| File name: | magicline4nx_setup.exe |
| Full analysis: | https://app.any.run/tasks/b447f3d8-010a-41a8-a4b7-93ee7a497780 |
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2020, 00:09:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 071FEA9474154F4E3F4AEB9D70BB9B51 |
| SHA1: | 59624DE3135499420493E6DE00A61F581ECCB3F7 |
| SHA256: | 79226F291A18F03C48A303909C9C0FBAD01C78C73029A460A380E4C14FCC871E |
| SSDEEP: | 196608:pcFM1H5icKcrP3+iHVn/YJyvK6qQBGG1y+8dkrrkRauWlcfC:t18cKcrLRFICqsrkL1fC |
MALICIOUS
Loads dropped or rewritten executable
- magicline4nx_setup.exe (PID: 3376)
- certutil.exe (PID: 3568)
- certutil.exe (PID: 3696)
- MagicLine4NX.exe (PID: 2740)
- MagicLine4NX.exe (PID: 3832)
Application was dropped or rewritten from another process
- ns8324.tmp (PID: 1828)
- ns841F.tmp (PID: 3524)
- ns950B.tmp (PID: 4012)
- ns8CFA.tmp (PID: 3952)
- ns9095.tmp (PID: 1948)
- certmgr.exe (PID: 2348)
- certutil.exe (PID: 3696)
- ns9981.tmp (PID: 4012)
- ns9C13.tmp (PID: 2120)
- MagicLine4NX.exe (PID: 2740)
- ns973E.tmp (PID: 2668)
- ns9B38.tmp (PID: 3696)
- MagicLine4NXServices.exe (PID: 3884)
- nsA06B.tmp (PID: 1748)
- certutil.exe (PID: 3568)
- ns9C82.tmp (PID: 2232)
- MagicLine4NXServices.exe (PID: 1380)
- MagicLine4NX.exe (PID: 3832)
Changes settings of System certificates
- certmgr.exe (PID: 2348)
Changes internet zones settings
- magicline4nx_setup.exe (PID: 3376)
Changes the autorun value in the registry
- magicline4nx_setup.exe (PID: 3376)
SUSPICIOUS
Starts CMD.EXE for commands execution
- magicline4nx_setup.exe (PID: 3376)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2776)
- cmd.exe (PID: 3792)
Starts application with an unusual extension
- magicline4nx_setup.exe (PID: 3376)
Executable content was dropped or overwritten
- magicline4nx_setup.exe (PID: 3376)
Starts SC.EXE for service management
- ns8324.tmp (PID: 1828)
- ns841F.tmp (PID: 3524)
- nsA06B.tmp (PID: 1748)
Creates files in the program directory
- magicline4nx_setup.exe (PID: 3376)
Modifies the open verb of a shell class
- magicline4nx_setup.exe (PID: 3376)
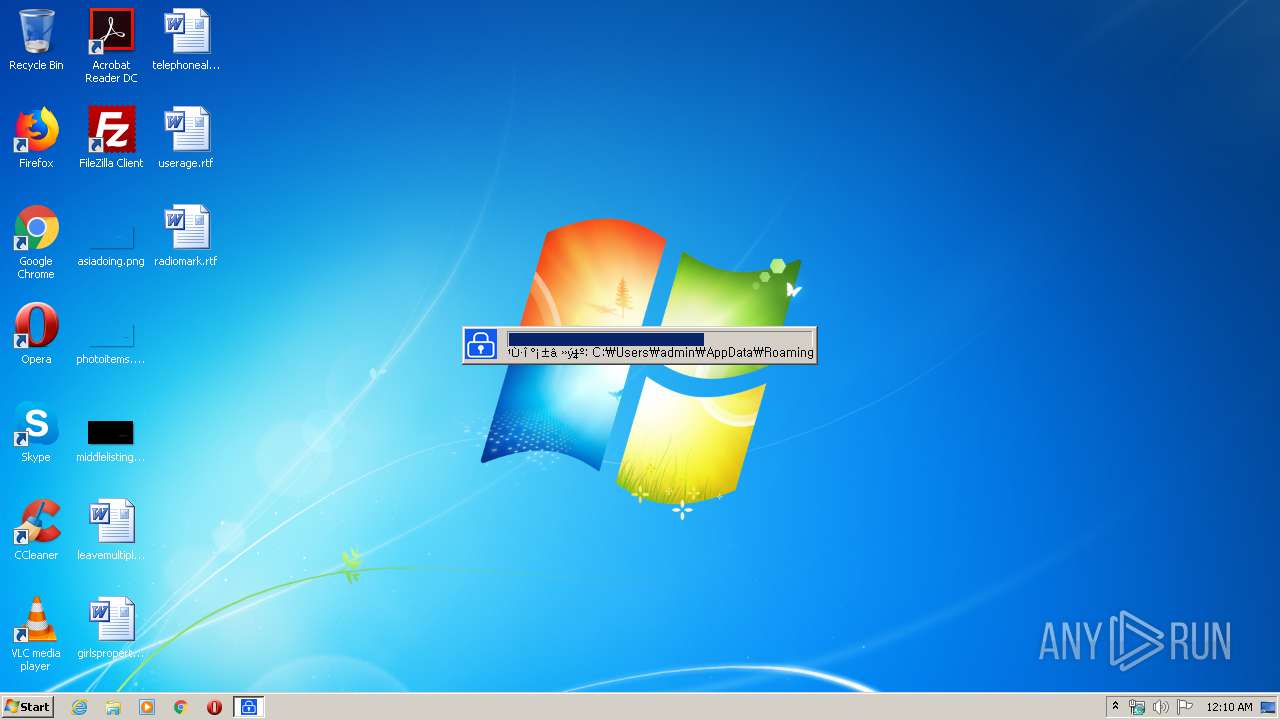
Creates files in the user directory
- magicline4nx_setup.exe (PID: 3376)
- certutil.exe (PID: 3696)
Executes scripts
- ns9095.tmp (PID: 1948)
- ns950B.tmp (PID: 4012)
Creates a software uninstall entry
- magicline4nx_setup.exe (PID: 3376)
Uses NETSH.EXE for network configuration
- ns973E.tmp (PID: 2668)
- ns9981.tmp (PID: 4012)
Executed as Windows Service
- MagicLine4NXServices.exe (PID: 1380)
Modifies files in Chrome extension folder
- chrome.exe (PID: 772)
INFO
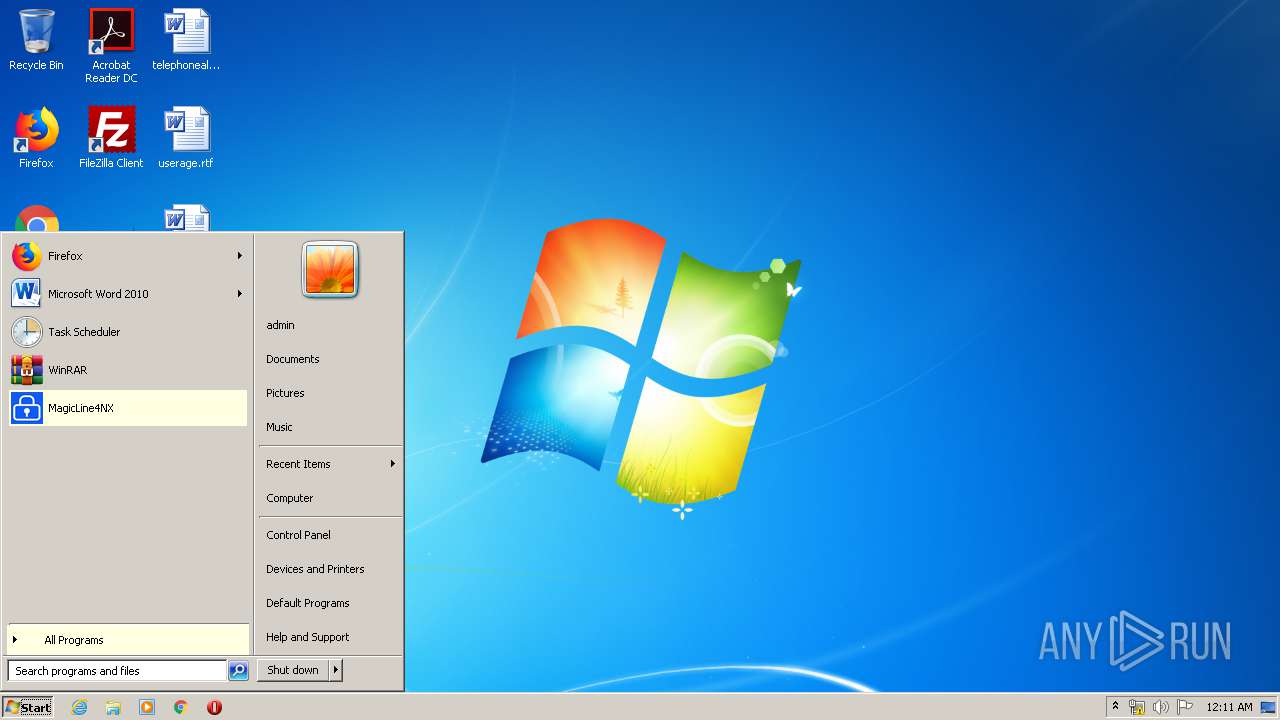
Manual execution by user
- chrome.exe (PID: 772)
- MagicLine4NX.exe (PID: 3832)
Reads the hosts file
- chrome.exe (PID: 772)
- chrome.exe (PID: 3564)
Application launched itself
- chrome.exe (PID: 772)
Reads settings of System Certificates
- chrome.exe (PID: 3564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x320c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.14 |
| ProductVersionNumber: | 1.0.0.14 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Korean |
| CharacterSet: | Windows, Korea (Shift - KSC 5601) |
| CompanyName: | Dreamsecurity, Inc. |
| FileDescription: | MagicLine4NX |
| FileVersion: | 1.0.0.14 |
| LegalCopyright: | Copyright (C) 2016 Dreamsecurity Co., Ltd. All rights reserved. |
| ProductName: | MagicLine4NX |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:41 |
| Detected languages: |
|
| CompanyName: | Dreamsecurity, Inc. |
| FileDescription: | MagicLine4NX |
| FileVersion: | 1.0.0.14 |
| LegalCopyright: | Copyright (C) 2016 Dreamsecurity Co., Ltd. All rights reserved. |
| ProductName: | MagicLine4NX |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000628F | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44221 |
.rdata | 0x00008000 | 0x0000135C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.24004 |
.data | 0x0000A000 | 0x00025518 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.04938 |
.ndata | 0x00030000 | 0x0000C000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003C000 | 0x00005E90 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.52202 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28794 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.76625 | 5189 | UNKNOWN | English - United States | RT_ICON |
3 | 4.68558 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.68846 | 3240 | UNKNOWN | English - United States | RT_ICON |
5 | 6.12825 | 1864 | UNKNOWN | English - United States | RT_ICON |
6 | 0.573426 | 1384 | UNKNOWN | English - United States | RT_ICON |
103 | 2.91321 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.46055 | 236 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.85274 | 264 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.36476 | 76 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
116
Monitored processes
61
Malicious processes
4
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,12497350797665708912,1771760666796734181,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7417979259700053164 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1056,12497350797665708912,1771760666796734181,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13955518585099252377 --mojo-platform-channel-handle=3844 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1056,12497350797665708912,1771760666796734181,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10028357469455499359 --mojo-platform-channel-handle=2764 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1056,12497350797665708912,1771760666796734181,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11172670302708601045 --mojo-platform-channel-handle=3100 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1332 | "C:\Users\admin\AppData\Local\Temp\magicline4nx_setup.exe" | C:\Users\admin\AppData\Local\Temp\magicline4nx_setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Dreamsecurity, Inc. Integrity Level: MEDIUM Description: MagicLine4NX Exit code: 3221226540 Version: 1.0.0.14 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\DreamSecurity\MagicLine4NX\MagicLine4NXServices.exe" | C:\Program Files\DreamSecurity\MagicLine4NX\MagicLine4NXServices.exe | services.exe | ||||||||||||
User: SYSTEM Company: Dreamsecurity Integrity Level: SYSTEM Description: MagicLine4NXServices Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1056,12497350797665708912,1771760666796734181,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4571349885413885482 --mojo-platform-channel-handle=3128 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1056,12497350797665708912,1771760666796734181,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14961609533267485335 --mojo-platform-channel-handle=3556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1748 | "C:\Users\admin\AppData\Local\Temp\nsb7E70.tmp\nsA06B.tmp" sc start MagicLine4NXSVC | C:\Users\admin\AppData\Local\Temp\nsb7E70.tmp\nsA06B.tmp | — | magicline4nx_setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
917
Read events
712
Write events
201
Delete events
4
Modification events
| (PID) Process: | (3376) magicline4nx_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3376) magicline4nx_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2348) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\0BAFEC00CC085C92F94FD1F2DECA2374C72EFFDA |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000000BAFEC00CC085C92F94FD1F2DECA2374C72EFFDA200000000100000068030000308203643082024CA003020102020101300D06092A864886F70D01010B0500304A310B3009060355040613024B52311B3019060355040A1312447265616D736563757269747920496E632E311E301C06035504031315447265616D736563757269747920524F4F54204341301E170D3135303930333034313133345A170D3335303832393034313133345A304A310B3009060355040613024B52311B3019060355040A1312447265616D736563757269747920496E632E311E301C06035504031315447265616D736563757269747920524F4F5420434130820122300D06092A864886F70D01010105000382010F003082010A02820101009DA80827BDF5CF6AEF602D766C4BB961C246FFBB986A7F6F68F9D3DA62F8B11204EA0CFDC66329E238A4A1F477C7E29875A2567B870C8F1A37FCB798B55F7684BB06B81BF1479499B835877EBE79C1411AC22A88A304C275A56F6E3533BA564054E0CC7E1457D8D64A86C596AD797BA242E7DC584F258E8907ABB14AAB23FB5100B10A290AE63AEC24B128E8AE22F77620DF0CAD0DF37F6C71BA81105236E4A99B5E8708DD61441B52D33F610BB76D1918346107F9E2A653524E63FB45C2EF95E63774DB97C19388851887F867A3153664FD6EA3F42B7220DF106627EC309A8F361C953C7772937AEAE2ED6E6551292E8D5F86C2654FFD874092436F0C77A7290203010001A355305330120603551D130101FF040830060101FF020100301D0603551D0E0416041401CA541FACA7DBD3FEAF2327C5AF91273057E1D5300B0603551D0F040403020106301106096086480186F8420101040403020007300D06092A864886F70D01010B050003820101007BE5E98B4D75A4A6789BE6E9E3A499D6EC706BFA78AAD5EEDB6B234CD6439014567A306E10C06A51B1C75B5BFC45543DED522363D25B8562BD1D54662AB22D23093BBAF93AC9D71659048224C27A90BCCD4D6208F68364CFDB826CC1959D526CEEC3D8AA0B2E6EC0DEB0909CEA52394CBE06B4BA22677DDBC751CF8DE1B74314756B4C145727CF80F757496130FB241A3165246DE6361C5C9B6990B512AE627356FA2C665279F7DDE067F0438A2CE89344D6A9F936ADCA46EEF534085B200F5480DC1AA45530BF80FCF9E87DC525F1B7558FC7B9B226554D65CA52B51E32389C18667AFD0061234ED7D5B5892BBB2F5194A3D190AF2179B54349D3003AA09754 | |||
| (PID) Process: | (3376) magicline4nx_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MagicLine4NX |
| Operation: | write | Name: | DisplayName |
Value: MagicLine4NX | |||
| (PID) Process: | (3376) magicline4nx_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MagicLine4NX |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0.0.14 | |||
| (PID) Process: | (3376) magicline4nx_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MagicLine4NX |
| Operation: | write | Name: | Publisher |
Value: Dreamsecurity, Inc. | |||
| (PID) Process: | (3376) magicline4nx_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MagicLine4NX |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\DreamSecurity\MagicLine4NX\MagicLine4NX_Uninstall.exe | |||
| (PID) Process: | (3376) magicline4nx_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MagicLine4NX |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\DreamSecurity\MagicLine4NX\MagicLine4NX_Uninstall.exe | |||
| (PID) Process: | (3376) magicline4nx_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MagicLine4NX |
| Operation: | write | Name: | EstimatedSize |
Value: 17435 | |||
| (PID) Process: | (3376) magicline4nx_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\NTSMagicLineNP |
| Operation: | write | Name: | |
Value: URL:NTSMagicLineNP Protocol | |||
Executable files
39
Suspicious files
41
Text files
273
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | magicline4nx_setup.exe | C:\Users\admin\AppData\Local\Temp\nsb7E70.tmp\ns841F.tmp | — | |
MD5:— | SHA256:— | |||
| 3376 | magicline4nx_setup.exe | C:\Program Files\DreamSecurity\MagicLine4NX\CertManager.dll | executable | |
MD5:— | SHA256:— | |||
| 3376 | magicline4nx_setup.exe | C:\Users\admin\AppData\Local\Temp\nsb7E70.tmp\nsProcess.dll | executable | |
MD5:FAA7F034B38E729A983965C04CC70FC1 | SHA256:579A034FF5AB9B732A318B1636C2902840F604E8E664F5B93C07A99253B3C9CF | |||
| 3376 | magicline4nx_setup.exe | C:\Users\admin\AppData\Local\Temp\nsb7E70.tmp\ns8324.tmp | executable | |
MD5:— | SHA256:— | |||
| 3376 | magicline4nx_setup.exe | C:\Program Files\DreamSecurity\MagicLine4NX\MagicLine4NX.exe | executable | |
MD5:— | SHA256:— | |||
| 3376 | magicline4nx_setup.exe | C:\Program Files\DreamSecurity\MagicLine4NX\MagicLine4NX.exe.hmac | binary | |
MD5:— | SHA256:— | |||
| 3376 | magicline4nx_setup.exe | C:\Users\admin\AppData\Local\Temp\nsb7E70.tmp\System.dll | executable | |
MD5:FBE295E5A1ACFBD0A6271898F885FE6A | SHA256:A1390A78533C47E55CC364E97AF431117126D04A7FAED49390210EA3E89DD0E1 | |||
| 3376 | magicline4nx_setup.exe | C:\Users\admin\AppData\Local\Temp\nsb7E70.tmp\KillProcDLL.dll | executable | |
MD5:83142EAC84475F4CA889C73F10D9C179 | SHA256:AE2F1658656E554F37E6EAC896475A3862841A18FFC6FAD2754E2D3525770729 | |||
| 3376 | magicline4nx_setup.exe | C:\Program Files\DreamSecurity\MagicLine4NX\KOR.ini | text | |
MD5:A8E649082B174EBC810DD565F02EBFF1 | SHA256:CD3EC7C1CC5515839299A00E2D172564939D39C52FF2DADBEDACB3C0CB8E3BBC | |||
| 3376 | magicline4nx_setup.exe | C:\Program Files\DreamSecurity\MagicLine4NX\DSCToolkitV30-v3.4.2.20.dll | executable | |
MD5:A48558F7999A0382CD5D5F3063D87E96 | SHA256:C5B6BC8DA03C677EAA37E67F6FBC8735943DCC1329548CDDDA7BFFBEEA6EFCEE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
39
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3564 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
3564 | chrome.exe | GET | 200 | 173.194.183.73:80 | http://r4---sn-aigl6ned.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.217.117.55&mm=28&mn=sn-aigl6ned&ms=nvh&mt=1583971815&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
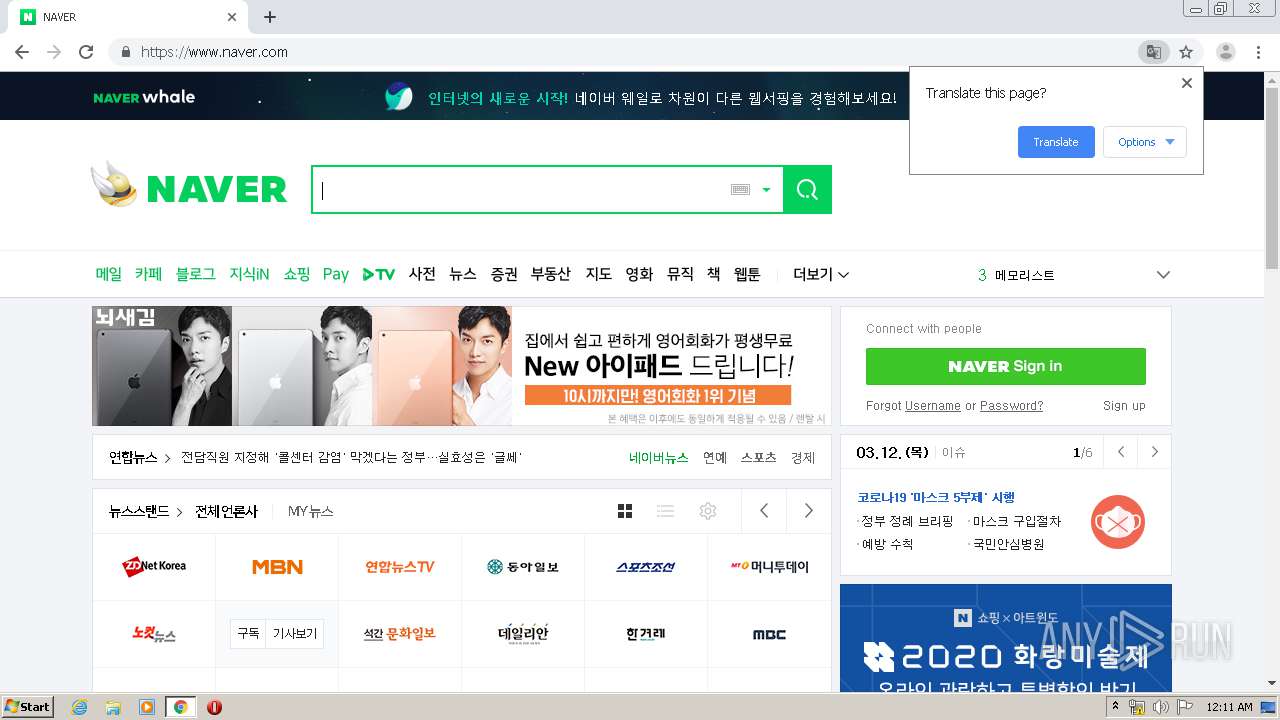
3564 | chrome.exe | GET | 301 | 210.89.164.90:80 | http://naver.com/ | KR | html | 162 b | unknown |
3564 | chrome.exe | GET | 200 | 173.194.139.6:80 | http://r1---sn-aigzrn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.217.117.55&mm=28&mn=sn-aigzrn7k&ms=nvh&mt=1583971815&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3564 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
3564 | chrome.exe | GET | 302 | 23.210.249.75:80 | http://www.naver.com/ | NL | html | 138 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3564 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3564 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3564 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3564 | chrome.exe | 216.58.206.14:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
3564 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3564 | chrome.exe | 172.217.23.142:443 | apis.google.com | Google Inc. | US | whitelisted |
3564 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3564 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
3564 | chrome.exe | 216.58.208.35:443 | www.google.co.uk | Google Inc. | US | whitelisted |
— | — | 216.58.208.35:443 | www.google.co.uk | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.co.uk |
| whitelisted |
Threats
Process | Message |
|---|---|
MagicLine4NX.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
MagicLine4NXServices.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
MagicLine4NXServices.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
MagicLine4NX.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|