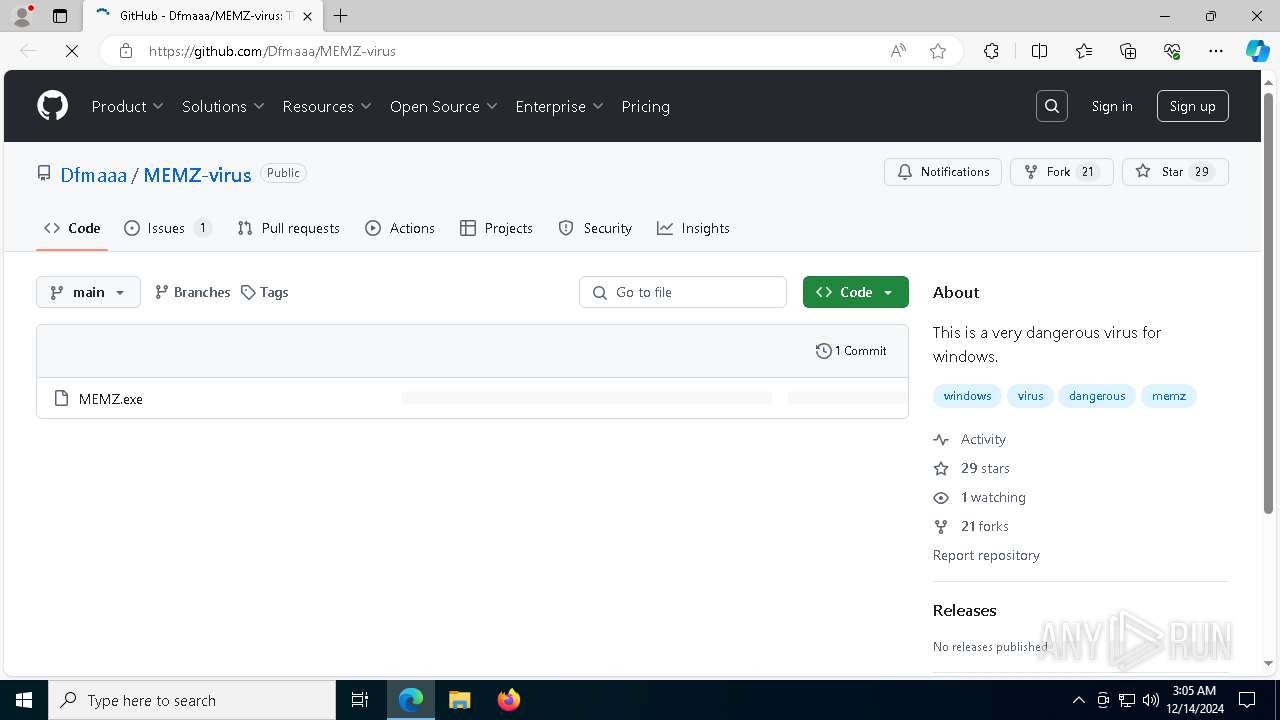
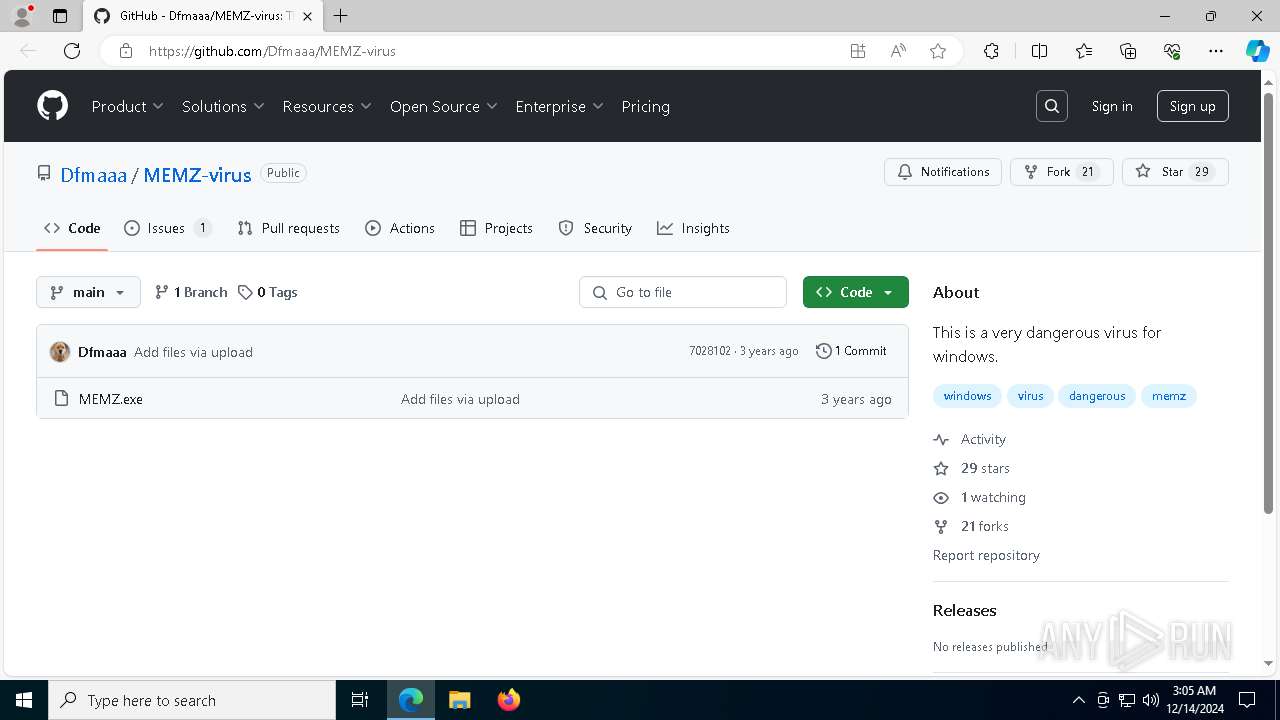
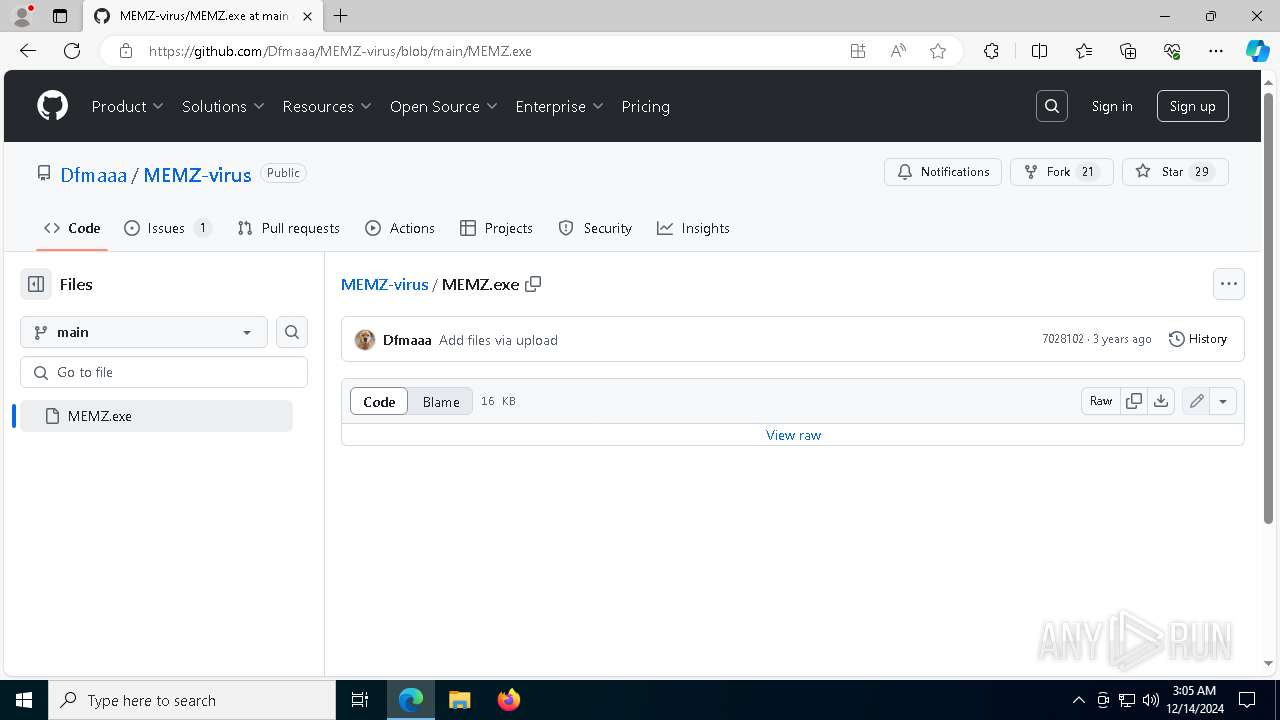
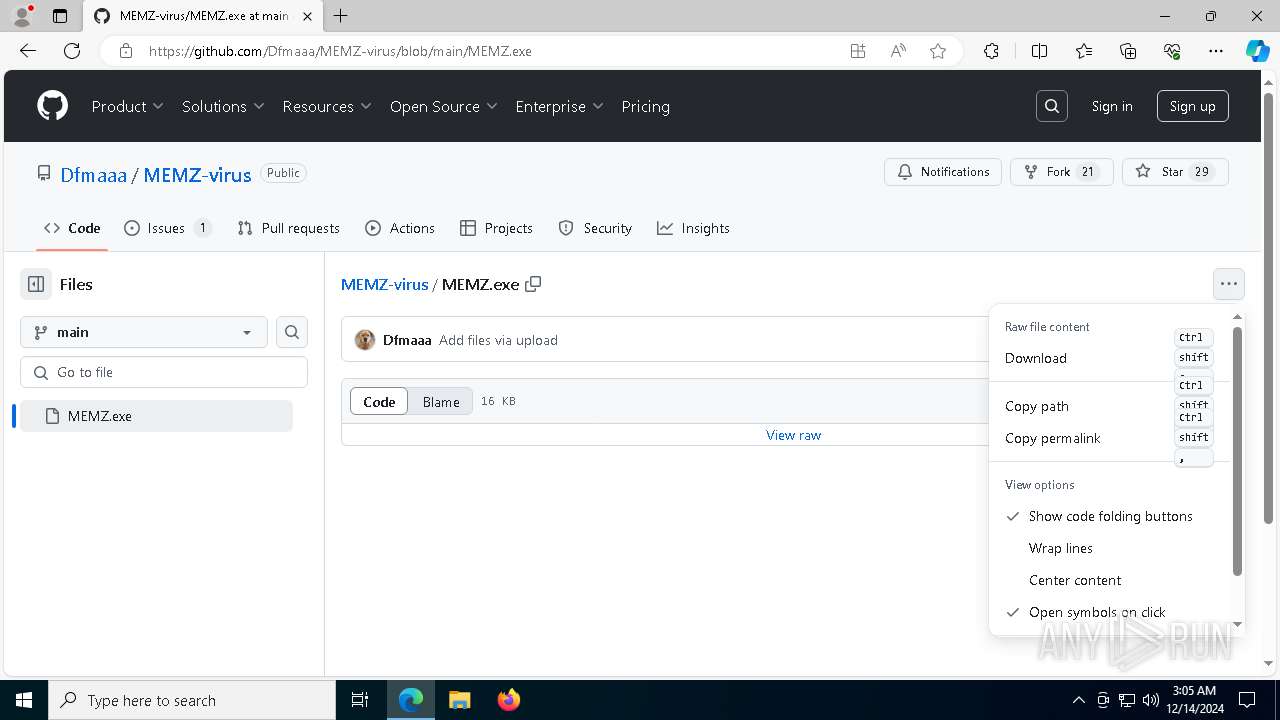
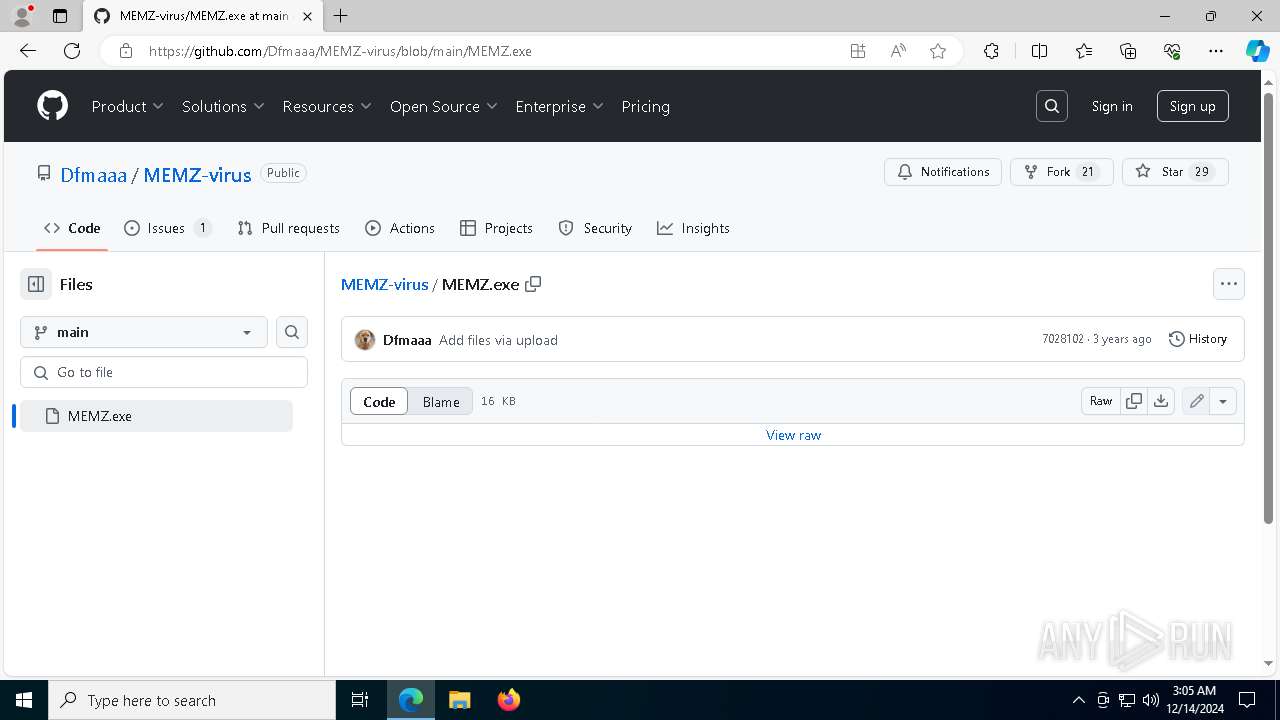
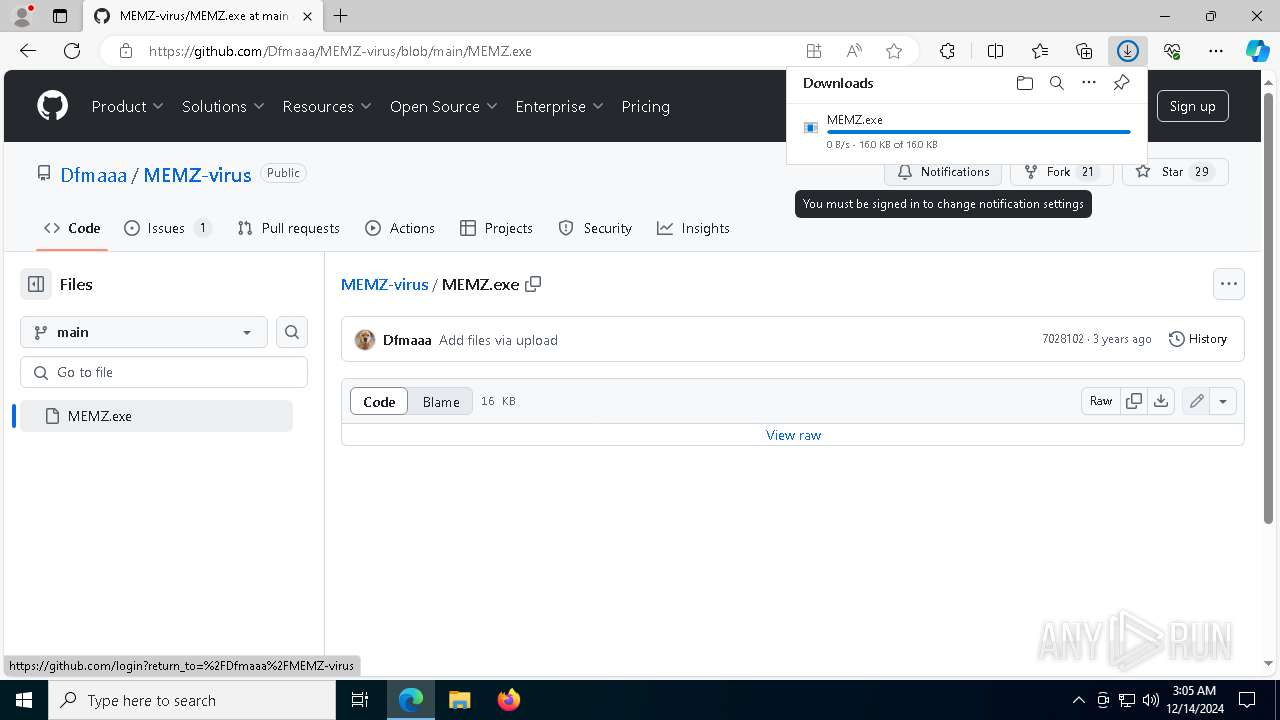
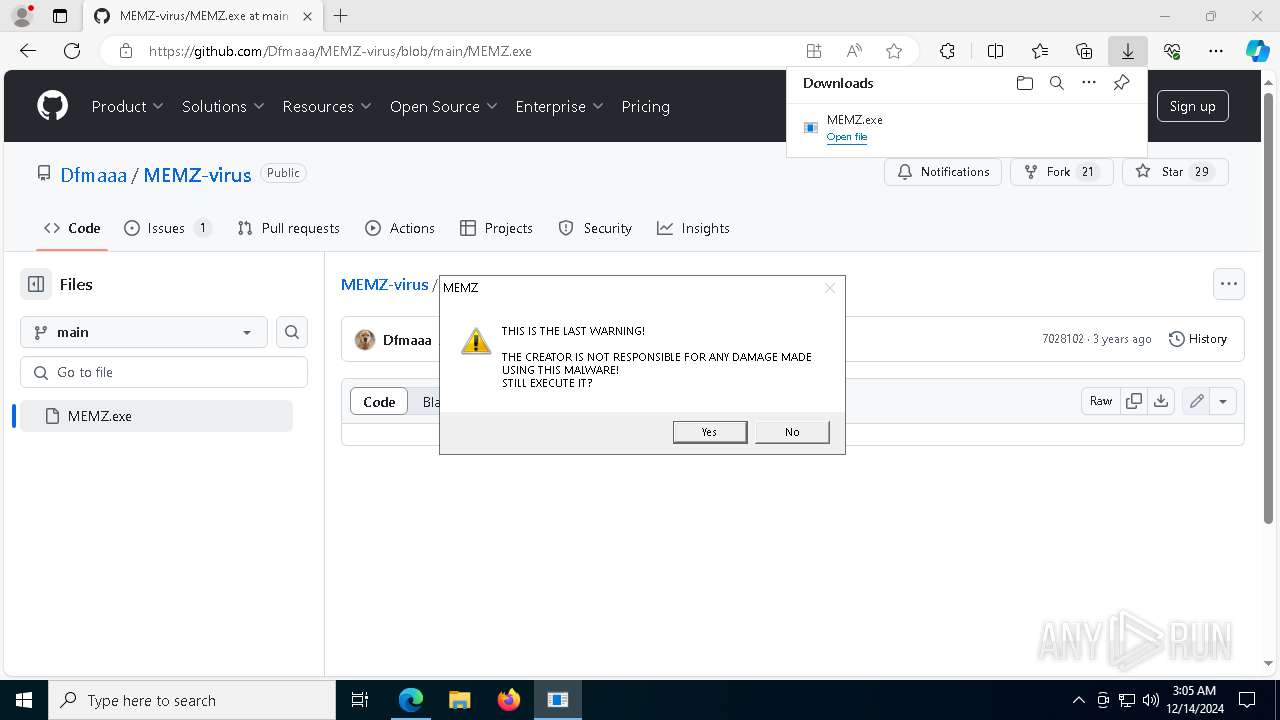
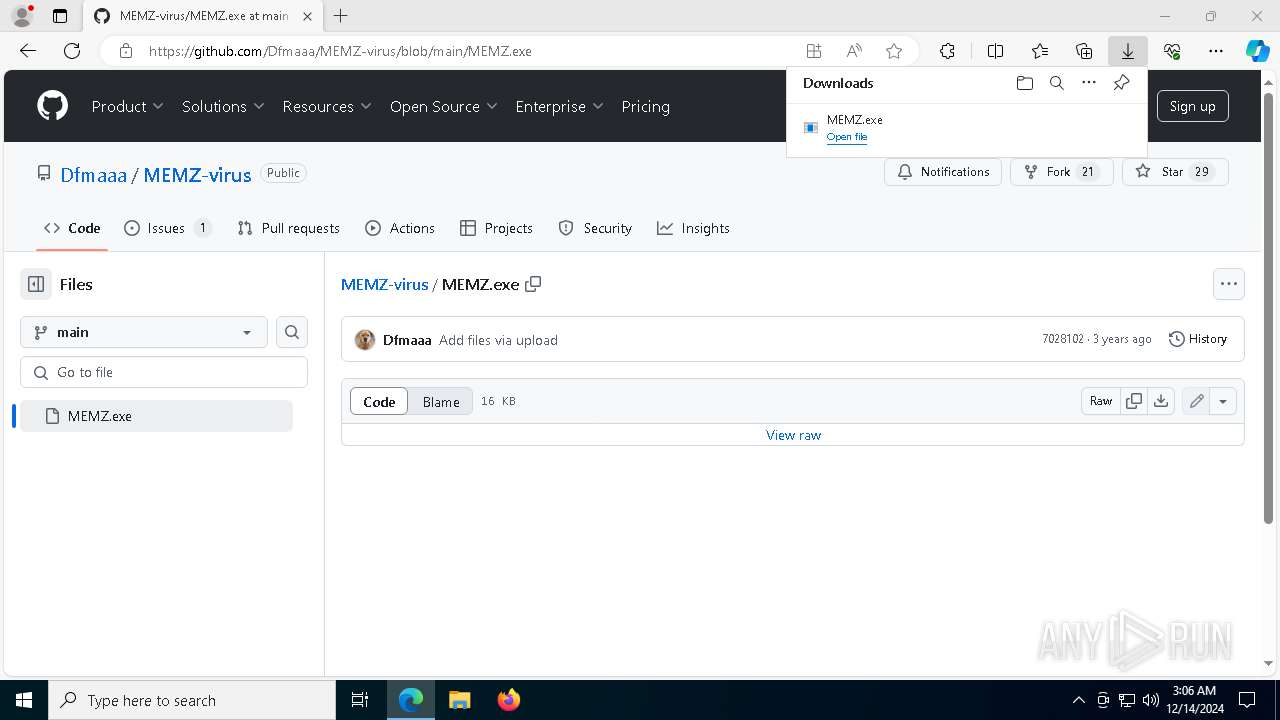
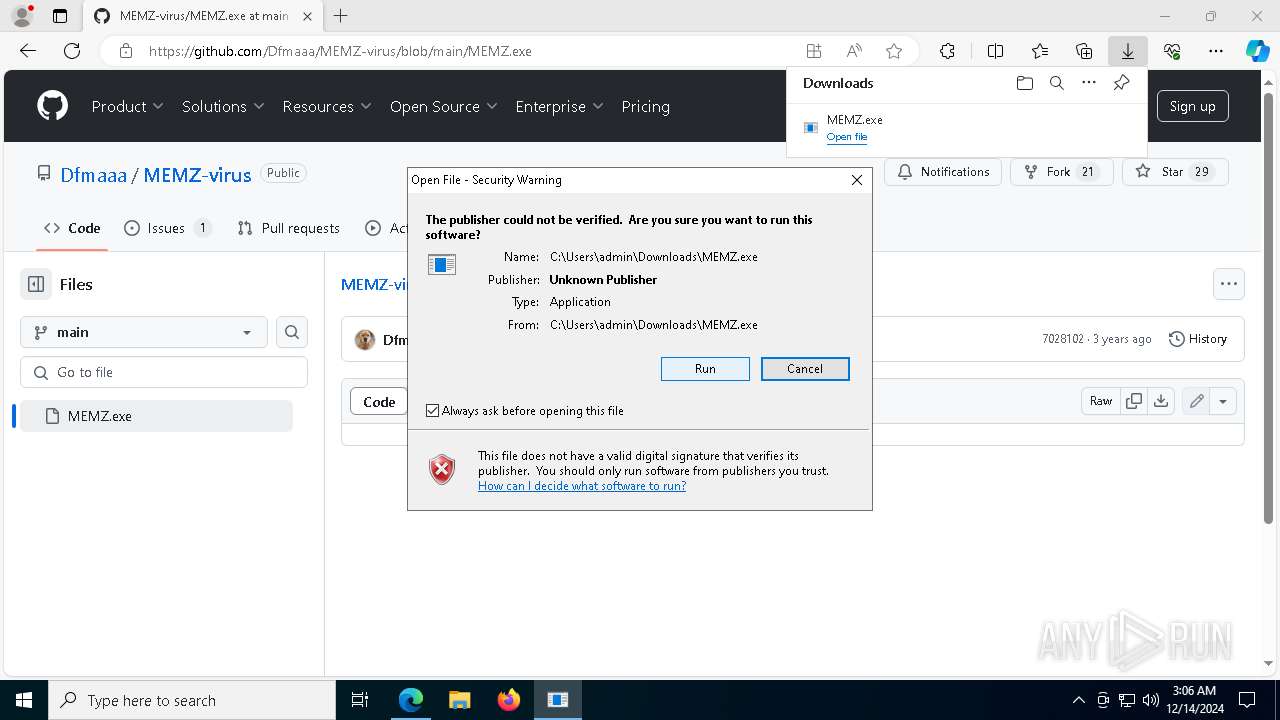
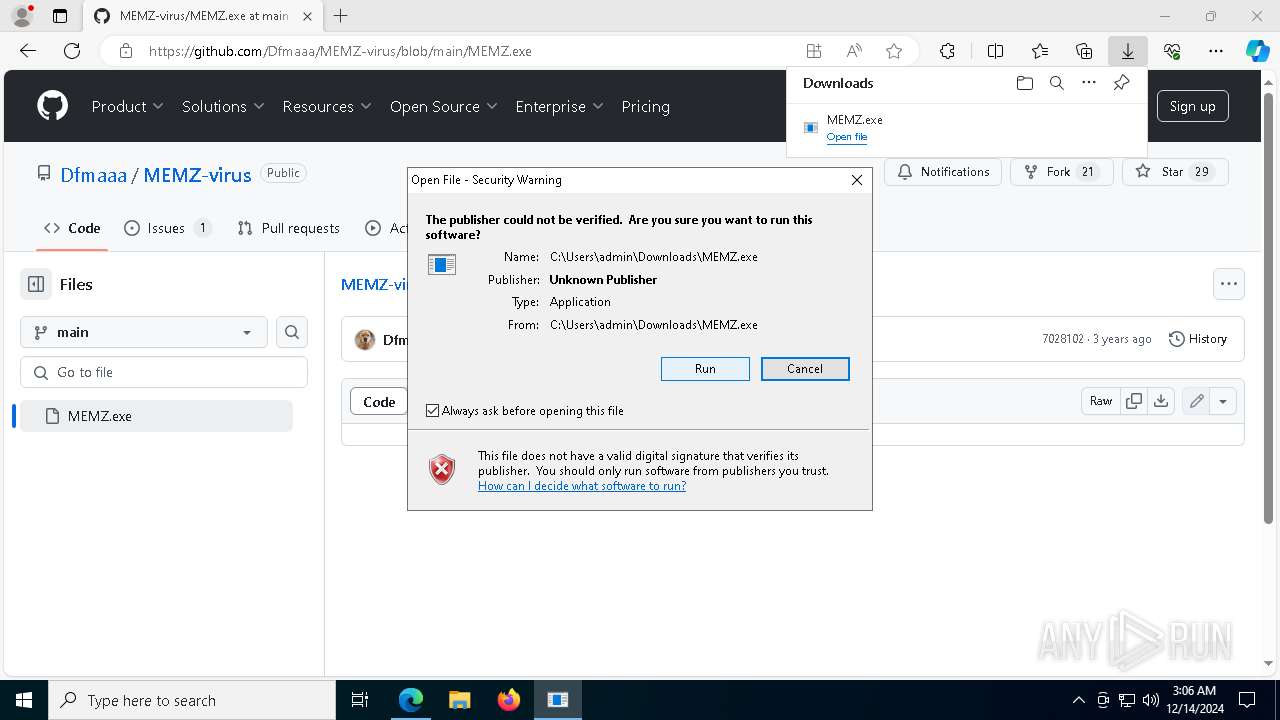
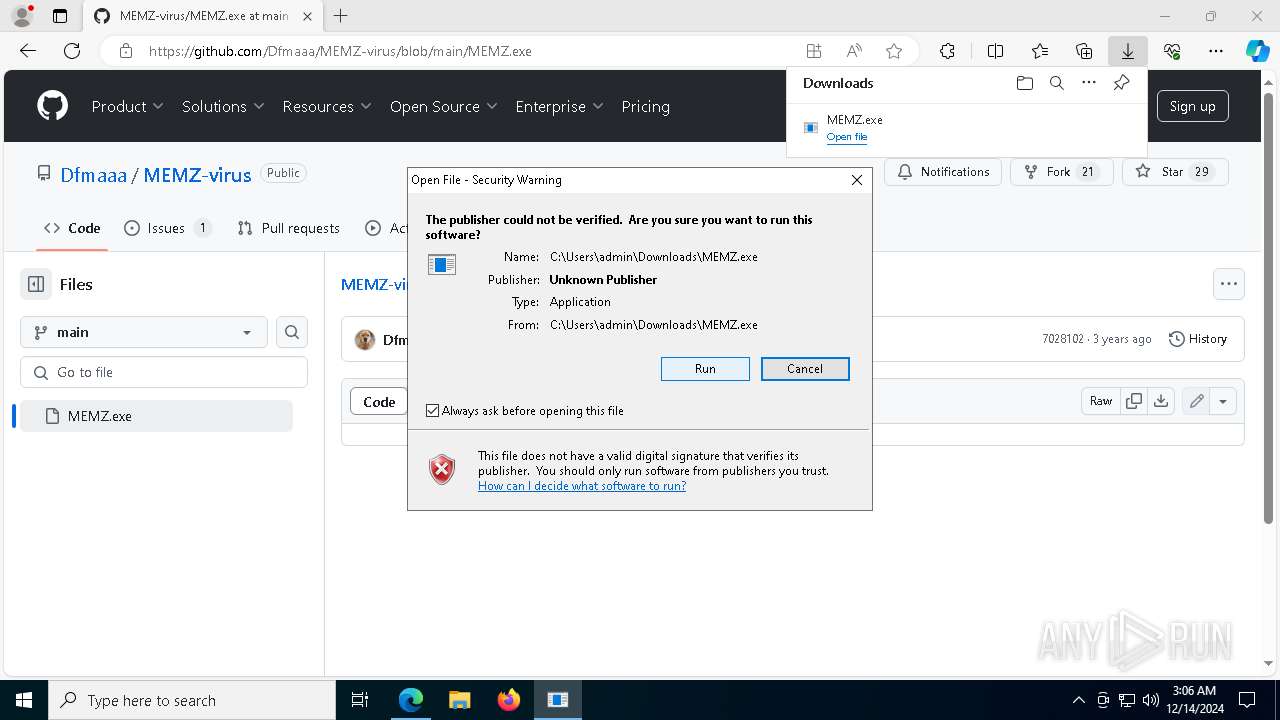
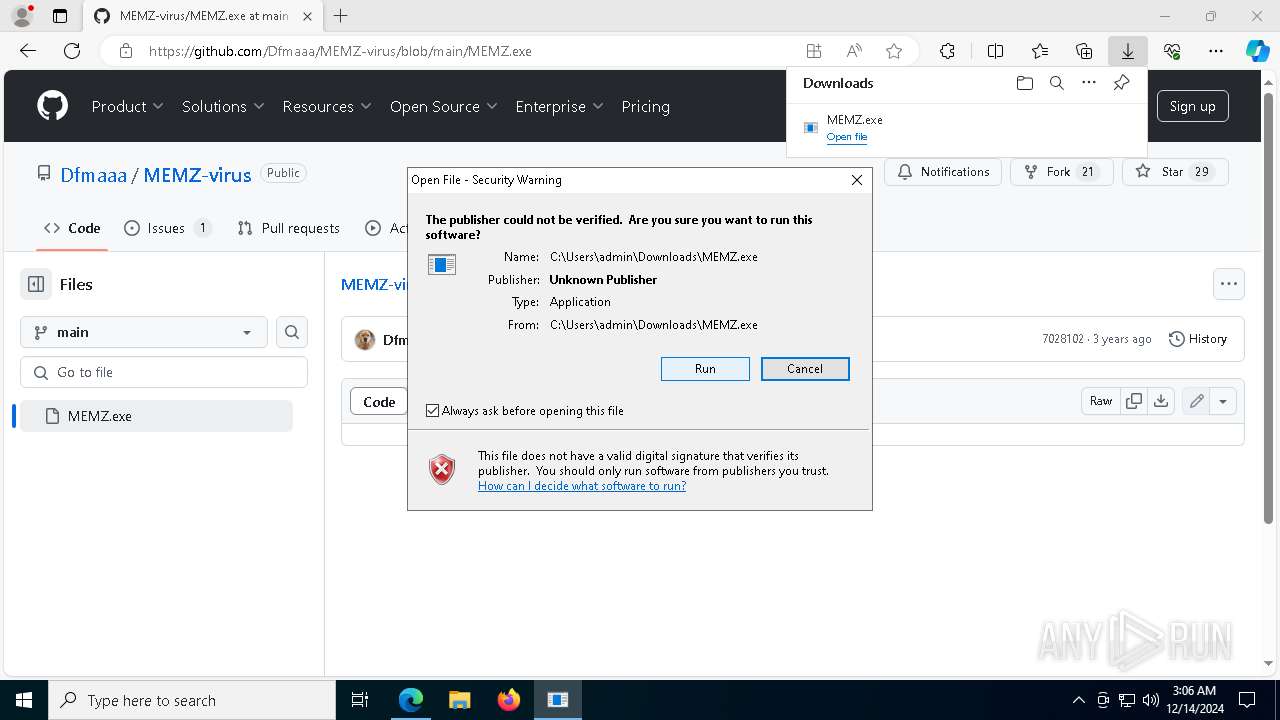
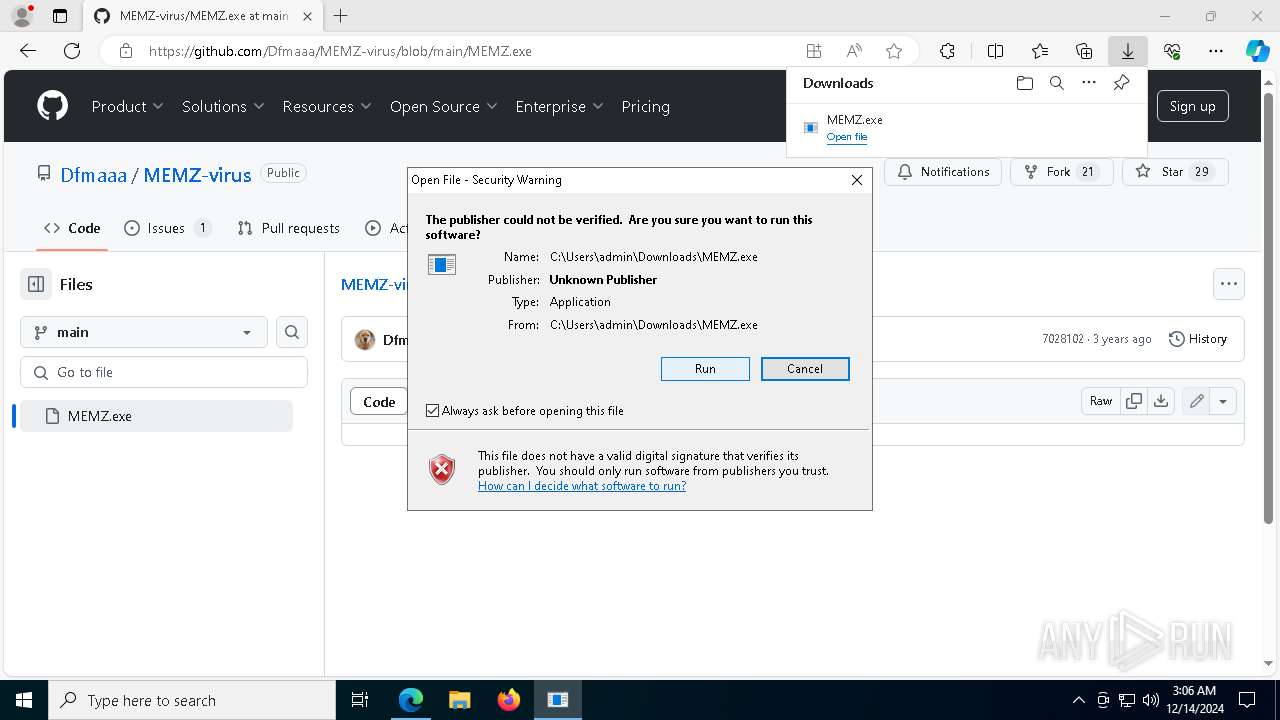
| URL: | https://github.com/Dfmaaa/MEMZ-virus |
| Full analysis: | https://app.any.run/tasks/34188966-7d20-4be2-82e8-b979e4c4cc00 |
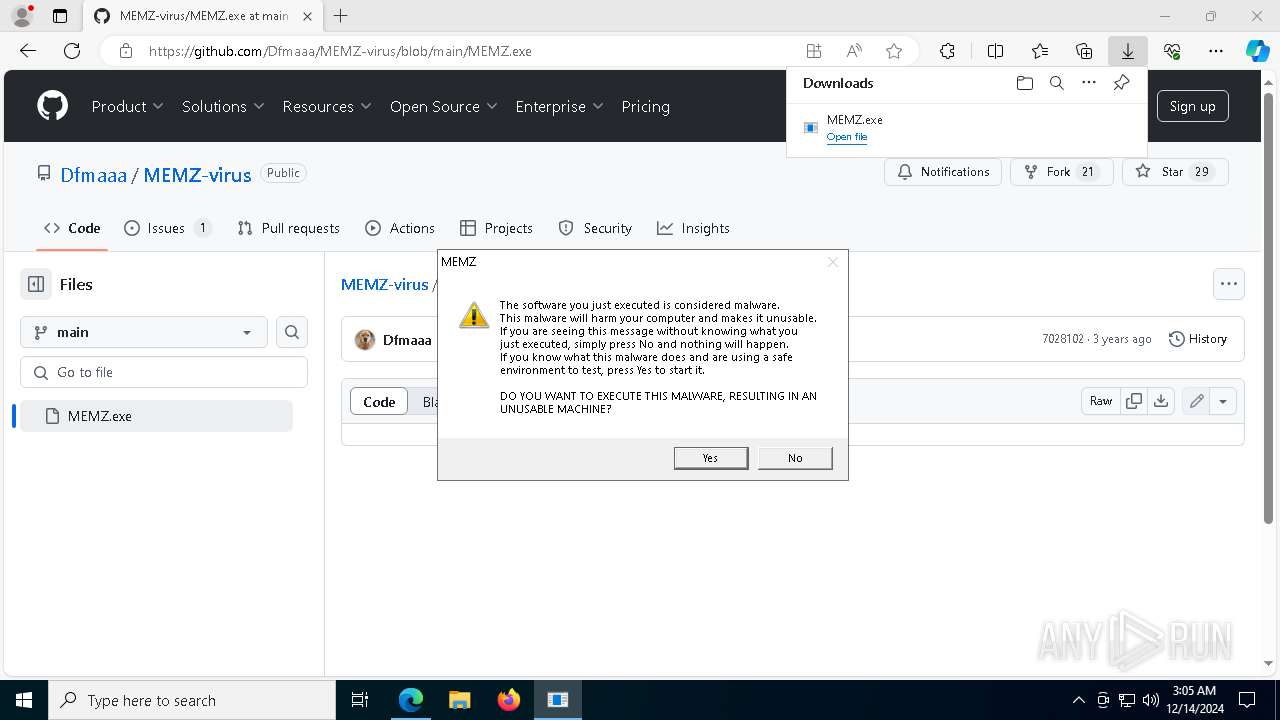
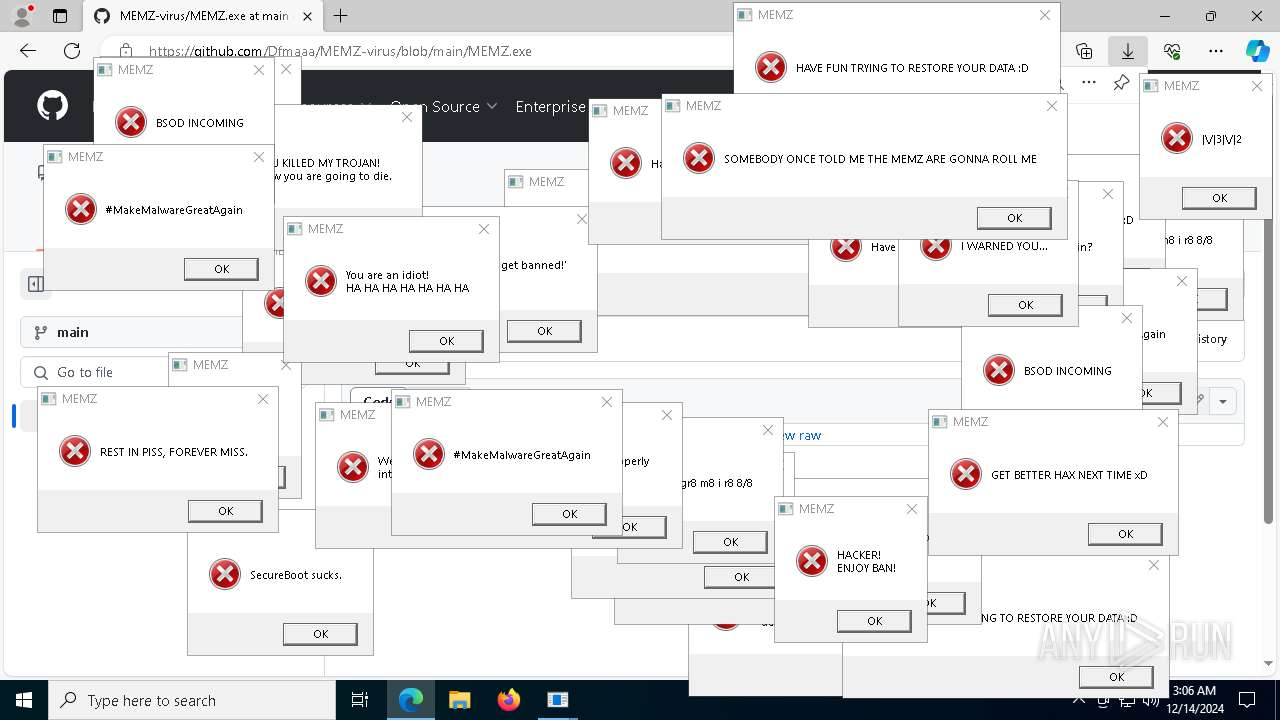
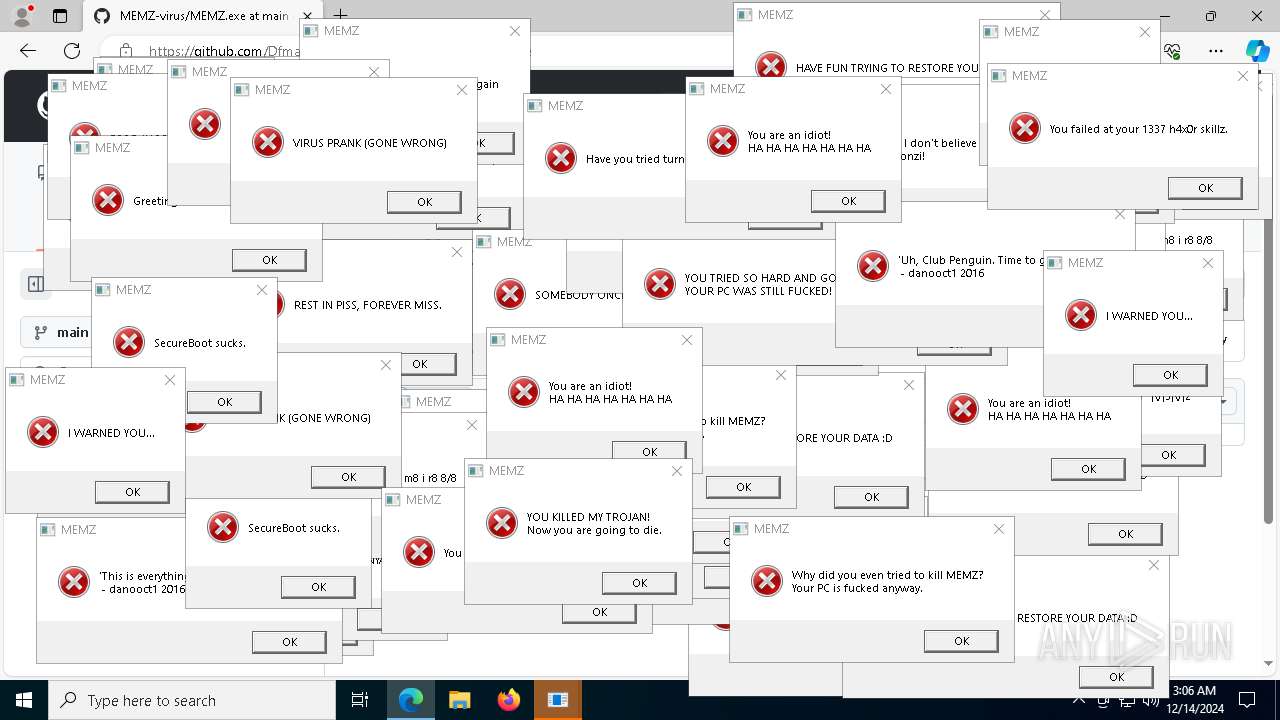
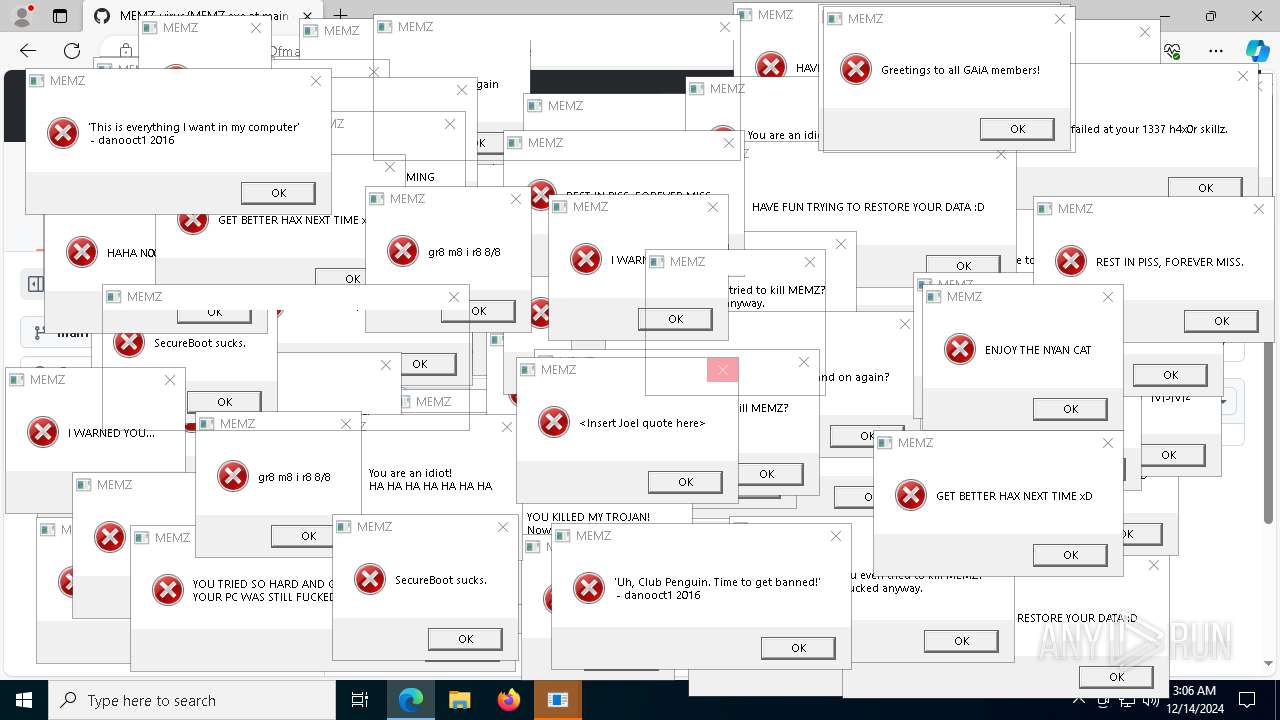
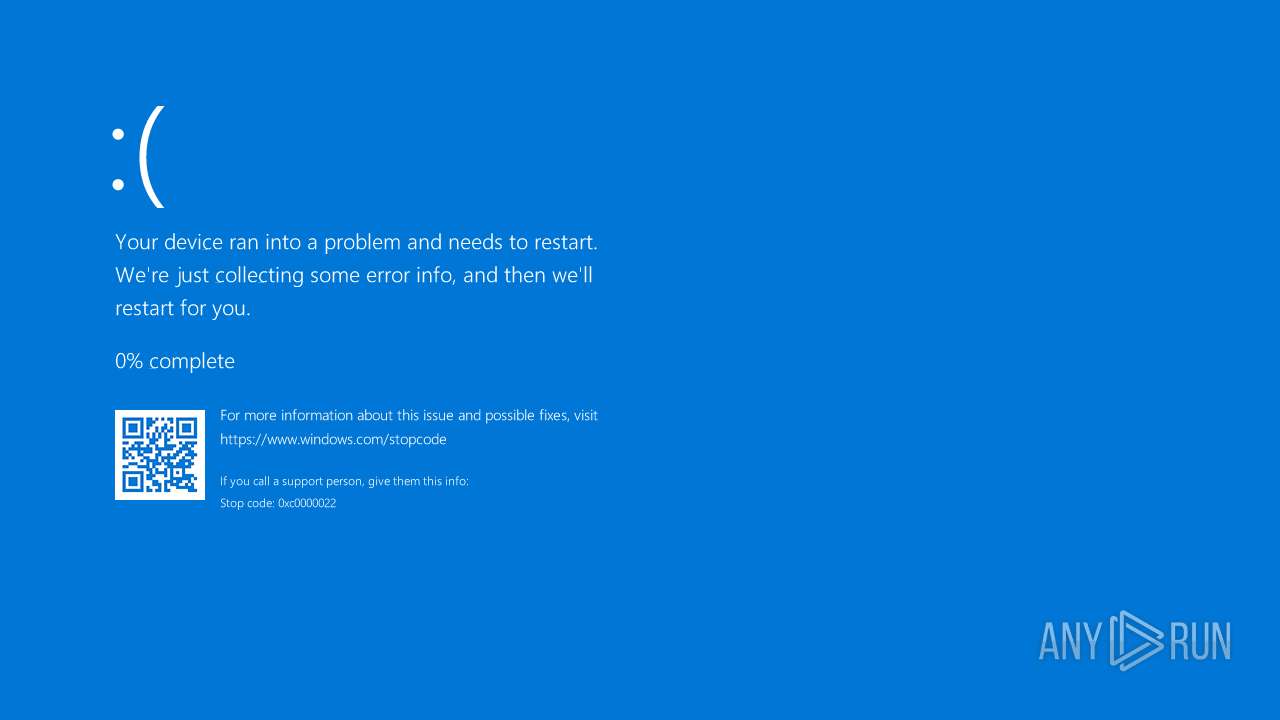
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 03:05:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0ACD7C68F6C7EFD9B34A3096200DE247 |
| SHA1: | 8CE3EA00277717AB1AD1E5C4D9BBB915B6DD16DD |
| SHA256: | 792F1BF45BA3F9D590CBBB5F13310C8DEC4198B2E6CDEA5BDAEB4B2E8233C08D |
| SSDEEP: | 3:N8tEd1YMzn:2uwG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks Windows Trust Settings
- MEMZ.exe (PID: 8052)
Reads security settings of Internet Explorer
- MEMZ.exe (PID: 8052)
- StartMenuExperienceHost.exe (PID: 4744)
Application launched itself
- MEMZ.exe (PID: 8052)
Detected use of alternative data streams (AltDS)
- svchost.exe (PID: 2500)
- svchost.exe (PID: 1772)
Reads the date of Windows installation
- StartMenuExperienceHost.exe (PID: 4744)
- SearchApp.exe (PID: 5028)
- SystemSettings.exe (PID: 6712)
Creates file in the systems drive root
- wininit.exe (PID: 644)
- svchost.exe (PID: 1772)
Searches for installed software
- svchost.exe (PID: 5664)
INFO
Application launched itself
- msedge.exe (PID: 644)
- chrome.exe (PID: 1940)
- chrome.exe (PID: 6188)
- chrome.exe (PID: 3992)
- msedge.exe (PID: 1160)
- msedge.exe (PID: 1172)
Reads the machine GUID from the registry
- MEMZ.exe (PID: 8052)
- MEMZ.exe (PID: 7308)
- MEMZ.exe (PID: 2260)
- MEMZ.exe (PID: 8160)
- MEMZ.exe (PID: 2456)
- MEMZ.exe (PID: 8188)
- OfficeClickToRun.exe (PID: 2960)
- SearchApp.exe (PID: 5028)
Checks supported languages
- MEMZ.exe (PID: 8160)
- MEMZ.exe (PID: 8188)
- MEMZ.exe (PID: 2456)
- identity_helper.exe (PID: 3876)
- MEMZ.exe (PID: 7420)
- MEMZ.exe (PID: 7308)
- MEMZ.exe (PID: 2260)
- OfficeClickToRun.exe (PID: 2960)
- PLUGScheduler.exe (PID: 1320)
- StartMenuExperienceHost.exe (PID: 4744)
- SearchApp.exe (PID: 5028)
- TextInputHost.exe (PID: 6132)
- MEMZ.exe (PID: 8052)
- SystemSettings.exe (PID: 6712)
- uhssvc.exe (PID: 6236)
Process checks computer location settings
- MEMZ.exe (PID: 8052)
- StartMenuExperienceHost.exe (PID: 4744)
- SearchApp.exe (PID: 5028)
Reads the computer name
- identity_helper.exe (PID: 3876)
- MEMZ.exe (PID: 2456)
- MEMZ.exe (PID: 7308)
- MEMZ.exe (PID: 8160)
- MEMZ.exe (PID: 8188)
- MEMZ.exe (PID: 2260)
- OfficeClickToRun.exe (PID: 2960)
- StartMenuExperienceHost.exe (PID: 4744)
- SearchApp.exe (PID: 5028)
- TextInputHost.exe (PID: 6132)
- PLUGScheduler.exe (PID: 1320)
- MEMZ.exe (PID: 8052)
- SystemSettings.exe (PID: 6712)
- uhssvc.exe (PID: 6236)
Executable content was dropped or overwritten
- msedge.exe (PID: 644)
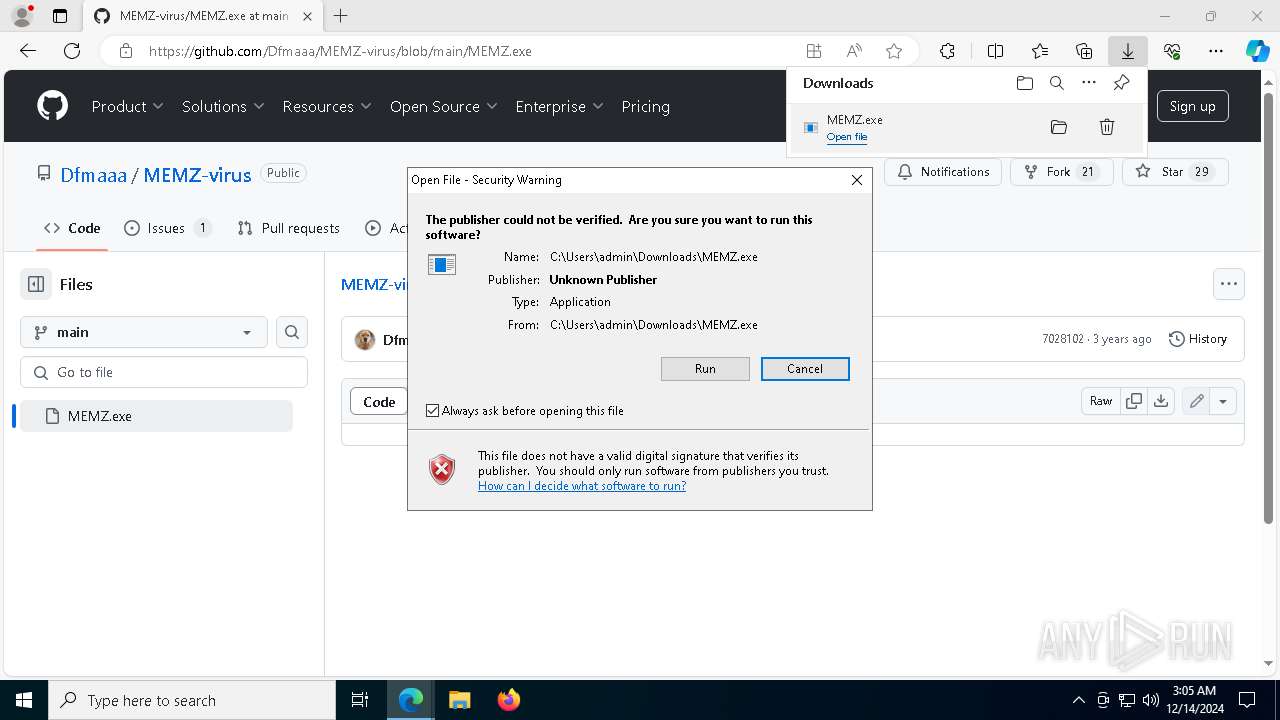
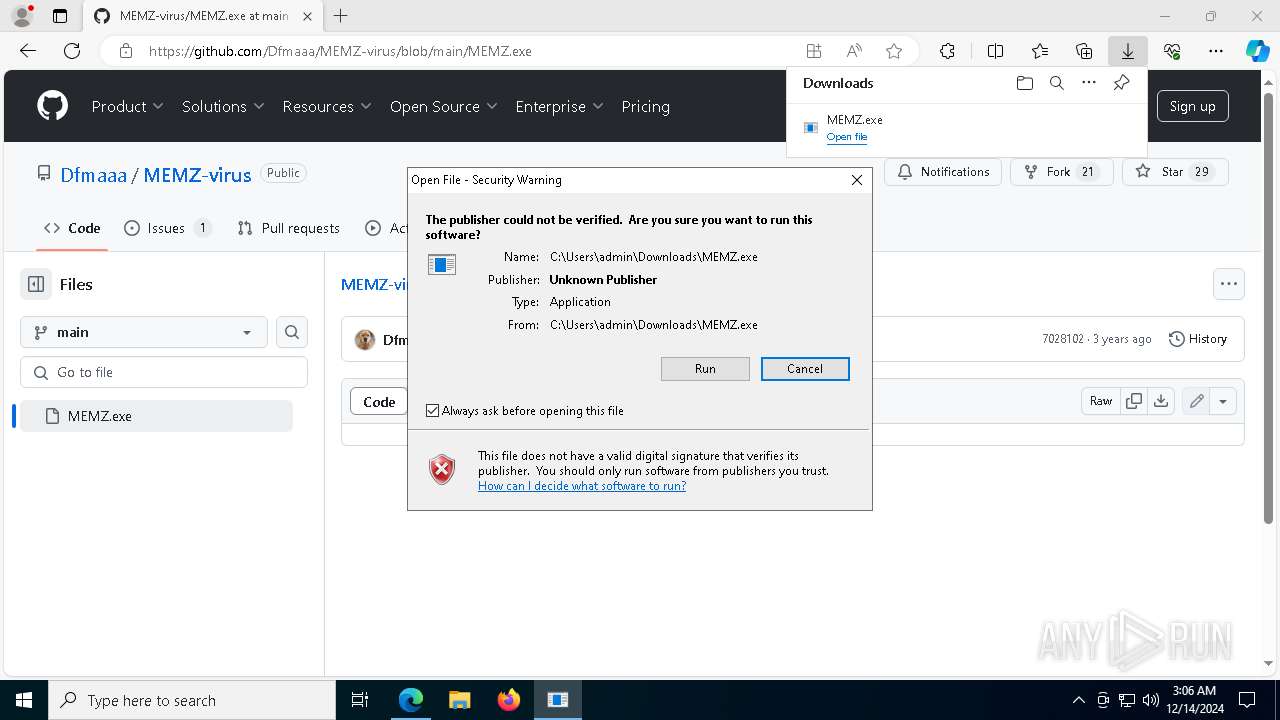
Manual execution by a user
- csrss.exe (PID: 544)
- chrome.exe (PID: 3992)
- chrome.exe (PID: 1940)
- chrome.exe (PID: 6188)
Reads the time zone
- svchost.exe (PID: 1412)
- svchost.exe (PID: 936)
- svchost.exe (PID: 2356)
- svchost.exe (PID: 2992)
- WmiPrvSE.exe (PID: 6548)
- svchost.exe (PID: 6912)
- MoUsoCoreWorker.exe (PID: 7000)
- svchost.exe (PID: 2872)
Sends debugging messages
- svchost.exe (PID: 1652)
- StartMenuExperienceHost.exe (PID: 4744)
- backgroundTaskHost.exe (PID: 5616)
Creates files in the program directory
- svchost.exe (PID: 2264)
- svchost.exe (PID: 4668)
- PLUGScheduler.exe (PID: 1320)
- svchost.exe (PID: 5948)
- svchost.exe (PID: 1112)
- svchost.exe (PID: 6912)
- MoUsoCoreWorker.exe (PID: 7000)
- uhssvc.exe (PID: 6236)
Reads security settings of Internet Explorer
- svchost.exe (PID: 2356)
- svchost.exe (PID: 3108)
- svchost.exe (PID: 3104)
- svchost.exe (PID: 3720)
- dllhost.exe (PID: 5160)
- RuntimeBroker.exe (PID: 4888)
- dllhost.exe (PID: 2700)
- backgroundTaskHost.exe (PID: 5616)
- dllhost.exe (PID: 5744)
- RuntimeBroker.exe (PID: 4296)
- dllhost.exe (PID: 3604)
- ApplicationFrameHost.exe (PID: 6720)
- backgroundTaskHost.exe (PID: 6424)
- RuntimeBroker.exe (PID: 3384)
- svchost.exe (PID: 4200)
Reads Microsoft Office registry keys
- OfficeClickToRun.exe (PID: 2960)
Checks proxy server information
- OfficeClickToRun.exe (PID: 2960)
- svchost.exe (PID: 3104)
- dllhost.exe (PID: 2700)
- SearchApp.exe (PID: 5028)
- backgroundTaskHost.exe (PID: 6424)
Reads the software policy settings
- WerFault.exe (PID: 796)
- OfficeClickToRun.exe (PID: 2960)
- SearchApp.exe (PID: 5028)
- lsass.exe (PID: 816)
- backgroundTaskHost.exe (PID: 6424)
Drops encrypted VBS script (Microsoft Script Encoder)
- svchost.exe (PID: 1364)
Disables trace logs
- svchost.exe (PID: 3396)
Creates files or folders in the user directory
- dllhost.exe (PID: 5160)
- dllhost.exe (PID: 3604)
- lsass.exe (PID: 816)
Reads Environment values
- SearchApp.exe (PID: 5028)
- identity_helper.exe (PID: 3876)
- uhssvc.exe (PID: 6236)
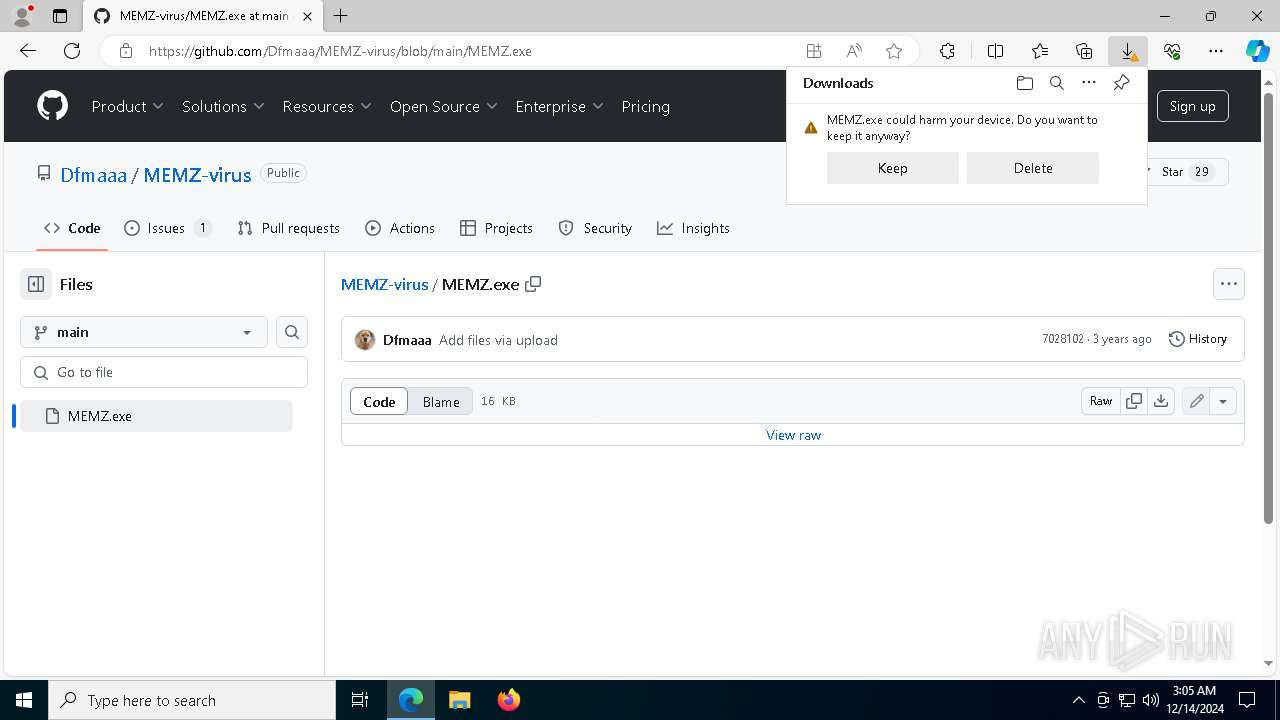
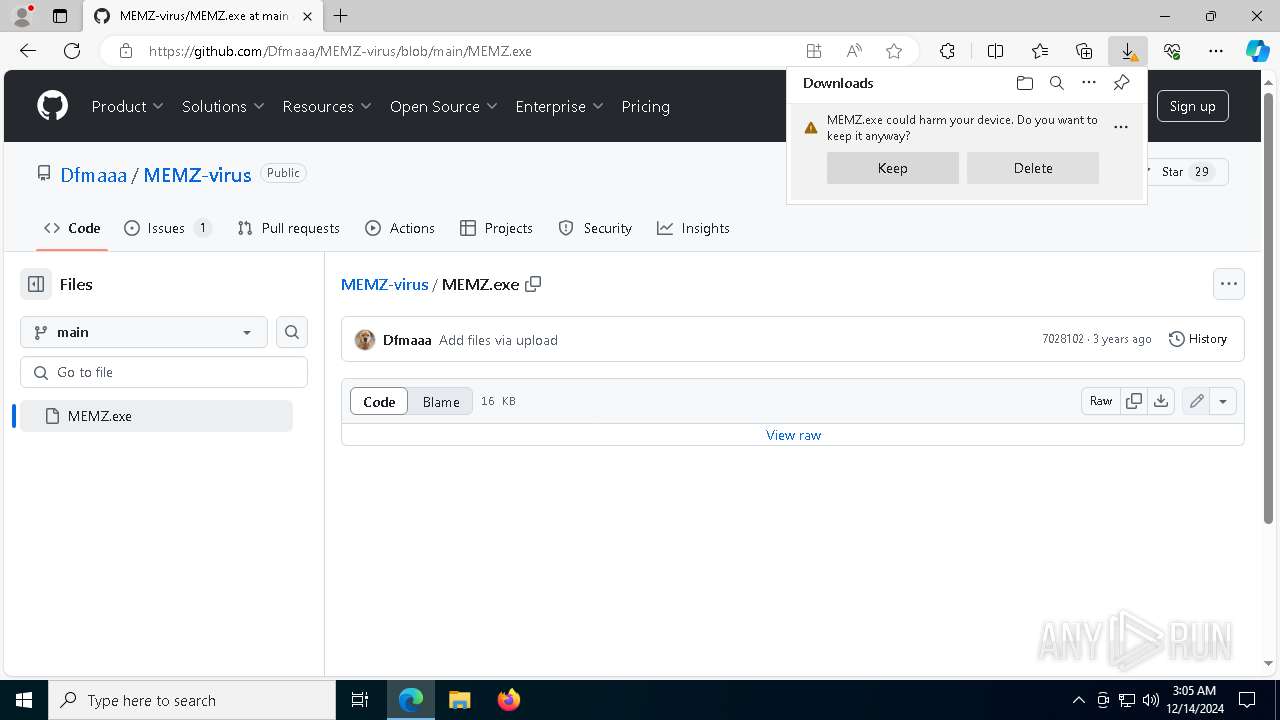
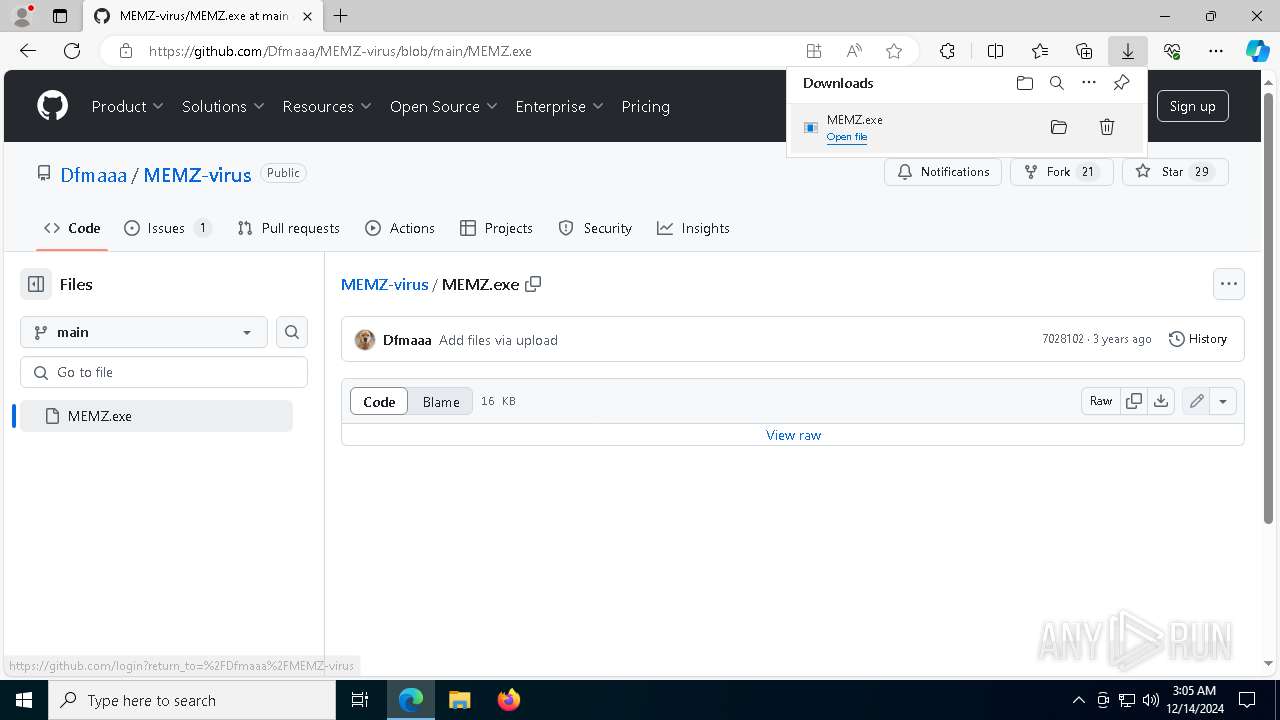
The process uses the downloaded file
- msedge.exe (PID: 7592)
- MEMZ.exe (PID: 8052)
- msedge.exe (PID: 644)
- SystemSettings.exe (PID: 6712)
Create files in a temporary directory
- svchost.exe (PID: 6484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
338
Monitored processes
193
Malicious processes
5
Suspicious processes
1
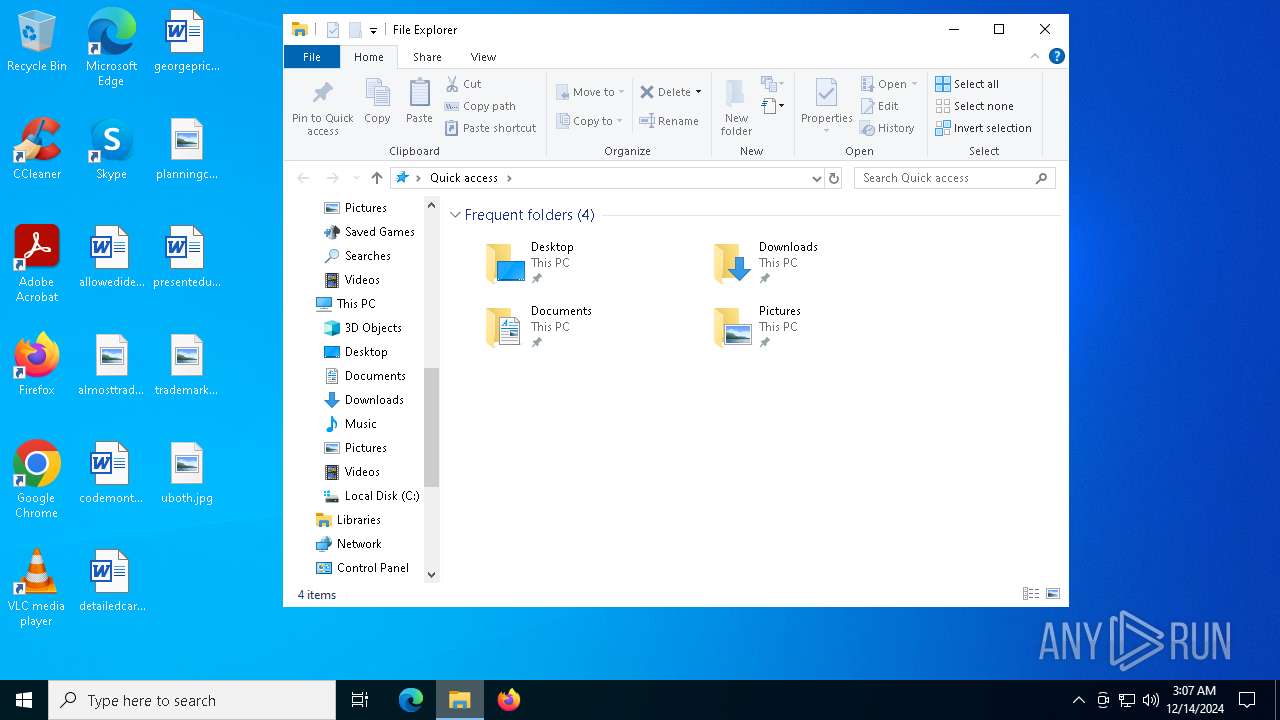
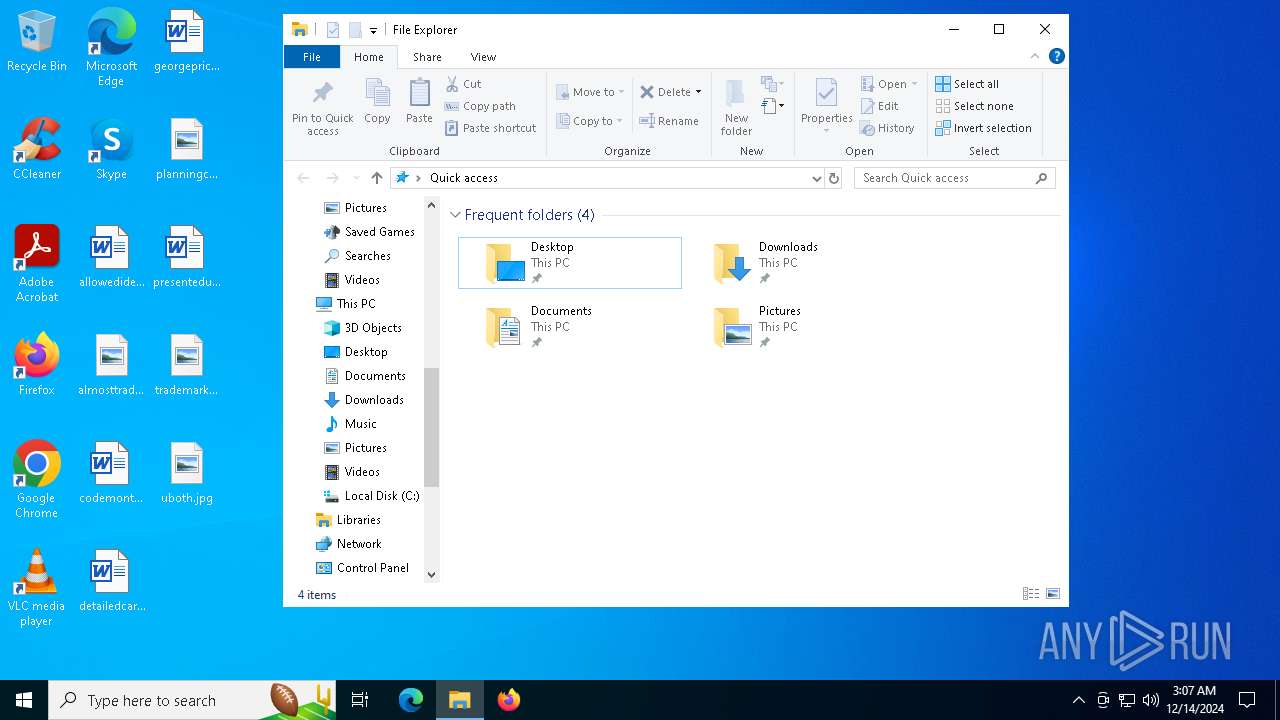
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6308 --field-trial-handle=2440,i,10593084484718563235,3806186991363341582,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 476 | C:\WINDOWS\system32\svchost.exe -k RPCSS -p | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 492 | C:\WINDOWS\System32\svchost.exe -k LocalService -p -s netprofm | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 504 | C:\WINDOWS\system32\svchost.exe -k DcomLaunch -p -s LSM | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 544 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,20480,768 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | smss.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x21c,0x220,0x224,0x200,0x228,0x7ff97856dc40,0x7ff97856dc4c,0x7ff97856dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=4516 --field-trial-handle=1896,i,5741949694818648238,2598304559882048520,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 640 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5608 --field-trial-handle=2440,i,10593084484718563235,3806186991363341582,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/Dfmaaa/MEMZ-virus" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | wininit.exe | C:\Windows\System32\wininit.exe | — | smss.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Start-Up Application Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
233 078
Read events
214 686
Write events
17 959
Delete events
433
Modification events
| (PID) Process: | (644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (644) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 16BF0880C8872F00 | |||
| (PID) Process: | (644) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BB531180C8872F00 | |||
| (PID) Process: | (644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262936 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DAE61F0A-84A9-4F1D-B940-0B97BC6D87E4} | |||
| (PID) Process: | (644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262936 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B1EF28DF-5C14-4FD9-8A70-2FEE00A5735D} | |||
| (PID) Process: | (644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262936 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7FEBE20B-78BB-4DD2-80D2-722B0C2F936B} | |||
| (PID) Process: | (644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262936 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2CD21171-51C3-4754-B506-2B6B6F63F935} | |||
Executable files
5
Suspicious files
581
Text files
201
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF134fc9.TMP | — | |
MD5:— | SHA256:— | |||
| 644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF134fd9.TMP | — | |
MD5:— | SHA256:— | |||
| 644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF134fd9.TMP | — | |
MD5:— | SHA256:— | |||
| 644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF134fe8.TMP | — | |
MD5:— | SHA256:— | |||
| 644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135036.TMP | — | |
MD5:— | SHA256:— | |||
| 644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
123
DNS requests
106
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5864 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5864 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1864 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1734555378&P2=404&P3=2&P4=DCITdzqRL6NCfp%2fMlxEX1t8v98sVmD%2bidqsGIwQQ5FVeXzjy30LVQS98vtfa%2fnYos%2bCuWK154IVvOvZgqCEZqw%3d%3d | unknown | — | — | whitelisted |
1864 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1734555378&P2=404&P3=2&P4=DCITdzqRL6NCfp%2fMlxEX1t8v98sVmD%2bidqsGIwQQ5FVeXzjy30LVQS98vtfa%2fnYos%2bCuWK154IVvOvZgqCEZqw%3d%3d | unknown | — | — | whitelisted |
1864 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1734555378&P2=404&P3=2&P4=DCITdzqRL6NCfp%2fMlxEX1t8v98sVmD%2bidqsGIwQQ5FVeXzjy30LVQS98vtfa%2fnYos%2bCuWK154IVvOvZgqCEZqw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
372 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6404 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
644 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6404 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| shared |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6404 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6404 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |