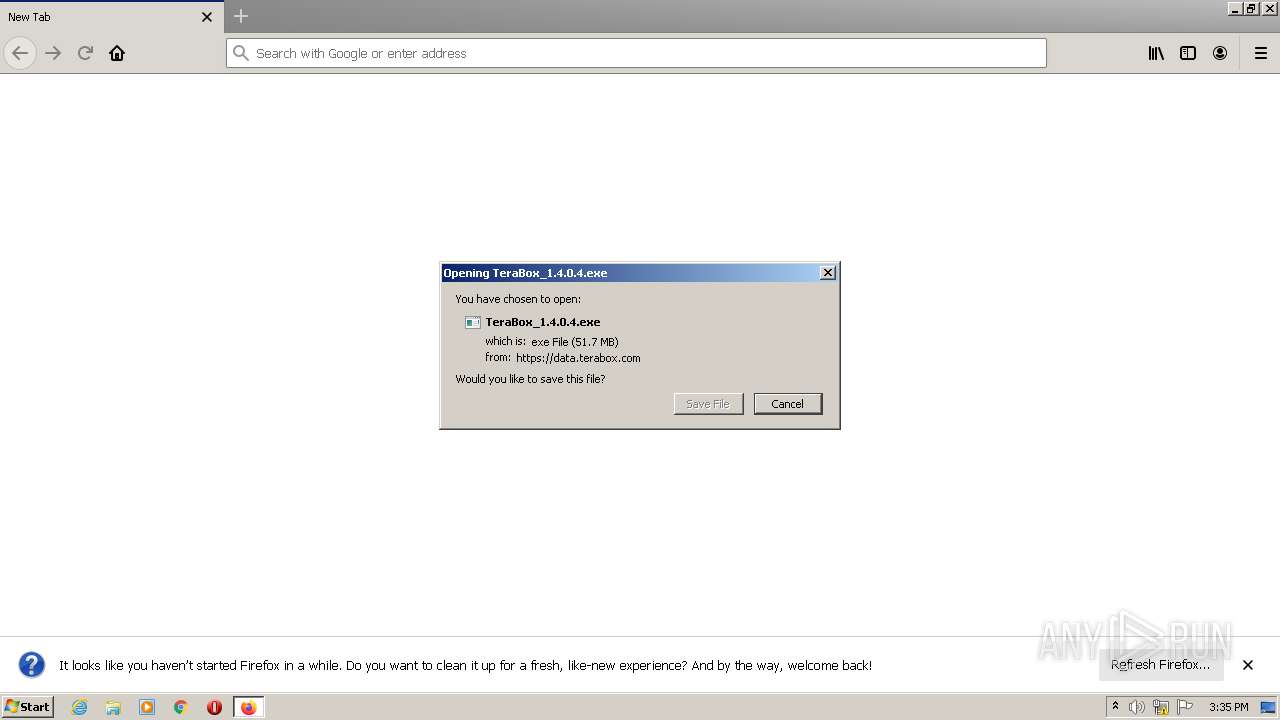
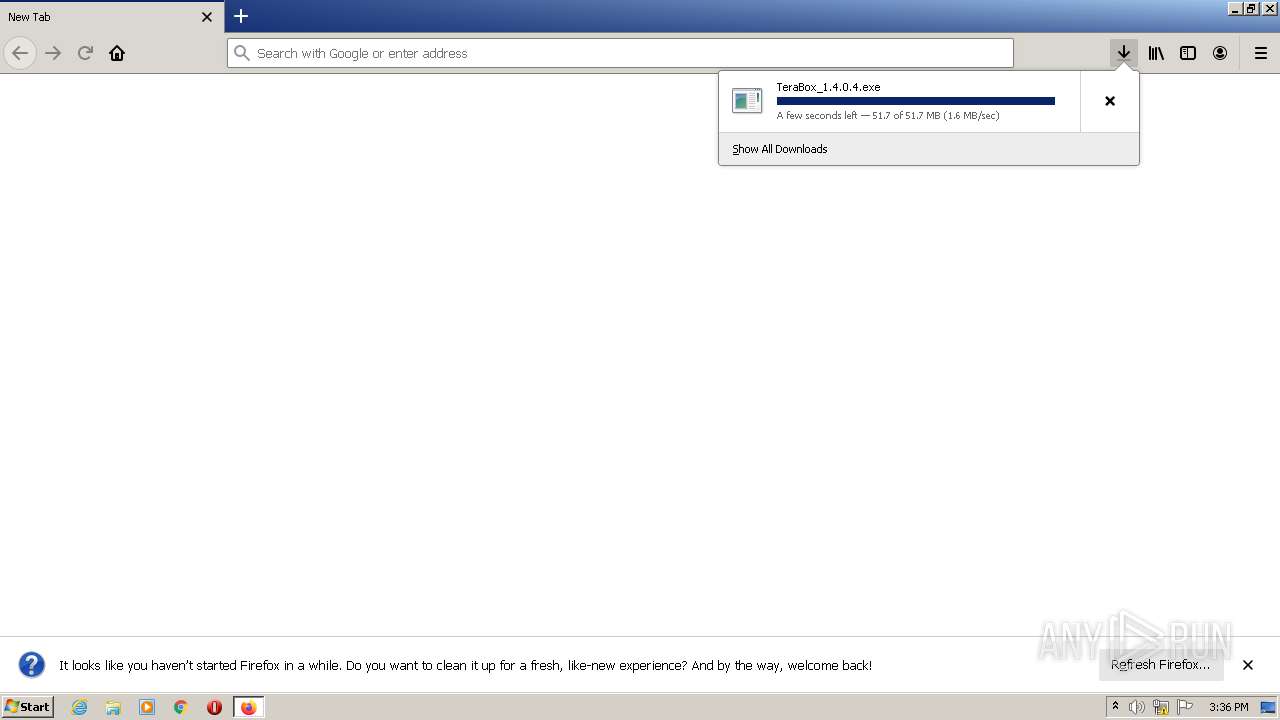
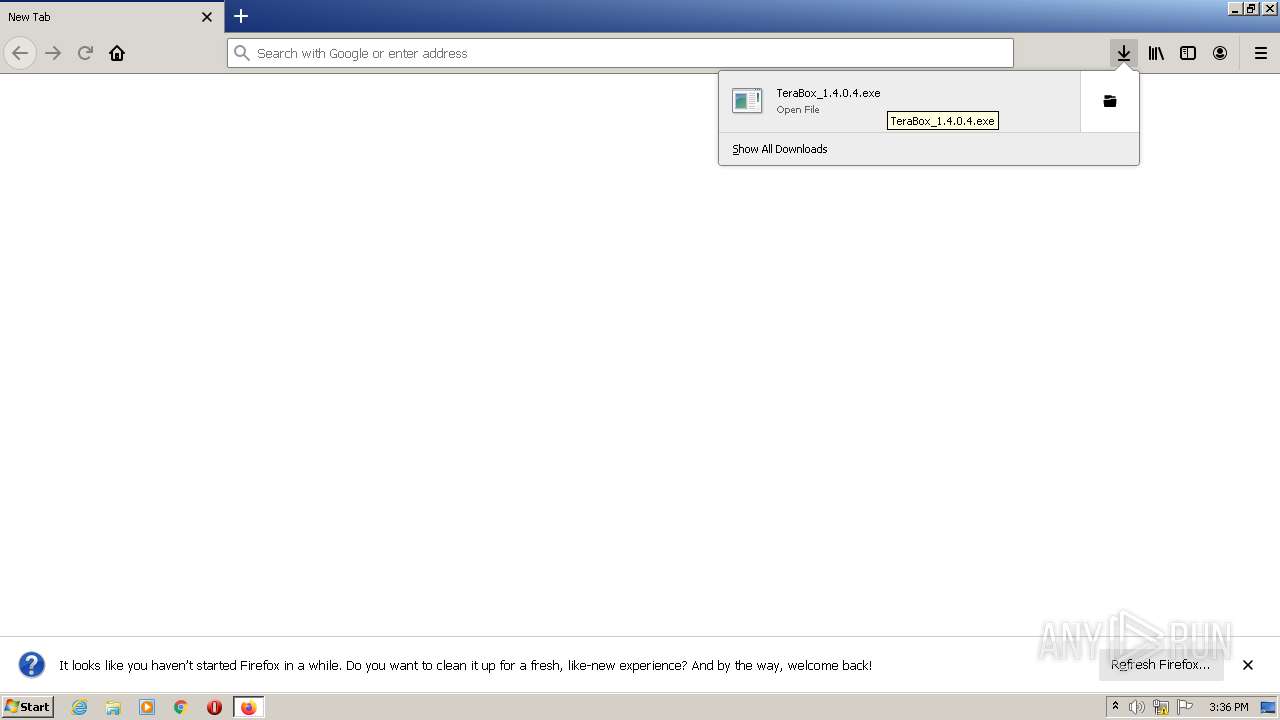
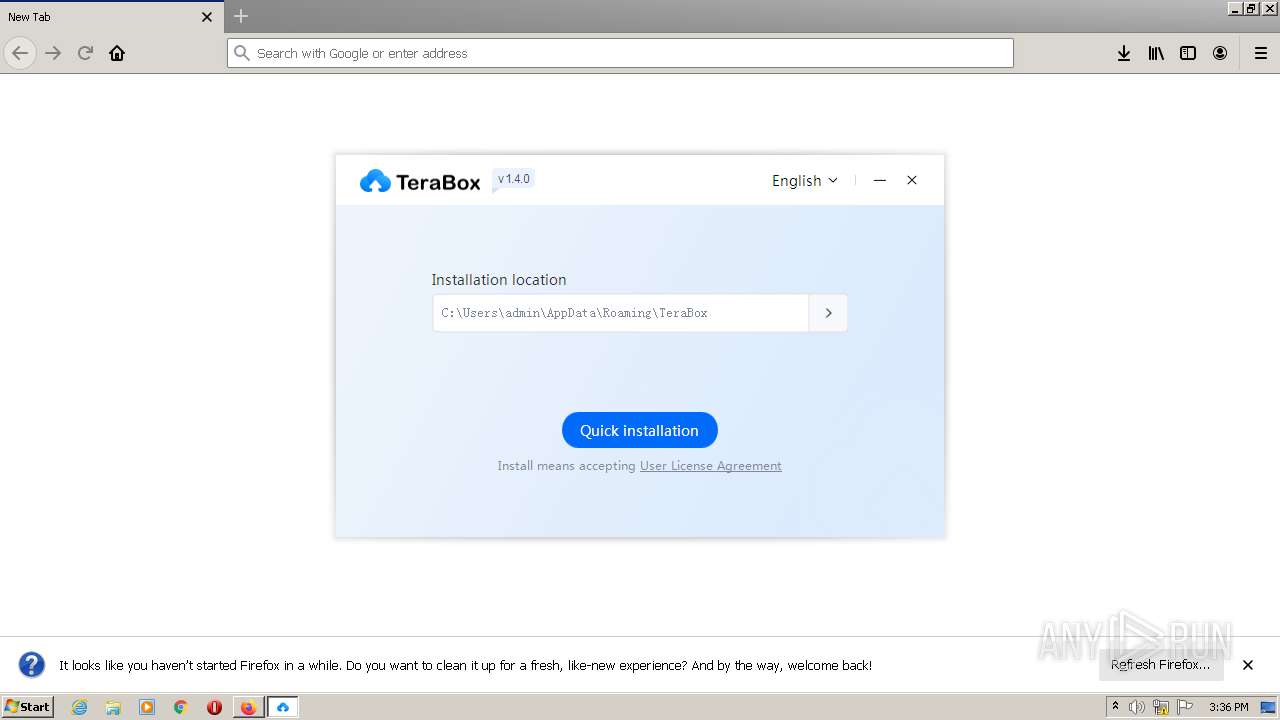
| URL: | https://data.terabox.com/issue/terabox/PCTeraBox/TeraBox_1.4.0.4.exe |
| Full analysis: | https://app.any.run/tasks/3a5b0fb7-b12e-4a47-9190-8b69466f4705 |
| Verdict: | Malicious activity |
| Analysis date: | February 04, 2022, 15:35:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DF0F1C7E71F7AA09853D0D41EA723972 |
| SHA1: | 708762D2F3F10FB00102EAC954A9A66DE730D84B |
| SHA256: | 787650365A32884937A546956CDC2B0C9C6831092E821F2A5F9CA0364501078F |
| SSDEEP: | 3:N8cily+2JAVVAX7+Kdr7:2ch+KAVVAX7+Kdr7 |
MALICIOUS
Application was dropped or rewritten from another process
- TeraBox_1.4.0.4.exe (PID: 3628)
- TeraBox_1.4.0.4.exe (PID: 2516)
- TeraBox.exe (PID: 3484)
- YunUtilityService.exe (PID: 3880)
- YunWebService.exe (PID: 3364)
- YunWebService.exe (PID: 2068)
- TeraBox.exe (PID: 2640)
- TeraBoxRender.exe (PID: 2408)
- YunUtilityService.exe (PID: 3600)
- TeraBoxHost.exe (PID: 3796)
- TeraBoxHost.exe (PID: 3792)
- TeraBoxHost.exe (PID: 3484)
- TeraBoxRender.exe (PID: 1248)
- AutoUpdate.exe (PID: 3996)
Loads dropped or rewritten executable
- TeraBox_1.4.0.4.exe (PID: 2516)
- TeraBox.exe (PID: 3484)
- YunWebService.exe (PID: 3364)
- YunUtilityService.exe (PID: 3880)
- TeraBox.exe (PID: 2640)
- YunWebService.exe (PID: 2068)
- TeraBoxRender.exe (PID: 2408)
- YunUtilityService.exe (PID: 3600)
- TeraBoxHost.exe (PID: 3796)
- TeraBoxHost.exe (PID: 3792)
- TeraBoxHost.exe (PID: 3484)
- TeraBoxRender.exe (PID: 1248)
Registers / Runs the DLL via REGSVR32.EXE
- TeraBox_1.4.0.4.exe (PID: 2516)
Changes the autorun value in the registry
- TeraBox.exe (PID: 3484)
Changes settings of System certificates
- YunUtilityService.exe (PID: 3600)
SUSPICIOUS
Executable content was dropped or overwritten
- firefox.exe (PID: 4040)
- TeraBox_1.4.0.4.exe (PID: 2516)
Reads Environment values
- TeraBox_1.4.0.4.exe (PID: 2516)
Drops a file with a compile date too recent
- TeraBox_1.4.0.4.exe (PID: 2516)
Drops a file that was compiled in debug mode
- TeraBox_1.4.0.4.exe (PID: 2516)
Checks supported languages
- TeraBox_1.4.0.4.exe (PID: 2516)
- TeraBox.exe (PID: 3484)
- YunWebService.exe (PID: 3364)
- YunUtilityService.exe (PID: 3880)
- TeraBox.exe (PID: 2640)
- YunWebService.exe (PID: 2068)
- TeraBoxRender.exe (PID: 2408)
- YunUtilityService.exe (PID: 3600)
- TeraBoxHost.exe (PID: 3796)
- TeraBoxHost.exe (PID: 3792)
- TeraBoxHost.exe (PID: 3484)
- TeraBoxRender.exe (PID: 1248)
- AutoUpdate.exe (PID: 3996)
Reads the computer name
- TeraBox_1.4.0.4.exe (PID: 2516)
- TeraBox.exe (PID: 3484)
- YunUtilityService.exe (PID: 3880)
- YunWebService.exe (PID: 2068)
- TeraBox.exe (PID: 2640)
- YunUtilityService.exe (PID: 3600)
- TeraBoxHost.exe (PID: 3796)
- TeraBoxHost.exe (PID: 3792)
- AutoUpdate.exe (PID: 3996)
Creates files in the user directory
- TeraBox.exe (PID: 3484)
- TeraBox_1.4.0.4.exe (PID: 2516)
- TeraBox.exe (PID: 2640)
- TeraBoxRender.exe (PID: 2408)
- YunWebService.exe (PID: 2068)
- TeraBoxHost.exe (PID: 3796)
- AutoUpdate.exe (PID: 3996)
Reads the date of Windows installation
- TeraBox.exe (PID: 3484)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2140)
- regsvr32.exe (PID: 2408)
Creates a software uninstall entry
- TeraBox_1.4.0.4.exe (PID: 2516)
Changes default file association
- YunWebService.exe (PID: 3364)
Executed as Windows Service
- YunUtilityService.exe (PID: 3600)
Adds / modifies Windows certificates
- YunUtilityService.exe (PID: 3600)
Creates files in the Windows directory
- YunUtilityService.exe (PID: 3600)
INFO
Application launched itself
- firefox.exe (PID: 3636)
- firefox.exe (PID: 4040)
Checks supported languages
- firefox.exe (PID: 2732)
- firefox.exe (PID: 4040)
- firefox.exe (PID: 3636)
- firefox.exe (PID: 3956)
- firefox.exe (PID: 2792)
- firefox.exe (PID: 1872)
- firefox.exe (PID: 1448)
- regsvr32.exe (PID: 2408)
- regsvr32.exe (PID: 2140)
Reads the computer name
- firefox.exe (PID: 2732)
- firefox.exe (PID: 1872)
- firefox.exe (PID: 2792)
- firefox.exe (PID: 4040)
- firefox.exe (PID: 1448)
- firefox.exe (PID: 3956)
Reads CPU info
- firefox.exe (PID: 4040)
Creates files in the user directory
- firefox.exe (PID: 4040)
Creates files in the program directory
- firefox.exe (PID: 4040)
Checks Windows Trust Settings
- firefox.exe (PID: 4040)
- TeraBox.exe (PID: 2640)
- YunWebService.exe (PID: 2068)
- YunUtilityService.exe (PID: 3600)
Reads settings of System Certificates
- firefox.exe (PID: 4040)
- TeraBox.exe (PID: 2640)
- YunWebService.exe (PID: 2068)
- YunUtilityService.exe (PID: 3600)
Dropped object may contain Bitcoin addresses
- TeraBox_1.4.0.4.exe (PID: 2516)
Reads the date of Windows installation
- firefox.exe (PID: 4040)
Reads the hosts file
- TeraBox.exe (PID: 2640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
23
Malicious processes
12
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1248 | "C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxRender.exe" --type=utility --channel="2640.1.951940373\2039090129" --lang=en-US --no-sandbox --no-sandbox --lang=en-US --locales-dir-path="C:\Users\admin\AppData\Roaming\TeraBox\browserres\locales" --log-file="C:\Users\admin\AppData\Roaming\TeraBox\debug.log" --log-severity=disable --resources-dir-path="C:\Users\admin\AppData\Roaming\TeraBox\browserres" --user-agent="Mozilla/5.0; (Windows NT 6.1); AppleWebKit/537.36; (KHTML, like Gecko); Chrome/49.0.2623.110; Safari/537.36; terabox;1.4.0.4;PC;PC-Windows;6.1.7601;WindowsTeraBox" /prefetch:8 | C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxRender.exe | — | TeraBox.exe | |||||||||||
User: admin Company: Flextech Inc. Integrity Level: MEDIUM Description: TeraBoxRender Exit code: 0 Version: 2.0.1.1 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4040.6.3089490\740757383" -childID 1 -isForBrowser -prefsHandle 3044 -prefMapHandle 3040 -prefsLen 245 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 4040 "\\.\pipe\gecko-crash-server-pipe.4040" 3056 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1872 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4040.13.642008184\1309640257" -childID 2 -isForBrowser -prefsHandle 2412 -prefMapHandle 2464 -prefsLen 6644 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 4040 "\\.\pipe\gecko-crash-server-pipe.4040" 2384 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2068 | C:\Users\admin\AppData\Roaming\TeraBox\YunWebService.exe | C:\Users\admin\AppData\Roaming\TeraBox\YunWebService.exe | TeraBox_1.4.0.4.exe | ||||||||||||
User: admin Company: Flextech Inc. Integrity Level: MEDIUM Description: YunWebService Exit code: 0 Version: 1.4.0.4 Modules
| |||||||||||||||
| 2140 | "C:\Windows\system32\regsvr32.exe" "/s" "C:\Users\admin\AppData\Roaming\TeraBox\npYunWebDetect.dll" | C:\Windows\system32\regsvr32.exe | — | TeraBox_1.4.0.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2408 | "C:\Windows\system32\regsvr32.exe" "/s" "C:\Users\admin\AppData\Roaming\TeraBox\YunShellExt.dll" | C:\Windows\system32\regsvr32.exe | — | TeraBox_1.4.0.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2408 | "C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxRender.exe" --type=renderer --no-sandbox --lang=en-US --lang=en-US --locales-dir-path="C:\Users\admin\AppData\Roaming\TeraBox\browserres\locales" --log-file="C:\Users\admin\AppData\Roaming\TeraBox\debug.log" --log-severity=disable --resources-dir-path="C:\Users\admin\AppData\Roaming\TeraBox\browserres" --user-agent="Mozilla/5.0; (Windows NT 6.1); AppleWebKit/537.36; (KHTML, like Gecko); Chrome/49.0.2623.110; Safari/537.36; terabox;1.4.0.4;PC;PC-Windows;6.1.7601;WindowsTeraBox" --disable-extensions --ppapi-flash-path="C:\Users\admin\AppData\Roaming\TeraBox\pepflashplayer.dll" --ppapi-flash-version=20.0.0.306 --device-scale-factor=1 --num-raster-threads=2 --content-image-texture-target=3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2640.0.2120592654\849306451" /prefetch:1 | C:\Users\admin\AppData\Roaming\TeraBox\TeraBoxRender.exe | — | TeraBox.exe | |||||||||||
User: admin Company: Flextech Inc. Integrity Level: MEDIUM Description: TeraBoxRender Exit code: 0 Version: 2.0.1.1 Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\Downloads\TeraBox_1.4.0.4.exe" | C:\Users\admin\Downloads\TeraBox_1.4.0.4.exe | firefox.exe | ||||||||||||
User: admin Company: Flextech Integrity Level: HIGH Description: TeraBox Installer Exit code: 2 Version: 1.4.0.4 Modules
| |||||||||||||||
| 2640 | C:\Users\admin\AppData\Roaming\TeraBox\TeraBox.exe | C:\Users\admin\AppData\Roaming\TeraBox\TeraBox.exe | TeraBox_1.4.0.4.exe | ||||||||||||
User: admin Company: Flextech Inc. Integrity Level: MEDIUM Description: TeraBox Exit code: 0 Version: 1.4.0.4 Modules
| |||||||||||||||
| 2732 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="4040.0.747823453\2024456920" -parentBuildID 20201112153044 -prefsHandle 1108 -prefMapHandle 892 -prefsLen 1 -prefMapSize 238726 -appdir "C:\Program Files\Mozilla Firefox\browser" - 4040 "\\.\pipe\gecko-crash-server-pipe.4040" 1188 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
Total events
36 398
Read events
35 887
Write events
491
Delete events
20
Modification events
| (PID) Process: | (3636) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 12C032D574000000 | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 7BC732D574000000 | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|ServicesSettingsServer |
Value: https://firefox.settings.services.mozilla.com/v1 | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SecurityContentSignatureRootHash |
Value: 97:E8:BA:9C:F1:2F:B3:DE:53:CC:42:A4:E6:57:7E:D6:4D:F4:93:C2:47:B4:14:FE:A0:36:81:8D:38:23:56:0E | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4040) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
79
Suspicious files
167
Text files
42
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4040 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionstore-backups\recovery.jsonlz4.tmp | jsonlz4 | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_ORSm5fG40RGaABF | binary | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionstore-backups\recovery.jsonlz4 | jsonlz4 | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:— | SHA256:— | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4040 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
120
DNS requests
102
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3996 | AutoUpdate.exe | GET | 200 | 210.154.124.148:80 | http://www.terabox.com/autoupdate | JP | — | — | unknown |
4040 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4040 | firefox.exe | POST | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr3dvtlsca2020 | US | der | 1.39 Kb | whitelisted |
4040 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
4040 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2068 | YunWebService.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHe9DgdC1dnp0EnXdNAqb5o%3D | US | der | 1.40 Kb | whitelisted |
4040 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3600 | YunUtilityService.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAxPYp2eJgrWa%2BdSWltJyU0%3D | US | der | 727 b | whitelisted |
2640 | TeraBox.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
4040 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4040 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
4040 | firefox.exe | 35.86.38.2:443 | push.services.mozilla.com | Merit Network Inc. | US | unknown |
4040 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4040 | firefox.exe | 210.154.124.144:443 | data.terabox.com | NTT Communications Corporation | JP | unknown |
4040 | firefox.exe | 142.250.185.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
4040 | firefox.exe | 13.224.189.54:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
4040 | firefox.exe | 104.18.20.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
4040 | firefox.exe | 52.88.6.42:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
4040 | firefox.exe | 13.224.189.113:443 | snippets.cdn.mozilla.net | — | US | suspicious |
4040 | firefox.exe | 13.225.80.100:443 | firefox-settings-attachments.cdn.mozilla.net | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
data.terabox.com |
| unknown |
location.services.mozilla.com |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
cdn.globalsigncdn.com.cdn.cloudflare.net |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4040 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
4040 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
4040 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
4040 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |