| File name: | ActivationAcronisTIH.exe |
| Full analysis: | https://app.any.run/tasks/d33c7598-6476-4f82-b919-2cb0a9b88973 |
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2020, 04:45:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F13674039DCA80780934E0B15D32D6C6 |
| SHA1: | 066BD9723E4D83211C8A703813EC681D83964CFF |
| SHA256: | 78D30DC57AEC580F462CB2A4C1E3E6EA7D1E643228F31A956C3101763677A767 |
| SSDEEP: | 24576:eu+40vPX5+JiaG8mTKXzvGAeq+fBsmcfgLP8UI0N+gwE:h+4SX5a8WXzaq+fUfg4UI0d |
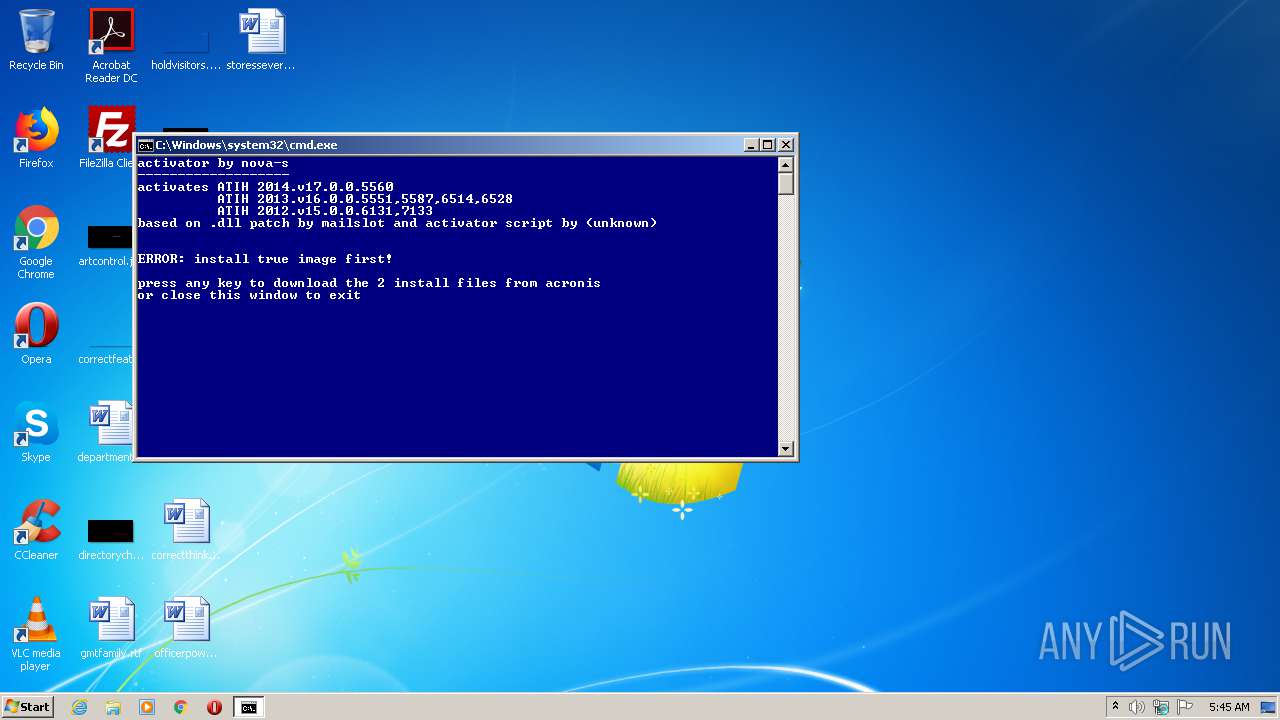
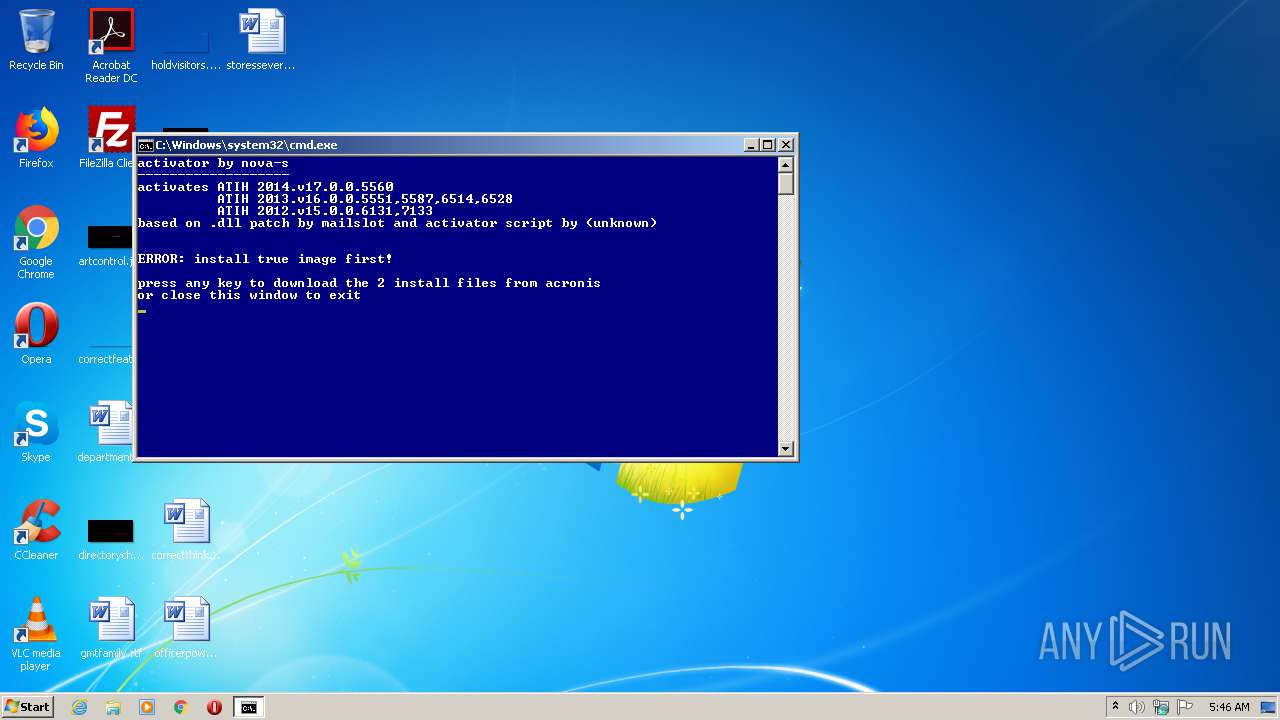
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2424)
SUSPICIOUS
Executable content was dropped or overwritten
- ActivationAcronisTIH.exe (PID: 2716)
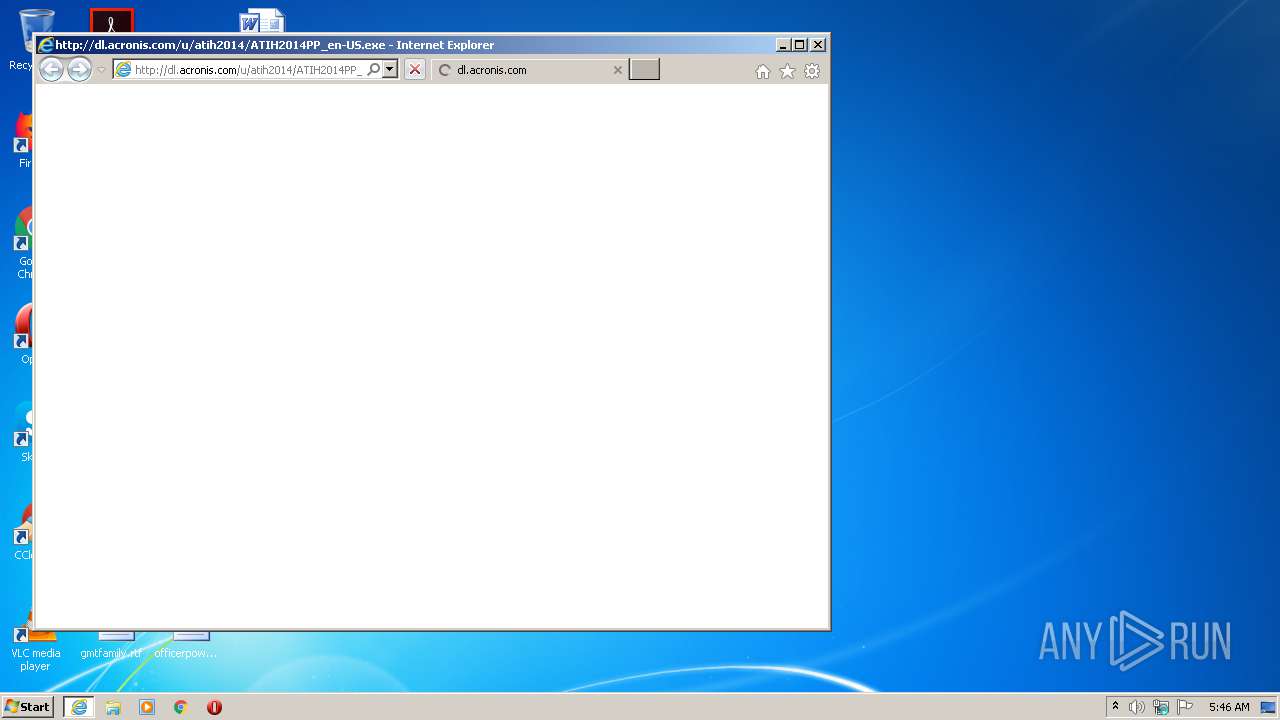
Starts Internet Explorer
- cmd.exe (PID: 2424)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2612)
Starts CMD.EXE for commands execution
- ActivationAcronisTIH.exe (PID: 2716)
- cmd.exe (PID: 2424)
Checks supported languages
- reg.exe (PID: 3480)
Checks Windows language
- reg.exe (PID: 3480)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 960)
- iexplore.exe (PID: 1028)
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 2848)
Changes internet zones settings
- iexplore.exe (PID: 960)
- iexplore.exe (PID: 4052)
Modifies the phishing filter of IE
- iexplore.exe (PID: 960)
Application launched itself
- iexplore.exe (PID: 960)
- iexplore.exe (PID: 4052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2005:01:16 18:28:05+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 77824 |
| InitializedDataSize: | 20992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1215f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 17.0.0.5560 |
| ProductVersionNumber: | 17.0.0.5560 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | not by Acronis |
| FileDescription: | activates build 17.0.0.5560 and earlier |
| FileVersion: | 1, 0, 0, 0 |
| InternalName: | Acronis True Image 2014 Activator |
| LegalCopyright: | not by Acronis |
| LegalTrademarks: | - |
| OriginalFileName: | Acronis True Image 2014 Activator |
| PrivateBuild: | - |
| ProductName: | Acronis True Image 2014 Activator |
| ProductVersion: | 1, 0, 0, 0 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jan-2005 17:28:05 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | not by Acronis |
| FileDescription: | activates build 17.0.0.5560 and earlier |
| FileVersion: | 1, 0, 0, 0 |
| InternalName: | Acronis True Image 2014 Activator |
| LegalCopyright: | not by Acronis |
| LegalTrademarks: | - |
| OriginalFilename: | Acronis True Image 2014 Activator |
| PrivateBuild: | - |
| ProductName: | Acronis True Image 2014 Activator |
| ProductVersion: | 1, 0, 0, 0 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 16-Jan-2005 17:28:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00012F4E | 0x00013000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42377 |
.rdata | 0x00014000 | 0x000039F0 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.32978 |
.data | 0x00018000 | 0x000009F0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.83549 |
.rsrc | 0x00019000 | 0x00000D64 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.21808 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.37906 | 1040 | UNKNOWN | English - United States | RT_VERSION |
5 | 1.43775 | 52 | UNKNOWN | English - United States | RT_STRING |
50 | 2.5172 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
164 | 2.16096 | 20 | UNKNOWN | Dutch - Belgium | RT_GROUP_ICON |
500 | 3.10381 | 184 | UNKNOWN | English - United States | RT_DIALOG |
MAINICON | 2.32322 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
COMCTL32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
USER32.dll |
Total processes
46
Monitored processes
10
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\Program Files\Internet Explorer\iexplore.exe" http://download.acronis.com/ATIH2014_trial_en-US.exe | C:\Program Files\Internet Explorer\iexplore.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4052 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1928 | "C:\Users\admin\AppData\Local\Temp\ActivationAcronisTIH.exe" | C:\Users\admin\AppData\Local\Temp\ActivationAcronisTIH.exe | — | explorer.exe | |||||||||||
User: admin Company: not by Acronis Integrity Level: MEDIUM Description: activates build 17.0.0.5560 and earlier Exit code: 3221226540 Version: 1, 0, 0, 0 Modules
| |||||||||||||||
| 2424 | cmd /c .\Activation.cmd | C:\Windows\system32\cmd.exe | — | ActivationAcronisTIH.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2612 | C:\Windows\system32\cmd.exe /c REG QUERY "HKLM\SYSTEM\CurrentControlSet\Control\Nls\Language" /v InstallLanguage | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2636 | ping -n 16 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2716 | "C:\Users\admin\AppData\Local\Temp\ActivationAcronisTIH.exe" | C:\Users\admin\AppData\Local\Temp\ActivationAcronisTIH.exe | explorer.exe | ||||||||||||
User: admin Company: not by Acronis Integrity Level: HIGH Description: activates build 17.0.0.5560 and earlier Exit code: 0 Version: 1, 0, 0, 0 Modules
| |||||||||||||||
| 2848 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:960 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3480 | REG QUERY "HKLM\SYSTEM\CurrentControlSet\Control\Nls\Language" /v InstallLanguage | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4052 | "C:\Program Files\Internet Explorer\iexplore.exe" http://dl.acronis.com/u/atih2014/ATIH2014PP_en-US.exe | C:\Program Files\Internet Explorer\iexplore.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
417
Read events
317
Write events
100
Delete events
0
Modification events
| (PID) Process: | (2424) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 01000000000000004C9B09B44F3DD601 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3322872210 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30817615 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (960) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
6
Suspicious files
1
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
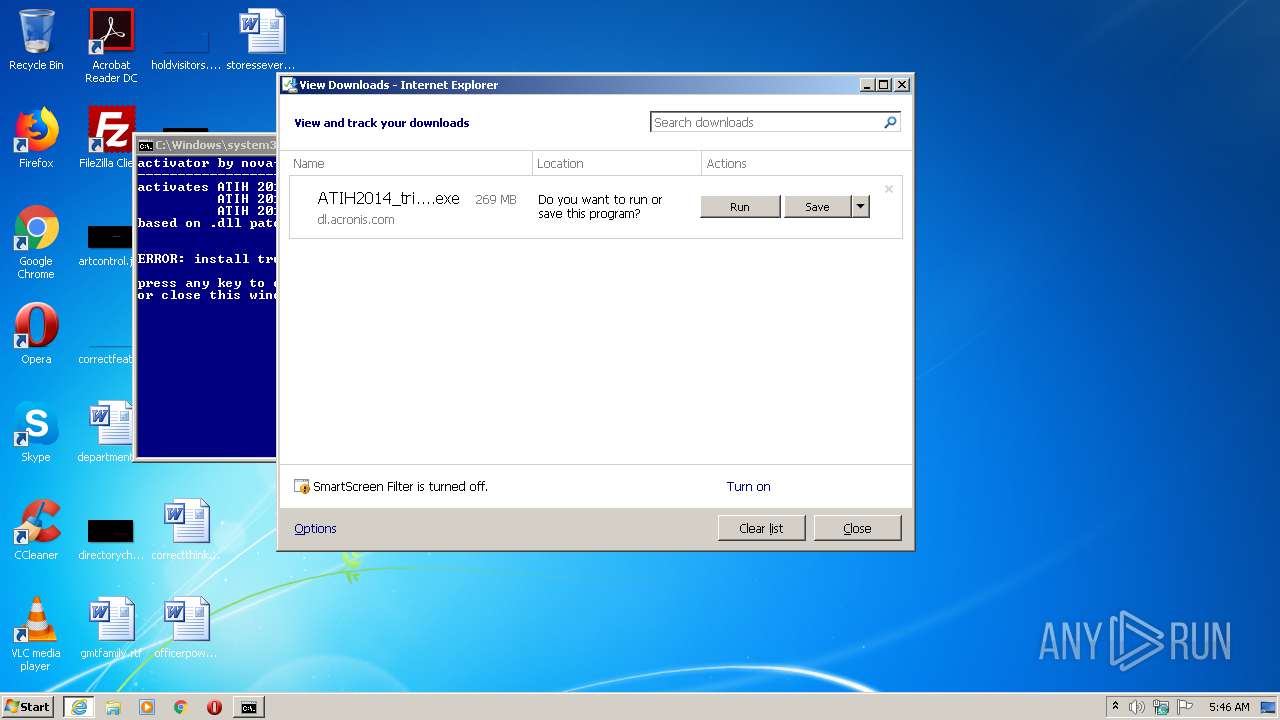
| 2848 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\ATIH2014_trial_en-US[1].exe | — | |
MD5:— | SHA256:— | |||
| 960 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFEADFA8090DFF00C5.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2716 | ActivationAcronisTIH.exe | C:\Users\admin\AppData\Local\Temp\7zS76E7.tmp\Activation_en.cmd | text | |
MD5:— | SHA256:— | |||
| 960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\{F1C6D79F-A942-11EA-8526-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 2716 | ActivationAcronisTIH.exe | C:\Users\admin\AppData\Local\Temp\7zS76E7.tmp\Activation_de.cmd | text | |
MD5:— | SHA256:— | |||
| 2716 | ActivationAcronisTIH.exe | C:\Users\admin\AppData\Local\Temp\7zS76E7.tmp\Version.vbs | text | |
MD5:— | SHA256:— | |||
| 2716 | ActivationAcronisTIH.exe | C:\Users\admin\AppData\Local\Temp\7zS76E7.tmp\Acronis_x64.reg | text | |
MD5:— | SHA256:— | |||
| 2716 | ActivationAcronisTIH.exe | C:\Users\admin\AppData\Local\Temp\7zS76E7.tmp\Acronis_x86.reg | text | |
MD5:— | SHA256:— | |||
| 2716 | ActivationAcronisTIH.exe | C:\Users\admin\AppData\Local\Temp\7zS76E7.tmp\Activation.cmd | text | |
MD5:6064161BD7E5740E958C1BA8B8E2CBC9 | SHA256:D5C827805F59C9E845177D4CF4A4CEECF81F1D732553CA84E815CE537FB30FB4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
8
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1028 | iexplore.exe | GET | — | 2.16.107.50:80 | http://dl.acronis.com/u/atih2014/ATIH2014PP_en-US.exe | unknown | — | — | whitelisted |
2848 | iexplore.exe | GET | — | 2.16.107.50:80 | http://dl.acronis.com/u/ATIH2014_trial_en-US.exe | unknown | — | — | whitelisted |
2848 | iexplore.exe | GET | 302 | 69.20.59.72:80 | http://download.acronis.com/ATIH2014_trial_en-US.exe | US | html | 138 b | suspicious |
4052 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2848 | iexplore.exe | 69.20.59.72:80 | download.acronis.com | Rackspace Ltd. | US | unknown |
— | — | 2.16.107.50:80 | dl.acronis.com | Akamai International B.V. | — | suspicious |
2848 | iexplore.exe | 2.16.107.50:80 | dl.acronis.com | Akamai International B.V. | — | suspicious |
4052 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.acronis.com |
| suspicious |
dl.acronis.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2848 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |