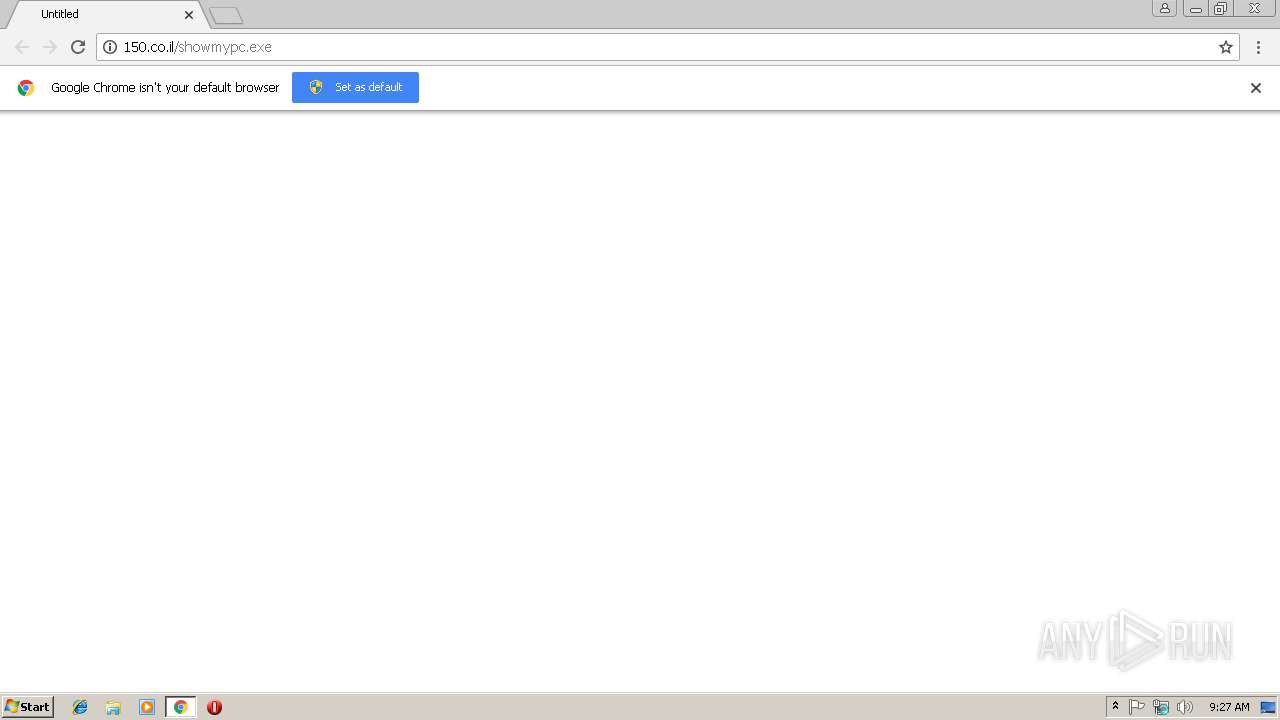
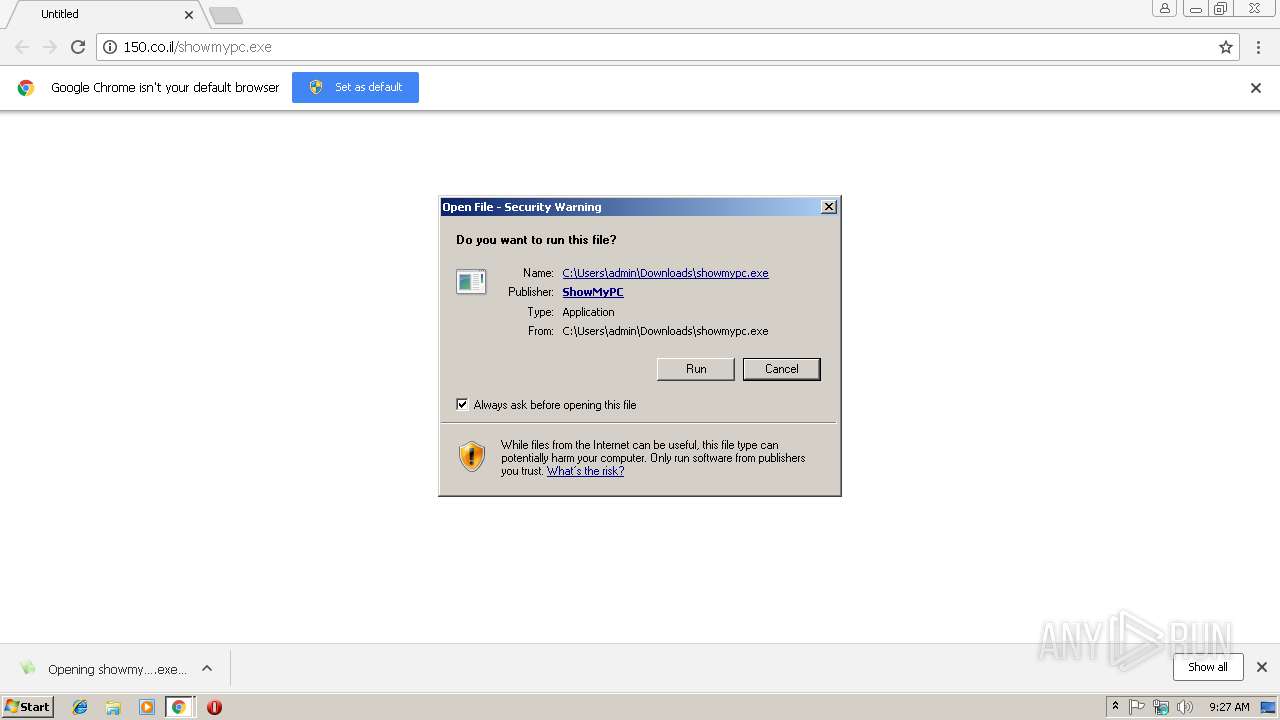
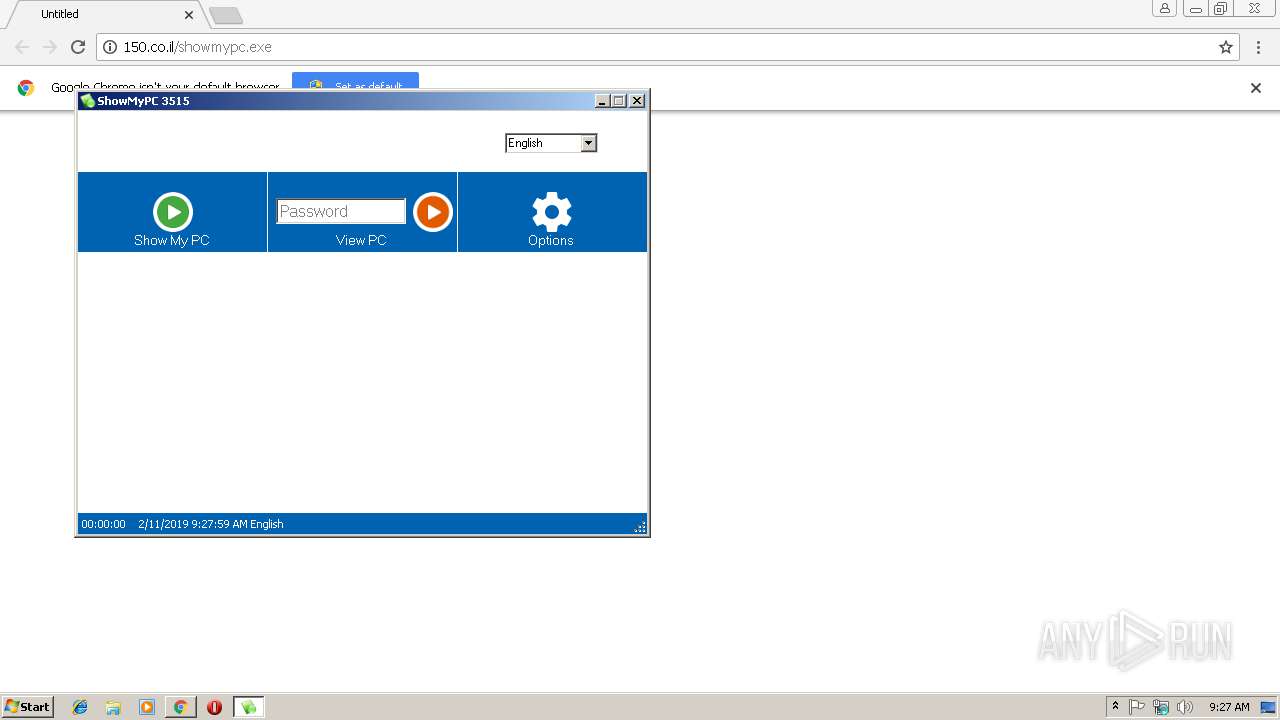
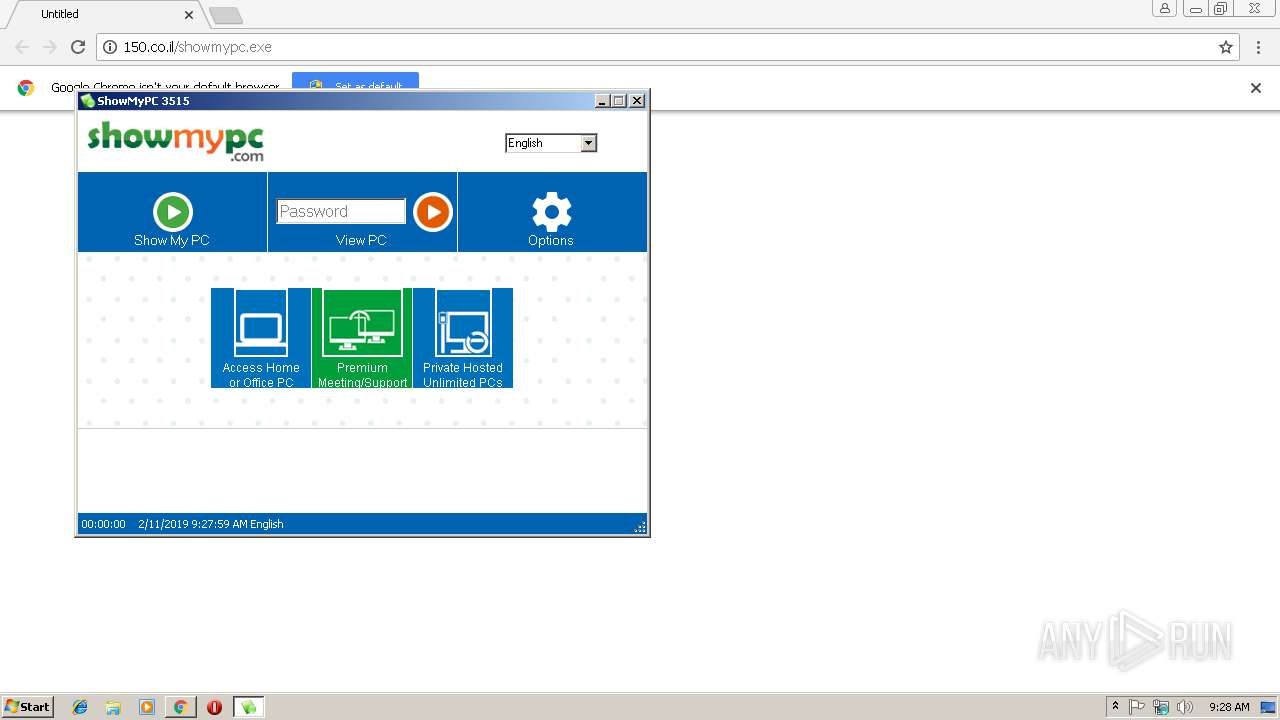
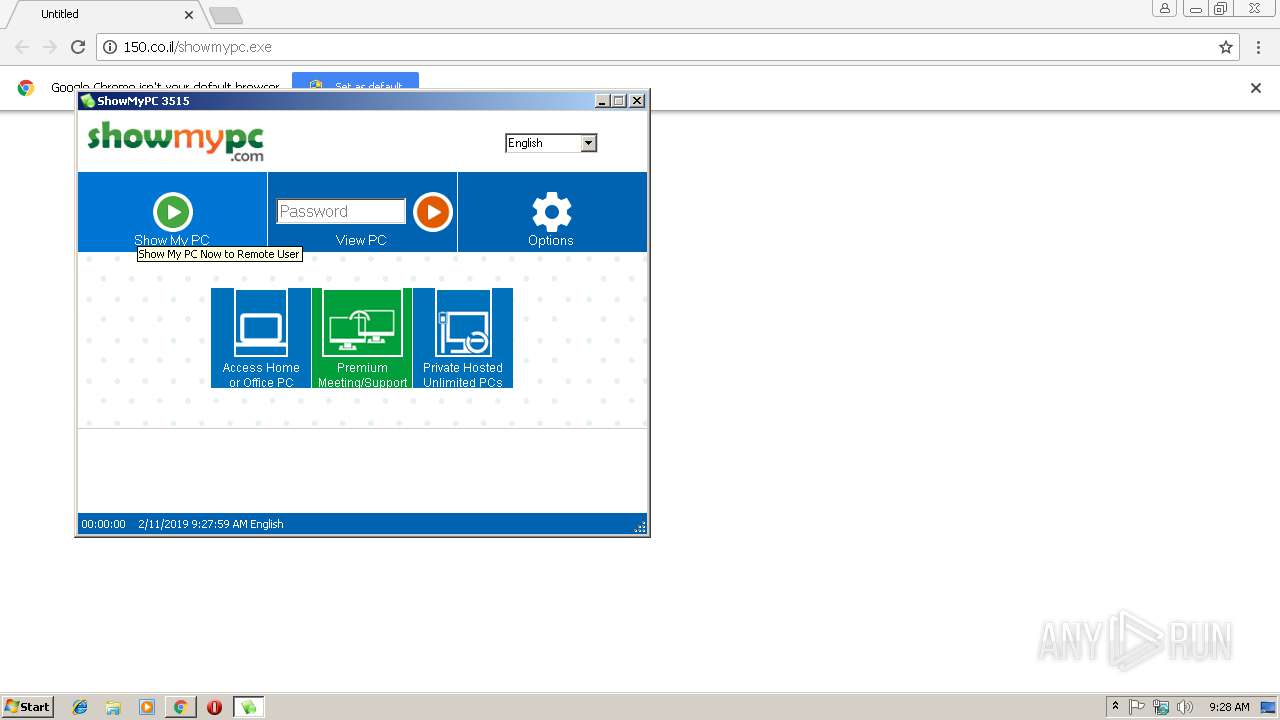
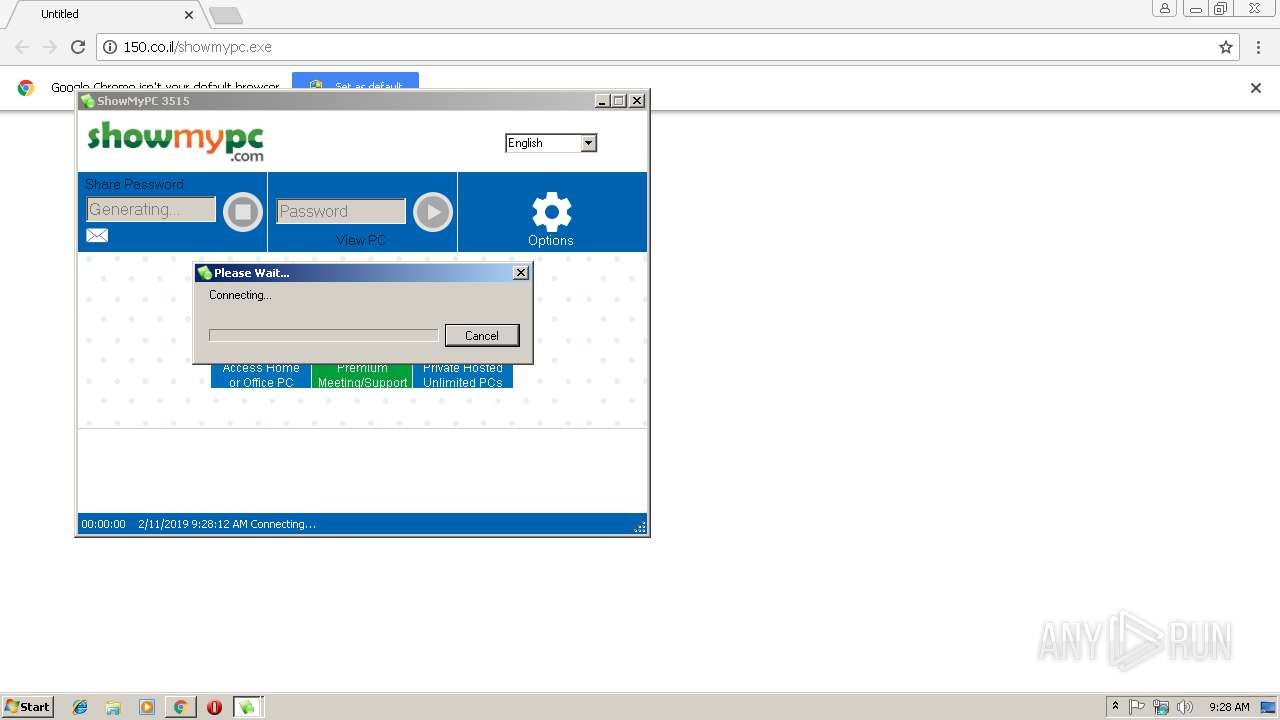
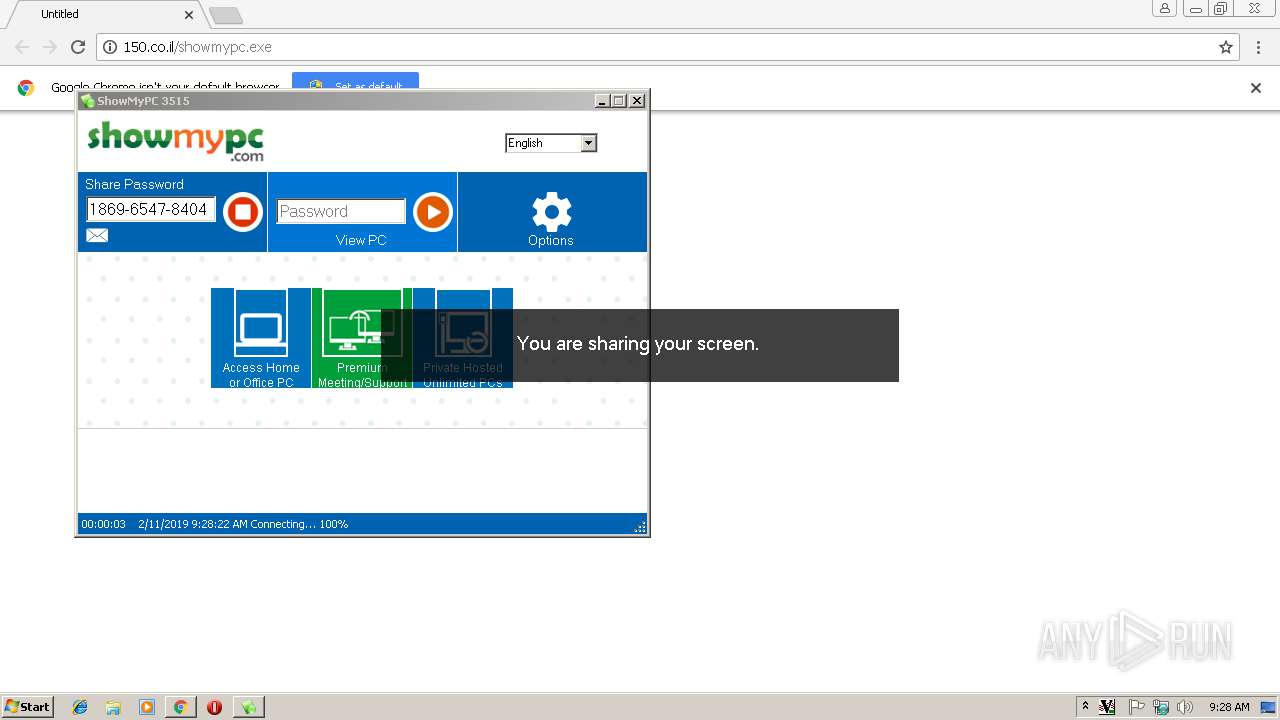
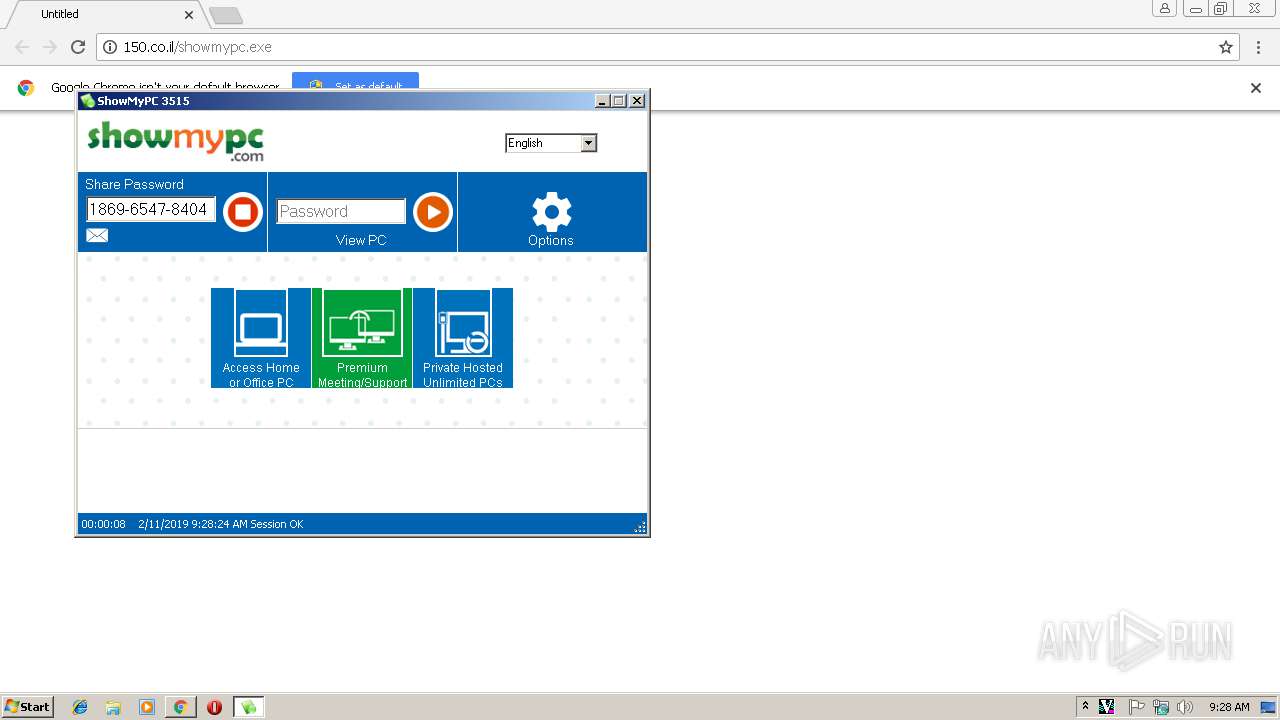
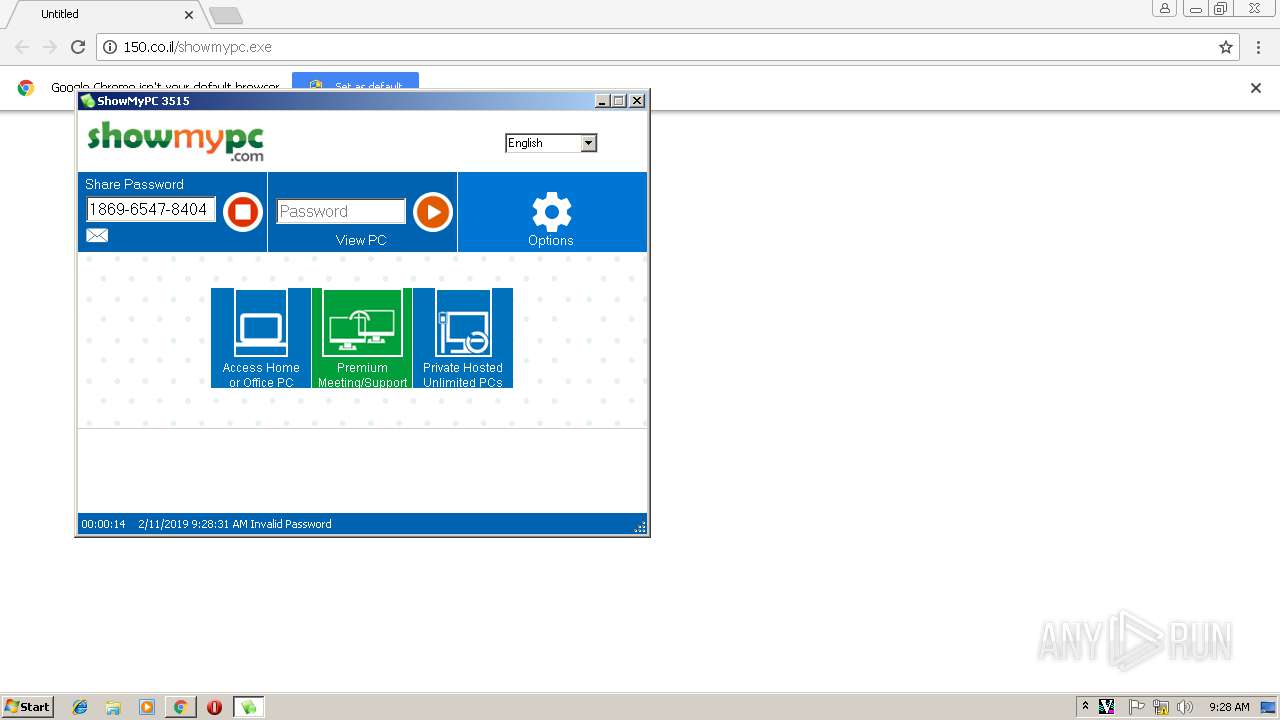
| URL: | http://150.co.il/showmypc.exe |
| Full analysis: | https://app.any.run/tasks/c0bc8332-5d5b-45f1-aca8-65a08870e860 |
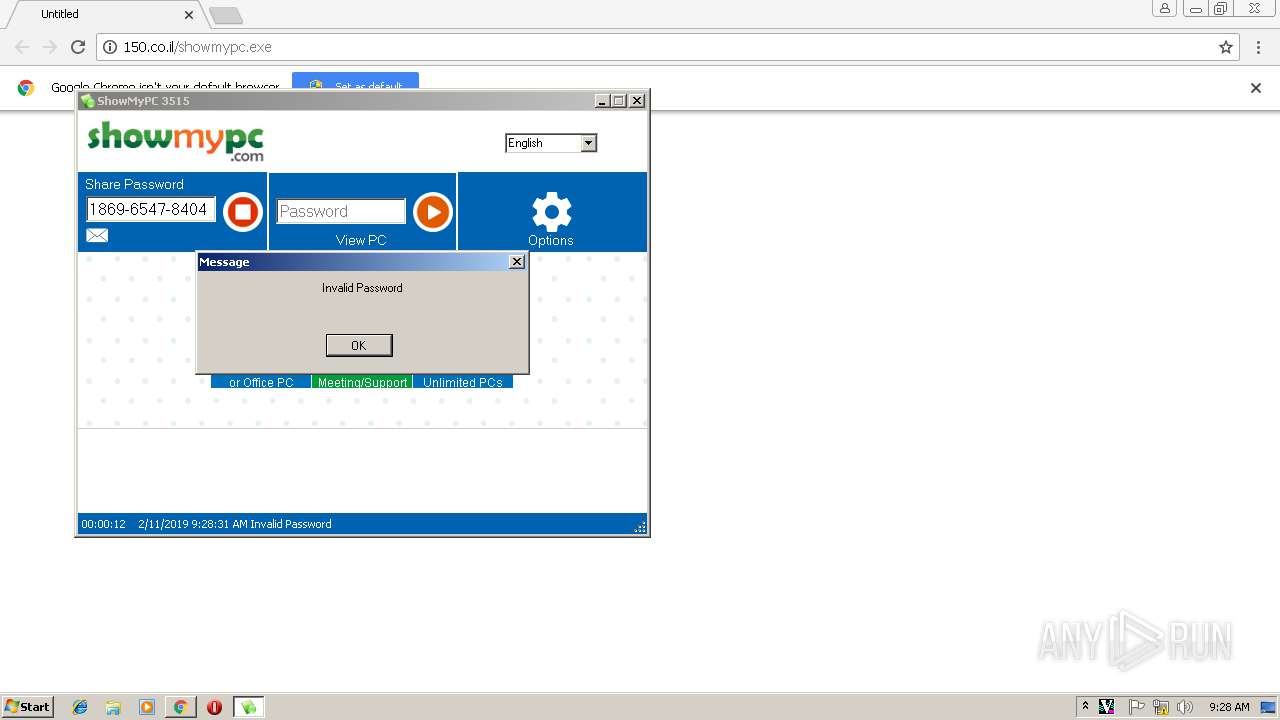
| Verdict: | Malicious activity |
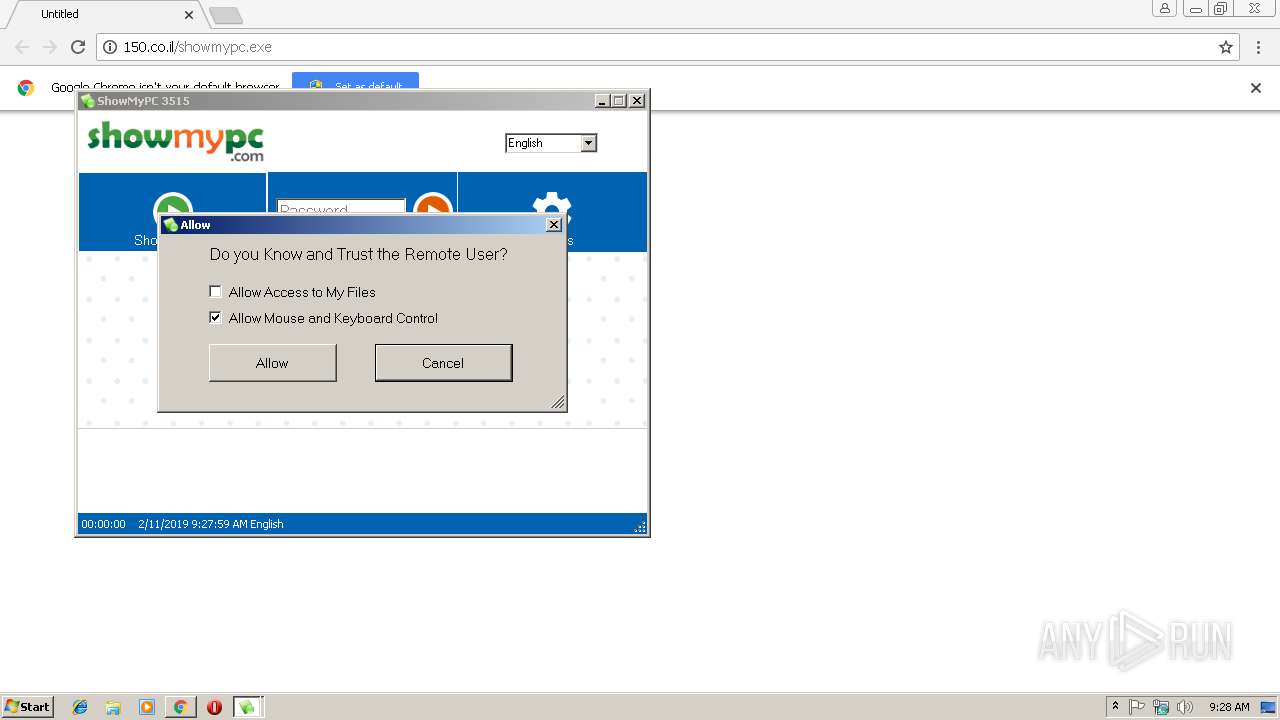
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | February 11, 2019, 09:27:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2A92D9760DD6EE9E5B444BEE43C0033A |
| SHA1: | EFC7C7B7AB5450B4C7A3DA44A69F2CE7D07636F7 |
| SHA256: | 78957DA8BCA65789EDA8C9834D82DC714605BEAECF2753F9798CB8A2D361CB3F |
| SSDEEP: | 3:N1KoVZLmY7c7dA:Coft78A |
MALICIOUS
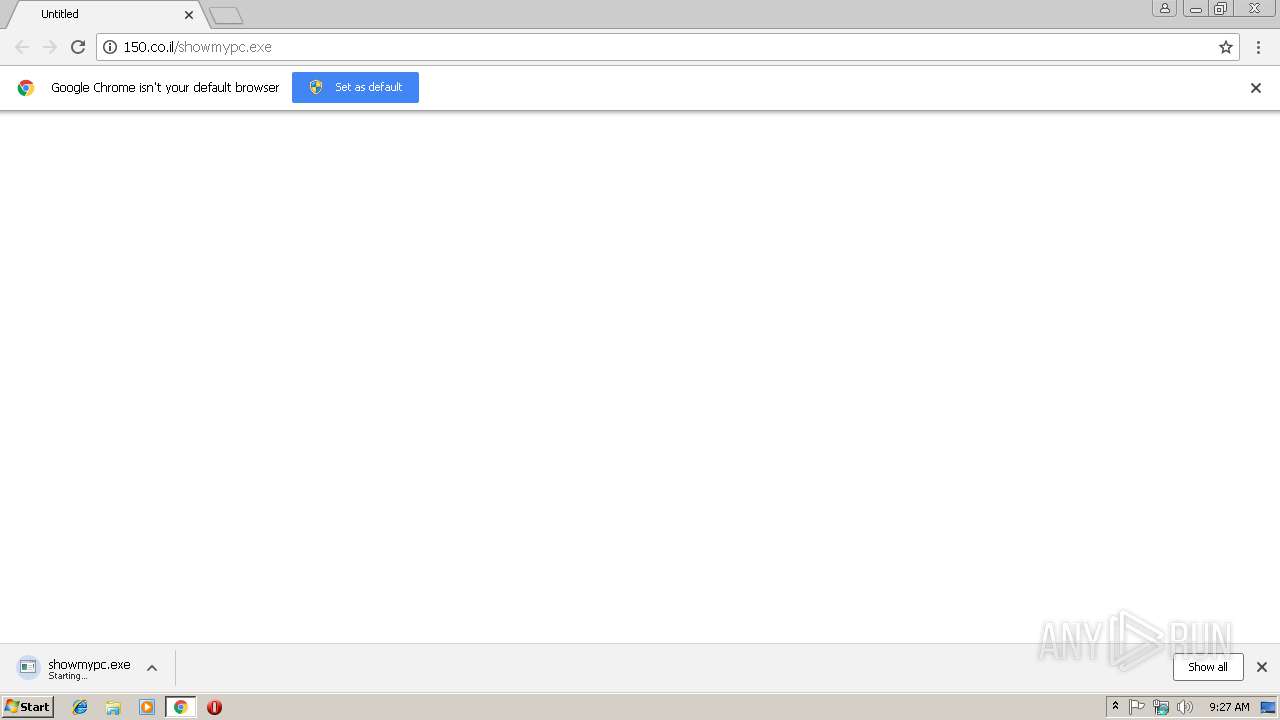
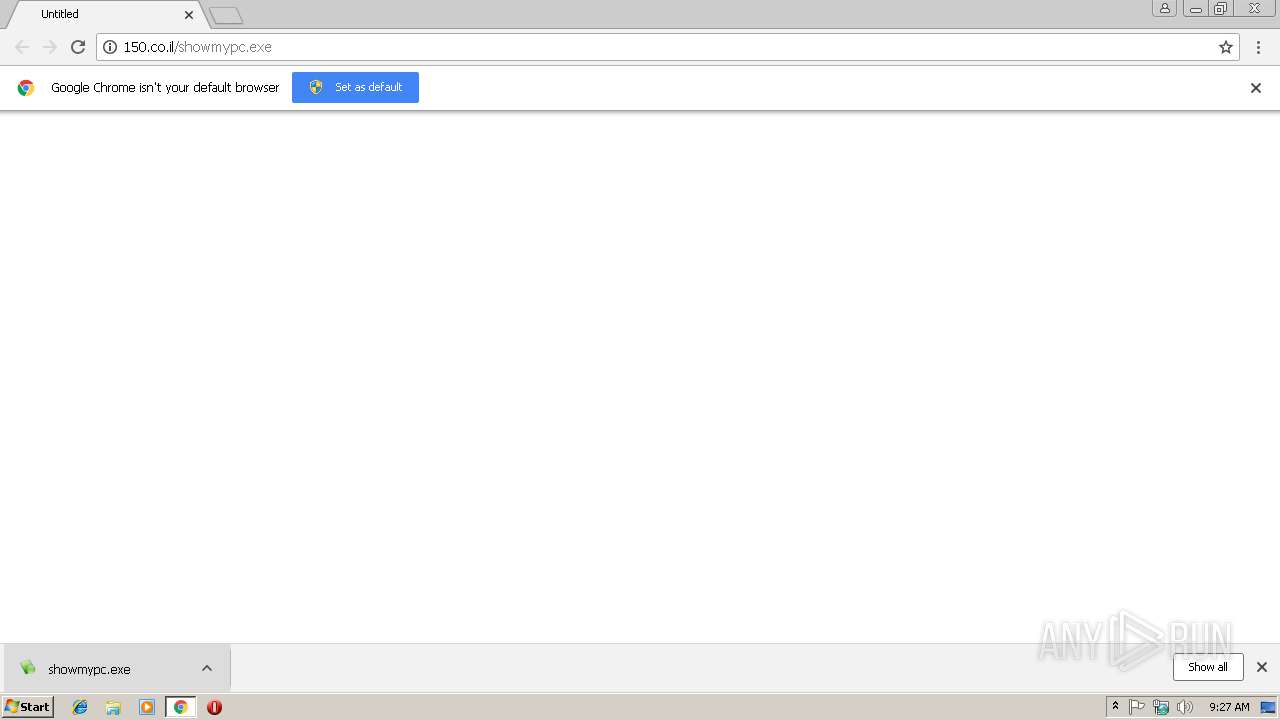
Downloads executable files from the Internet
- chrome.exe (PID: 3000)
Application was dropped or rewritten from another process
- showmypc.exe (PID: 568)
- SMPCSetup.exe (PID: 2488)
- SMPCSetup.exe (PID: 3664)
- tvnserver.exe (PID: 4068)
- spcplink.exe (PID: 1516)
- tvnserver.exe (PID: 3372)
- tvnserver.exe (PID: 3376)
- smpcview.exe (PID: 2296)
- tvnserver.exe (PID: 2324)
Loads dropped or rewritten executable
- showmypc.exe (PID: 568)
- SMPCSetup.exe (PID: 2488)
- SMPCSetup.exe (PID: 3664)
- regsvr32.exe (PID: 2176)
Starts NET.EXE for service management
- SMPCSetup.exe (PID: 2488)
- SMPCSetup.exe (PID: 3664)
Changes the autorun value in the registry
- tvnserver.exe (PID: 4068)
Registers / Runs the DLL via REGSVR32.EXE
- SMPCSetup.exe (PID: 3664)
Changes settings of System certificates
- SMPCSetup.exe (PID: 3664)
- smpcview.exe (PID: 2296)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3000)
- showmypc.exe (PID: 568)
- SMPCSetup.exe (PID: 3664)
Reads internet explorer settings
- SMPCSetup.exe (PID: 2488)
- SMPCSetup.exe (PID: 3664)
Application launched itself
- SMPCSetup.exe (PID: 2488)
- tvnserver.exe (PID: 3376)
Reads Environment values
- SMPCSetup.exe (PID: 2488)
- SMPCSetup.exe (PID: 3664)
Reads Internet Cache Settings
- SMPCSetup.exe (PID: 3664)
Uses NETSH.EXE for network configuration
- SMPCSetup.exe (PID: 2488)
- SMPCSetup.exe (PID: 3664)
Creates files in the user directory
- SMPCSetup.exe (PID: 3664)
Adds / modifies Windows certificates
- SMPCSetup.exe (PID: 3664)
- smpcview.exe (PID: 2296)
Creates files in the program directory
- SMPCSetup.exe (PID: 3664)
Creates COM task schedule object
- regsvr32.exe (PID: 2176)
INFO
Application launched itself
- chrome.exe (PID: 3000)
Creates files in the user directory
- chrome.exe (PID: 3000)
Changes settings of System certificates
- chrome.exe (PID: 3000)
Reads Internet Cache Settings
- chrome.exe (PID: 3000)
Reads settings of System Certificates
- SMPCSetup.exe (PID: 2488)
- chrome.exe (PID: 3000)
- SMPCSetup.exe (PID: 3664)
- smpcview.exe (PID: 2296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
105
Monitored processes
49
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | "C:\Users\admin\Downloads\showmypc.exe" | C:\Users\admin\Downloads\showmypc.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1008 | "C:\Windows\System32\netsh.exe" firewall add allowedprogram "C:\Users\admin\AppData\Local\Temp\ShowMyPC\-showmypc\SMPCSetup.exe" "ShowMyPCAuto" ENABLE | C:\Windows\System32\netsh.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1012 | C:\Windows\system32\net1 stop uvnc_service | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=51A7732C4E7F040A34A171274E68CDC0 --mojo-platform-channel-handle=796 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1516 | "C:\Users\admin\AppData\Local\Temp\ShowMyPC\-showmypc\spcplink.exe" -C -4 -ssh -2 -P 443 -N -R 18698:localhost:6900 -L 18699:download3.showmypc.com:80 -R 18702:localhost:18702 -smpi df7452852a7e sshuser-eec832613dae@svr4.showmypc.com | C:\Users\admin\AppData\Local\Temp\ShowMyPC\-showmypc\spcplink.exe | SMPCSetup.exe | ||||||||||||
User: admin Company: ShowMyPC Integrity Level: HIGH Description: ShowMyPC Exit code: 0 Version: Release 2509 Modules
| |||||||||||||||
| 1728 | "C:\Windows\System32\netsh.exe" firewall delete allowedprogram "C:\Users\admin\AppData\Local\Temp\ShowMyPC\-showmypc\tvnserver.exe" | C:\Windows\System32\netsh.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,1271383365220138652,16944992696421106841,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D047695F52D4E5A856185BA6D38AF85B --mojo-platform-channel-handle=980 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2176 | "C:\Windows\System32\regsvr32.exe" "C:\Users\admin\AppData\Local\Temp\ShowMyPC\-showmypc\wodVPN.dll" /s | C:\Windows\System32\regsvr32.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2192 | "C:\Windows\System32\net.exe" stop uvnc_service | C:\Windows\System32\net.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2244 | "C:\Windows\System32\netsh.exe" firewall delete allowedprogram "C:\Users\admin\AppData\Local\Temp\ShowMyPC\-showmypc\SMPCSetup.exe" | C:\Windows\System32\netsh.exe | — | SMPCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 424
Read events
2 397
Write events
1 024
Delete events
3
Modification events
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3000-13194350855050125 |
Value: 259 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3000-13194350855050125 |
Value: 259 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
20
Suspicious files
54
Text files
101
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\83f5afba-a556-4815-9882-34b2f247f92e.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ed896082-3c2b-42a5-93e1-f3058c278858.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\590e3378-7853-4813-b40a-ea9632749e64.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF246d12.TMP | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\Downloads\31870c02-95a2-455a-9199-6b4254a9bda9.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\Downloads\Unconfirmed 346251.crdownload | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF246d03.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
61
TCP/UDP connections
75
DNS requests
46
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2488 | SMPCSetup.exe | GET | — | 35.239.221.136:80 | http://showmypc.com/app/about-us1.html?pv=3515 | US | — | — | malicious |
3664 | SMPCSetup.exe | GET | 200 | 52.216.132.173:80 | http://s3.showmypc.com/js/themes/base/ui.datepicker.css | US | text | 3.90 Kb | shared |
3664 | SMPCSetup.exe | GET | 200 | 172.217.16.194:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 29.4 Kb | whitelisted |
3664 | SMPCSetup.exe | GET | 200 | 35.239.221.136:80 | http://showmypc.com/app/about-us1.html?pv=3515 | US | html | 4.92 Kb | malicious |
3000 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSACodeSigningCA.crt | GB | der | 1.47 Kb | whitelisted |
3664 | SMPCSetup.exe | GET | 200 | 52.216.132.173:80 | http://s3.showmypc.com/js/themes/base/ui.all.css | US | text | 49 b | shared |
3664 | SMPCSetup.exe | GET | 200 | 52.216.132.173:80 | http://s3.showmypc.com/js/themes/base/ui.dialog.css | US | text | 1.15 Kb | shared |
3664 | SMPCSetup.exe | GET | 200 | 52.216.132.173:80 | http://s3.showmypc.com/js/themes/base/ui.theme.css | US | text | 17.5 Kb | shared |
3000 | chrome.exe | GET | 200 | 84.95.150.12:80 | http://150.co.il/showmypc.exe | IL | executable | 2.46 Mb | suspicious |
3664 | SMPCSetup.exe | GET | 200 | 52.216.132.173:80 | http://s3.showmypc.com/js/jquery-1.11.2.min.js | US | text | 93.6 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3000 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 172.217.23.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 84.95.150.12:80 | 150.co.il | 012 Smile Communications LTD. | IL | suspicious |
3000 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 216.58.206.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2488 | SMPCSetup.exe | 35.239.221.136:80 | showmypc.com | — | US | suspicious |
3664 | SMPCSetup.exe | 35.239.221.136:80 | showmypc.com | — | US | suspicious |
3664 | SMPCSetup.exe | 35.239.221.136:443 | showmypc.com | — | US | suspicious |
3664 | SMPCSetup.exe | 52.216.132.173:80 | s3.showmypc.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
150.co.il |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
crt.comodoca.com |
| whitelisted |
showmypc.com |
| malicious |
s3.showmypc.com |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3000 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2296 | smpcview.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2296 | smpcview.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2296 | smpcview.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2296 | smpcview.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2296 | smpcview.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |
2296 | smpcview.exe | Generic Protocol Command Decode | SURICATA STREAM FIN out of window |