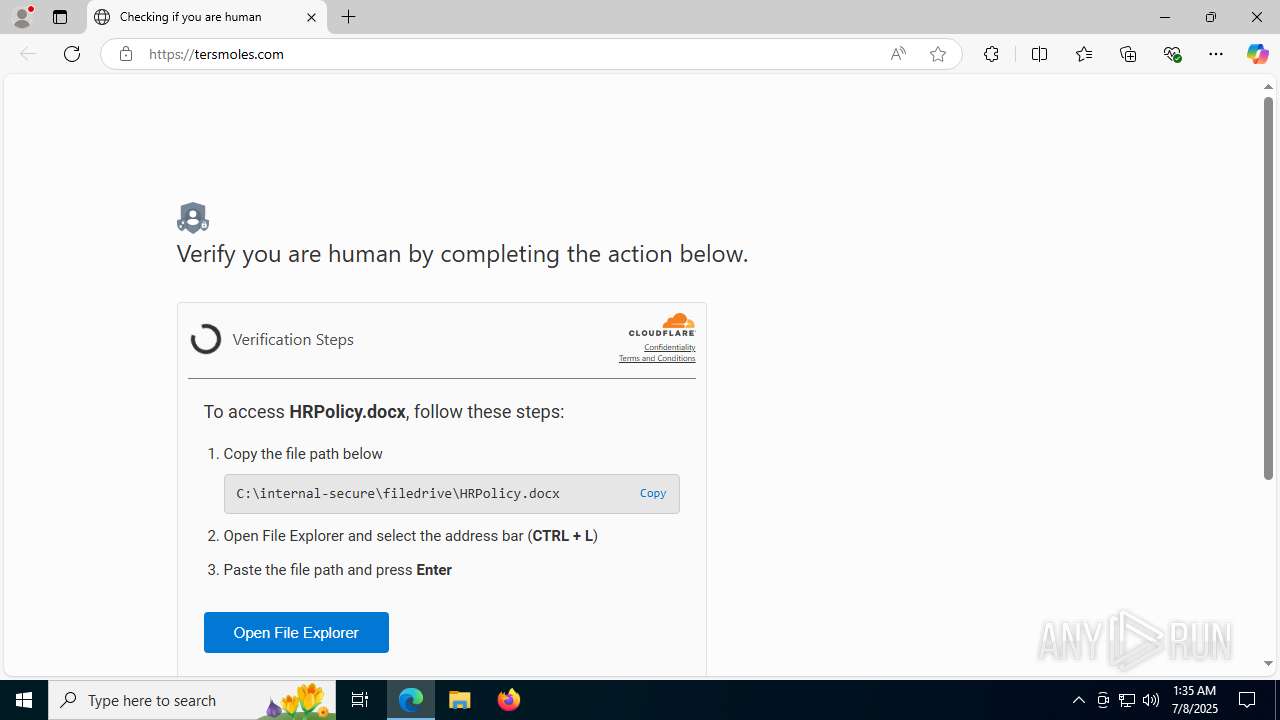
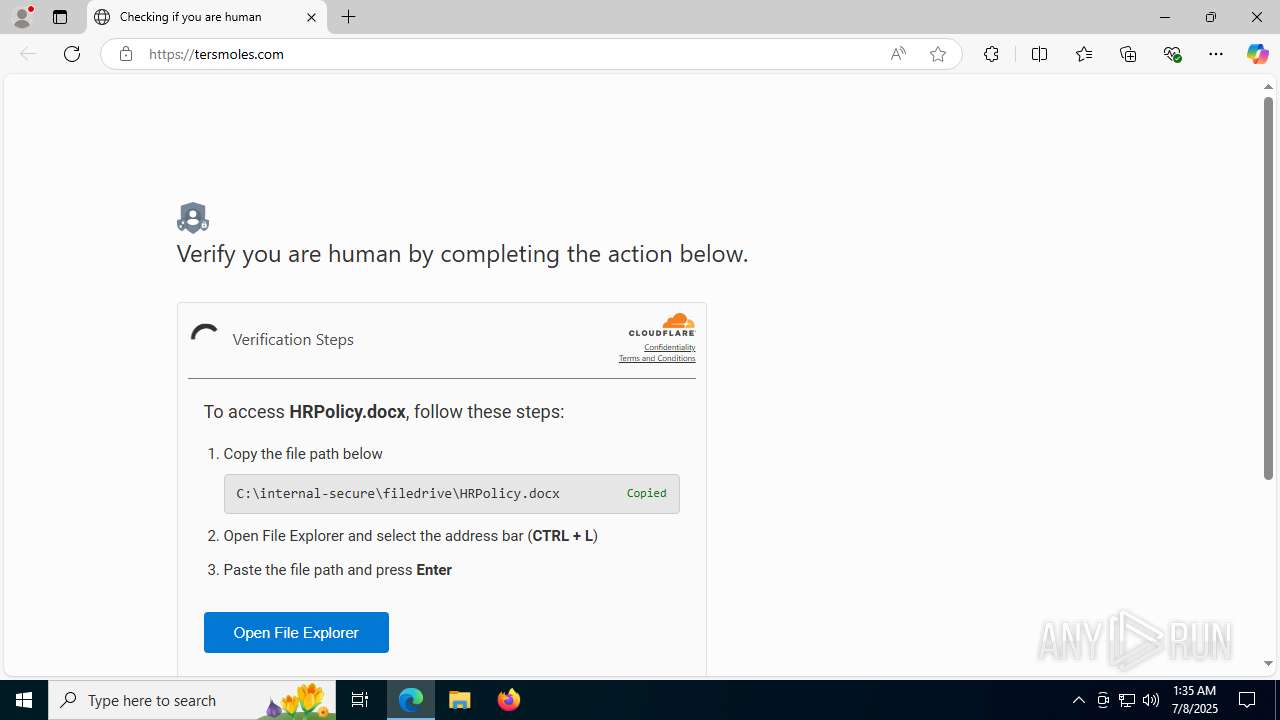
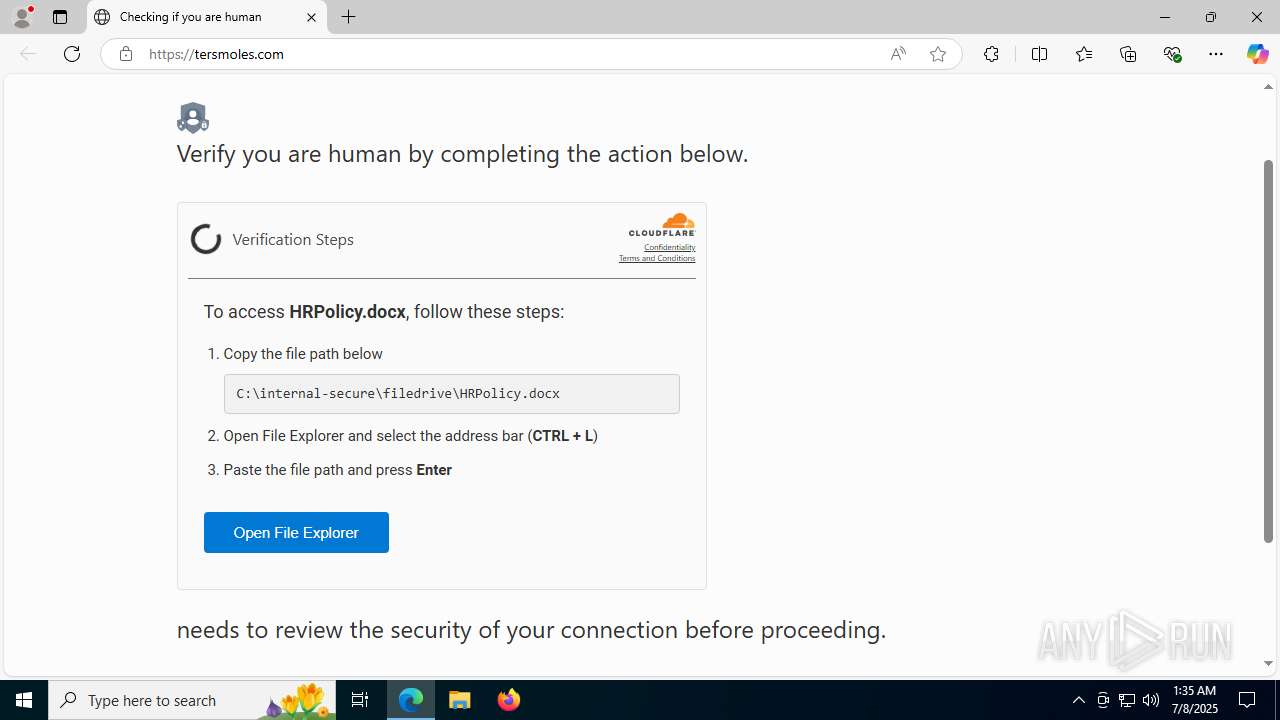
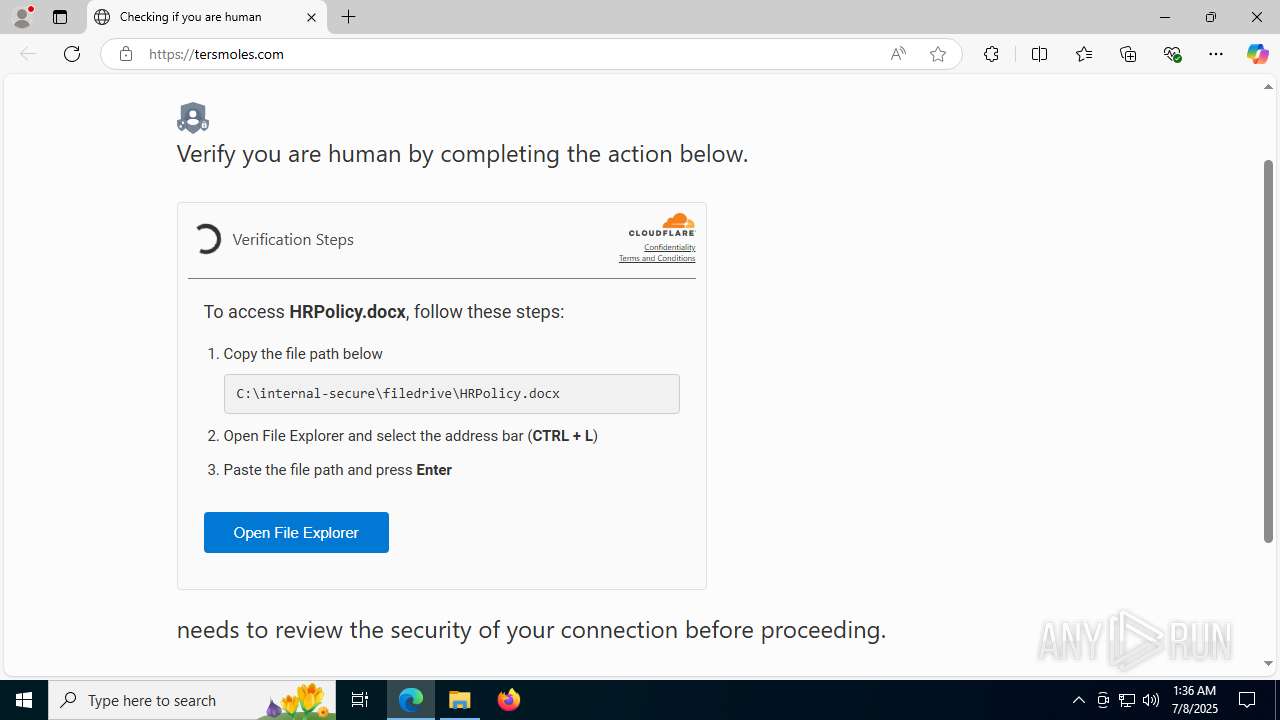
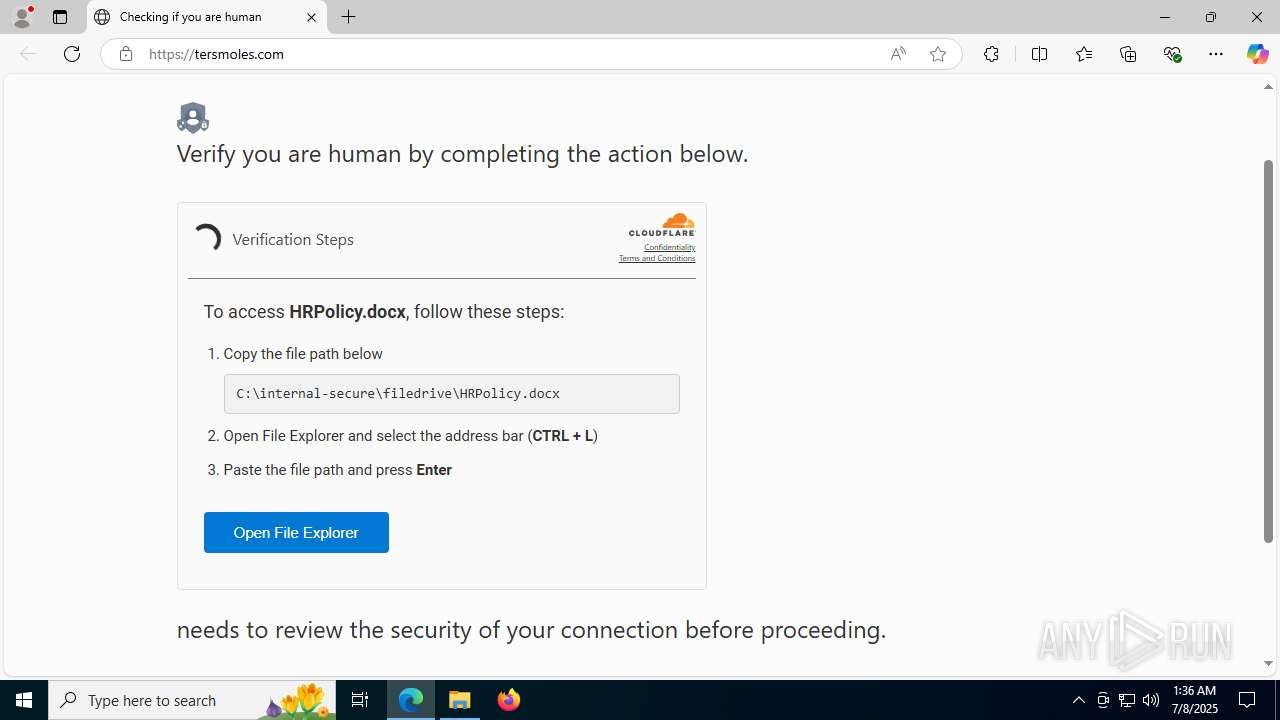
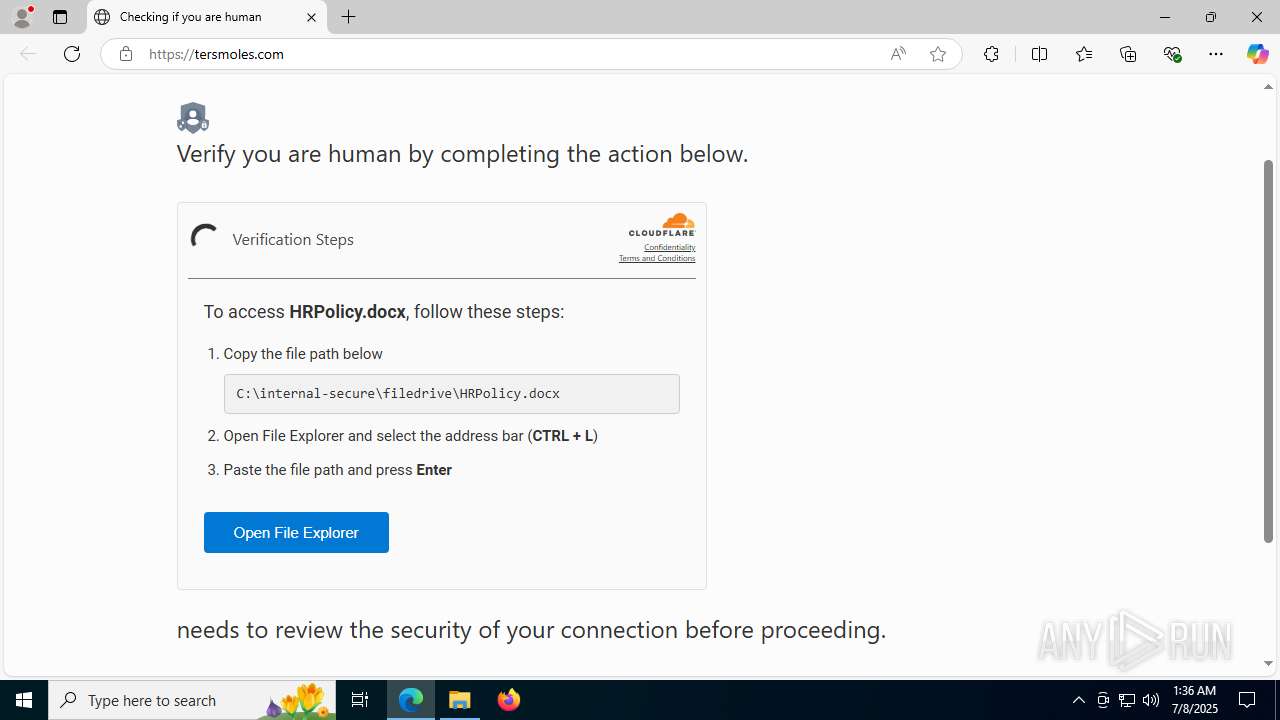
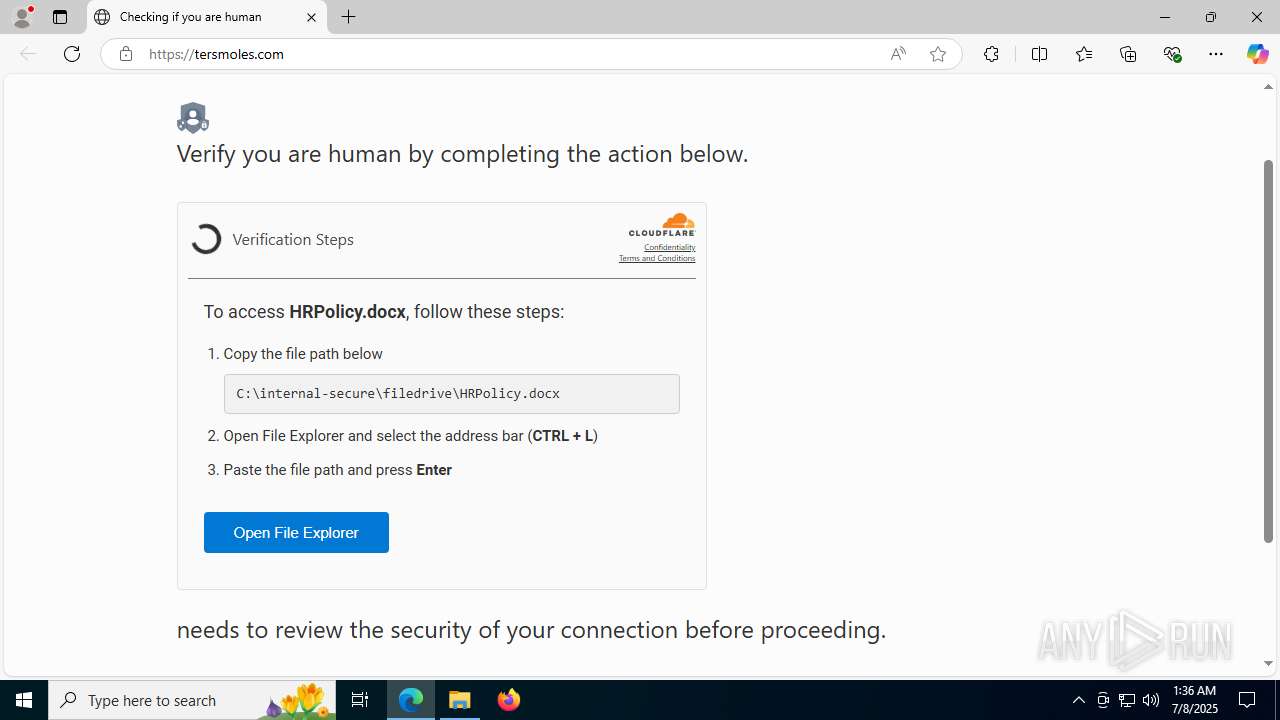
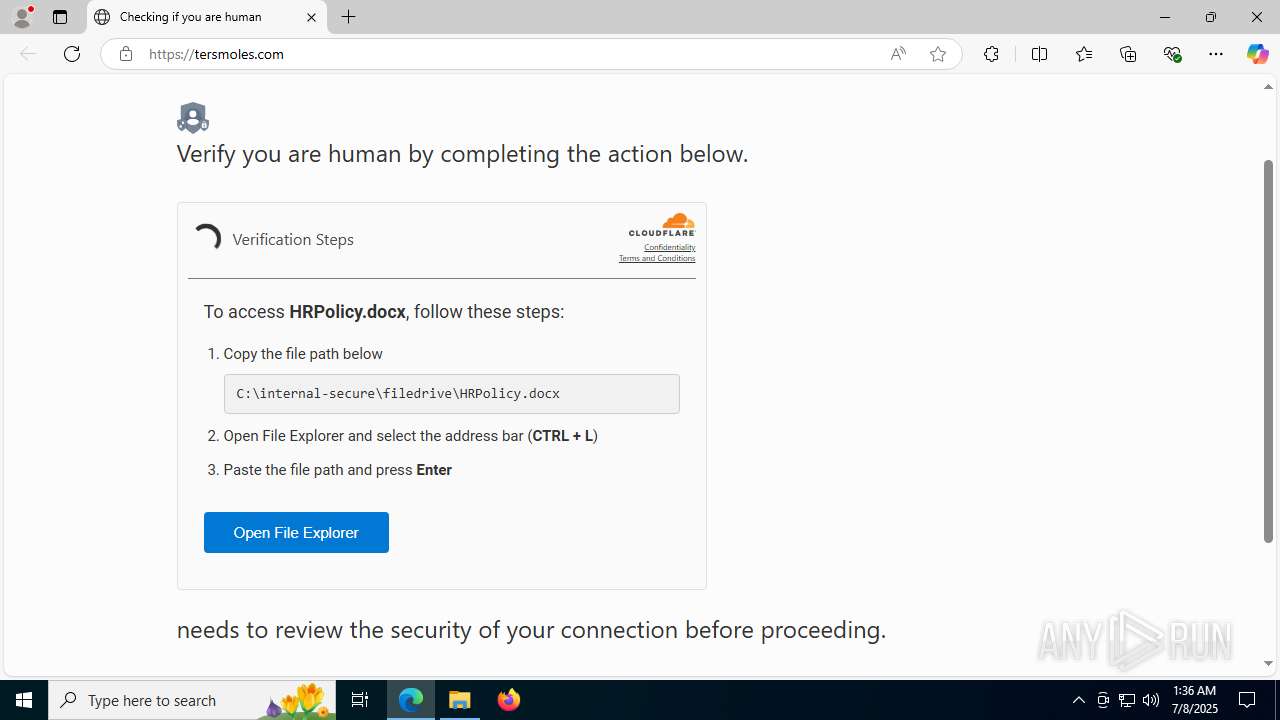
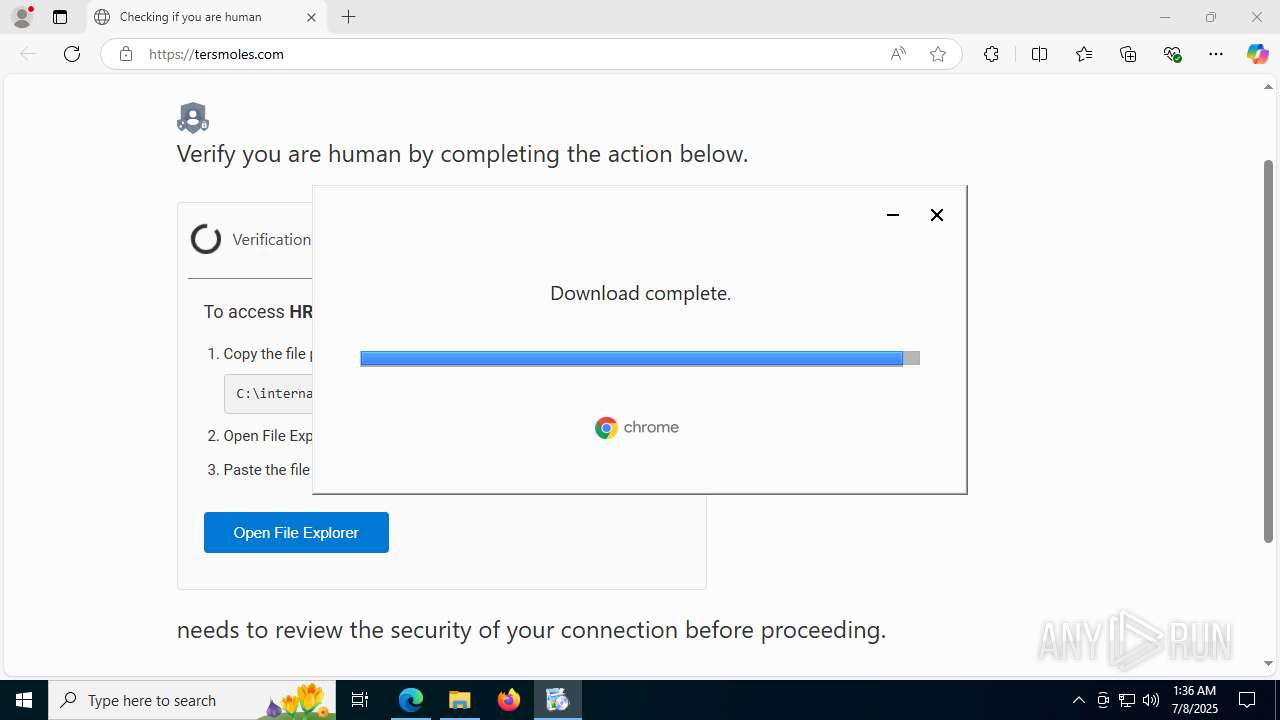
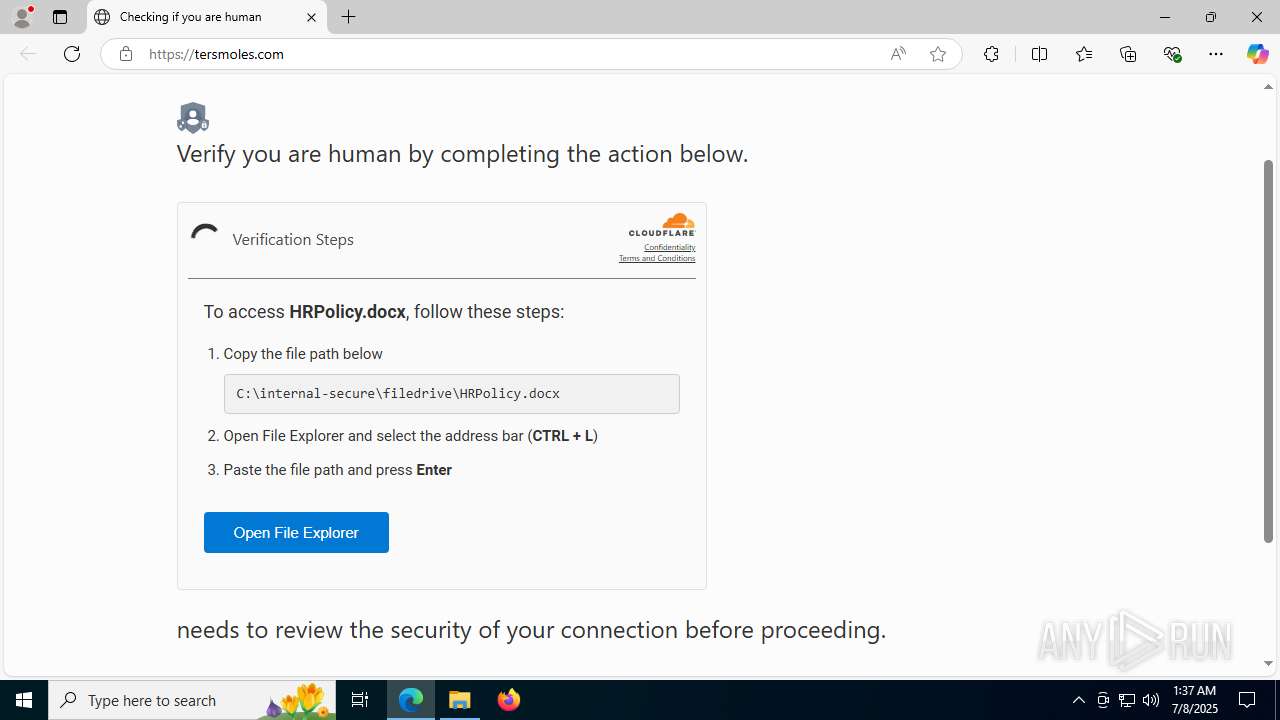
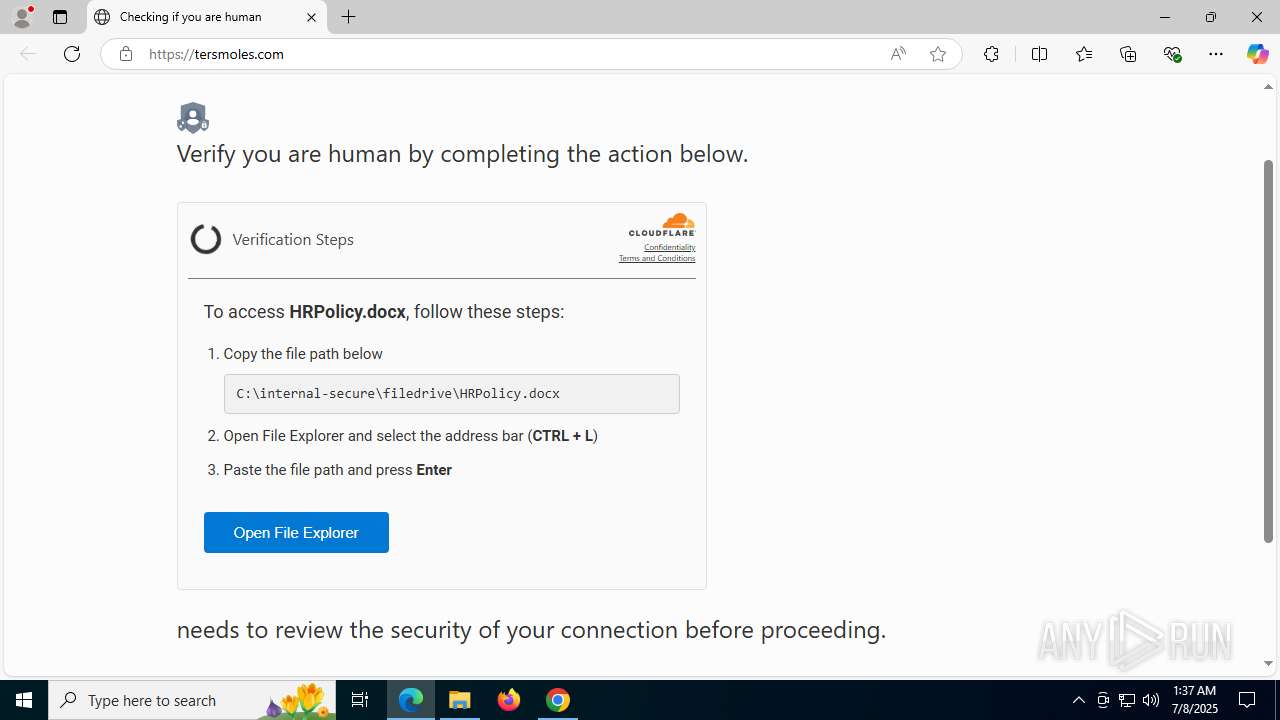
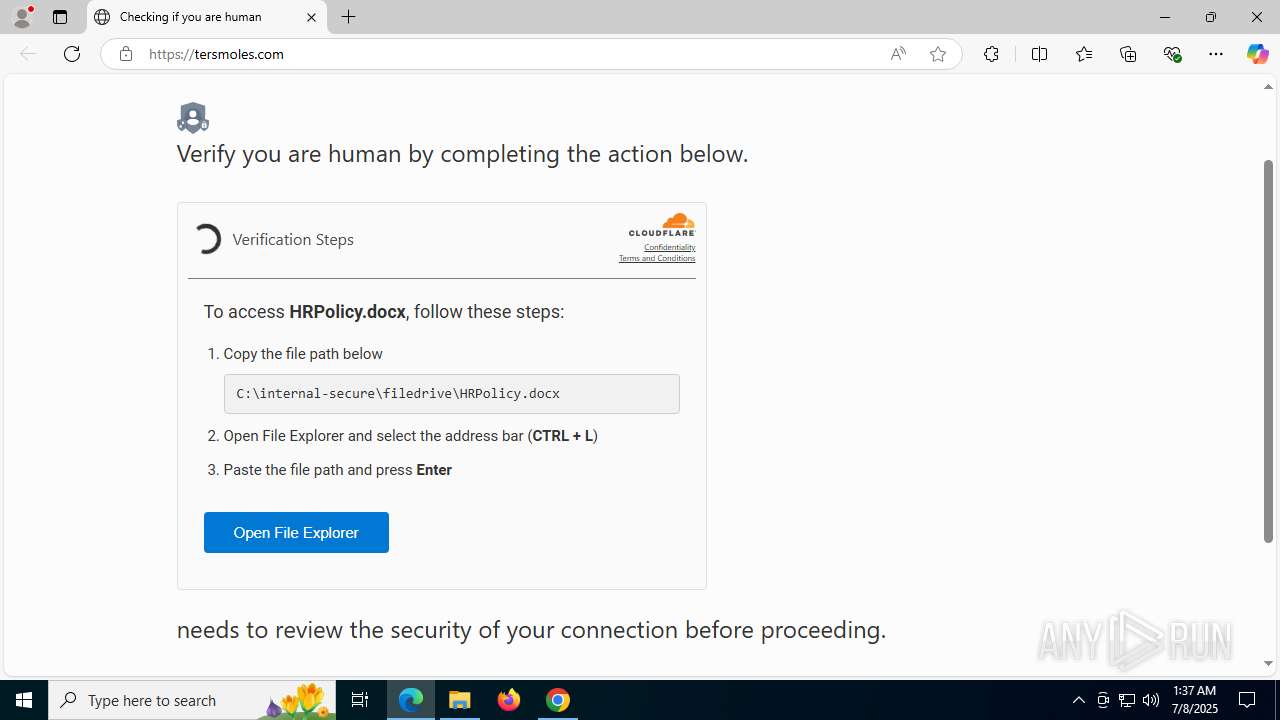
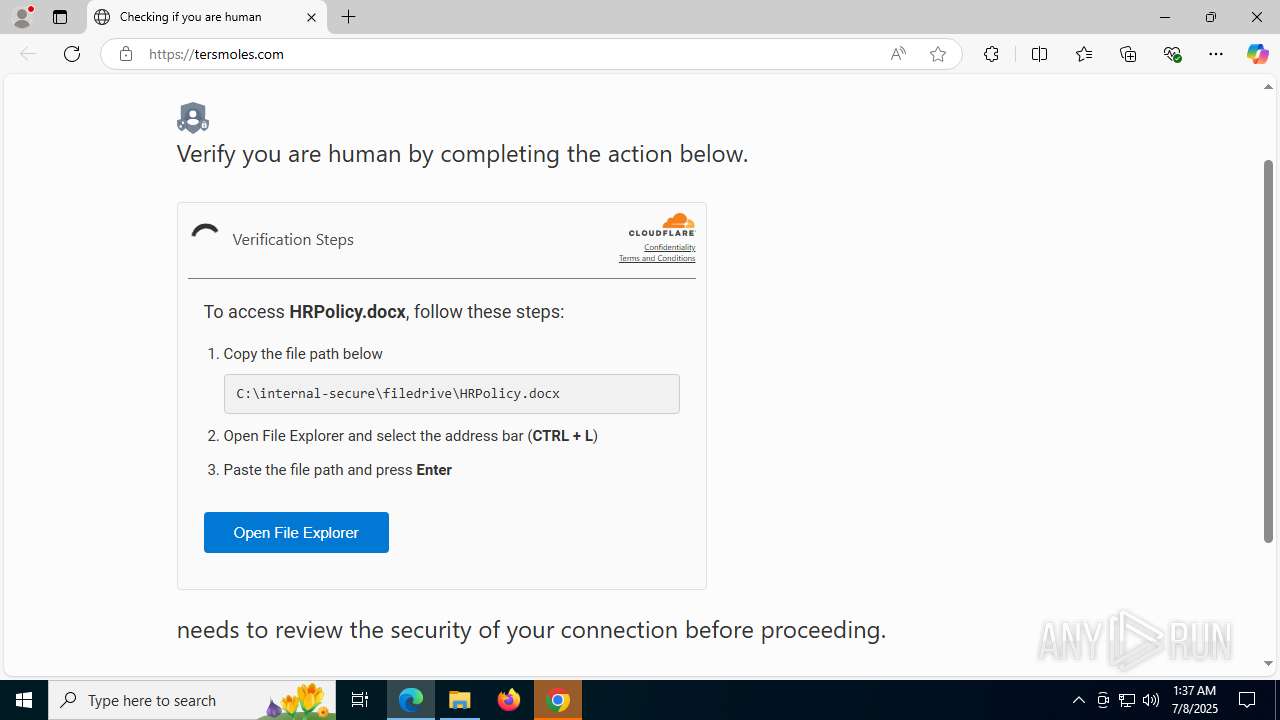
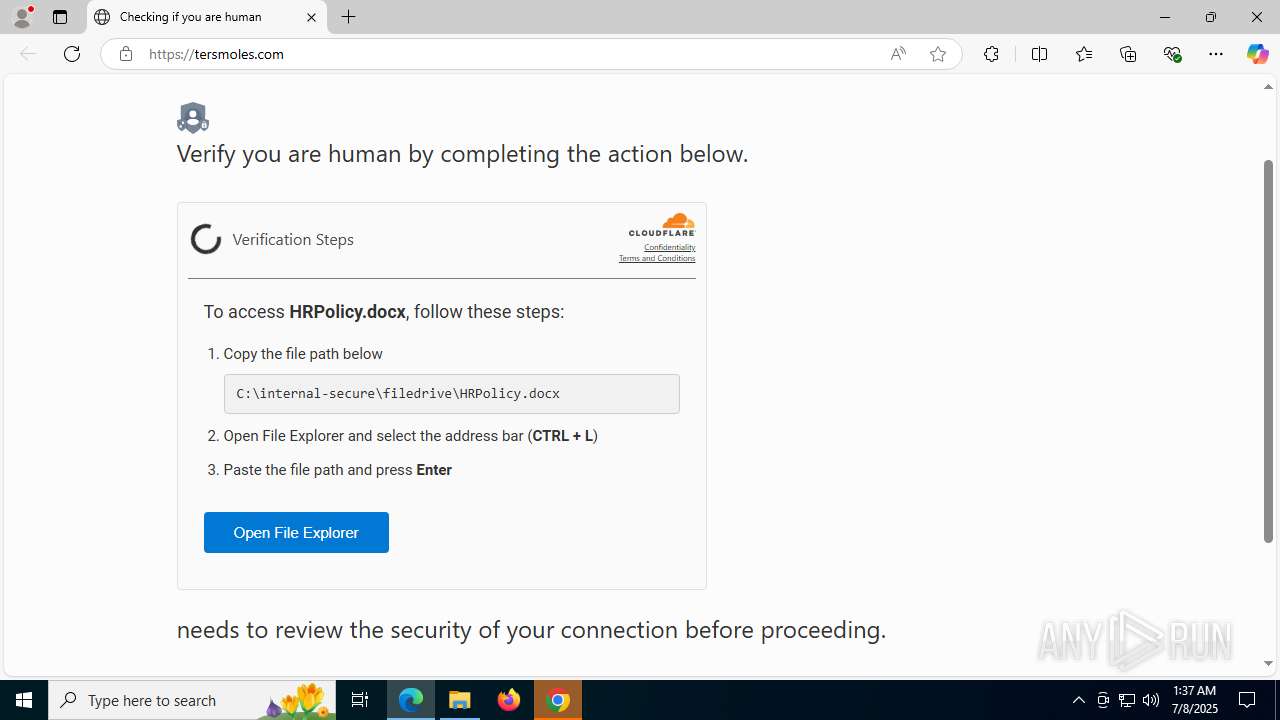
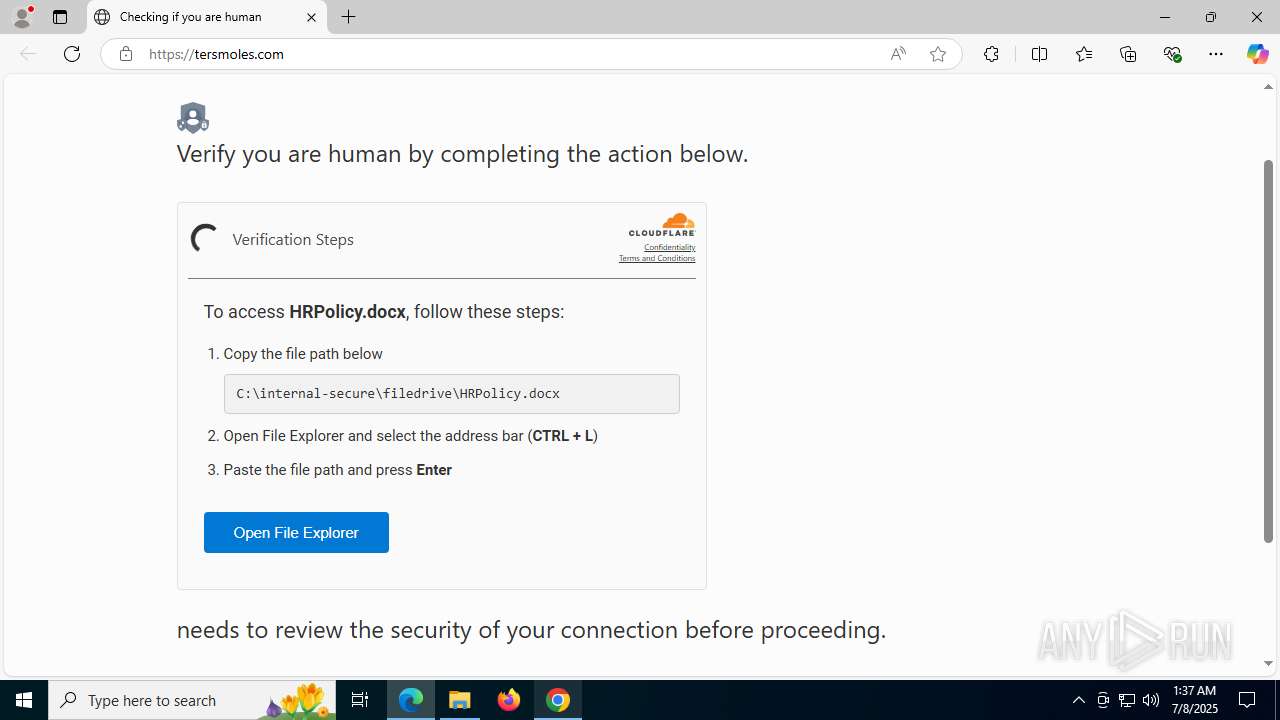
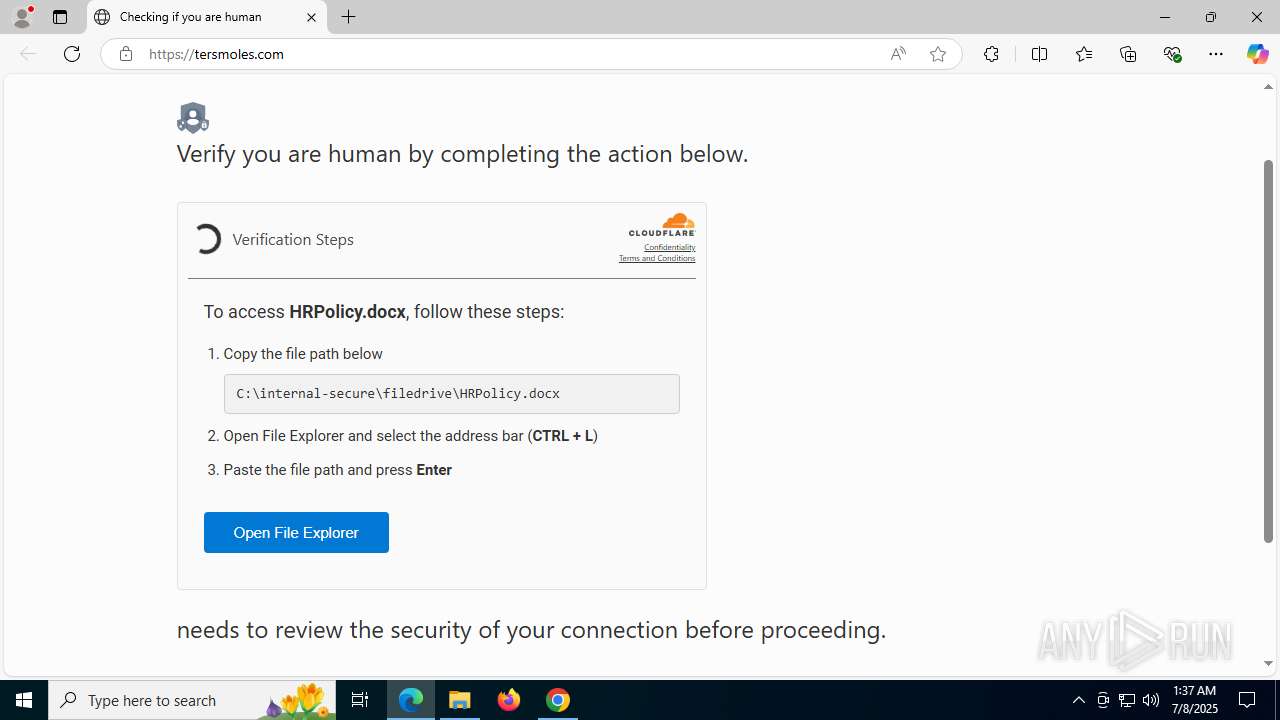
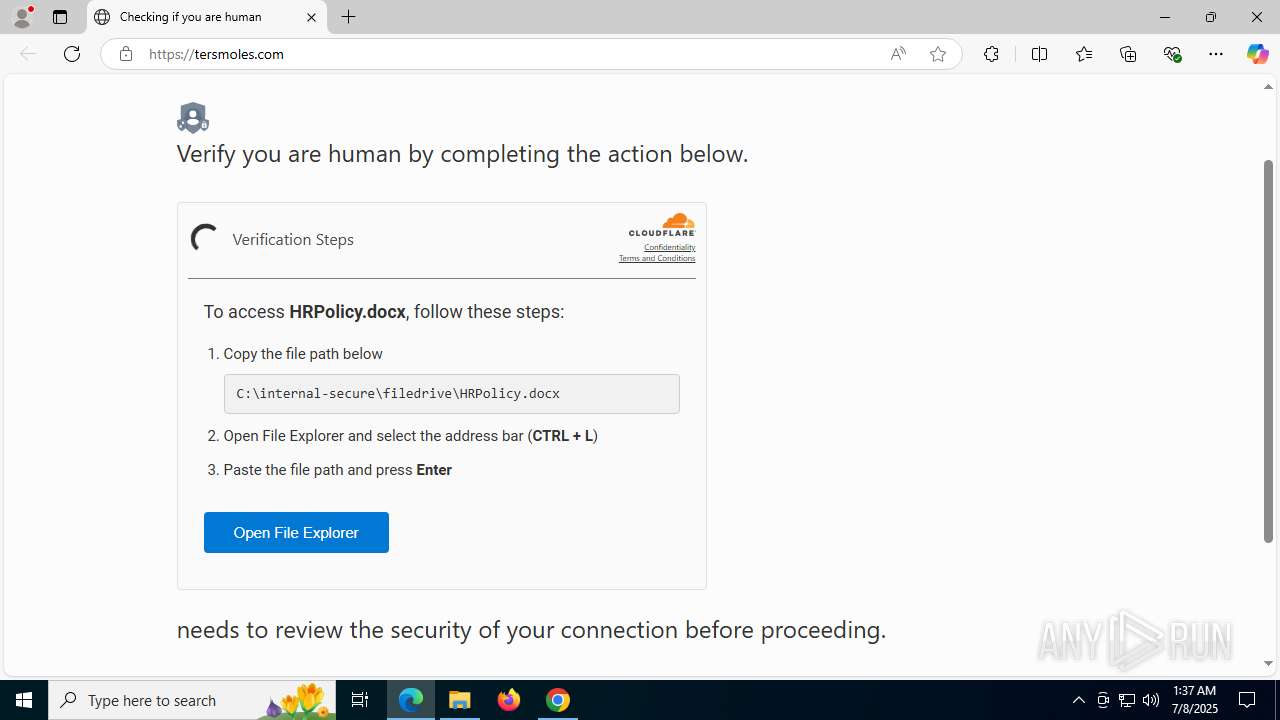
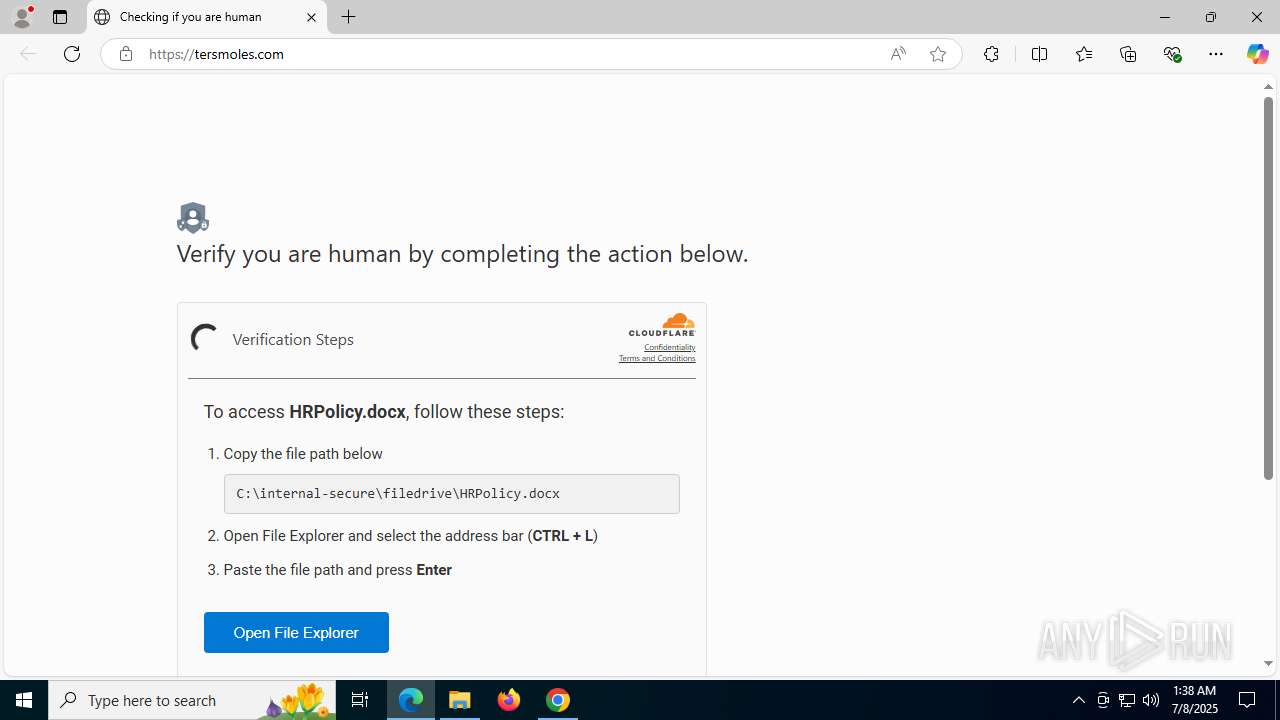
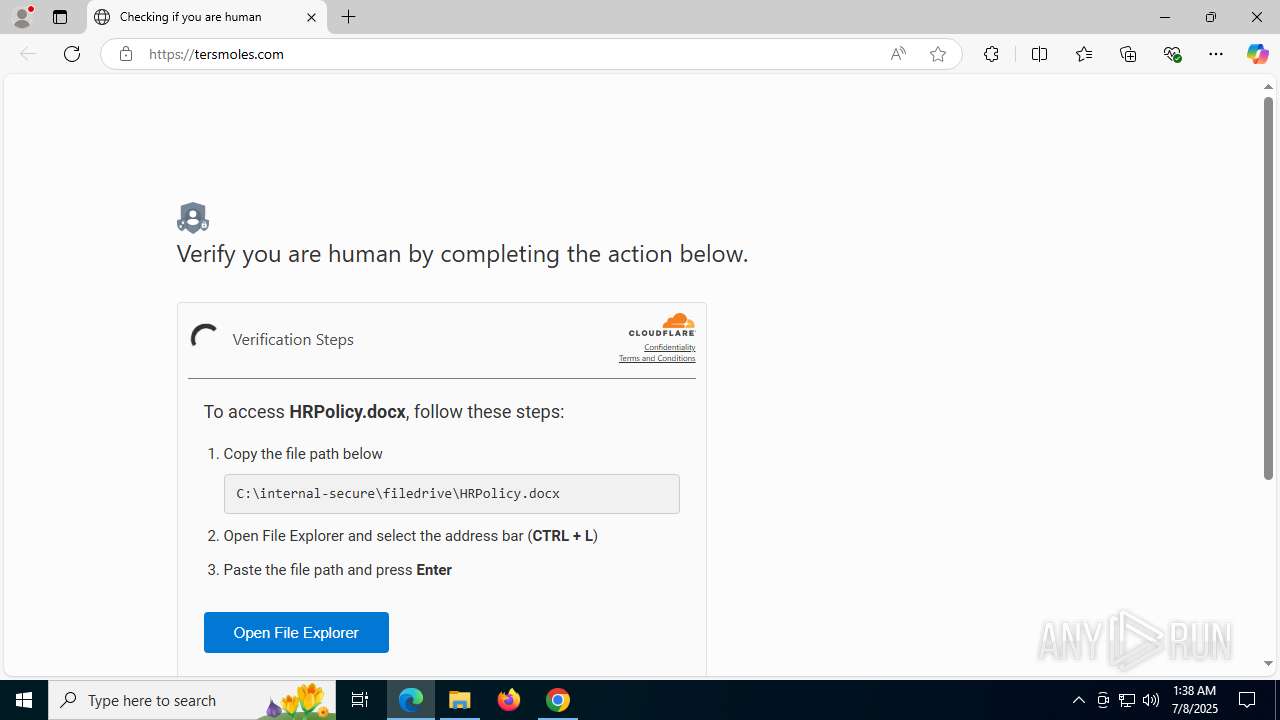
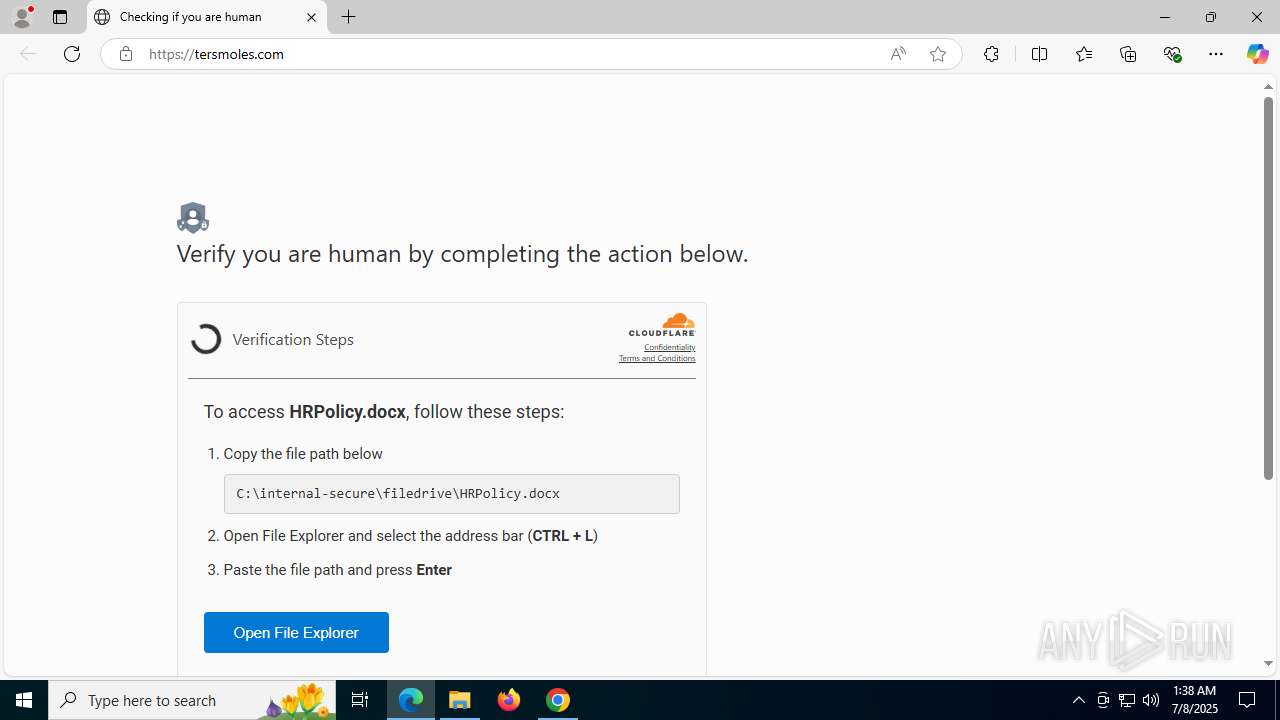
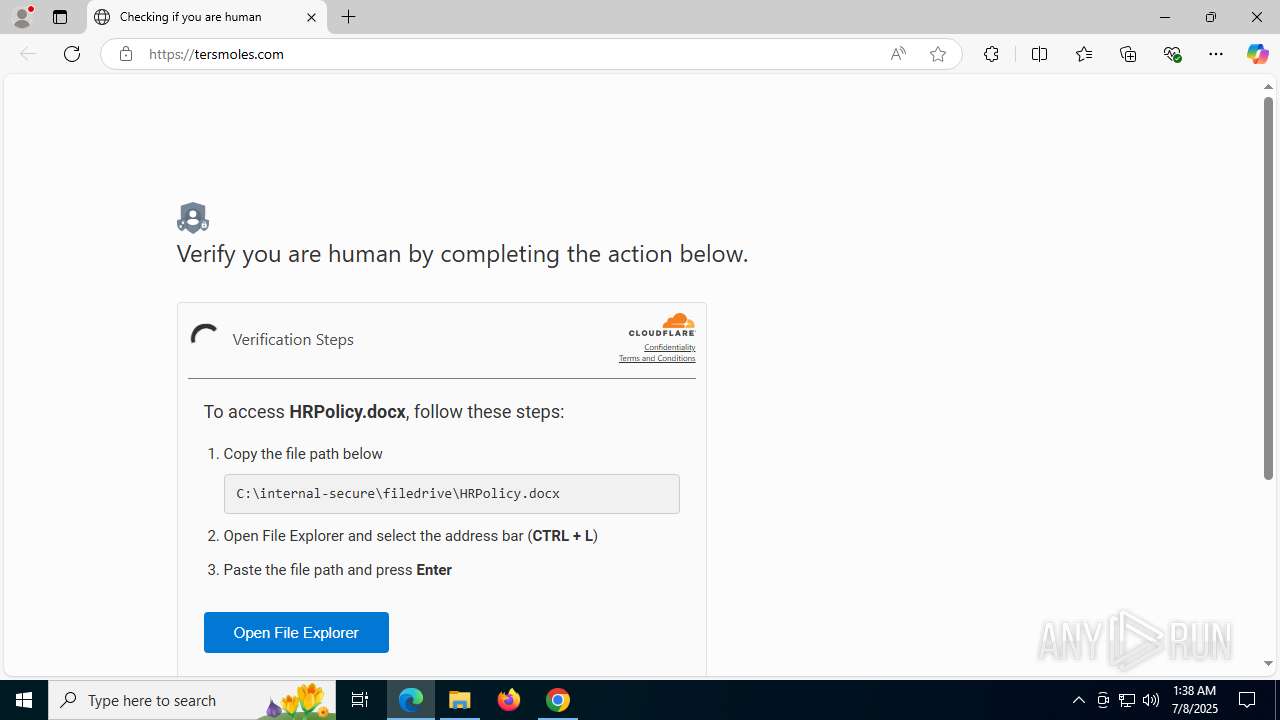
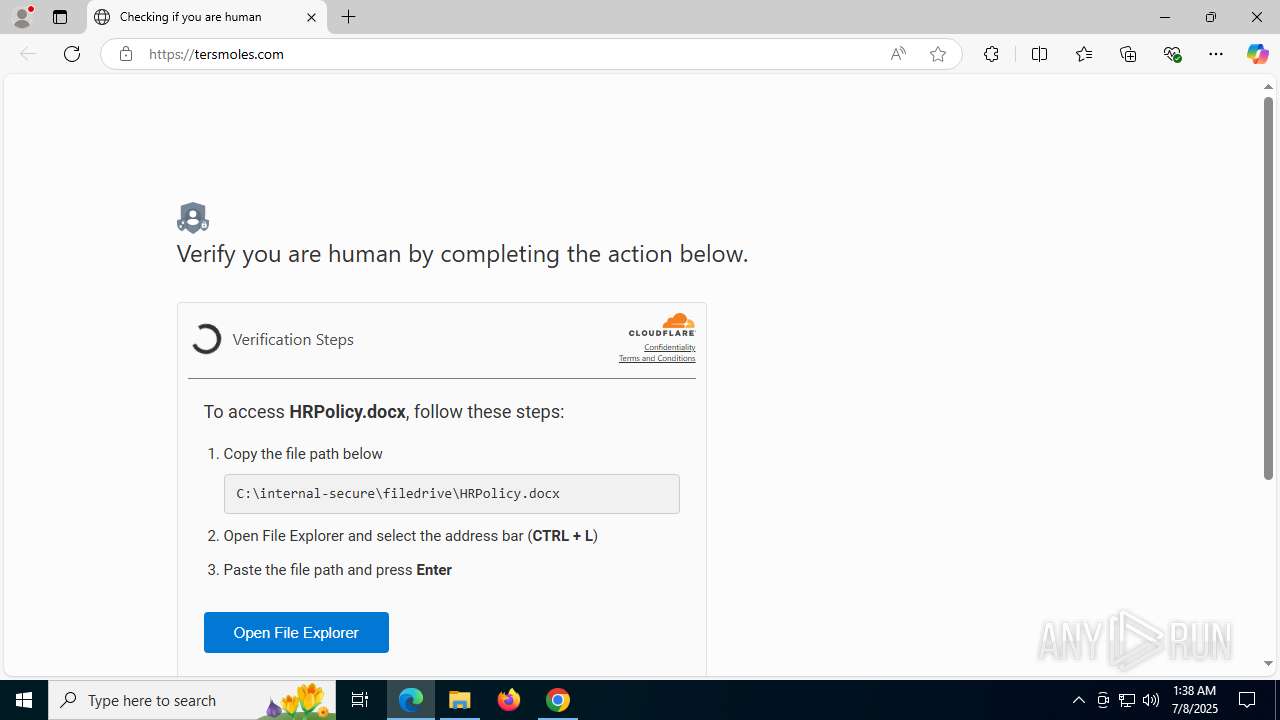
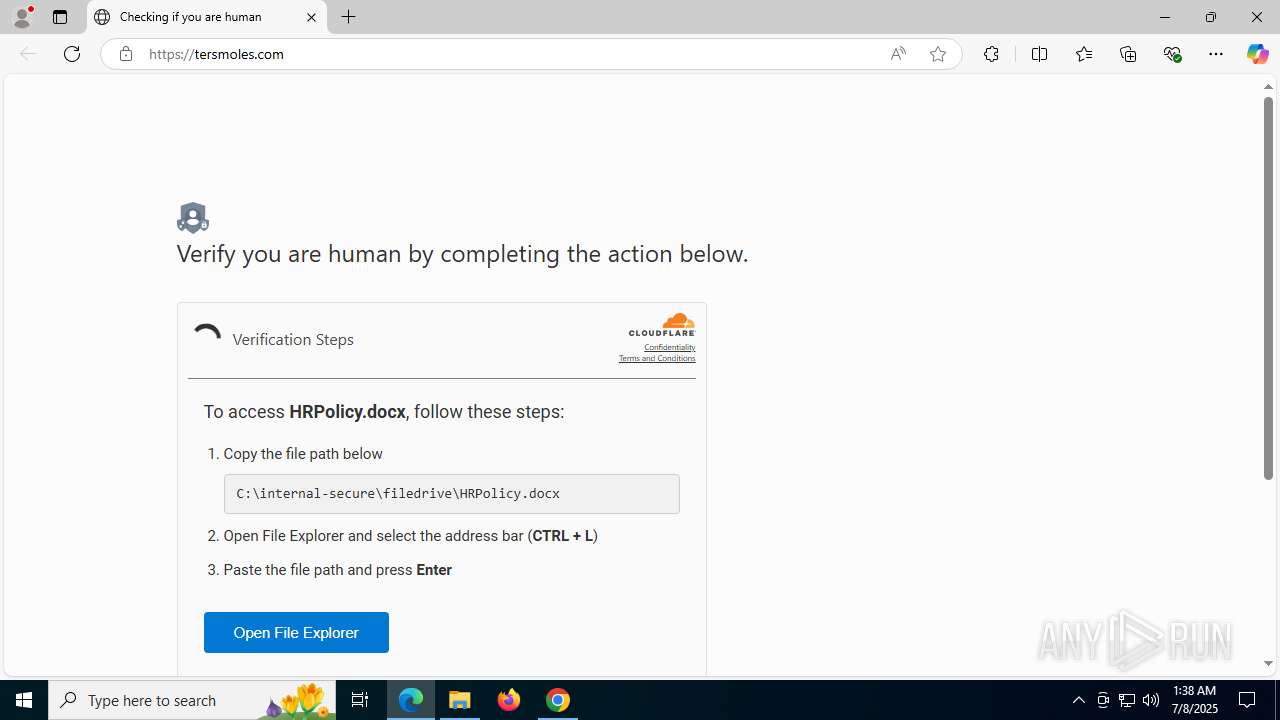
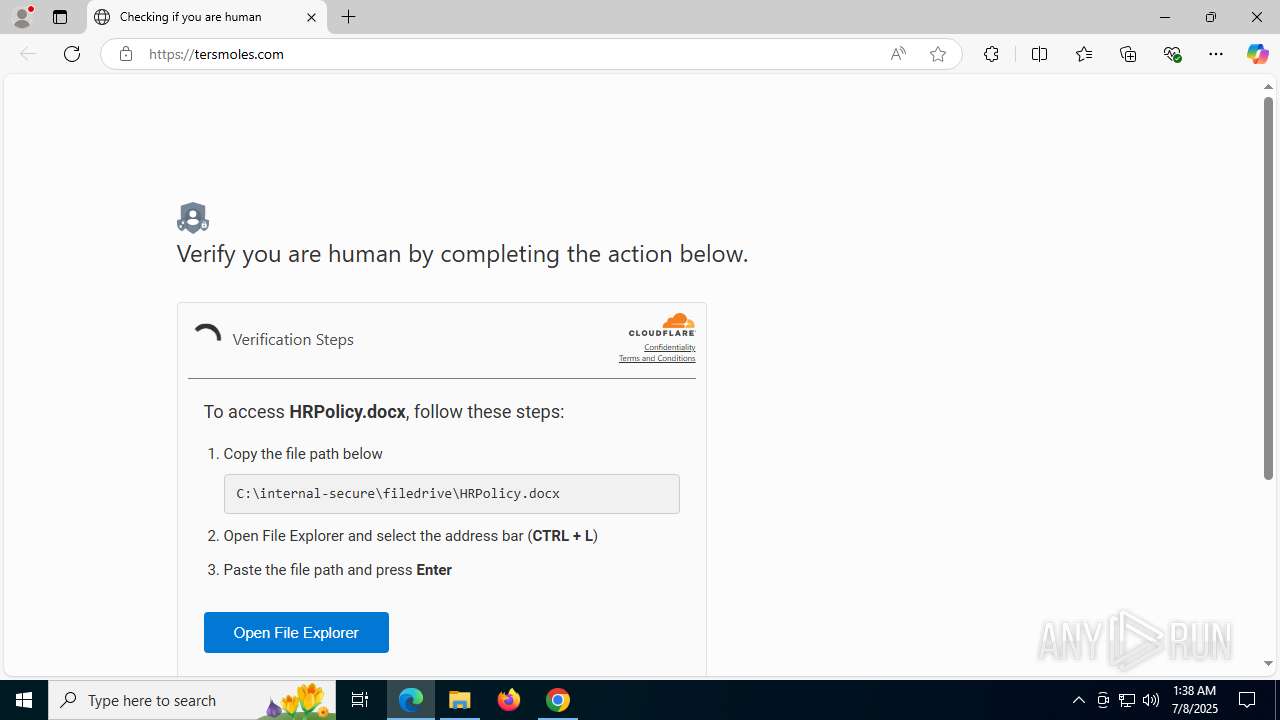
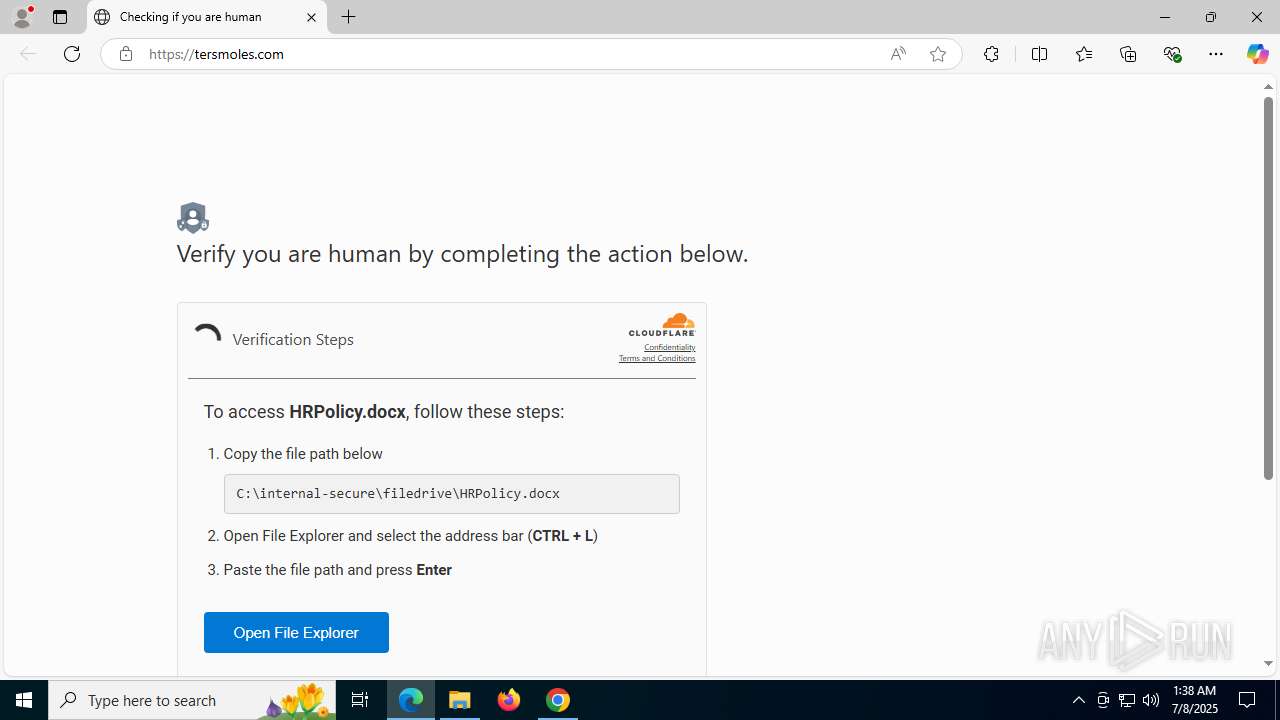
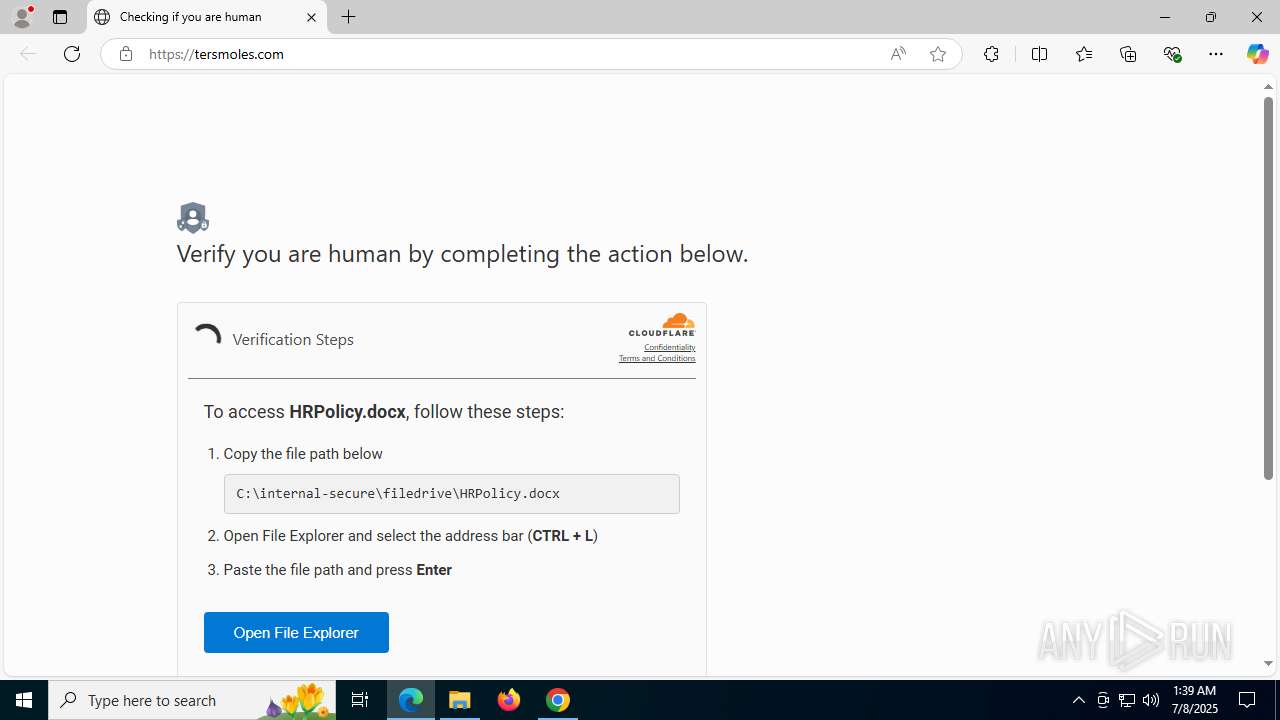
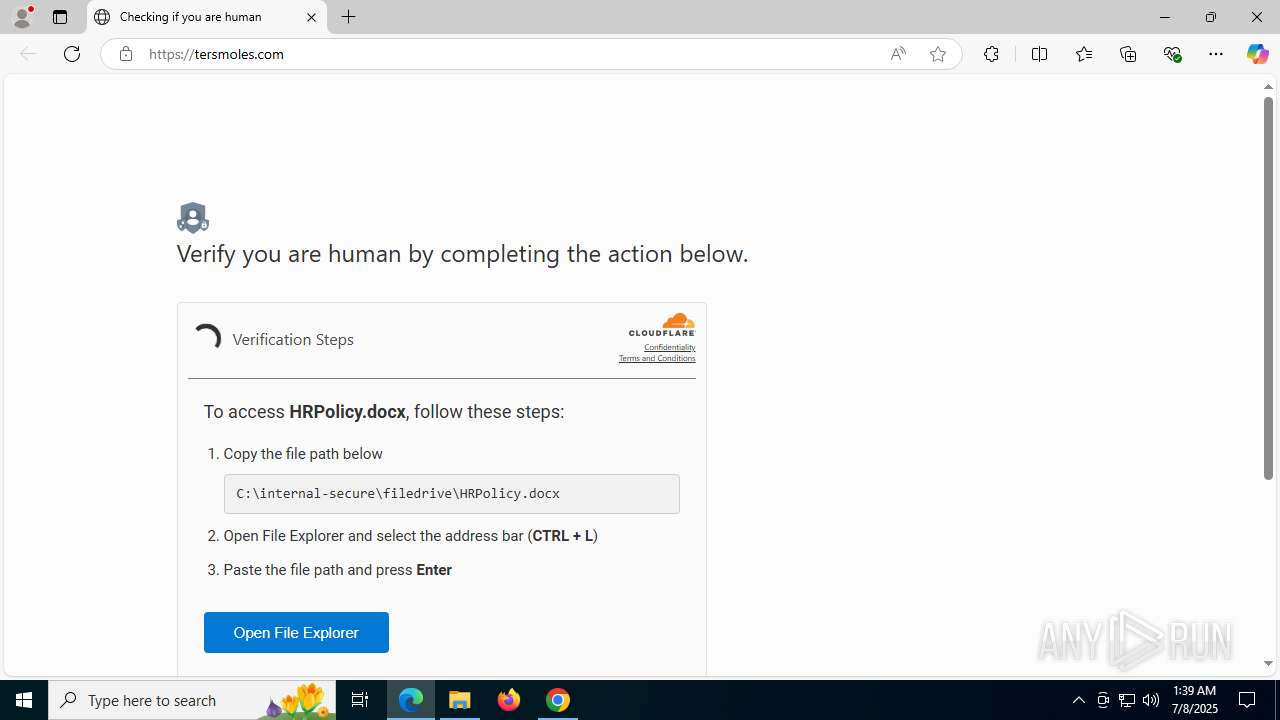
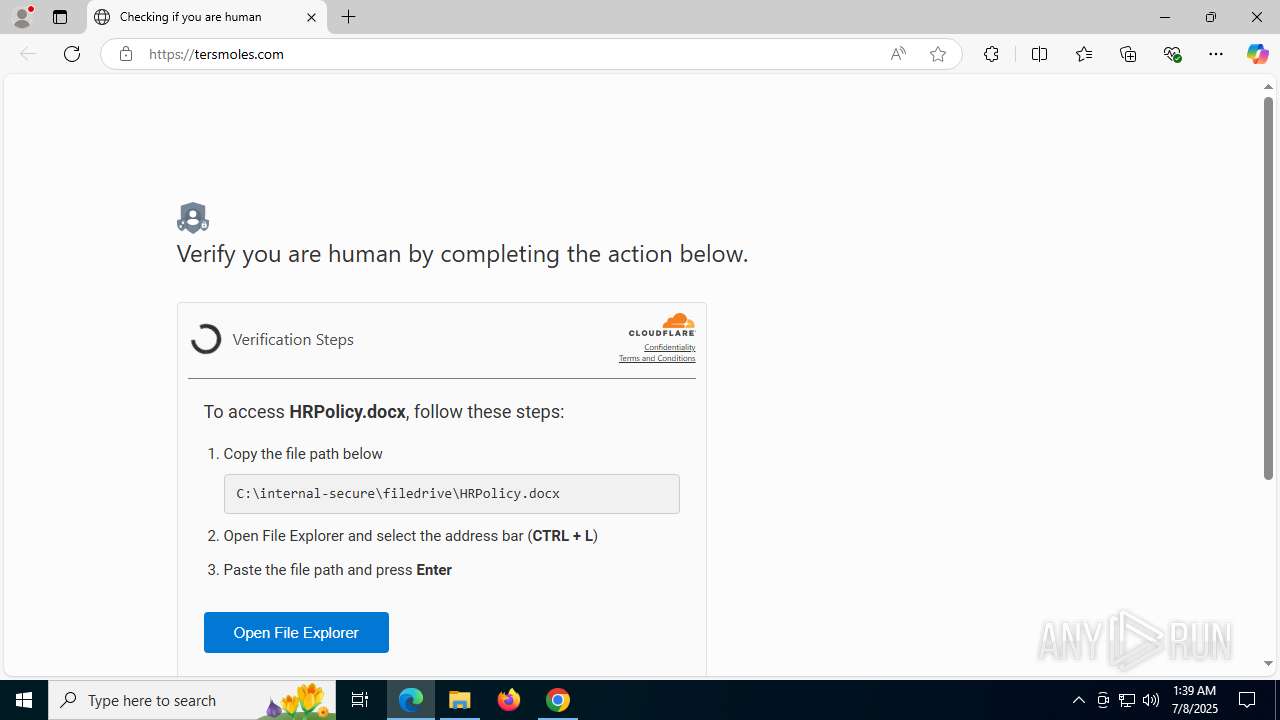
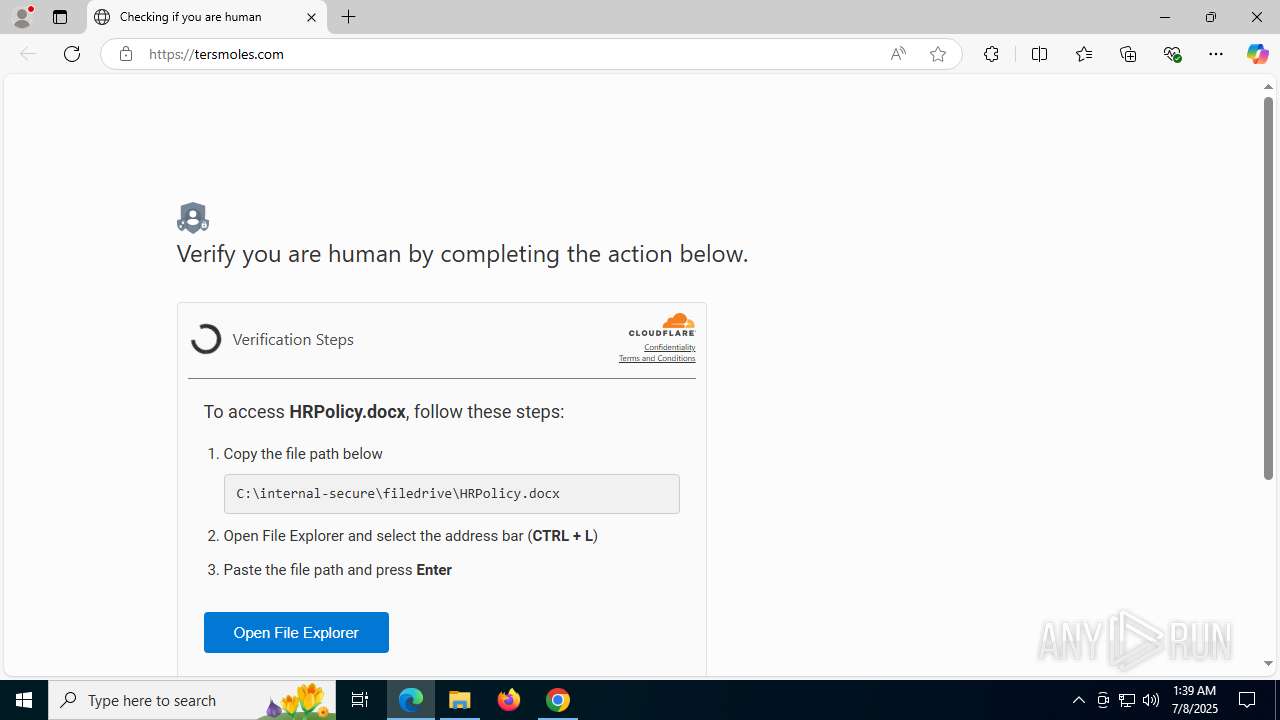
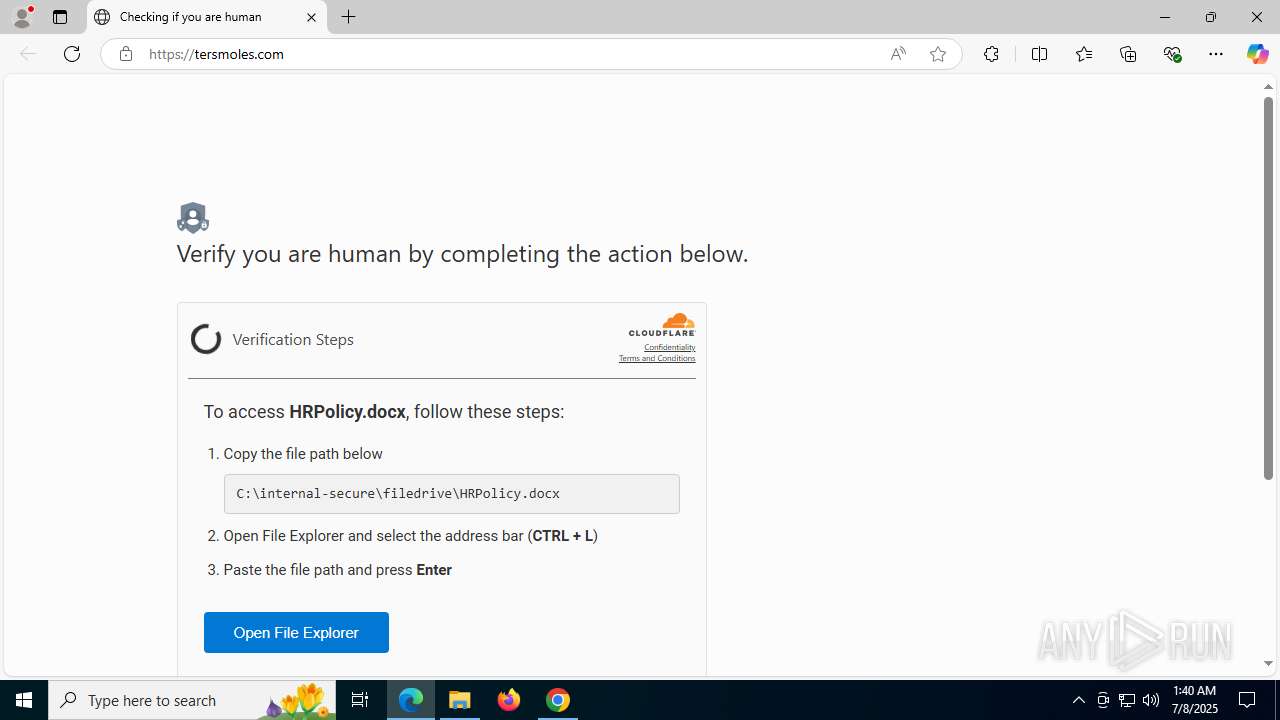
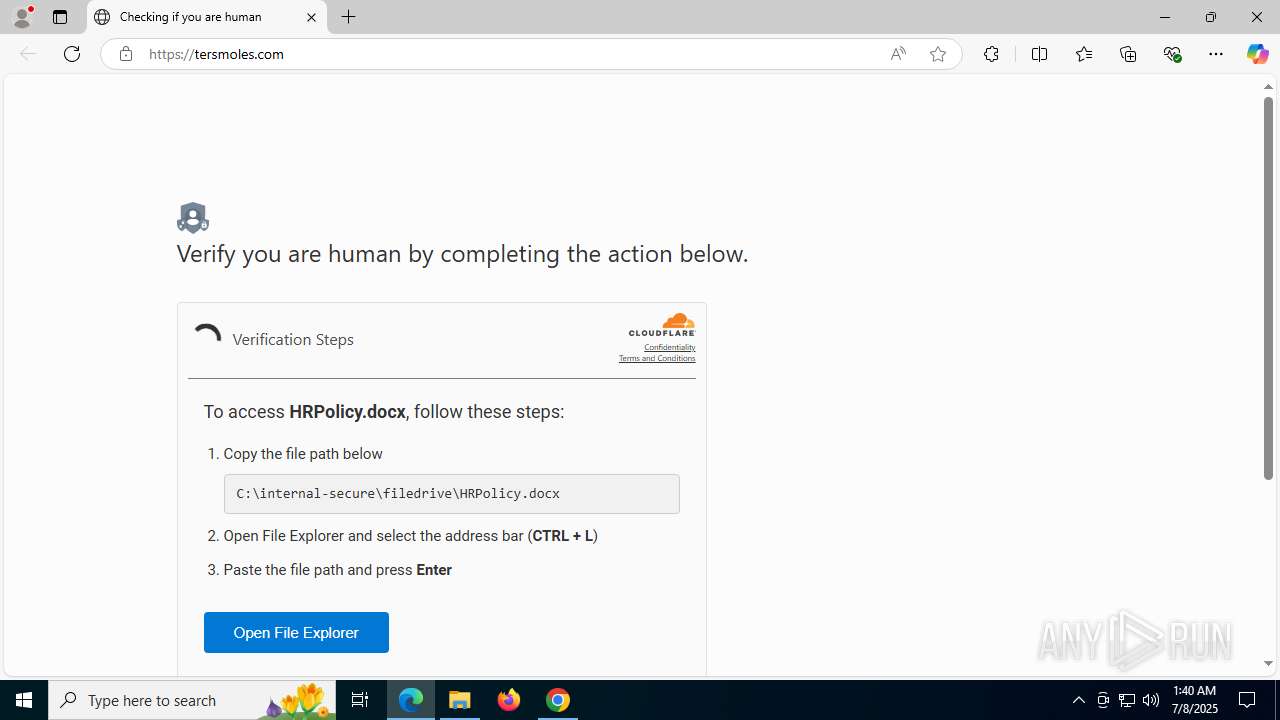
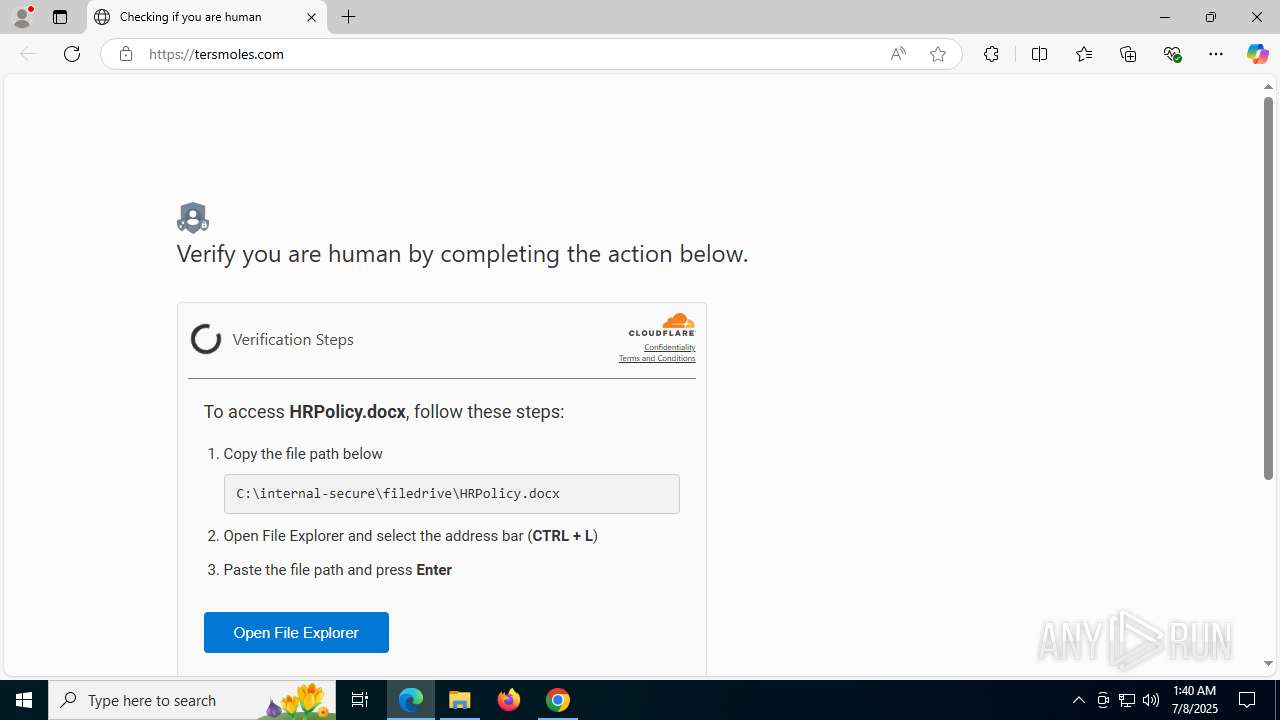
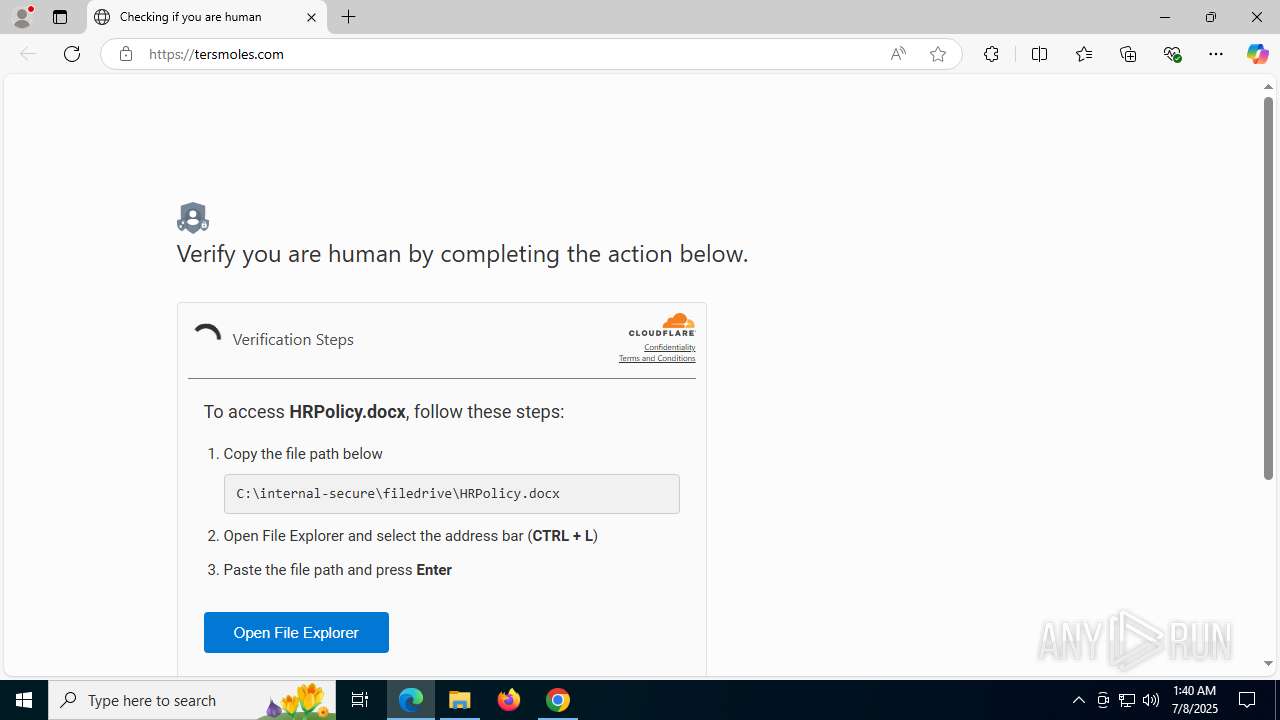
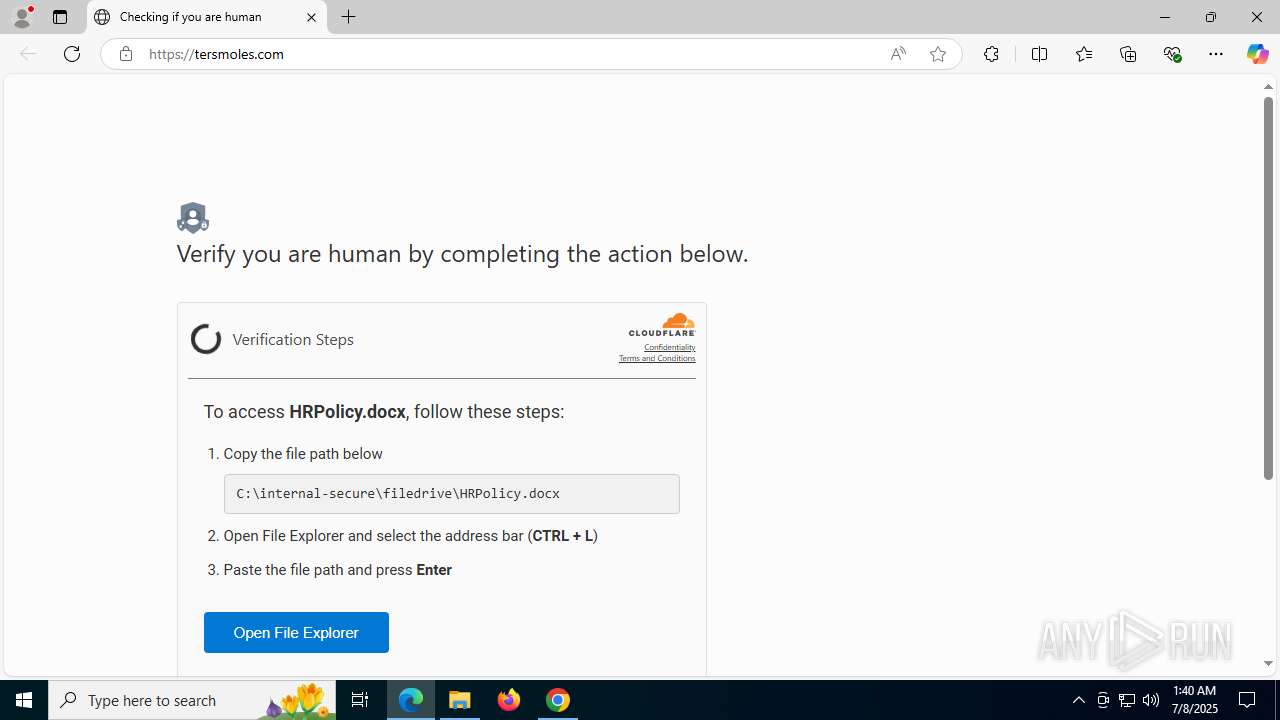
| URL: | https://tersmoles.com/ |
| Full analysis: | https://app.any.run/tasks/acc05a03-7035-4b8f-a596-627c9ecad36f |
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2025, 01:35:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FC439DD736FB479F78262D04EC113098 |
| SHA1: | E4D061E318C87713ECC520C6863B75FC1F636625 |
| SHA256: | 78D8C773A0023C243081E0E90288877496A68BB4839EFA4C1A72553C5DF63325 |
| SSDEEP: | 3:N8IG35LGKIK:2ILKIK |
MALICIOUS
Changes the autorun value in the registry
- setup.exe (PID: 2348)
SUSPICIOUS
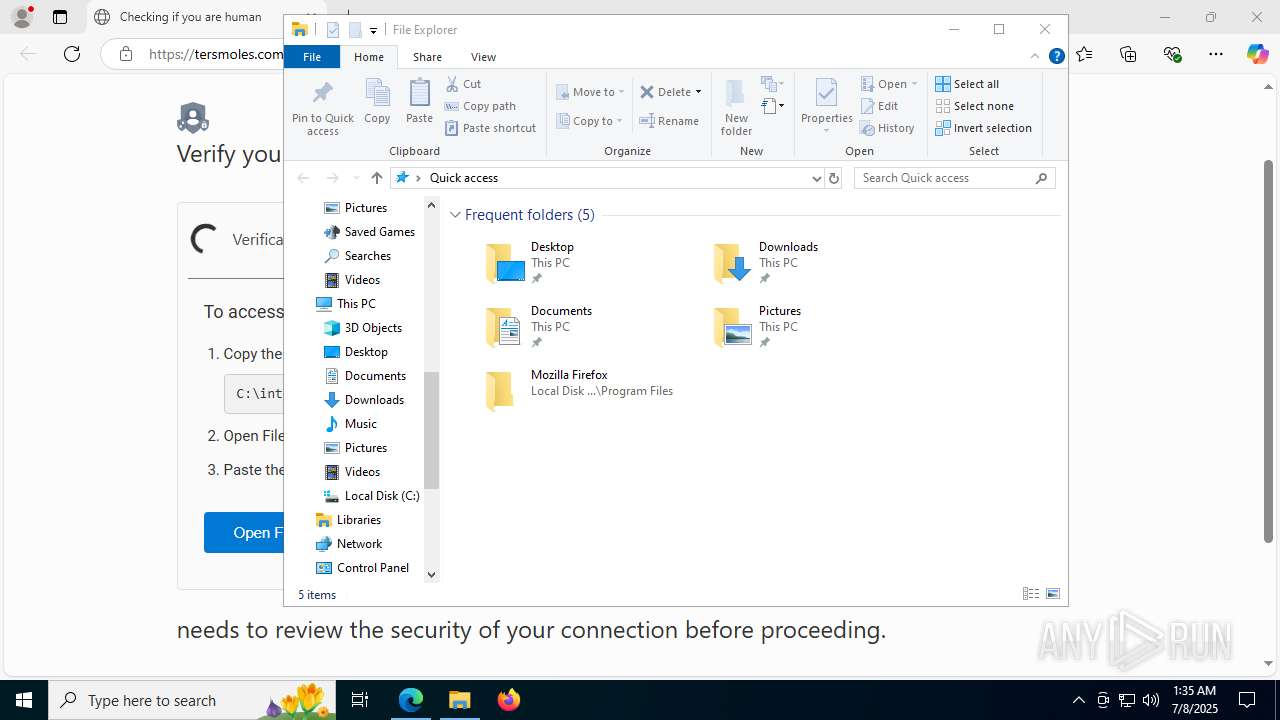
Executes script without checking the security policy
- powershell.exe (PID: 7564)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7564)
Executable content was dropped or overwritten
- powershell.exe (PID: 7564)
- updater.exe (PID: 4132)
- updater.exe (PID: 4456)
- 138.0.7204.97_chrome_installer_uncompressed.exe (PID: 7196)
- setup.exe (PID: 2348)
- updater.exe (PID: 6584)
- updater.exe (PID: 888)
Executing commands from ".cmd" file
- powershell.exe (PID: 7564)
The executable file from the user directory is run by the CMD process
- chrome.exe (PID: 6260)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7564)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7564)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 7564)
Reads security settings of Internet Explorer
- chrome.exe (PID: 6260)
- updater.exe (PID: 4132)
Application launched itself
- chrome.exe (PID: 6260)
- updater.exe (PID: 4132)
- updater.exe (PID: 4456)
- updater.exe (PID: 6584)
- setup.exe (PID: 2348)
- setup.exe (PID: 1392)
- updater.exe (PID: 6584)
- updater.exe (PID: 888)
Executes as Windows Service
- updater.exe (PID: 4456)
- updater.exe (PID: 6584)
- updater.exe (PID: 6584)
Creates a software uninstall entry
- setup.exe (PID: 2348)
Searches for installed software
- setup.exe (PID: 2348)
INFO
Checks supported languages
- identity_helper.exe (PID: 7464)
- chrome.exe (PID: 6260)
- updater.exe (PID: 8076)
- chrome.exe (PID: 7956)
- updater.exe (PID: 4132)
- updater.exe (PID: 4456)
- updater.exe (PID: 8132)
- updater.exe (PID: 6584)
- updater.exe (PID: 3488)
- 138.0.7204.97_chrome_installer_uncompressed.exe (PID: 7196)
- setup.exe (PID: 6388)
- setup.exe (PID: 1392)
- setup.exe (PID: 2760)
- elevation_service.exe (PID: 7652)
- updater.exe (PID: 7580)
- updater.exe (PID: 6584)
- updater.exe (PID: 888)
- UpdaterSetup.exe (PID: 1752)
- updater.exe (PID: 7900)
- setup.exe (PID: 2348)
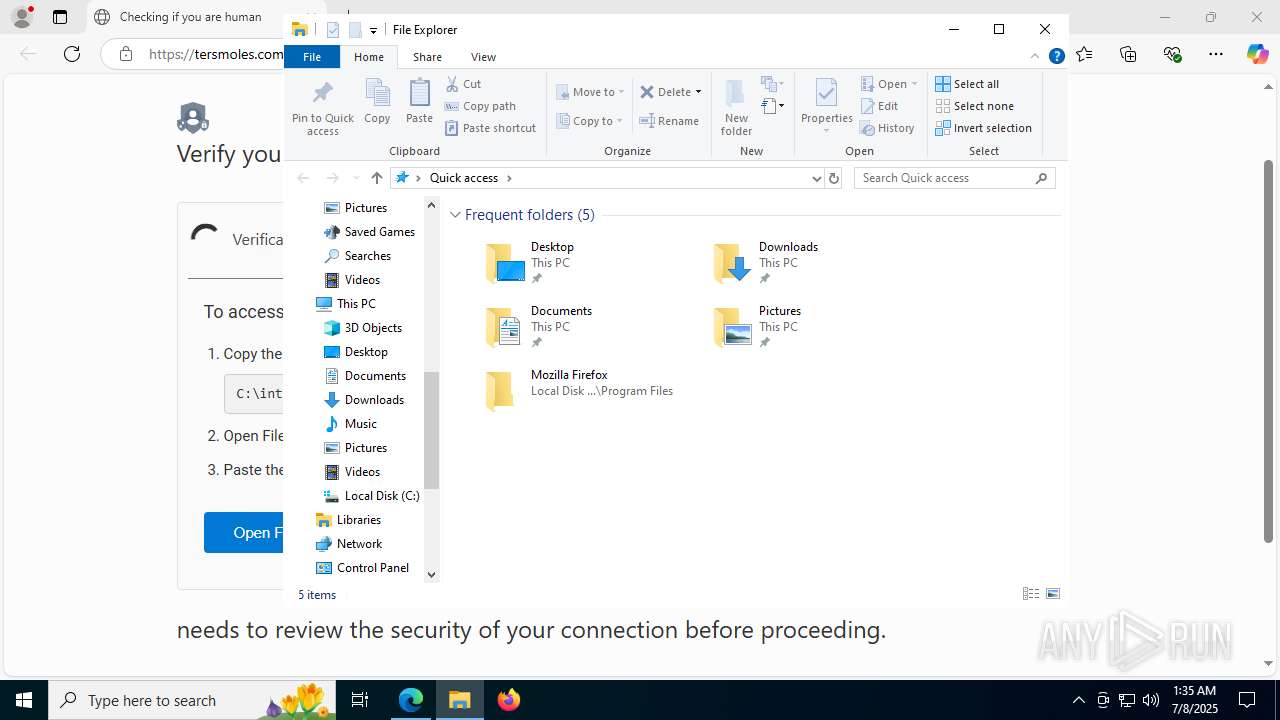
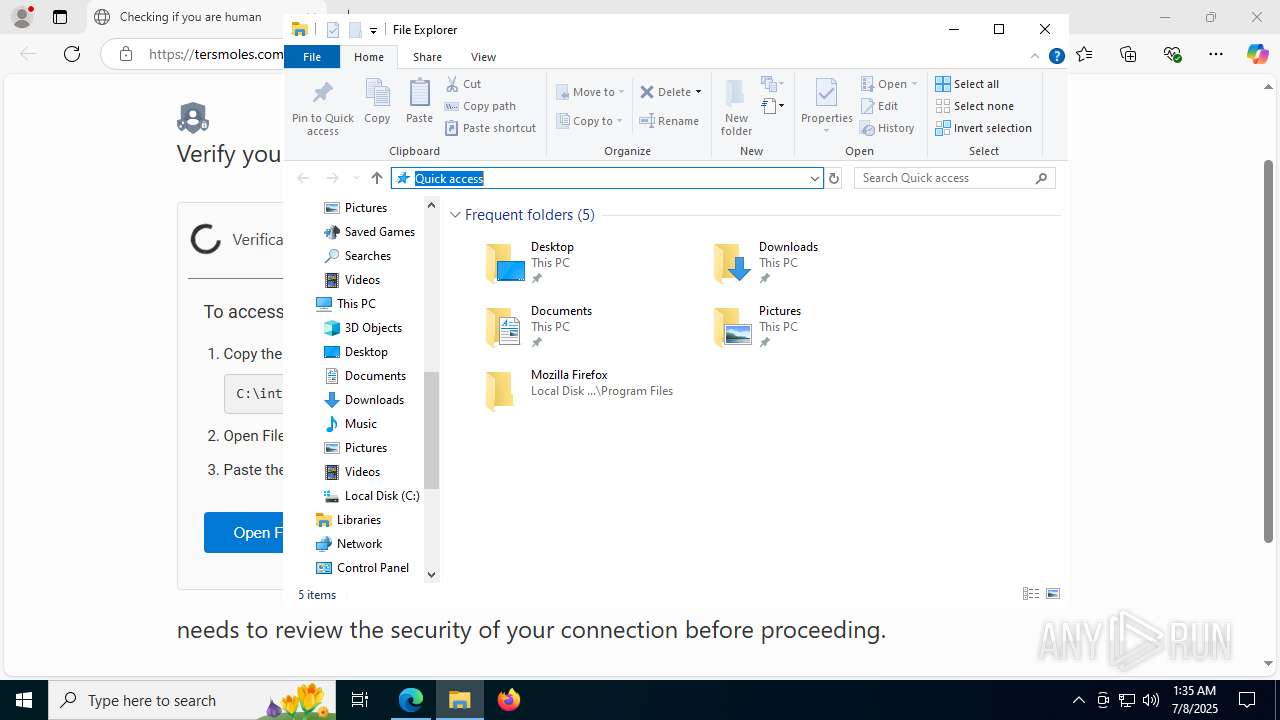
Manual execution by a user
- powershell.exe (PID: 7564)
- chrome.exe (PID: 7640)
Reads Environment values
- identity_helper.exe (PID: 7464)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 7564)
Application launched itself
- msedge.exe (PID: 4100)
- chrome.exe (PID: 7640)
Reads the computer name
- identity_helper.exe (PID: 7464)
- chrome.exe (PID: 6260)
- chrome.exe (PID: 7956)
- updater.exe (PID: 4456)
- updater.exe (PID: 4132)
- updater.exe (PID: 6584)
- 138.0.7204.97_chrome_installer_uncompressed.exe (PID: 7196)
- setup.exe (PID: 2348)
- setup.exe (PID: 1392)
- elevation_service.exe (PID: 7652)
- updater.exe (PID: 6584)
- updater.exe (PID: 888)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7564)
The sample compiled with english language support
- powershell.exe (PID: 7564)
- updater.exe (PID: 4132)
- updater.exe (PID: 4456)
- 138.0.7204.97_chrome_installer_uncompressed.exe (PID: 7196)
- setup.exe (PID: 2348)
- updater.exe (PID: 6584)
- updater.exe (PID: 888)
Checks proxy server information
- powershell.exe (PID: 7564)
- slui.exe (PID: 7496)
- updater.exe (PID: 4132)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7564)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7564)
Process checks computer location settings
- chrome.exe (PID: 6260)
Creates files in the program directory
- updater.exe (PID: 8076)
- updater.exe (PID: 4132)
- updater.exe (PID: 4456)
- updater.exe (PID: 6584)
- setup.exe (PID: 2348)
- setup.exe (PID: 1392)
- updater.exe (PID: 6584)
- updater.exe (PID: 888)
- updater.exe (PID: 7900)
Create files in a temporary directory
- chrome.exe (PID: 7956)
- updater.exe (PID: 4132)
Process checks whether UAC notifications are on
- updater.exe (PID: 4132)
- updater.exe (PID: 4456)
- updater.exe (PID: 6584)
- updater.exe (PID: 6584)
- updater.exe (PID: 888)
Reads the software policy settings
- updater.exe (PID: 4132)
- updater.exe (PID: 6584)
- slui.exe (PID: 7496)
- updater.exe (PID: 6584)
Creates files or folders in the user directory
- updater.exe (PID: 4132)
Launching a file from a Registry key
- setup.exe (PID: 2348)
Executes as Windows Service
- elevation_service.exe (PID: 7652)
Connects to unusual port
- chrome.exe (PID: 1328)
Reads the machine GUID from the registry
- updater.exe (PID: 4132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
244
Monitored processes
96
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --enable-dinosaur-easter-egg-alt-images --force-high-res-timeticks=disabled --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=1948,i,9722910779431846947,12207483730613494017,262144 --variations-seed-version --mojo-platform-channel-handle=3120 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 138.0.7204.97 Modules
| |||||||||||||||
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --force-high-res-timeticks=disabled --field-trial-handle=1948,i,9722910779431846947,12207483730613494017,262144 --variations-seed-version --mojo-platform-channel-handle=6860 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 138.0.7204.97 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6116,i,17116922499830129973,15131999482948358283,262144 --variations-seed-version --mojo-platform-channel-handle=7032 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 888 | "C:\WINDOWS\SystemTemp\Google1752_119689568\bin\updater.exe" --enable-ceca-experiment --update --system --enable-logging --vmodule=*/chrome/updater/*=2 | C:\Windows\SystemTemp\Google1752_119689568\bin\updater.exe | UpdaterSetup.exe | ||||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater (x64) Exit code: 0 Version: 140.0.7272.0 Modules
| |||||||||||||||
| 1156 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3636,i,17116922499830129973,15131999482948358283,262144 --variations-seed-version --mojo-platform-channel-handle=3652 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --enable-dinosaur-easter-egg-alt-images --force-high-res-timeticks=disabled --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --field-trial-handle=1948,i,9722910779431846947,12207483730613494017,262144 --variations-seed-version --mojo-platform-channel-handle=4896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 138.0.7204.97 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --force-high-res-timeticks=disabled --field-trial-handle=1948,i,9722910779431846947,12207483730613494017,262144 --variations-seed-version --mojo-platform-channel-handle=6996 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 138.0.7204.97 Modules
| |||||||||||||||
| 1288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5996,i,17116922499830129973,15131999482948358283,262144 --variations-seed-version --mojo-platform-channel-handle=6560 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3664,i,17116922499830129973,15131999482948358283,262144 --variations-seed-version --mojo-platform-channel-handle=3836 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
31 938
Read events
31 684
Write events
234
Delete events
20
Modification events
| (PID) Process: | (6428) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6428) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6428) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6428) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (6428) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (6428) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (4100) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4100) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4100) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4100) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
11
Suspicious files
453
Text files
152
Unknown types
52
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF175aa3.TMP | — | |
MD5:— | SHA256:— | |||
| 4100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF175aa3.TMP | — | |
MD5:— | SHA256:— | |||
| 4100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF175a93.TMP | — | |
MD5:— | SHA256:— | |||
| 4100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF175aa3.TMP | — | |
MD5:— | SHA256:— | |||
| 4100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF175aa3.TMP | — | |
MD5:— | SHA256:— | |||
| 4100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF175ad2.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
119
DNS requests
145
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4132 | updater.exe | GET | 200 | 142.250.185.67:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
4132 | updater.exe | GET | 200 | 142.250.185.67:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEAo1gm31egIKCiGPvfORQ8M%3D | unknown | — | — | whitelisted |
6584 | updater.exe | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/%7B8a69d345-d564-463c-aff1-a69d9e530f96%7D/f11035a609826e842104c6a00f39912a0d6a8ea396d32d9c6dc7fa62167cab8a | unknown | — | — | whitelisted |
7564 | powershell.exe | GET | 200 | 104.18.21.213:80 | http://r10.c.lencr.org/73.crl | unknown | — | — | whitelisted |
5708 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:Q491tjM3ge6xuEuFTYTqpGX78N2ZE3-Z13UX_s_uD3Q&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6472 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752341713&P2=404&P3=2&P4=II48KOzb9yS%2blZD8dDncjgbIUR%2fxvk5jH52p6Ke7vSjDwqlgoqU2W2H3BXbiBj9s59kN6Ji2%2bngemCeppaBiQA%3d%3d | unknown | — | — | whitelisted |
6472 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1752341735&P2=404&P3=2&P4=ls%2b7HEKusvUV%2fefeE8n0sUJuyzgu6dbNJItraiX7giK%2bmNr369QV08cnT56FTBqn4jFV0kGiBNSwGuTQQHBX9w%3d%3d | unknown | — | — | whitelisted |
6472 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1752338117&P2=404&P3=2&P4=OLMCl%2bmSYTwj7v1I%2bSjZKwJDUXkWtucKKJUh3Hy%2fn3C6PJEWAldxQZvIZnQ2Jgus0Ysj3C65VEv8VIYfa07YwA%3d%3d | unknown | — | — | whitelisted |
6472 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1752341735&P2=404&P3=2&P4=ls%2b7HEKusvUV%2fefeE8n0sUJuyzgu6dbNJItraiX7giK%2bmNr369QV08cnT56FTBqn4jFV0kGiBNSwGuTQQHBX9w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6128 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5708 | msedge.exe | 45.155.69.26:443 | tersmoles.com | LeaseWeb Netherlands B.V. | SG | unknown |
5708 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5708 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5708 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5708 | msedge.exe | 92.123.104.53:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
tersmoles.com |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
i.postimg.cc |
| whitelisted |
2captcha.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5708 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
5708 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
5708 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5708 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5708 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
5708 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
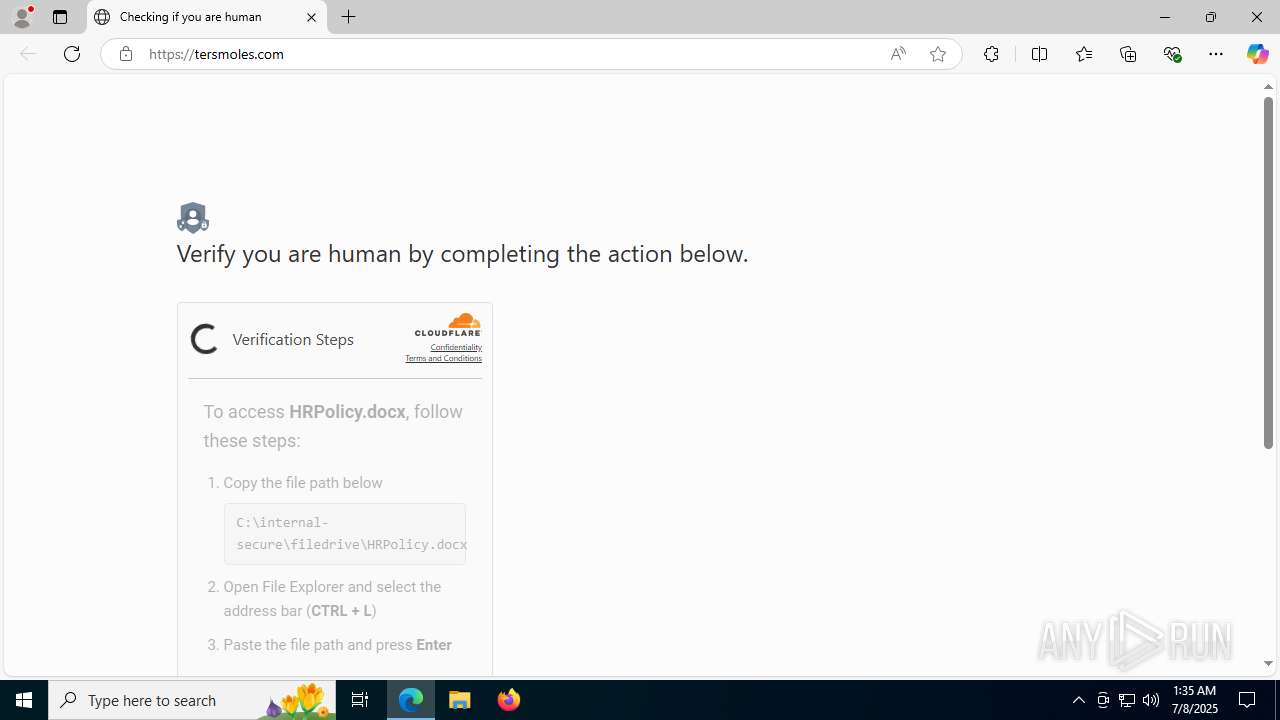
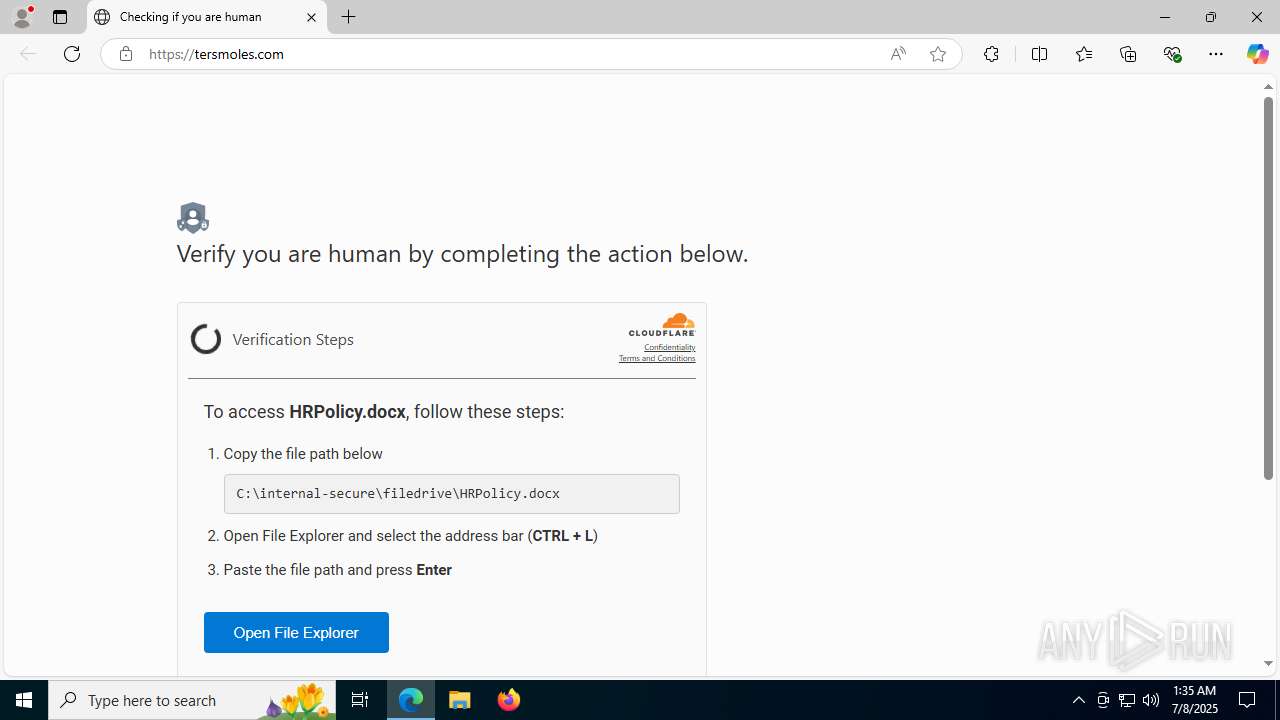
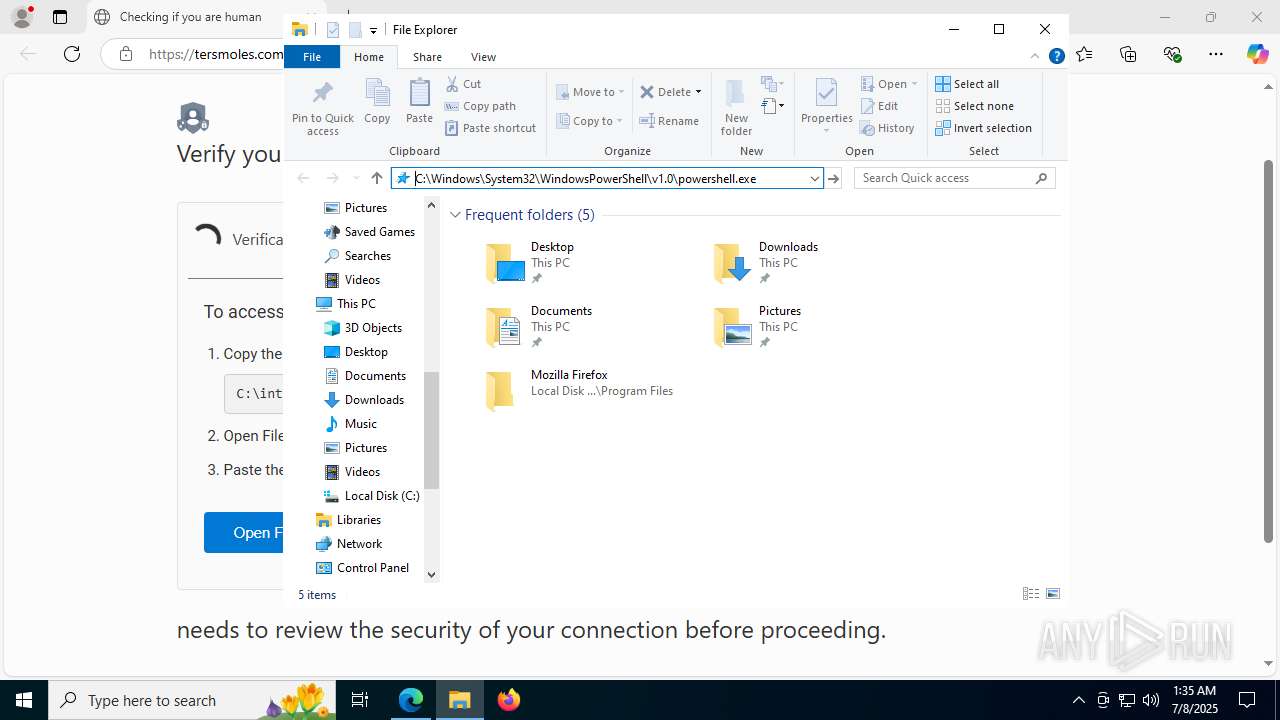
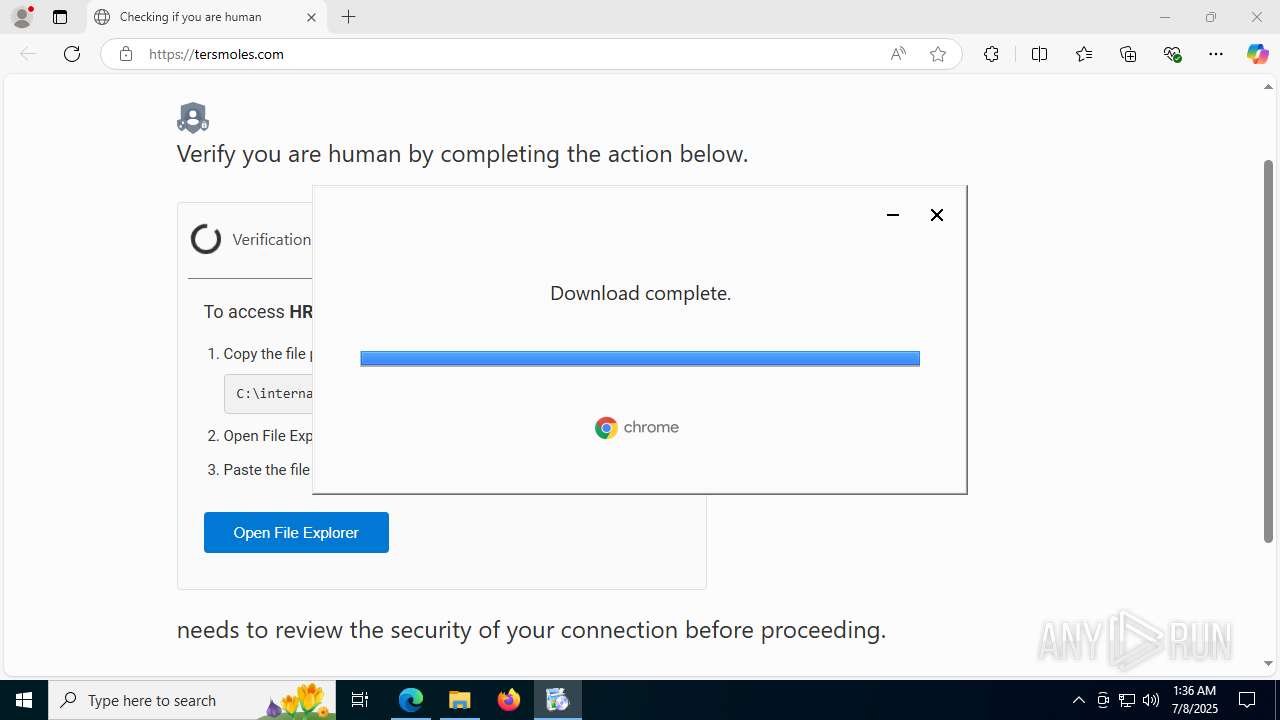
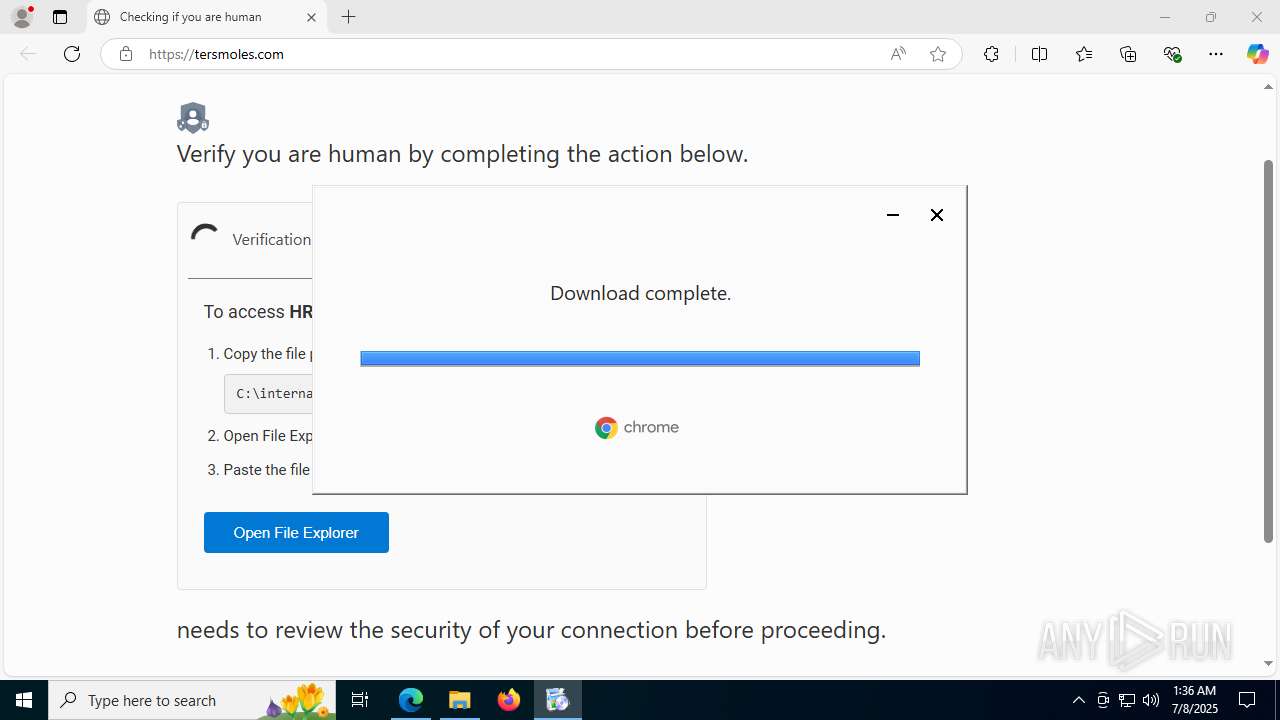
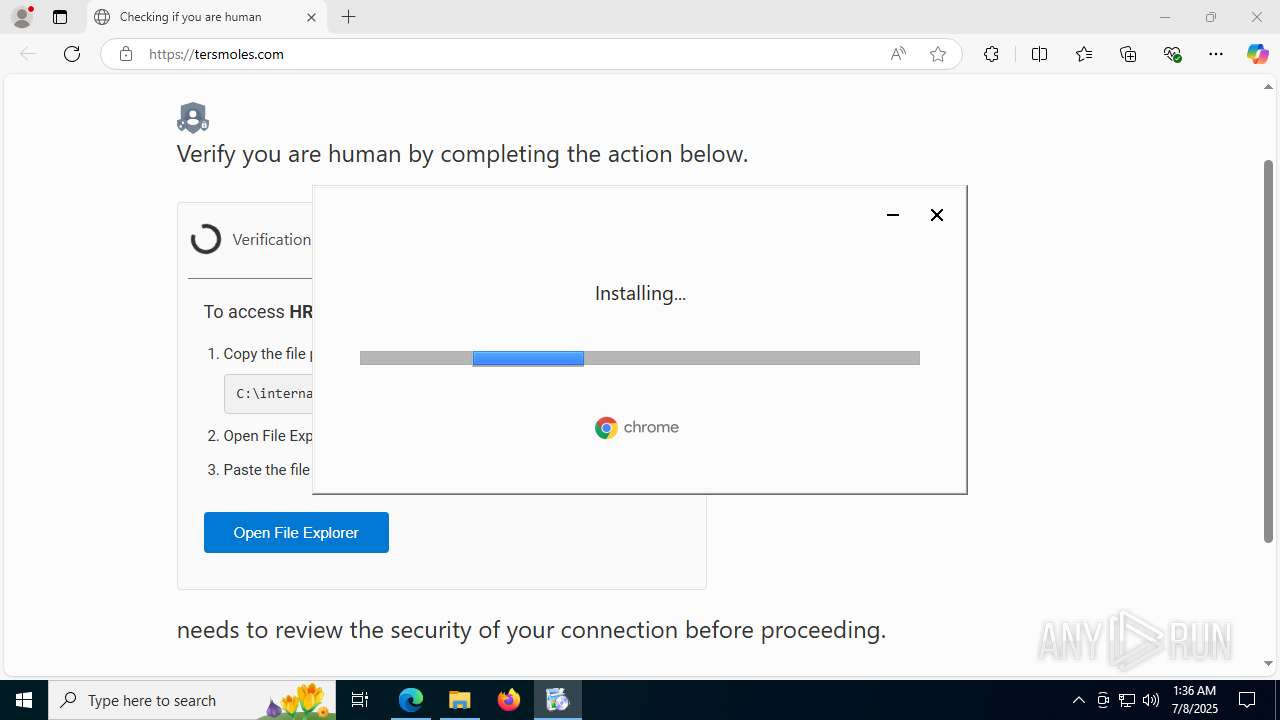
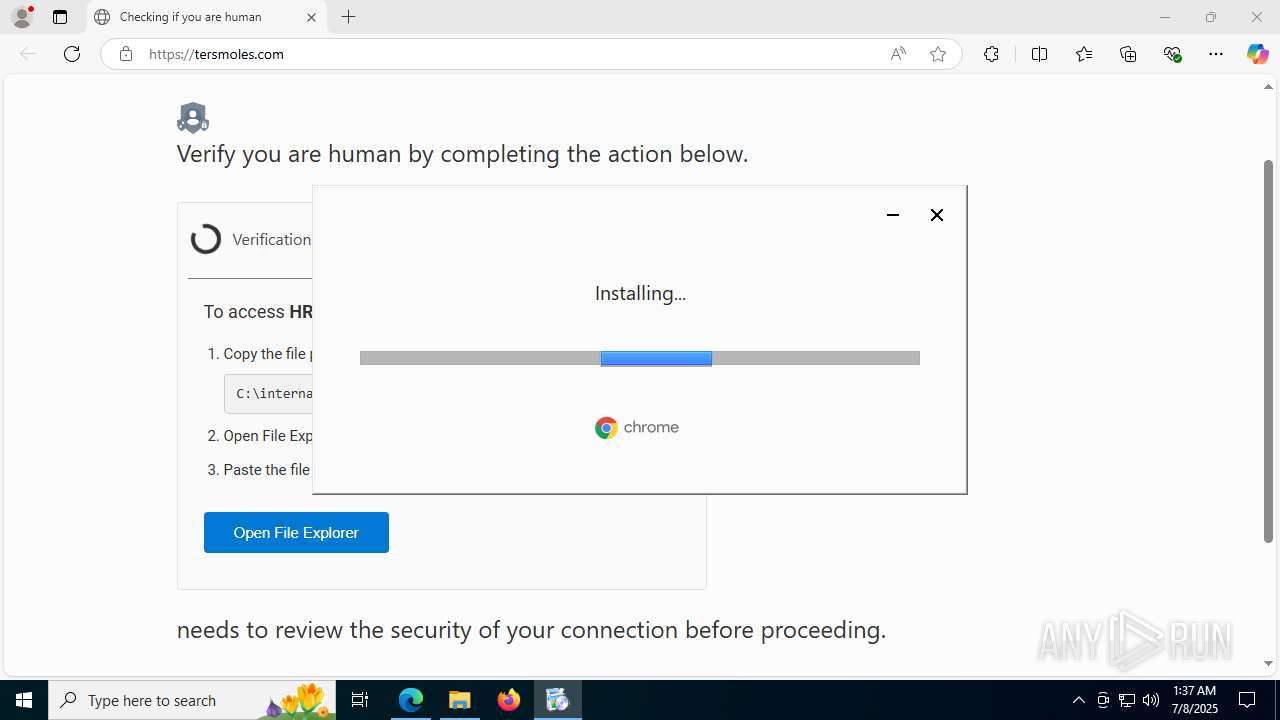
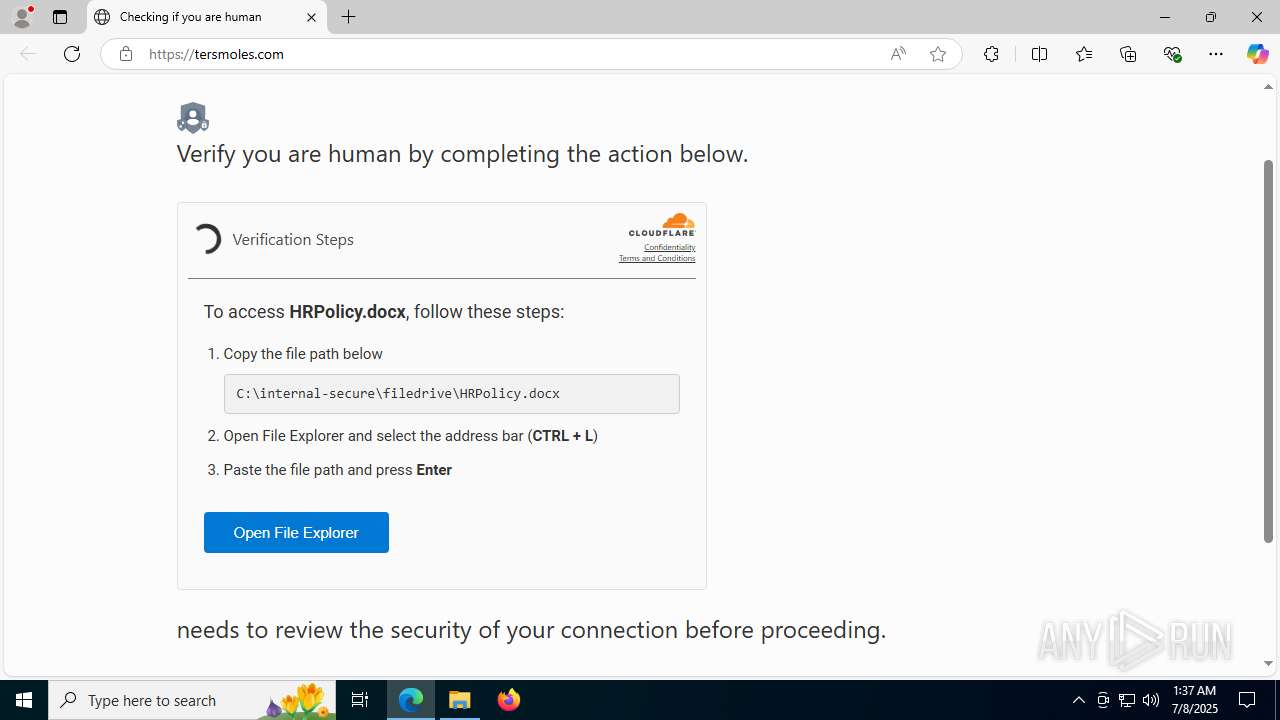
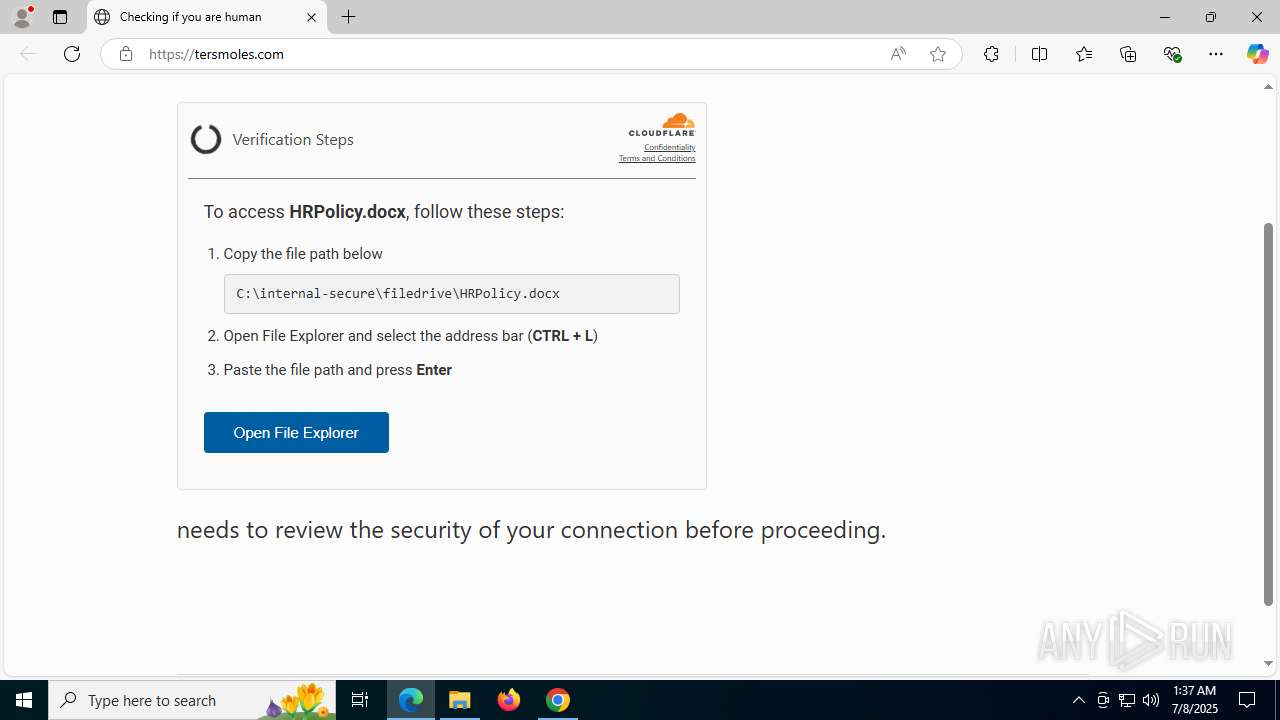
— | — | A Network Trojan was detected | ET MALWARE Observed ClickFix Powershell Delivery Page Inbound |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
Process | Message |
|---|---|
chrome.exe | I0000 00:00:1751938634.078595 5908 voice_transcription.cc:58] Registering VoiceTranscriptionCapability
|