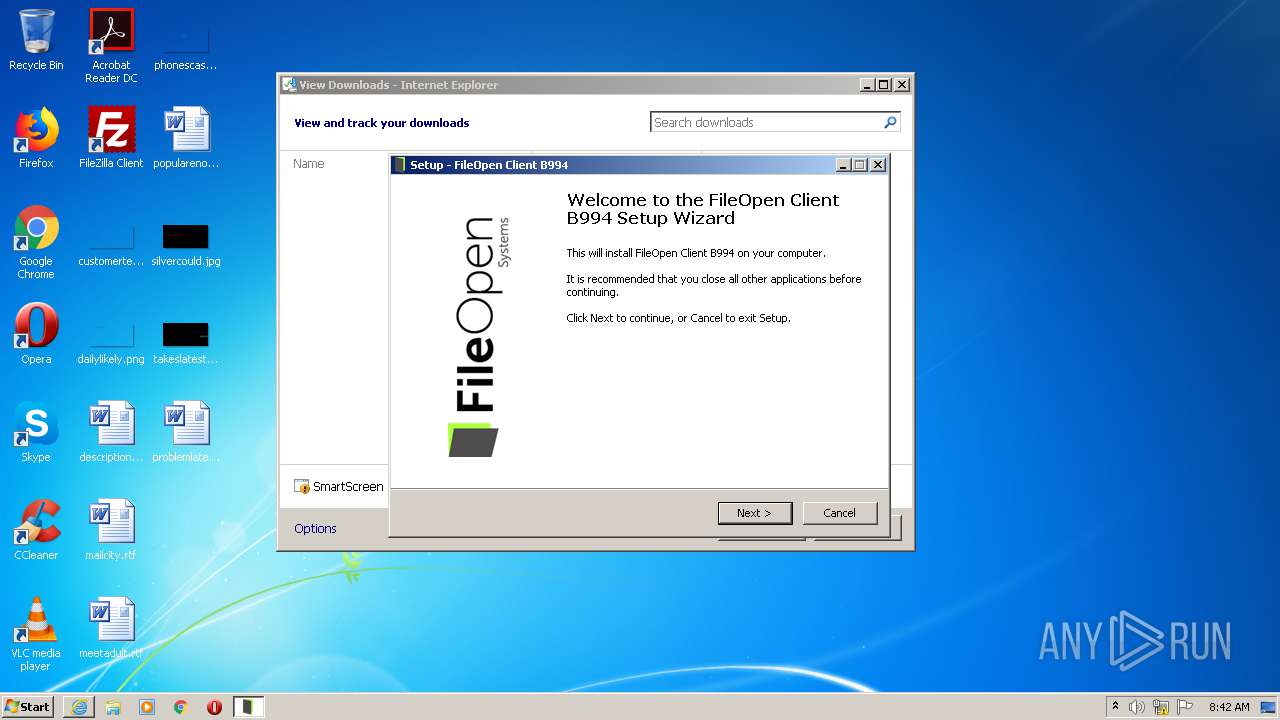
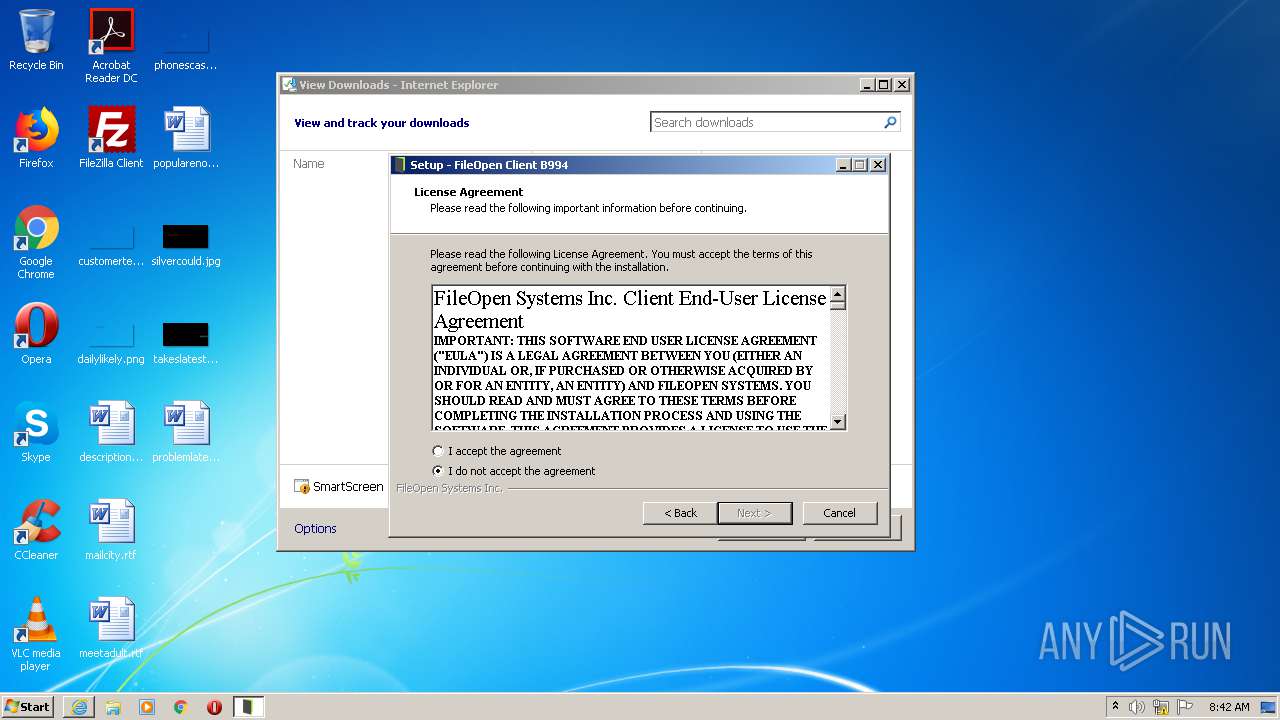
| URL: | https://plugin.fileopen.com/current/FileOpenInstaller.exe |
| Full analysis: | https://app.any.run/tasks/09f40fda-5dd2-4c1b-a7d1-30539d8d401e |
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2020, 08:41:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EDAEB3738A26998BC3358FDF12CA4709 |
| SHA1: | E62F8AAD619534AF319278424743DD499E070854 |
| SHA256: | 7933129C22CEFE786E6B28C4A01C4DAF87300C9C616EFD4B2771649546B05887 |
| SSDEEP: | 3:N8NXKLQJN7dQiJyYZOXLNn:2BQU7dOAOXLN |
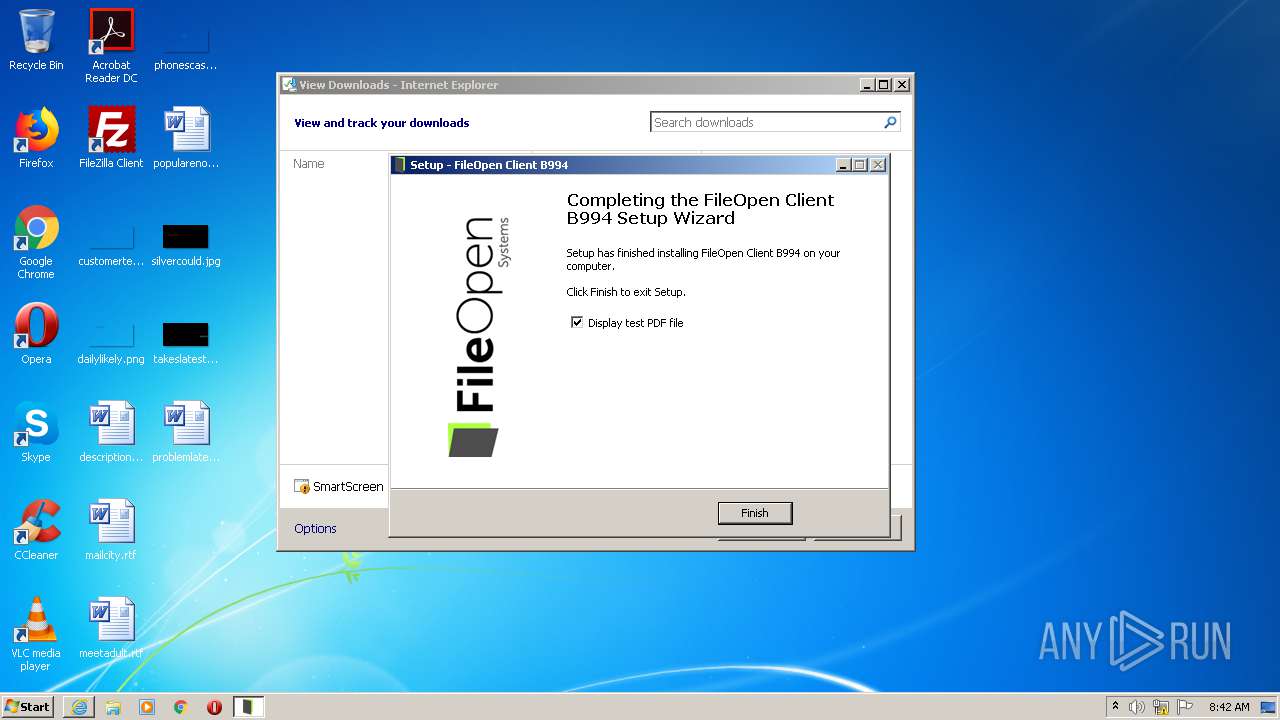
MALICIOUS
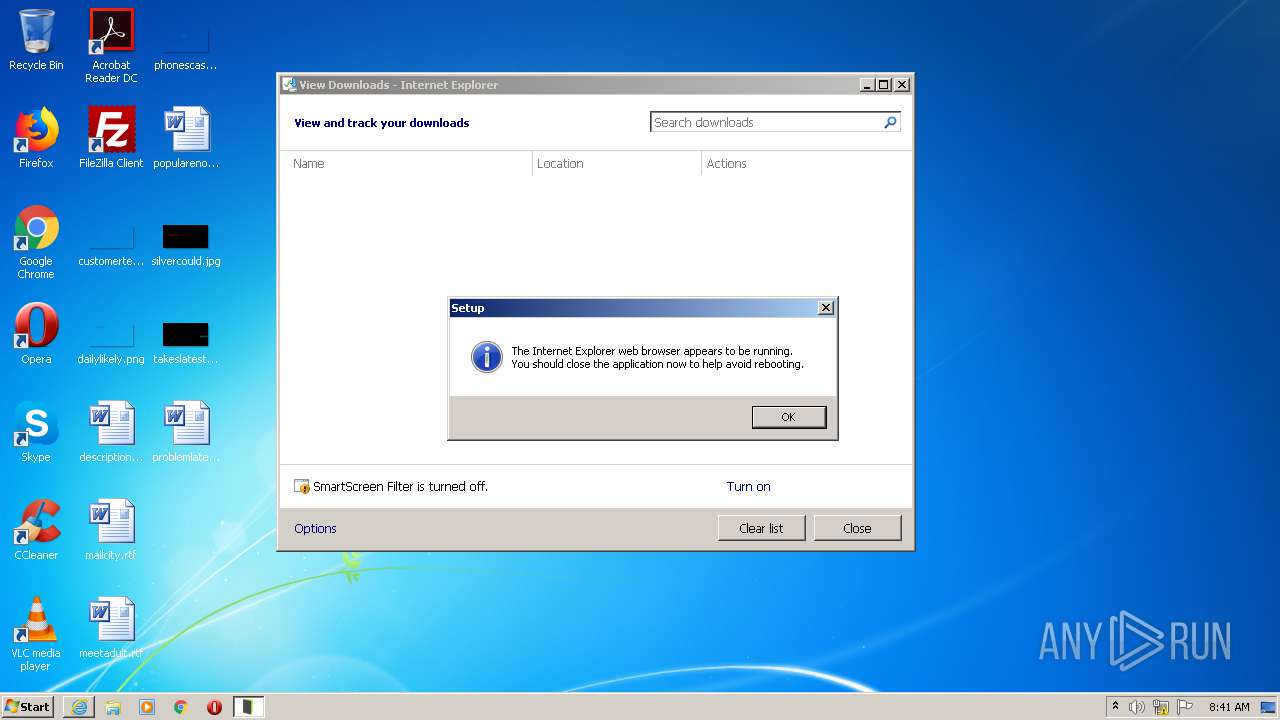
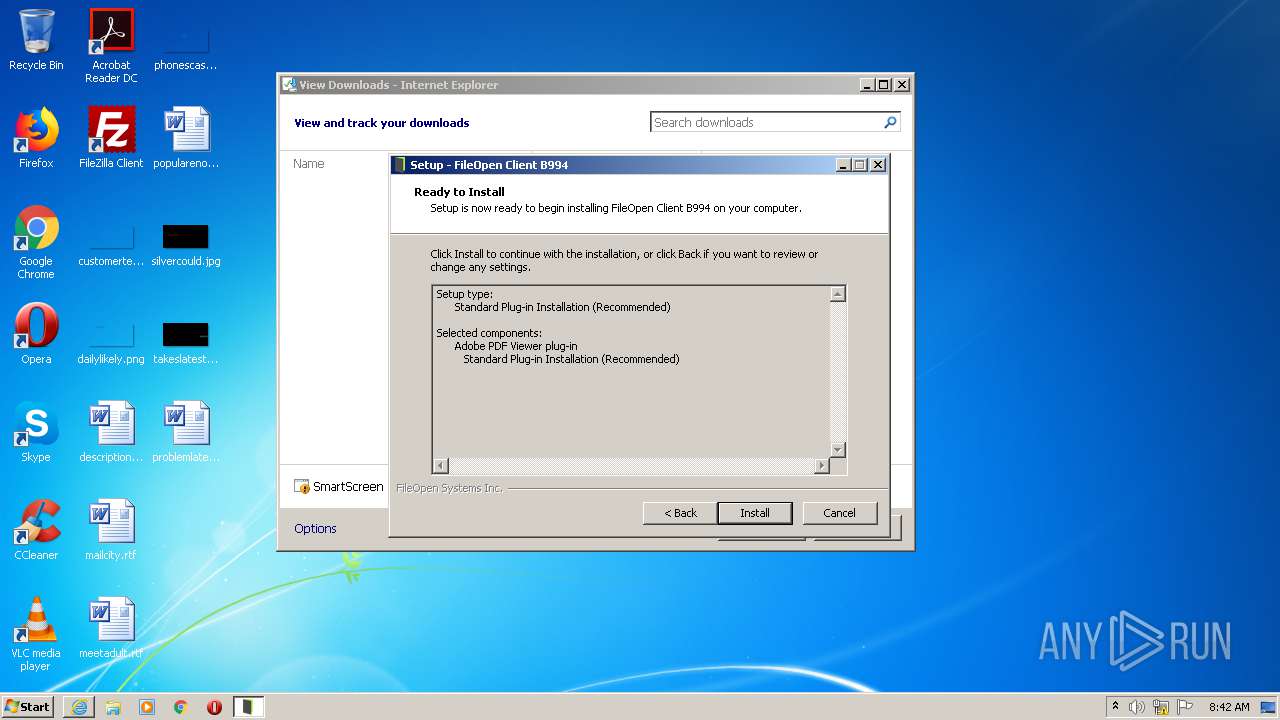
Drops executable file immediately after starts
- FileOpenInstaller.exe (PID: 2552)
- FileOpenInstaller.exe (PID: 2308)
- FileOpenInstaller.tmp (PID: 2720)
Application was dropped or rewritten from another process
- FileOpenInstaller.exe (PID: 2552)
- FileOpenInstaller.exe (PID: 2308)
- FileOpenBroker32.exe (PID: 1860)
- FileOpenManager32.exe (PID: 604)
Changes the autorun value in the registry
- FileOpenInstaller.tmp (PID: 2720)
Loads dropped or rewritten executable
- AcroRd32.exe (PID: 3644)
SUSPICIOUS
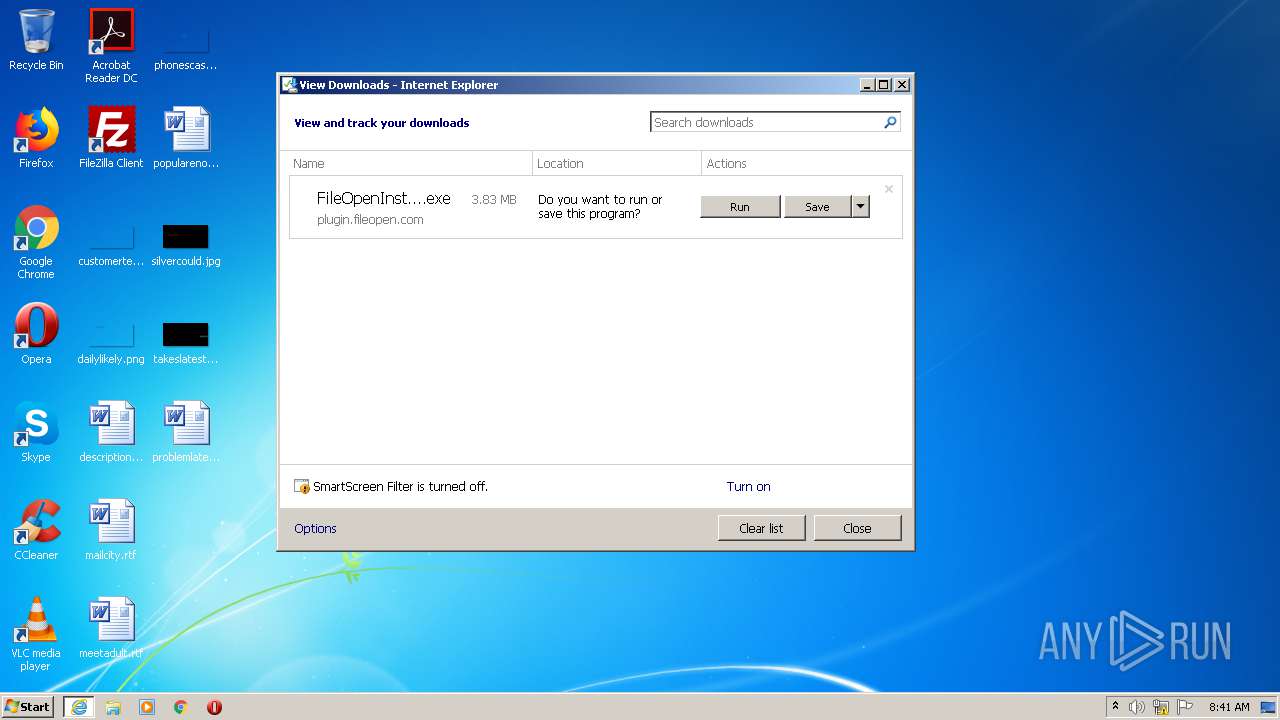
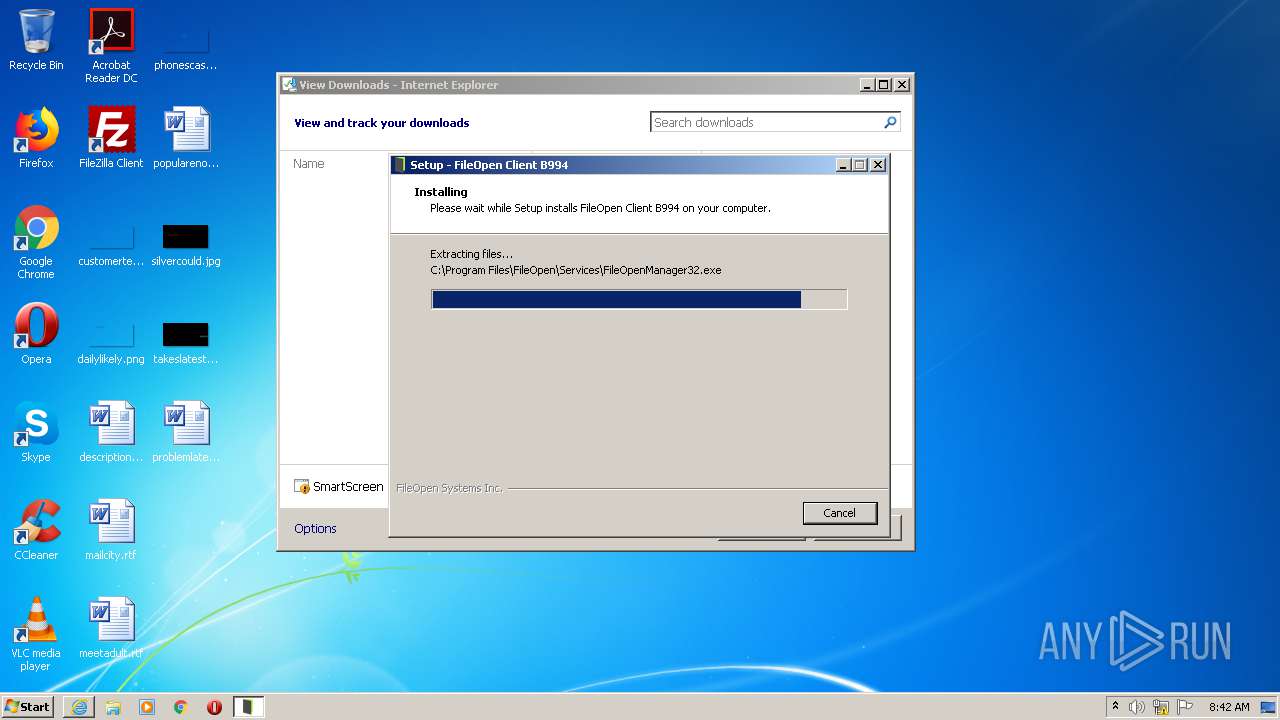
Executable content was dropped or overwritten
- iexplore.exe (PID: 2700)
- iexplore.exe (PID: 2592)
- FileOpenInstaller.exe (PID: 2308)
- FileOpenInstaller.tmp (PID: 2720)
- FileOpenInstaller.exe (PID: 2552)
Reads the Windows organization settings
- FileOpenInstaller.tmp (PID: 2720)
Reads Windows owner or organization settings
- FileOpenInstaller.tmp (PID: 2720)
Creates or modifies windows services
- FileOpenManager32.exe (PID: 604)
Starts SC.EXE for service management
- FileOpenInstaller.tmp (PID: 2720)
Executed as Windows Service
- FileOpenManager32.exe (PID: 604)
Drops a file that was compiled in debug mode
- FileOpenInstaller.tmp (PID: 2720)
Creates a directory in Program Files
- FileOpenInstaller.tmp (PID: 2720)
Creates files in the user directory
- FileOpenBroker32.exe (PID: 1860)
INFO
Modifies the phishing filter of IE
- iexplore.exe (PID: 2700)
Application launched itself
- iexplore.exe (PID: 2700)
- RdrCEF.exe (PID: 3288)
- AcroRd32.exe (PID: 2368)
Changes internet zones settings
- iexplore.exe (PID: 2700)
Reads settings of System Certificates
- iexplore.exe (PID: 2700)
- FileOpenBroker32.exe (PID: 1860)
Changes settings of System certificates
- iexplore.exe (PID: 2700)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2700)
Application was dropped or rewritten from another process
- FileOpenInstaller.tmp (PID: 2720)
- FileOpenInstaller.tmp (PID: 2264)
Creates files in the program directory
- FileOpenInstaller.tmp (PID: 2720)
Creates a software uninstall entry
- FileOpenInstaller.tmp (PID: 2720)
Loads dropped or rewritten executable
- FileOpenInstaller.tmp (PID: 2720)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 2368)
Reads the hosts file
- RdrCEF.exe (PID: 3288)
Creates files in the user directory
- AcroRd32.exe (PID: 2368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
16
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Program Files\FileOpen\Services\FileOpenManager32.exe" | C:\Program Files\FileOpen\Services\FileOpenManager32.exe | — | services.exe | |||||||||||
User: SYSTEM Company: FileOpen Systems Inc. Integrity Level: SYSTEM Description: FileOpen Client - Manager Service Exit code: 0 Version: 19.4.1.16 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3288.1.844659969\748309332" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\FileOpen\Services\FileOpenBroker32.exe" | C:\Program Files\FileOpen\Services\FileOpenBroker32.exe | FileOpenInstaller.tmp | ||||||||||||
User: admin Company: FileOpen Systems Inc. Integrity Level: MEDIUM Description: FileOpen Client - Broker Exit code: 0 Version: 19.4.1.16 Modules
| |||||||||||||||
| 2264 | "C:\Users\admin\AppData\Local\Temp\is-JITQ2.tmp\FileOpenInstaller.tmp" /SL5="$20194,3581517,662016,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\FileOpenInstaller.exe" | C:\Users\admin\AppData\Local\Temp\is-JITQ2.tmp\FileOpenInstaller.tmp | — | FileOpenInstaller.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2308 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\FileOpenInstaller.exe" /SPAWNWND=$2019C /NOTIFYWND=$20194 | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\FileOpenInstaller.exe | FileOpenInstaller.tmp | ||||||||||||
User: admin Company: FileOpen Systems Inc. Integrity Level: HIGH Description: {cm:FileOpenClient} B994 Exit code: 0 Version: 1.0.92.994 Modules
| |||||||||||||||
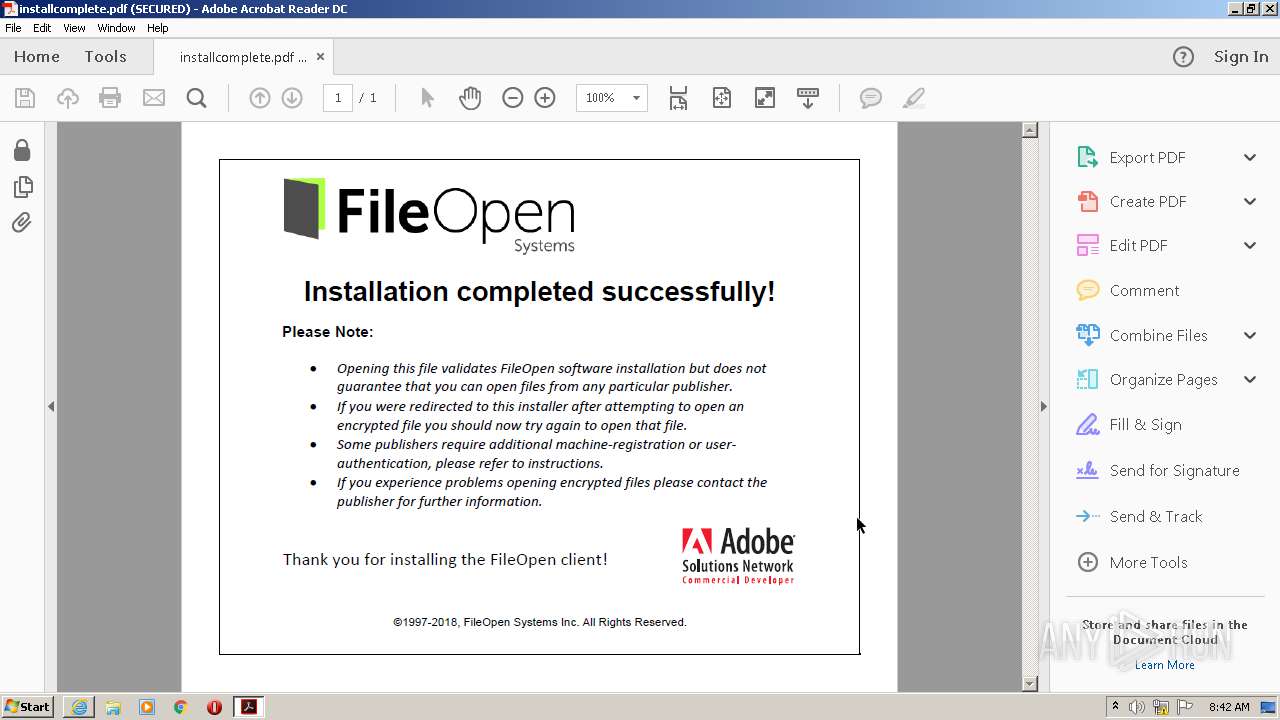
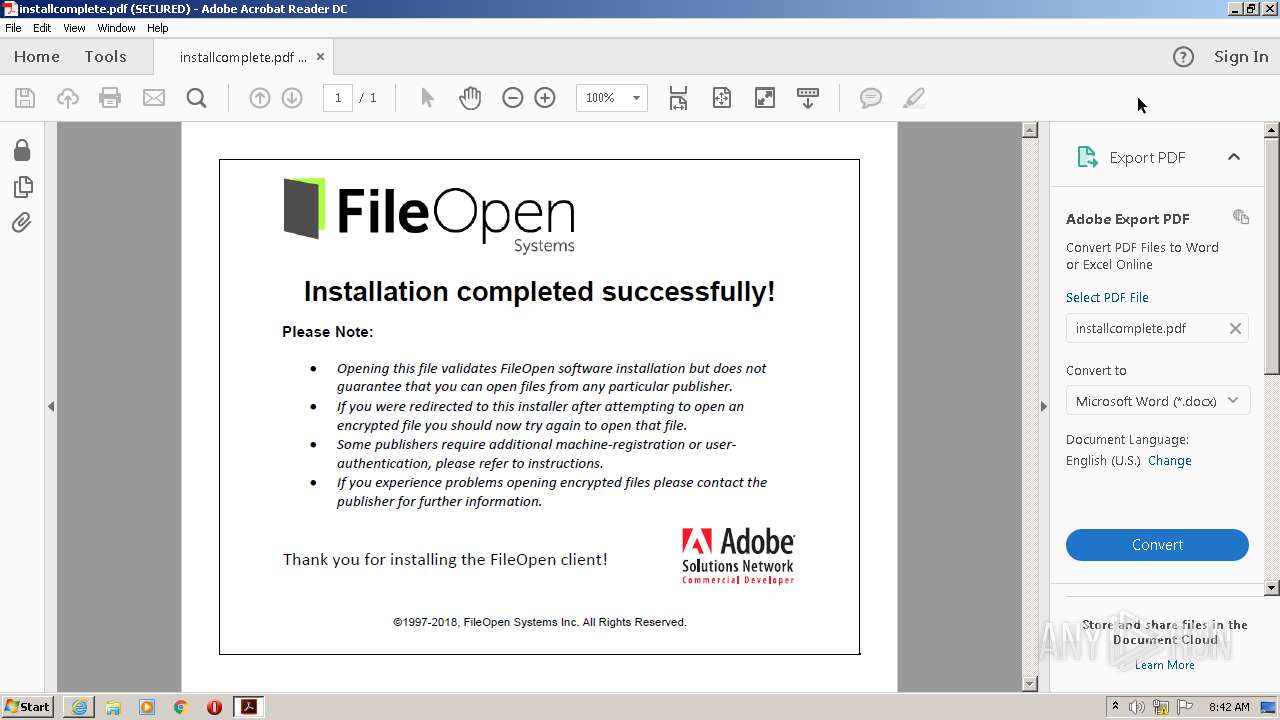
| 2368 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" installcomplete.pdf | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | FileOpenInstaller.tmp | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2512 | "C:\Windows\system32\sc.exe" create FileOpenManager binpath= "\"C:\Program Files\FileOpen\Services\FileOpenManager32.exe\"" start= auto | C:\Windows\system32\sc.exe | — | FileOpenInstaller.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2552 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\FileOpenInstaller.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\FileOpenInstaller.exe | iexplore.exe | ||||||||||||
User: admin Company: FileOpen Systems Inc. Integrity Level: MEDIUM Description: {cm:FileOpenClient} B994 Exit code: 0 Version: 1.0.92.994 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2700 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
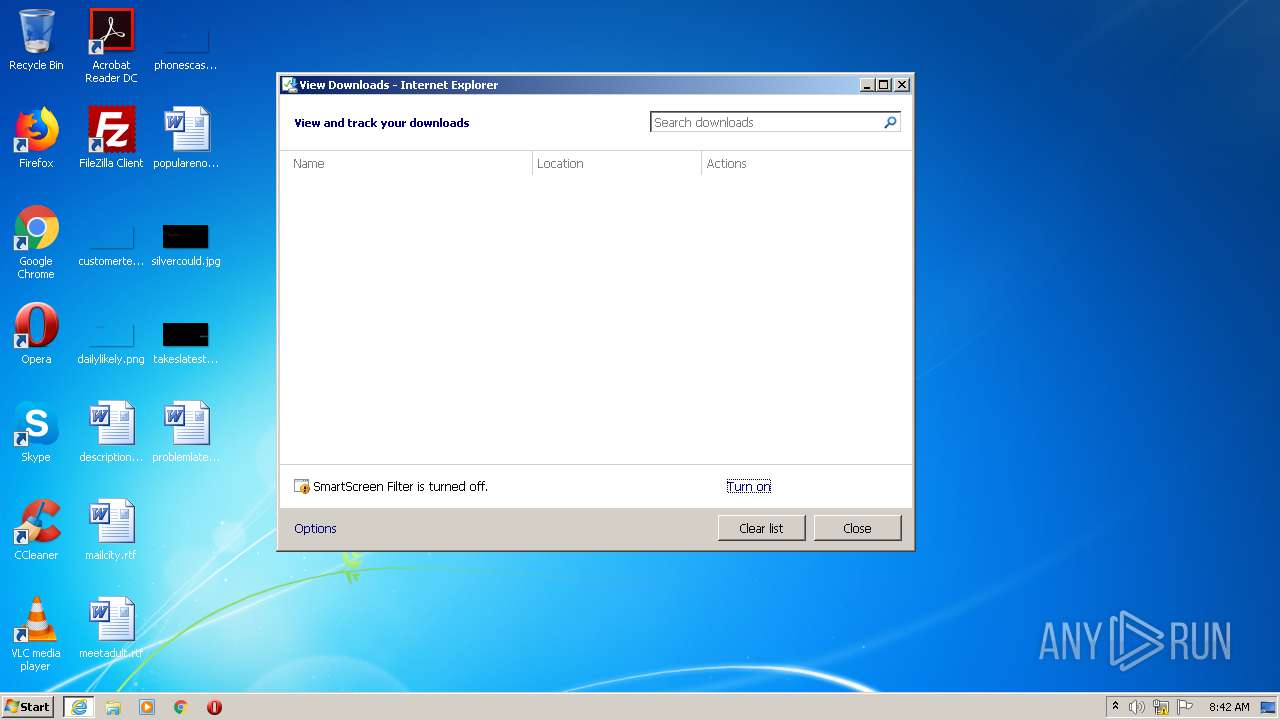
| 2700 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://plugin.fileopen.com/current/FileOpenInstaller.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 303
Read events
1 036
Write events
255
Delete events
12
Modification events
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3043043058 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30852852 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
14
Suspicious files
11
Text files
15
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2592 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2EBA.tmp | — | |
MD5:— | SHA256:— | |||
| 2592 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2EBB.tmp | — | |
MD5:— | SHA256:— | |||
| 2700 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2DDE09BCA344BA8E.TMP | — | |
MD5:— | SHA256:— | |||
| 2700 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\FileOpenInstaller.exe.308l081.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2720 | FileOpenInstaller.tmp | C:\Program Files\FileOpen\is-M00SN.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | FileOpenInstaller.tmp | C:\Program Files\FileOpen\is-UJSHF.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | FileOpenInstaller.tmp | C:\Program Files\FileOpen\examples\is-78B9G.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | FileOpenInstaller.tmp | C:\Program Files\Adobe\Acrobat Reader DC\Reader\plug_ins\is-USJIV.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | FileOpenInstaller.tmp | C:\Program Files\Adobe\Acrobat Reader DC\Reader\plug_ins\is-N0TOF.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | FileOpenInstaller.tmp | C:\Program Files\FileOpen\Services\is-KFS38.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2592 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2592 | iexplore.exe | 64.106.211.88:443 | plugin.fileopen.com | DataPipe, Inc. | US | unknown |
1860 | FileOpenBroker32.exe | 64.106.211.88:443 | plugin.fileopen.com | DataPipe, Inc. | US | unknown |
2592 | iexplore.exe | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
plugin.fileopen.com |
| suspicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
Threats
Process | Message |
|---|---|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - Checking HKEY for SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\AcroRd32.exe
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - Found file: C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - app path search: plug_ins dir = C:\Program Files\Adobe\Acrobat Reader DC\Reader\plug_ins
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - Found version: 15
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - Checking HKEY for SOFTWARE\Adobe\Acrobat Reader\DC\InstallPath
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - install path search: plug_ins dir = C:\Program Files\Adobe\Acrobat Reader DC\Reader\plug_ins
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - Checking HKEY for SOFTWARE\Adobe\Acrobat Reader\2019\InstallPath
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - AcroFind::installpath_search(): The handle is invalid.
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - Checking HKEY for SOFTWARE\Adobe\Acrobat Reader\2018\InstallPath
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - AcroFind::installpath_search(): The handle is invalid.
|