| File name: | TempLAM93.exe |
| Full analysis: | https://app.any.run/tasks/876d24a3-aa9f-4770-afde-c9e5c2809b8e |
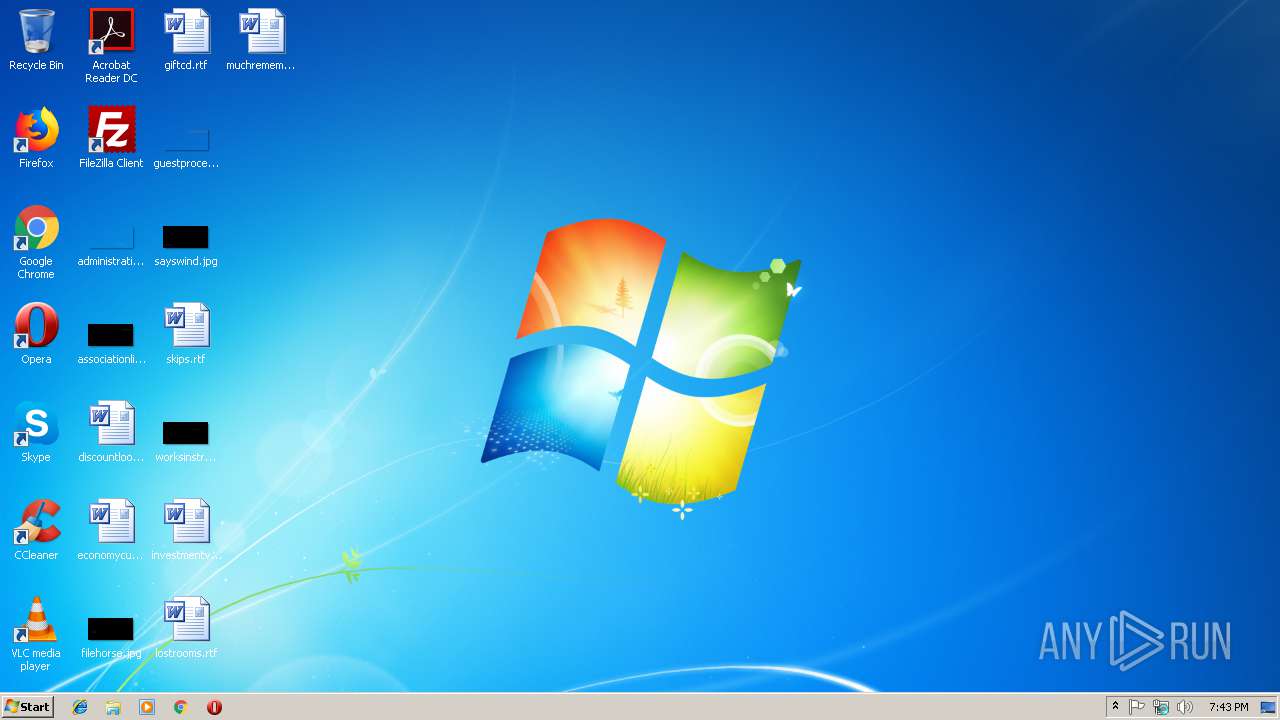
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | January 22, 2019, 19:43:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FB38C7D94688B4FD62AF14A26D32EE73 |
| SHA1: | D4AB66983502C844D046B44CD6A5510E9813DE94 |
| SHA256: | 792DFAF27D70A22CF6EE6F74BC31AAA417A106993642C908AB66A016EAE0DC03 |
| SSDEEP: | 6144:uEHYHiBCO8VB5PKebAzE9nFET72EqE35LpaPug4pj5O97epw1B:7YHiBCOEBp9/a2EF5l0ci9ipw |
MALICIOUS
GandCrab keys found
- TempLAM93.exe (PID: 2976)
Writes file to Word startup folder
- TempLAM93.exe (PID: 2976)
Actions looks like stealing of personal data
- TempLAM93.exe (PID: 2976)
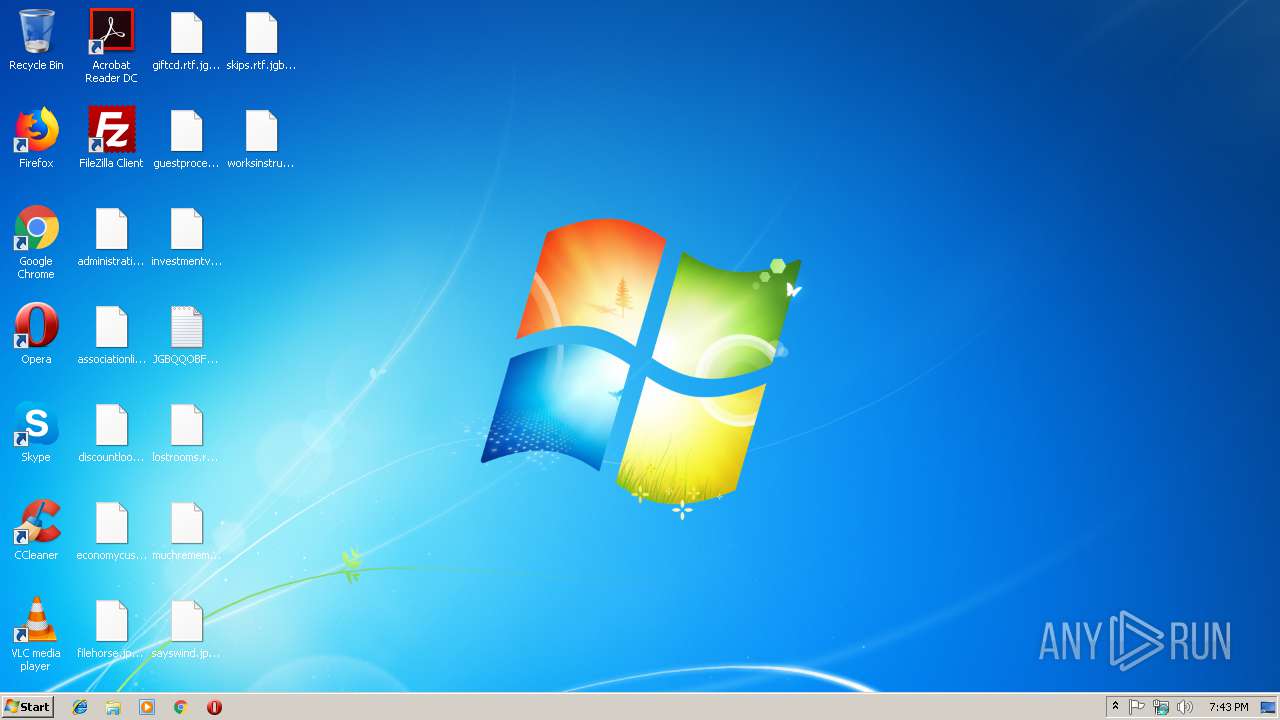
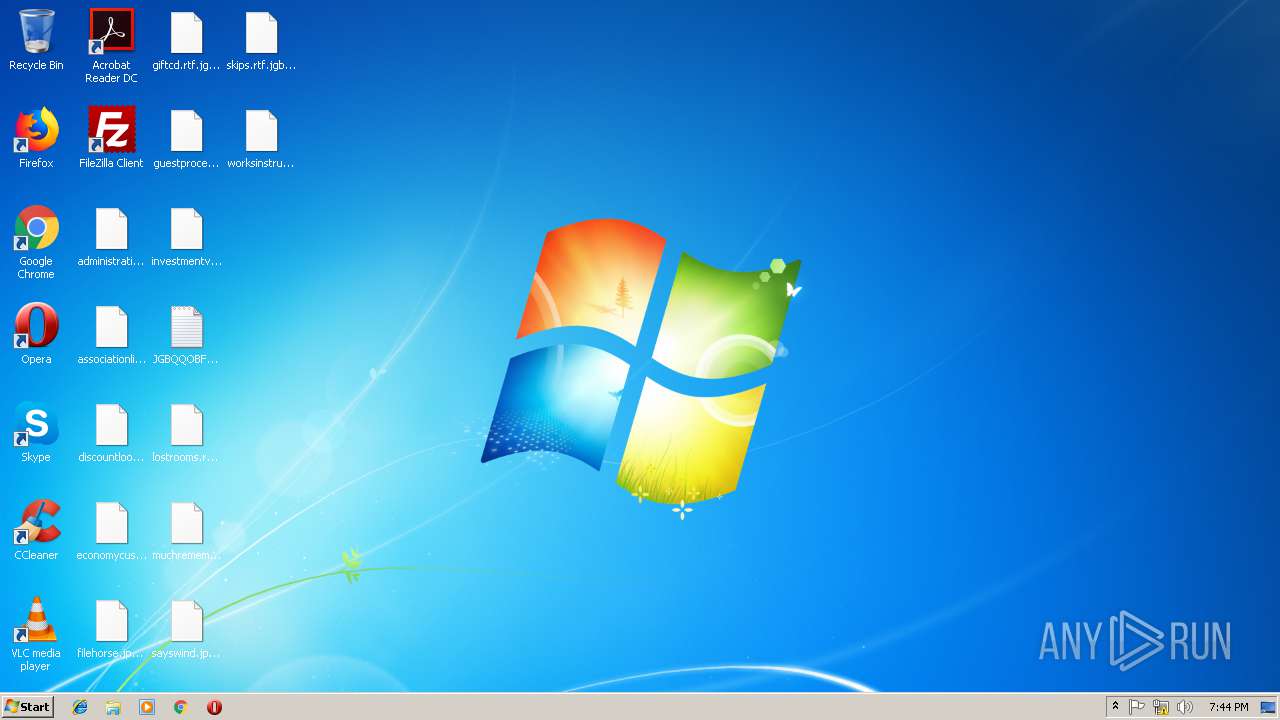
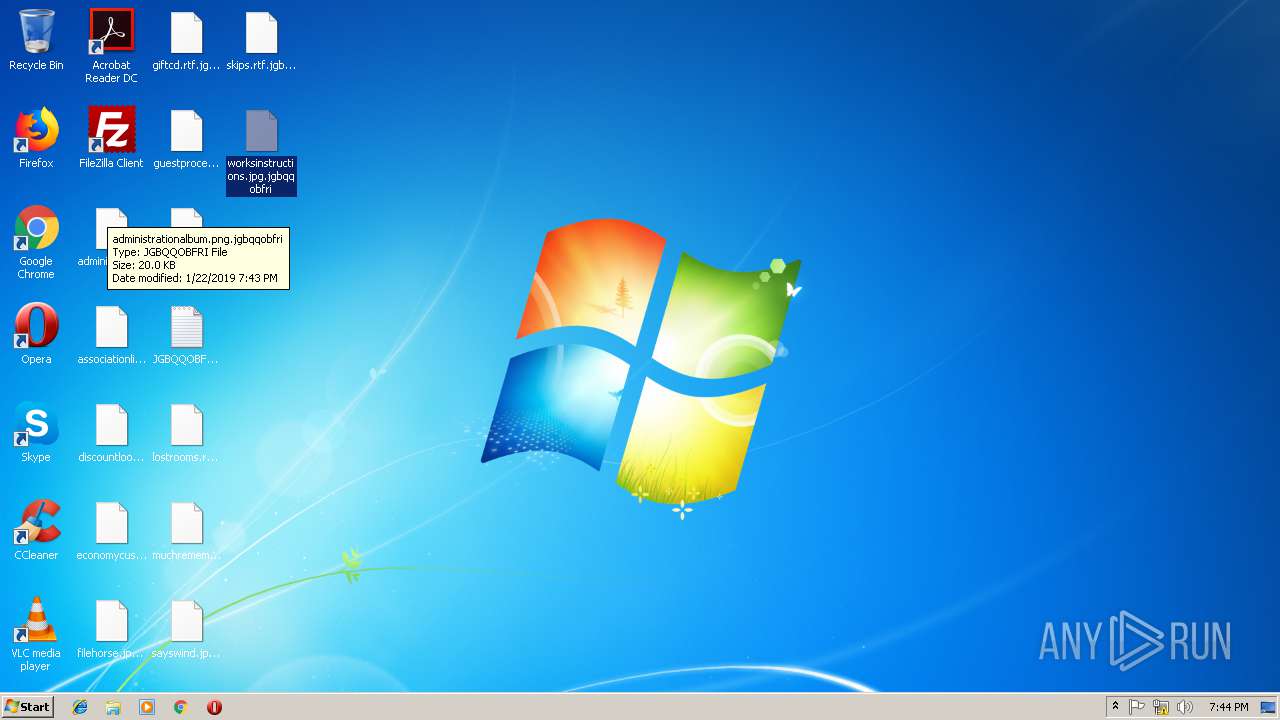
Renames files like Ransomware
- TempLAM93.exe (PID: 2976)
Deletes shadow copies
- TempLAM93.exe (PID: 2976)
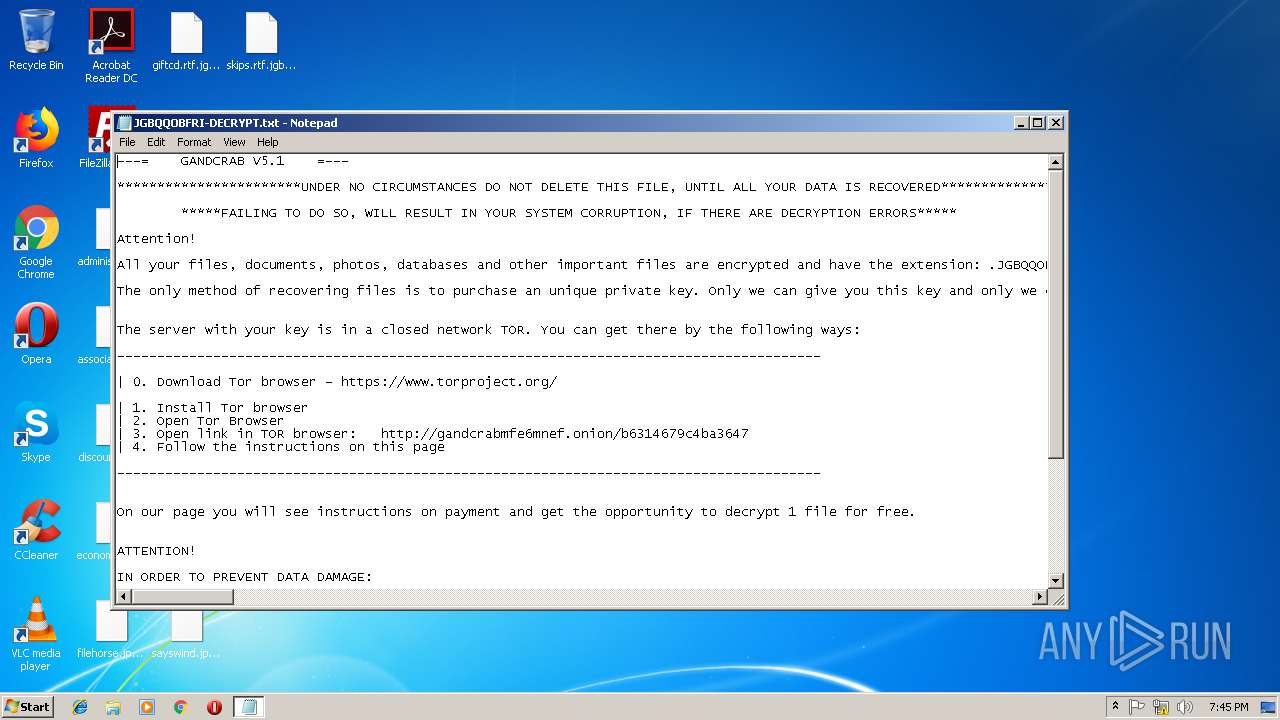
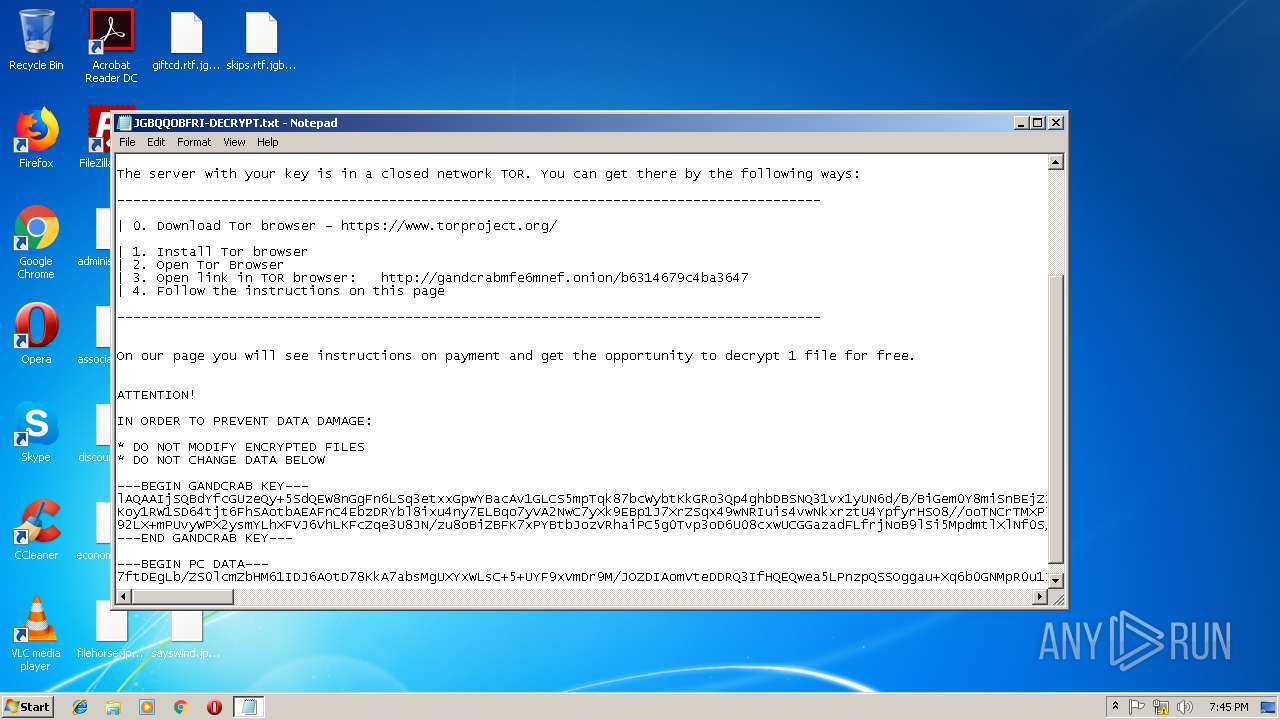
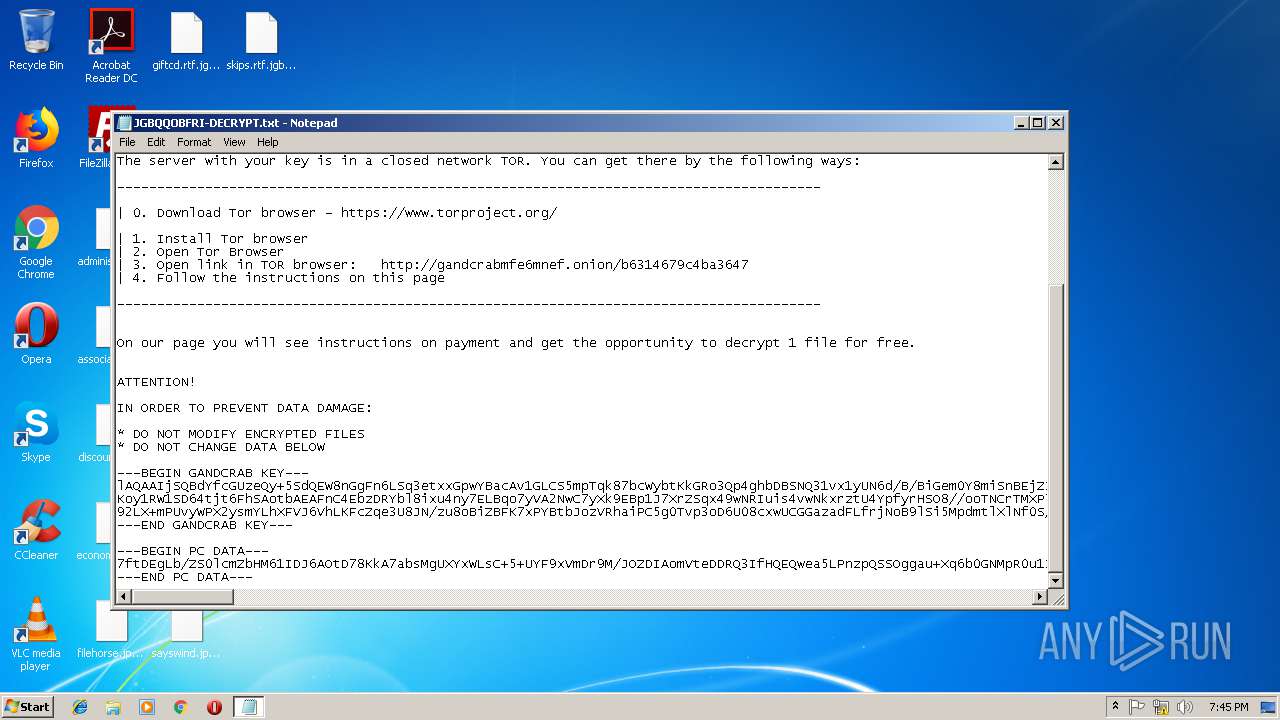
Dropped file may contain instructions of ransomware
- TempLAM93.exe (PID: 2976)
SUSPICIOUS
Creates files in the program directory
- TempLAM93.exe (PID: 2976)
Reads the cookies of Mozilla Firefox
- TempLAM93.exe (PID: 2976)
Creates files like Ransomware instruction
- TempLAM93.exe (PID: 2976)
Creates files in the user directory
- TempLAM93.exe (PID: 2976)
INFO
Dropped object may contain TOR URL's
- TempLAM93.exe (PID: 2976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:08:30 18:46:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 111104 |
| InitializedDataSize: | 190464 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3061 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x004f |
| FileFlags: | (none) |
| FileOS: | Unknown (0x40534) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (457A) |
| CharacterSet: | Unknown (A56B) |
| FileVersion: | 8.4.9.55 |
| InternalName: | sewumi.exe |
| LegalCopyright: | Copyright (C) 2018, difihixubizup |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Aug-2017 16:46:17 |
| Detected languages: |
|
| FileVersion: | 8.4.9.55 |
| InternalName: | sewumi.exe |
| LegalCopyright: | Copyright (C) 2018, difihixubizup |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 30-Aug-2017 16:46:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001B092 | 0x0001B200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55974 |
.rdata | 0x0001D000 | 0x00004B88 | 0x00004C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.01702 |
.data | 0x00022000 | 0x0001D914 | 0x00019200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.97561 |
.mysec3 | 0x00040000 | 0x00000005 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.mysec | 0x00041000 | 0x0000100A | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.mysec10d | 0x00043000 | 0x00000064 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00044000 | 0x0000A090 | 0x0000A200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.55158 |
.reloc | 0x0004F000 | 0x00001800 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.30592 | 432 | UNKNOWN | Croatian - Croatia | RT_VERSION |
2 | 4.83825 | 2216 | UNKNOWN | Croatian - Croatia | RT_ICON |
3 | 4.75423 | 1736 | UNKNOWN | Croatian - Croatia | RT_ICON |
4 | 4.26111 | 1384 | UNKNOWN | Croatian - Croatia | RT_ICON |
5 | 5.00277 | 9640 | UNKNOWN | Croatian - Croatia | RT_ICON |
6 | 5.20711 | 4264 | UNKNOWN | Croatian - Croatia | RT_ICON |
7 | 4.90611 | 2440 | UNKNOWN | Croatian - Croatia | RT_ICON |
8 | 5.31384 | 1128 | UNKNOWN | Croatian - Croatia | RT_ICON |
104 | 2.62775 | 76 | UNKNOWN | Croatian - Croatia | RT_DIALOG |
105 | 3.30593 | 796 | UNKNOWN | Croatian - Croatia | RT_DIALOG |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.DLL |
SHELL32.dll |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
_MyFunc2@12 | 1 | 0x0001B718 |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1104 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | TempLAM93.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2272 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\JGBQQOBFRI-DECRYPT.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2788 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2976 | "C:\Users\admin\AppData\Local\Temp\TempLAM93.exe" | C:\Users\admin\AppData\Local\Temp\TempLAM93.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
97
Read events
90
Write events
7
Delete events
0
Modification events
| (PID) Process: | (2976) TempLAM93.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E006A0067006200710071006F0062006600720069000000 | |||
| (PID) Process: | (2976) TempLAM93.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A400005253413100080000010001009F41A79A2BDDA2888D71E244C8530CE96D87835B456FD7225631441D6D1589FA967DD38BEEBBB45226FF33C590A1896EE57AB7F83765FD17E93E487E9BA06EBCA0ECAC8EEF146CB91DE2BBE85D4677C5E4E90B4C55D80401173171B76F341AA84FB06F39F749FA607D12B4AF2FDE0EE017692686A5A22933E0D17959F900CD3FCFD3E7AF1347BCC1CBCCD3CC02E1A8BC01801C0A023FEE5FACEBB46814DCA5747F3B2FB391A4BCE7601F145C1B693E4682FD6C56EE6AAF4FCE8A4AB03DA4D0CF884DB864D0A80521BB8EA63ED63F27D28EB45E09AD00757A62B67E969E2BD2B3CB758F9561EA3F93F7AAF446113AB70479E3AA5CE5D476A4BD27A34E744BE7E0 | |||
| (PID) Process: | (2976) TempLAM93.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | private |
Value: 9404000088D24017587DC194CDE432FB949D4045BC9C68059FA2D2AB77ADC711A9C1805A700BF518B092E66A53AA4F3B6DC5B26ED2A4191A37429E2085B0C148D437D6FC75C9437A77F07F06219E9B463C9A24A70448D920DFBE961E1CD844E8F31796E04D0F93939E4346071C4965157F66926413C92D0272E23E043769B78FC9766BFEB179571D93AA89192421D862B6D6280B84E4F466E08A502351D95229593946A0417CC82CF6847FBABE62233B4BF77BA637273727746AB7A4023F573F4372CE23EEF75EAAC7F98226AB822A9CC7178704D12E8BF5E270C5B97F3F8E48AB098C29AB4E668AF05E0F7207B981F82A8EA7048CAB4C6224226E332C81D8DB9F46617E714A800B97A794C6F4336CE9B7BBD9C5F0D07DA2F569DC2D26D77CB367D970A8CE8AC5E092283AA4CFFD0F640B4C0B15C92831D20E8CC3427CDFA9D6C6FDBC45A46A2930BA1A53CC65033A593133229CEF72804B17A89833DFA7FD5B54CA3D760A63E1238DCF97B96FDF0DD00B00D0CC8EDA2CA823A7B264ED500F054A5EE9B018E6D841FE4BFE5910F14C99D4B0A387DB92609886B5D00E2F47768FC52CE14A3559E8C31C51153961806CC1A6F65A1333D12B0CC5AA46931F6BEEBCA7A5F297C034404913027E1050FA0908A79CA53548CEDBF146F3CBFEF50AE3B590DBA4D48DDFF4F4C9C9C623A24B74EEB318DB06C520D7254B6A20D31153CA116AEB0346480D87D57F6A28AC077567D818CA31A49EBFE92D50EDA176C55156DF182F6C9C1C6E35DBC006AB1BB14A81185E50C459334AC61B40A34480C058A92D70F1C81ECB5B6242CF37D648FEDB5C66E271100E45A69FB9C35102A43EF7738FE2AF94001E7DEBCA2F106D2585DE88A6ED887B954B5FD021DC430A0296493AB6815A0A3EBF263BF5A5E5B07F15C475A153EEEDF0B2D93D3A1EC41CE18688B9670798A2936B50C5FA6767DB2842F76071F20238E5AE16EA21290247F90854637DE5C577866A1A396BBE8214CCFB63541D441403F02E0BD22DBEC8E54339B0D8A5596610ACEF01899A1FD09F6C9AC49BA89B9927037DE6CF7030D908D19D4414E82A8CB5456D520FAE2D8EDE85852028B5B0040059C2E046F30D161B97C8B1BB89F2EC42C1AA8EF2540D8DC02EF25E4F44069D49ED7AD94AAC78F7035122E8ACE2FC0D931AF3B54E18A5FCAB1D23BCFFFA284CD0AB4CC5CFEFDE2F7314E4C7FE447C15879BA305D930BE44B64646636FFCC0C5746888274B0607F0C18FA6C1562593E3B0C11F342DF683BA4C3B5FA9F3E4F4E581AA0D44CE9A21252396D4A39F44AFFA29DC64AC0AB6921A395839310EF2158D66D2EF3DFFE4C31135A36C8E74B169C389980350FF7357384624CC93BBF2E34C474E121EA2ECE728FBF1CE7A5CA9EC3410091ADC75669F5C79C6417B0316AD70C9F006F2EE92084558A9F6EAFE9FE898CEA4461B6F986EC858D328AB6B8A8D279DA573C15E93972499D7BCE3F3E73A35045033FF86BE667CE08DDA5A7CFB74B8D78B2BB1072311B6674F4BD9B33C9273B640AEF2BD8BD5F0FD51973510716023BB4FF4613D02F7BBAA2C3818A654906B40CF2DAA5248E3FEC3A555D282DED6317F9AA58188E3B0B1333D921413394A054661B9727188507B9D969EF6F90243358101ADB478B48BB143C1633046199C6CDA5F67348E7286EFFC54C3BD50858E6B5A1E21881941AF75ED81774882BD888069F4EC63F9A9076BB18D1E8F9FE7285725F78D57EAA8B9099AD81D091E1D37C17E586F813AEF1E80A71C1507F7728A6DEDA3238A9D45ABE68C0256B44B0183D3001DFE47C59314FF1FEB503A4435F52B693B07C26020BB66585139FABB4D4E8D491D01BAD92D94D8EF0623932C7099514B4B910E40ECD349E7646C89D22EBD9BCD92C33B11B5AFAE425BFBED658891C609C3B6CC5BF6F5C1D1F29FBA185EEA2269883BEAB3DF575A42EEF490527DE2A14139B6E7657997D14E713A258329516B9EED01353E13F0876DFCD51E7FAFCC3B584FC42D1A048AC45C3A0FC6DA0362ADD14833BD04E126C89E087F2C49DA80092989B6AA9C2E433CE2D1779B230829F7EEECC1B15C4406D429C30890F98237858BC63BB4183E9EDD956F1088B68C09753BABCA682687CAAA2EBFED054EB3D0D58295DA831E97231E0A252055D6A7F762D7FA63D4BF258F5F6CAC9982E15C5549E9584B285719A9EDD4F0937FCEEF2806264114AEF13D806D6C9A3355185A88F0B98344EFA77A03E94D3C731C1408619ACDA7452DFAE336807D9528B9329766B655E535FD12FCCEAF1AA00F97381B62CA17427F94645491A11DC66FA91E547DCF70227C0F9F5F0C3F506F0AFAB8B666E6816B93B94D5752D255D6C64F8797E3D0BA0E620B50DA | |||
| (PID) Process: | (2976) TempLAM93.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2976) TempLAM93.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
426
Text files
318
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | TempLAM93.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 2976 | TempLAM93.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.jgbqqobfri | — | |
MD5:— | SHA256:— | |||
| 2976 | TempLAM93.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2976 | TempLAM93.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 2976 | TempLAM93.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2976 | TempLAM93.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{38e8535f-27d0-4352-aa3a-ce4178930102}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2976 | TempLAM93.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{3cc0f82b-873a-4e59-b89f-689fbdf88af9}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2976 | TempLAM93.exe | C:\PerfLogs\JGBQQOBFRI-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 2976 | TempLAM93.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{5c4beaff-a038-4df7-9b35-072a18f8e3d6}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2976 | TempLAM93.exe | C:\Users\JGBQQOBFRI-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report