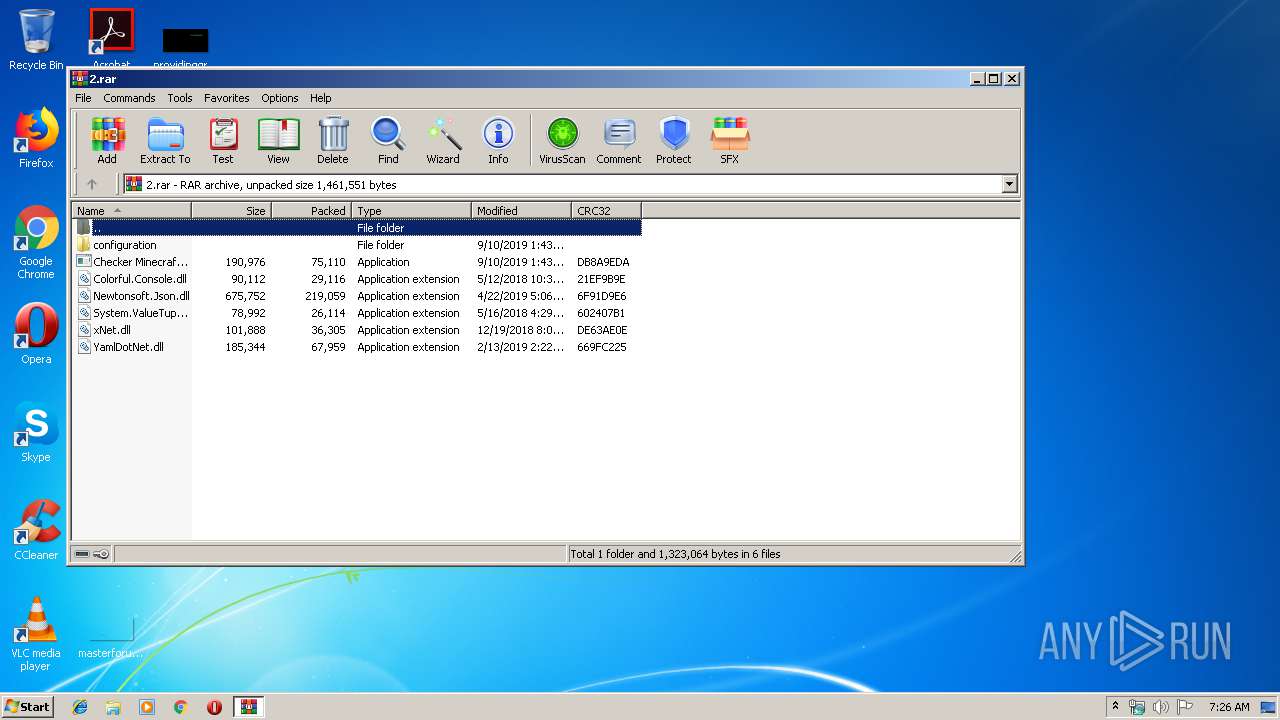
| File name: | 2.rar |
| Full analysis: | https://app.any.run/tasks/45661ed2-b27a-4283-a3c6-2cf2615cdb82 |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 06:26:03 |
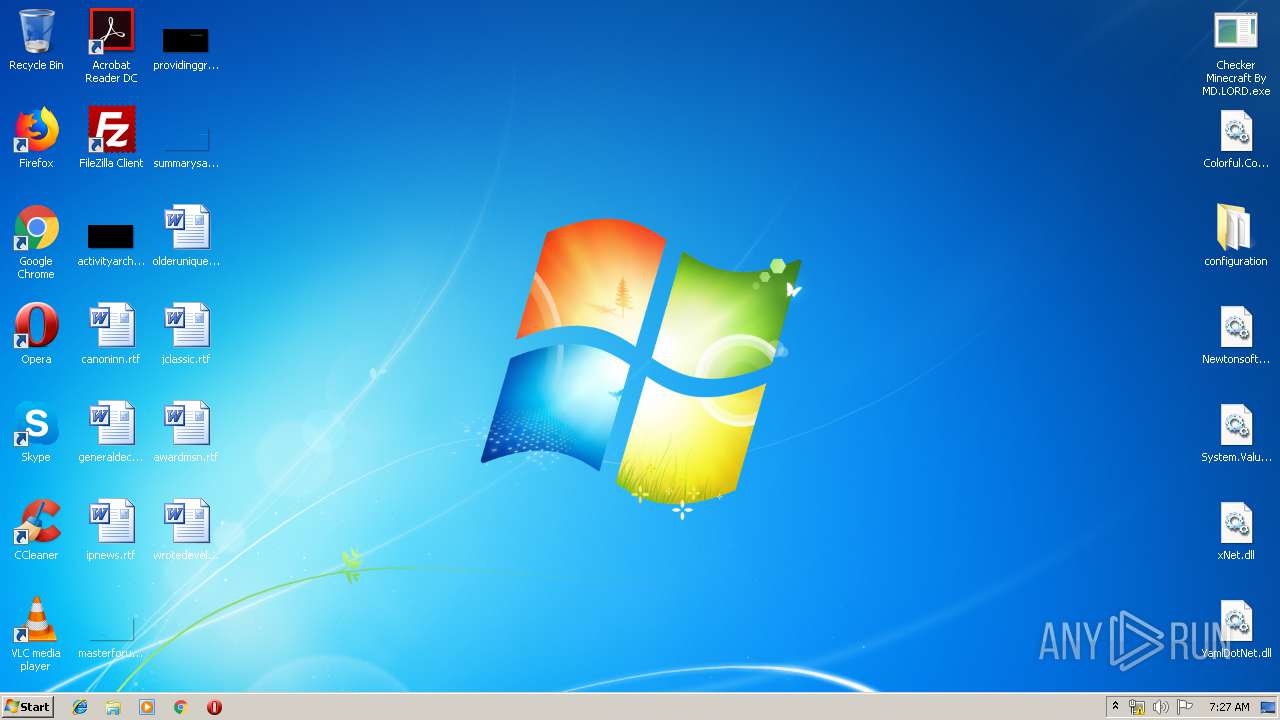
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 123C821A84C2F7B60C8D9DF44B8E5A8E |
| SHA1: | 023D7C8D9B9D24D6F1F58F666B92F2807E761B15 |
| SHA256: | 78786F8519A63410DEA010530B1B7E2E26C54BFA31AF49F2EF612F06C782C41D |
| SSDEEP: | 6144:DrSaHfkLH4POPnnFt8vlQBLLpdgwra4v4+KVBHipFiC0f6cUO716yNMRWIXABLRI:/KLH4WPnGlQBJJL46sANRpABLRXFUWXY |
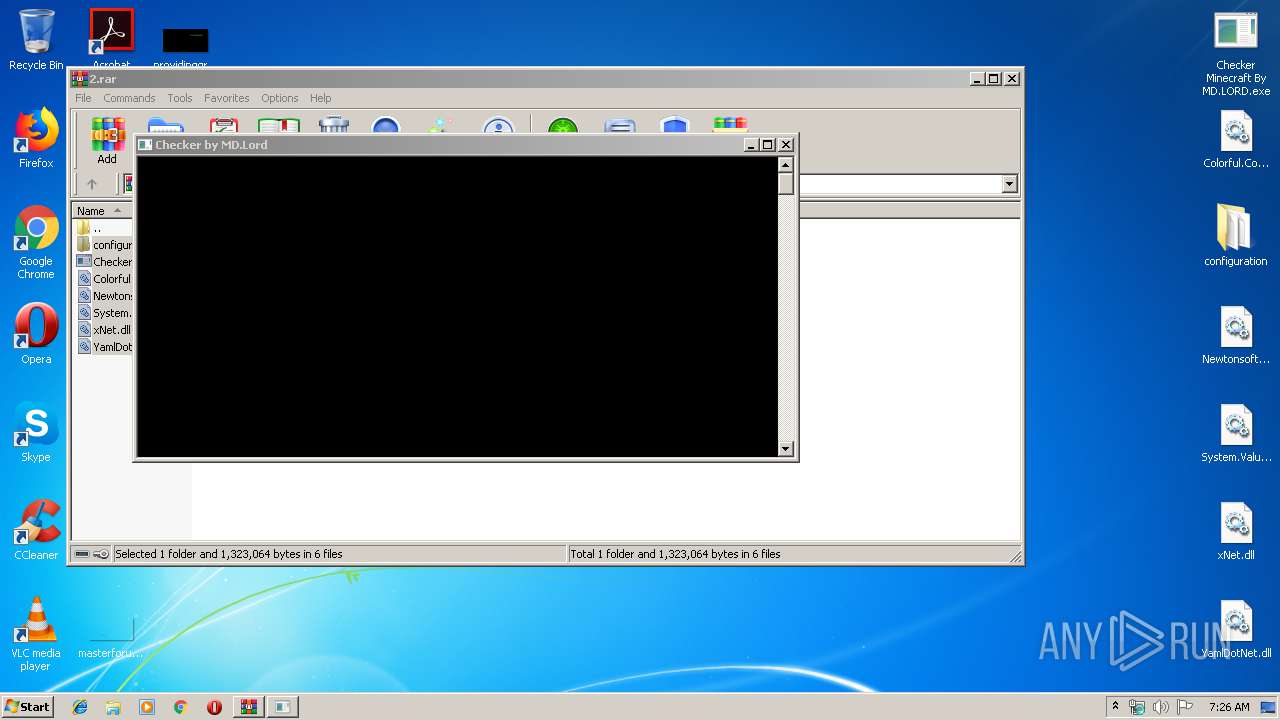
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 392)
- Checker Minecraft By MD.LORD.exe (PID: 3532)
- explorer.exe (PID: 276)
Application was dropped or rewritten from another process
- Checker Minecraft By MD.LORD.exe (PID: 3532)
SUSPICIOUS
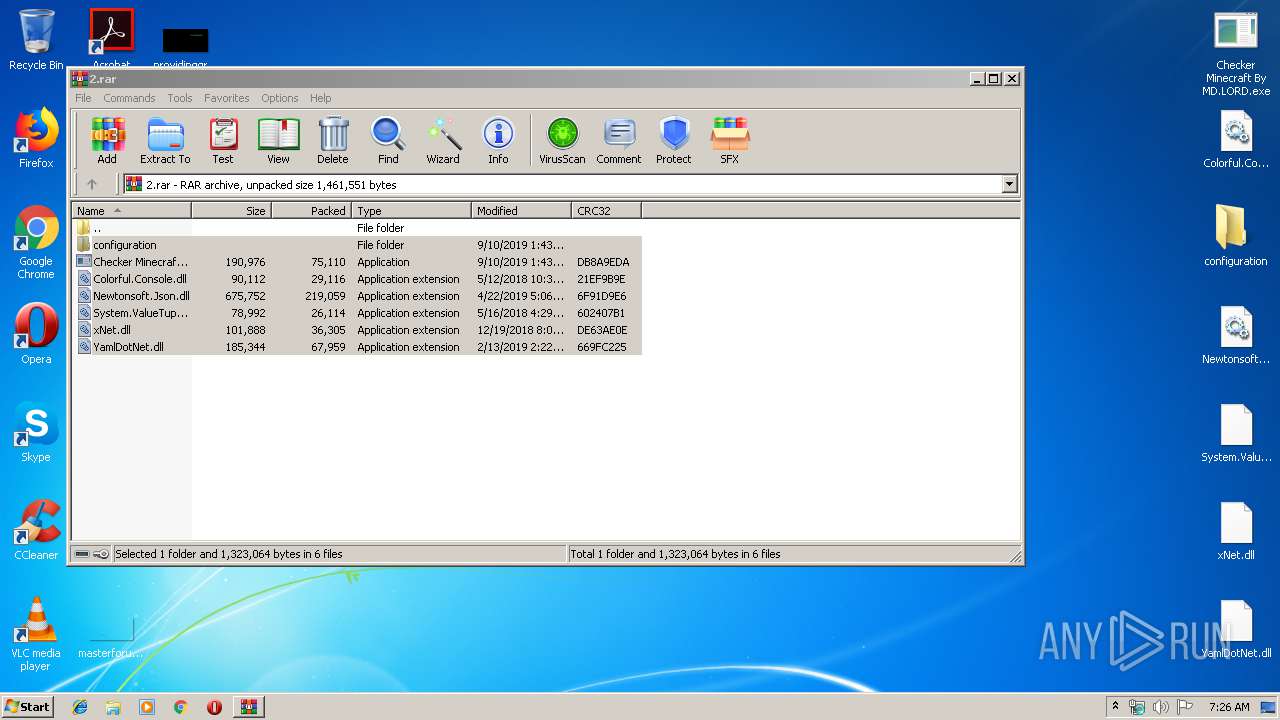
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2872)
Reads Environment values
- Checker Minecraft By MD.LORD.exe (PID: 3532)
INFO
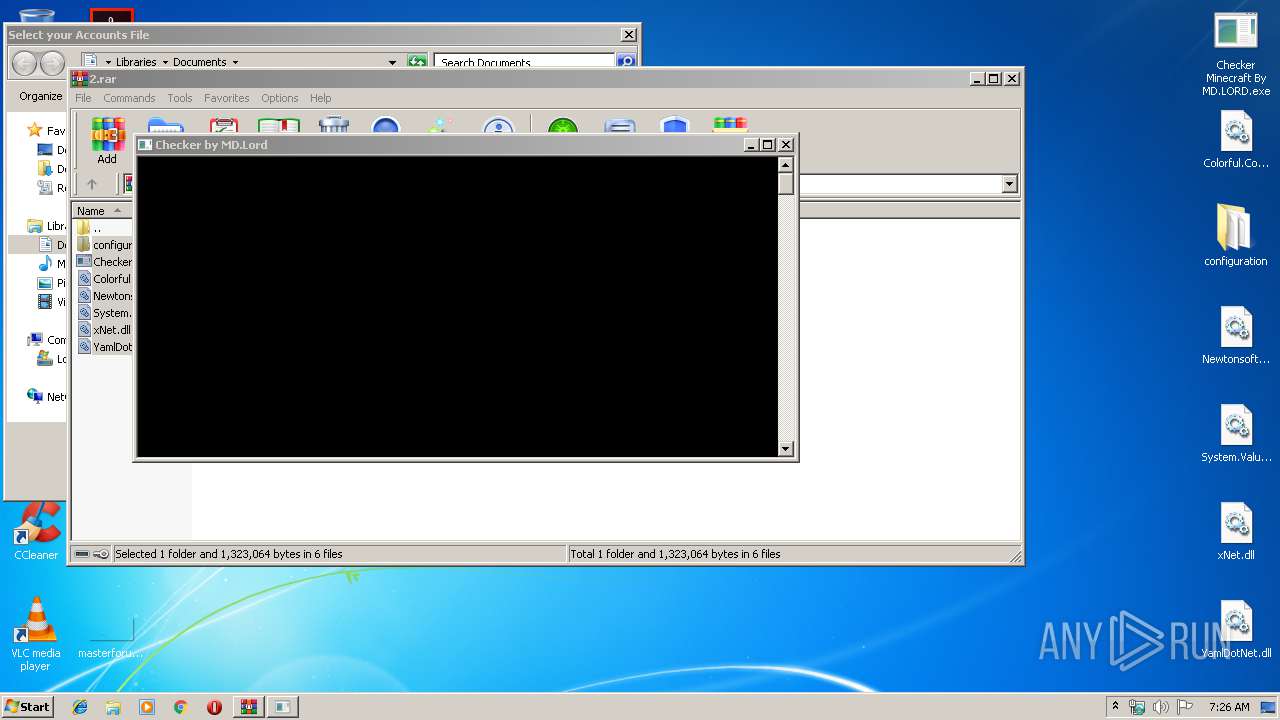
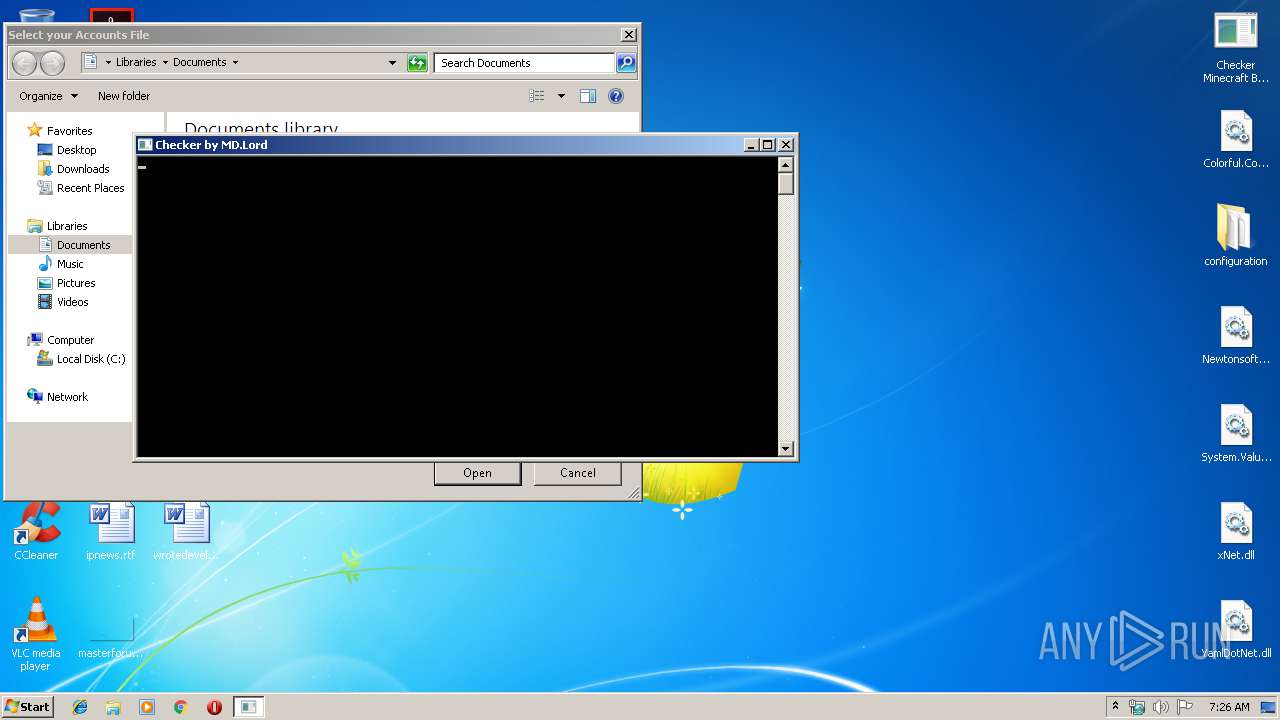
Manual execution by user
- Checker Minecraft By MD.LORD.exe (PID: 3532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
37
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2872 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\2.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3532 | "C:\Users\admin\Desktop\Checker Minecraft By MD.LORD.exe" | C:\Users\admin\Desktop\Checker Minecraft By MD.LORD.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: LZTest Exit code: 3221225786 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
2 238
Read events
2 165
Write events
73
Delete events
0
Modification events
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\2.rar | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
10
Suspicious files
0
Text files
3
Unknown types
0
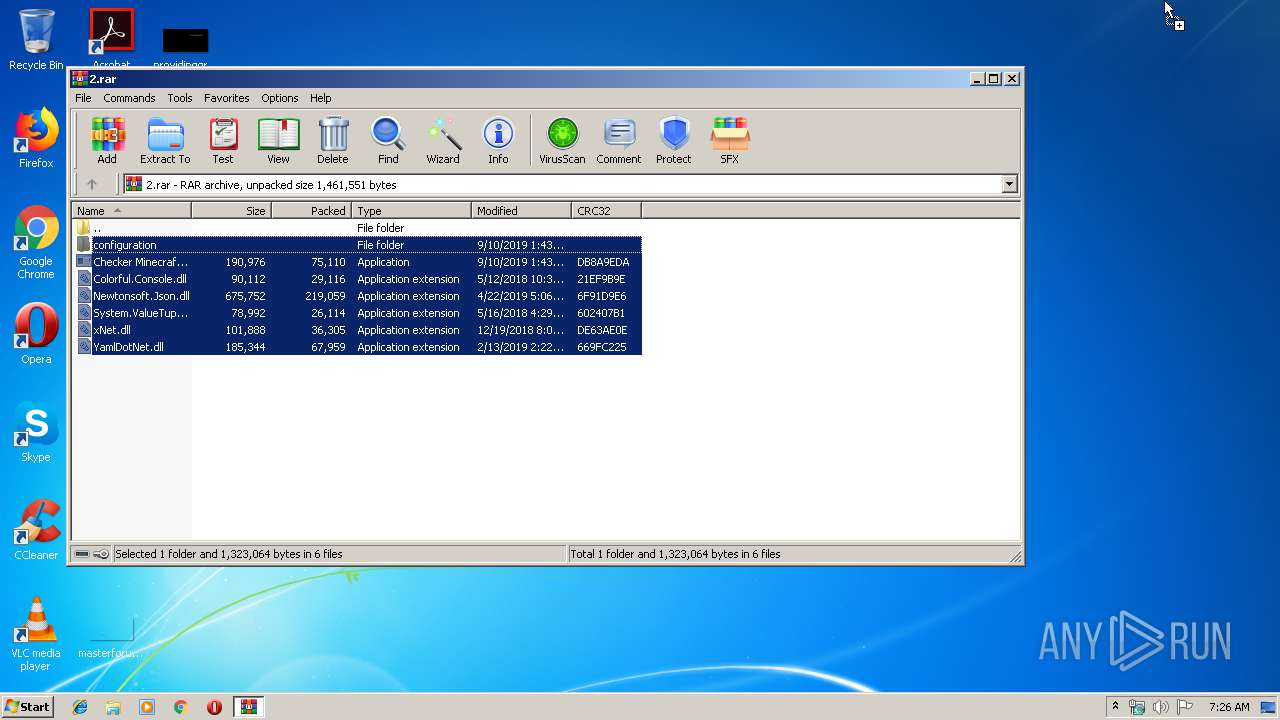
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2872.20806\Checker Minecraft By MD.LORD.exe | — | |
MD5:— | SHA256:— | |||
| 2872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2872.20806\Colorful.Console.dll | — | |
MD5:— | SHA256:— | |||
| 276 | explorer.exe | C:\Users\admin\Desktop\configuration | — | |
MD5:— | SHA256:— | |||
| 2872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2872.20806\configuration\mail-list.txt | text | |
MD5:— | SHA256:— | |||
| 276 | explorer.exe | C:\Users\admin\Desktop\Checker Minecraft By MD.LORD.exe | executable | |
MD5:— | SHA256:— | |||
| 2872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2872.20806\configuration\og-names.txt | text | |
MD5:— | SHA256:— | |||
| 2872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2872.20806\configuration\config.yml | text | |
MD5:— | SHA256:— | |||
| 276 | explorer.exe | C:\Users\admin\Desktop\Newtonsoft.Json.dll | executable | |
MD5:4DF6C8781E70C3A4912B5BE796E6D337 | SHA256:3598CCCAD5B535FEA6F93662107A4183BFD6167BF1D0F80260436093EDC2E3AF | |||
| 276 | explorer.exe | C:\Users\admin\Desktop\Colorful.Console.dll | executable | |
MD5:AC1A142F7F25B35C48D5B4FB04C3F821 | SHA256:4F228EC1979076FDA183D9B87045A79E5FC116BDE28F931886F043FAE2081B71 | |||
| 276 | explorer.exe | C:\Users\admin\Desktop\YamlDotNet.dll | executable | |
MD5:7C6265507A9F201C0DE4DE5D37D65054 | SHA256:2784A032C3056C89DB9710E6B30D068A125A9BD1733D74B2B1BB7508B1ECE5EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
2
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3532 | Checker Minecraft By MD.LORD.exe | 162.159.133.233:443 | discordapp.com | Cloudflare Inc | — | shared |
3532 | Checker Minecraft By MD.LORD.exe | 198.27.74.146:443 | wtfismyip.com | OVH SAS | CA | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wtfismyip.com |
| shared |
discordapp.com |
| whitelisted |
Threats
4 ETPRO signatures available at the full report