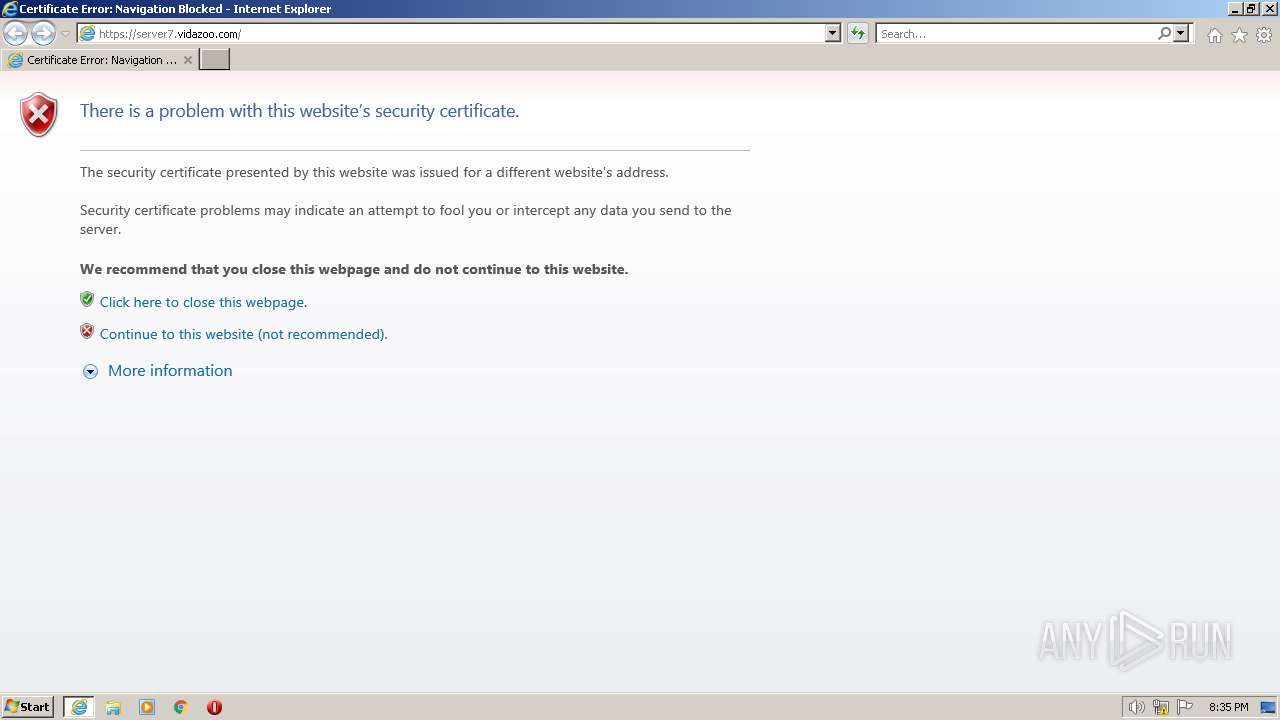
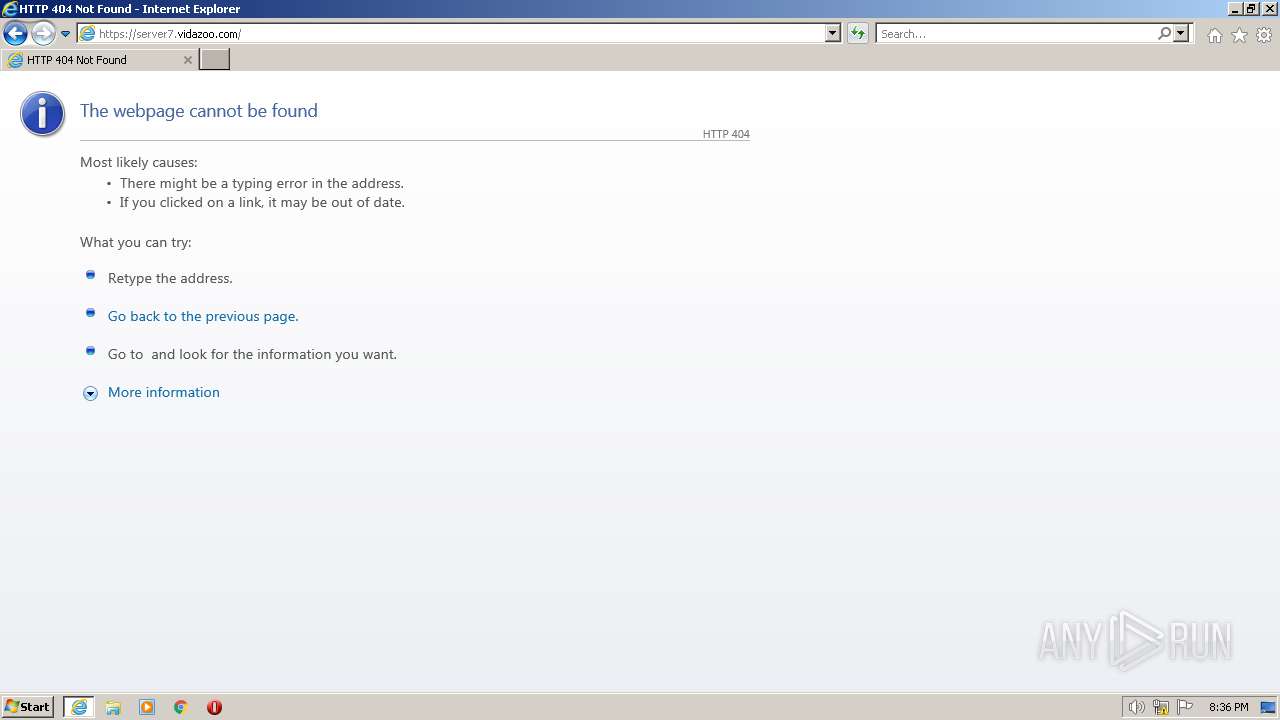
| URL: | https://server7.vidazoo.com |
| Full analysis: | https://app.any.run/tasks/59a32ec3-40c2-4b08-b2e9-6ee0238aa830 |
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2023, 19:34:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4FAE696878B4ABE3CD802EB01733DDDA |
| SHA1: | 6DDE8F20EBD225F8455E1037A6260976774A902B |
| SHA256: | 78DE1D9E5140AE331F3DDE6E63AADDBD6ABF56384CC399B642A778077AAE660C |
| SSDEEP: | 3:N8Nm4YKyKIn:2sTKIn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2964)
Create files in a temporary directory
- iexplore.exe (PID: 2964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2964 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://server7.vidazoo.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3284 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2964 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
28 770
Read events
28 482
Write events
288
Delete events
0
Modification events
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
29
DNS requests
18
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2964 | iexplore.exe | GET | 404 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e07030052cb14120 | US | xml | 341 b | whitelisted |
3284 | iexplore.exe | GET | 404 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a1e1110f85b52617 | US | xml | 341 b | whitelisted |
1076 | svchost.exe | GET | 404 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?075b11ce9eaec7a1 | US | xml | 341 b | whitelisted |
3284 | iexplore.exe | GET | 404 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2bcf7d2637bda0c7 | US | xml | 341 b | whitelisted |
3284 | iexplore.exe | GET | 404 | 3.226.182.14:80 | http://vidazoo.com/ | US | xml | 341 b | shared |
3284 | iexplore.exe | GET | 404 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e541c8aceb1d9179 | US | xml | 341 b | whitelisted |
2964 | iexplore.exe | GET | 404 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?43d0d04822d88ebd | US | xml | 341 b | whitelisted |
3284 | iexplore.exe | GET | 404 | 8.9.31.55:80 | http://server7.vidazoo.com/ | US | xml | 341 b | suspicious |
3284 | iexplore.exe | GET | 404 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?199c8e719bb87825 | US | xml | 341 b | whitelisted |
2964 | iexplore.exe | GET | 404 | 8.238.30.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fc6a4dc40636befa | US | xml | 341 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2964 | iexplore.exe | 104.94.2.181:443 | go.microsoft.com | AKAMAI-AS | FR | suspicious |
1076 | svchost.exe | 8.238.30.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
3284 | iexplore.exe | 13.107.5.80:443 | api.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3284 | iexplore.exe | 8.9.31.55:80 | — | AS-CHOOPA | US | suspicious |
— | — | 13.107.5.80:443 | api.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3284 | iexplore.exe | 3.226.182.14:80 | vidazoo.com | AMAZON-AES | US | shared |
3284 | iexplore.exe | 8.238.30.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
3284 | iexplore.exe | 8.9.31.55:443 | — | AS-CHOOPA | US | suspicious |
2964 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | EDGECAST | US | whitelisted |
— | — | 8.238.30.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
vidazoo.com |
| shared |
Threats
13 ETPRO signatures available at the full report