| File name: | TempLAM93.exe_unapck |
| Full analysis: | https://app.any.run/tasks/d39da8c9-546e-4b69-8f6d-01eeb912ff9c |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | January 23, 2019, 08:24:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FB38C7D94688B4FD62AF14A26D32EE73 |
| SHA1: | D4AB66983502C844D046B44CD6A5510E9813DE94 |
| SHA256: | 792DFAF27D70A22CF6EE6F74BC31AAA417A106993642C908AB66A016EAE0DC03 |
| SSDEEP: | 6144:uEHYHiBCO8VB5PKebAzE9nFET72EqE35LpaPug4pj5O97epw1B:7YHiBCOEBp9/a2EF5l0ci9ipw |
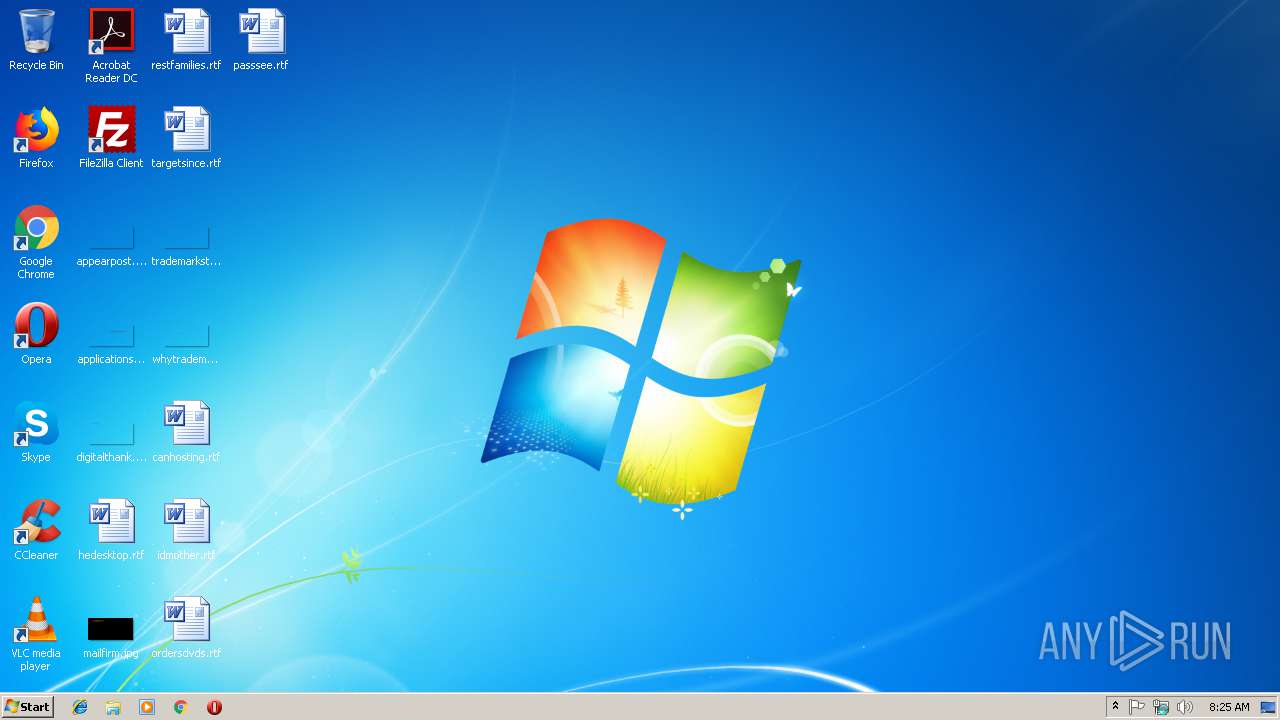
MALICIOUS
GandCrab keys found
- TempLAM93.exe_unapck.exe (PID: 2960)
Actions looks like stealing of personal data
- TempLAM93.exe_unapck.exe (PID: 2960)
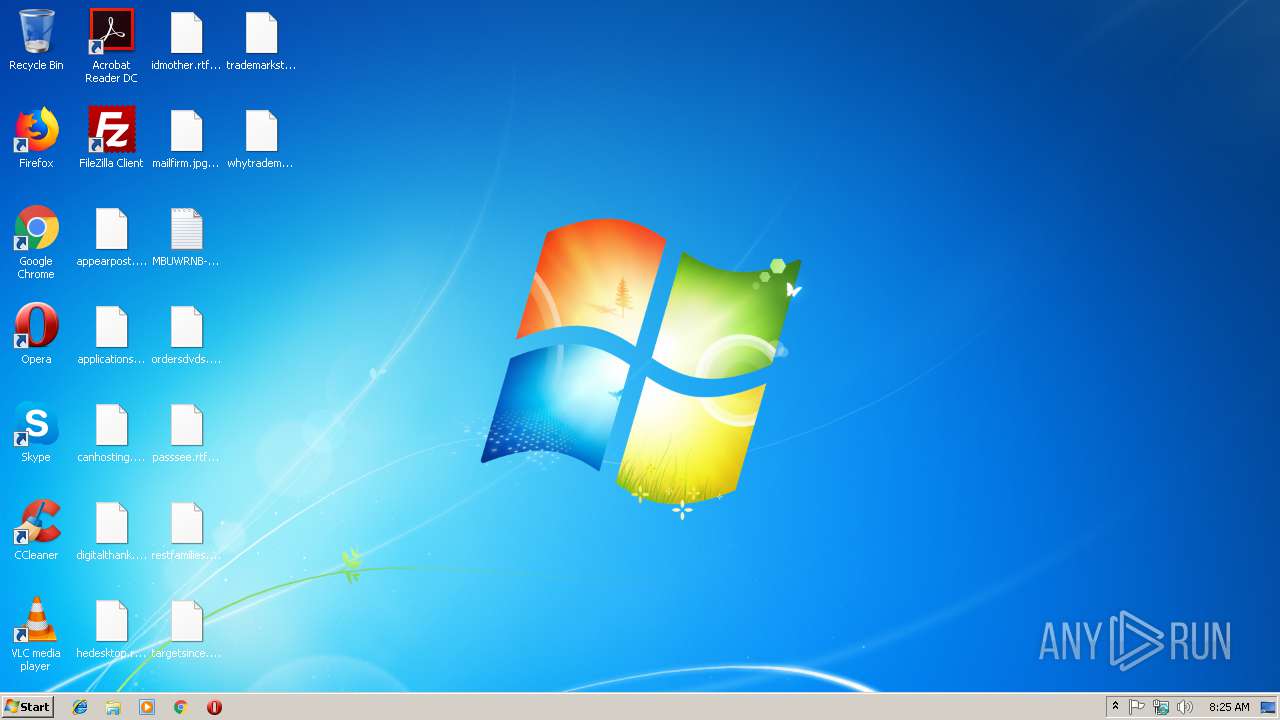
Renames files like Ransomware
- TempLAM93.exe_unapck.exe (PID: 2960)
Deletes shadow copies
- TempLAM93.exe_unapck.exe (PID: 2960)
Dropped file may contain instructions of ransomware
- TempLAM93.exe_unapck.exe (PID: 2960)
Writes file to Word startup folder
- TempLAM93.exe_unapck.exe (PID: 2960)
Changes settings of System certificates
- TempLAM93.exe_unapck.exe (PID: 2960)
SUSPICIOUS
Creates files in the program directory
- TempLAM93.exe_unapck.exe (PID: 2960)
Creates files like Ransomware instruction
- TempLAM93.exe_unapck.exe (PID: 2960)
Reads the cookies of Mozilla Firefox
- TempLAM93.exe_unapck.exe (PID: 2960)
Adds / modifies Windows certificates
- TempLAM93.exe_unapck.exe (PID: 2960)
Creates files in the user directory
- TempLAM93.exe_unapck.exe (PID: 2960)
INFO
Dropped object may contain TOR URL's
- TempLAM93.exe_unapck.exe (PID: 2960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:08:30 18:46:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 111104 |
| InitializedDataSize: | 190464 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3061 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x004f |
| FileFlags: | (none) |
| FileOS: | Unknown (0x40534) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (457A) |
| CharacterSet: | Unknown (A56B) |
| FileVersion: | 8.4.9.55 |
| InternalName: | sewumi.exe |
| LegalCopyright: | Copyright (C) 2018, difihixubizup |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Aug-2017 16:46:17 |
| Detected languages: |
|
| FileVersion: | 8.4.9.55 |
| InternalName: | sewumi.exe |
| LegalCopyright: | Copyright (C) 2018, difihixubizup |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 30-Aug-2017 16:46:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001B092 | 0x0001B200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55974 |
.rdata | 0x0001D000 | 0x00004B88 | 0x00004C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.01702 |
.data | 0x00022000 | 0x0001D914 | 0x00019200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.97561 |
.mysec3 | 0x00040000 | 0x00000005 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.mysec | 0x00041000 | 0x0000100A | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.mysec10d | 0x00043000 | 0x00000064 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00044000 | 0x0000A090 | 0x0000A200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.55158 |
.reloc | 0x0004F000 | 0x00001800 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.30592 | 432 | UNKNOWN | Croatian - Croatia | RT_VERSION |
2 | 4.83825 | 2216 | UNKNOWN | Croatian - Croatia | RT_ICON |
3 | 4.75423 | 1736 | UNKNOWN | Croatian - Croatia | RT_ICON |
4 | 4.26111 | 1384 | UNKNOWN | Croatian - Croatia | RT_ICON |
5 | 5.00277 | 9640 | UNKNOWN | Croatian - Croatia | RT_ICON |
6 | 5.20711 | 4264 | UNKNOWN | Croatian - Croatia | RT_ICON |
7 | 4.90611 | 2440 | UNKNOWN | Croatian - Croatia | RT_ICON |
8 | 5.31384 | 1128 | UNKNOWN | Croatian - Croatia | RT_ICON |
104 | 2.62775 | 76 | UNKNOWN | Croatian - Croatia | RT_DIALOG |
105 | 3.30593 | 796 | UNKNOWN | Croatian - Croatia | RT_DIALOG |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.DLL |
SHELL32.dll |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
_MyFunc2@12 | 1 | 0x0001B718 |
Total processes
37
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2708 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2960 | "C:\Users\admin\AppData\Local\Temp\TempLAM93.exe_unapck.exe" | C:\Users\admin\AppData\Local\Temp\TempLAM93.exe_unapck.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
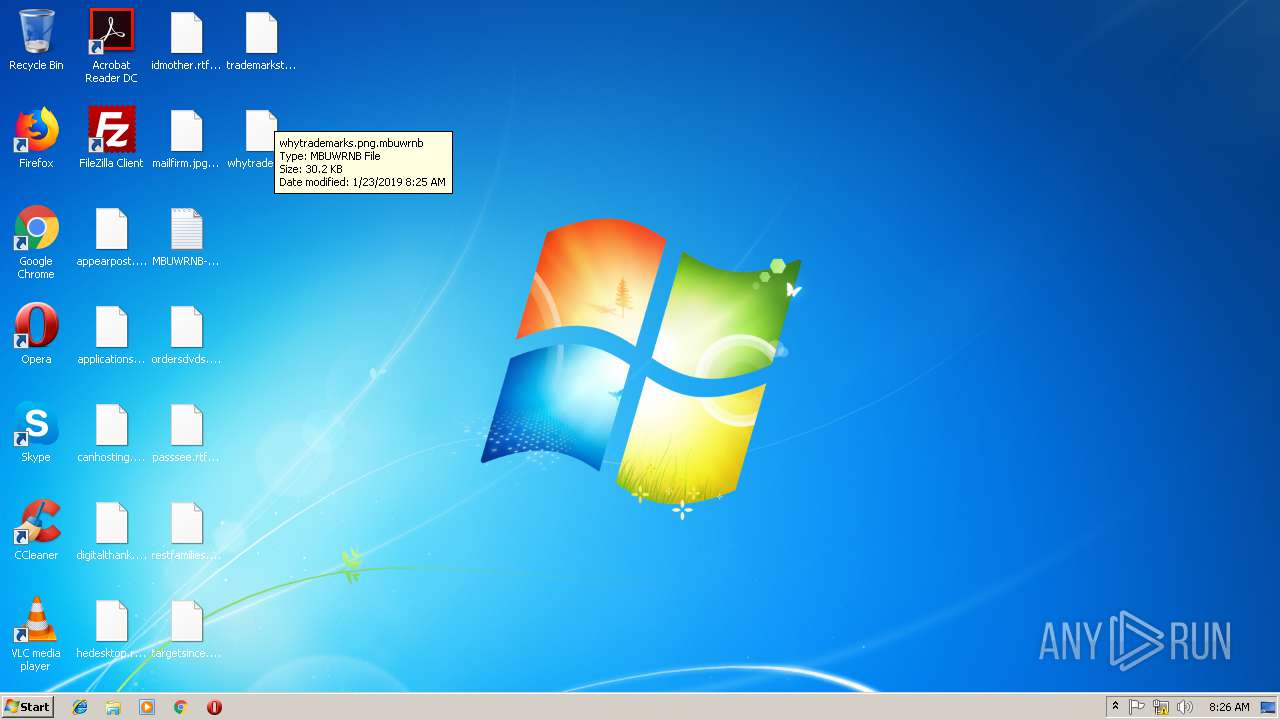
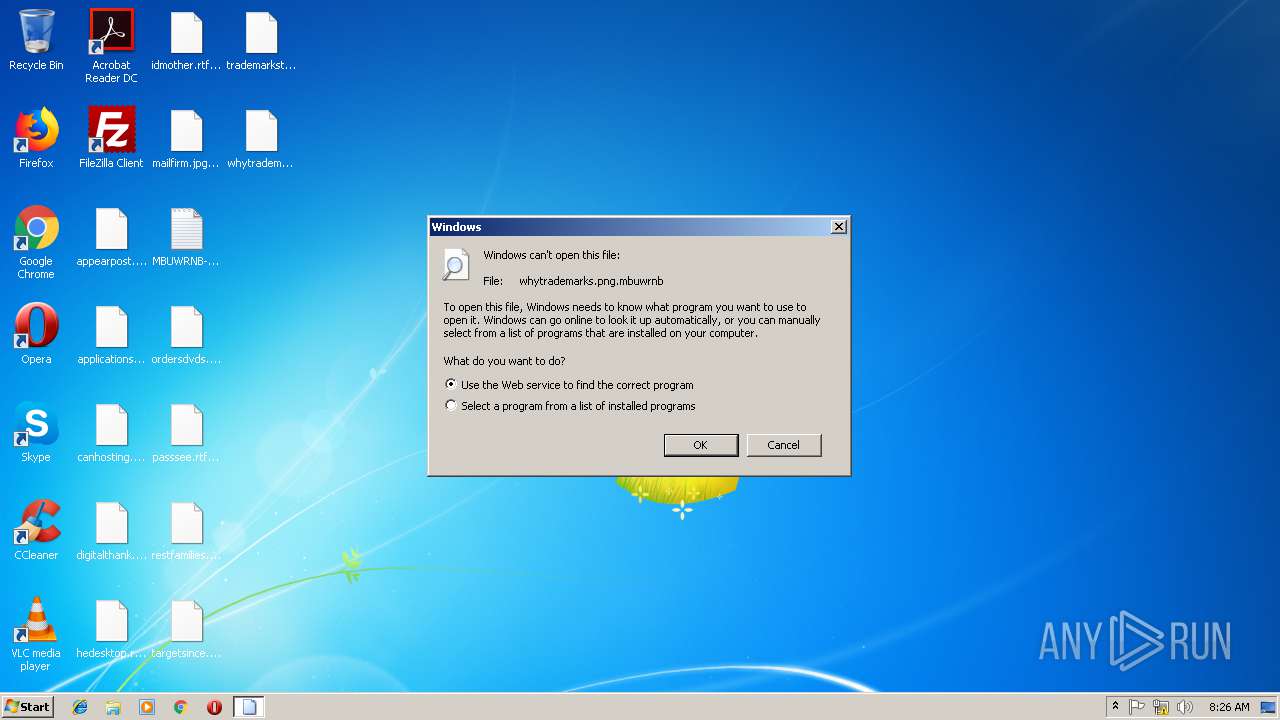
| 3092 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\whytrademarks.png.mbuwrnb | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3652 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | TempLAM93.exe_unapck.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
136
Read events
98
Write events
38
Delete events
0
Modification events
| (PID) Process: | (2960) TempLAM93.exe_unapck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E006D0062007500770072006E0062000000 | |||
| (PID) Process: | (2960) TempLAM93.exe_unapck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A40000525341310008000001000100E5EA933CAC26D43D29E15CD799AD5FD1F3B1CA18905752B5D6D542E10D0FFA884142F02E19EE1BFEAEFEF327120542F6207D9714347425AFFDA99241D2EC67E6EAB39DBFB1F53A18E8EA9FDA7EF18E27EADF7BBF2A8A5AF06F7822B26E5E147138AACD766506635EC49B2CCDF25B568ABECF91123D271333897E7E11687FA234E0D9B6360F41EF78B039E4E2FCD3707B58200CFFA533E0DE6DFA390CAFF4D863A598AD283AD29B95FF6EBF58493145FCDC7C5F201FDC79453A19B6FEC05B218897D4BC8F136ECD220AEB61951B079F55BEAF677F5A8E4C2BDF91159D5C2B2B413DF889F463D694BAFC228BBD639089232F4BC0B2B31563FB3CFBC2BA7ACF3EAB | |||
| (PID) Process: | (2960) TempLAM93.exe_unapck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | private |
Value: 9404000087C8BD3BD48AB5895A5C54CF587B1392C9DFA2D0328CA5DD614552346A3103914F50EA59206587ABDC5087A90F371EB8EE0F06DA2D99FCD8ECAED3DD93FC7CD3B89C22D090EF52F06C414899BCCE14FD5E7EF289C16F7D0A33222EC492E9775BA457A1C7A7C7C875175B44B6F98874DDB847030512F65337547C6EEC506C26E2B9BB201959B0209ECEADFDD67BA3A5CC19AC8AA11BE38CE300CE4B7D6981155CB559D773D8496196BC711A034ECFCEE85A1E8AABE733BBBE2A1776694E30D233B4CF7AAEDDF34B34A3468B3DBA33B01D605CC6FD24BE59191DB66E93DFE2B5409491D7CA0A9F1AA8F23E413D701697693C05593C668721108129DC3F8430422894BADC0B101918245B411E8C57529B8ABF5A387CE446D4AA273F5126327FA362198D1D55426CD0054D2ABCA77389A2BDD55FE458D618DED38792B629B7EB57D9E0504A950711EB8136127535F50FAF87AEDBF12A70B97C4ACD6A60232D7ED2BC9BB0BDAECD4C94C95B844A181FB9C60E81D197ED170FB4F65FFFB71A4A3F05CA3B3A4DA1FA0A61F7F21D9BA38B34C30BDB6E9344CF6CE92F9AF97285BCE643E847052123974592F992079280EABDB5C8007CC5DDA7EB382FD6FD5078BA718BA729C34A404422880B4A57071466B564077F8BD5D8158E1819D4B2EA5BBEC924D646DFFAE4BE1C67AC4ABE2D0BE32A896166367BA54D78BC270D10BE4485AF286264D79E3D430E5C0FAFFF419B9A8DB4EEDBB460A02EB0F03874A2C9CBF00A30B602417155C9C5F551304A3AA011471F9987EF6BE771D2ED84B36565754D3184E7603019D060A55EFFA7C021369F045CA7D6AEA9C6DF267A3B59F77C87CC063C7153F2E10C880B88BA69E9447E7345E5D956CF758B5EDACC40A3B5FB59085B74C0584A5C7FD28D6373A094D799FD5C6DB0B6D51556381E598B26F51C270CDBA8A1F60BC3C6E01AFA585E816023ADA7F818E72AD2FA399C00764D706D13E78FCD2EBDB0416EEB7AE67AA29740DAF8FA079CF03FA33C622A54115C55EFBA195FD713A2984137FB06E7414301D408C3B6172C028C1BE0AC86A94AB6EB0C74173F5365BA16D6FF6F1B487C9ABCBD84FE3CC8F6A8AAB9B7ACDF0E2DE43E2FC71663B0750814FBB95AE7BC933E3CCFB215F7EE206A7393D16C86C7B576CBBE6983341AC1E42CCB9A13ACD72308D50C1D984A0AC6200DA0B0A90A93251405676A706B9709A59C6B52395DA9C9B311DA2733DD536544C5D810D8C3A8565485B2F8CC15C4A83B89FB6D15AFEB8EE23F64B2E80F60D83CFA51F4FE4E105DC699D483401CF910AEF438D44E8BC6D3C48547A64E3A5D791DC6AFFEF4507507C642CA334ABE8685CB535BE969DC35A97639565685F8941A058B026EC262F6501A4F1CD8F9A99CF401A2435398B45380D2822111D5E12CB8B446556433A2C3A48FF56F756200E5361AFA5586E25701964EC36408D9E1CF161E50D801EDBEBA278E245D50CA225B5AD8F0C40FC2FCBF5B98C2A599BCA529C5889F1F206B64F5D95773A04B3616FCE0D35845BB5C06CF439862FEB07B0CA801404341427772800564CDEB0A992D3D4BAC2CAFAE400C4905B9BE90B0CD7DBA3D33997F0B19AF46807E0924F6088CACE28B14ED90130725A310E35C0E6696F75FB7FB3187DC3A7C1F8BDF627A15FBF95C8BFA49F86AABC26304E78304A7710435C3ECF8A2D3F946C5A3B9C77E4CF306EFE2EA0273F389D8DCB486ADFB0000D5A38C46698BE162F745ED86E45504301D16DD3B460B44B041FFC1D3D5790C344E0E61F8DBE7523E6A2E3F49B18ECC4471A241197CE9DE8A6023E73B6E8549CE8351F8A41A190B5001DDB08181CD1FB0E4317146C93513FE3BCD00EB442F33F7BF00A5D577F1819E88ADBED3B3B105465729EC89A1352D91F7600607B64C20A5EA1F59A9657200A2983325210146D1ECFCA3C34E2BA75D1D7C1C7E537AB3CD7AC1785A667D521C628F098DFA54B5FC61338A0C8B3EF0AFE5C1C554174AD504FC96B0585837F23F25A4C7FEB4031C7C8F0DE214B3861015A34B5A19C7A1827765F2EE31928878D1FF55B901DF6F5E365996B4675848600B3D6B4F4BAA9F00EA820C34BD3C71AE7F96BB1E3A209668882E0CB2B9F672BAA3DF71C3A396256E8245DDF5E1B65B5D4FD9C44E86A89693C9270E8D39AFF5D31DBE1FB13D77A66F884D7838449A78ABC7553D76A31A2358B55ED4D5685E689C00B9C00C09A5171C01693F721711D2707F54D5E0C5EDFA08F0664FCA36911C9408489C7BEE4765ED172ED12FA47047C2BAA4F4B79F2FC3437789DB6A7372457578B61316BA88E7A1A3A5941A11194A0CCA8AB5BA94A4BF85469ACA2CBC8C08DF5D01698ADEFDD0D934DC17FF3C24C1C2 | |||
| (PID) Process: | (2960) TempLAM93.exe_unapck.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2960) TempLAM93.exe_unapck.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2960) TempLAM93.exe_unapck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\TempLAM93_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2960) TempLAM93.exe_unapck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\TempLAM93_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2960) TempLAM93.exe_unapck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\TempLAM93_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2960) TempLAM93.exe_unapck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\TempLAM93_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2960) TempLAM93.exe_unapck.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\TempLAM93_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
430
Text files
320
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | TempLAM93.exe_unapck.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 2960 | TempLAM93.exe_unapck.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.mbuwrnb | — | |
MD5:— | SHA256:— | |||
| 2960 | TempLAM93.exe_unapck.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 2960 | TempLAM93.exe_unapck.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2960 | TempLAM93.exe_unapck.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2960 | TempLAM93.exe_unapck.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{38e8535f-27d0-4352-aa3a-ce4178930102}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2960 | TempLAM93.exe_unapck.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{3cc0f82b-873a-4e59-b89f-689fbdf88af9}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2960 | TempLAM93.exe_unapck.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-500\MBUWRNB-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 2960 | TempLAM93.exe_unapck.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{5c4beaff-a038-4df7-9b35-072a18f8e3d6}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2960 | TempLAM93.exe_unapck.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\MBUWRNB-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2960 | TempLAM93.exe_unapck.exe | GET | 301 | 138.201.162.99:80 | http://www.kakaocorp.link/ | DE | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2960 | TempLAM93.exe_unapck.exe | 138.201.162.99:80 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
2960 | TempLAM93.exe_unapck.exe | 138.201.162.99:443 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |