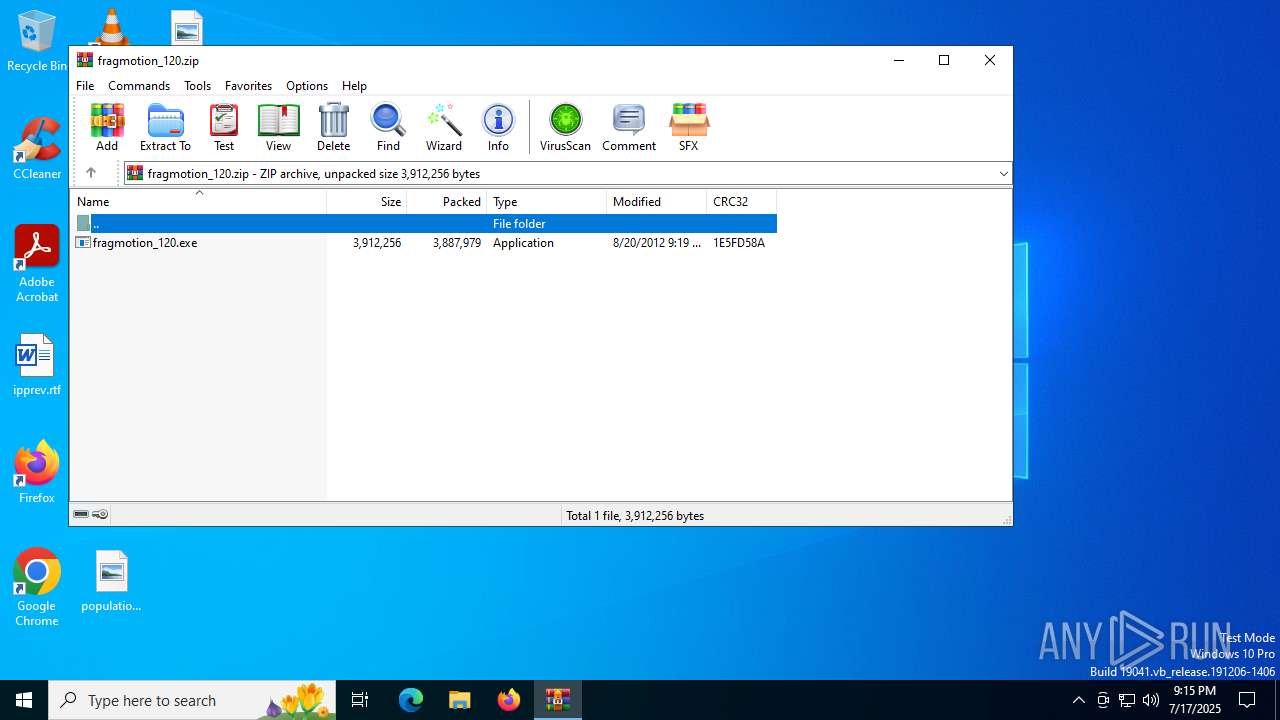
| File name: | fragmotion_120.zip |
| Full analysis: | https://app.any.run/tasks/93c62405-08de-4eb5-b87d-354478011989 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2025, 21:15:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | D2BCB018C57D150E08FCAE6E15D9AEB7 |
| SHA1: | AD7017A3DAE187E06C253C81F84997DE1DF7A541 |
| SHA256: | 787EE0A16FF52A0321E15EFE48865469D1B0EA0A754E949FF83F7658F9FF7452 |
| SSDEEP: | 98304:FlWXpHtHkXS06ieNyEtdfzGT+iRuHWuekXV0w4QhEy7tZB/xPIt2x0W7MSQcVVVH:Mh6Gr |
MALICIOUS
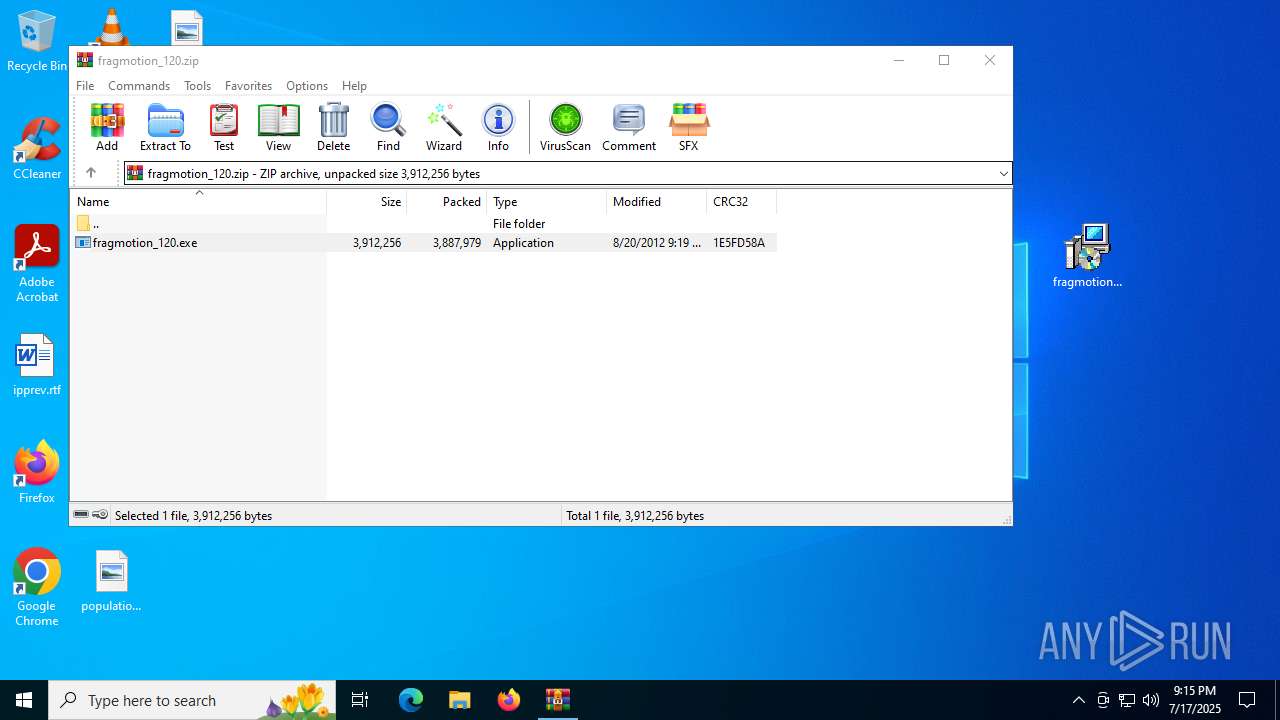
Generic archive extractor
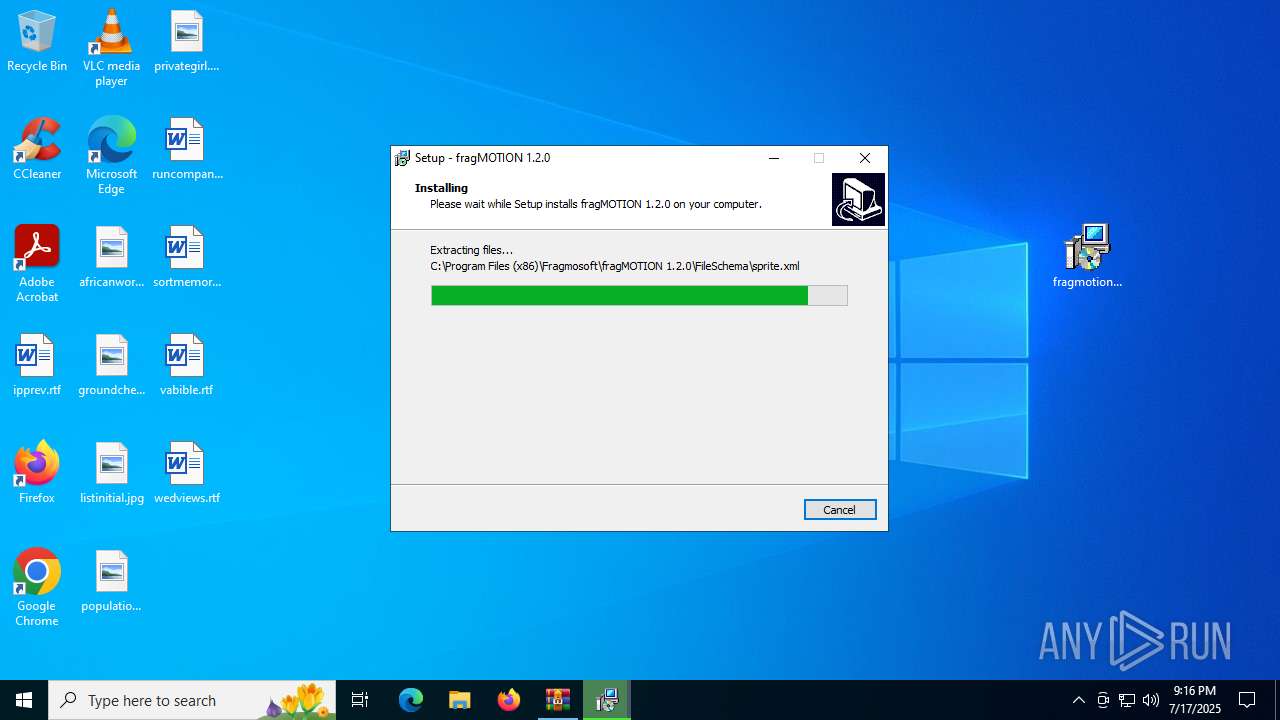
- WinRAR.exe (PID: 2524)
SUSPICIOUS
Executable content was dropped or overwritten
- fragmotion_120.exe (PID: 1520)
- fragmotion_120.tmp (PID: 5476)
- fragmotion_120.exe (PID: 5552)
Reads security settings of Internet Explorer
- fragmotion_120.tmp (PID: 3860)
Process drops legitimate windows executable
- fragmotion_120.tmp (PID: 5476)
Reads the Windows owner or organization settings
- fragmotion_120.tmp (PID: 5476)
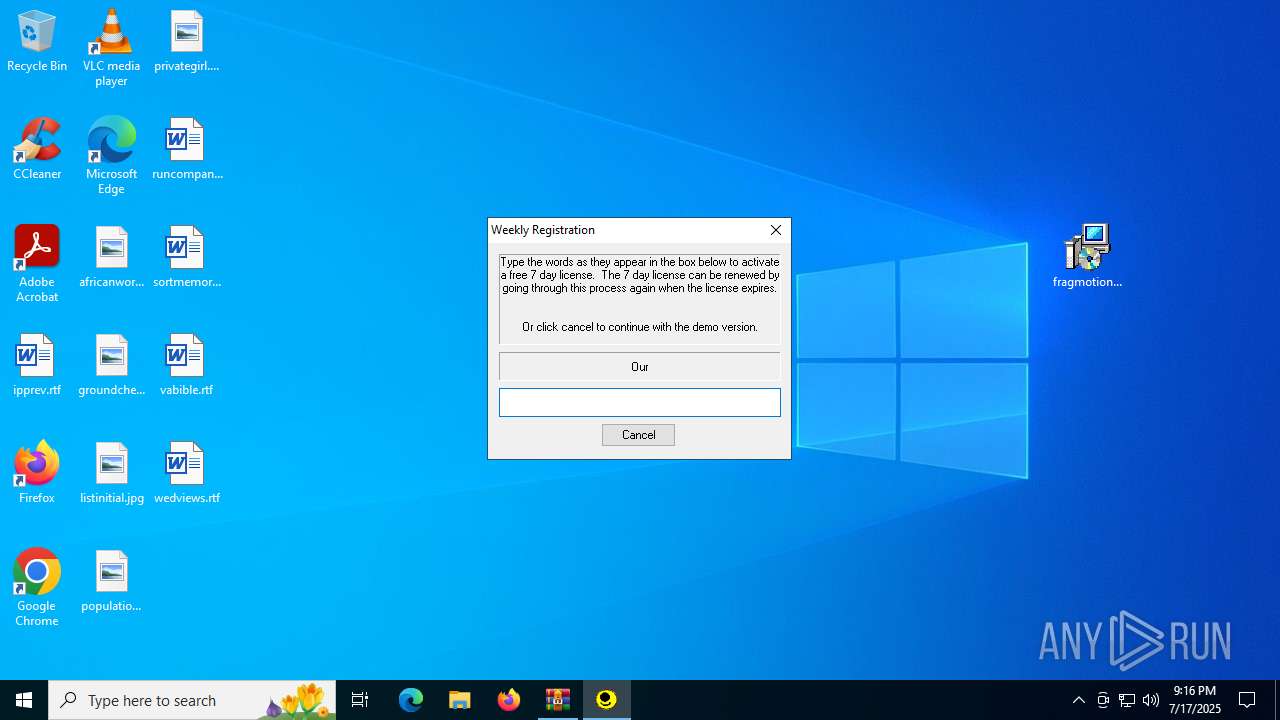
There is functionality for taking screenshot (YARA)
- fragMOTION.exe (PID: 2032)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2524)
Checks supported languages
- fragmotion_120.exe (PID: 1520)
- fragmotion_120.tmp (PID: 3860)
- finish.exe (PID: 1592)
- fragmotion_120.exe (PID: 5552)
- fragmotion_120.tmp (PID: 5476)
- fragMOTION.exe (PID: 2032)
Create files in a temporary directory
- fragmotion_120.exe (PID: 1520)
- fragmotion_120.tmp (PID: 5476)
- fragmotion_120.exe (PID: 5552)
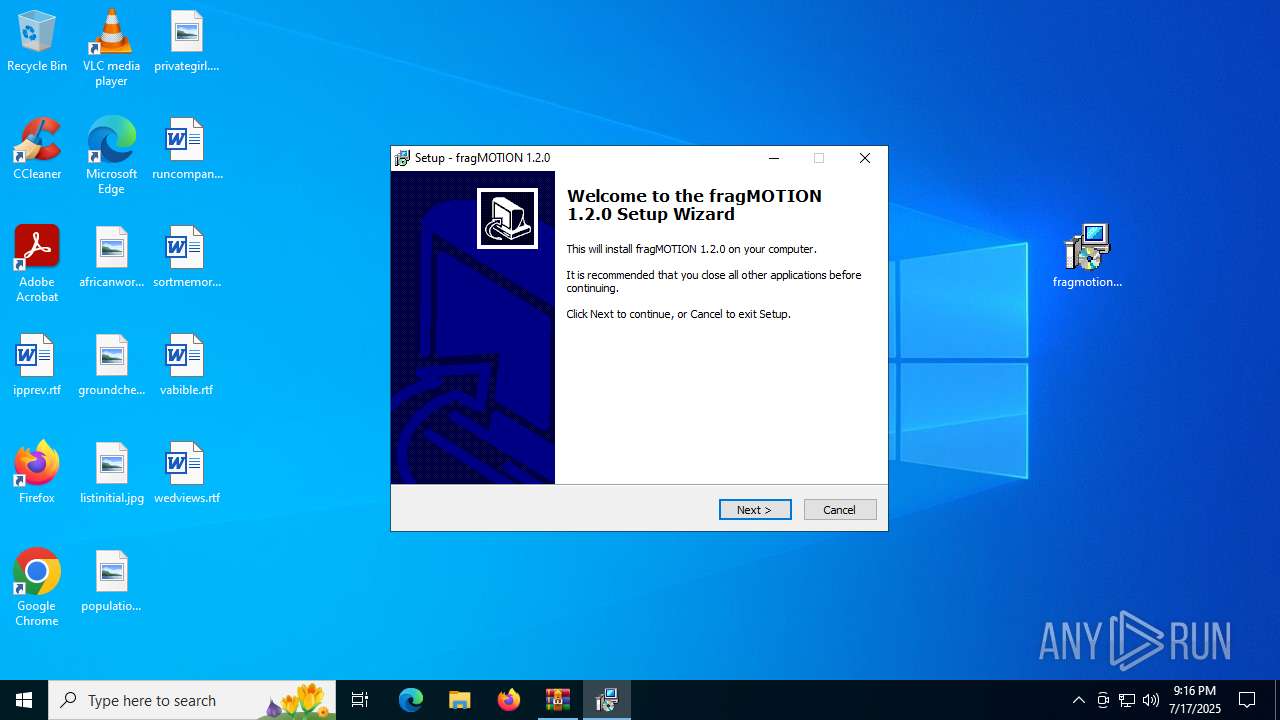
Manual execution by a user
- fragmotion_120.exe (PID: 1520)
Reads the computer name
- fragmotion_120.tmp (PID: 3860)
- fragmotion_120.tmp (PID: 5476)
- fragMOTION.exe (PID: 2032)
Creates files in the program directory
- fragmotion_120.tmp (PID: 5476)
Compiled with Borland Delphi (YARA)
- fragmotion_120.tmp (PID: 3860)
- fragmotion_120.tmp (PID: 5476)
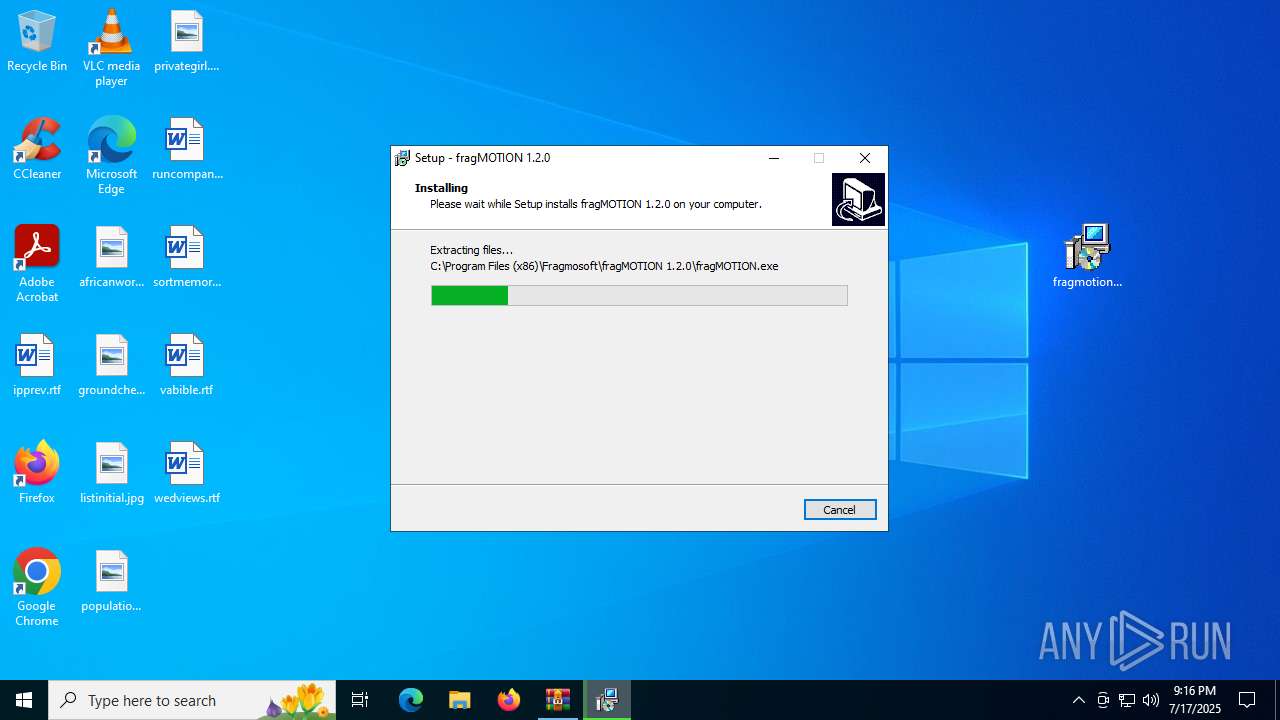
Detects InnoSetup installer (YARA)
- fragmotion_120.tmp (PID: 3860)
- fragmotion_120.exe (PID: 1520)
- fragmotion_120.exe (PID: 5552)
- fragmotion_120.tmp (PID: 5476)
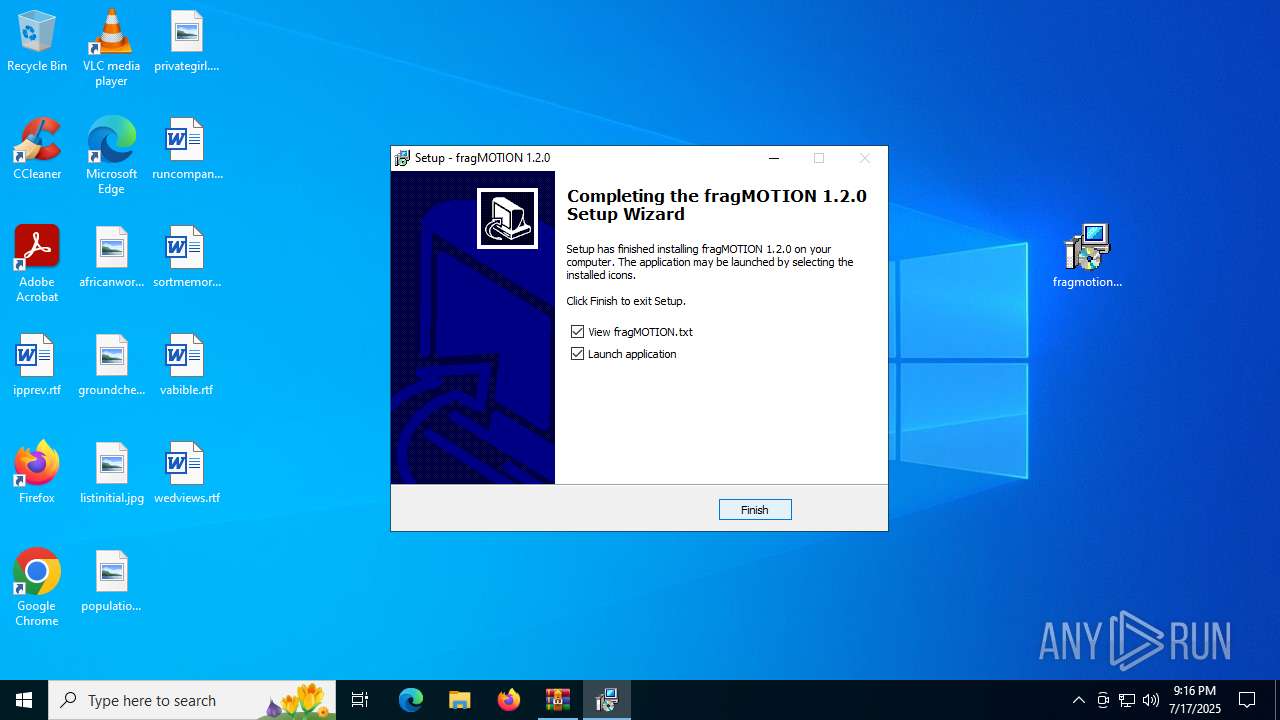
Creates a software uninstall entry
- fragmotion_120.tmp (PID: 5476)
The sample compiled with english language support
- fragmotion_120.tmp (PID: 5476)
Process checks computer location settings
- fragmotion_120.tmp (PID: 3860)
Creates files or folders in the user directory
- fragMOTION.exe (PID: 2032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2012:08:20 21:19:52 |
| ZipCRC: | 0x1e5fd58a |
| ZipCompressedSize: | 3887979 |
| ZipUncompressedSize: | 3912256 |
| ZipFileName: | fragmotion_120.exe |
Total processes
143
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1520 | "C:\Users\admin\Desktop\fragmotion_120.exe" | C:\Users\admin\Desktop\fragmotion_120.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: fragMOTION 1.2.0 Setup Exit code: 0 Version: 1.2.0.0 Modules
| |||||||||||||||
| 1592 | "C:\Program Files (x86)\Fragmosoft\fragMOTION 1.2.0\finish.exe" -C:\Program Files (x86)\Fragmosoft\fragMOTION 1.2.0\fragMOTION.exe | C:\Program Files (x86)\Fragmosoft\fragMOTION 1.2.0\finish.exe | — | fragmotion_120.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1660 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2032 | "C:\Program Files (x86)\Fragmosoft\fragMOTION 1.2.0\fragMOTION.exe" | C:\Program Files (x86)\Fragmosoft\fragMOTION 1.2.0\fragMOTION.exe | — | fragmotion_120.tmp | |||||||||||
User: admin Company: Fragmosoft Integrity Level: MEDIUM Description: fragMOTION Version: 1, 2, 0, 0 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\fragmotion_120.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3860 | "C:\Users\admin\AppData\Local\Temp\is-A9EAQ.tmp\fragmotion_120.tmp" /SL5="$902DC,3655013,54272,C:\Users\admin\Desktop\fragmotion_120.exe" | C:\Users\admin\AppData\Local\Temp\is-A9EAQ.tmp\fragmotion_120.tmp | — | fragmotion_120.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 5476 | "C:\Users\admin\AppData\Local\Temp\is-FI7C7.tmp\fragmotion_120.tmp" /SL5="$B02D6,3655013,54272,C:\Users\admin\Desktop\fragmotion_120.exe" /SPAWNWND=$B02F4 /NOTIFYWND=$902DC | C:\Users\admin\AppData\Local\Temp\is-FI7C7.tmp\fragmotion_120.tmp | fragmotion_120.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 5552 | "C:\Users\admin\Desktop\fragmotion_120.exe" /SPAWNWND=$B02F4 /NOTIFYWND=$902DC | C:\Users\admin\Desktop\fragmotion_120.exe | fragmotion_120.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: fragMOTION 1.2.0 Setup Exit code: 0 Version: 1.2.0.0 Modules
| |||||||||||||||
Total events
2 342
Read events
2 314
Write events
28
Delete events
0
Modification events
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\fragmotion_120.zip | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2524) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5476) fragmotion_120.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Fragmosoft\fragMOTION 1.2.0\CompileMDL |
| Operation: | write | Name: | Compiler |
Value: C:\Program Files (x86)\Fragmosoft\fragMOTION 1.2.0\studiomdl.exe | |||
| (PID) Process: | (5476) fragmotion_120.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Fragmosoft\fragMOTION 1.2.0\DecompileMDL |
| Operation: | write | Name: | Decompiler |
Value: C:\Program Files (x86)\Fragmosoft\fragMOTION 1.2.0\mdldec.exe | |||
Executable files
98
Suspicious files
8
Text files
450
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2524 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2524.26855\fragmotion_120.exe | executable | |
MD5:62F26E669AE527C9173CA8635DC6AE5D | SHA256:5629B3F0B6EA256BE323D5A4851705DE18E5DD5BBC97BDA1494EFEA388AFBF72 | |||
| 1520 | fragmotion_120.exe | C:\Users\admin\AppData\Local\Temp\is-A9EAQ.tmp\fragmotion_120.tmp | executable | |
MD5:8AA8C628F7B7B7F3E96EFF00557BD0BF | SHA256:14D4FA3EA6C3FBF6E9D284DE717E73A1EBB5E77F3D5C8C98808E40ADE359EA9D | |||
| 5476 | fragmotion_120.tmp | C:\Users\admin\AppData\Local\Temp\is-DUNJR.tmp\_isetup\_setup64.tmp | executable | |
MD5:4FF75F505FDDCC6A9AE62216446205D9 | SHA256:A4C86FC4836AC728D7BD96E7915090FD59521A9E74F1D06EF8E5A47C8695FD81 | |||
| 5476 | fragmotion_120.tmp | C:\Users\admin\AppData\Local\Temp\is-DUNJR.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:0EE914C6F0BB93996C75941E1AD629C6 | SHA256:4DC09BAC0613590F1FAC8771D18AF5BE25A1E1CB8FDBF4031AA364F3057E74A2 | |||
| 5476 | fragmotion_120.tmp | C:\Users\admin\AppData\Local\Temp\is-DUNJR.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 5552 | fragmotion_120.exe | C:\Users\admin\AppData\Local\Temp\is-FI7C7.tmp\fragmotion_120.tmp | executable | |
MD5:8AA8C628F7B7B7F3E96EFF00557BD0BF | SHA256:14D4FA3EA6C3FBF6E9D284DE717E73A1EBB5E77F3D5C8C98808E40ADE359EA9D | |||
| 5476 | fragmotion_120.tmp | C:\Program Files (x86)\Fragmosoft\fragMOTION 1.2.0\is-B5MRB.tmp | executable | |
MD5:2B8A6F2DD9673FAF117ABB70BEB5159F | SHA256:C5365237CEFD5F2B67FD96B7FCFF801A6EFB80F751C99DD2CDD0A3217B8DA313 | |||
| 5476 | fragmotion_120.tmp | C:\Program Files (x86)\Fragmosoft\fragMOTION 1.2.0\fragMOTION.exe | executable | |
MD5:1DFC992A8EF02B7679BD52094A9D4B73 | SHA256:3682C1C4E9DBBA8912781241434AB67F292011ADB75BEC236FA417344C59B895 | |||
| 5476 | fragmotion_120.tmp | C:\Program Files (x86)\Fragmosoft\fragMOTION 1.2.0\unins000.exe | executable | |
MD5:72858EDF667DB05238C85F166E8F5AF1 | SHA256:B3E87FBB2DBB5DA6078BBBF73D9D8607627F05A16D6B4171734399BFA3952DA7 | |||
| 5476 | fragmotion_120.tmp | C:\Program Files (x86)\Fragmosoft\fragMOTION 1.2.0\backface.bmp | image | |
MD5:0CCB0675E1494413F39A9652E39C2D3B | SHA256:D2870B721703190181359AF5B94C5EC2D546A538F76A96CF55DE5E8F69C58990 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2460 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2276 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2276 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
684 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.32:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2460 | svchost.exe | 20.190.160.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |