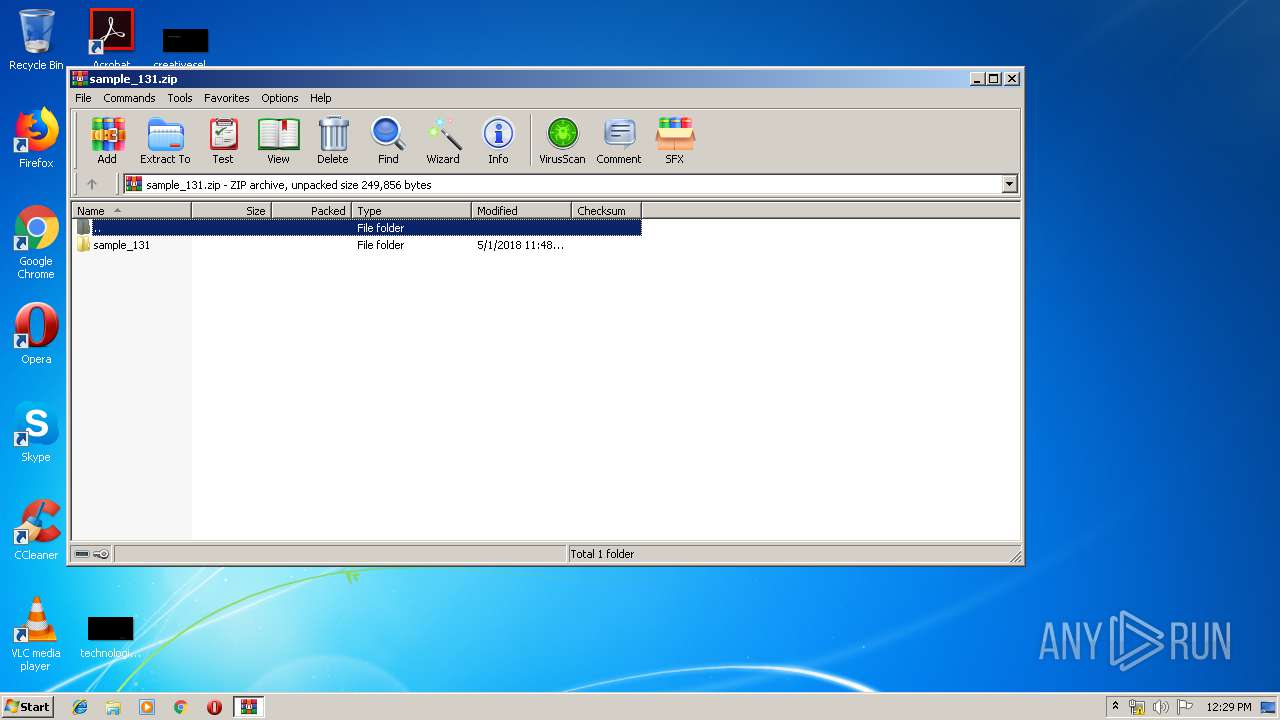
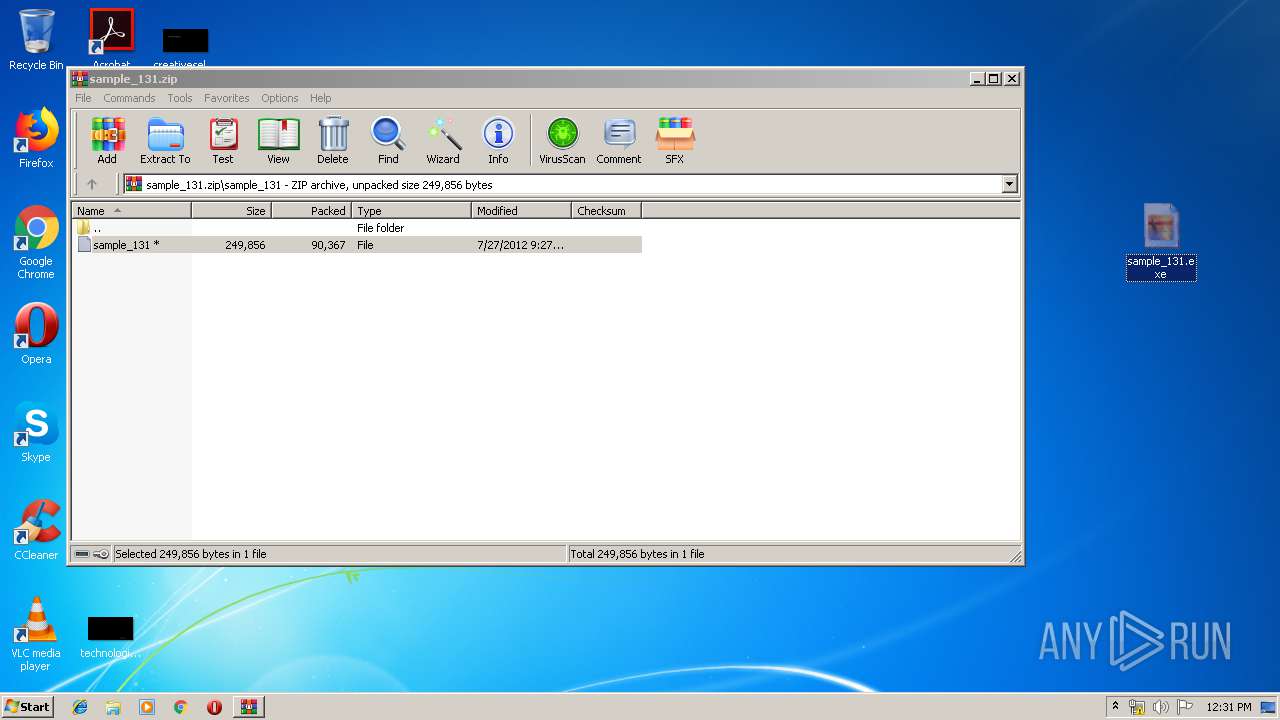
| File name: | sample_131.zip |
| Full analysis: | https://app.any.run/tasks/378153af-aa30-4540-bb9a-16ca159b3946 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 11:29:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 484FBEF0831326EC1916056254CE2BD8 |
| SHA1: | 667DA226C126F00EBE129FA38ED5C0F5108852A5 |
| SHA256: | 78AB6EEB9D05B02FB051CF15976EC0B2B75C6408D64C81584AED30145AE83269 |
| SSDEEP: | 1536:qzTWdd2OA9j/uEa8Clqf3YLYW1CiYSDUdj6/zv4nF/djt6Dcaqr+Z8ie2ADc5nCj:qHWb2xj/da8h/Efmj67vCFVjOqaAen8z |
MALICIOUS
Application was dropped or rewritten from another process
- sample_131.exe (PID: 2976)
- pfbot.exe (PID: 2176)
Changes the autorun value in the registry
- sample_131.exe (PID: 2976)
- pfbot.exe (PID: 2176)
Changes Windows auto-update feature
- sample_131.exe (PID: 2976)
- pfbot.exe (PID: 2176)
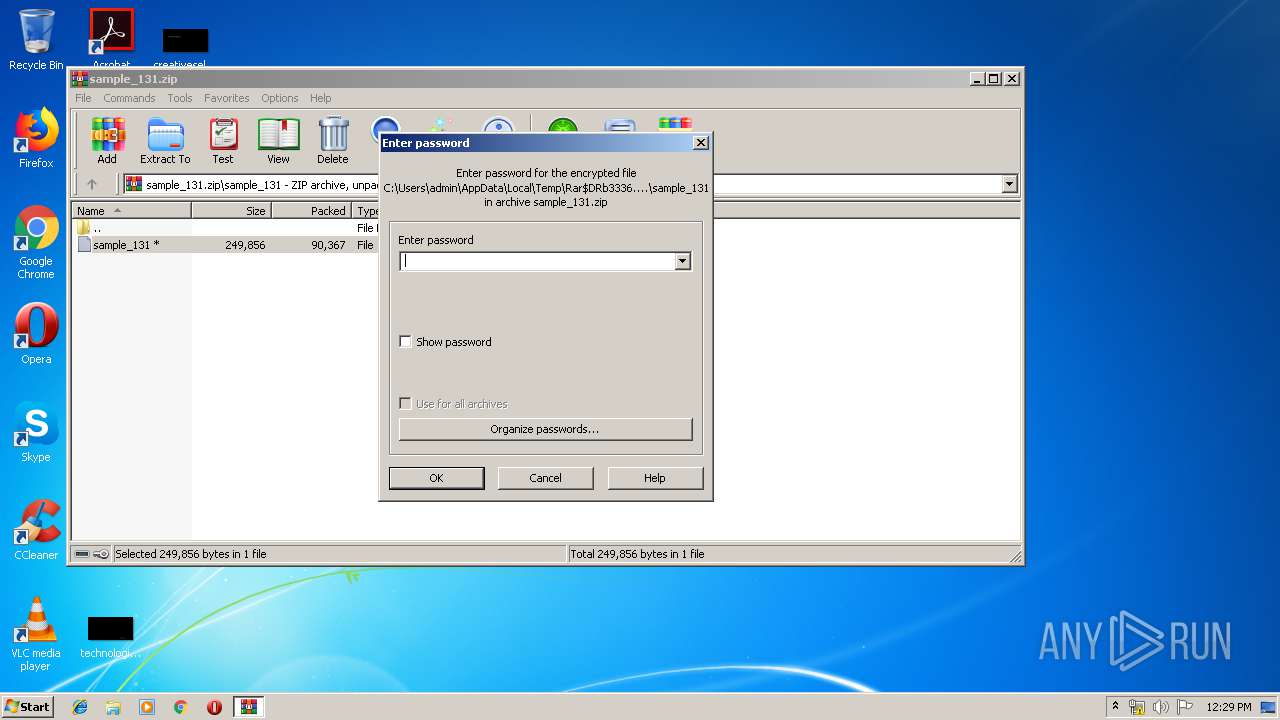
SUSPICIOUS
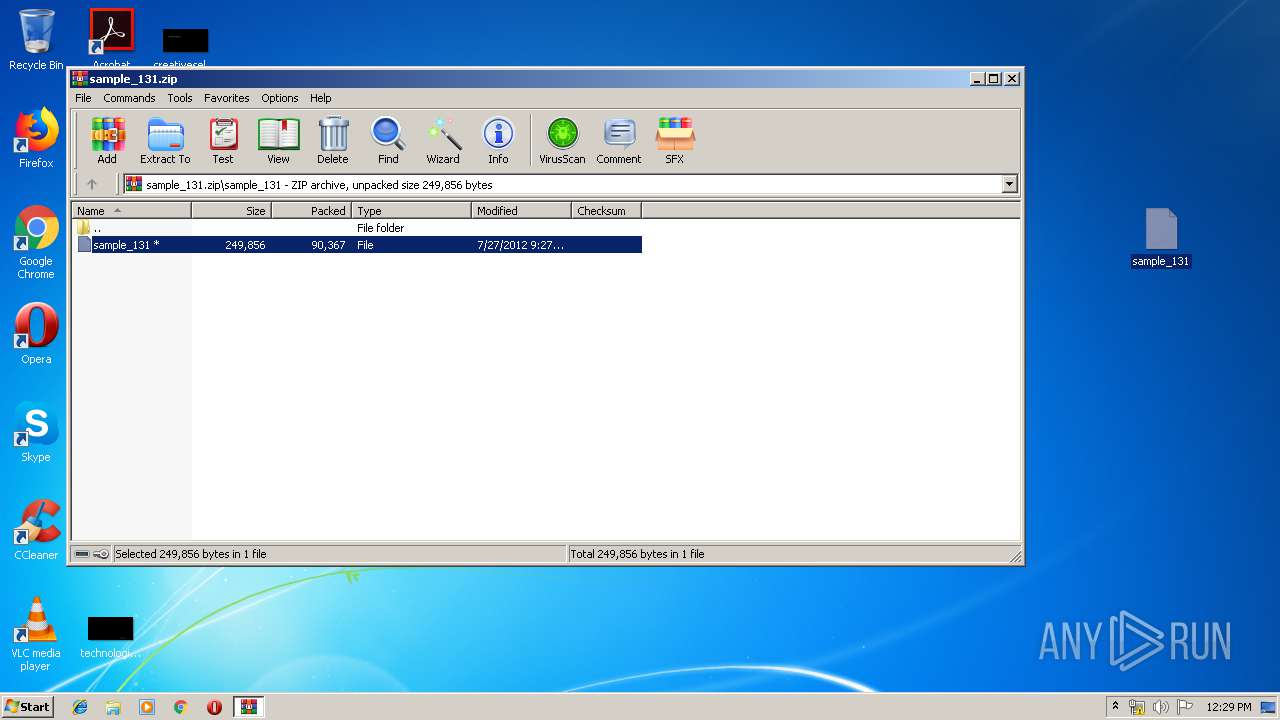
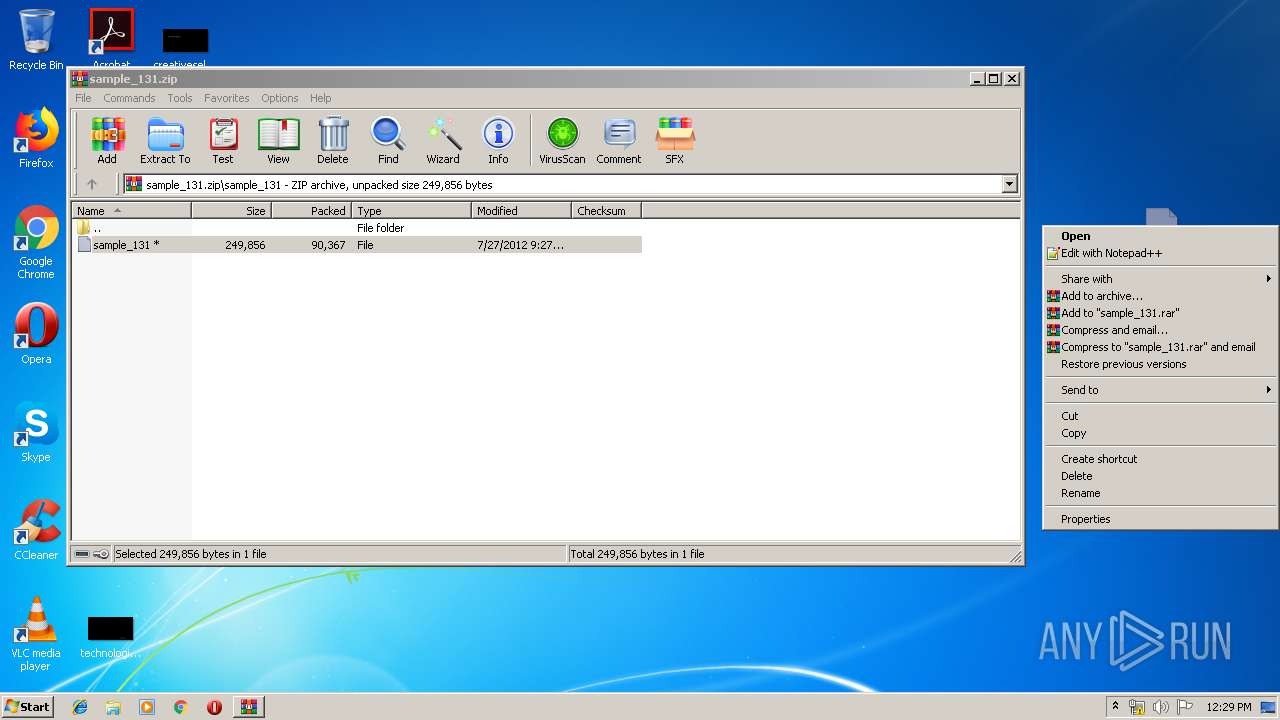
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3336)
- sample_131.exe (PID: 2976)
Starts itself from another location
- sample_131.exe (PID: 2976)
INFO
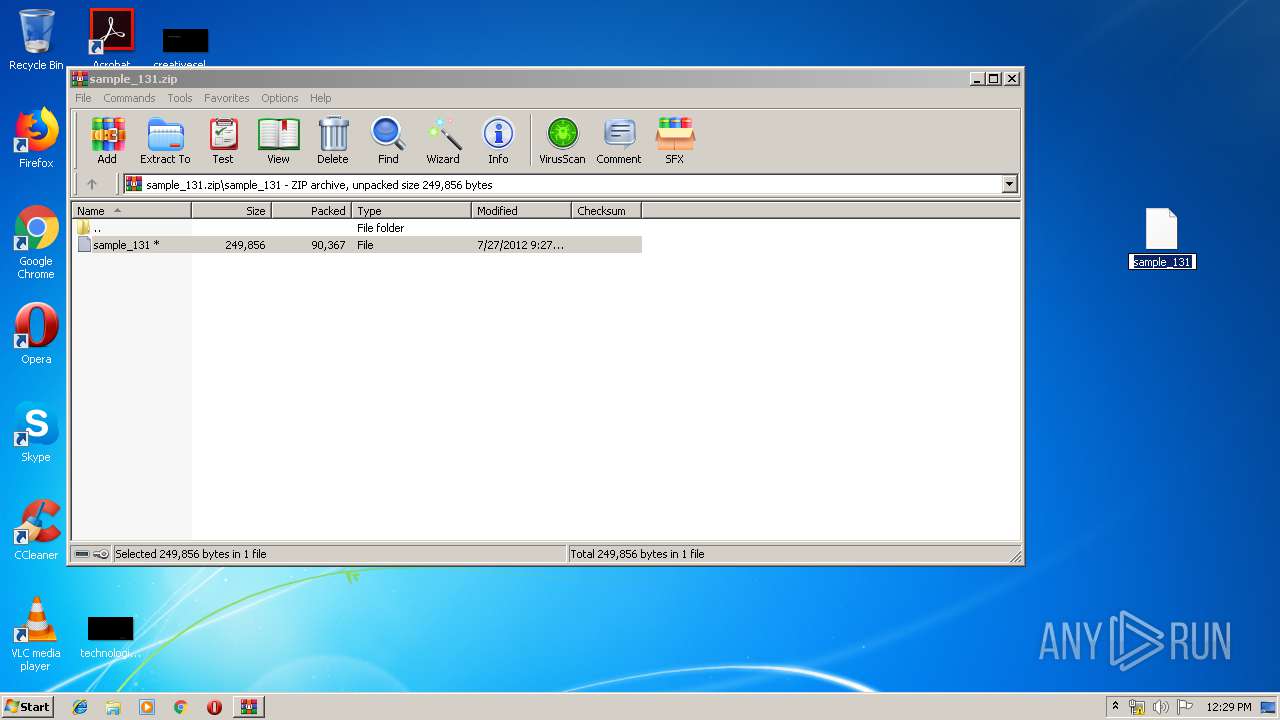
Manual execution by user
- sample_131.exe (PID: 2976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:05:01 18:48:22 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | sample_131/ |
Total processes
35
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2176 | "C:\Users\admin\pfbot.exe" | C:\Users\admin\pfbot.exe | sample_131.exe | ||||||||||||
User: admin Company: Denominava copyrightable oblongly Integrity Level: MEDIUM Description: esthesiogen Exit code: 0 Version: 5.03 Modules
| |||||||||||||||
| 2976 | "C:\Users\admin\Desktop\sample_131.exe" | C:\Users\admin\Desktop\sample_131.exe | explorer.exe | ||||||||||||
User: admin Company: Denominava copyrightable oblongly Integrity Level: MEDIUM Description: esthesiogen Exit code: 0 Version: 5.03 Modules
| |||||||||||||||
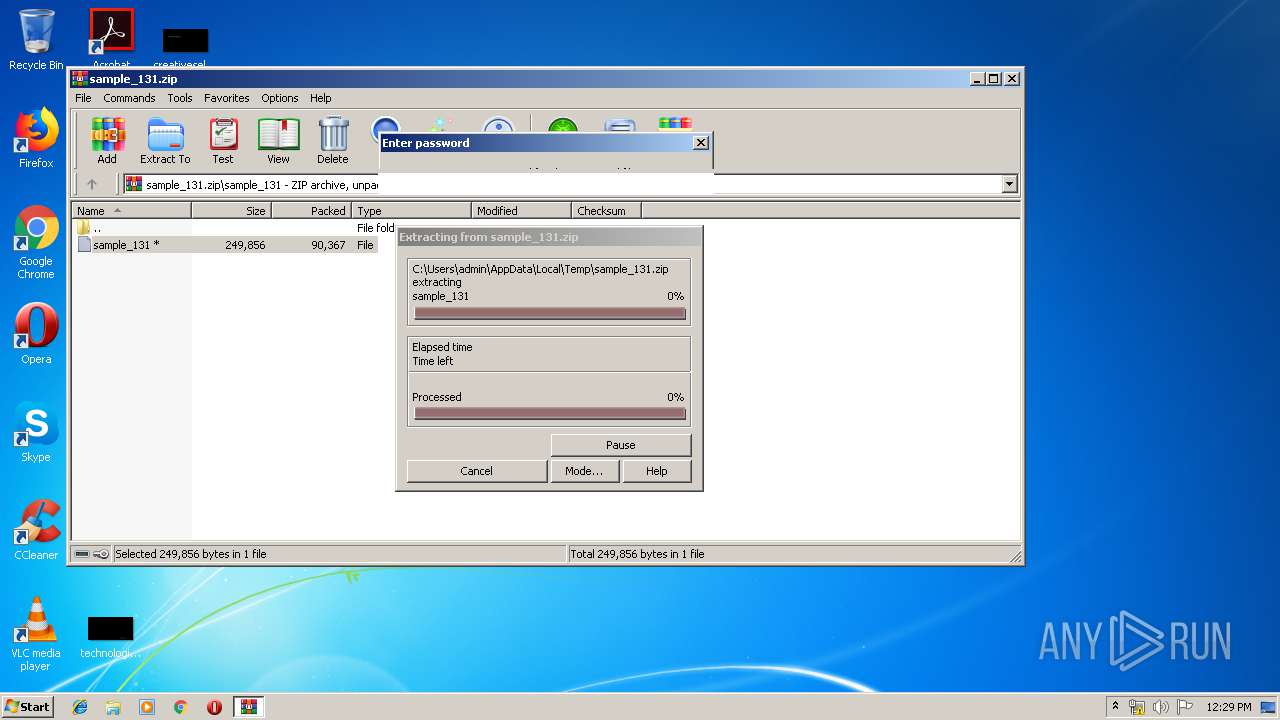
| 3336 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample_131.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 036
Read events
762
Write events
274
Delete events
0
Modification events
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_131.zip | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2976) sample_131.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
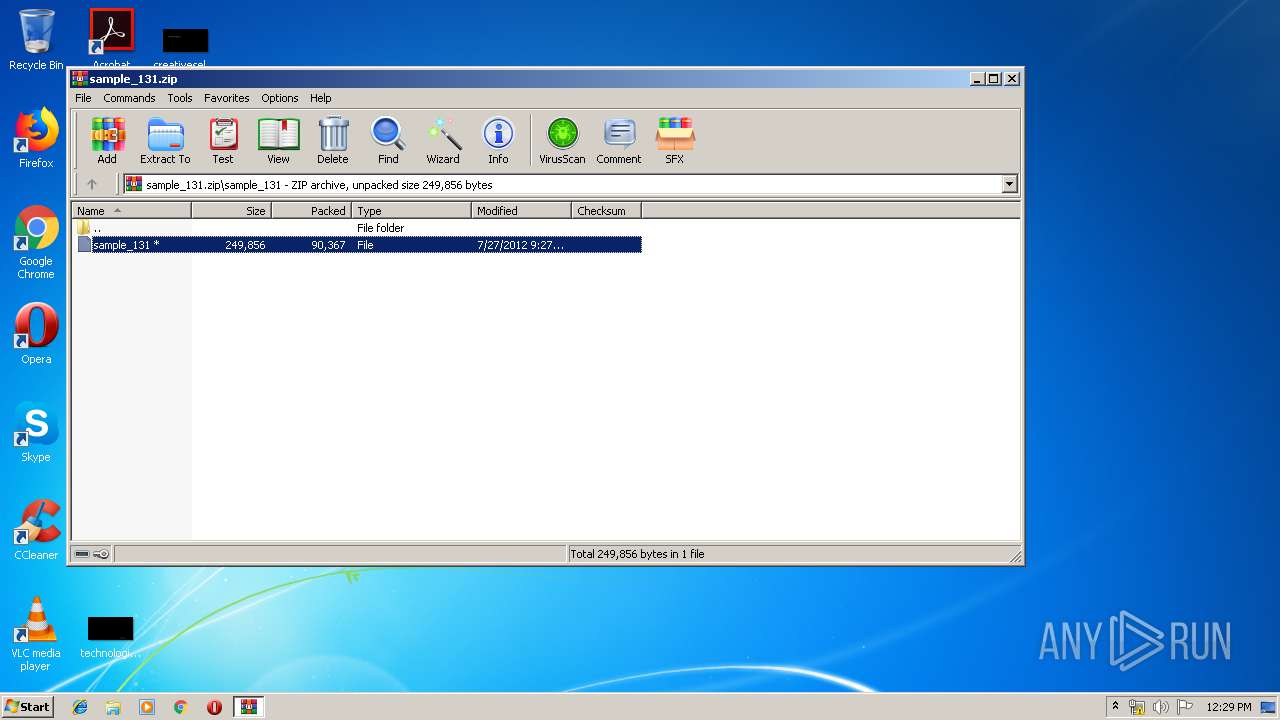
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3336 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3336.49233\sample_131\sample_131 | executable | |
MD5:— | SHA256:— | |||
| 2976 | sample_131.exe | C:\Users\admin\pfbot.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
ns1.musiczipz.com |
| malicious |
ns1.musicmixa.net |
| unknown |
ns1.musicmixa.org |
| unknown |
ns1.musicmixb.co |
| malicious |
ns1.musicmixc.com |
| unknown |