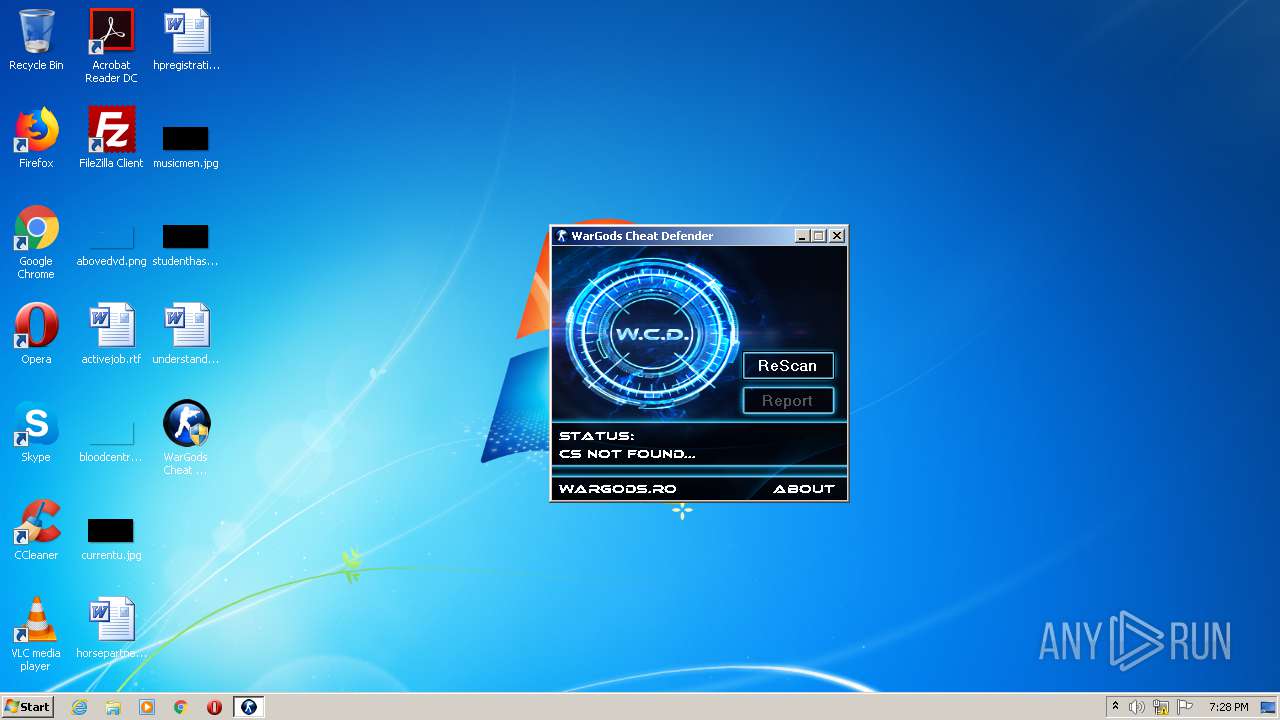
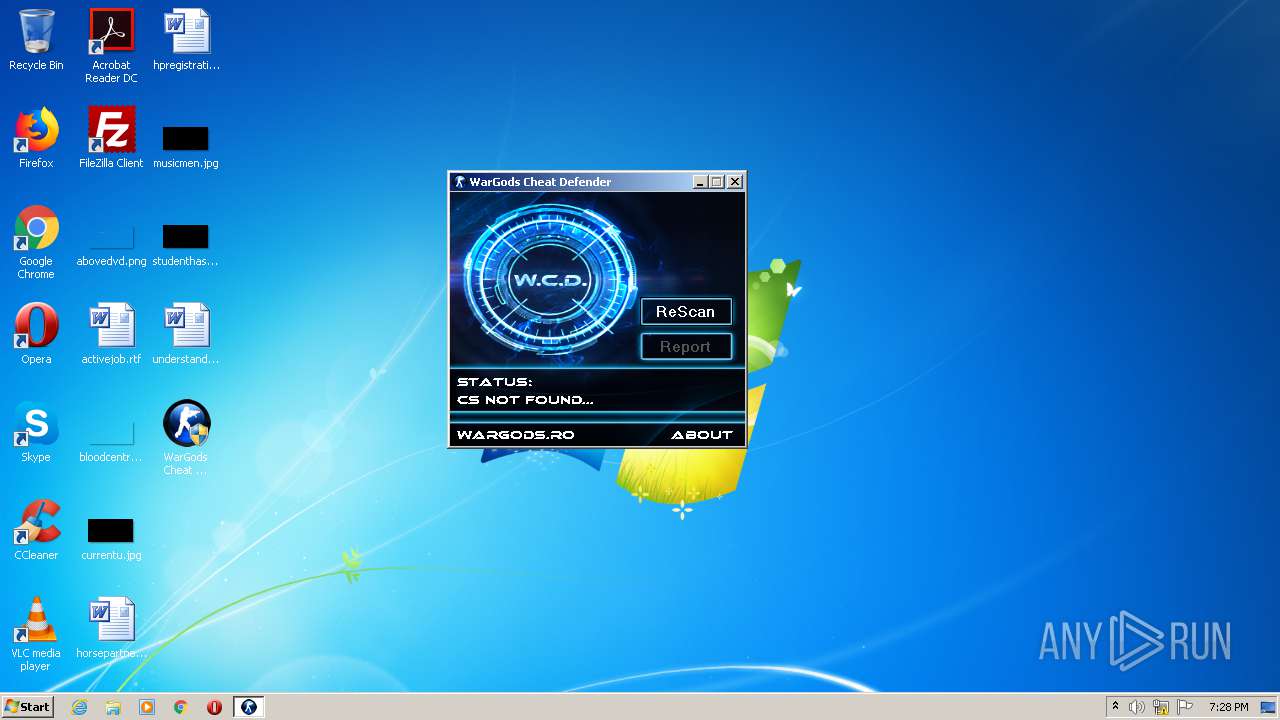
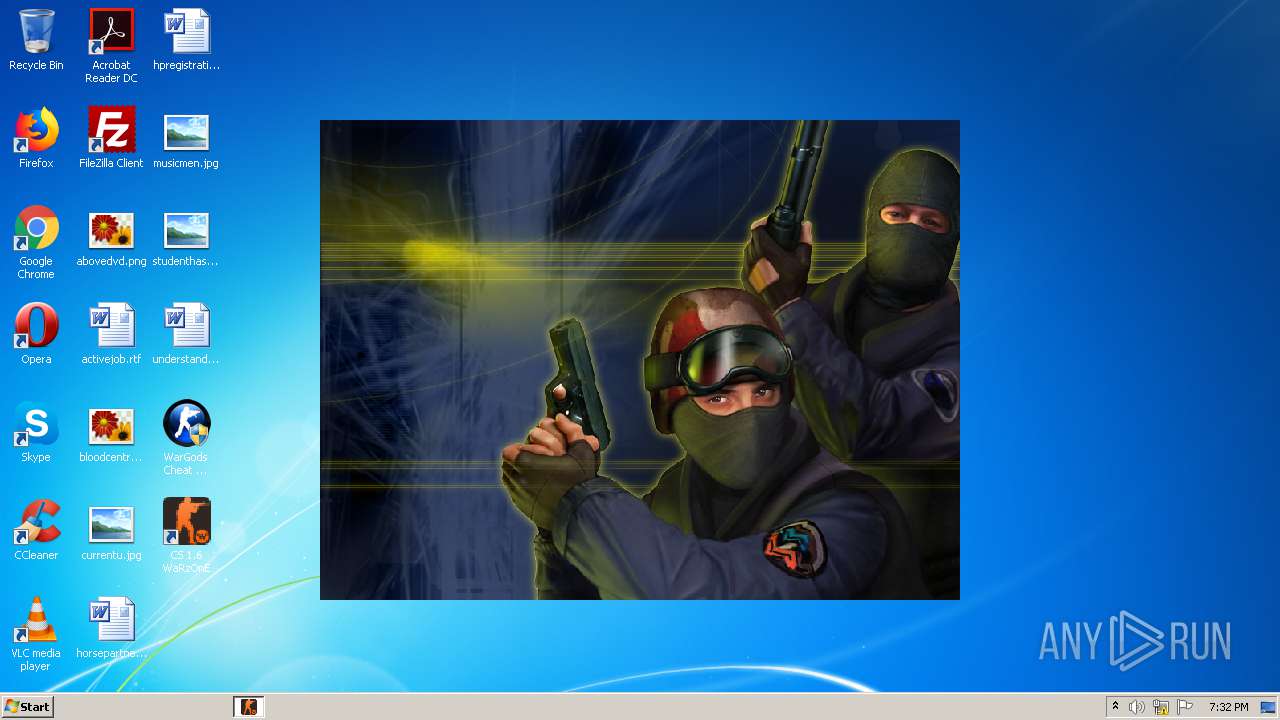
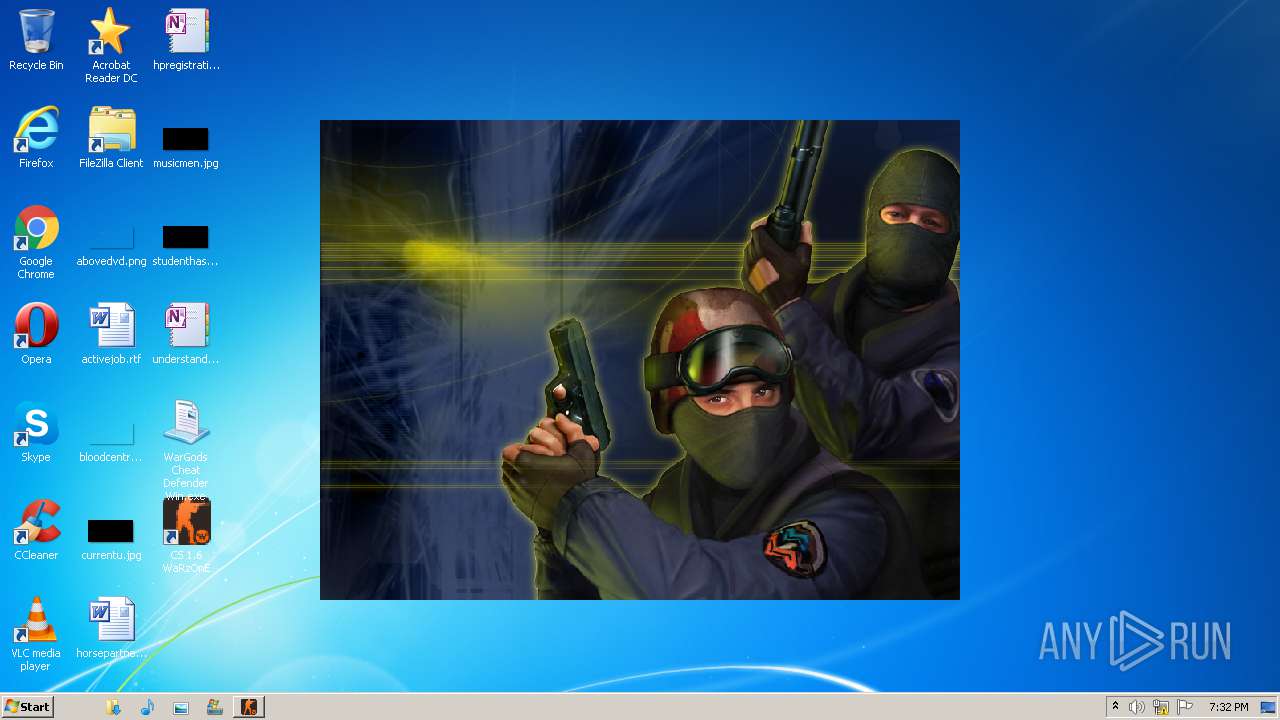
| File name: | WarGods Cheat Defender Win.exe |
| Full analysis: | https://app.any.run/tasks/c1b31190-b894-4b8f-a97c-89b35048f55f |
| Verdict: | Malicious activity |
| Analysis date: | July 15, 2020, 18:28:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 39BDC55A9E26E6EAE4FA2B46CF79D79F |
| SHA1: | 19132AA7801A6C841AF2E0DE9BBB61339CDA46DD |
| SHA256: | 78BC50BBD753CB431221E4D2C5F67177C18611C0AFCC83438F2A14C70AA0B9F2 |
| SSDEEP: | 24576:RNqJDH6M7Wveswi6ulT+zG2JRKykrRy4jYt7oDCs:3qZaMmP/lTGG2YrRJjoz |
MALICIOUS
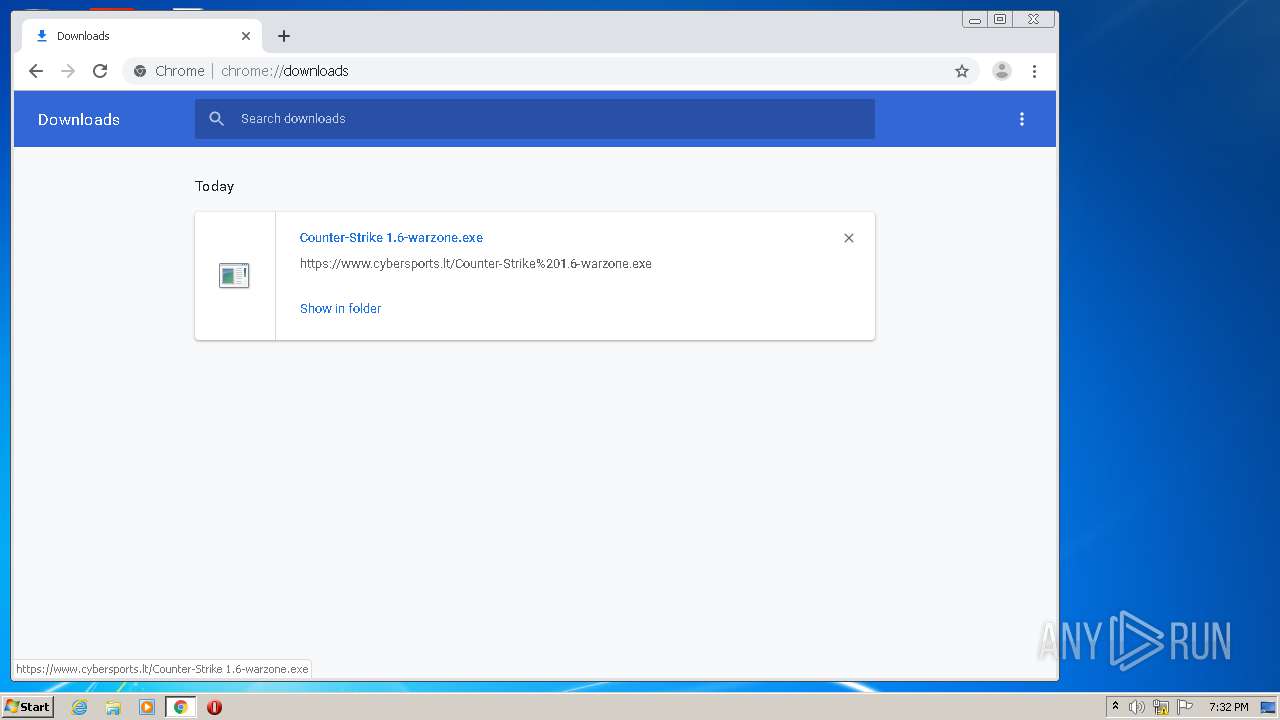
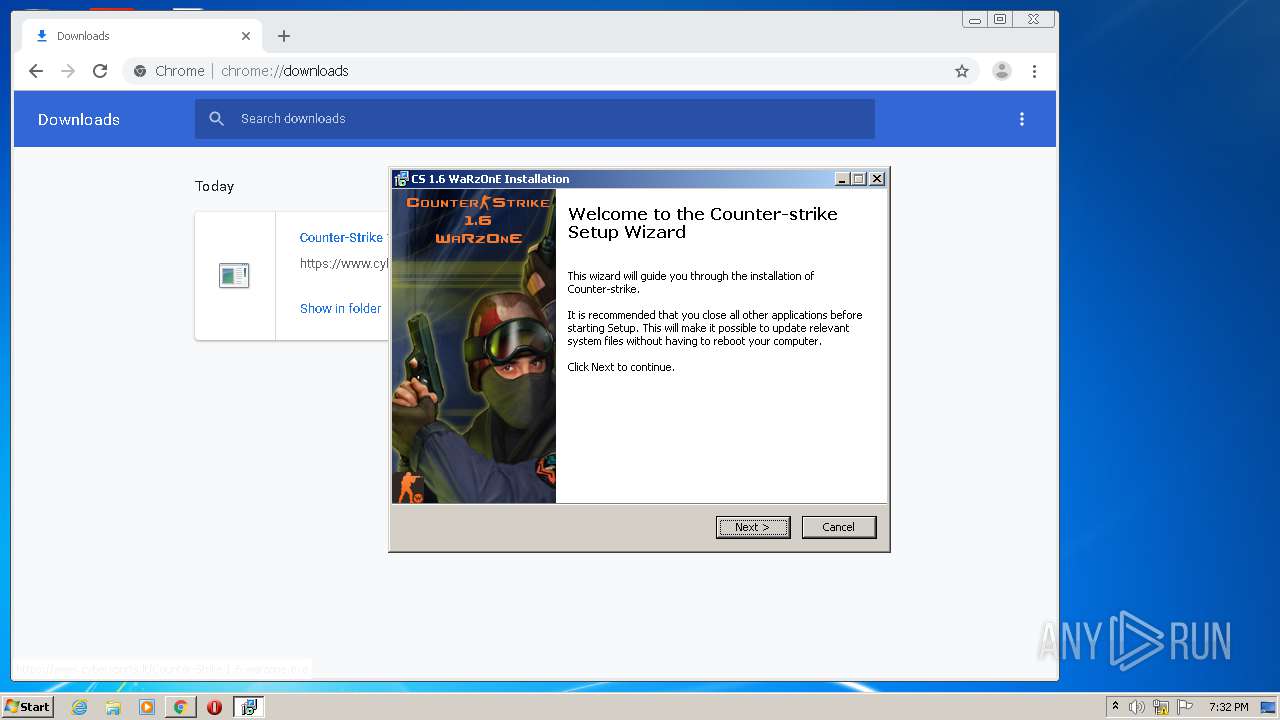
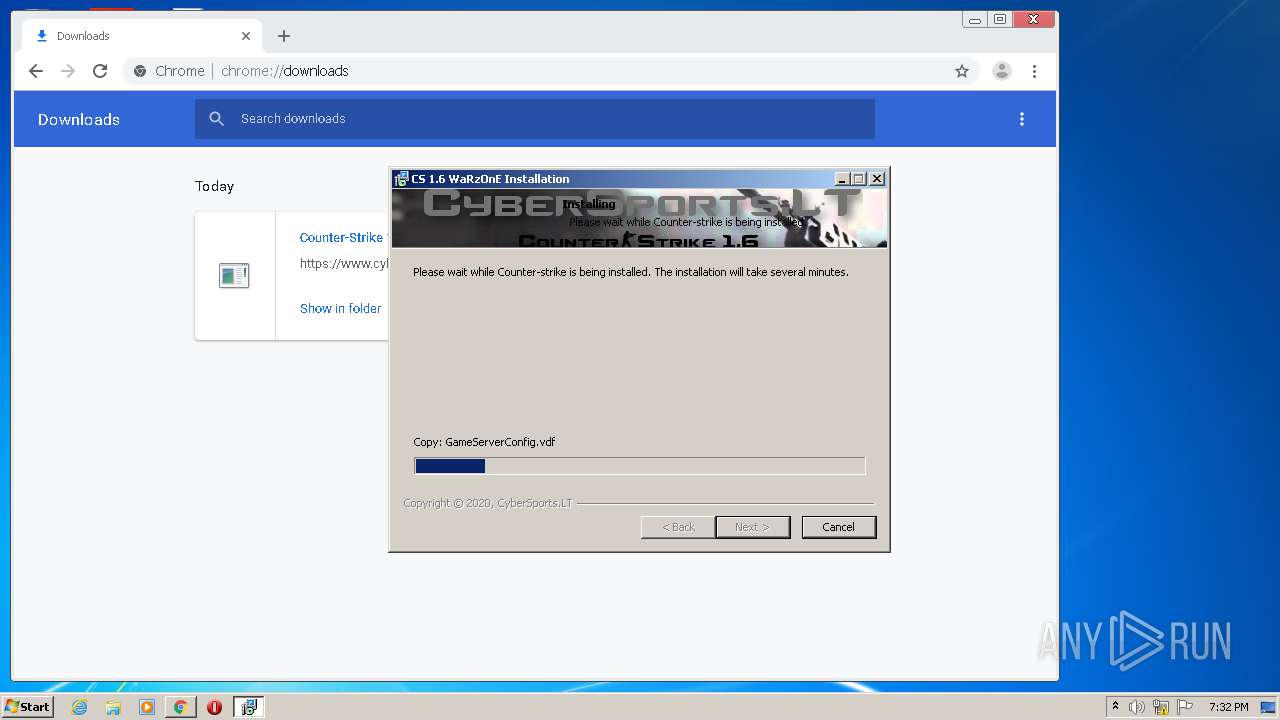
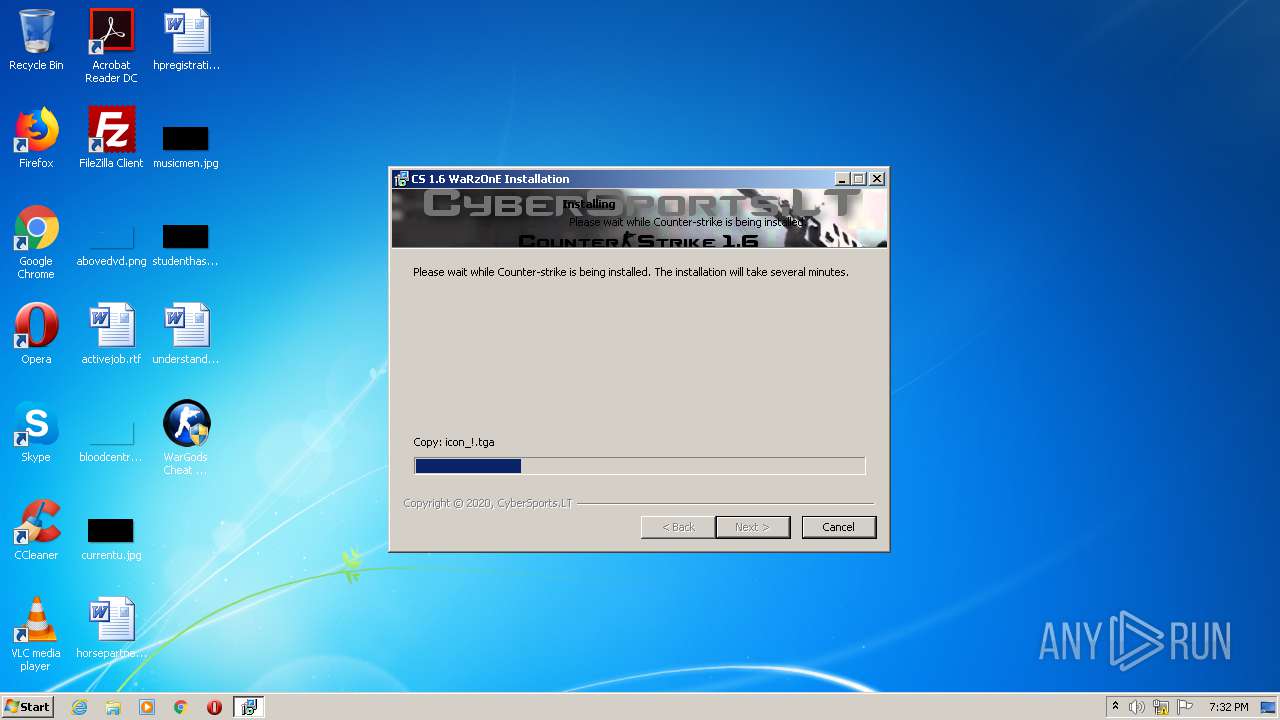
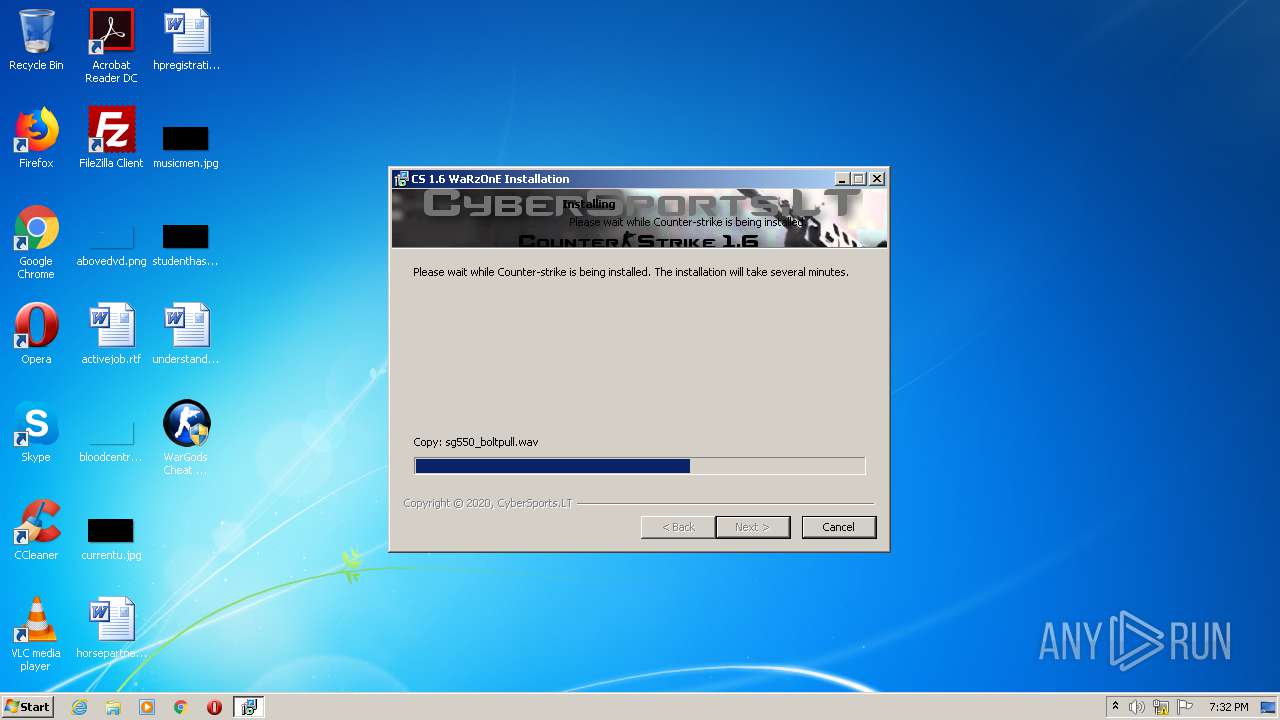
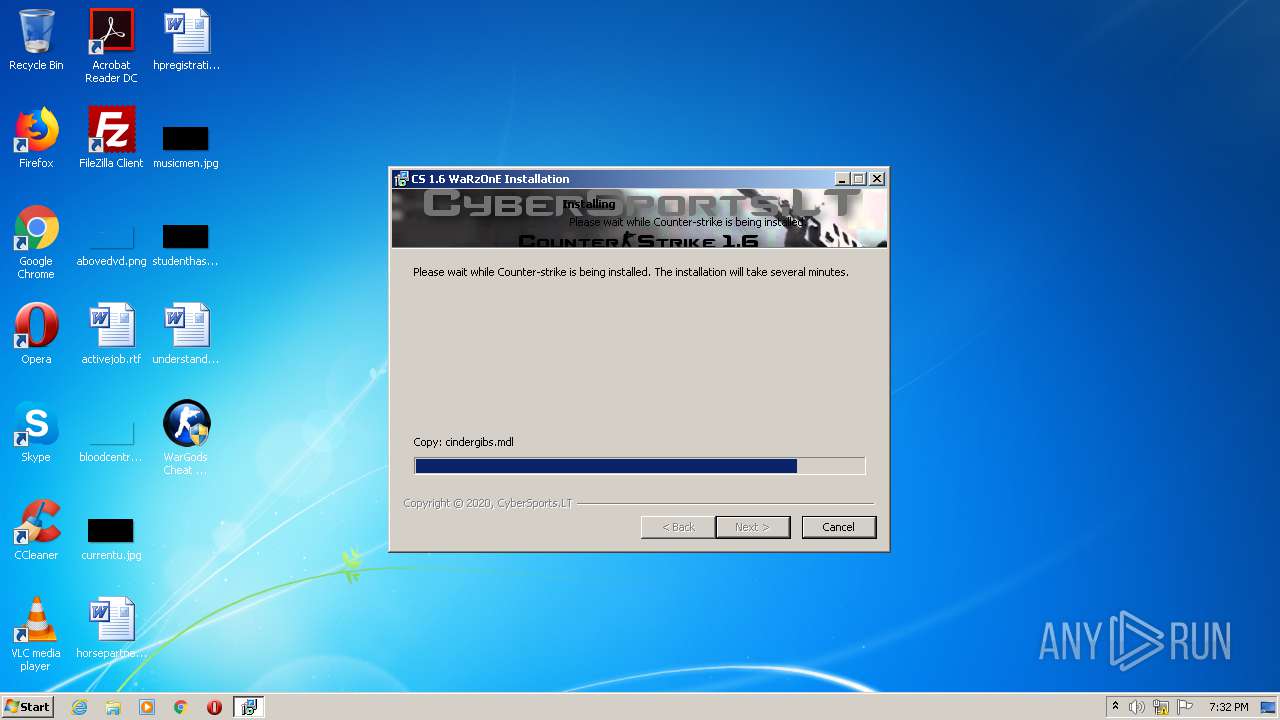
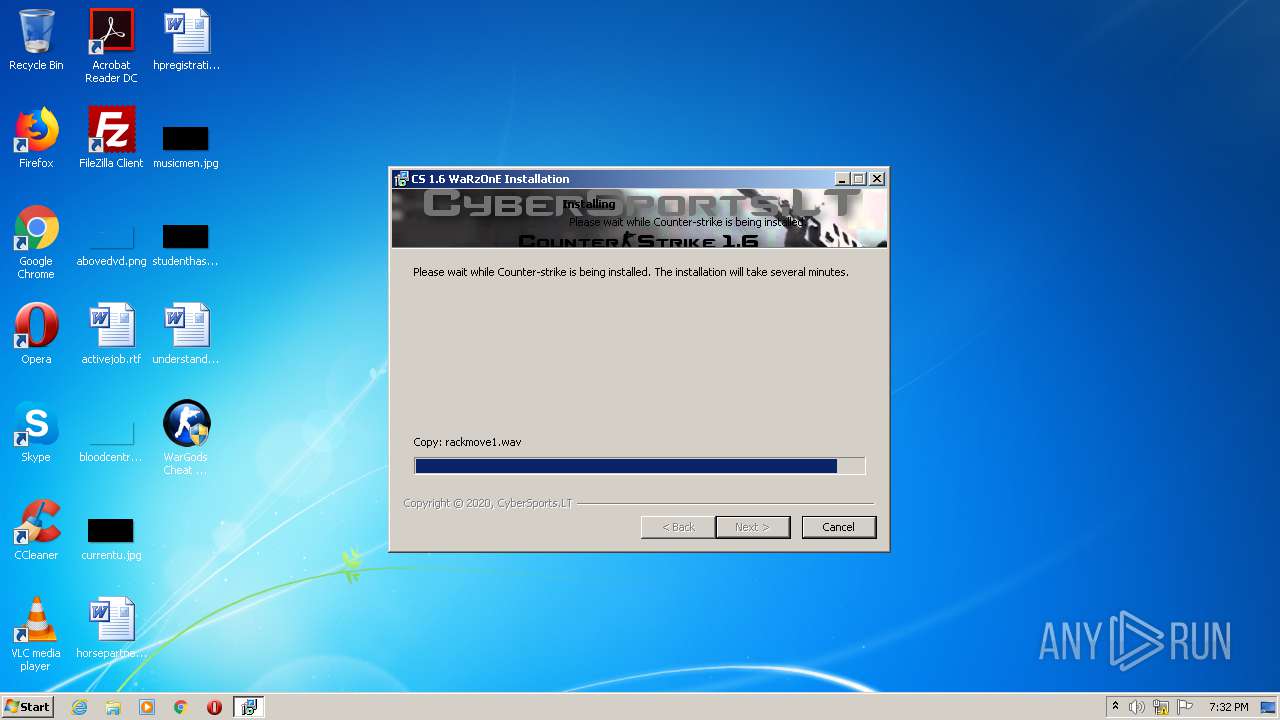
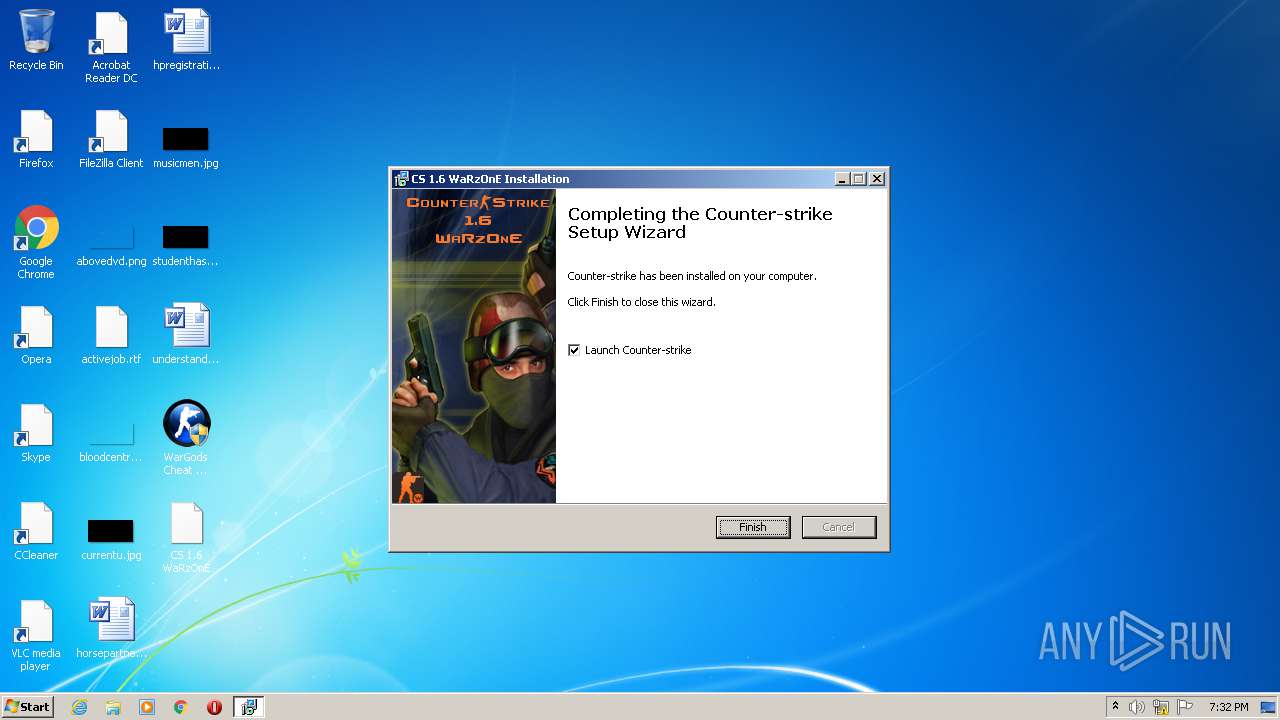
Application was dropped or rewritten from another process
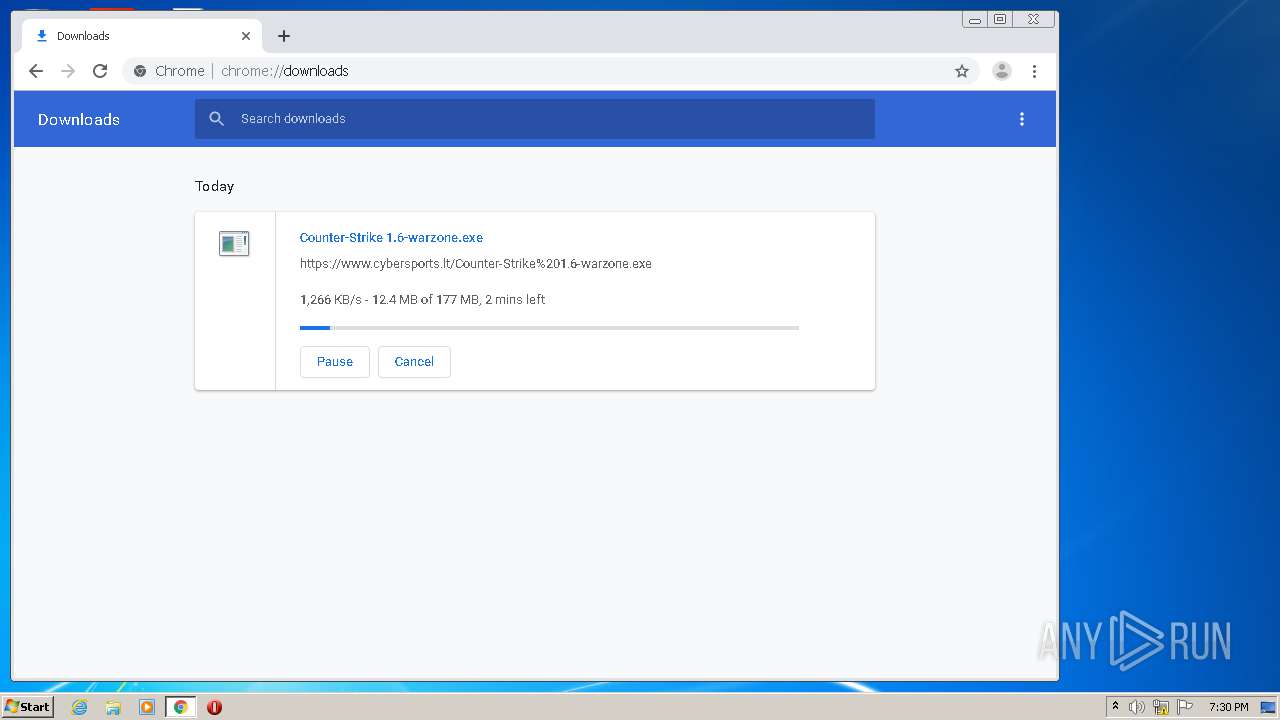
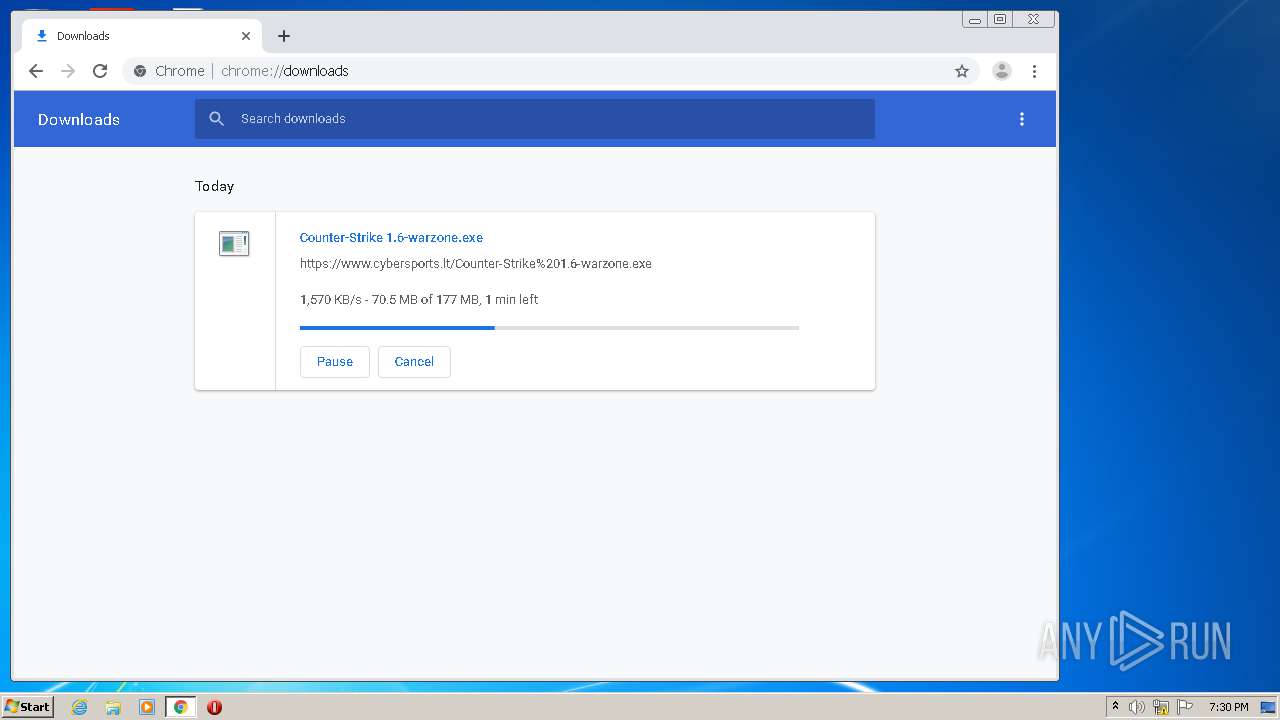
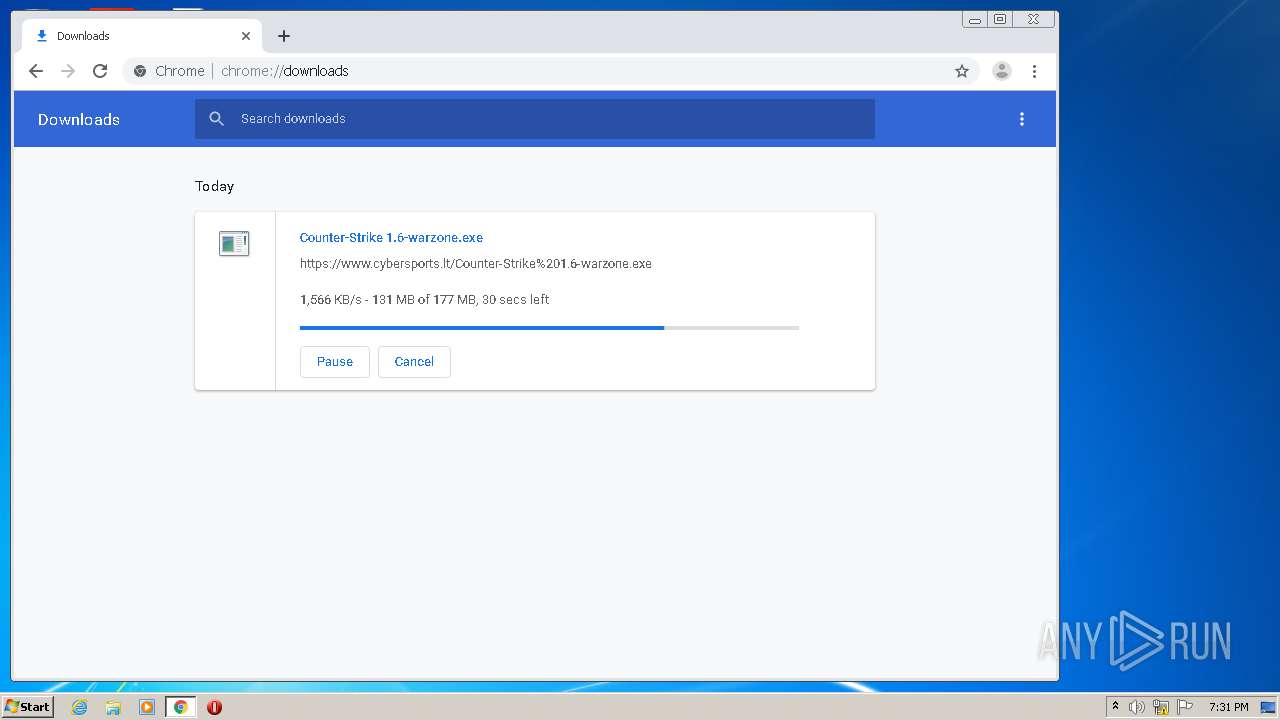
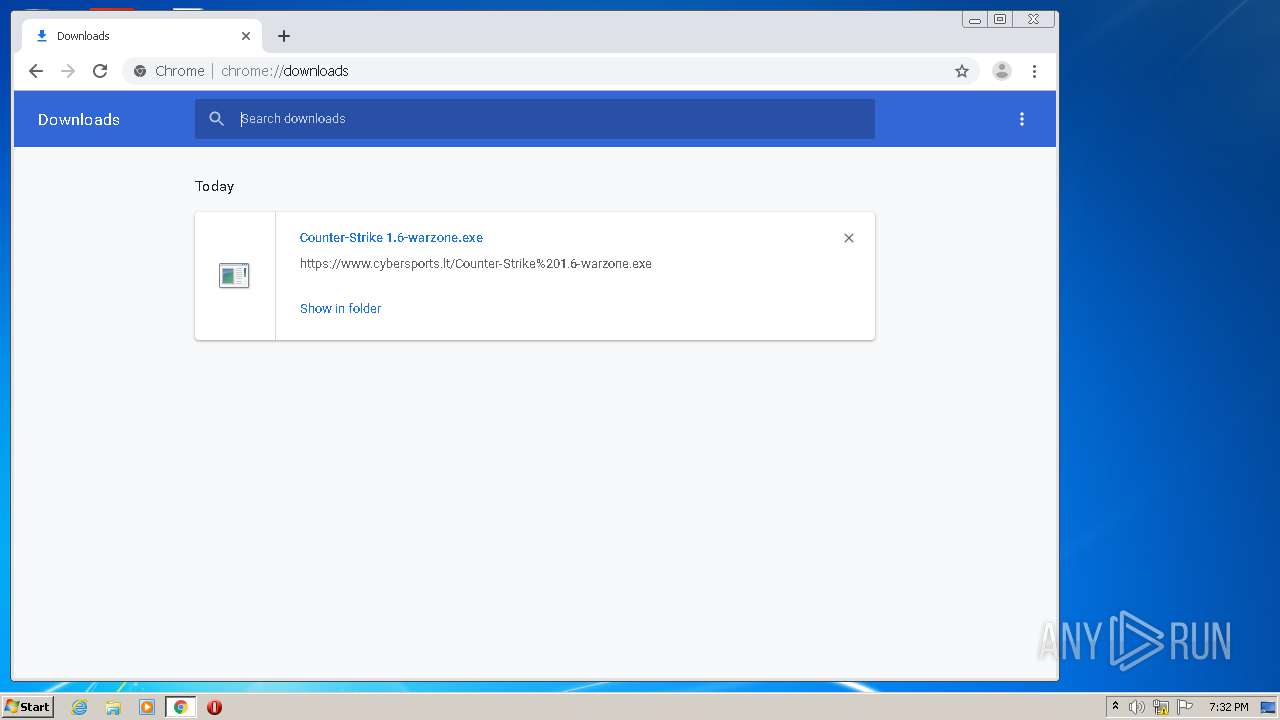
- Counter-Strike 1.6-warzone.exe (PID: 960)
- Counter-Strike 1.6-warzone.exe (PID: 3224)
- hl.exe (PID: 2516)
Loads dropped or rewritten executable
- cmd.exe (PID: 3736)
- hl.exe (PID: 2516)
- svchost.exe (PID: 864)
SUSPICIOUS
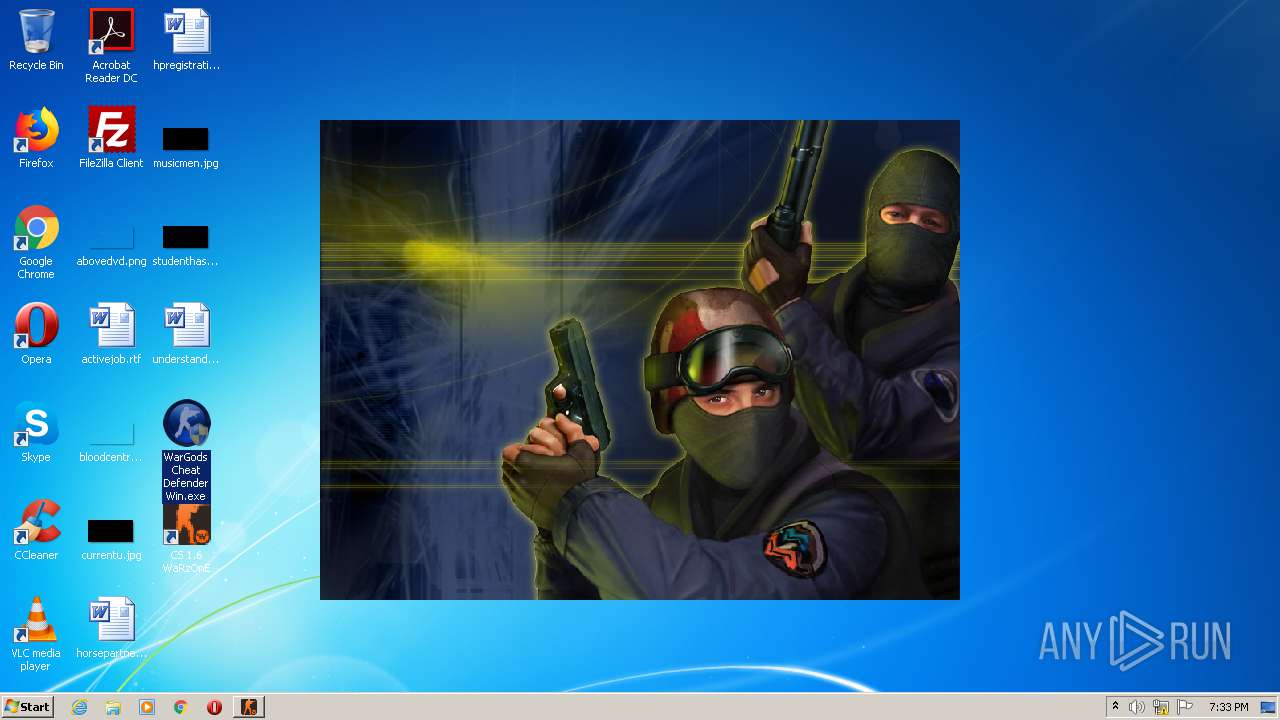
Application launched itself
- WarGods Cheat Defender Win.exe (PID: 1868)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3720)
Executable content was dropped or overwritten
- chrome.exe (PID: 3720)
- Counter-Strike 1.6-warzone.exe (PID: 3224)
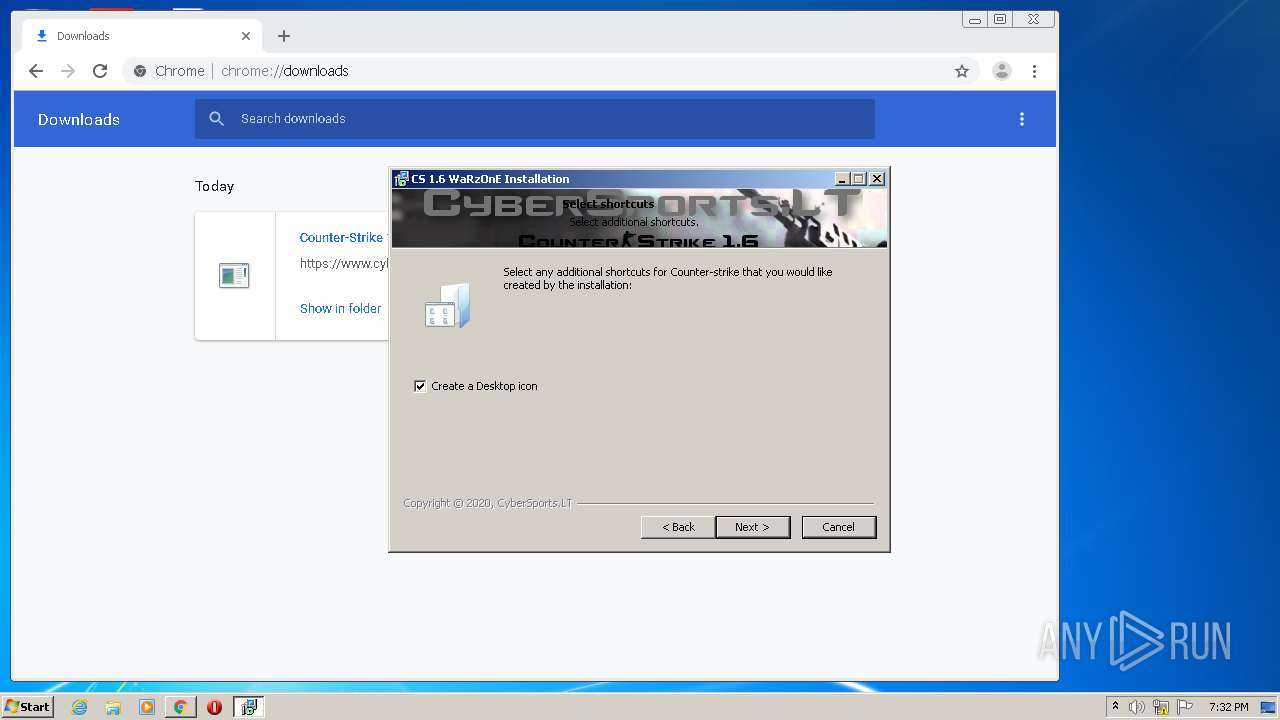
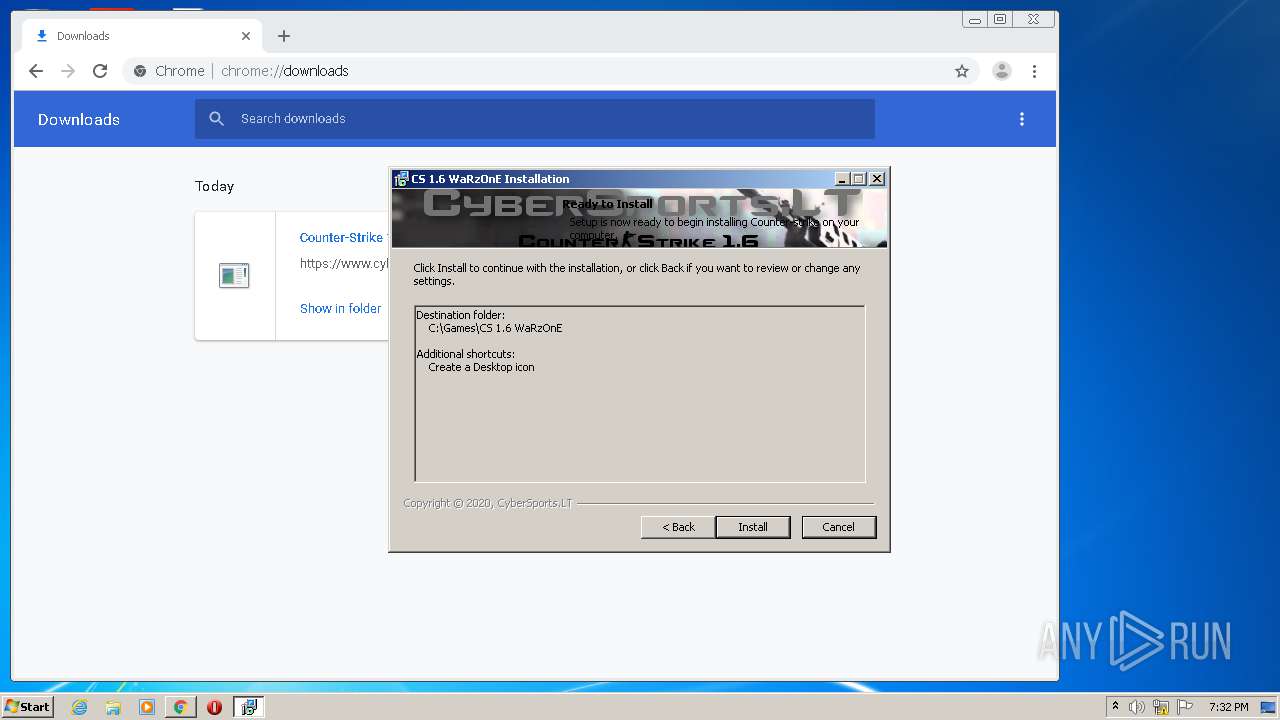
Creates a software uninstall entry
- Counter-Strike 1.6-warzone.exe (PID: 3224)
Low-level read access rights to disk partition
- hl.exe (PID: 2516)
Starts CMD.EXE for commands execution
- Counter-Strike 1.6-warzone.exe (PID: 3224)
INFO
Reads the hosts file
- chrome.exe (PID: 3720)
- chrome.exe (PID: 3020)
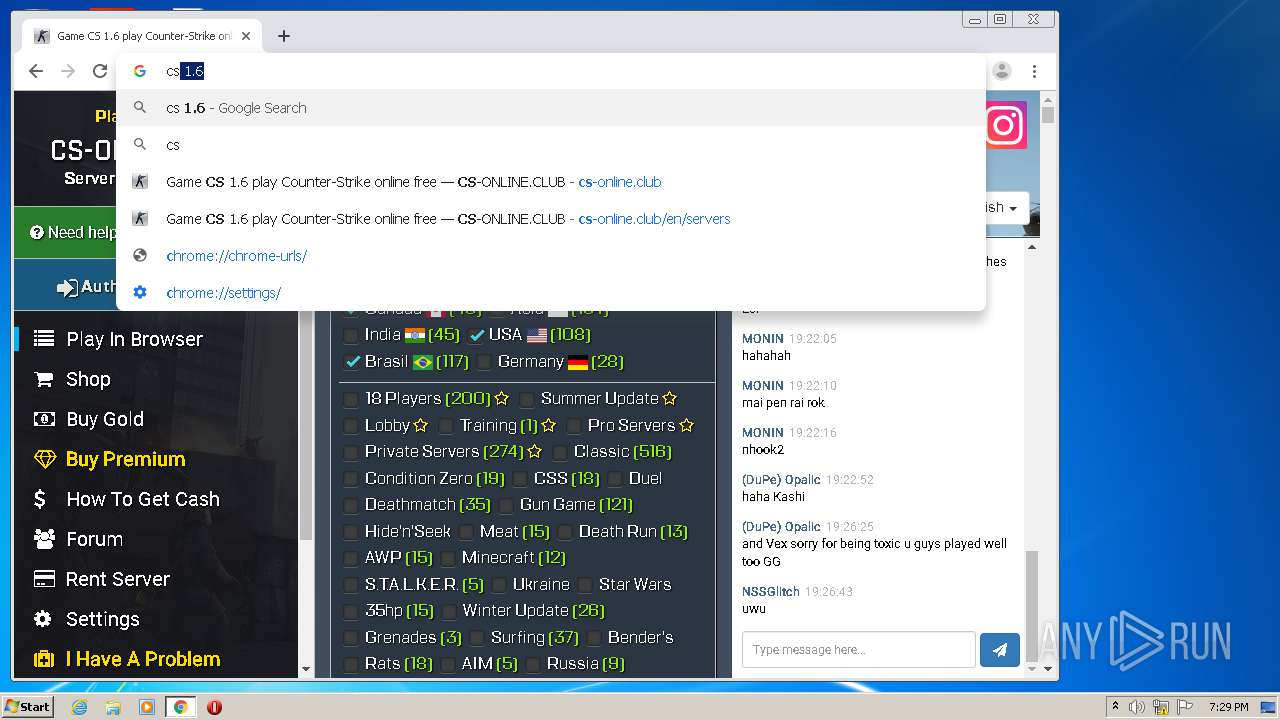
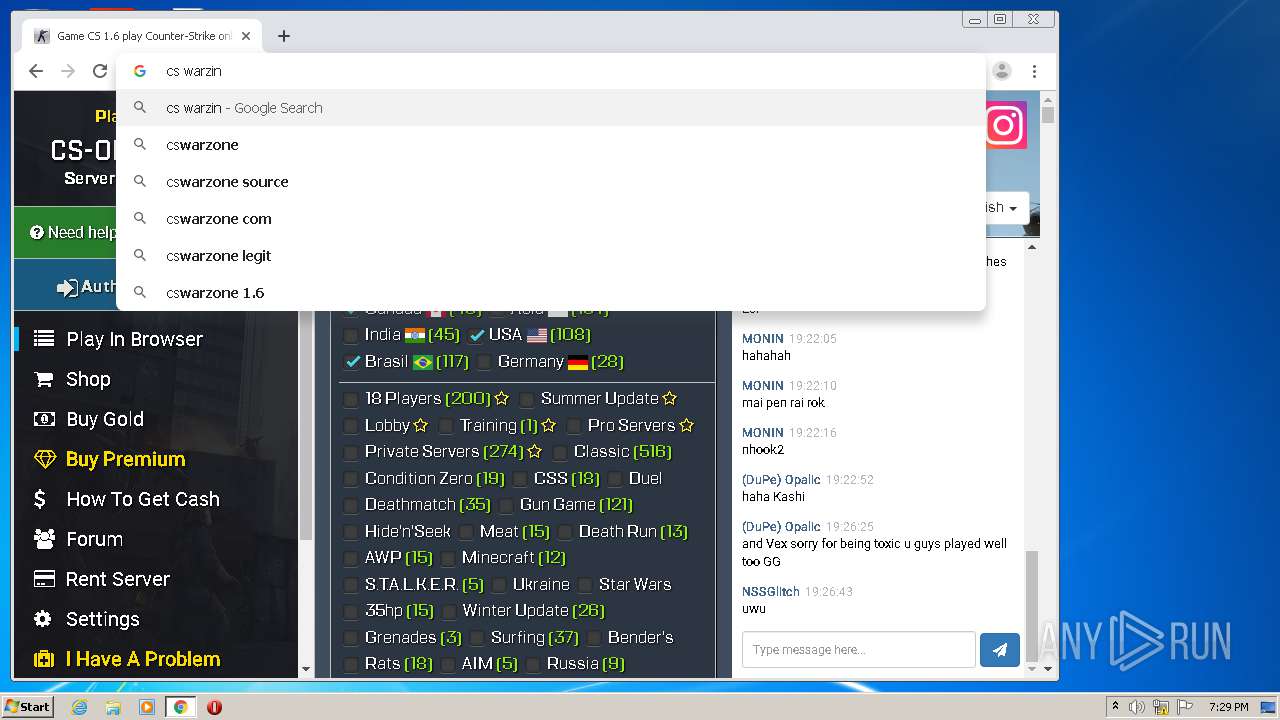
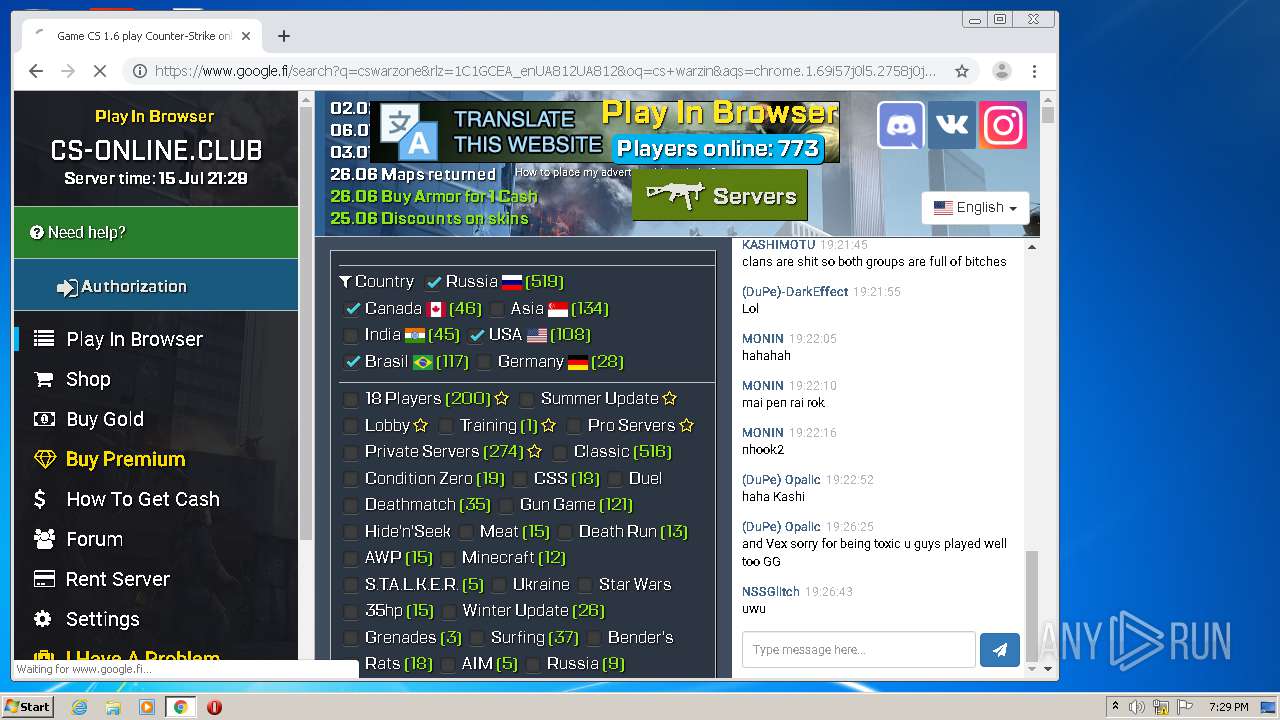
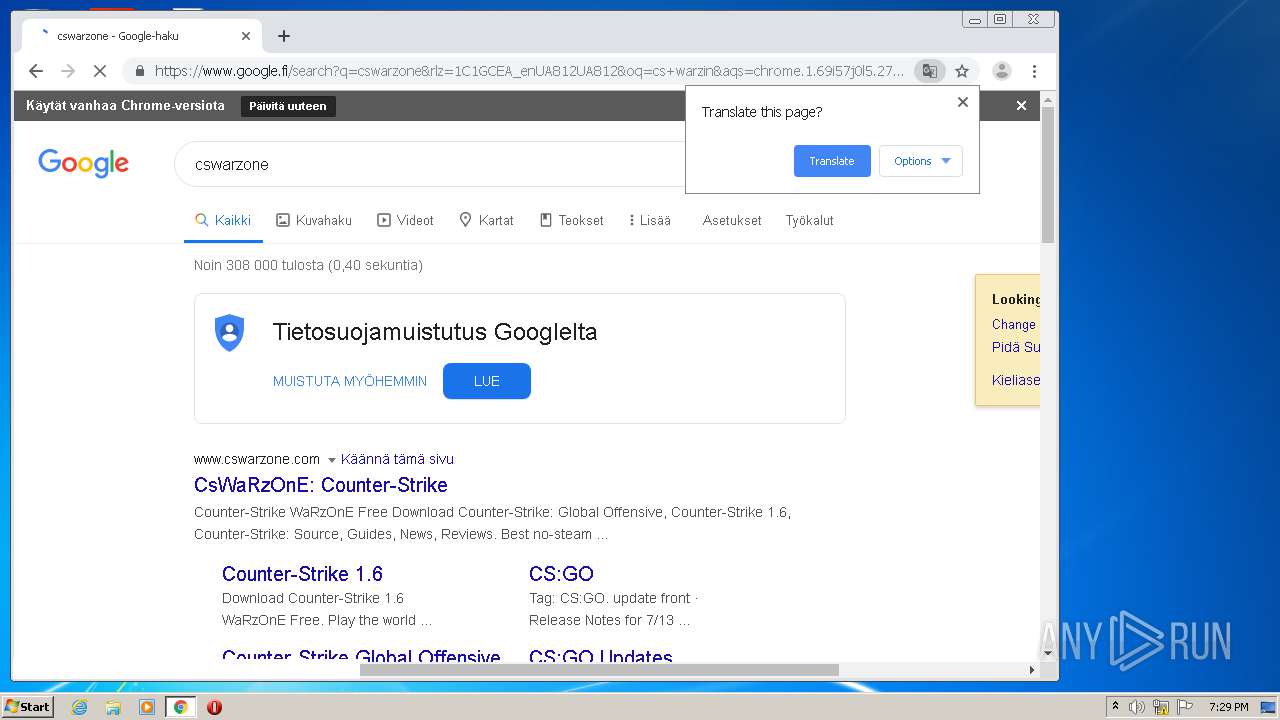
Manual execution by user
- chrome.exe (PID: 3720)
- WarGods Cheat Defender Win.exe (PID: 2348)
- WarGods Cheat Defender Win.exe (PID: 2508)
- WarGods Cheat Defender Win.exe (PID: 2912)
- WarGods Cheat Defender Win.exe (PID: 3000)
Reads Internet Cache Settings
- chrome.exe (PID: 3720)
Application launched itself
- chrome.exe (PID: 3720)
Reads settings of System Certificates
- chrome.exe (PID: 3020)
Dropped object may contain Bitcoin addresses
- Counter-Strike 1.6-warzone.exe (PID: 3224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:06:08 16:32:12+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 822784 |
| InitializedDataSize: | 736256 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x18408a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.4.0.4 |
| ProductVersionNumber: | 2.4.0.4 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
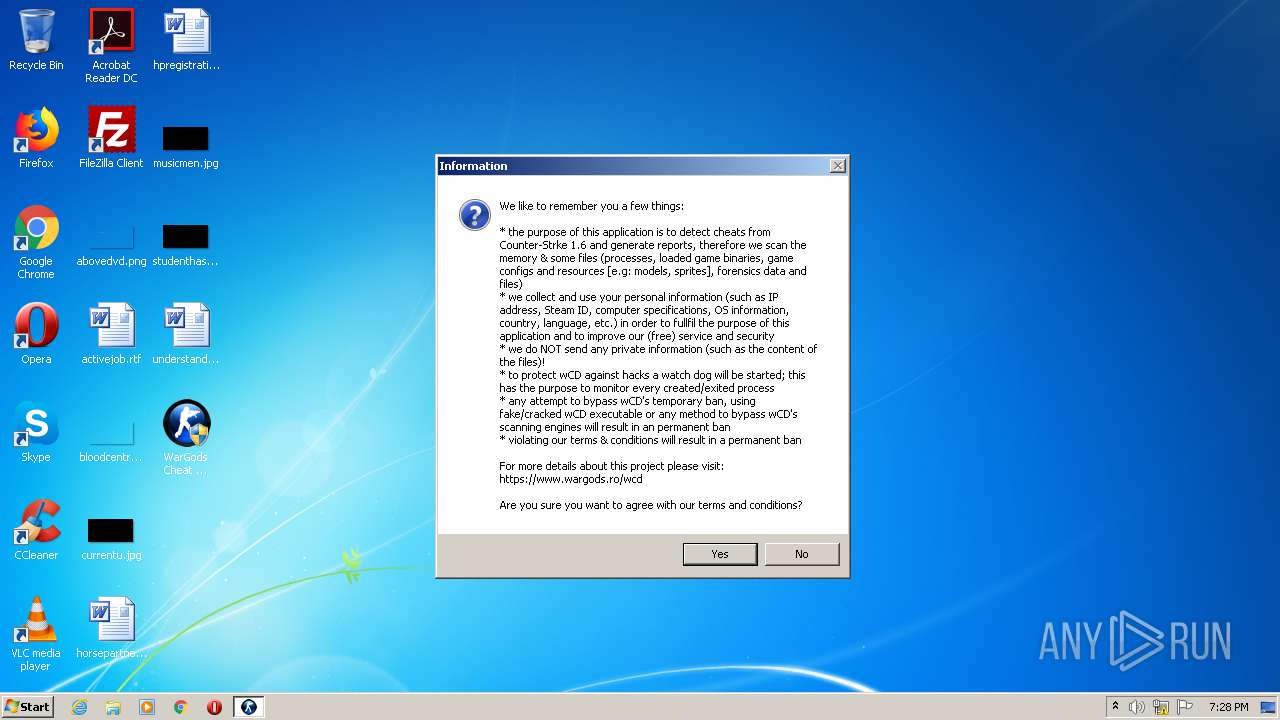
| Comments: | WarGods Cheat Defender |
| CompanyName: | WarGods.ro |
| FileDescription: | WarGods Cheat Defender |
| FileVersion: | 2.4.0.4 |
| InternalName: | WarGods Cheat Defender.exe |
| LegalCopyright: | Tiger @ wGods |
| LegalTrademarks: | www.wargods.ro |
| OriginalFileName: | WarGods Cheat Defender.exe |
| ProductName: | WarGods Cheat Defender |
| ProductVersion: | 2.4.0.4 |
| AssemblyVersion: | 2.4.0.4 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Jun-2020 14:32:12 |
| Comments: | WarGods Cheat Defender |
| CompanyName: | WarGods.ro |
| FileDescription: | WarGods Cheat Defender |
| FileVersion: | 2.4.0.4 |
| InternalName: | WarGods Cheat Defender.exe |
| LegalCopyright: | Tiger @ wGods |
| LegalTrademarks: | www.wargods.ro |
| OriginalFilename: | WarGods Cheat Defender.exe |
| ProductName: | WarGods Cheat Defender |
| ProductVersion: | 2.4.0.4 |
| Assembly Version: | 2.4.0.4 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 08-Jun-2020 14:32:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
yq\x0c0\x127\x1ca4\xcc\x0a | 0x00002000 | 0x000ACC34 | 0x000ACE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99974 |
.text | 0x000B0000 | 0x000C8AE8 | 0x000C8C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.46674 |
.rsrc | 0x0017A000 | 0x00006A08 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.08482 |
.reloc | 0x00182000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
0x00184000 | 0x00000090 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 2.57363 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.99431 | 3132 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.33071 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.71938 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 5.89247 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 6.0358 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.82464 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.69913 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
115
Monitored processes
63
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,15802629037190457333,10054335425654353853,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1726701171129576625 --mojo-platform-channel-handle=2612 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 864 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 900 | "C:\Users\admin\Desktop\WarGods Cheat Defender Win.exe" | C:\Users\admin\Desktop\WarGods Cheat Defender Win.exe | — | WarGods Cheat Defender Win.exe | |||||||||||
User: admin Company: WarGods.ro Integrity Level: HIGH Description: WarGods Cheat Defender Exit code: 0 Version: 2.4.0.4 Modules
| |||||||||||||||
| 900 | "C:\Users\admin\Desktop\WarGods Cheat Defender Win.exe" | C:\Users\admin\Desktop\WarGods Cheat Defender Win.exe | — | explorer.exe | |||||||||||
User: admin Company: WarGods.ro Integrity Level: MEDIUM Description: WarGods Cheat Defender Exit code: 3221226540 Version: 2.4.0.4 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,15802629037190457333,10054335425654353853,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1637682454873115880 --mojo-platform-channel-handle=3972 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
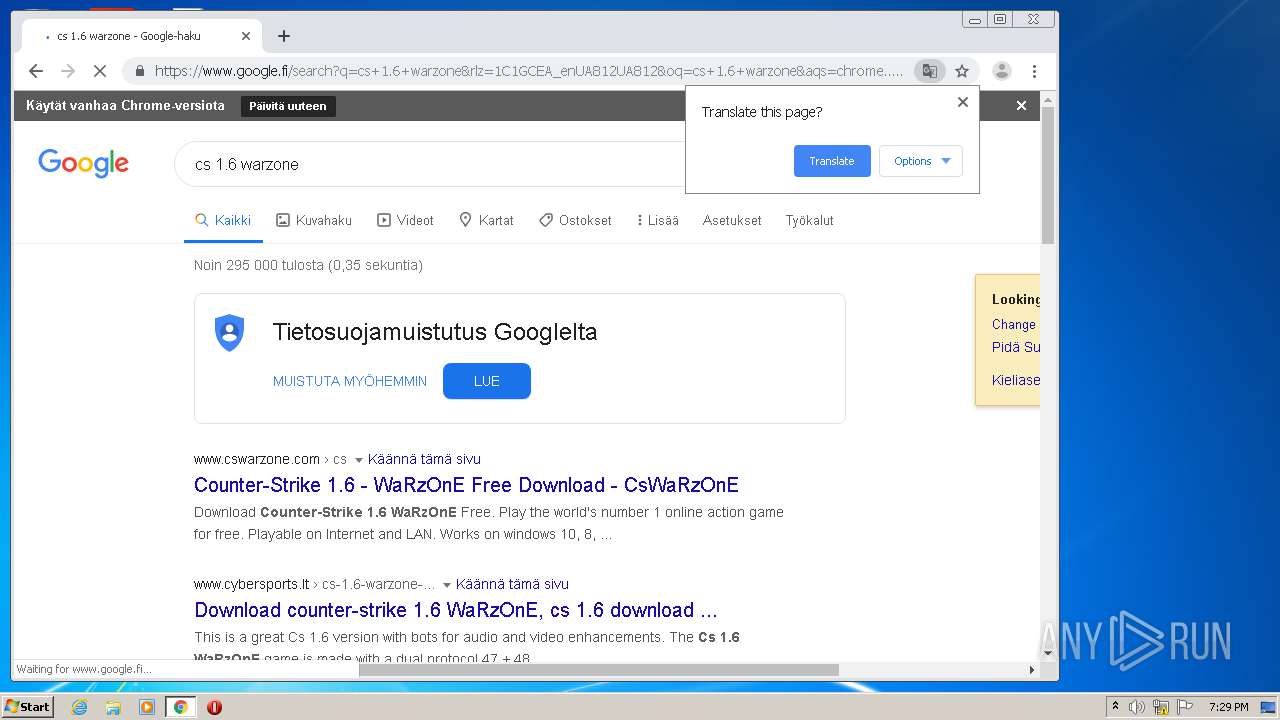
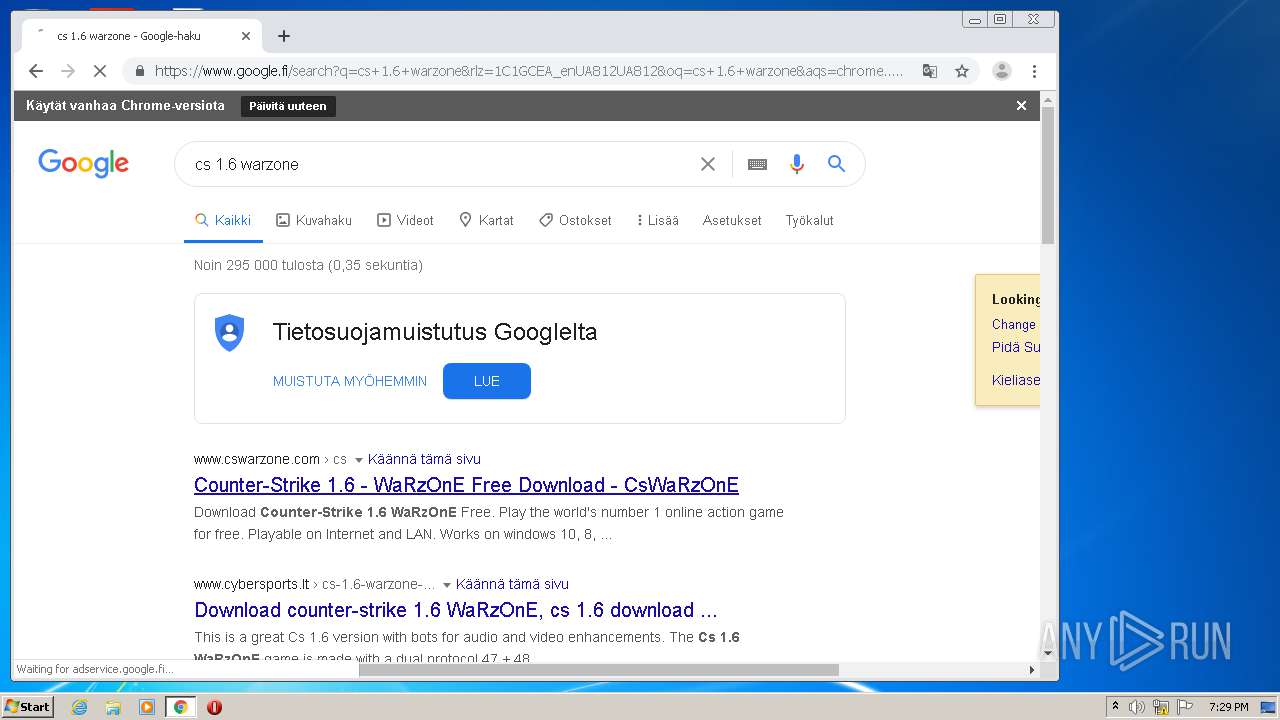
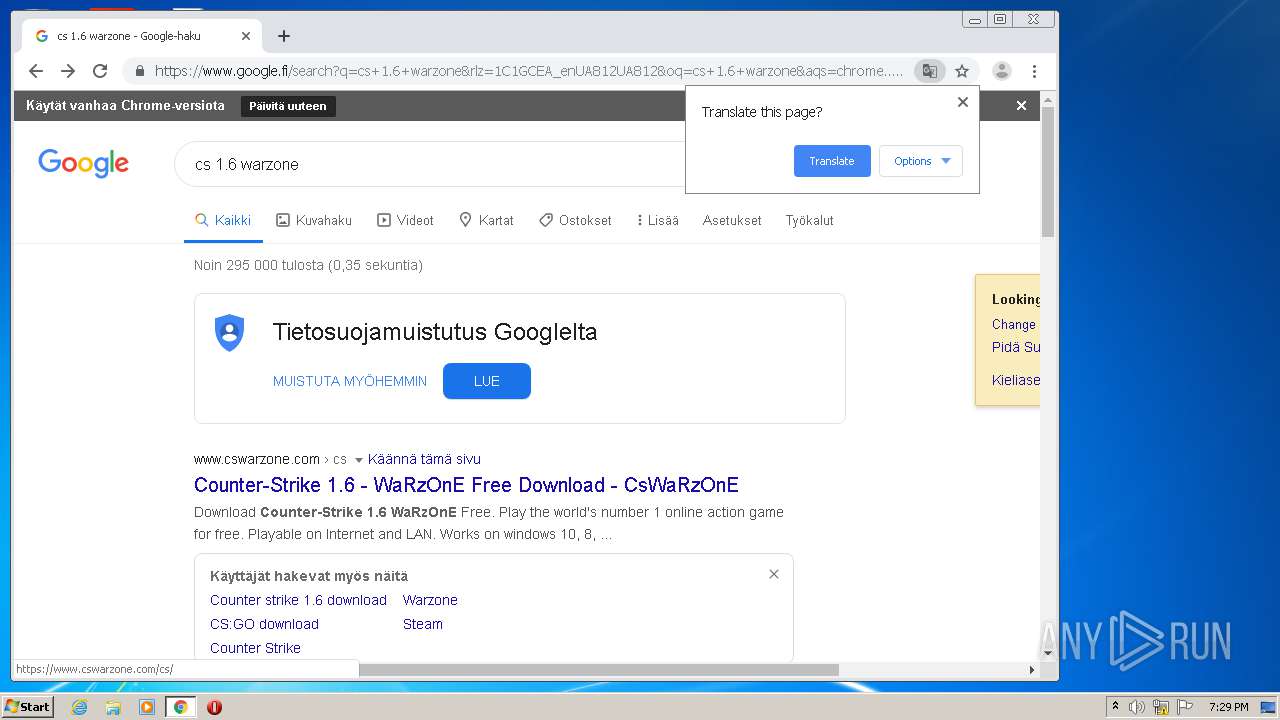
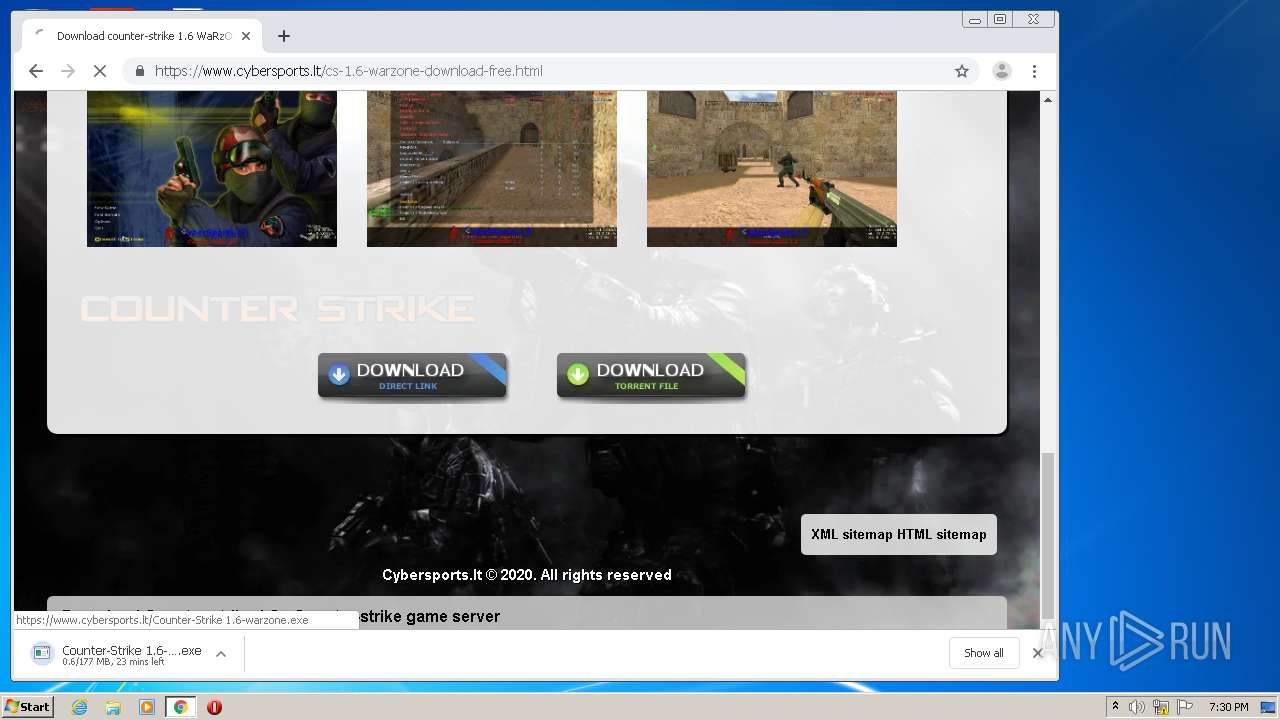
| 960 | "C:\Users\admin\Downloads\Counter-Strike 1.6-warzone.exe" | C:\Users\admin\Downloads\Counter-Strike 1.6-warzone.exe | — | chrome.exe | |||||||||||
User: admin Company: Valve (CyberSports WaRzOnE) Integrity Level: MEDIUM Description: Counter-strike 1.6 Installation Exit code: 3221226540 Version: 1.6 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,15802629037190457333,10054335425654353853,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8466151038694913698 --mojo-platform-channel-handle=3796 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,15802629037190457333,10054335425654353853,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14959136318460985612 --mojo-platform-channel-handle=3400 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,15802629037190457333,10054335425654353853,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8300739317988482607 --mojo-platform-channel-handle=2296 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,15802629037190457333,10054335425654353853,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1995907835509348716 --mojo-platform-channel-handle=4720 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 448
Read events
1 248
Write events
195
Delete events
5
Modification events
| (PID) Process: | (1868) WarGods Cheat Defender Win.exe | Key: | HKEY_CURRENT_USER\Software\wCD |
| Operation: | write | Name: | Eula |
Value: 4 | |||
| (PID) Process: | (1868) WarGods Cheat Defender Win.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1868) WarGods Cheat Defender Win.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (900) WarGods Cheat Defender Win.exe | Key: | HKEY_CURRENT_USER\Software\wCD |
| Operation: | write | Name: | ID |
Value: 7008A69E488B4D6DA1F563131F31E44E | |||
| (PID) Process: | (900) WarGods Cheat Defender Win.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\wCD |
| Operation: | write | Name: | DATA |
Value: 1647087396899E7BE42F01A2492D614B704136AAB23652117445AD1135FEB25FE6A7FF1D3ECF40DCED285393792B10BE48054827ABC456FA50D391325ECE59BDE0DDFABF7782C1081EACF8BE6FB45A06 | |||
| (PID) Process: | (864) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 3 | |||
| (PID) Process: | (864) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 2 | |||
| (PID) Process: | (3852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3720-13239311359368125 |
Value: 259 | |||
| (PID) Process: | (3720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
51
Suspicious files
225
Text files
1 566
Unknown types
2 930
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0F4AFF-E88.pma | — | |
MD5:— | SHA256:— | |||
| 3720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\814c4e88-82b4-4ec3-989c-6f927ee76efa.tmp | — | |
MD5:— | SHA256:— | |||
| 3720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF24d10c.TMP | text | |
MD5:— | SHA256:— | |||
| 864 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 3720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF24d0dd.TMP | text | |
MD5:— | SHA256:— | |||
| 3720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF24d14b.TMP | text | |
MD5:— | SHA256:— | |||
| 3720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
119
DNS requests
69
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3020 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNmRlQUFXU0o1UkNFTWx3aGRUUHBsWUJUZw/7819.902.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
3020 | chrome.exe | GET | 304 | 68.232.34.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
3020 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
3020 | chrome.exe | GET | 200 | 68.232.34.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
3020 | chrome.exe | GET | 200 | 173.194.150.204:80 | http://r6---sn-5goeen7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNmRlQUFXU0o1UkNFTWx3aGRUUHBsWUJUZw/7819.902.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=8p&mip=196.244.192.14&mm=28&mn=sn-5goeen7k&ms=nvh&mt=1594837692&mv=m&mvi=6&pl=24&shardbypass=yes | US | crx | 824 Kb | whitelisted |
3020 | chrome.exe | GET | 200 | 173.194.150.219:80 | http://r5---sn-5goeen7r.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=196.244.192.14&mm=28&mn=sn-5goeen7r&ms=nvh&mt=1594837692&mv=m&mvi=5&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3020 | chrome.exe | 172.217.16.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3020 | chrome.exe | 172.217.23.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3020 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3020 | chrome.exe | 172.217.18.110:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
3020 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
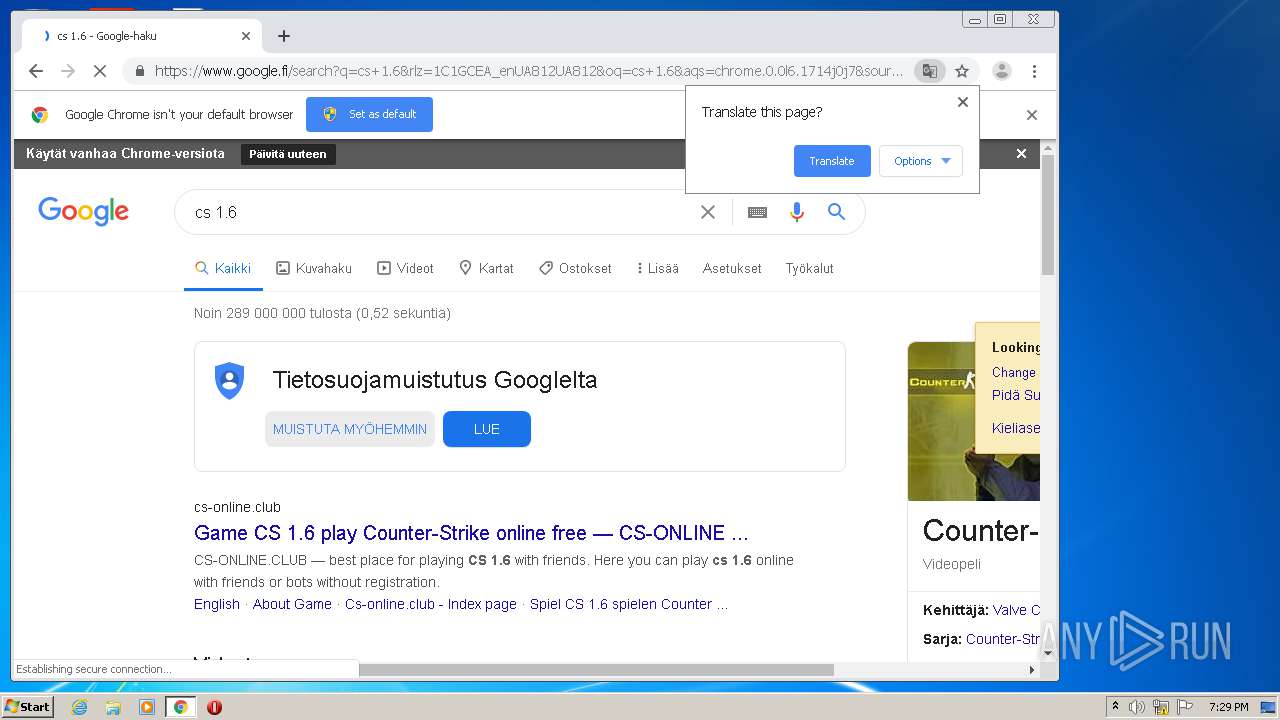
3020 | chrome.exe | 216.58.205.227:443 | www.google.fi | Google Inc. | US | whitelisted |
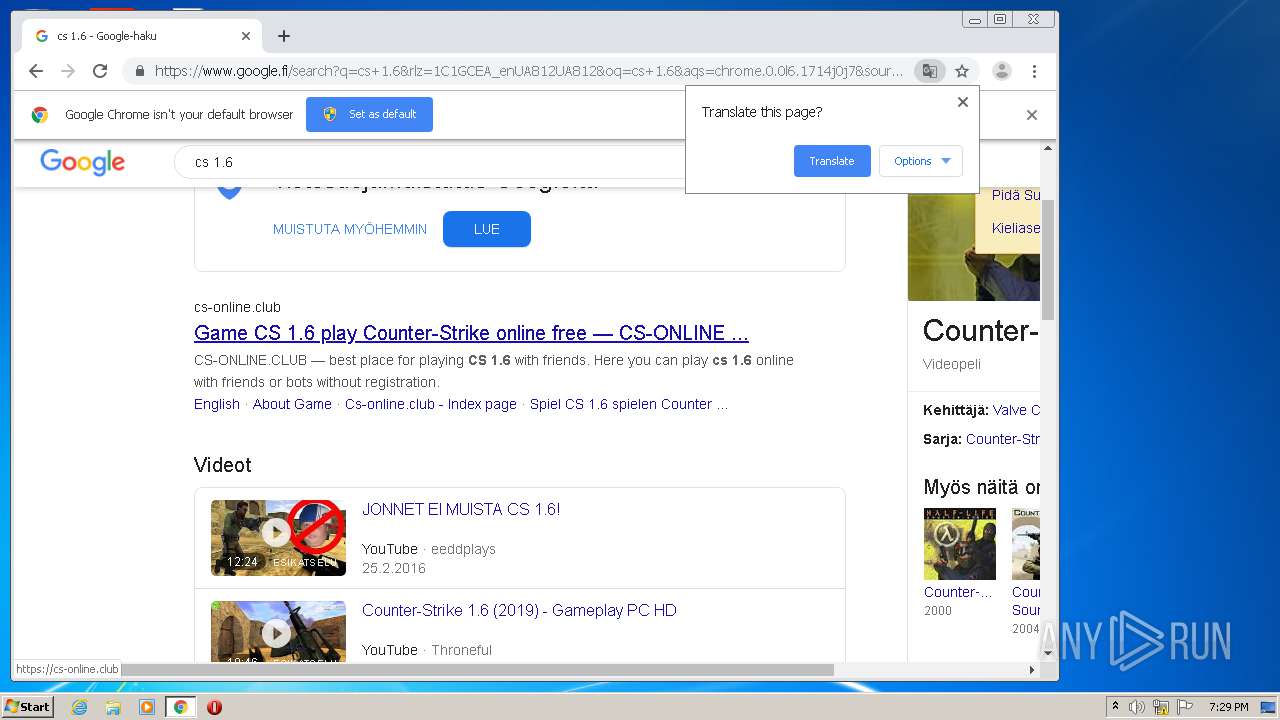
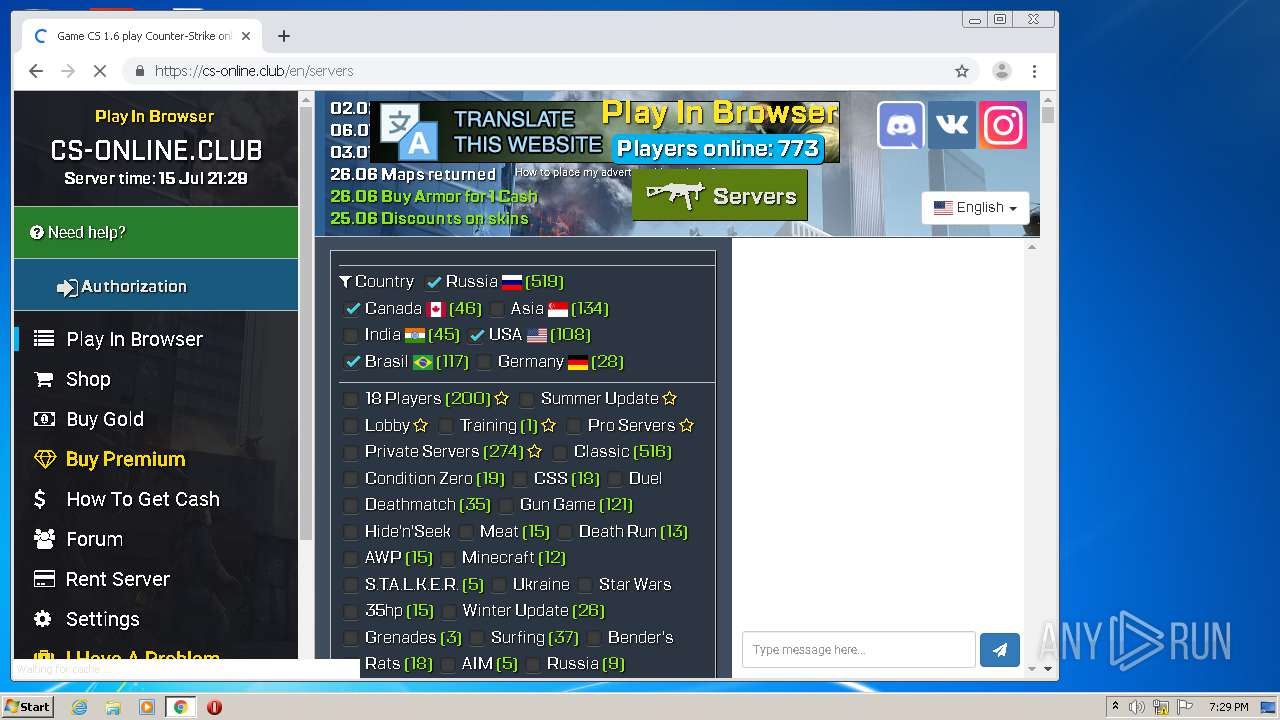
3020 | chrome.exe | 104.26.9.224:443 | cs-online.club | Cloudflare Inc | US | unknown |
3020 | chrome.exe | 172.217.18.14:443 | consent.google.com | Google Inc. | US | whitelisted |
3020 | chrome.exe | 104.16.133.229:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3020 | chrome.exe | 216.58.212.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.fi |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
Process | Message |
|---|---|
hl.exe | AppActive: active
|
hl.exe | AppActive: not active
|
hl.exe | Missing shutdown function for Sys_Init() : Sys_Shutdown()
|
hl.exe | Missing shutdown function for Sys_InitMemory() : Sys_ShutdownMemory()
|
hl.exe | Missing shutdown function for Sys_InitLauncherInterface() : Sys_ShutdownLauncherInterface()
|
hl.exe | Shutdown function FileSystem_Shutdown() not in list!!!
|
hl.exe | AppActive: active
|
hl.exe | 0:Initializing platform...
|
hl.exe | Platform config directory: c:\games\cs 1.6 warzone\platform\config
|
hl.exe | AppActive: not active
|