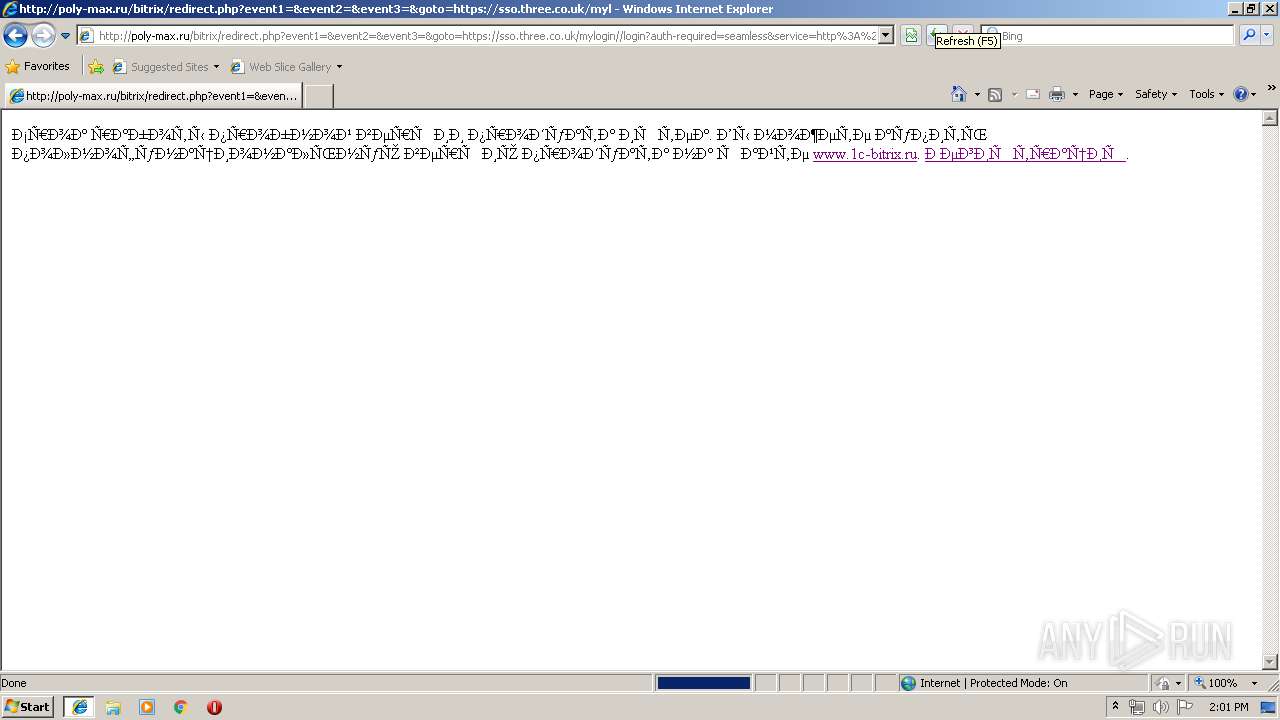
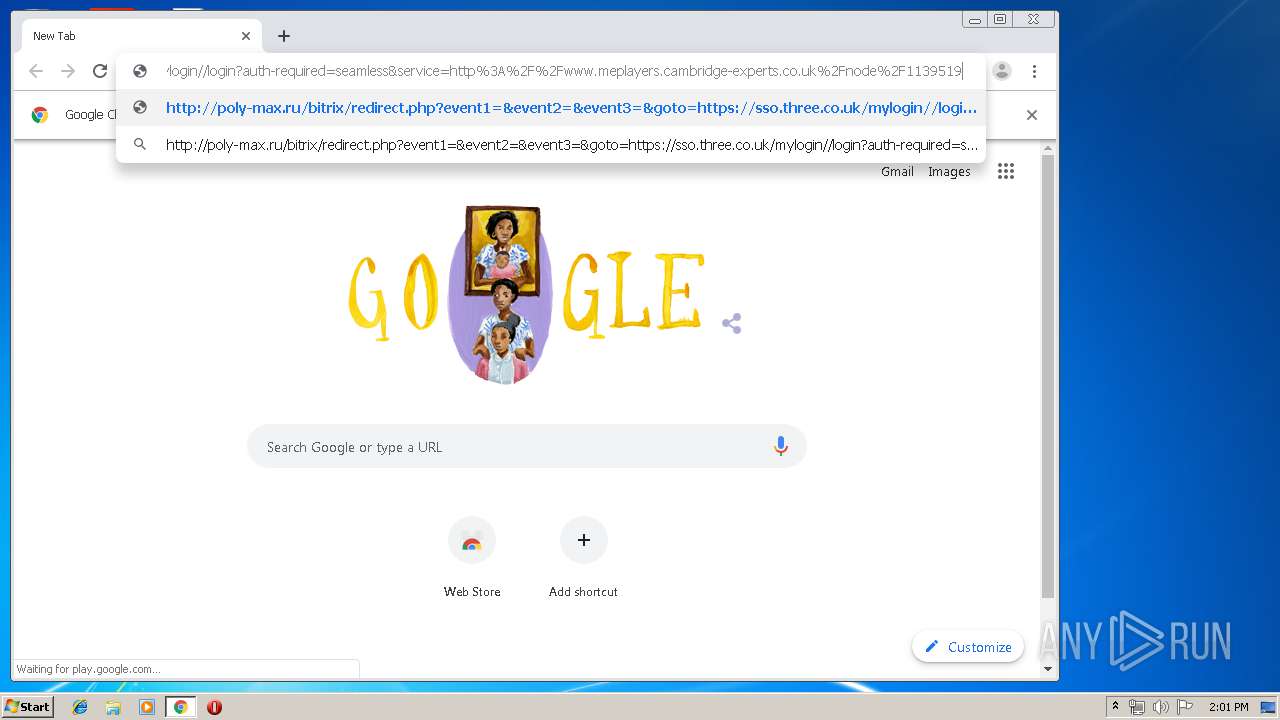
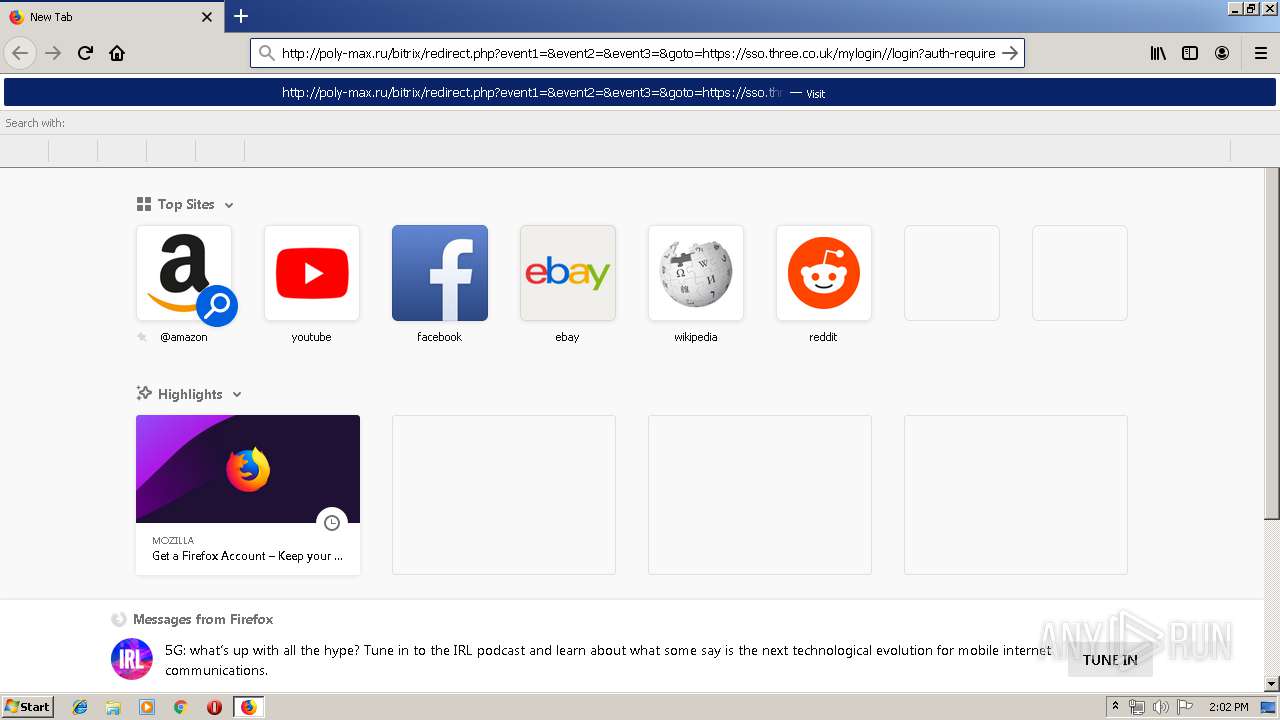
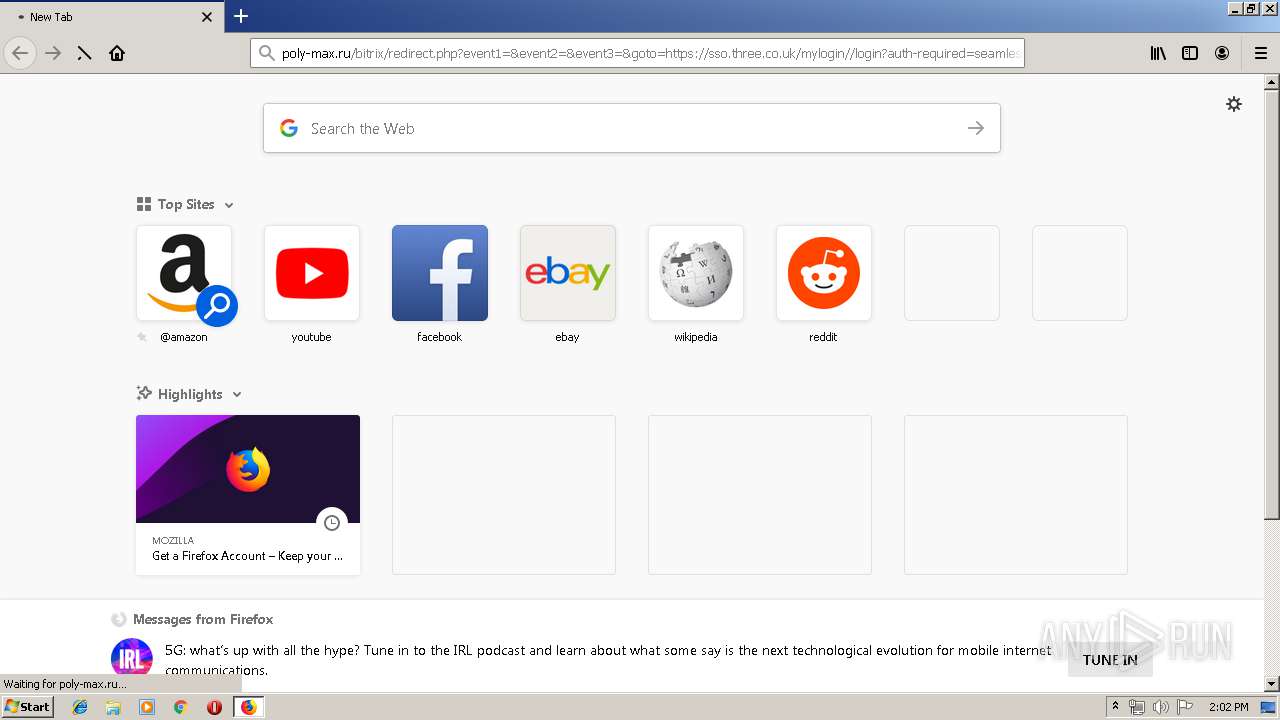
| URL: | http://poly-max.ru/bitrix/redirect.php?event1=&event2=&event3 |
| Full analysis: | https://app.any.run/tasks/aaa38c65-98e4-404c-9619-968de2b95495 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 12:59:50 |
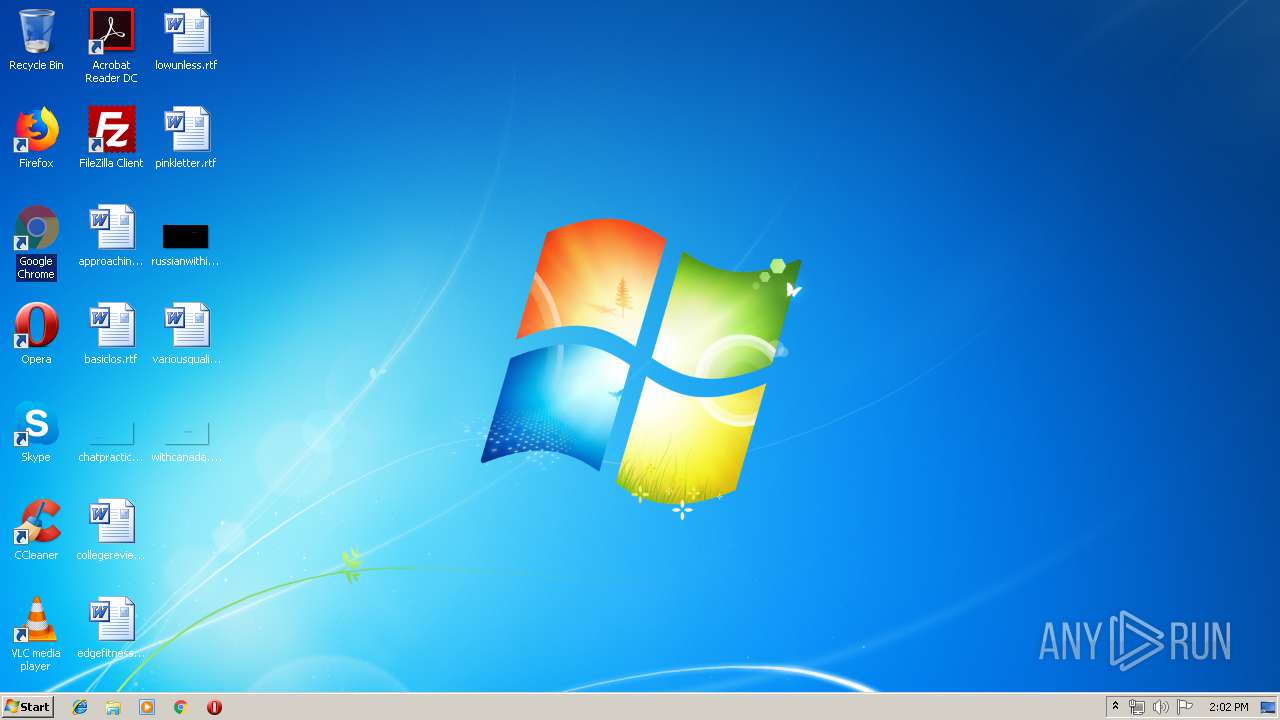
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DD5E5AD25EDC96258F28B7784B88AE08 |
| SHA1: | 3799301EDD447188FFF739D641C68923F74148B4 |
| SHA256: | 78BCD7C2281CED78BD06EBB134EF8C53C3385E12095D824B1C3582A2B048BB03 |
| SSDEEP: | 3:N1KOKFFiMK6HRXPKWn:COGiMK6HxNn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 276)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3576)
INFO
Creates files in the user directory
- iexplore.exe (PID: 3168)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 276)
- iexplore.exe (PID: 1208)
- firefox.exe (PID: 2716)
Changes internet zones settings
- iexplore.exe (PID: 3168)
Application launched itself
- iexplore.exe (PID: 3168)
- firefox.exe (PID: 2716)
- chrome.exe (PID: 3576)
Reads Internet Cache Settings
- iexplore.exe (PID: 1208)
- iexplore.exe (PID: 3168)
Reads internet explorer settings
- iexplore.exe (PID: 1208)
Reads settings of System Certificates
- iexplore.exe (PID: 3168)
- chrome.exe (PID: 764)
Manual execution by user
- firefox.exe (PID: 2736)
- chrome.exe (PID: 3576)
Reads CPU info
- firefox.exe (PID: 2716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
36
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,3055307667274509394,8890469505252328193,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9684661274677032056 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 276 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,3055307667274509394,8890469505252328193,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3493428343359915685 --mojo-platform-channel-handle=2224 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,3055307667274509394,8890469505252328193,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1362089961629827799 --mojo-platform-channel-handle=1616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2716.20.1922599401\1514061224" -childID 3 -isForBrowser -prefsHandle 3772 -prefMapHandle 3776 -prefsLen 7232 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2716 "\\.\pipe\gecko-crash-server-pipe.2716" 3788 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2716.3.1977933056\494063312" -childID 1 -isForBrowser -prefsHandle 1692 -prefMapHandle 1688 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2716 "\\.\pipe\gecko-crash-server-pipe.2716" 1712 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1208 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3168 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,3055307667274509394,8890469505252328193,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14517472930896164318 --mojo-platform-channel-handle=3360 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,3055307667274509394,8890469505252328193,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7548835707684996979 --mojo-platform-channel-handle=4220 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,3055307667274509394,8890469505252328193,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17650553608088732626 --mojo-platform-channel-handle=3940 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 454
Read events
1 267
Write events
179
Delete events
8
Modification events
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {45732BD3-BDCA-11E9-9885-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307080002000D000D0000000600D003 | |||
Executable files
0
Suspicious files
98
Text files
362
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3168 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3168 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1208 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@www.1c-bitrix[1].txt | — | |
MD5:— | SHA256:— | |||
| 1208 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@1c-bitrix[1].txt | — | |
MD5:— | SHA256:— | |||
| 1208 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\FN9WVVVZ\1c-bitrix_ru[1].txt | — | |
MD5:— | SHA256:— | |||
| 1208 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\FN9WVVVZ\1c-bitrix_ru[1].htm | html | |
MD5:— | SHA256:— | |||
| 1208 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1208 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1208 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1208 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\9XAZS9CB\redirect[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
82
DNS requests
99
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
764 | chrome.exe | GET | 204 | 216.58.205.238:80 | http://translate.google.com/gen204?sl=bg&tl=en&textlen=236&sp=nmt&ttt=772&ttl=294&ttf=778&sr=1&nca=te_time&client=te_lib&logld=vTE_20190724_00 | US | — | — | whitelisted |
764 | chrome.exe | GET | 204 | 216.58.205.238:80 | http://translate.google.com/gen204?nca=te_li&client=te_lib&logld=vTE_20190724_00 | US | — | — | whitelisted |
3168 | iexplore.exe | GET | 404 | 87.236.16.29:80 | http://poly-max.ru/favicon.ico | RU | html | 355 b | suspicious |
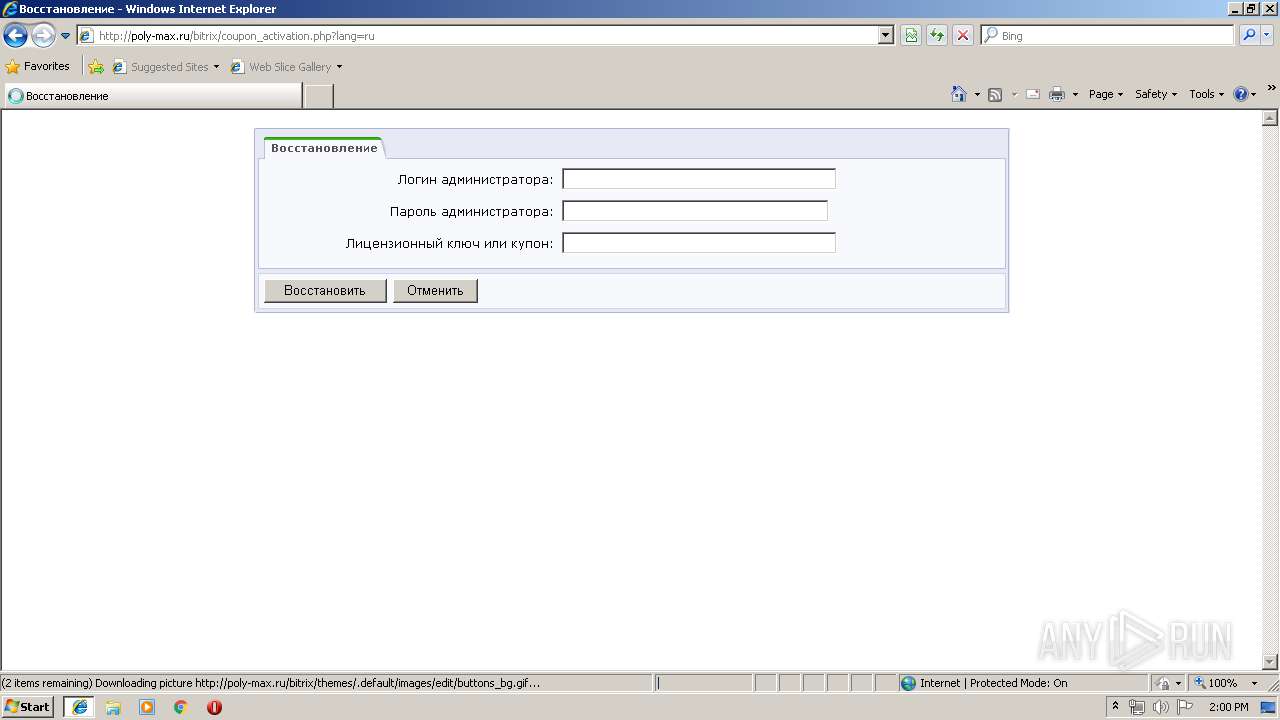
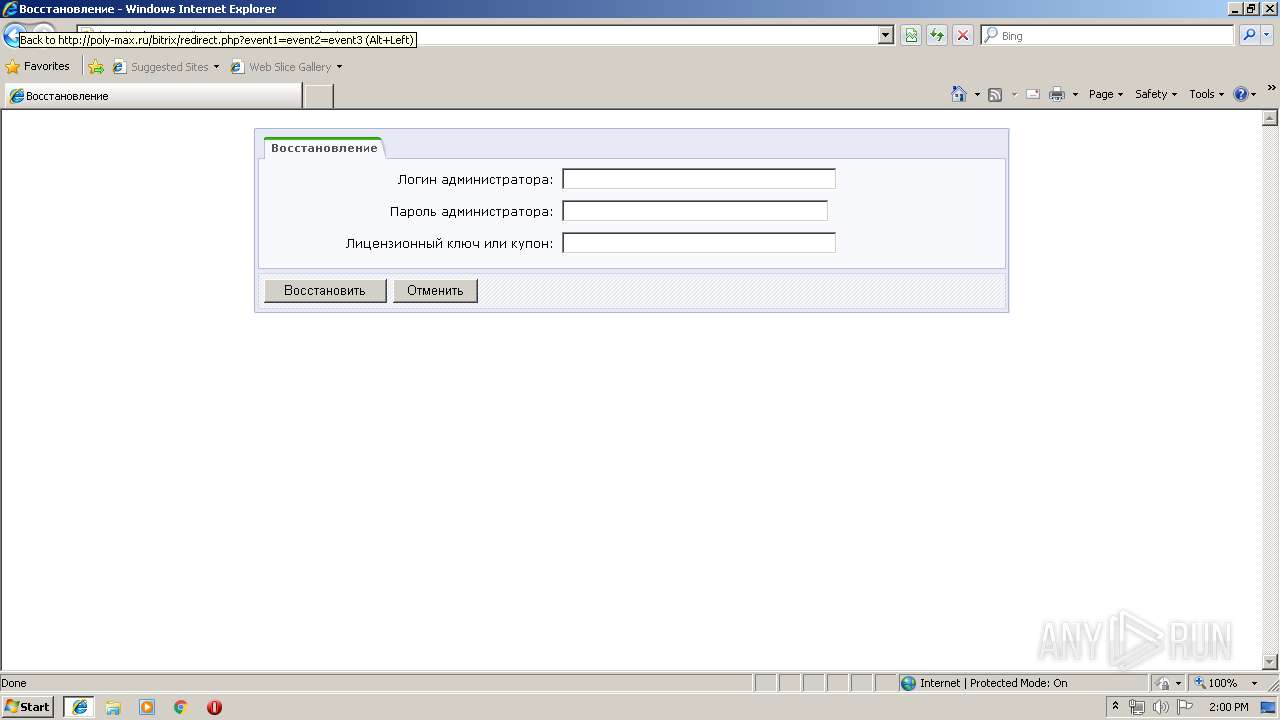
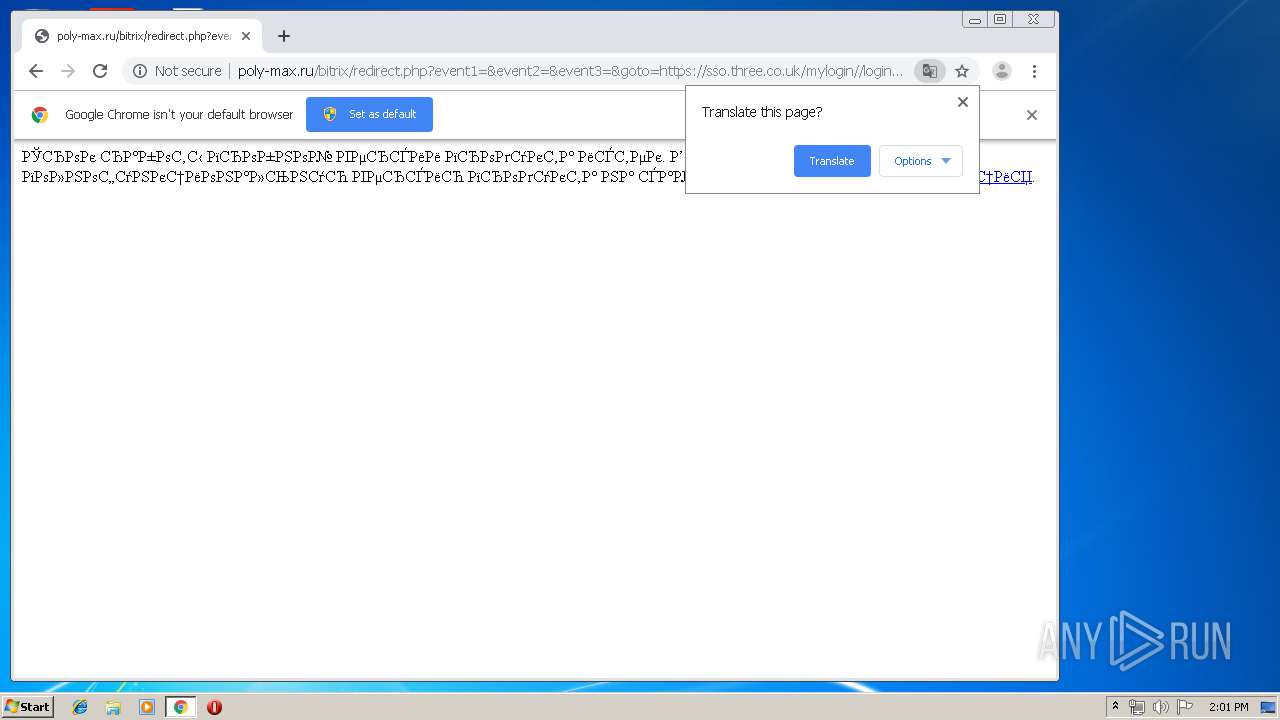
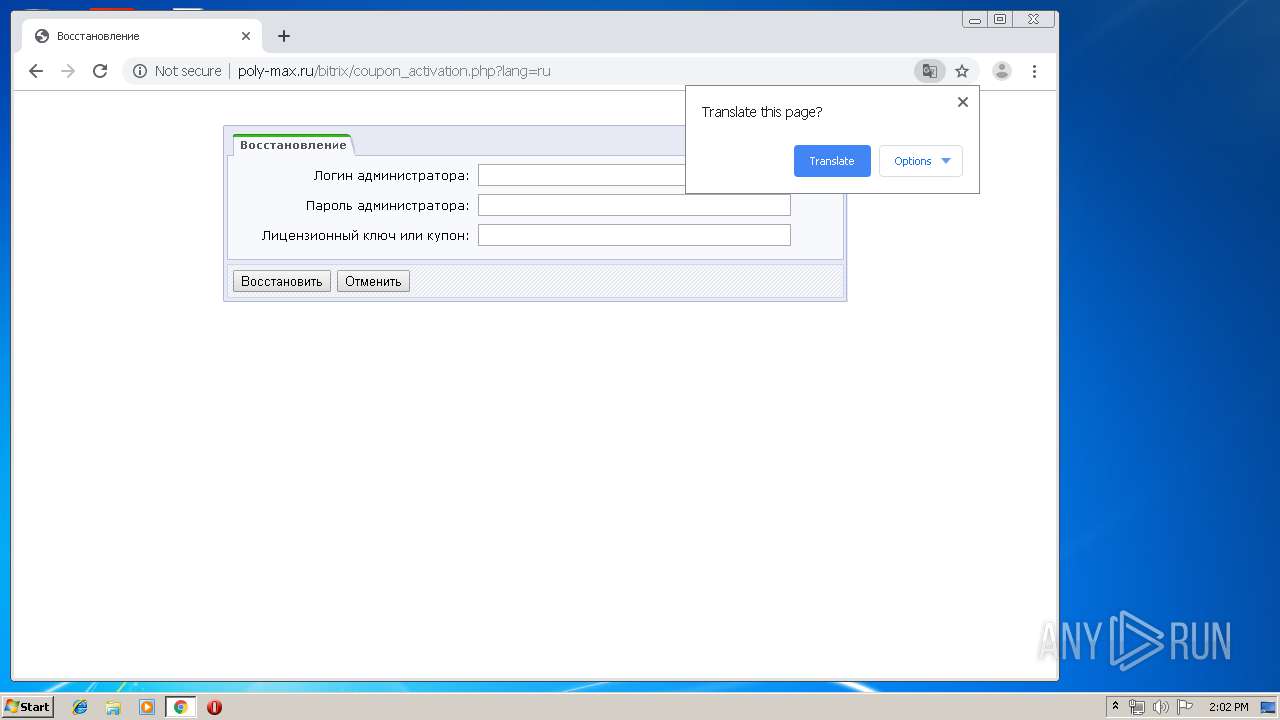
1208 | iexplore.exe | GET | 200 | 87.236.16.29:80 | http://poly-max.ru/bitrix/coupon_activation.php?lang=ru | RU | html | 773 b | suspicious |
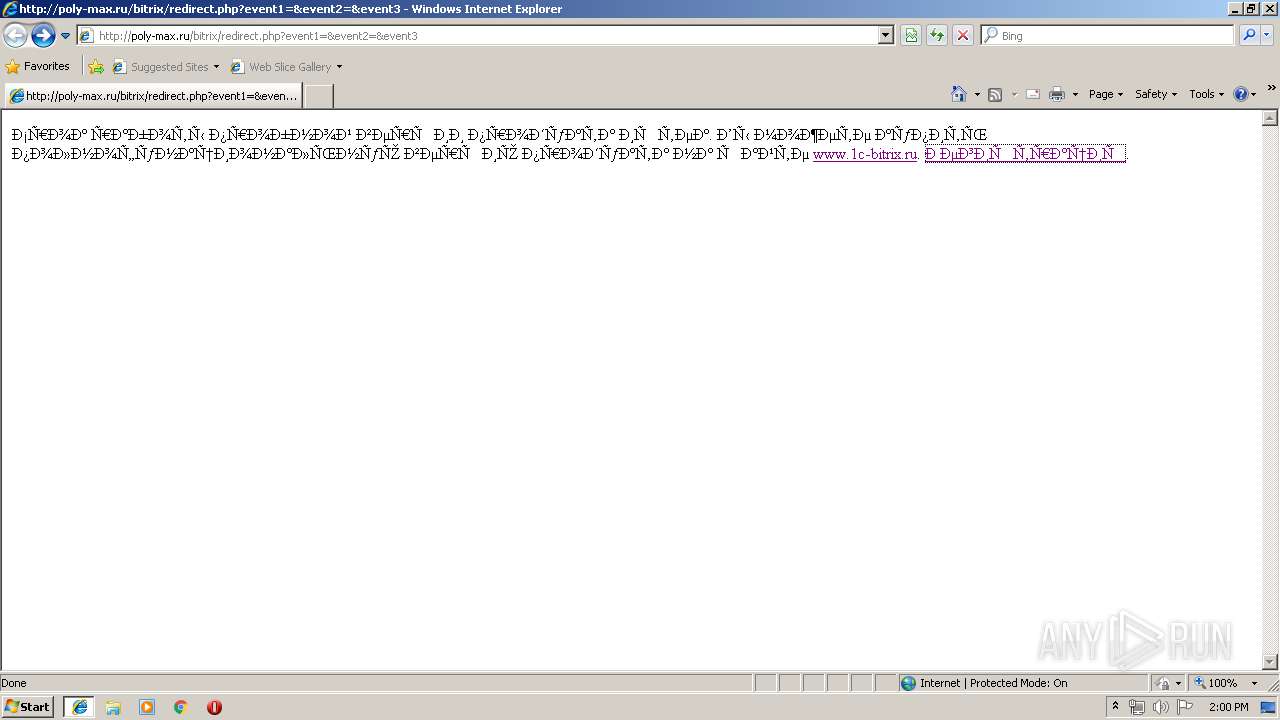
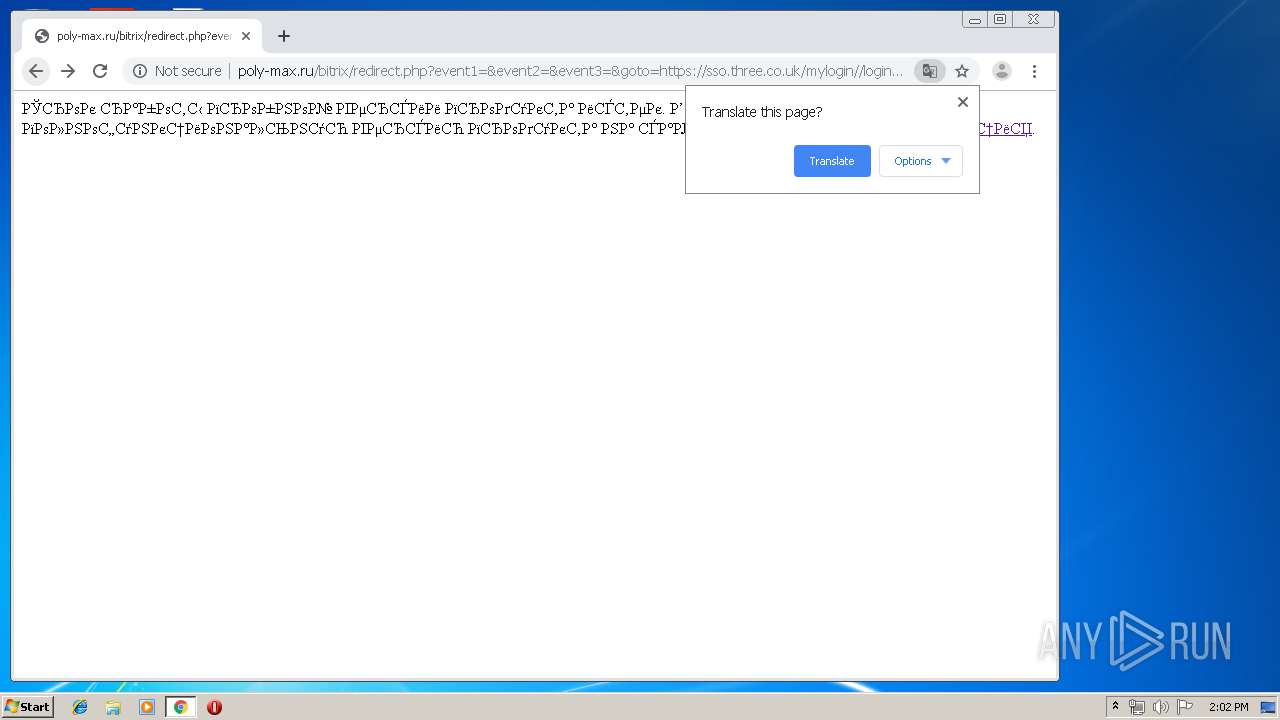
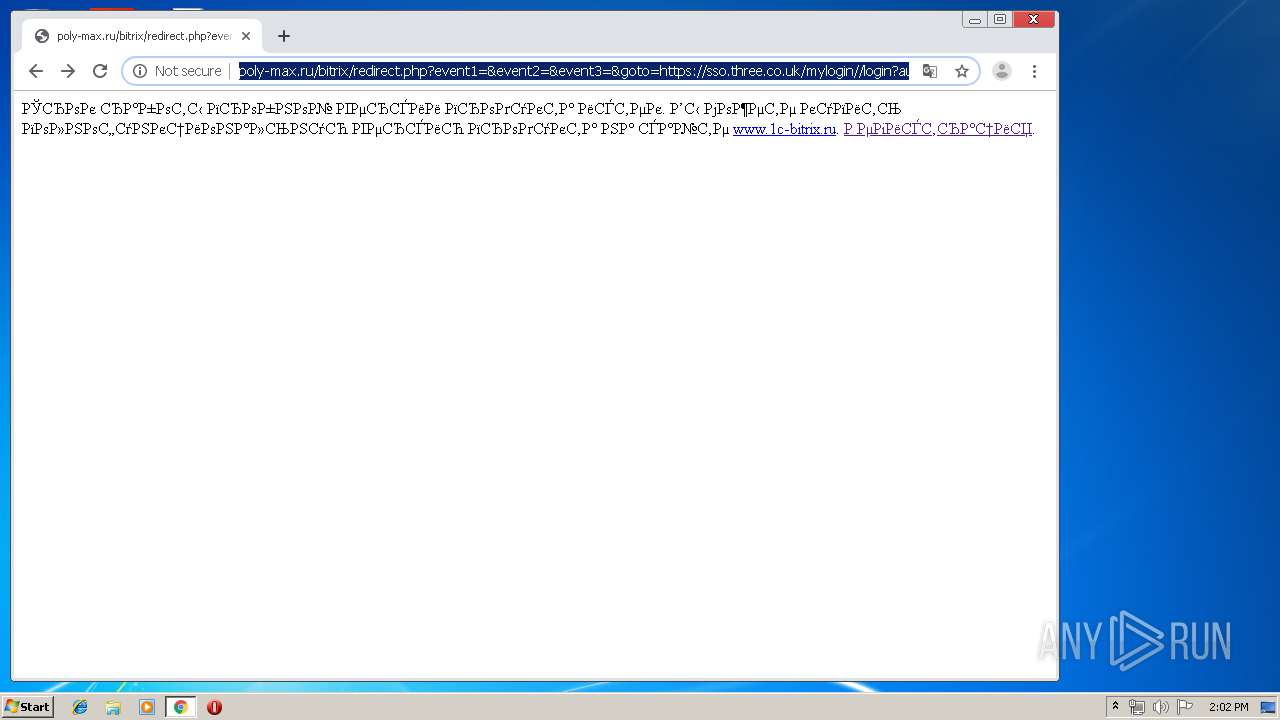
1208 | iexplore.exe | GET | 200 | 87.236.16.29:80 | http://poly-max.ru/bitrix/redirect.php?event1=&event2=&event3 | RU | html | 268 b | suspicious |
3168 | iexplore.exe | GET | 404 | 87.236.16.29:80 | http://poly-max.ru/favicon.ico | RU | html | 355 b | suspicious |
764 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
764 | chrome.exe | GET | 404 | 87.236.16.29:80 | http://poly-max.ru/favicon.ico | RU | html | 355 b | suspicious |
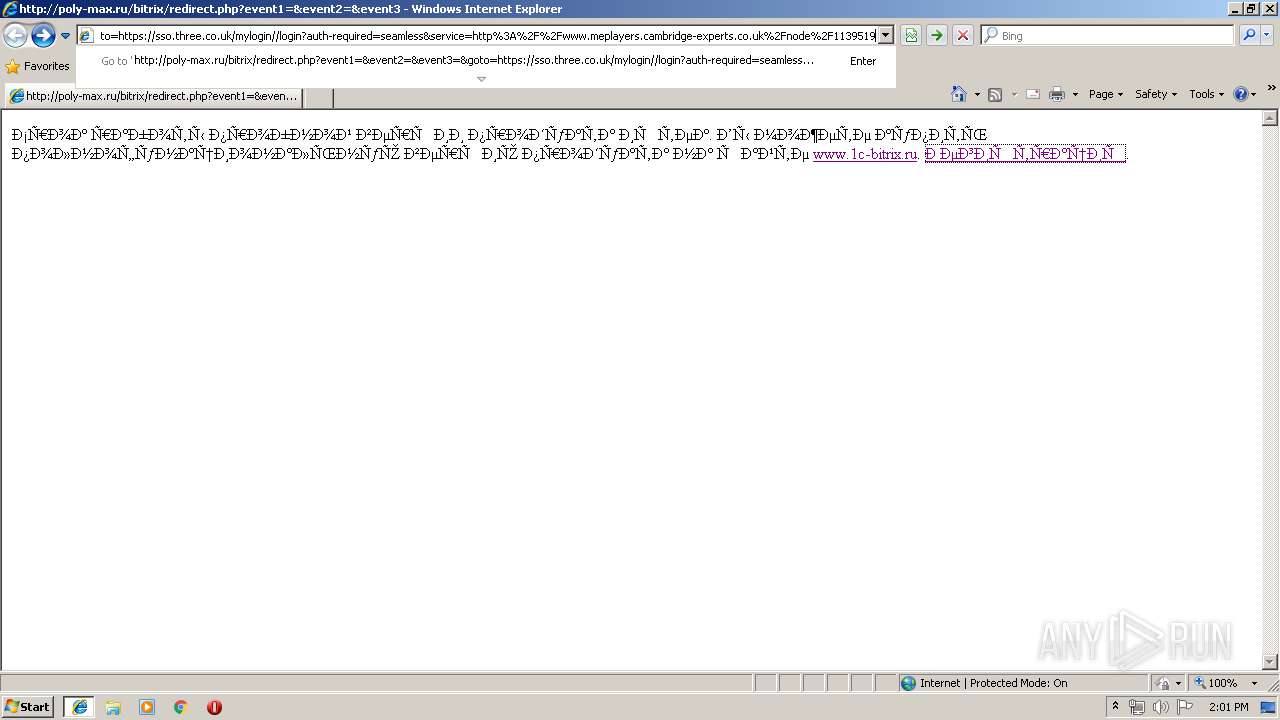
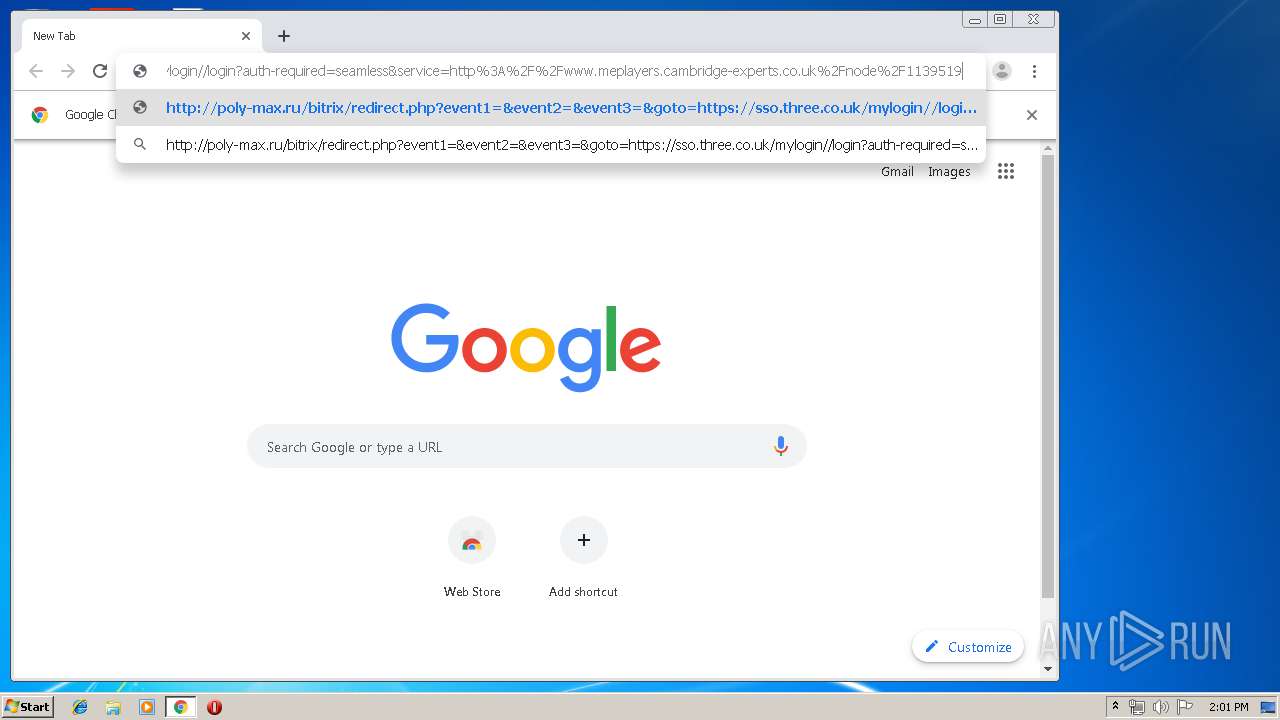
764 | chrome.exe | GET | 200 | 87.236.16.29:80 | http://poly-max.ru/bitrix/redirect.php?event1=&event2=&event3=&goto=https://sso.three.co.uk/mylogin//login?auth-required=seamless&service=http%3A%2F%2Fwww.meplayers.cambridge-experts.co.uk%2Fnode%2F1139519 | RU | html | 268 b | suspicious |
1208 | iexplore.exe | GET | 200 | 87.236.16.29:80 | http://poly-max.ru/bitrix/themes/.default/sysupdate.css | RU | text | 1.06 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3168 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1208 | iexplore.exe | 46.235.53.93:443 | www.1c-bitrix.ru | Amtel-svyaz Zao | RU | unknown |
3168 | iexplore.exe | 87.236.16.29:80 | poly-max.ru | Beget Ltd | RU | suspicious |
1208 | iexplore.exe | 46.235.53.93:80 | www.1c-bitrix.ru | Amtel-svyaz Zao | RU | unknown |
1208 | iexplore.exe | 93.186.225.197:443 | vk.com | VKontakte Ltd | RU | unknown |
1208 | iexplore.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
1208 | iexplore.exe | 5.254.23.206:443 | opt-99999999.ssl.1c-bitrix-cdn.ru | — | RO | unknown |
1208 | iexplore.exe | 172.217.21.206:443 | www.youtube.com | Google Inc. | US | whitelisted |
1208 | iexplore.exe | 172.217.22.8:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
1208 | iexplore.exe | 216.58.207.46:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
poly-max.ru |
| unknown |
www.bing.com |
| whitelisted |
www.1c-bitrix.ru |
| suspicious |
connect.facebook.net |
| whitelisted |
vk.com |
| whitelisted |
opt-99999999.ssl.1c-bitrix-cdn.ru |
| suspicious |
www.youtube.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
bitrix.info |
| whitelisted |
s.ytimg.com |
| whitelisted |