analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
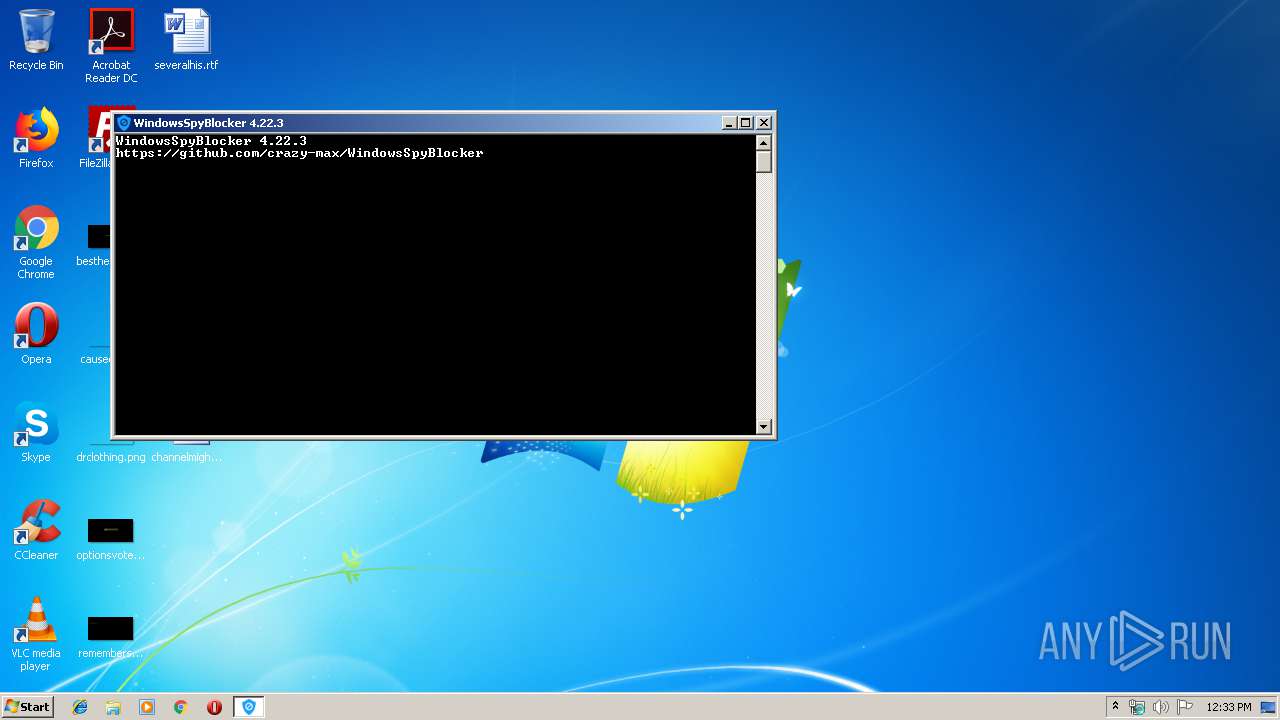
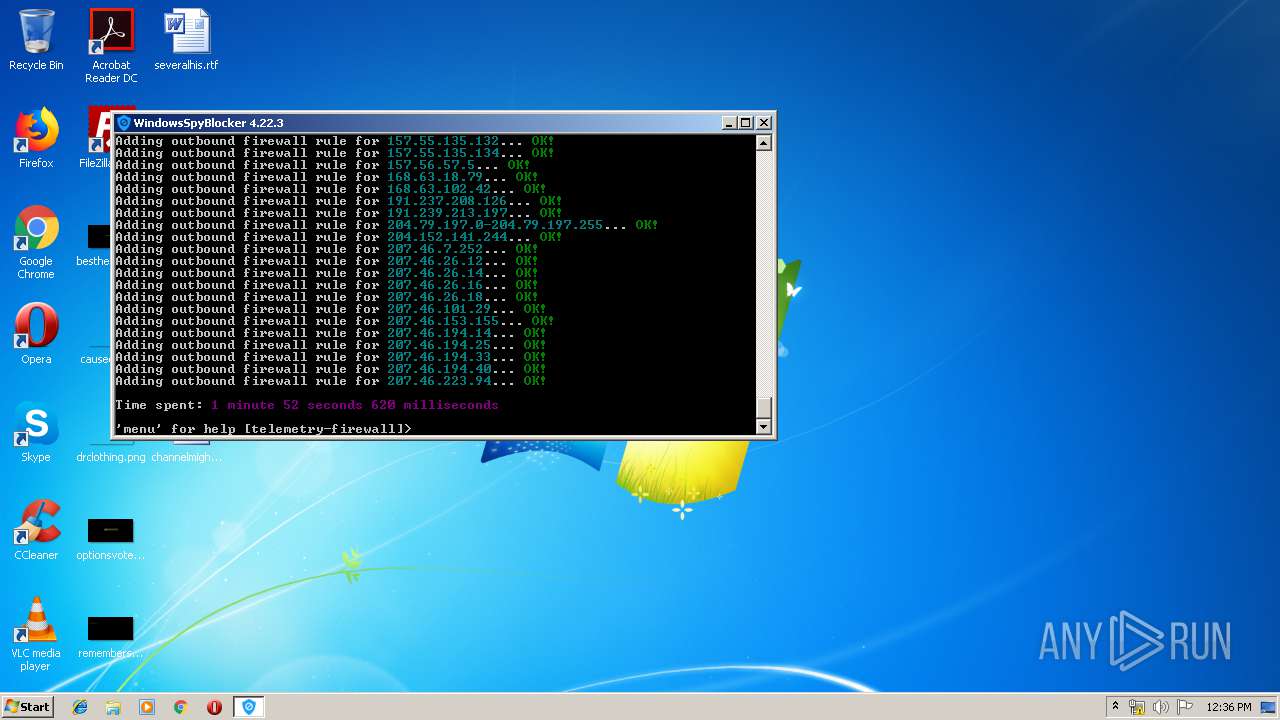
| File name: | WindowsSpyBlocker.exe |
| Full analysis: | https://app.any.run/tasks/c0b7fd7e-6292-4a5c-a4bb-ab588462f563 |
| Verdict: | Malicious activity |
| Analysis date: | August 17, 2019, 11:33:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | F7CF1793C2682A5B27DDAAA5D0CF77CE |
| SHA1: | BA123F97F619C269704D5744AA565B94264E1D05 |
| SHA256: | 78A60DE864E66A787118B9F381847AF45DA6CEBFC58AFD1737B36412BA6188BA |
| SSDEEP: | 98304:9VcR3q+rWZk4KzNx+iiEPwPwseY7g0DeccaAWn97eX:9VoWMzNsQDYZXp |
MALICIOUS
No malicious indicators.SUSPICIOUS
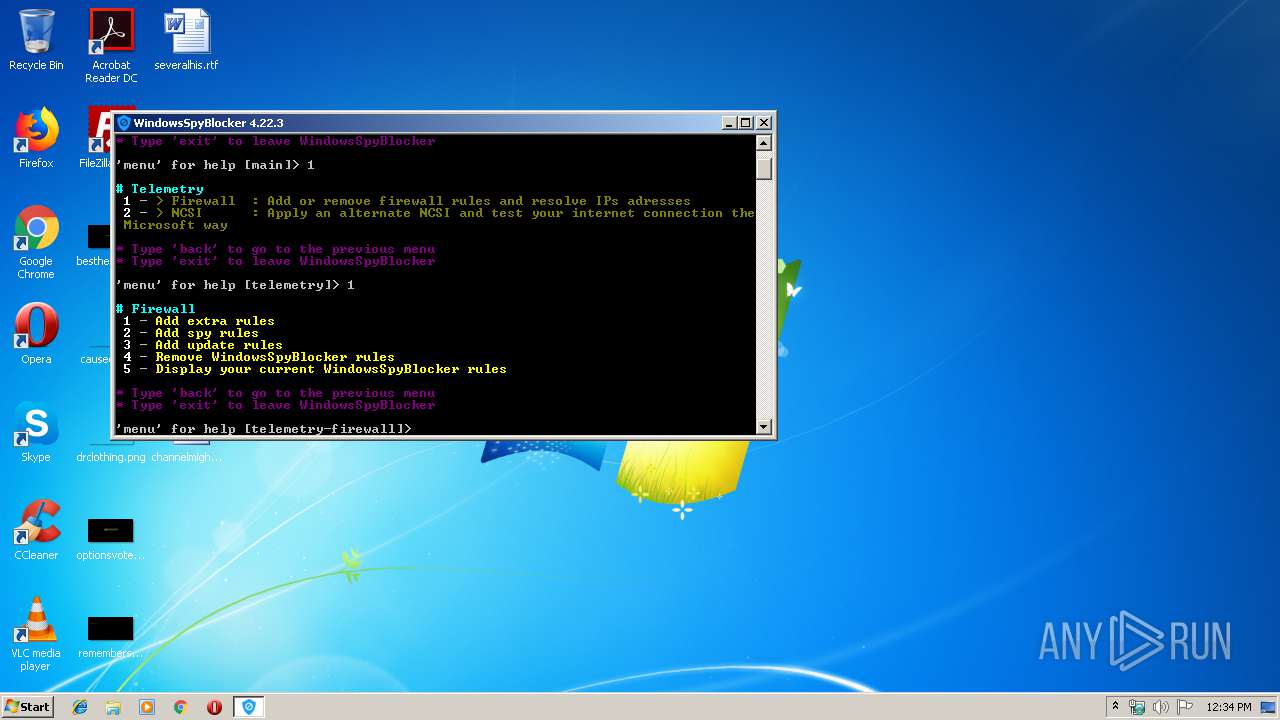
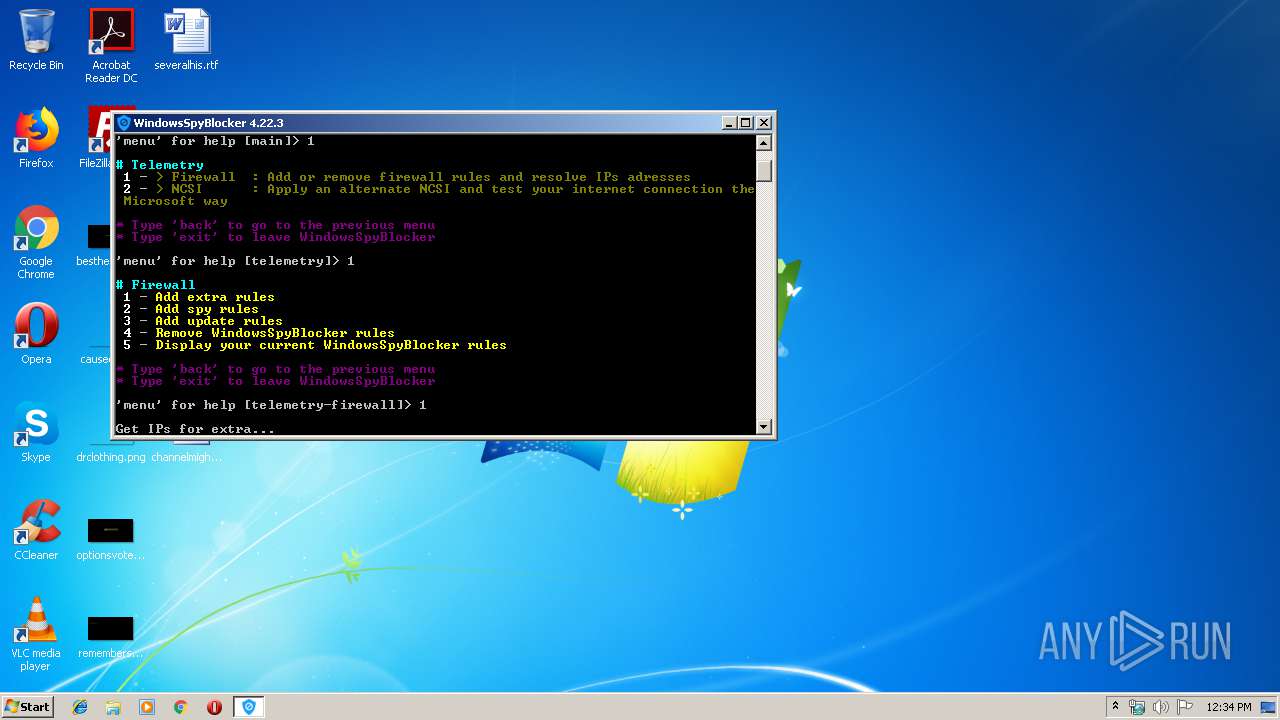
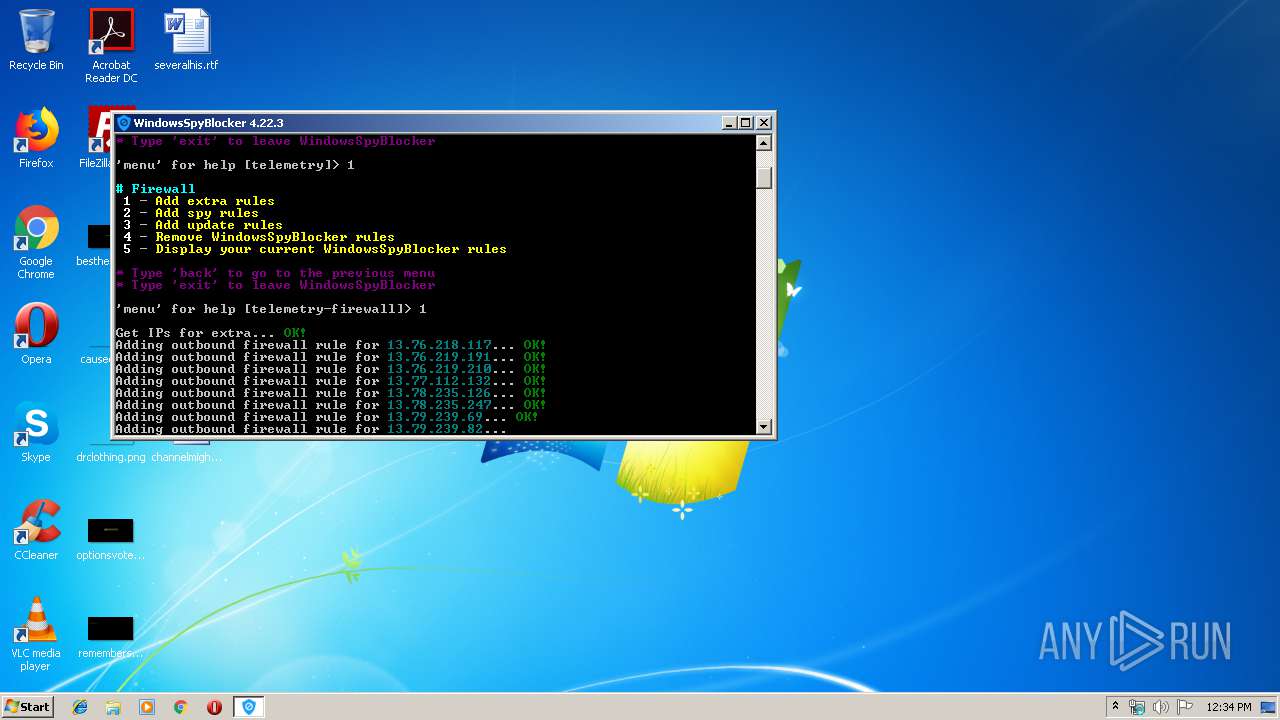
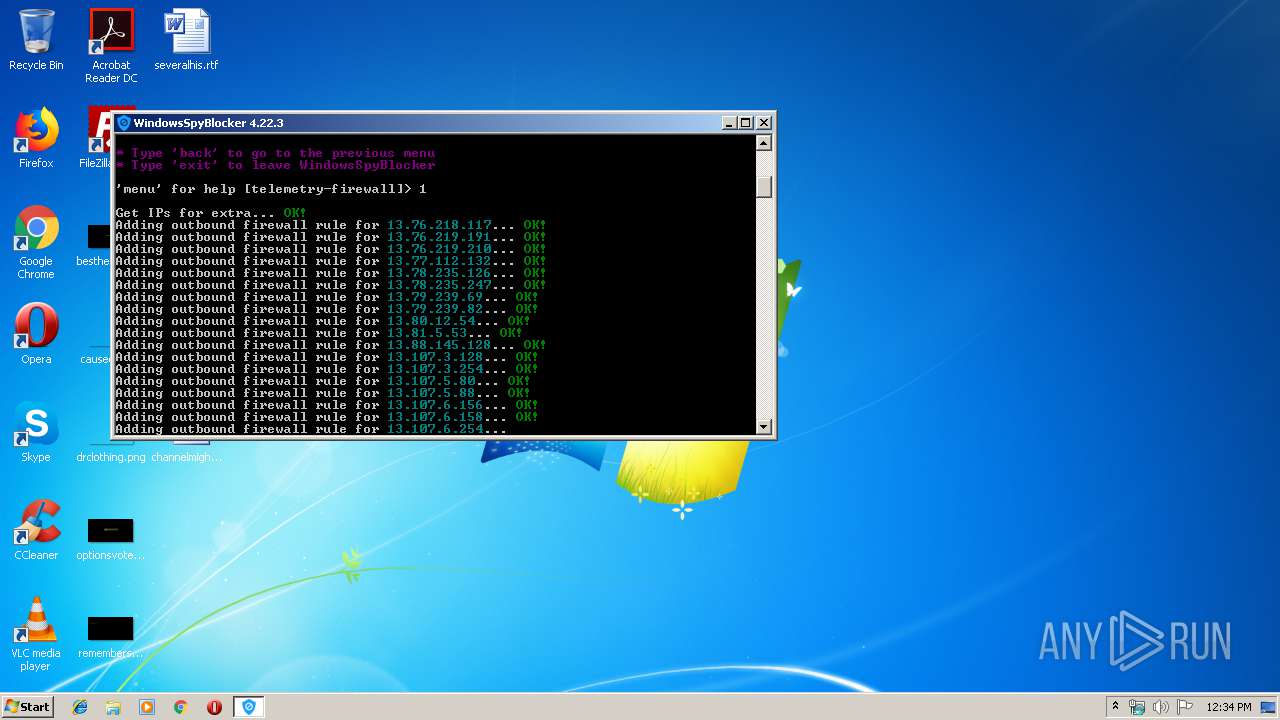
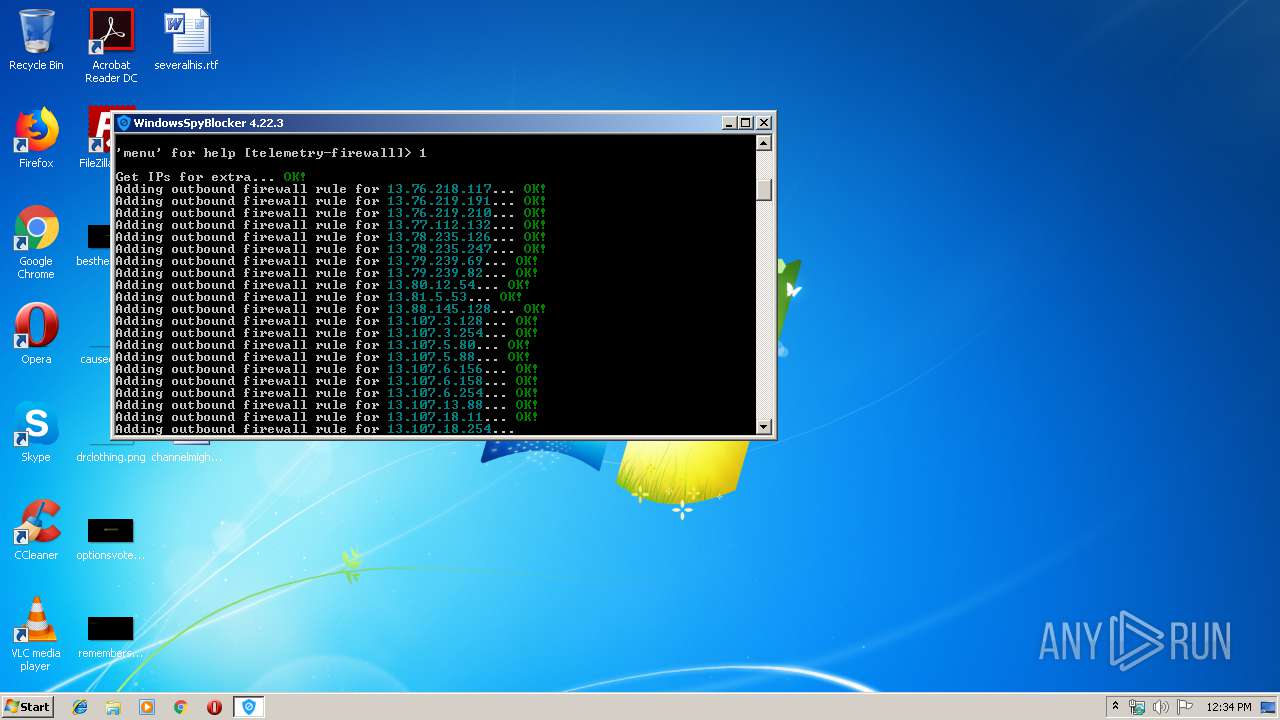
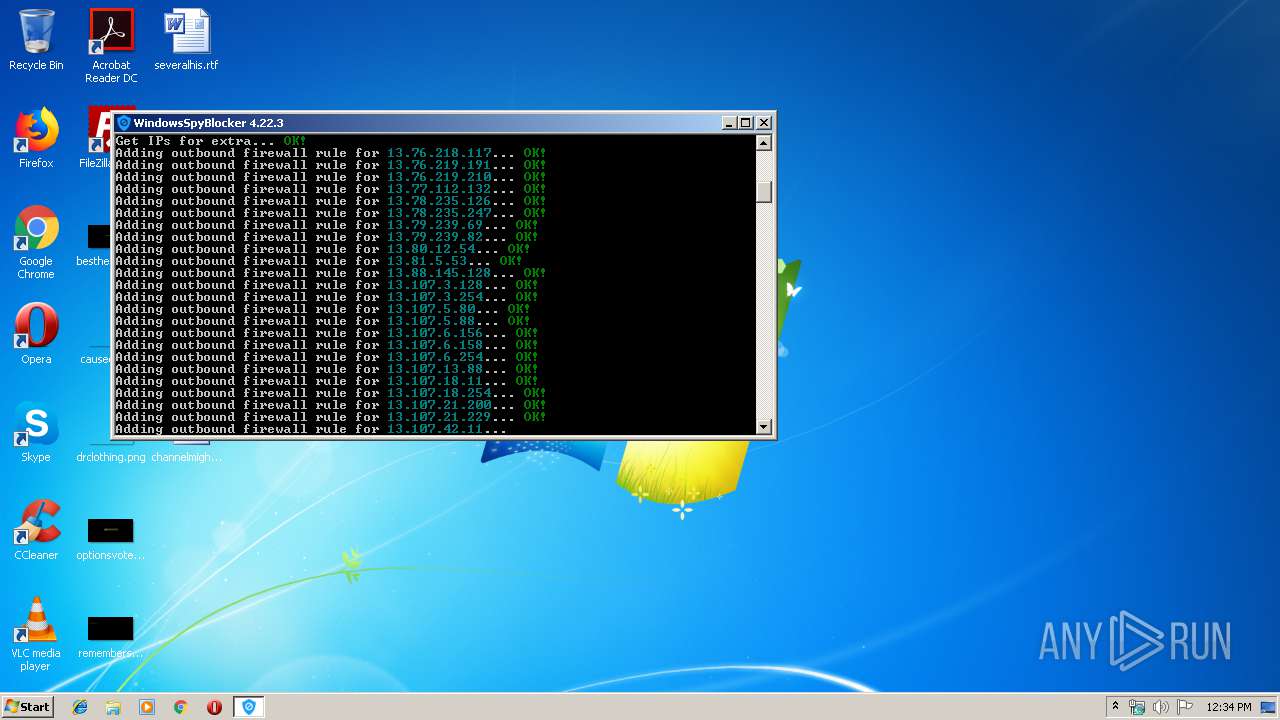
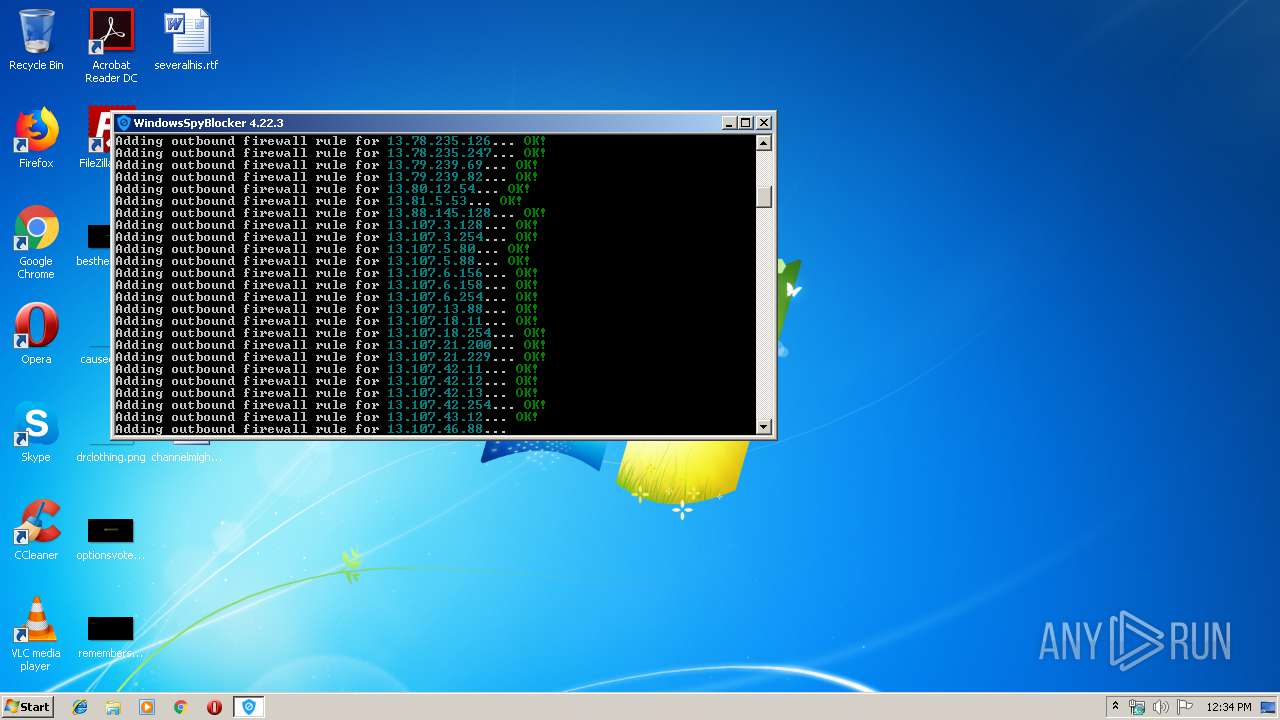
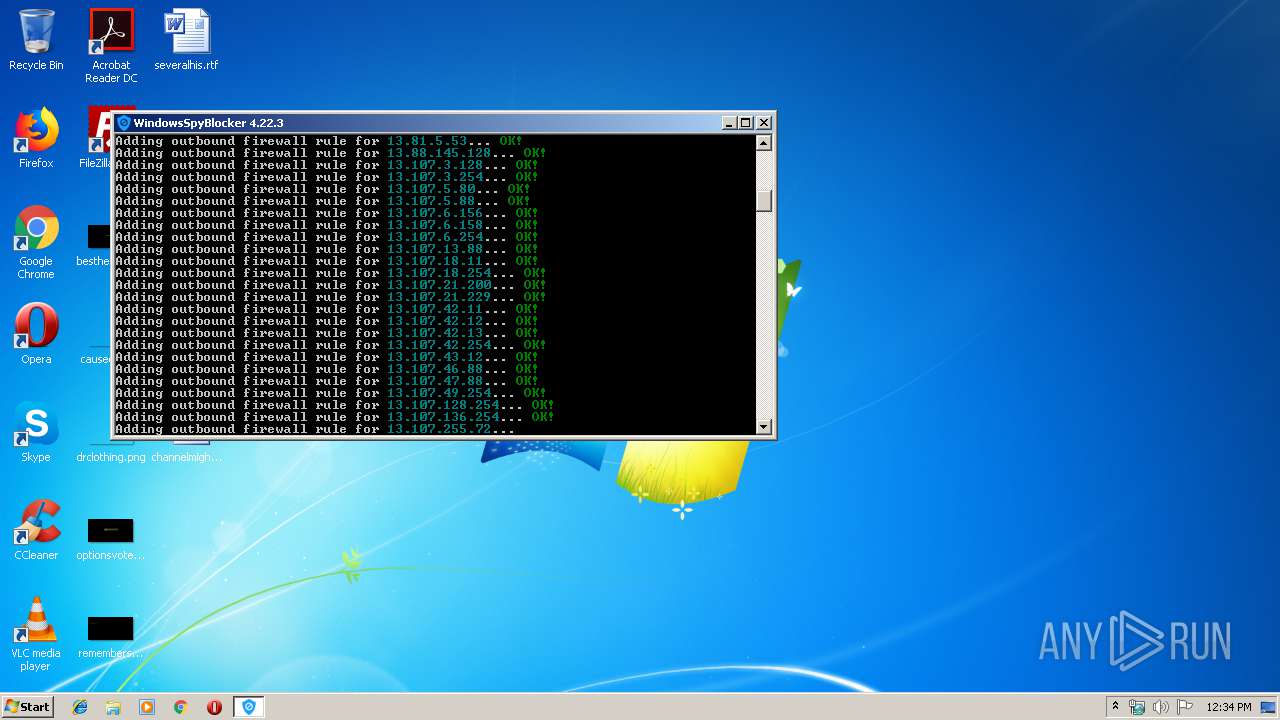
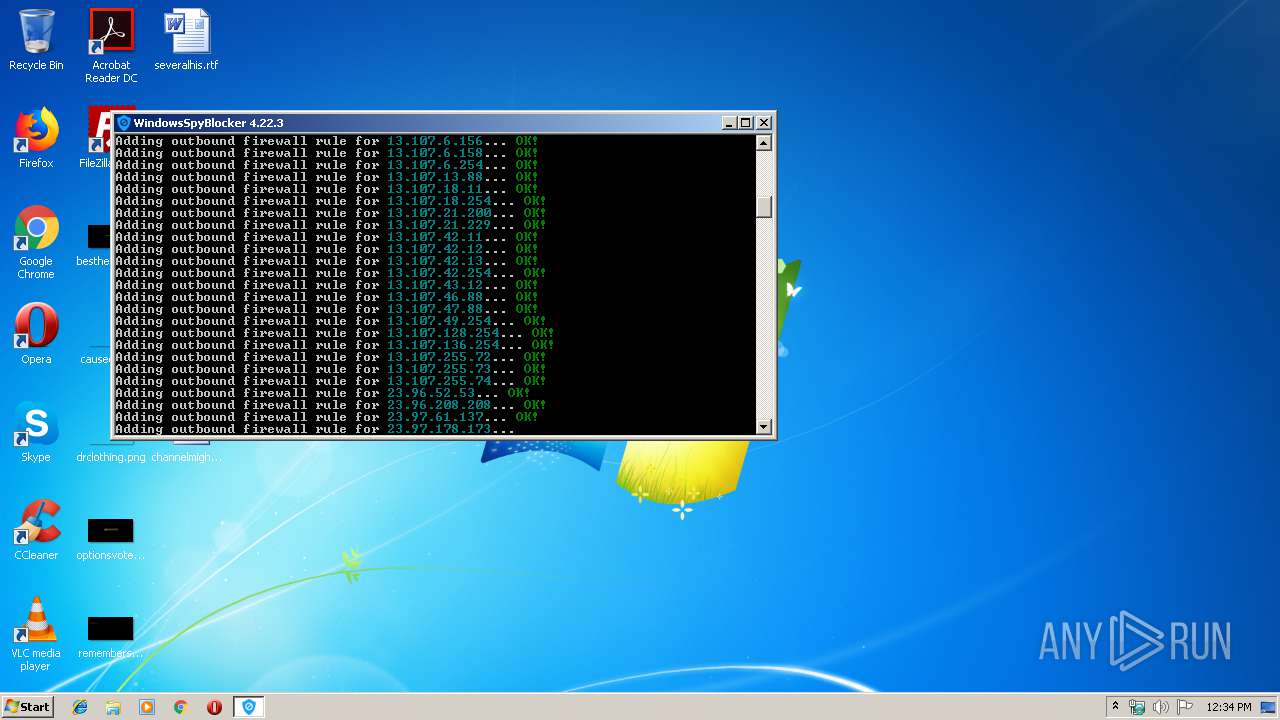
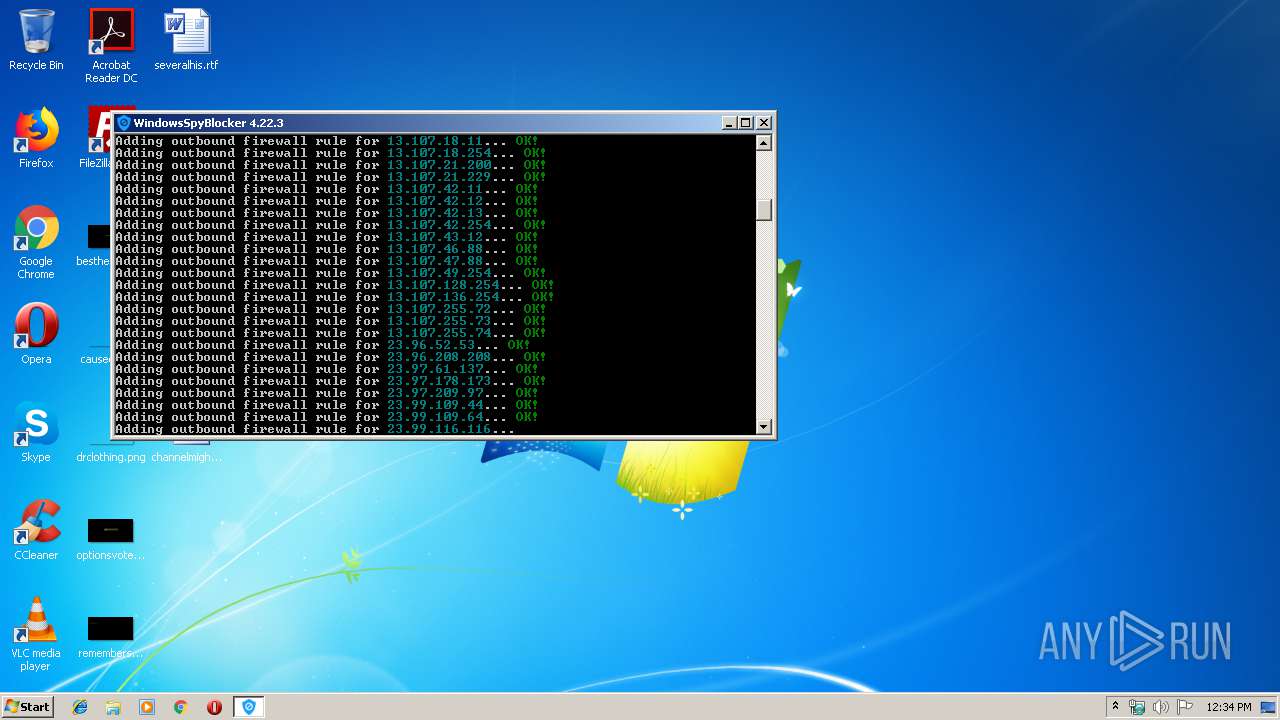
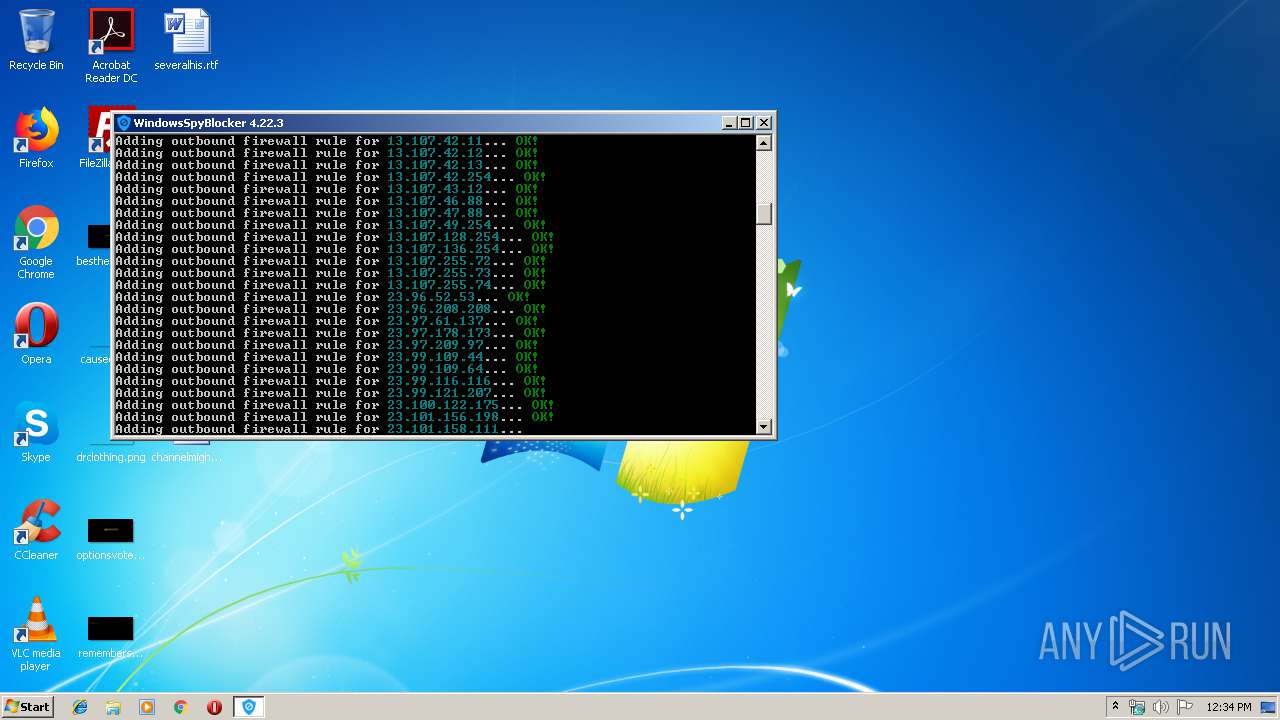
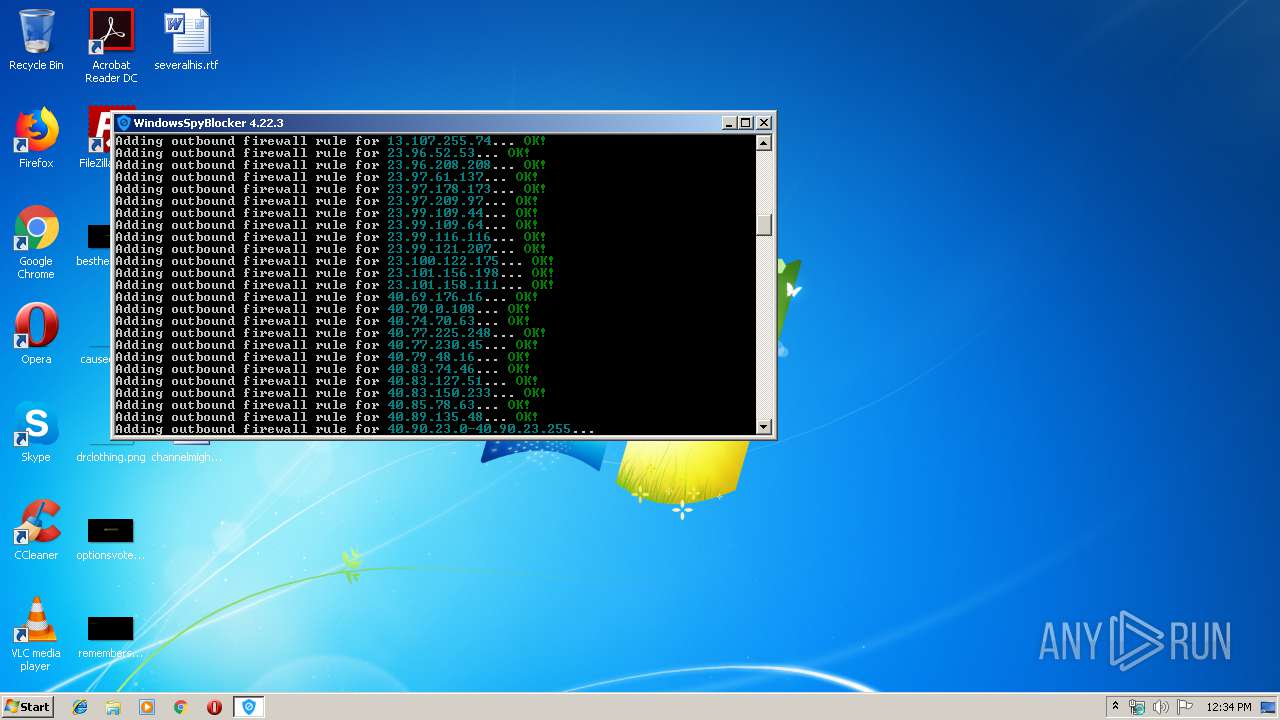
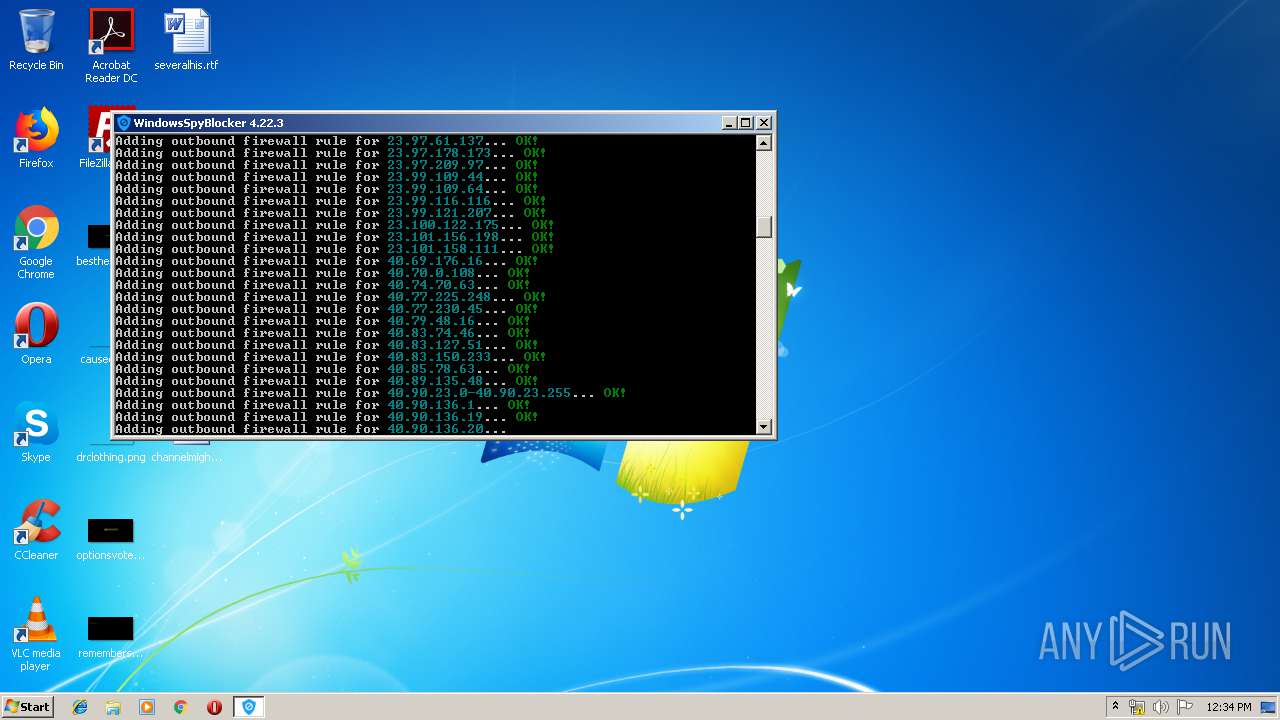
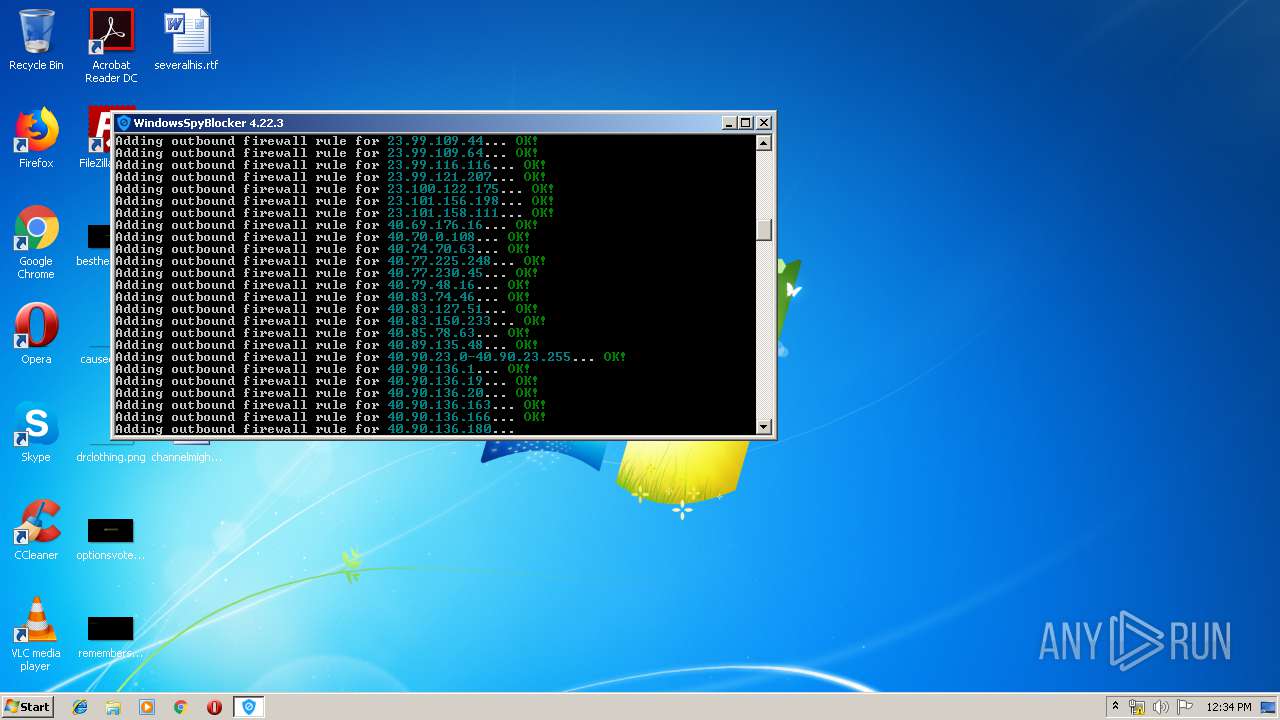
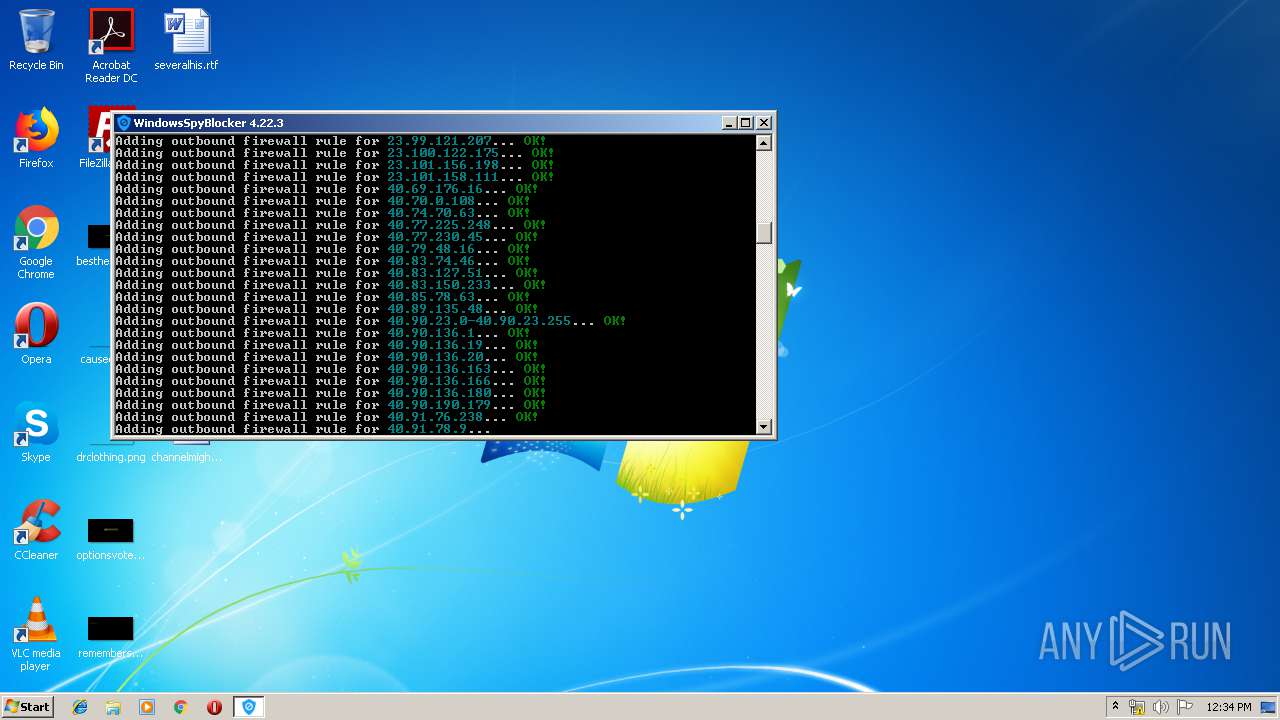
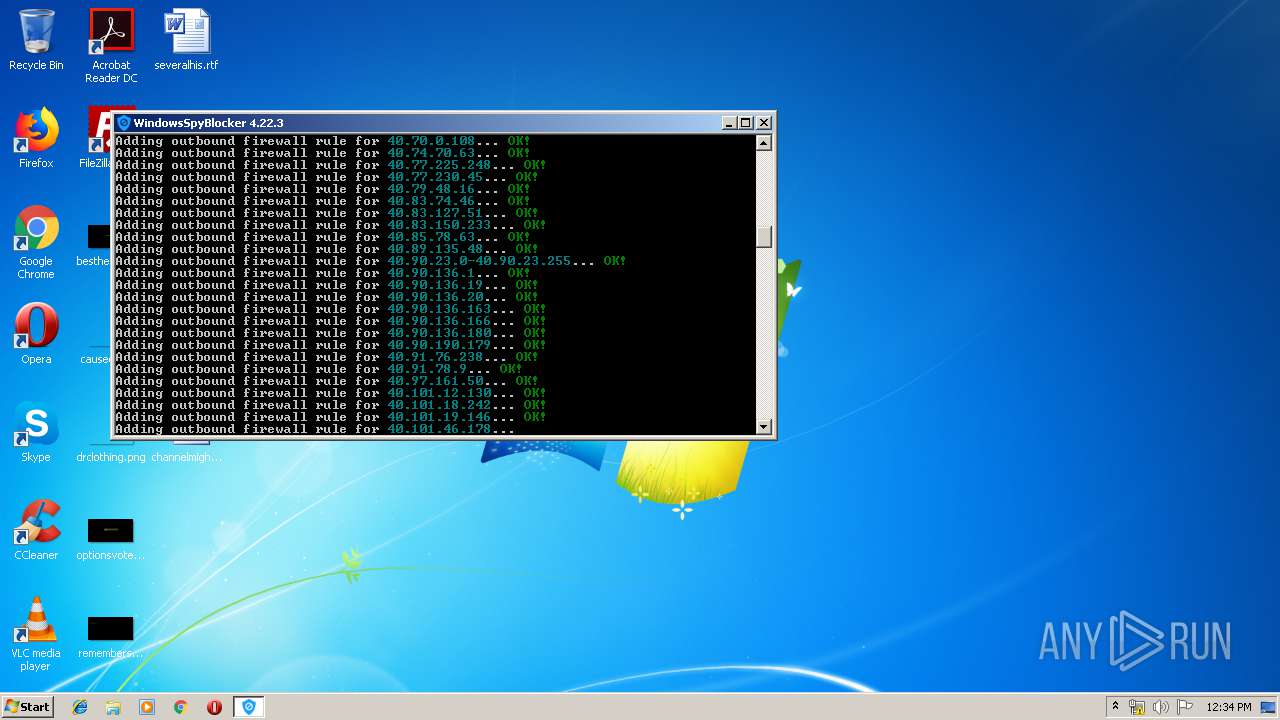
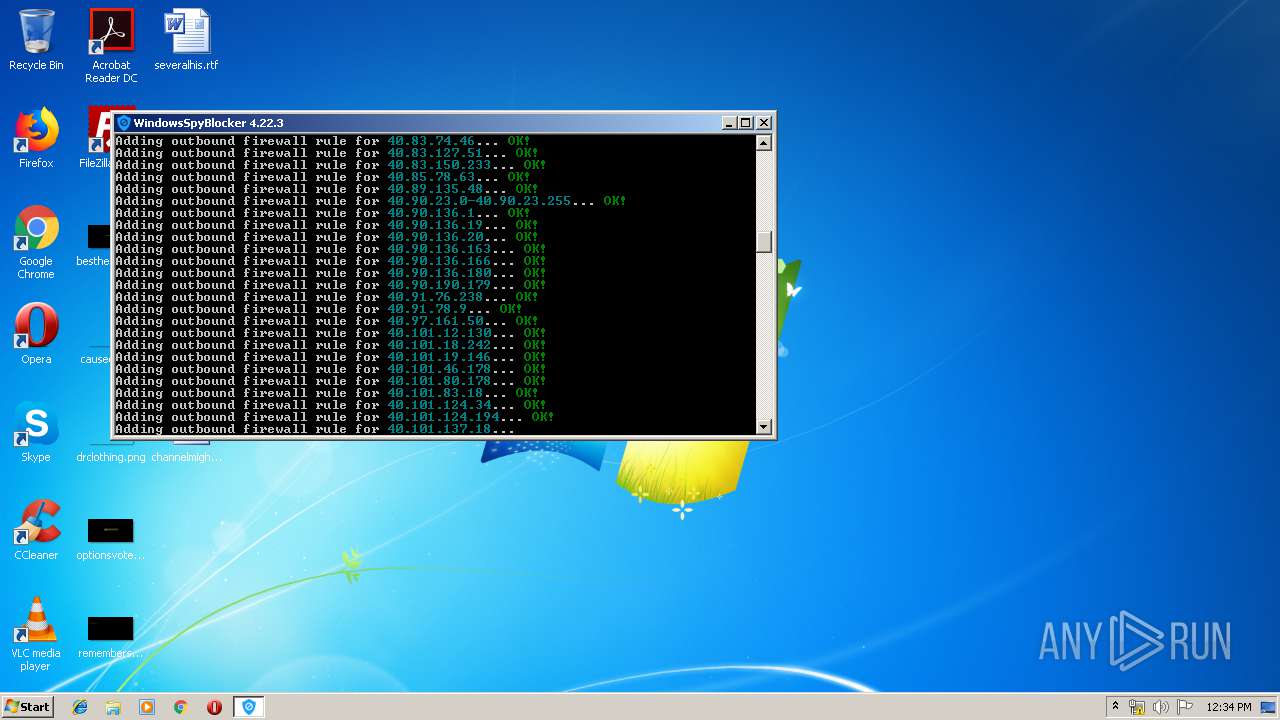
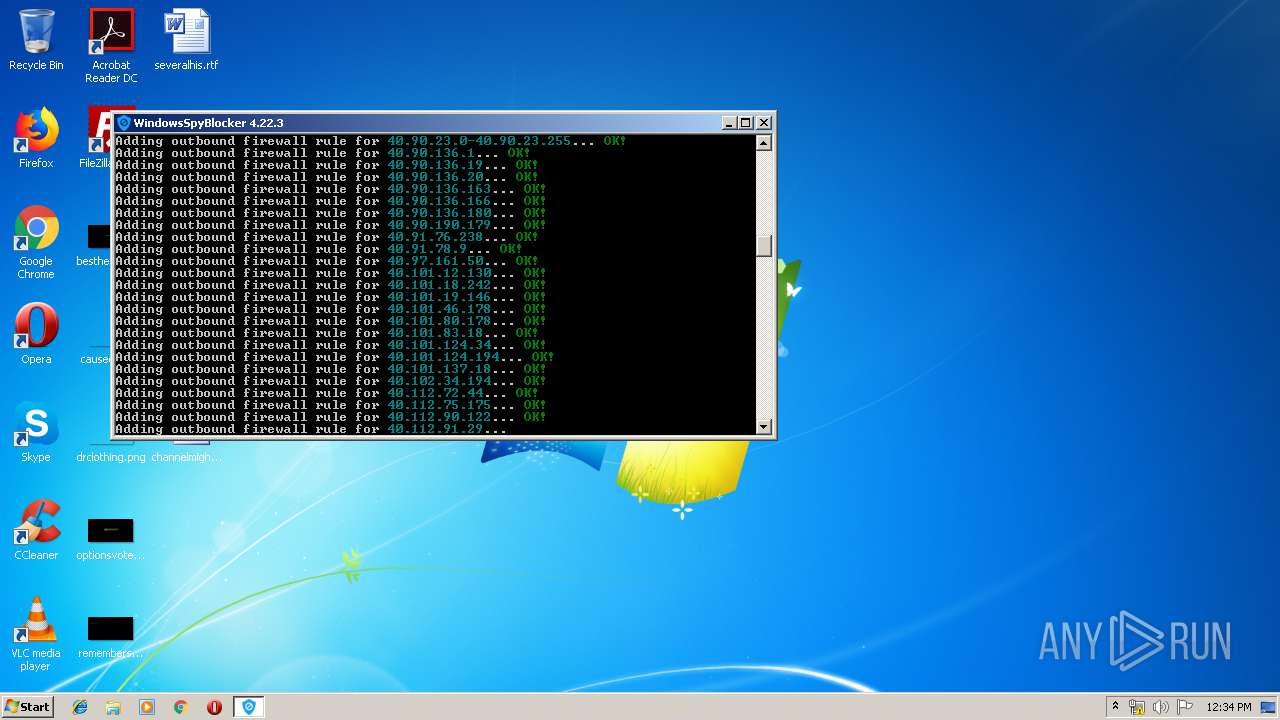
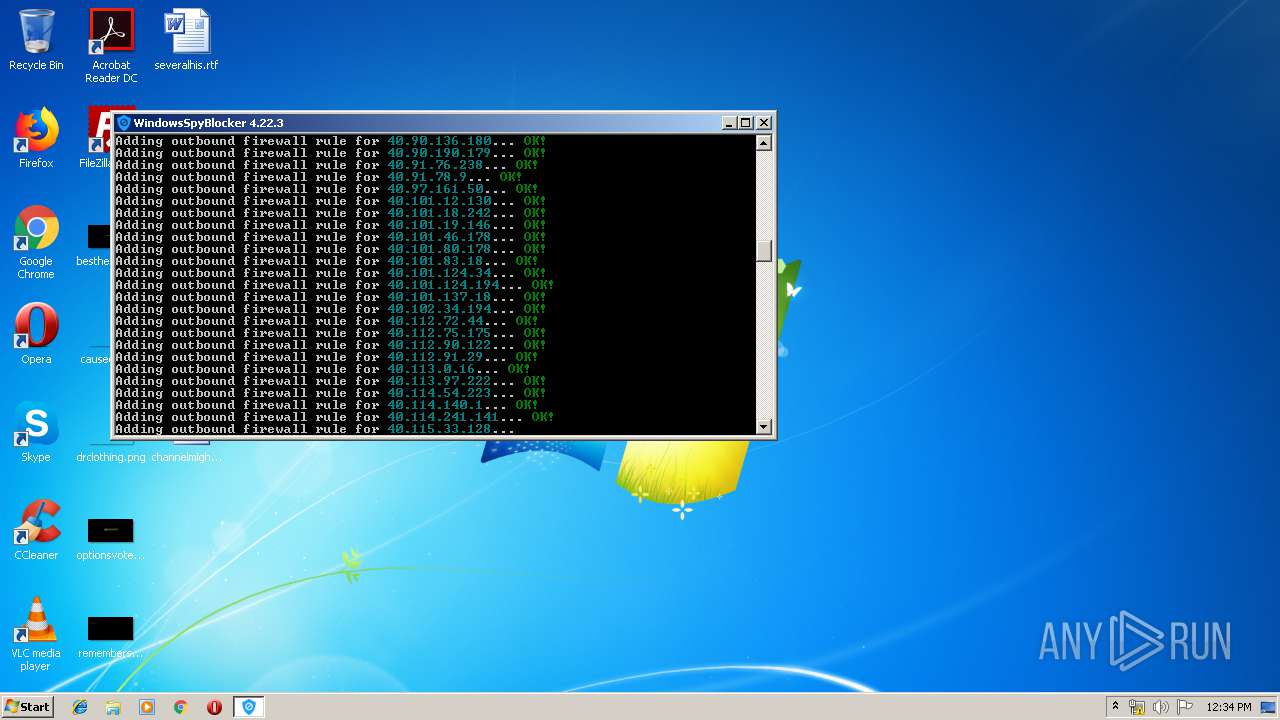
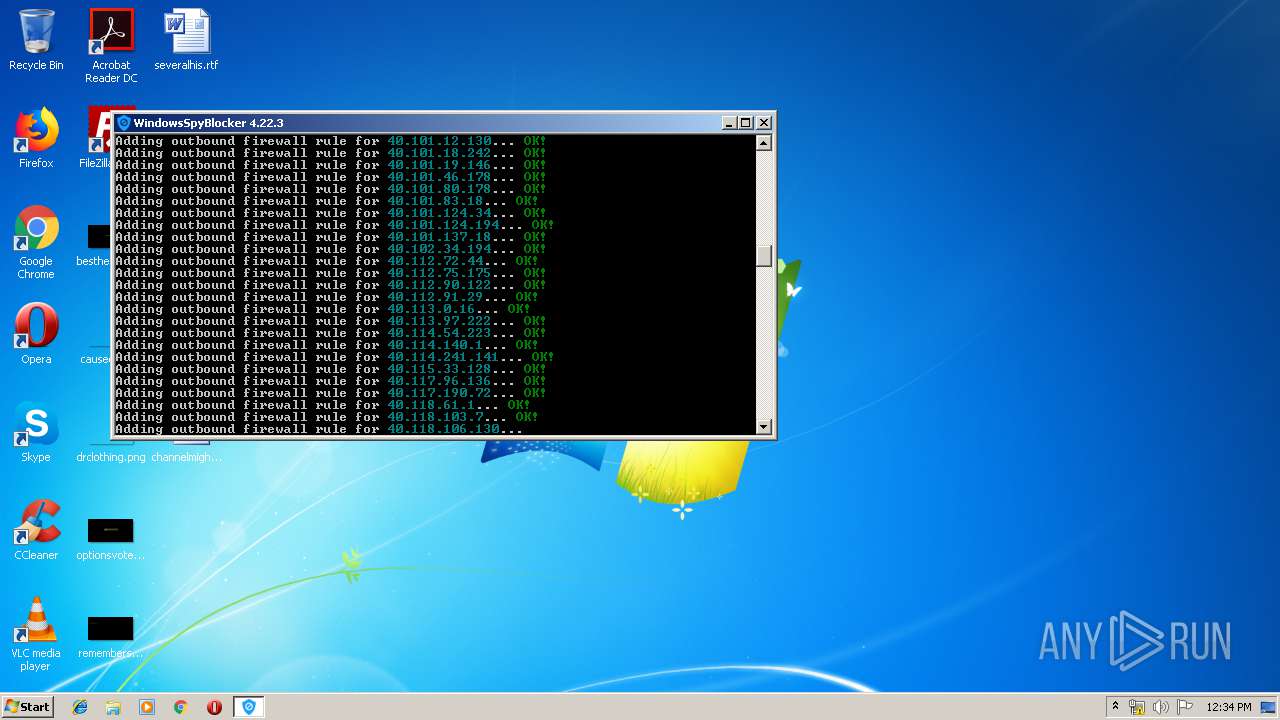
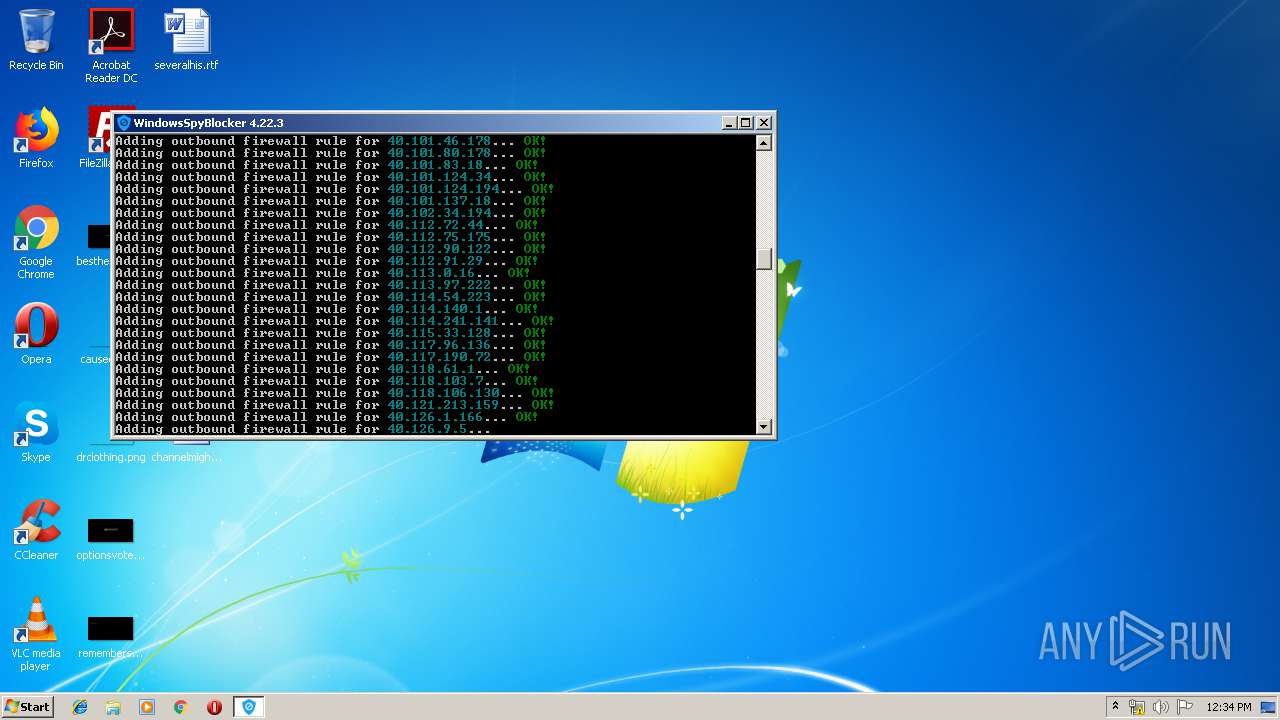
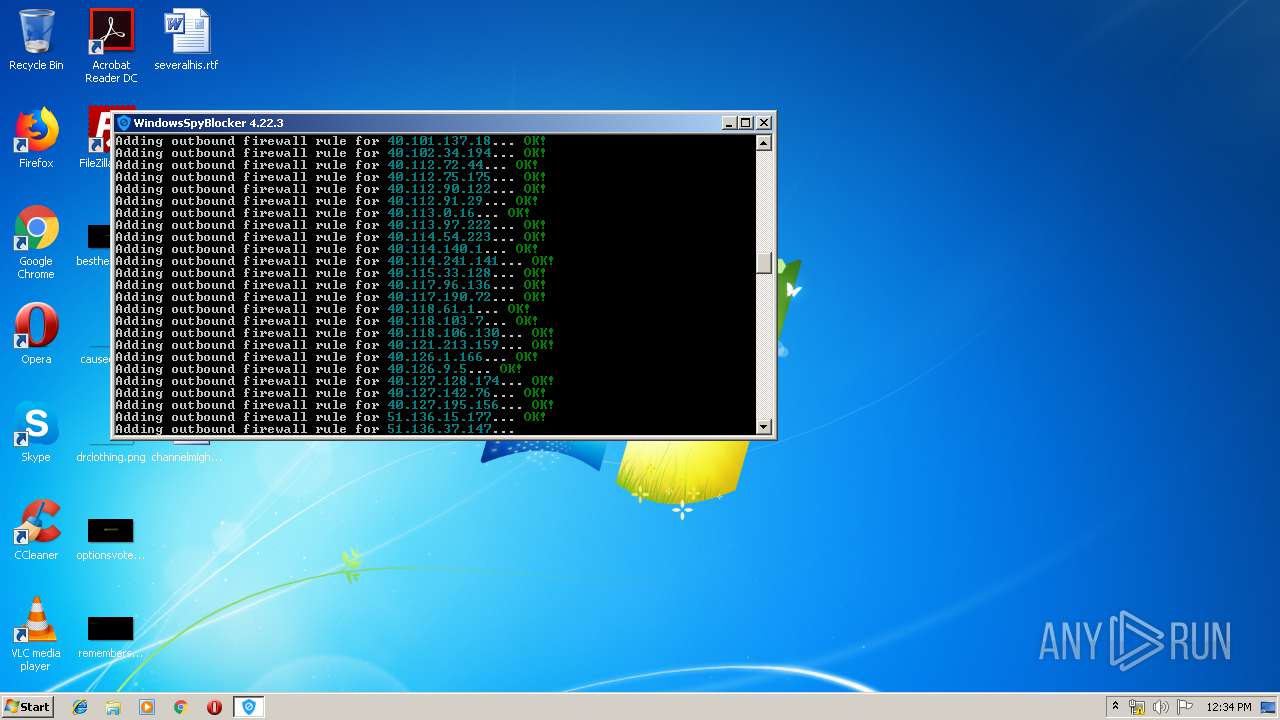
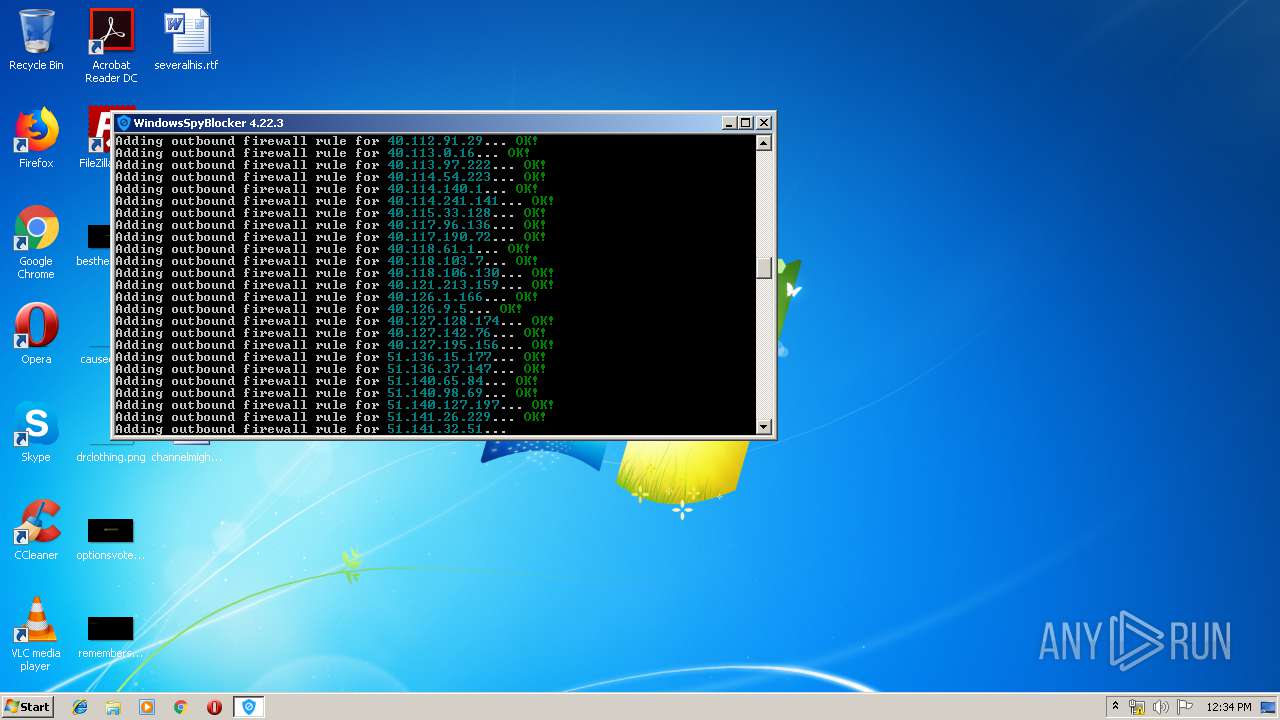
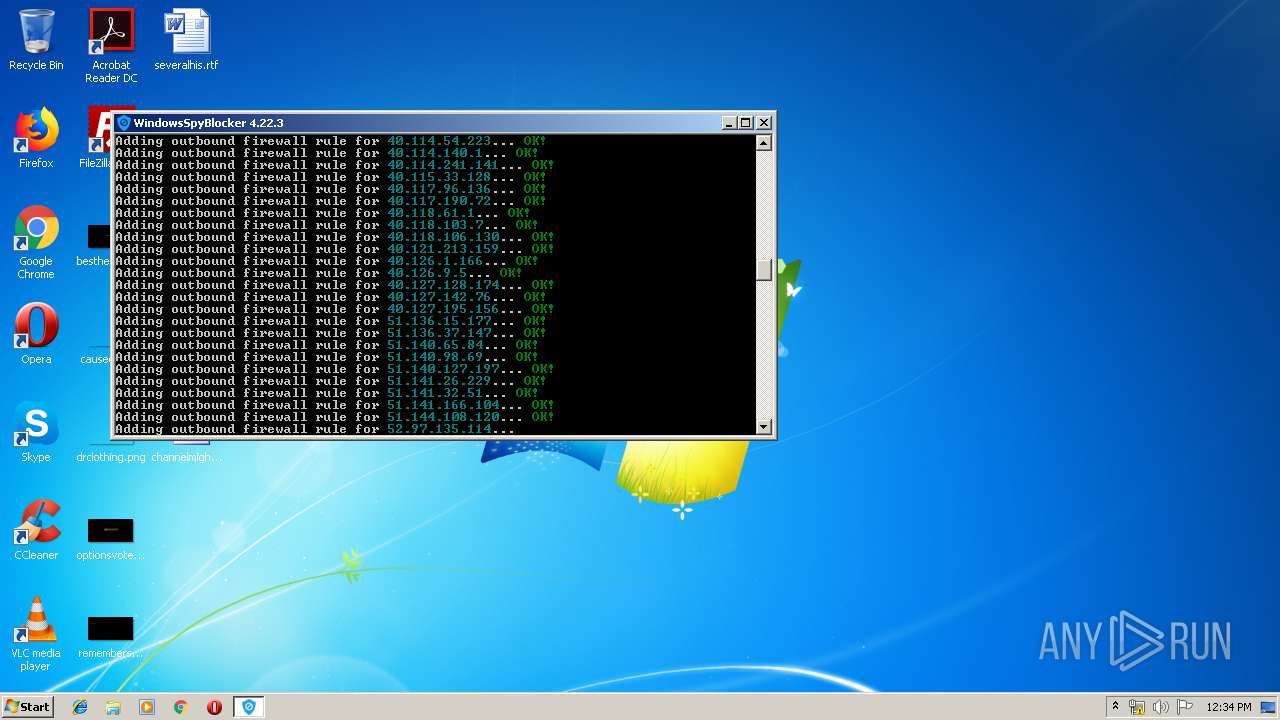
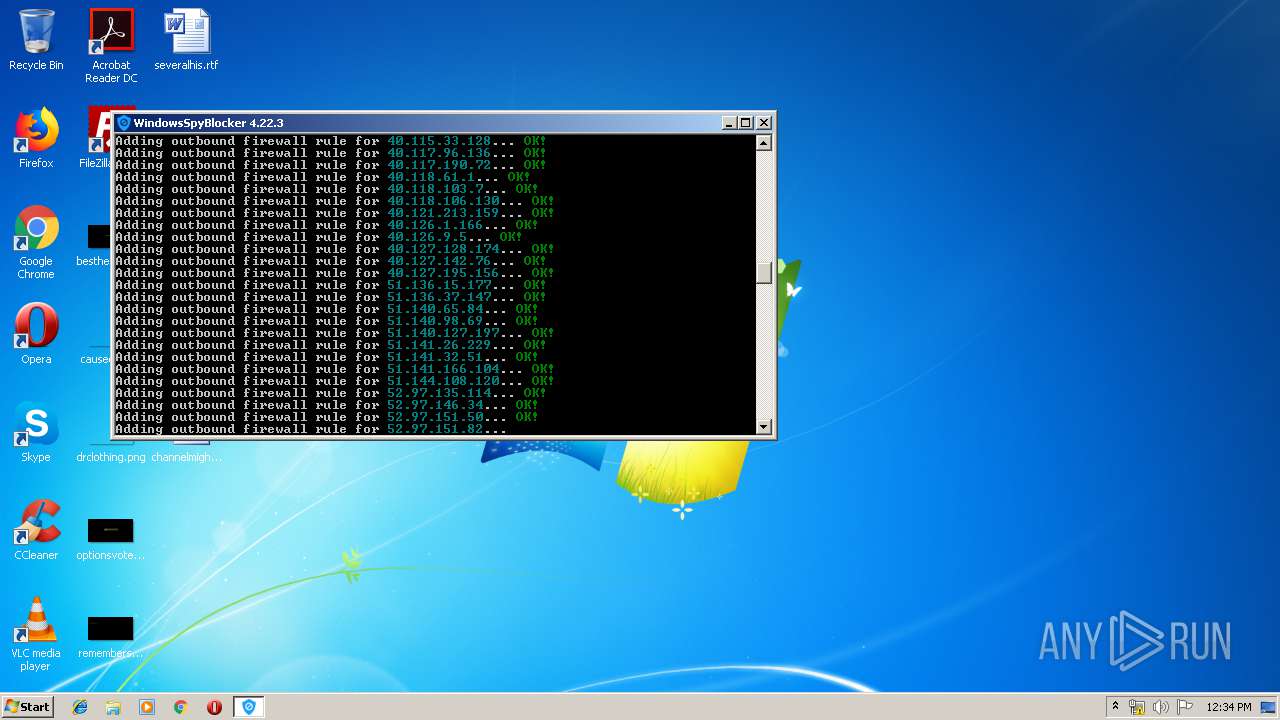
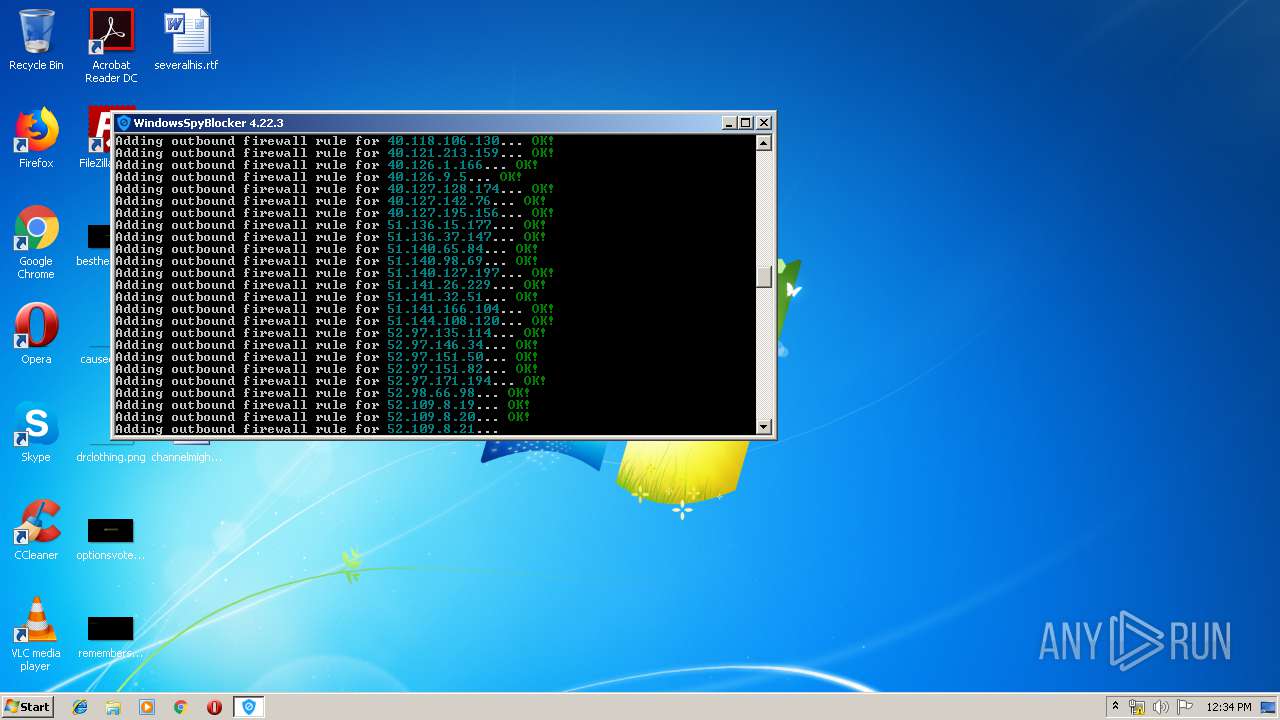
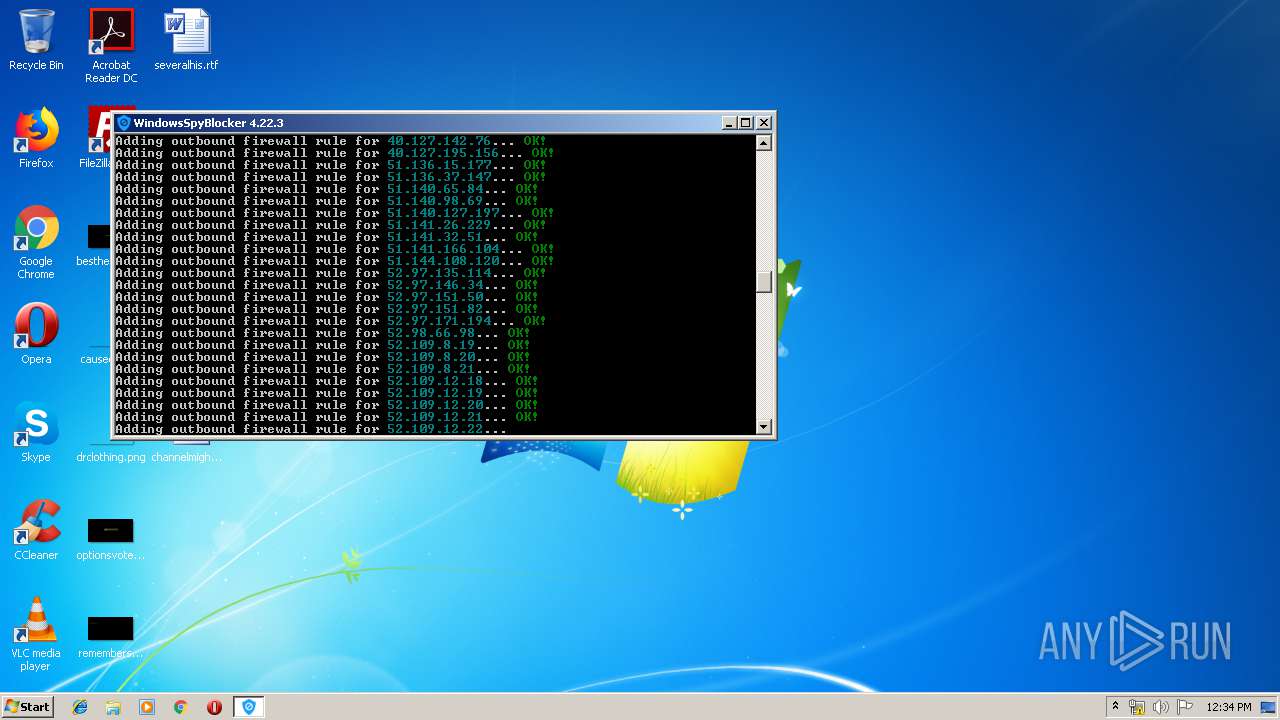
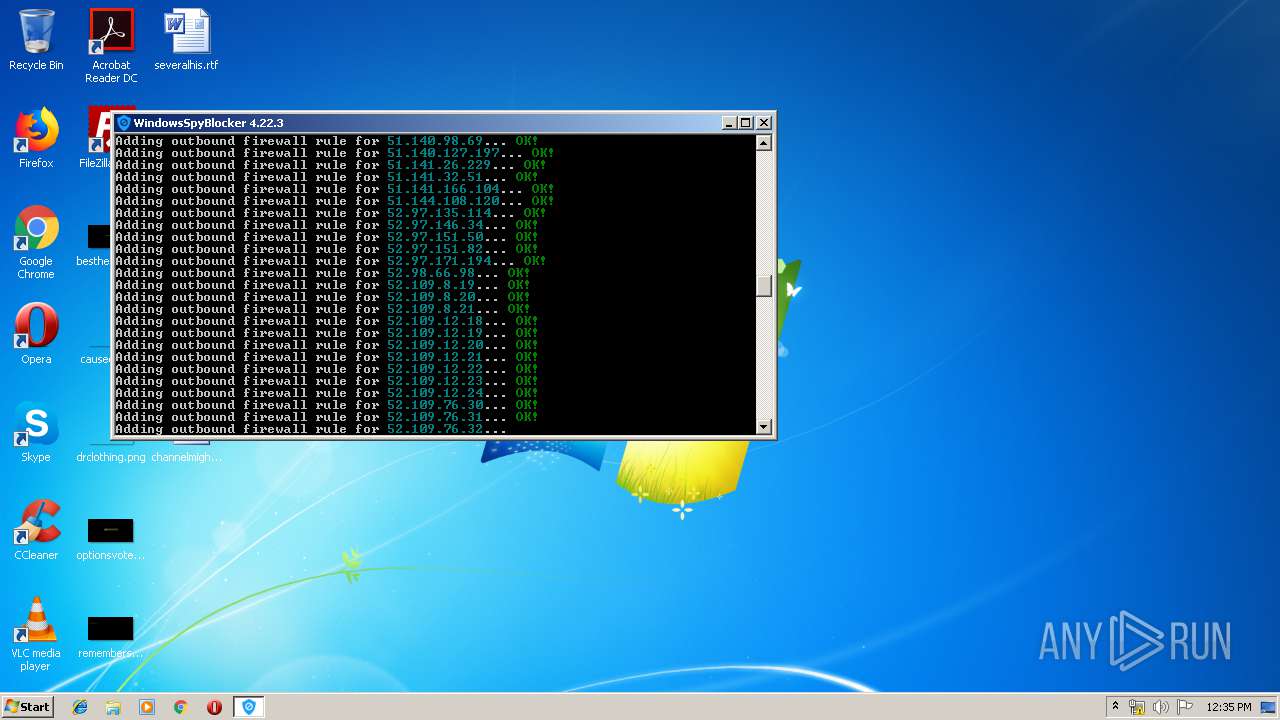
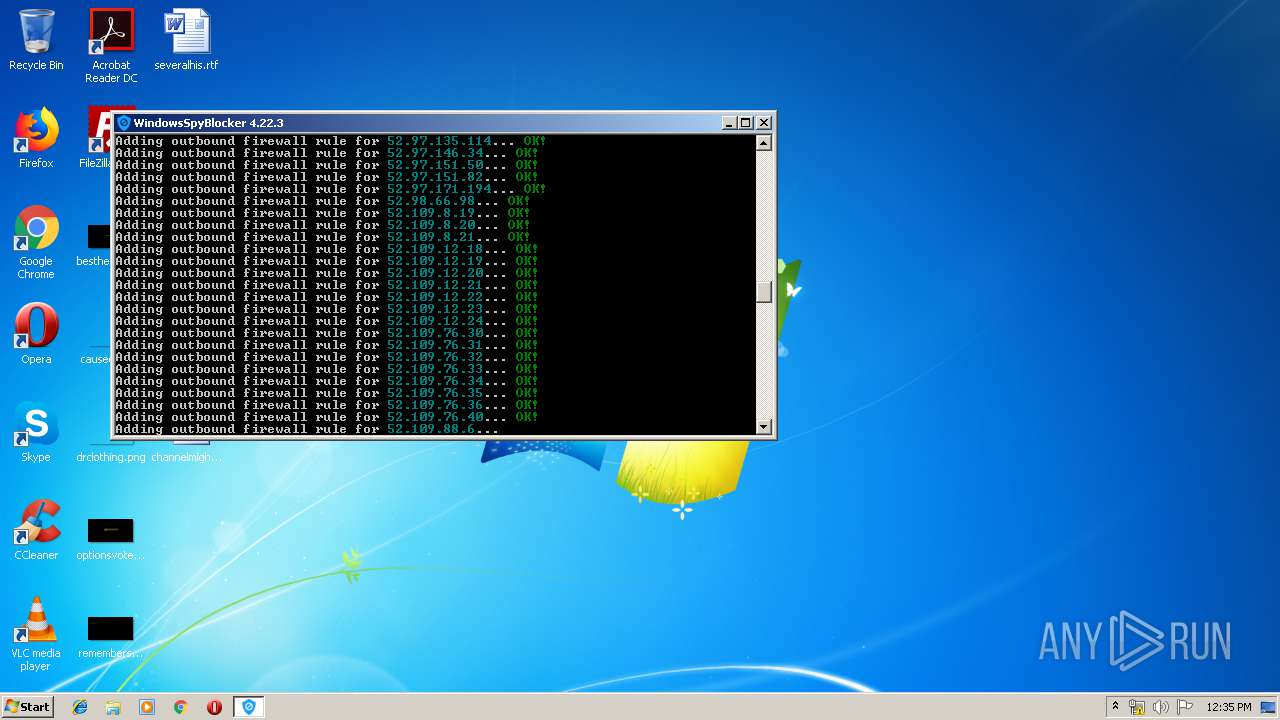
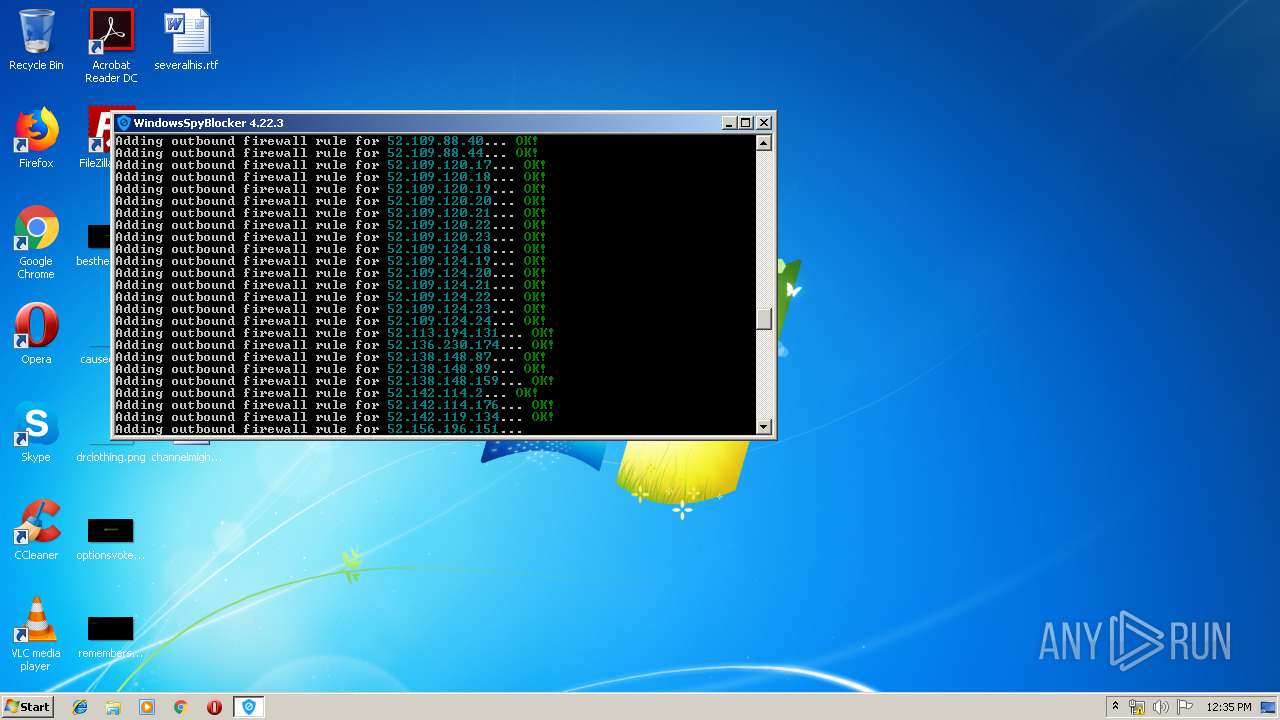
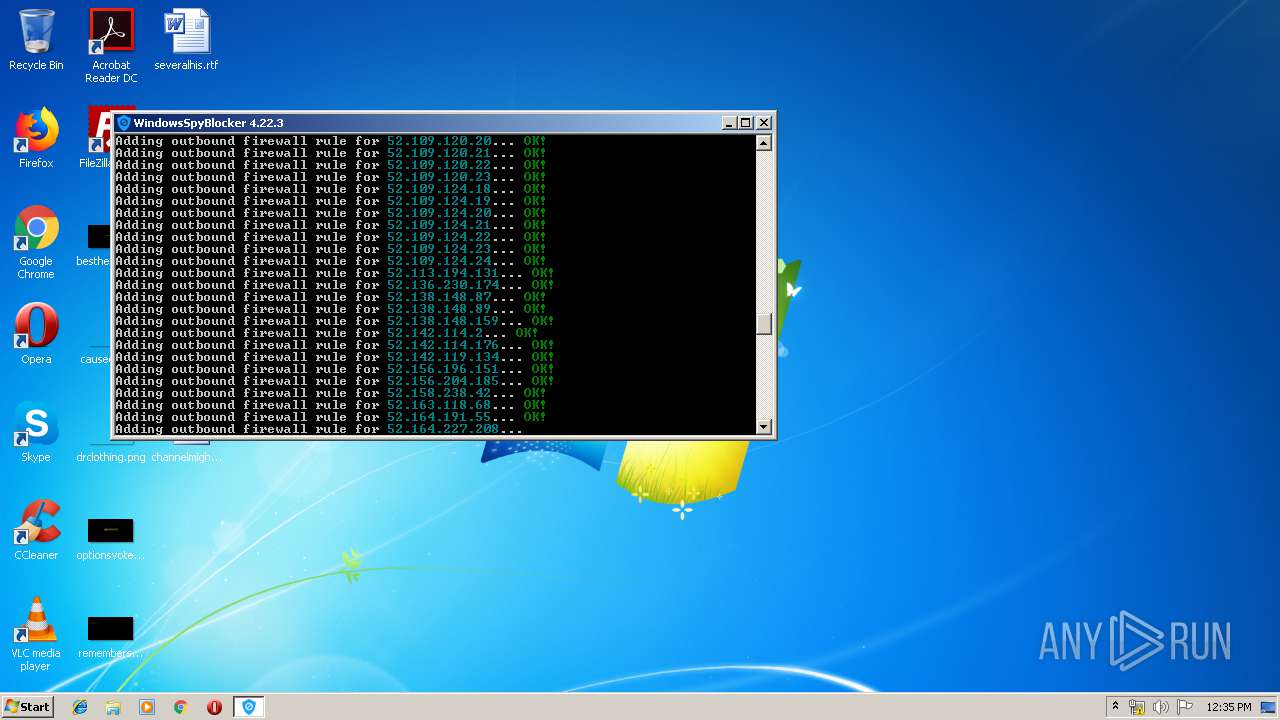
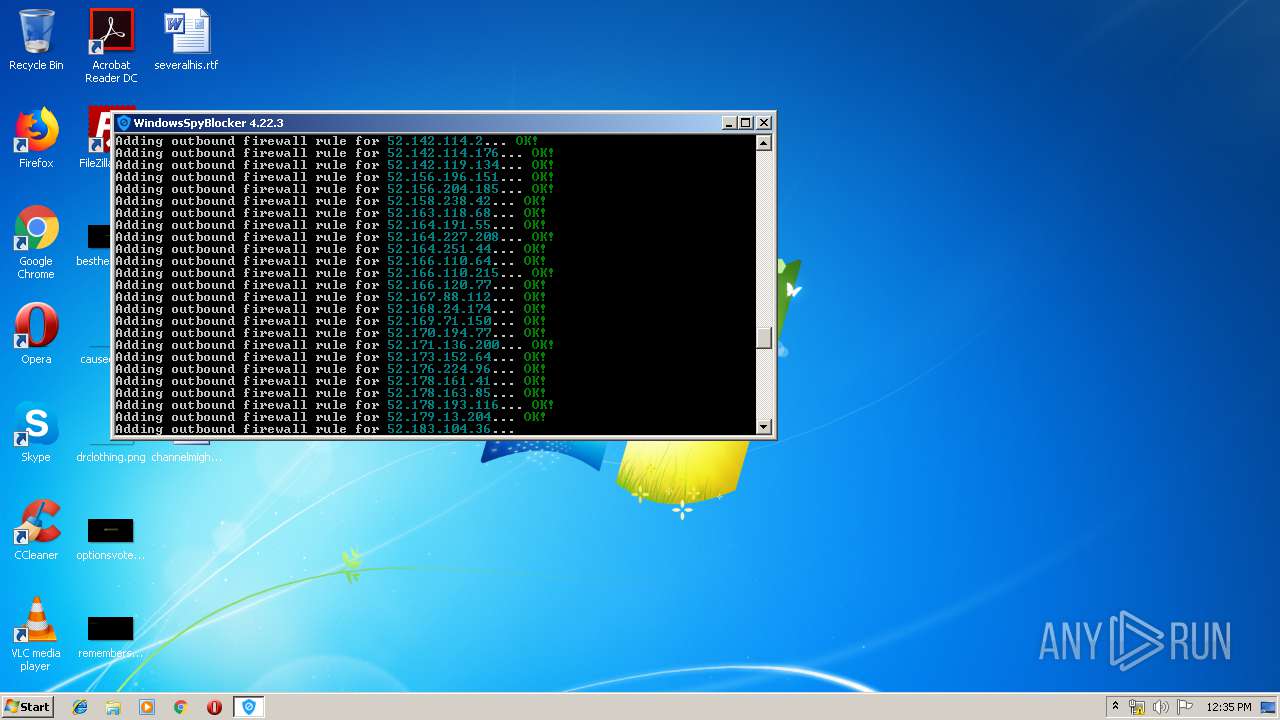
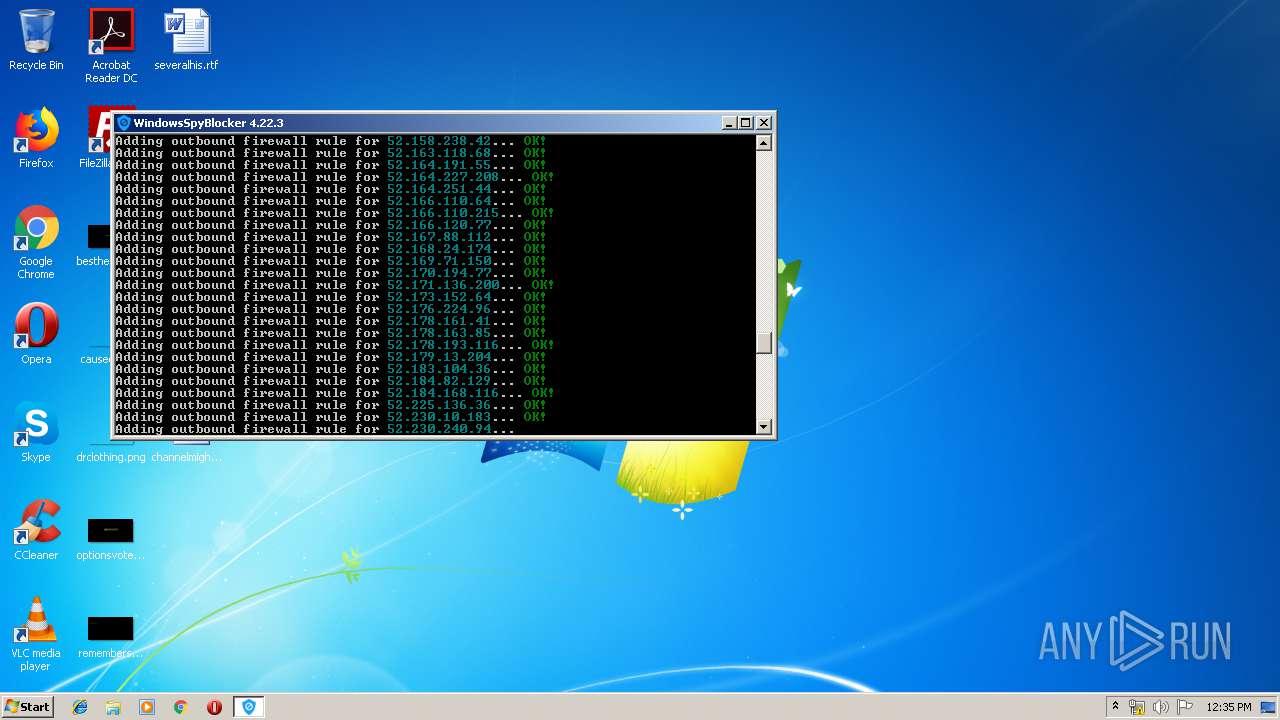
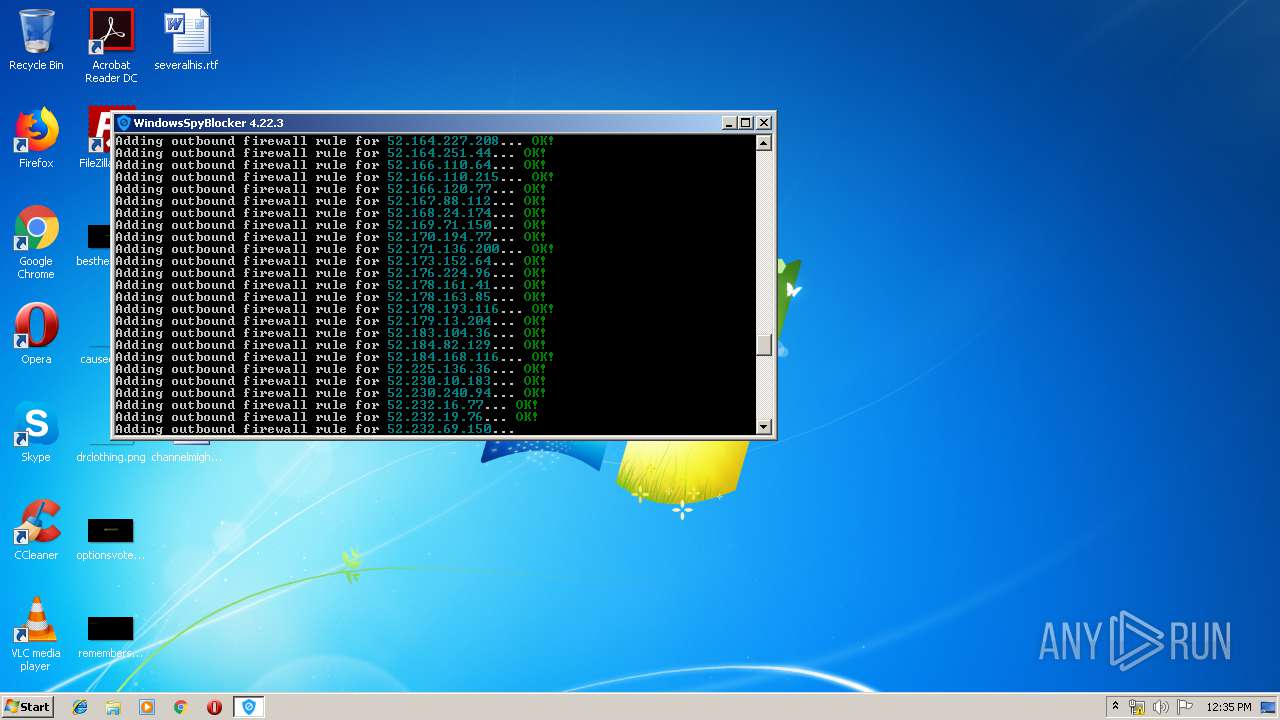
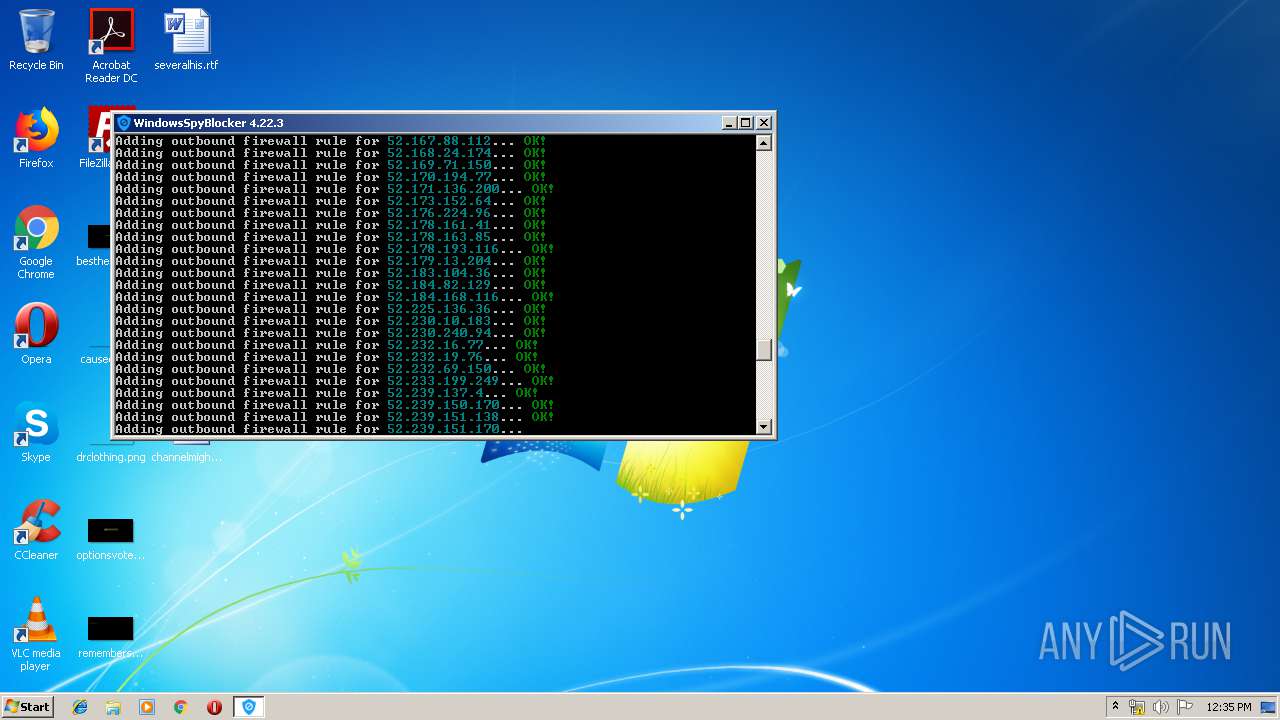
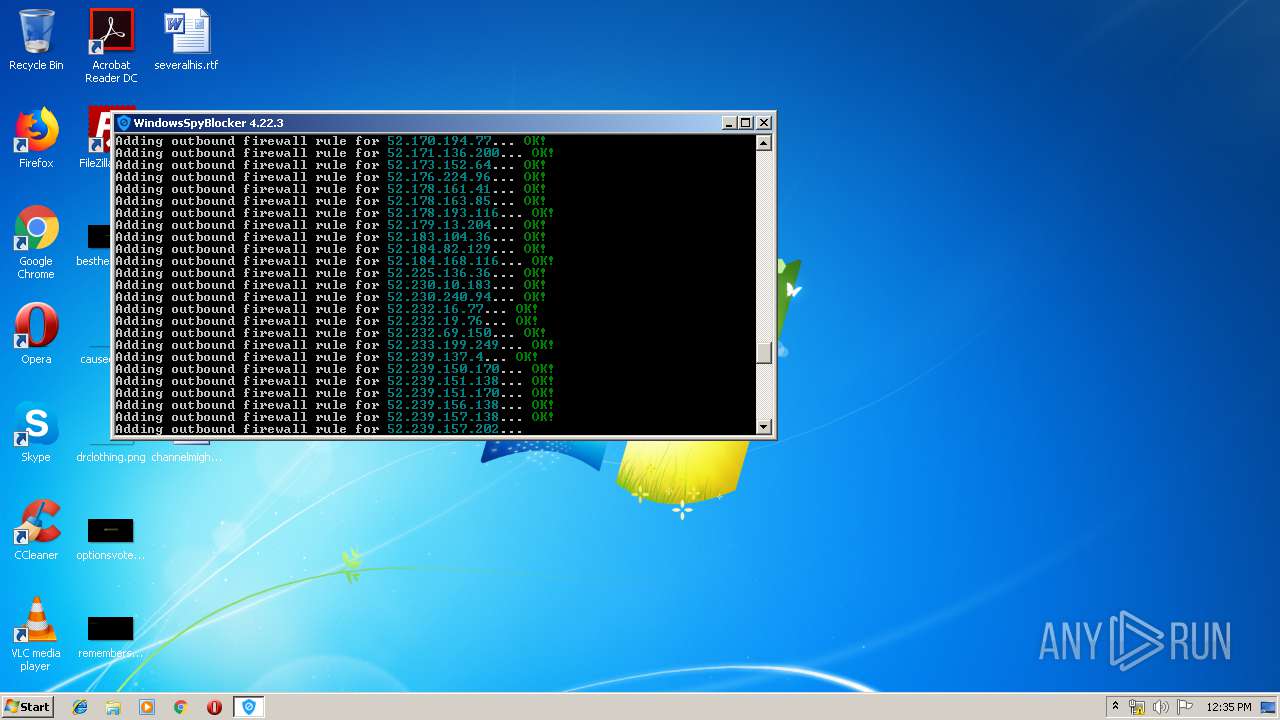
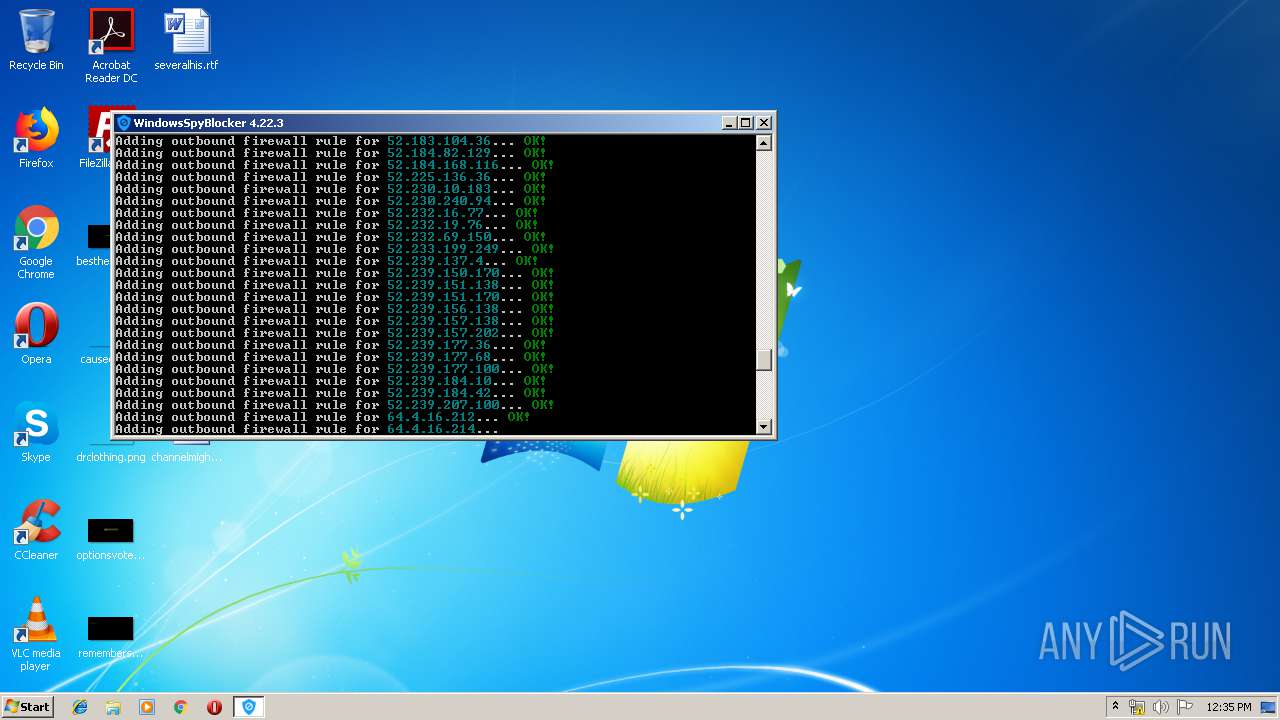
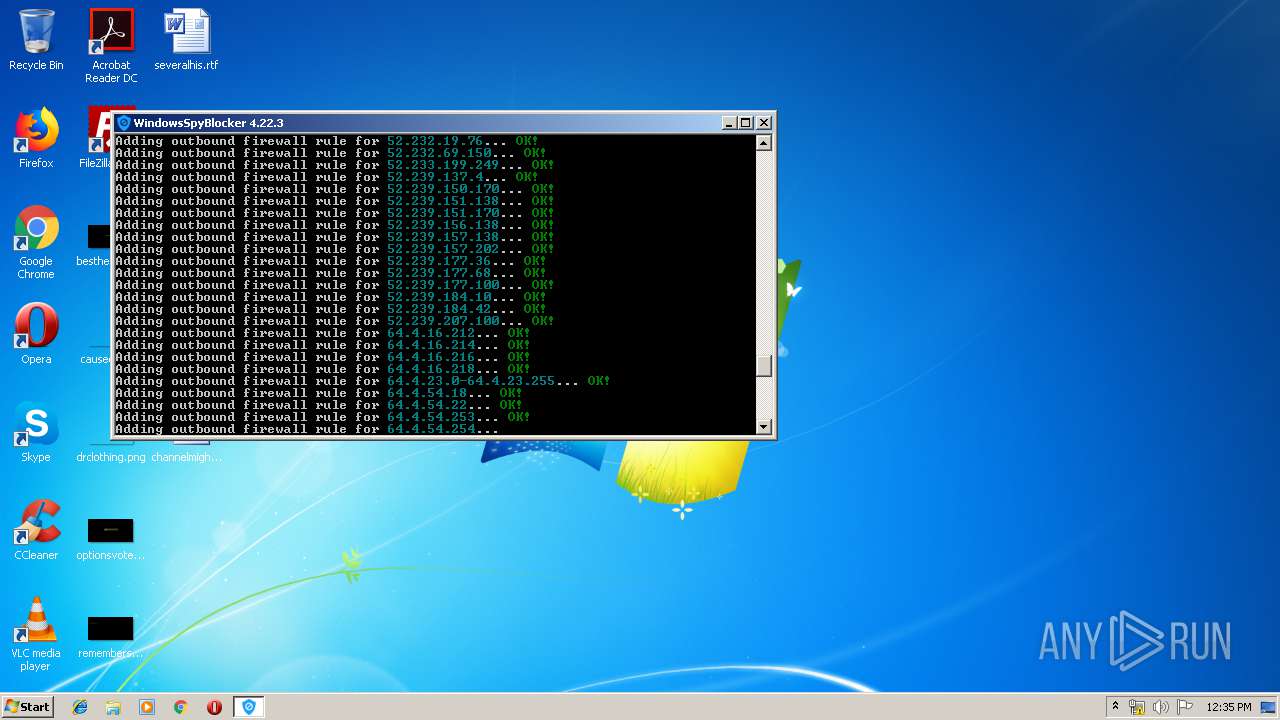
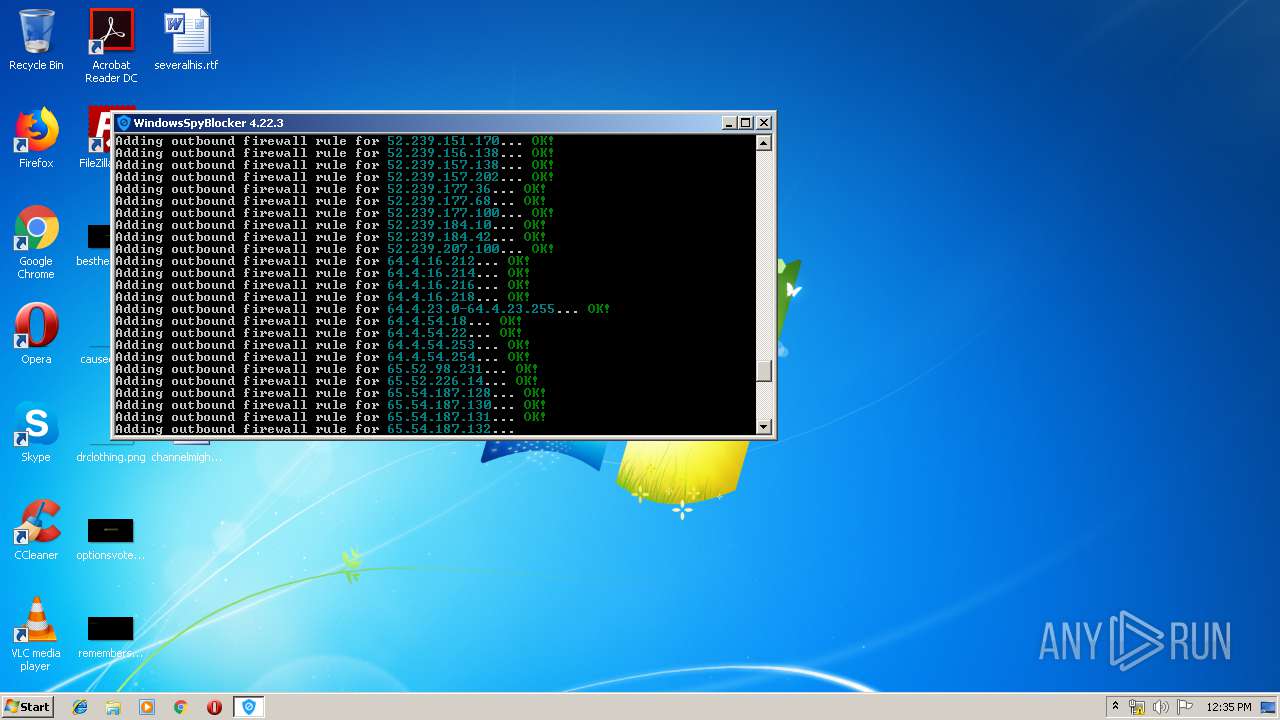
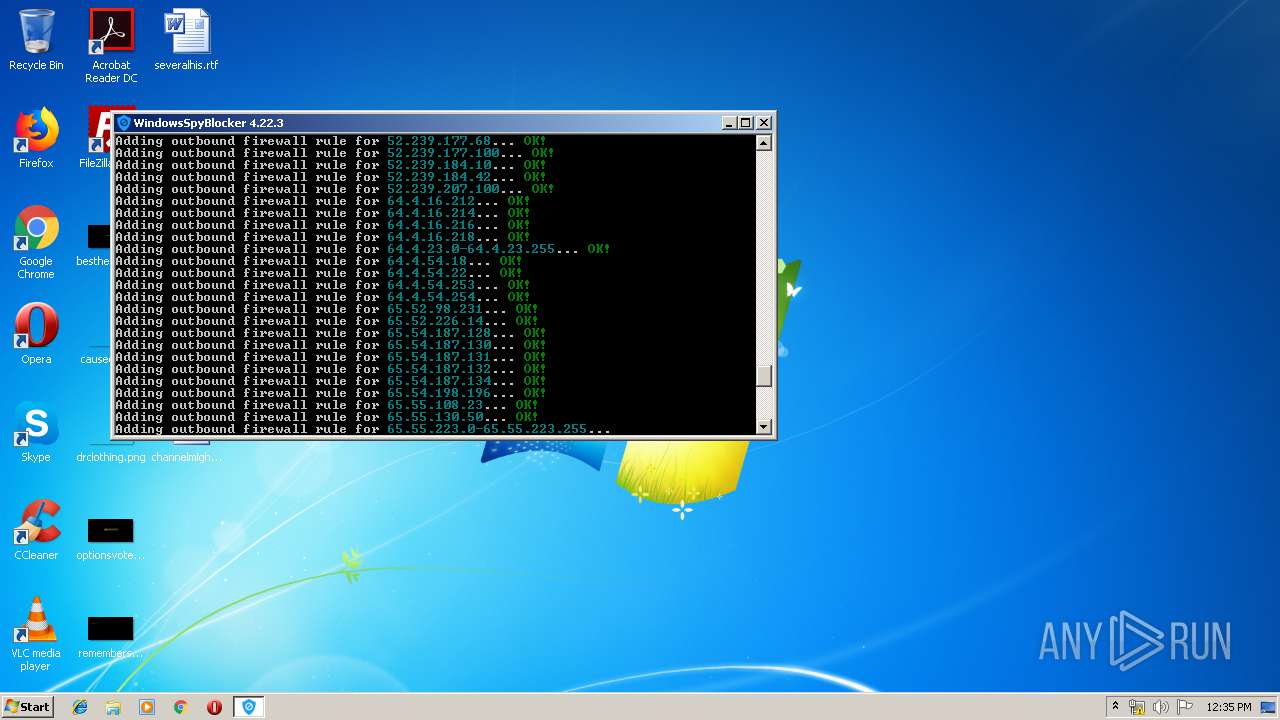
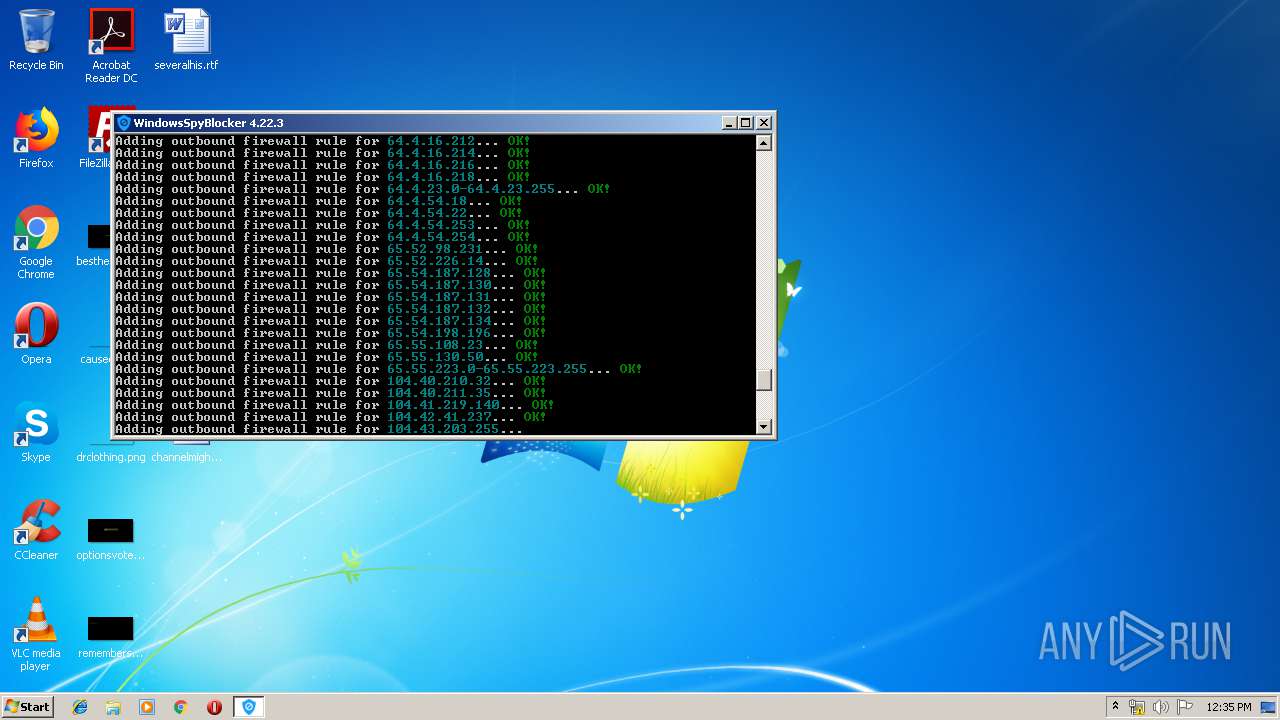
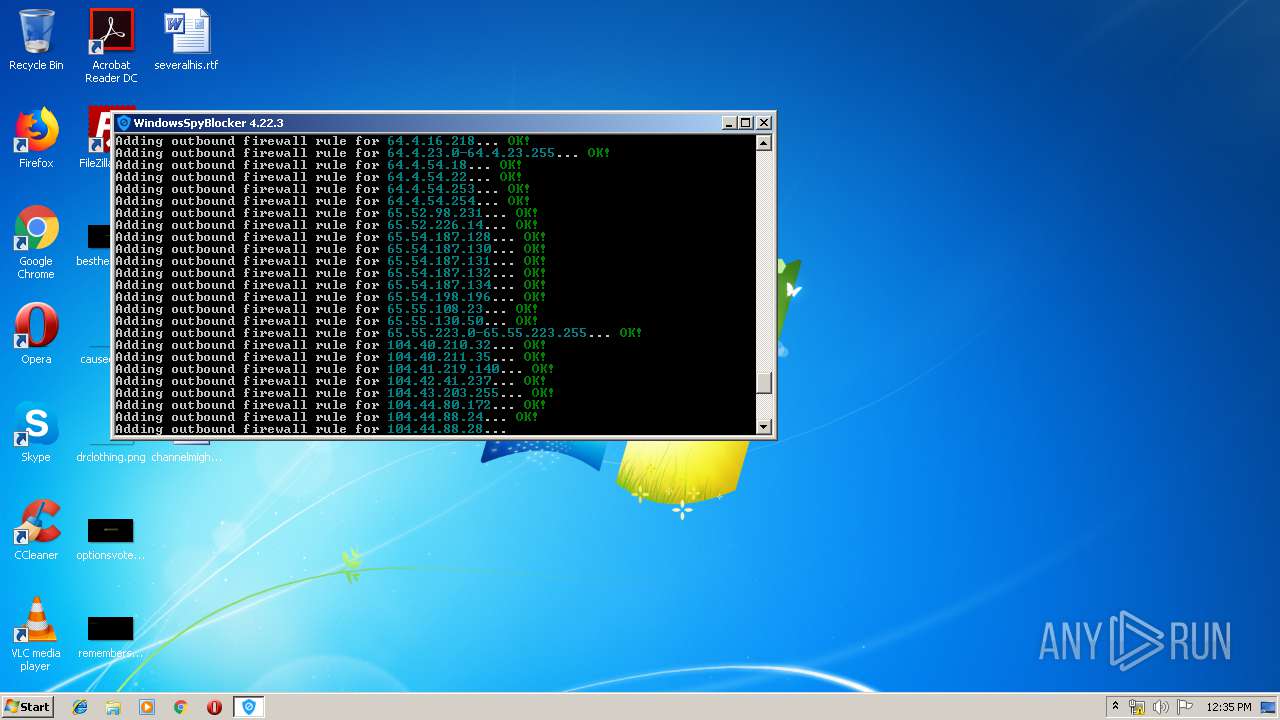
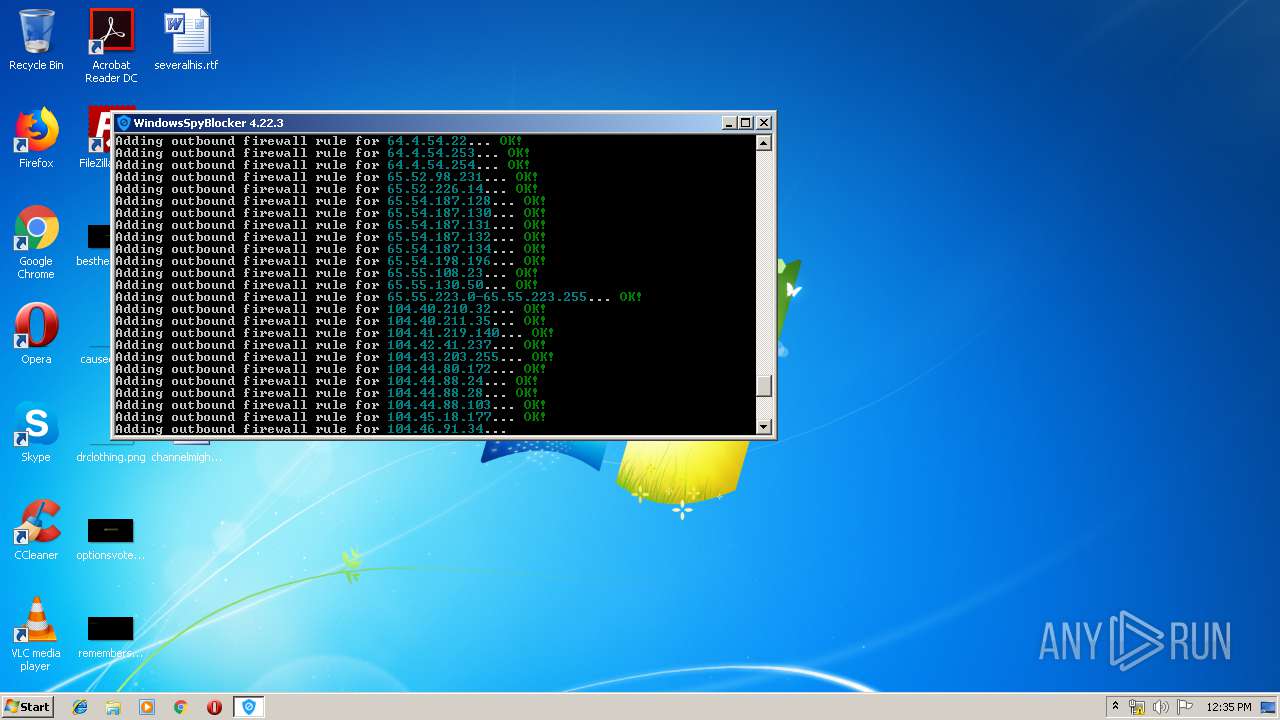
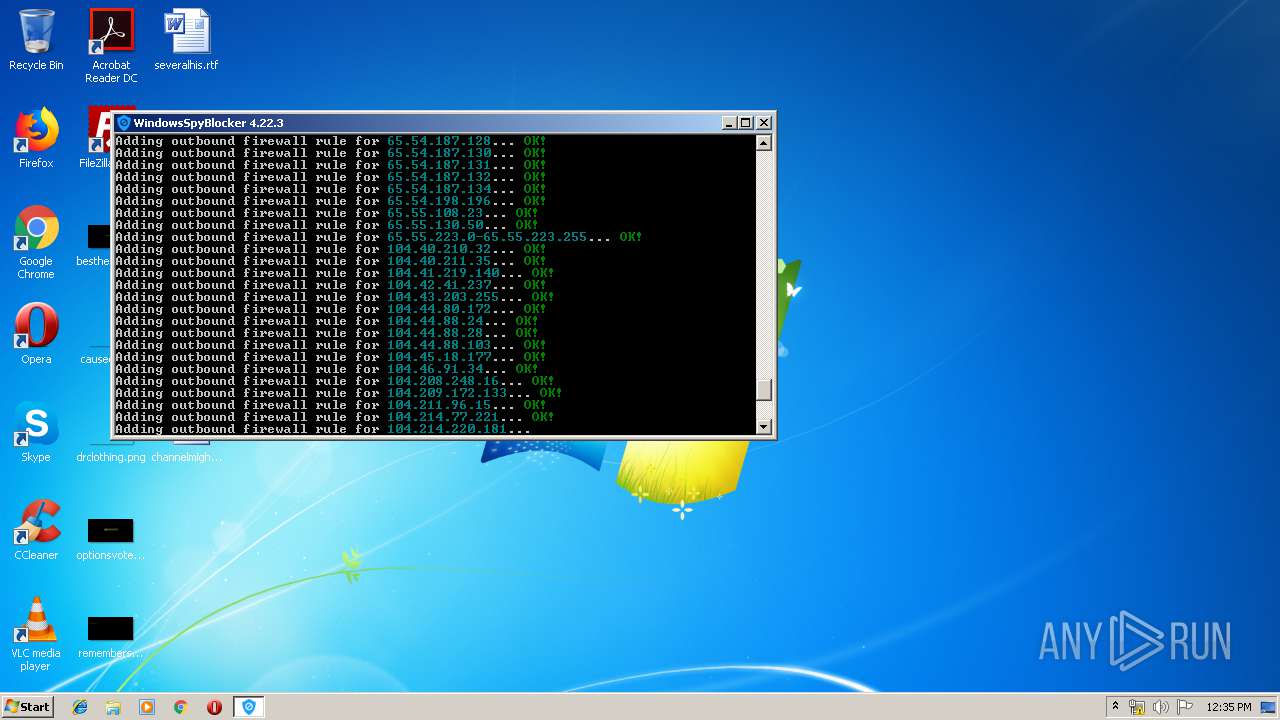
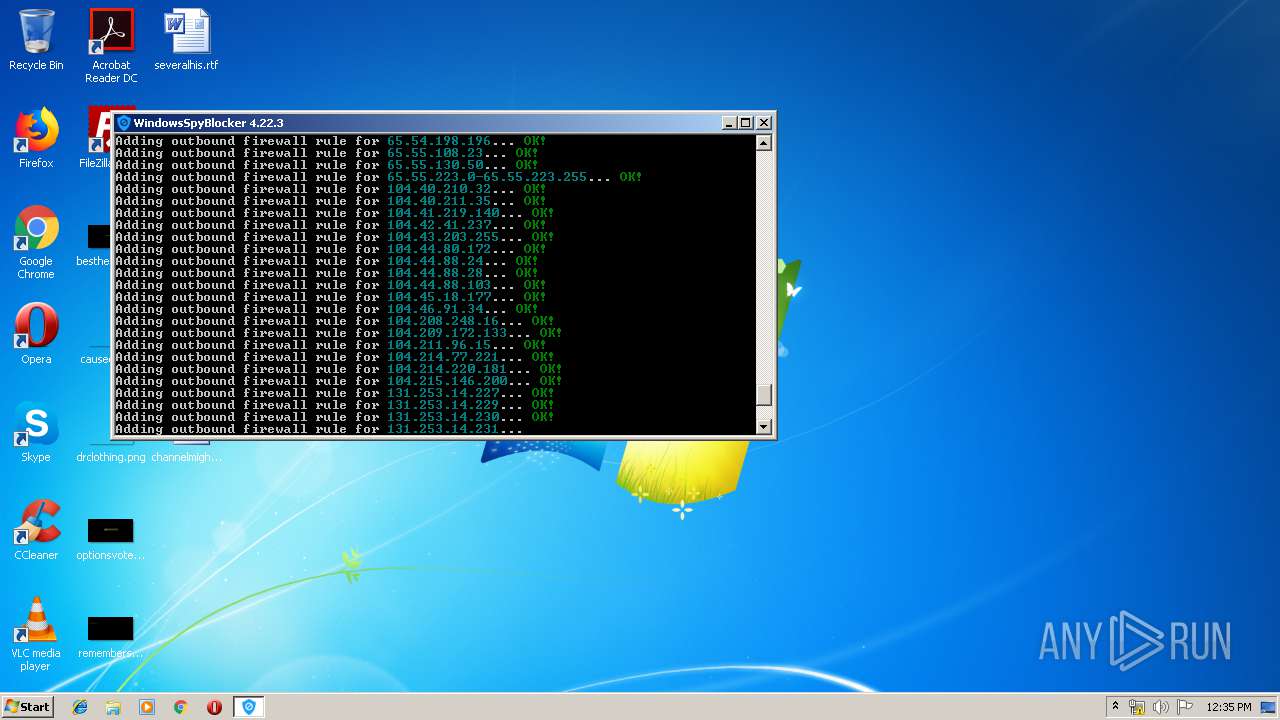
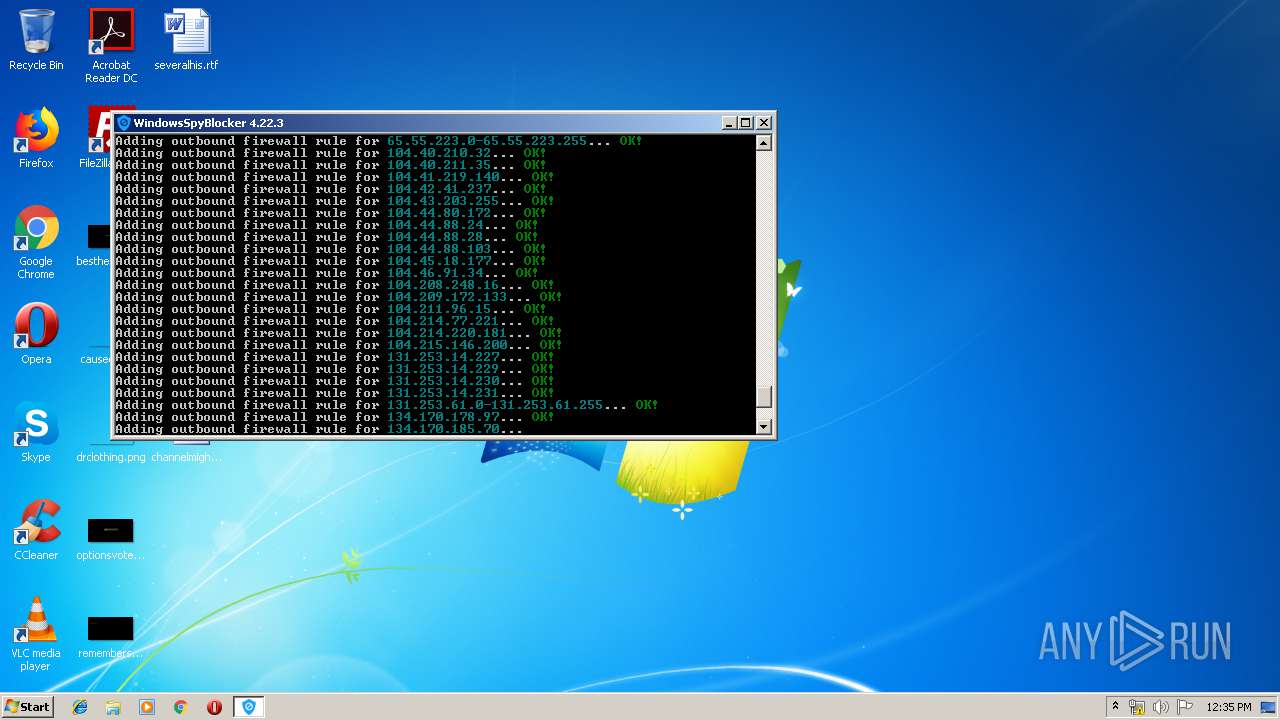
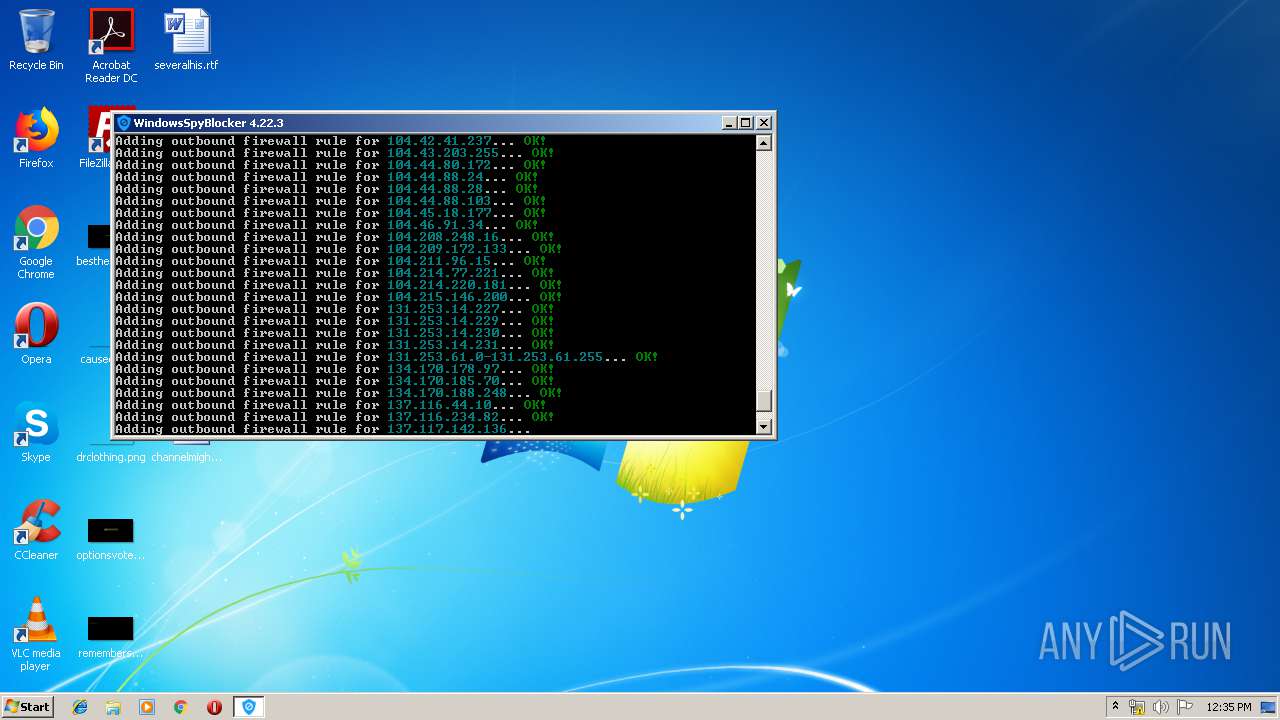
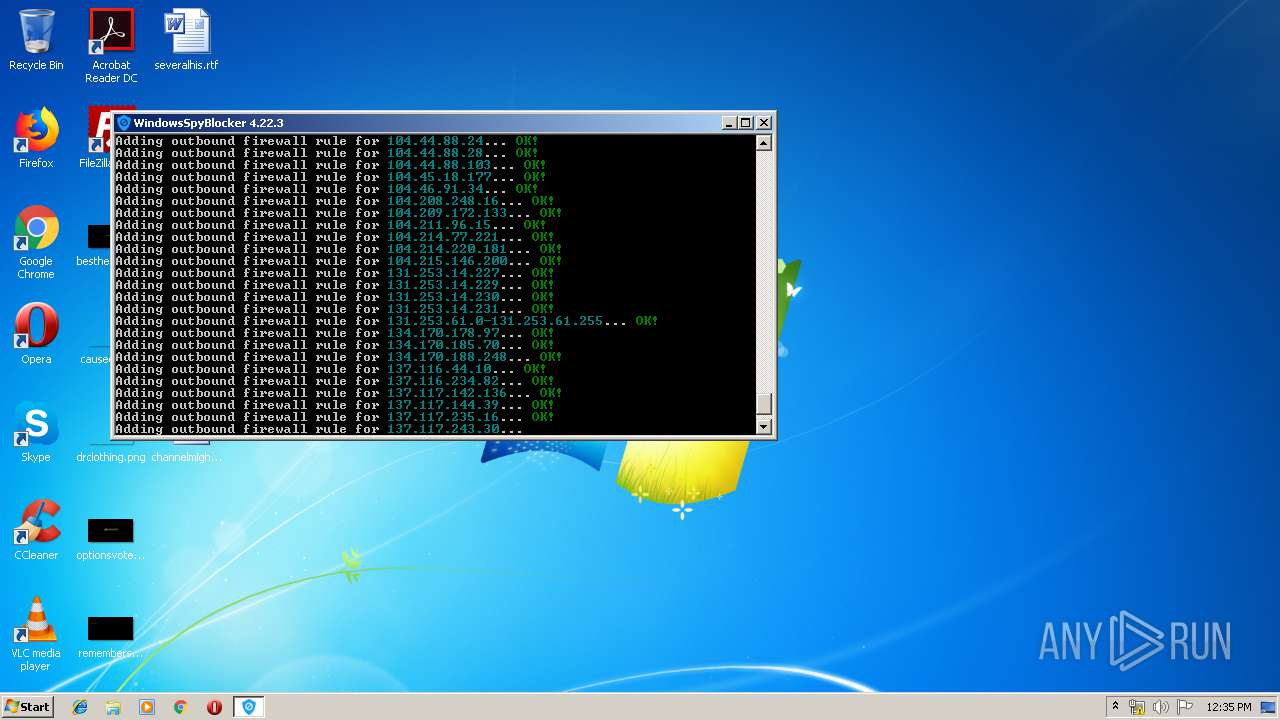
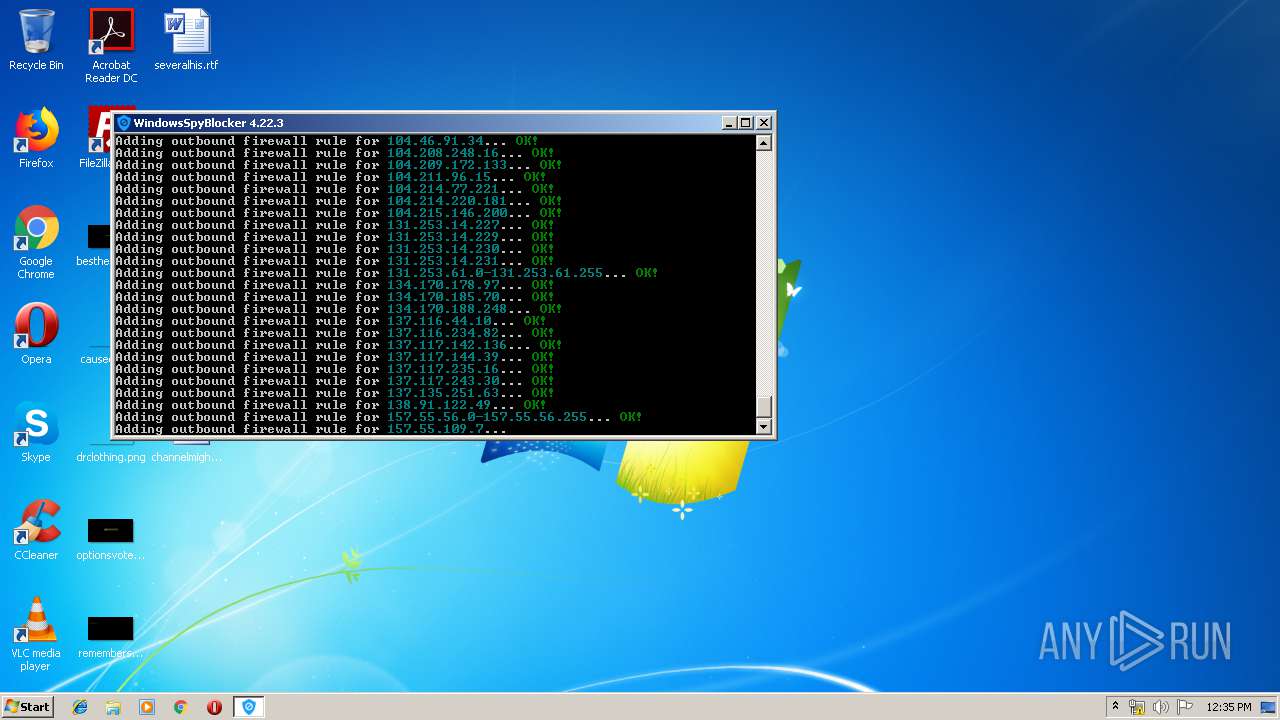
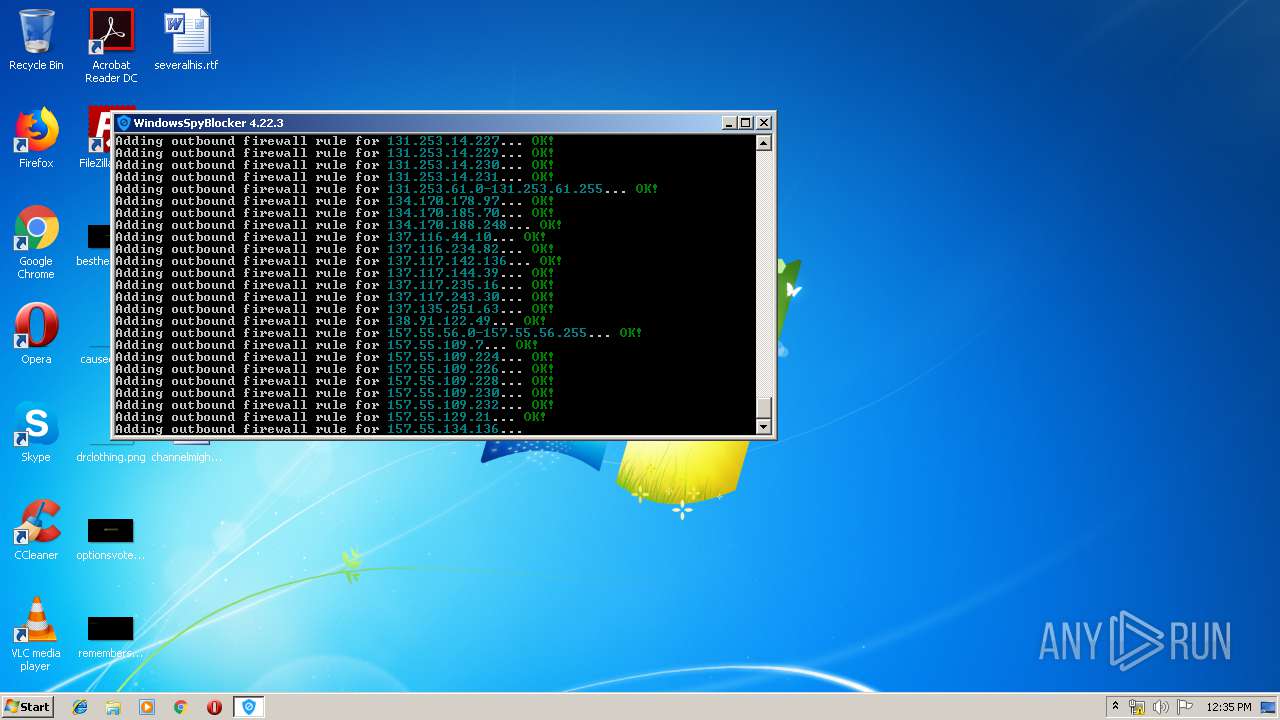
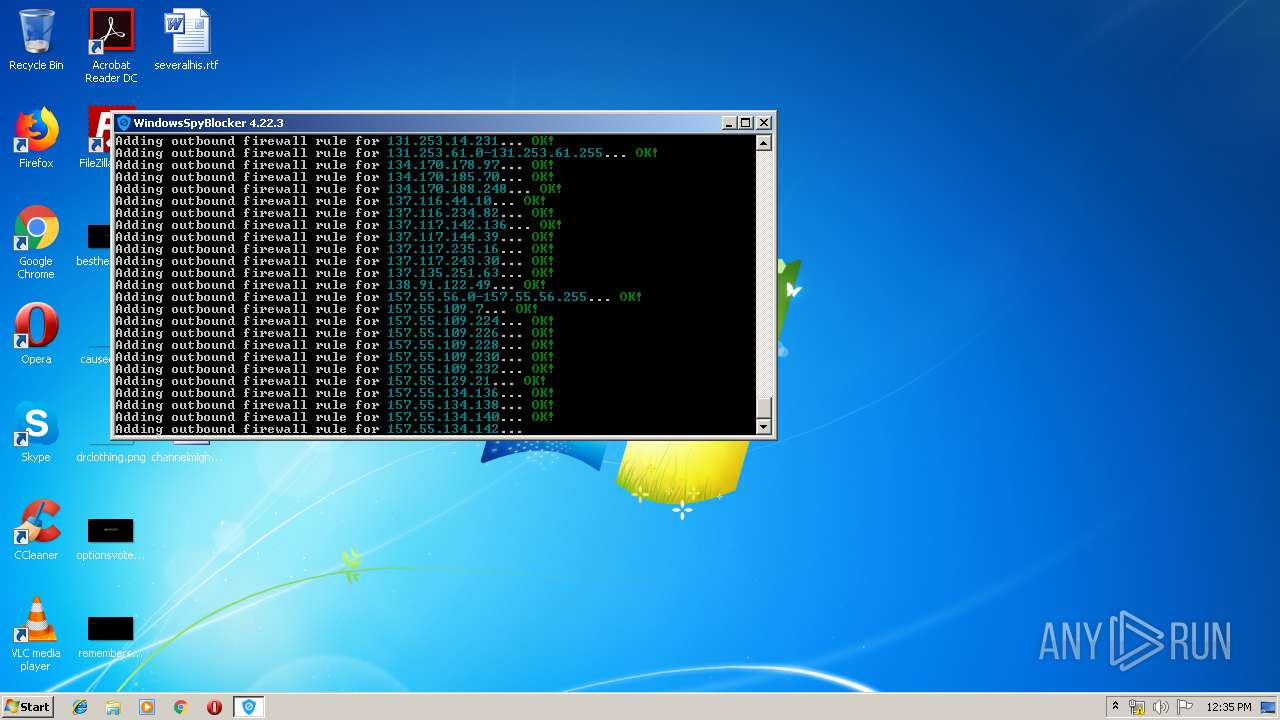
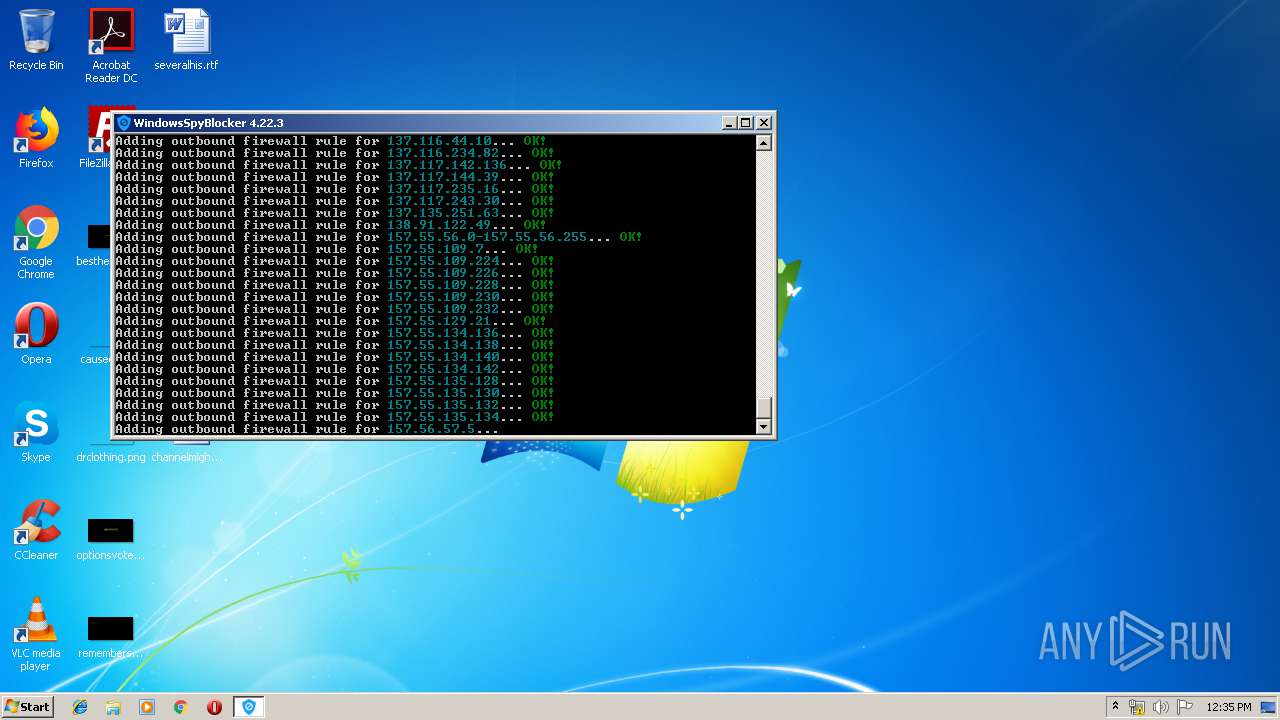
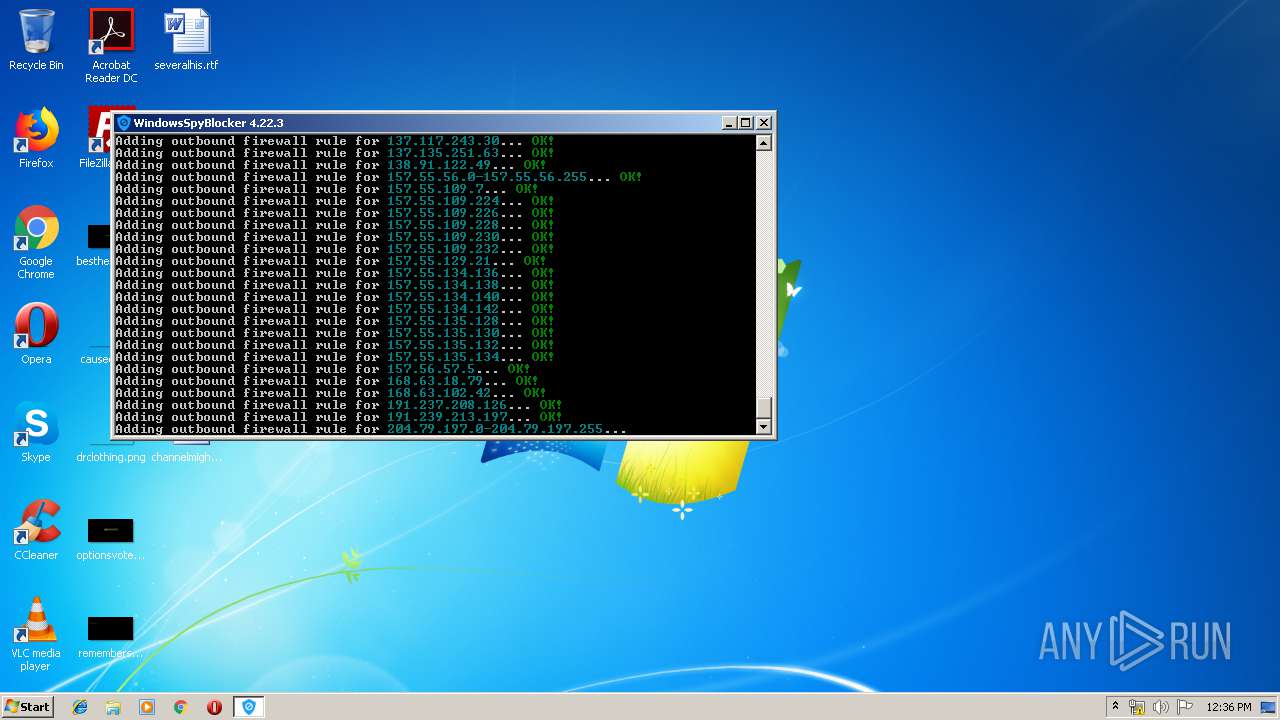
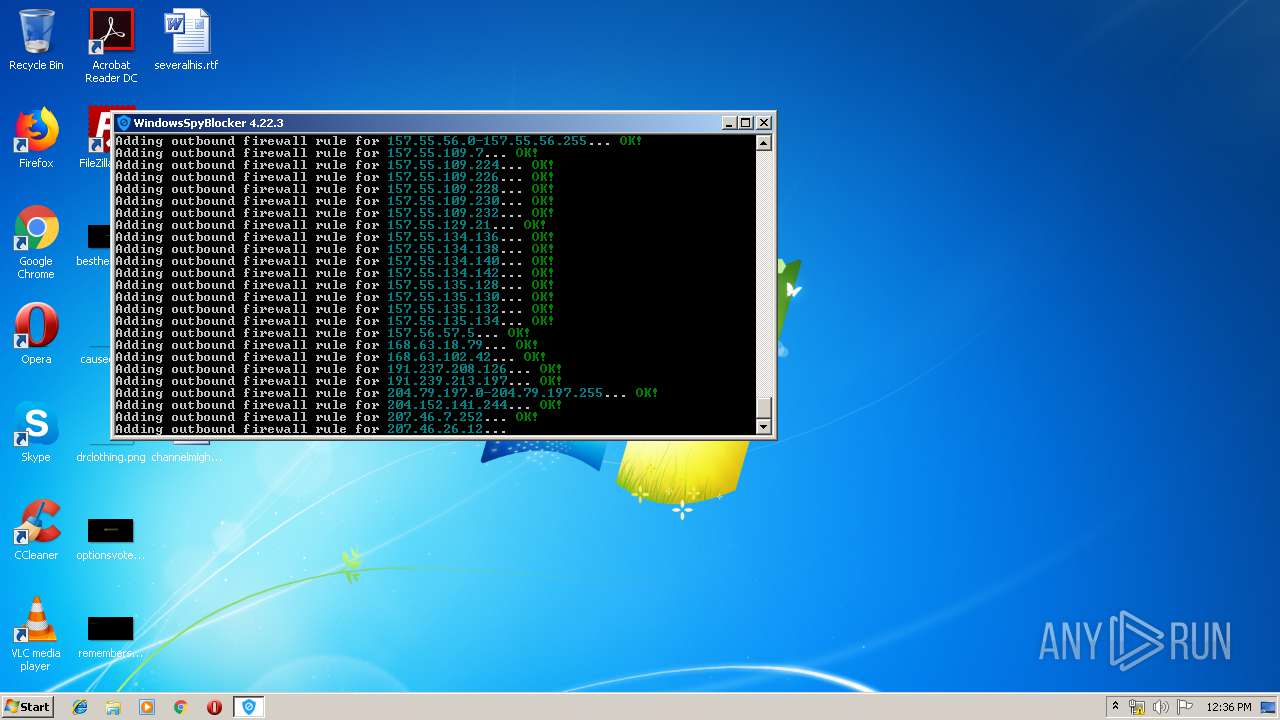
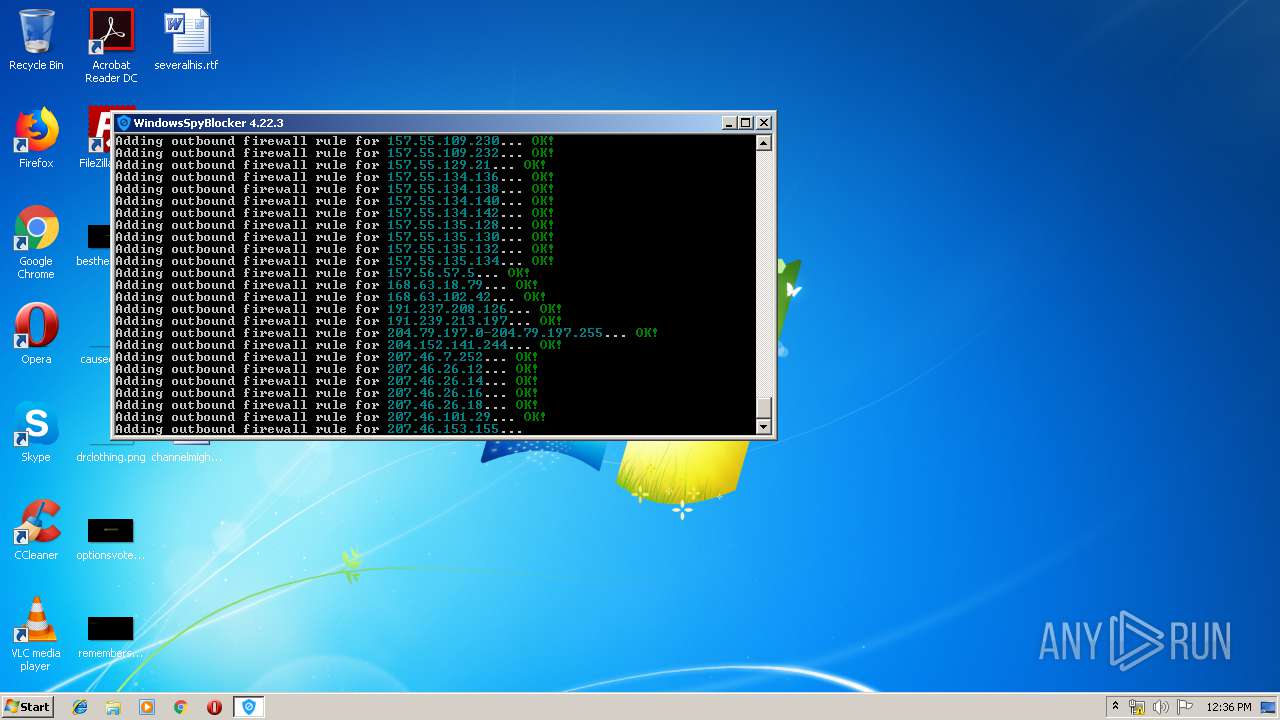
Uses NETSH.EXE for network configuration
- WindowsSpyBlocker.exe (PID: 872)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| ProductVersion: | 4.22.3.13 |
|---|---|
| ProductName: | WindowsSpyBlocker |
| OriginalFileName: | WindowsSpyBlocker.exe |
| LegalCopyright: | https://github.com/crazy-max/WindowsSpyBlocker |
| FileVersion: | 4.22.3.13 |
| FileDescription: | Block spying and tracking on Windows |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x4e860 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 252416 |
| CodeSize: | 3147776 |
| LinkerVersion: | 3 |
| PEType: | PE32 |
| TimeStamp: | 0000:00:00 00:00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 01-Jan-1970 00:00:00 |
| Detected languages: |
|
| FileDescription: | Block spying and tracking on Windows |
| FileVersion: | 4.22.3.13 |
| LegalCopyright: | https://github.com/crazy-max/WindowsSpyBlocker |
| OriginalFilename: | WindowsSpyBlocker.exe |
| ProductName: | WindowsSpyBlocker |
| ProductVersion: | 4.22.3.13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0004 |
| Size of header: | 0x0000 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x008B |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 01-Jan-1970 00:00:00 |
| Pointer to Symbol Table: | 0x006B0800 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0030075F | 0x00300800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.0706 |
.rdata | 0x00302000 | 0x00371C90 | 0x00371E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.79523 |
.data | 0x00674000 | 0x00053A08 | 0x0003DA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.3571 |
.idata | 0x006C8000 | 0x00000312 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.92632 |
.symtab | 0x006C9000 | 0x00000004 | 0x00000200 | IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0203931 |
.rsrc | 0x006CA000 | 0x00022A75 | 0x00022C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.61414 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.70942 | 429 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.01783 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
3 | 3.41654 | 1128 | UNKNOWN | English - United States | RT_ICON |
4 | 3.24494 | 2440 | UNKNOWN | English - United States | RT_ICON |
5 | 3.10232 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 2.85641 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 2.69202 | 16936 | UNKNOWN | English - United States | RT_ICON |
8 | 2.49991 | 38056 | UNKNOWN | English - United States | RT_ICON |
9 | 2.39593 | 67624 | UNKNOWN | English - United States | RT_ICON |
Imports
kernel32.dll |
Total processes
336
Monitored processes
299
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3736 | "C:\Users\admin\AppData\Local\Temp\WindowsSpyBlocker.exe" | C:\Users\admin\AppData\Local\Temp\WindowsSpyBlocker.exe | — | explorer.exe |
User: admin Integrity Level: MEDIUM Description: Block spying and tracking on Windows Exit code: 3221226540 Version: 4.22.3.13 | ||||
| 872 | "C:\Users\admin\AppData\Local\Temp\WindowsSpyBlocker.exe" | C:\Users\admin\AppData\Local\Temp\WindowsSpyBlocker.exe | explorer.exe | |
User: admin Integrity Level: HIGH Description: Block spying and tracking on Windows Exit code: 3221225786 Version: 4.22.3.13 | ||||
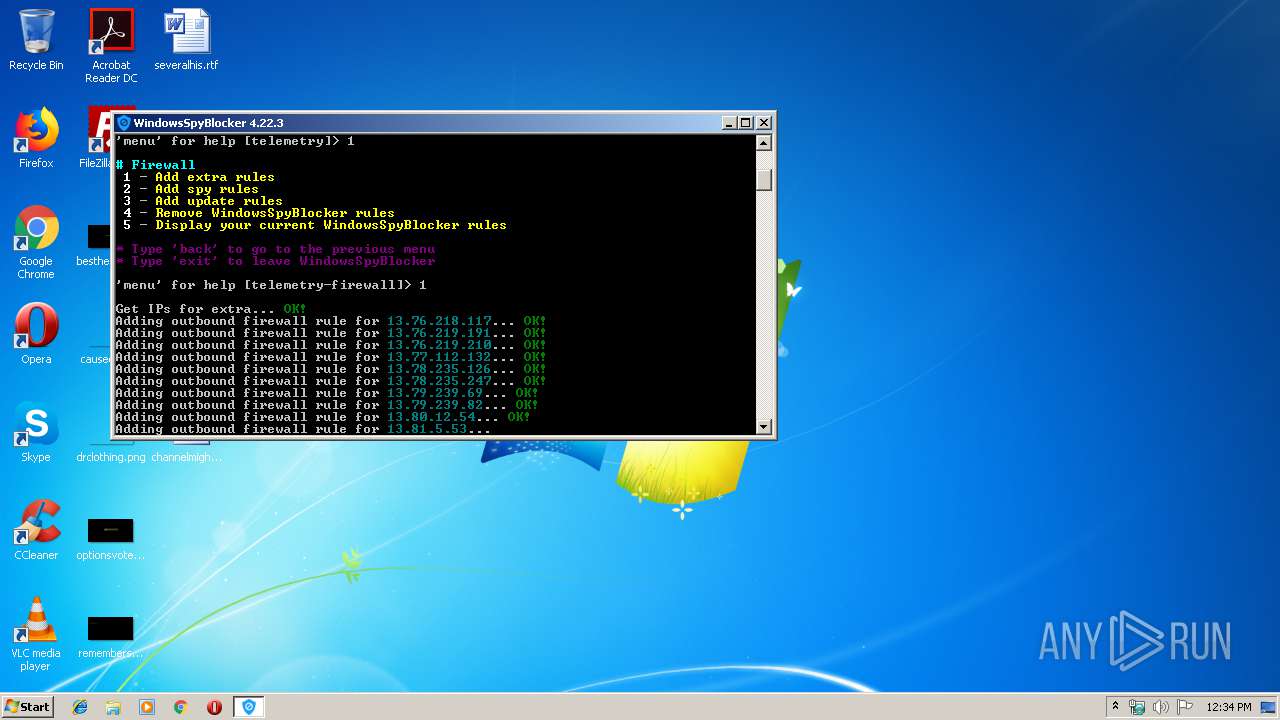
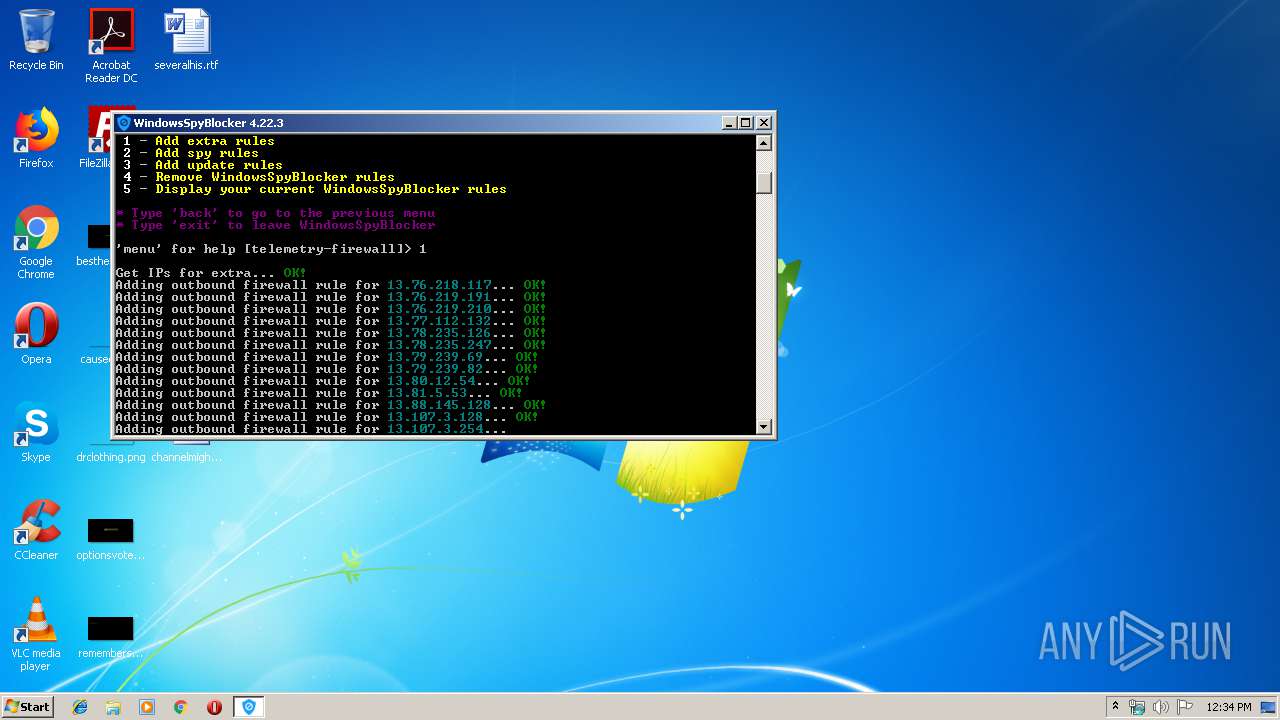
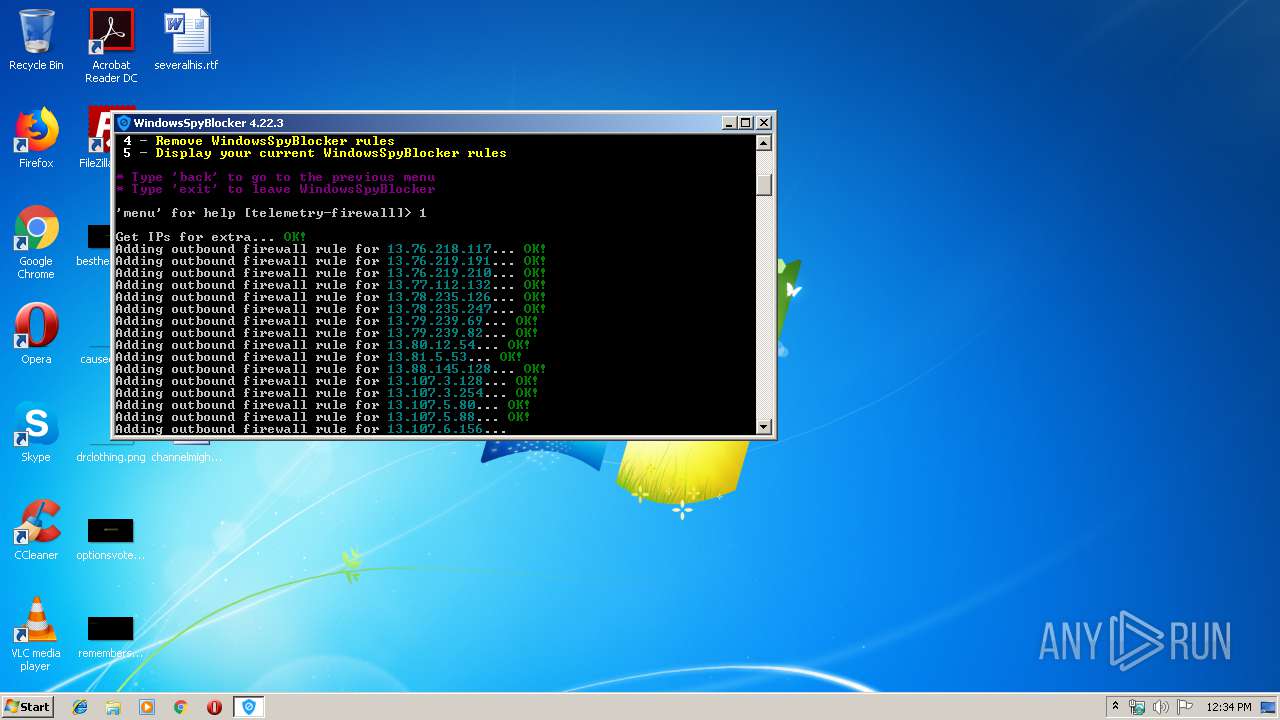
| 3764 | netsh advfirewall firewall add rule name=\"windowsSpyBlockerExtra-13.76.218.117\" dir=out protocol=any action=block remoteip=\"13.76.218.117\" | C:\Windows\system32\netsh.exe | — | WindowsSpyBlocker.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 2692 | netsh advfirewall firewall add rule name=\"windowsSpyBlockerExtra-13.76.219.191\" dir=out protocol=any action=block remoteip=\"13.76.219.191\" | C:\Windows\system32\netsh.exe | — | WindowsSpyBlocker.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 3412 | netsh advfirewall firewall add rule name=\"windowsSpyBlockerExtra-13.76.219.210\" dir=out protocol=any action=block remoteip=\"13.76.219.210\" | C:\Windows\system32\netsh.exe | — | WindowsSpyBlocker.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 3860 | netsh advfirewall firewall add rule name=\"windowsSpyBlockerExtra-13.77.112.132\" dir=out protocol=any action=block remoteip=\"13.77.112.132\" | C:\Windows\system32\netsh.exe | — | WindowsSpyBlocker.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 3768 | netsh advfirewall firewall add rule name=\"windowsSpyBlockerExtra-13.78.235.126\" dir=out protocol=any action=block remoteip=\"13.78.235.126\" | C:\Windows\system32\netsh.exe | — | WindowsSpyBlocker.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 3268 | netsh advfirewall firewall add rule name=\"windowsSpyBlockerExtra-13.78.235.247\" dir=out protocol=any action=block remoteip=\"13.78.235.247\" | C:\Windows\system32\netsh.exe | — | WindowsSpyBlocker.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 3780 | netsh advfirewall firewall add rule name=\"windowsSpyBlockerExtra-13.79.239.69\" dir=out protocol=any action=block remoteip=\"13.79.239.69\" | C:\Windows\system32\netsh.exe | — | WindowsSpyBlocker.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 2408 | netsh advfirewall firewall add rule name=\"windowsSpyBlockerExtra-13.79.239.82\" dir=out protocol=any action=block remoteip=\"13.79.239.82\" | C:\Windows\system32\netsh.exe | — | WindowsSpyBlocker.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
Total events
13 128
Read events
628
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 872 | WindowsSpyBlocker.exe | C:\Users\admin\AppData\Local\Temp\app.conf | text | |
MD5:106B1A270FCEC61AD19F98E7CDE5DE66 | SHA256:70D7C2D5E259FA32573AC16EFC0D17823B30879F11756B63222700F76D31262A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
872 | WindowsSpyBlocker.exe | 151.101.0.133:443 | raw.githubusercontent.com | Fastly | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
raw.githubusercontent.com |
| shared |