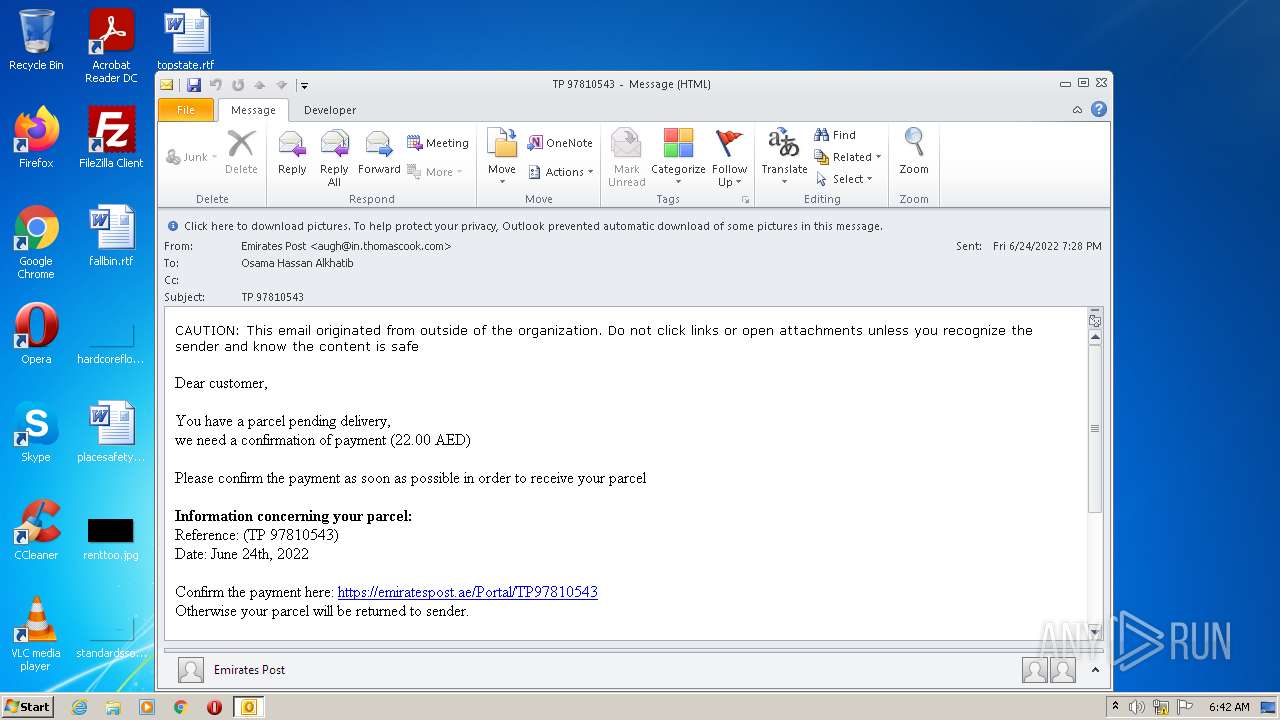
| File name: | TP 97810543.msg |
| Full analysis: | https://app.any.run/tasks/7edfd376-ad70-406c-a6c3-88e450fc7577 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 05:42:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 5B2D83E0106C3B368934912718C3E7DB |
| SHA1: | 90A4C5A0022F3F63843E36C773DD9664BAB45E00 |
| SHA256: | 78B38B12CD68F7CA25B1BCFD12D71CF990511C5D5FB94D4766A87CD7A53B6A59 |
| SSDEEP: | 768:9ysKcP4LWLsKRfFYEsKBsKB3K3ndsn4MxnJOt4O6/5rP0wIKxZHgLRCeLbMzY07q:sbcP4LWL17p5indCLfxO6/BIKJg |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2604)
SUSPICIOUS
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2604)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2216)
INFO
Checks supported languages
- OUTLOOK.EXE (PID: 2604)
- iexplore.exe (PID: 3500)
- iexplore.exe (PID: 2216)
Reads the computer name
- OUTLOOK.EXE (PID: 2604)
- iexplore.exe (PID: 3500)
- iexplore.exe (PID: 2216)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2604)
- iexplore.exe (PID: 2216)
- iexplore.exe (PID: 3500)
Application launched itself
- iexplore.exe (PID: 3500)
Reads settings of System Certificates
- iexplore.exe (PID: 2216)
- iexplore.exe (PID: 3500)
Checks Windows Trust Settings
- iexplore.exe (PID: 3500)
- iexplore.exe (PID: 2216)
Searches for installed software
- OUTLOOK.EXE (PID: 2604)
Changes internet zones settings
- iexplore.exe (PID: 3500)
Reads internet explorer settings
- iexplore.exe (PID: 2216)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3500)
Changes settings of System certificates
- iexplore.exe (PID: 3500)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
42
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2216 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3500 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\TP 97810543.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
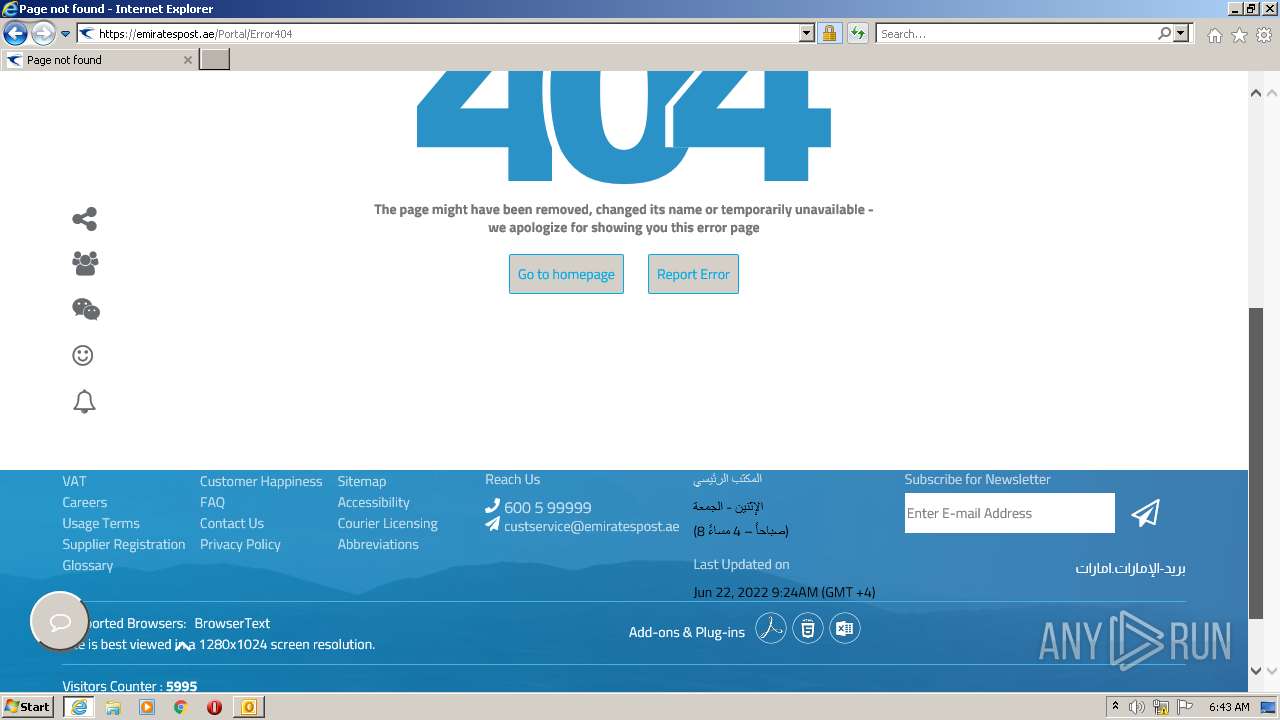
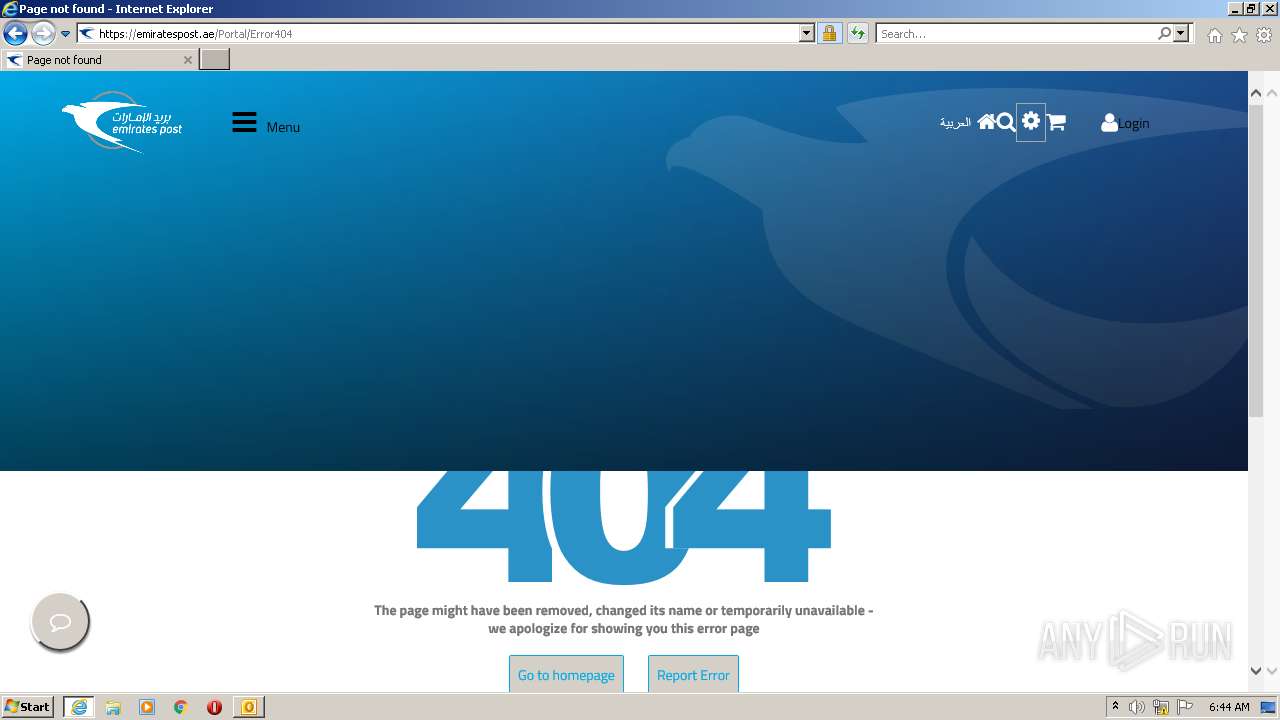
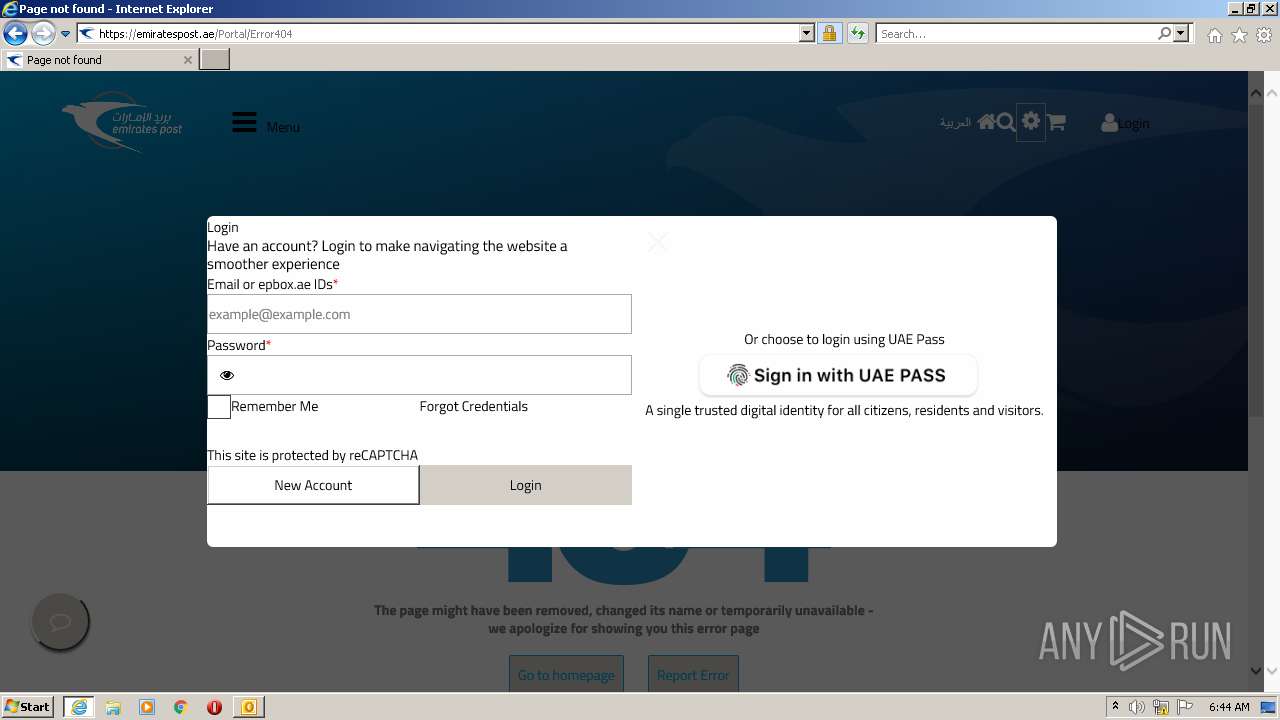
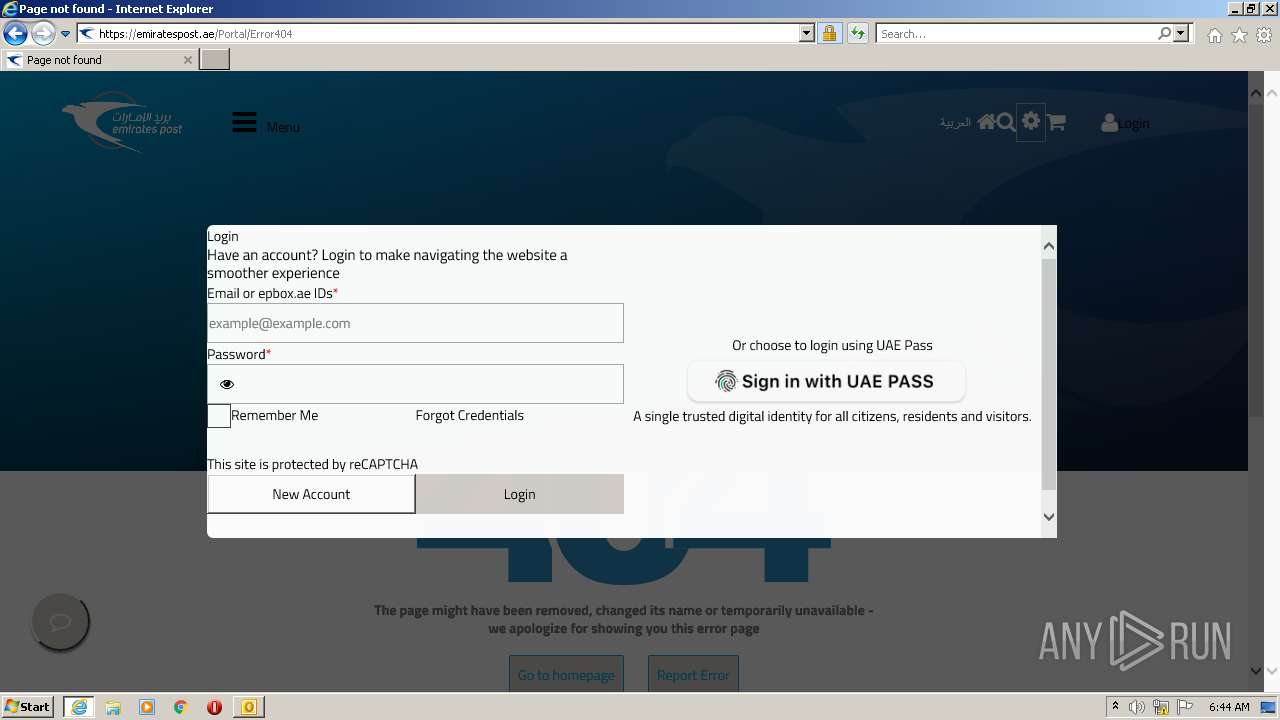
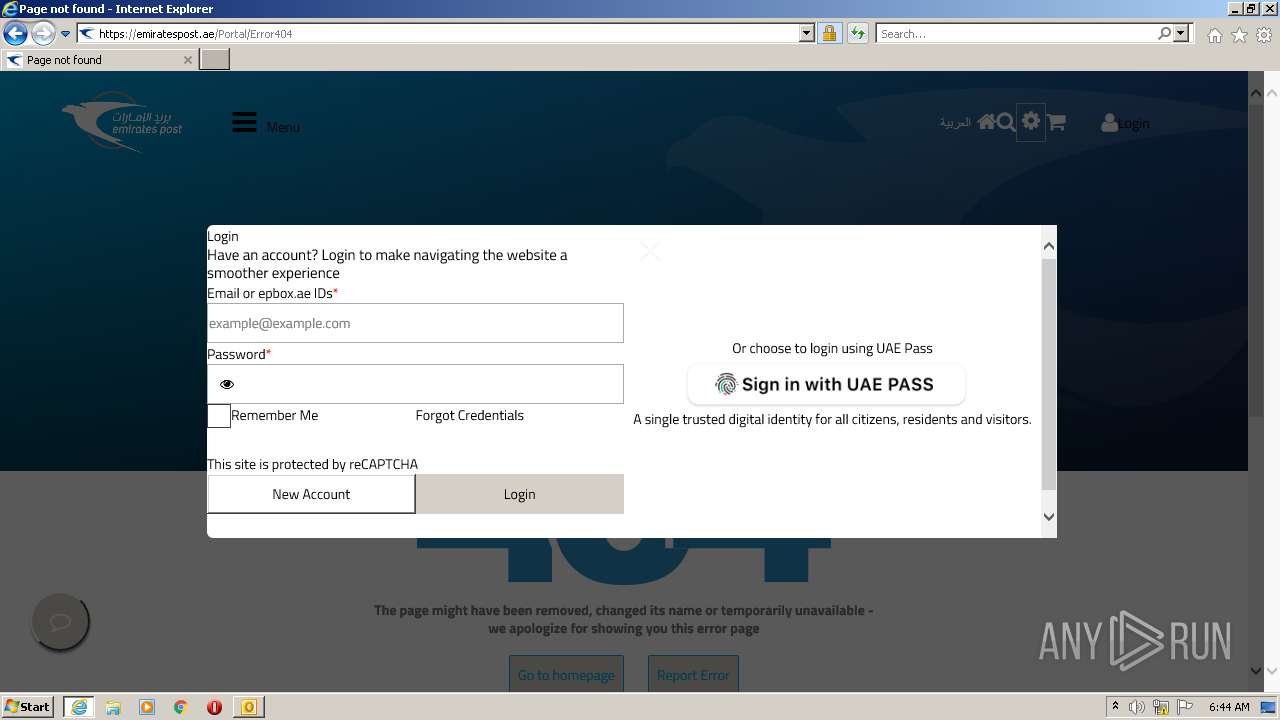
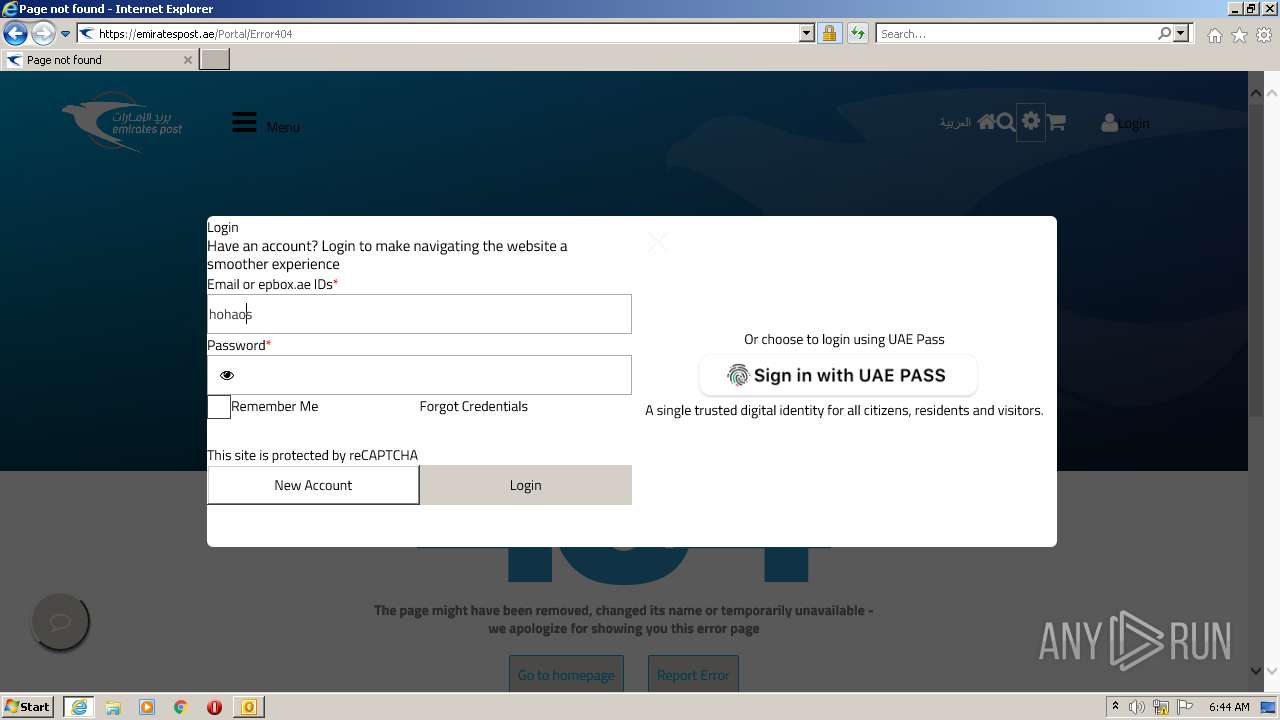
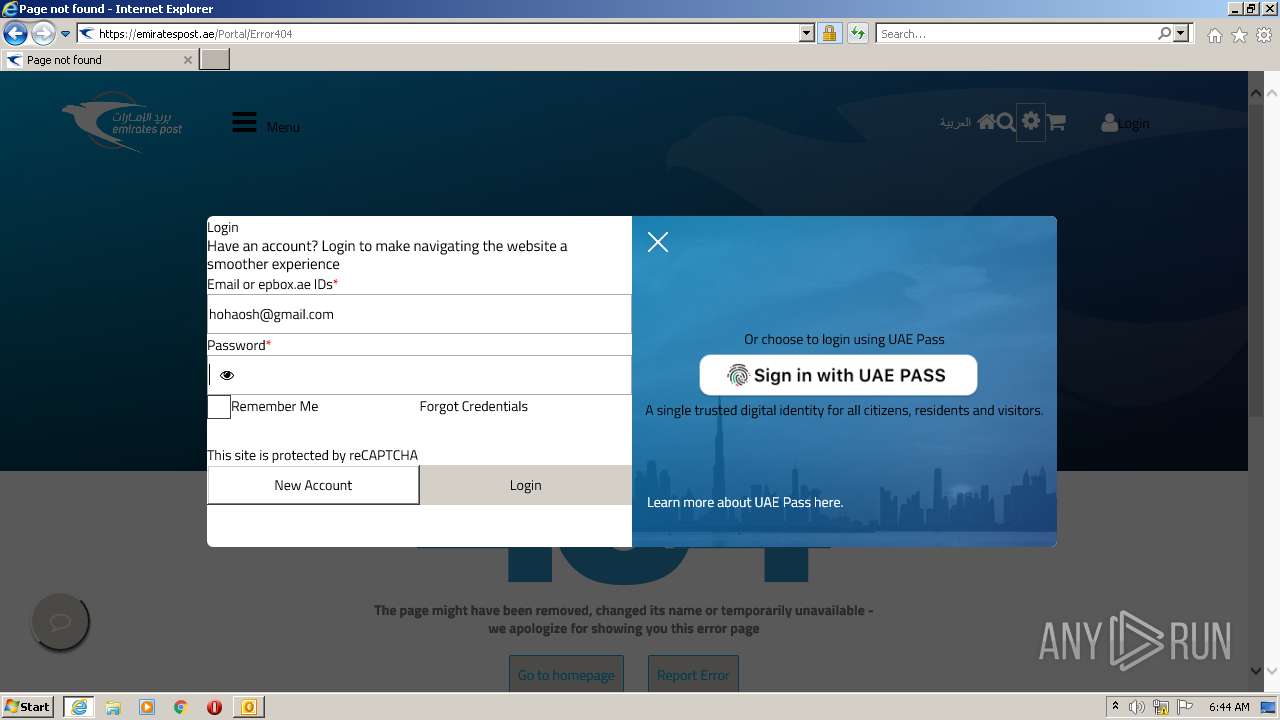
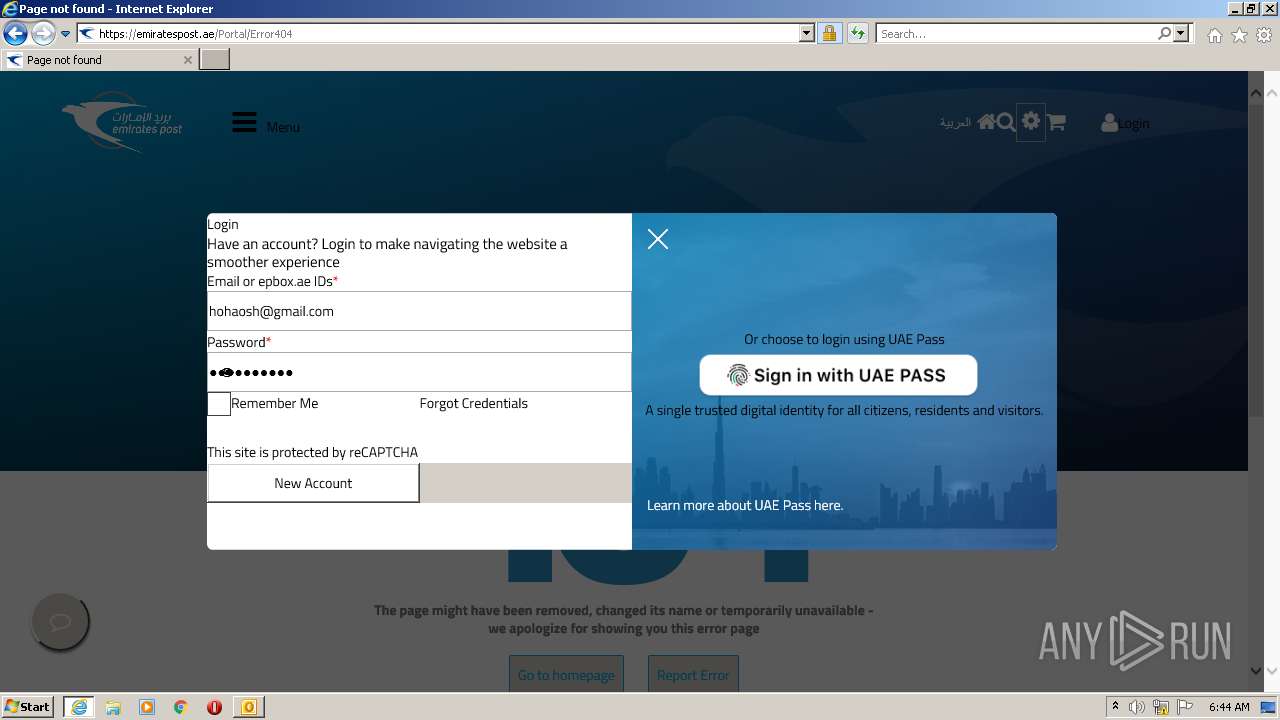
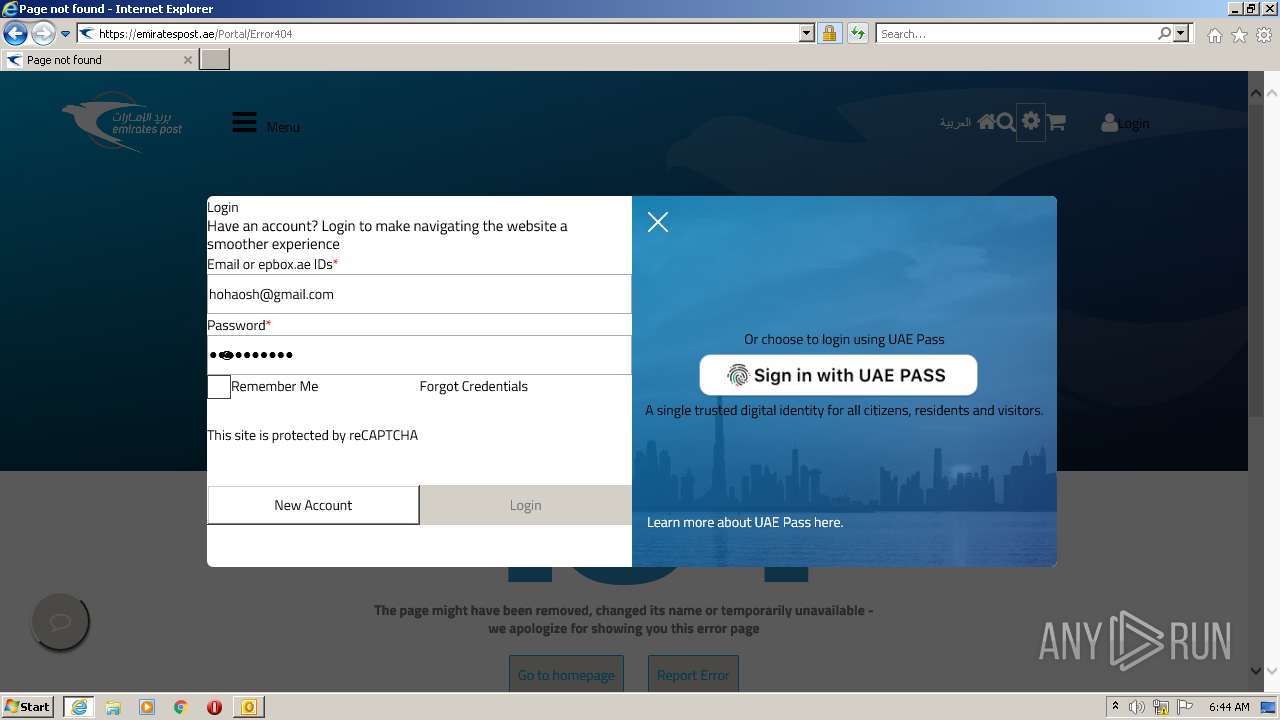
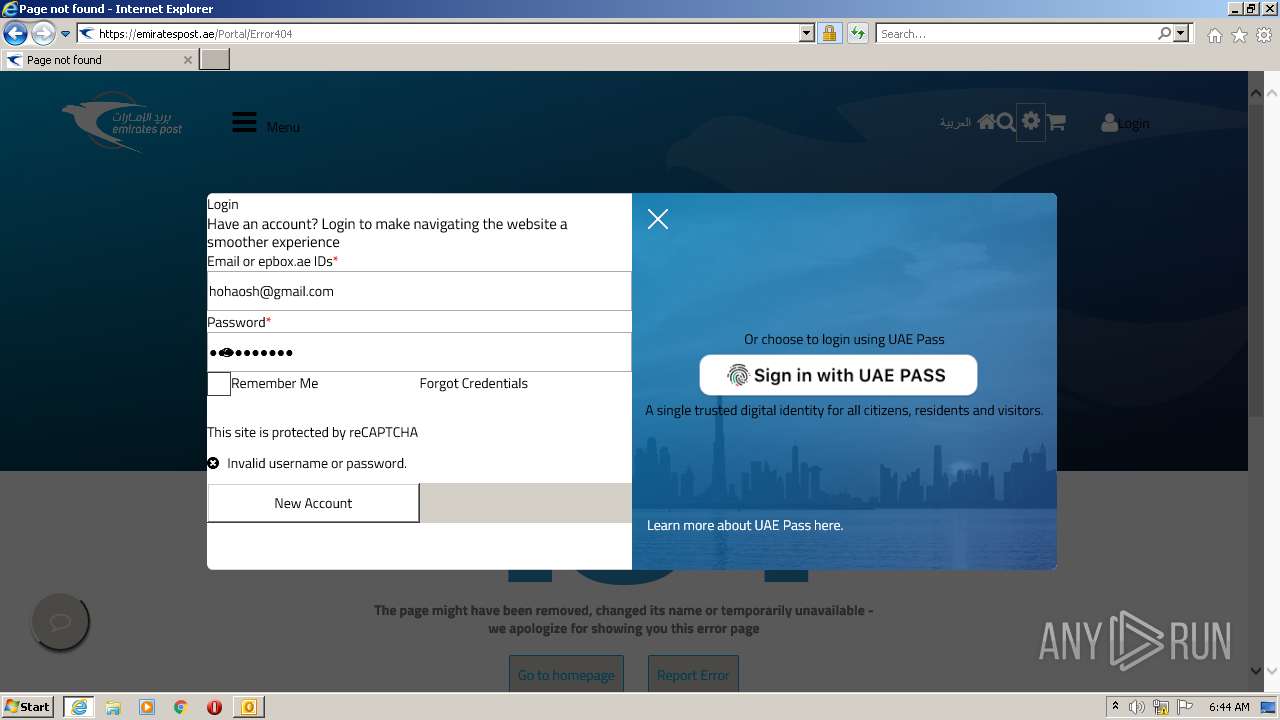
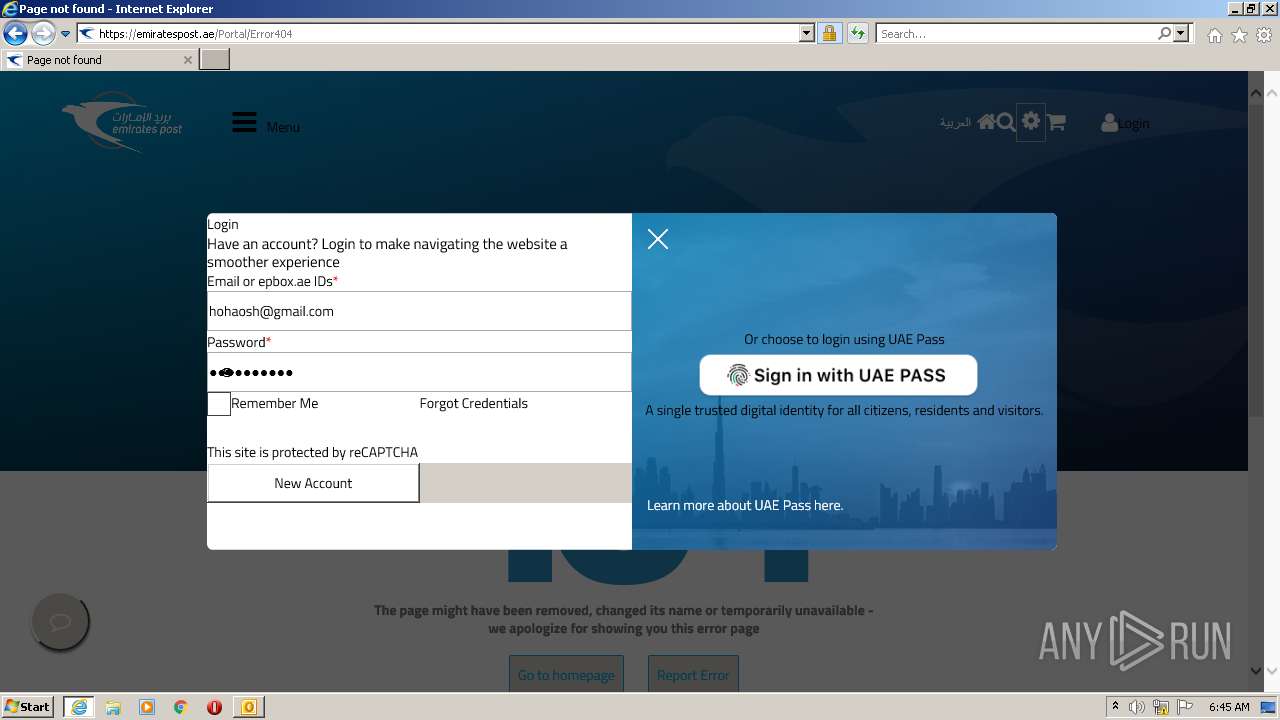
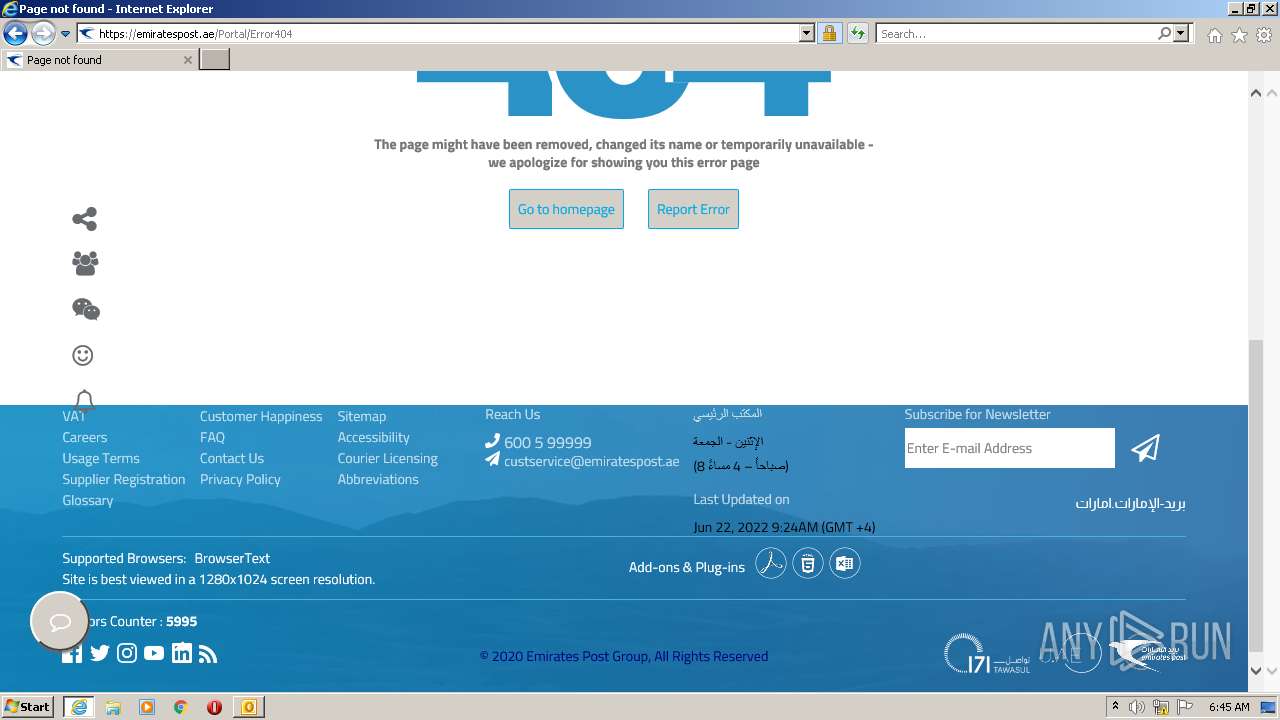
| 3500 | "C:\Program Files\Internet Explorer\iexplore.exe" https://emiratespost.ae/Portal/TP97810543 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
26 518
Read events
25 359
Write events
1 136
Delete events
23
Modification events
| (PID) Process: | (2604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
24
Text files
229
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2604 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRCF9B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2604 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2604 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2604 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
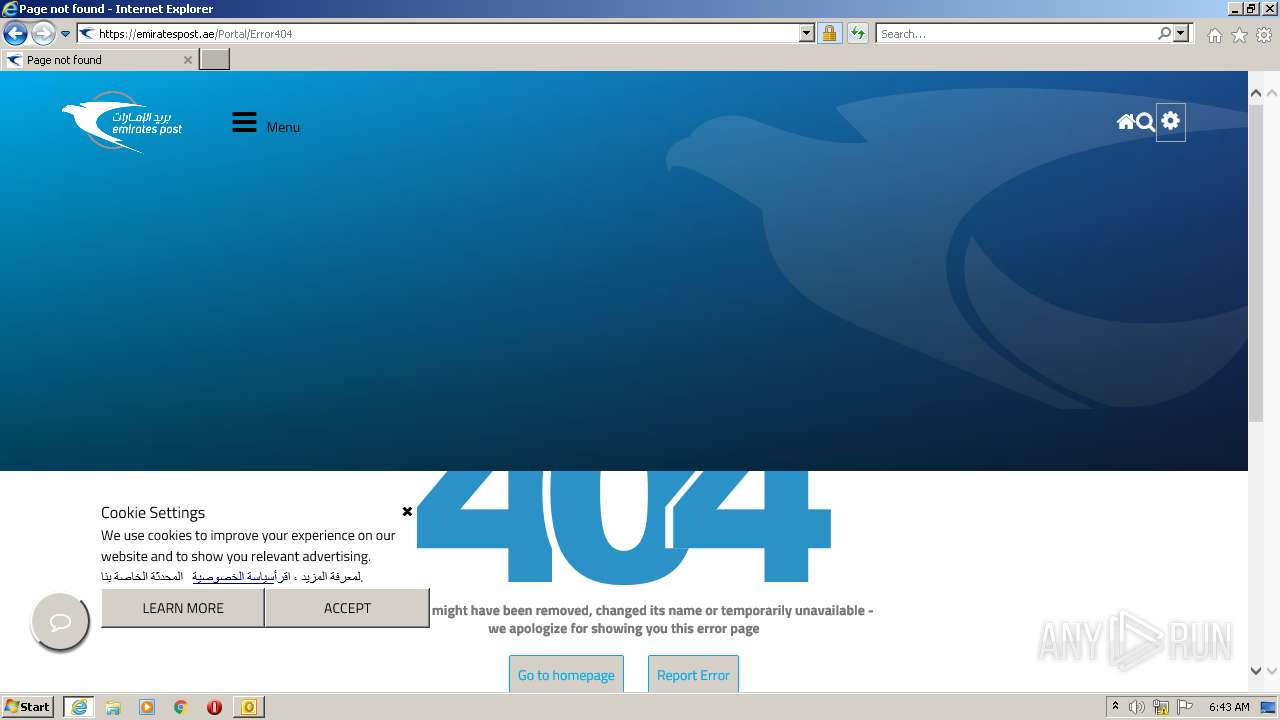
| 2216 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Error404[1].htm | html | |
MD5:— | SHA256:— | |||
| 2216 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E573CDF4C6D731D56A665145182FD759_D70C98E6754A7BBE7C74F55AD600E350 | der | |
MD5:— | SHA256:— | |||
| 2216 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E573CDF4C6D731D56A665145182FD759_D70C98E6754A7BBE7C74F55AD600E350 | binary | |
MD5:— | SHA256:— | |||
| 2216 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2216 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:— | SHA256:— | |||
| 2216 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\OutSystemsManifestLoader[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
112
DNS requests
31
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2604 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2216 | iexplore.exe | GET | — | 92.123.224.235:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPAXKr9ELNVNQRykOTIvmb3tA%3D%3D | unknown | — | — | shared |
2216 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2216 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCqm%2FLZVwk%2FcRLv5CtSZANu | US | der | 472 b | whitelisted |
2216 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEA%2BH%2BKgWdIVJQayF1uFYIlw%3D | US | der | 471 b | whitelisted |
2216 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEESz3%2FmlG2yGCtBzjzp1dVc%3D | US | der | 471 b | whitelisted |
2216 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
3500 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
2216 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCfB0sRdF8W%2FBIjdfpYeZPw | US | der | 472 b | whitelisted |
3500 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2604 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2216 | iexplore.exe | 185.54.16.176:443 | emiratespost.ae | Telecommunication Regulatory Authority | AE | unknown |
2216 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3500 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3500 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3500 | iexplore.exe | 185.54.16.176:443 | emiratespost.ae | Telecommunication Regulatory Authority | AE | unknown |
2216 | iexplore.exe | 92.123.225.51:443 | use.typekit.net | Akamai International B.V. | — | suspicious |
2216 | iexplore.exe | 142.250.186.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2216 | iexplore.exe | 142.250.185.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2216 | iexplore.exe | 172.217.18.110:443 | translate.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
emiratespost.ae |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
use.typekit.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
translate.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2216 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2216 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2216 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2216 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2216 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2216 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2216 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2216 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2216 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2216 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |