| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/08802123-5517-4270-92cb-c59ec69c6987 |
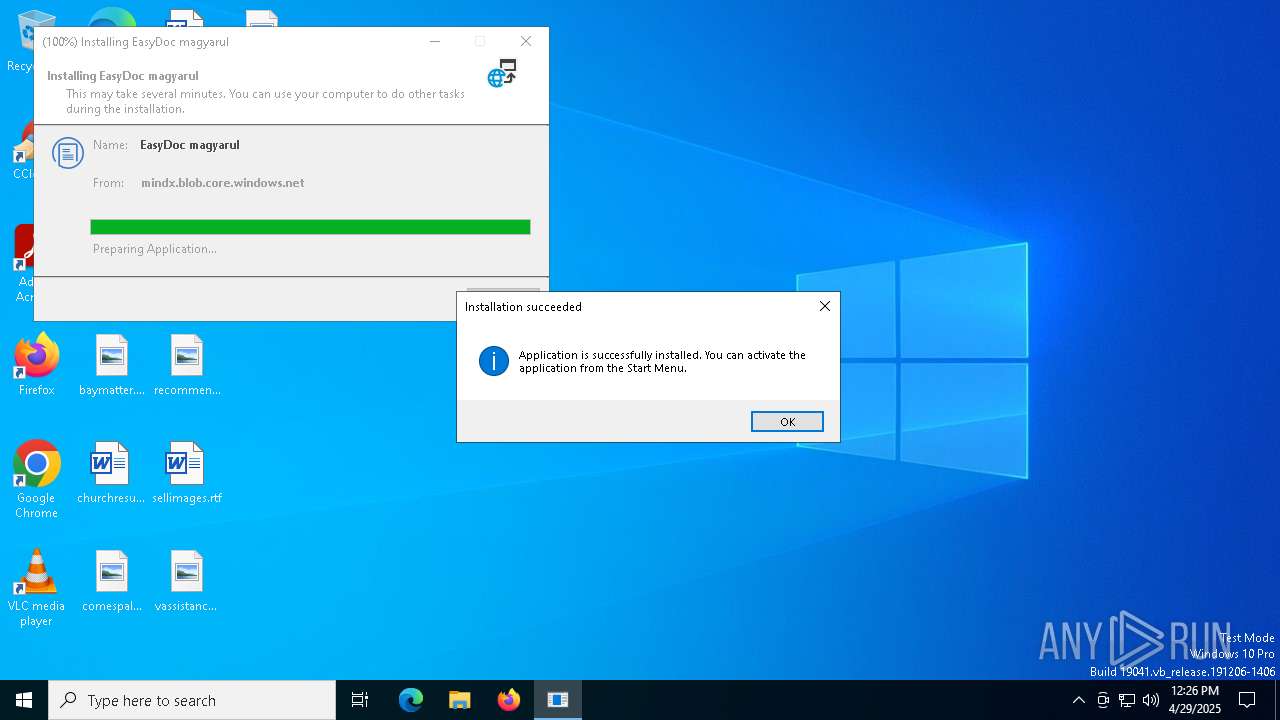
| Verdict: | Malicious activity |
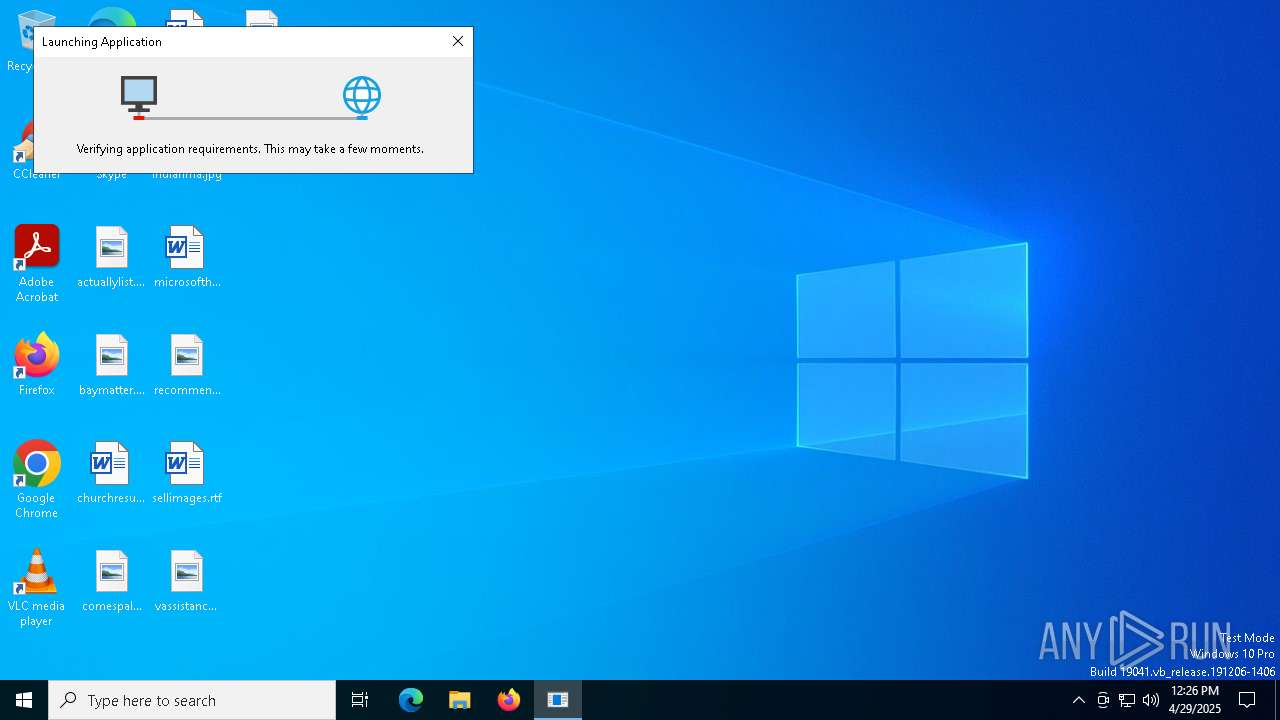
| Analysis date: | April 29, 2025, 12:26:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 17ED987C69AF8C11C15A55BB76C3464B |
| SHA1: | 446EAD75C0FC5A49A3617E907A63D2703CC325E7 |
| SHA256: | 788AD6B598524732C3A4116596308EA3D0D853B2F5F0FD6B4F846961E7F99E94 |
| SSDEEP: | 12288:F66gANxcjZVR/zBFWi1qQucIcFTjMtqZZrAttJVVVVVVVVVVVVVVVVVVVOVVVVVF:F66gAgZVR/7hoQHOJ2/nTDV |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- setup.exe (PID: 2568)
- dfsvc.exe (PID: 6876)
- EasyDoc.exe (PID: 3132)
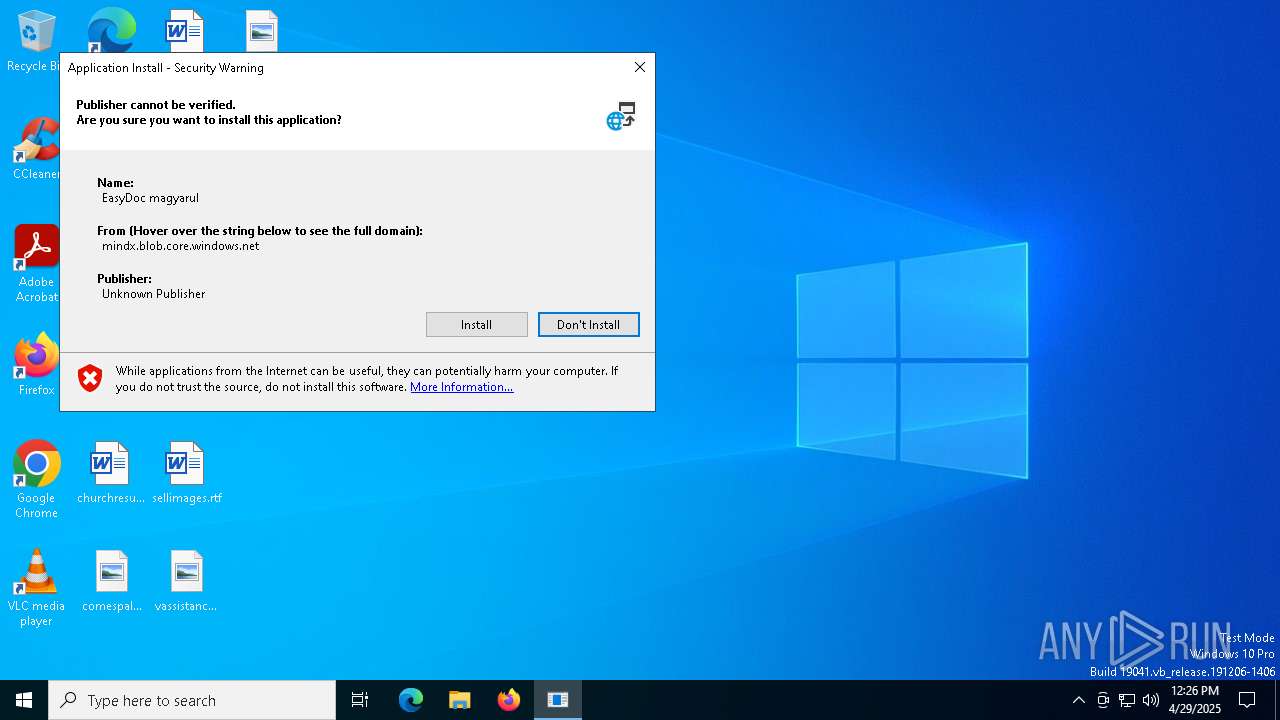
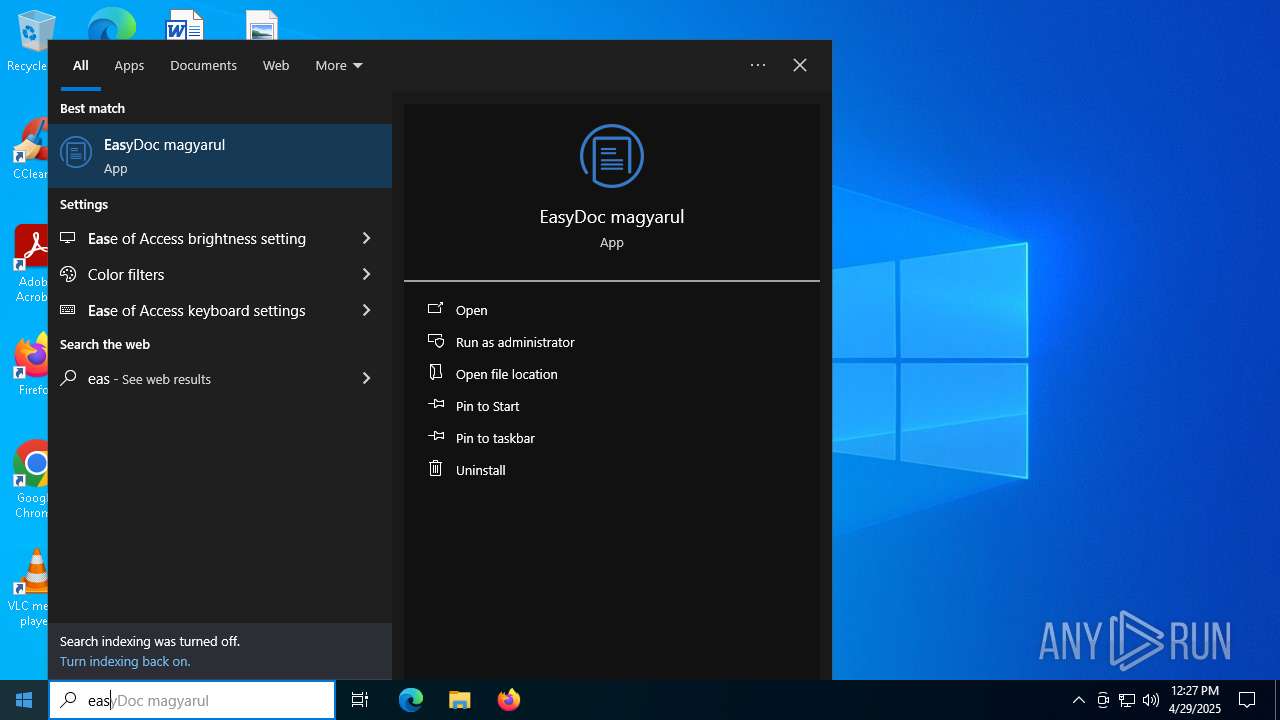
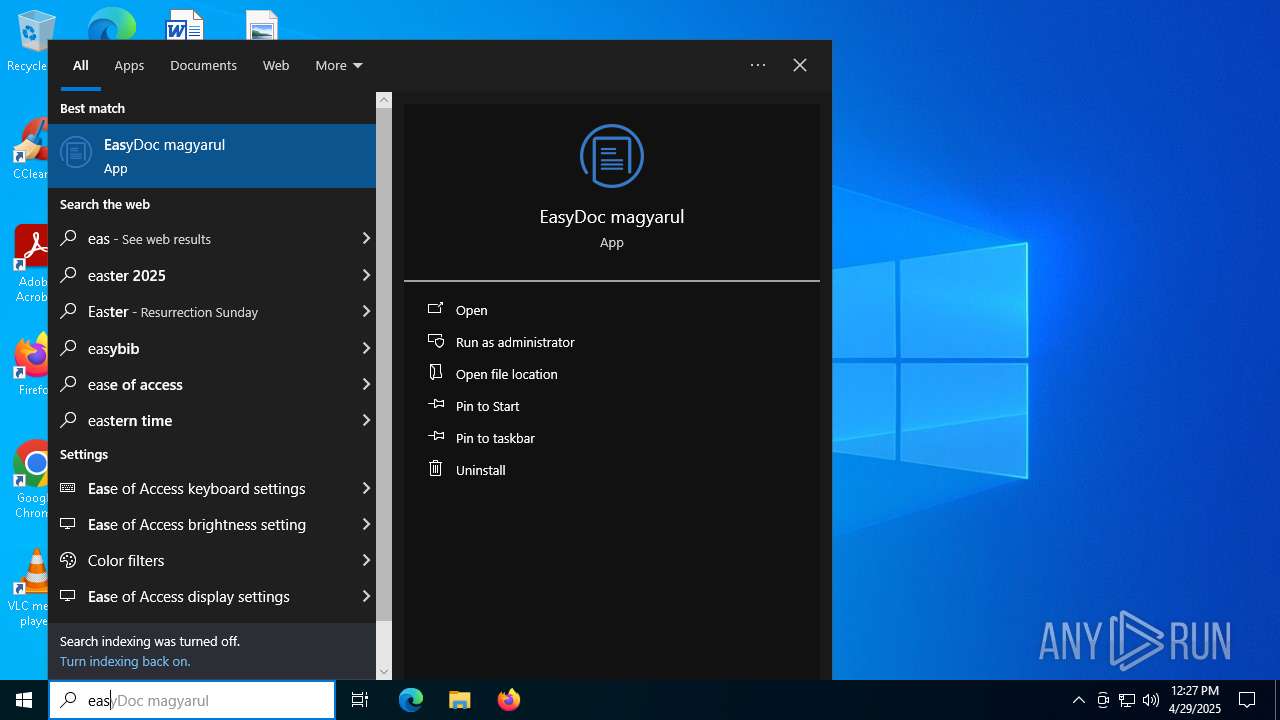
Creates a software uninstall entry
- dfsvc.exe (PID: 6876)
Searches for installed software
- dfsvc.exe (PID: 6876)
Reads the date of Windows installation
- dfsvc.exe (PID: 6876)
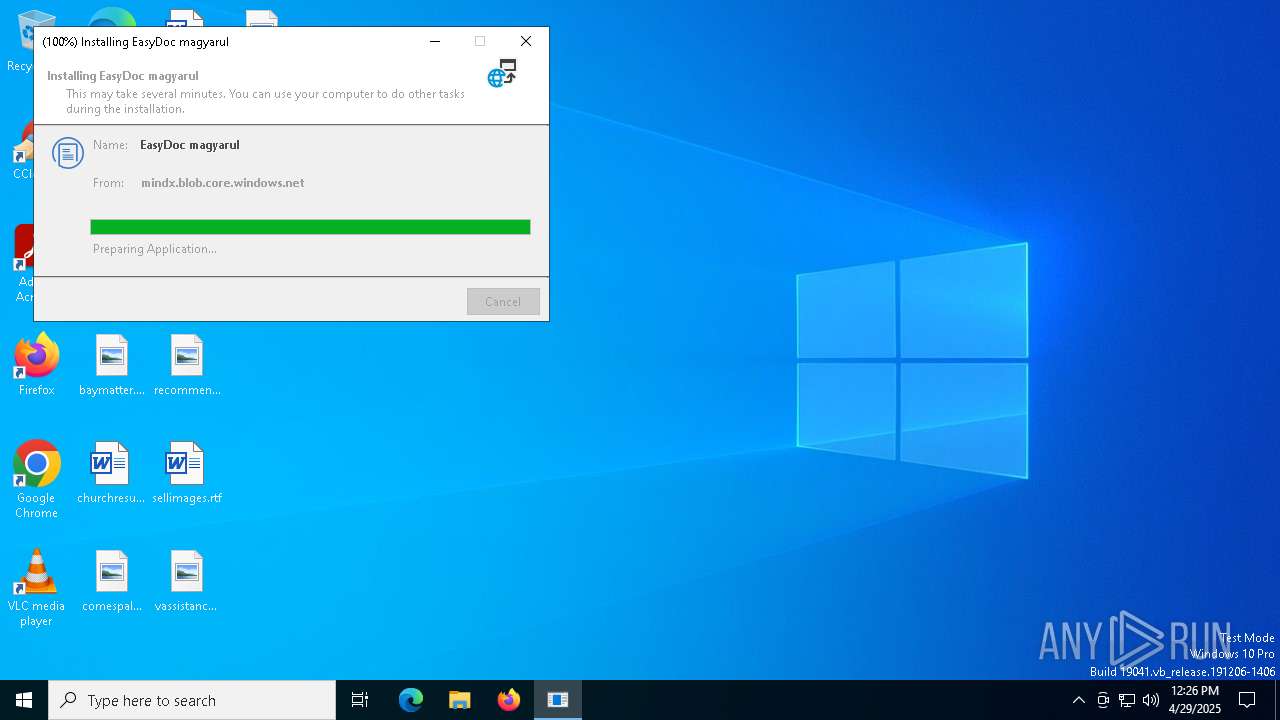
Executable content was dropped or overwritten
- MSFRM.exe (PID: 5304)
- EasyDoc.exe (PID: 3132)
- dfsvc.exe (PID: 6876)
Cleans NTFS data stream (Zone Identifier)
- MSFRM.exe (PID: 5304)
Process drops legitimate windows executable
- MSFRM.exe (PID: 5304)
- dfsvc.exe (PID: 6876)
INFO
Reads the software policy settings
- setup.exe (PID: 2568)
- dfsvc.exe (PID: 6876)
- EasyDoc.exe (PID: 3132)
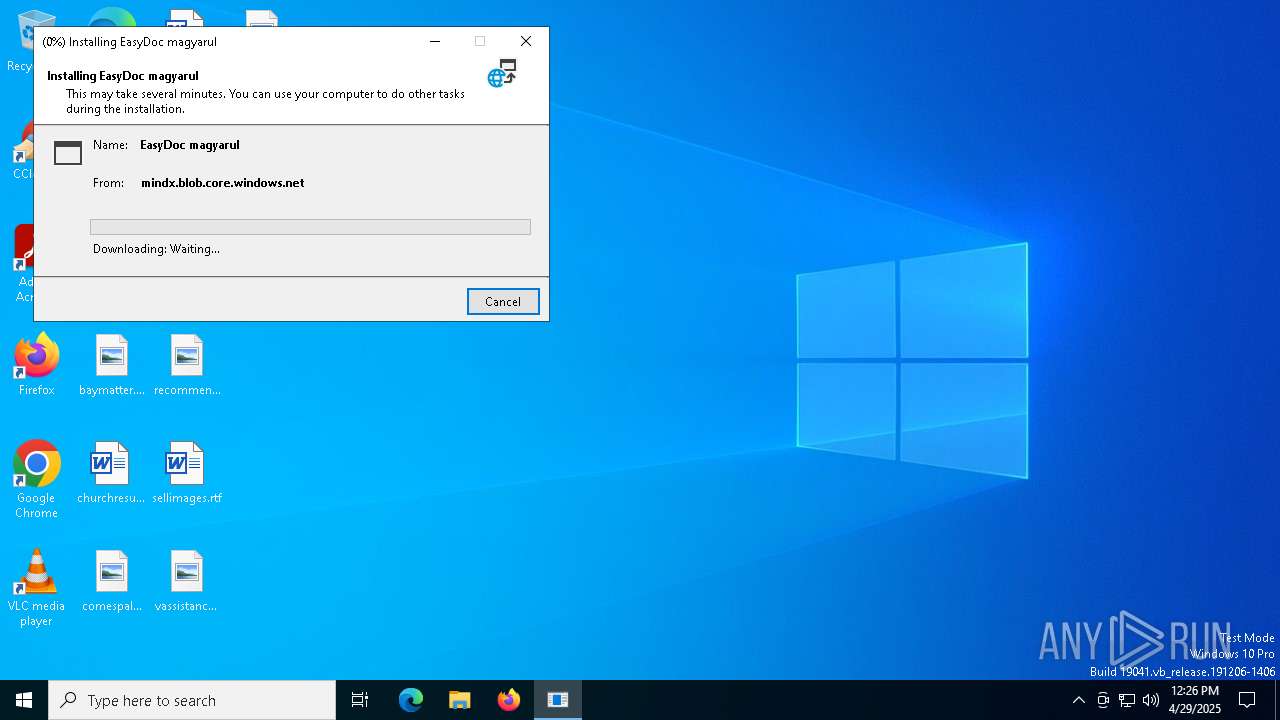
Create files in a temporary directory
- setup.exe (PID: 2568)
- dfsvc.exe (PID: 6876)
Reads the computer name
- setup.exe (PID: 2568)
- dfsvc.exe (PID: 6876)
- MSFRM.exe (PID: 5304)
- EasyDoc.exe (PID: 3132)
Reads the machine GUID from the registry
- setup.exe (PID: 2568)
- dfsvc.exe (PID: 6876)
- MSFRM.exe (PID: 5304)
- EasyDoc.exe (PID: 3132)
Checks supported languages
- setup.exe (PID: 2568)
- dfsvc.exe (PID: 6876)
- MSFRM.exe (PID: 5304)
- EasyDoc.exe (PID: 3132)
Checks proxy server information
- setup.exe (PID: 2568)
- dfsvc.exe (PID: 6876)
- EasyDoc.exe (PID: 3132)
Creates files or folders in the user directory
- setup.exe (PID: 2568)
- dfsvc.exe (PID: 6876)
- MSFRM.exe (PID: 5304)
- EasyDoc.exe (PID: 3132)
Reads Environment values
- dfsvc.exe (PID: 6876)
- EasyDoc.exe (PID: 3132)
Disables trace logs
- dfsvc.exe (PID: 6876)
- EasyDoc.exe (PID: 3132)
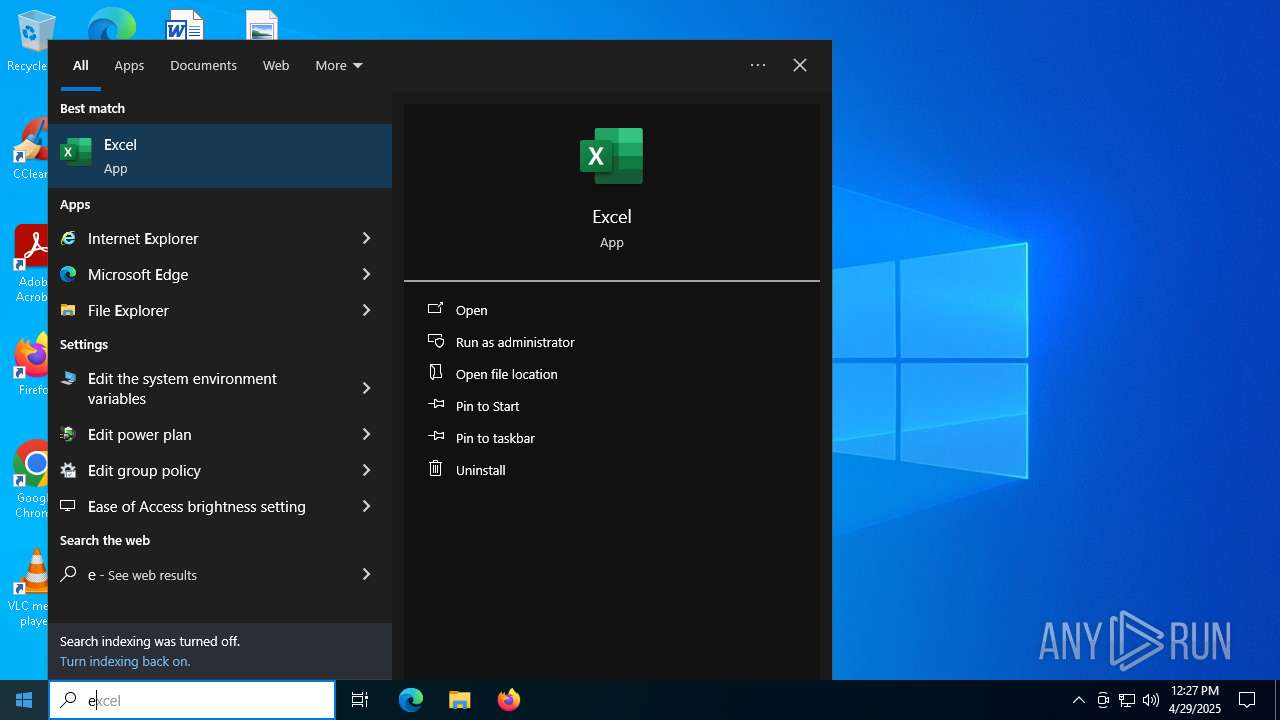
Manual execution by a user
- rundll32.exe (PID: 4448)
Process checks computer location settings
- dfsvc.exe (PID: 6876)
The sample compiled with english language support
- MSFRM.exe (PID: 5304)
- dfsvc.exe (PID: 6876)
Creates files in the program directory
- EasyDoc.exe (PID: 3132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:05 22:42:21+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.36 |
| CodeSize: | 395776 |
| InitializedDataSize: | 168448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3a950 |
| OSVersion: | 5.1 |
| ImageVersion: | 10 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 17.0.34205.153 |
| ProductVersionNumber: | 17.0.34205.153 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | Setup |
| FileVersion: | 17.0.34205.153 built by: CBA-1005_145330 |
| InternalName: | setup.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | setup.exe |
| ProductName: | - |
| ProductVersion: | 17.0.34205.153 |
Total processes
136
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2568 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Exit code: 0 Version: 17.0.34205.153 built by: CBA-1005_145330 Modules
| |||||||||||||||
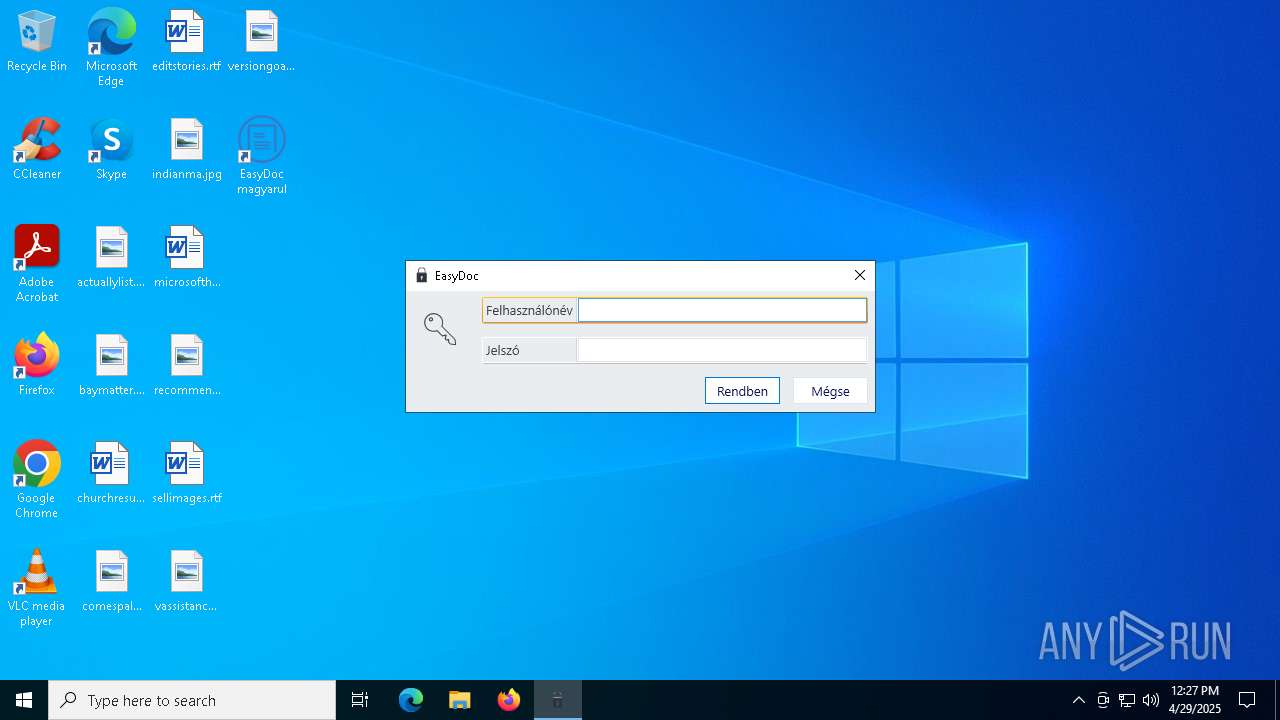
| 3132 | "C:\Users\admin\AppData\Local\Mindsoft\MSNG\https___mindx.blob.core.windows.net_public_Apps_EasyDoc_MSFRM.application\EasyDoc.exe" C:\Users\admin\AppData\Local\Apps\2.0\W7GR879O.X0G\EZ2YD0HZ.9VV\easydoc_7ee96d8638353ee1_0001.0006_883e51ace50596ab\MSFRM.exe | C:\Users\admin\AppData\Local\Mindsoft\MSNG\https___mindx.blob.core.windows.net_public_Apps_EasyDoc_MSFRM.application\EasyDoc.exe | MSFRM.exe | ||||||||||||
User: admin Company: MindSoft Kft Integrity Level: MEDIUM Description: EasyDoc Version: 1.6.0.35543 Modules
| |||||||||||||||
| 4448 | "C:\Windows\System32\rundll32.exe" "C:\Windows\System32\dfshim.dll",ShOpenVerbShortcut C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\MindSoft Kft\EasyDoc magyarul.appref-ms| | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5112 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5304 | "C:\Users\admin\AppData\Local\Apps\2.0\W7GR879O.X0G\EZ2YD0HZ.9VV\easydoc_7ee96d8638353ee1_0001.0006_883e51ace50596ab\MSFRM.exe" | C:\Users\admin\AppData\Local\Apps\2.0\W7GR879O.X0G\EZ2YD0HZ.9VV\easydoc_7ee96d8638353ee1_0001.0006_883e51ace50596ab\MSFRM.exe | dfsvc.exe | ||||||||||||
User: admin Company: Mindsoft Kft. Integrity Level: MEDIUM Description: MSFRM Exit code: 0 Version: 1.6.0.40351 Modules
| |||||||||||||||
| 6876 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ClickOnce Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
16 278
Read events
14 915
Write events
1 131
Delete events
232
Modification events
| (PID) Process: | (6876) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: PAPVQL200DADTBVDEE205PEJ | |||
| (PID) Process: | (6876) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete value | Name: | ComponentStore_RandomString |
Value: PAPVQL200DADTBVDEE205PEJ | |||
| (PID) Process: | (6876) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6876) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0 |
| Operation: | write | Name: | ComponentStore_RandomString |
Value: W7GR879OX0GEZ2YD0HZ9VVZR | |||
| (PID) Process: | (6876) dfsvc.exe | Key: | HKEY_CLASSES_ROOT\Software\Microsoft\Windows\CurrentVersion\Deployment\SideBySide\2.0\StateManager |
| Operation: | write | Name: | StateStore_RandomString |
Value: 5KRRJ5EE6A0M2QKZ7N5A9VDT | |||
| (PID) Process: | (6876) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6876) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6876) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6876) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6876) dfsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dfsvc_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
312
Suspicious files
202
Text files
305
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2568 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\MSFRM[1].application | xml | |
MD5:FECBA91273D25F2C0742E1408F0478B7 | SHA256:0BCAF2D7A169419A694A21AA704BB28B9A0583FB7F56DD381CDC4F3C4441BE2B | |||
| 6876 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\JZZKPDAV.CH5\P8L7X37P.W9W\x64\SQLite.Interop.dll | executable | |
MD5:56A504A34D2CFBFC7EAA2B68E34AF8AD | SHA256:9309FB2A3F326D0F2CC3F2AB837CFD02E4F8CB6B923B3B2BE265591FD38F4961 | |||
| 2568 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | binary | |
MD5:EA5B224935CF12F3040CD4F61431990B | SHA256:C91376618B500445676D4B9A966725F4FC1F3107136226896A6C27F6BABE4D70 | |||
| 2568 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | binary | |
MD5:7EDCC2F8FD122636E37A34E819B046B8 | SHA256:51C585682EA77A3B985FD3D21409AA320FCAE26793147FCD3DB8A45611040D93 | |||
| 2568 | setup.exe | C:\Users\admin\AppData\Local\Temp\VSDC035.tmp\install.log | binary | |
MD5:25F0F75965CF00268244C8AA84AE5B2D | SHA256:91D83C5BB8900D1B3C89681CB2EE10051F3E241151EAD3B021D5EE708BBE89CE | |||
| 6876 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\JZZKPDAV.CH5\P8L7X37P.W9W\MSFRM.exe.config | xml | |
MD5:B94FF824B47A788BC3C3110756033E4D | SHA256:CE11095FF42FD09C4B84043267C8D3A92D62FFC764666CE291446093ECB0F093 | |||
| 6876 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\JZZKPDAV.CH5\P8L7X37P.W9W\dragonz.actb.dll | executable | |
MD5:3AE44261FB146A3BF8A2508F560EE67C | SHA256:85F2E230D7BCCA6B4621870F7BB74035A207AAE3F3AD311259E9AA694449B373 | |||
| 6876 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\JZZKPDAV.CH5\P8L7X37P.W9W\Microsoft.Extensions.Options.dll | executable | |
MD5:6BD82EA5BD4D7708FC7C5B1BB5733319 | SHA256:C8F808556FCE5D9705CAF6E25160C2A06F48038366A44D243DC355B85A84B162 | |||
| 6876 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\JZZKPDAV.CH5\P8L7X37P.W9W\Microsoft.Extensions.Configuration.FileExtensions.dll | executable | |
MD5:B2D3E0B839D7F9C2E448C9BE0C208DE5 | SHA256:ACE39C65491081755DC441805DC139142C3FB19ABD7DF1F58DD17096C087D2CA | |||
| 6876 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\JZZKPDAV.CH5\P8L7X37P.W9W\Telerik.Reporting.OpenXmlRendering.dll | executable | |
MD5:E457F3331AFEA802F4D76FA1EFBBF039 | SHA256:51B05180BC9306887EBA204C1CF994F45A9EAA03C74FD44B6F46B1EED7F3245E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
36
DNS requests
24
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2568 | setup.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6988 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6876 | dfsvc.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEGIdbQxSAZ47kHkVIIkhHAo%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2568 | setup.exe | 52.239.140.10:443 | mindx.blob.core.windows.net | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2568 | setup.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
mindx.blob.core.windows.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |