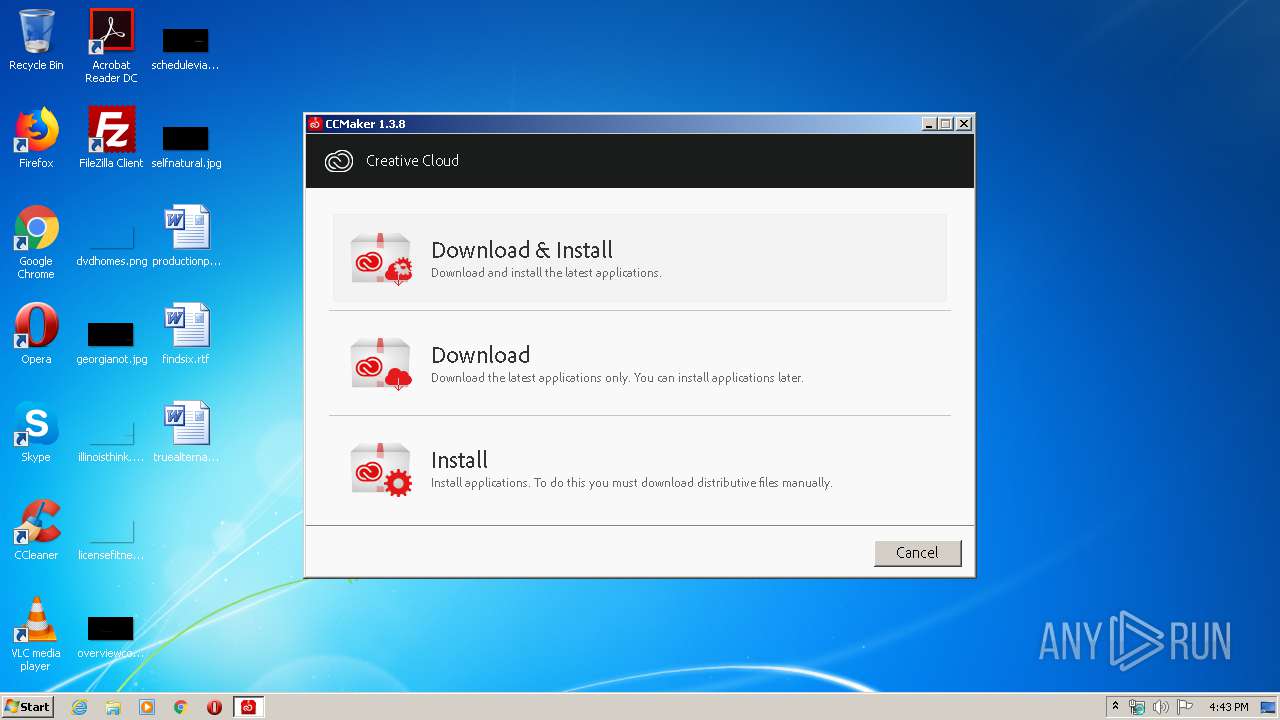
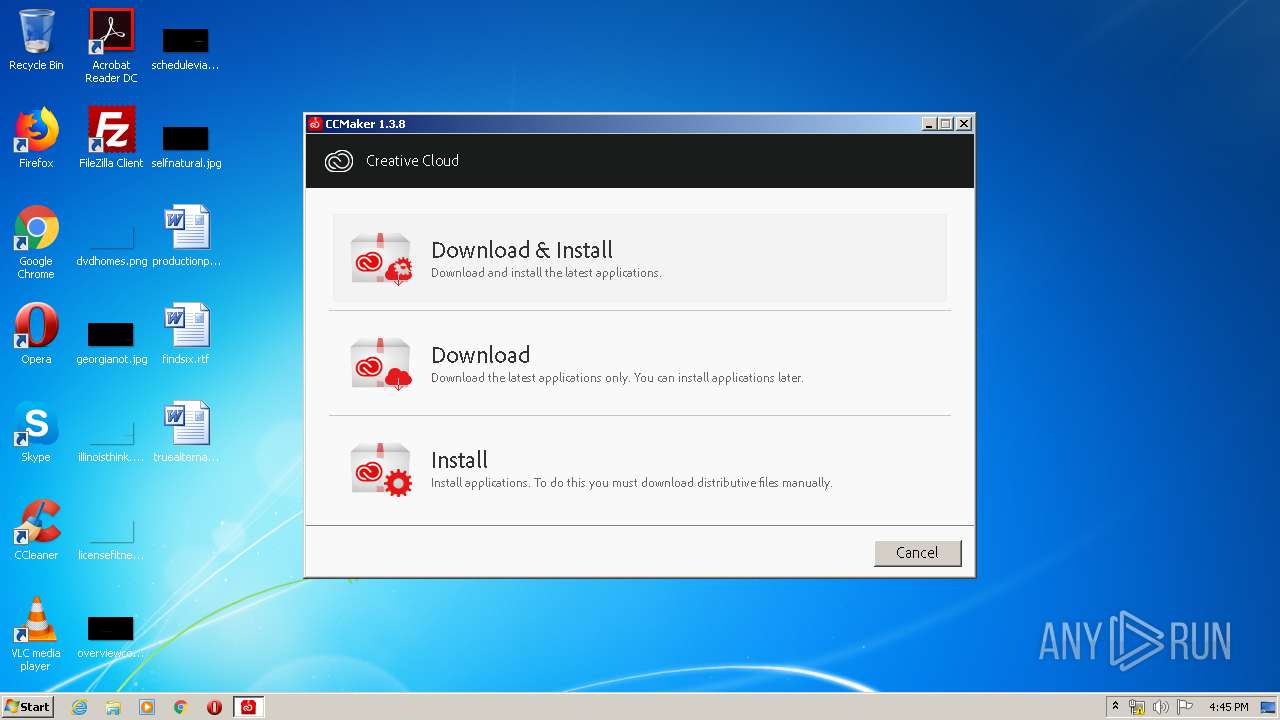
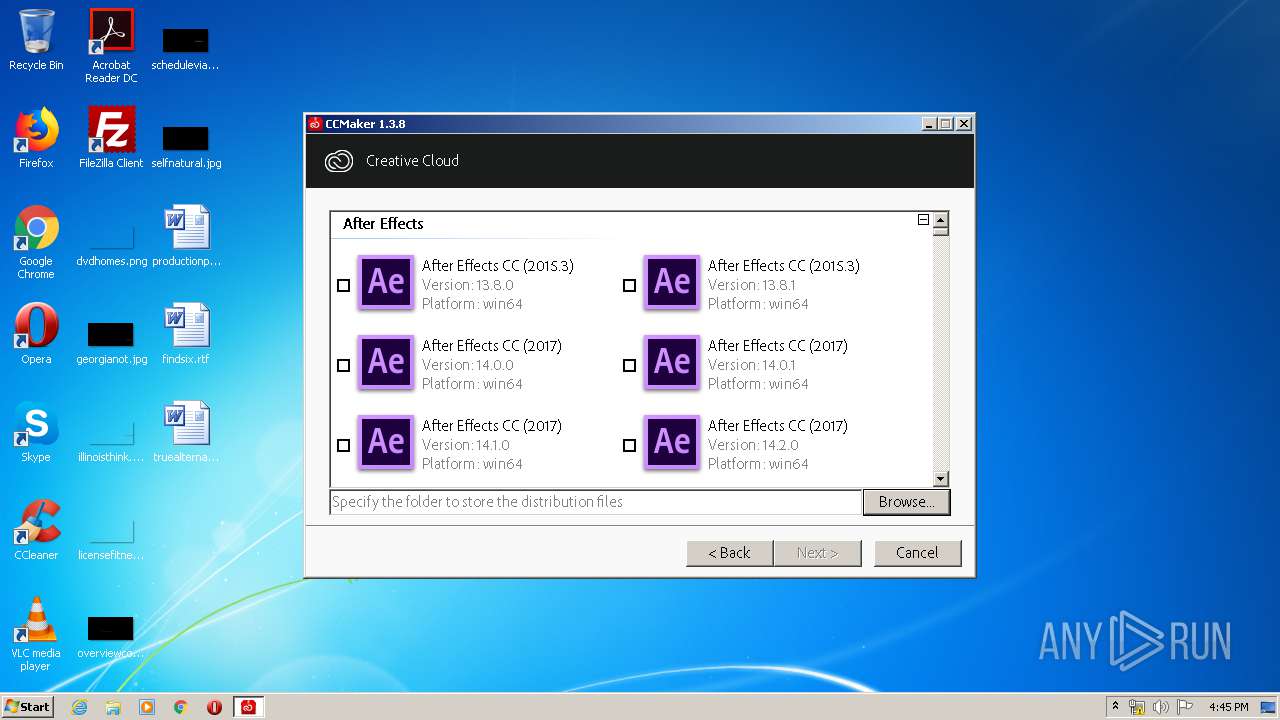
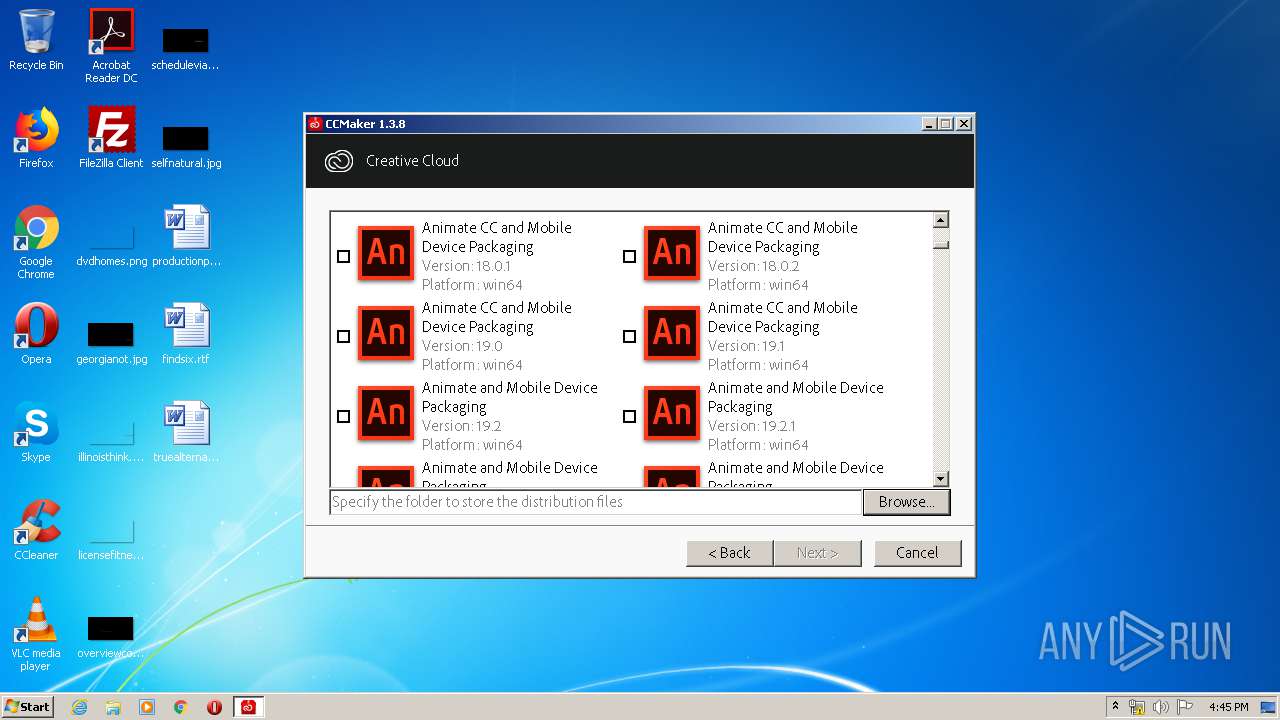
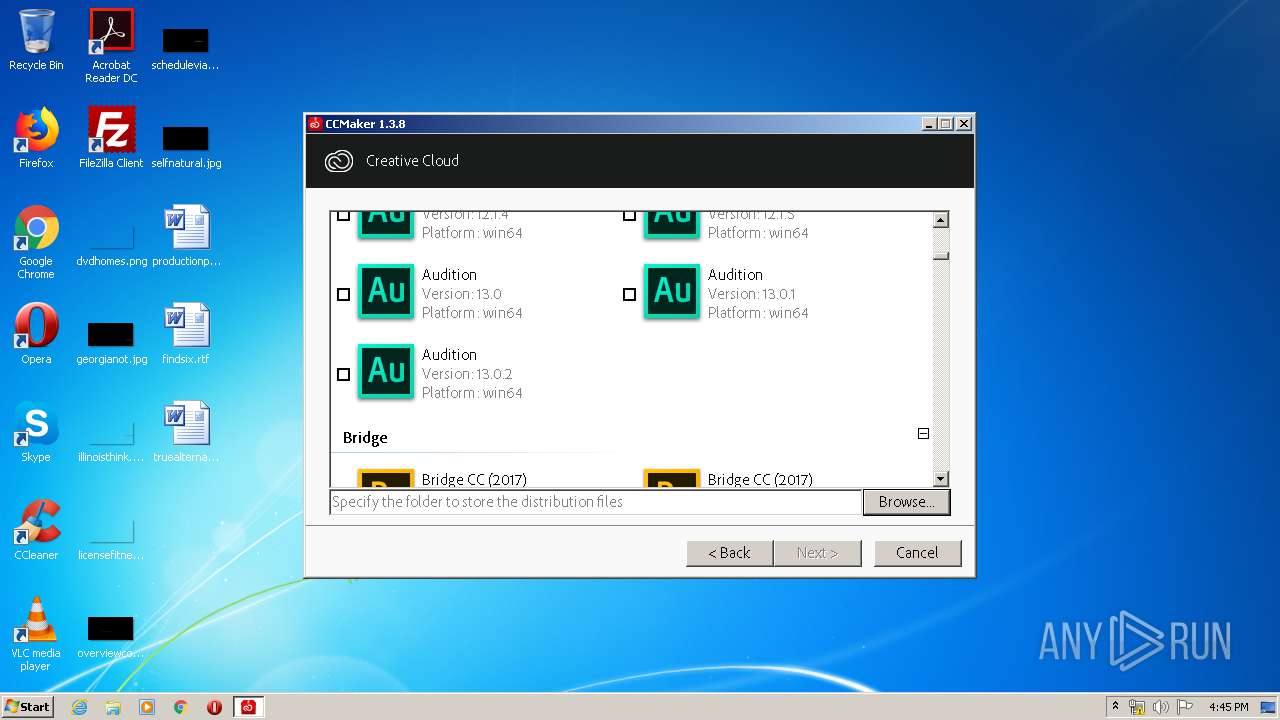
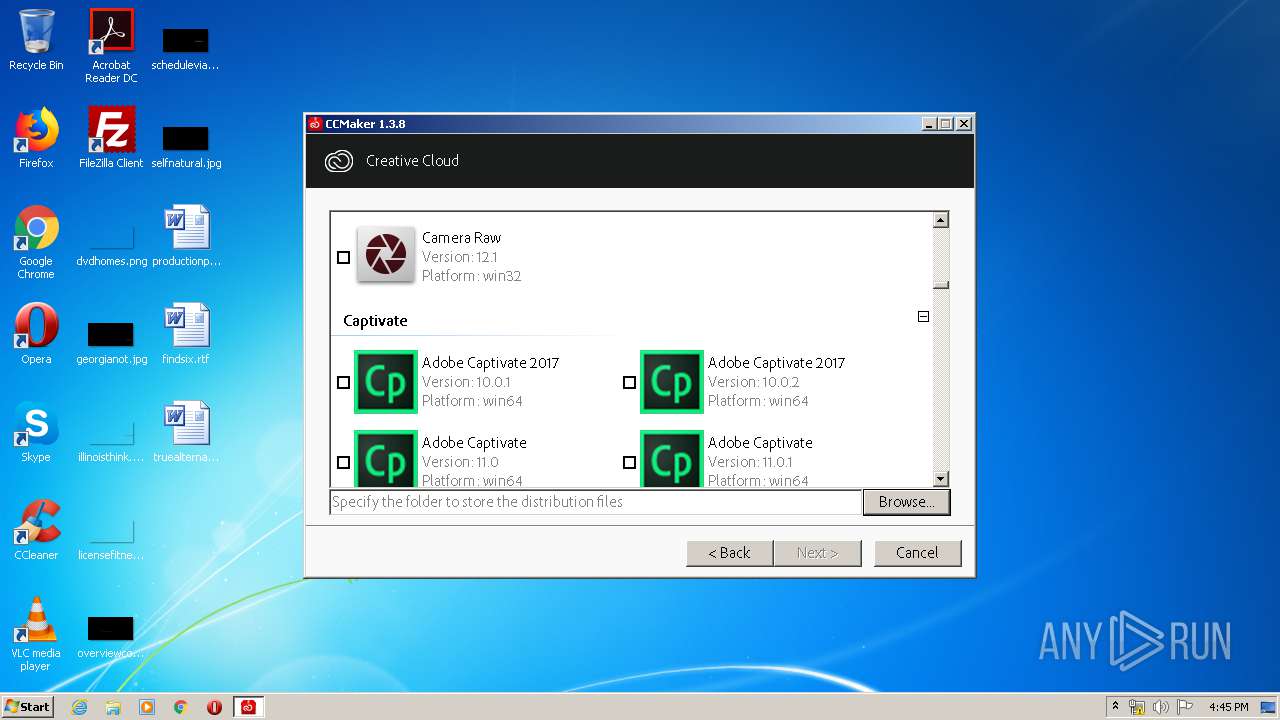
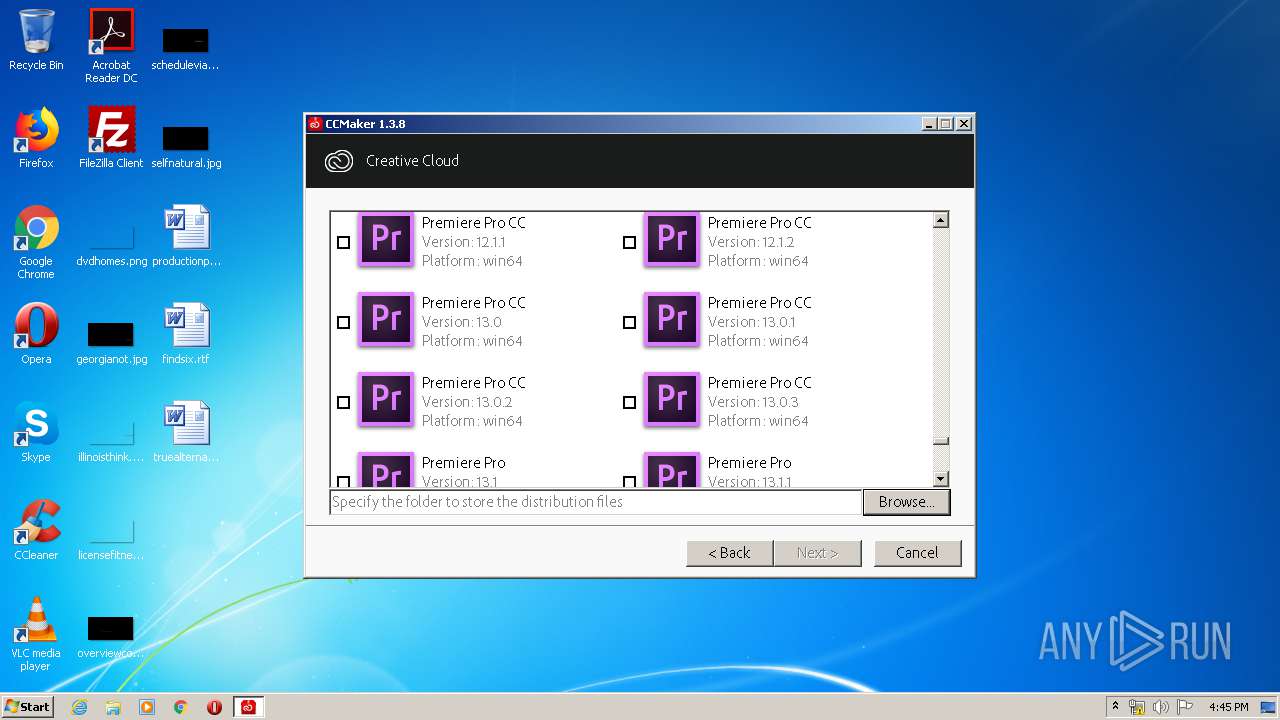
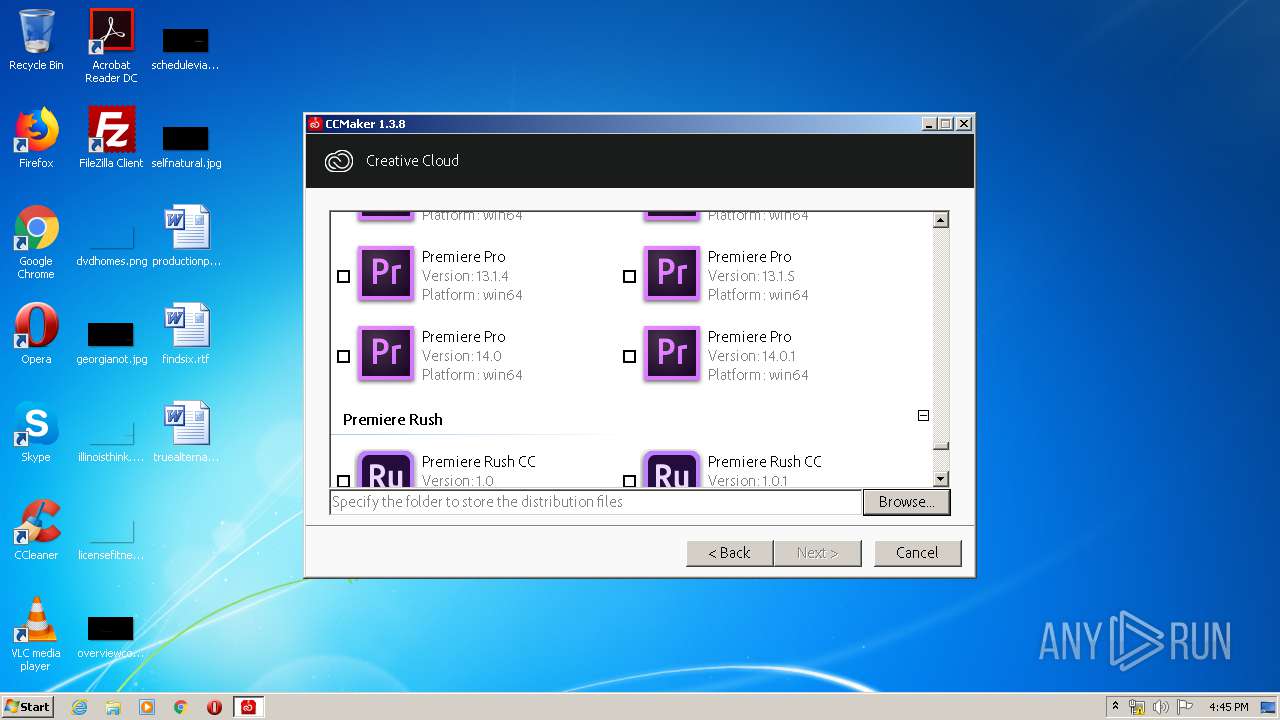
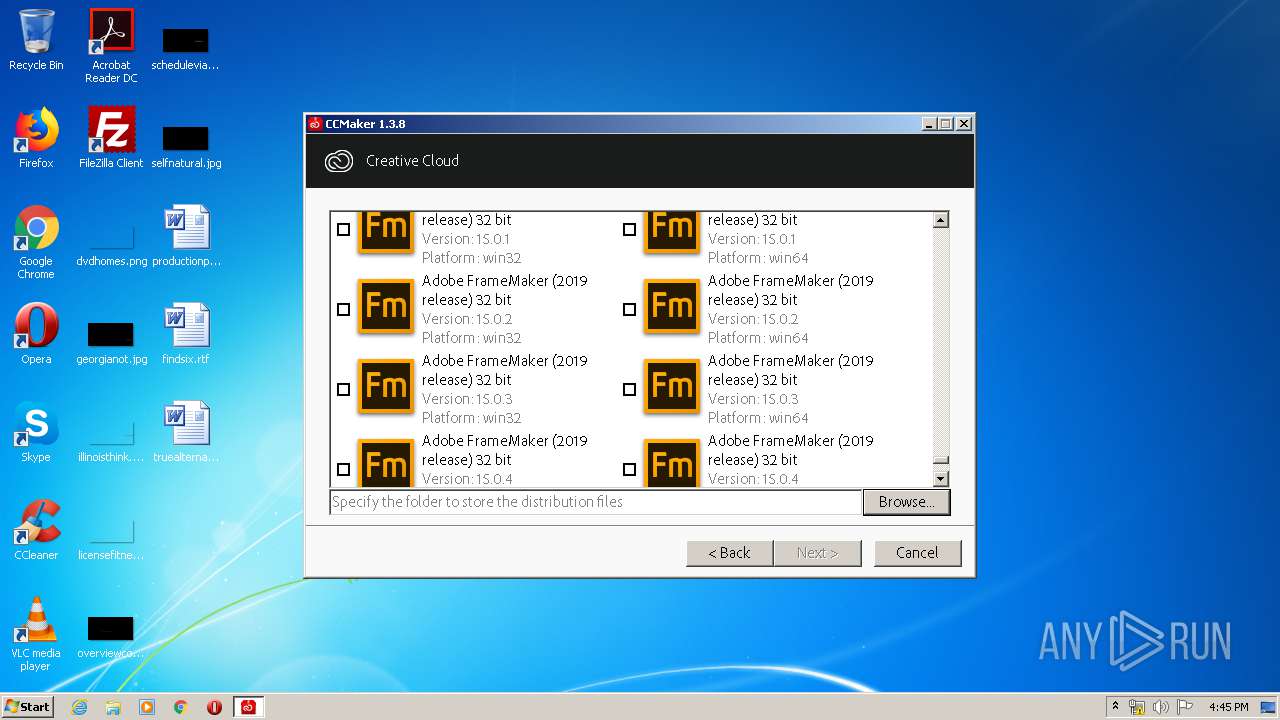
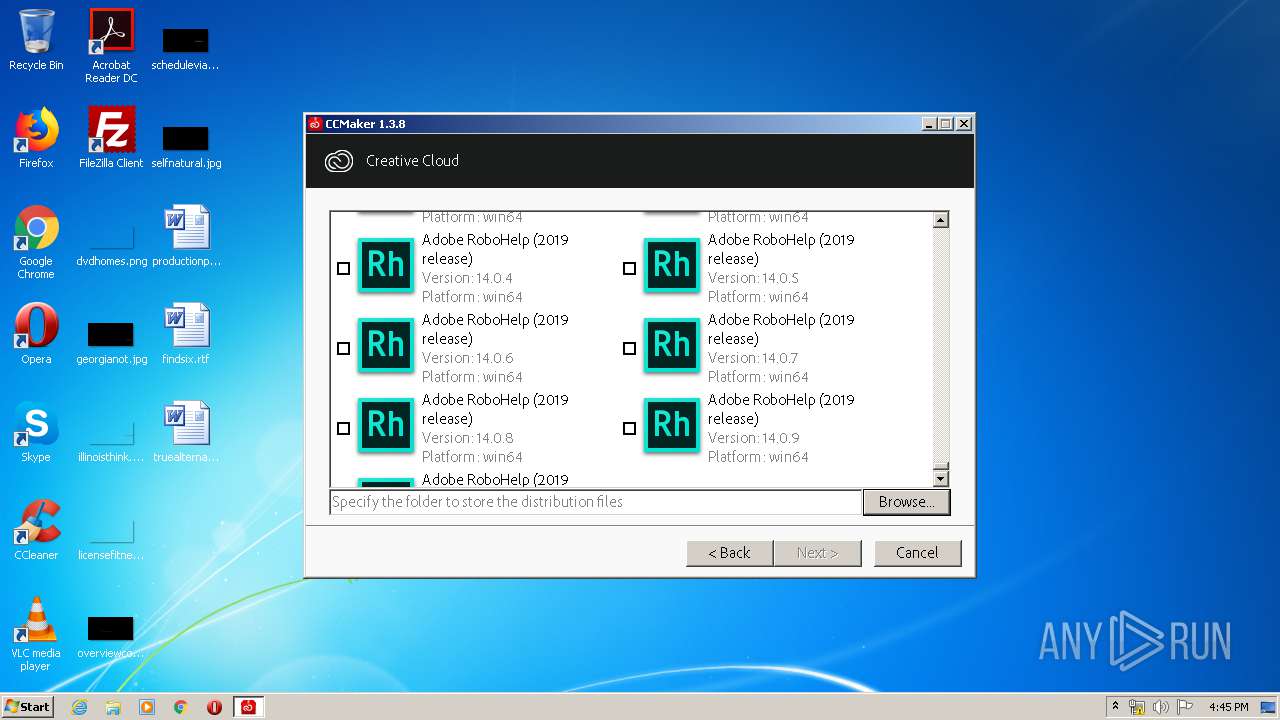
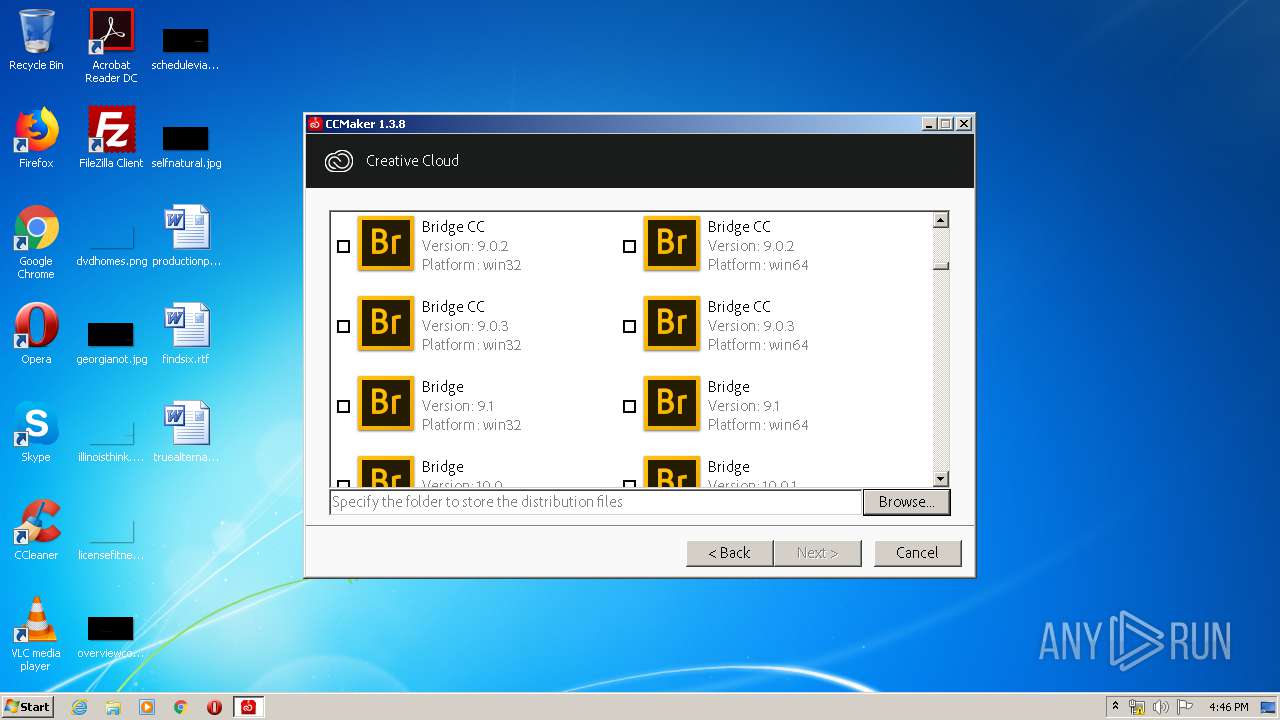
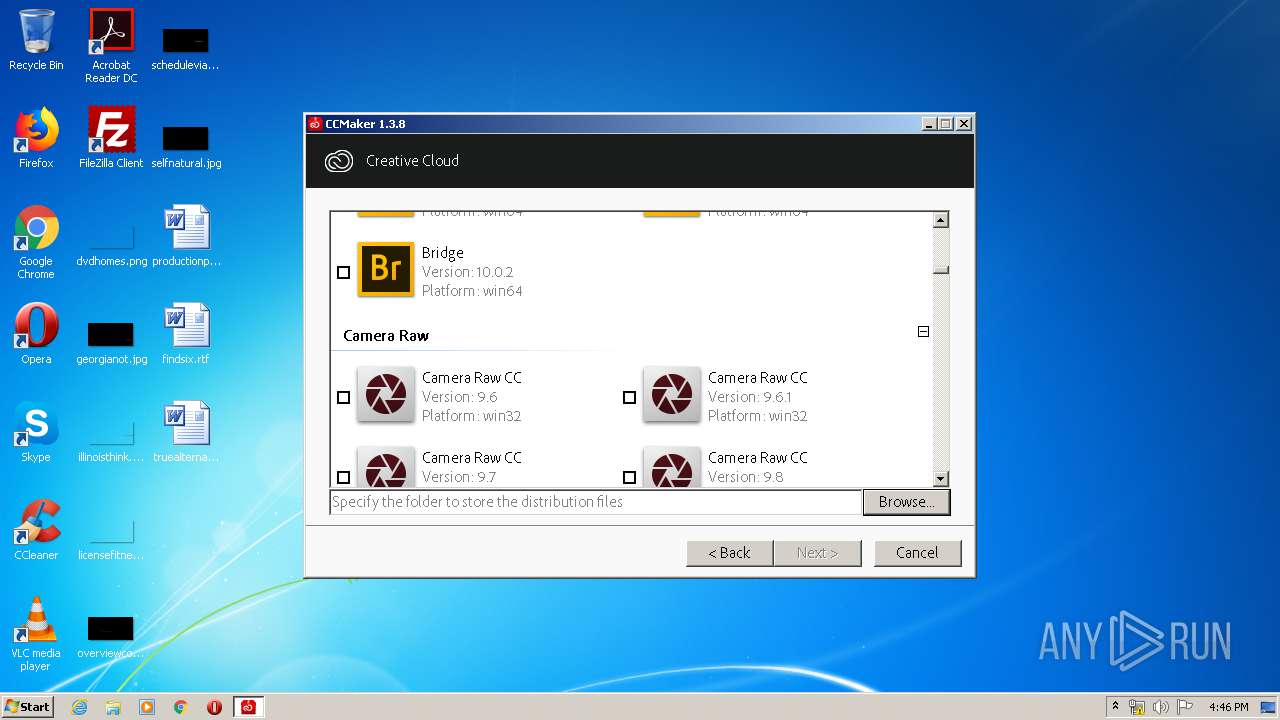
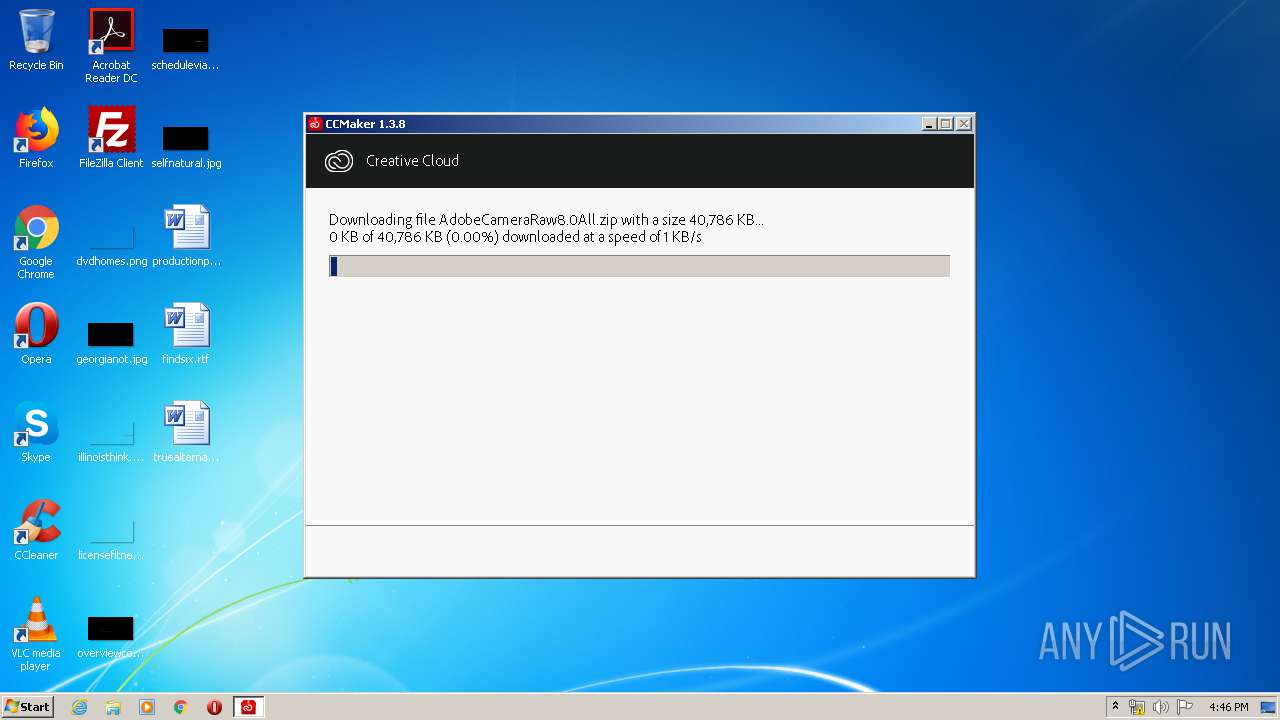
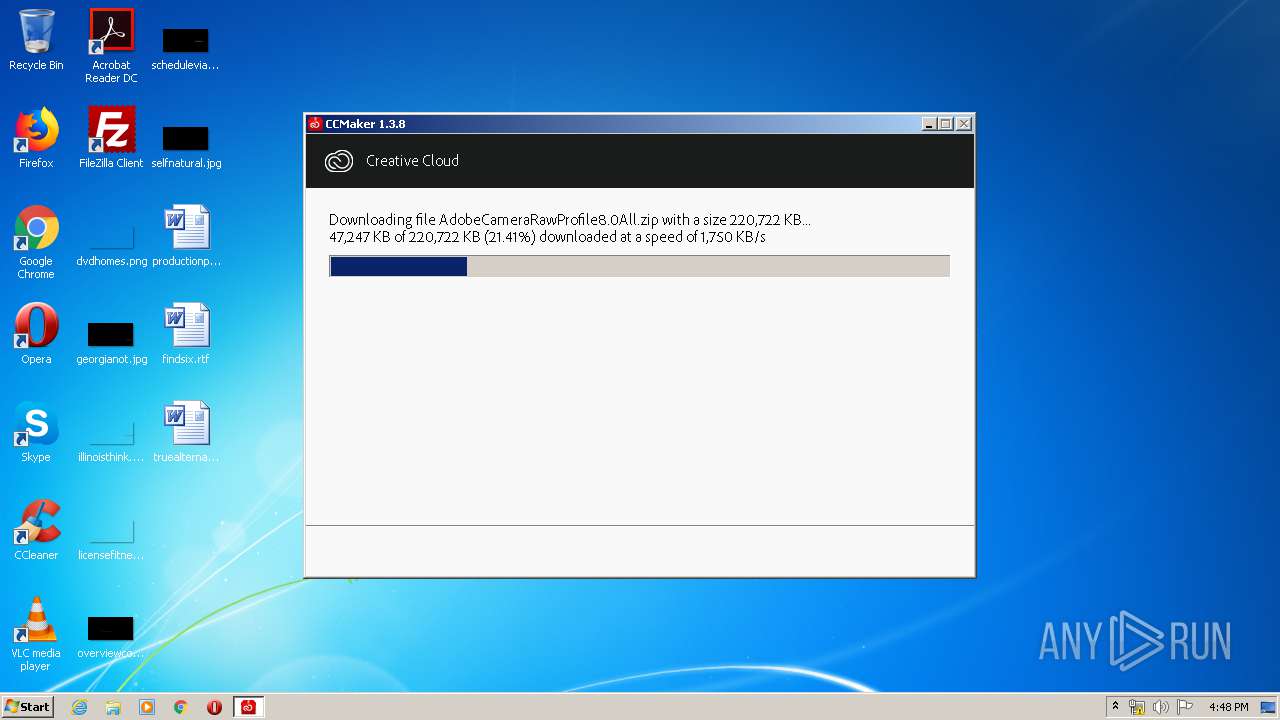
| File name: | CCMaker.exe |
| Full analysis: | https://app.any.run/tasks/fe38f142-39d2-465b-978b-5bfaf6915413 |
| Verdict: | Malicious activity |
| Analysis date: | January 31, 2020, 16:43:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7080B67C5E0BBB0BDA76867078B4A926 |
| SHA1: | 2BBA01C5E2794A1EA57F8A2E80EEF5019891E5E3 |
| SHA256: | 7908914795B42D6976D8DE7BFCD33295BCAD56982F6A69FD18179B9CE9C60E57 |
| SSDEEP: | 49152:UctlfxMSp8Zx34SDBWM4KonJCZ8hnr8U4pb0ziatN6yGe5WCucHInozkuf:rf2AexodykAwnkpb0zFttMCzHZkS |
MALICIOUS
Changes settings of System certificates
- CCMaker.tmp (PID: 3792)
SUSPICIOUS
Reads Windows owner or organization settings
- CCMaker.tmp (PID: 3792)
Executable content was dropped or overwritten
- CCMaker.exe (PID: 3976)
- CCMaker.tmp (PID: 3792)
Reads the Windows organization settings
- CCMaker.tmp (PID: 3792)
Reads Internet Cache Settings
- CCMaker.tmp (PID: 3792)
Adds / modifies Windows certificates
- CCMaker.tmp (PID: 3792)
INFO
Application was dropped or rewritten from another process
- CCMaker.tmp (PID: 3792)
Loads dropped or rewritten executable
- CCMaker.tmp (PID: 3792)
Reads settings of System Certificates
- CCMaker.tmp (PID: 3792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:10:02 07:04:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 86016 |
| InitializedDataSize: | 82944 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16478 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.8.0 |
| ProductVersionNumber: | 1.3.8.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Pendejo Software |
| FileDescription: | CCMaker |
| FileVersion: | 1.3.8 |
| LegalCopyright: | |
| ProductName: | CCMaker |
| ProductVersion: | 1.3.8 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Oct-2012 05:04:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Pendejo Software |
| FileDescription: | CCMaker |
| FileVersion: | 1.3.8 |
| LegalCopyright: | - |
| ProductName: | CCMaker |
| ProductVersion: | 1.3.8 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 02-Oct-2012 05:04:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000143F8 | 0x00014400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4822 |
.itext | 0x00016000 | 0x00000BE8 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.01516 |
.data | 0x00017000 | 0x00000D9C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.66929 |
.bss | 0x00018000 | 0x00005750 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001E000 | 0x00000F9E | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96778 |
.tls | 0x0001F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00020000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.190489 |
.rsrc | 0x00021000 | 0x00012380 | 0x00012400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.72566 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.1535 | 1582 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.71082 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.36809 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 7.94332 | 5750 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 7.93596 | 12665 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 3.13038 | 196 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.36196 | 204 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.34841 | 372 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.29351 | 924 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
39
Monitored processes
3
Malicious processes
2
Suspicious processes
0
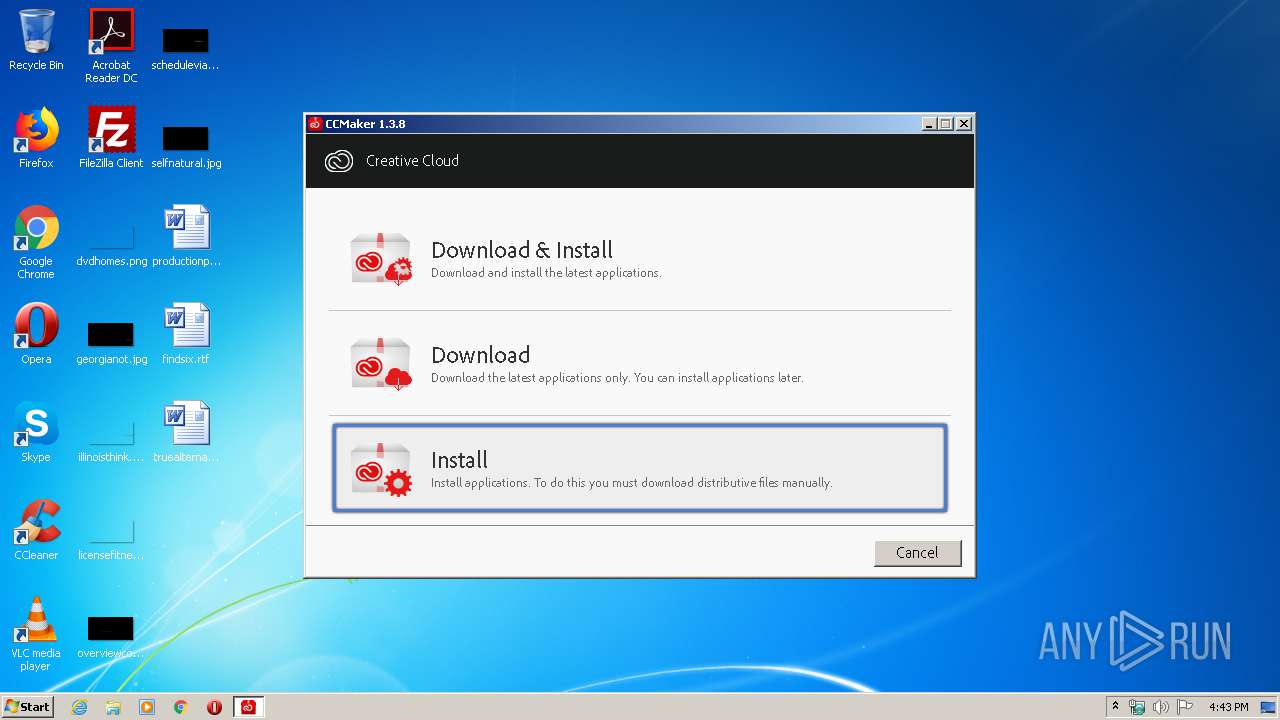
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3264 | "C:\Users\admin\AppData\Local\Temp\CCMaker.exe" | C:\Users\admin\AppData\Local\Temp\CCMaker.exe | — | explorer.exe | |||||||||||
User: admin Company: Pendejo Software Integrity Level: MEDIUM Description: CCMaker Exit code: 3221226540 Version: 1.3.8 Modules
| |||||||||||||||
| 3792 | "C:\Users\admin\AppData\Local\Temp\is-90MHC.tmp\CCMaker.tmp" /SL5="$A0140,1695615,169984,C:\Users\admin\AppData\Local\Temp\CCMaker.exe" | C:\Users\admin\AppData\Local\Temp\is-90MHC.tmp\CCMaker.tmp | CCMaker.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3976 | "C:\Users\admin\AppData\Local\Temp\CCMaker.exe" | C:\Users\admin\AppData\Local\Temp\CCMaker.exe | explorer.exe | ||||||||||||
User: admin Company: Pendejo Software Integrity Level: HIGH Description: CCMaker Exit code: 0 Version: 1.3.8 Modules
| |||||||||||||||
Total events
1 862
Read events
621
Write events
1 240
Delete events
1
Modification events
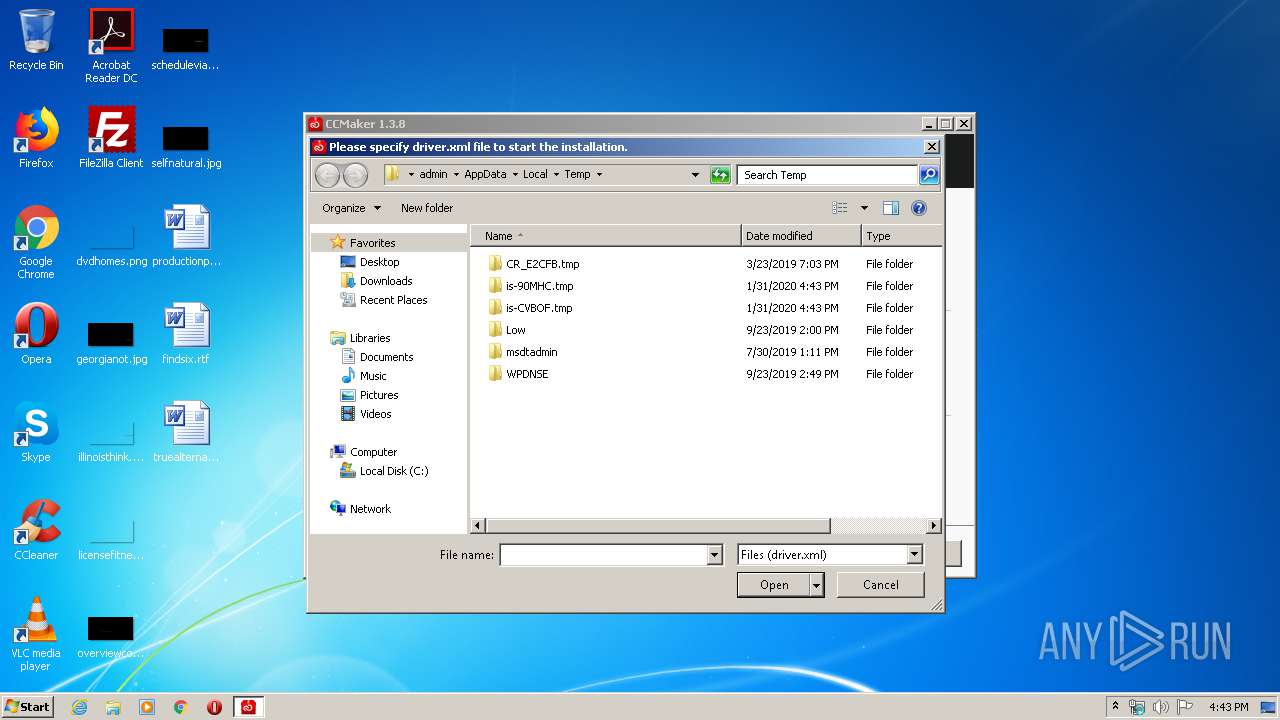
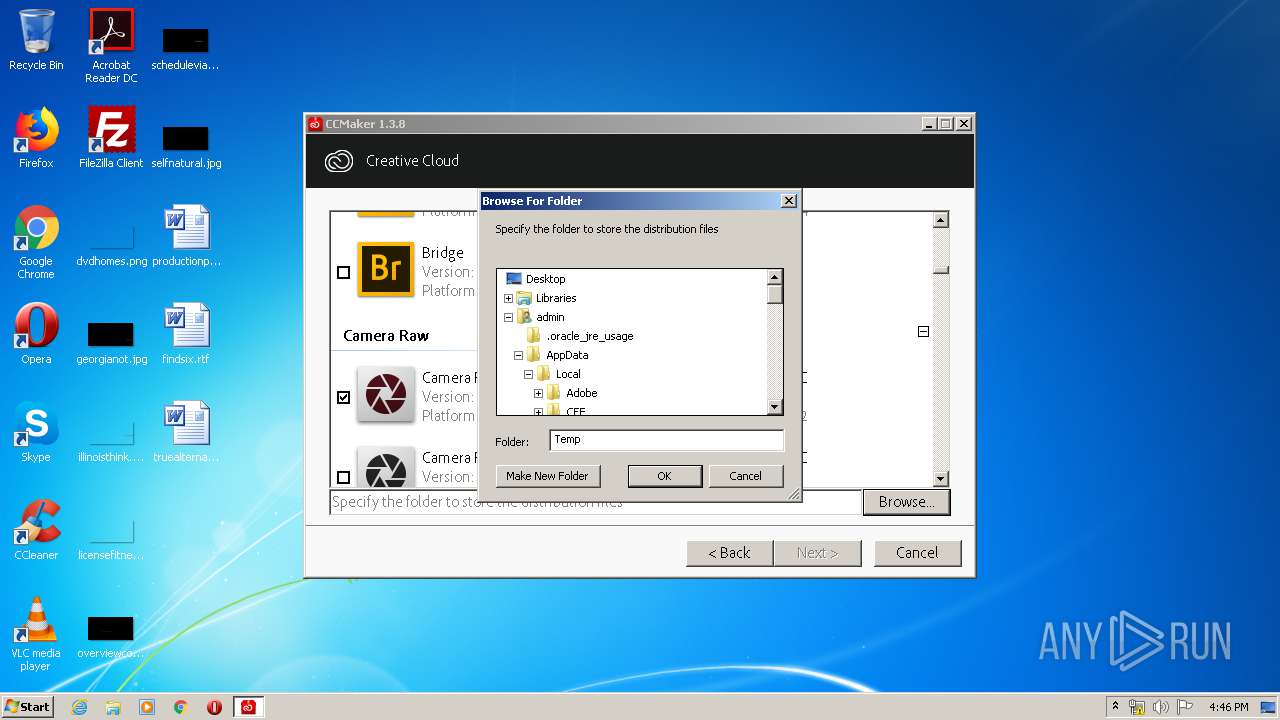
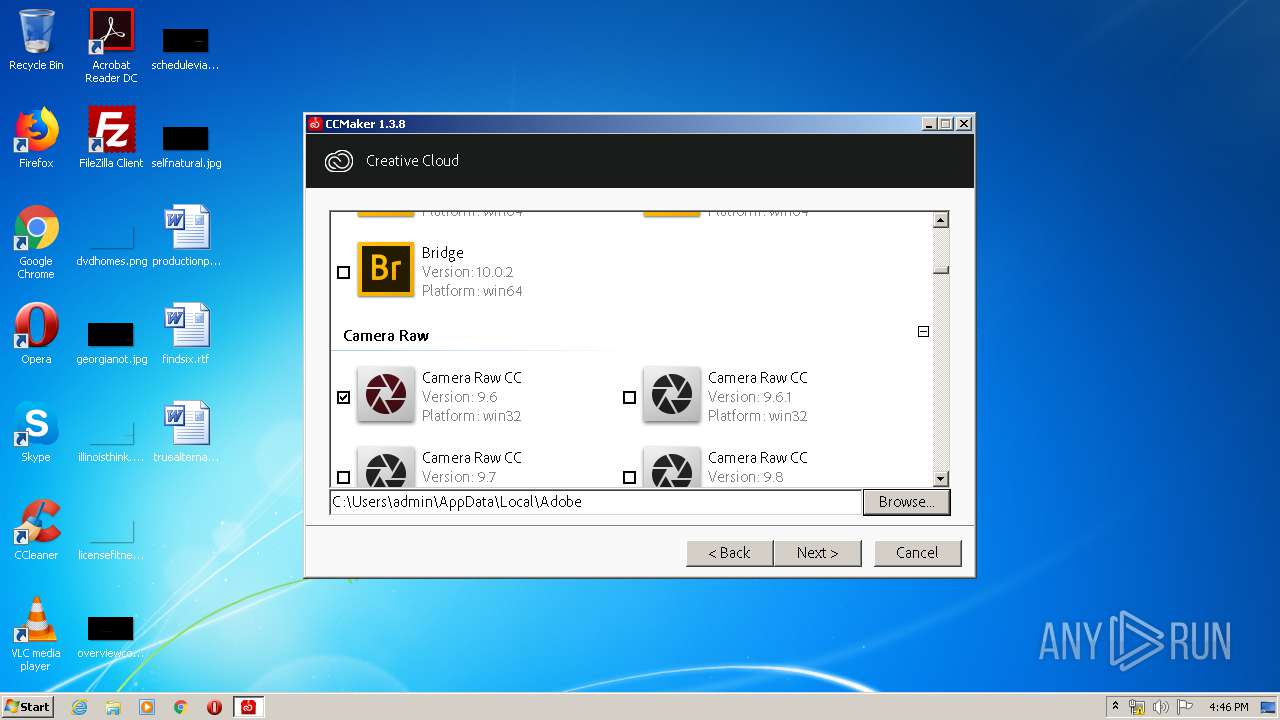
| (PID) Process: | (3792) CCMaker.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00690073002D00390030004D00480043002E0074006D0070005C00430043004D0061006B00650072002E0074006D007000000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070000000 | |||
| (PID) Process: | (3792) CCMaker.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (3792) CCMaker.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3792) CCMaker.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0700000001000000020000000A00000009000000080000000000000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3792) CCMaker.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (3792) CCMaker.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3792) CCMaker.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 1 |
Value: 430043004D0061006B00650072002E0074006D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000003201000086000000B203000066020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (3792) CCMaker.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | 1 |
Value: 430043004D0061006B00650072002E0074006D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000003201000086000000B203000066020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (3792) CCMaker.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 1 |
Value: 430043004D0061006B00650072002E0074006D0070000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002F01000070000000D103000043020000000000000000000000000000000000003201000086000000B203000066020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (3792) CCMaker.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
Executable files
4
Suspicious files
9
Text files
5
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3792 | CCMaker.tmp | C:\Users\admin\AppData\Local\Temp\is-CVBOF.tmp\NEW.PNG | — | |
MD5:— | SHA256:— | |||
| 3792 | CCMaker.tmp | C:\Users\admin\AppData\Local\Temp\CabCCCE.tmp | — | |
MD5:— | SHA256:— | |||
| 3792 | CCMaker.tmp | C:\Users\admin\AppData\Local\Temp\TarCCCF.tmp | — | |
MD5:— | SHA256:— | |||
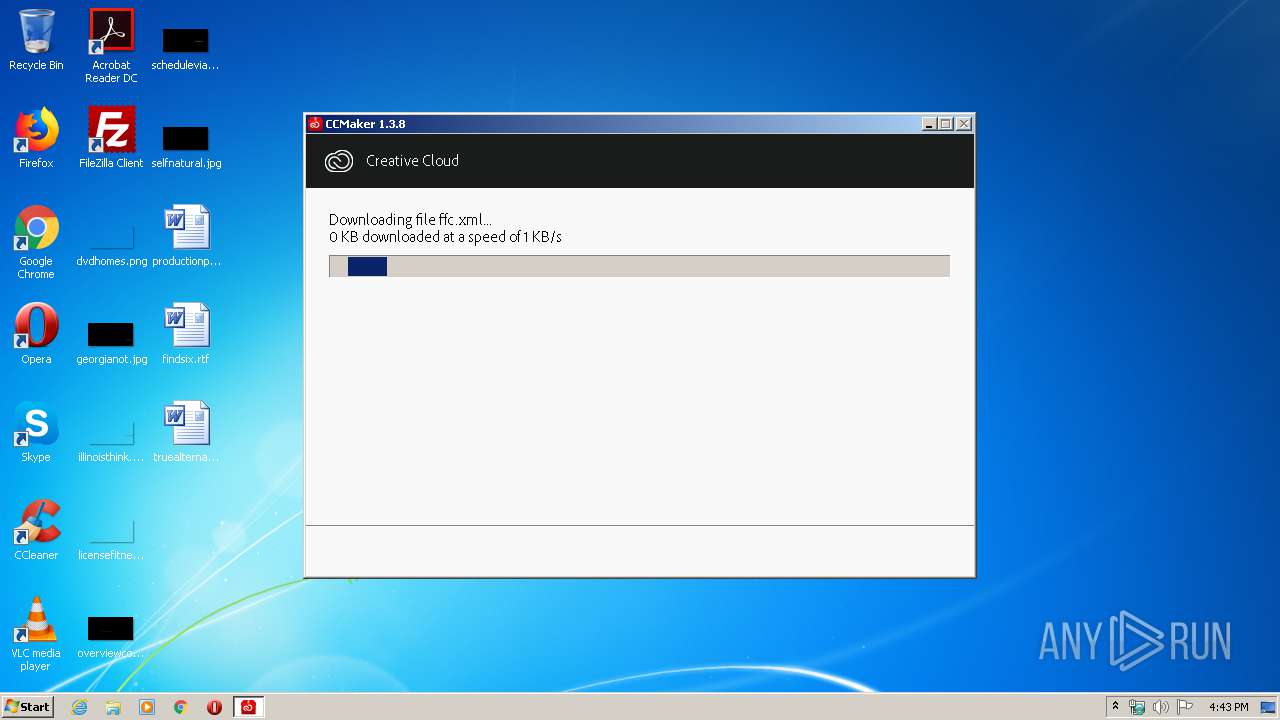
| 3792 | CCMaker.tmp | C:\Users\admin\AppData\Local\Temp\is-CVBOF.tmp\ffc.xml.partial | — | |
MD5:— | SHA256:— | |||
| 3792 | CCMaker.tmp | C:\Users\admin\AppData\Local\Temp\is-CVBOF.tmp\ffc.xml | — | |
MD5:— | SHA256:— | |||
| 3792 | CCMaker.tmp | C:\Users\admin\AppData\Local\Temp\is-CVBOF.tmp\group.png.partial | — | |
MD5:— | SHA256:— | |||
| 3792 | CCMaker.tmp | C:\Users\admin\AppData\Local\Temp\is-CVBOF.tmp\group.png | — | |
MD5:— | SHA256:— | |||
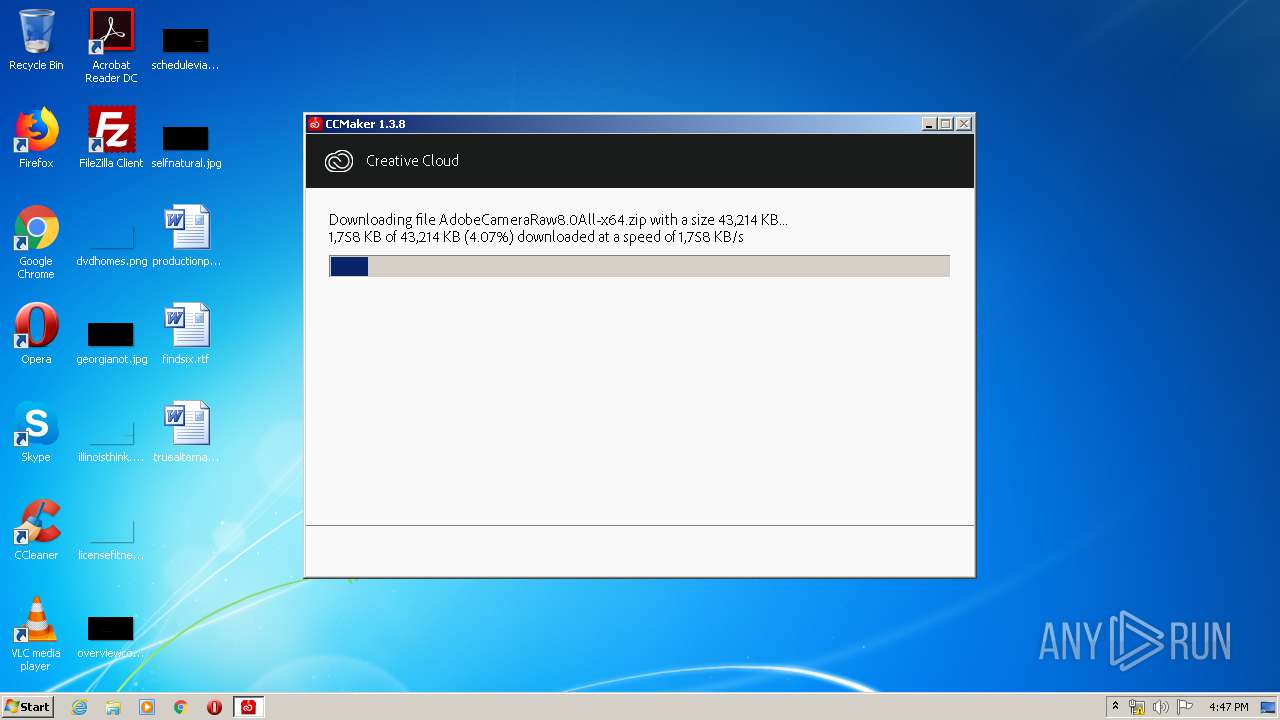
| 3792 | CCMaker.tmp | C:\Users\admin\AppData\Local\Temp\is-CVBOF.tmp\win32\ACR\9.6.0.126\application.json.partial | — | |
MD5:— | SHA256:— | |||
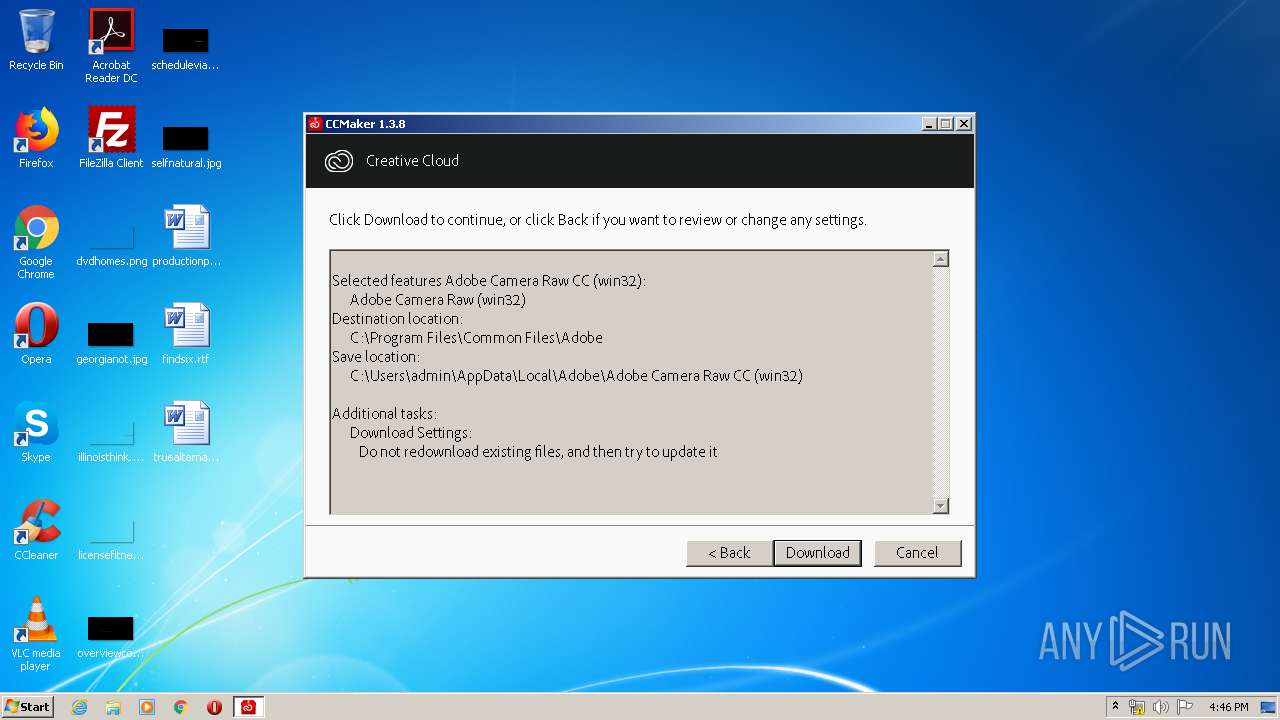
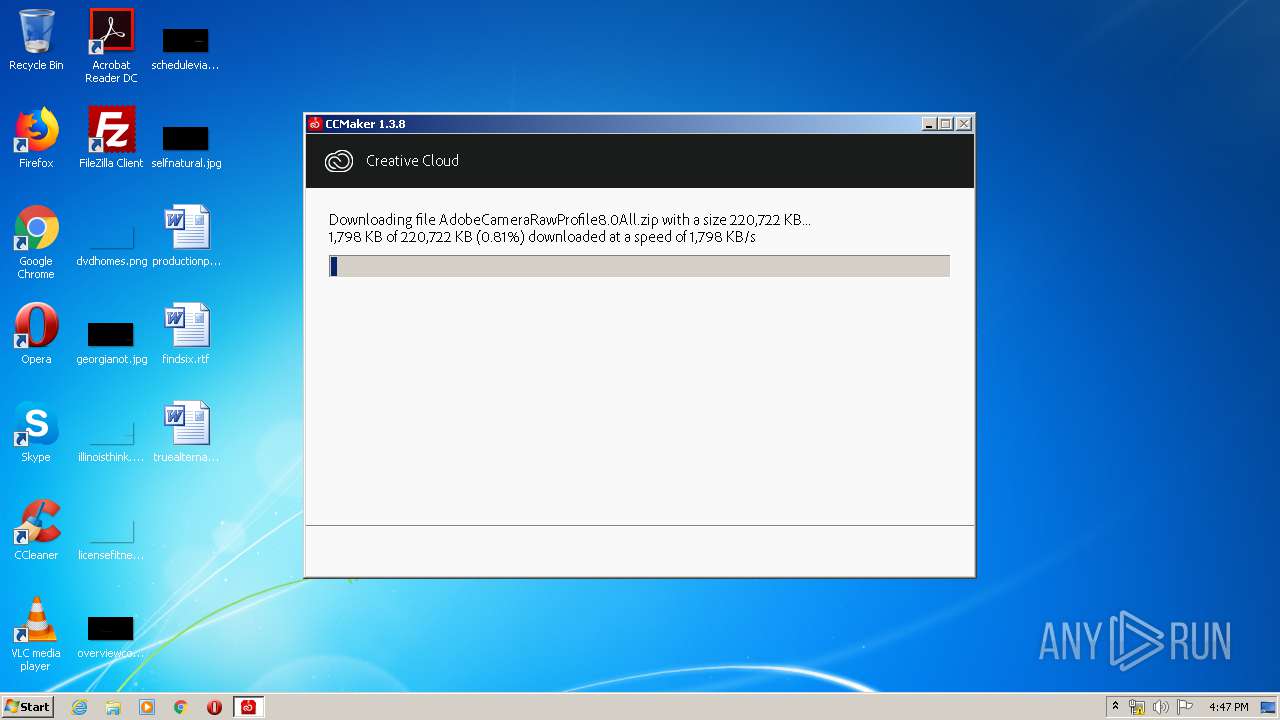
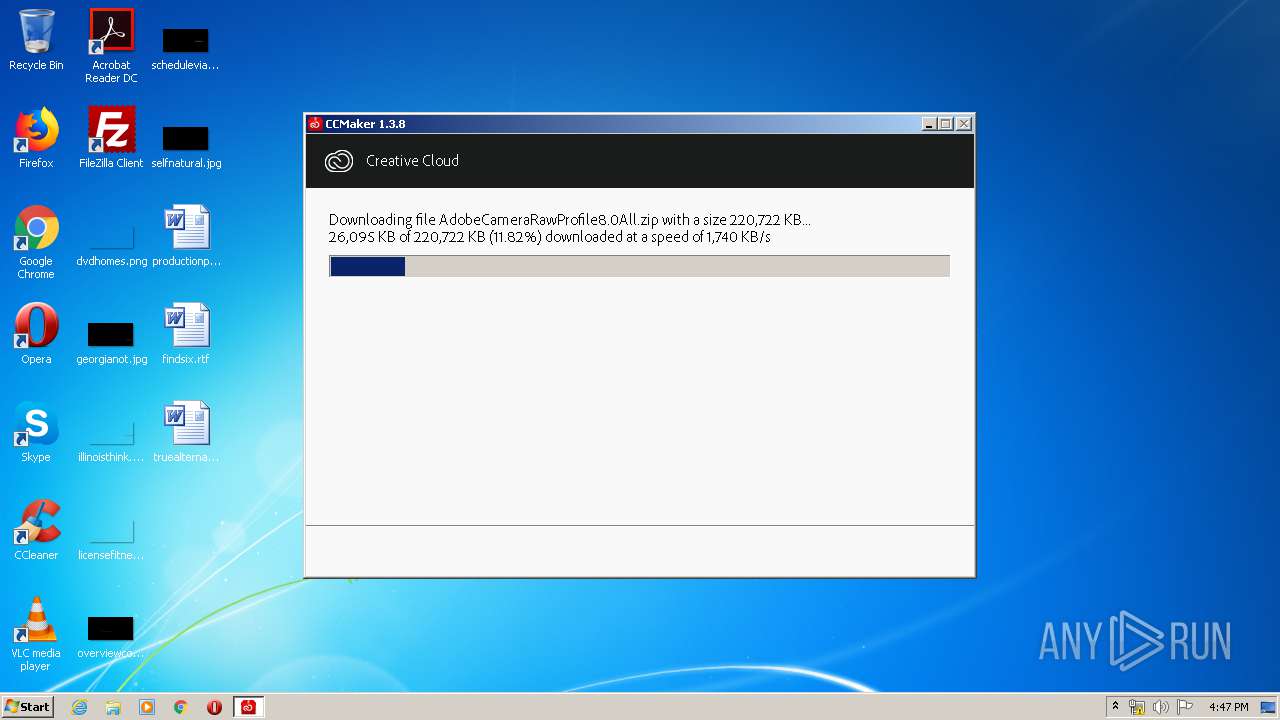
| 3792 | CCMaker.tmp | C:\Users\admin\AppData\Local\Adobe\Adobe Camera Raw CC (win32)\products\ACR\CameraRawRIBSCoExistPackage.zip.partial | — | |
MD5:— | SHA256:— | |||
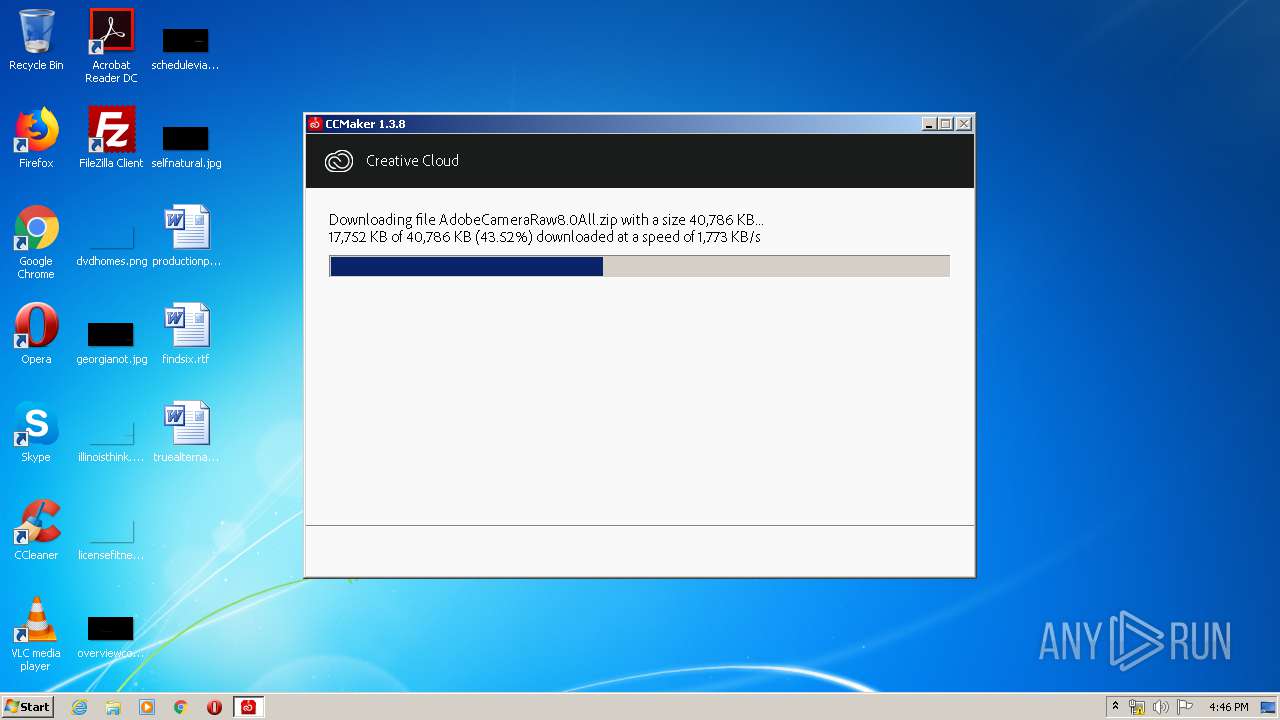
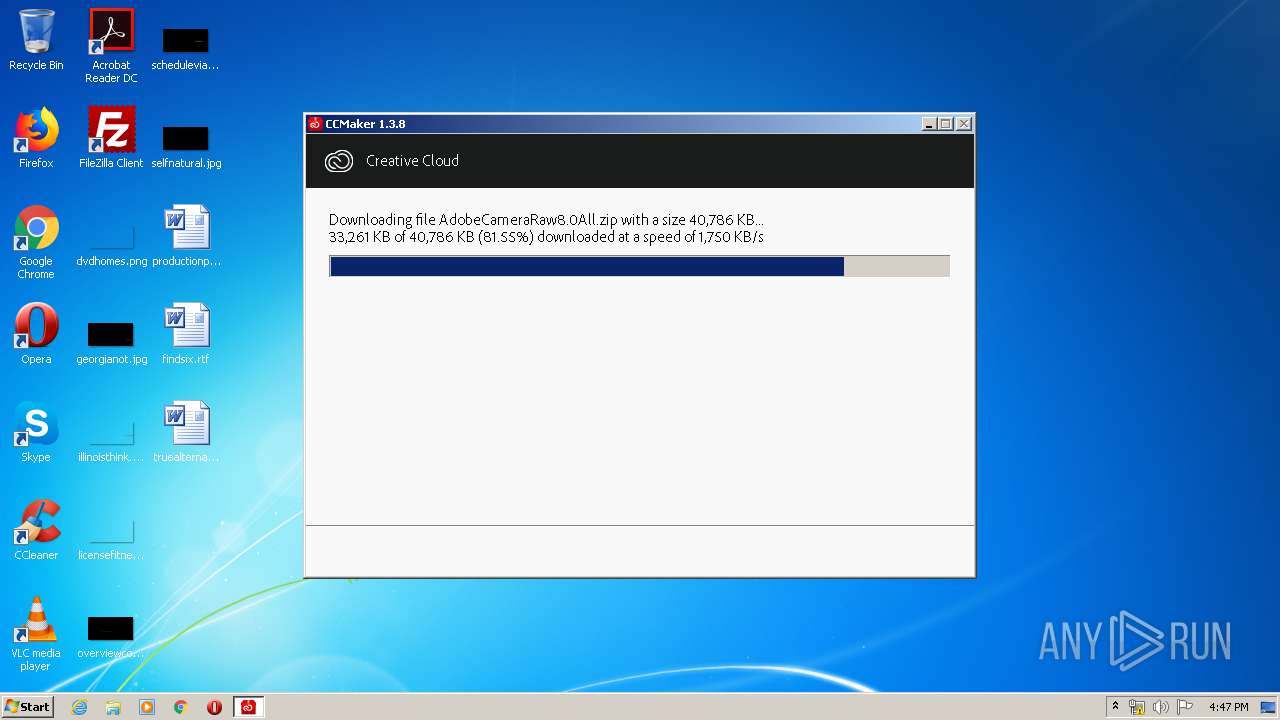
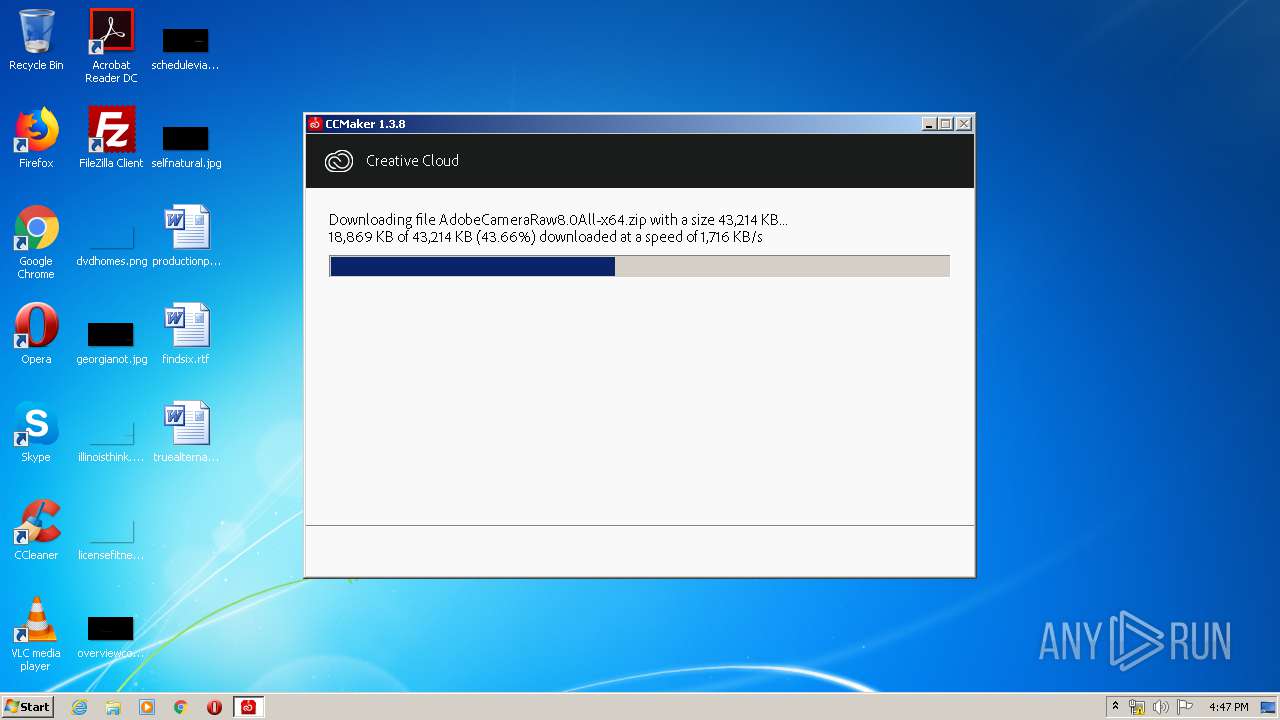
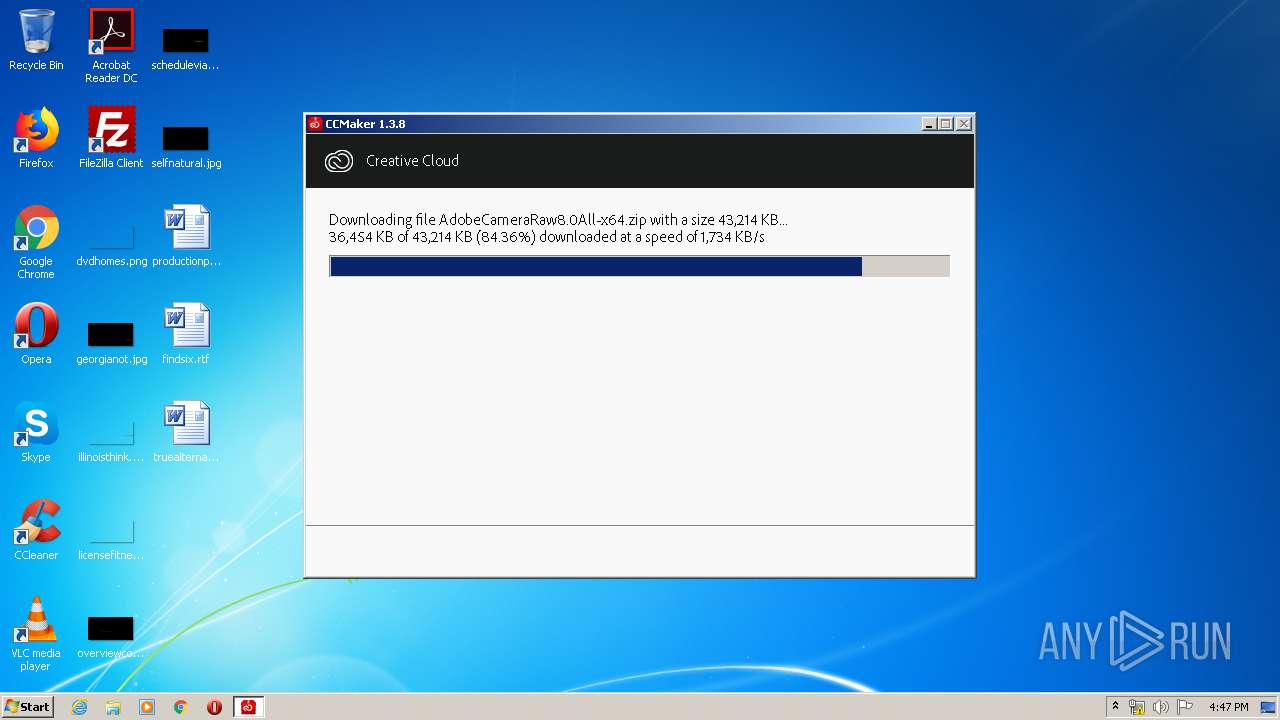
| 3792 | CCMaker.tmp | C:\Users\admin\AppData\Local\Adobe\Adobe Camera Raw CC (win32)\products\ACR\AdobeCameraRaw8.0All.zip.partial | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
69
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3792 | CCMaker.tmp | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAGC%2BAmOouYmuRo7J4Qfua8%3D | US | der | 1.47 Kb | whitelisted |
3792 | CCMaker.tmp | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAaXeCLH7hTEMEVhH1RjhNo%3D | US | der | 471 b | whitelisted |
3792 | CCMaker.tmp | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuqL92L3tjkN67RNFF%2FEdvT6NEzAQUwBKyKHRoRmfpcCV0GgBFWwZ9XEQCEAgt9o7pxpMVvr9yB5s4EP0%3D | US | der | 471 b | whitelisted |
3792 | CCMaker.tmp | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3792 | CCMaker.tmp | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
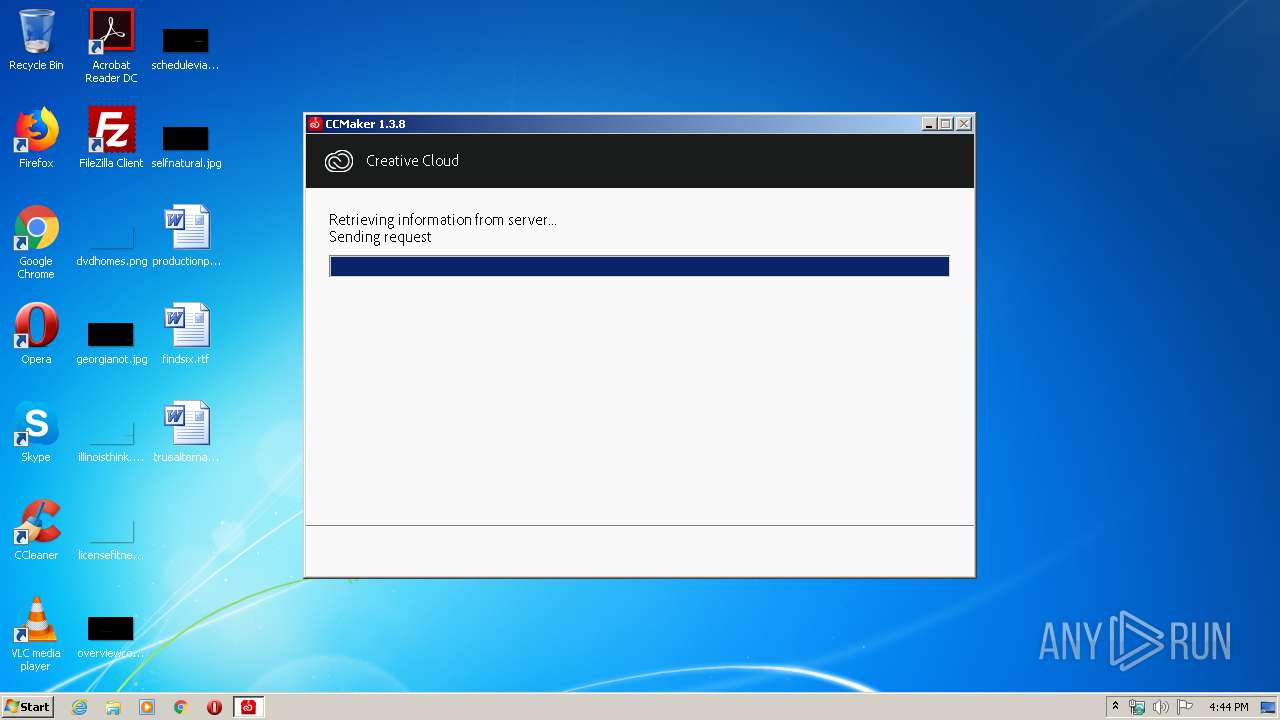
3792 | CCMaker.tmp | 34.199.102.97:443 | prod-rel-ffc-ccm.oobesaas.adobe.com | Amazon.com, Inc. | US | unknown |
3792 | CCMaker.tmp | 143.204.204.44:443 | cdn-ffc.oobesaas.adobe.com | — | US | unknown |
3792 | CCMaker.tmp | 2.22.118.241:443 | ccmdls.adobe.com | Akamai International B.V. | GB | suspicious |
3792 | CCMaker.tmp | 52.216.239.179:443 | adobe-oobe-prod-data-store-ue1.s3.amazonaws.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
prod-rel-ffc-ccm.oobesaas.adobe.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cdn-ffc.oobesaas.adobe.com |
| whitelisted |
adobe-oobe-prod-data-store-ue1.s3.amazonaws.com |
| shared |
ccmdls.adobe.com |
| whitelisted |
Threats
Process | Message |
|---|---|
CCMaker.tmp | Extra call to Release() !!!
|
CCMaker.tmp | Extra call to Release() !!!
|
CCMaker.tmp | Extra call to Release() !!!
|
CCMaker.tmp | Extra call to Release() !!!
|
CCMaker.tmp | Extra call to Release() !!!
|
CCMaker.tmp | Extra call to Release() !!!
|
CCMaker.tmp | Extra call to Release() !!!
|
CCMaker.tmp | Extra call to Release() !!!
|
CCMaker.tmp | Extra call to Release() !!!
|
CCMaker.tmp | Extra call to Release() !!!
|