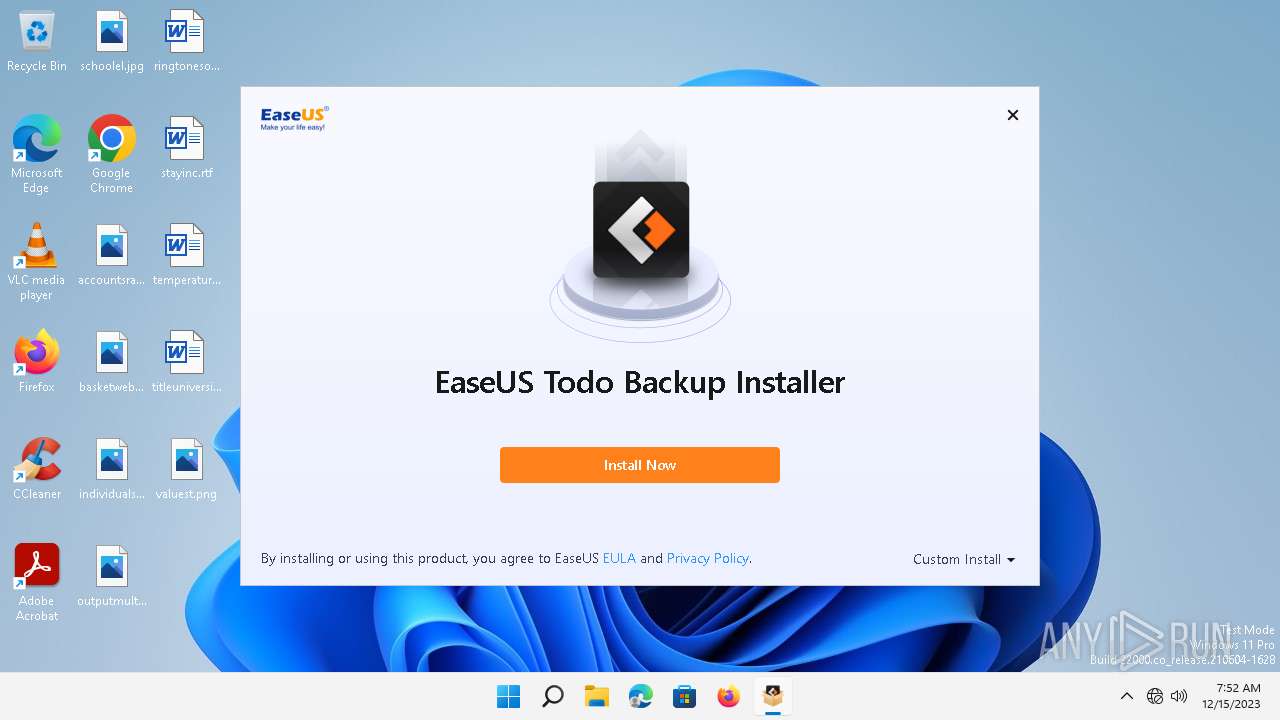
| File name: | TB_Free_Installer_20231215.681457.exe |
| Full analysis: | https://app.any.run/tasks/ff4e668d-e329-4dc7-b9f9-1cfbe35a957f |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | December 15, 2023, 07:52:00 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | B9A625522B3DBDE8B3DAF4CDA02AA696 |
| SHA1: | A9D8CF95D8BB989FFAE0F9B07FEA292CA16D7A93 |
| SHA256: | 7898ACFCC553E78206FA6EF705BF1F1EABE04F3A37F774B03EA57D11163D669E |
| SSDEEP: | 98304:OKEaB1r/sNZEbLyUdNqR5+8cPeEqO0qAVLgctuCuswgGe25sTwaT0o+ssv6OqIPl:T |
MALICIOUS
Drops the executable file immediately after the start
- TB_Free_Installer_20231215.681457.exe (PID: 5512)
- EDownloader.exe (PID: 3964)
- TB_free_easeus.exe (PID: 1972)
- DrvSetup.exe (PID: 3568)
- EnsUtils.exe (PID: 3396)
- TB_free_easeus.tmp (PID: 2528)
- Agent.exe (PID: 3468)
Scans artifacts that could help determine the target
- AliyunWrapExe.exe (PID: 2024)
- AliyunWrapExe.exe (PID: 6056)
- ensserver.exe (PID: 2132)
- AliyunWrapExe.exe (PID: 3492)
- AliyunWrapExe.exe (PID: 5172)
Actions looks like stealing of personal data
- TB_free_easeus.tmp (PID: 2528)
- TrayProcess.exe (PID: 1336)
- TBConsoleUI.exe (PID: 3888)
Creates a writable file in the system directory
- TB_free_easeus.tmp (PID: 2528)
- msdtc.exe (PID: 2176)
- DrvSetup.exe (PID: 3568)
- InfDefaultInstall.exe (PID: 4100)
- AliyunWrapExe.exe (PID: 3492)
- Agent.exe (PID: 3468)
Starts NET.EXE for service management
- net.exe (PID: 2992)
- net.exe (PID: 2872)
- cmd.exe (PID: 208)
- net.exe (PID: 3852)
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 208)
SUSPICIOUS
Reads the Internet Settings
- AliyunWrapExe.exe (PID: 2024)
- EDownloader.exe (PID: 3964)
- runonce.exe (PID: 952)
- AliyunWrapExe.exe (PID: 6056)
- TB_free_easeus.tmp (PID: 2528)
- AliyunWrapExe.exe (PID: 5172)
Reads Microsoft Outlook installation path
- EDownloader.exe (PID: 3964)
Reads the Windows owner or organization settings
- TB_free_easeus.tmp (PID: 2528)
Reads Internet Explorer settings
- EDownloader.exe (PID: 3964)
Process requests binary or script from the Internet
- EDownloader.exe (PID: 3964)
Process drops legitimate windows executable
- TB_free_easeus.tmp (PID: 2528)
- EnsUtils.exe (PID: 3396)
The process drops C-runtime libraries
- TB_free_easeus.tmp (PID: 2528)
- EnsUtils.exe (PID: 3396)
Starts CMD.EXE for commands execution
- TB_free_easeus.tmp (PID: 2528)
The process executes VB scripts
- cmd.exe (PID: 208)
Executes as Windows Service
- dllhost.exe (PID: 4308)
- msdtc.exe (PID: 2176)
- VSSVC.exe (PID: 532)
- ensserver.exe (PID: 2132)
- Agent.exe (PID: 3468)
- vds.exe (PID: 4364)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 4976)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 4976)
Drops a system driver (possible attempt to evade defenses)
- TB_free_easeus.tmp (PID: 2528)
- DrvSetup.exe (PID: 3568)
- InfDefaultInstall.exe (PID: 4100)
Drops 7-zip archiver for unpacking
- TB_free_easeus.tmp (PID: 2528)
Process checks presence of unattended files
- TB_free_easeus.tmp (PID: 2528)
Creates files in the driver directory
- TB_free_easeus.tmp (PID: 2528)
- DrvSetup.exe (PID: 3568)
Executing commands from ".cmd" file
- TB_free_easeus.tmp (PID: 2528)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 208)
Uses TASKKILL.EXE to kill process
- DrvSetup.exe (PID: 3568)
Searches for installed software
- TB_free_easeus.tmp (PID: 2528)
- EDownloader.exe (PID: 3964)
Checks Windows Trust Settings
- ensserver.exe (PID: 2132)
Reads the date of Windows installation
- TB_free_easeus.tmp (PID: 2528)
- EDownloader.exe (PID: 3964)
Uses WMIC.EXE to obtain operating system information
- SetupUE.exe (PID: 6104)
- TBConsoleUI.exe (PID: 3888)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 1864)
- WMIC.exe (PID: 3440)
The process checks if it is being run in the virtual environment
- Agent.exe (PID: 3468)
Detected use of alternative data streams (AltDS)
- Agent.exe (PID: 3468)
INFO
Dropped object may contain TOR URL's
- TB_Free_Installer_20231215.681457.exe (PID: 5512)
Checks supported languages
- TB_Free_Installer_20231215.681457.exe (PID: 5512)
- InfoForSetup.exe (PID: 2872)
- EDownloader.exe (PID: 3964)
- InfoForSetup.exe (PID: 2508)
- AliyunWrapExe.exe (PID: 2024)
- InfoForSetup.exe (PID: 3444)
- InfoForSetup.exe (PID: 1812)
- InfoForSetup.exe (PID: 1144)
- InfoForSetup.exe (PID: 2004)
- TB_free_easeus.tmp (PID: 2528)
- InfoForSetup.exe (PID: 1556)
- TB_free_easeus.exe (PID: 1972)
- DrvSetup.exe (PID: 3568)
- AppSetup.exe (PID: 1688)
- EnsUtils.exe (PID: 3396)
- AliyunWrapExe.exe (PID: 6056)
- AliyunWrapExe.exe (PID: 3492)
- ensserver.exe (PID: 2132)
- SetupSendData2Downloader.exe (PID: 4988)
- Agent.exe (PID: 604)
- Agent.exe (PID: 3468)
- InfoForSetup.exe (PID: 4428)
- TrayProcess.exe (PID: 1336)
- SetupUE.exe (PID: 6104)
- EUinApp.exe (PID: 3632)
- InfoForSetup.exe (PID: 2964)
- InfoForSetup.exe (PID: 4464)
- wpn-grant.exe (PID: 6036)
- InfoForSetup.exe (PID: 3856)
- AliyunWrapExe.exe (PID: 5172)
- TodoBackupService.exe (PID: 5140)
- TBConsoleUI.exe (PID: 3888)
- InfoForSetup.exe (PID: 3276)
- Loader.exe (PID: 4060)
- EuDownload.exe (PID: 1408)
- EuDownload.exe (PID: 4872)
- EuDownload.exe (PID: 4020)
Create files in a temporary directory
- EDownloader.exe (PID: 3964)
- TB_Free_Installer_20231215.681457.exe (PID: 5512)
- AliyunWrapExe.exe (PID: 2024)
- InfoForSetup.exe (PID: 2508)
- TB_free_easeus.tmp (PID: 2528)
- TB_free_easeus.exe (PID: 1972)
Reads the computer name
- EDownloader.exe (PID: 3964)
- AliyunWrapExe.exe (PID: 2024)
- TB_free_easeus.tmp (PID: 2528)
- DrvSetup.exe (PID: 3568)
- AppSetup.exe (PID: 1688)
- AliyunWrapExe.exe (PID: 6056)
- EnsUtils.exe (PID: 3396)
- ensserver.exe (PID: 2132)
- AliyunWrapExe.exe (PID: 3492)
- Agent.exe (PID: 3468)
- Agent.exe (PID: 604)
- TrayProcess.exe (PID: 1336)
- wpn-grant.exe (PID: 6036)
- AliyunWrapExe.exe (PID: 5172)
- TodoBackupService.exe (PID: 5140)
- TBConsoleUI.exe (PID: 3888)
- EuDownload.exe (PID: 1408)
- EuDownload.exe (PID: 4872)
- EuDownload.exe (PID: 4020)
Reads the machine GUID from the registry
- EDownloader.exe (PID: 3964)
- ensserver.exe (PID: 2132)
- wpn-grant.exe (PID: 6036)
- EuDownload.exe (PID: 4872)
- EuDownload.exe (PID: 1408)
- EuDownload.exe (PID: 4020)
Checks proxy server information
- AliyunWrapExe.exe (PID: 2024)
- EDownloader.exe (PID: 3964)
- AliyunWrapExe.exe (PID: 6056)
- AliyunWrapExe.exe (PID: 5172)
Creates files or folders in the user directory
- AliyunWrapExe.exe (PID: 2024)
- AliyunWrapExe.exe (PID: 6056)
- AliyunWrapExe.exe (PID: 5172)
Creates files in the program directory
- TB_free_easeus.tmp (PID: 2528)
- DrvSetup.exe (PID: 3568)
- EnsUtils.exe (PID: 3396)
- ensserver.exe (PID: 2132)
- Agent.exe (PID: 604)
- AliyunWrapExe.exe (PID: 6056)
- AliyunWrapExe.exe (PID: 3492)
- Agent.exe (PID: 3468)
- AliyunWrapExe.exe (PID: 5172)
- EuDownload.exe (PID: 4872)
- EuDownload.exe (PID: 1408)
- EuDownload.exe (PID: 4020)
Reads security settings of Internet Explorer
- cscript.exe (PID: 2712)
- cscript.exe (PID: 4976)
Checks transactions between databases Windows and Oracle
- dllhost.exe (PID: 4308)
- msdtc.exe (PID: 2176)
- cscript.exe (PID: 2712)
- cscript.exe (PID: 4976)
Creates files in the driver directory
- InfDefaultInstall.exe (PID: 4100)
Reads the time zone
- runonce.exe (PID: 952)
Drops the executable file immediately after the start
- InfDefaultInstall.exe (PID: 4100)
Creates a software uninstall entry
- TB_free_easeus.tmp (PID: 2528)
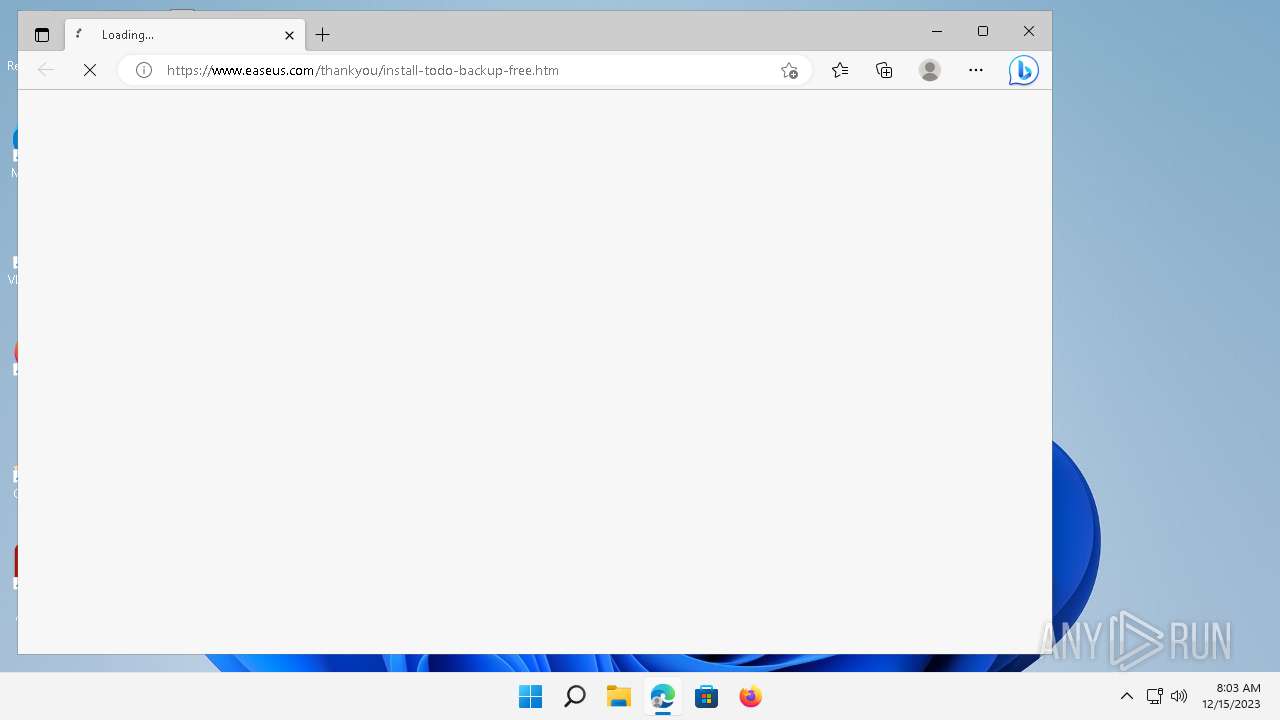
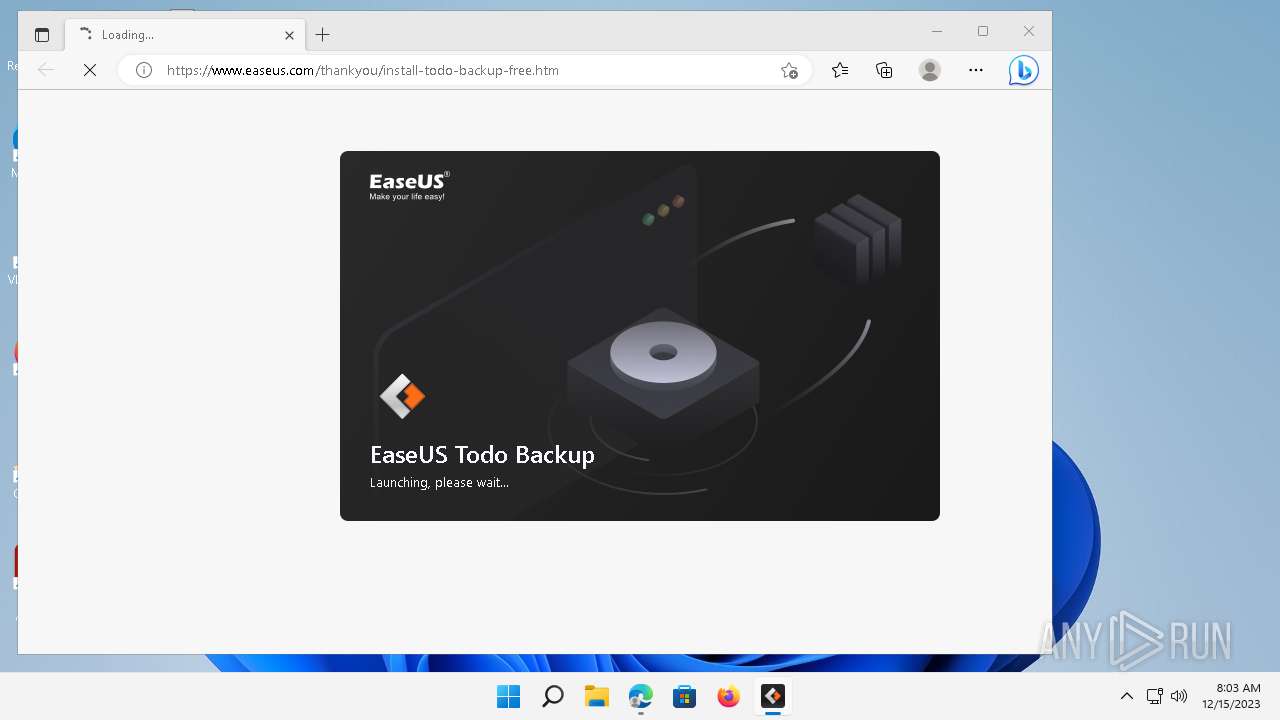
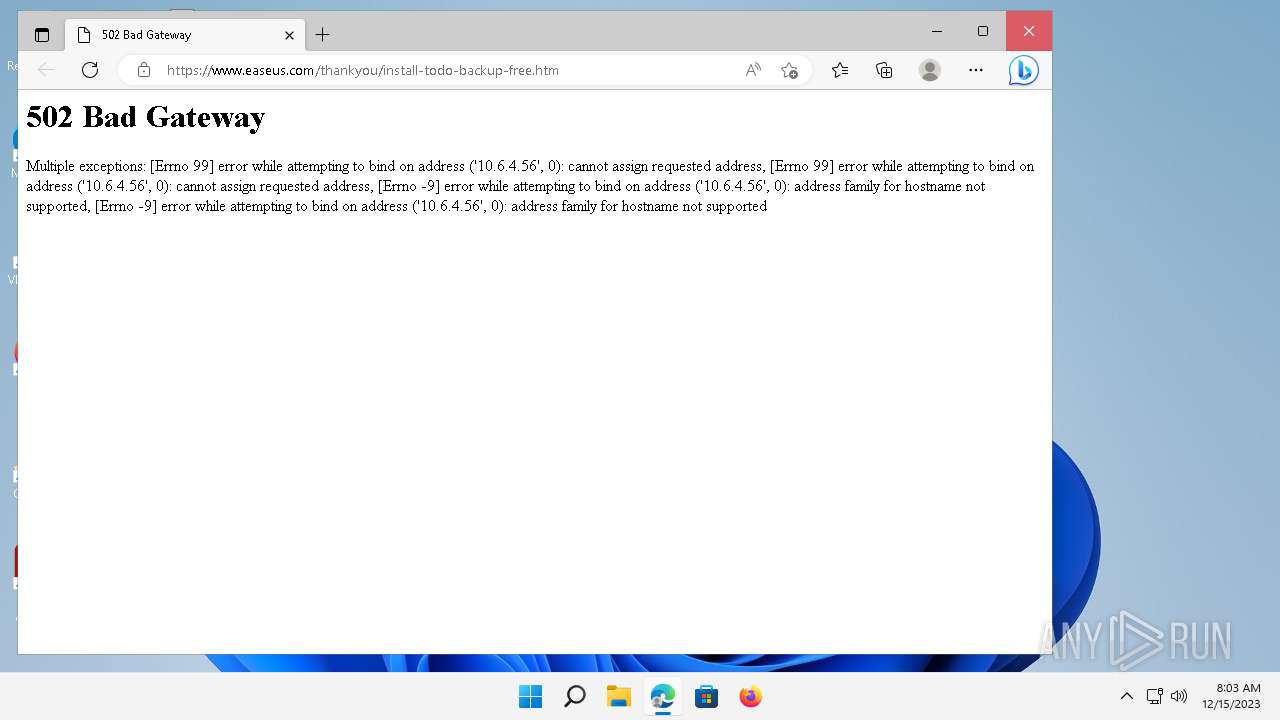
Application launched itself
- msedge.exe (PID: 2972)
- msedge.exe (PID: 5076)
- msedge.exe (PID: 6840)
Manual execution by a user
- msedge.exe (PID: 5076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 04:57:48+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
224
Monitored processes
111
Malicious processes
11
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files (x86)\EaseUS\Todo Backup\bin\x64\install-EaseUSprovider.cmd"" | C:\Windows\System32\cmd.exe | — | TB_free_easeus.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | C:\Windows\system32\net1 stop swprv | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.22000.434 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 532 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 604 | "C:\Program Files (x86)\EaseUS\Todo Backup\bin\Agent.exe" install | C:\Program Files (x86)\EaseUS\Todo Backup\bin\Agent.exe | TB_free_easeus.tmp | ||||||||||||
User: admin Company: CHENGDU YIWO Tech Development Co., Ltd Integrity Level: HIGH Description: EaseUS Todo Backup Agent Application Exit code: 1 Version: 5.8.0.0 Modules
| |||||||||||||||
| 632 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SetupSendData2Downloader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 952 | "C:\Windows\system32\runonce.exe" -r | C:\Windows\System32\runonce.exe | — | InfDefaultInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | reg.exe delete HKLM\SYSTEM\CurrentControlSet\Services\Eventlog\Application\VssEaseusProvider /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | EUinApp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1144 | /SendInfo Window "Downloading" Activity "Result_Download_Program" Attribute "{\"Average_Networkspeed\":\"503.00KB\",\"Cdn\":\"https://d1.easeus.com/tb/free/TodoBackup16.0_free.exe\",\"Elapsedtime\":\"290\",\"Errorinfo\":\"0\",\"Result\":\"Success\"}" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3free\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1336 | "C:\Program Files (x86)\EaseUS\Todo Backup\bin\TrayProcess.exe" install | C:\Program Files (x86)\EaseUS\Todo Backup\bin\TrayProcess.exe | TB_free_easeus.tmp | ||||||||||||
User: admin Company: CHENGDU YIWO Tech Development Co., Ltd Integrity Level: HIGH Description: EaseUS Todo Backup Application Exit code: 0 Version: 16.0.0.0 Modules
| |||||||||||||||
Total events
26 354
Read events
26 209
Write events
132
Delete events
13
Modification events
| (PID) Process: | (2024) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2024) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2024) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2024) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2024) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2024) AliyunWrapExe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3964) EDownloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3964) EDownloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3964) EDownloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3964) EDownloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2 026
Suspicious files
280
Text files
3 636
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5512 | TB_Free_Installer_20231215.681457.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3free\EDownloader.exe | executable | |
MD5:53832E0D7970B48218429C20777D3965 | SHA256:472B7D98B11719A38A097B64D24B4703FB12D9F70DA71C5087AE9F84911AC106 | |||
| 5512 | TB_Free_Installer_20231215.681457.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3free\Korean.ini | text | |
MD5:2388DF23E3BFE3A7455062E00DE35E65 | SHA256:9D3EF37D66FDB9B3F102CF1E0031EE84A792B7A7DBC4D5328BD00C3C8AA22E5E | |||
| 5512 | TB_Free_Installer_20231215.681457.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3free\Japanese.ini | text | |
MD5:D7E405065BB8CBF3666DB39FBD1FA1D1 | SHA256:31493DBDF2D62781A76AD0785F33E83EADFC7C201AFC9ADF6ACFDAD6C9F3555A | |||
| 5512 | TB_Free_Installer_20231215.681457.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3free\Portuguese.ini | text | |
MD5:533CD0B13D84F650315CA141D2F12891 | SHA256:0713AD4E63CE692EF53417A91D394341C455F14EC63ED8C49A480384C0FF6A4D | |||
| 5512 | TB_Free_Installer_20231215.681457.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3free\english.ini | text | |
MD5:DDAF4E9F7E89D3AD8AC541CC7C82888E | SHA256:A82964B0605B60EED9997EA9F3D7BC23C5AD9FF95F083D51F4EBBDB137B88C94 | |||
| 5512 | TB_Free_Installer_20231215.681457.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3free\Chinese.ini | text | |
MD5:2C1109202C5BD64CFBD15440DBFB9E15 | SHA256:503DED4C87EC70CF80920CD35985A34A7F7DF4280E8ACD2915BB105140057AA4 | |||
| 5512 | TB_Free_Installer_20231215.681457.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3free\Italian.ini | text | |
MD5:528492B1C61DD427C0030AF1E85021CB | SHA256:2E31D7ACE9D3417EBA9BC93E44C645D5783C23F2C6570807BCC48E94ADE2C857 | |||
| 5512 | TB_Free_Installer_20231215.681457.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\3free\LanguageTransfor.ini | text | |
MD5:008516FB41014EEE340FF4B4AB030CBC | SHA256:80193C8D307D982CF45FBF62F0EEE3B7EC5522DECA8A027155875D610C63657C | |||
| 3964 | EDownloader.exe | C:\Users\admin\AppData\Local\Temp\TB_free_easeus.exe.temp | — | |
MD5:— | SHA256:— | |||
| 3964 | EDownloader.exe | C:\Users\admin\AppData\Local\Temp\TB_free_easeus.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
101
TCP/UDP connections
117
DNS requests
45
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3964 | EDownloader.exe | POST | 200 | 143.204.98.38:80 | http://download.easeus.com/api2/index.php/Apicp/Drwdl202004/index/ | US | binary | 489 b | unknown |
2024 | AliyunWrapExe.exe | GET | 200 | 163.171.156.15:80 | http://track.easeus.com/product/index.php?c=main&a=getstatus&pid=0 | DE | binary | 21 b | unknown |
2024 | AliyunWrapExe.exe | POST | 200 | 47.252.97.212:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_tbp_downloader/shards/lb | US | — | — | unknown |
2024 | AliyunWrapExe.exe | POST | 200 | 47.252.97.212:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_tbp_downloader/shards/lb | US | — | — | unknown |
2024 | AliyunWrapExe.exe | POST | 200 | 47.252.97.212:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_tbp_downloader/shards/lb | US | — | — | unknown |
880 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ba8520f5c7f95796 | GB | compressed | 4.66 Kb | unknown |
2024 | AliyunWrapExe.exe | POST | 200 | 47.252.97.212:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_tbp_downloader/shards/lb | US | — | — | unknown |
1396 | svchost.exe | GET | 200 | 104.124.11.219:80 | http://www.msftconnecttest.com/connecttest.txt | DE | text | 22 b | unknown |
3964 | EDownloader.exe | GET | — | 18.66.112.111:443 | https://d1.easeus.com/tb/free/TodoBackup16.0_free.exe | US | — | — | unknown |
3964 | EDownloader.exe | GET | — | 18.66.112.38:443 | https://d1.easeus.com/tb/free/TodoBackup16.0_free.exe | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4560 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2024 | AliyunWrapExe.exe | 163.171.156.15:80 | track.easeus.com | QUANTILNETWORKS | DE | unknown |
3964 | EDownloader.exe | 143.204.98.38:80 | download.easeus.com | AMAZON-02 | US | unknown |
1396 | svchost.exe | 104.124.11.185:80 | — | Akamai International B.V. | DE | unknown |
5848 | OfficeC2RClient.exe | 52.109.32.97:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | GB | unknown |
2024 | AliyunWrapExe.exe | 47.252.97.212:80 | easeusinfo.us-east-1.log.aliyuncs.com | Alibaba US Technology Co., Ltd. | US | unknown |
880 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
880 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3964 | EDownloader.exe | 18.66.112.38:443 | d1.easeus.com | AMAZON-02 | US | unknown |
2852 | svchost.exe | 20.189.173.2:443 | v20.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.easeus.com |
| unknown |
track.easeus.com |
| unknown |
easeusinfo.us-east-1.log.aliyuncs.com |
| unknown |
login.live.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
d1.easeus.com |
| unknown |
v20.events.data.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
mrodevicemgr.officeapps.live.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2024 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
2024 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
2024 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
2024 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
1396 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
2024 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
2024 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
2024 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6056 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6056 | AliyunWrapExe.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
Process | Message |
|---|---|
Agent.exe |
Ldq : Agent call CreateService is success!
|
Agent.exe | Init Log |
Agent.exe | Ldq : Agent start install! |
Agent.exe |
Ldq : Agent call CreateService!
|
Agent.exe | Init Log |
Agent.exe |
Ldq : Agent entry ServiceMain!
|
Agent.exe |
Ldq : Agent set service description!
|
Agent.exe | socket closed
|
Agent.exe | Failed to Load lib (Err=0x12529002) CheckTool |
Agent.exe |
Zy : Instance CheckTool!
|