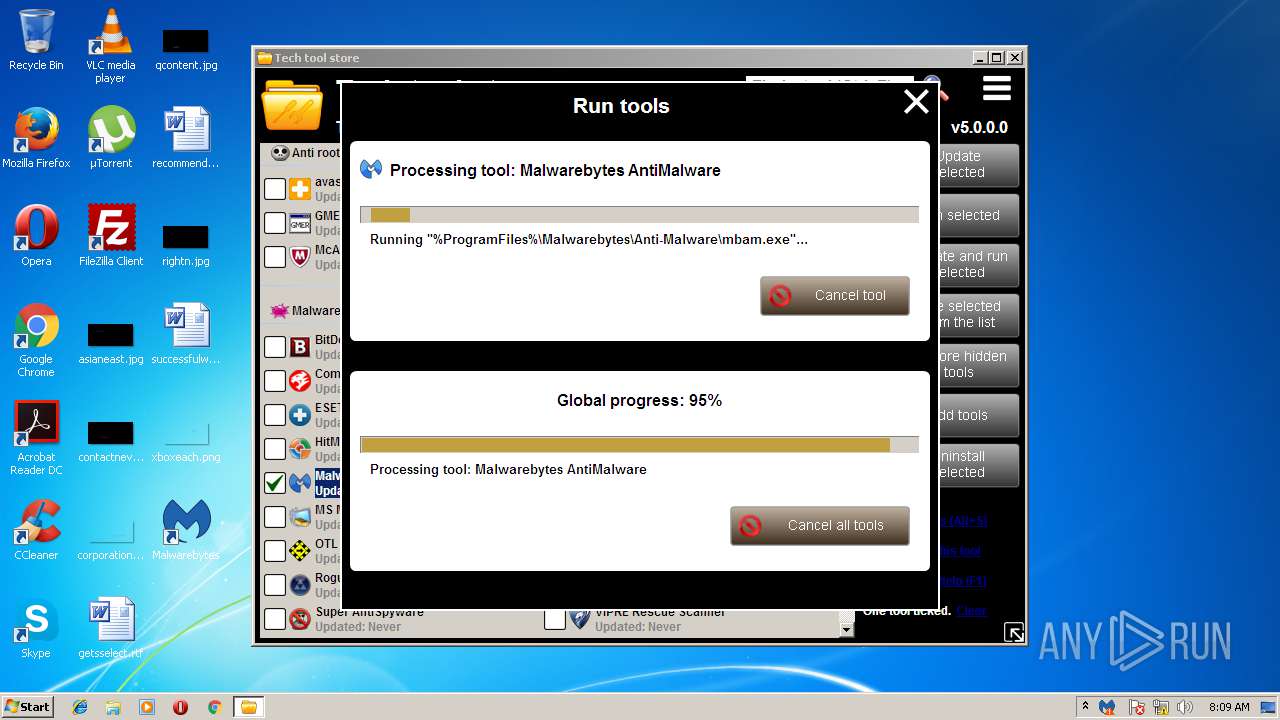
| download: | TechToolStore.exe |
| Full analysis: | https://app.any.run/tasks/564d33c1-59ab-4bee-ad21-59b8336e9f2c |
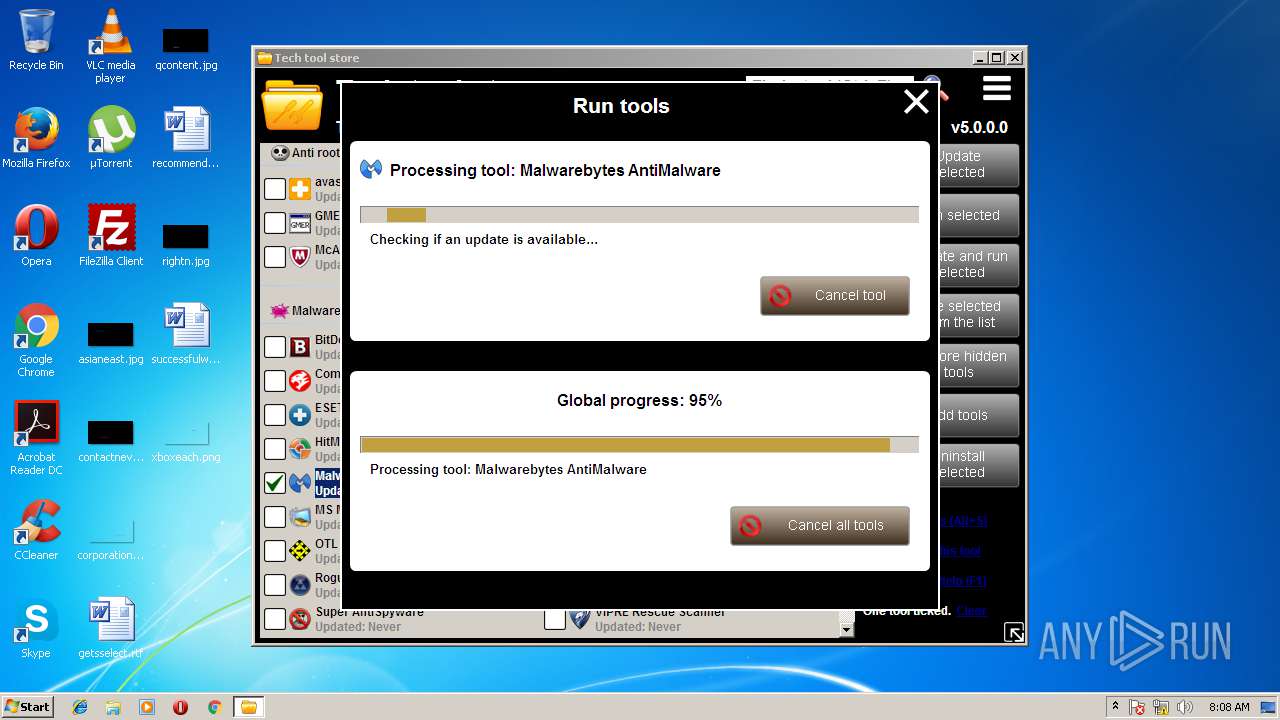
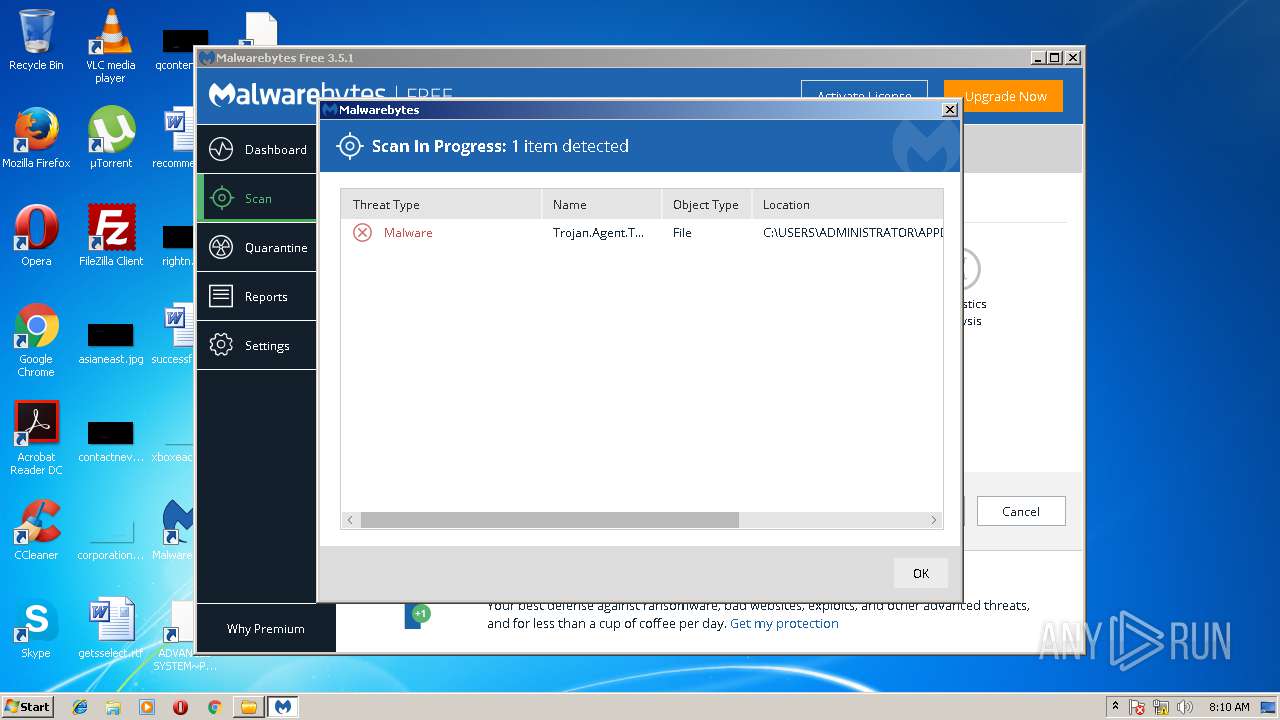
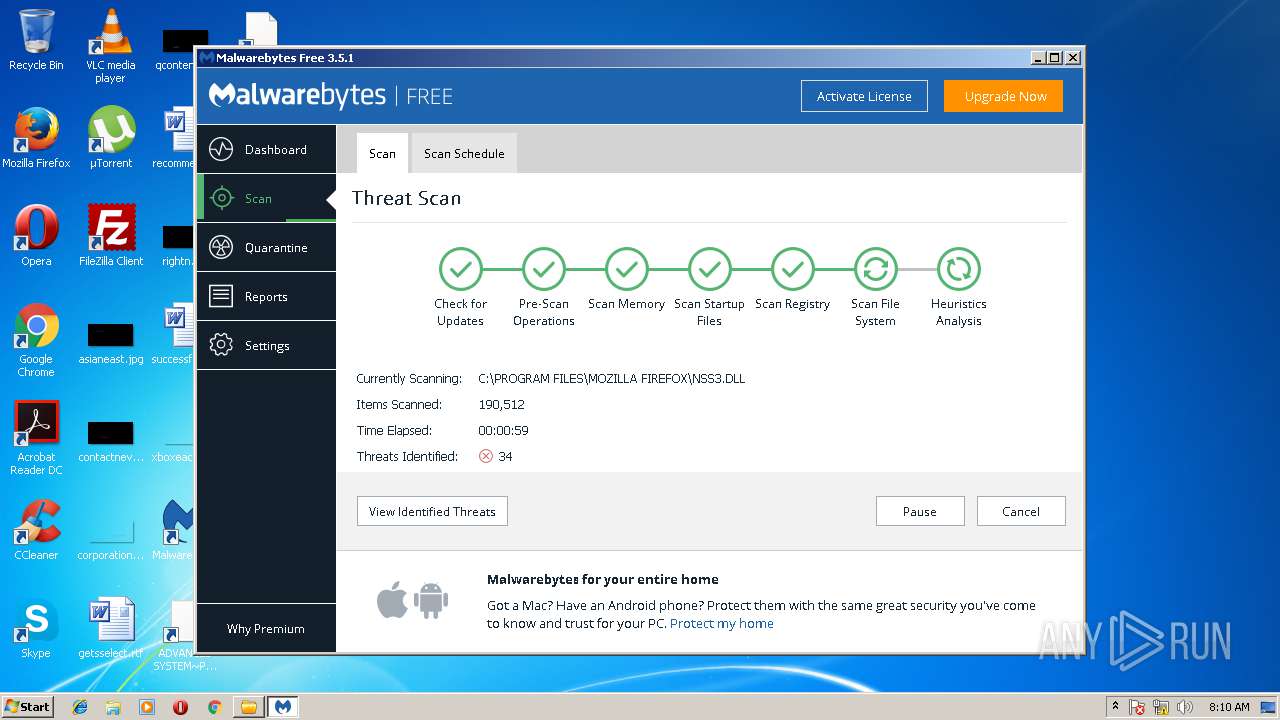
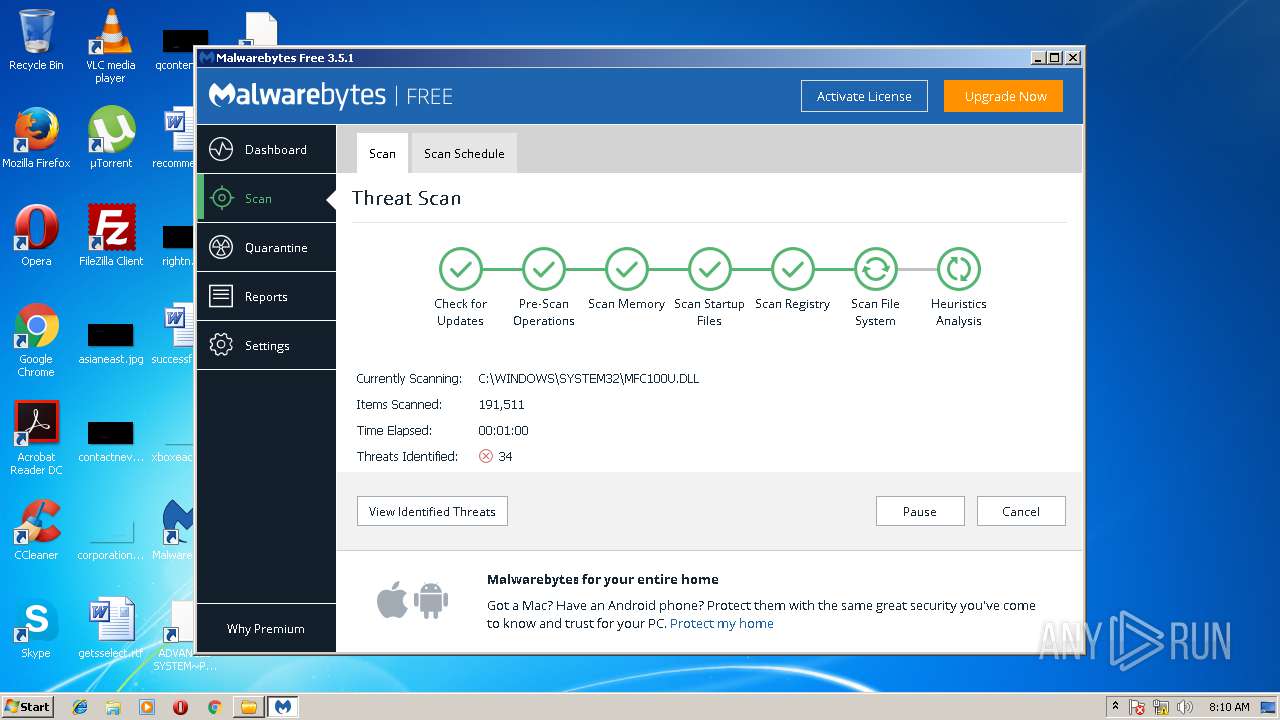
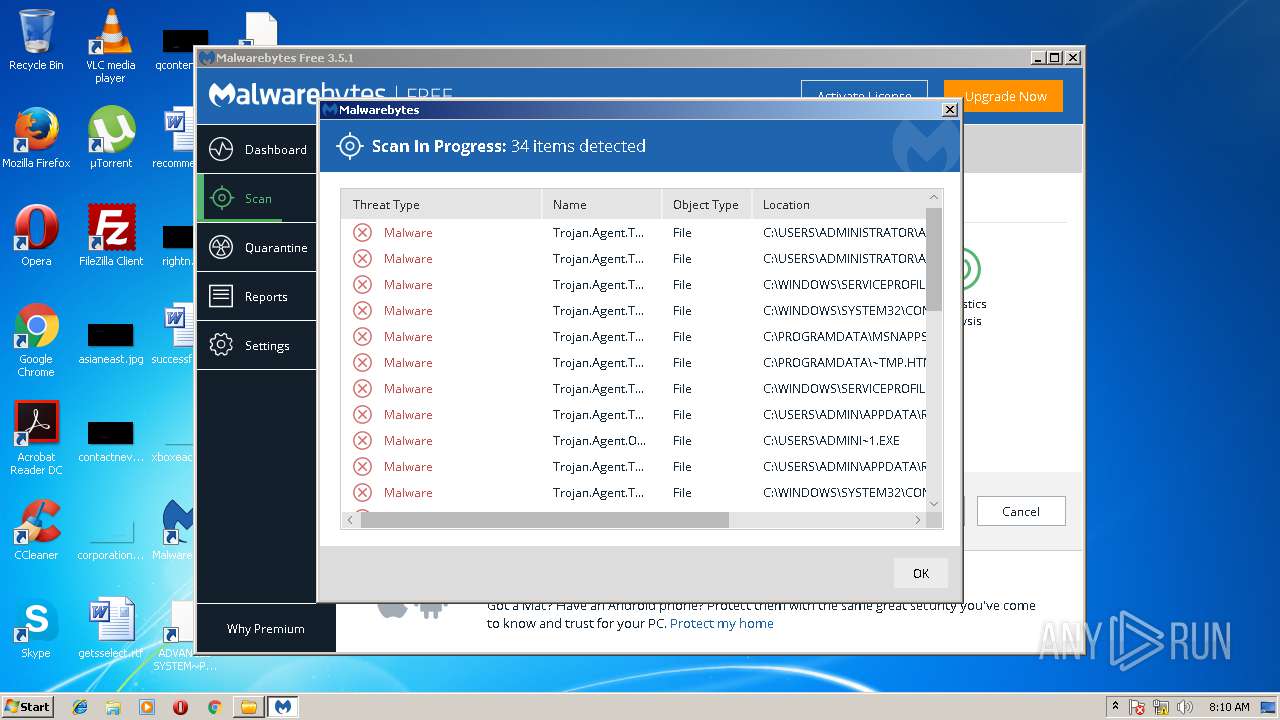
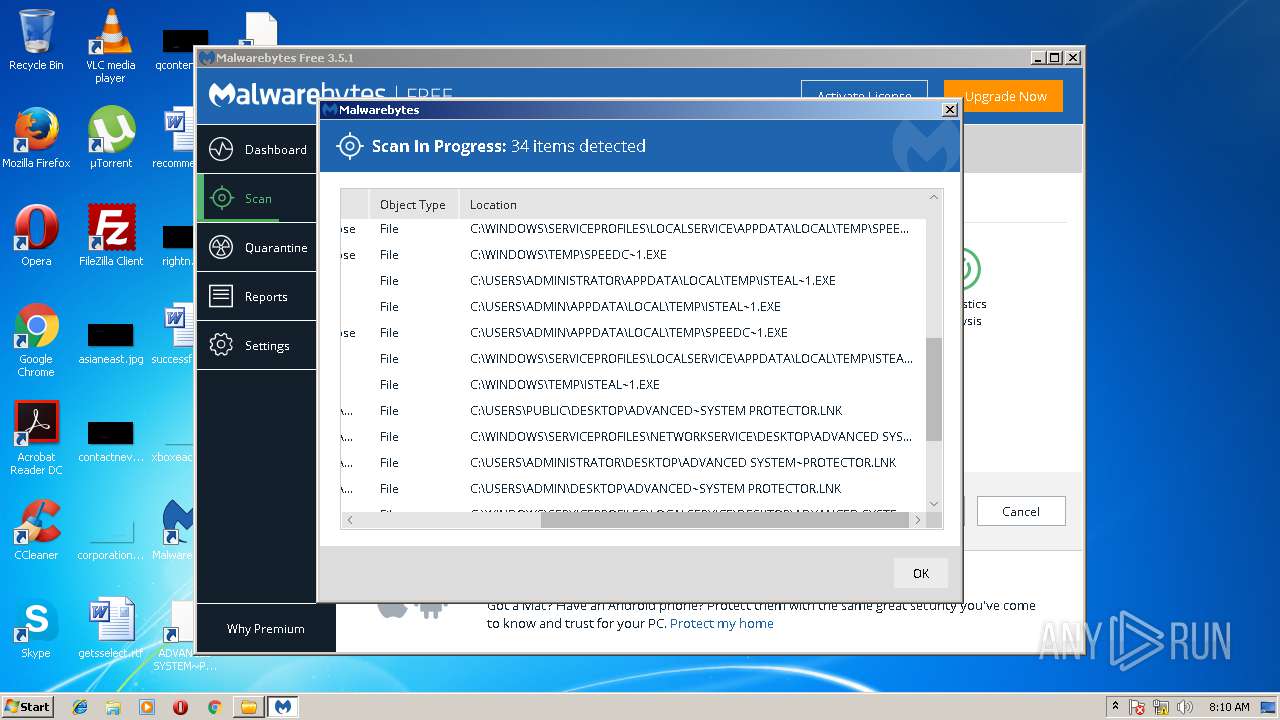
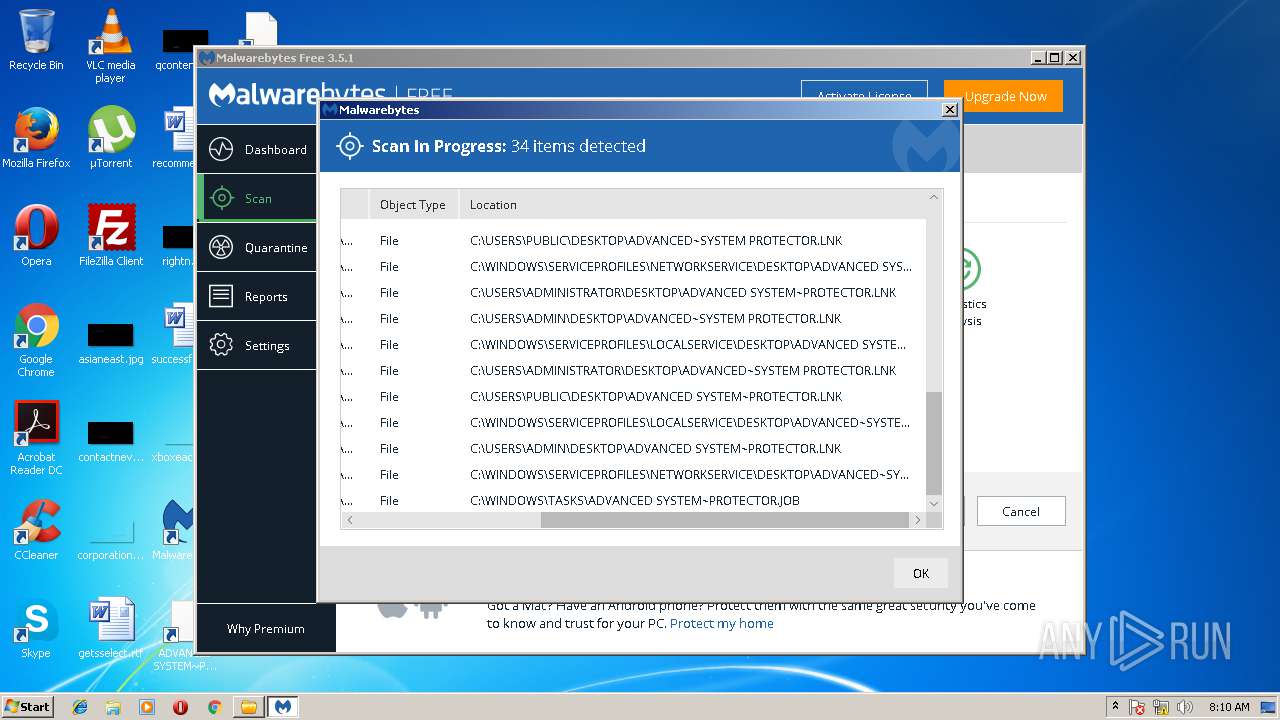
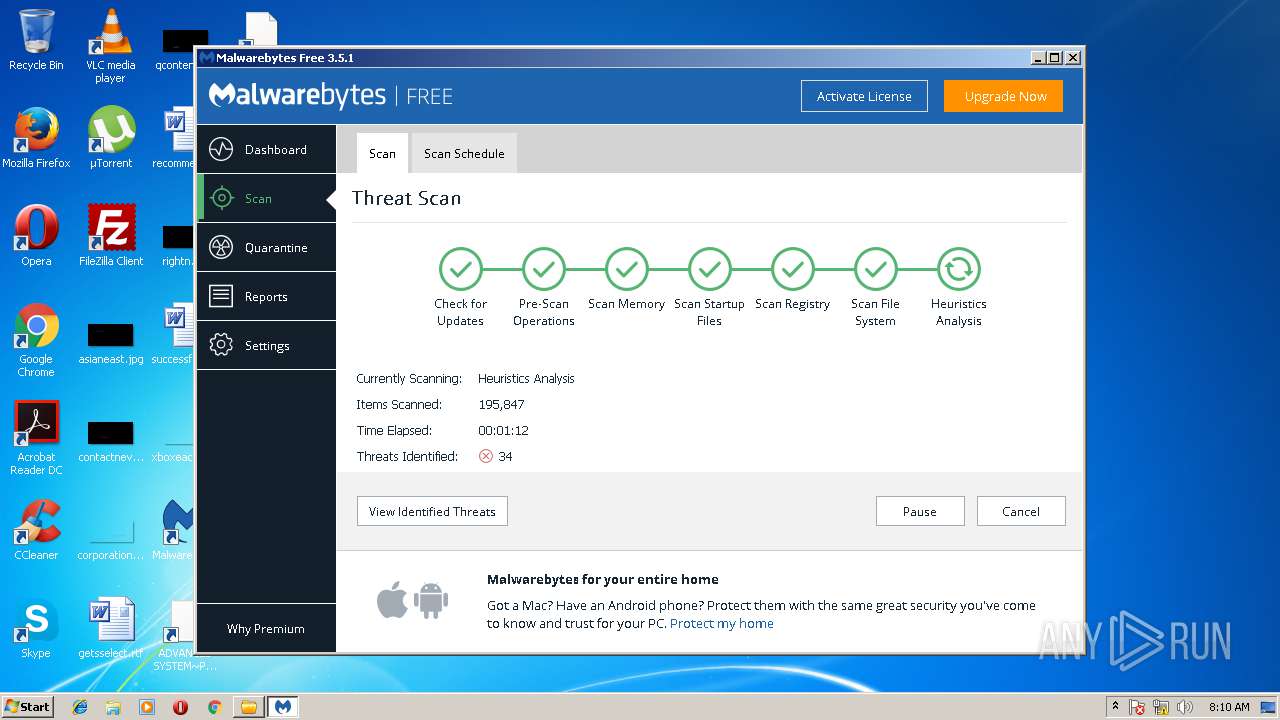
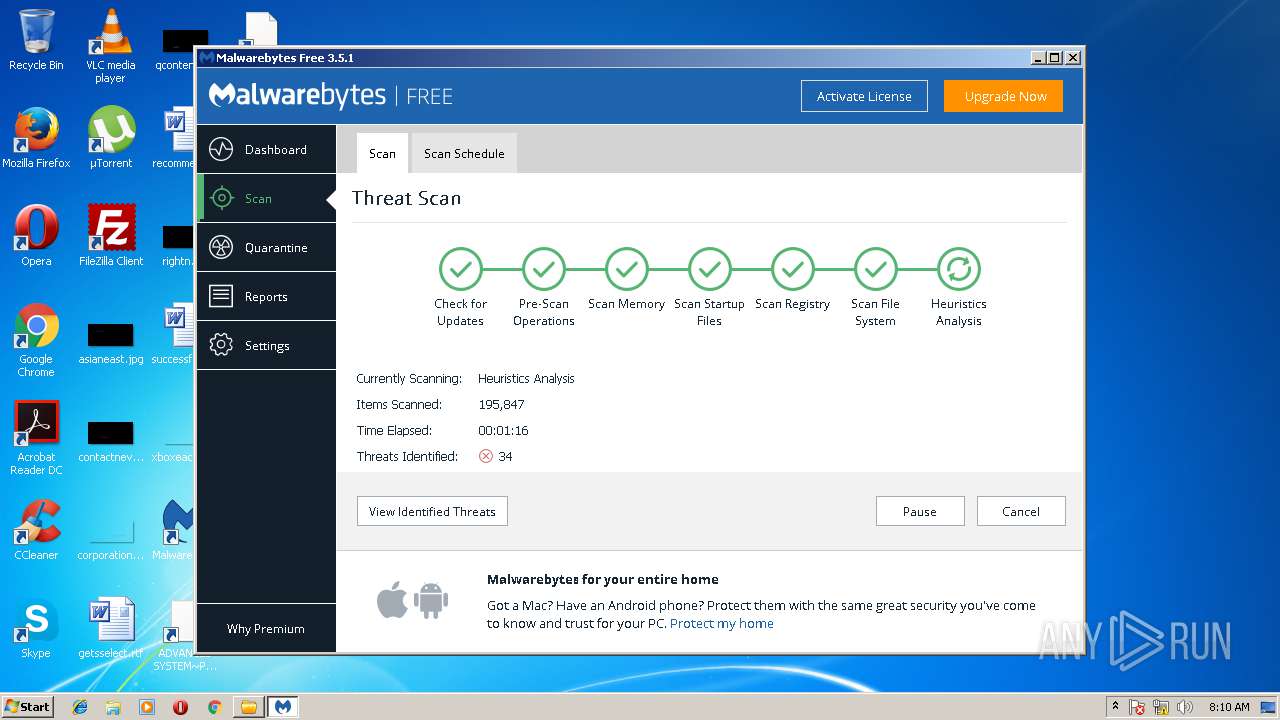
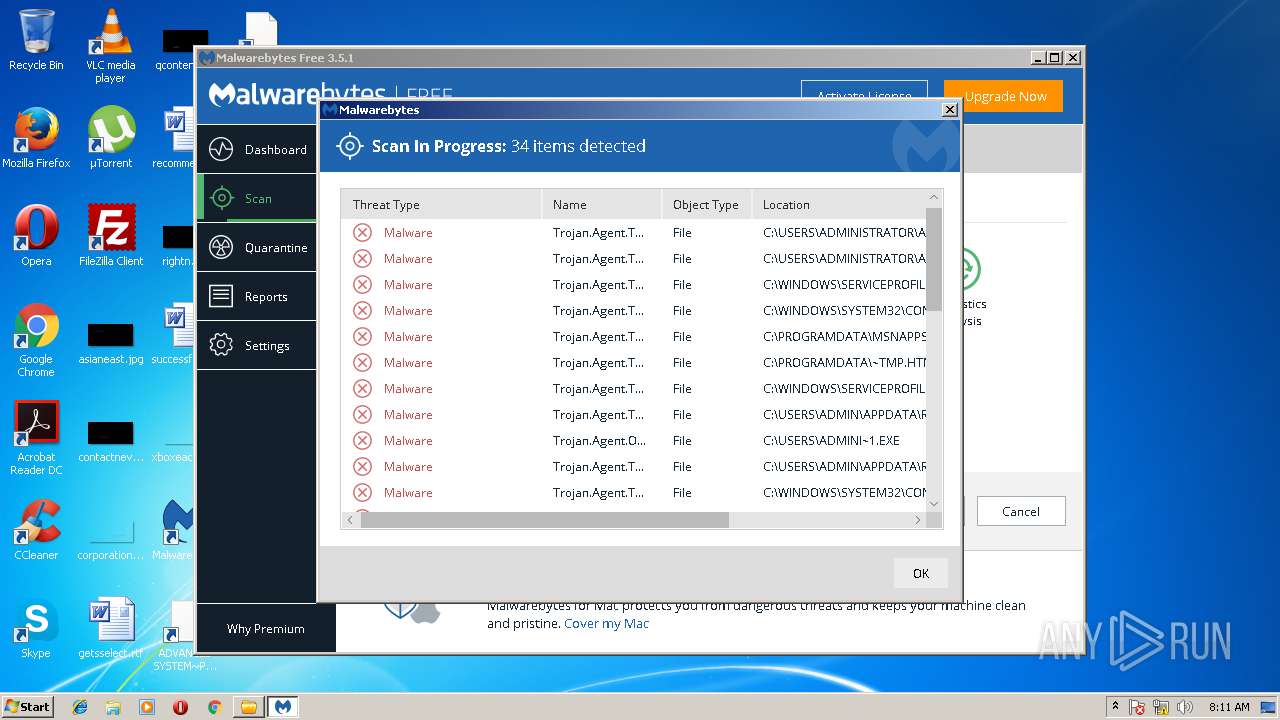
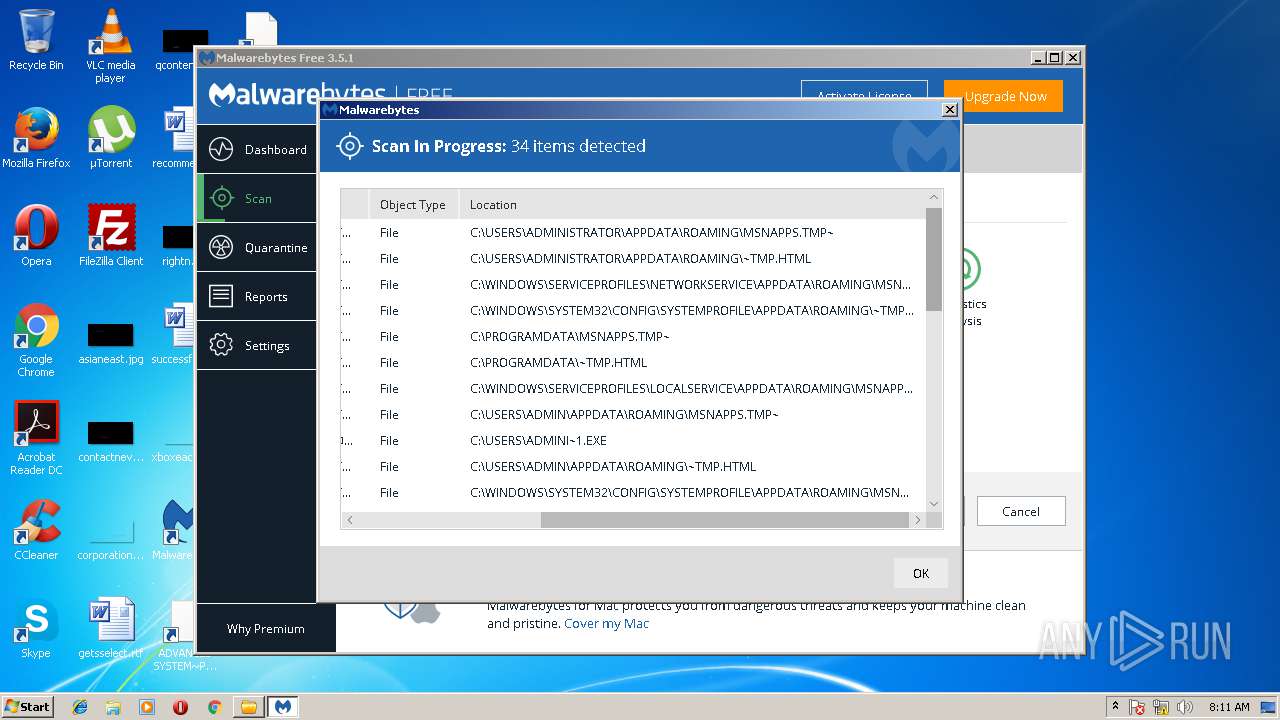
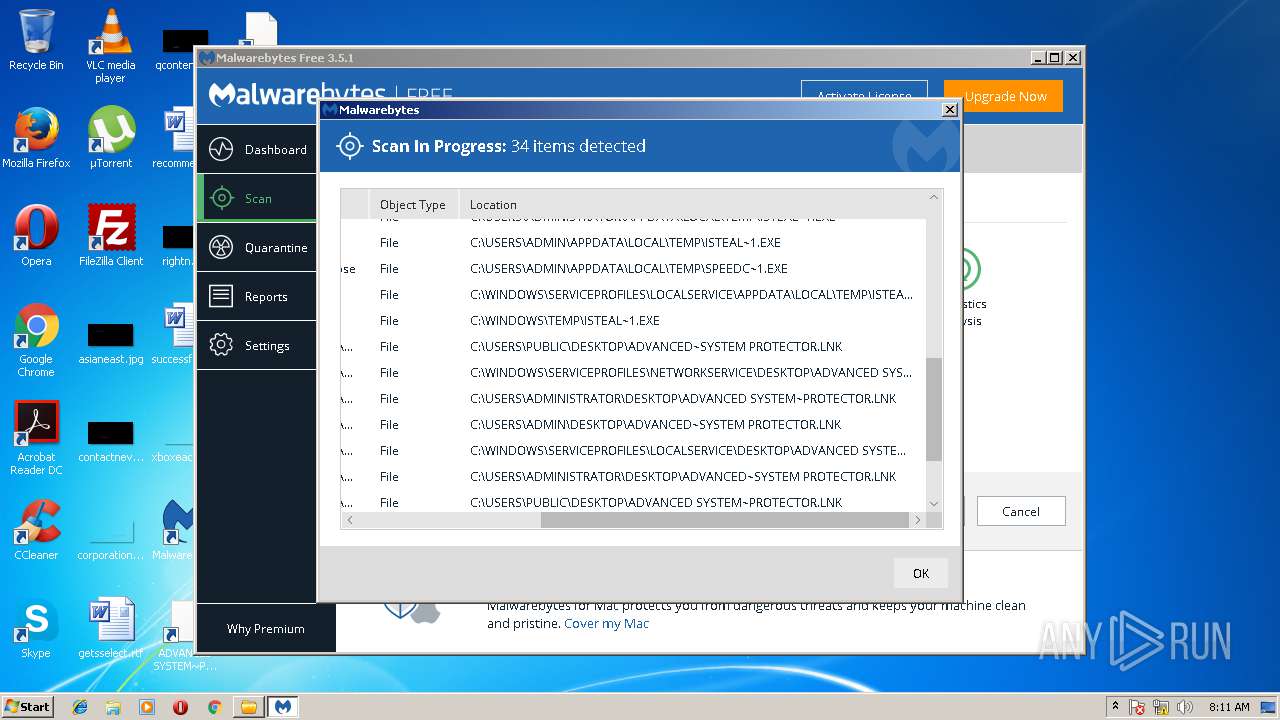
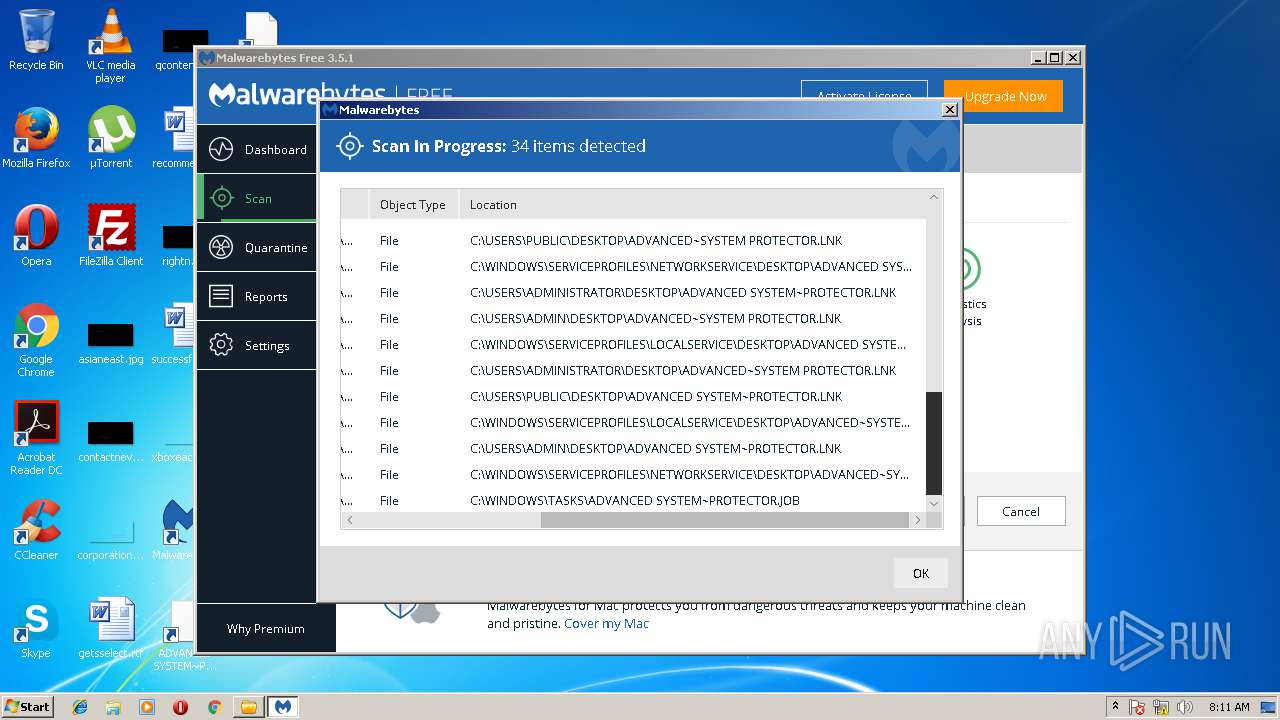
| Verdict: | Malicious activity |
| Analysis date: | June 03, 2018, 07:08:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8EB732C76CF676C42171BCA8BDC0F9E5 |
| SHA1: | B85629E0805DEEBB234A658A269945F22FFCAECF |
| SHA256: | 78904AE5A15A6E4461CF6C452C8F69B697A526998C4F986217ABF945B401D8BB |
| SSDEEP: | 49152:oeShDD5u2zmJkS9RPLtFa14BMw+U/KHWki4DBMuLSzmJkF9RPLtFa14BMw+UGX/:R4DQVJZ24LKi41Ma5Je248 |
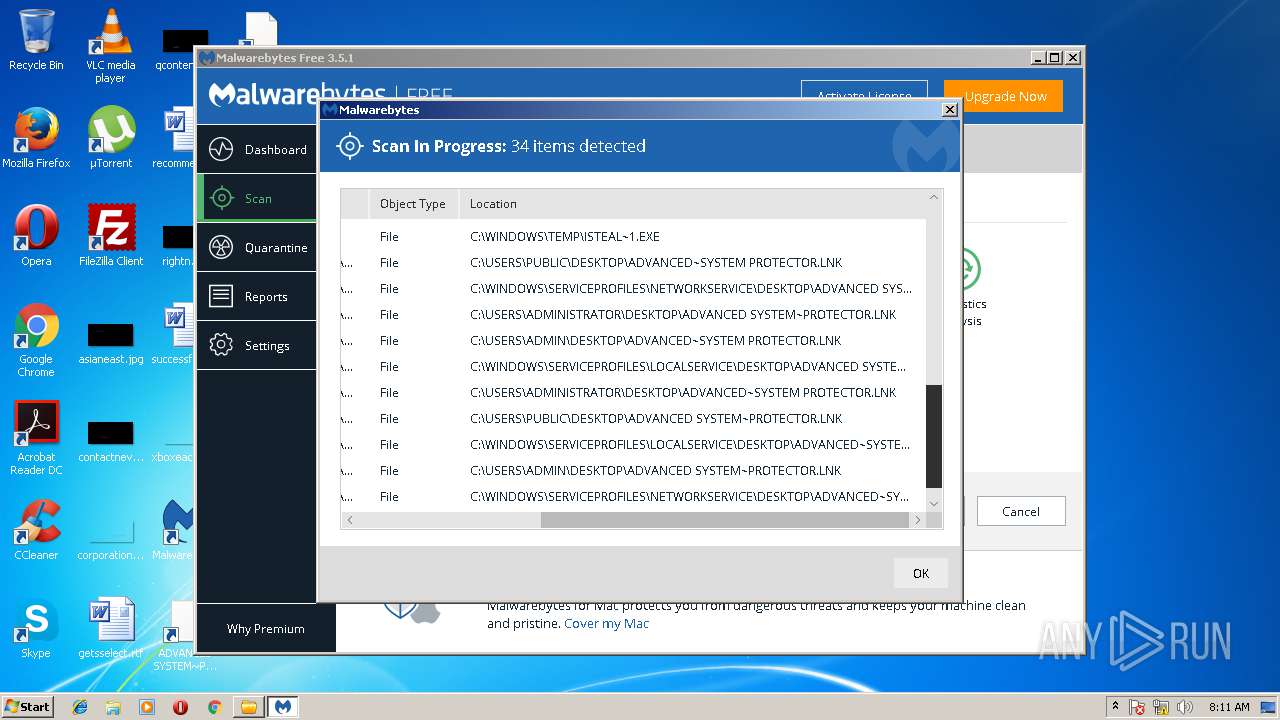
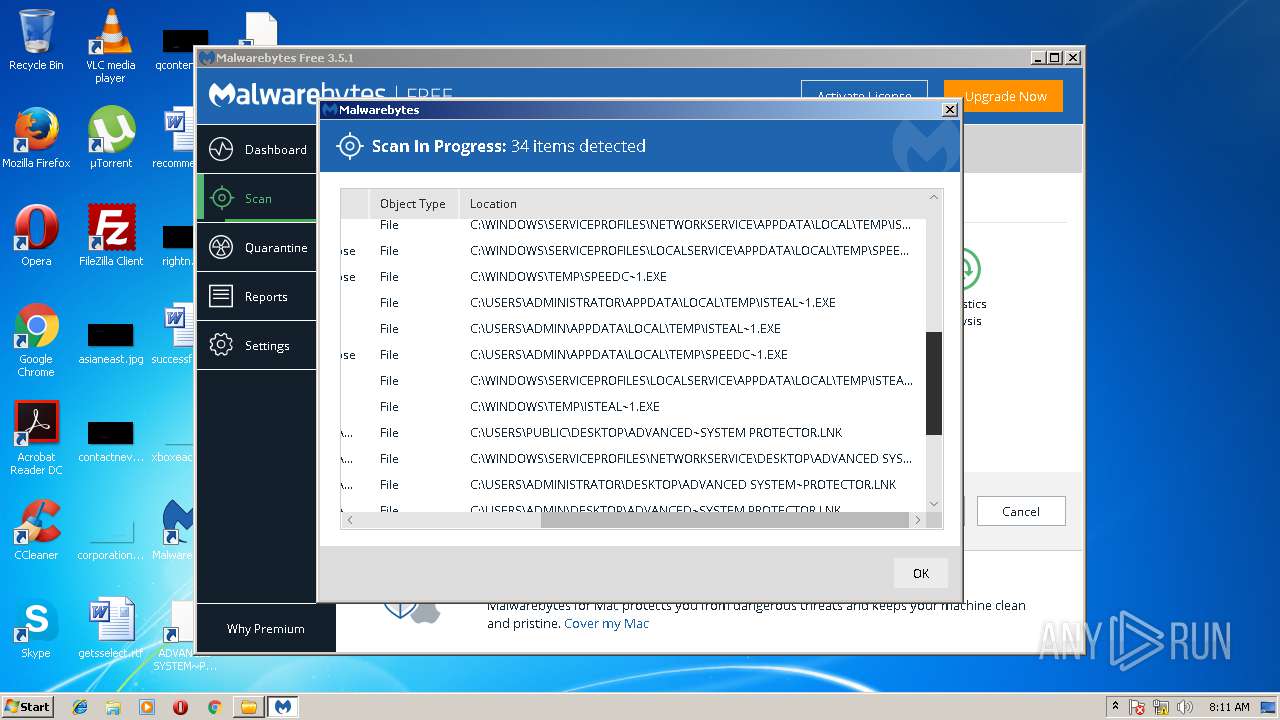
MALICIOUS
Changes settings of System certificates
- certutil.exe (PID: 1572)
- certutil.exe (PID: 3312)
- mbamservice.exe (PID: 3056)
Application was dropped or rewritten from another process
- mbamservice.exe (PID: 3056)
- mbamtray.exe (PID: 2268)
- mbam.exe (PID: 2824)
- assistant.exe (PID: 3900)
- MBAMWsc.exe (PID: 3692)
- MBAMWsc.exe (PID: 3568)
- MBAMWsc.exe (PID: 1488)
- MBAMWsc.exe (PID: 2040)
- MBAMWsc.exe (PID: 2596)
- mbamservice.exe (PID: 1340)
Loads dropped or rewritten executable
- mbamtray.exe (PID: 2268)
- mbamservice.exe (PID: 3056)
- assistant.exe (PID: 3900)
- mbam.exe (PID: 2824)
SUSPICIOUS
Reads the Windows organization settings
- MBAMSetup.tmp (PID: 3404)
Reads internet explorer settings
- TechToolStore.exe (PID: 1832)
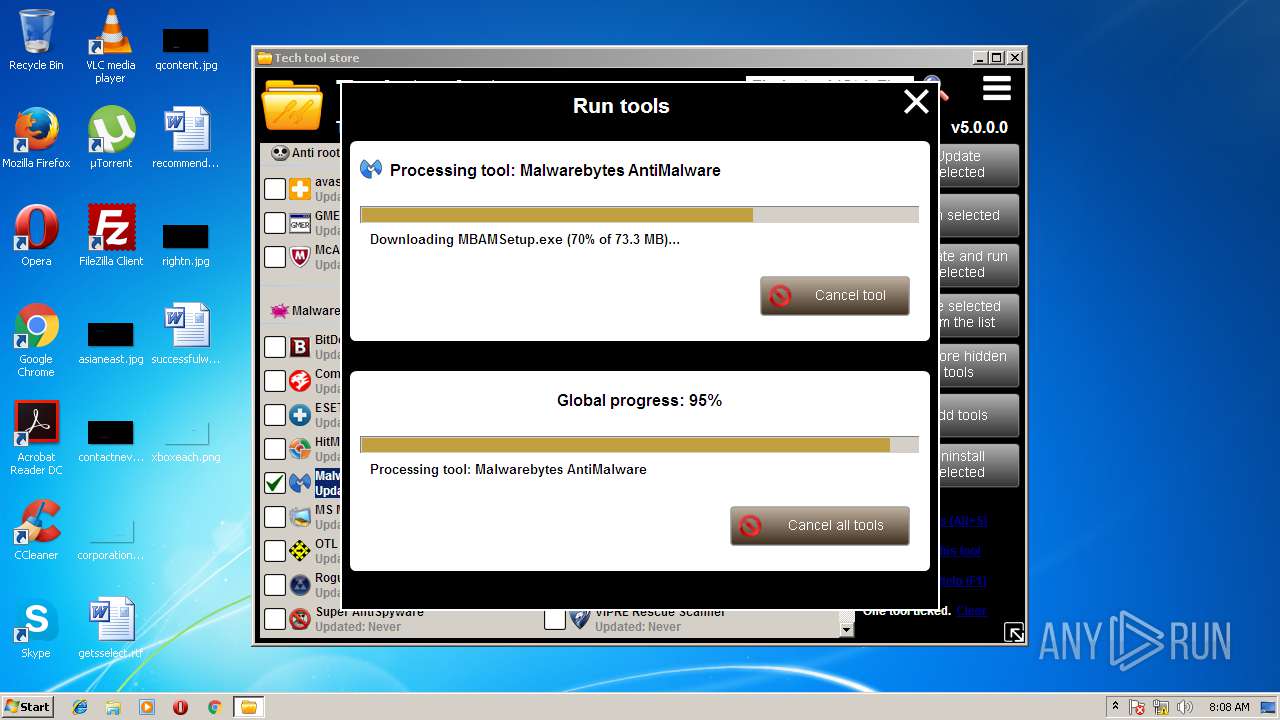
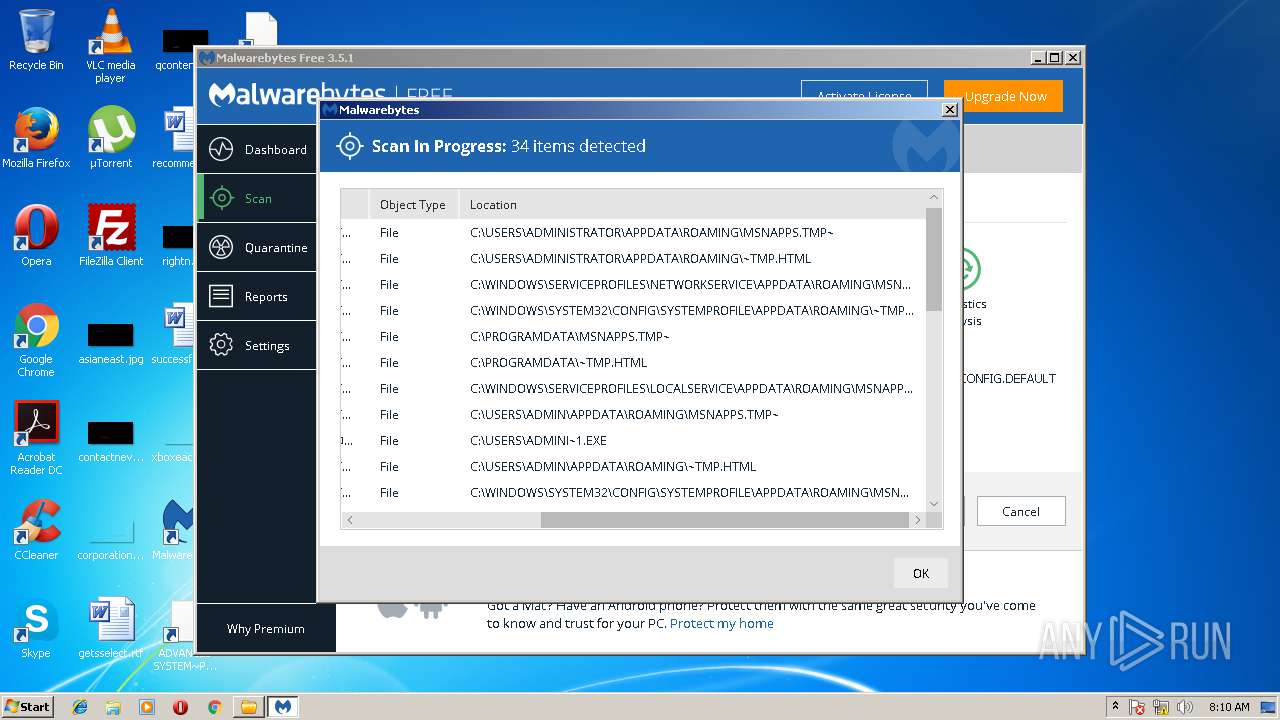
Executable content was dropped or overwritten
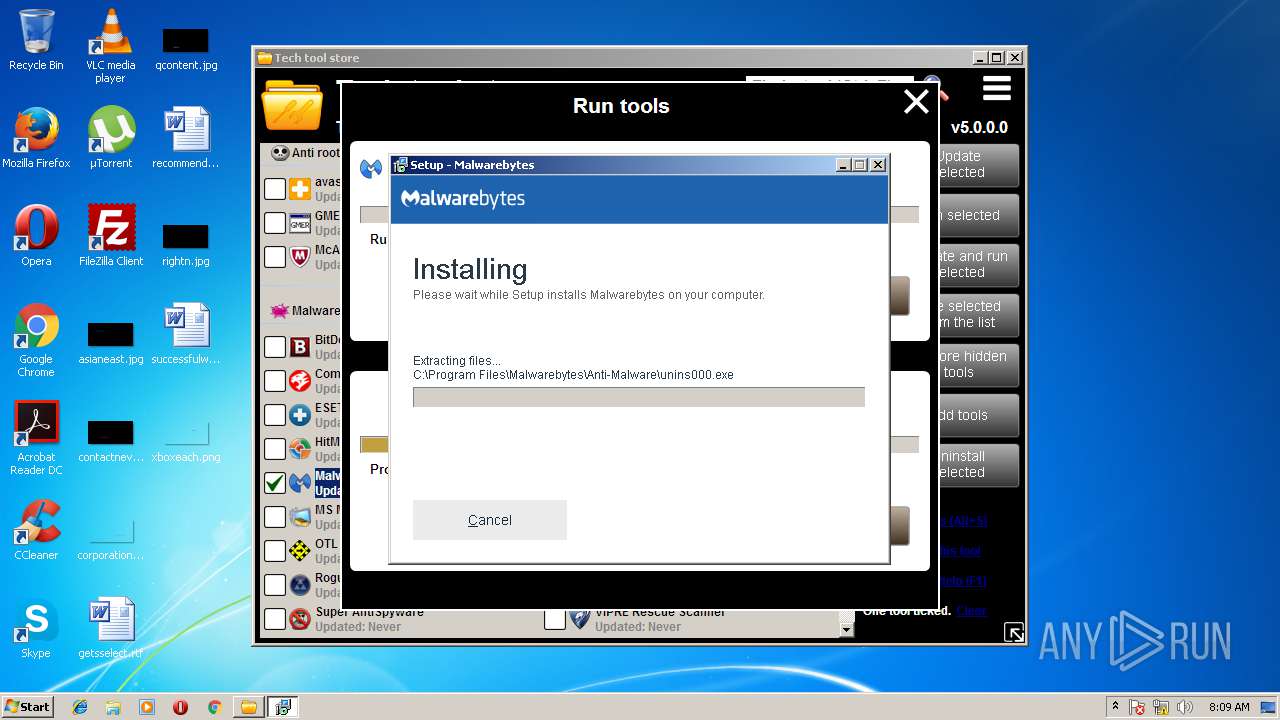
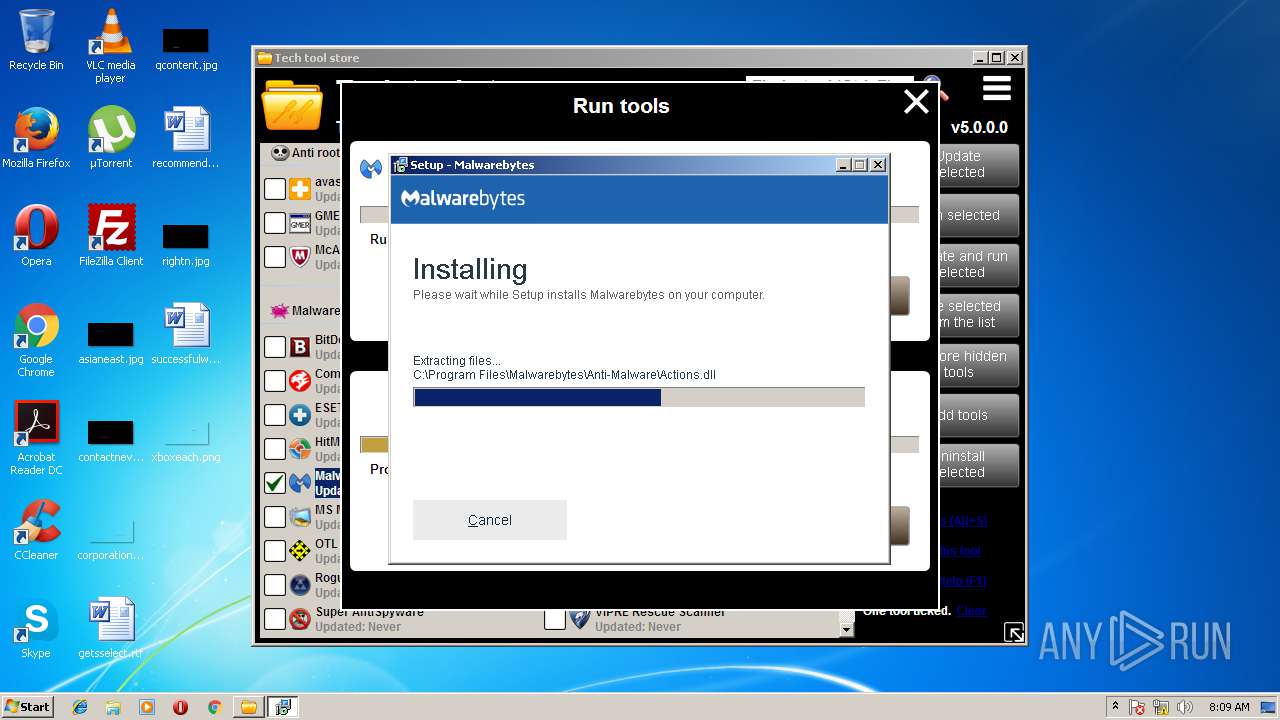
- MBAMSetup.exe (PID: 2668)
- MBAMSetup.tmp (PID: 3404)
- mbamservice.exe (PID: 3056)
Creates files in the program directory
- TechToolStore.exe (PID: 1832)
- mbamservice.exe (PID: 3056)
Creates files in the driver directory
- MBAMSetup.tmp (PID: 3404)
- mbamservice.exe (PID: 3056)
Reads Windows owner settings
- MBAMSetup.tmp (PID: 3404)
Changes IE settings (feature browser emulation)
- MBAMSetup.tmp (PID: 3404)
Creates files in the Windows directory
- MBAMSetup.tmp (PID: 3404)
- certutil.exe (PID: 1572)
- certutil.exe (PID: 3312)
- mbamservice.exe (PID: 3056)
Modifies the open verb of a shell class
- MBAMSetup.tmp (PID: 3404)
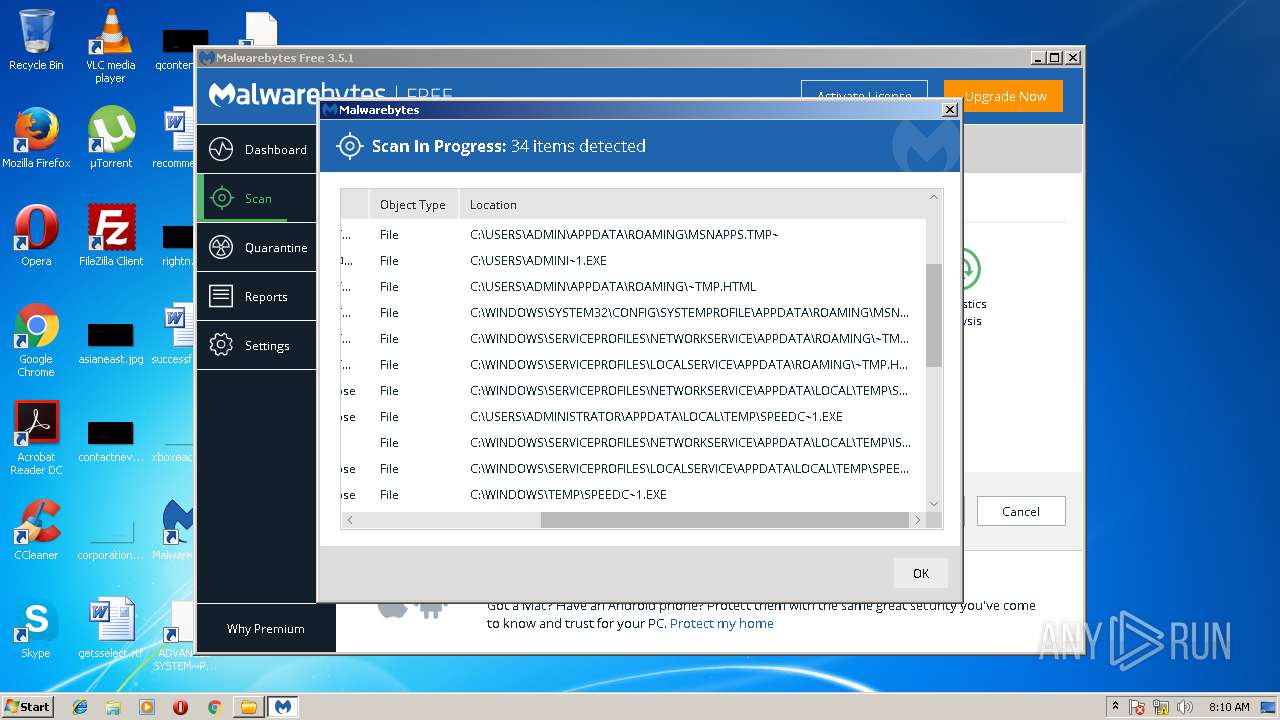
Removes files from Windows directory
- certutil.exe (PID: 1572)
- certutil.exe (PID: 3312)
- mbamservice.exe (PID: 3056)
Creates or modifies windows services
- mbamservice.exe (PID: 1340)
- mbamservice.exe (PID: 3056)
Searches for installed software
- MBAMSetup.tmp (PID: 3404)
- mbamservice.exe (PID: 3056)
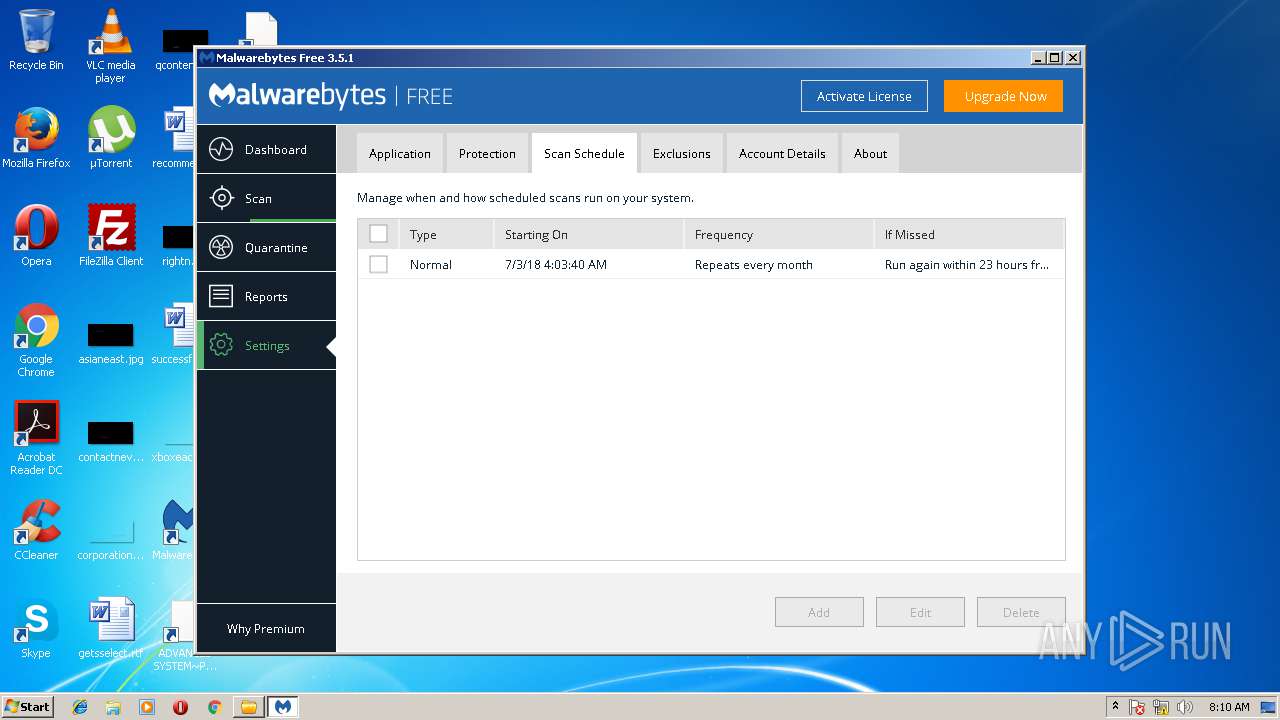
Creates COM task schedule object
- mbamservice.exe (PID: 3056)
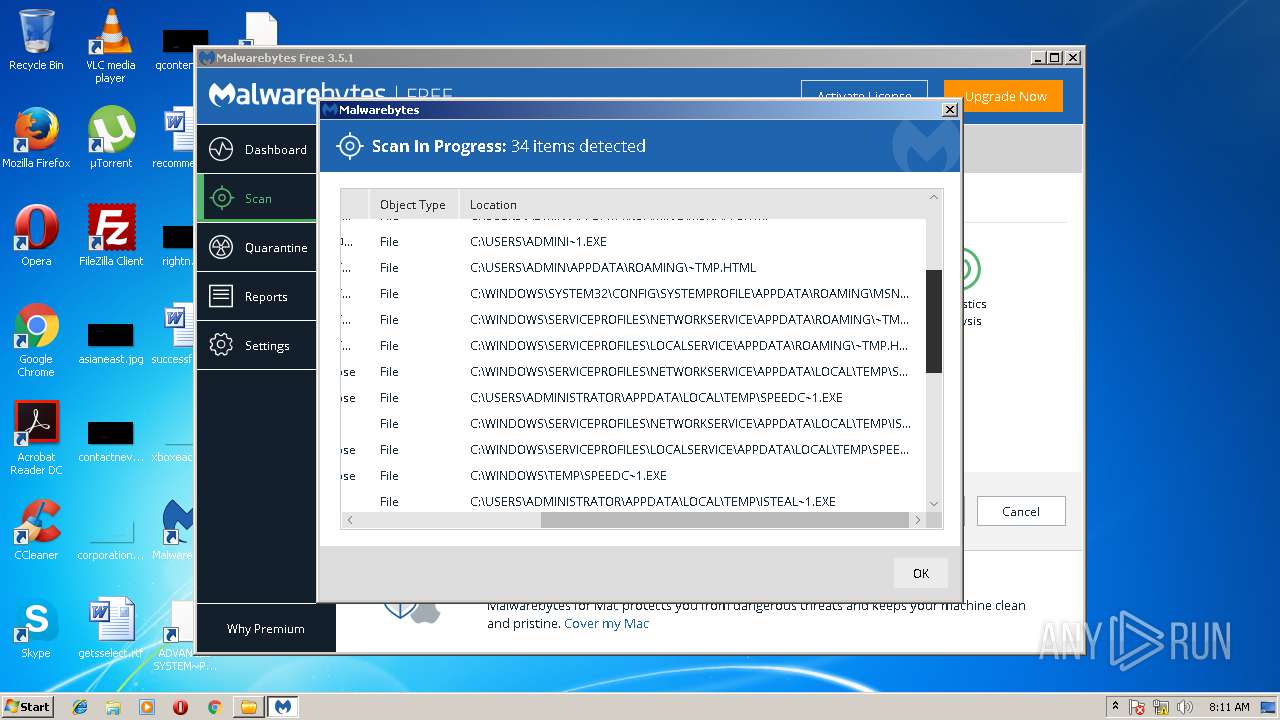
Creates files in the user directory
- mbam.exe (PID: 2824)
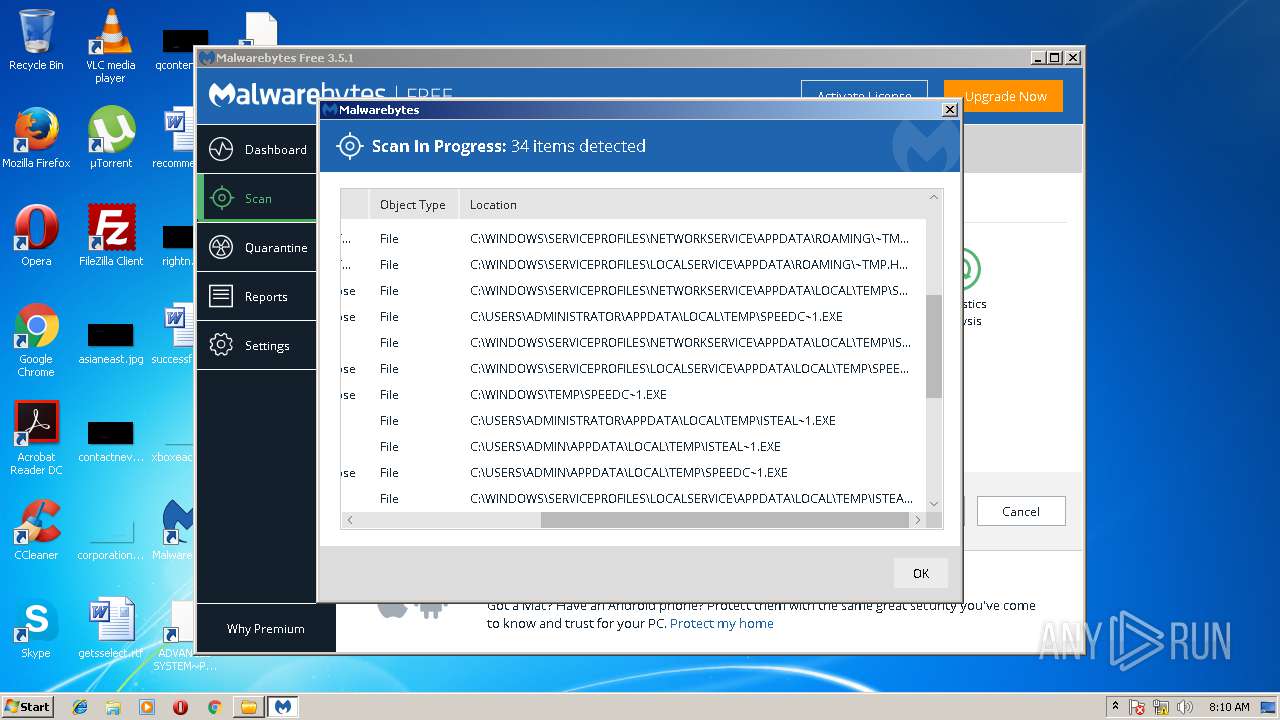
Adds / modifies Windows certificates
- mbamservice.exe (PID: 3056)
INFO
Loads dropped or rewritten executable
- MBAMSetup.tmp (PID: 3404)
Application was dropped or rewritten from another process
- MBAMSetup.tmp (PID: 3404)
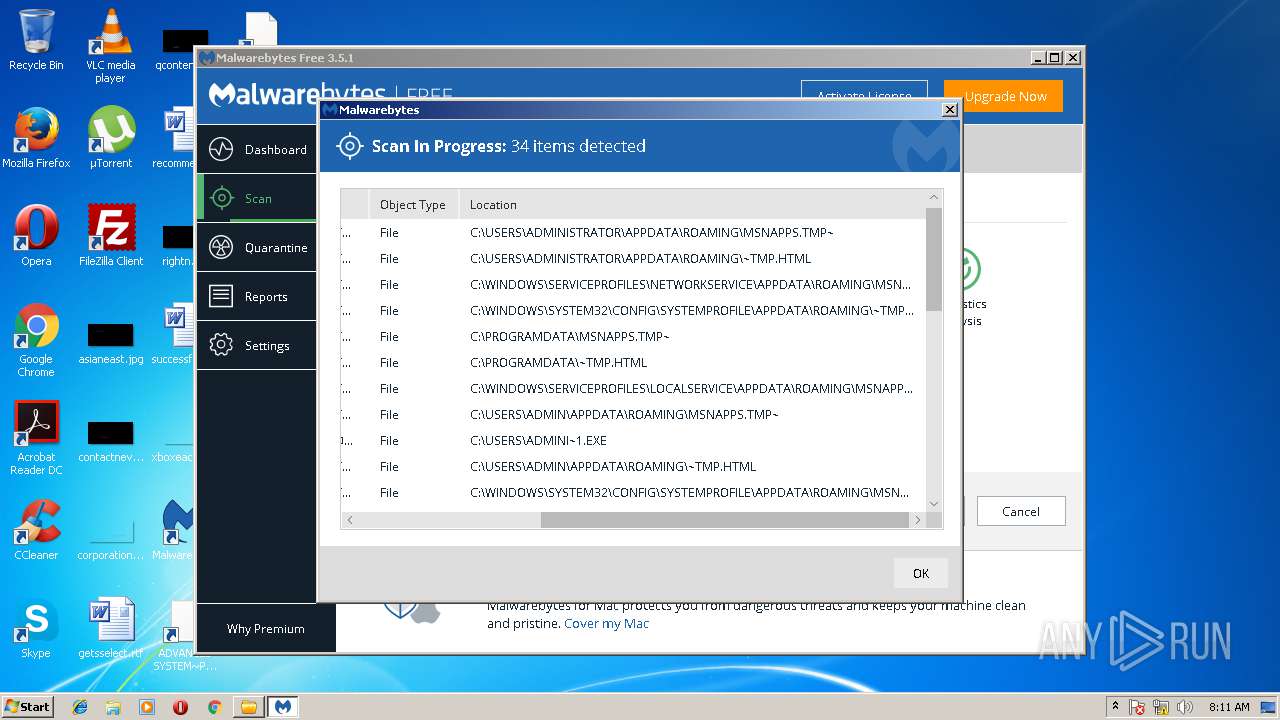
Dropped object may contain Bitcoin addresses
- MBAMSetup.tmp (PID: 3404)
- mbamservice.exe (PID: 3056)
Creates a software uninstall entry
- MBAMSetup.tmp (PID: 3404)
Creates files in the program directory
- MBAMSetup.tmp (PID: 3404)
Dropped object may contain URL's
- TechToolStore.exe (PID: 1832)
- mbamservice.exe (PID: 3056)
- MBAMSetup.tmp (PID: 3404)
Reads settings of System Certificates
- mbamservice.exe (PID: 3056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:04:27 14:43:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.13 |
| CodeSize: | 543232 |
| InitializedDataSize: | 4524032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x550dc |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.0.0 |
| ProductVersionNumber: | 5.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Pre-release, Private build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
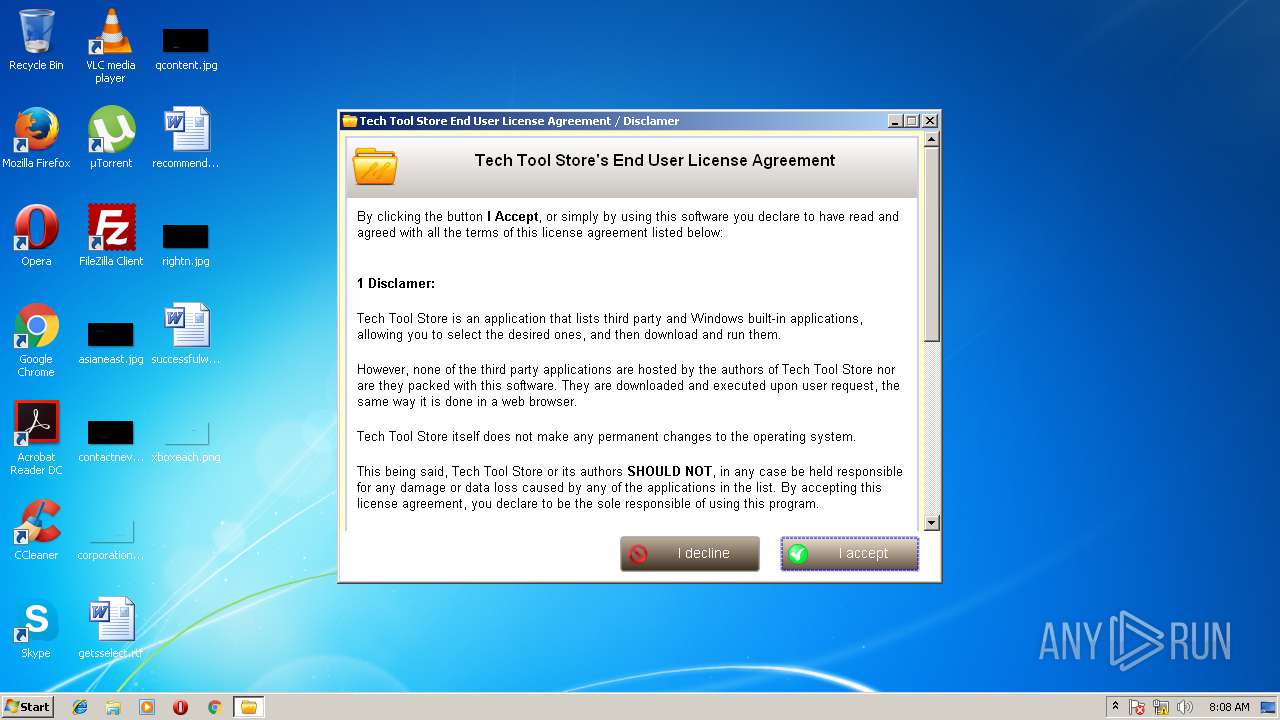
| CompanyName: | Carifred |
| FileDescription: | Tech tool store |
| FileVersion: | 5.0.0.0 |
| InternalName: | Tech tool store |
| LegalCopyright: | Carifred © 2010 - 2018 |
| LegalTrademarks: | Carifred.com |
| OriginalFileName: | Tech tool store.exe |
| ProductName: | Tech tool store |
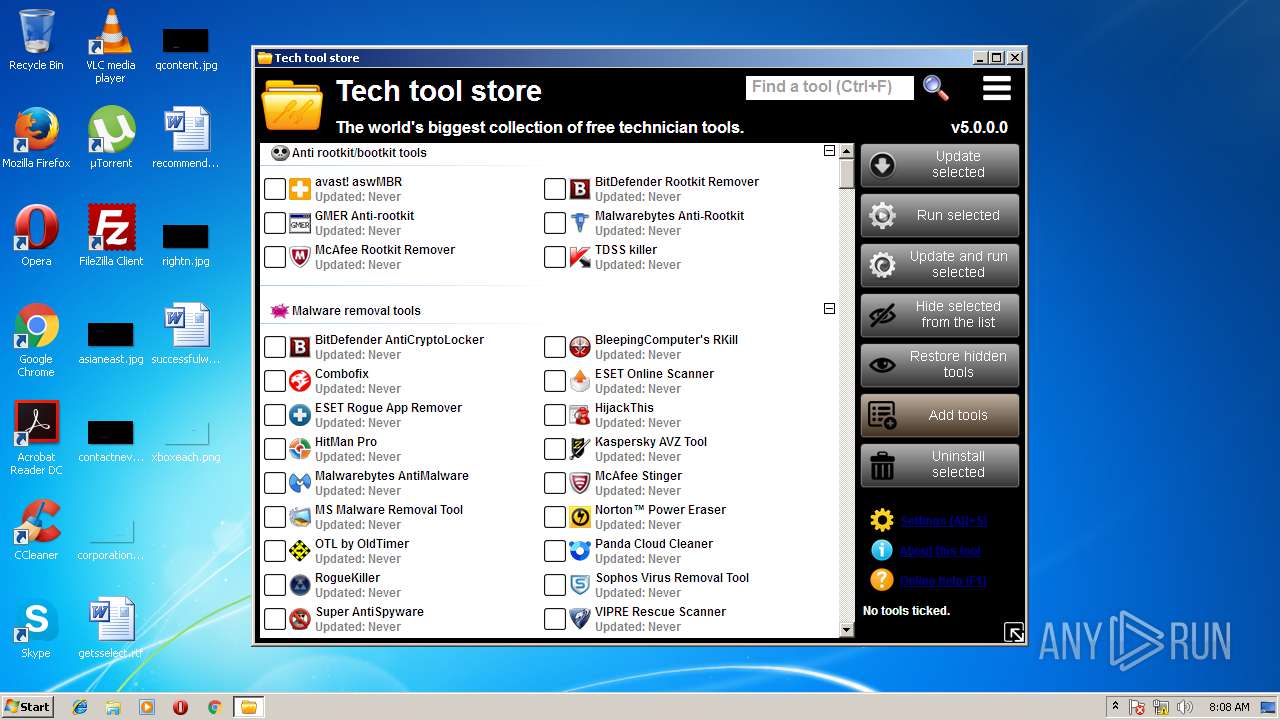
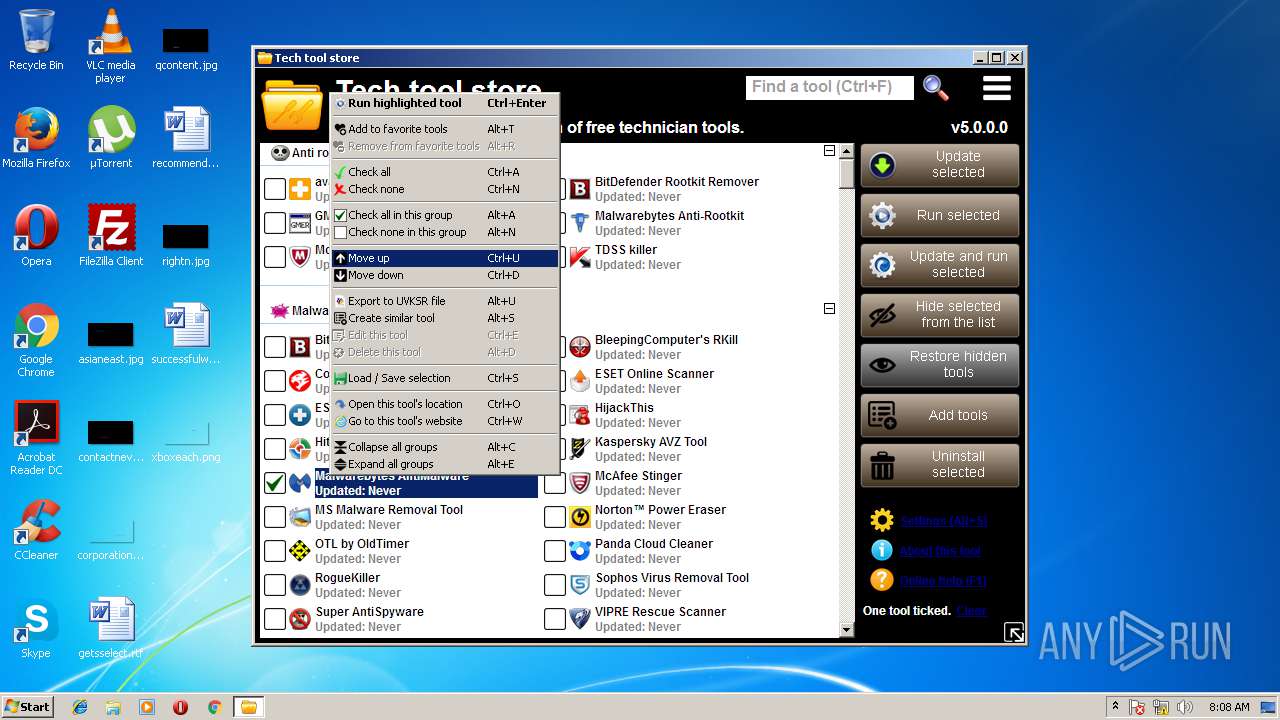
| Comments: | Tech tool store is an IT professional application that allows you to download and run more than 600 technician tools. |
| ProductVersion: | 5.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2018 12:43:50 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Carifred |
| FileDescription: | Tech tool store |
| FileVersion: | 5.0.0.0 |
| InternalName: | Tech tool store |
| LegalCopyright: | Carifred © 2010 - 2018 |
| LegalTrademarks: | Carifred.com |
| OriginalFilename: | Tech tool store.exe |
| ProductName: | Tech tool store |
| Comments: | Tech tool store is an IT professional application that allows you to download and run more than 600 technician tools. |
| ProductVersion: | 5.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Apr-2018 12:43:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00084946 | 0x00084A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49191 |
.rdata | 0x00086000 | 0x00036D3A | 0x00036E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15064 |
.data | 0x000BD000 | 0x000022DC | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.1448 |
.rsrc | 0x000C0000 | 0x004118C8 | 0x00411A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.83667 |
.reloc | 0x004D2000 | 0x00005BCC | 0x00005C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.7039 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.32288 | 1126 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.05295 | 4392 | UNKNOWN | English - United States | RT_ICON |
3 | 4.76405 | 9832 | UNKNOWN | English - United States | RT_ICON |
4 | 4.77926 | 17448 | UNKNOWN | English - United States | RT_ICON |
5 | 7.96265 | 31047 | UNKNOWN | English - United States | RT_ICON |
131 | 7.95878 | 59882 | UNKNOWN | English - United States | IMAGE |
132 | 7.94285 | 5048 | UNKNOWN | English - United States | IMAGE |
133 | 7.92574 | 4032 | UNKNOWN | English - United States | IMAGE |
134 | 7.94309 | 4547 | UNKNOWN | English - United States | IMAGE |
135 | 7.87969 | 2420 | UNKNOWN | English - United States | IMAGE |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
53
Monitored processes
16
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1340 | "C:\Program Files\Malwarebytes\Anti-Malware\mbamservice.exe" /service | C:\Program Files\Malwarebytes\Anti-Malware\mbamservice.exe | — | MBAMSetup.tmp | |||||||||||
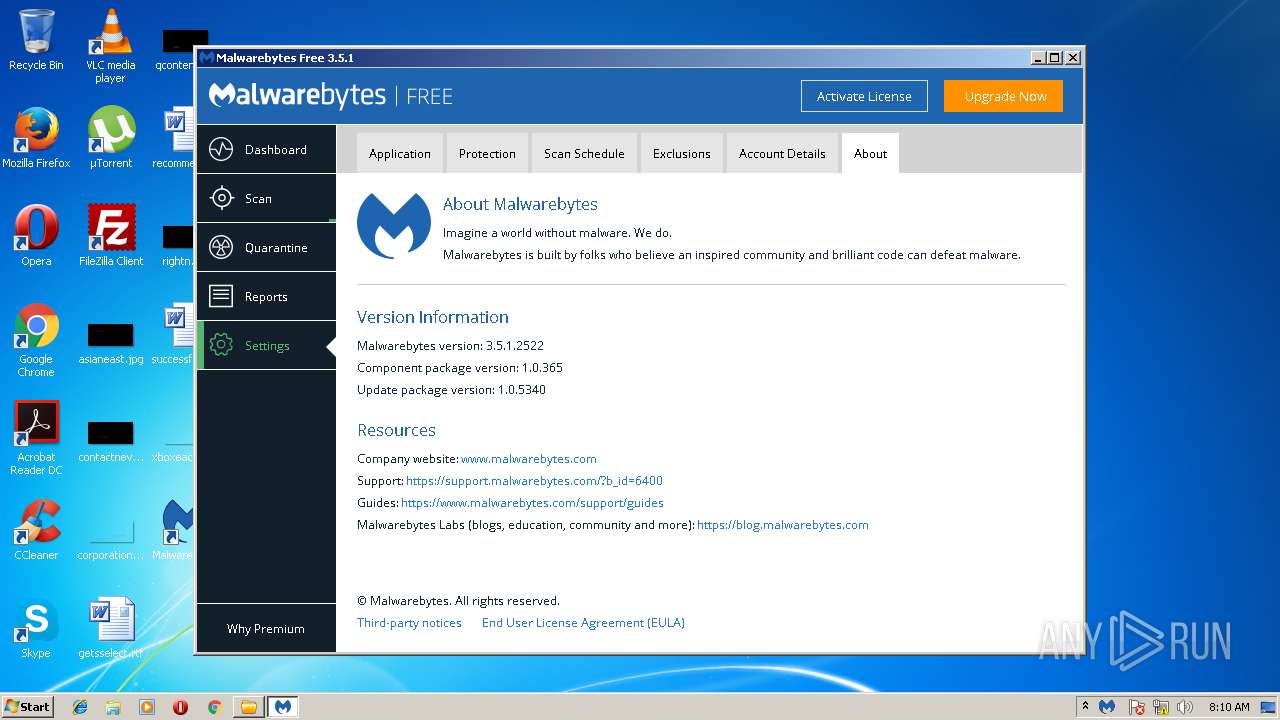
User: admin Company: Malwarebytes Integrity Level: HIGH Description: Malwarebytes Service Exit code: 0 Version: 3.1.0.667 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Malwarebytes\Anti-Malware\MBAMWsc.exe" /wac 1 /uninstall /updatesubstatus none /scansubstatus none /settingssubstatus none | C:\Program Files\Malwarebytes\Anti-Malware\MBAMWsc.exe | — | mbamservice.exe | |||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Exit code: 0 Version: 3.0.0.167 Modules
| |||||||||||||||
| 1572 | "certutil.exe" -f -addStore root "C:\Users\admin\AppData\Local\Temp\is-0SDCK.tmp\BaltimoreCyberTrustRoot.crt" | C:\Windows\system32\certutil.exe | — | MBAMSetup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1832 | "C:\Users\admin\AppData\Local\Temp\TechToolStore.exe" | C:\Users\admin\AppData\Local\Temp\TechToolStore.exe | explorer.exe | ||||||||||||
User: admin Company: Carifred Integrity Level: HIGH Description: Tech tool store Exit code: 0 Version: 5.0.0.0 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Malwarebytes\Anti-Malware\MBAMWsc.exe" /wac 1 /uninstall /updatesubstatus none /scansubstatus none /settingssubstatus none | C:\Program Files\Malwarebytes\Anti-Malware\MBAMWsc.exe | — | mbamservice.exe | |||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Exit code: 0 Version: 3.0.0.167 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Malwarebytes\Anti-Malware\mbamtray.exe" | C:\Program Files\Malwarebytes\Anti-Malware\mbamtray.exe | mbamservice.exe | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: MEDIUM Description: Malwarebytes Tray Application Exit code: 0 Version: 3.0.0.1490 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Malwarebytes\Anti-Malware\MBAMWsc.exe" /wac 1 /uninstall /updatesubstatus none /scansubstatus none /settingssubstatus none | C:\Program Files\Malwarebytes\Anti-Malware\MBAMWsc.exe | — | mbamservice.exe | |||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Exit code: 0 Version: 3.0.0.167 Modules
| |||||||||||||||
| 2668 | "C:\Users\admin\AppData\Local\Temp\Tech tool store tools\MBAMSetup.exe" /silent | C:\Users\admin\AppData\Local\Temp\Tech tool store tools\MBAMSetup.exe | TechToolStore.exe | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: HIGH Description: Malwarebytes Exit code: 0 Version: 3.5.1.2522 Modules
| |||||||||||||||
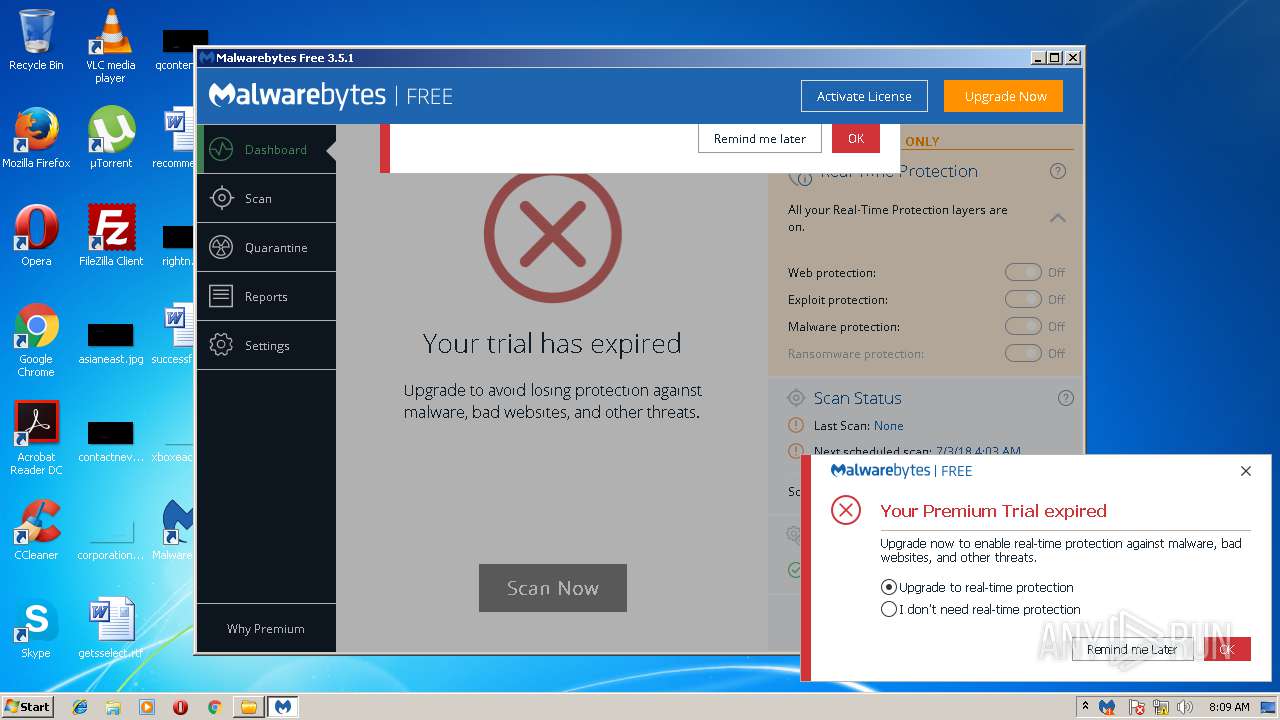
| 2824 | "C:\Program Files\Malwarebytes\Anti-Malware\mbam.exe" | C:\Program Files\Malwarebytes\Anti-Malware\mbam.exe | TechToolStore.exe | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: HIGH Description: Malwarebytes Exit code: 0 Version: 3.0.0.1490 Modules
| |||||||||||||||
| 3056 | "C:\Program Files\Malwarebytes\Anti-Malware\mbamservice.exe" | C:\Program Files\Malwarebytes\Anti-Malware\mbamservice.exe | services.exe | ||||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Description: Malwarebytes Service Exit code: 0 Version: 3.1.0.667 Modules
| |||||||||||||||
Total events
2 619
Read events
1 076
Write events
1 535
Delete events
8
Modification events
| (PID) Process: | (1832) TechToolStore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1832) TechToolStore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1832) TechToolStore.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: TechToolStore.exe | |||
| (PID) Process: | (1832) TechToolStore.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | ID |
Value: 1524833030 | |||
| (PID) Process: | (1832) TechToolStore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018060320180604 |
| Operation: | write | Name: | CachePath |
Value: %USERPROFILE%\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018060320180604 | |||
| (PID) Process: | (1832) TechToolStore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018060320180604 |
| Operation: | write | Name: | CachePrefix |
Value: :2018060320180604: | |||
| (PID) Process: | (1832) TechToolStore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018060320180604 |
| Operation: | write | Name: | CacheLimit |
Value: 8192 | |||
| (PID) Process: | (1832) TechToolStore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018060320180604 |
| Operation: | write | Name: | CacheOptions |
Value: 11 | |||
| (PID) Process: | (1832) TechToolStore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018060320180604 |
| Operation: | write | Name: | CacheRepair |
Value: 0 | |||
| (PID) Process: | (1832) TechToolStore.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: TechToolStore.exe | |||
Executable files
125
Suspicious files
89
Text files
179
Unknown types
50
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1832 | TechToolStore.exe | C:\Users\admin\AppData\Local\Temp\tts_settings.dat | — | |
MD5:— | SHA256:— | |||
| 1832 | TechToolStore.exe | C:\Users\admin\AppData\Local\Temp\tts_tools.dat | — | |
MD5:— | SHA256:— | |||
| 1832 | TechToolStore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LM4BD81N\mb3-setup-consumer-3.5.1.2522-1.0.365-1.0.5330[1].exe | — | |
MD5:— | SHA256:— | |||
| 1832 | TechToolStore.exe | C:\Users\admin\AppData\Local\Temp\Tech tool store tools\MBAMSetup.exe | — | |
MD5:— | SHA256:— | |||
| 3404 | MBAMSetup.tmp | C:\Users\admin\AppData\Local\Temp\is-0SDCK.tmp\mb-header100.bmp | — | |
MD5:— | SHA256:— | |||
| 3404 | MBAMSetup.tmp | C:\Users\admin\AppData\Local\Temp\is-0SDCK.tmp\mb-header-options100.bmp | — | |
MD5:— | SHA256:— | |||
| 3404 | MBAMSetup.tmp | C:\Program Files\Malwarebytes\Anti-Malware\is-G3091.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | MBAMSetup.tmp | C:\Program Files\Malwarebytes\Anti-Malware\is-J1O7B.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | MBAMSetup.tmp | C:\Program Files\Malwarebytes\Anti-Malware\is-28NG7.tmp | — | |
MD5:— | SHA256:— | |||
| 3404 | MBAMSetup.tmp | C:\Program Files\Malwarebytes\Anti-Malware\is-T71IO.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
39
DNS requests
32
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1832 | TechToolStore.exe | GET | — | 2.18.233.58:80 | http://data-cdn.mbamupdates.com/web/mb3-setup-consumer/mb3-setup-consumer-3.5.1.2522-1.0.365-1.0.5330.exe | unknown | — | — | whitelisted |
1832 | TechToolStore.exe | GET | — | 2.18.233.58:80 | http://data-cdn.mbamupdates.com/web/mb3-setup-consumer/mb3-setup-consumer-3.5.1.2522-1.0.365-1.0.5330.exe | unknown | — | — | whitelisted |
1832 | TechToolStore.exe | GET | 302 | 205.185.208.98:80 | http://downloads.malwarebytes.org/file/mbam/ | US | html | 289 b | unknown |
— | — | GET | 200 | 23.37.43.27:80 | http://ts-ocsp.ws.symantec.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRi82PVYYKWGJWdgVNyePy5kYTdqQQUX5r1blzMzHSa1N197z%2Fb7EyALt0CEA7P9DjI%2Fr81bgTYapgbGlA%3D | NL | der | 1.43 Kb | whitelisted |
1832 | TechToolStore.exe | GET | 302 | 205.185.208.98:80 | http://downloads.malwarebytes.org/file/mbam/ | US | html | 289 b | unknown |
— | — | GET | 200 | 23.37.43.27:80 | http://ocsp.thawte.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQJ1TBLBrQ9OnPHXPVaWb87MxkNlgQUwu79F9f%2Btw%2FGciJ7fvbA4gIz7D4CEH6T6%2Ft8xk5Z6kuad9QG%2FDs%3D | NL | der | 1.30 Kb | whitelisted |
— | — | GET | 200 | 23.37.43.27:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEFIA5aolVvwahu2WydRLM8c%3D | NL | der | 1.71 Kb | whitelisted |
— | — | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ%2FYHKj6JjF6UBieQioTYpFsuEriQQUtnf6aUhHn1MS1cLqBzJ2B9GXBxkCEHsFsdRJaFFE98mJ0pwZnRI%3D | NL | der | 1.68 Kb | shared |
3056 | mbamservice.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA%2BoSQYV1wCgviF2%2FcXsbb0%3D | US | der | 471 b | whitelisted |
3056 | mbamservice.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSYagvY3tfizDNoybzVSPFZmSEm0wQUe2jOKarAF75JeuHlP9an90WPNTICEAROO%2FWJdogP%2FQdESKj3oFg%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3056 | mbamservice.exe | 34.225.40.224:443 | sirius.mwbsys.com | Amazon.com, Inc. | US | suspicious |
— | — | 52.85.183.42:443 | hubble.mb-cosmos.com | Amazon.com, Inc. | US | unknown |
1832 | TechToolStore.exe | 205.185.208.98:80 | downloads.malwarebytes.org | Highwinds Network Group, Inc. | US | unknown |
1832 | TechToolStore.exe | 2.18.233.58:80 | data-cdn.mbamupdates.com | Akamai International B.V. | — | whitelisted |
2268 | mbamtray.exe | 2.18.233.58:443 | data-cdn.mbamupdates.com | Akamai International B.V. | — | whitelisted |
2268 | mbamtray.exe | 54.201.218.151:443 | cleo.mb-internal.com | Amazon.com, Inc. | US | unknown |
3056 | mbamservice.exe | 107.23.215.203:443 | keystone.mwbsys.com | Amazon.com, Inc. | US | unknown |
2824 | mbam.exe | 2.18.233.58:443 | data-cdn.mbamupdates.com | Akamai International B.V. | — | whitelisted |
3056 | mbamservice.exe | 34.197.244.237:443 | keystone.mwbsys.com | Amazon.com, Inc. | US | unknown |
2824 | mbam.exe | 54.69.23.173:443 | cleo.mb-internal.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
downloads.malwarebytes.org |
| unknown |
data-cdn.mbamupdates.com |
| whitelisted |
links.malwarebytes.com |
| whitelisted |
cleo.mb-internal.com |
| unknown |
keystone.mwbsys.com |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iris.mwbsys.com |
| unknown |
sirius.mwbsys.com |
| suspicious |
cdn.mwbsys.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1832 | TechToolStore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1832 | TechToolStore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
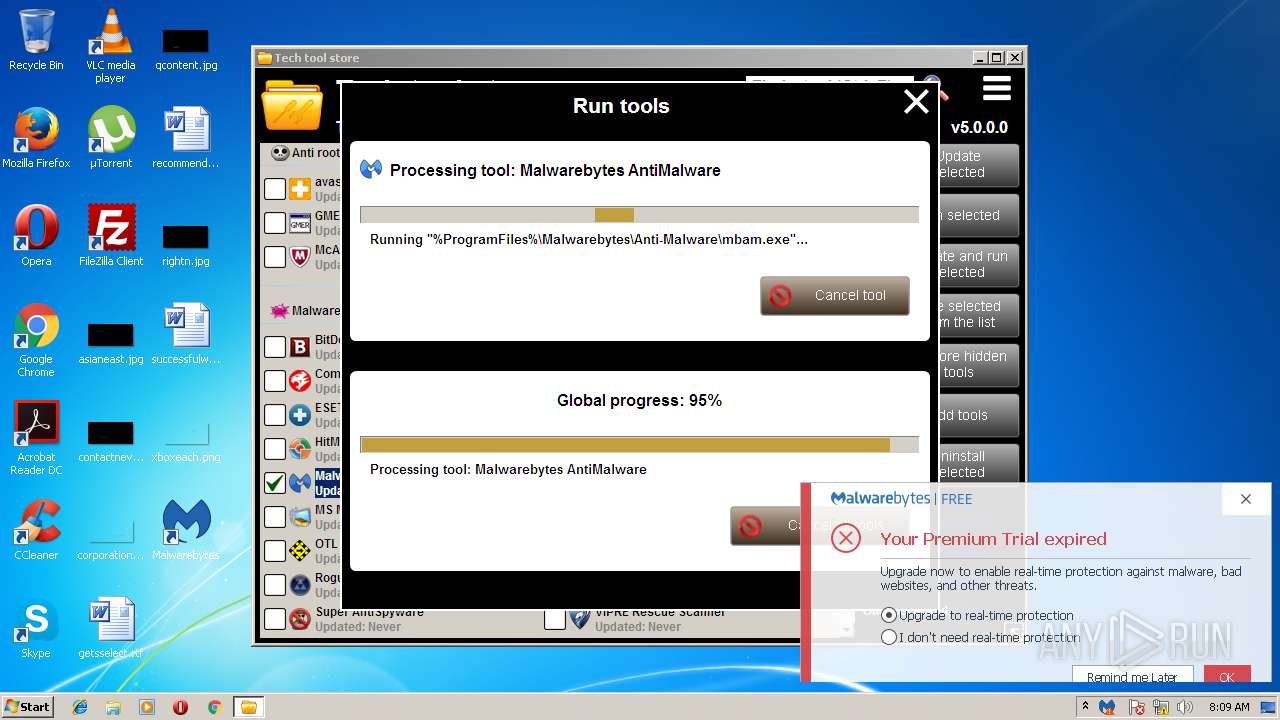
mbamtray.exe | QAxBase::setControl: requested control {F36AD0D0-B5F0-4C69-AF08-603D177FEF0E} could not be instantiated
|
mbamtray.exe | Code : 16389
|
mbamtray.exe | Code : 16389
|
mbamtray.exe | Source :
|
mbamtray.exe | Description:
|
mbamtray.exe | Help :
|
mbamtray.exe | Connect to the exception(int,QString,QString,QString) signal to catch this exception
|
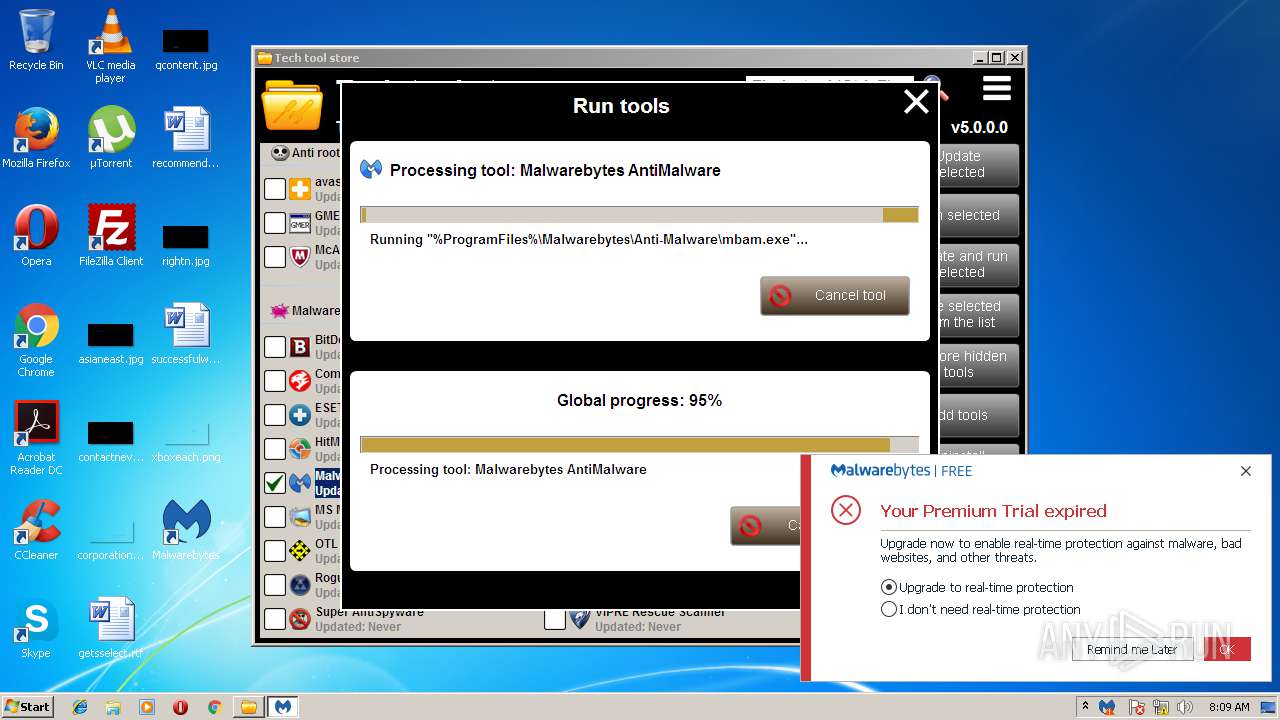
mbamtray.exe | "2018-06-03T08:09:18" void __thiscall TrayLicenseNotificationsModel::HandleTrialNotifications(enum LicenseState::enum_type) Handling trial notifications for state: LicenseState::enum_type(Unknown)
|
mbamtray.exe | void __thiscall PageStatusMonitor::OnRequestFinished(class QNetworkReply *) "Page: https://links.malwarebytes.com/link/3x_cart?affiliate=&uuid=&x-source=h_15million&x-action=comparison_chart&lang=en received code: 307"
|
mbamtray.exe | class QUrl __thiscall PageStatusMonitor::processRedirectUrl(const class QUrl &,const class QUrl &) const Potential Redirect is: "https://cleo.mb-internal.com/?x-source=h_15million&ADDITIONAL_x-source=inproduct&x-action=comparison_chart" Last Redirect is: ""
|